| File name: | 2025-05-18_98c0bfa620856a8084ad59e2313b3a53_black-basta_hacktools_mimikatz |
| Full analysis: | https://app.any.run/tasks/4ea36160-768a-4a10-8e57-71ac123c9b94 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 10:25:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 98C0BFA620856A8084AD59E2313B3A53 |
| SHA1: | CAC621518C83F972D7DA7DC75D711907245EE847 |
| SHA256: | CA2DA04FEF5AB84D873E3C11A0852DB4203925835FD2B78CEC07F04222BDA9AB |
| SSDEEP: | 49152:6ZMe5W265pQL8j+U8vGt1OF8KTUc/bcA:gEw8CZvm1OF8KTUcwA |
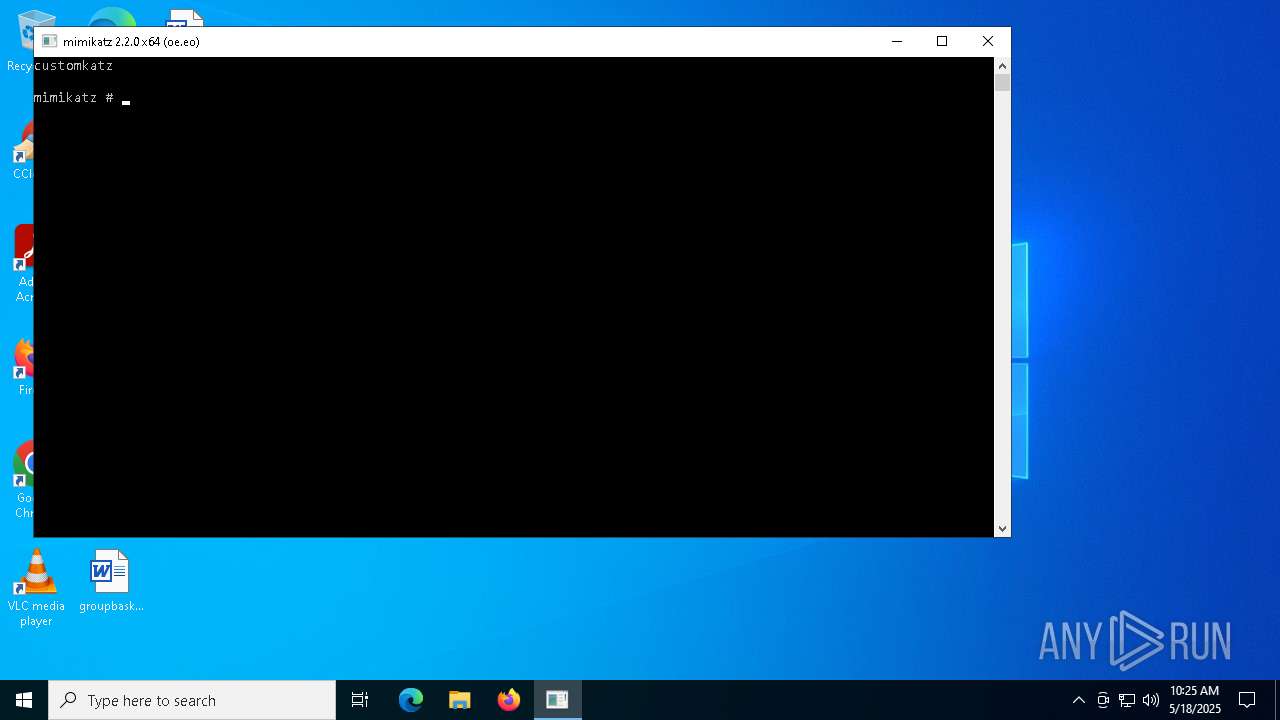
MALICIOUS
MIMIKATZ has been detected (YARA)
- 2025-05-18_98c0bfa620856a8084ad59e2313b3a53_black-basta_hacktools_mimikatz.exe (PID: 7372)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- 2025-05-18_98c0bfa620856a8084ad59e2313b3a53_black-basta_hacktools_mimikatz.exe (PID: 7372)
The sample compiled with english language support
- 2025-05-18_98c0bfa620856a8084ad59e2313b3a53_black-basta_hacktools_mimikatz.exe (PID: 7372)
Reads the computer name
- 2025-05-18_98c0bfa620856a8084ad59e2313b3a53_black-basta_hacktools_mimikatz.exe (PID: 7372)
Checks proxy server information
- slui.exe (PID: 7788)
Reads the software policy settings
- slui.exe (PID: 7788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:16 20:58:42+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 923648 |
| InitializedDataSize: | 541696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc2f38 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 2.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Pre-release, Private build, Special build |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | kmssrv |
| ProductVersion: | 1.0.0.1 |
| CompanyName: | kmssrv |
| FileDescription: | kmssrv |
| FileVersion: | 1.0.0.0 |
| InternalName: | kmssrv |
| LegalCopyright: | kmssrv |
| OriginalFileName: | kmssrv |
| PrivateBuild: | kmssrv |
| SpecialBuild: | kmssrv |
Total processes
124
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7372 | "C:\Users\admin\Desktop\2025-05-18_98c0bfa620856a8084ad59e2313b3a53_black-basta_hacktools_mimikatz.exe" | C:\Users\admin\Desktop\2025-05-18_98c0bfa620856a8084ad59e2313b3a53_black-basta_hacktools_mimikatz.exe | explorer.exe | ||||||||||||
User: admin Company: kmssrv Integrity Level: MEDIUM Description: kmssrv Version: 1.0.0.0 Modules
| |||||||||||||||
| 7380 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 2025-05-18_98c0bfa620856a8084ad59e2313b3a53_black-basta_hacktools_mimikatz.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7788 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 410
Read events
3 410
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
23
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7260 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7788 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |