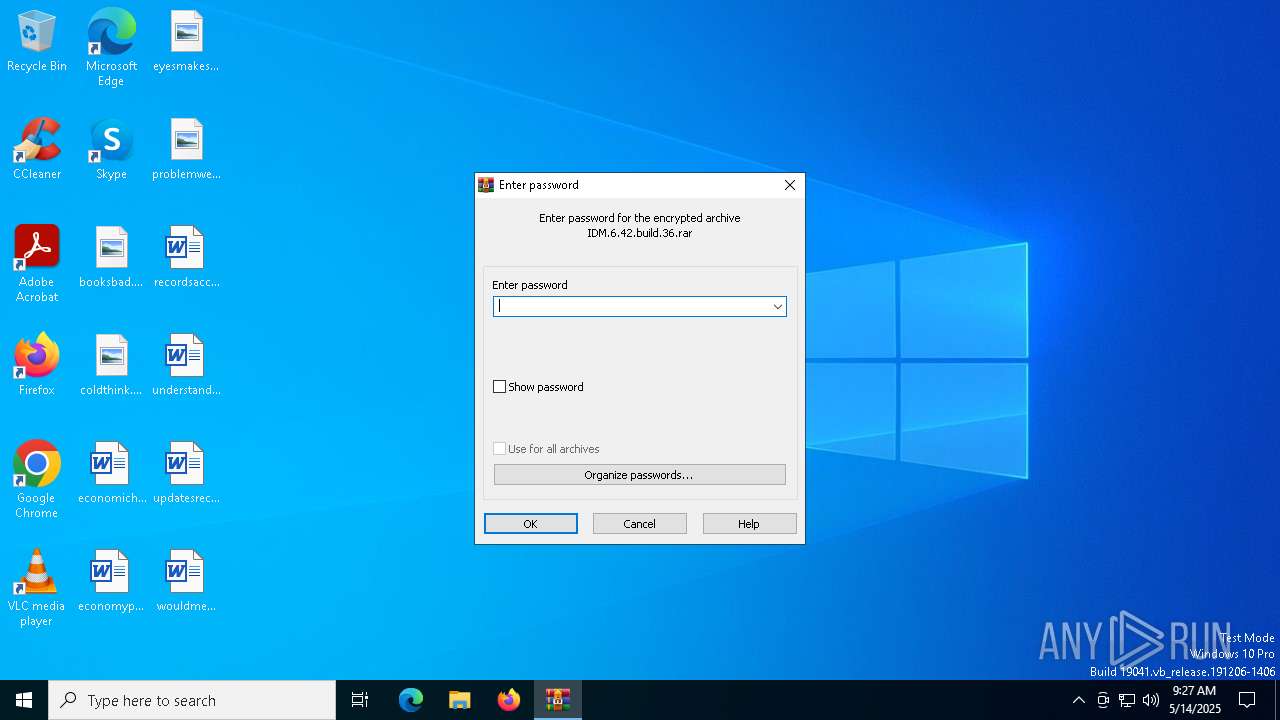
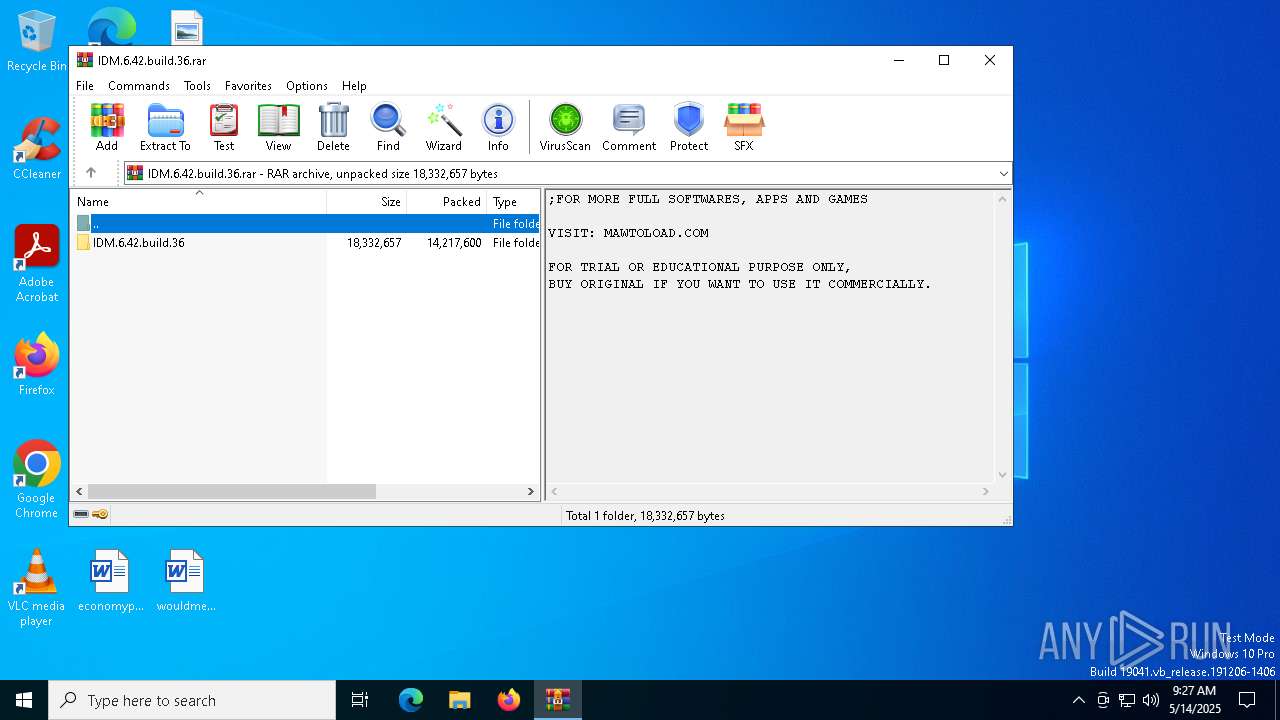
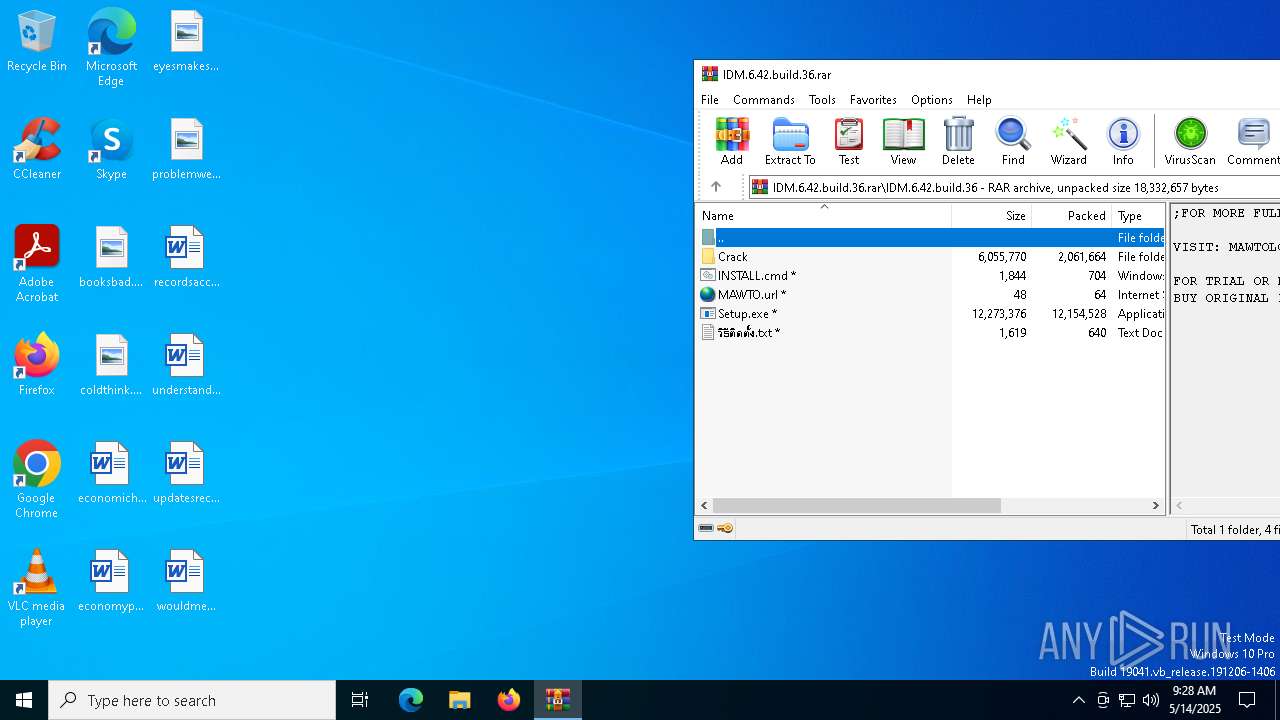
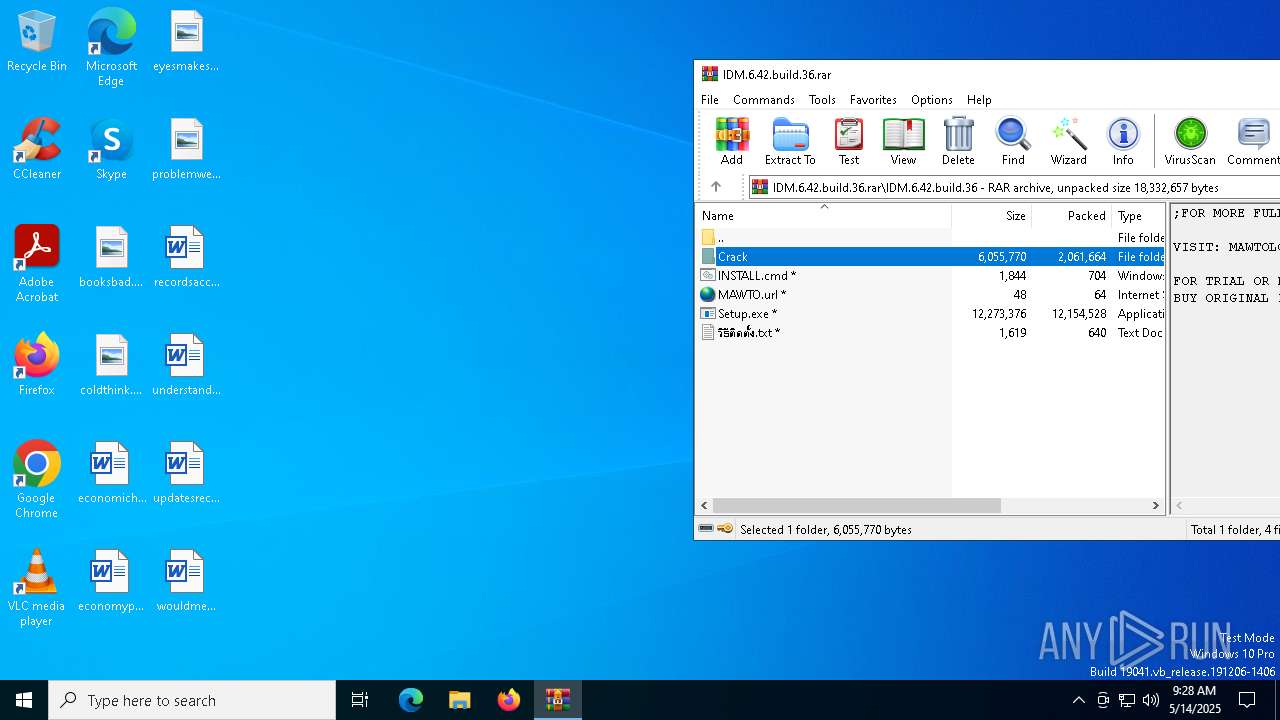
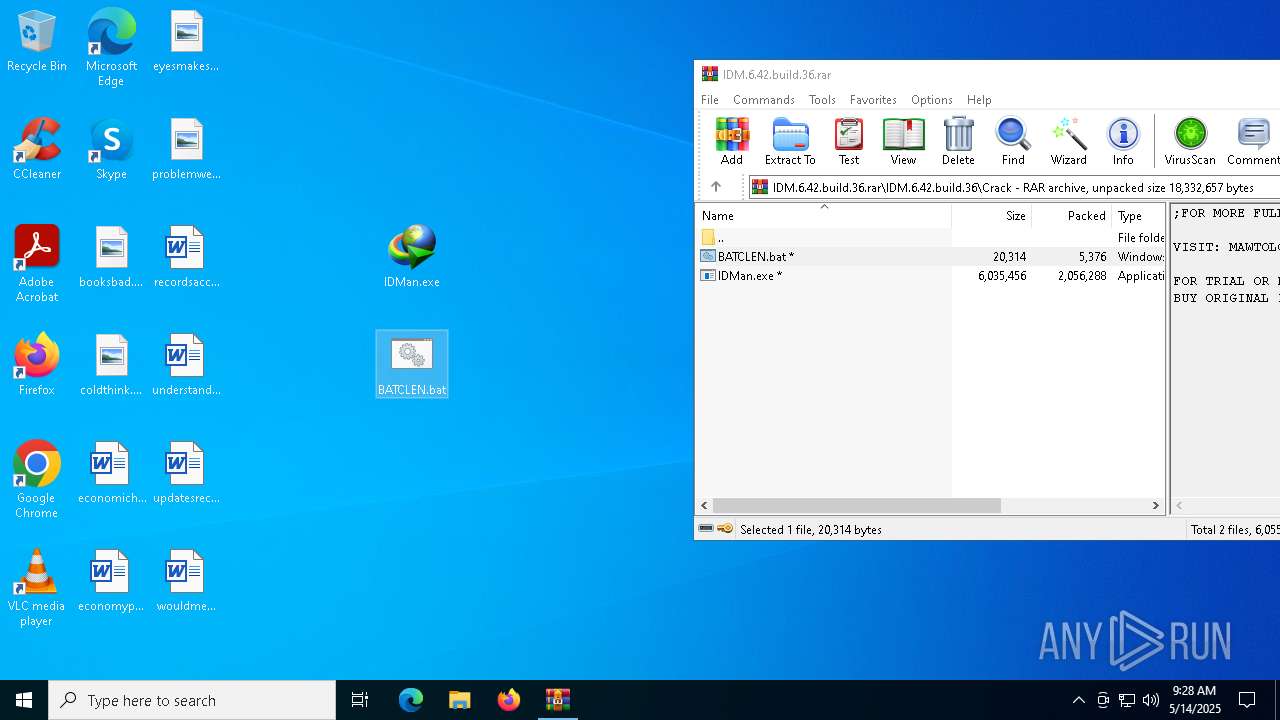
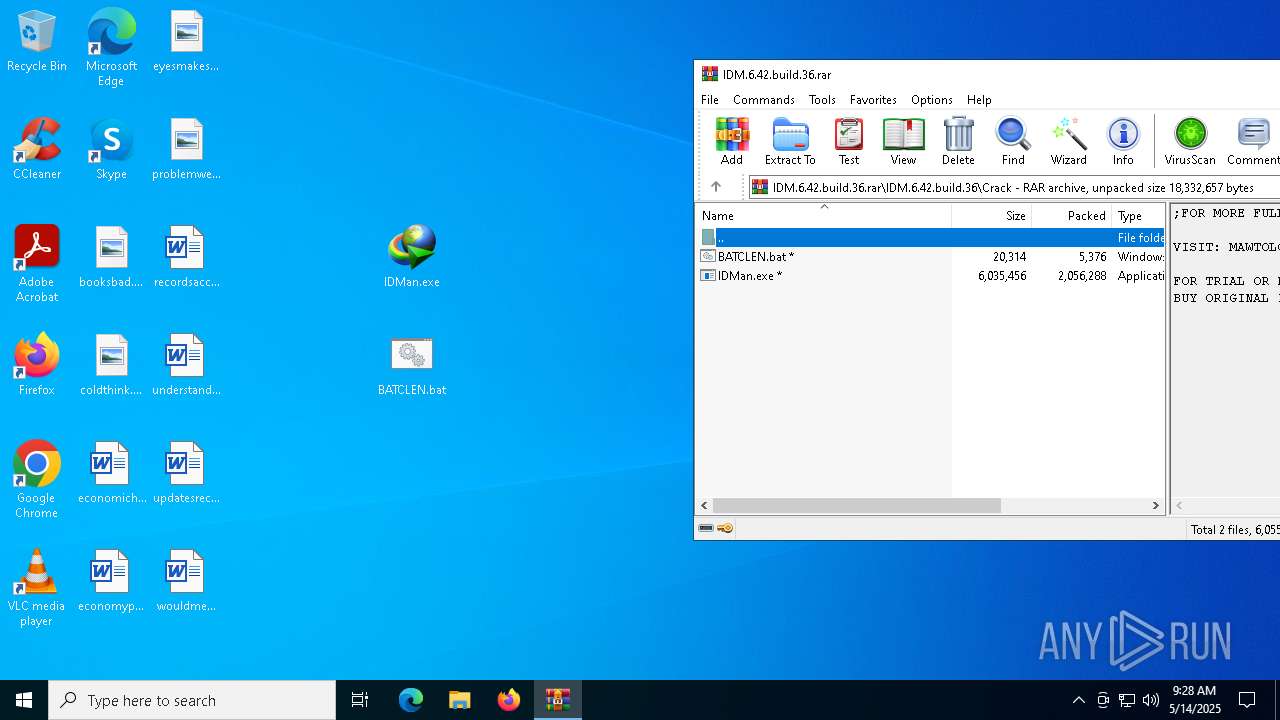
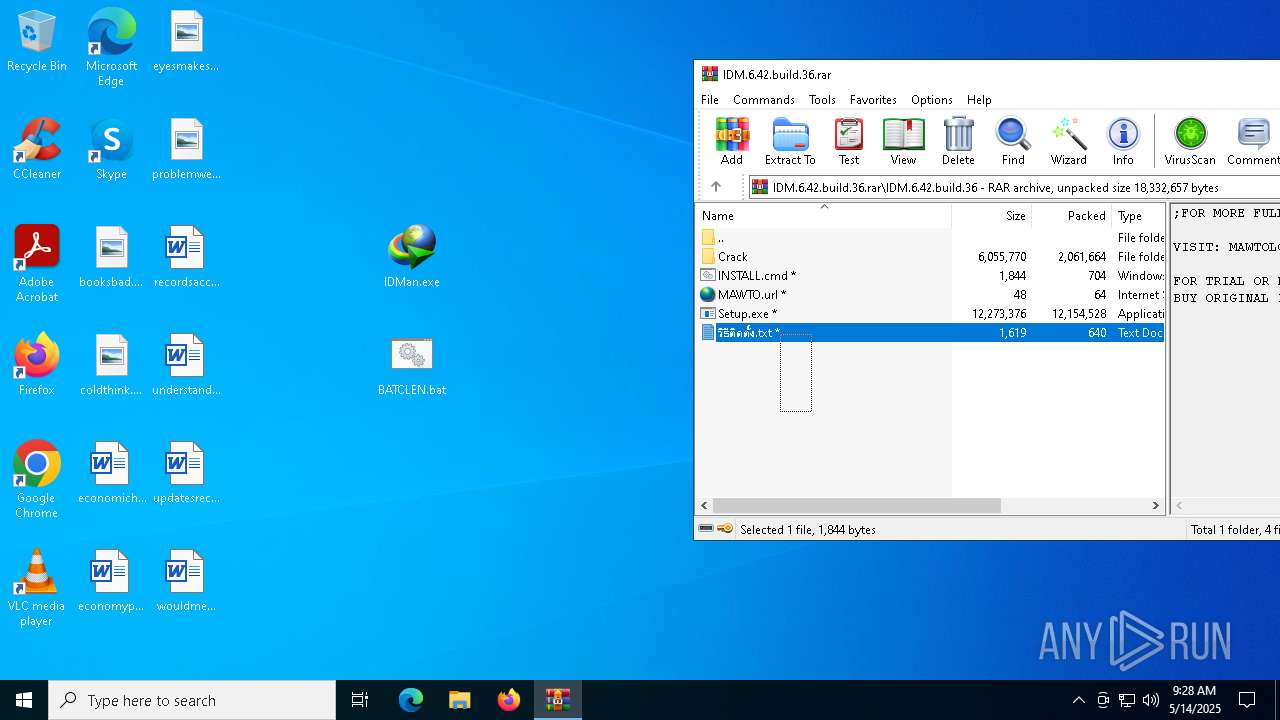
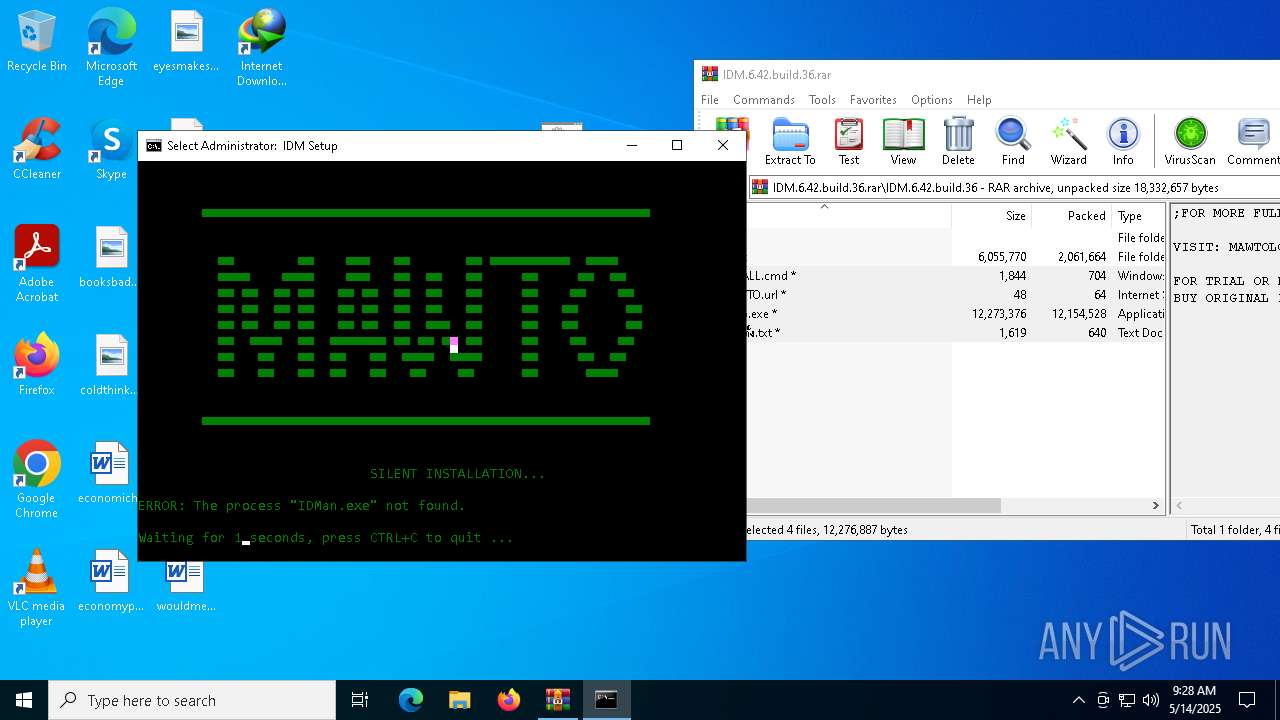
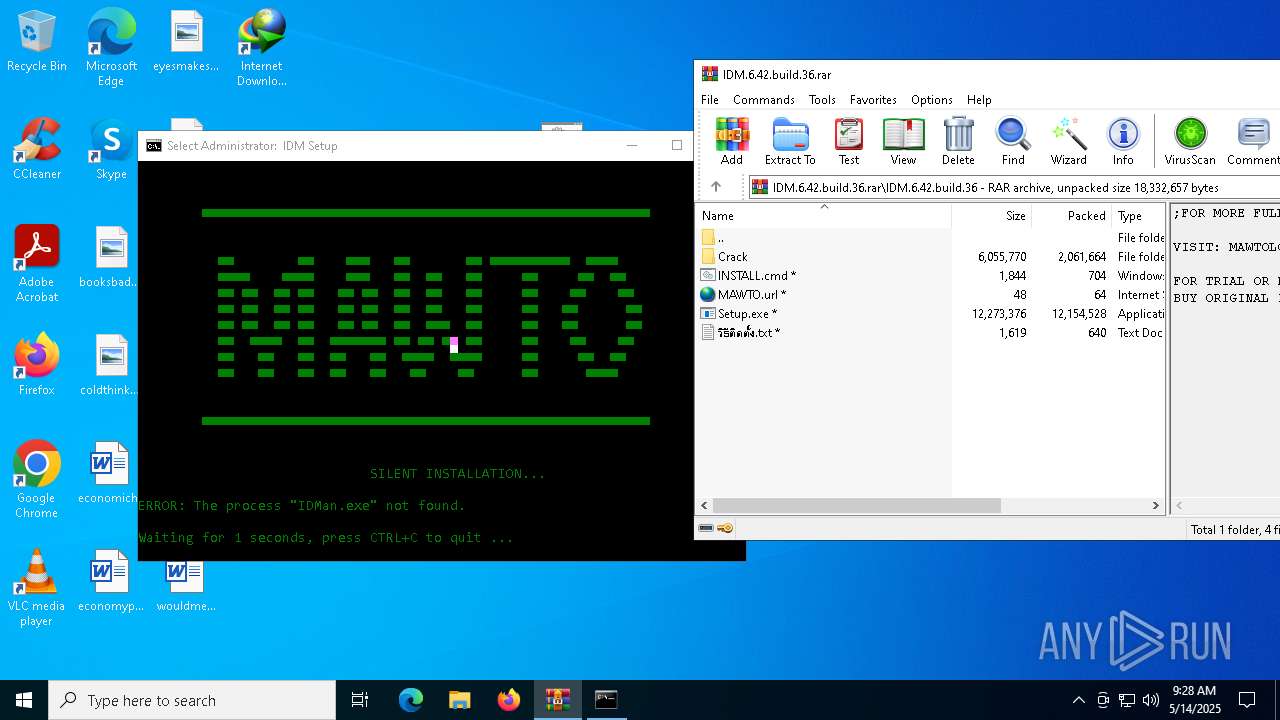
| File name: | IDM.6.42.build.36.rar |
| Full analysis: | https://app.any.run/tasks/33835e83-ecd8-4129-8165-45dfa57f5c65 |
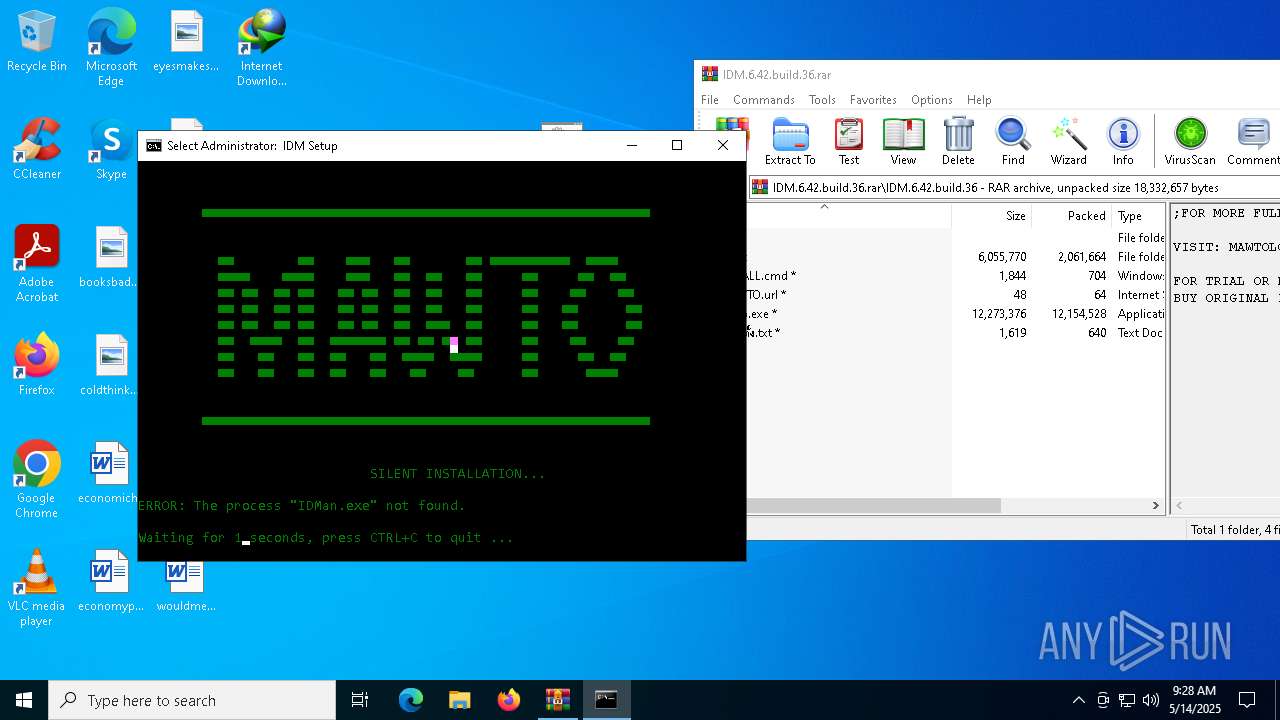
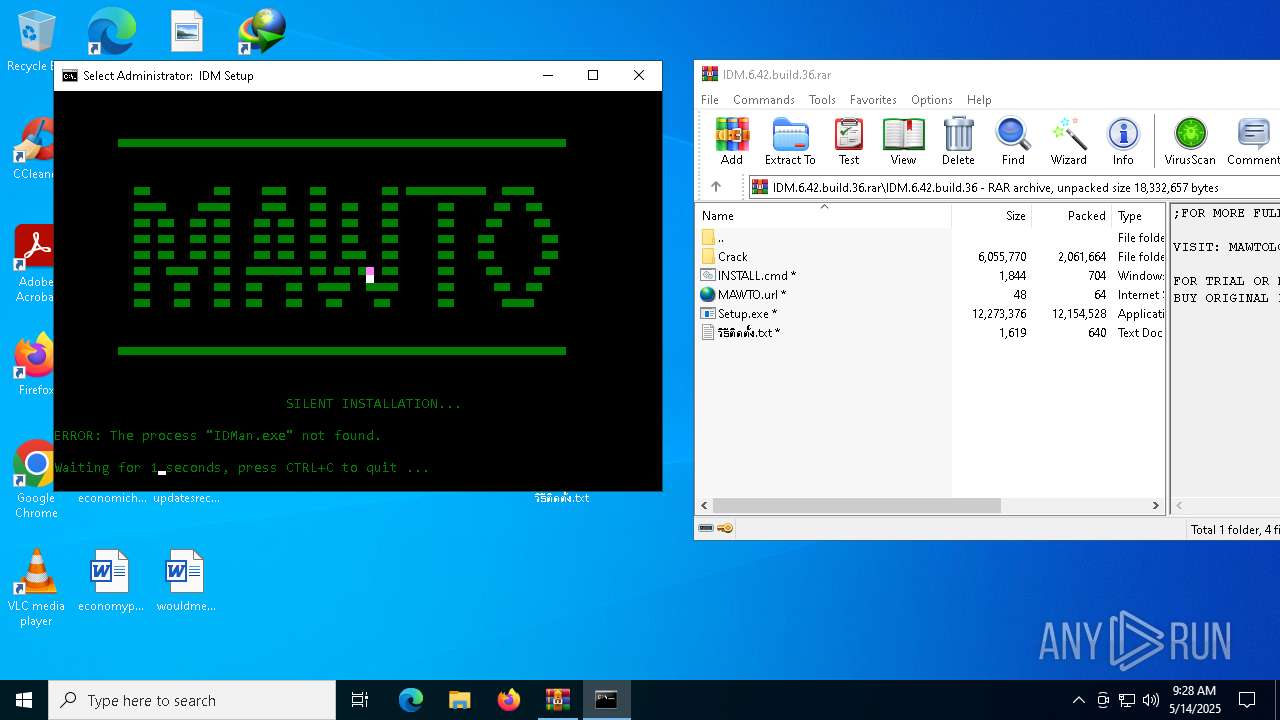
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2025, 09:27:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2CE1A9FCF128027728216063FF056BAB |
| SHA1: | 857A6C1F70C7C7F76099AACE8AA5488BD82FE4D6 |
| SHA256: | C9FE84FD7B1858D31FB89D1F2A44C3AB420CB42BDD6C851913C7D0F4F1A28D90 |
| SSDEEP: | 196608:5E0j8EyCuKLrnUPKDdgZ5RMbdFnj0XWwsp7/:idEDLZOsPnOWj |
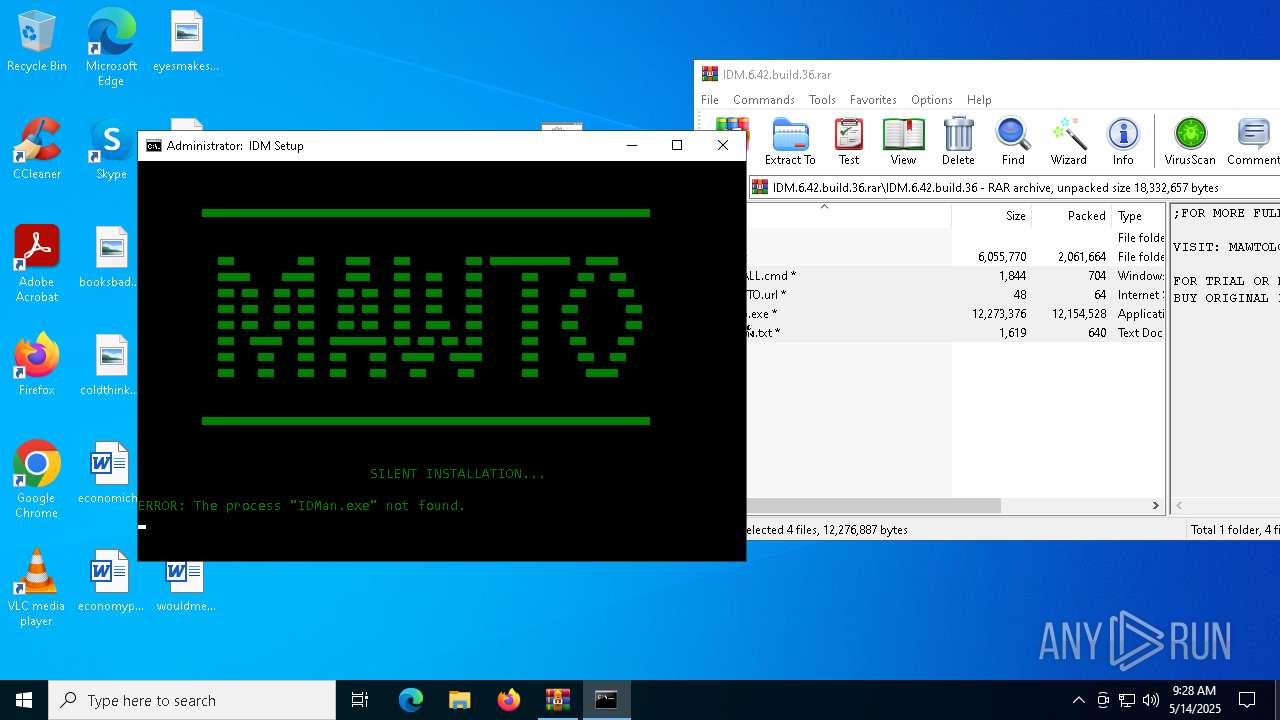
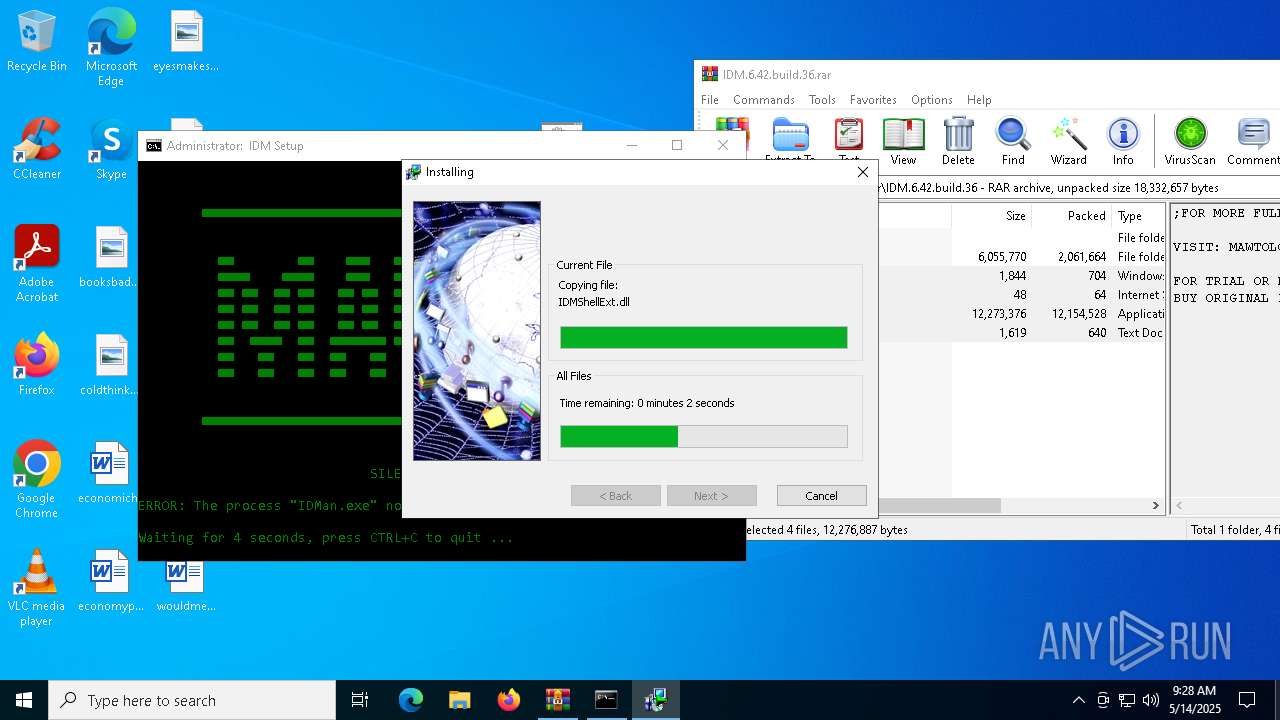
MALICIOUS
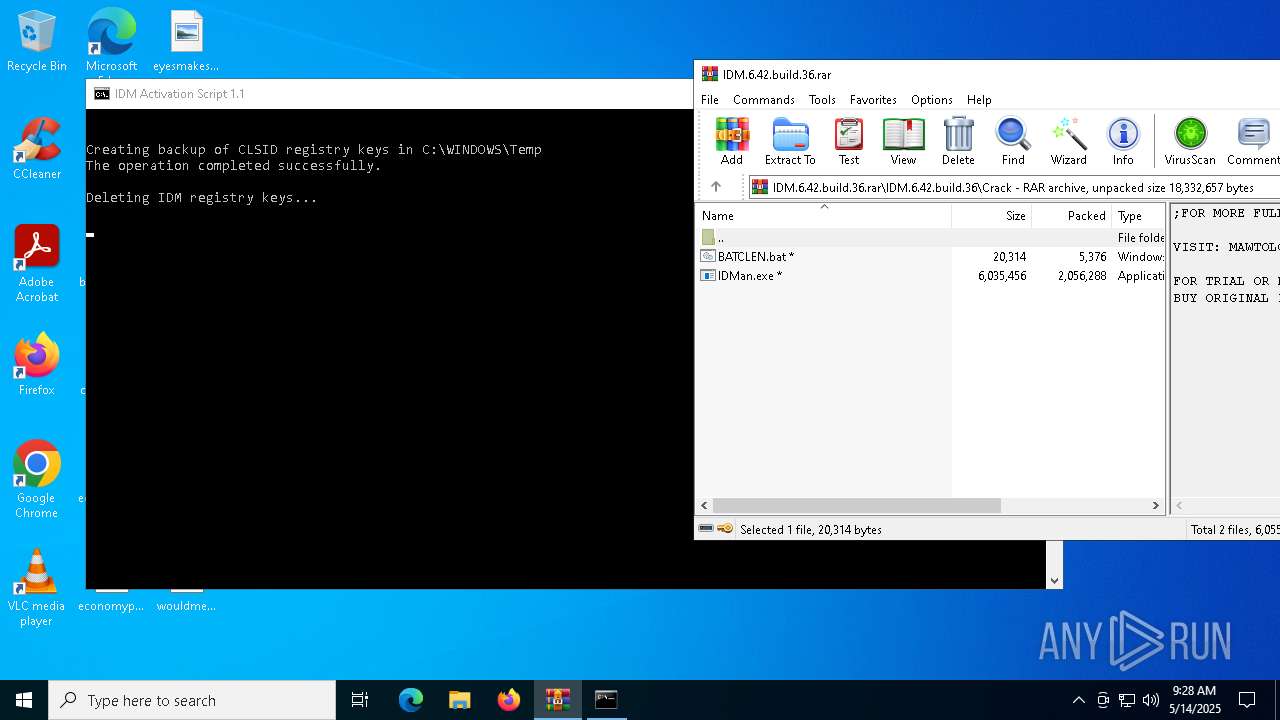
Registers / Runs the DLL via REGSVR32.EXE
- IDM1.tmp (PID: 2236)
- IDMan.exe (PID: 7500)
- Uninstall.exe (PID: 3768)
Starts NET.EXE for service management
- Uninstall.exe (PID: 3768)
- net.exe (PID: 4212)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2140)
- IDM1.tmp (PID: 2236)
- IDMan.exe (PID: 7500)
- Uninstall.exe (PID: 3768)
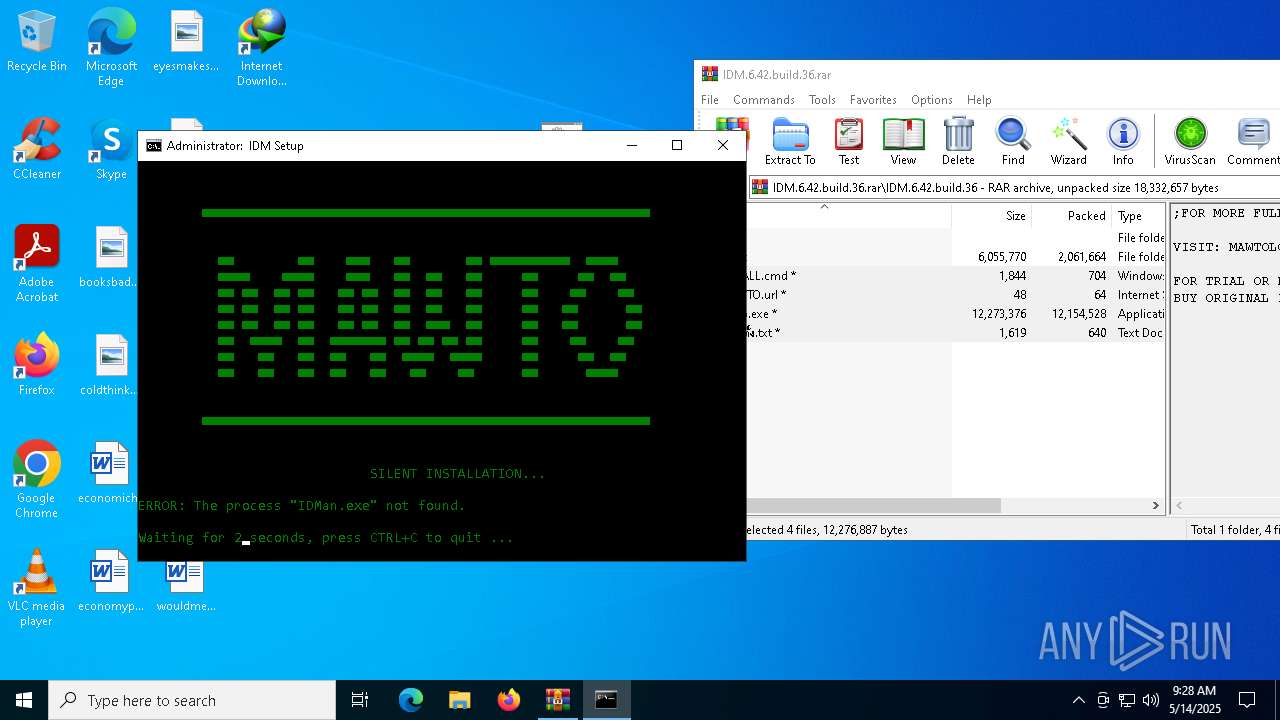
Application launched itself
- cmd.exe (PID: 7884)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 7992)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7884)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 7992)
- wscript.exe (PID: 6876)
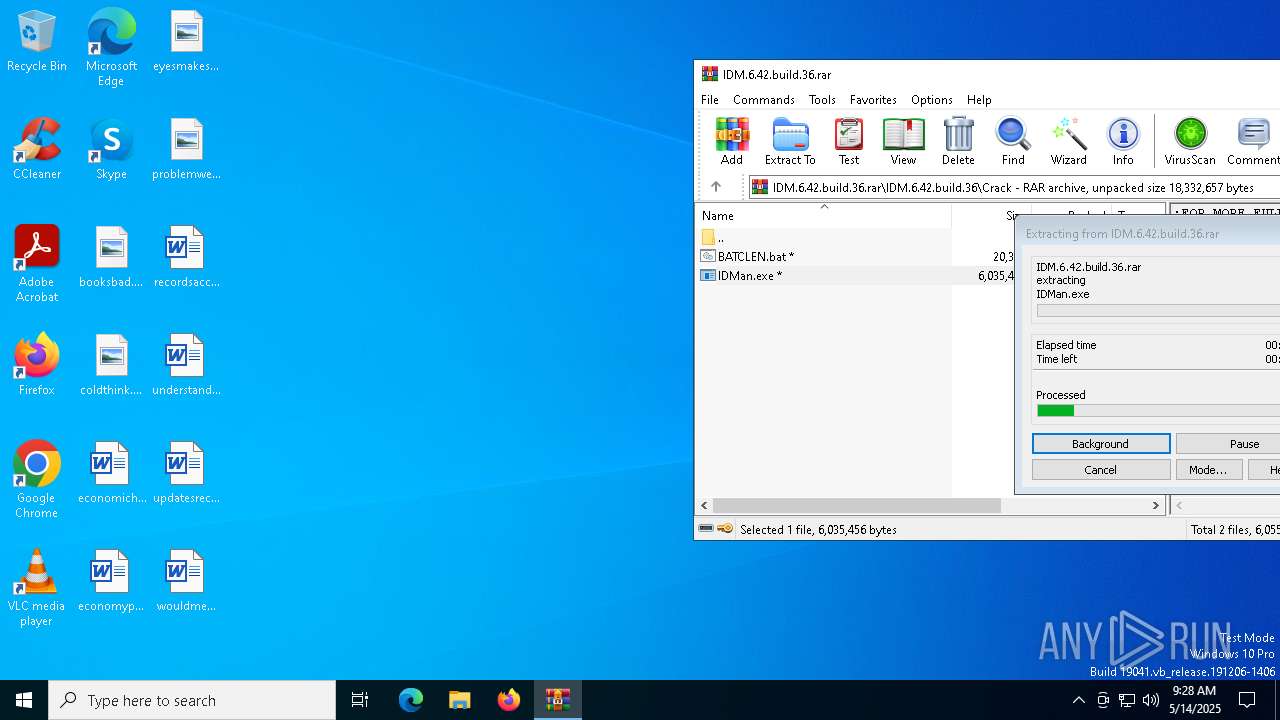
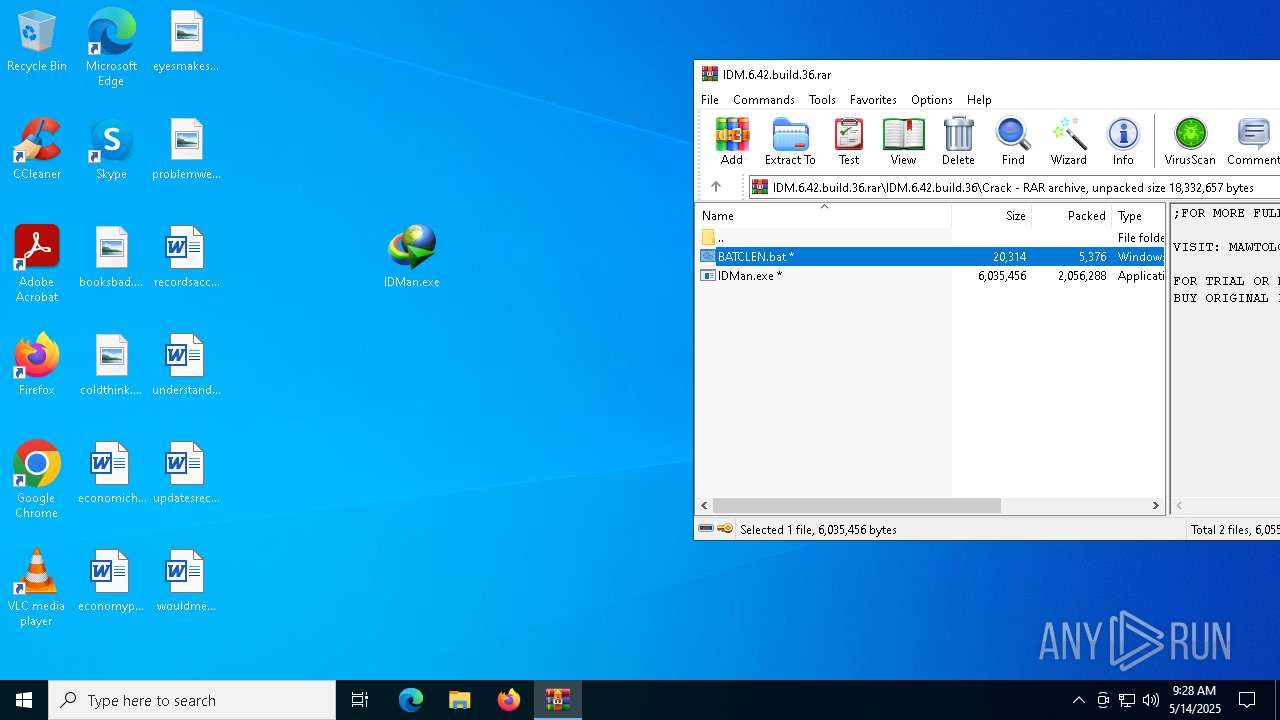
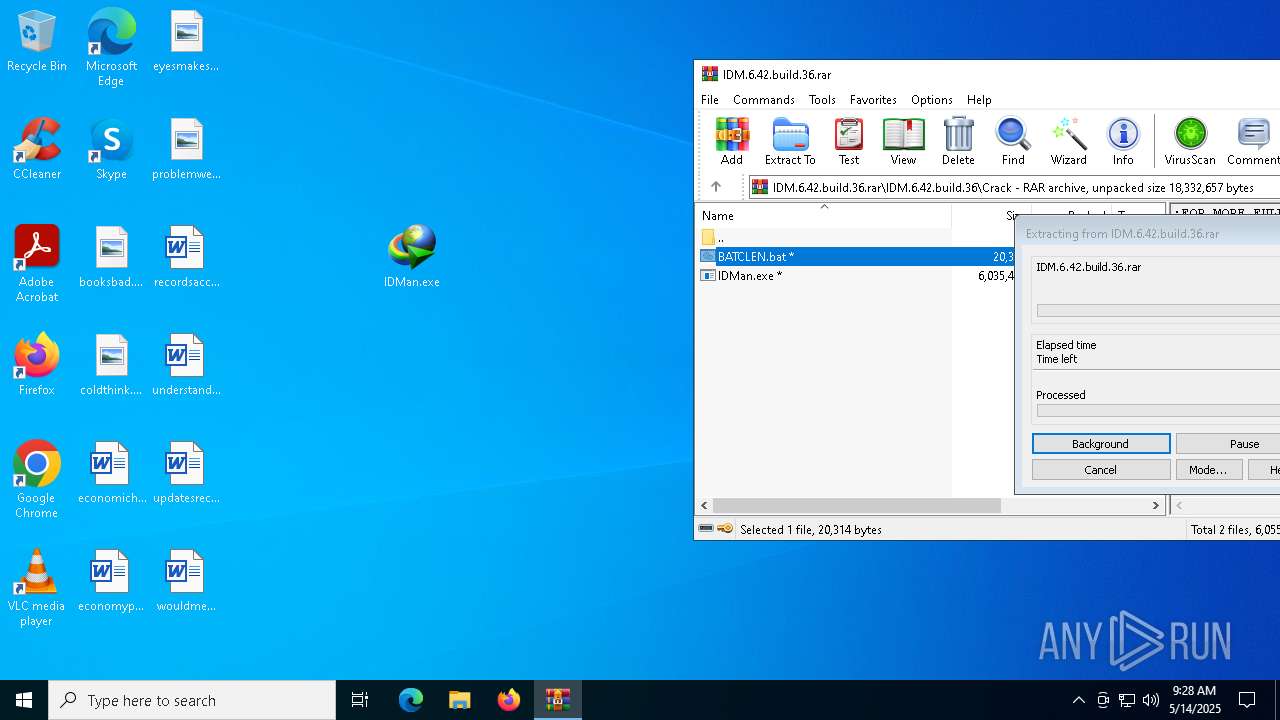
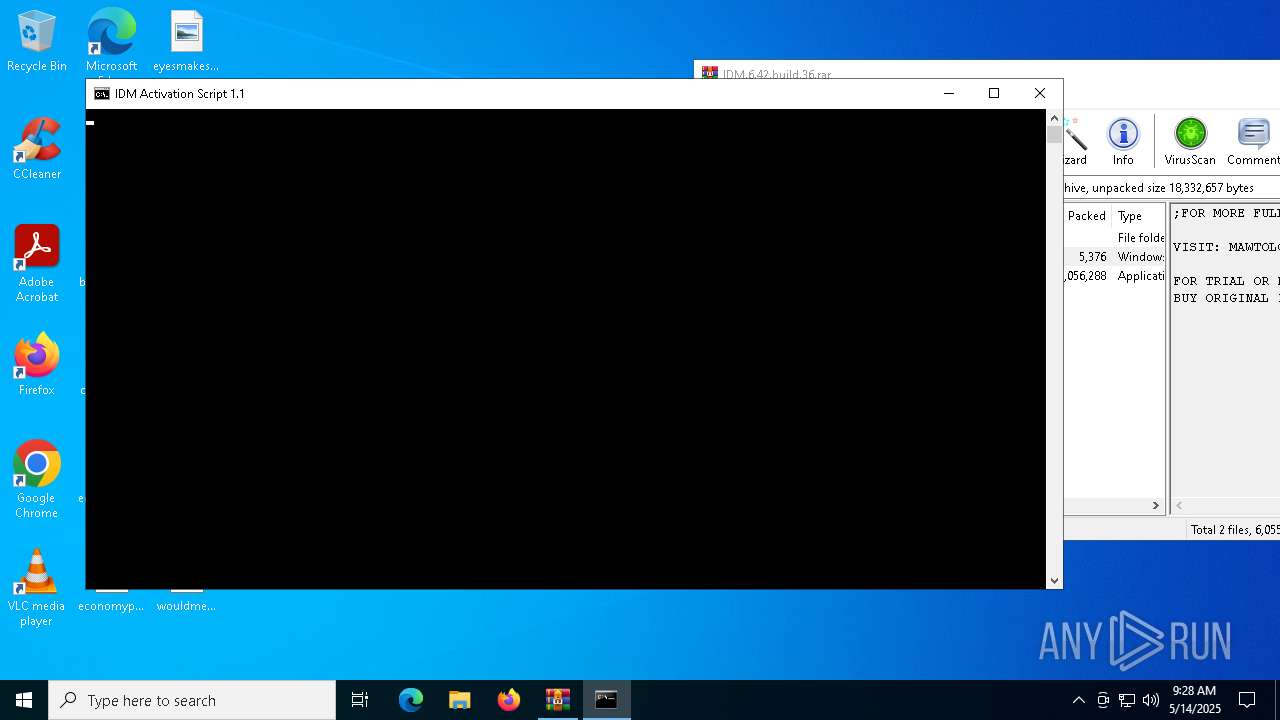
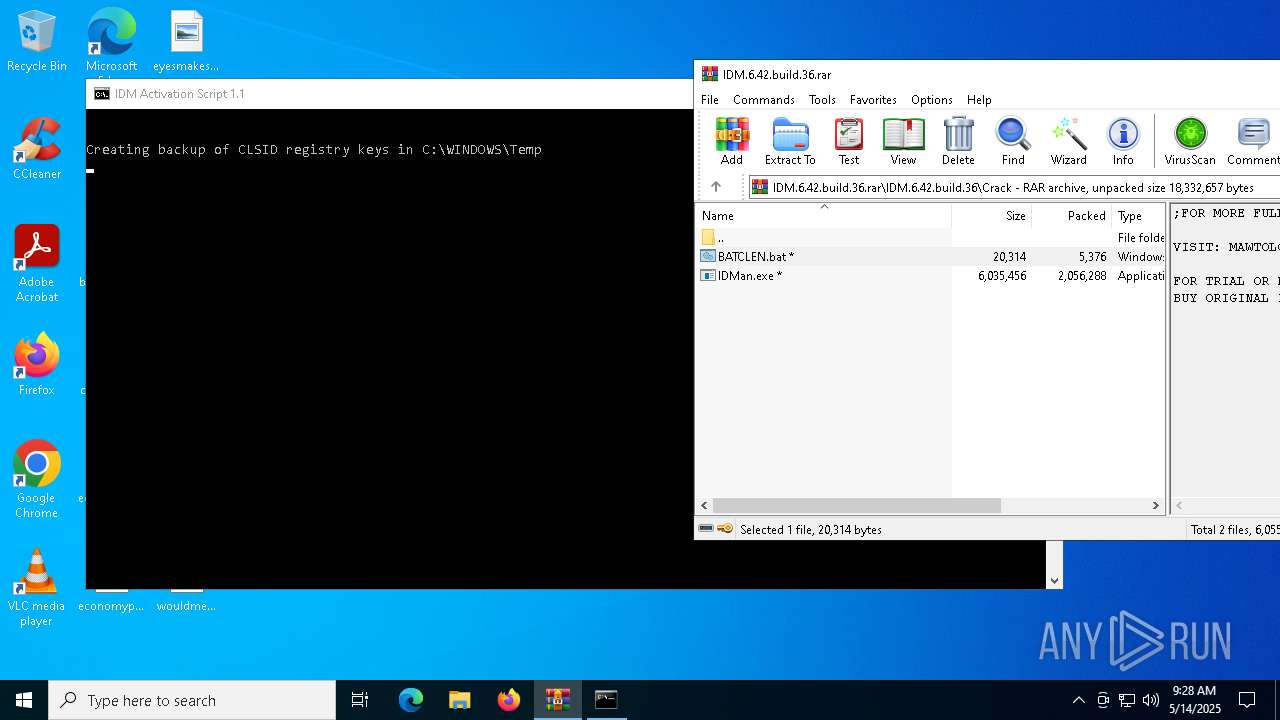
Executing commands from a ".bat" file
- cmd.exe (PID: 7760)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7760)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7760)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 3768)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7760)
Hides command output
- cmd.exe (PID: 2236)
- cmd.exe (PID: 7400)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7760)
- cmd.exe (PID: 7400)
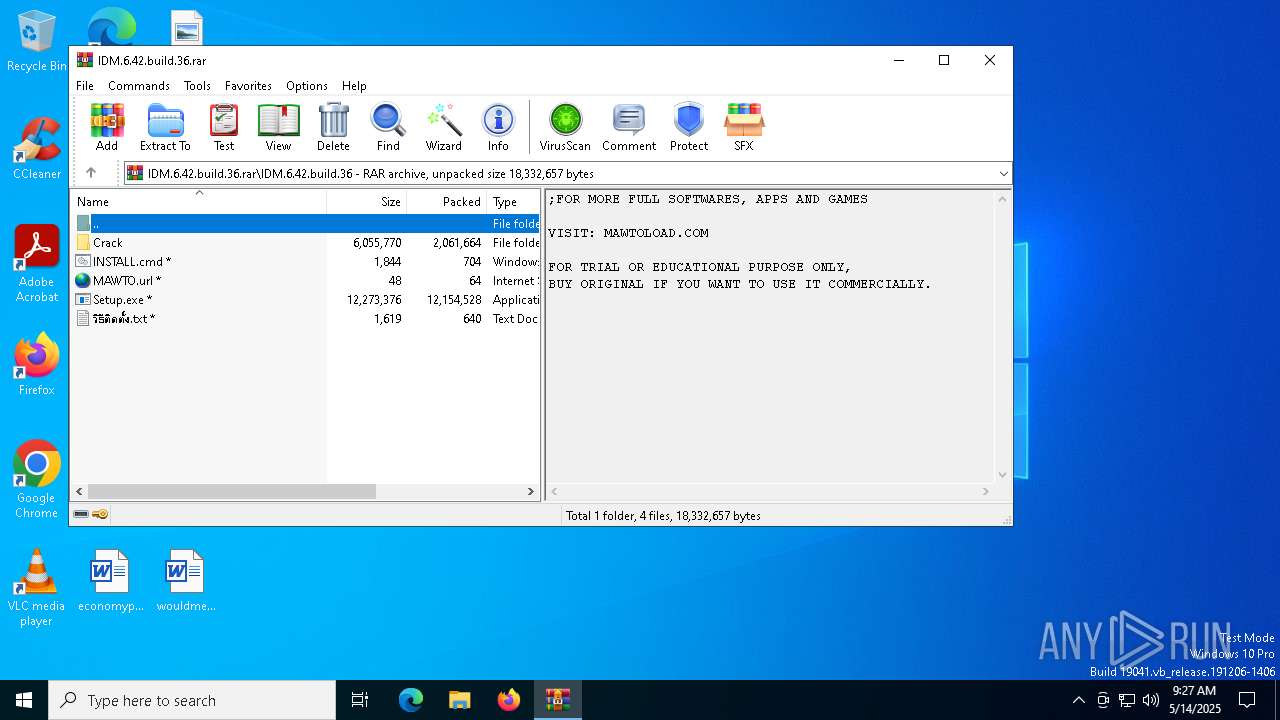
Starts application with an unusual extension
- cmd.exe (PID: 7760)
- Setup.exe (PID: 960)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1020)
Executing commands from ".cmd" file
- cmd.exe (PID: 7992)
- wscript.exe (PID: 6876)
The process executes VB scripts
- cmd.exe (PID: 7992)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6876)
Creates file in the systems drive root
- cmd.exe (PID: 1020)
The process creates files with name similar to system file names
- IDM1.tmp (PID: 2236)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1020)
Creates/Modifies COM task schedule object
- IDM1.tmp (PID: 2236)
- regsvr32.exe (PID: 7420)
- regsvr32.exe (PID: 5972)
- IDMan.exe (PID: 7500)
- regsvr32.exe (PID: 8136)
- regsvr32.exe (PID: 7600)
Creates a software uninstall entry
- IDM1.tmp (PID: 2236)
Executable content was dropped or overwritten
- IDMan.exe (PID: 7500)
- rundll32.exe (PID: 1388)
- drvinst.exe (PID: 2552)
Creates files in the driver directory
- drvinst.exe (PID: 2552)
Drops a system driver (possible attempt to evade defenses)
- rundll32.exe (PID: 1388)
- drvinst.exe (PID: 2552)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 3768)
INFO
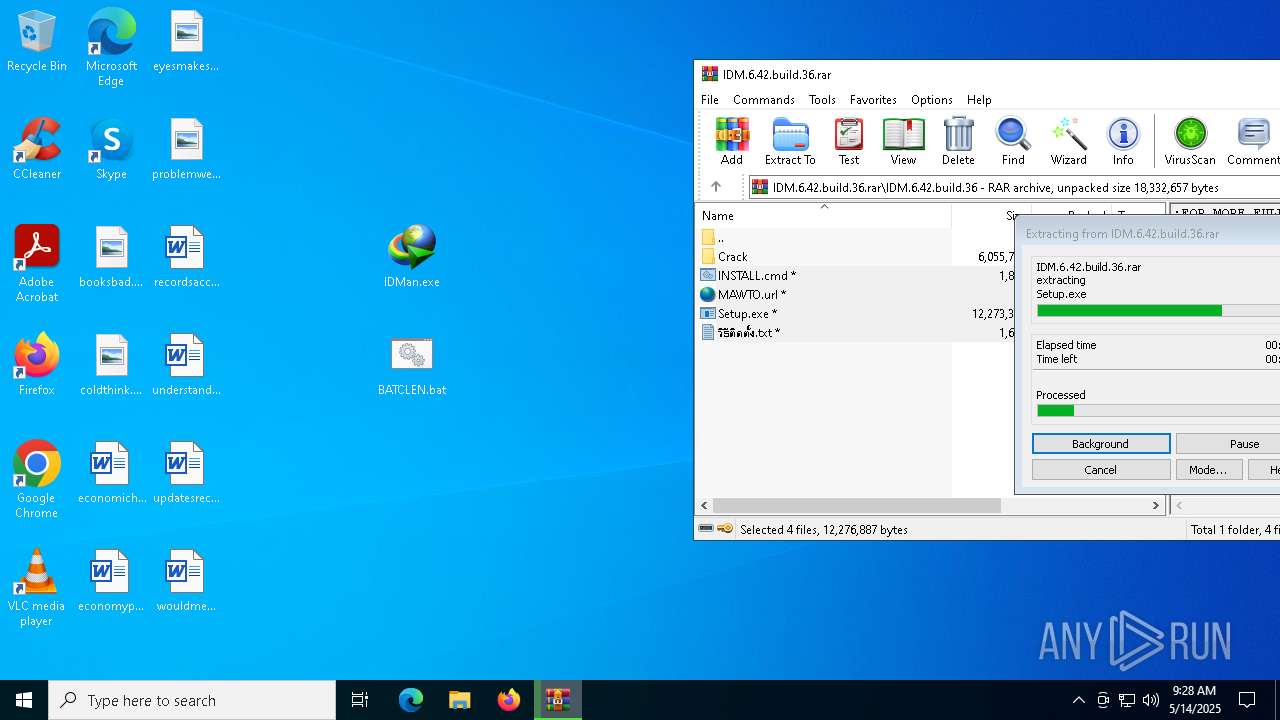
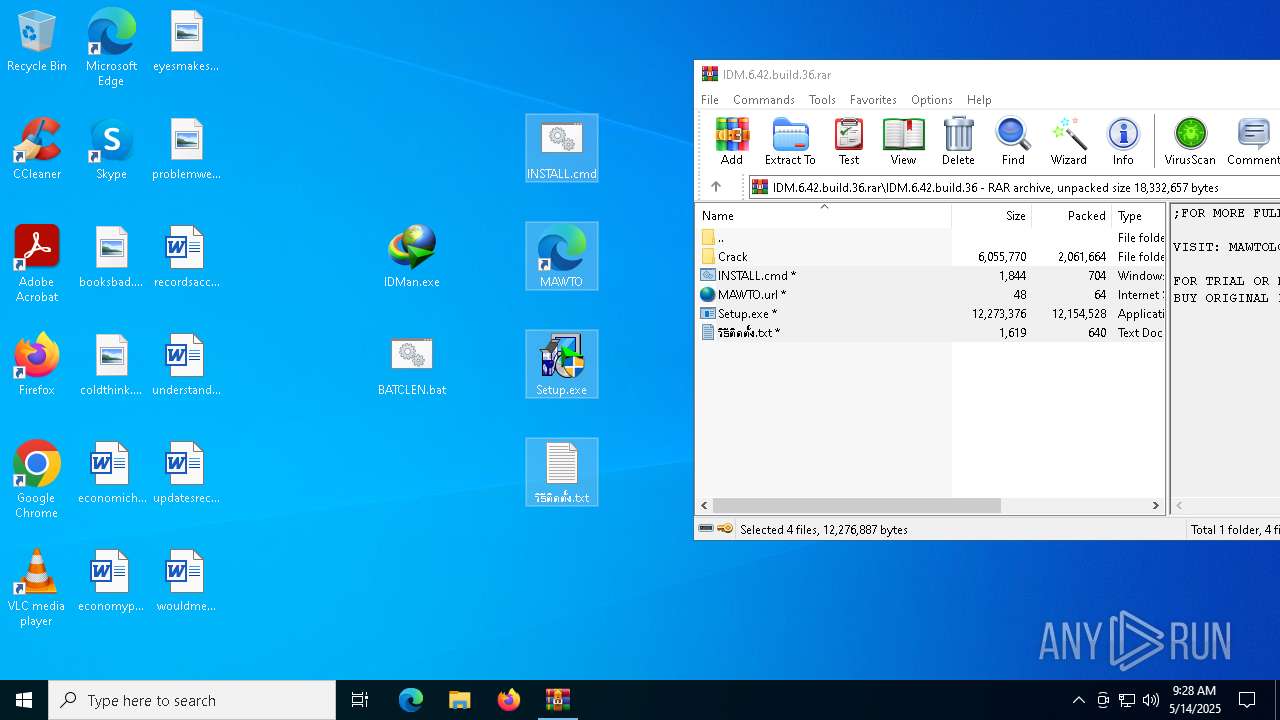
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2140)
Checks operating system version
- cmd.exe (PID: 7760)
Manual execution by a user
- cmd.exe (PID: 7760)
- cmd.exe (PID: 7992)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 2140)
The sample compiled with english language support
- WinRAR.exe (PID: 2140)
- drvinst.exe (PID: 2552)
- IDMan.exe (PID: 7500)
- rundll32.exe (PID: 1388)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 976)
Checks supported languages
- chcp.com (PID: 7716)
- mode.com (PID: 3240)
- Setup.exe (PID: 960)
- idmBroker.exe (PID: 7432)
- IDM1.tmp (PID: 2236)
- IDMan.exe (PID: 7500)
- drvinst.exe (PID: 4268)
- drvinst.exe (PID: 2552)
- Uninstall.exe (PID: 3768)
Create files in a temporary directory
- reg.exe (PID: 7588)
- IDM1.tmp (PID: 2236)
- Setup.exe (PID: 960)
- IDMan.exe (PID: 7500)
- rundll32.exe (PID: 1388)
Changes the display of characters in the console
- cmd.exe (PID: 7760)
Starts MODE.COM to configure console settings
- mode.com (PID: 3240)
INTERNETDOWNLOADMANAGER mutex has been found
- Setup.exe (PID: 960)
- IDM1.tmp (PID: 2236)
- IDMan.exe (PID: 7500)
Creates files in the program directory
- IDM1.tmp (PID: 2236)
- IDMan.exe (PID: 7500)
Reads the computer name
- IDM1.tmp (PID: 2236)
- idmBroker.exe (PID: 7432)
- Setup.exe (PID: 960)
- IDMan.exe (PID: 7500)
- drvinst.exe (PID: 2552)
Creates files or folders in the user directory
- IDM1.tmp (PID: 2236)
- IDMan.exe (PID: 7500)
Process checks computer location settings
- IDM1.tmp (PID: 2236)
- IDMan.exe (PID: 7500)
Reads the machine GUID from the registry
- IDMan.exe (PID: 7500)
- drvinst.exe (PID: 2552)
Disables trace logs
- IDMan.exe (PID: 7500)
Checks proxy server information
- IDMan.exe (PID: 7500)
Reads the software policy settings
- IDMan.exe (PID: 7500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
232
Monitored processes
102
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Users\admin\Desktop\Setup.exe" /skipdlgs | C:\Users\admin\Desktop\Setup.exe | — | cmd.exe | |||||||||||
User: admin Company: Tonec Inc. Integrity Level: HIGH Description: Internet Download Manager installer Exit code: 0 Version: 6, 42, 36, 1 Modules
| |||||||||||||||
| 976 | powershell.exe "$sid = 'S-1-5-21-1693682860-607145093-2874071422-1001'; $HKCUsync = 1; $lockKey = $null; $deleteKey = 1; $f=[io.file]::ReadAllText('C:\Users\admin\Desktop\BATCLEN.bat') -split ':regscan\:.*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | "C:\Windows\System32\cmd.exe" /k cd "C:\Users\admin\Desktop\" && "C:\Users\admin\Desktop\INSTALL.cmd" "" | C:\Windows\System32\cmd.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | reg query "HKCU\Software\DownloadManager" "/v" "LstCheck" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | reg add HKCU\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | reg query "HKCU\Software\DownloadManager" "/v" "Serial" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | reg query "HKCU\Software\DownloadManager" "/v" "LastCheckQU" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | reg delete HKU\S-1-5-21-1693682860-607145093-2874071422-1001\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "C:\WINDOWS\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 177
Read events
38 563
Write events
473
Delete events
141
Modification events
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\IDM.6.42.build.36.rar | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7420) reg.exe | Key: | HKEY_CURRENT_USER\IAS_TEST |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
16
Suspicious files
41
Text files
24
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6324 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iuysoaes.2do.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2140 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2140.20157\IDM.6.42.build.36\Crack\BATCLEN.bat | text | |
MD5:4605F66ACEE4B5907D31D5EEDB0C0AC4 | SHA256:94E01CC28F6CEC7145F8FB4E7A294D025BE2C5903F26CCCBCB8520F40F8943E0 | |||
| 6068 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_f4g5c0iu.liv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6324 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bsydfua5.flu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8168 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jvlbe0um.vye.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7588 | reg.exe | C:\Users\admin\AppData\Local\Temp\REG3209.tmp | text | |
MD5:345823A0BDDB596A43415D67C9880B8A | SHA256:D9CB0467BD3FC677837C380F3A7D5C69291E001B210907FD302B3CE61FF98682 | |||
| 976 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5o23mbzq.o0q.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7988 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:1BB3AE0526A6869650A8AE59EB0C4EED | SHA256:755A0BC29590E4F103B6048468DC85DA22D85171411050023E96C5794CEBD590 | |||
| 7988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_arvr2xdt.dk5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_a0couo3p.fc3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3784 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3784 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |