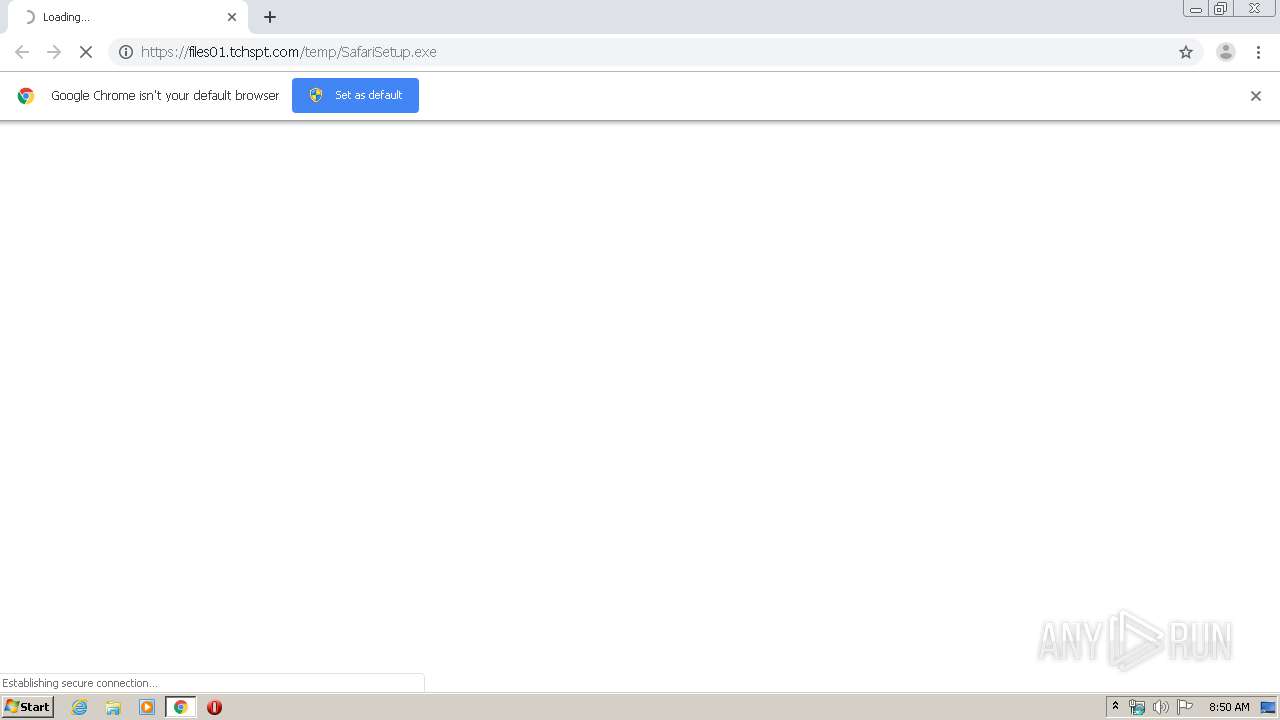
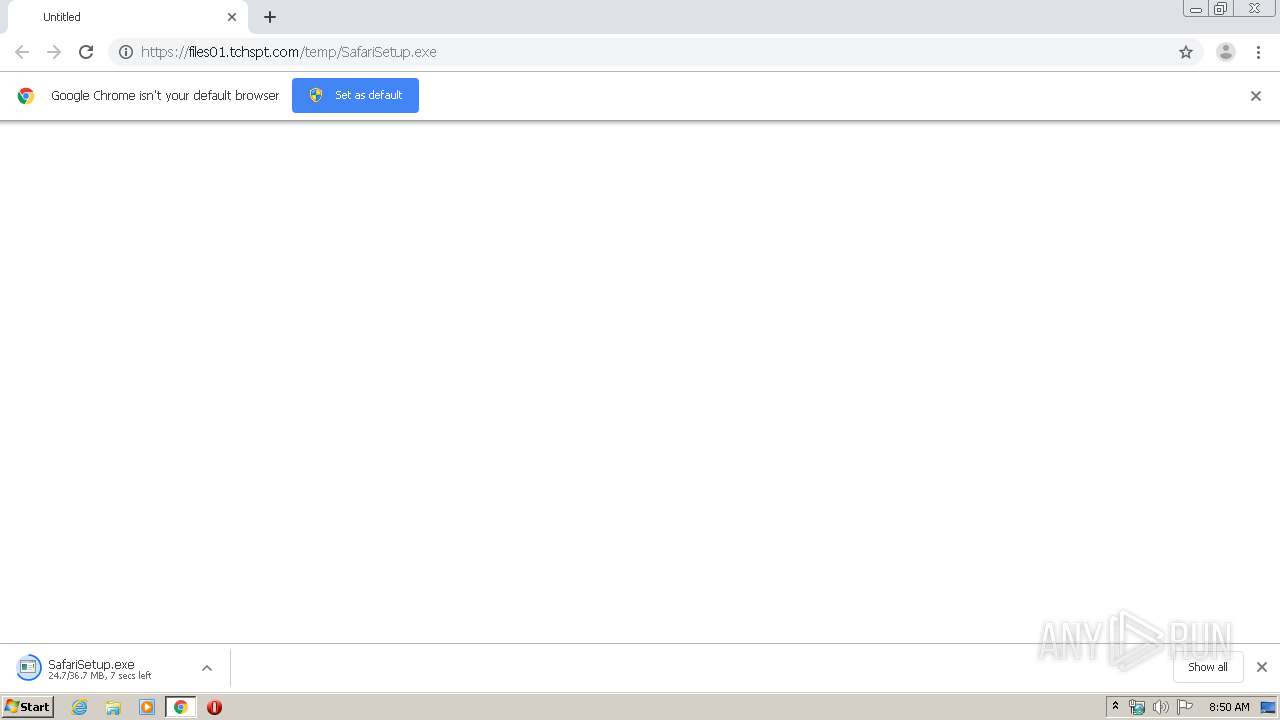
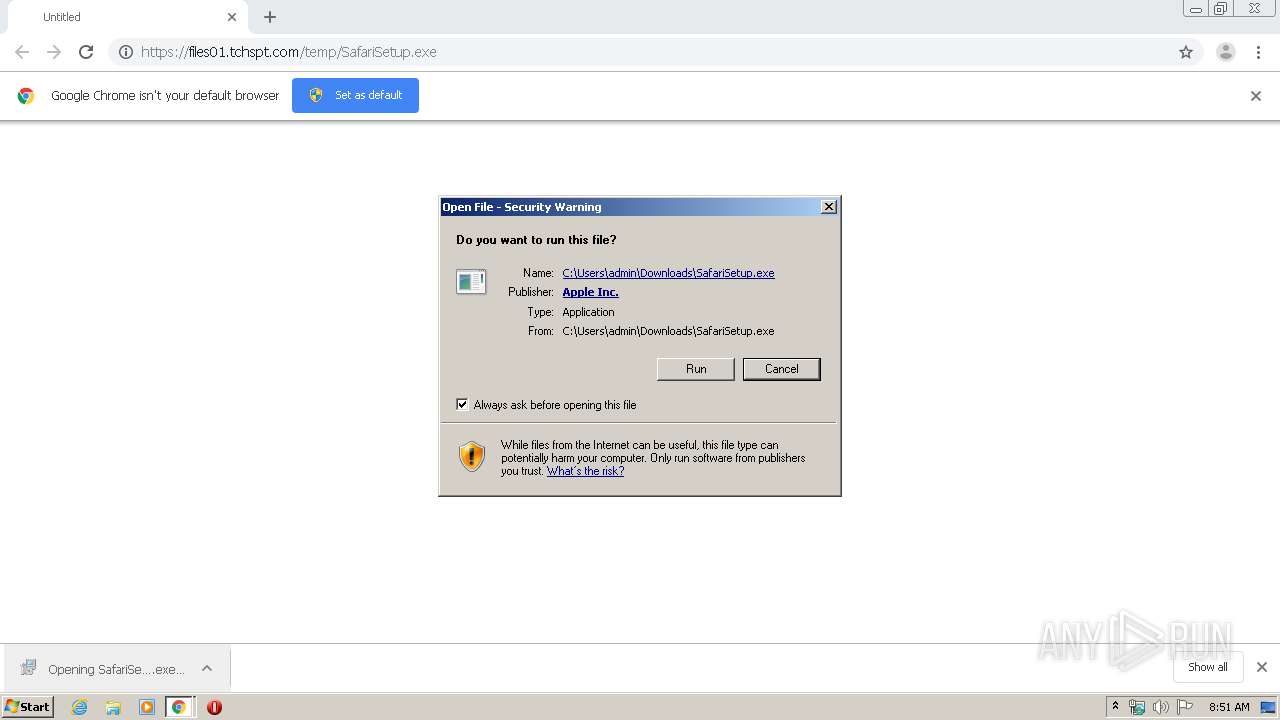
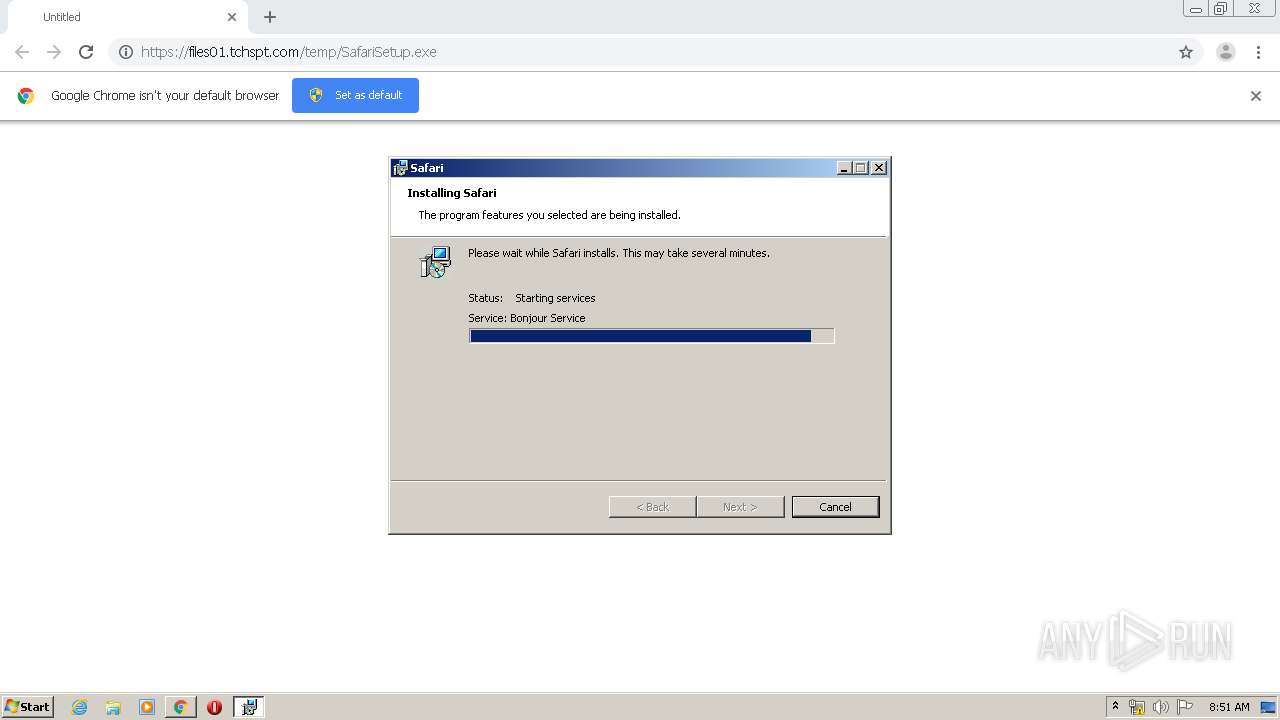
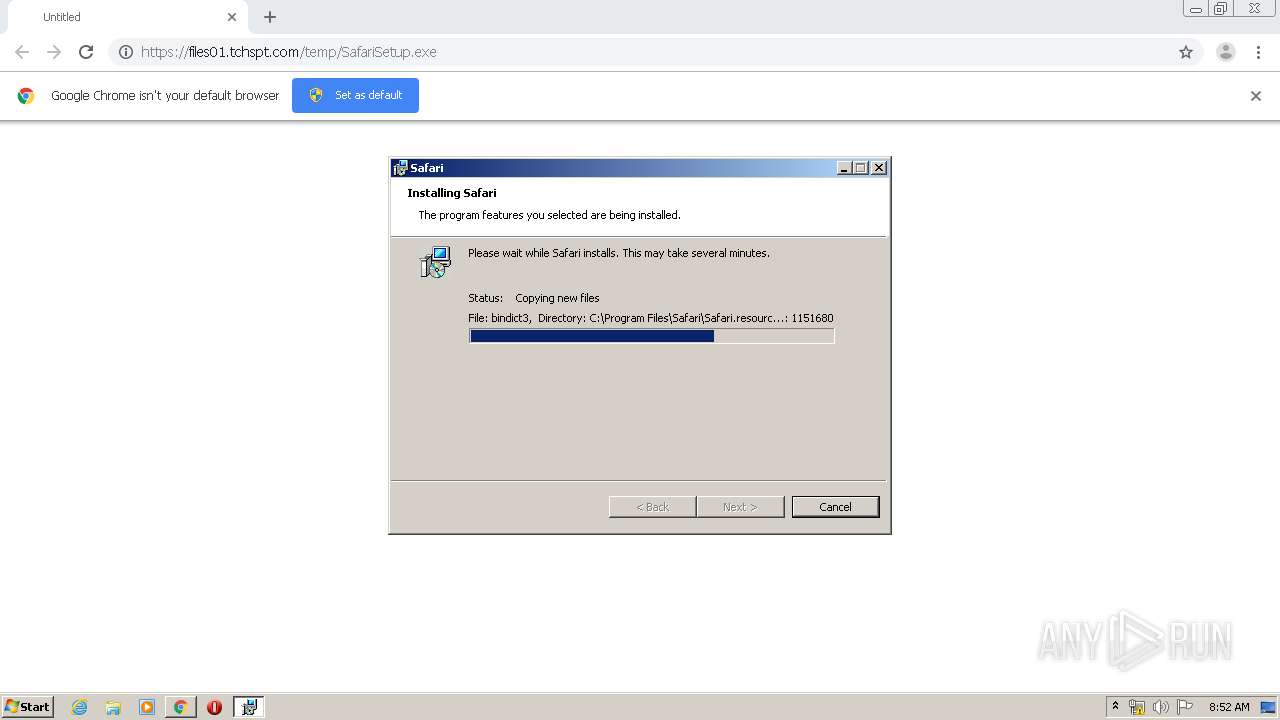
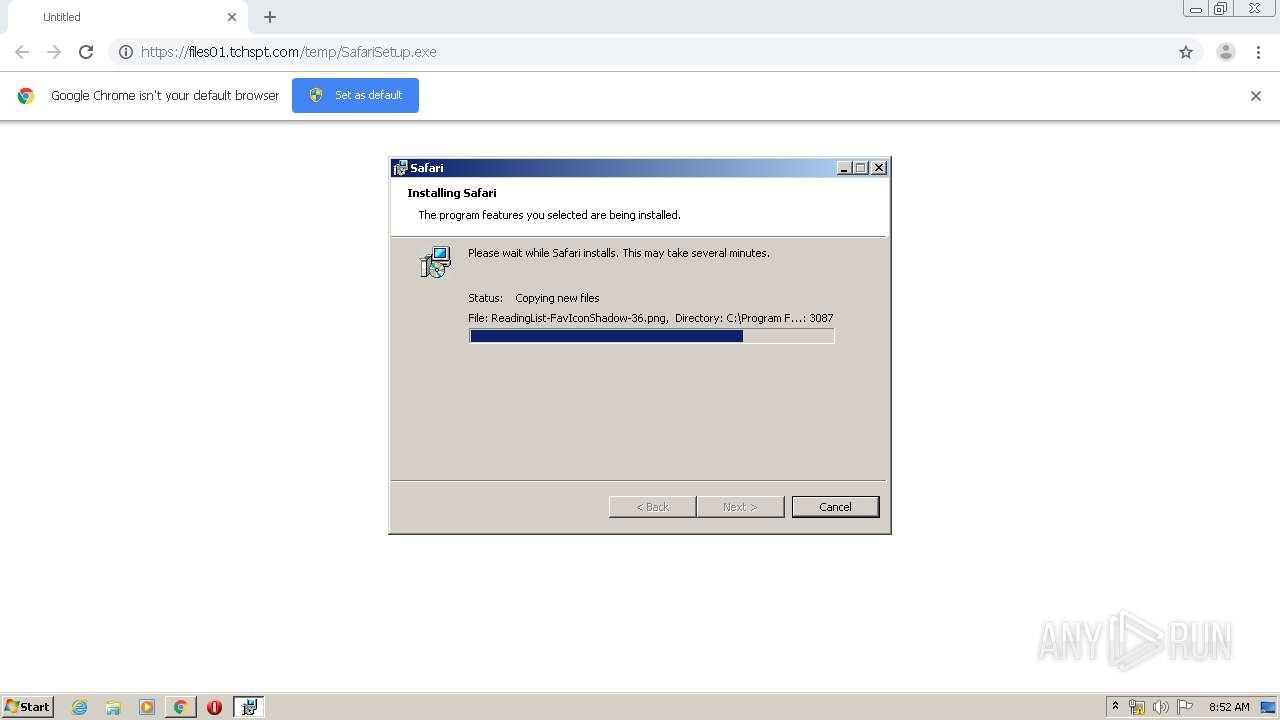
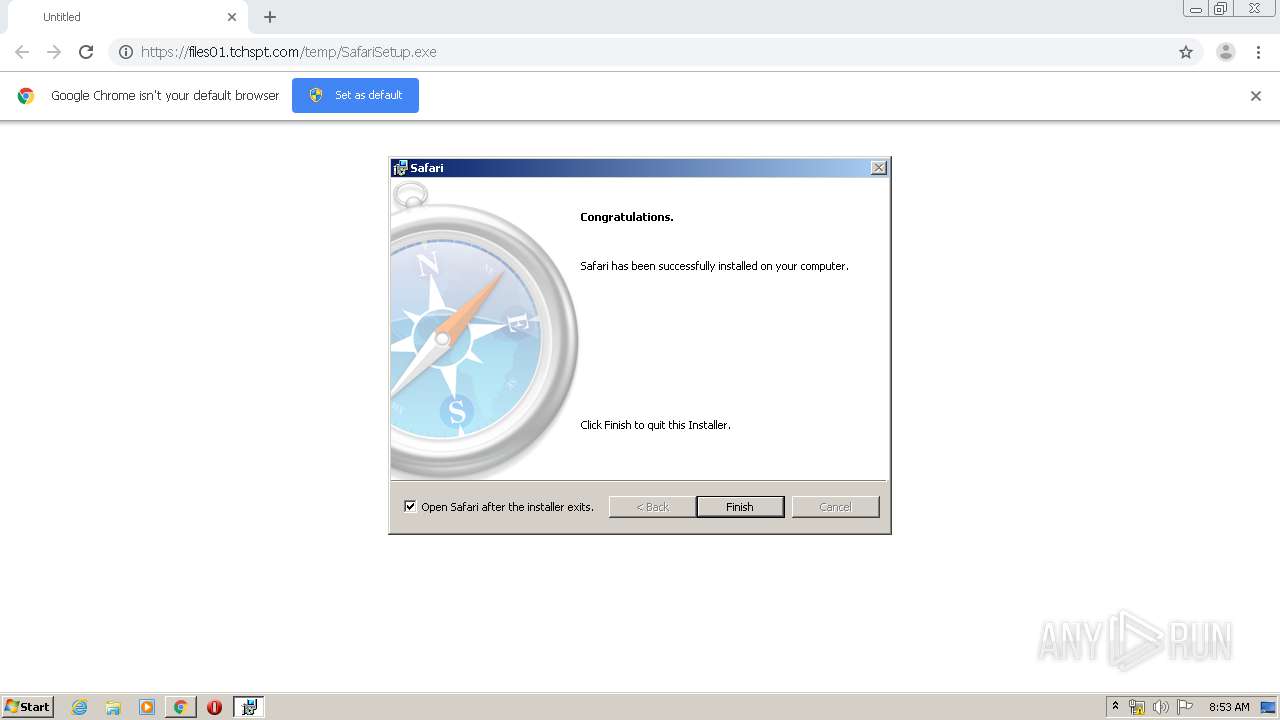
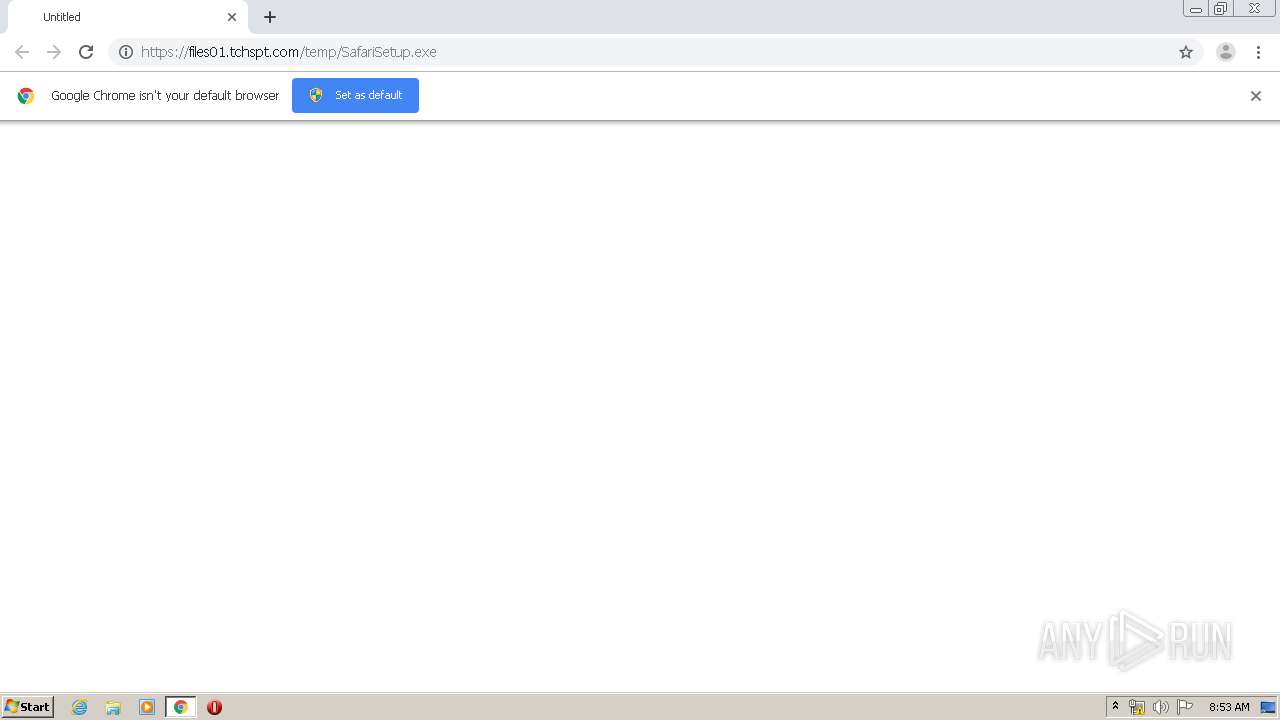
| URL: | https://files01.tchspt.com/temp/SafariSetup.exe |
| Full analysis: | https://app.any.run/tasks/df5da5ad-33b7-4036-88fe-a0e236264aa6 |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2020, 07:50:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 807F603018ABD88AAF1B678047FBD47F |
| SHA1: | 226DABF4AA488C50E574C5400D2FDB2F21717874 |
| SHA256: | C9F52A0E7D2327469E9198AF72ACE99590817728A71EA71C62B5BE4D8A7D5643 |
| SSDEEP: | 3:N8SrccRlA:2SrdlA |
MALICIOUS
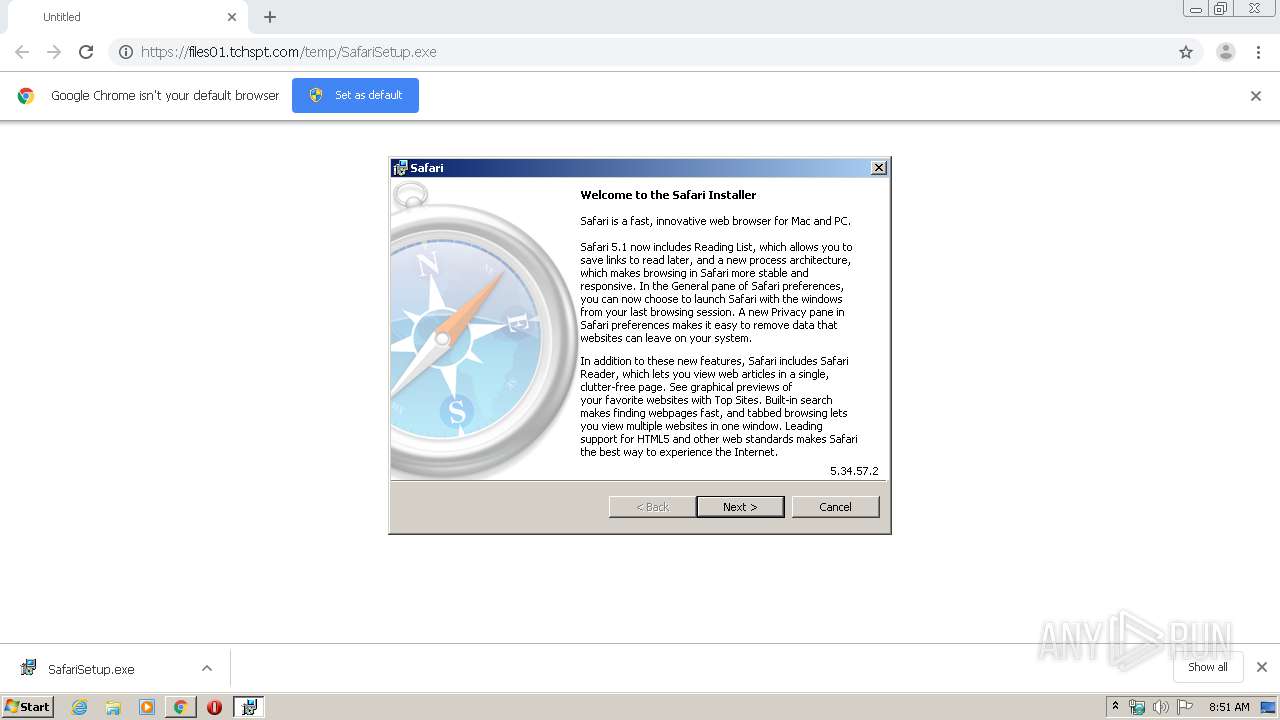
Application was dropped or rewritten from another process
- SetupAdmin.exe (PID: 2576)
- SafariSetup.exe (PID: 3788)
- SetupAdmin.exe (PID: 1084)
- SoftwareUpdate.exe (PID: 3928)
- mDNSResponder.exe (PID: 3576)
- Safari.exe (PID: 2796)
- WebKit2WebProcess.exe (PID: 3284)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3360)
- SoftwareUpdate.exe (PID: 3928)
- svchost.exe (PID: 668)
- DllHost.exe (PID: 2876)
- MsiExec.exe (PID: 2592)
- chrome.exe (PID: 2644)
- Safari.exe (PID: 2796)
- WebKit2WebProcess.exe (PID: 3284)
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 3852)
- DllHost.exe (PID: 2876)
Actions looks like stealing of personal data
- Safari.exe (PID: 2796)
Changes settings of System certificates
- WebKit2WebProcess.exe (PID: 3284)
- Safari.exe (PID: 2796)
- msiexec.exe (PID: 3072)
SUSPICIOUS
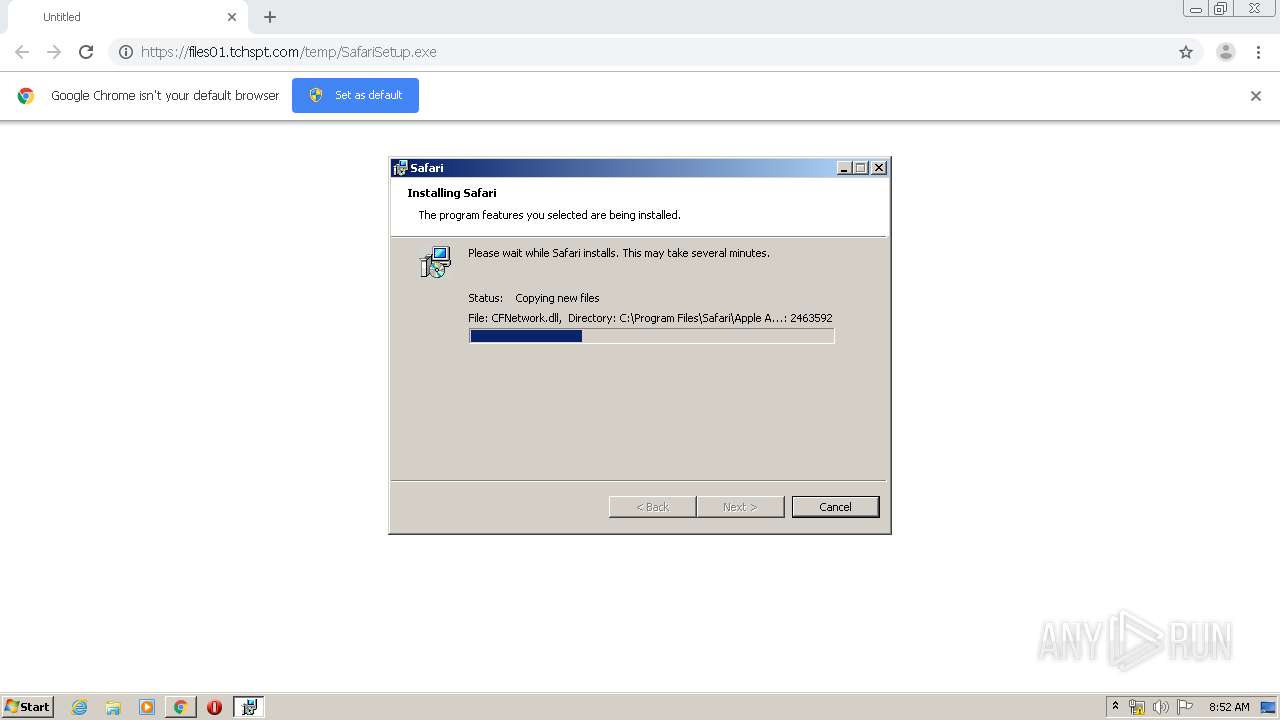
Executable content was dropped or overwritten
- SafariSetup.exe (PID: 3788)
- msiexec.exe (PID: 2288)
- chrome.exe (PID: 3556)
- msiexec.exe (PID: 3072)
Creates COM task schedule object
- MsiExec.exe (PID: 3360)
- msiexec.exe (PID: 3072)
Starts Microsoft Installer
- SafariSetup.exe (PID: 3788)
Executed via COM
- DllHost.exe (PID: 2876)
- DllHost.exe (PID: 3068)
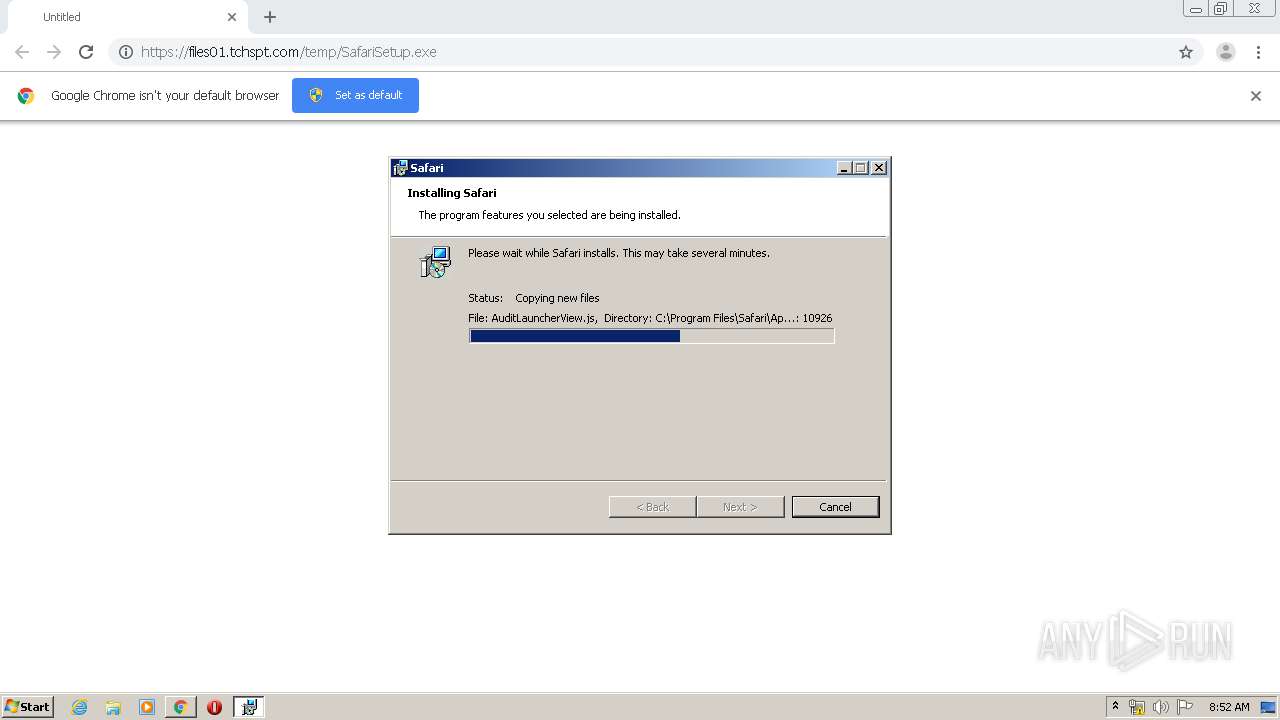
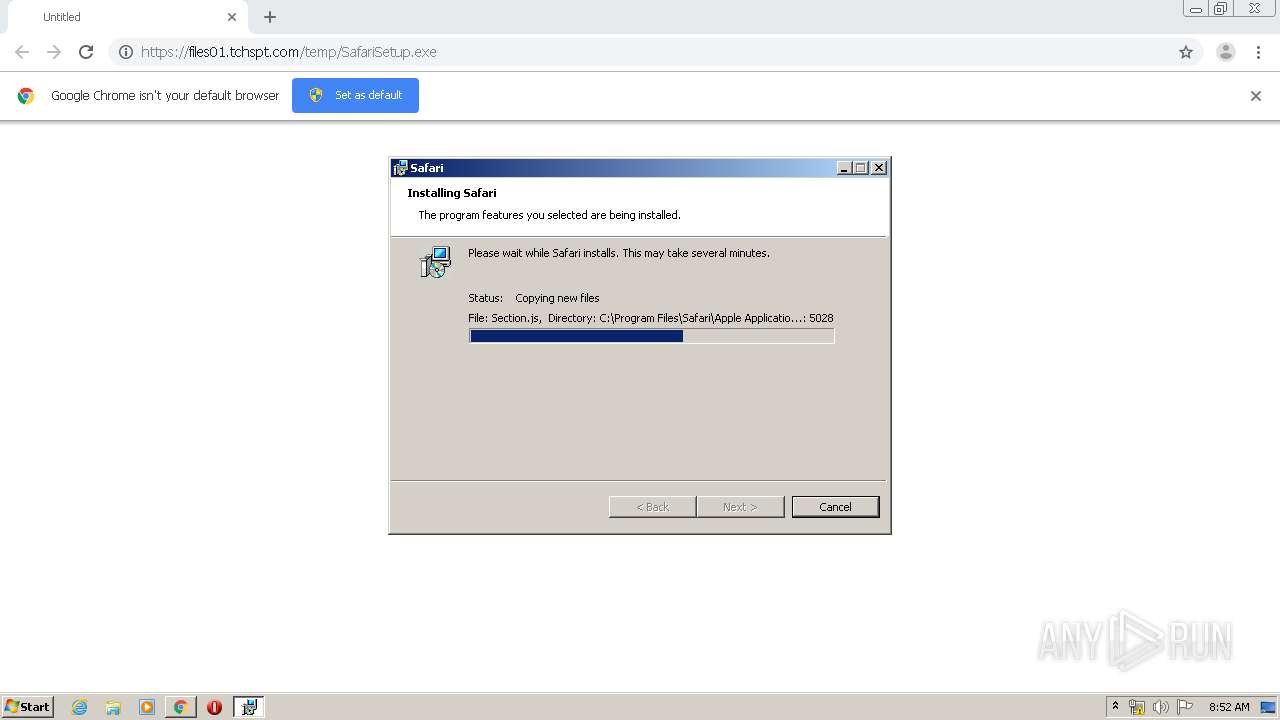
Creates files in the Windows directory
- msiexec.exe (PID: 3072)
Executed as Windows Service
- mDNSResponder.exe (PID: 3576)
- vssvc.exe (PID: 3332)
Creates files in the user directory
- msiexec.exe (PID: 3072)
- Safari.exe (PID: 2796)
- WebKit2WebProcess.exe (PID: 3284)
Modifies the open verb of a shell class
- msiexec.exe (PID: 3072)
Removes files from Windows directory
- msiexec.exe (PID: 3072)
Reads Internet Cache Settings
- Safari.exe (PID: 2796)
- WebKit2WebProcess.exe (PID: 3284)
- DllHost.exe (PID: 3068)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3556)
Adds / modifies Windows certificates
- WebKit2WebProcess.exe (PID: 3284)
- Safari.exe (PID: 2796)
- msiexec.exe (PID: 3072)
INFO
Reads the hosts file
- chrome.exe (PID: 2644)
- chrome.exe (PID: 3556)
Application launched itself
- chrome.exe (PID: 3556)
- msiexec.exe (PID: 3072)
Reads Internet Cache Settings
- chrome.exe (PID: 3556)
Reads settings of System Certificates
- msiexec.exe (PID: 3072)
- chrome.exe (PID: 2644)
Creates a software uninstall entry
- msiexec.exe (PID: 3072)
Searches for installed software
- msiexec.exe (PID: 3072)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3072)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3332)
Creates files in the program directory
- msiexec.exe (PID: 3072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
92
Monitored processes
49
Malicious processes
6
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | C:\Windows\system32\MsiExec.exe -Embedding 863C27F8BA3E17AA47DB4D184E1252BD | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 668 | C:\Windows\system32\svchost.exe -k RPCSS | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17403871459118496839 --mojo-platform-channel-handle=4512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10808945302748789825 --mojo-platform-channel-handle=4112 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1084 | "C:\Users\admin\AppData\Local\Temp\IXP905.TMP\SetupAdmin.exe" /evt E9EB /pid 3800 /mon 524 536 | C:\Users\admin\AppData\Local\Temp\IXP905.TMP\SetupAdmin.exe | MsiExec.exe | ||||||||||||
User: admin Company: Apple Inc. Integrity Level: HIGH Description: Apple Installer (Elevated) Exit code: 0 Version: 5.34.57.2 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5389828718131783193 --mojo-platform-channel-handle=572 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8796055900561642329 --mojo-platform-channel-handle=4576 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebaa9d0,0x6ebaa9e0,0x6ebaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2288 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\IXP905.TMP\Safari.msi" | C:\Windows\system32\msiexec.exe | SafariSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4982825233084278600 --mojo-platform-channel-handle=4892 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
6 232
Read events
2 734
Write events
3 442
Delete events
56
Modification events
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3216) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3556-13231151428454500 |
Value: 259 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
130
Suspicious files
105
Text files
1 112
Unknown types
48
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E92C844-DE4.pma | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\abf1d470-c7fc-4119-9ca8-fd995bcd3475.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa6f39f.TMP | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6f5b3.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
31
DNS requests
25
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
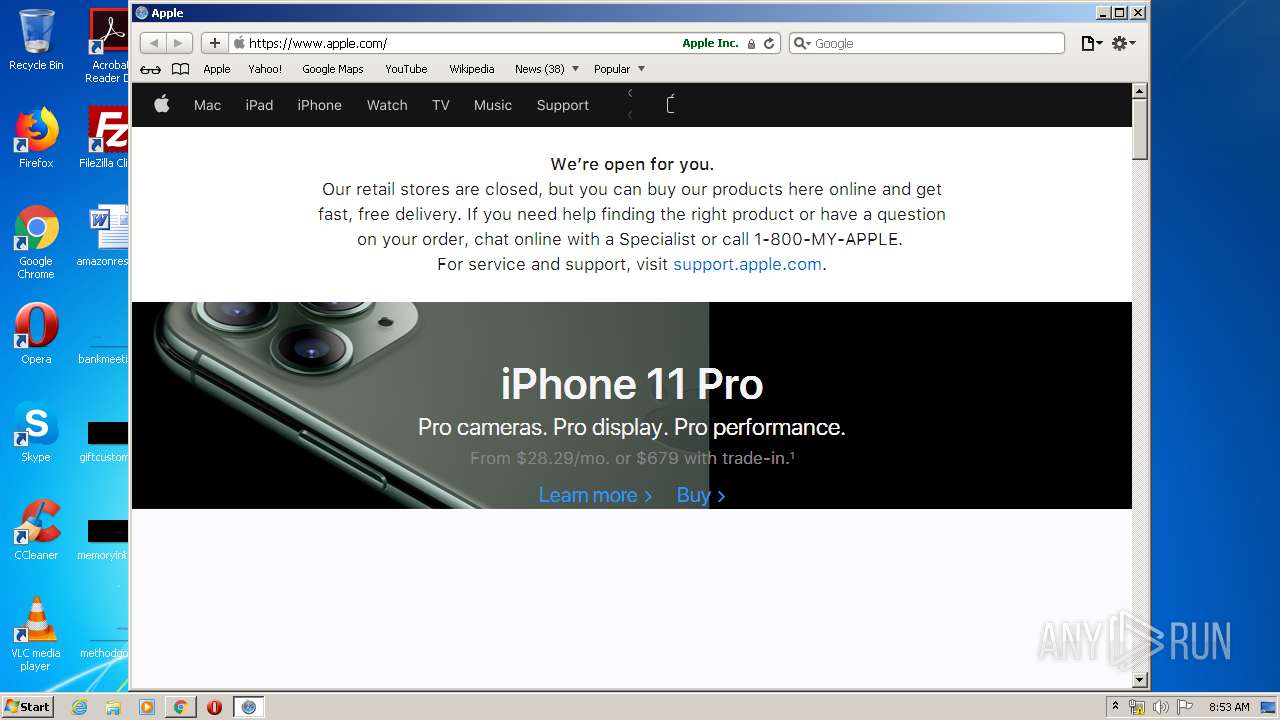
3284 | WebKit2WebProcess.exe | GET | 301 | 184.31.91.23:80 | http://www.apple.com/startpage/ | NL | — | — | whitelisted |
3284 | WebKit2WebProcess.exe | GET | 301 | 184.31.91.23:80 | http://www.apple.com/ | NL | — | — | whitelisted |
2796 | Safari.exe | GET | 301 | 216.58.207.46:80 | http://news.google.com/?output=rss | US | — | — | whitelisted |
3284 | WebKit2WebProcess.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2644 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3284 | WebKit2WebProcess.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEARgGBo5Qfjbr%2F1R0FS30Is%3D | US | der | 471 b | whitelisted |
2644 | chrome.exe | GET | 200 | 173.194.129.231:80 | http://r2---sn-q0c7rn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=81.17.242.238&mm=28&mn=sn-q0c7rn76&ms=nvh&mt=1586677588&mv=u&mvi=1&pl=20&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2796 | Safari.exe | GET | 200 | 184.30.216.40:80 | http://configuration.apple.com/configurations/internetservices/safari/ConfigurationsWin-5.1.7.plist.signed | NL | nib | 19.1 Kb | suspicious |
2644 | chrome.exe | GET | 200 | 74.125.168.8:80 | http://r3---sn-q0cedn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=81.17.242.238&mm=28&mn=sn-q0cedn7s&ms=nvh&mt=1586677588&mv=u&mvi=2&pl=20&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2644 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2644 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3284 | WebKit2WebProcess.exe | 184.31.91.23:80 | www.apple.com | Akamai International B.V. | NL | whitelisted |
2796 | Safari.exe | 184.30.216.40:80 | configuration.apple.com | Akamai International B.V. | NL | whitelisted |
3284 | WebKit2WebProcess.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3284 | WebKit2WebProcess.exe | 66.117.29.3:443 | apple.tt.omtrdc.net | Adobe Systems Inc. | US | whitelisted |
3284 | WebKit2WebProcess.exe | 184.31.91.23:443 | www.apple.com | Akamai International B.V. | NL | whitelisted |
2644 | chrome.exe | 206.190.128.220:443 | files01.tchspt.com | WestHost, Inc. | US | suspicious |
2644 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
files01.tchspt.com |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients4.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
b._dns-sd._udp.8ÓL |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3284 | WebKit2WebProcess.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3284 | WebKit2WebProcess.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
Process | Message |
|---|---|
WebKit2WebProcess.exe | Safari
|
WebKit2WebProcess.exe | ASL checking for logging parameters in environment variable "asl.log"
|
WebKit2WebProcess.exe | ASL checking for logging parameters in environment variable "WebKit2WebProcess.exe.log"
|
WebKit2WebProcess.exe | ASL logging to file "C:\Users\admin\AppData\Roaming\Apple Computer\Logs\asl.085334_12Apr20.log"
|
WebKit2WebProcess.exe | [com.apple.WebKit2WebProcess WebKit2WebProcess.exe] (Initialize|Accept)SecurityContext failed with error 0x80090326
|
WebKit2WebProcess.exe | [com.apple.WebKit2WebProcess WebKit2WebProcess.exe] CertGetCertificateChain failed with error 0x80090301
|
WebKit2WebProcess.exe | [com.apple.WebKit2WebProcess WebKit2WebProcess.exe] (Initialize|Accept)SecurityContext failed with error 0x80090326
|
WebKit2WebProcess.exe | [com.apple.WebKit2WebProcess WebKit2WebProcess.exe] CertGetCertificateChain failed with error 0x80090301
|