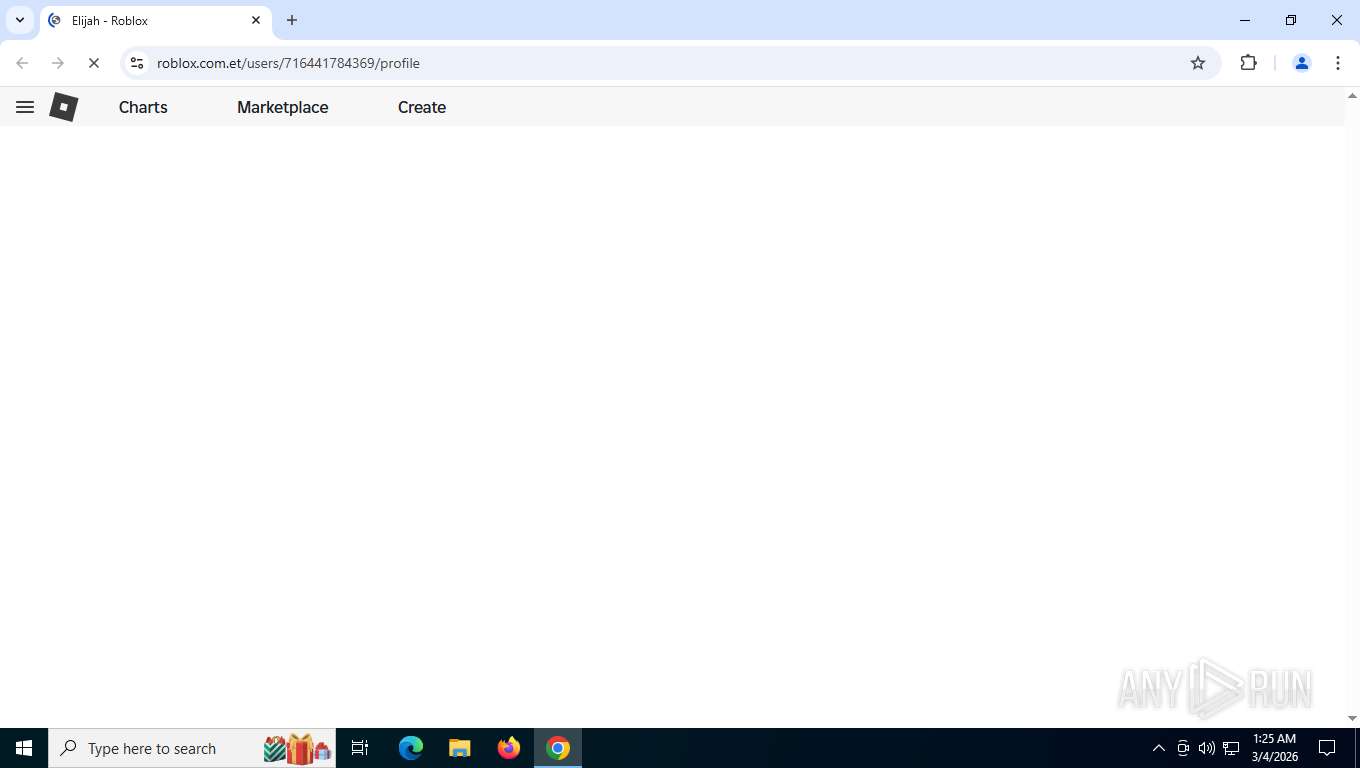
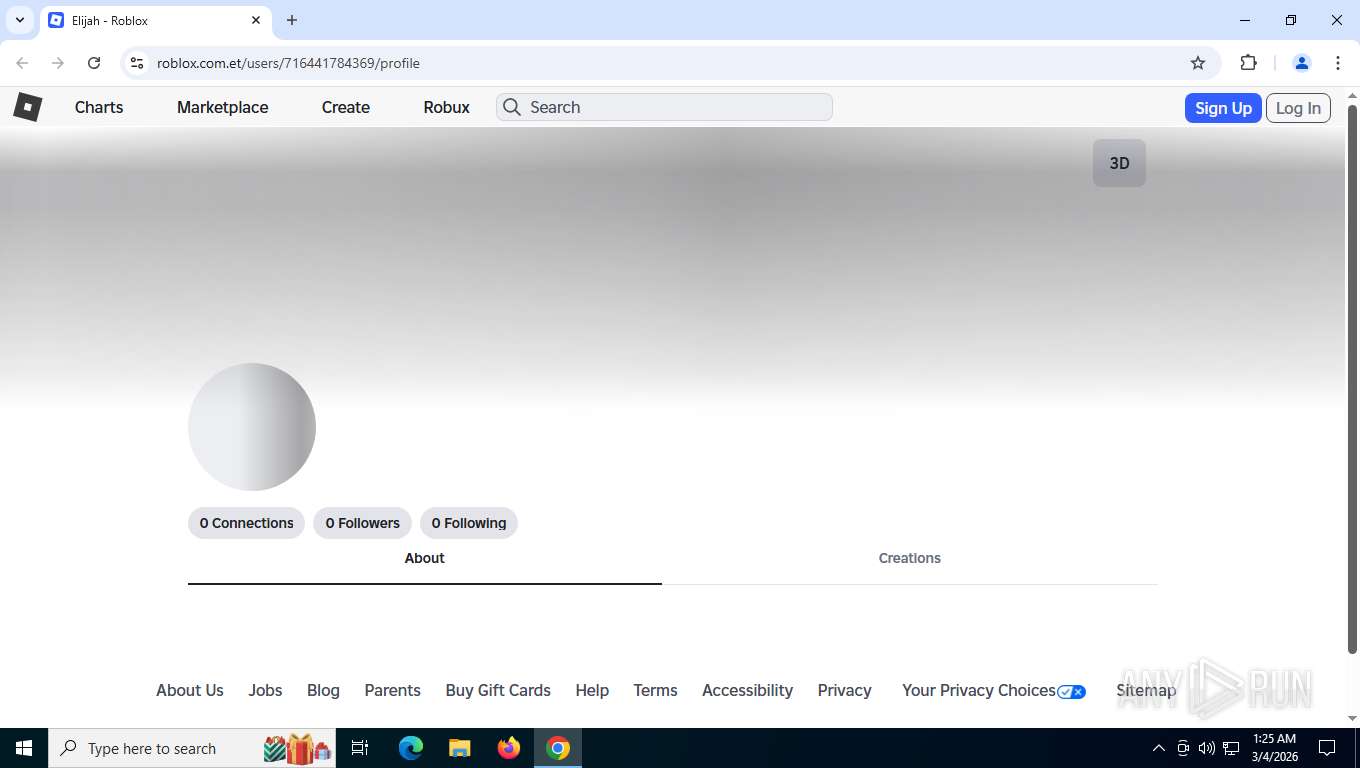
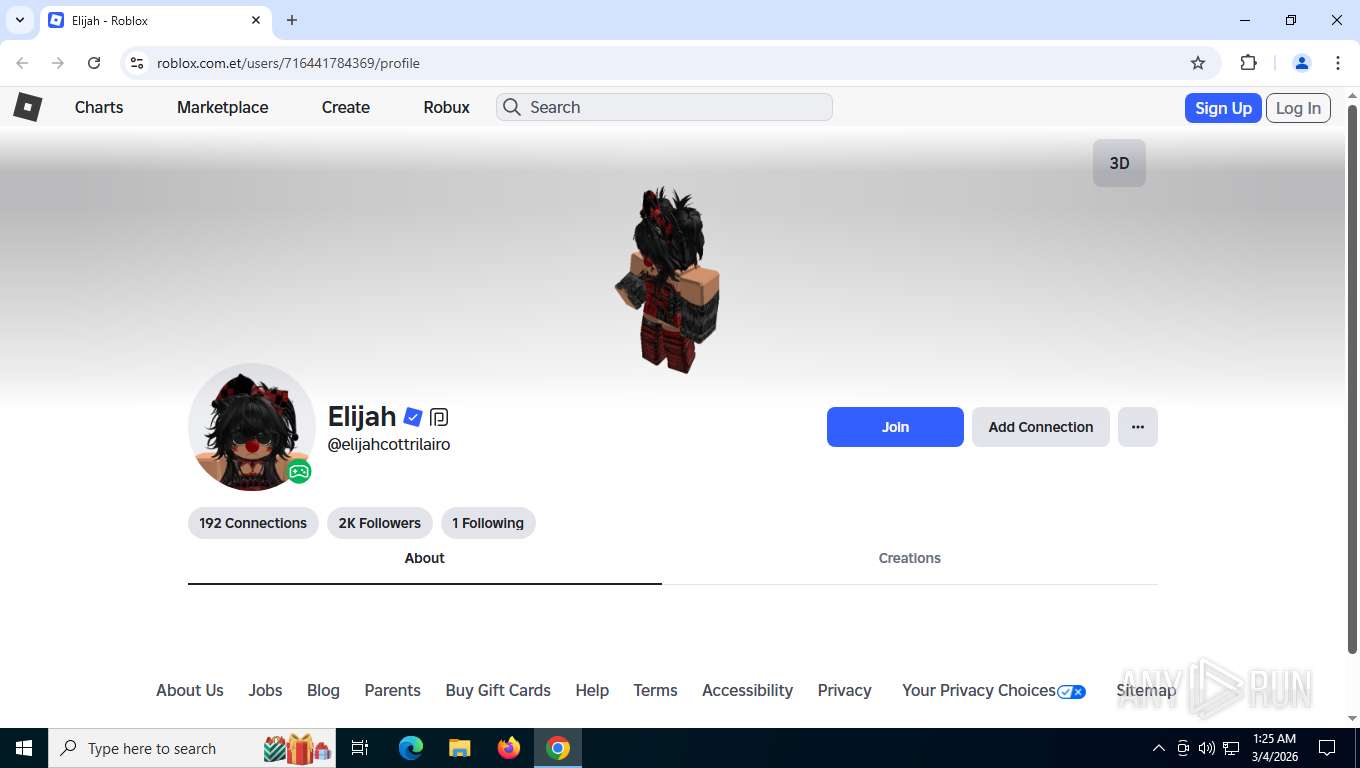
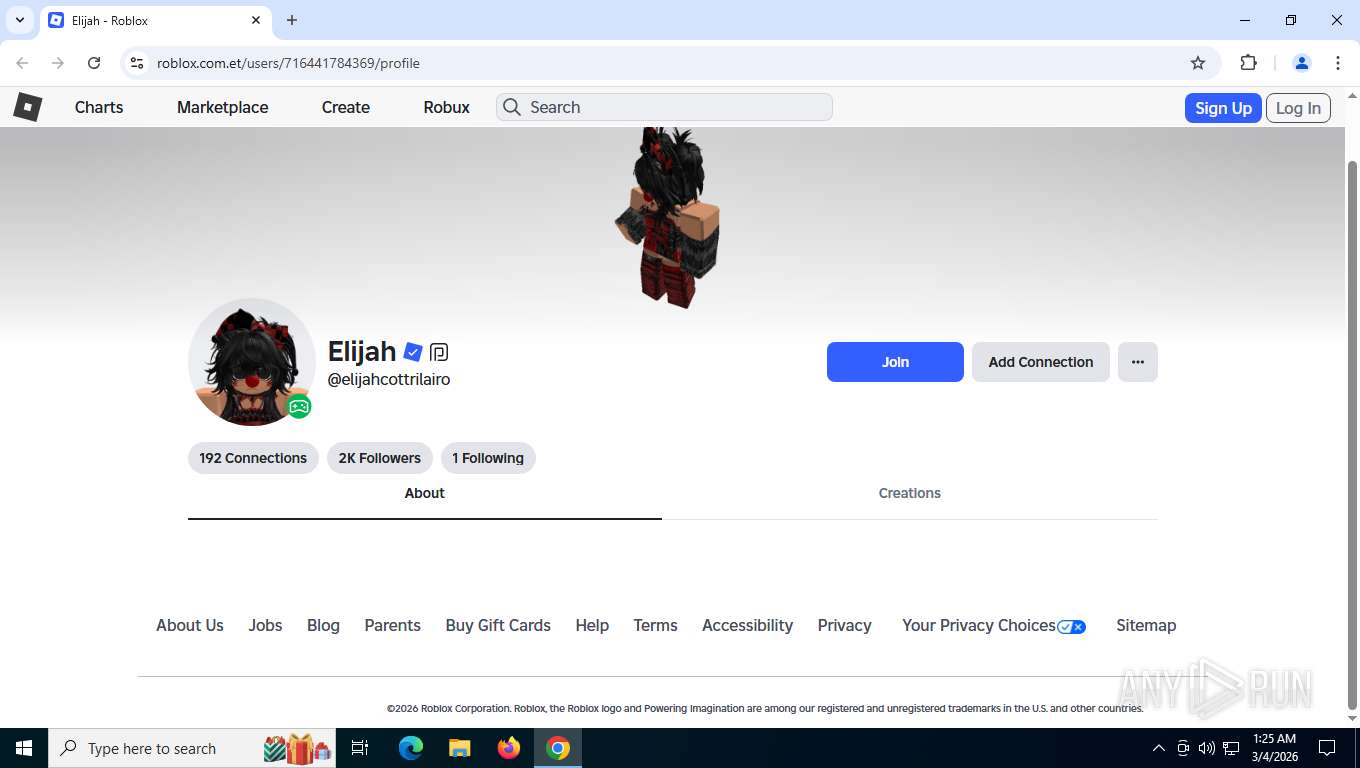
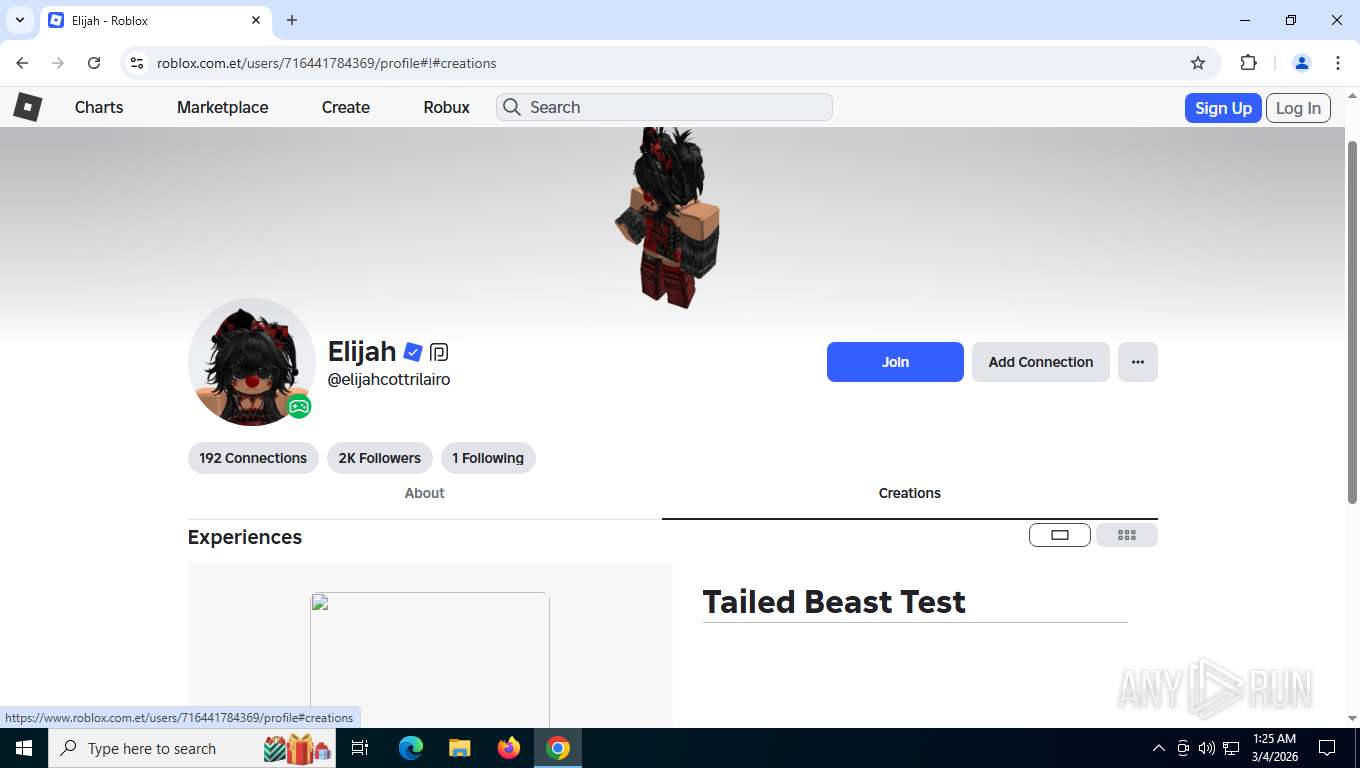
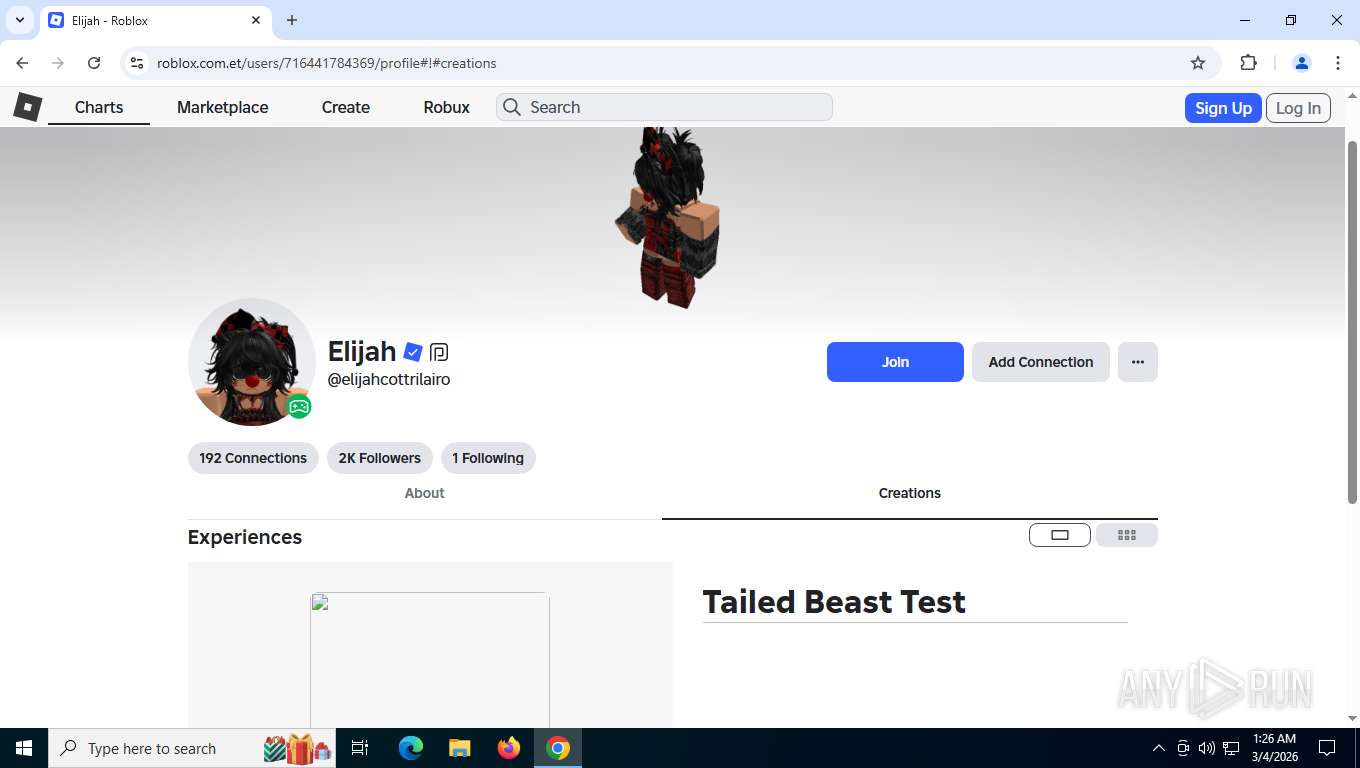
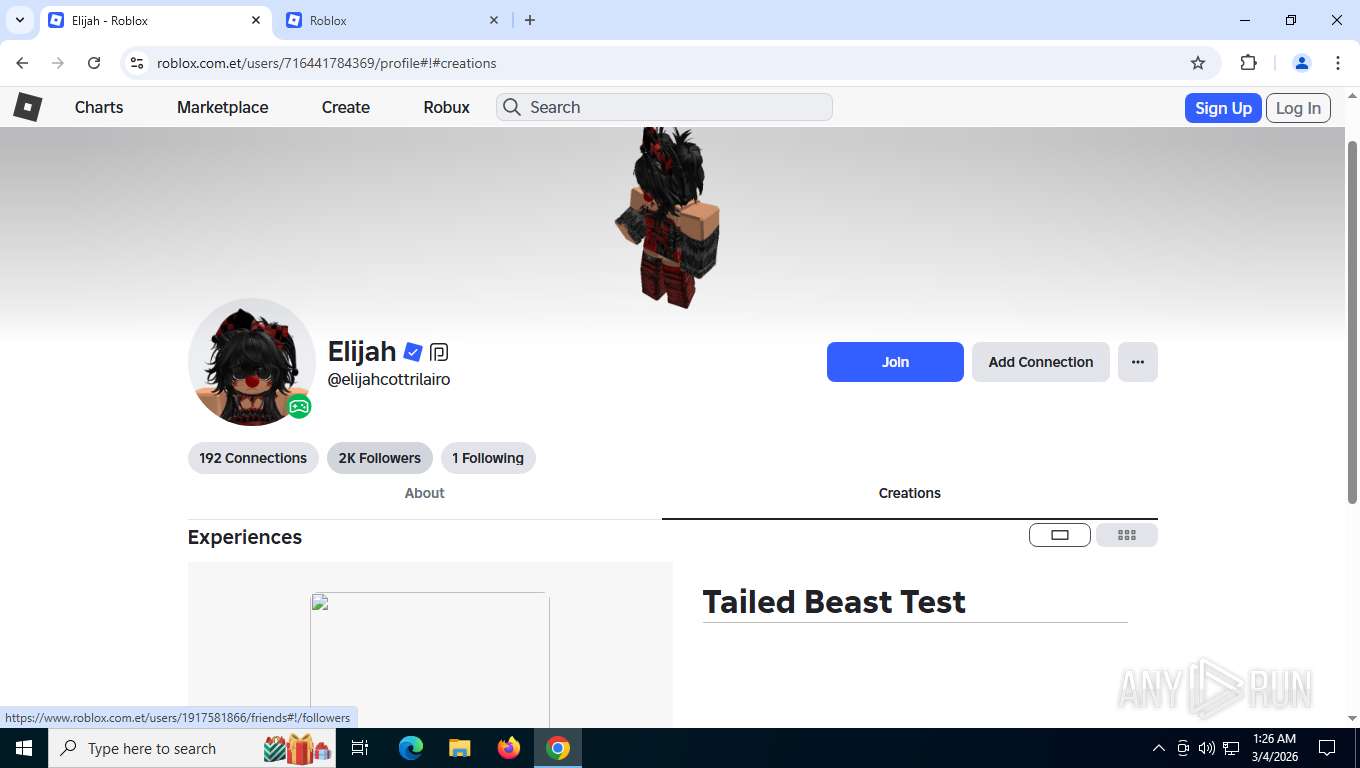
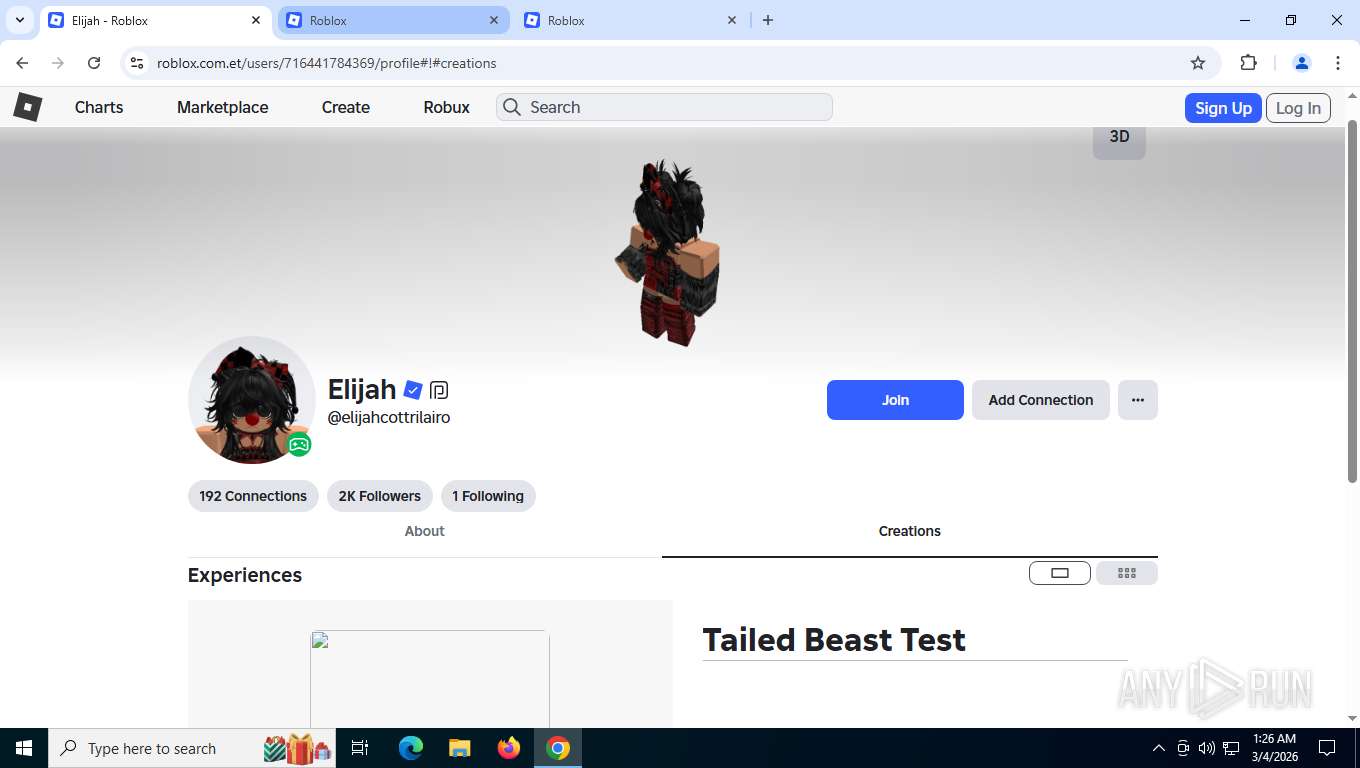
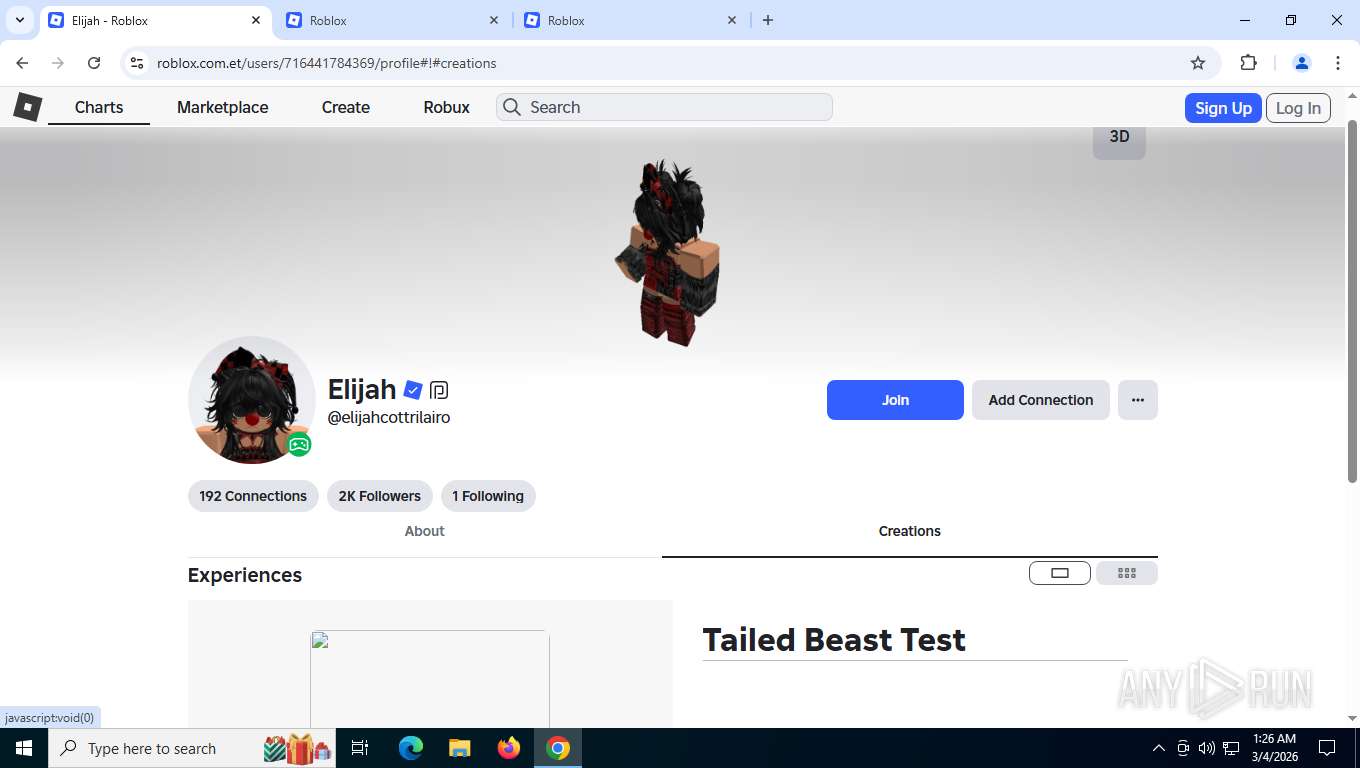
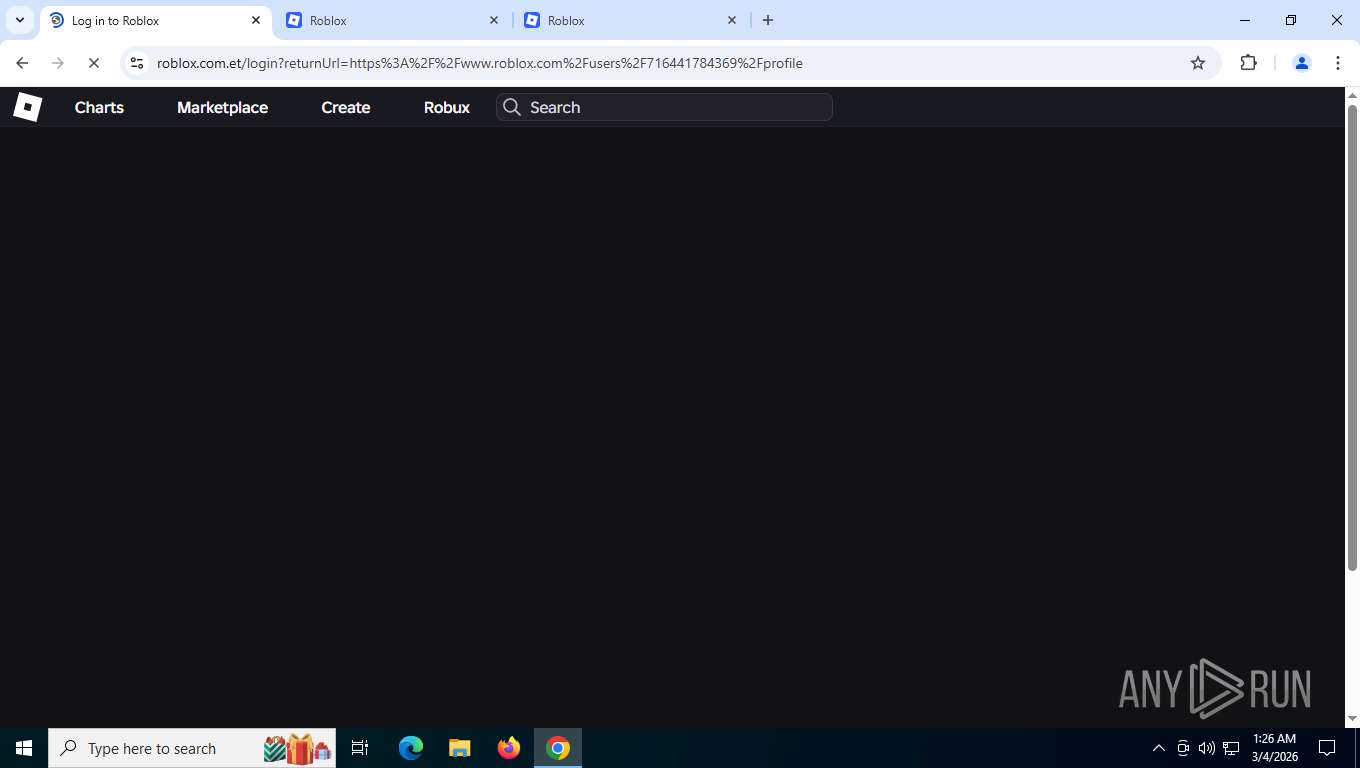
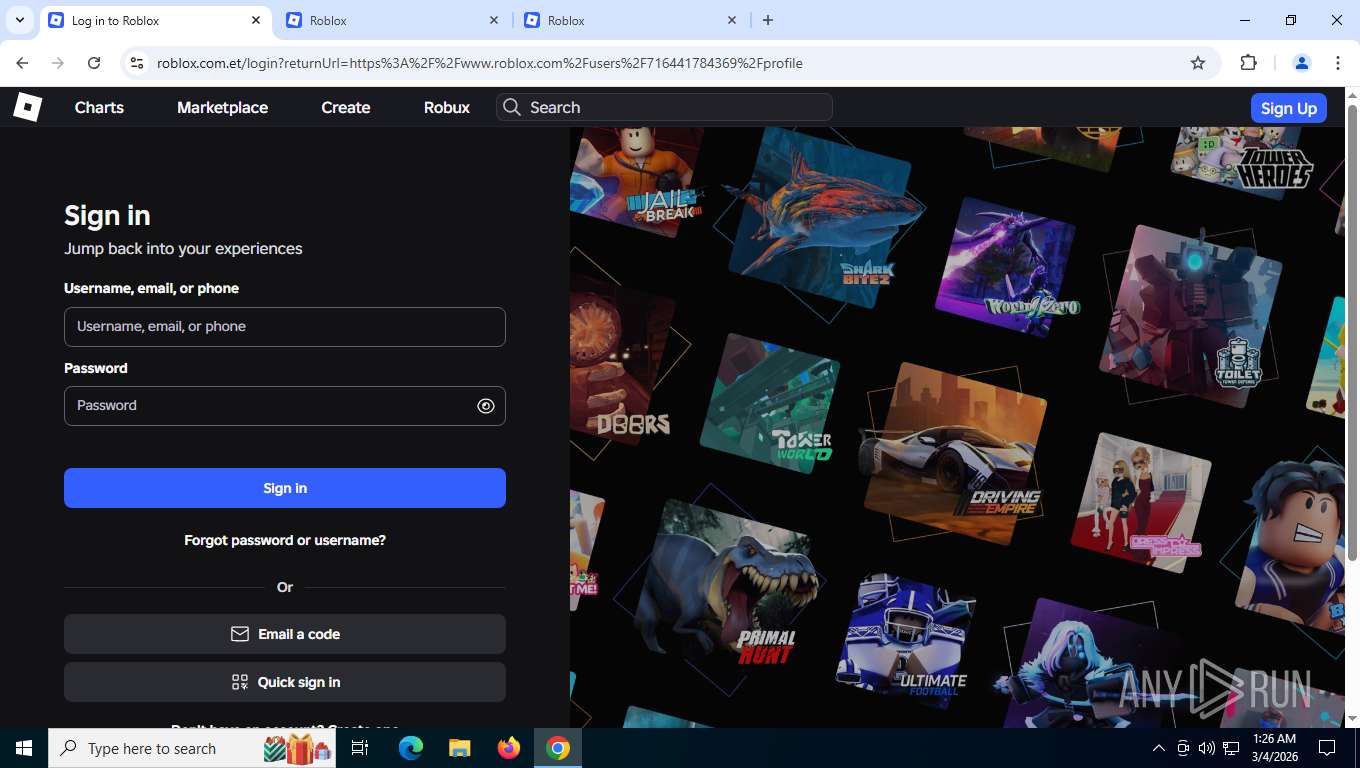
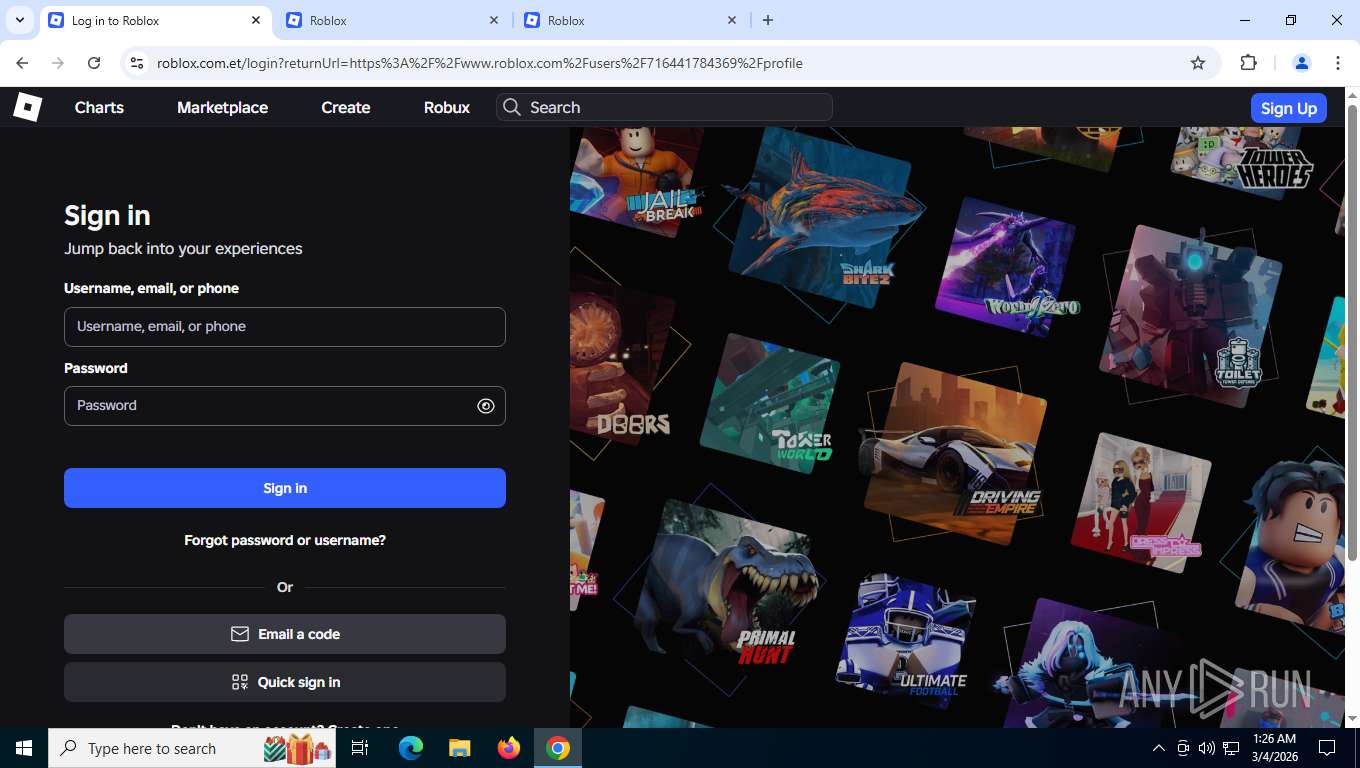
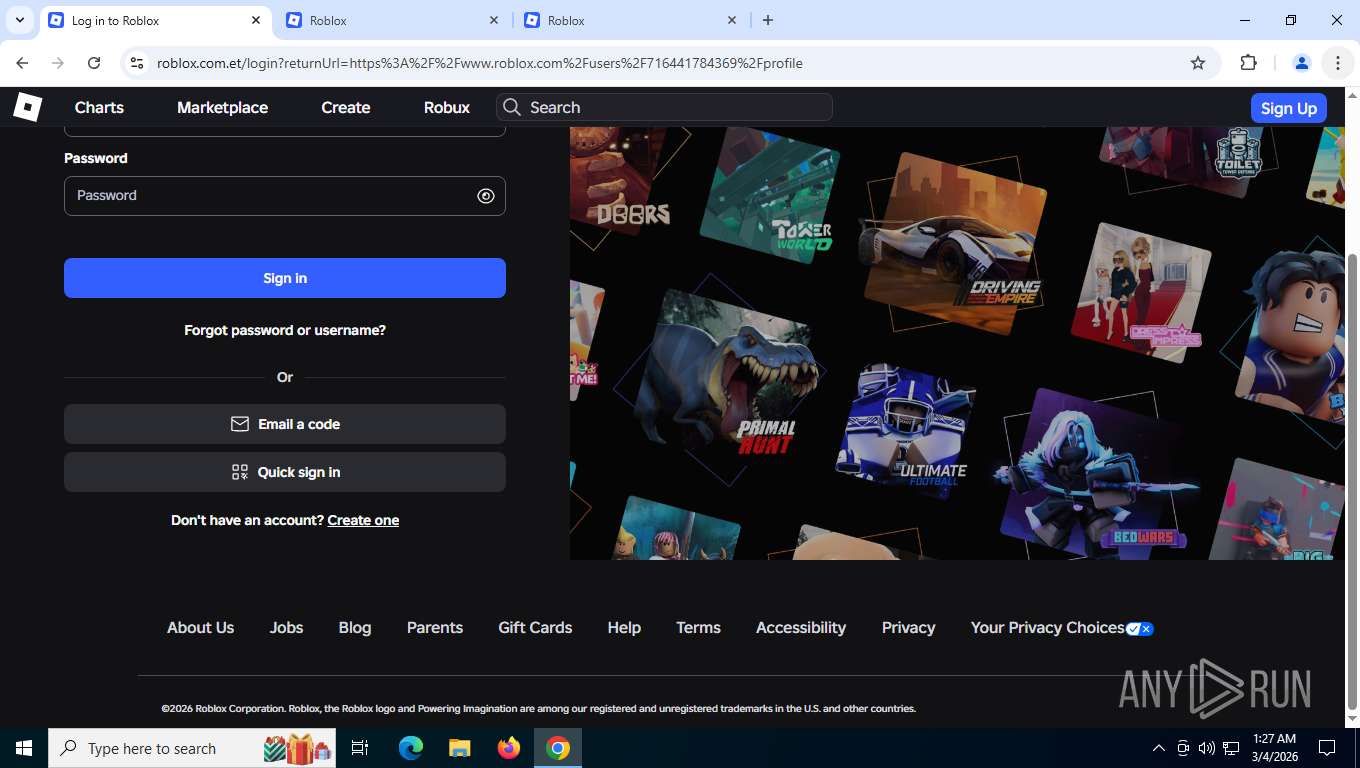
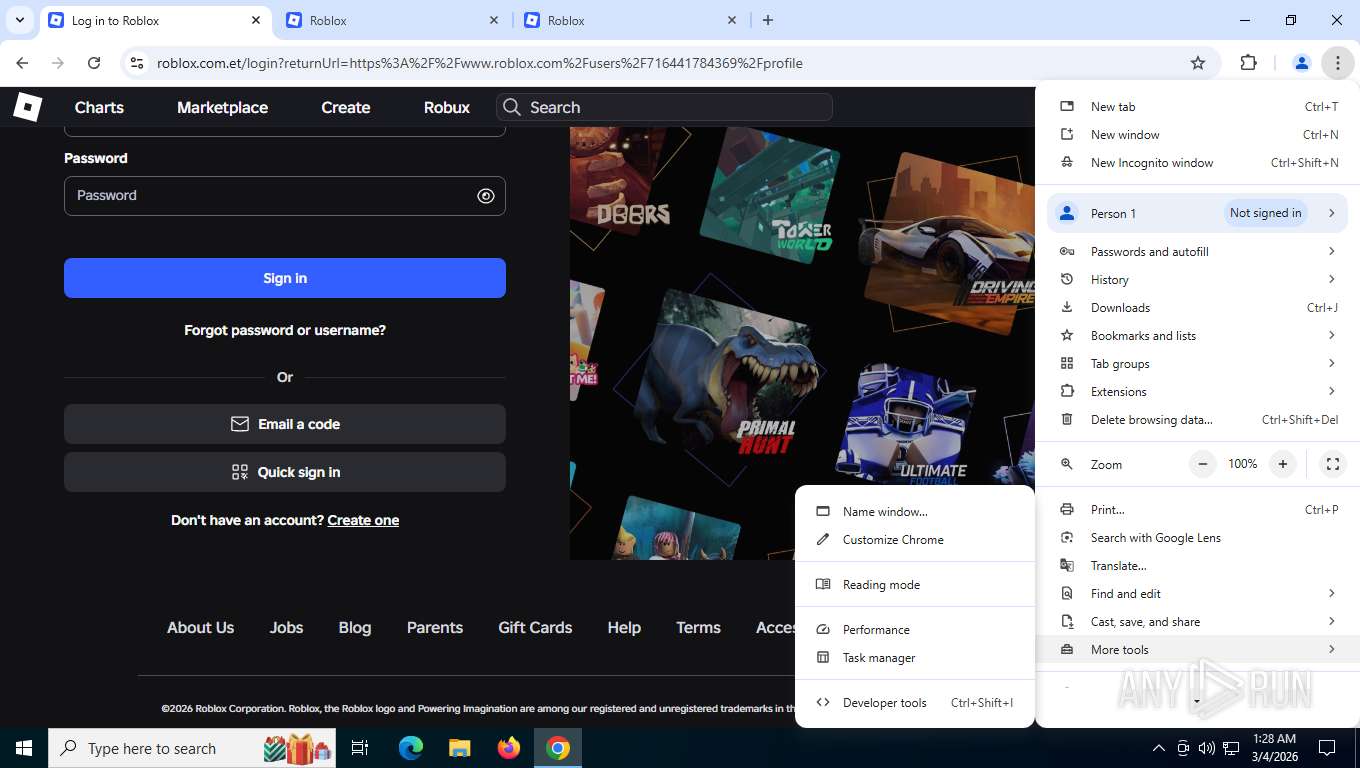
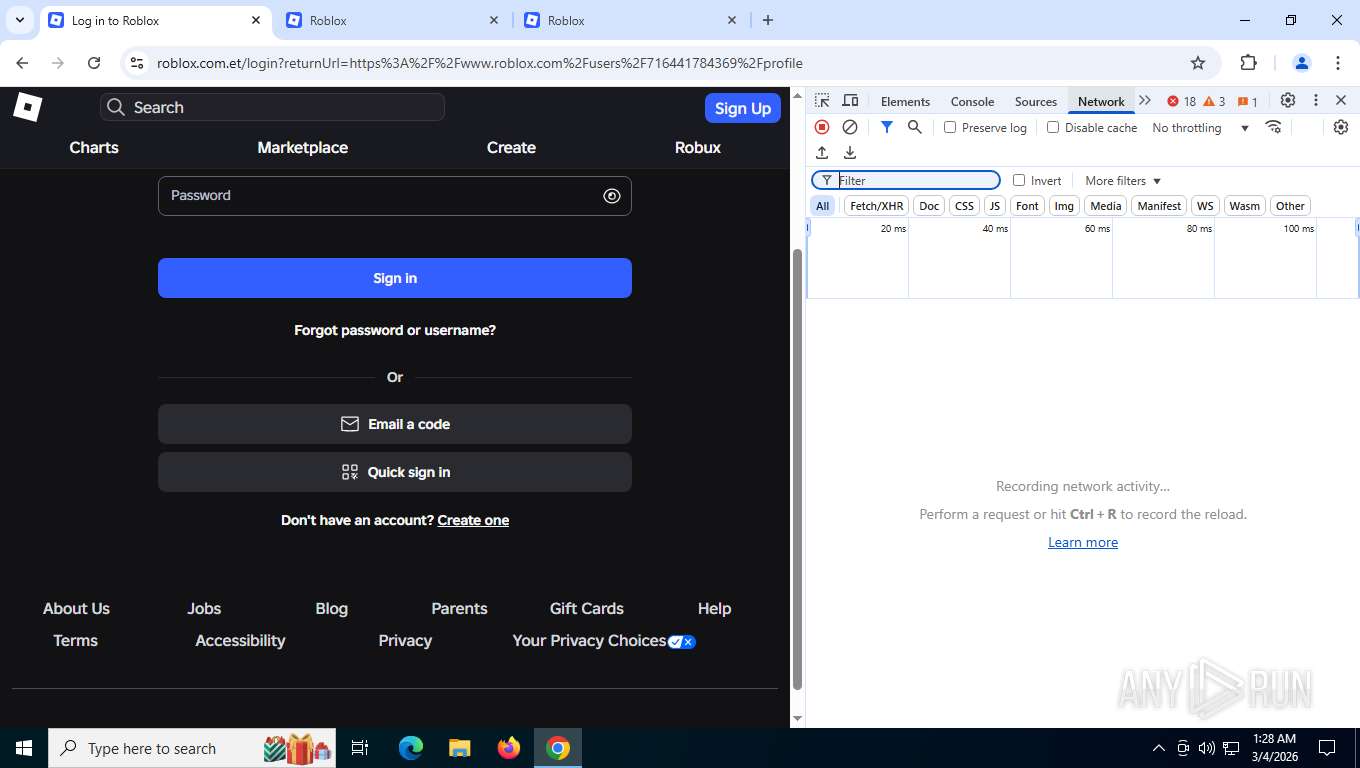
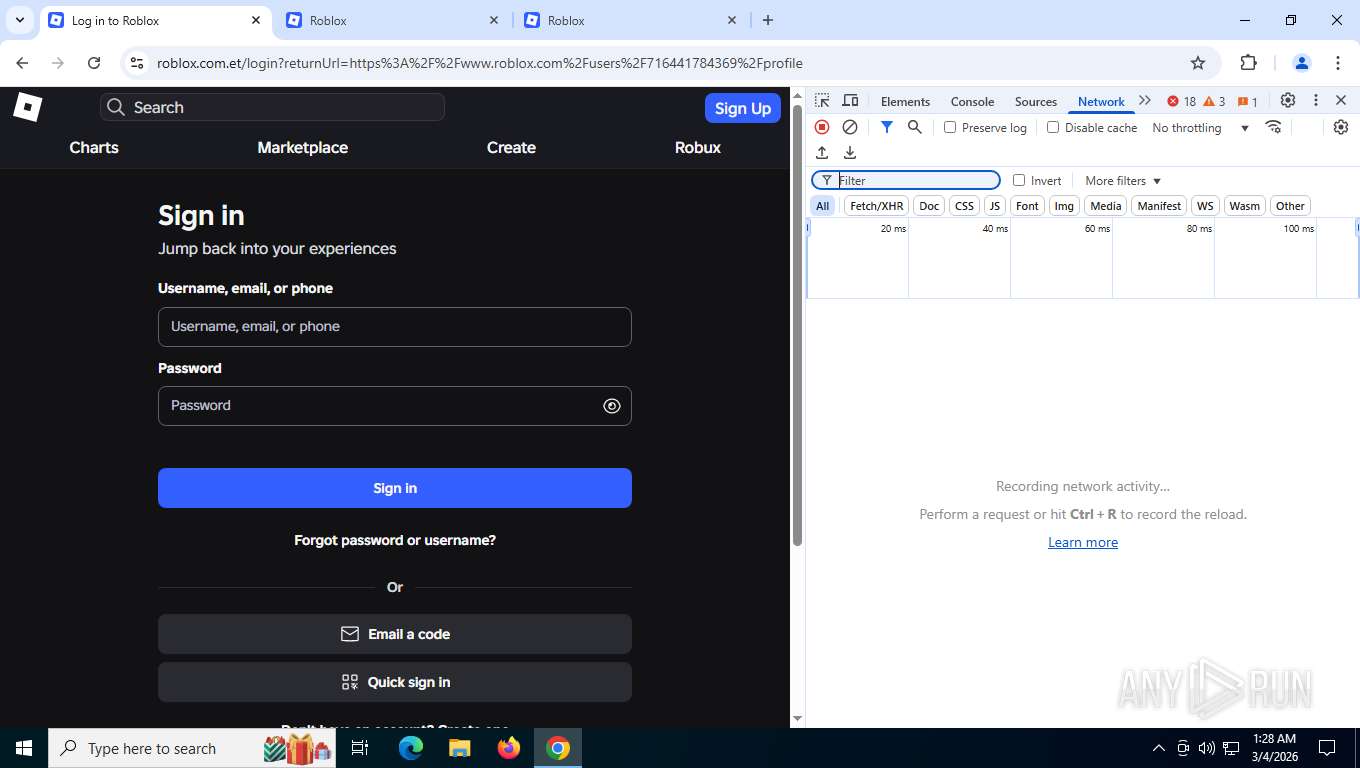
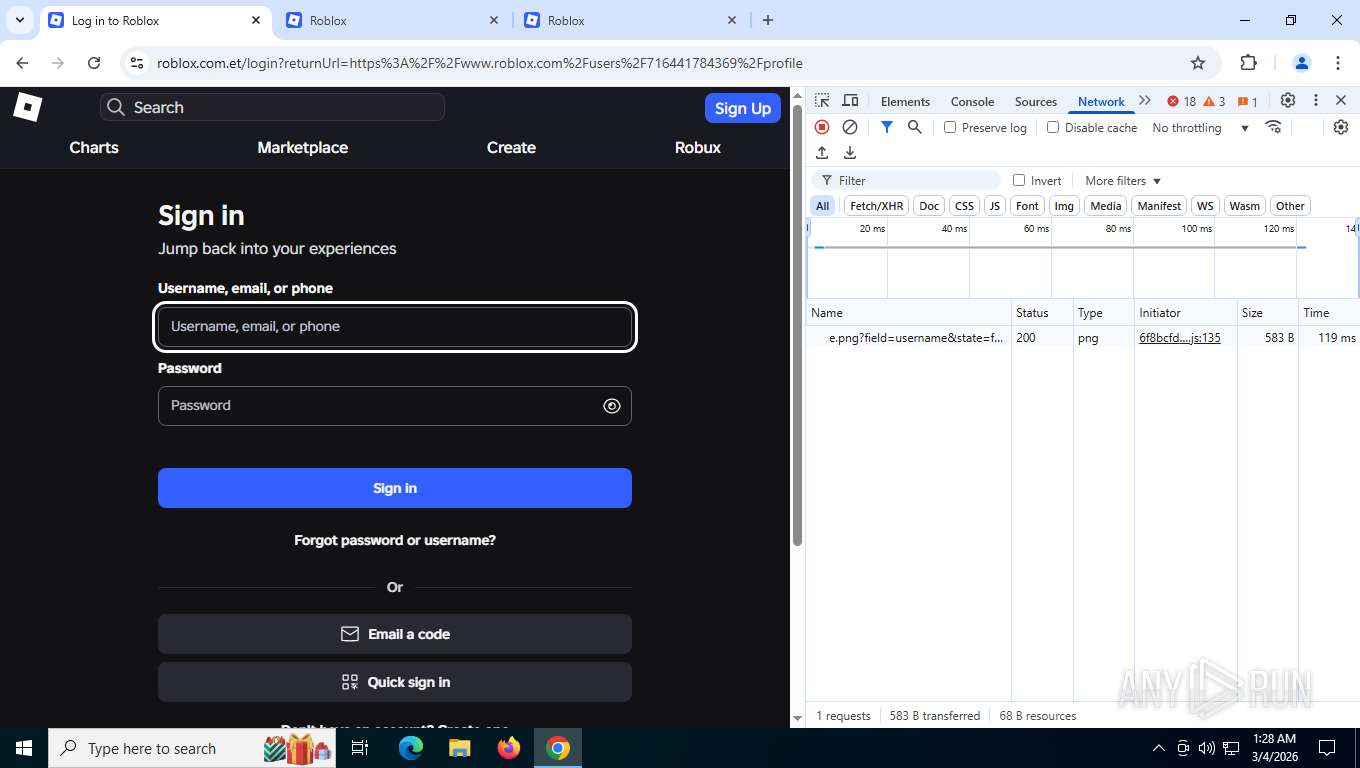
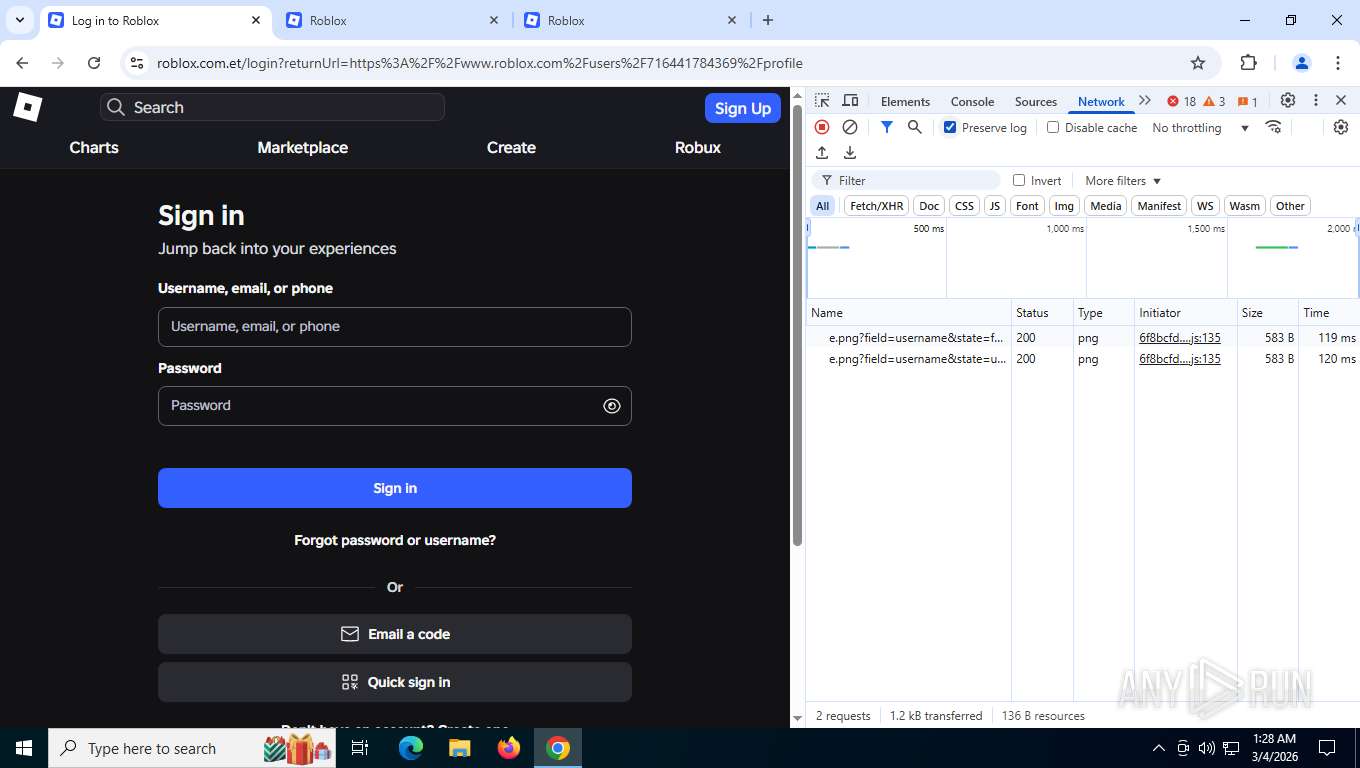
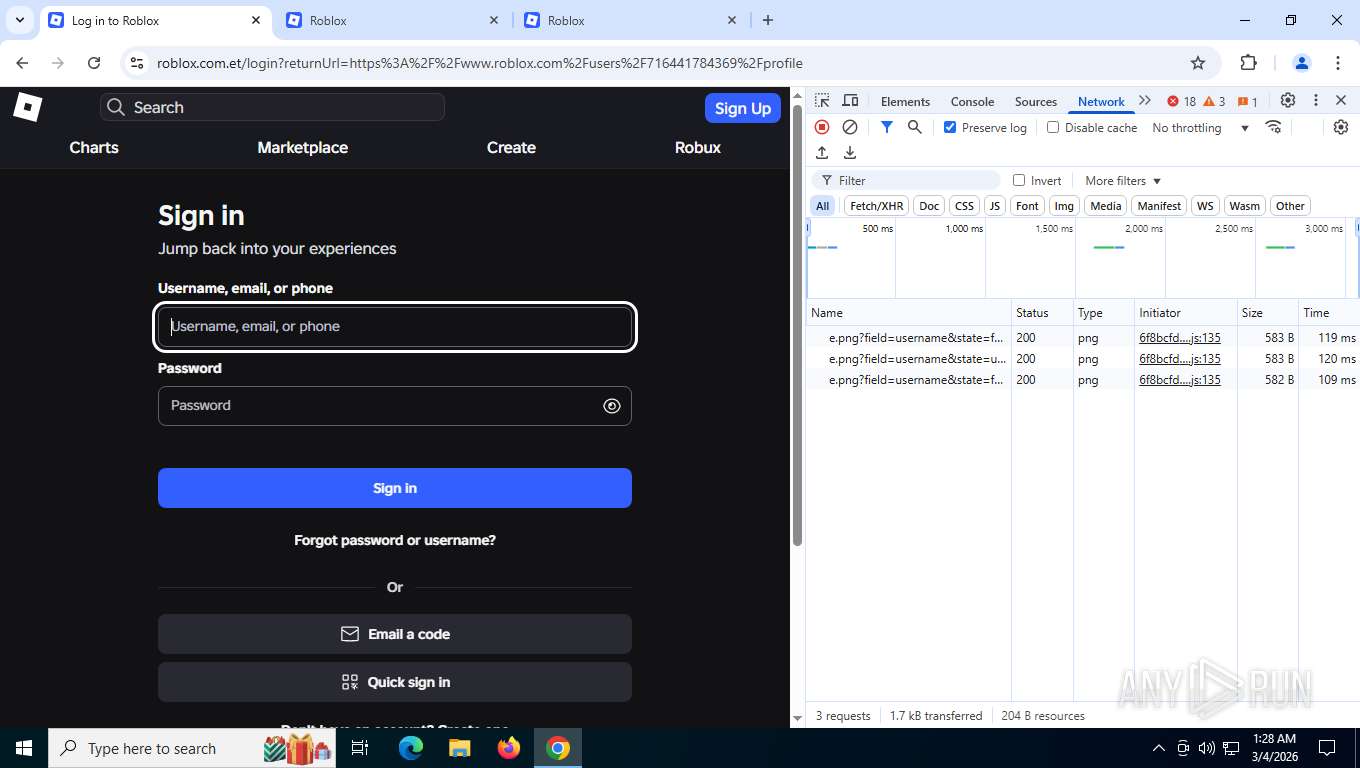
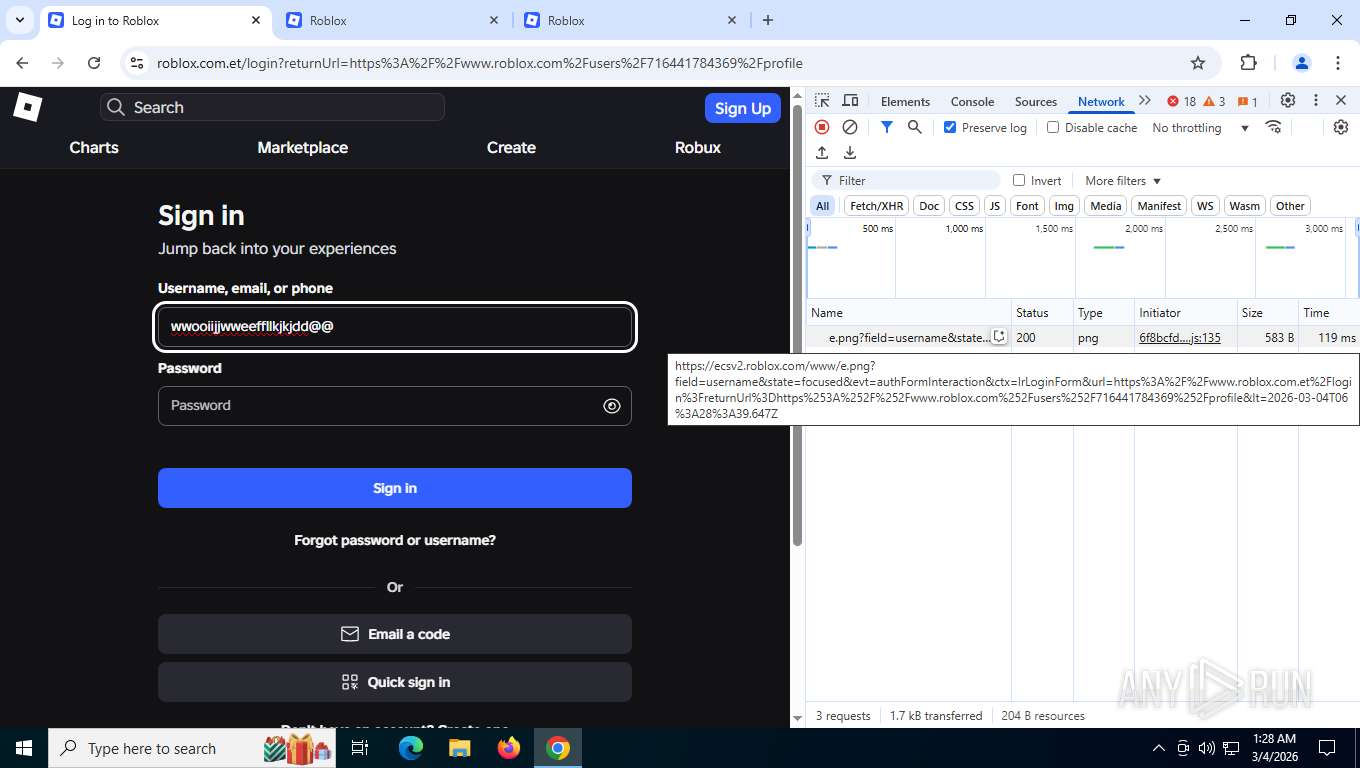
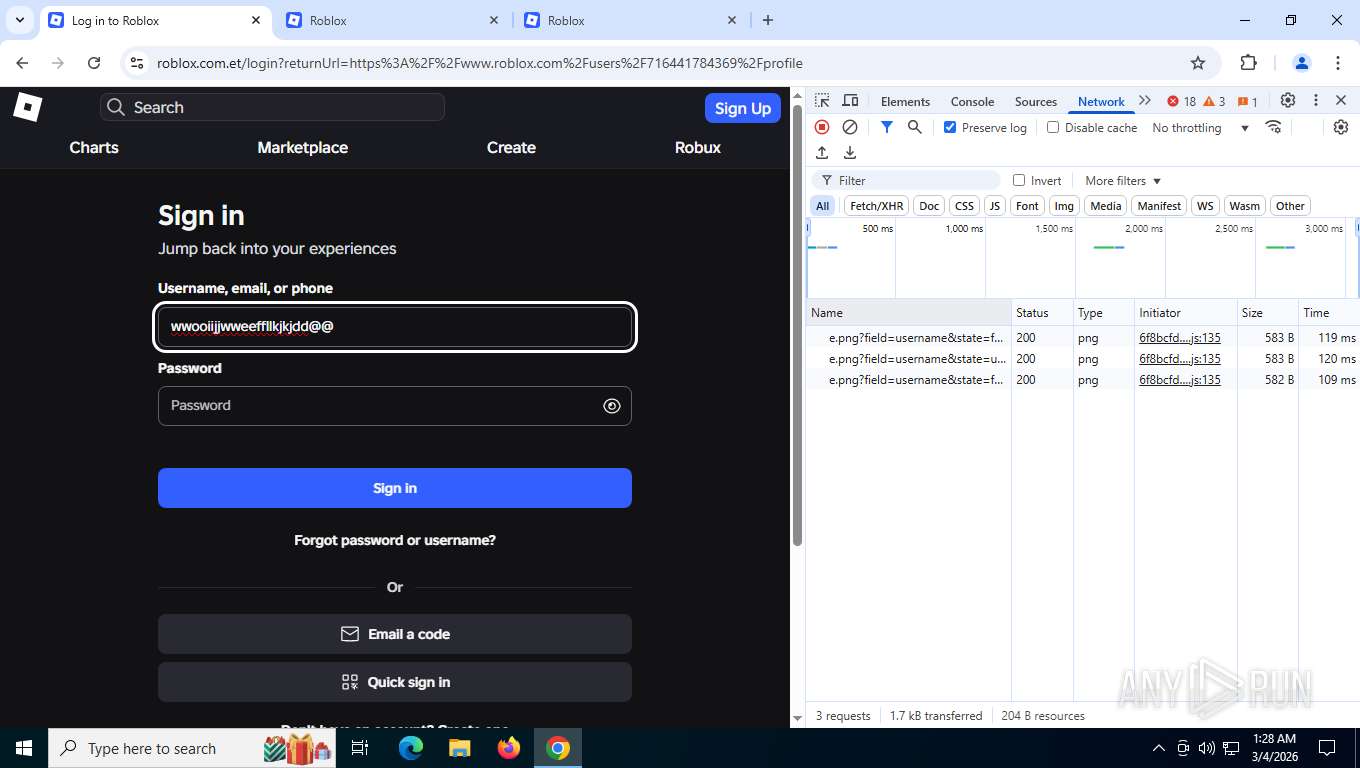
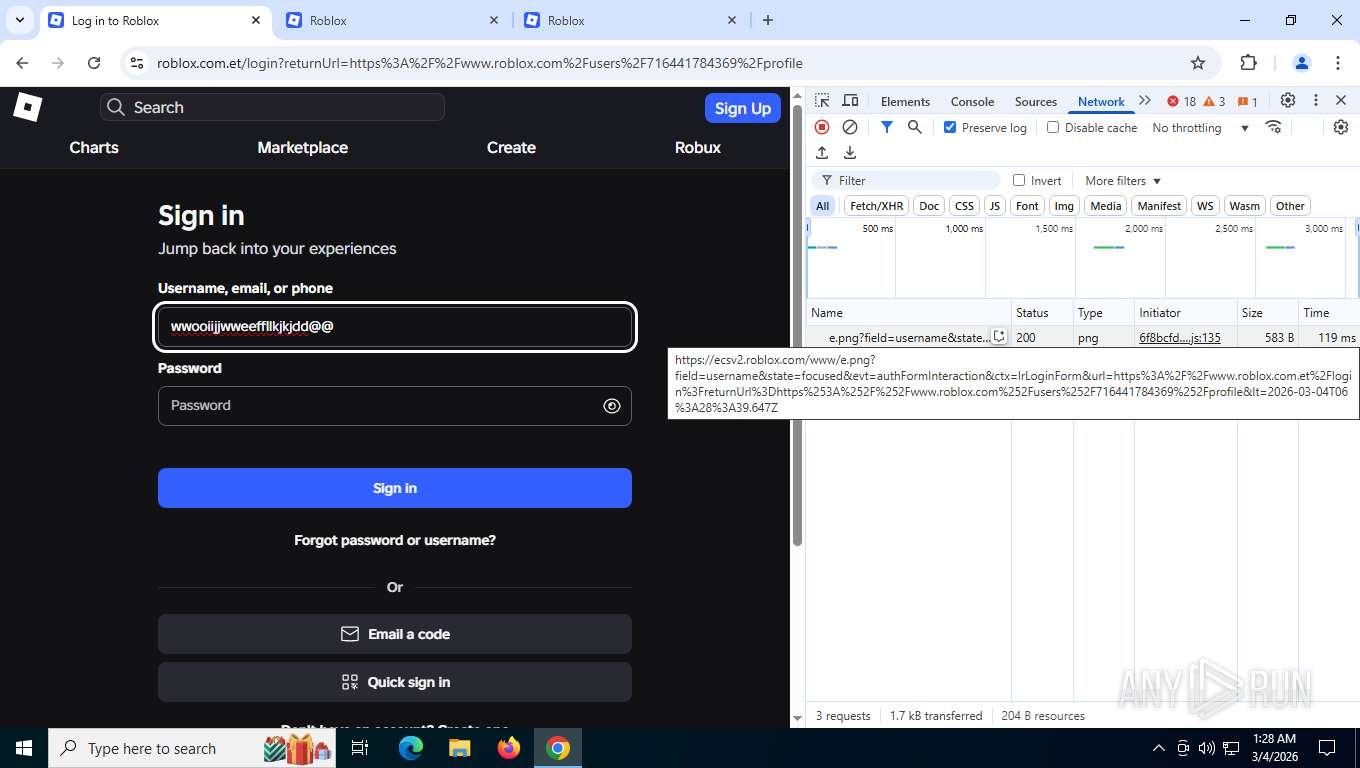
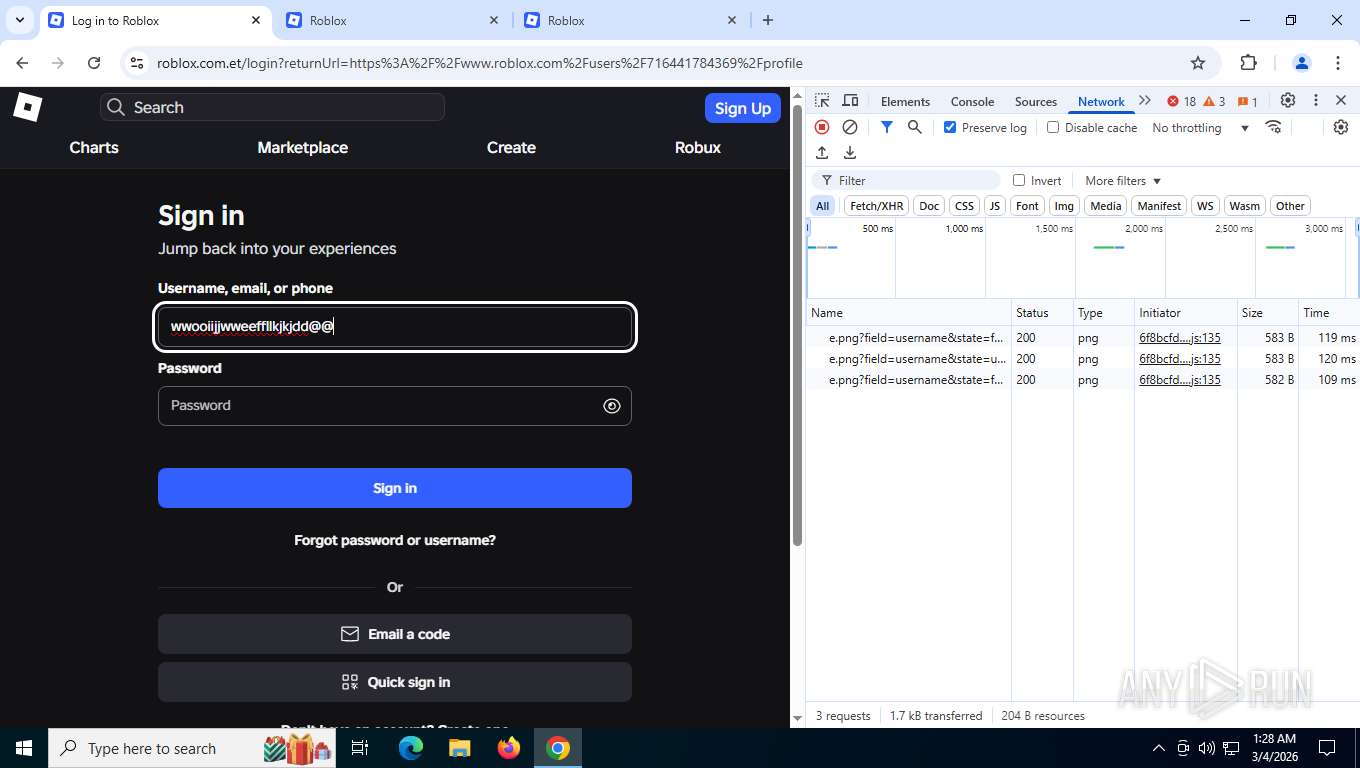
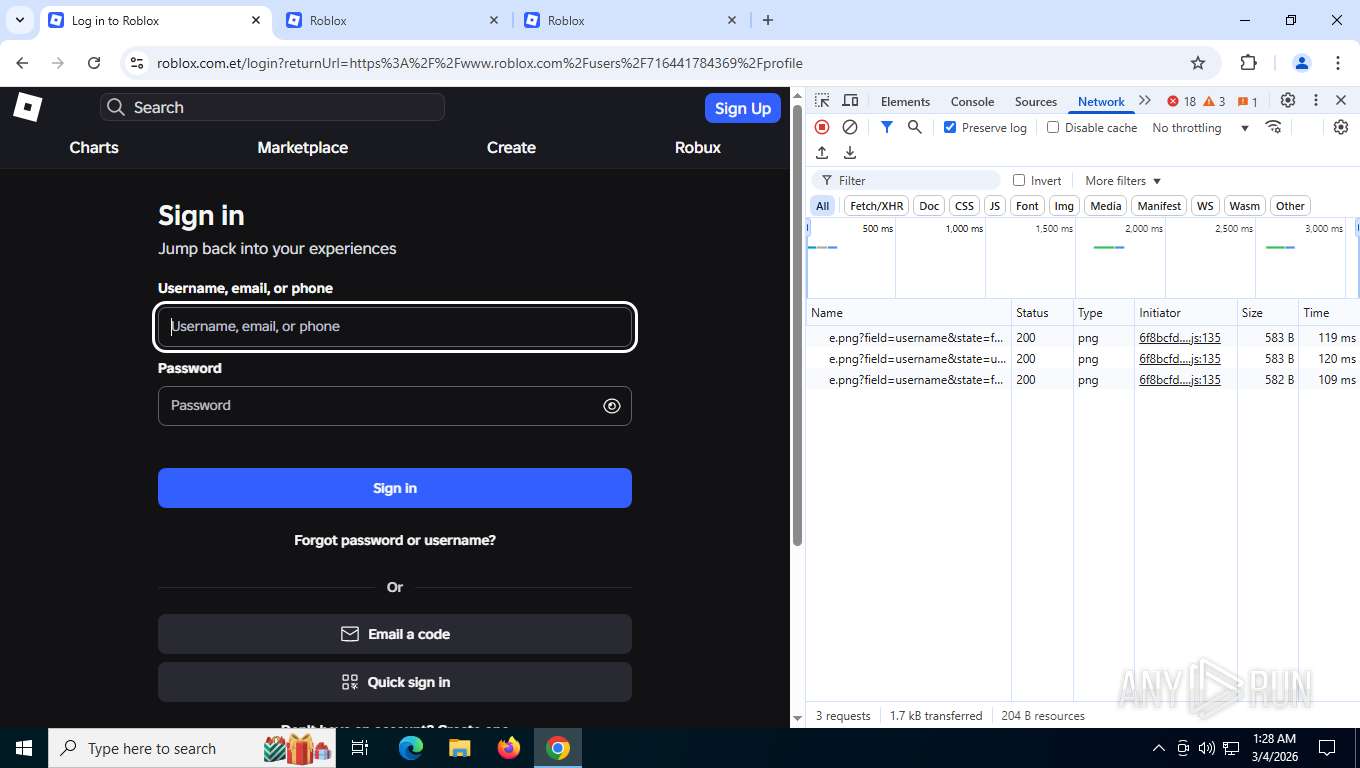
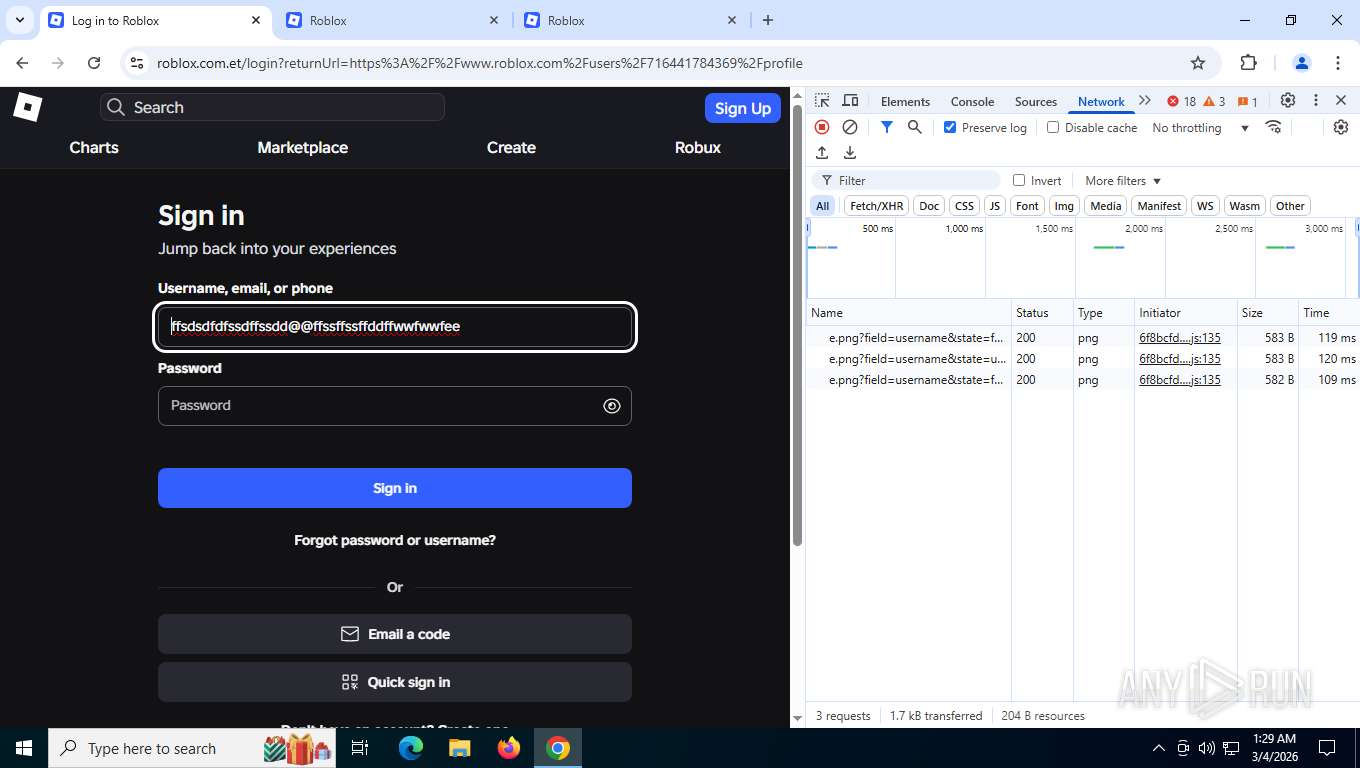
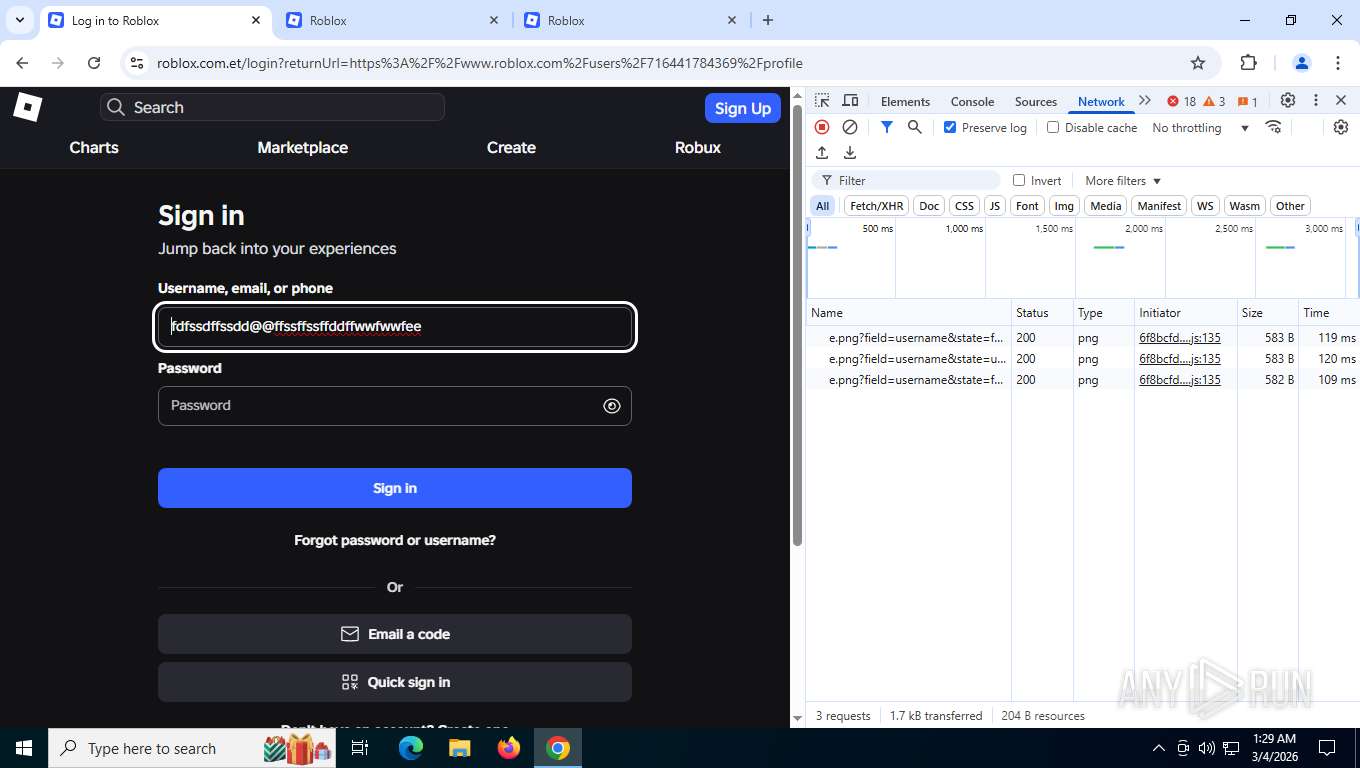
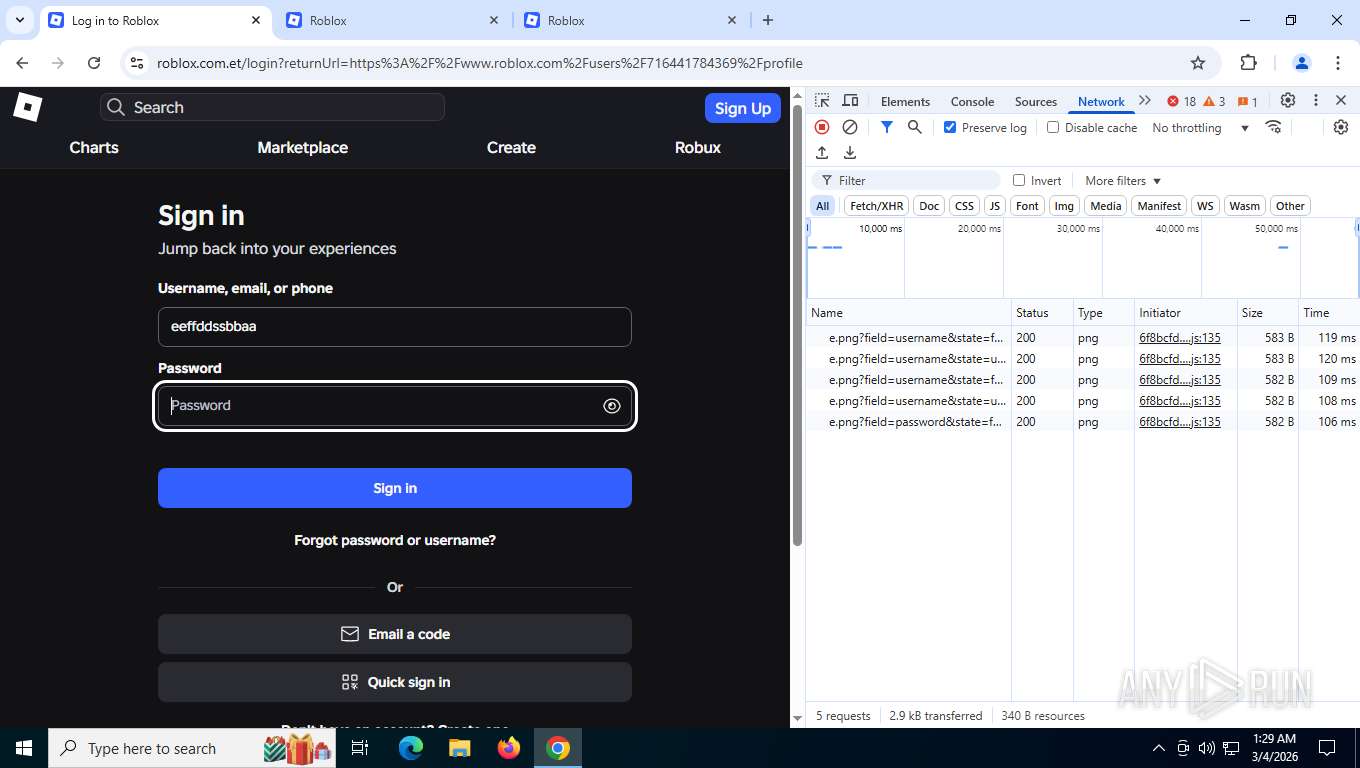
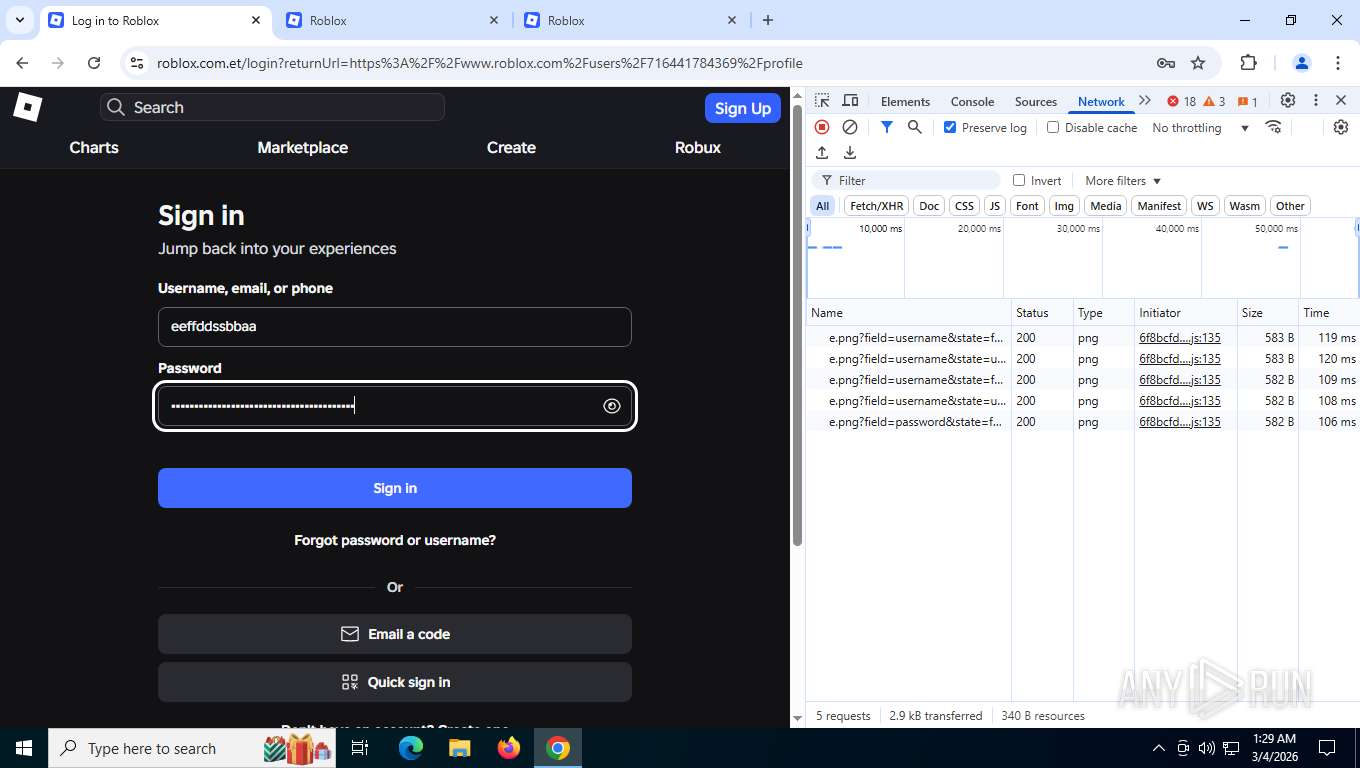
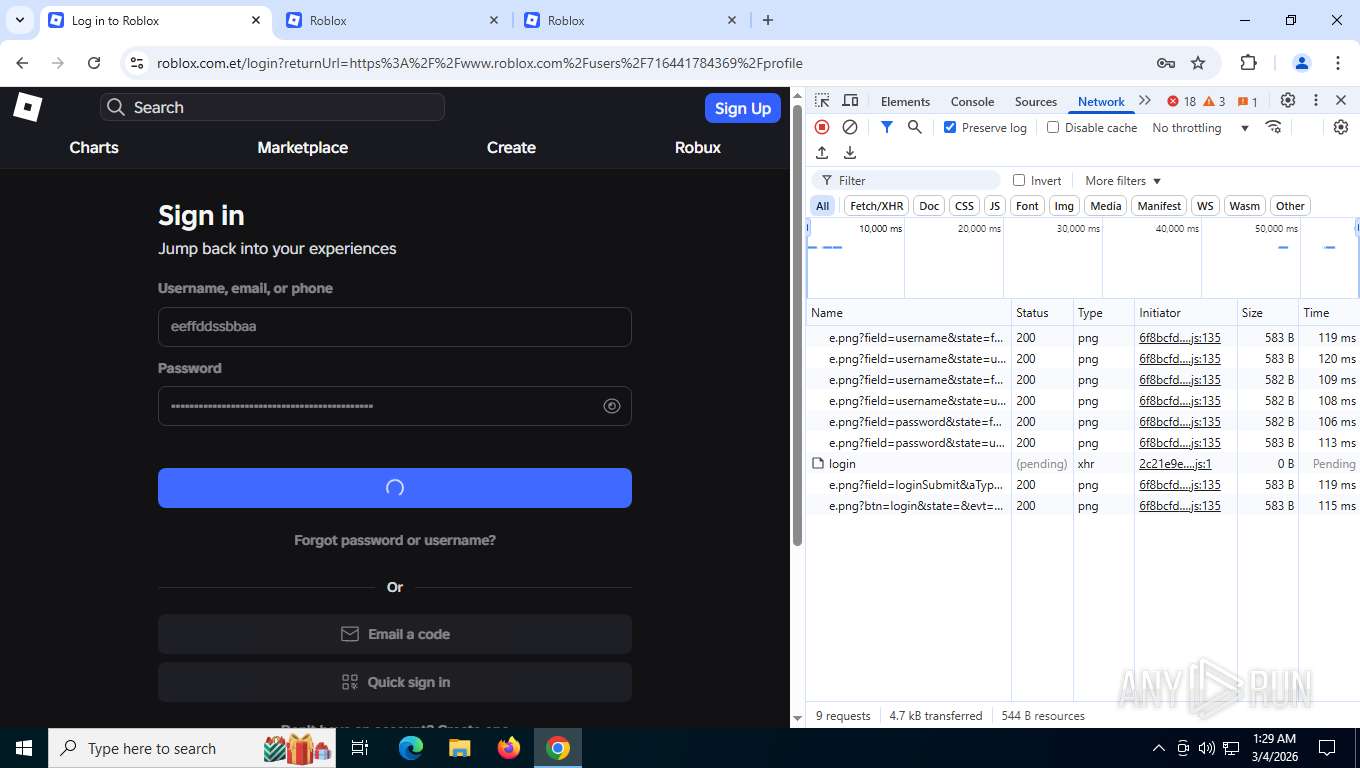
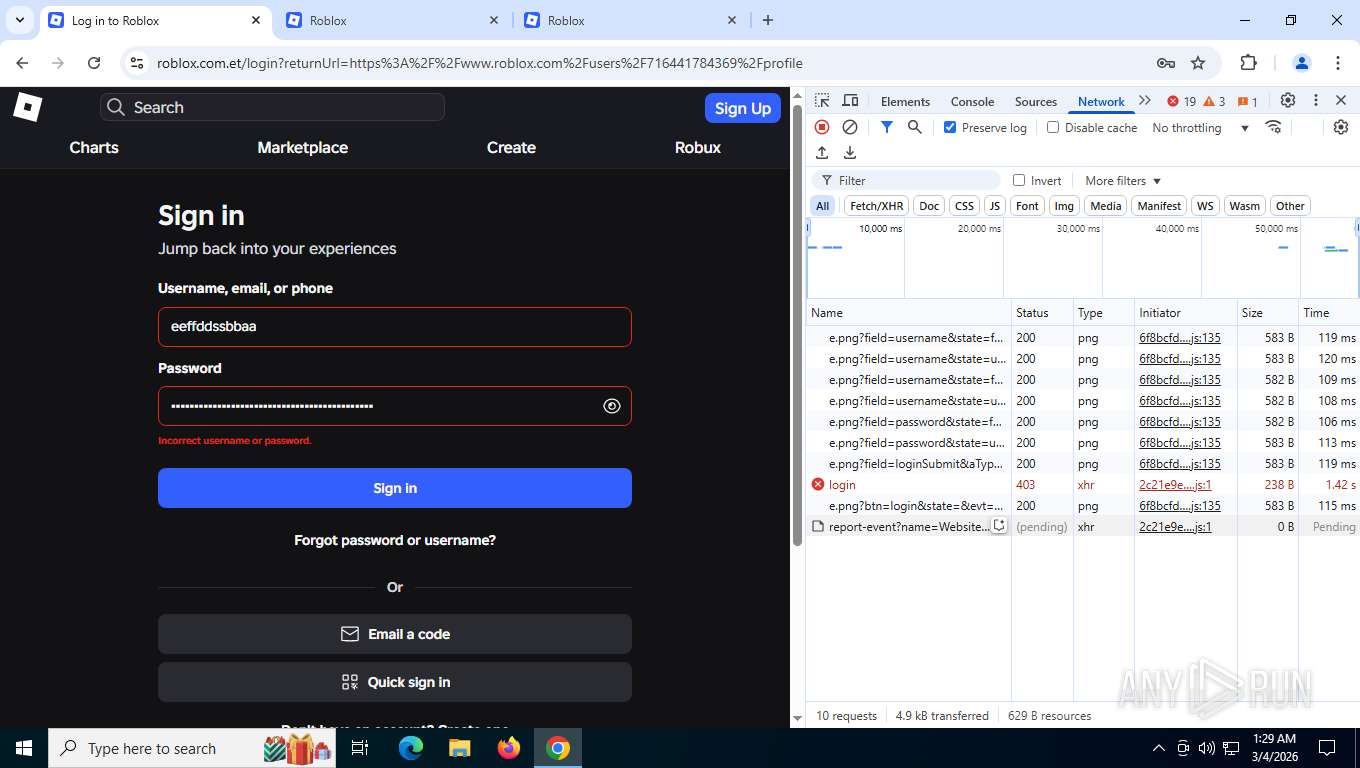
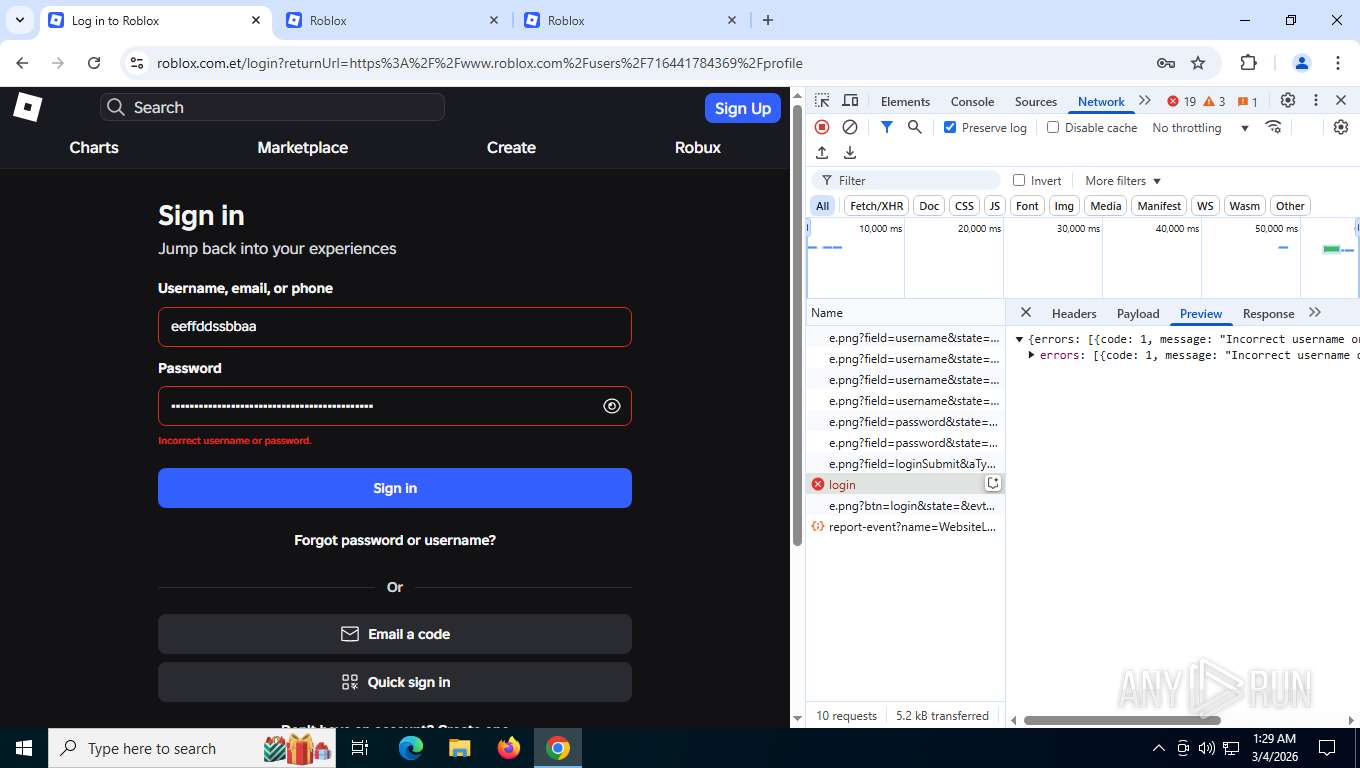
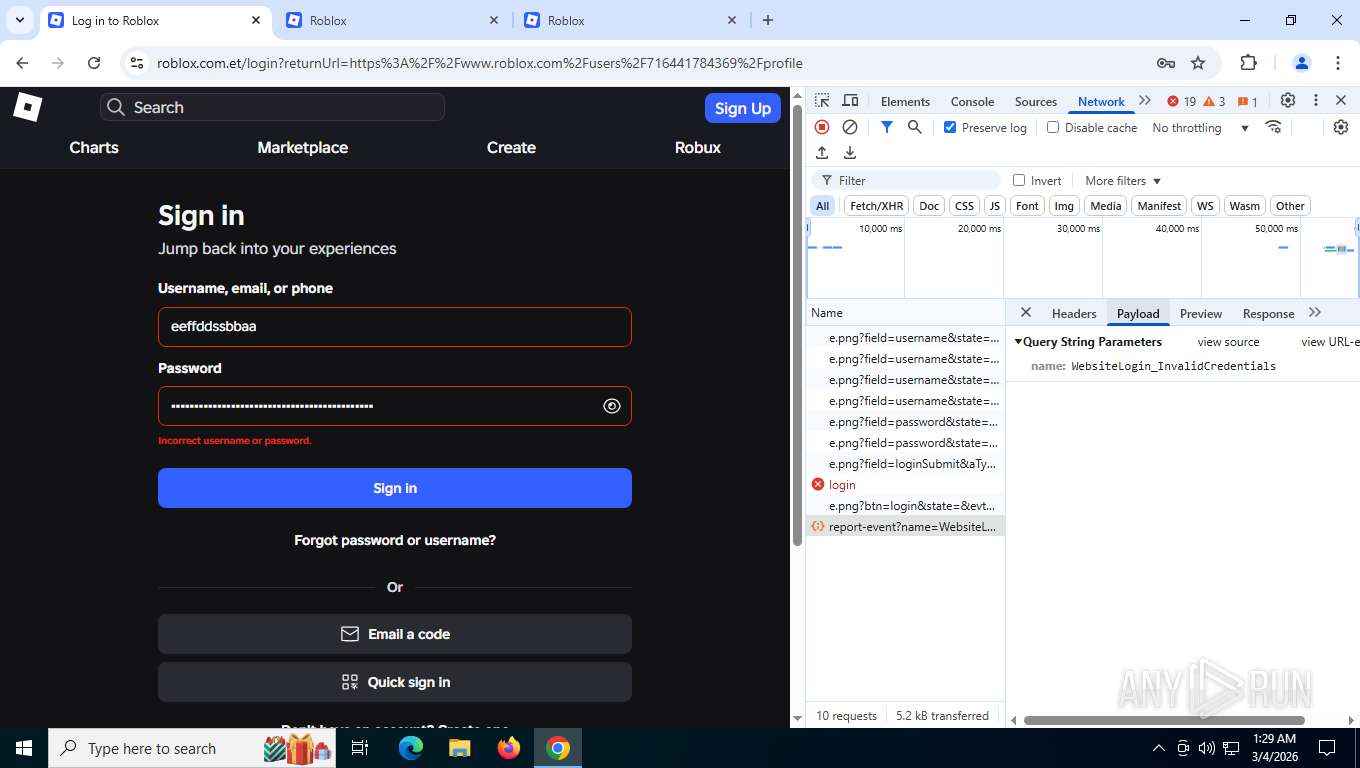
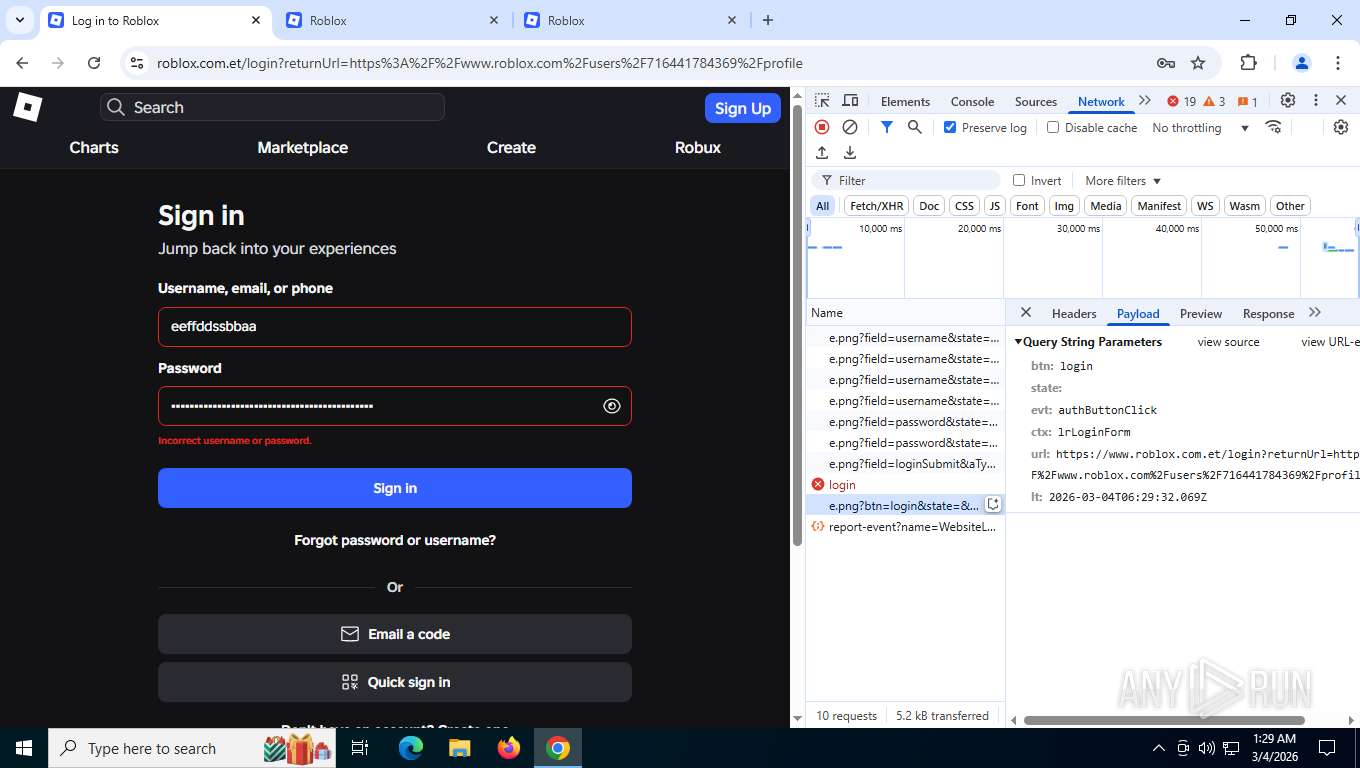
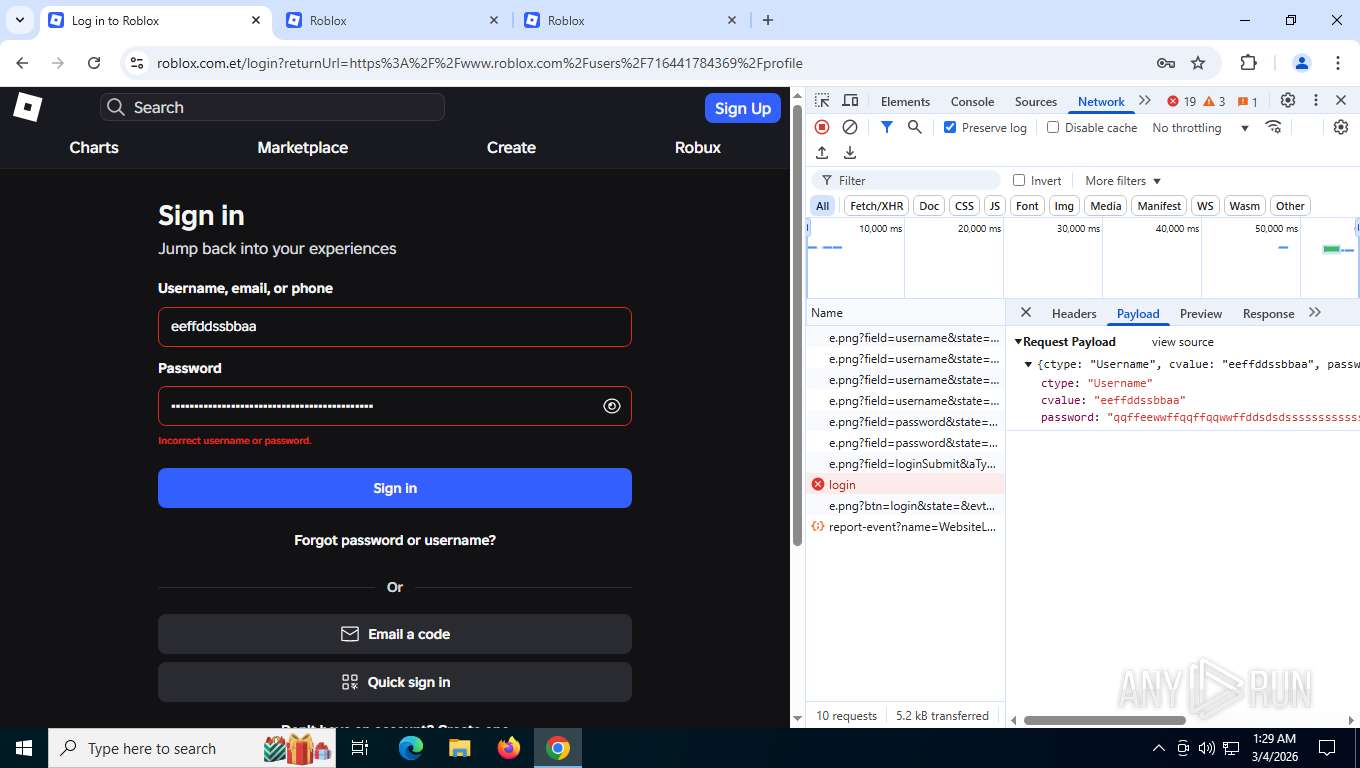
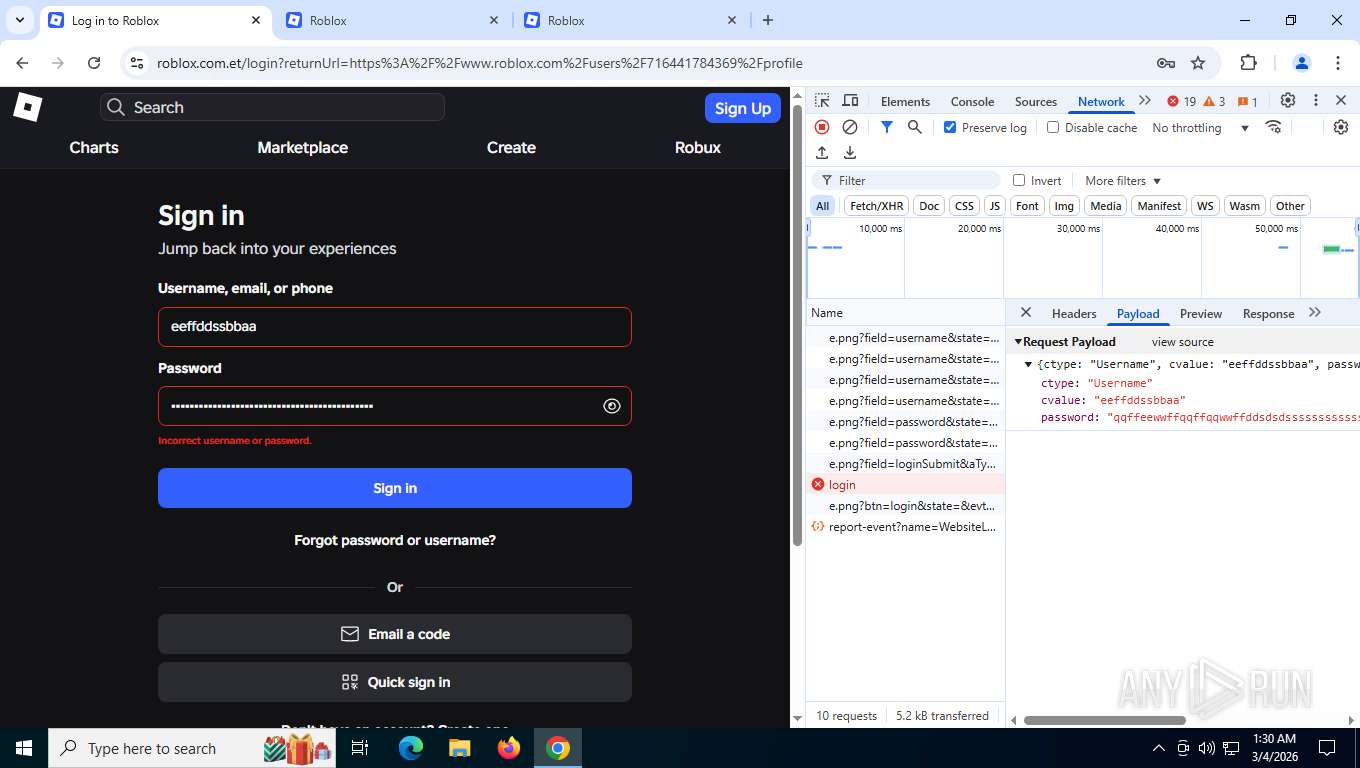
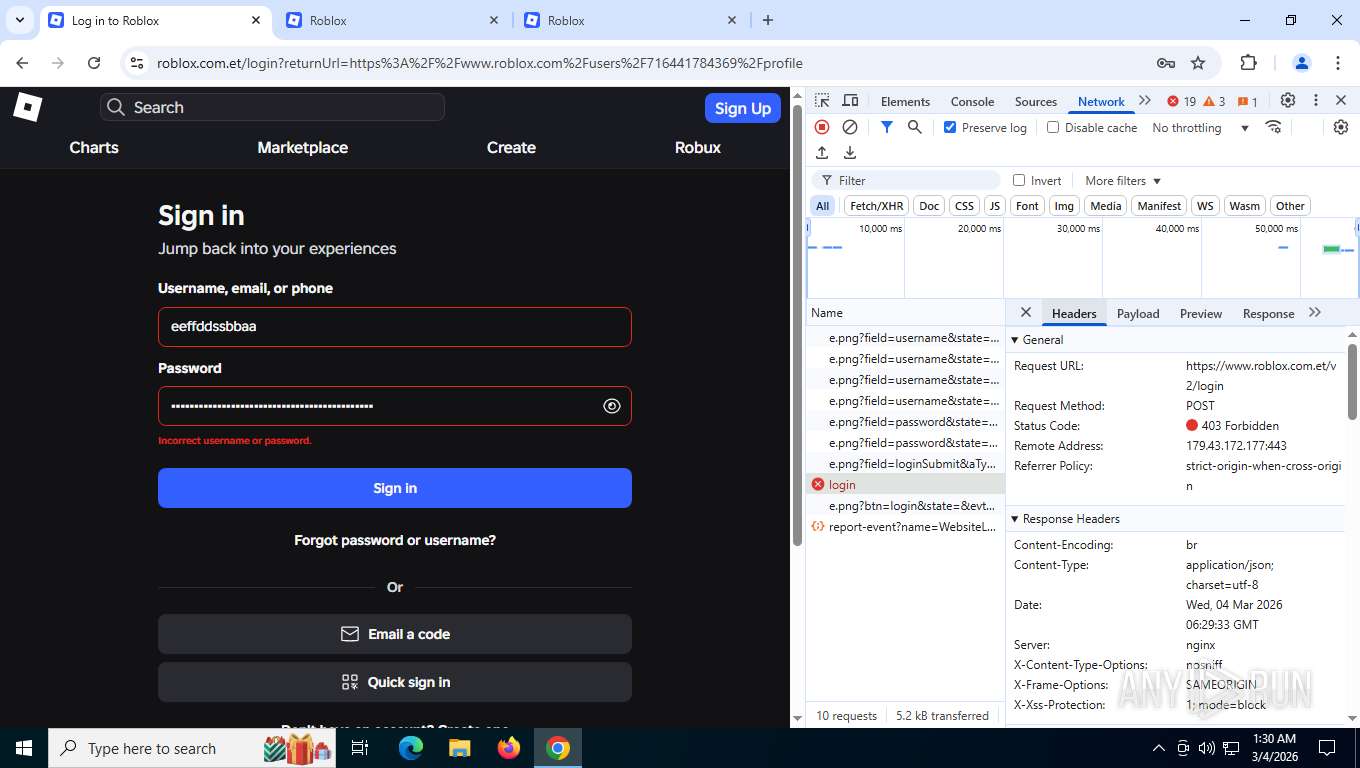
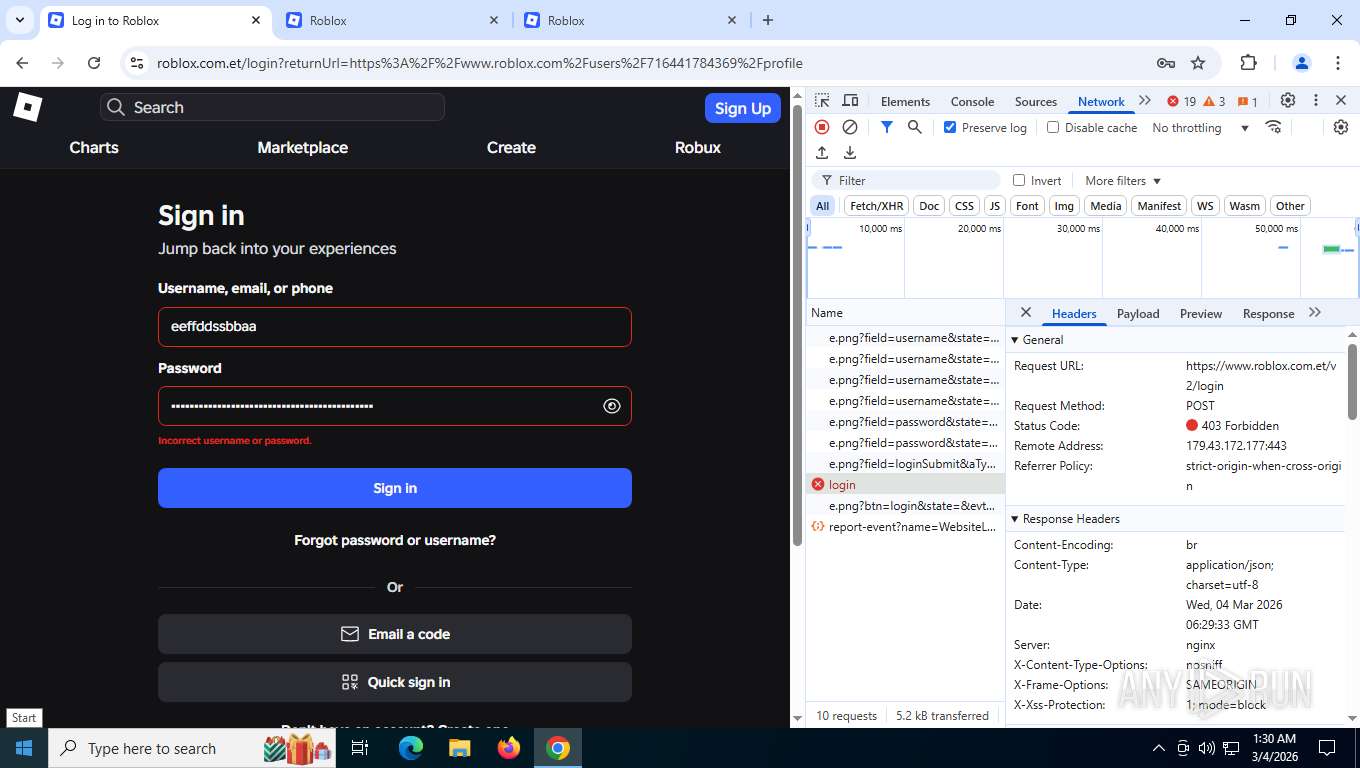
| URL: | www.roblox.com.et/users/716441784369/profile |
| Full analysis: | https://app.any.run/tasks/2f63b7b2-f17e-47a6-92b4-6e7b9da05d5c |
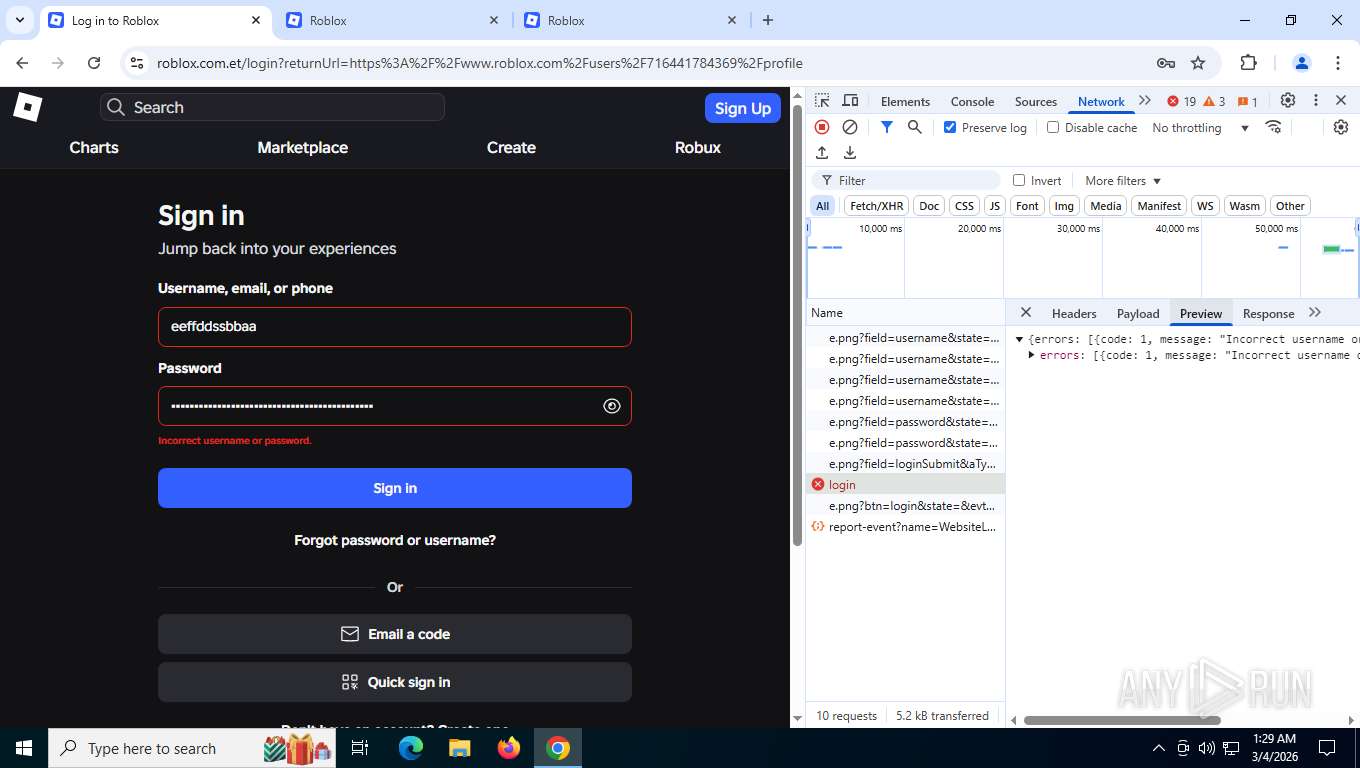
| Verdict: | Malicious activity |
| Analysis date: | March 04, 2026, 06:25:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1CB82204043974CEE11E0D3C1736FAF7 |
| SHA1: | E06E0B8F57CB613E2AD55C87832FA57275DB5737 |
| SHA256: | CA105EB77DB9694AEDBB24940E75FC545DA38C467C27C20D59C481F50FFFB05E |
| SSDEEP: | 3:EgE3IoKQmJqdRUcOXY9n:BoCJqdRg4n |
MALICIOUS
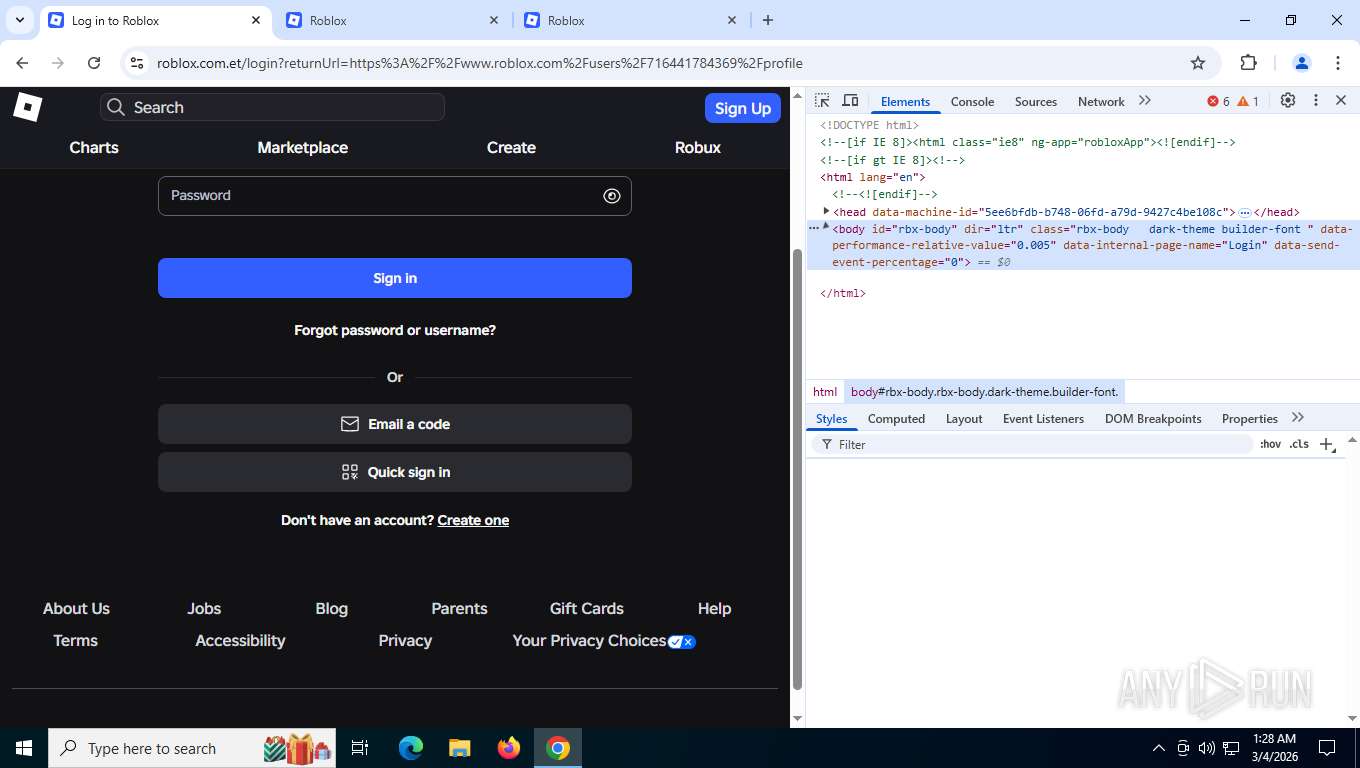
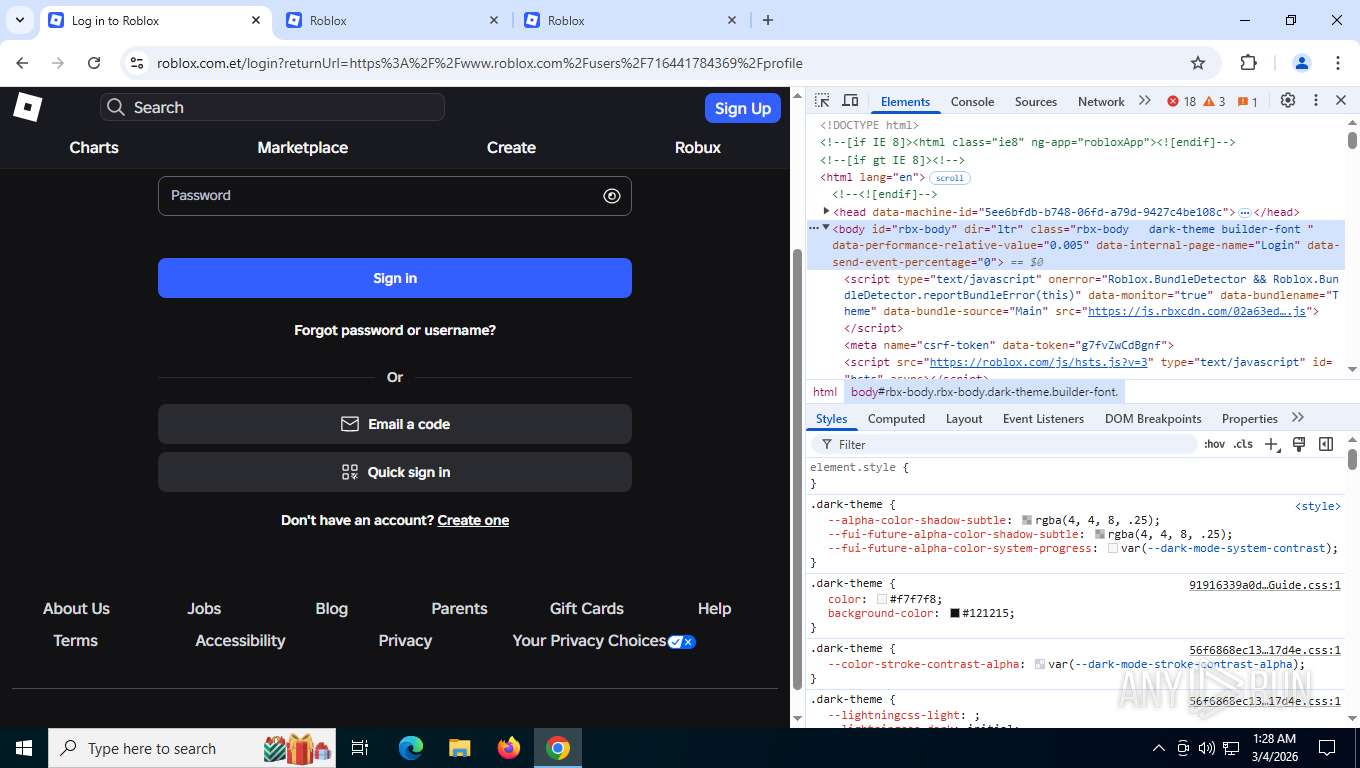
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 8852)
SUSPICIOUS
No suspicious indicators.INFO
Drops script file
- chrome.exe (PID: 8412)
Checks proxy server information
- slui.exe (PID: 4256)
The sample compiled with english language support
- chrome.exe (PID: 7452)
Executable content was dropped or overwritten
- chrome.exe (PID: 7452)
Application launched itself
- chrome.exe (PID: 8412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
192
Monitored processes
43
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5904,i,7512445910217415301,6900957685619037179,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6168 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5964,i,7512445910217415301,6900957685619037179,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5448 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5872,i,7512445910217415301,6900957685619037179,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5828 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=3496,i,7512445910217415301,6900957685619037179,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3704 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5700,i,7512445910217415301,6900957685619037179,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5844 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3136,i,7512445910217415301,6900957685619037179,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=28 --field-trial-handle=5684,i,7512445910217415301,6900957685619037179,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6044 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5216,i,7512445910217415301,6900957685619037179,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5832 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=40 --field-trial-handle=6956,i,7512445910217415301,6900957685619037179,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6908 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=38 --field-trial-handle=6244,i,7512445910217415301,6900957685619037179,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
3 485
Read events
3 485
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
739
Text files
179
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1e5523.TMP | — | |
MD5:— | SHA256:— | |||
| 8412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1e5532.TMP | — | |
MD5:— | SHA256:— | |||
| 8412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF1e5532.TMP | — | |
MD5:— | SHA256:— | |||
| 8412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1e5532.TMP | — | |
MD5:— | SHA256:— | |||
| 8412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1e5532.TMP | — | |
MD5:— | SHA256:— | |||
| 8412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
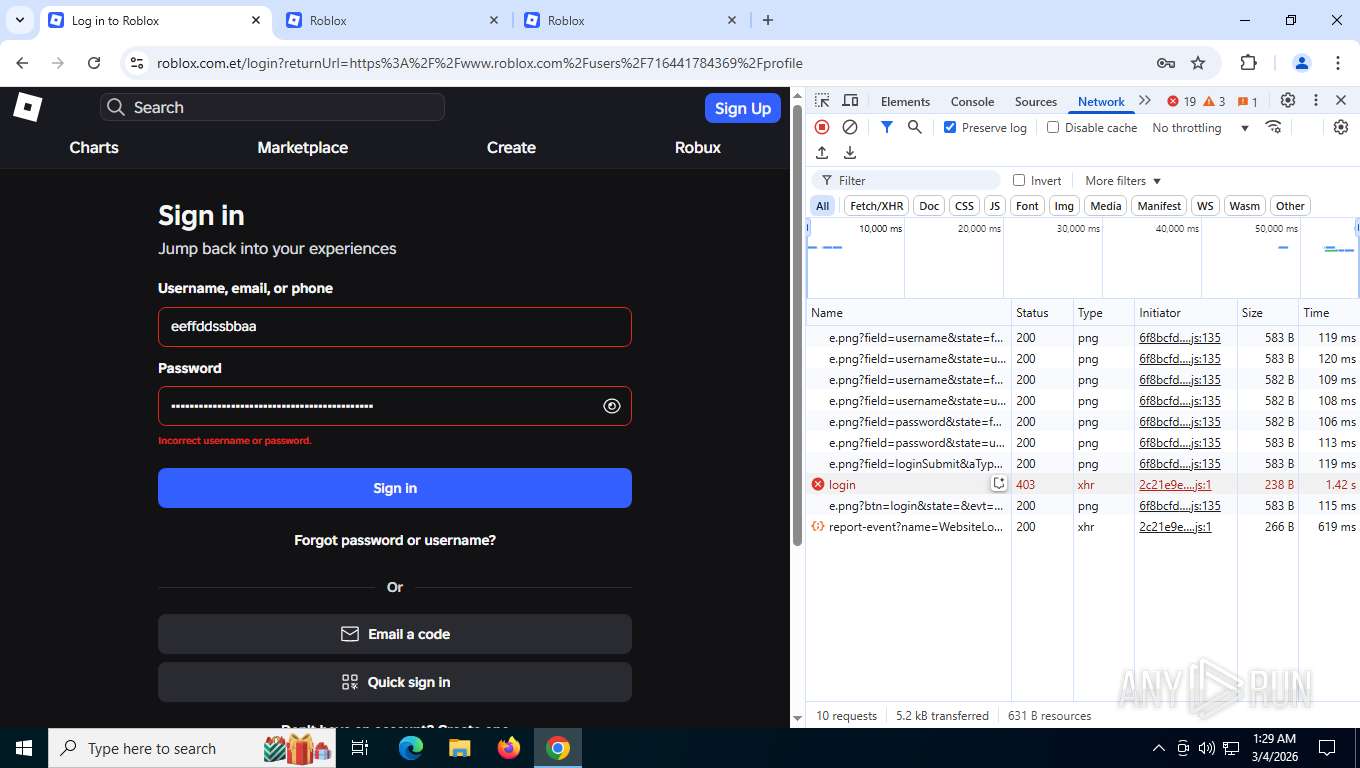
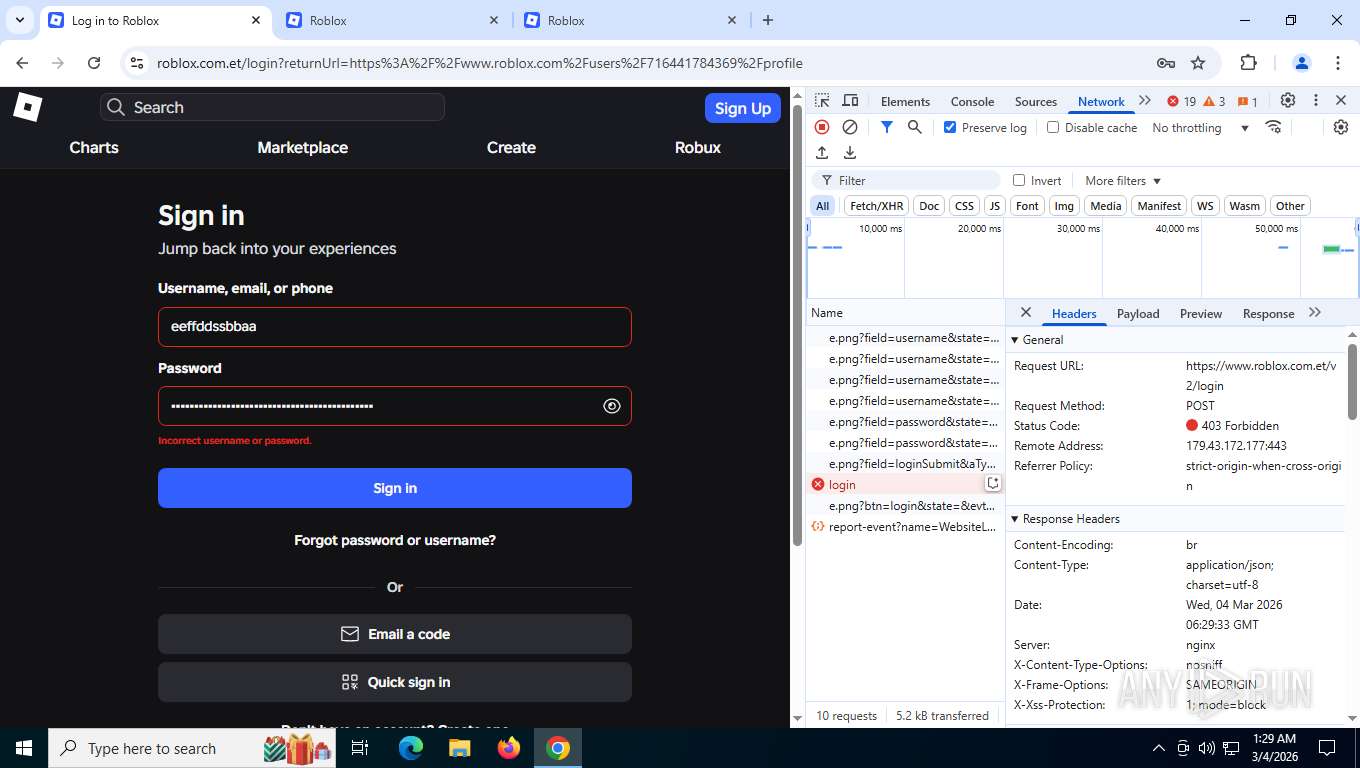
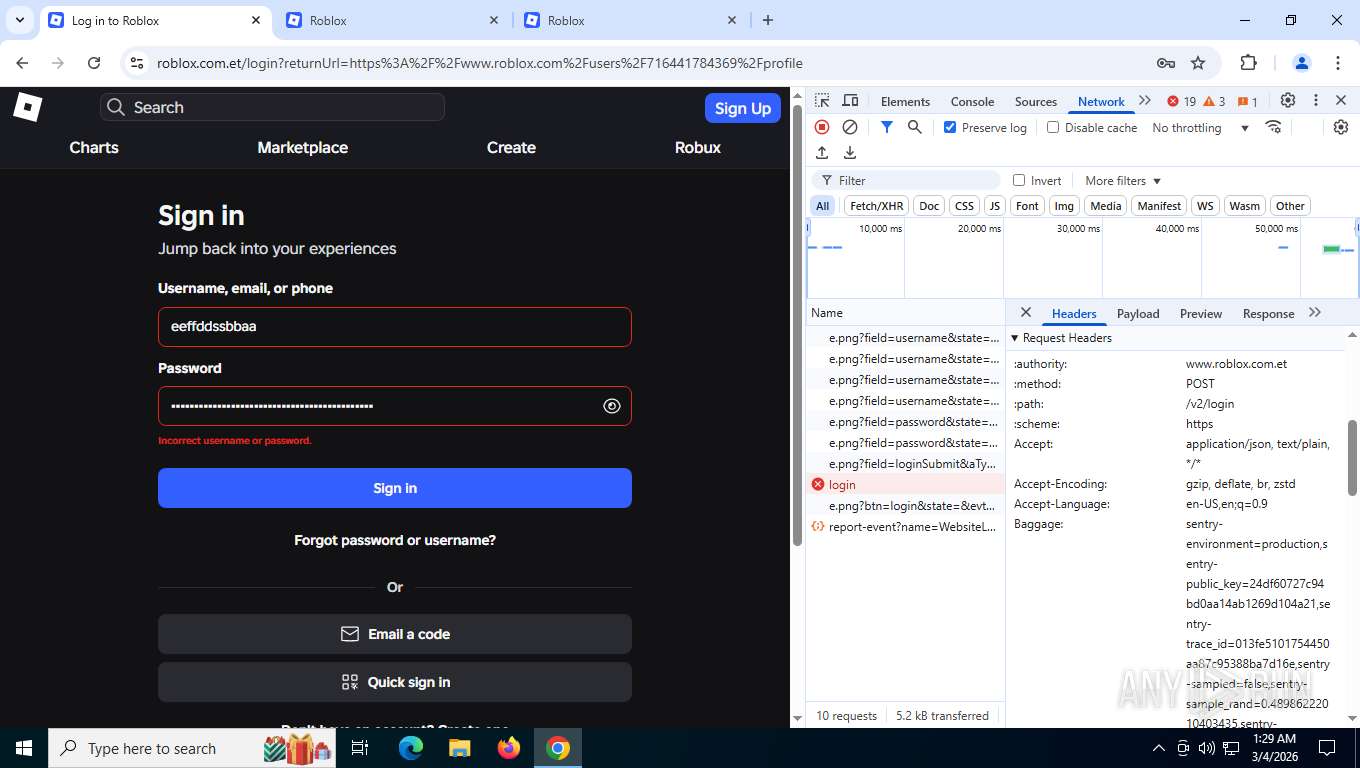
HTTP(S) requests
874
TCP/UDP connections
111
DNS requests
115
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
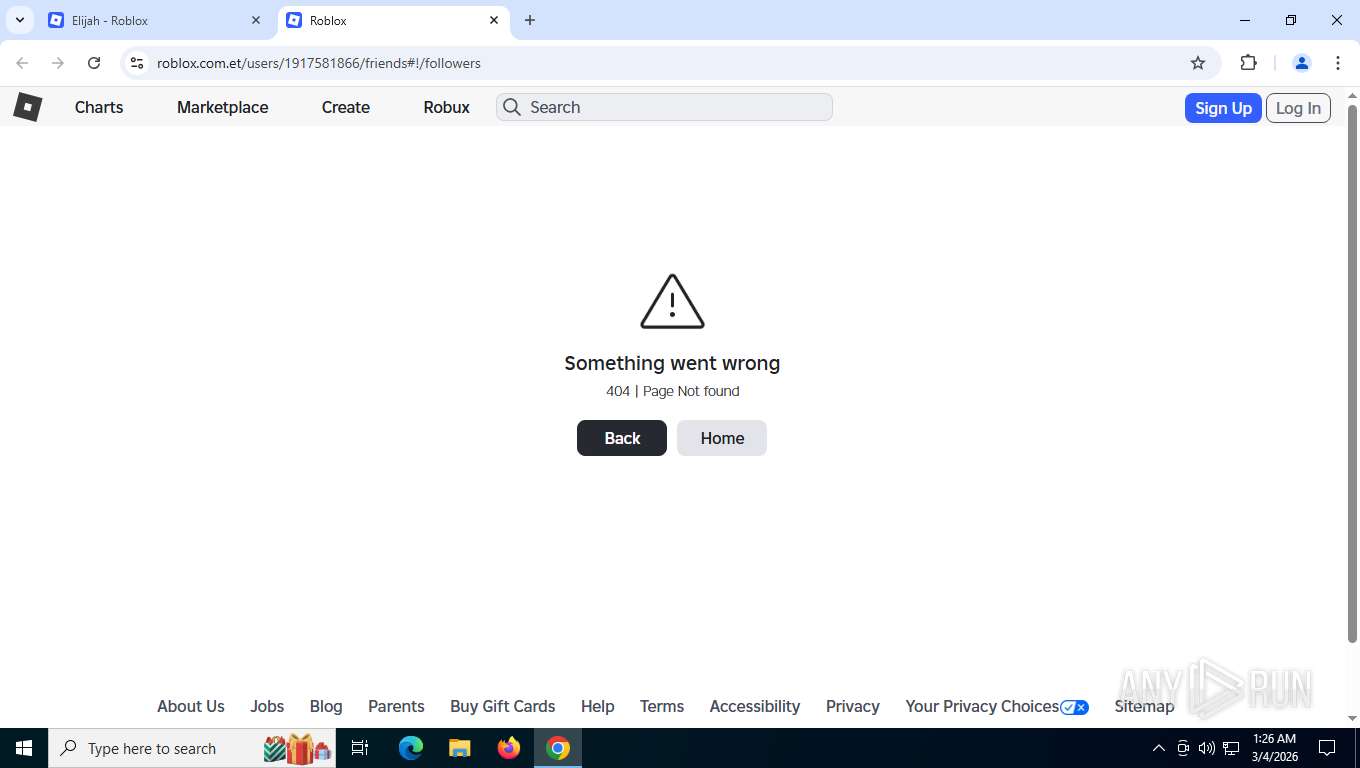
8852 | chrome.exe | GET | 301 | 179.43.172.177:80 | http://www.roblox.com.et/users/716441784369/profile | PA | html | 162 b | unknown |
8852 | chrome.exe | GET | 200 | 179.43.172.177:443 | https://www.roblox.com.et/users/716441784369/profile | PA | html | 126 Kb | unknown |
8852 | chrome.exe | GET | 200 | 142.251.141.131:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=133 | US | compressed | 87.3 Kb | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 960 b | whitelisted |
8852 | chrome.exe | GET | 200 | 216.58.206.42:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | US | binary | 41 b | whitelisted |
8852 | chrome.exe | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | US | text | 17 b | whitelisted |
8852 | chrome.exe | GET | 200 | 179.43.172.177:443 | https://www.roblox.com.et/privateJs/EnvironmentUrls.js | PA | text | 11.5 Kb | unknown |
8852 | chrome.exe | GET | 404 | 179.43.172.177:443 | https://www.roblox.com.et/js/utilities/bundleVerifier.js?v=91dceb4978eda412b09842312dd6cbaa | PA | html | 62.5 Kb | unknown |
8852 | chrome.exe | GET | 200 | 179.43.172.177:443 | https://www.roblox.com.et/privateJs/Thumbnails3d.js | PA | text | 7.62 Mb | unknown |
8852 | chrome.exe | GET | 200 | 179.43.172.177:443 | https://www.roblox.com.et/privateJs/Navigation.js | PA | text | 227 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2860 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5524 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.63:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8852 | chrome.exe | 216.58.206.42:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
www.roblox.com.et |
| malicious |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8852 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain Pattern (roblox .com .*) |
8852 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP2 invalid frame data |
8852 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP2 invalid frame data |
8852 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP2 invalid header |
8852 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP2 invalid header |
8852 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP2 invalid frame data |
8852 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP2 invalid frame data |
8852 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP2 invalid header |
8852 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP2 invalid header |
5524 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |