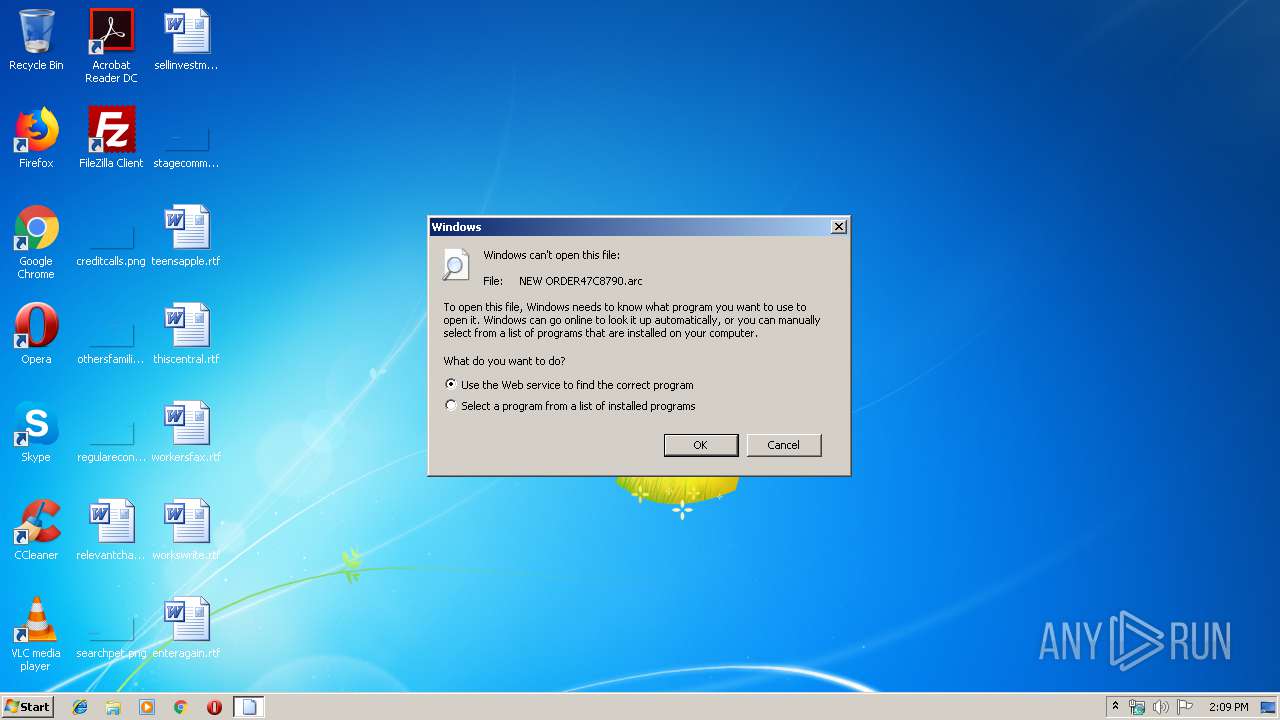
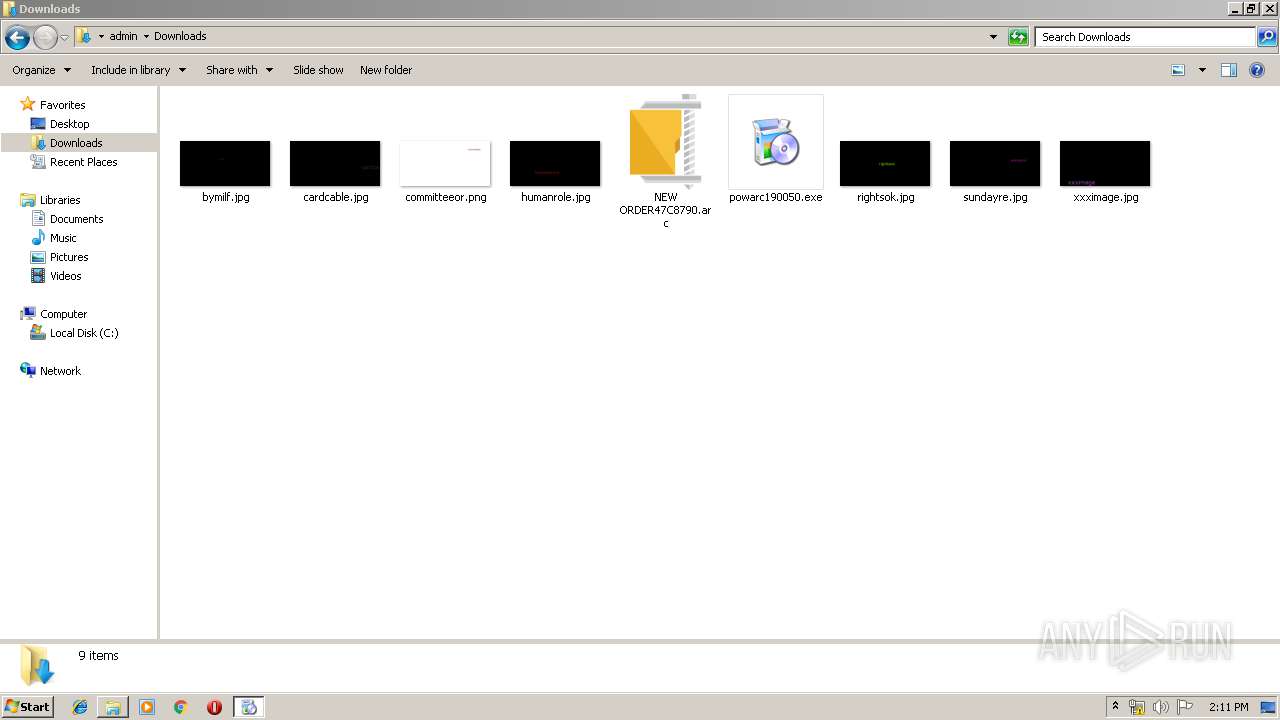
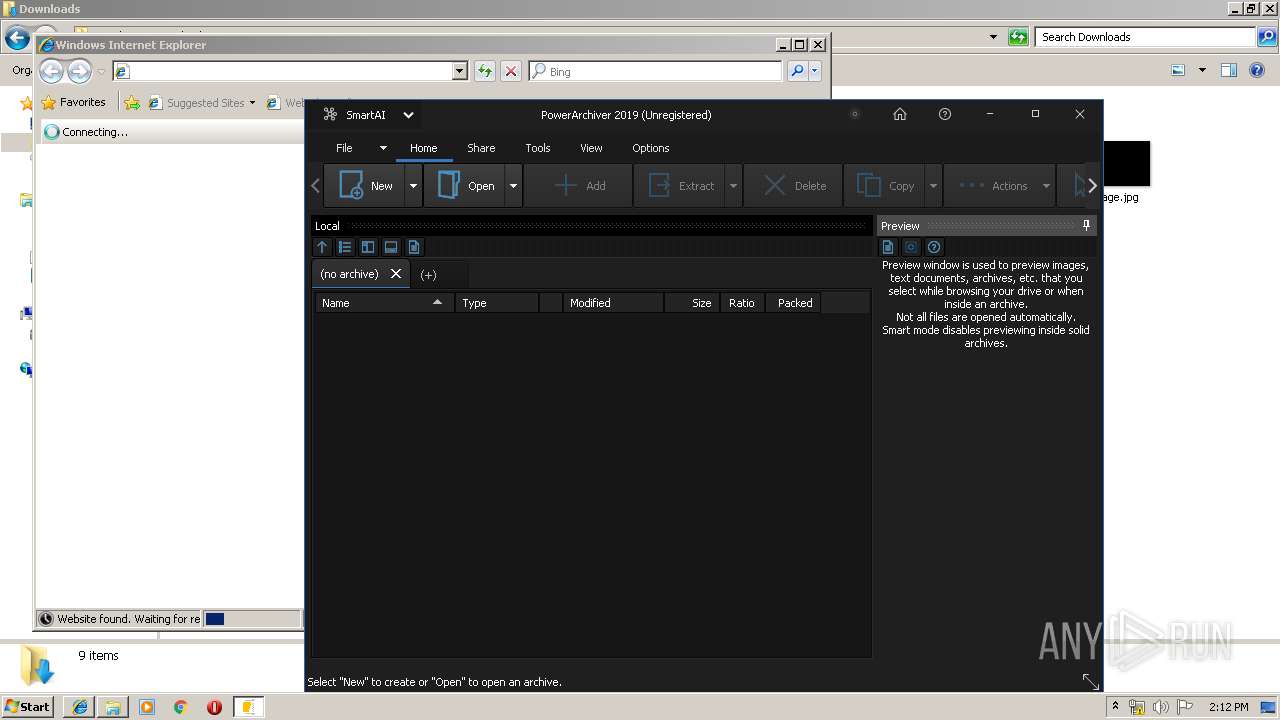
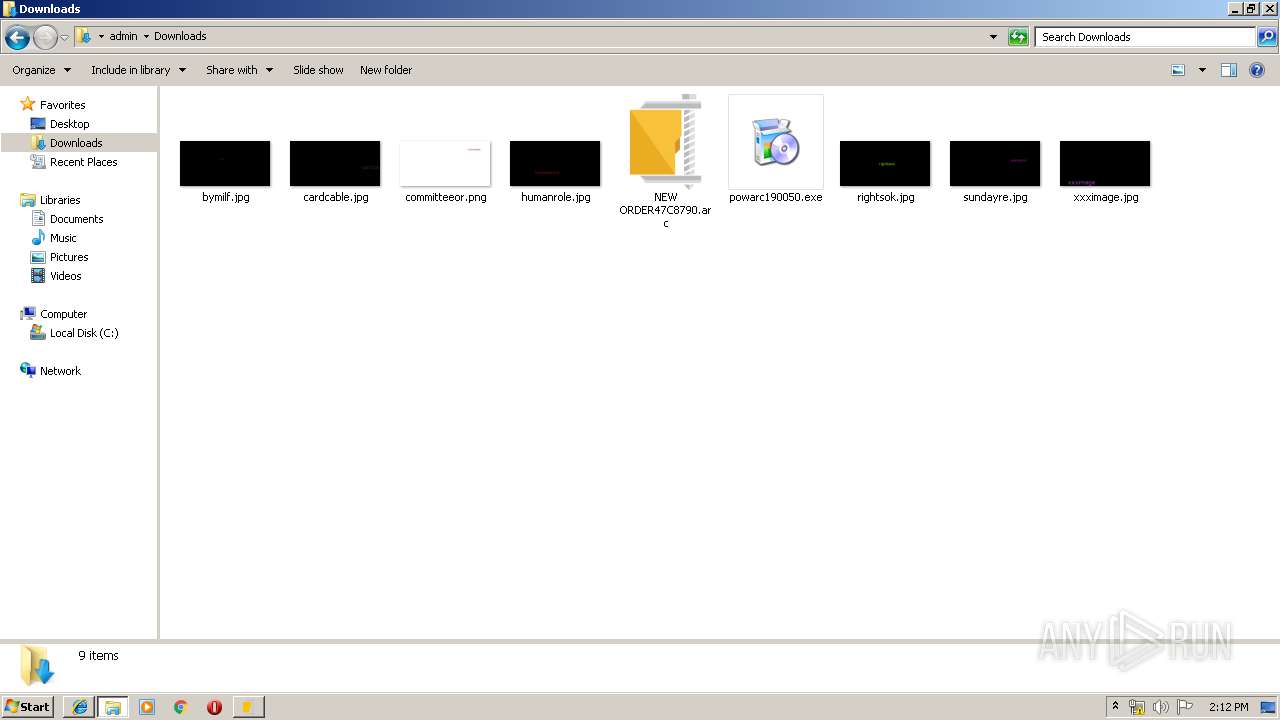
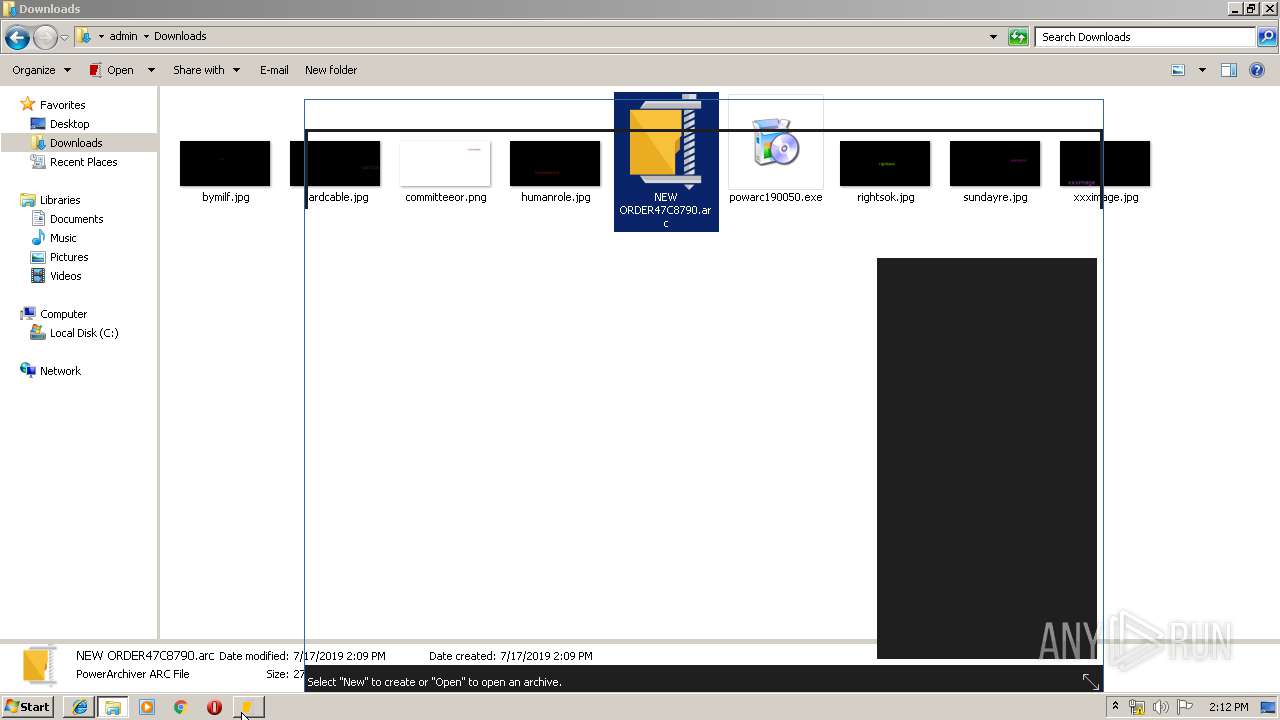
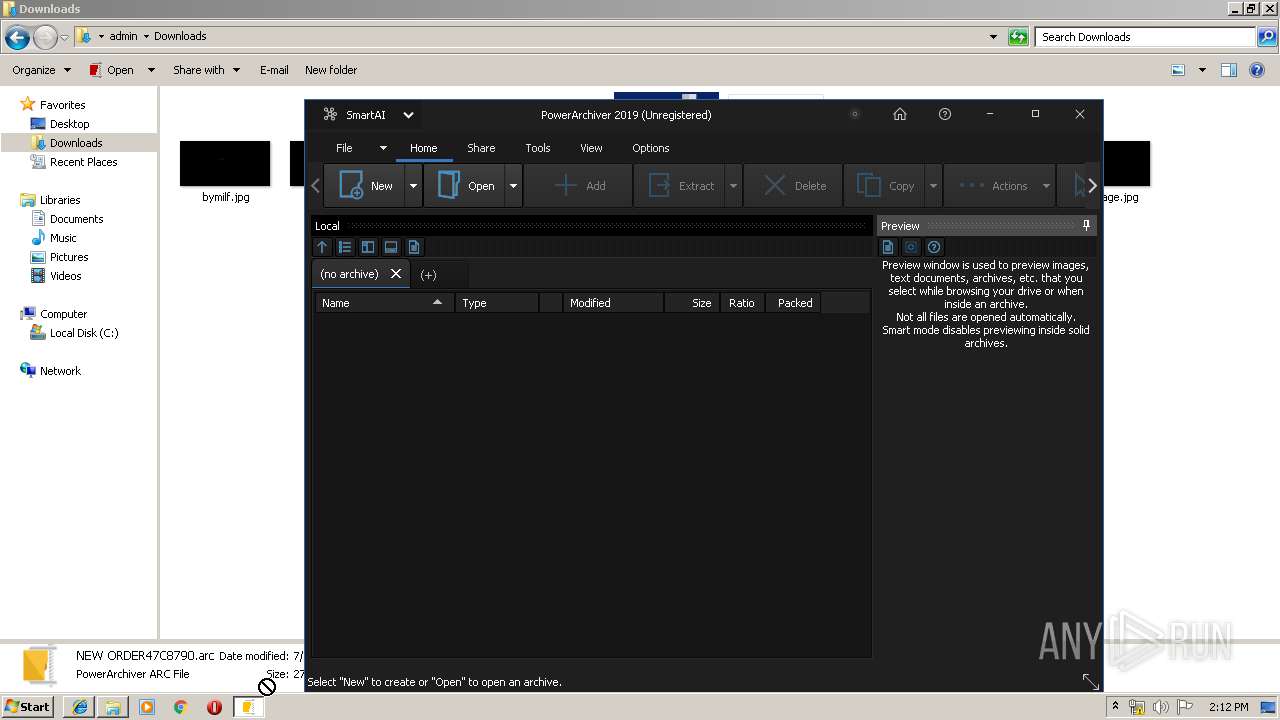
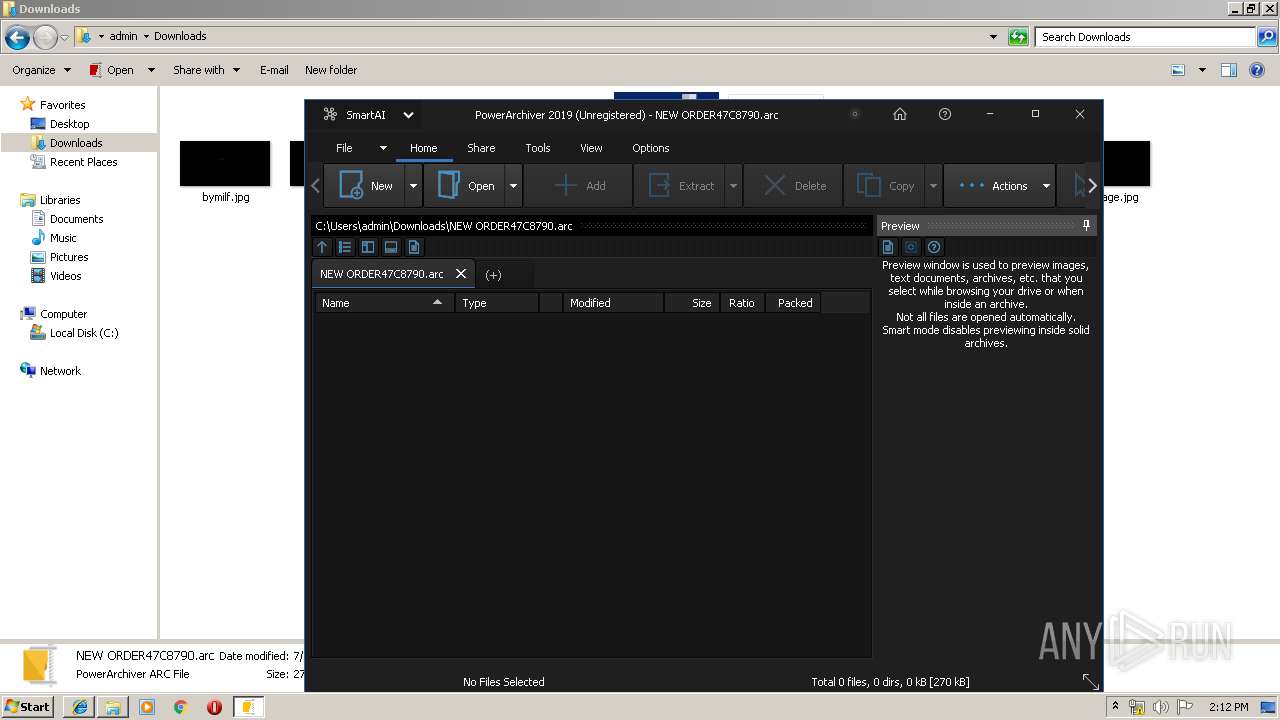
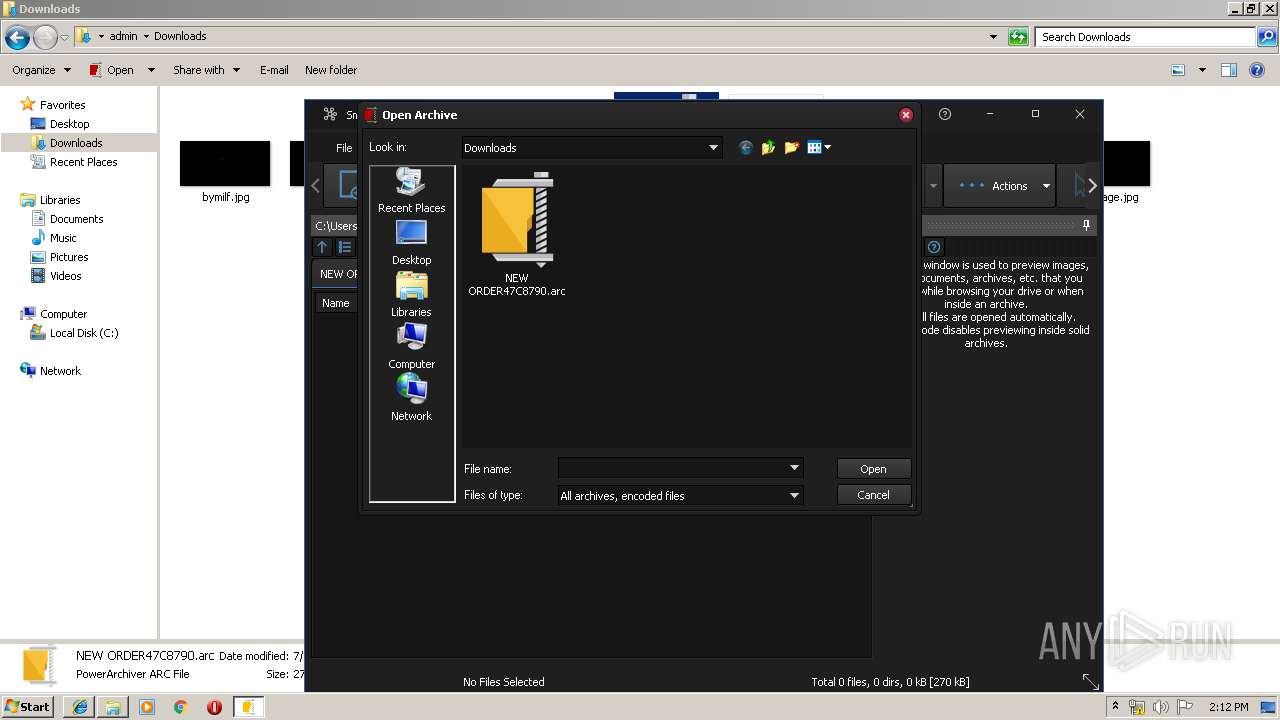
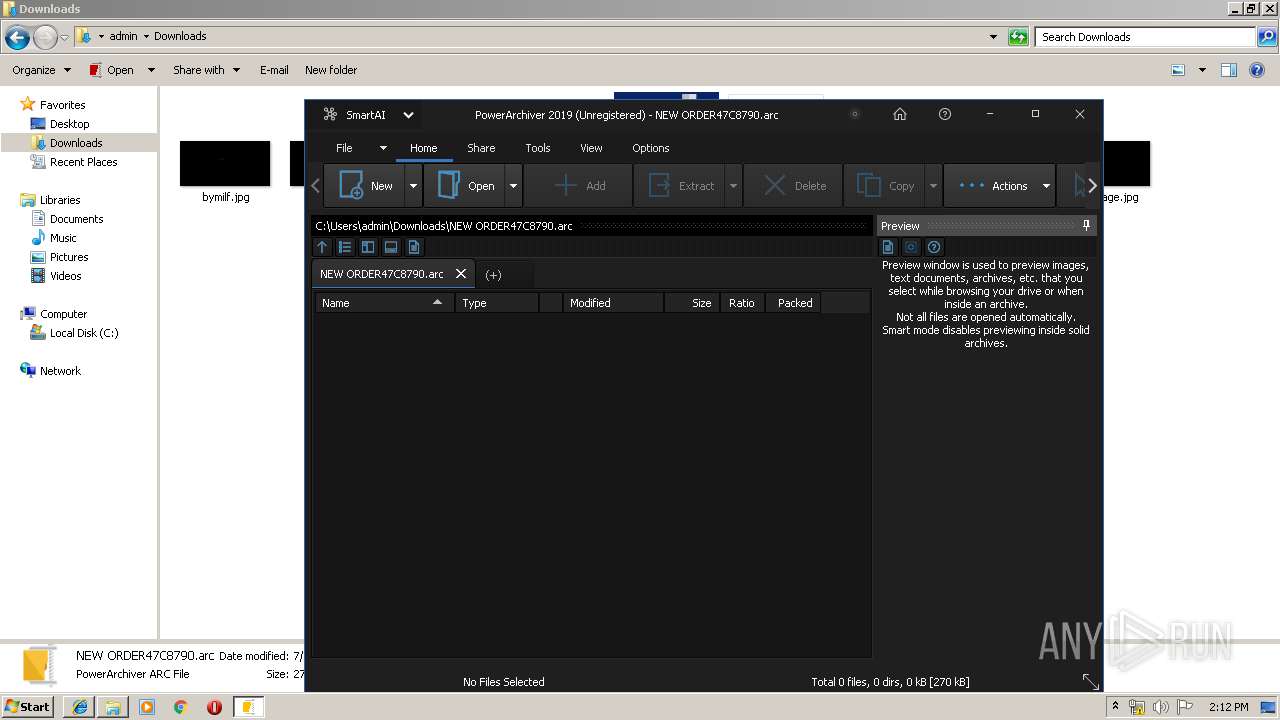
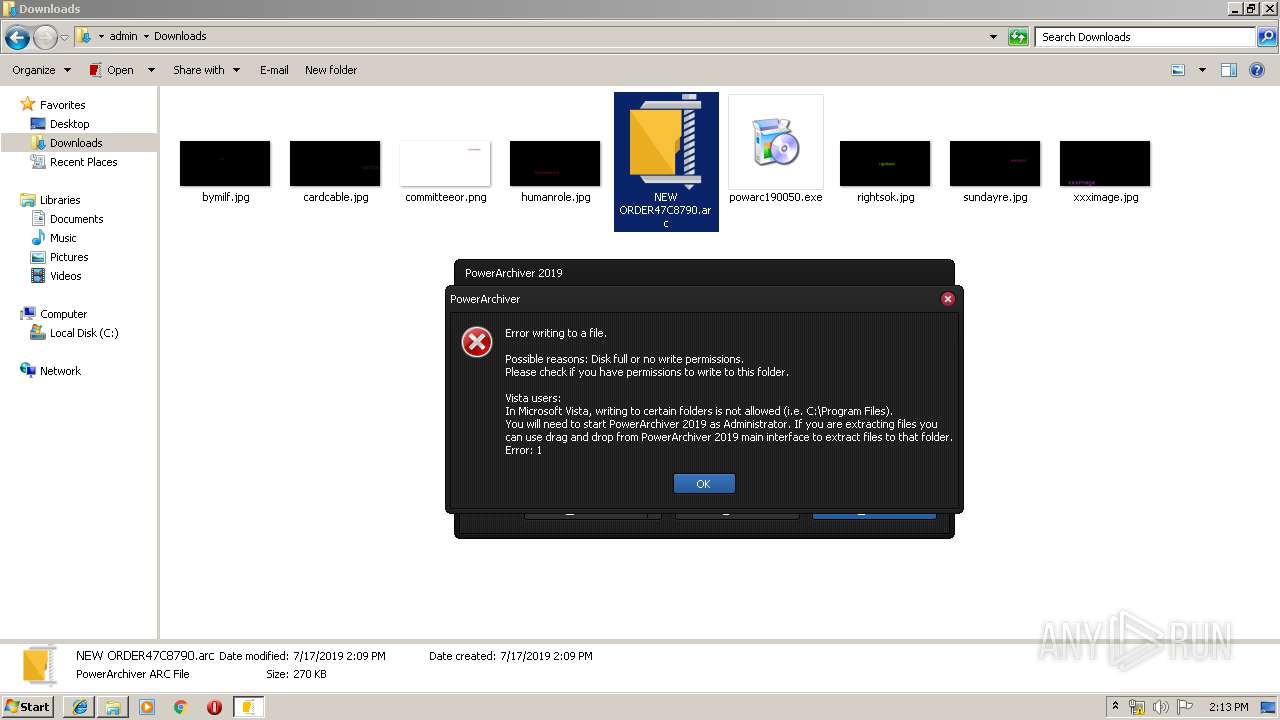
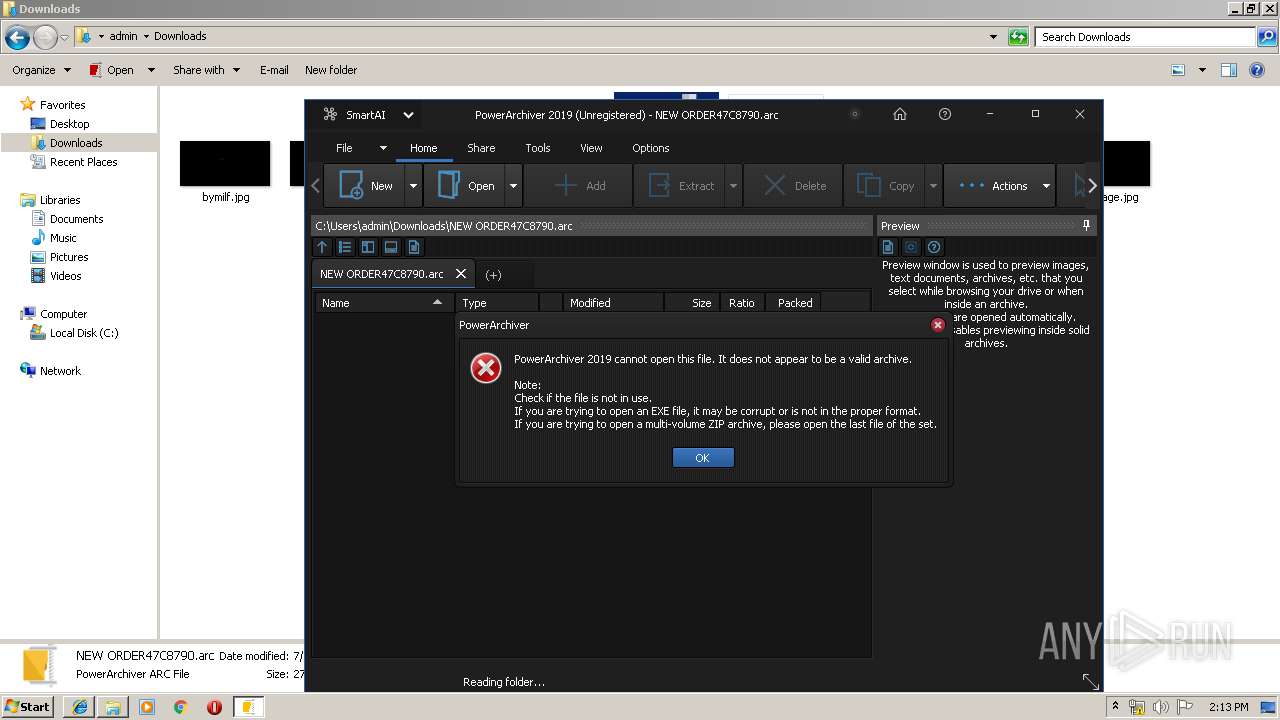
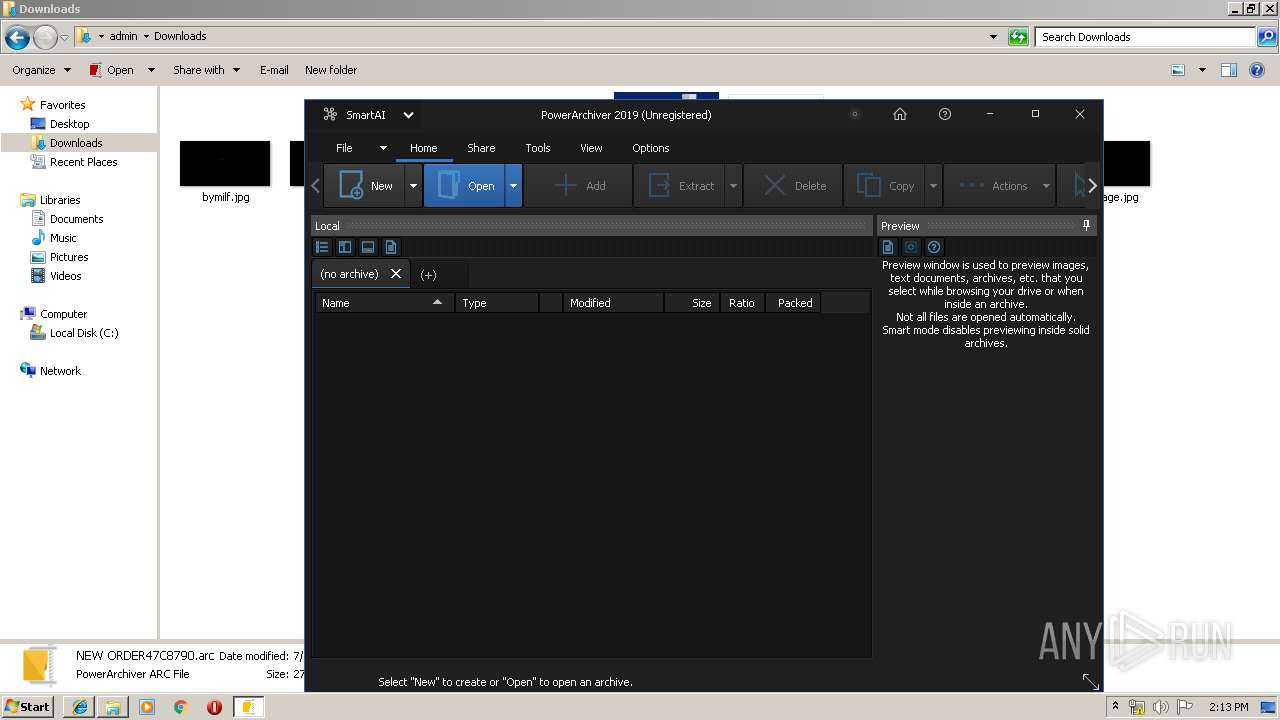
| File name: | NEW ORDER47C8790.arc |
| Full analysis: | https://app.any.run/tasks/fdfa45b9-e3fa-46ae-b9a3-5a473e11b7ca |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 13:09:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | FreeArc archive <http://freearc.org> |
| MD5: | 9632AE52D8967CF1C78288FCC9731A28 |
| SHA1: | FB943B69BEB827CA920B019733AA07BDED871A0F |
| SHA256: | CA0A241632813FB60E6929944107A59CDEB1BEA1EE92DDB3ADBC3B1B641636FA |
| SSDEEP: | 6144:L+YKi9usRWe00dElE362xuWBf3Wa/PVg2C7cDWx8fP1VGji:L++geEWBua3m2C7GWx8fDUi |
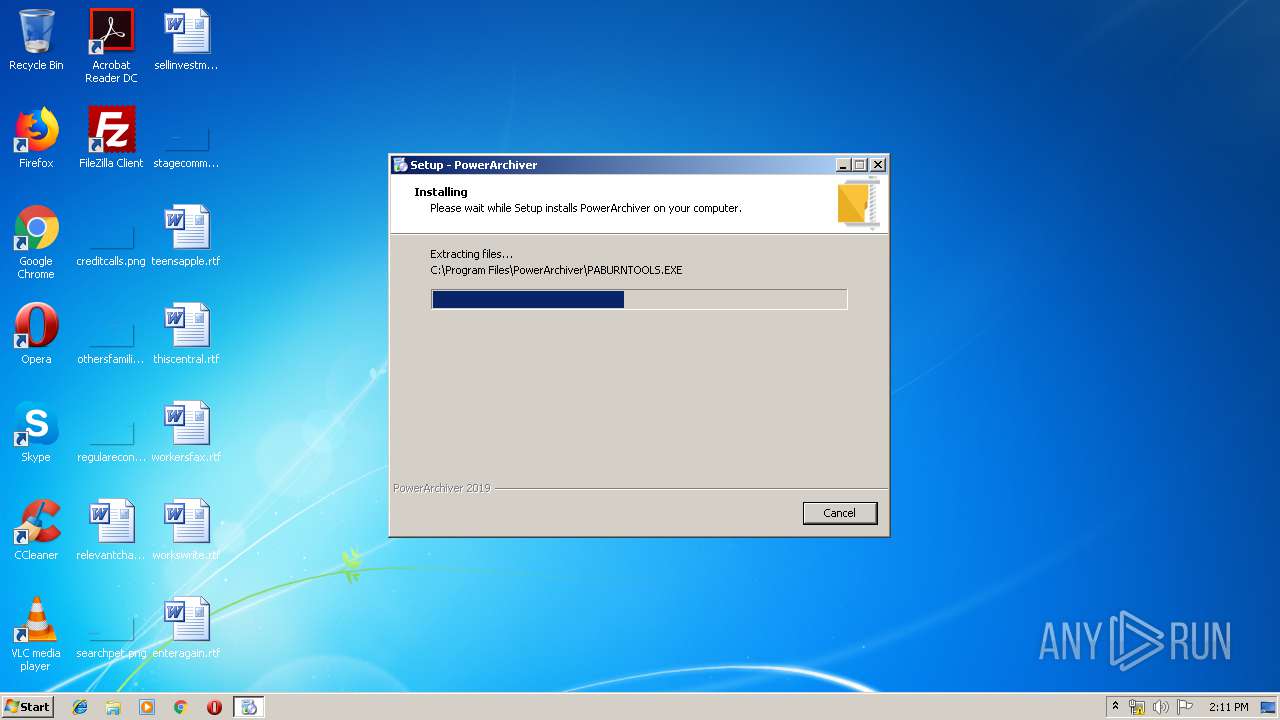
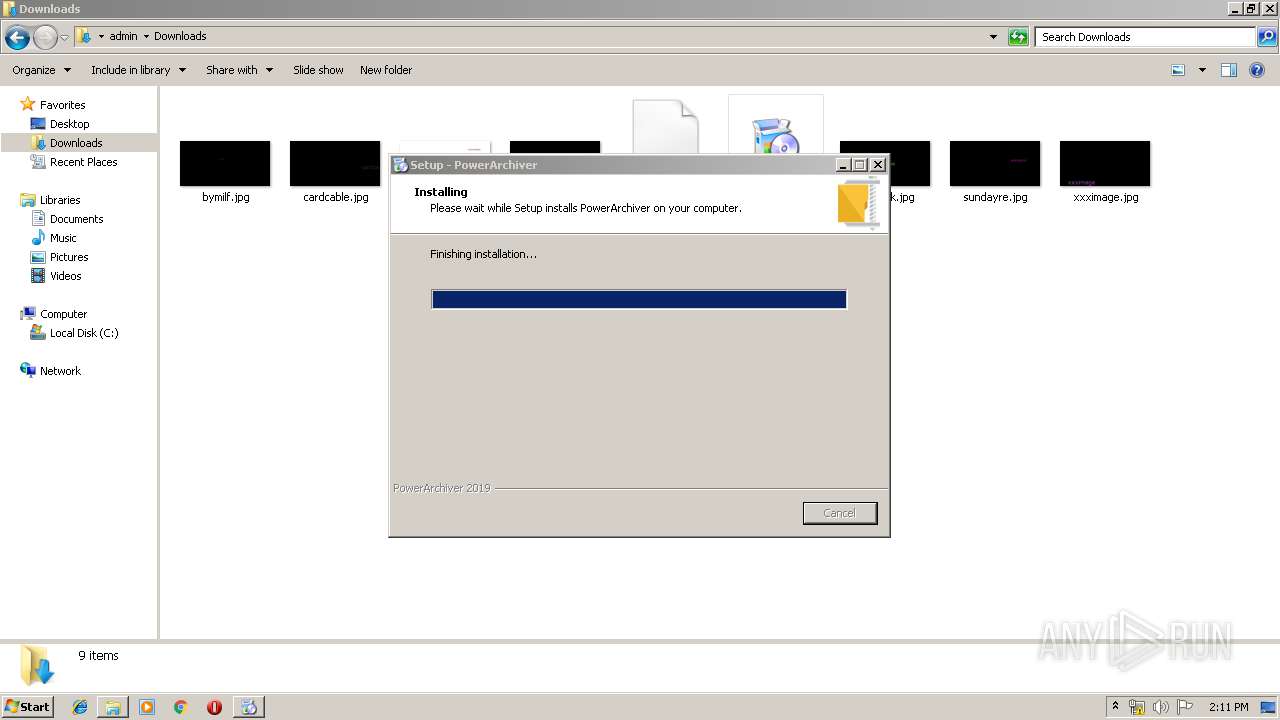
MALICIOUS
Application was dropped or rewritten from another process
- powarc190050.exe (PID: 2408)
- powarc190050.exe (PID: 1264)
- powerarc.exe (PID: 2124)
- _pautil.exe (PID: 4024)
- _pautil.exe (PID: 2716)
- _pautil.exe (PID: 3460)
- _PAutil.exe (PID: 3916)
Registers / Runs the DLL via REGSVR32.EXE
- powarc190050.tmp (PID: 2484)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 1764)
- powerarc.exe (PID: 2124)
- regsvr32.exe (PID: 2684)
- regsvr32.exe (PID: 3232)
- regsvr32.exe (PID: 1920)
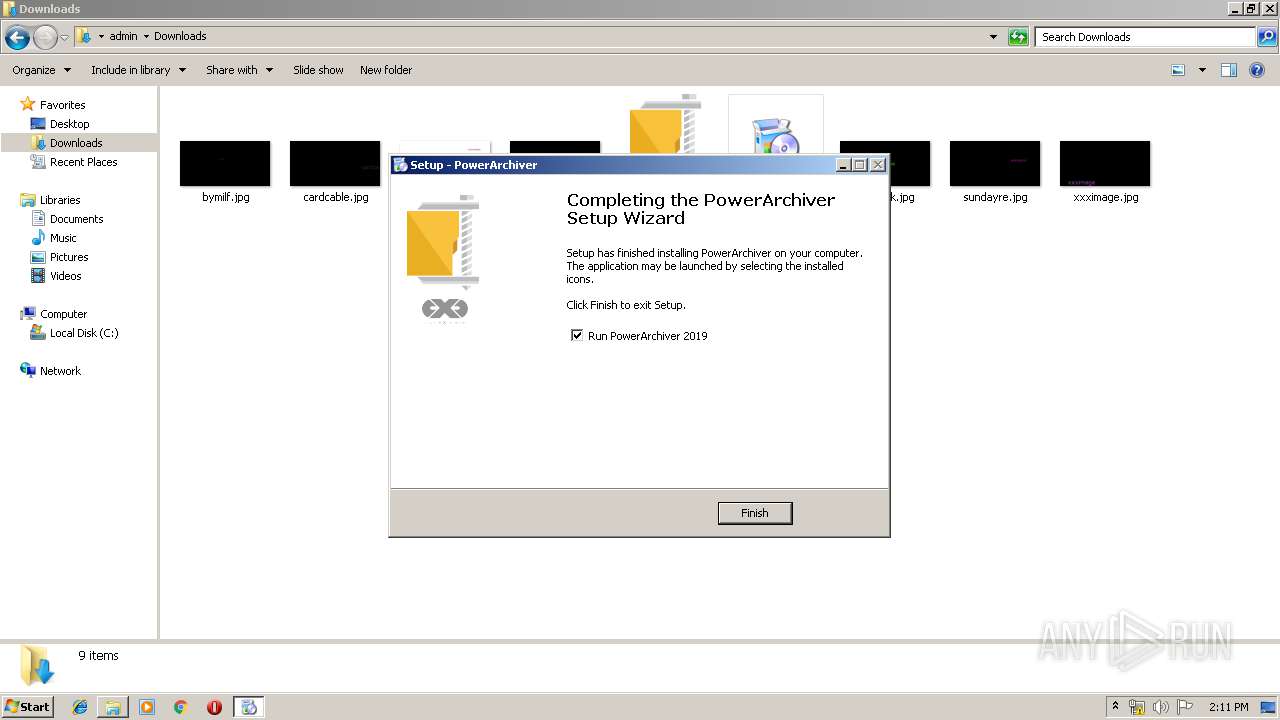
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3420)
Searches for installed software
- powarc190050.tmp (PID: 2484)
Executable content was dropped or overwritten
- chrome.exe (PID: 3420)
- powarc190050.tmp (PID: 2484)
- powarc190050.exe (PID: 1264)
- powarc190050.exe (PID: 2408)
Creates files in the user directory
- powarc190050.tmp (PID: 2484)
- powerarc.exe (PID: 2124)
Creates COM task schedule object
- regsvr32.exe (PID: 3232)
- regsvr32.exe (PID: 1764)
- regsvr32.exe (PID: 2684)
- regsvr32.exe (PID: 1920)
- _pautil.exe (PID: 4024)
- _pautil.exe (PID: 2716)
Modifies the open verb of a shell class
- _pautil.exe (PID: 4024)
- _pautil.exe (PID: 2716)
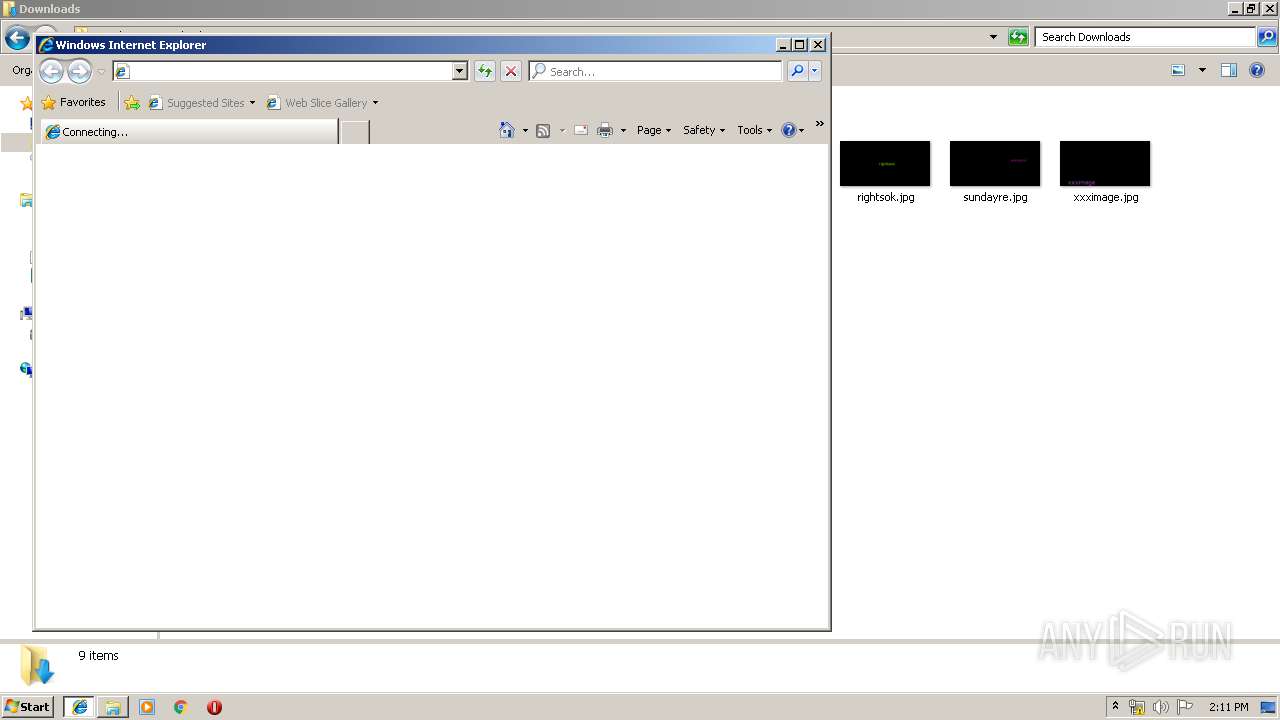
Starts Internet Explorer
- _pautil.exe (PID: 3460)
Reads Windows owner or organization settings
- powarc190050.tmp (PID: 2484)
Uses TASKKILL.EXE to kill process
- powarc190050.tmp (PID: 2484)
Reads the Windows organization settings
- powarc190050.tmp (PID: 2484)
INFO
Changes settings of System certificates
- chrome.exe (PID: 2496)
- iexplore.exe (PID: 1664)
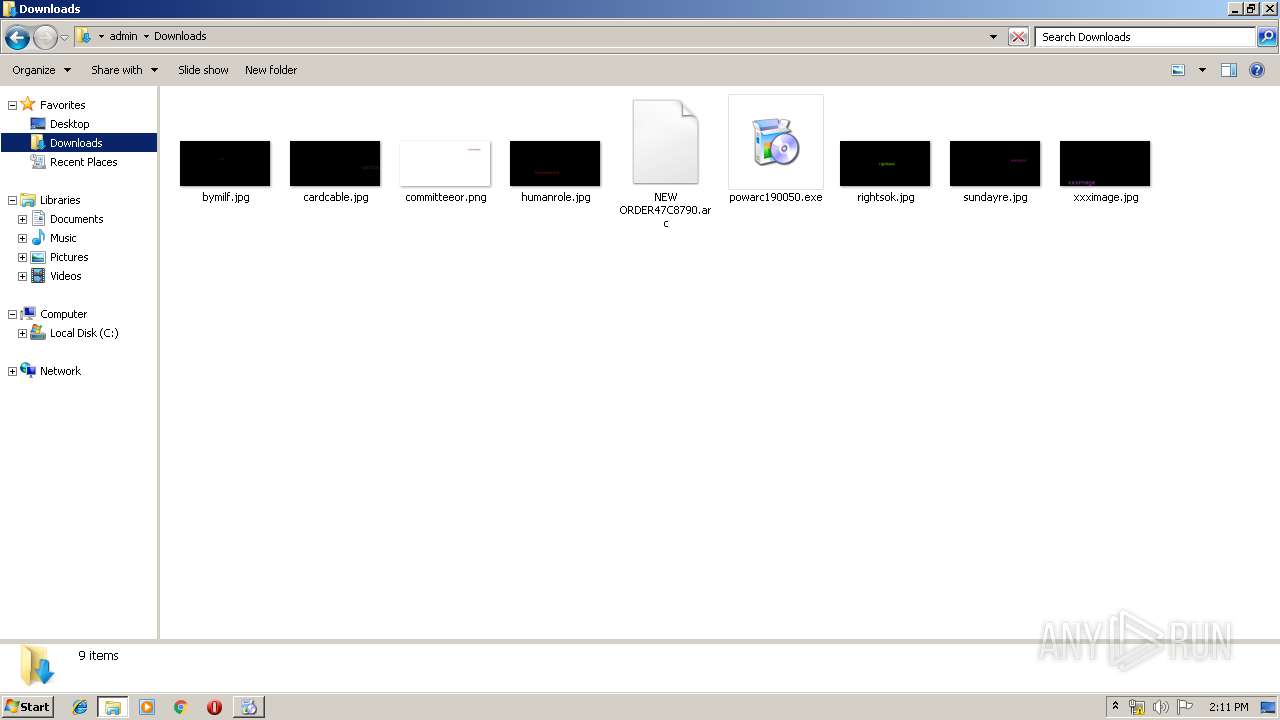
Application was dropped or rewritten from another process
- powarc190050.tmp (PID: 2540)
- powarc190050.tmp (PID: 2484)
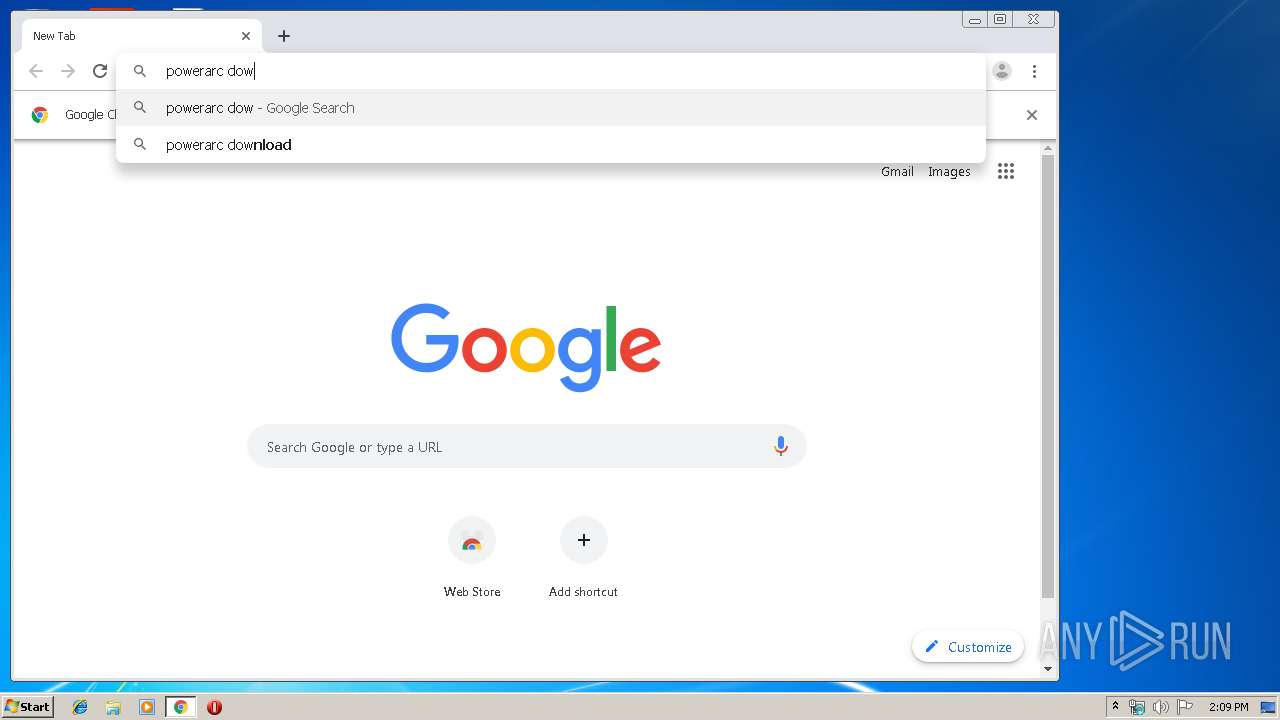
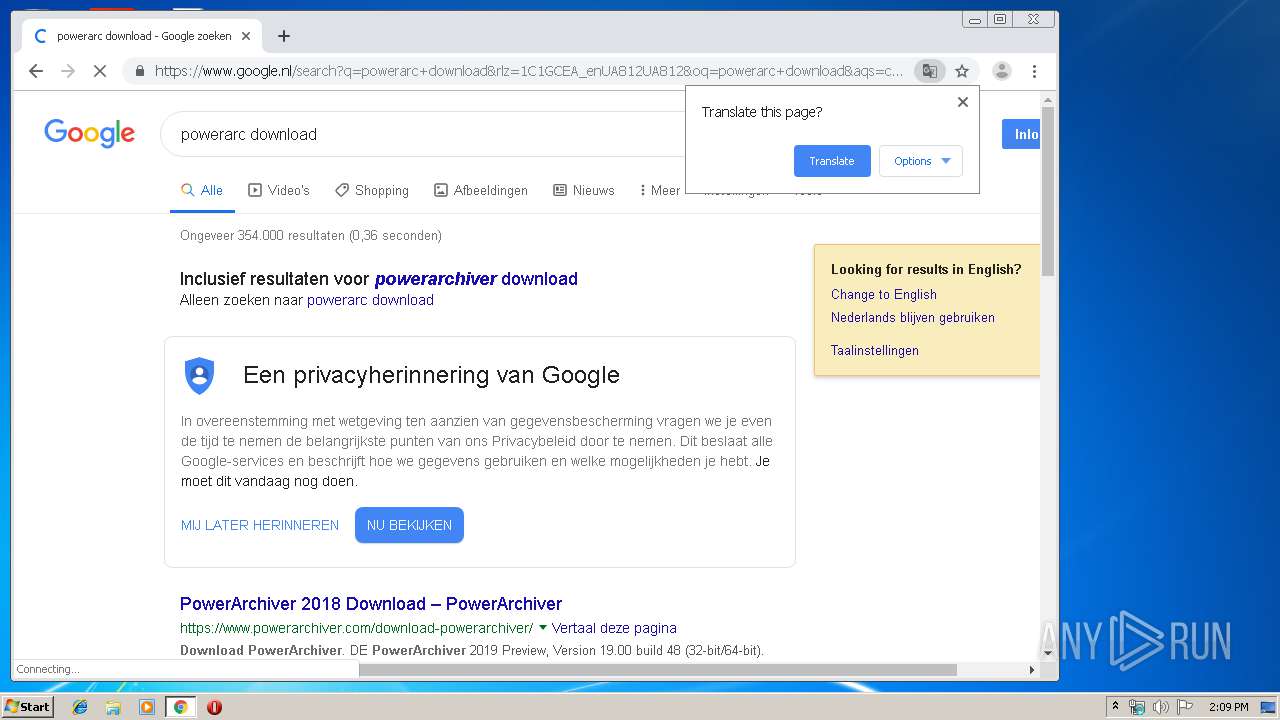
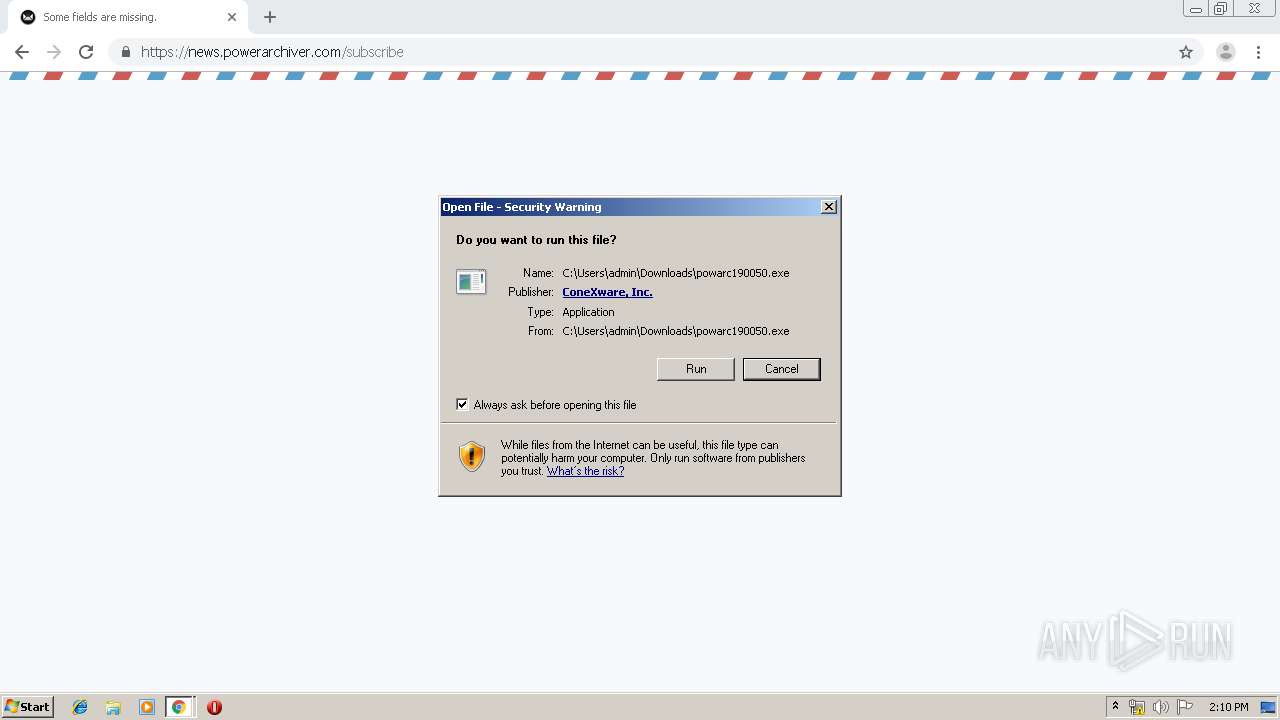
Manual execution by user
- chrome.exe (PID: 3420)
- explorer.exe (PID: 1664)
Reads Internet Cache Settings
- chrome.exe (PID: 3420)
- iexplore.exe (PID: 1664)
Application launched itself
- chrome.exe (PID: 3420)
- iexplore.exe (PID: 2224)
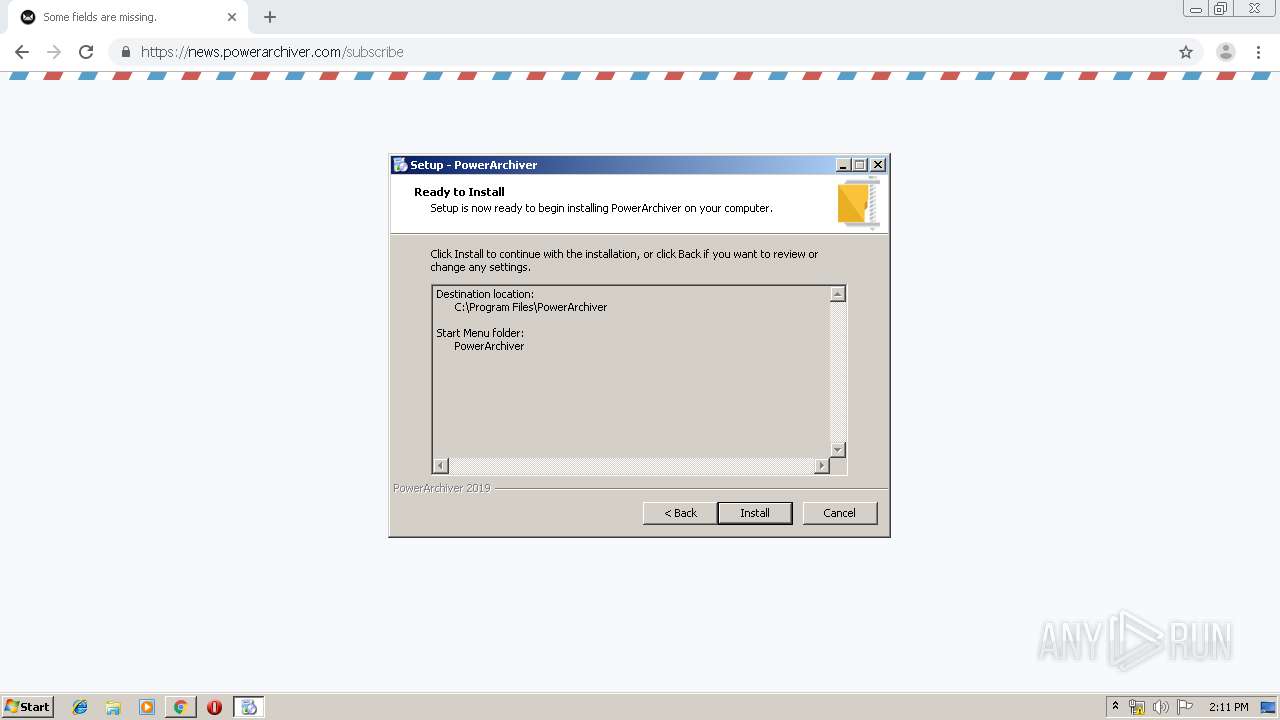
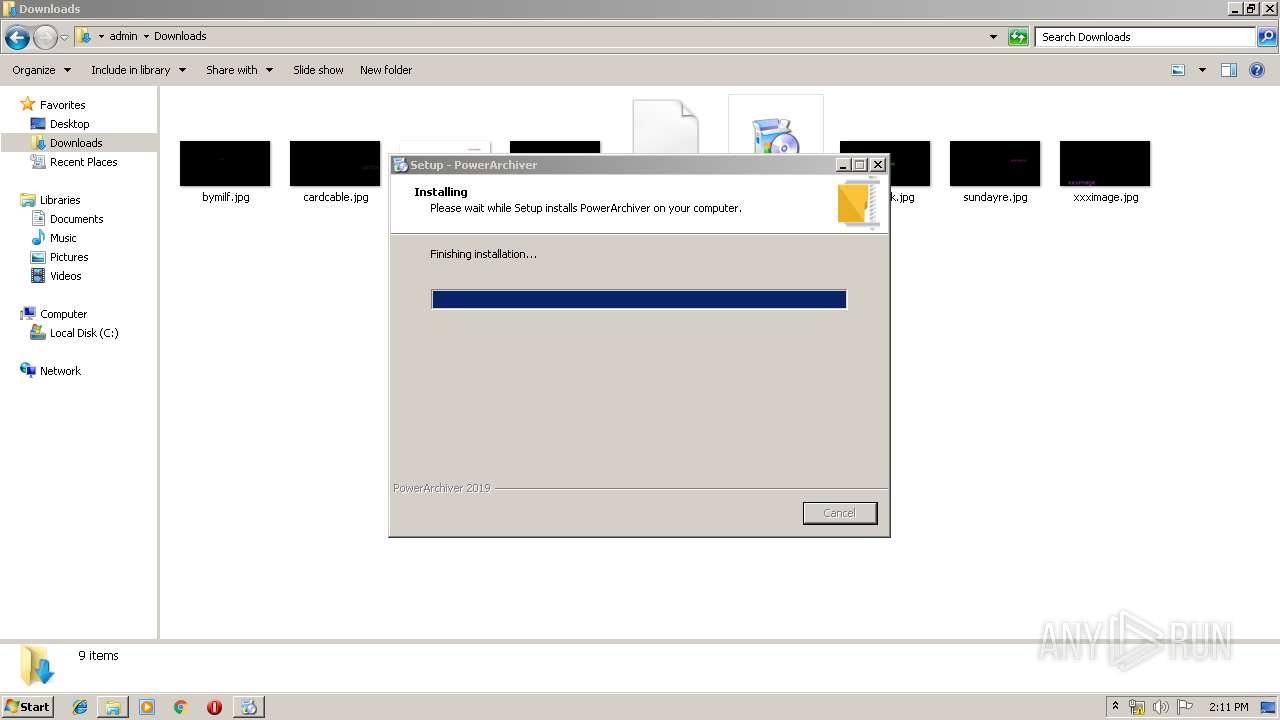
Creates a software uninstall entry
- powarc190050.tmp (PID: 2484)
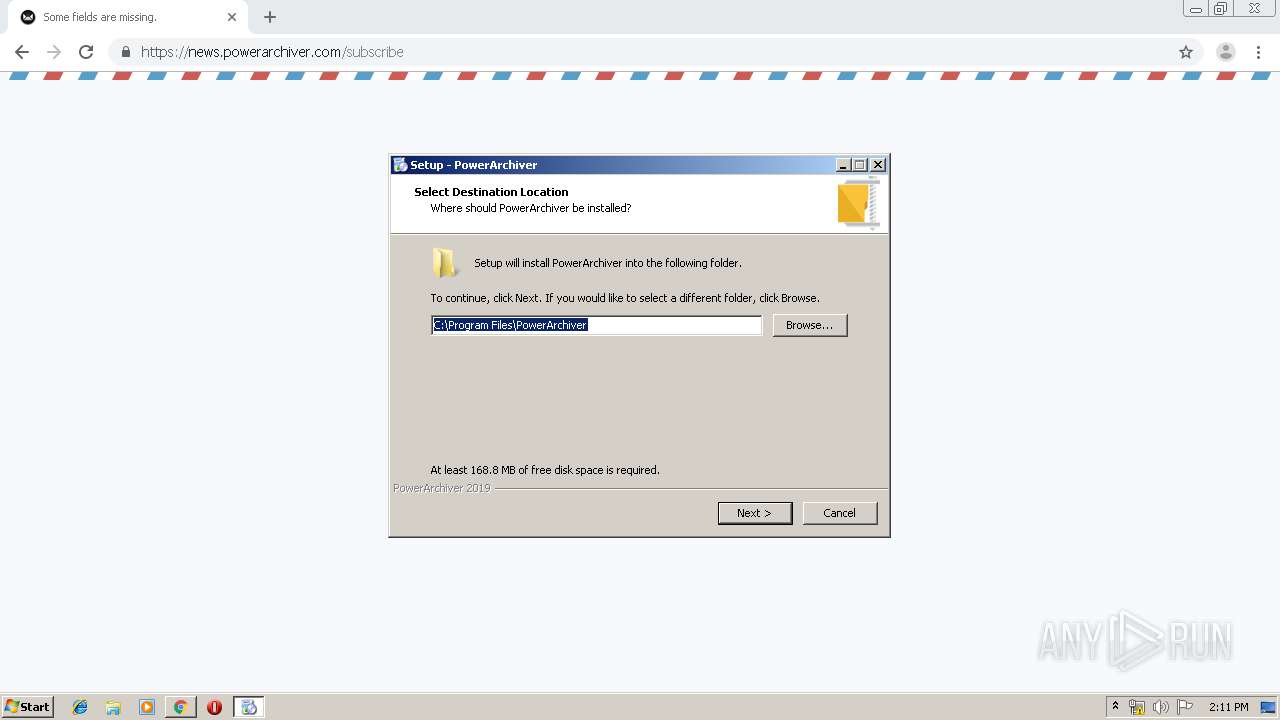
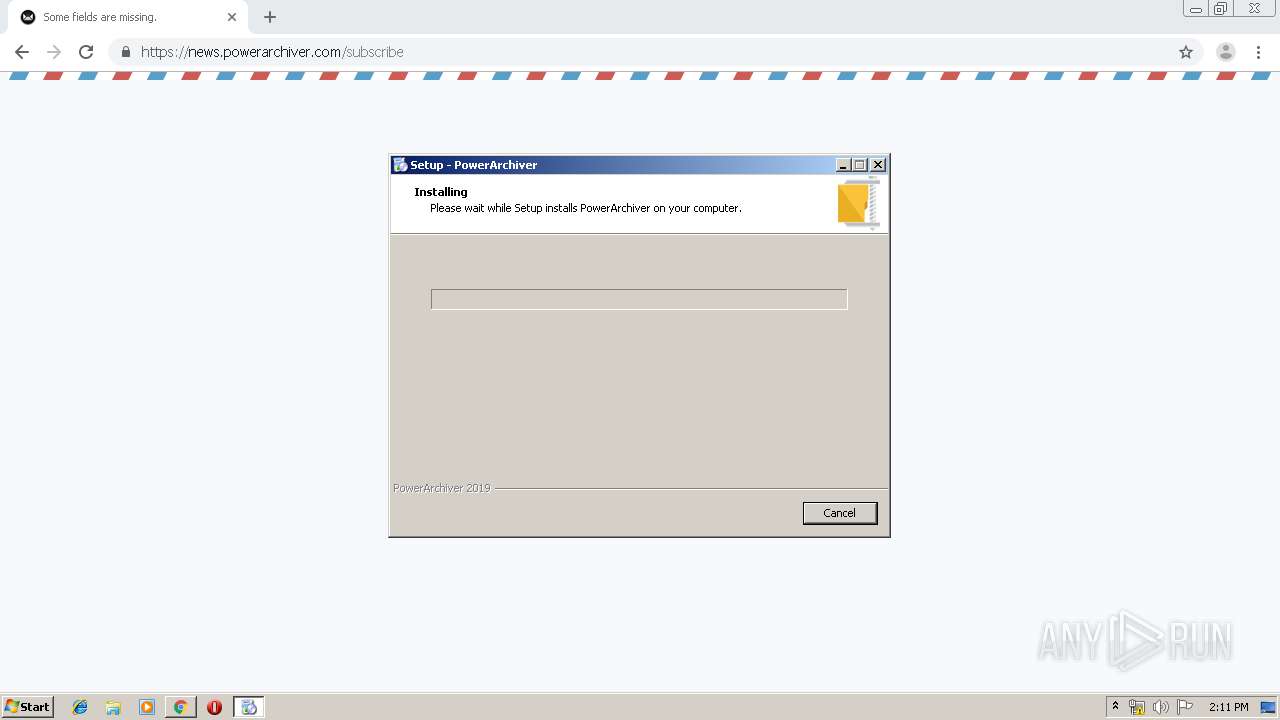
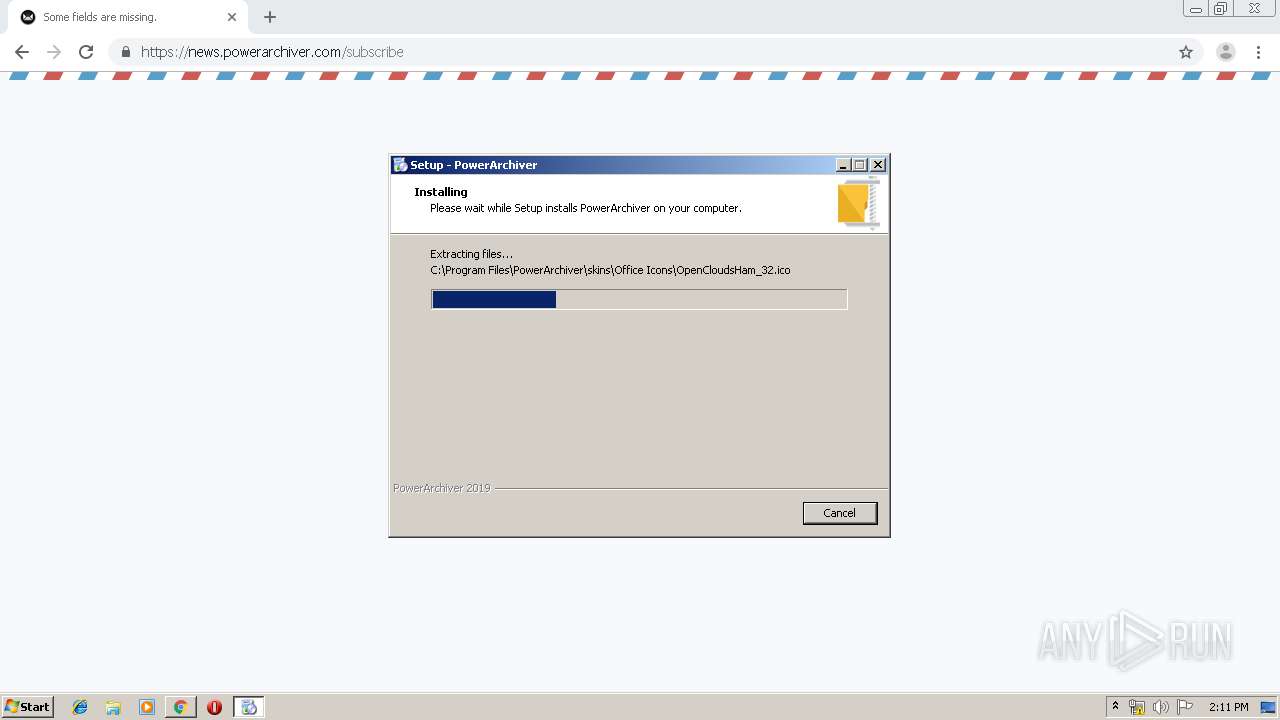
Creates files in the program directory
- powarc190050.tmp (PID: 2484)
Changes internet zones settings
- iexplore.exe (PID: 2224)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1664)
Creates files in the user directory
- iexplore.exe (PID: 1664)
Reads internet explorer settings
- iexplore.exe (PID: 1664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .arc | | | FreeArc compressed archive (100) |
|---|
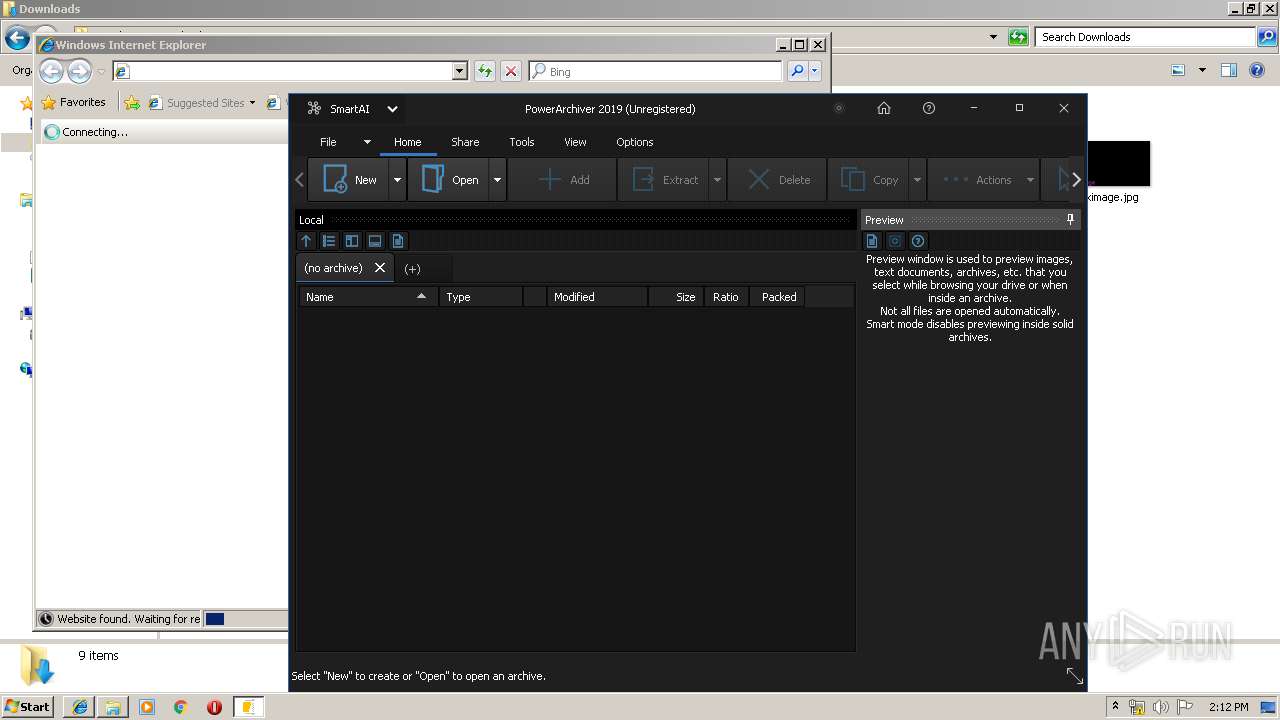
Total processes
119
Monitored processes
61
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,6722032064836467233,3696098140084490878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18085238028175263139 --mojo-platform-channel-handle=2540 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Windows\System32\tskill.exe" paburntools | C:\Windows\System32\tskill.exe | — | powarc190050.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Remote Desktop Services End Process Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,6722032064836467233,3696098140084490878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4266892875312759117 --mojo-platform-channel-handle=3512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,6722032064836467233,3696098140084490878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2166304948381861875 --mojo-platform-channel-handle=3964 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
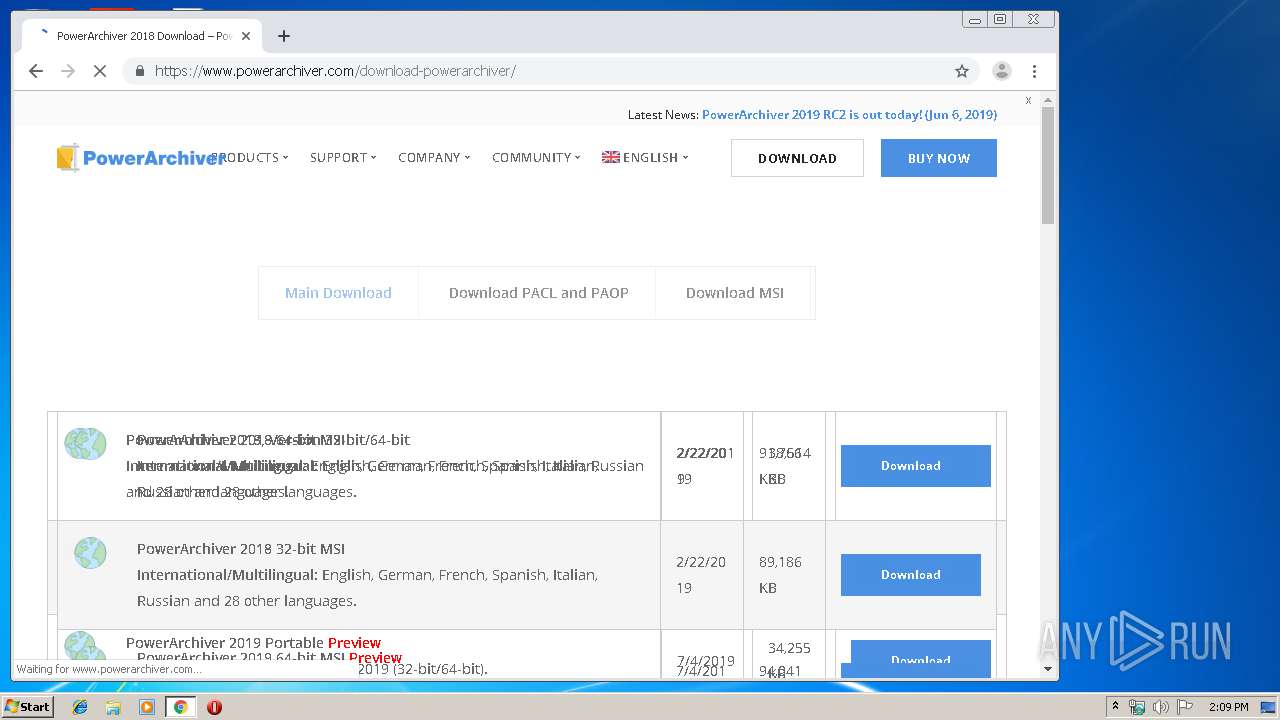
| 1264 | "C:\Users\admin\Downloads\powarc190050.exe" /SPAWNWND=$40140 /NOTIFYWND=$E018E | C:\Users\admin\Downloads\powarc190050.exe | powarc190050.tmp | ||||||||||||
User: admin Company: ConeXware, Inc. Integrity Level: HIGH Description: PowerArchiver Setup Exit code: 0 Version: 19.00.50 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,6722032064836467233,3696098140084490878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4305866164307845461 --mojo-platform-channel-handle=3188 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1664 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1664 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2224 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,6722032064836467233,3696098140084490878,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13316528604931944974 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,6722032064836467233,3696098140084490878,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6811227044182043841 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
9 126
Read events
2 592
Write events
6 169
Delete events
365
Modification events
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3420-13207842575208375 |
Value: 259 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
169
Suspicious files
250
Text files
601
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f3cb8870-286f-4e7e-8c13-5b7fa5d49363.tmp | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF18074e.TMP | text | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF18077d.TMP | text | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
87
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
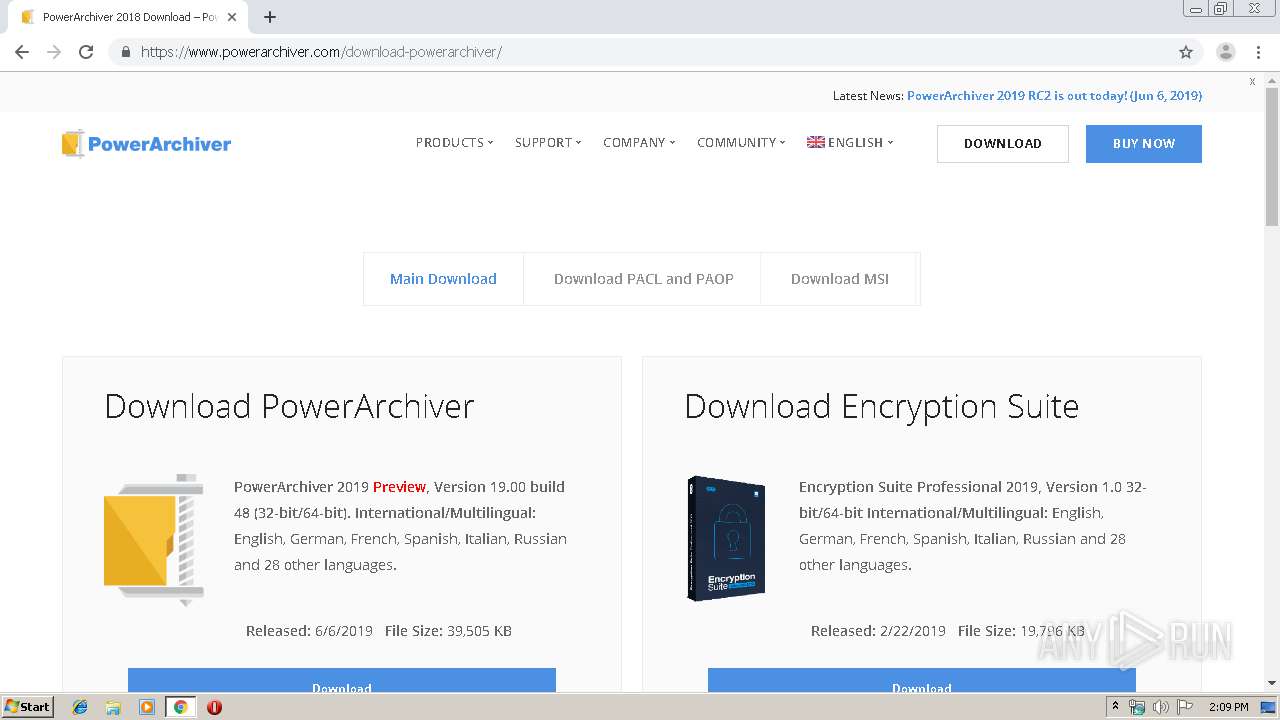
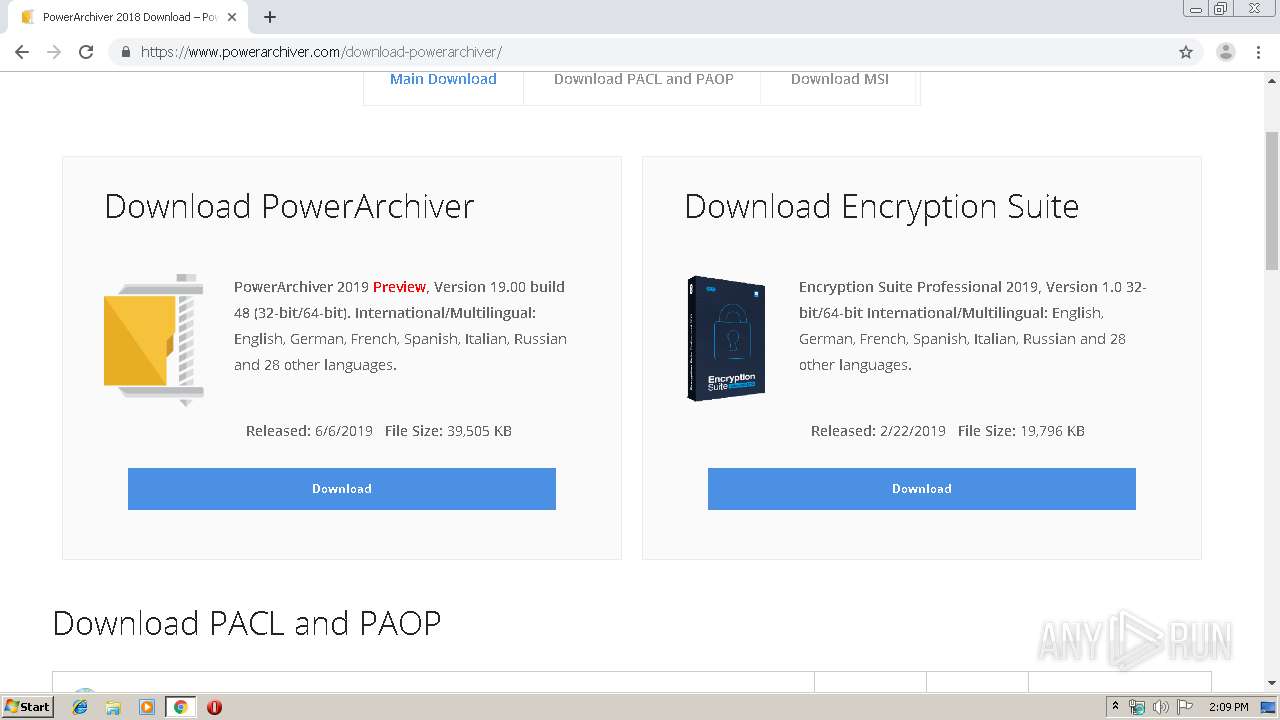
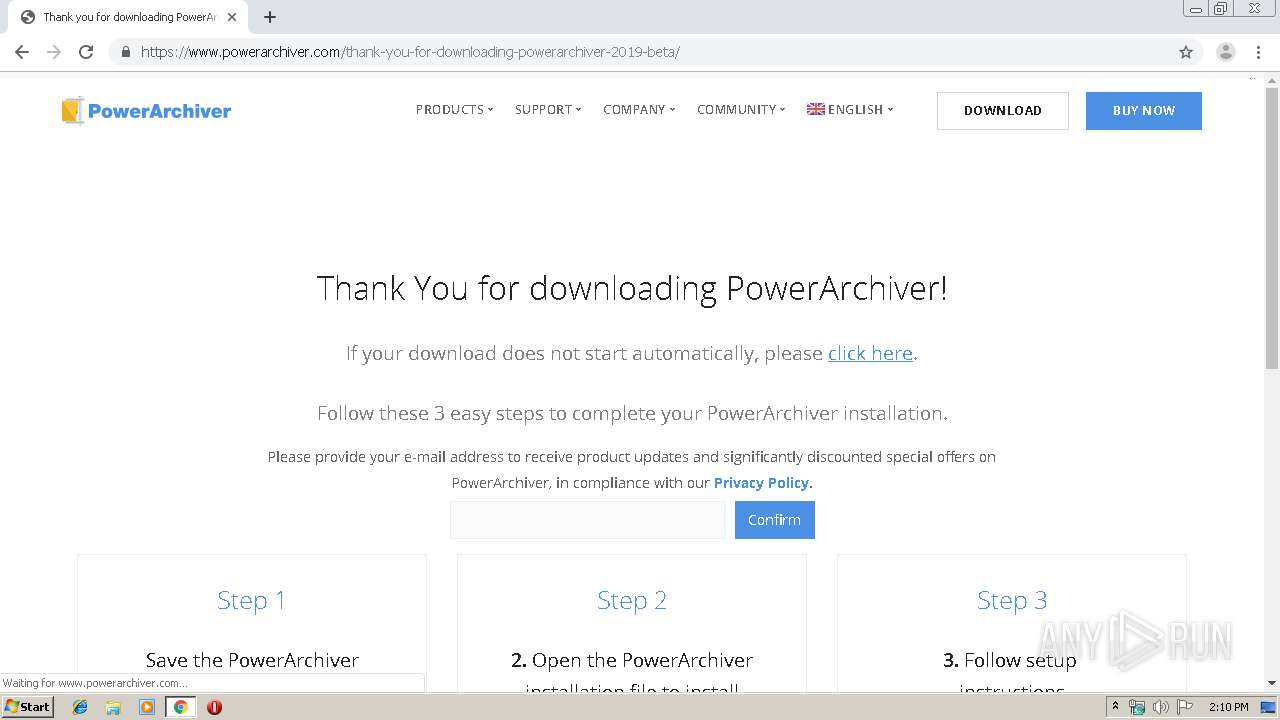
1664 | iexplore.exe | GET | 301 | 138.201.27.202:80 | http://www.powerarchiver.com/l/pa2019un | DE | html | 335 b | unknown |
2496 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2496 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 74.125.8.60:80 | http://r6---sn-5hne6n7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.44.113&mm=28&mn=sn-5hne6n7z&ms=nvh&mt=1563368905&mv=m&mvi=5&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2224 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2496 | chrome.exe | 216.58.210.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 172.217.22.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2496 | chrome.exe | 216.58.207.67:443 | www.google.nl | Google Inc. | US | whitelisted |
2496 | chrome.exe | 172.217.22.46:443 | ogs.google.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 172.217.16.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 216.58.206.14:443 | consent.google.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.nl |
| whitelisted |
ogs.google.com |
| whitelisted |