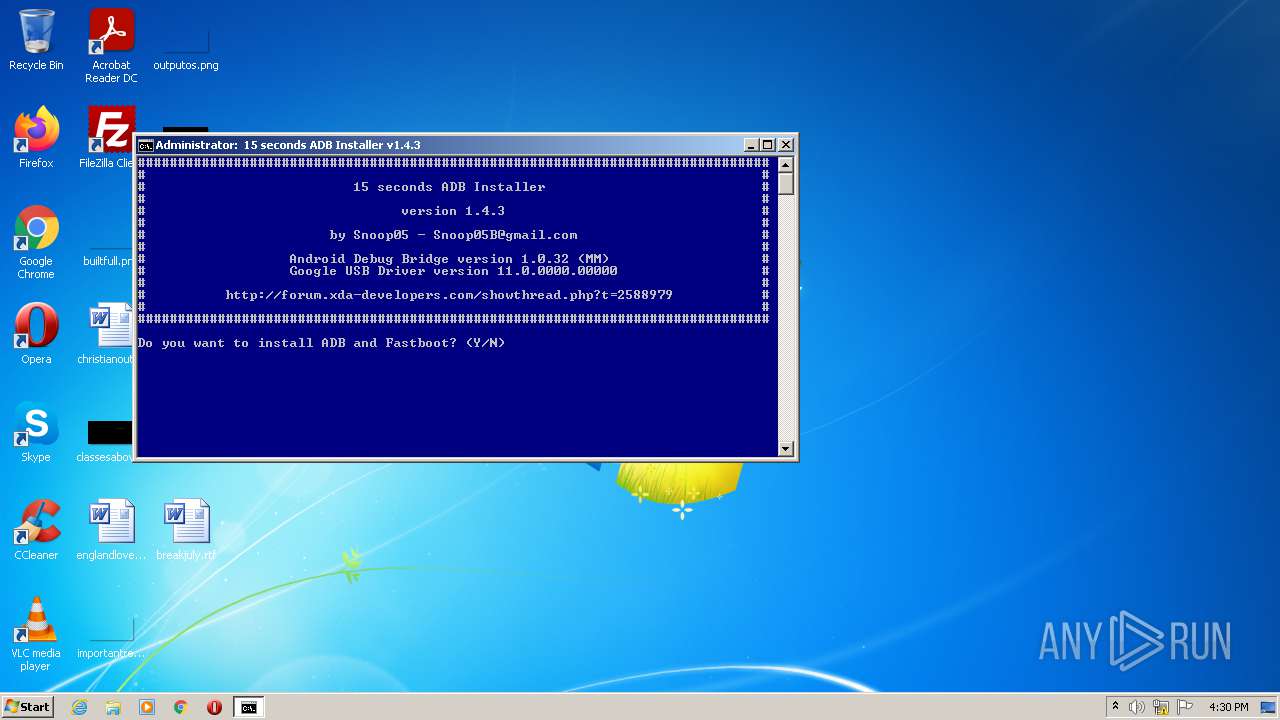
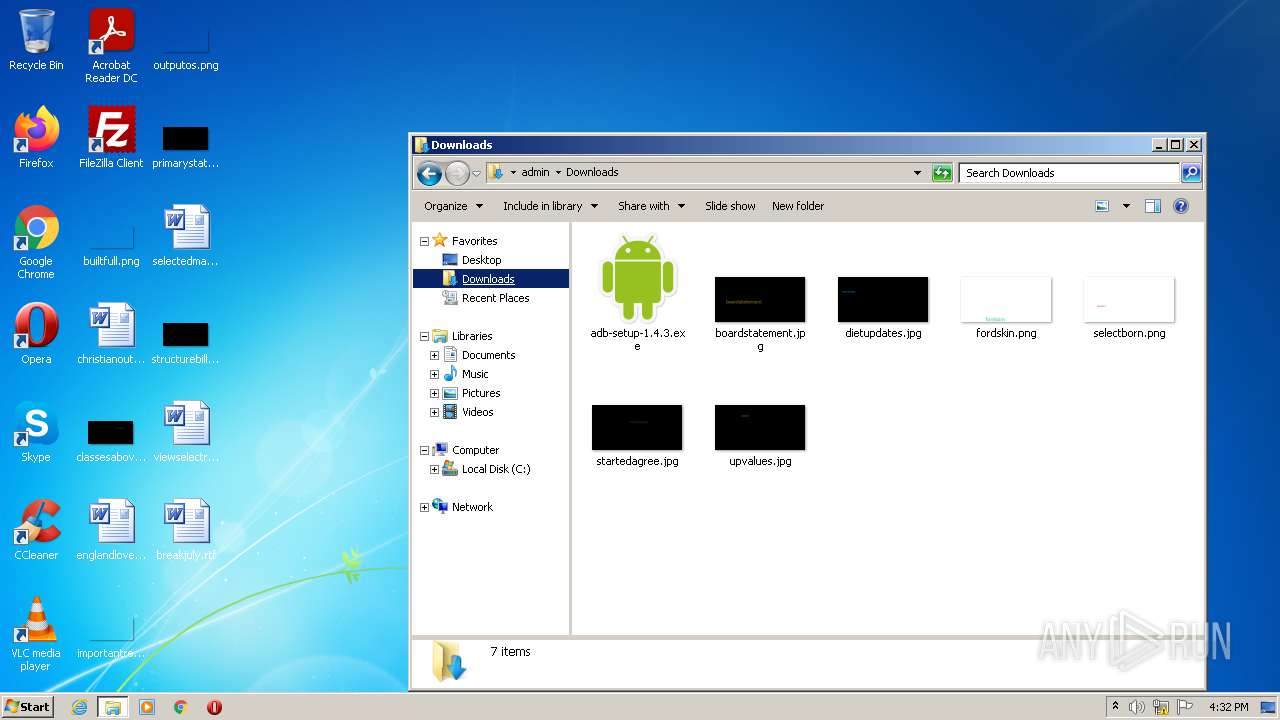
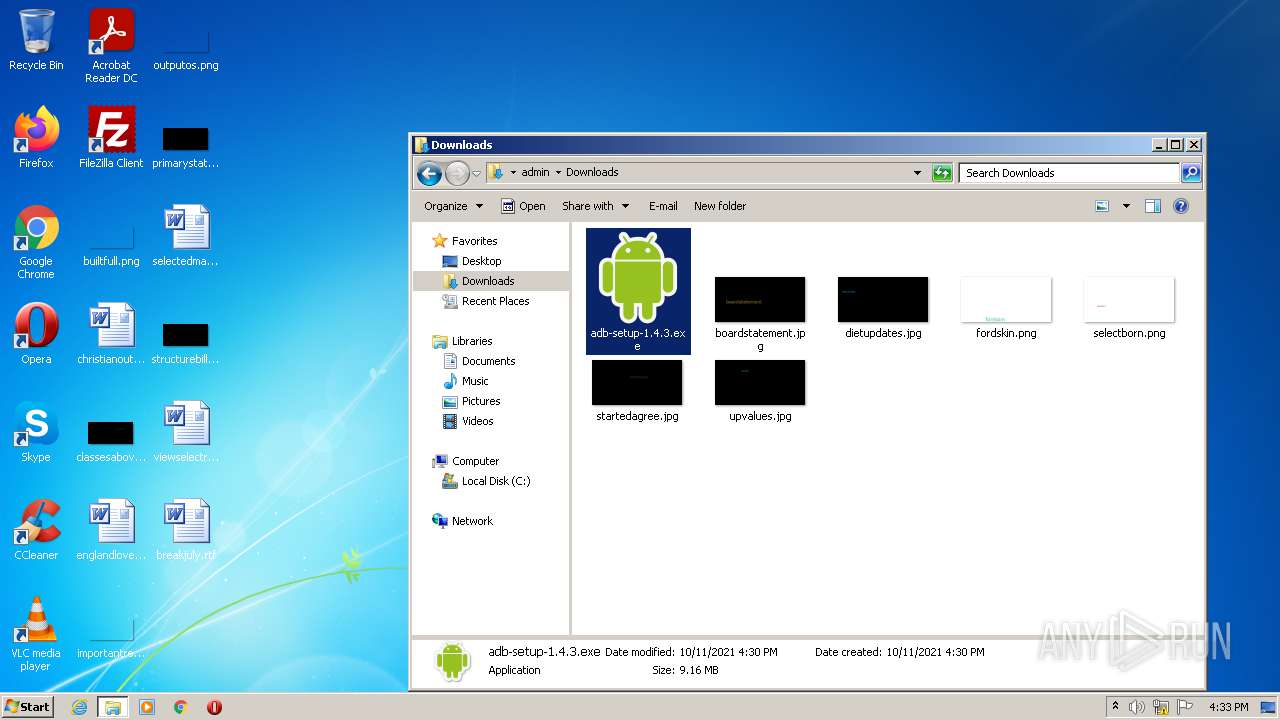
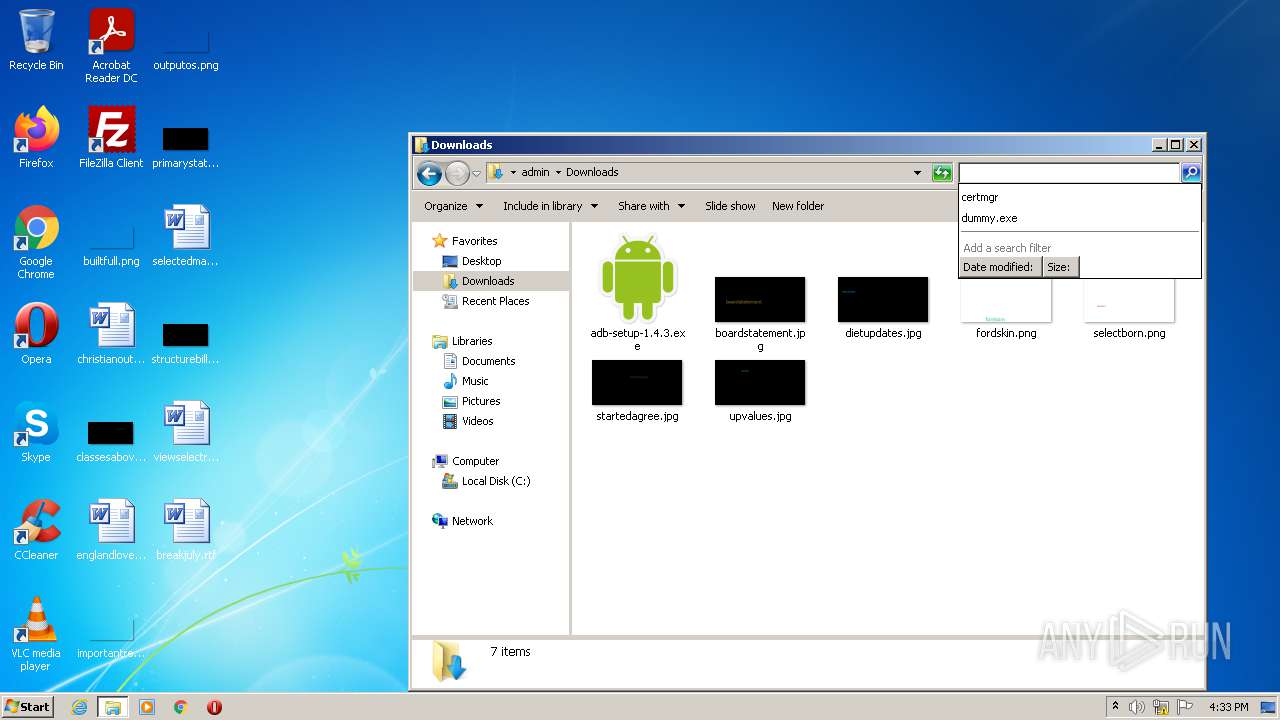
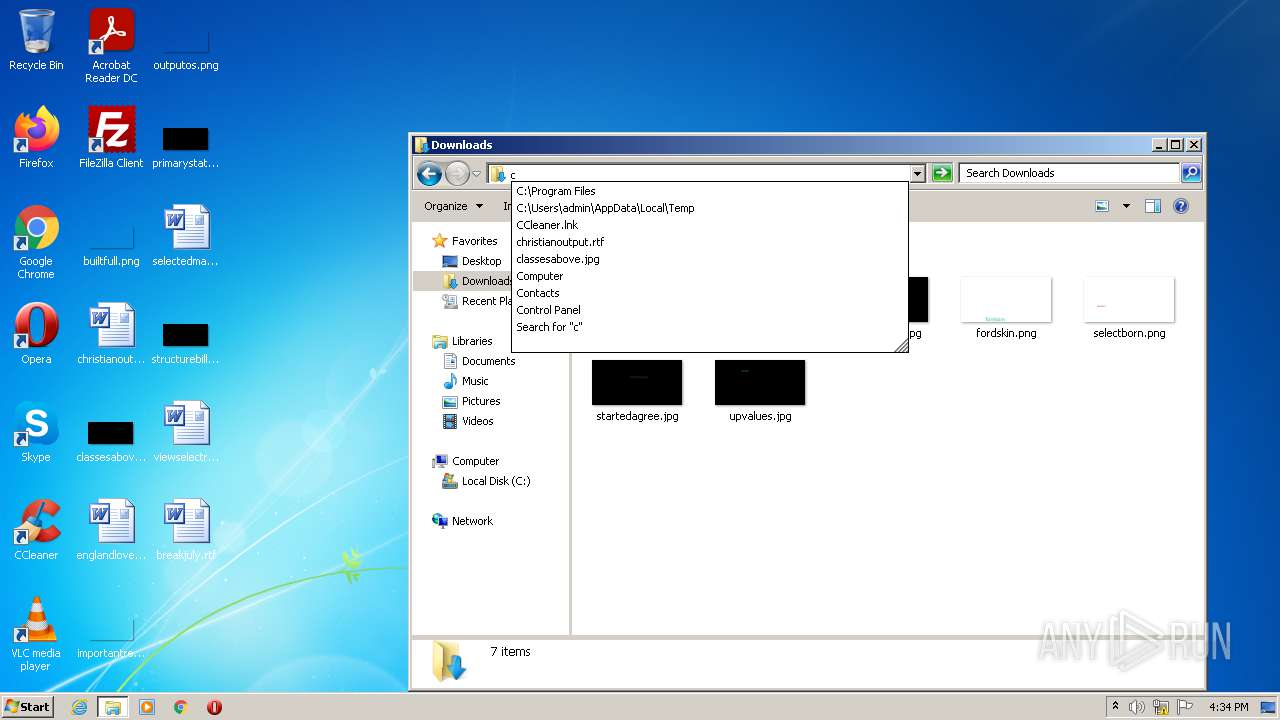
| File name: | adb-setup-1.4.3.exe |
| Full analysis: | https://app.any.run/tasks/0ea4bb5d-3048-4add-885c-50535f41f5fb |
| Verdict: | Malicious activity |
| Analysis date: | October 11, 2021, 15:30:27 |
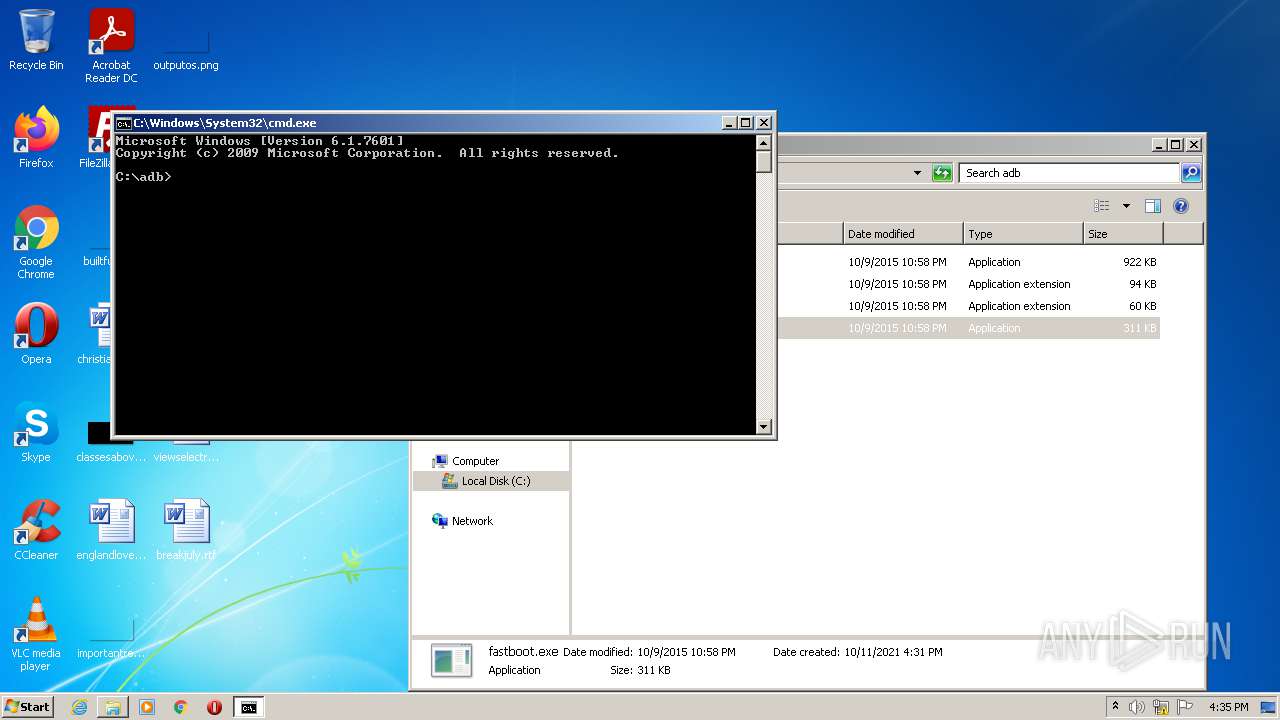
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 8C9085D4F753A2AAB26082FD2EB46A8E |
| SHA1: | EAE637085255A1C7D903A880374B20D108A3C38B |
| SHA256: | CA297F88AE58CC436028E07482E04E429E6BC81EAB291CBA814AA196D2C4F419 |
| SSDEEP: | 196608:cwYvfXDBYhBpeLHe3+EPegZT3VCz0TByC+Py7FU+LCZAsdX3LBO9:3ibBYDey3PFCuByPyhRwxBBI |
MALICIOUS
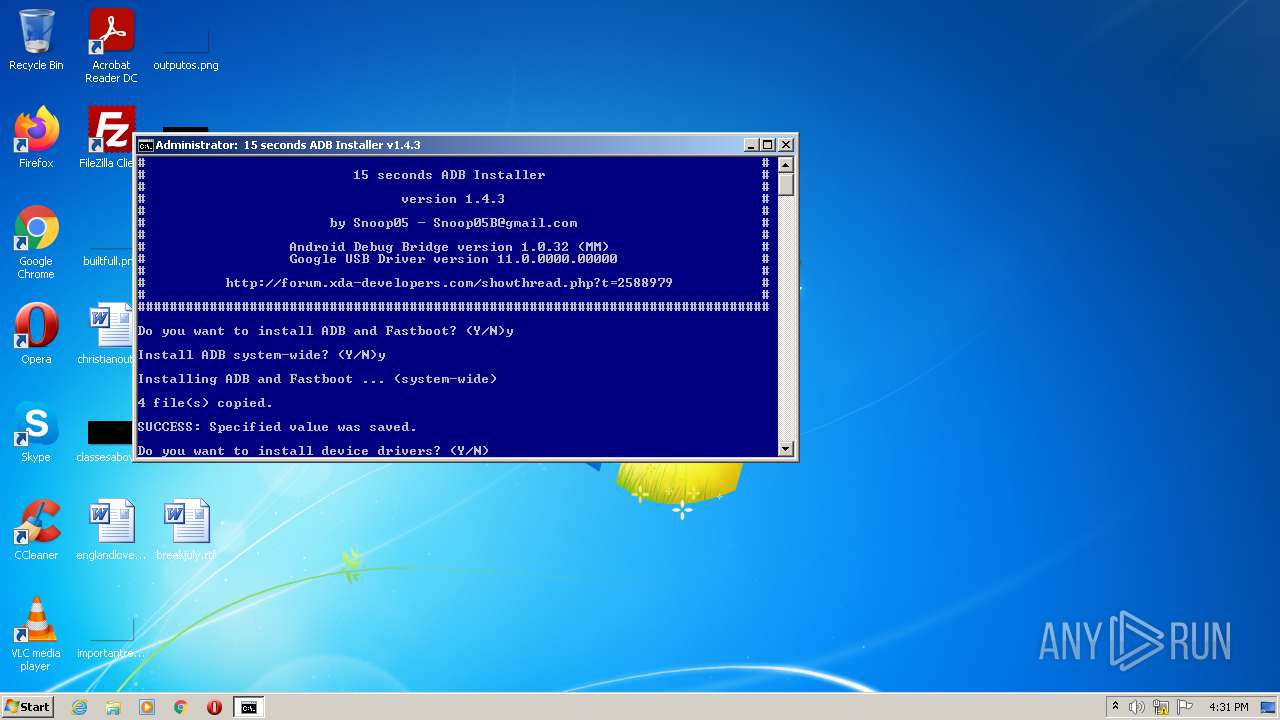
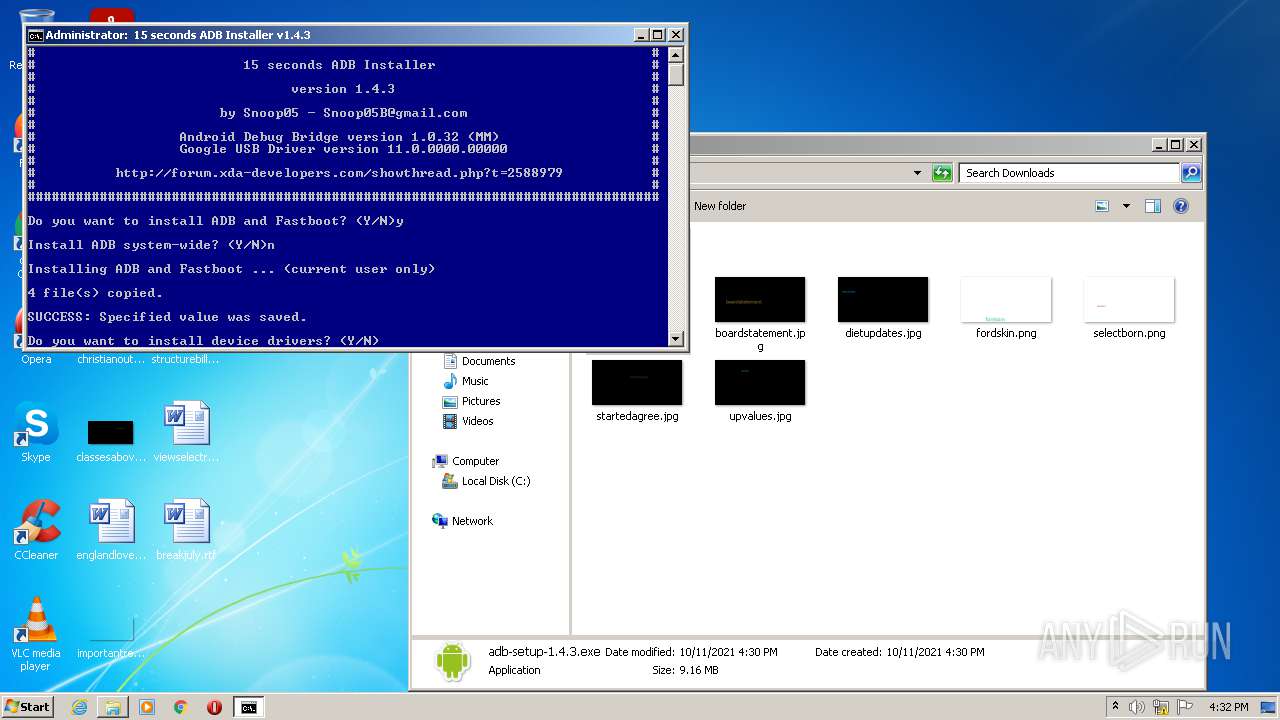
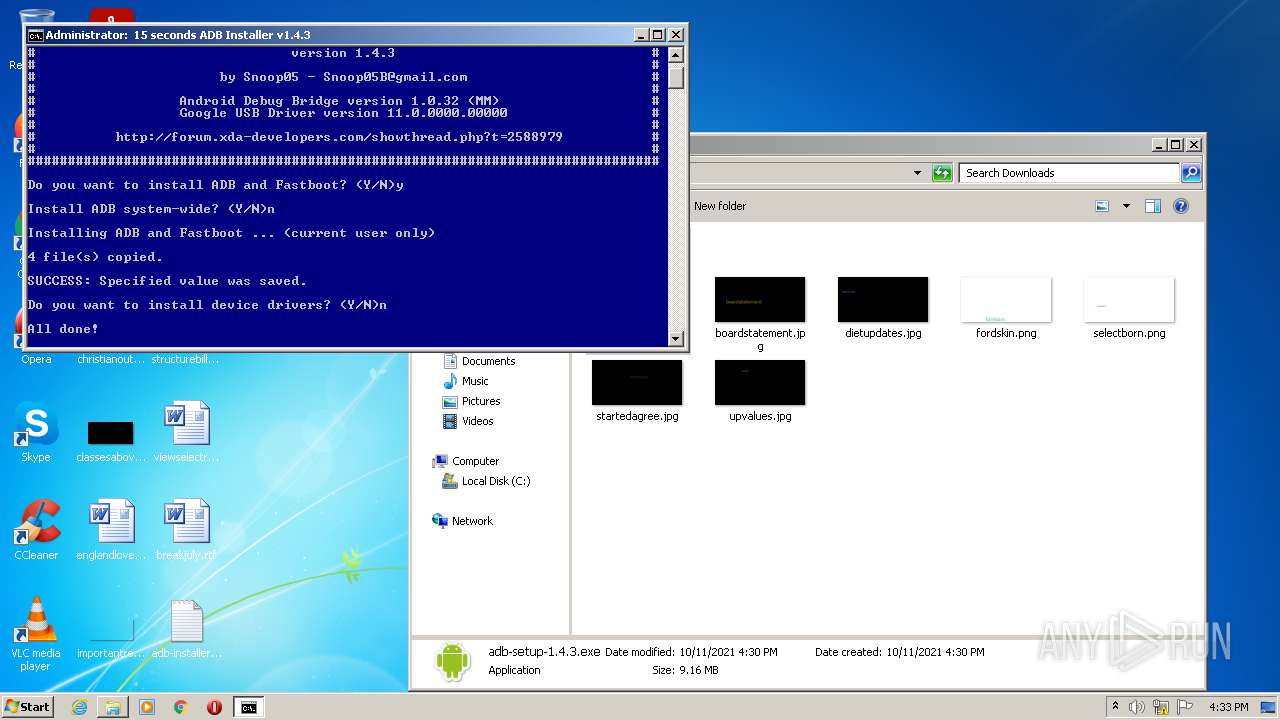
Drops executable file immediately after starts
- adb-setup-1.4.3.exe (PID: 3092)
- xcopy.exe (PID: 2396)
- xcopy.exe (PID: 2580)
- xcopy.exe (PID: 2248)
- xcopy.exe (PID: 2484)
- DrvInst.exe (PID: 2416)
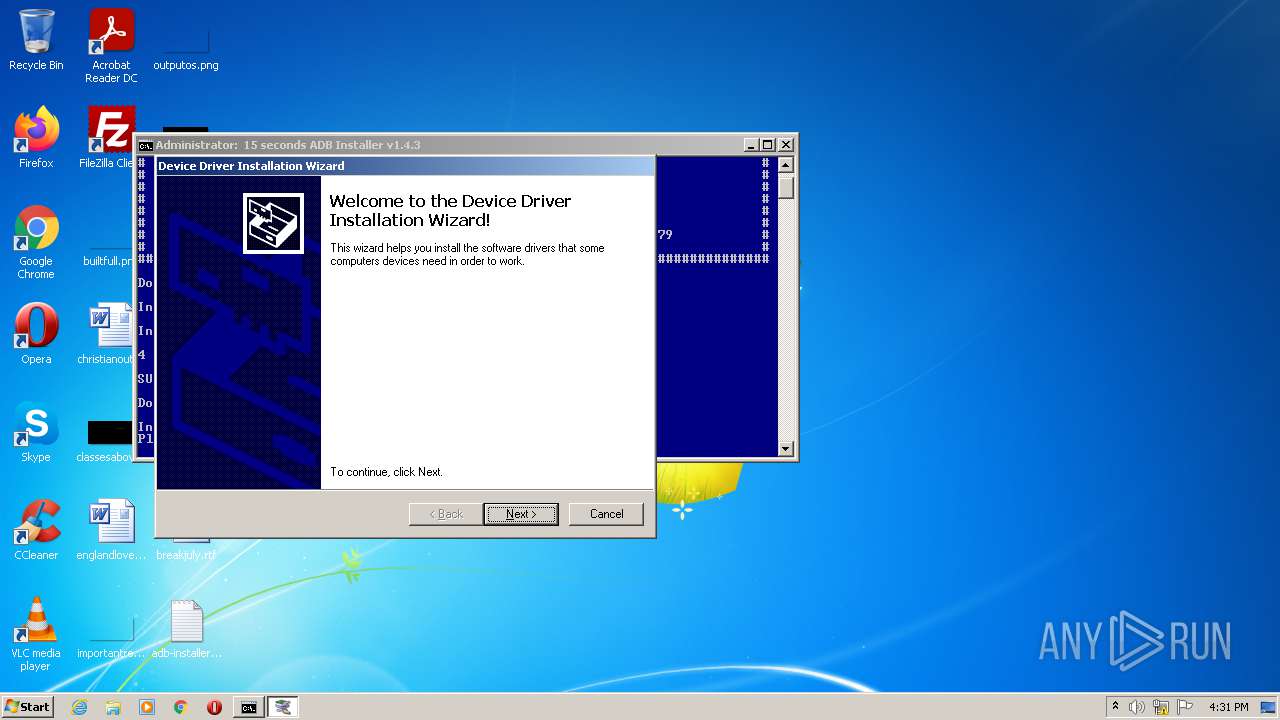
Application was dropped or rewritten from another process
- DPInst_x86.exe (PID: 3952)
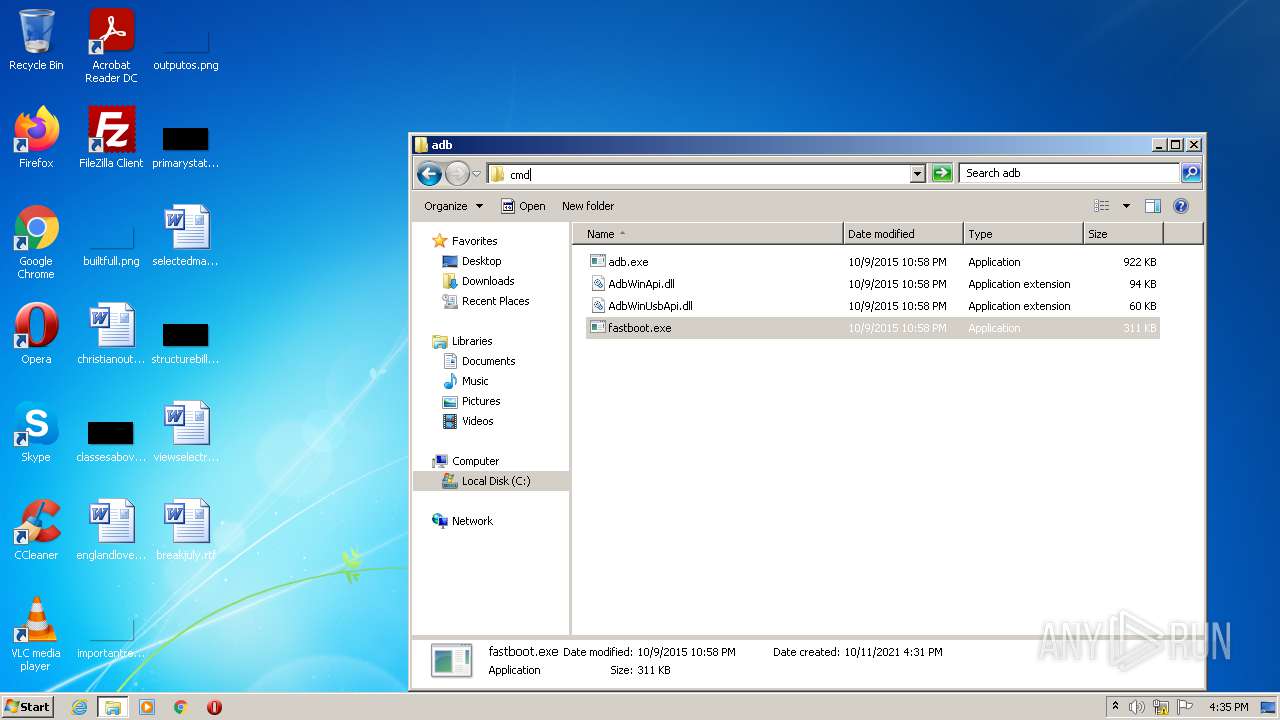
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3724)
SUSPICIOUS
Checks supported languages
- adb-setup-1.4.3.exe (PID: 3092)
- adb-setup-1.4.3.exe (PID: 2372)
- adb-setup-1.4.3.exe (PID: 3608)
- cmd.exe (PID: 3724)
- cmd.exe (PID: 2616)
- DPInst_x86.exe (PID: 3952)
- DrvInst.exe (PID: 2416)
Drops a file with too old compile date
- adb-setup-1.4.3.exe (PID: 3092)
- xcopy.exe (PID: 2396)
- xcopy.exe (PID: 2580)
- xcopy.exe (PID: 2484)
- xcopy.exe (PID: 2248)
- DPInst_x86.exe (PID: 3952)
- DrvInst.exe (PID: 2416)
Reads the computer name
- adb-setup-1.4.3.exe (PID: 2372)
- adb-setup-1.4.3.exe (PID: 3608)
- DPInst_x86.exe (PID: 3952)
- DrvInst.exe (PID: 2416)
Application launched itself
- adb-setup-1.4.3.exe (PID: 2372)
- adb-setup-1.4.3.exe (PID: 3092)
- cmd.exe (PID: 3724)
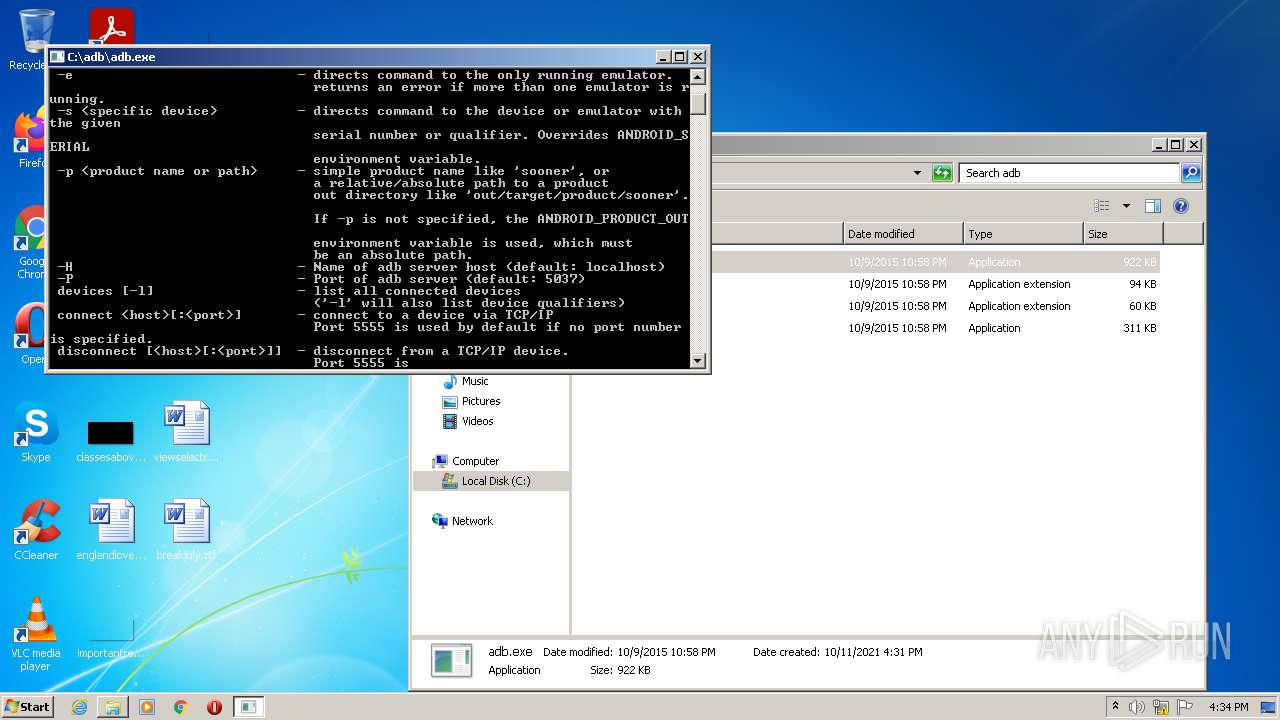
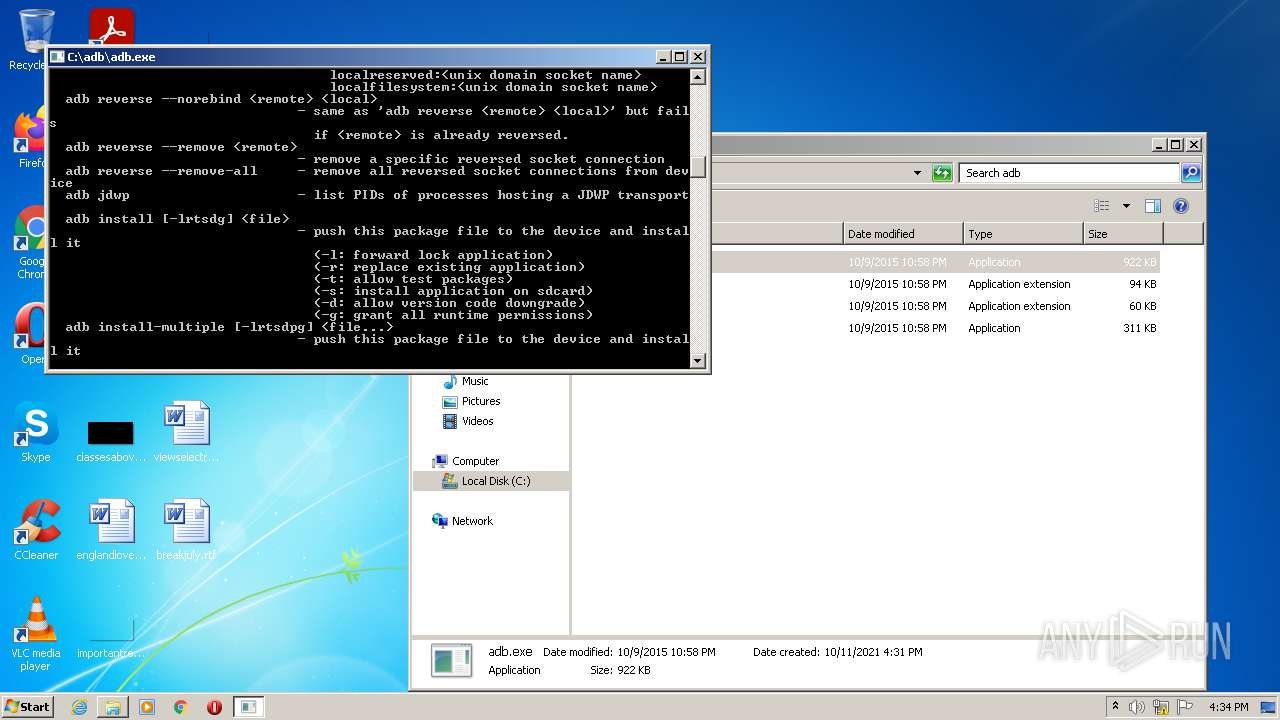
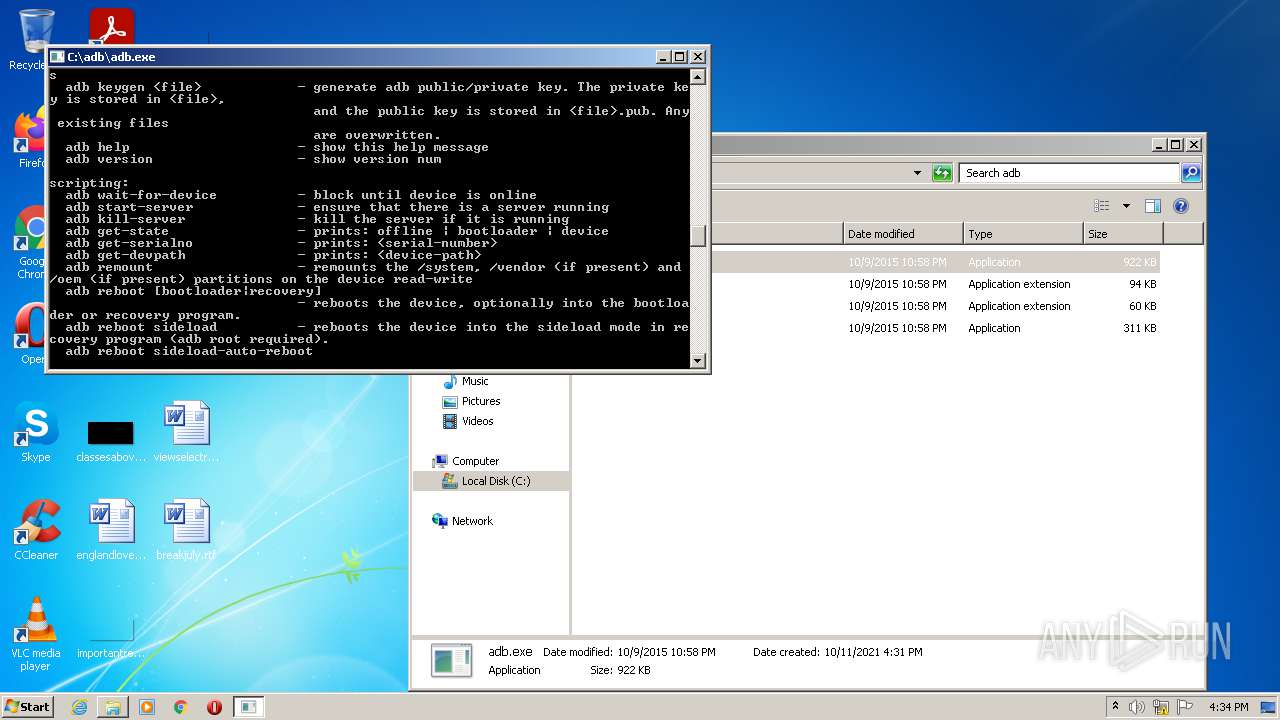
Starts CMD.EXE for commands execution
- adb-setup-1.4.3.exe (PID: 3608)
- cmd.exe (PID: 3724)
Drops a file that was compiled in debug mode
- adb-setup-1.4.3.exe (PID: 3092)
- xcopy.exe (PID: 2484)
- xcopy.exe (PID: 2580)
- DPInst_x86.exe (PID: 3952)
- DrvInst.exe (PID: 2416)
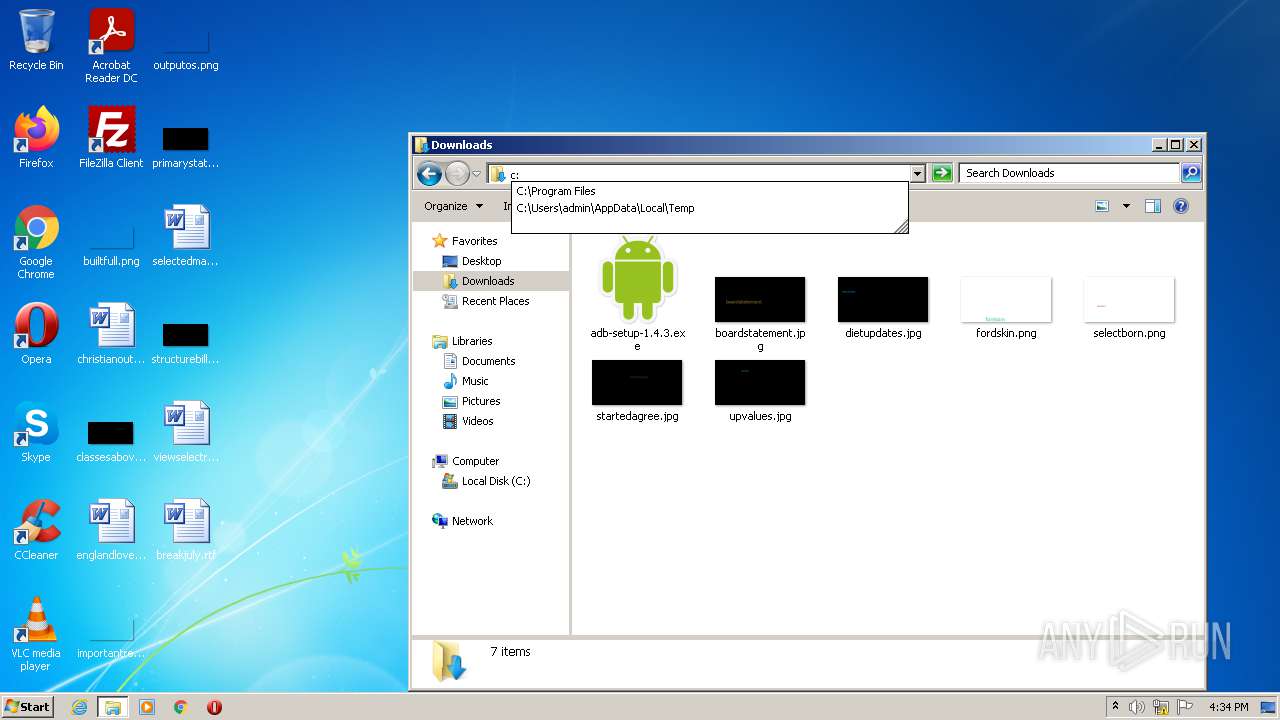
Executable content was dropped or overwritten
- adb-setup-1.4.3.exe (PID: 3092)
- xcopy.exe (PID: 2396)
- xcopy.exe (PID: 2580)
- xcopy.exe (PID: 2484)
- xcopy.exe (PID: 2248)
- DPInst_x86.exe (PID: 3952)
- DrvInst.exe (PID: 2416)
Creates files in the Windows directory
- DPInst_x86.exe (PID: 3952)
- DrvInst.exe (PID: 2416)
Executed via COM
- DrvInst.exe (PID: 2416)
Creates files in the driver directory
- DrvInst.exe (PID: 2416)
Removes files from Windows directory
- DrvInst.exe (PID: 2416)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 2416)
Executed as Windows Service
- vssvc.exe (PID: 3044)
Reads Environment values
- vssvc.exe (PID: 3044)
INFO
Checks supported languages
- xcopy.exe (PID: 2396)
- xcopy.exe (PID: 2580)
- xcopy.exe (PID: 2484)
- xcopy.exe (PID: 2248)
- find.exe (PID: 2940)
- setx.exe (PID: 3360)
- find.exe (PID: 3112)
- PING.EXE (PID: 2680)
- rundll32.exe (PID: 3720)
- vssvc.exe (PID: 3044)
Reads the computer name
- PING.EXE (PID: 2680)
- rundll32.exe (PID: 3720)
- vssvc.exe (PID: 3044)
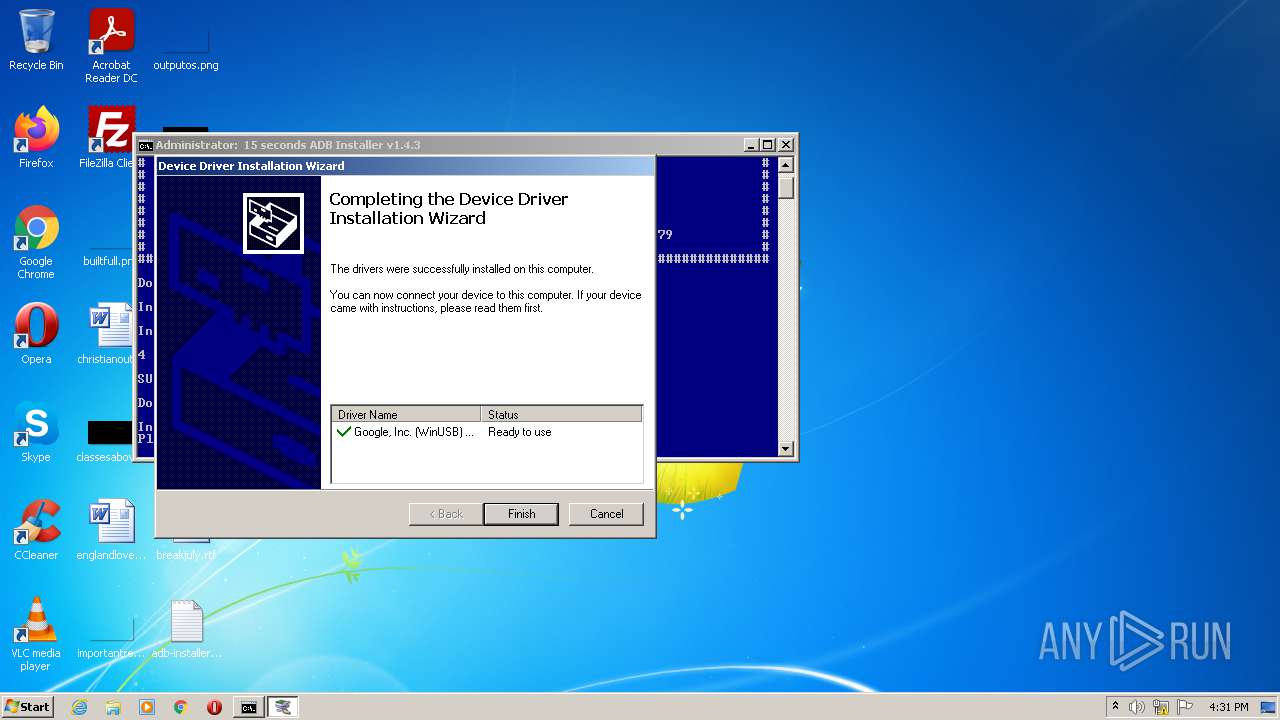
Checks Windows Trust Settings
- DrvInst.exe (PID: 2416)
- rundll32.exe (PID: 3720)
Reads settings of System Certificates
- DrvInst.exe (PID: 2416)
- rundll32.exe (PID: 3720)
Searches for installed software
- DrvInst.exe (PID: 2416)
Changes settings of System certificates
- DrvInst.exe (PID: 2416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:31 01:38:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 57344 |
| InitializedDataSize: | 307200 |
| UninitializedDataSize: | 389120 |
| EntryPoint: | 0x6cad0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.3.0 |
| ProductVersionNumber: | 1.4.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Snoop05 |
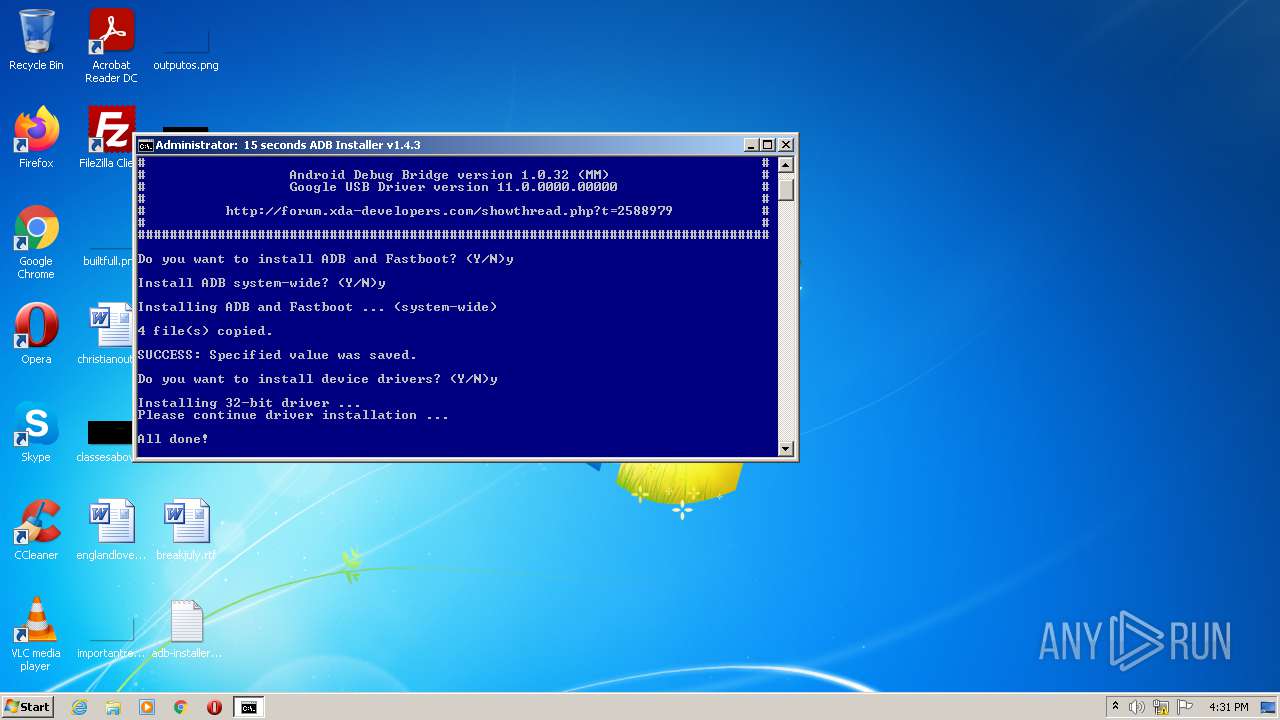
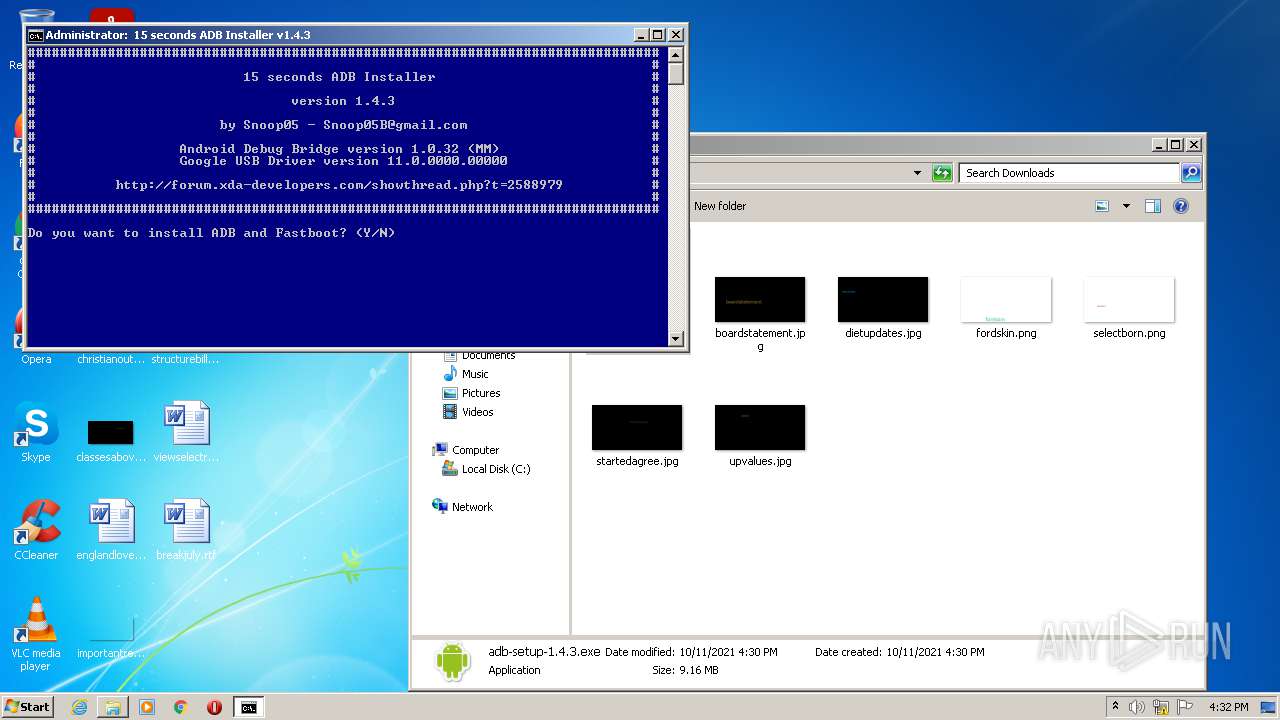
| FileDescription: | 15 seconds ADB Installer |
| FileVersion: | 1.4.3 |
| InternalName: | adb-installer |
| LegalCopyright: | - |
| OriginalFileName: | adb-installer-1.4.3.exe |
| PrivateBuild: | December 30, 2012 |
| ProductName: | 15 seconds ADB Installer |
| ProductVersion: | 1.4.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Dec-2012 00:38:38 |
| Detected languages: |
|
| CompanyName: | Snoop05 |
| FileDescription: | 15 seconds ADB Installer |
| FileVersion: | 1.4.3 |
| InternalName: | adb-installer |
| LegalCopyright: | - |
| OriginalFilename: | adb-installer-1.4.3.exe |
| PrivateBuild: | December 30, 2012 |
| ProductName: | 15 seconds ADB Installer |
| ProductVersion: | 1.4.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 31-Dec-2012 00:38:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0005F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00060000 | 0x0000E000 | 0x0000D800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97261 |
.rsrc | 0x0006E000 | 0x0004B000 | 0x0004B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.00963 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.23138 | 838 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.60602 | 744 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 2.63074 | 488 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 2.3817 | 296 | Latin 1 / Western European | Russian - Russia | RT_ICON |
5 | 3.28424 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.39214 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.17501 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 1.89055 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 2.75163 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 3.43924 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
58
Monitored processes
18
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
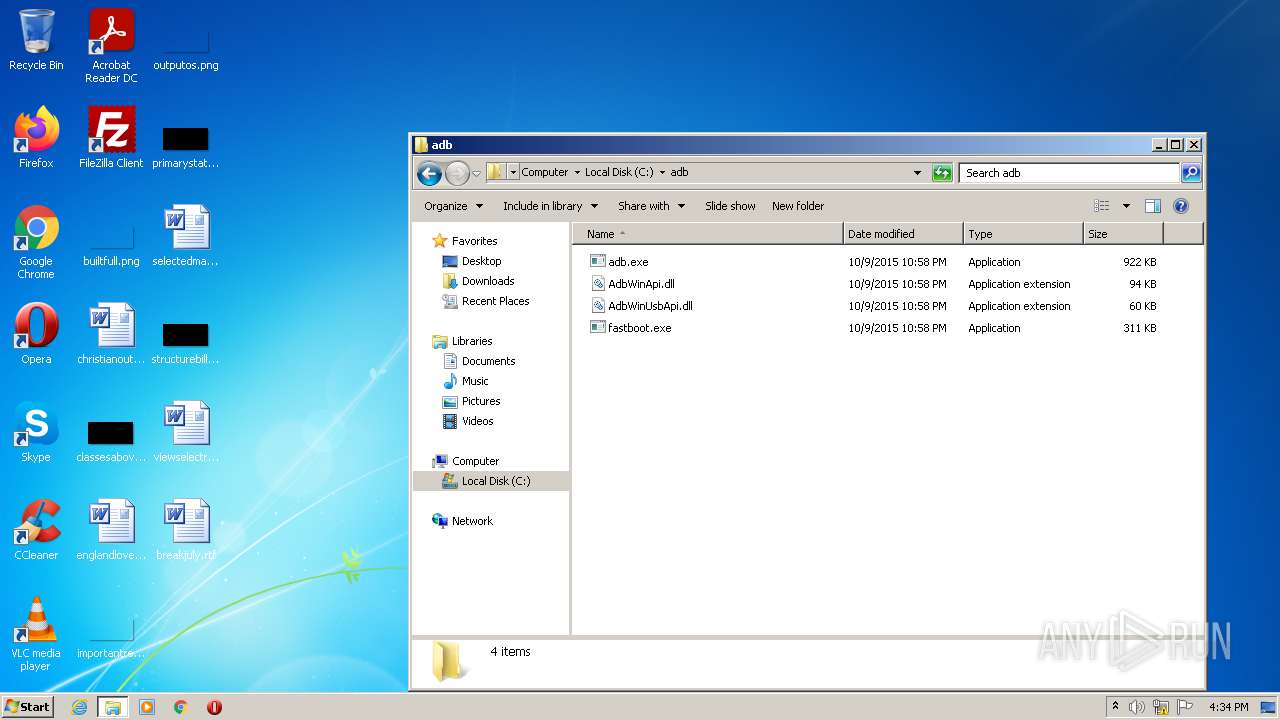
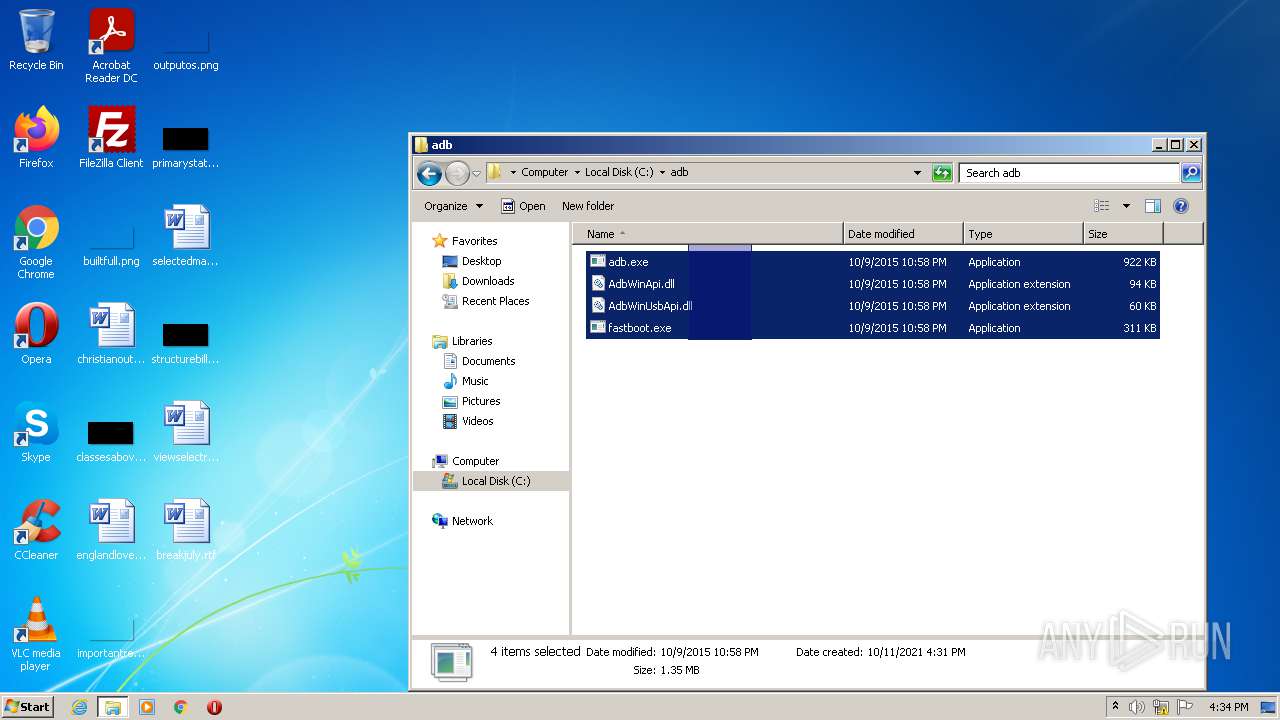
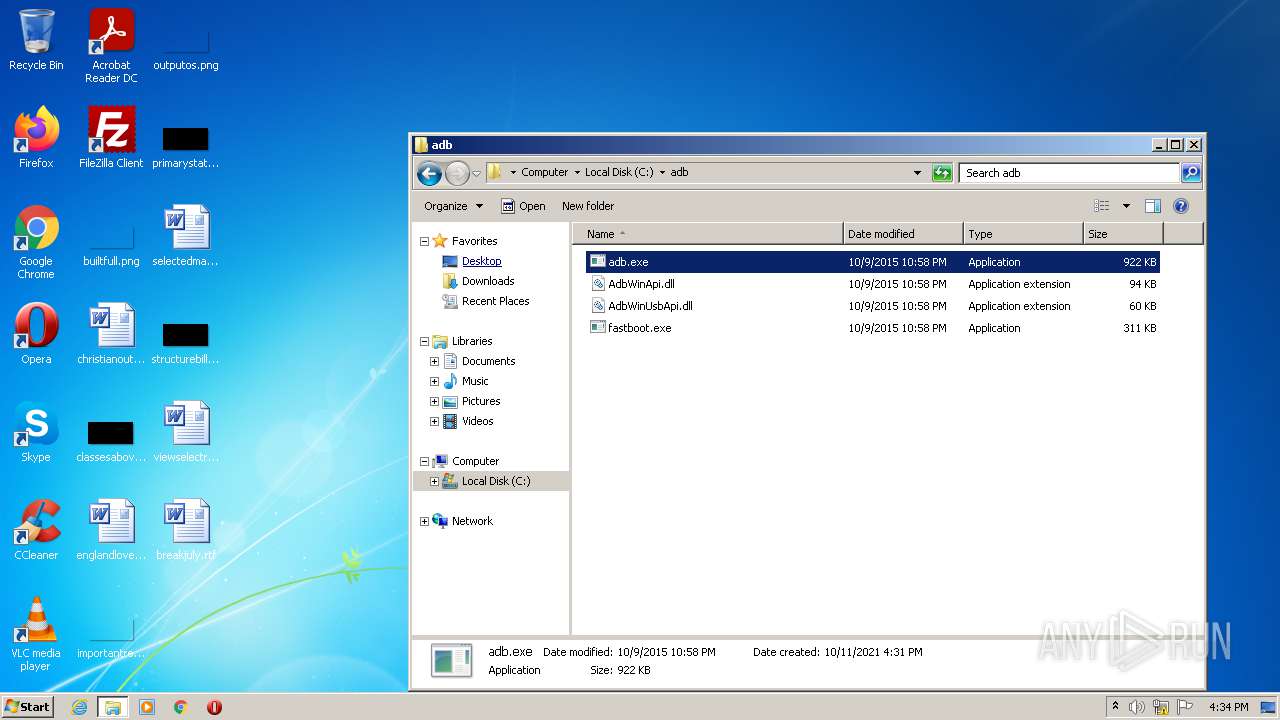
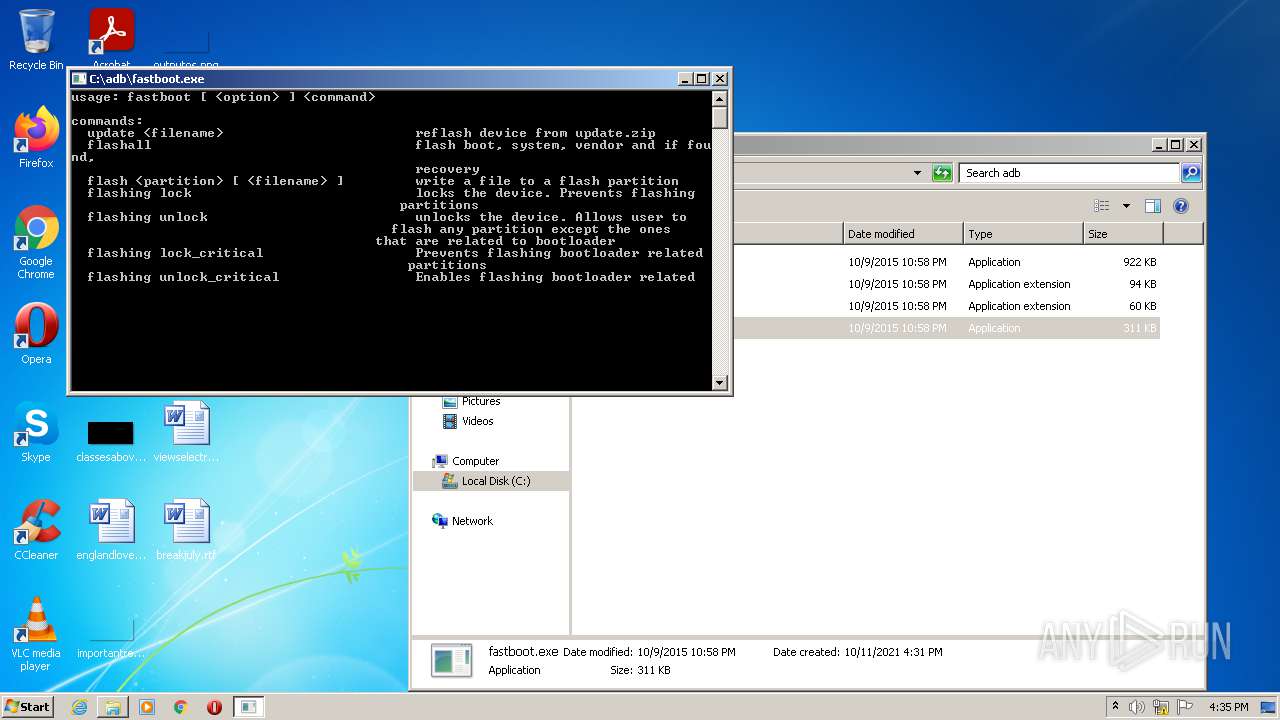
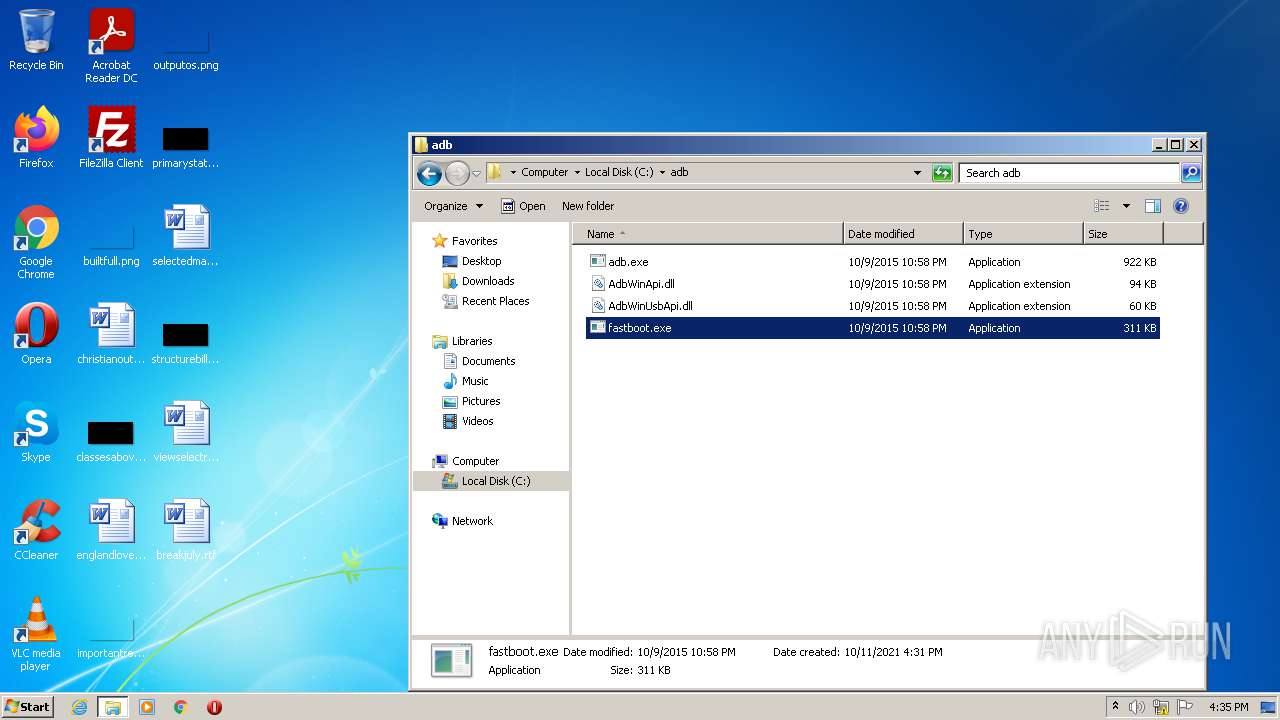
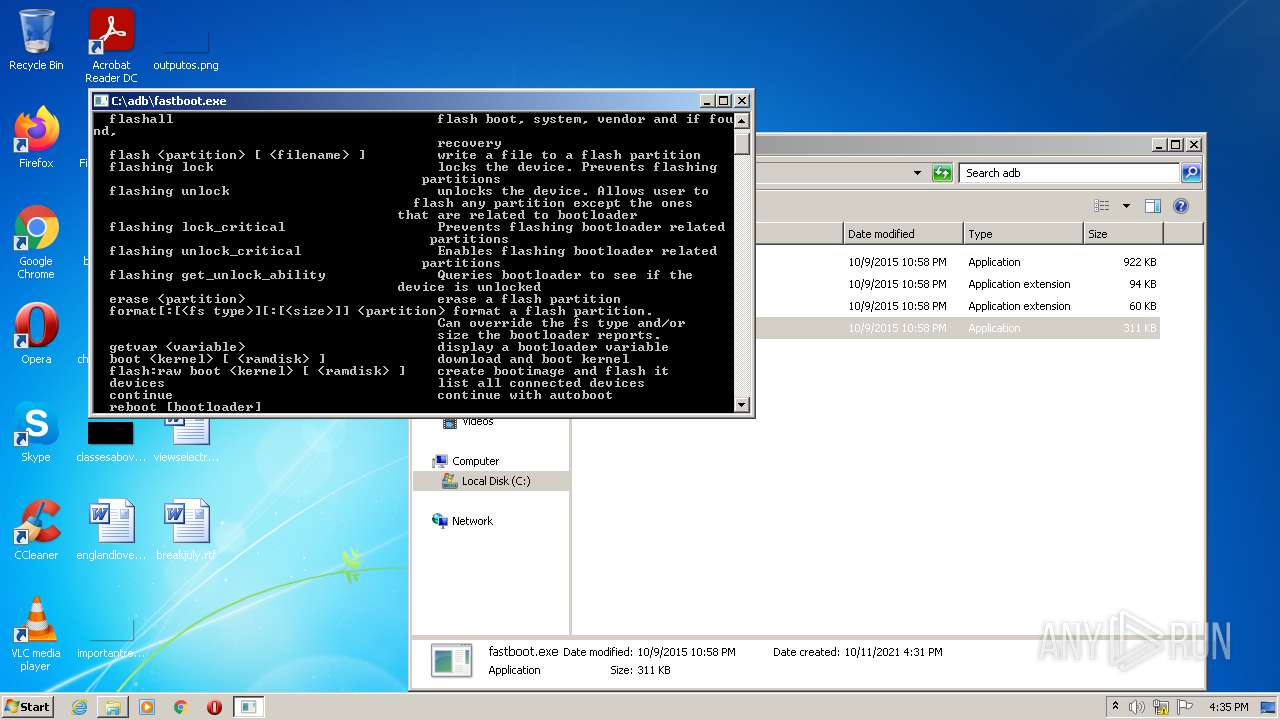
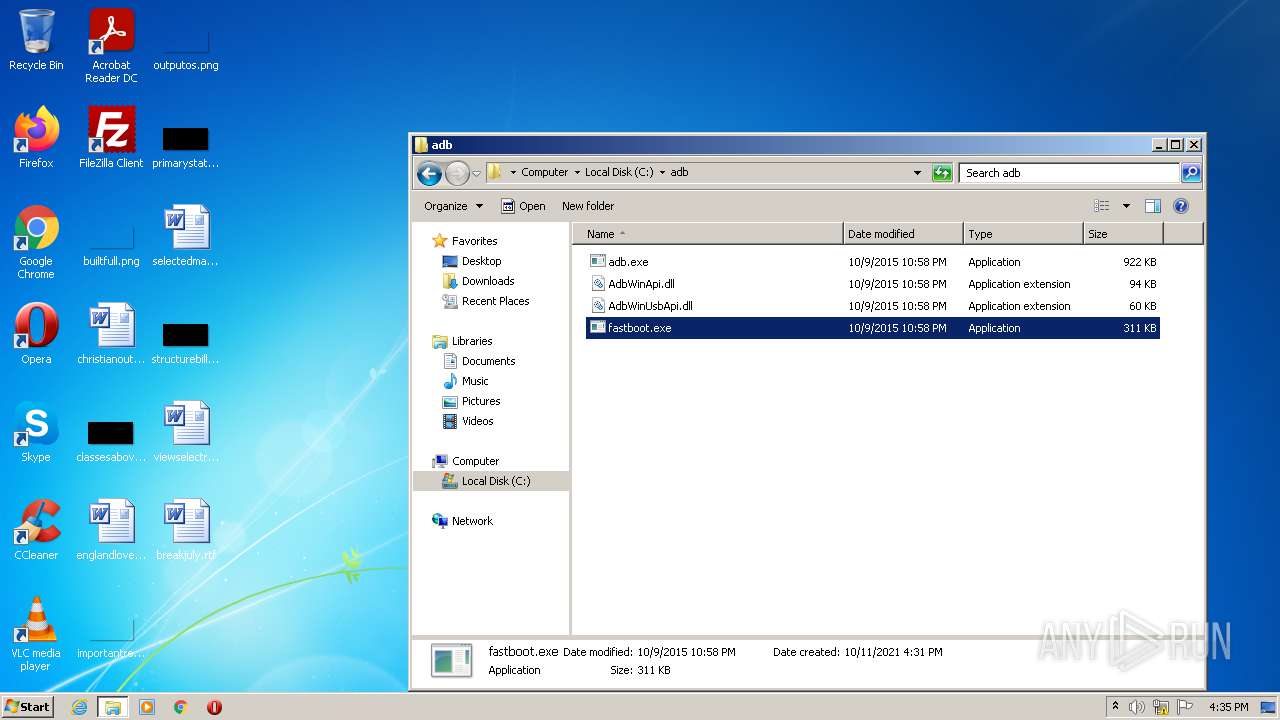
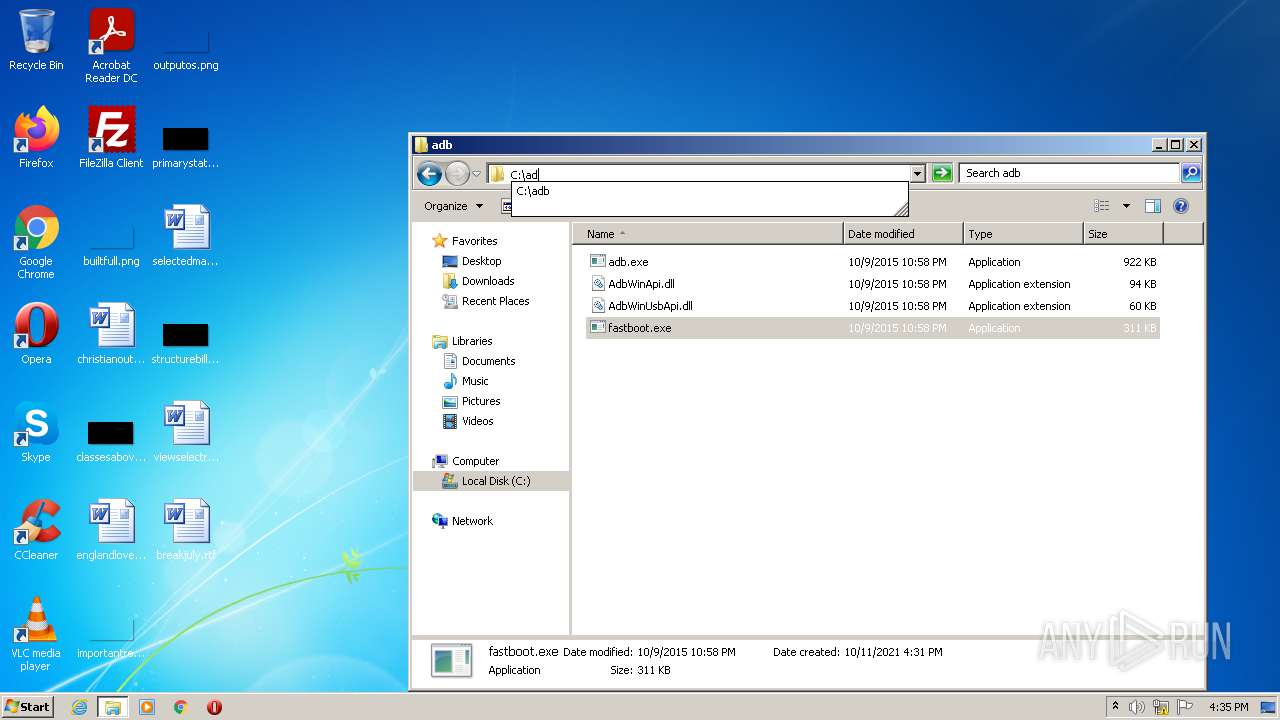
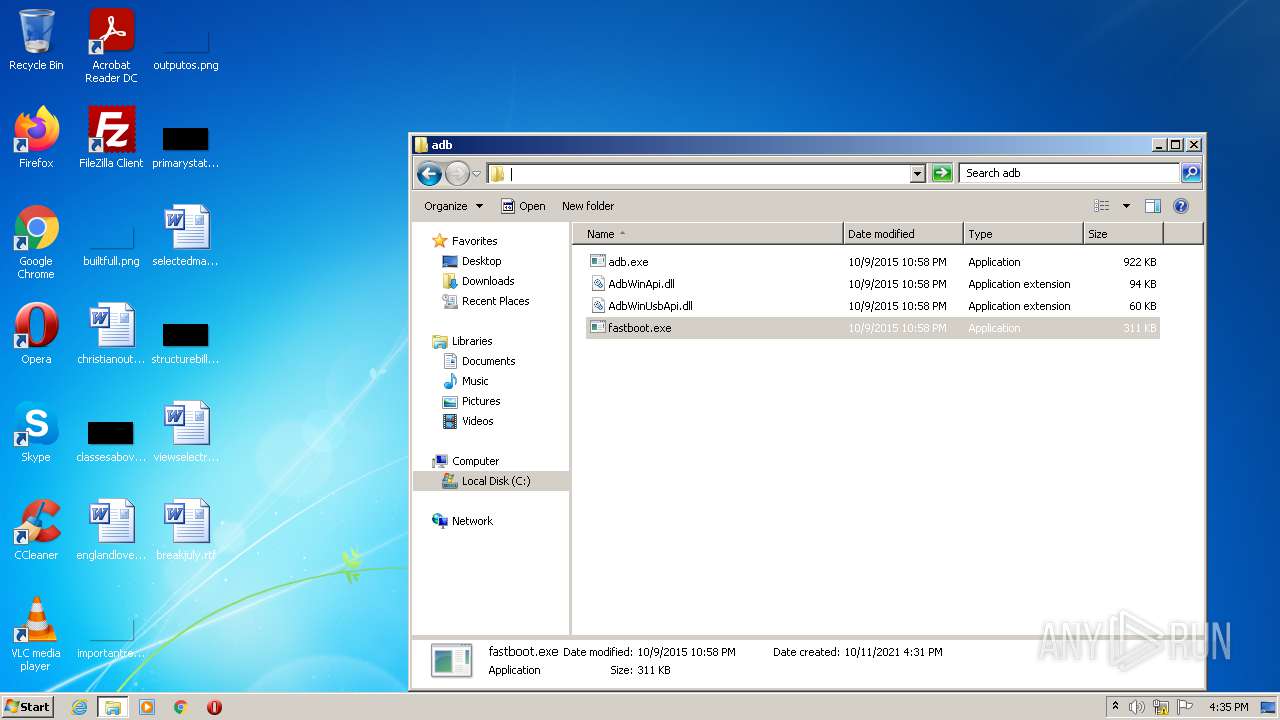
| 2248 | XCOPY adb\fastboot.exe C:\adb\ /y /q | C:\Windows\system32\xcopy.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | "C:\Users\admin\Downloads\adb-setup-1.4.3.exe" | C:\Users\admin\Downloads\adb-setup-1.4.3.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Snoop05 Integrity Level: MEDIUM Description: 15 seconds ADB Installer Exit code: 0 Version: 1.4.3 Modules
| |||||||||||||||
| 2396 | XCOPY adb\adb.exe C:\adb\ /y /q | C:\Windows\system32\xcopy.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{756fb985-3f5f-24da-ca1b-d64a7827c617}\android_winusb.inf" "0" "683c9e8f3" "000005DC" "WinSta0\Default" "0000057C" "208" "c:\users\admin\appdata\local\temp\7zipsfx.000\driver" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2484 | XCOPY adb\AdbWinUsbApi.dll C:\adb\ /y /q | C:\Windows\system32\xcopy.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | XCOPY adb\AdbWinApi.dll C:\adb\ /y /q | C:\Windows\system32\xcopy.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2616 | C:\Windows\system32\cmd.exe /S /D /c" VER " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2680 | PING localhost -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2940 | FIND "C:\adb" PATH.TMP | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3044 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 190
Read events
9 999
Write events
191
Delete events
0
Modification events
| (PID) Process: | (2372) adb-setup-1.4.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2372) adb-setup-1.4.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2372) adb-setup-1.4.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2372) adb-setup-1.4.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3608) adb-setup-1.4.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3608) adb-setup-1.4.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3608) adb-setup-1.4.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3608) adb-setup-1.4.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3360) setx.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | write | Name: | PATH |
Value: C:\Program Files\Common Files\Oracle\Java\javapath;C:\ProgramData\Oracle\Java\javapath;C:\Windows\system32;C:\Windows;C:\Windows\System32\Wbem;C:\Windows\System32\WindowsPowerShell\v1.0\;C:\adb | |||
| (PID) Process: | (3952) DPInst_x86.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
25
Suspicious files
5
Text files
5
Unknown types
6
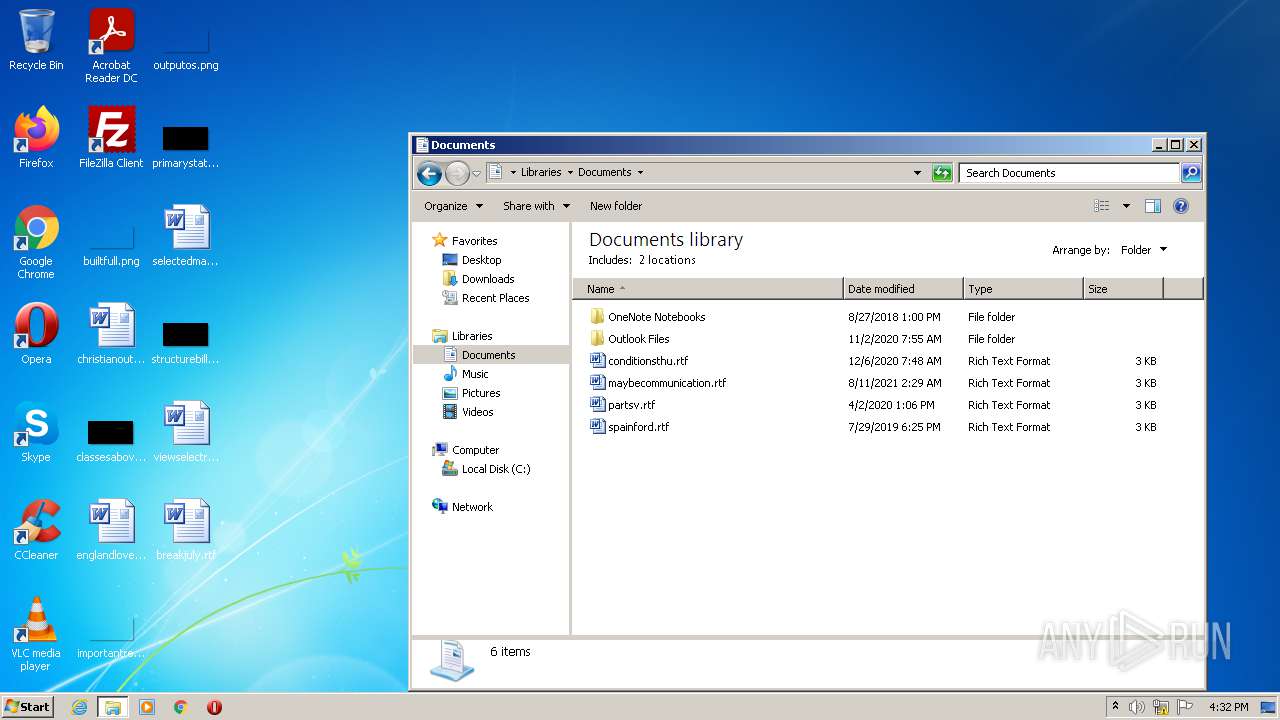
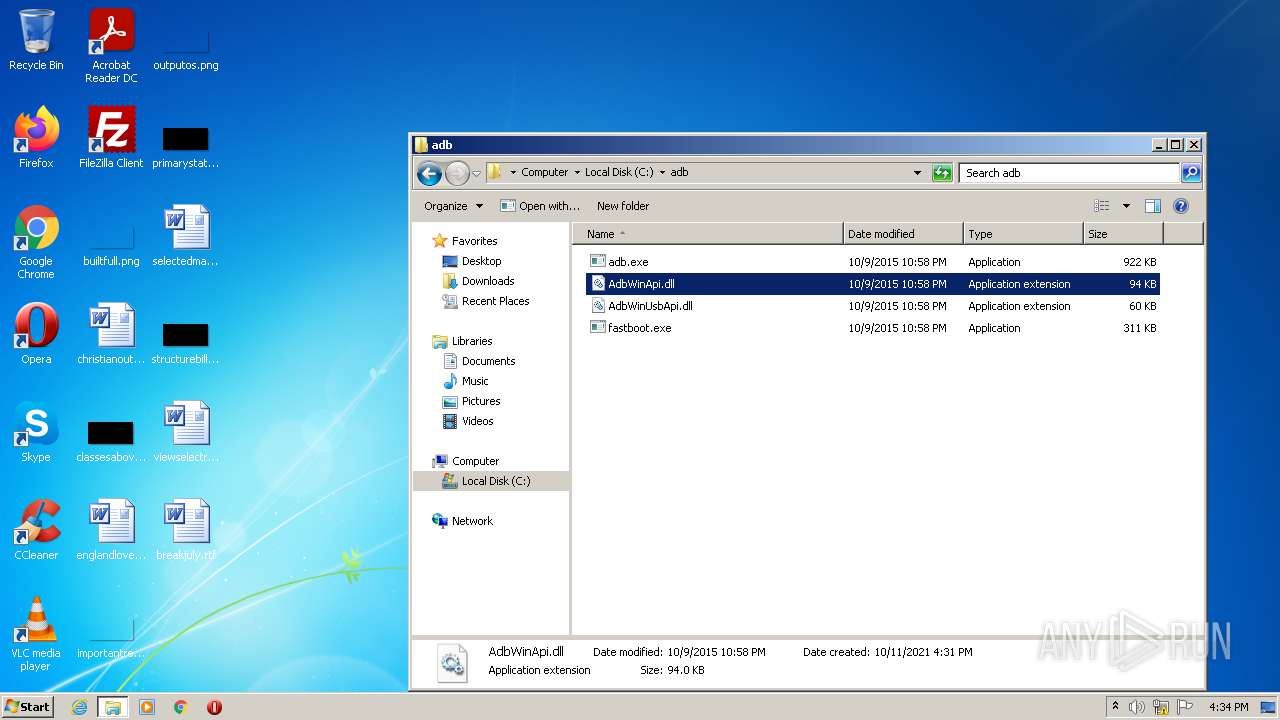
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\amd64\NOTICE.txt | text | |
MD5:EA7F2158B930BAF2C0FE799566489716 | SHA256:A19B767B9DDDA7306C78232E4A223D0BA966471B74DCE3C0C995307CAB5BF7B7 | |||
| 3092 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\DPInst_x64.exe | executable | |
MD5:4192A5B905374E423EC1E545599AA86E | SHA256:567F40A09F1D9E72396296AD194FA7CF48B72361D6E259D6B99DA774C2CD8981 | |||
| 3092 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\amd64\WdfCoInstaller01009.dll | executable | |
MD5:4DA5DA193E0E4F86F6F8FD43EF25329A | SHA256:18487B4FF94EDCCC98ED59D9FCA662D4A1331C5F1E14DF8DB3093256DD9F1C3E | |||
| 3092 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\amd64\winusbcoinstaller2.dll | executable | |
MD5:246900CE6474718730ECD4F873234CF5 | SHA256:981A17EFFDDBC20377512DDAEC9F22C2B7067E17A3E2A8CCF82BB7BB7B2420B6 | |||
| 3092 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\adb\AdbWinUsbApi.dll | executable | |
MD5:5F23F2F936BDFAC90BB0A4970AD365CF | SHA256:041C6859BB4FC78D3A903DD901298CD1ECFB75B6BE0646B74954CD722280A407 | |||
| 3092 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\adb\AdbWinApi.dll | executable | |
MD5:47A6EE3F186B2C2F5057028906BAC0C6 | SHA256:14A51482AA003DB79A400F4B15C158397FE6D57EE6606B3D633FA431A7BFDF4B | |||
| 3092 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\i386\winusbcoinstaller2.dll | executable | |
MD5:8E7B9F81E8823FEE2D82F7DE3A44300B | SHA256:EBE3B7708DD974EE87EFED3113028D266AF87CA8DBAE77C47C6F7612824D3D6C | |||
| 3092 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\i386\WdfCoInstaller01009.dll | executable | |
MD5:A9970042BE512C7981B36E689C5F3F9F | SHA256:7A6BF1F950684381205C717A51AF2D9C81B203CB1F3DB0006A4602E2DF675C77 | |||
| 3092 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\DPInst_x86.exe | executable | |
MD5:9568538CEF3A955A88811250C7B9F053 | SHA256:CB7F00F91AE5F7D88277AC2EE5CFB5D3A9F8E9E629C3DE317ABF226A8B6B76B6 | |||
| 3092 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\androidwinusba64.cat | cat | |
MD5:B83F9FA084F11007C7E6C668E6FA9E54 | SHA256:8F3F15BAEAF50AE7388562BE0303F5AC7EE3CB255448A24E3D33E1F094E0680E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | — | US | whitelisted |
1936 | svchost.exe | 20.73.194.208:443 | — | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |