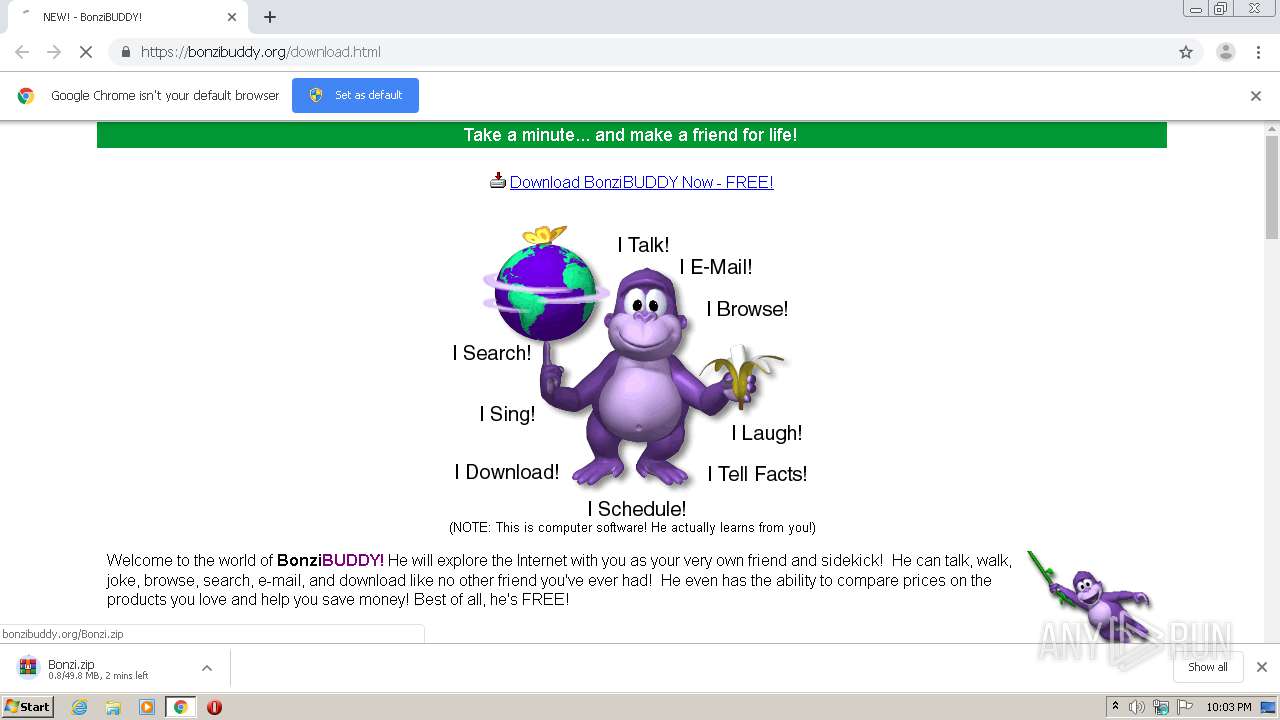
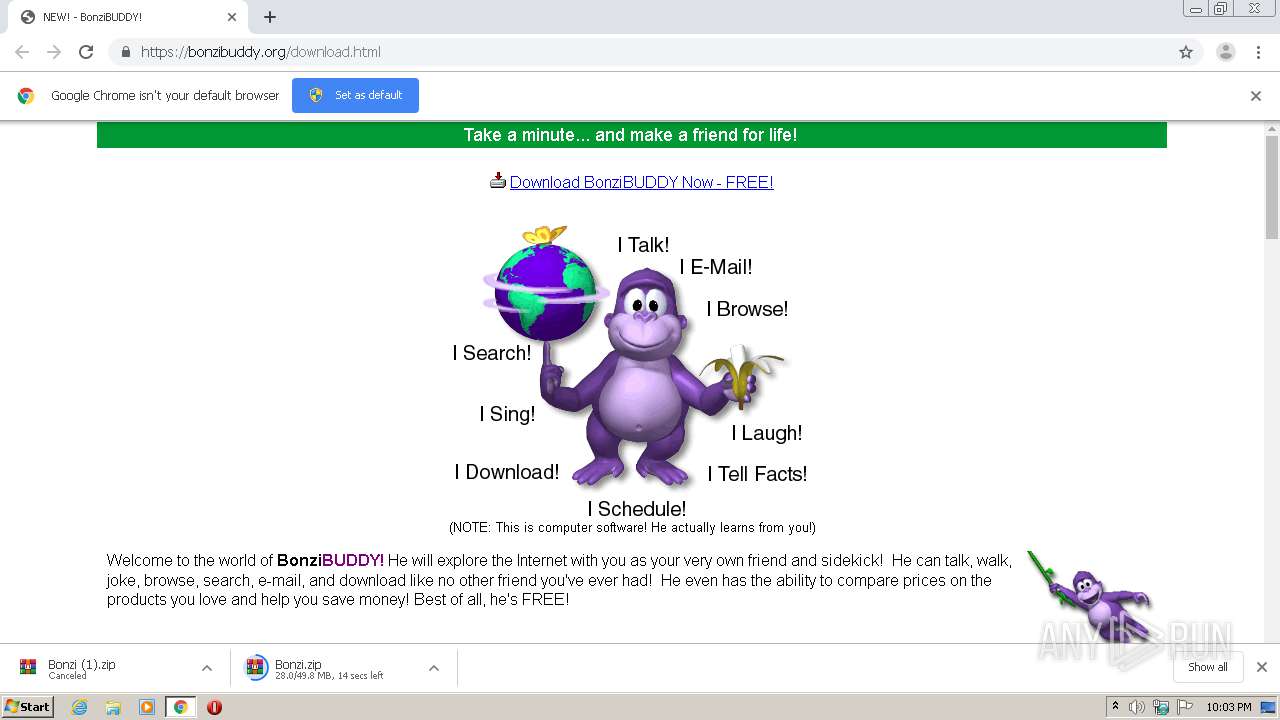
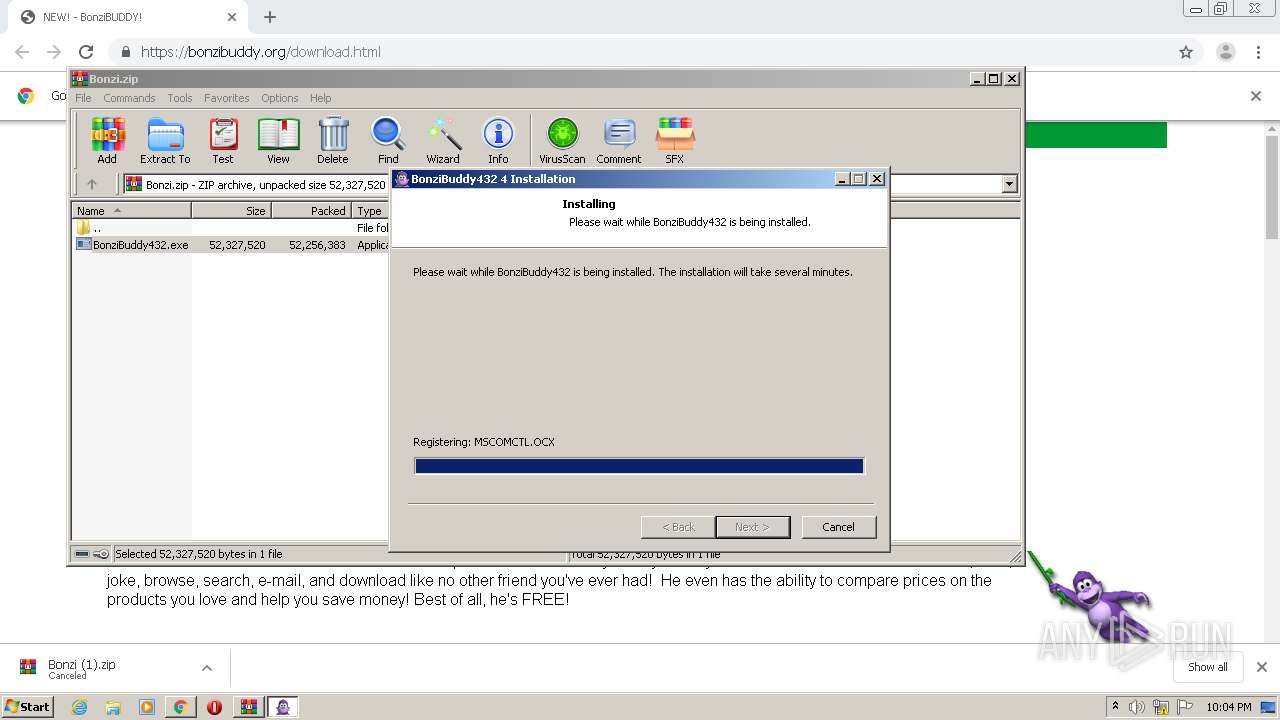
| URL: | https://bonzibuddy.org/download.html |
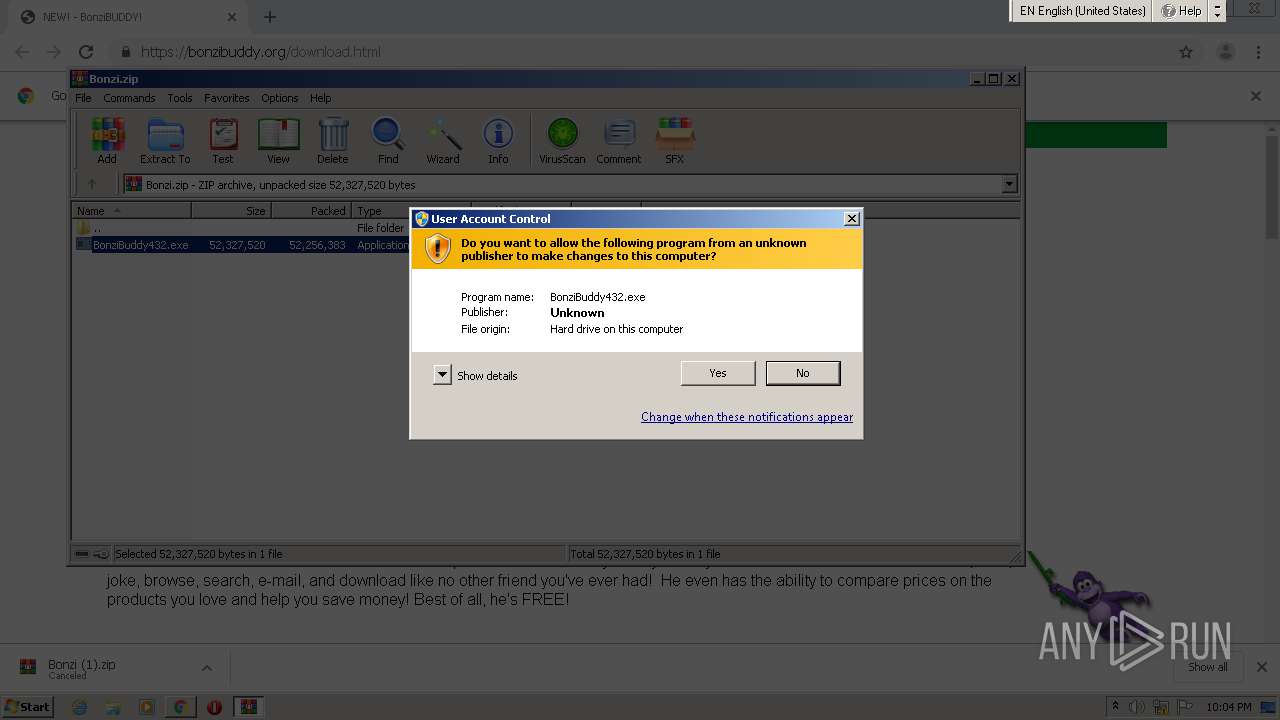
| Full analysis: | https://app.any.run/tasks/23fa4dae-8607-404b-a88b-4a6cac2ad025 |
| Verdict: | Malicious activity |
| Analysis date: | May 13, 2021, 21:02:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
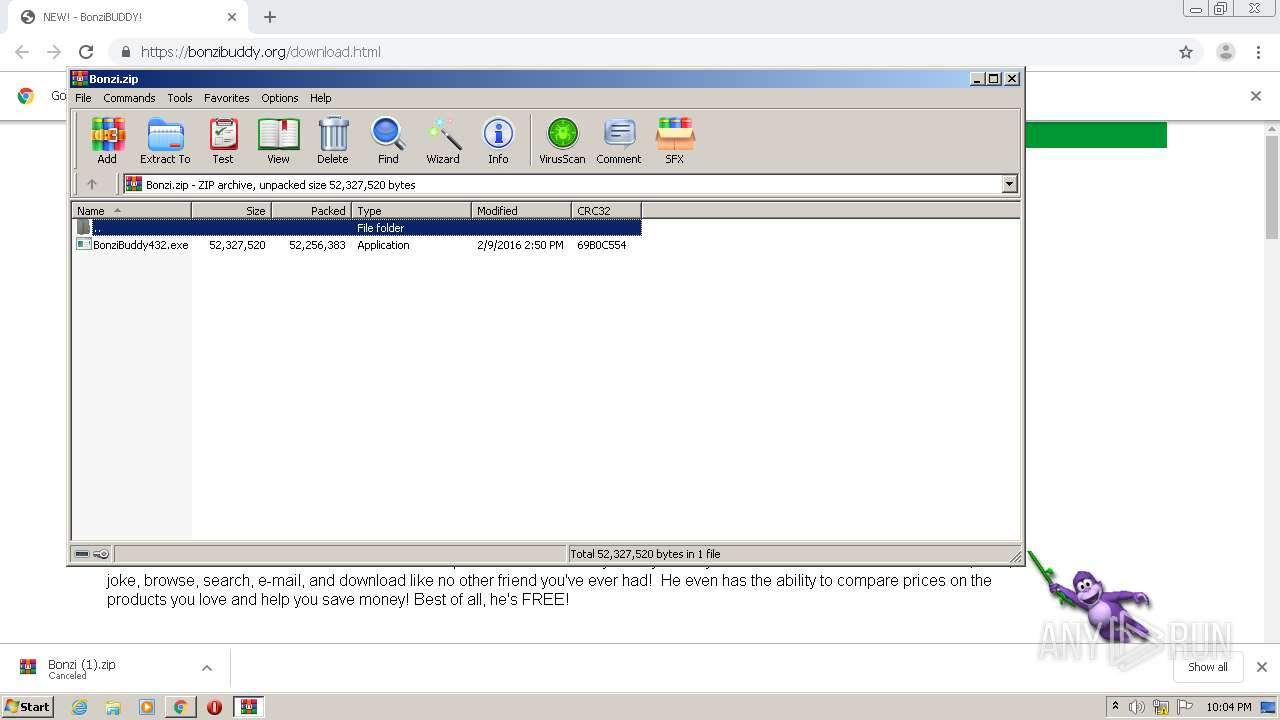
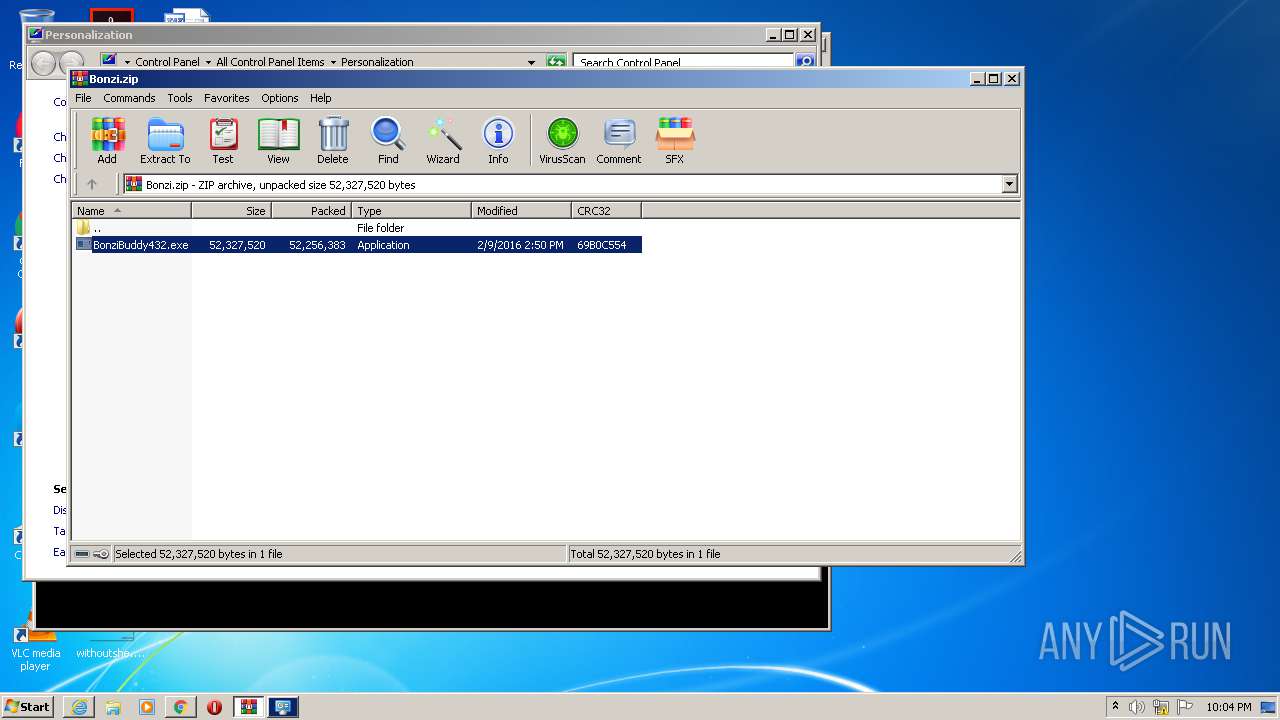
| MD5: | 8A56C620CE694BE321DD4B4ABEE33AC4 |
| SHA1: | 3856204BE8F661C8973766E2D67F40BCADD4E2FE |
| SHA256: | CA0C72BCBC2CFA4454EBE7DC9D70DE3A6AFE7205739FAF3AC2136C399C39DFC9 |
| SSDEEP: | 3:N89E3Q:296Q |
MALICIOUS
Loads dropped or rewritten executable
- tv_enua.exe (PID: 2564)
- regsvr32.exe (PID: 1404)
- regsvr32.exe (PID: 2716)
- regsvr32.exe (PID: 3892)
- regsvr32.exe (PID: 3116)
- regsvr32.exe (PID: 2872)
- BonziBDY_4.EXE (PID: 2092)
- BonziBuddy432.exe (PID: 1520)
- regsvr32.exe (PID: 3280)
- regsvr32.exe (PID: 1720)
- BonziBDY_35.EXE (PID: 3160)
- BonziBDY_35.EXE (PID: 2968)
- BonziBDY_2.EXE (PID: 2568)
- BonziBDY_4.EXE (PID: 3888)
Changes the autorun value in the registry
- tv_enua.exe (PID: 2564)
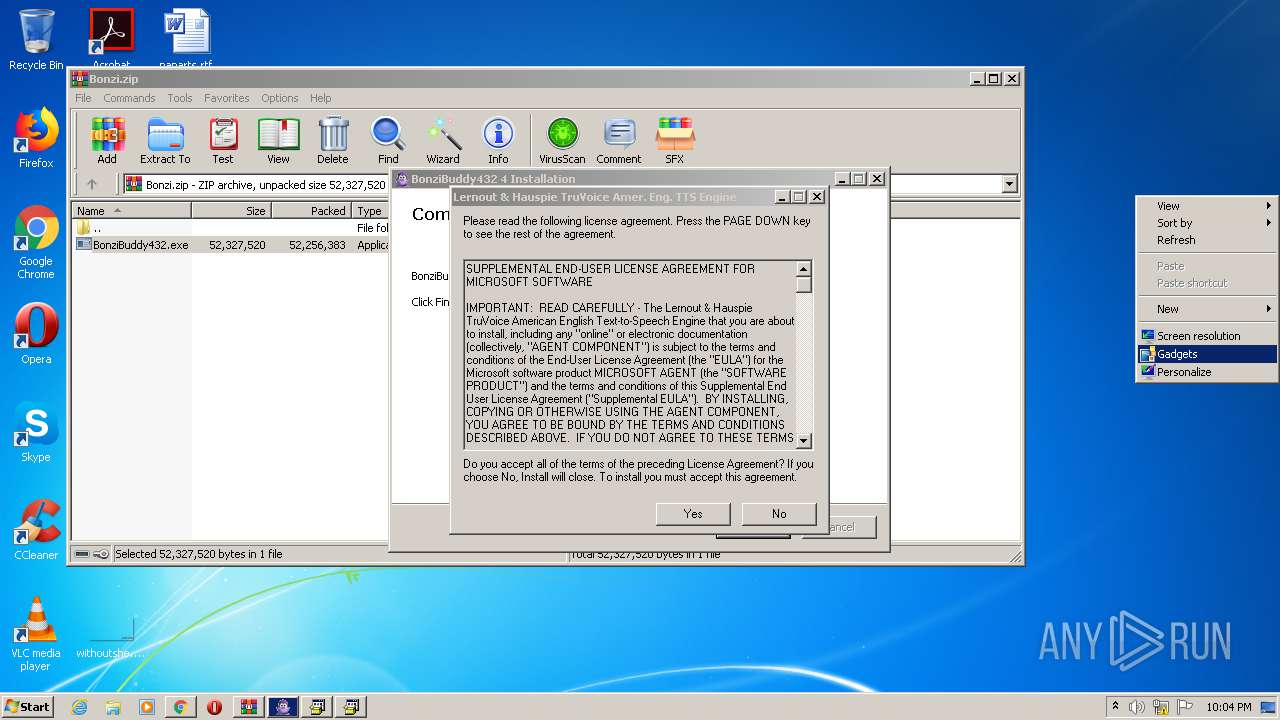
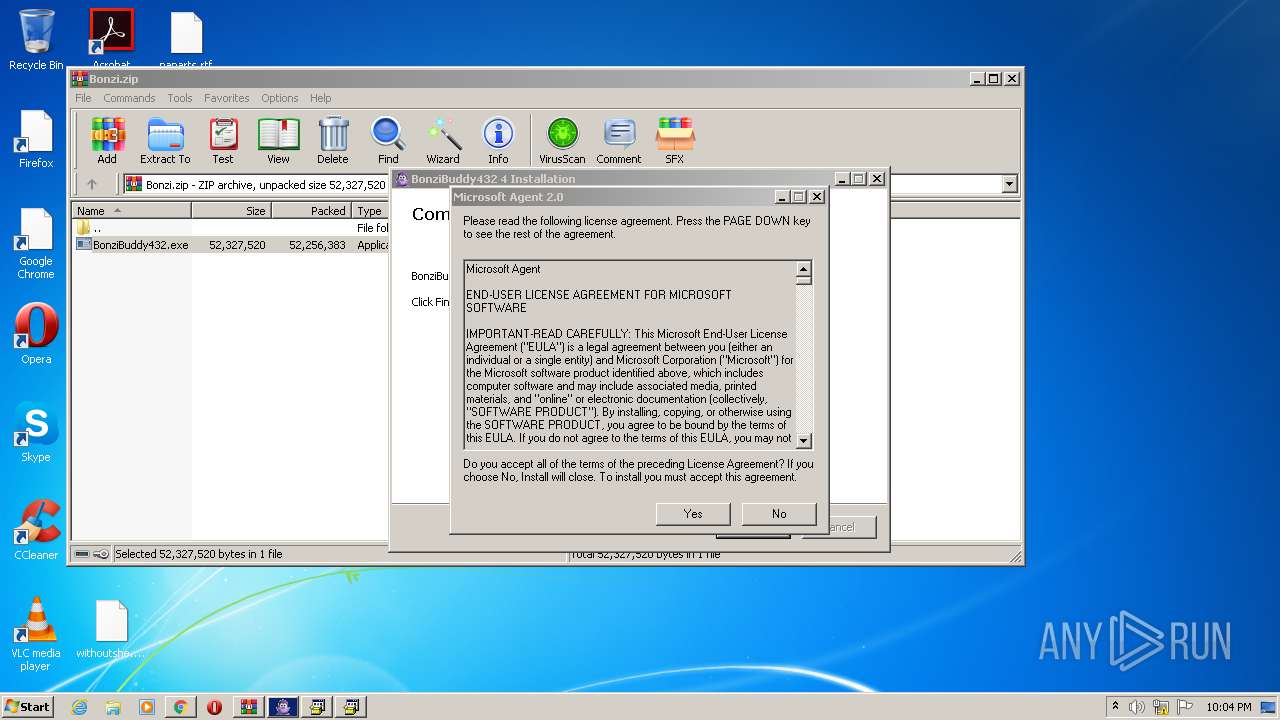
Registers / Runs the DLL via REGSVR32.EXE
- tv_enua.exe (PID: 2564)
- MSAGENT.EXE (PID: 2608)
Application was dropped or rewritten from another process
- MSAGENT.EXE (PID: 2608)
- tv_enua.exe (PID: 2564)
- BonziBDY_4.EXE (PID: 3888)
- BonziBDY_35.EXE (PID: 2968)
- BonziBDY_35.EXE (PID: 3160)
- BonziBDY_2.EXE (PID: 2568)
- BonziBDY_2.EXE (PID: 2064)
- AgentSvr.exe (PID: 632)
- BonziBDY_4.EXE (PID: 2092)
SUSPICIOUS
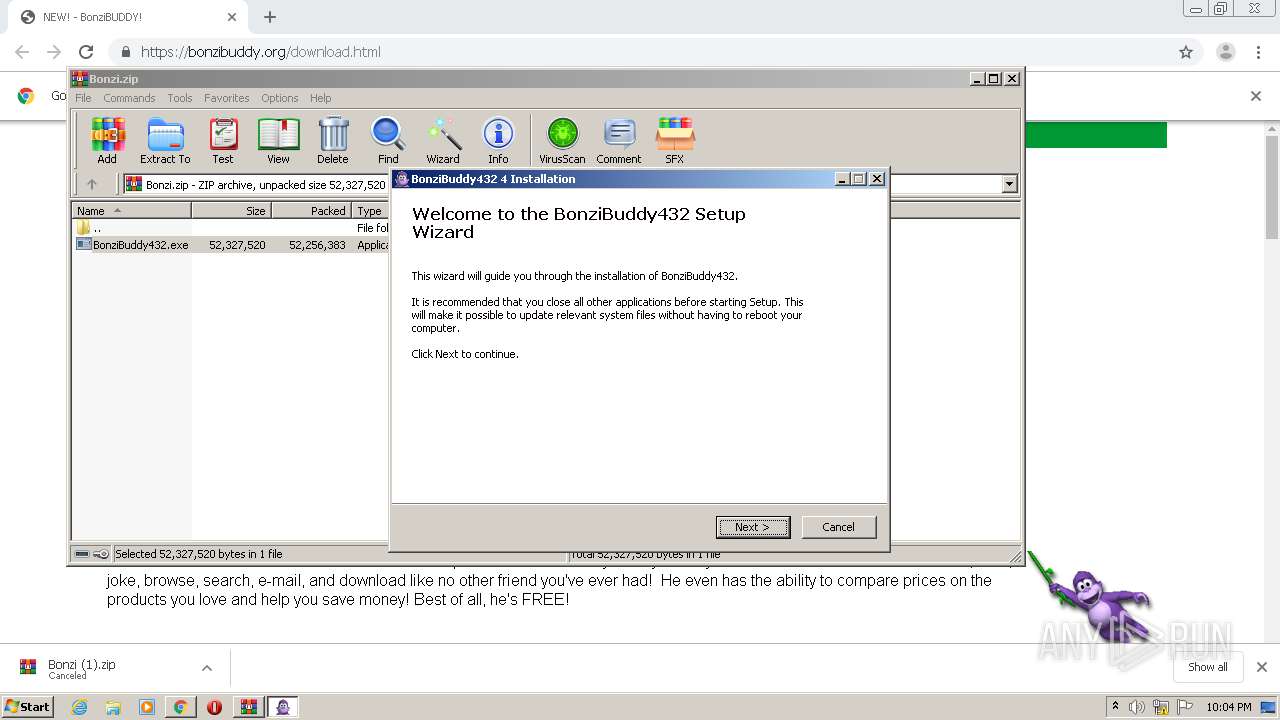
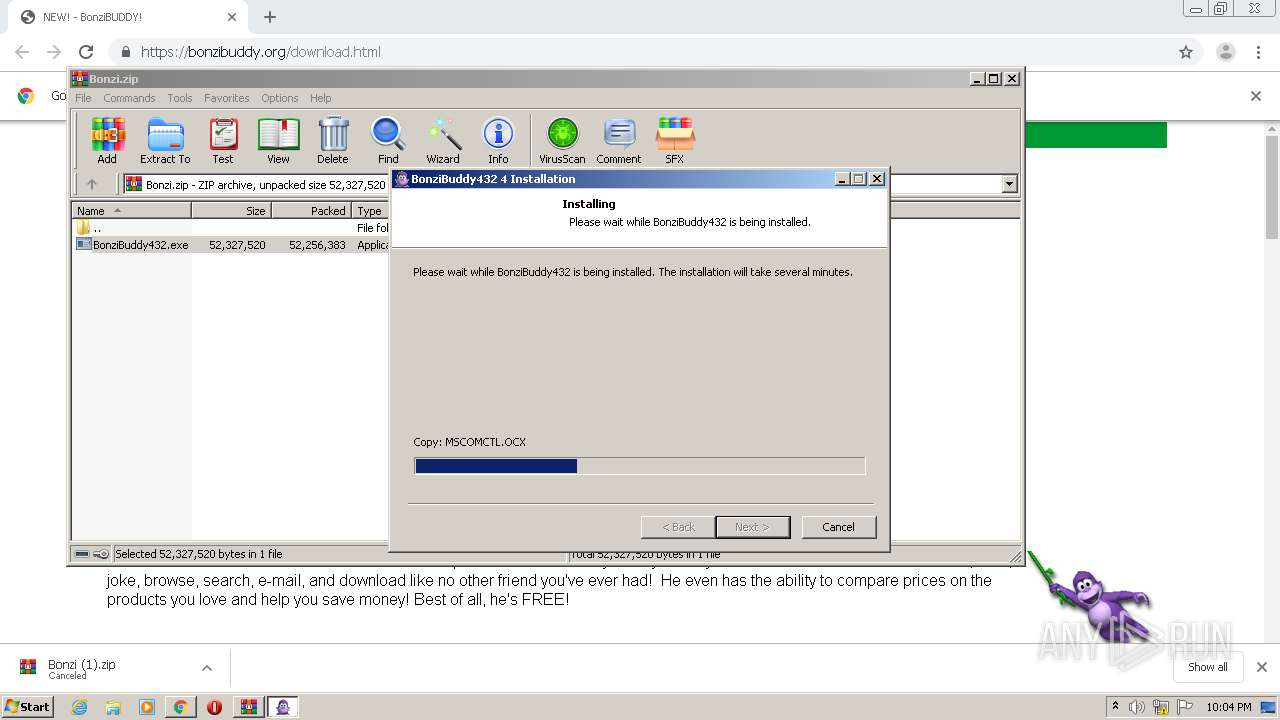
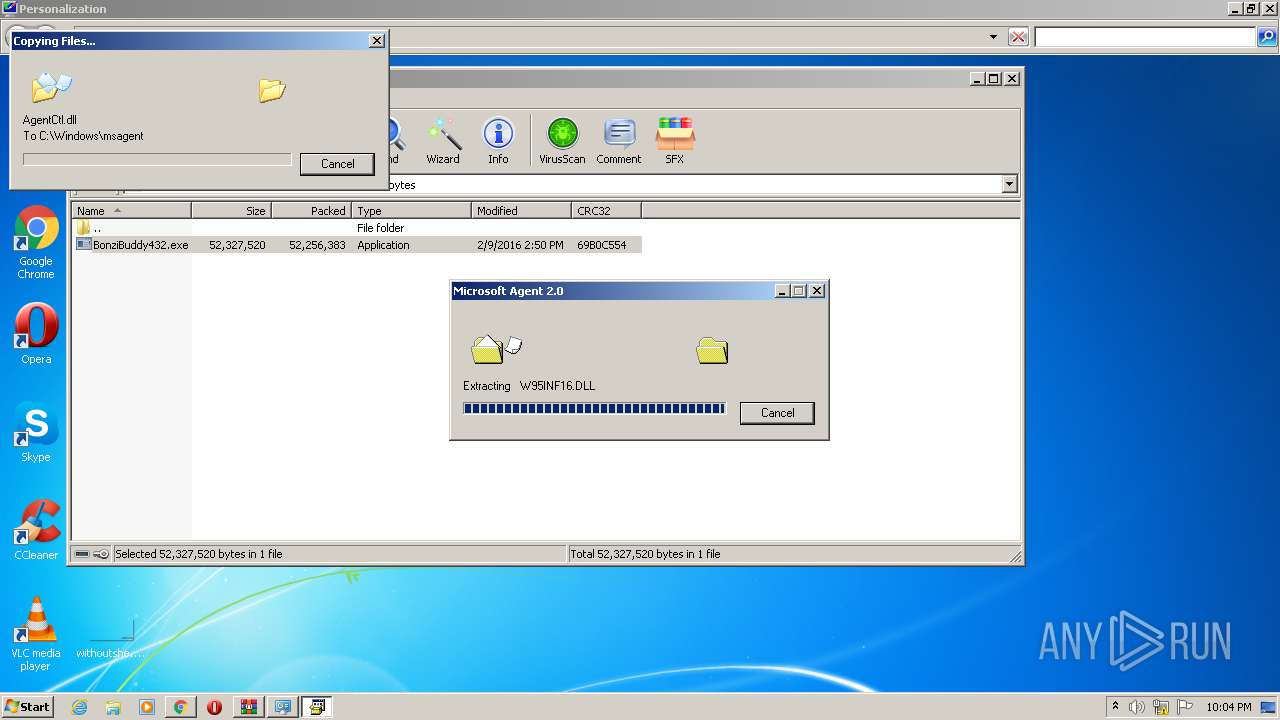
Creates files in the Windows directory
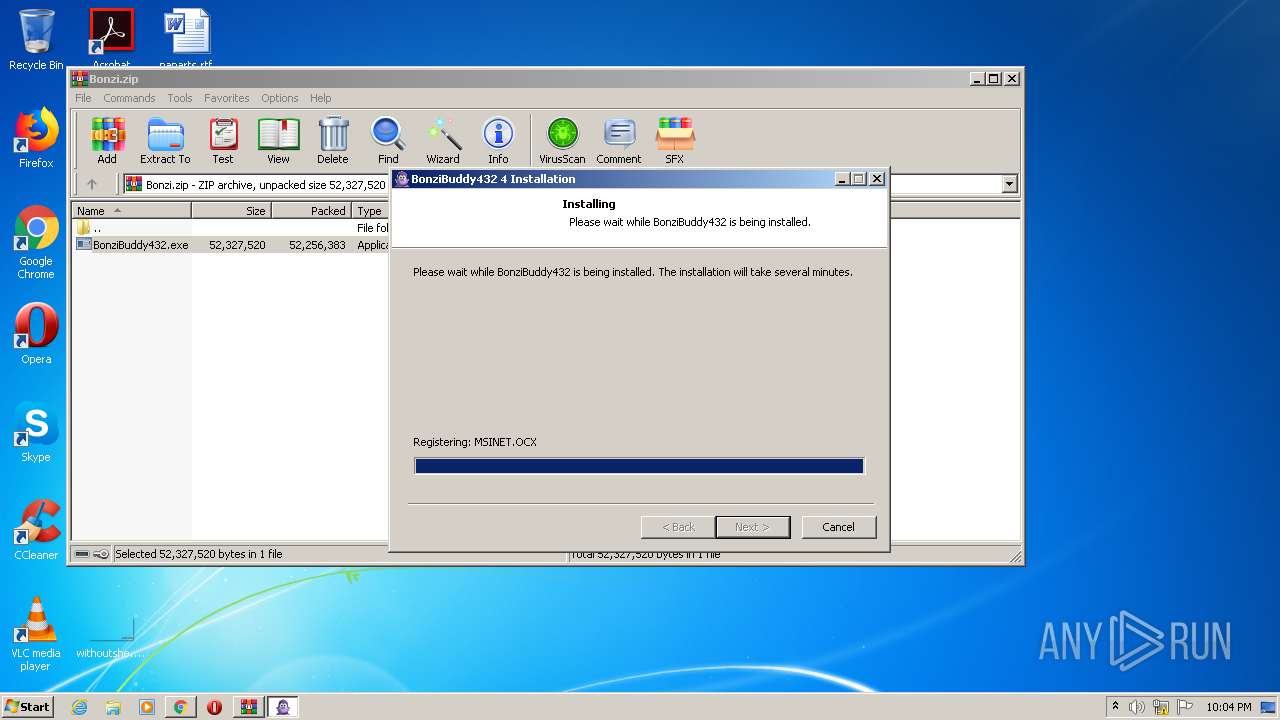
- BonziBuddy432.exe (PID: 1520)
- tv_enua.exe (PID: 2564)
- MSAGENT.EXE (PID: 2608)
Creates a directory in Program Files
- BonziBuddy432.exe (PID: 1520)
Creates a software uninstall entry
- BonziBuddy432.exe (PID: 1520)
- tv_enua.exe (PID: 2564)
Starts CMD.EXE for commands execution
- BonziBuddy432.exe (PID: 1520)
Drops a file with too old compile date
- BonziBuddy432.exe (PID: 1520)
- tv_enua.exe (PID: 2564)
- MSAGENT.EXE (PID: 2608)
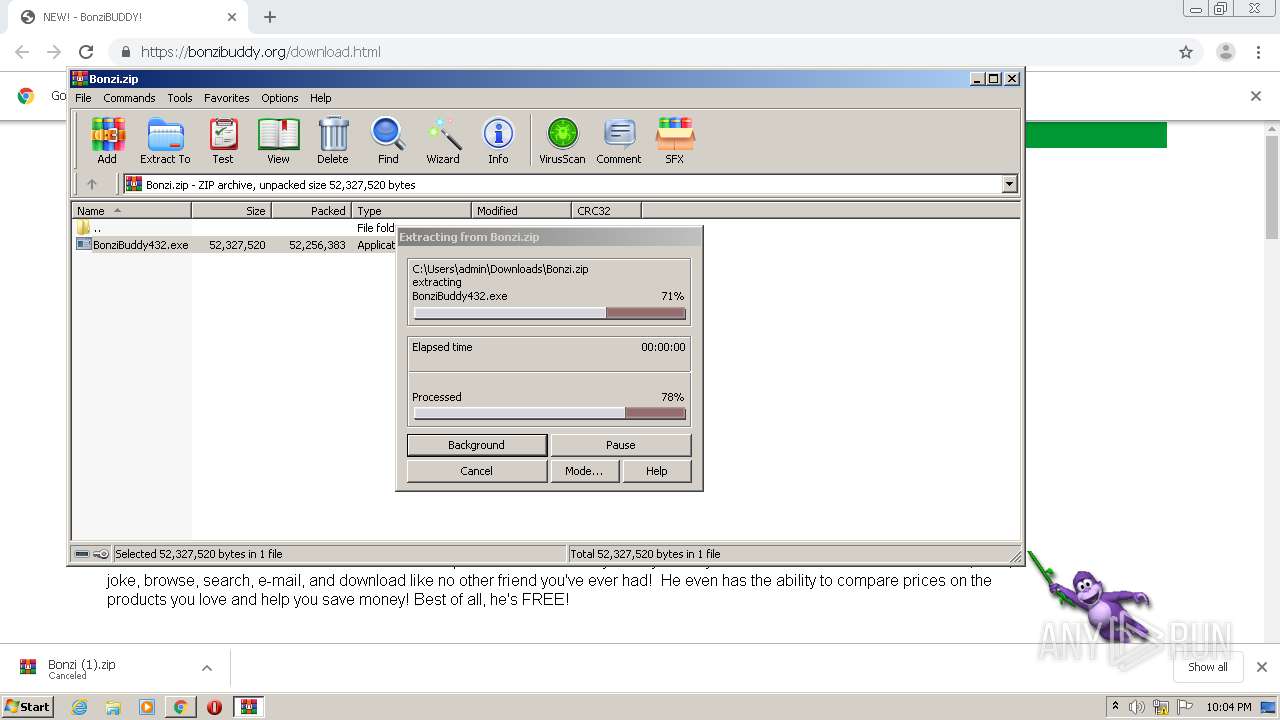
Executable content was dropped or overwritten
- BonziBuddy432.exe (PID: 1520)
- MSAGENT.EXE (PID: 2608)
- tv_enua.exe (PID: 2564)
Drops a file that was compiled in debug mode
- MSAGENT.EXE (PID: 2608)
- BonziBuddy432.exe (PID: 1520)
- tv_enua.exe (PID: 2564)
Starts Internet Explorer
- BonziBuddy432.exe (PID: 1520)
Removes files from Windows directory
- tv_enua.exe (PID: 2564)
- MSAGENT.EXE (PID: 2608)
Drops a file with a compile date too recent
- MSAGENT.EXE (PID: 2608)
- tv_enua.exe (PID: 2564)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1404)
- regsvr32.exe (PID: 1720)
- regsvr32.exe (PID: 3996)
- regsvr32.exe (PID: 3280)
- regsvr32.exe (PID: 2716)
- regsvr32.exe (PID: 2872)
- regsvr32.exe (PID: 3892)
- regsvr32.exe (PID: 3608)
- regsvr32.exe (PID: 3116)
Creates files in the user directory
- BonziBuddy432.exe (PID: 1520)
Creates files in the program directory
- BonziBuddy432.exe (PID: 1520)
INFO
Application launched itself
- chrome.exe (PID: 920)
- iexplore.exe (PID: 2344)
Reads the hosts file
- chrome.exe (PID: 2796)
- chrome.exe (PID: 920)
Changes internet zones settings
- iexplore.exe (PID: 2344)
Reads internet explorer settings
- iexplore.exe (PID: 692)
Changes settings of System certificates
- iexplore.exe (PID: 692)
Adds / modifies Windows certificates
- iexplore.exe (PID: 692)
Manual execution by user
- BonziBDY_4.EXE (PID: 3888)
- BonziBDY_35.EXE (PID: 2968)
- BonziBDY_35.EXE (PID: 3160)
- BonziBDY_2.EXE (PID: 2568)
- BonziBDY_4.EXE (PID: 2092)
- BonziBDY_2.EXE (PID: 2064)
Creates files in the user directory
- iexplore.exe (PID: 692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
39
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,5605076945616467074,16275771316228925106,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11197095058331261840 --mojo-platform-channel-handle=3216 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 524 | grpconv.exe -o | C:\Windows\system32\grpconv.exe | — | MSAGENT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 632 | "C:\Windows\msagent\AgentSvr.exe" /regserver | C:\Windows\msagent\AgentSvr.exe | — | MSAGENT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Agent Server Exit code: 0 Version: 2.00.0.2202 Modules
| |||||||||||||||
| 692 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2344 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://bonzibuddy.org/download.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,5605076945616467074,16275771316228925106,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14787214385025689695 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1404 | regsvr32 /s C:\Windows\lhsp\tv\tv_enua.dll | C:\Windows\system32\regsvr32.exe | — | tv_enua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
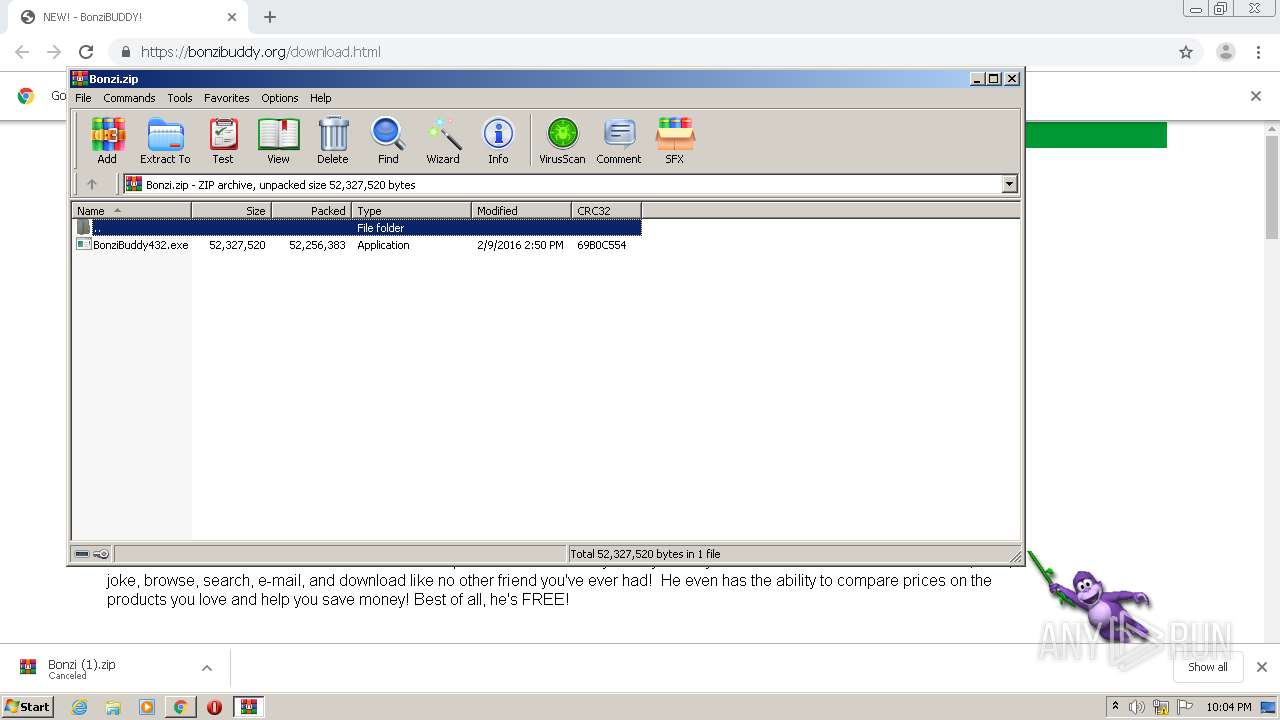
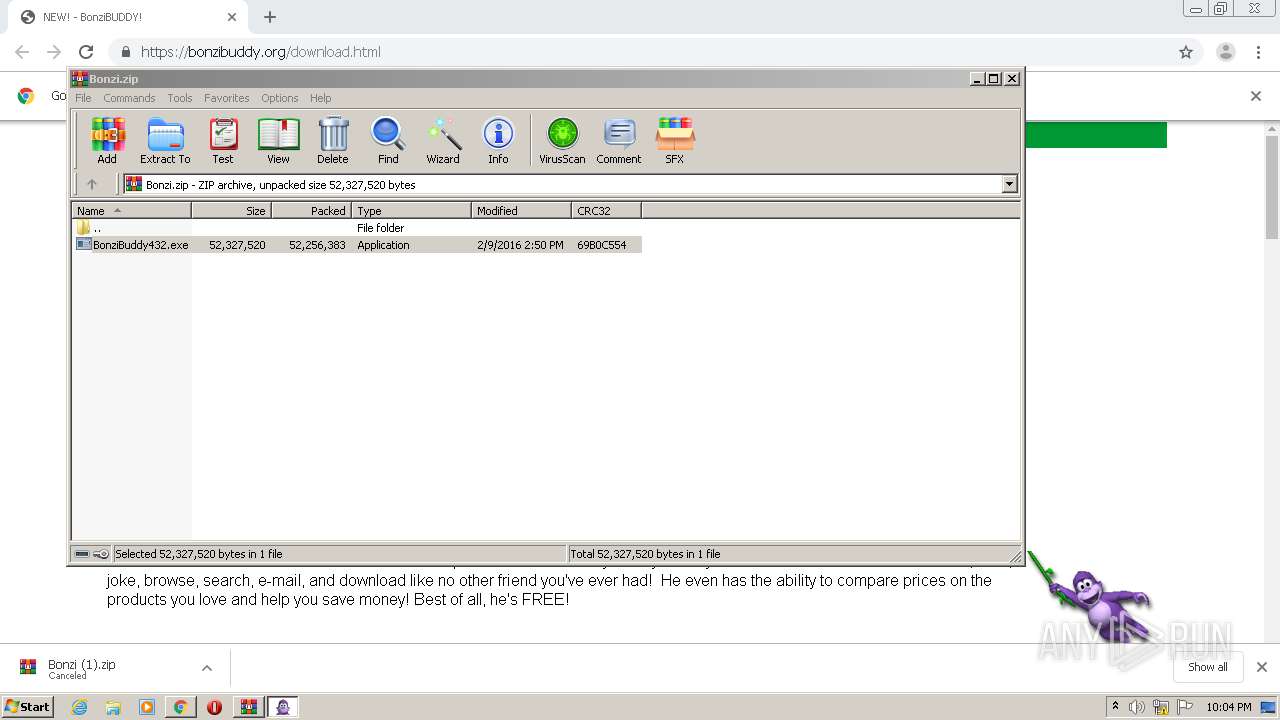
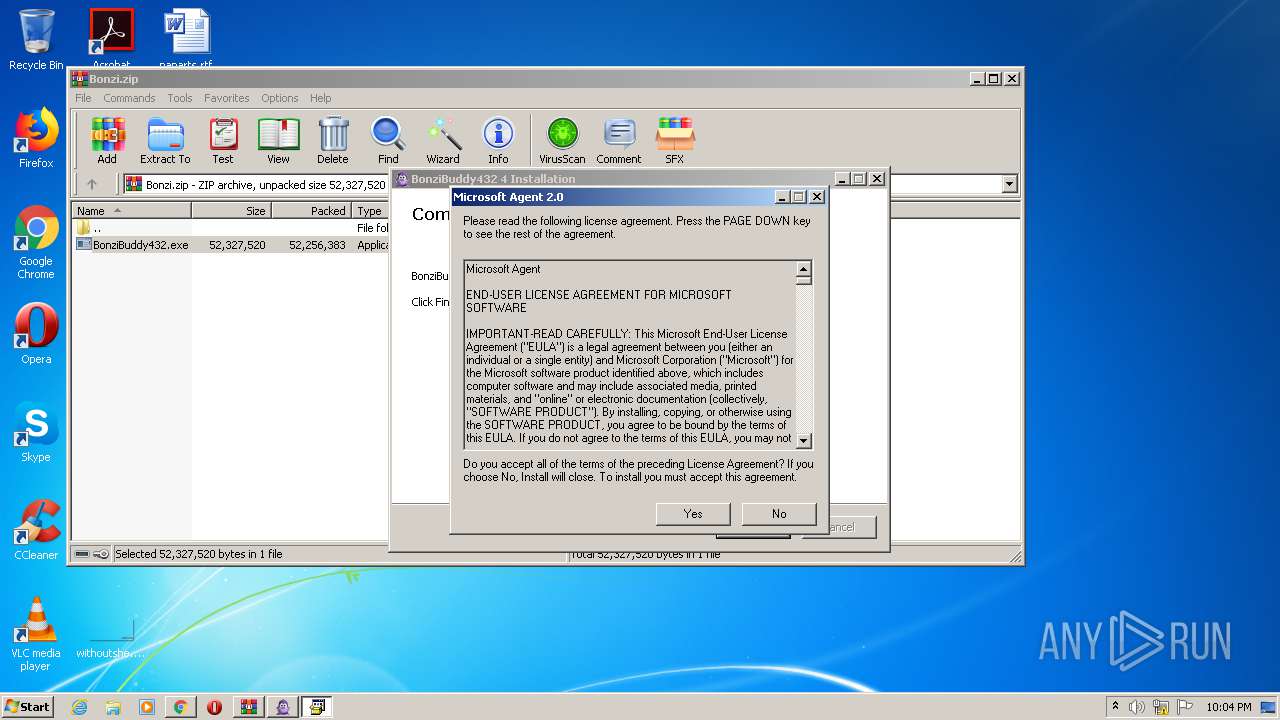
| 1516 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2352.17889\BonziBuddy432.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2352.17889\BonziBuddy432.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Bonzi Software Integrity Level: MEDIUM Description: BonziBuddy432 4 Installation Exit code: 3221226540 Version: 4 Modules
| |||||||||||||||
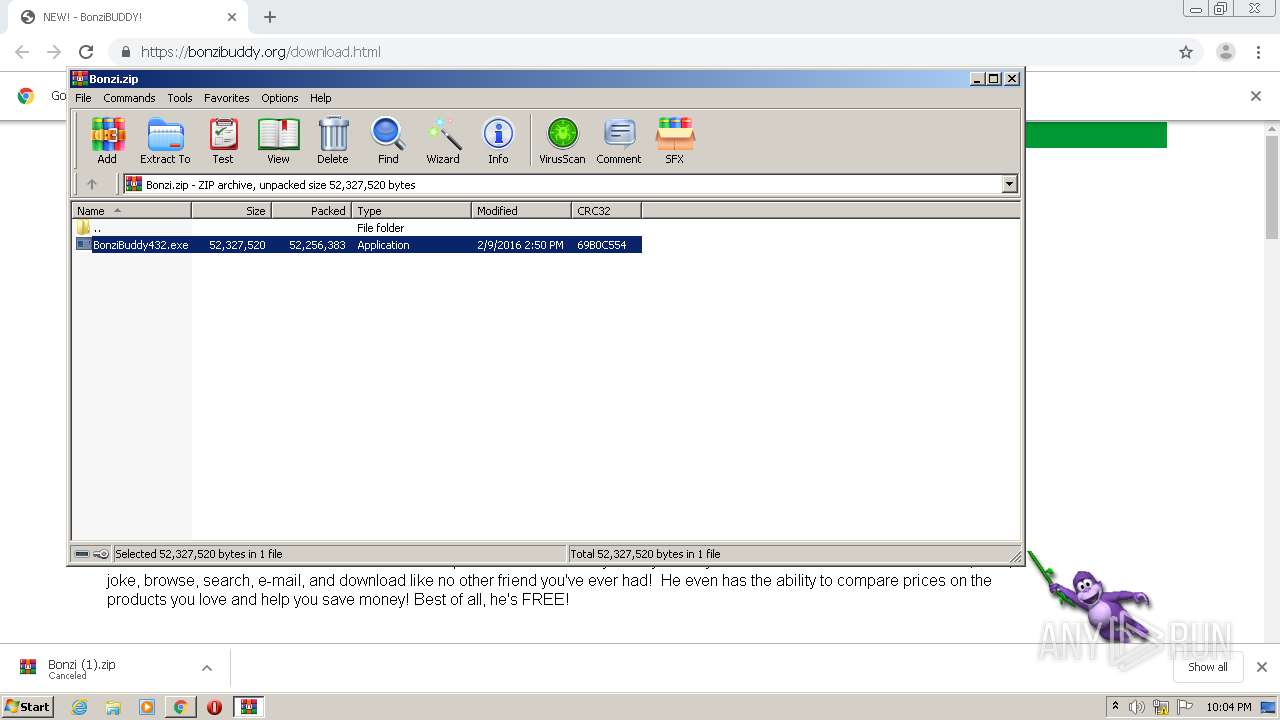
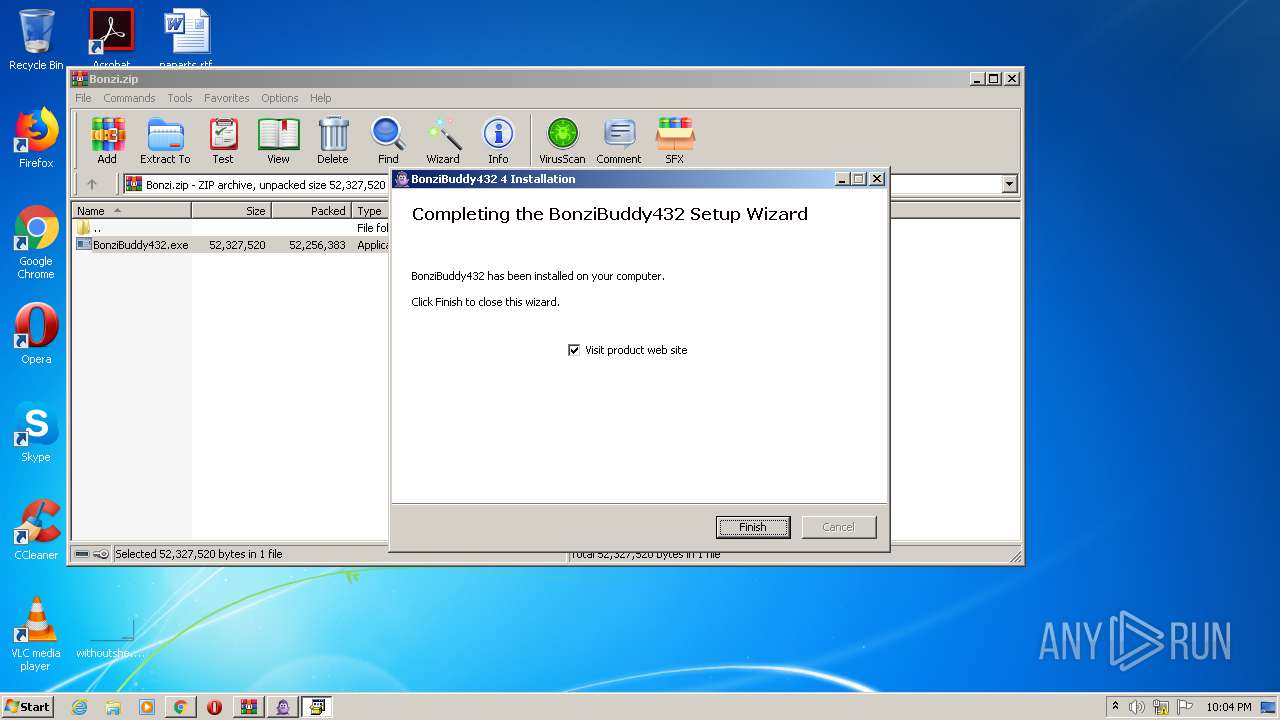
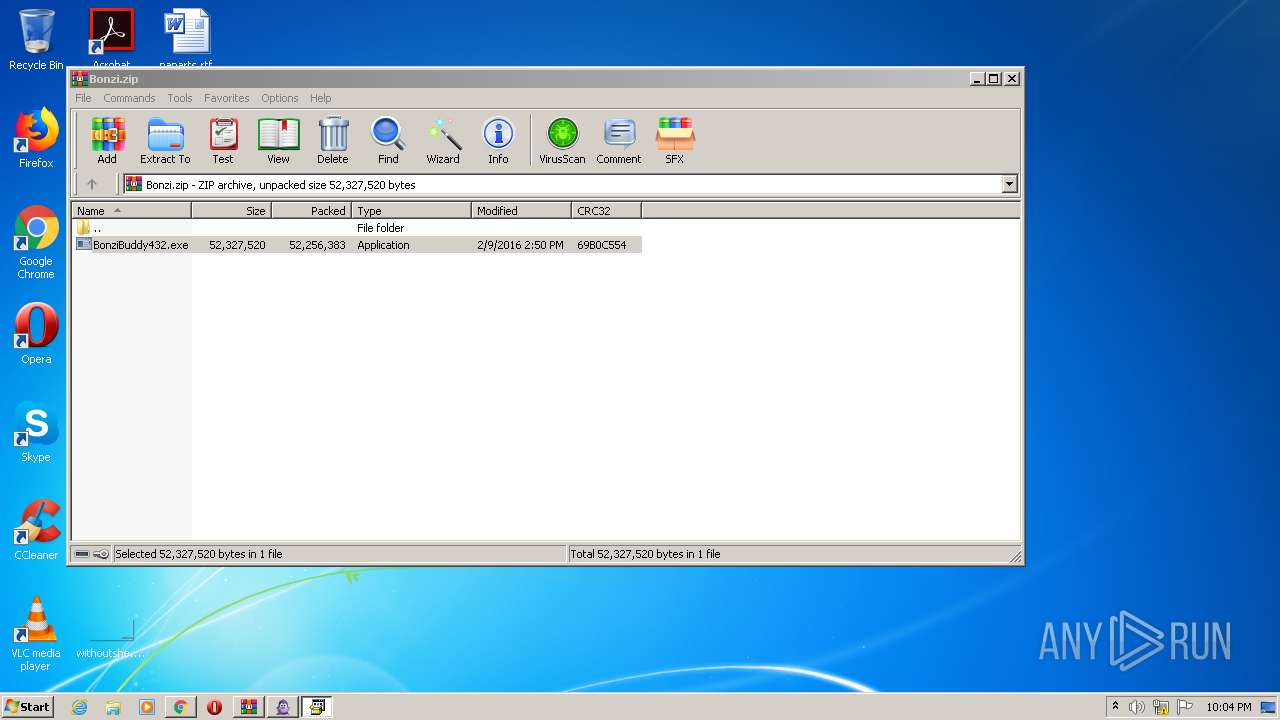
| 1520 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2352.17889\BonziBuddy432.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2352.17889\BonziBuddy432.exe | WinRAR.exe | ||||||||||||
User: admin Company: Bonzi Software Integrity Level: HIGH Description: BonziBuddy432 4 Installation Exit code: 0 Version: 4 Modules
| |||||||||||||||
| 1720 | regsvr32 /s "C:\Windows\msagent\AgentCtl.dll" | C:\Windows\system32\regsvr32.exe | — | MSAGENT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 883
Read events
2 035
Write events
1 781
Delete events
67
Modification events
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2940) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 920-13265413388512500 |
Value: 259 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 920-13265413388512500 |
Value: 259 | |||
Executable files
69
Suspicious files
50
Text files
298
Unknown types
29
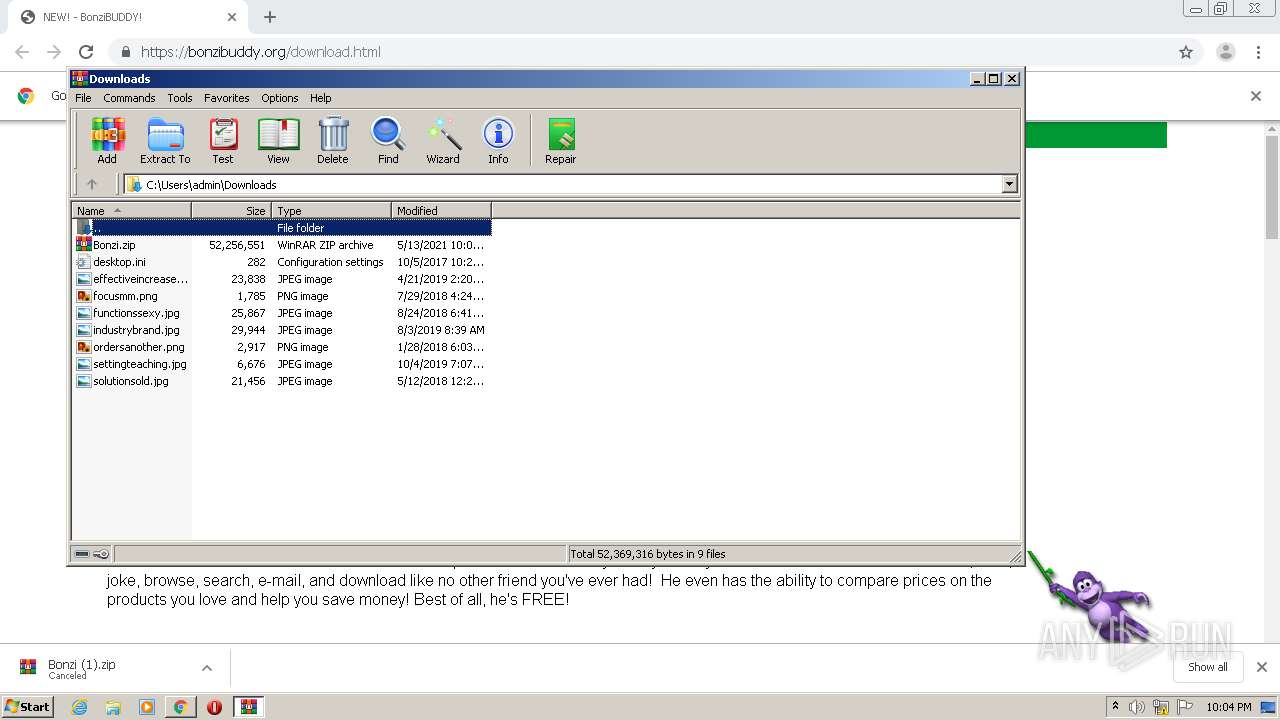
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-609D940D-398.pma | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\391326af-ce41-4d67-ab7d-28a8b5476df0.tmp | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF14fc31.TMP | text | |
MD5:1C97B70A4BAD7C026F79467C7D496AFA | SHA256:C5A02E4984DE3F30DADFC0A89A93F45418C06653C3962EAA94C93909E51D272D | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF14fc02.TMP | text | |
MD5:67F45CAA18C889645F50CD6216C81E65 | SHA256:33ED82CDDDFFD55A5059C147C6CD20F66C6712314F890A39576D3C10914D0029 | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF14fb95.TMP | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF14fea2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
31
DNS requests
17
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
692 | iexplore.exe | GET | 200 | 185.199.220.34:80 | http://bonzibuddy.tk/ | GB | html | 763 b | malicious |
2796 | chrome.exe | GET | 301 | 198.187.29.31:80 | http://bonzibuddy.org/Bonzi.zip | US | html | 240 b | malicious |
692 | iexplore.exe | GET | 200 | 172.217.19.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCu4OaM8pepHQMAAAAAy%2FdW | US | der | 472 b | whitelisted |
692 | iexplore.exe | GET | 200 | 185.199.220.34:80 | http://bonzibuddy.tk/spin.js | GB | text | 1.98 Kb | malicious |
692 | iexplore.exe | GET | 200 | 172.217.19.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDDhar4btqgzgUAAAAAh7wW | US | der | 472 b | whitelisted |
692 | iexplore.exe | GET | — | 185.199.220.34:80 | http://bonzibuddy.tk/survive.mp3 | GB | — | — | malicious |
692 | iexplore.exe | GET | 200 | 172.217.19.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
692 | iexplore.exe | GET | 404 | 185.199.220.34:80 | http://bonzibuddy.tk/favicon.ico | GB | html | 1.21 Kb | malicious |
692 | iexplore.exe | GET | 200 | 185.199.220.34:80 | http://bonzibuddy.tk/script.js | GB | text | 929 b | malicious |
692 | iexplore.exe | GET | 200 | 172.217.19.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDtqToB6jJa2wMAAAAAy%2FdX | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
692 | iexplore.exe | 172.217.19.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2796 | chrome.exe | 198.187.29.31:443 | bonzibuddy.org | Namecheap, Inc. | US | malicious |
2796 | chrome.exe | 198.187.29.31:80 | bonzibuddy.org | Namecheap, Inc. | US | malicious |
2796 | chrome.exe | 142.250.185.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
692 | iexplore.exe | 185.199.220.34:80 | bonzibuddy.tk | Krystal Hosting Ltd | GB | suspicious |
2796 | chrome.exe | 142.250.74.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
692 | iexplore.exe | 69.16.175.10:80 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
— | — | 192.168.100.7:137 | — | — | — | malicious |
692 | iexplore.exe | 142.250.74.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2344 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bonzibuddy.org |
| unknown |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
bonzibuddy.tk |
| malicious |
fonts.googleapis.com |
| whitelisted |
code.jquery.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2796 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
692 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
692 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
692 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
692 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
692 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
692 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |