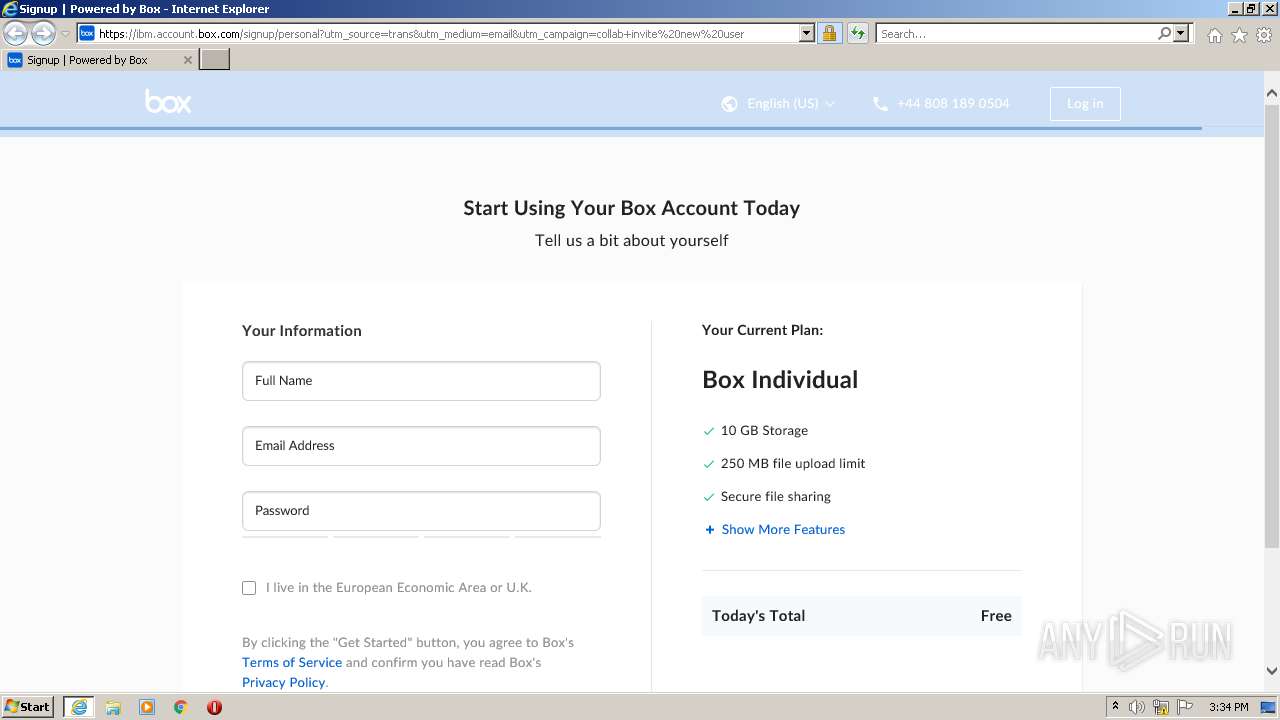
| URL: | https://ibm.account.box.com/signup/collab/ele8dki2j8?utm_source=trans&utm_medium=email&utm_campaign=collab+invite%20new%20user |
| Full analysis: | https://app.any.run/tasks/f5d6cf5c-cddb-474e-b281-c6878a24f314 |
| Verdict: | Suspicious activity |
| Analysis date: | September 27, 2022, 14:33:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 631071698F8B8194FE5E41DA3C3A0945 |
| SHA1: | F244D4ED3F5AB6E4042649B614F9CD871EE4BCEC |
| SHA256: | CA22758C4BCAAFC99145D00EE5EFF71F21D998E1E8DEF33C478909BCAA5B6198 |
| SSDEEP: | 3:N8BzGYdyKmMCkVIJJFAuQ3LWyRDRIYrJDEomW/MLTMRlFnX:2/kAV0J6xLWyRyQ3mWELeFnX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 3740)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 1000)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 1000)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 1000)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 1000)
INFO
Reads the computer name
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 3940)
Checks supported languages
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 3940)
Changes internet zones settings
- iexplore.exe (PID: 3740)
Checks Windows Trust Settings
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 3740)
Application launched itself
- iexplore.exe (PID: 3740)
Reads settings of System Certificates
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 3740)
Reads internet explorer settings
- iexplore.exe (PID: 3940)
Creates files in the user directory
- iexplore.exe (PID: 3940)
Reads CPU info
- iexplore.exe (PID: 3940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1000 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3740 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ibm.account.box.com/signup/collab/ele8dki2j8?utm_source=trans&utm_medium=email&utm_campaign=collab+invite%20new%20user" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3940 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3740 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
19 230
Read events
18 336
Write events
894
Delete events
0
Modification events
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 815078112 | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30986878 | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30986878 | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
26
Text files
117
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\personal[1].htm | html | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\XNEMZQ02.txt | text | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\2C8BC4SE.txt | text | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\runtime.5a890d7672[1].js | text | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E573CDF4C6D731D56A665145182FD759_392951F311F0459604720BBB05F119BE | binary | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E573CDF4C6D731D56A665145182FD759_392951F311F0459604720BBB05F119BE | der | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\LW6MY47A.txt | text | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\vendors~app.34de5797a6[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
110
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3940 | iexplore.exe | GET | 304 | 8.248.101.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e3124b720710ad90 | US | — | — | whitelisted |
3940 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEA7ze%2BiSFHmYKH4I97FkjrU%3D | US | der | 471 b | whitelisted |
3940 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3940 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHe9DgdC1dnp0EnXdNAqb5o%3D | US | der | 1.40 Kb | whitelisted |
3940 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA69wbklOYOsQ8xpjrp7KAk%3D | US | der | 471 b | whitelisted |
3940 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAiUAg1J7ie9IHbDN8v5koI%3D | US | der | 471 b | whitelisted |
3740 | iexplore.exe | GET | 200 | 8.248.101.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2232fbfc8c321370 | US | compressed | 4.70 Kb | whitelisted |
3940 | iexplore.exe | GET | 200 | 172.217.19.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3940 | iexplore.exe | GET | 200 | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?508b510f7b4d0572 | US | compressed | 4.70 Kb | whitelisted |
3740 | iexplore.exe | GET | 200 | 8.248.101.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f6e46d0794eb46dc | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3940 | iexplore.exe | 74.112.186.144:443 | ibm.account.box.com | GOOGLE-CLOUD-PLATFORM | US | suspicious |
3940 | iexplore.exe | 23.216.77.80:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | suspicious |
3740 | iexplore.exe | 131.253.33.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3940 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3940 | iexplore.exe | 23.216.77.69:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | suspicious |
3740 | iexplore.exe | 13.107.22.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3740 | iexplore.exe | 8.248.101.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
3740 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
3940 | iexplore.exe | 8.248.101.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
3940 | iexplore.exe | 104.16.74.20:443 | cdn01.boxcdn.net | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ibm.account.box.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
cdn01.boxcdn.net |
| whitelisted |
ibm.ent.box.com |
| whitelisted |