| File name: | c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8 |
| Full analysis: | https://app.any.run/tasks/ebc48ad7-ed6d-4695-b53a-813853d25a95 |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2025, 15:36:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | F0F300206AF1EED81B7B74357DF437DA |
| SHA1: | 08FE9443A43FFF0C40847B42345183038C159AE1 |
| SHA256: | C9FD60A7A3974913A39A4DCDAD4B4CCAEB93B614741AF2EB7EE0D892130689D8 |
| SSDEEP: | 49152:9TCIrcSO26tw3HSc8/qlvnQqjUD7AxRmCWpp:xQ/qdNUVf |
MALICIOUS
NESHTA mutex has been found
- c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe (PID: 6876)
- FileCoAuth.exe (PID: 6676)
- FileCoAuth.exe (PID: 812)
GENERIC has been found (auto)
- c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe (PID: 6876)
Executing a file with an untrusted certificate
- FileCoAuth.exe (PID: 5512)
- FileCoAuth.exe (PID: 7196)
- FileCoAuth.exe (PID: 8032)
SUSPICIOUS
Reads security settings of Internet Explorer
- c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe (PID: 6876)
- FileCoAuth.exe (PID: 6676)
- FileCoAuth.exe (PID: 812)
Executable content was dropped or overwritten
- c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe (PID: 6876)
- FileCoAuth.exe (PID: 6676)
- FileCoAuth.exe (PID: 812)
- FileCoAuth.exe (PID: 7636)
Mutex name with non-standard characters
- c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe (PID: 6876)
- FileCoAuth.exe (PID: 812)
- FileCoAuth.exe (PID: 6676)
There is functionality for taking screenshot (YARA)
- c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe (PID: 6876)
Starts a Microsoft application from unusual location
- FileCoAuth.exe (PID: 5512)
- FileCoAuth.exe (PID: 7196)
- FileCoAuth.exe (PID: 8032)
Process drops legitimate windows executable
- FileCoAuth.exe (PID: 6676)
- FileCoAuth.exe (PID: 812)
- FileCoAuth.exe (PID: 7636)
INFO
Checks supported languages
- c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe (PID: 6876)
- c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe (PID: 6048)
- FileCoAuth.exe (PID: 5512)
- FileCoAuth.exe (PID: 7196)
Create files in a temporary directory
- c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe (PID: 6876)
- FileCoAuth.exe (PID: 5512)
- FileCoAuth.exe (PID: 7196)
Reads the computer name
- c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe (PID: 6876)
- FileCoAuth.exe (PID: 5512)
- FileCoAuth.exe (PID: 7196)
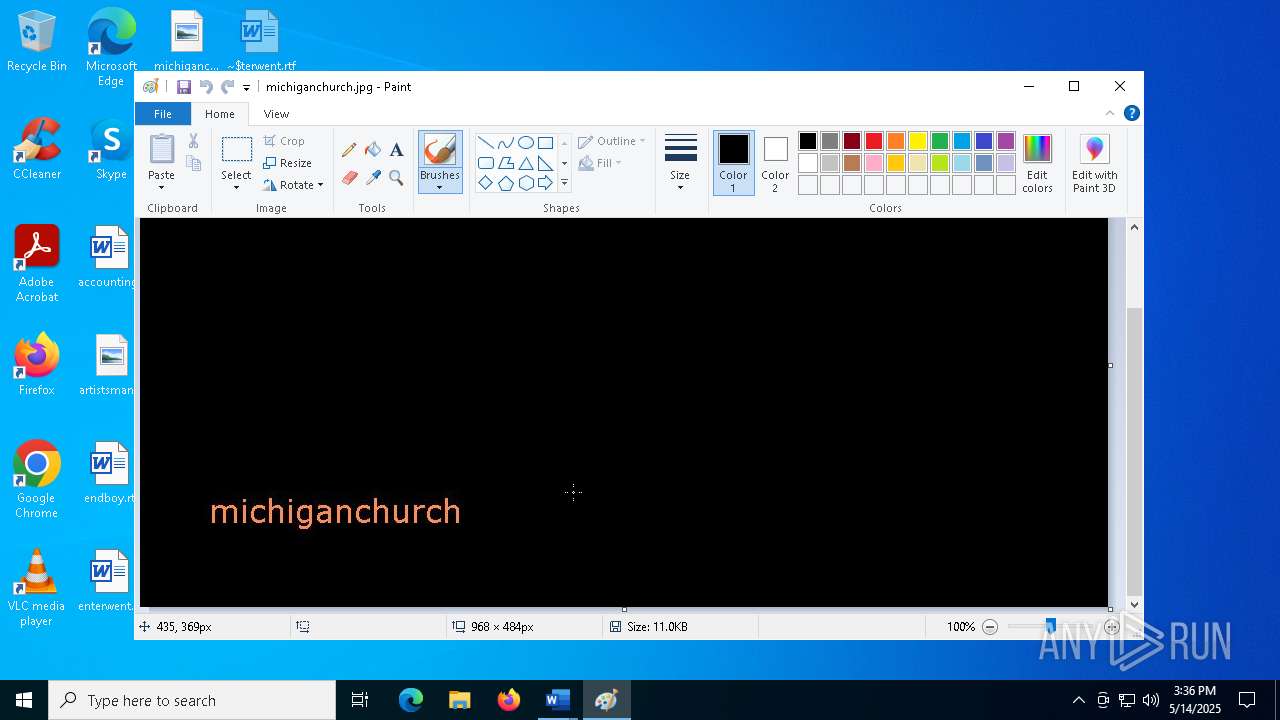
Manual execution by a user
- WINWORD.EXE (PID: 5116)
- mspaint.exe (PID: 2772)
- msedge.exe (PID: 7388)
- WINWORD.EXE (PID: 7972)
- mspaint.exe (PID: 8296)
Process checks computer location settings
- c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe (PID: 6876)
- FileCoAuth.exe (PID: 6676)
The sample compiled with english language support
- FileCoAuth.exe (PID: 6676)
- FileCoAuth.exe (PID: 812)
- FileCoAuth.exe (PID: 7636)
Creates files or folders in the user directory
- FileCoAuth.exe (PID: 5512)
- FileCoAuth.exe (PID: 7196)
Reads the machine GUID from the registry
- FileCoAuth.exe (PID: 5512)
- FileCoAuth.exe (PID: 7196)
Application launched itself
- msedge.exe (PID: 8144)
- msedge.exe (PID: 7388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 6 (89.3) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (4.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.2) |
| .exe | | | Win32 Executable (generic) (1.5) |
| .exe | | | Win16/32 Executable Delphi generic (0.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 29696 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x80e4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
177
Monitored processes
45
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 812 | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe -Embedding | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2772 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Desktop\officepool.png" | C:\Windows\System32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4428 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5020 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5560 --field-trial-handle=2376,i,13660586124210058661,3007214438044034156,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5116 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\otherliterature.rtf" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 5304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3228 --field-trial-handle=2376,i,13660586124210058661,3007214438044034156,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5512 | "C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe" -Embedding | C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe | — | FileCoAuth.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 6004 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2ac,0x7ffc72a15fd8,0x7ffc72a15fe4,0x7ffc72a15ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6048 | "C:\Users\admin\AppData\Local\Temp\3582-490\c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe | — | c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
Total events
22 516
Read events
22 062
Write events
428
Delete events
26
Modification events
| (PID) Process: | (5116) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (5116) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\5116 |
| Operation: | write | Name: | 0 |
Value: 0B0E10F87ECD62CAE8204788F916DC6AC2FEBF230046E7E09FFADE9CF1ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511FC27D2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (5116) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (5116) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (5116) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (5116) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (5116) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (5116) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (5116) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (5116) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
79
Suspicious files
667
Text files
118
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5116 | WINWORD.EXE | C:\Users\admin\Desktop\~$herliterature.rtf | binary | |
MD5:28E3C6B0EAB17B67AC2FE605EEA24E94 | SHA256:795FB293EBC2435B5EE8F32602D12E7985A2373A5D484AB087B1F2FDEBC55F5E | |||
| 6876 | c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncHelper.exe | executable | |
MD5:1C0BE16E6ED8F5B6F0910650A25F4FA7 | SHA256:3028F6A6A7A10DC5D63F256FEEB8275F3818BF3371EAF8B20A2D0BF2FCD5F4A9 | |||
| 6876 | c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncConfig.exe | executable | |
MD5:0C5EC1AE9A301408AF26032B445FBB08 | SHA256:3A8010F1E4E028782093877D969EB127B80AE48B7215A8D3F91E8AB9C165AC7A | |||
| 5116 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\334E5CF0-A26F-4B77-908E-C7DE937F2CC1 | xml | |
MD5:8326903E23F7978A129D61BE3E6DE960 | SHA256:8F2EE1D46BCC4ECCFC027A2CE2858573A4302DA58CF013B726349BA72C4D2DCC | |||
| 6876 | c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\OneDriveUpdaterService.exe | executable | |
MD5:E73AC057B2CFEF016B8199389F0DF590 | SHA256:20ABA9D6001E5CDC287CD5BD452D0F2D05980D83F851D2B309BF49E9D9A8AC4C | |||
| 6876 | c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\OneDriveStandaloneUpdater.exe | executable | |
MD5:A747FA4161FE3C00C3FBB4BF391D4D4E | SHA256:B7BA59428AF7AE08C5BF927B57E326D5259E6ED31BD4237AA6A44378177364C1 | |||
| 6876 | c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\OneDrive.exe | executable | |
MD5:178B773B3FB050FCE26E40A9E8C2EE9A | SHA256:1E03573733F25B44004049A535E7E79366FD86FE953F6DFEDAAD05513B46A6C5 | |||
| 6876 | c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | executable | |
MD5:13C2D5BF03C4A2B28E930F990CCC32DB | SHA256:12D24D0BC0E7CDC902E3540A3C6F7B755094F011A8EAD49A47A00563710B8F80 | |||
| 6876 | c9fd60a7a3974913a39a4dcdad4b4ccaeb93b614741af2eb7ee0d892130689d8.exe | C:\ProgramData\Adobe\ARM\S\388\AdobeARMHelper.exe | executable | |
MD5:85A67D34298E33D2D5A9EC789B6AB594 | SHA256:1DEE143B4F88F2375B85C6271A58E2E78FED081BEAE4090678CB2DD7A37FB2D4 | |||
| 5116 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:AAFD047657B7584A0B081EA093266083 | SHA256:901C4E9709A99B7593EC88B900E3739D0FBCDAAB79878F082EC635385591DF18 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
130
DNS requests
100
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.151:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5116 | WINWORD.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
7264 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7264 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5116 | WINWORD.EXE | GET | 200 | 23.48.23.183:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
5116 | WINWORD.EXE | GET | 200 | 23.48.23.183:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.183:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | — | — | whitelisted |
5116 | WINWORD.EXE | GET | 200 | 23.48.23.183:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.151:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5116 | WINWORD.EXE | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
5116 | WINWORD.EXE | 23.50.131.87:443 | omex.cdn.office.net | Akamai International B.V. | DE | whitelisted |
5116 | WINWORD.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5116 | WINWORD.EXE | 52.109.68.129:443 | roaming.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8184 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
8184 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |