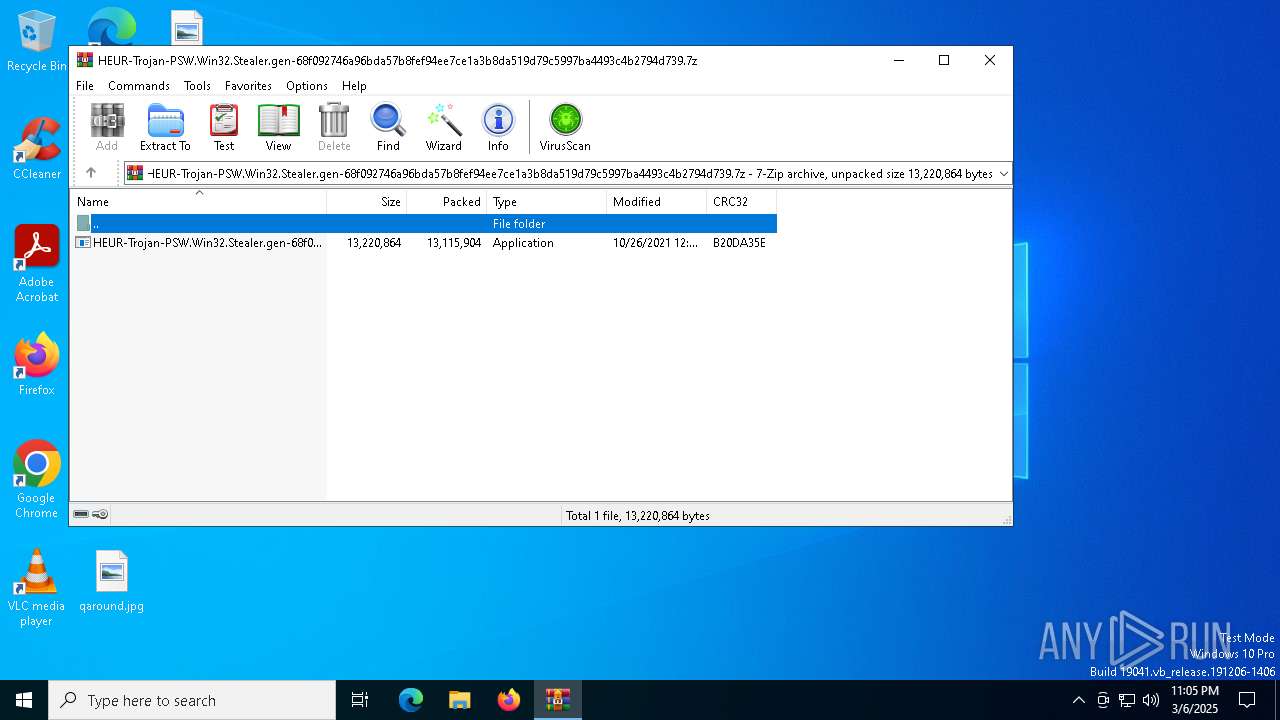
| File name: | HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.7z |
| Full analysis: | https://app.any.run/tasks/48afeeed-d3e0-408c-a3d2-d926c010fbd0 |
| Verdict: | Malicious activity |
| Analysis date: | March 06, 2025, 23:04:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | BBDC99F57C751904322E7C4B1E8671D5 |
| SHA1: | CCB0F7556A5912EF651CFD908A19E1D6C04E2B45 |
| SHA256: | CA2654C84901D3516EAACC90718DA8592AB9A051D3C211F4FA33EDB17B948F28 |
| SSDEEP: | 98304:XyMWRqeMVJ90/q2efRsp5snDaZEWoZvRbofCSnSNuQpUvOZDaCM0D5LLvzeR14OH:ZIbJPwosjlzrXhBoi1fY3 |
MALICIOUS
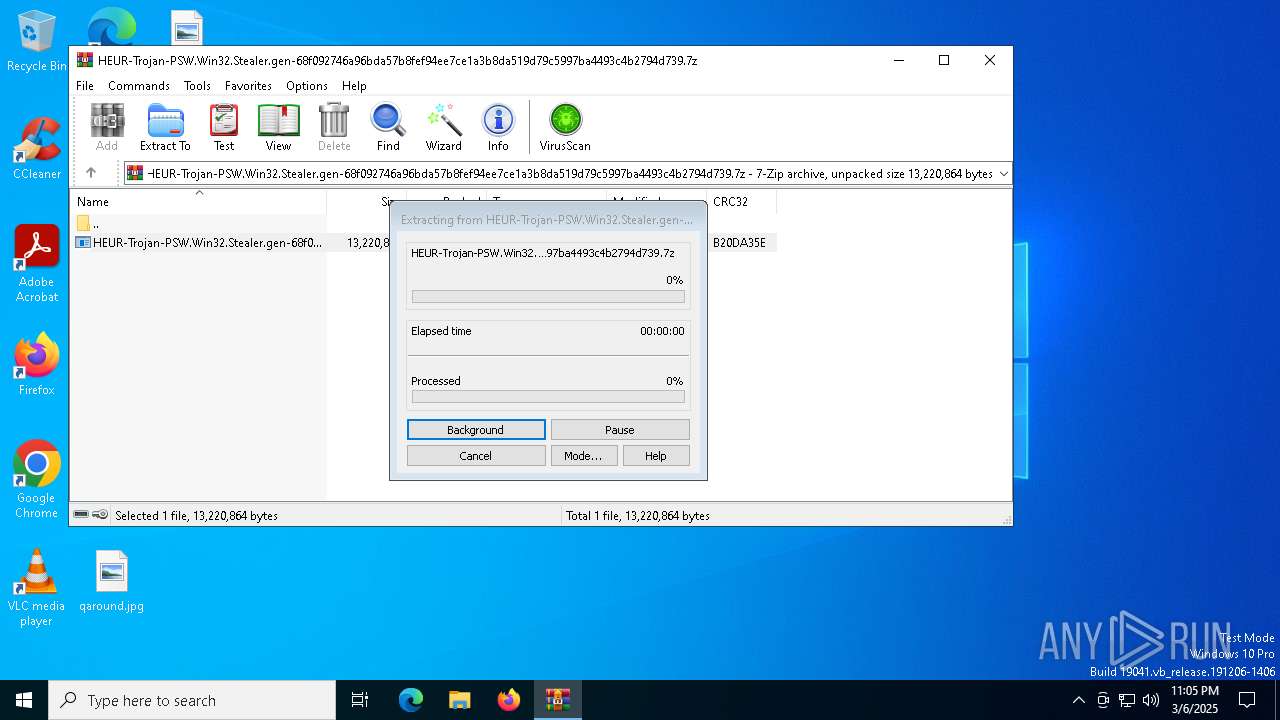
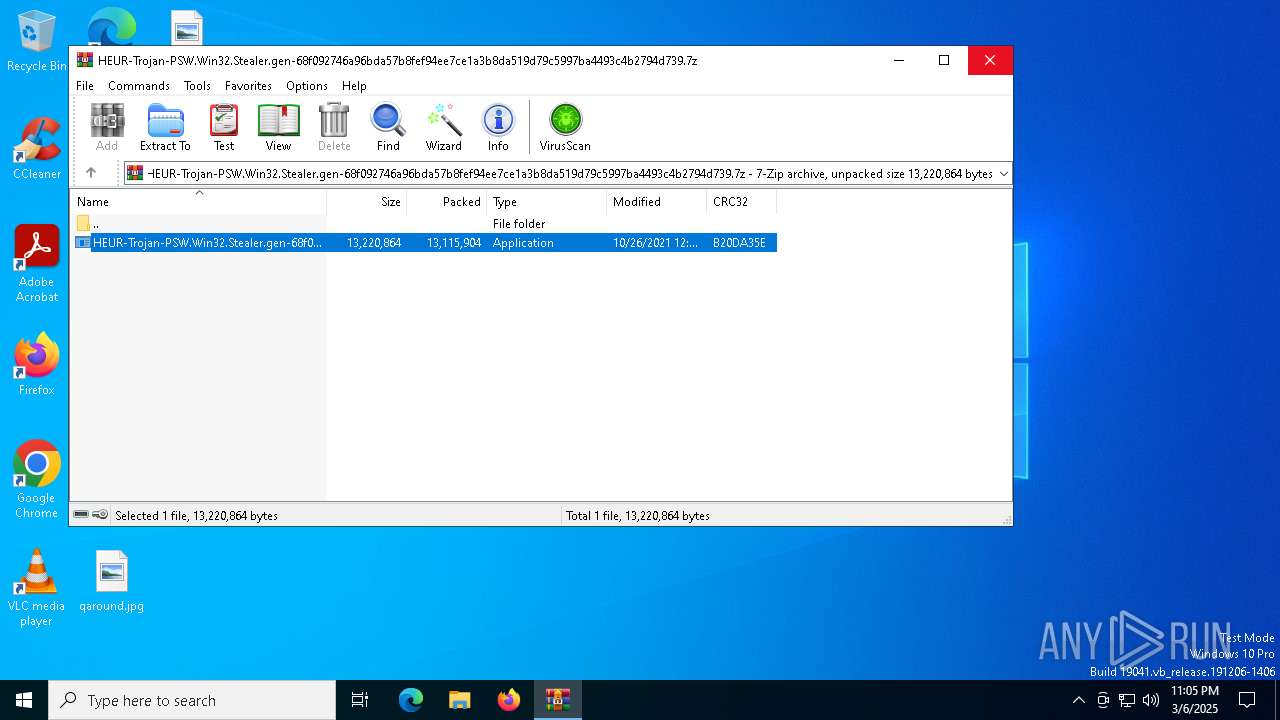
Generic archive extractor
- WinRAR.exe (PID: 1324)
SUSPICIOUS
Executes application which crashes
- HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.exe (PID: 8088)
Executable content was dropped or overwritten
- HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.exe (PID: 8088)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7600)
- BackgroundTransferHost.exe (PID: 7356)
- BackgroundTransferHost.exe (PID: 7900)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1324)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7600)
- WerFault.exe (PID: 7464)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7600)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7600)
Create files in a temporary directory
- HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.exe (PID: 8088)
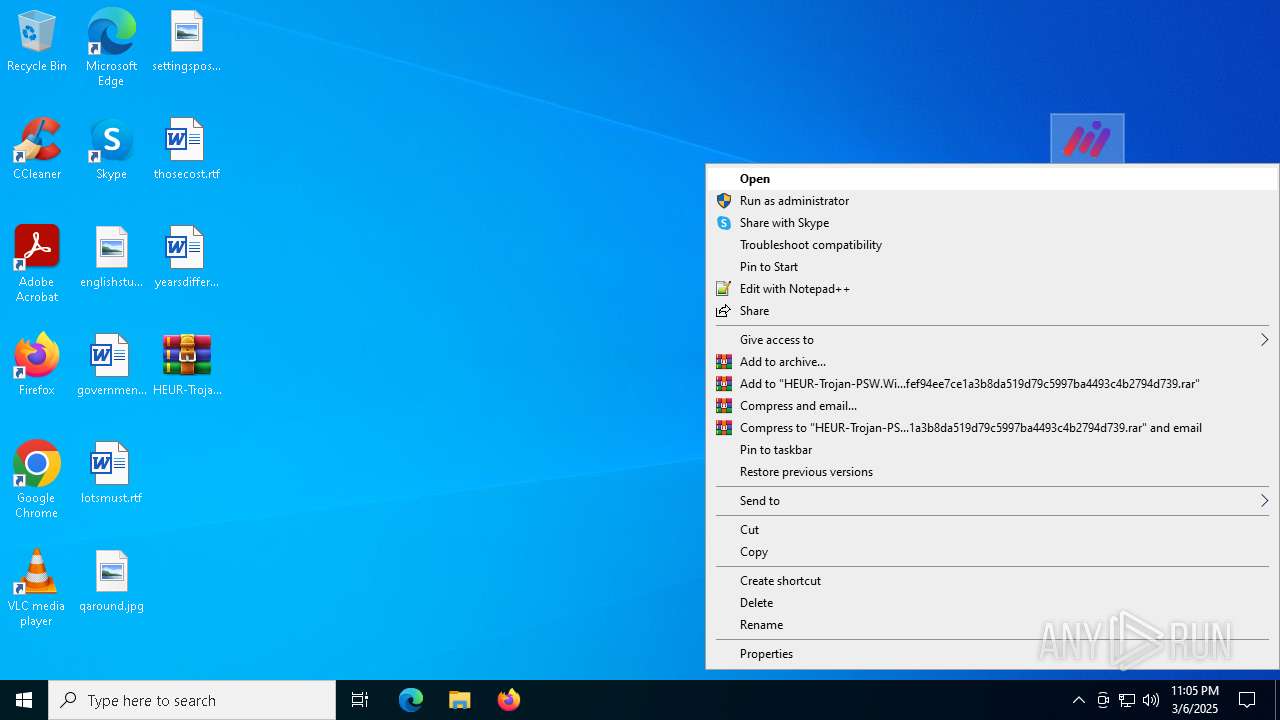
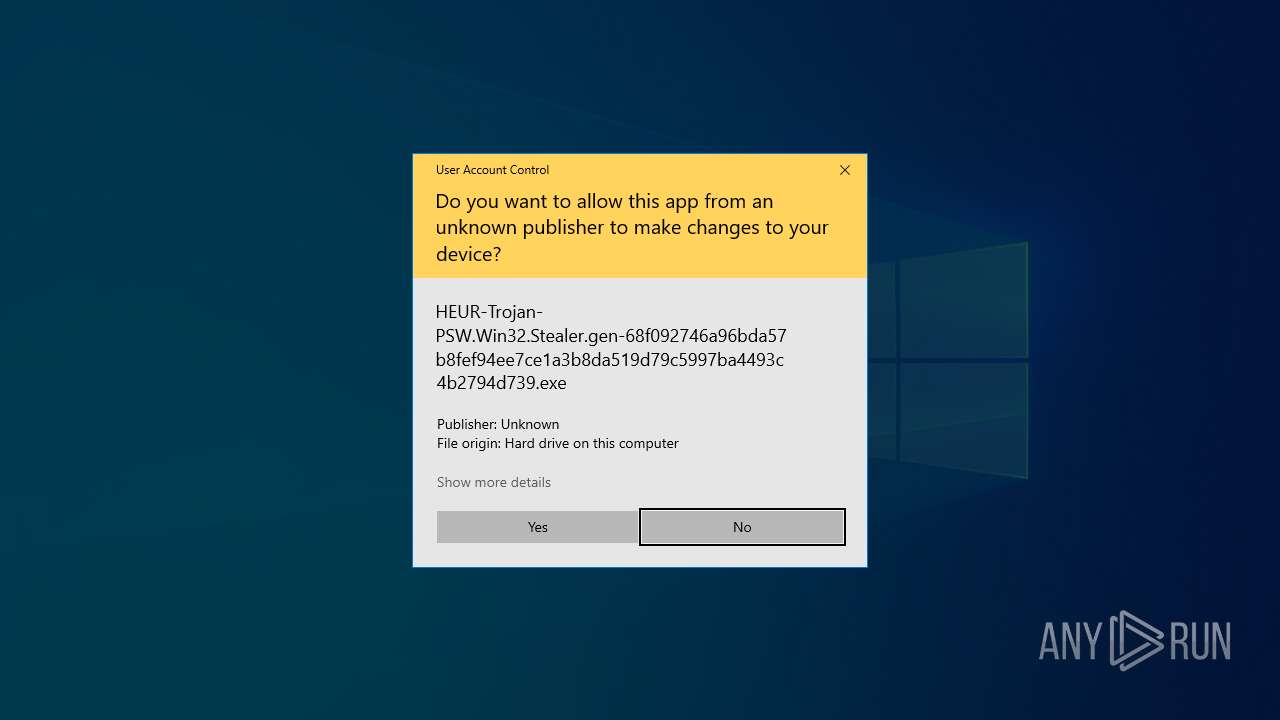
Manual execution by a user
- HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.exe (PID: 8088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2021:10:26 12:20:42+00:00 |
| ArchivedFileName: | HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.exe |
Total processes
141
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1324 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3896 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5072 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7248 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7356 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7464 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 8088 -s 1372 | C:\Windows\SysWOW64\WerFault.exe | — | HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7600 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7900 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8088 | "C:\Users\admin\Desktop\HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.exe" | C:\Users\admin\Desktop\HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Max Care Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 8148 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 737
Read events
4 697
Write events
37
Delete events
3
Modification events
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.7z | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
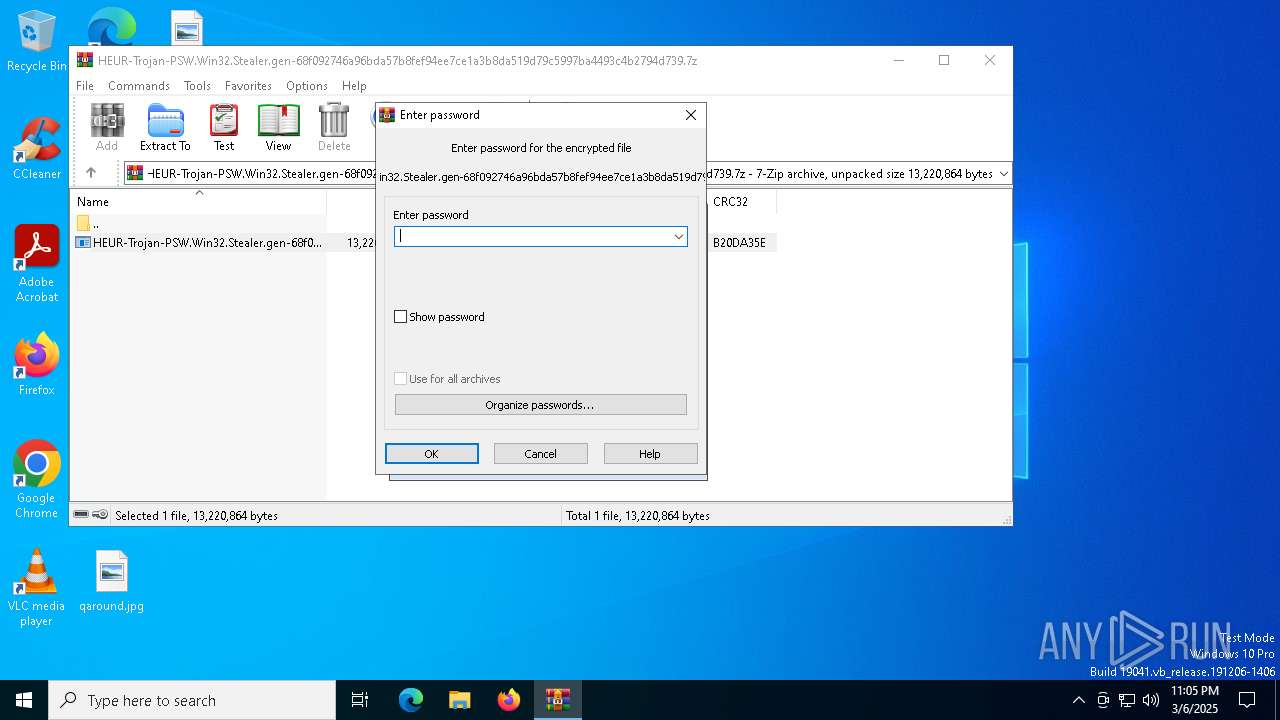
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
2
Suspicious files
7
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7600 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\8b47d3a7-8386-450c-b2c4-cbd514bc5847.down_data | — | |
MD5:— | SHA256:— | |||
| 7464 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_YBY1OEY5AVIVF2V5_16415a67222481b53f6237ec76b41a02f17ae2a_21976f6d_204529e9-50c8-41ab-8270-c4cf83314229\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7464 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.exe.8088.dmp | — | |
MD5:— | SHA256:— | |||
| 7600 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:9287F7EB4B6D3790136918B2ACD1F75A | SHA256:FF9488F849D3EDA8596B15B218B1D33E7FFF61920A7924ADE29B611F55DE8036 | |||
| 8088 | HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.exe | C:\Users\admin\AppData\Local\Temp\Runtime.MSIL.1.0.0.0\NativePRo.dll | executable | |
MD5:94173DE2E35AA8D621FC1C4F54B2A082 | SHA256:7E2C70B7732FB1A9A61D7CE3D7290BC7B31EA28CBFB1DBC79D377835615B941F | |||
| 1324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1324.11746\HEUR-Trojan-PSW.Win32.Stealer.gen-68f092746a96bda57b8fef94ee7ce1a3b8da519d79c5997ba4493c4b2794d739.exe | executable | |
MD5:7534A23F5588A3ED9F9A4ED4491E4688 | SHA256:68F092746A96BDA57B8FEF94EE7CE1A3B8DA519D79C5997BA4493C4B2794D739 | |||
| 7464 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER4FF.tmp.WERInternalMetadata.xml | binary | |
MD5:1A64CFA670BD3235108D9B918E88BAA6 | SHA256:D41D64ED364AC97321BF24A61D77E7BDCCB882CA903777DEFF9871BD3638B8FA | |||
| 7600 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\af8d65c0-f8f8-4969-bdb4-cb5427f8de05.042213bf-b004-4f0f-823b-1cc519713f3d.down_meta | binary | |
MD5:19A4F98D26418264858D624AEE5C55F9 | SHA256:E1CE5CD1310A1B0158C4D6C8CCEB16C46EA2F5A20A8B6786CBFC641B7161CFFF | |||
| 7464 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER3C6.tmp.dmp | binary | |
MD5:21C313FB794AA54FA46D016C0018D4AC | SHA256:DF54AC937C6347EEF614749BC42C74B478FE2C4DA9D5F6B188A45892069FBB40 | |||
| 7464 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER52F.tmp.xml | xml | |
MD5:2C697CC3F8597E2588FBB99267E19E91 | SHA256:CABB78B21FE8B513CD22B0AF2CCA45F3427DC1A136633C5B85C63368A18666E3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
21
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1196 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7600 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1196 | backgroundTaskHost.exe | 20.103.156.88:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1196 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7600 | BackgroundTransferHost.exe | 184.86.251.9:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |