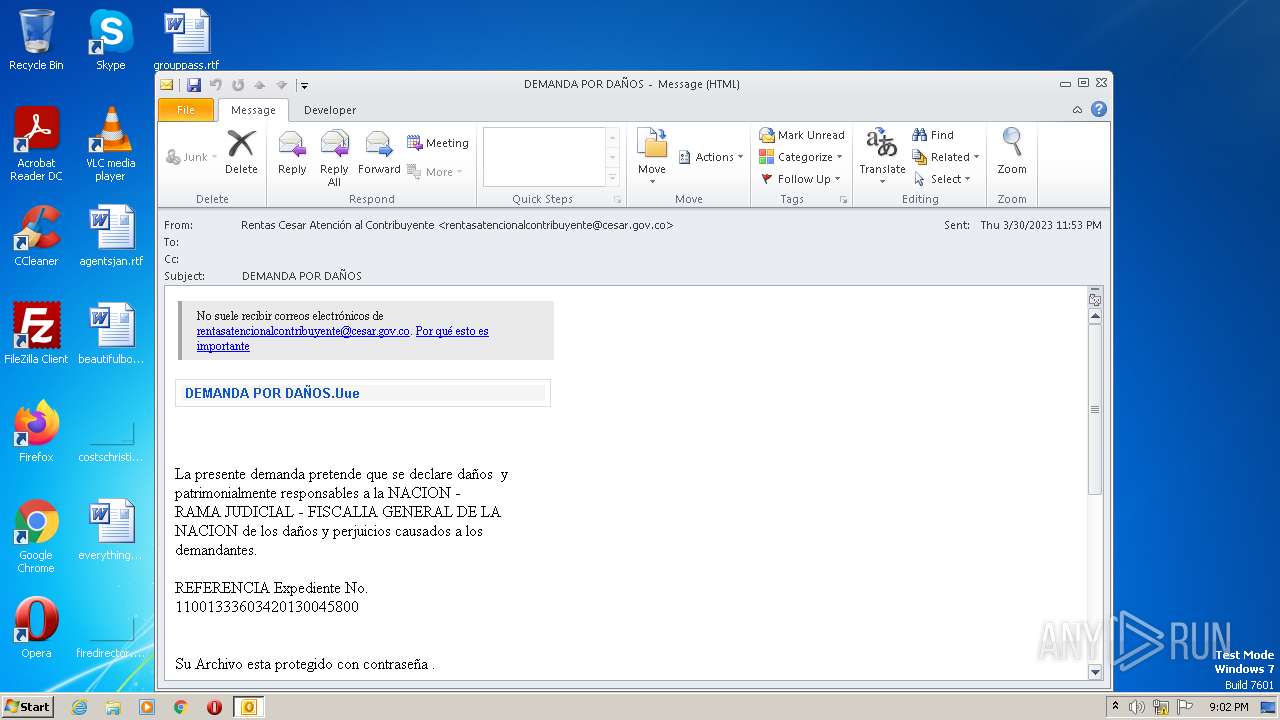
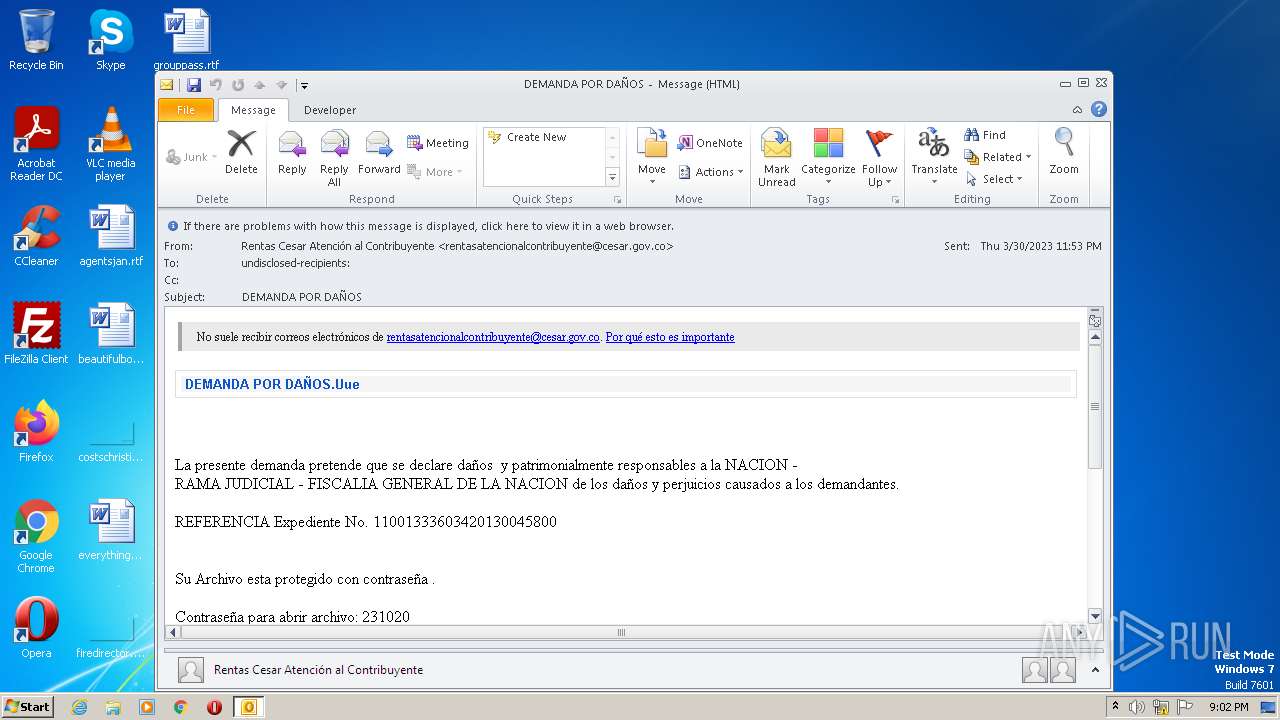
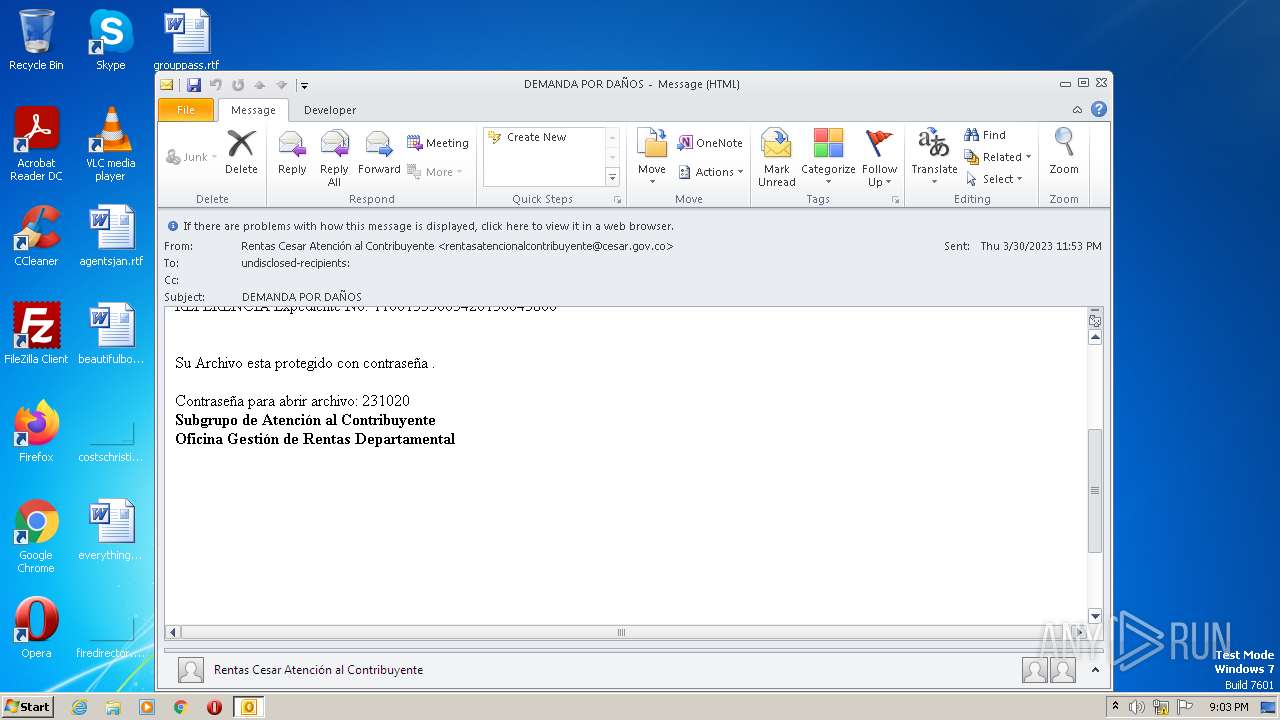
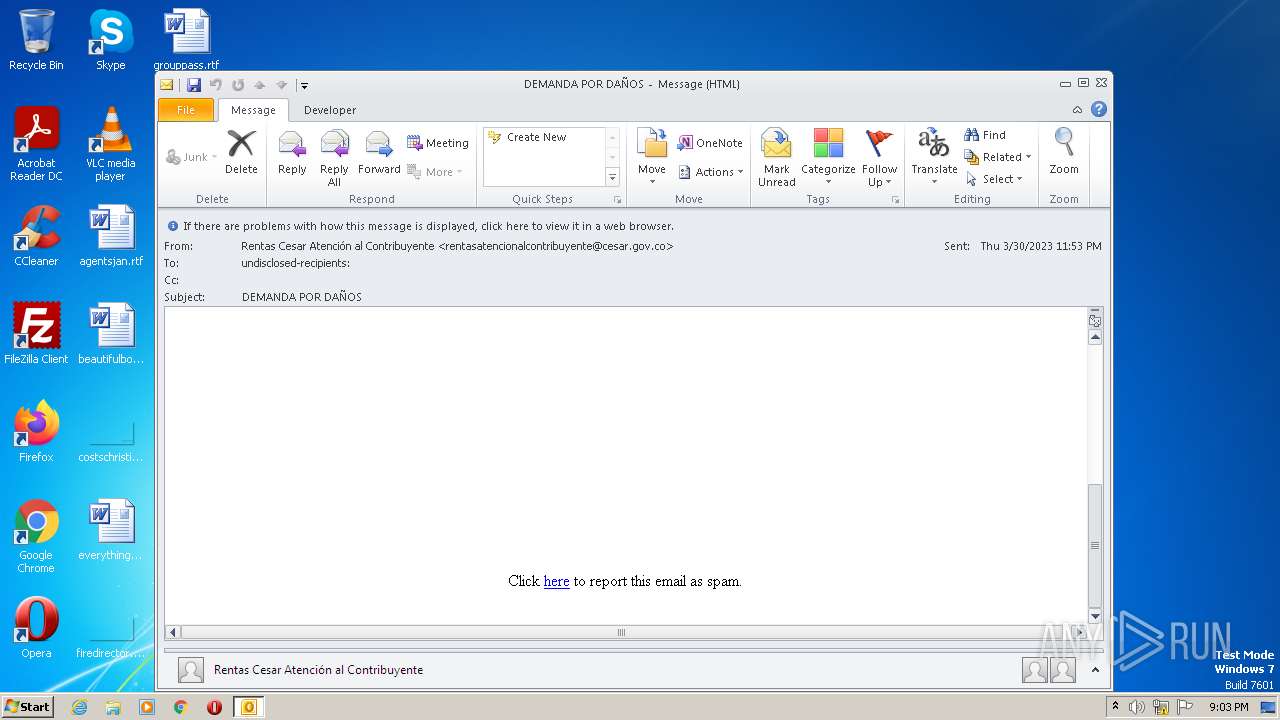
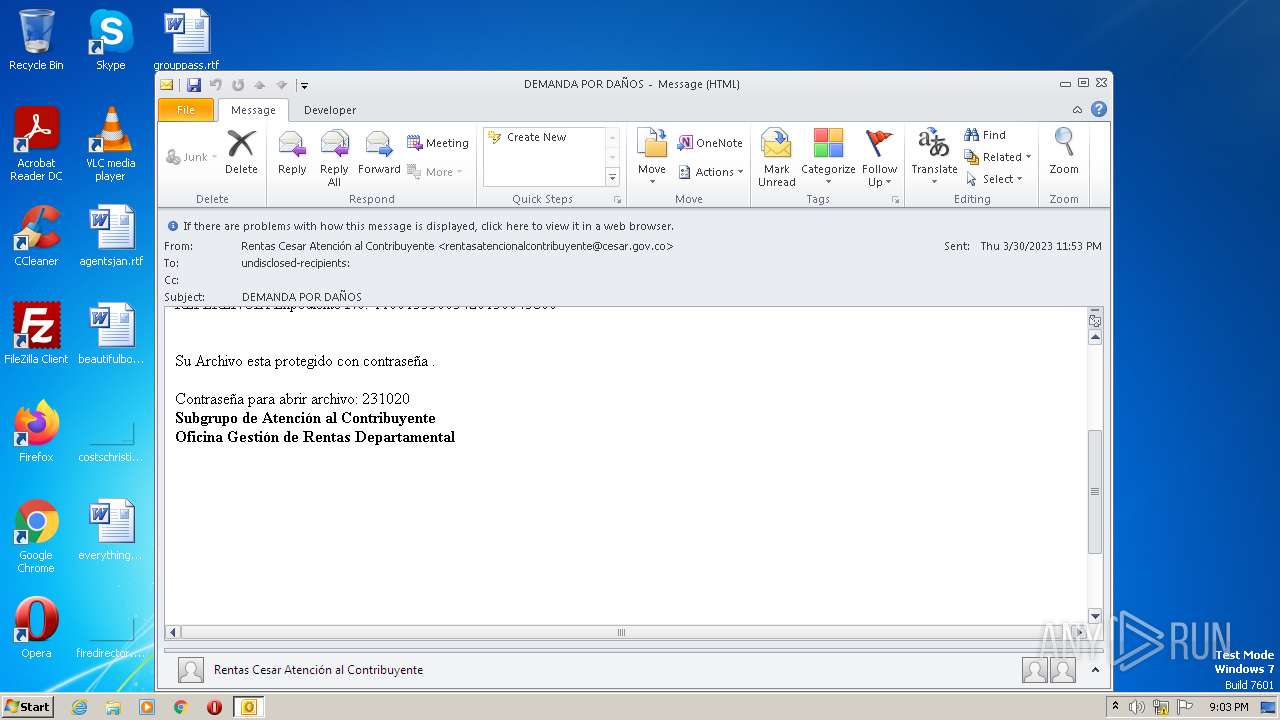
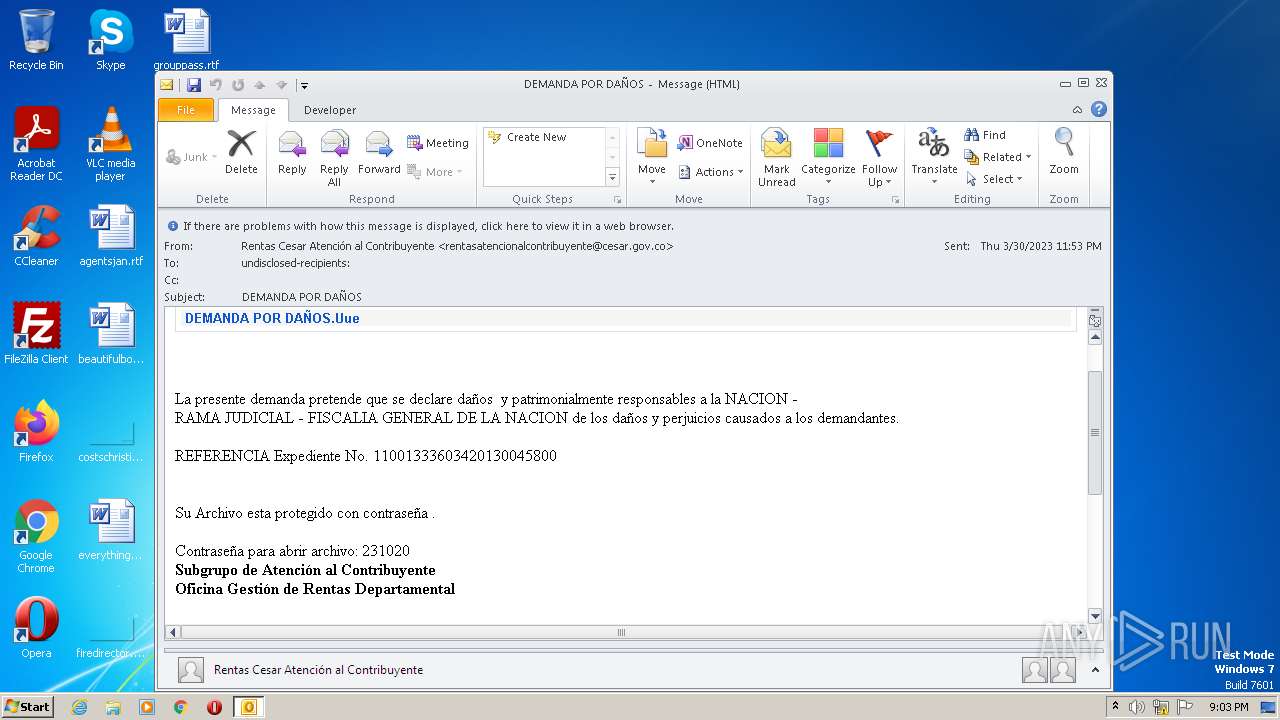
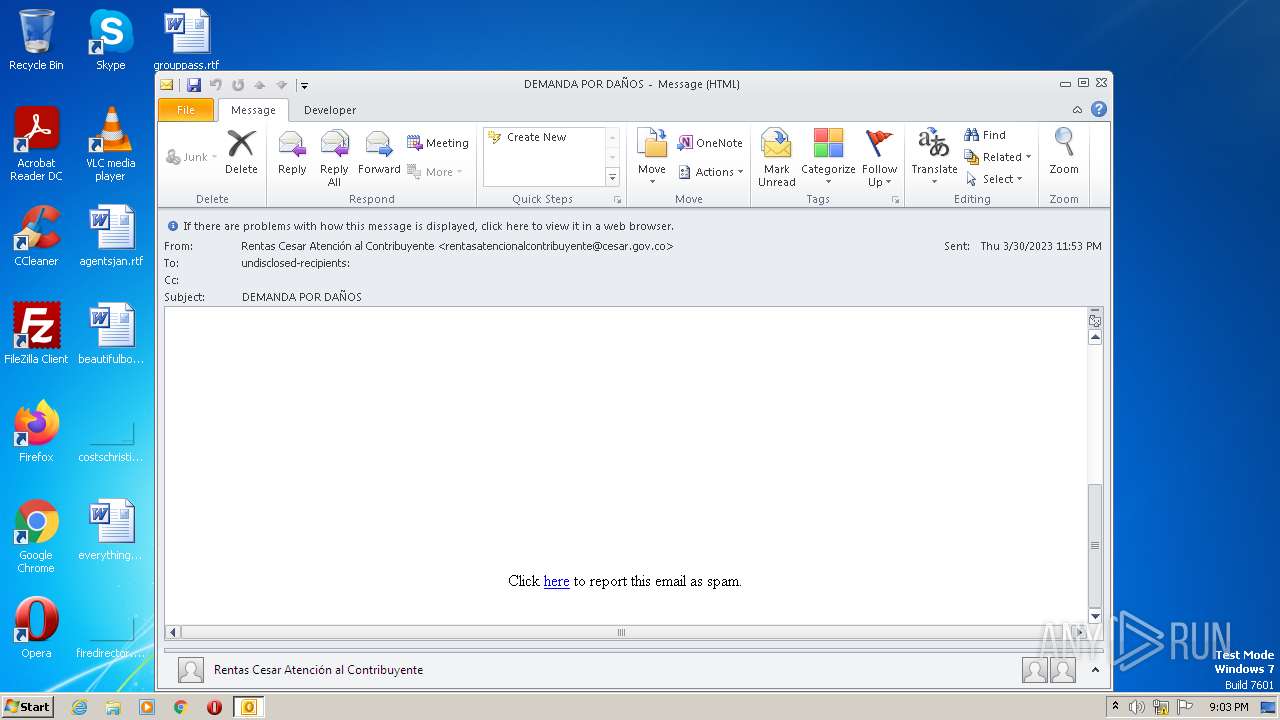
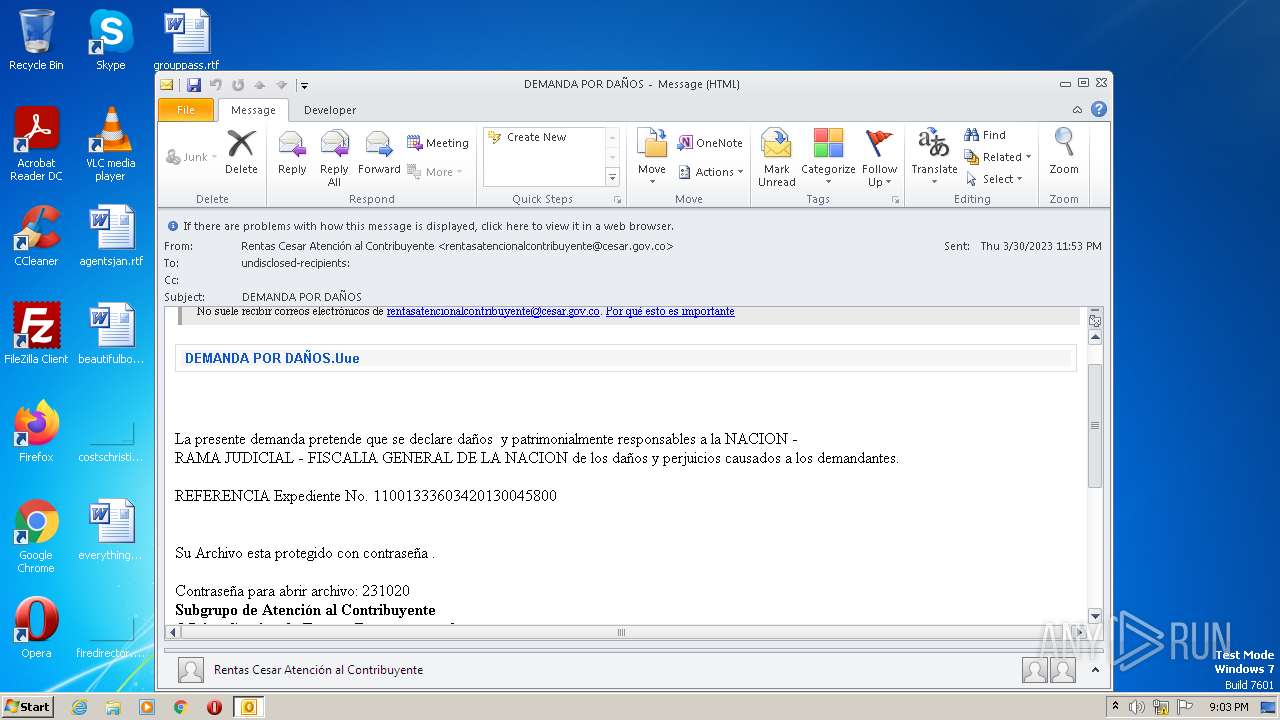
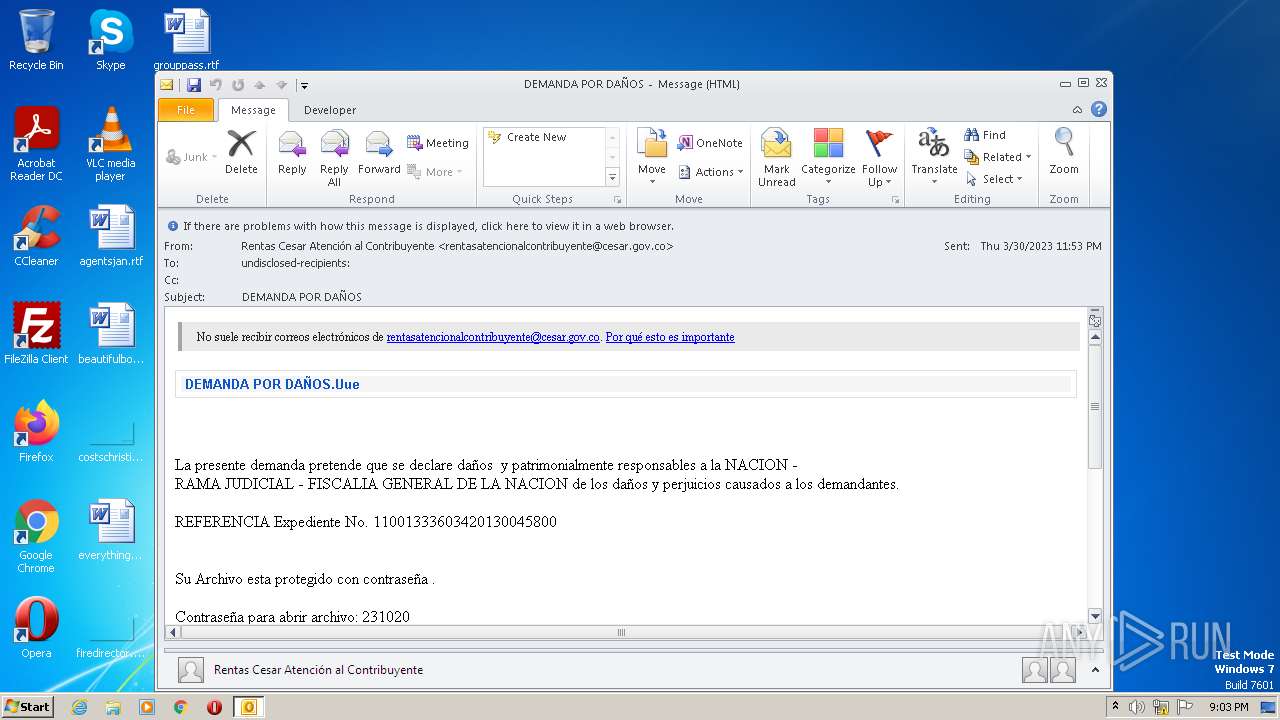
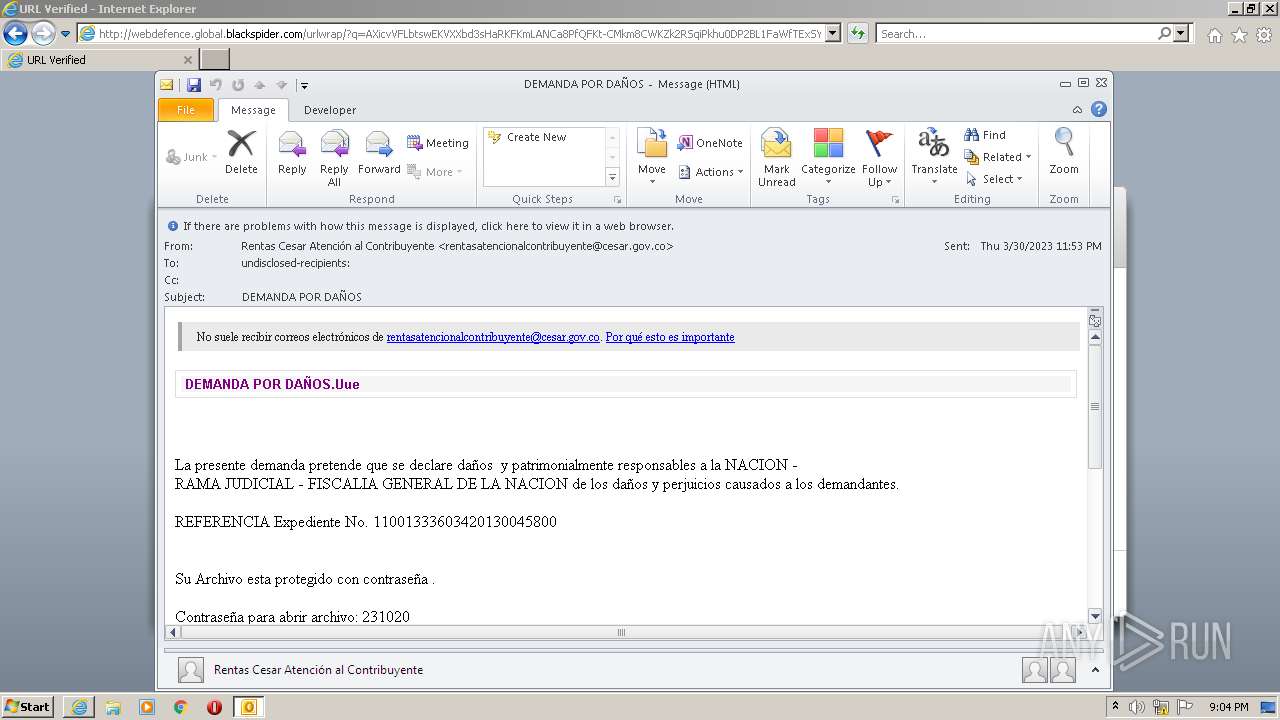
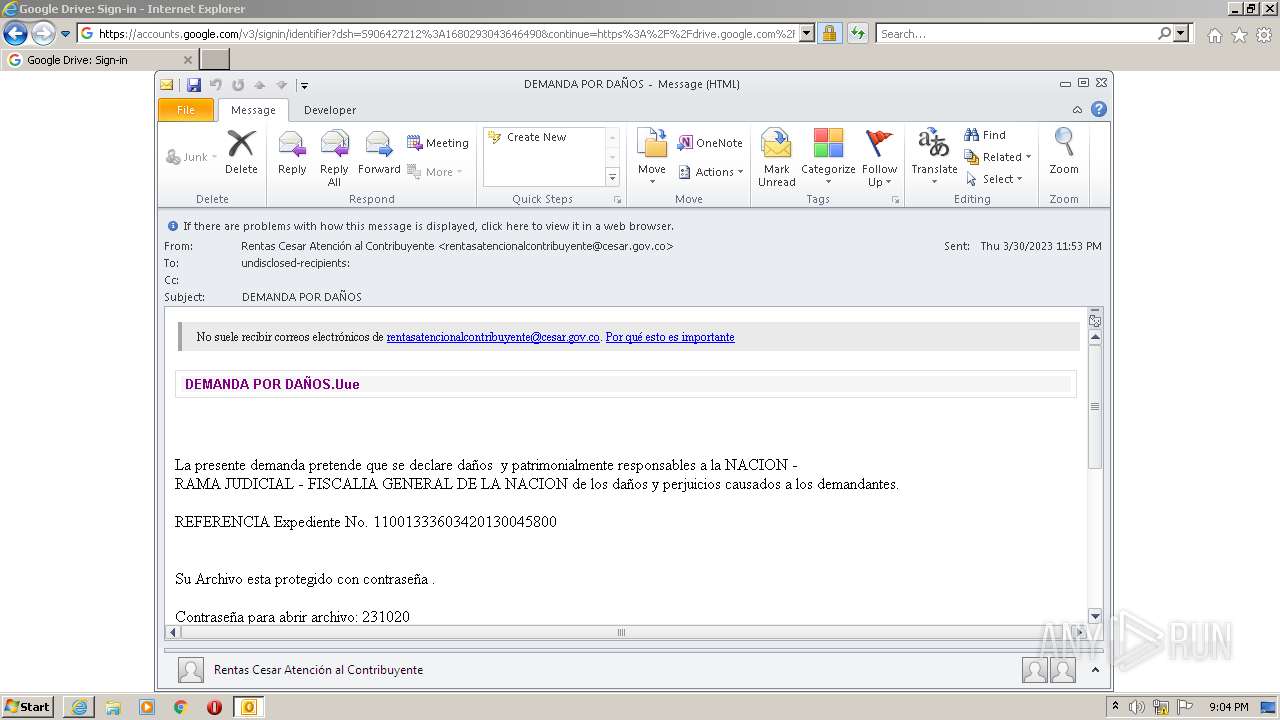
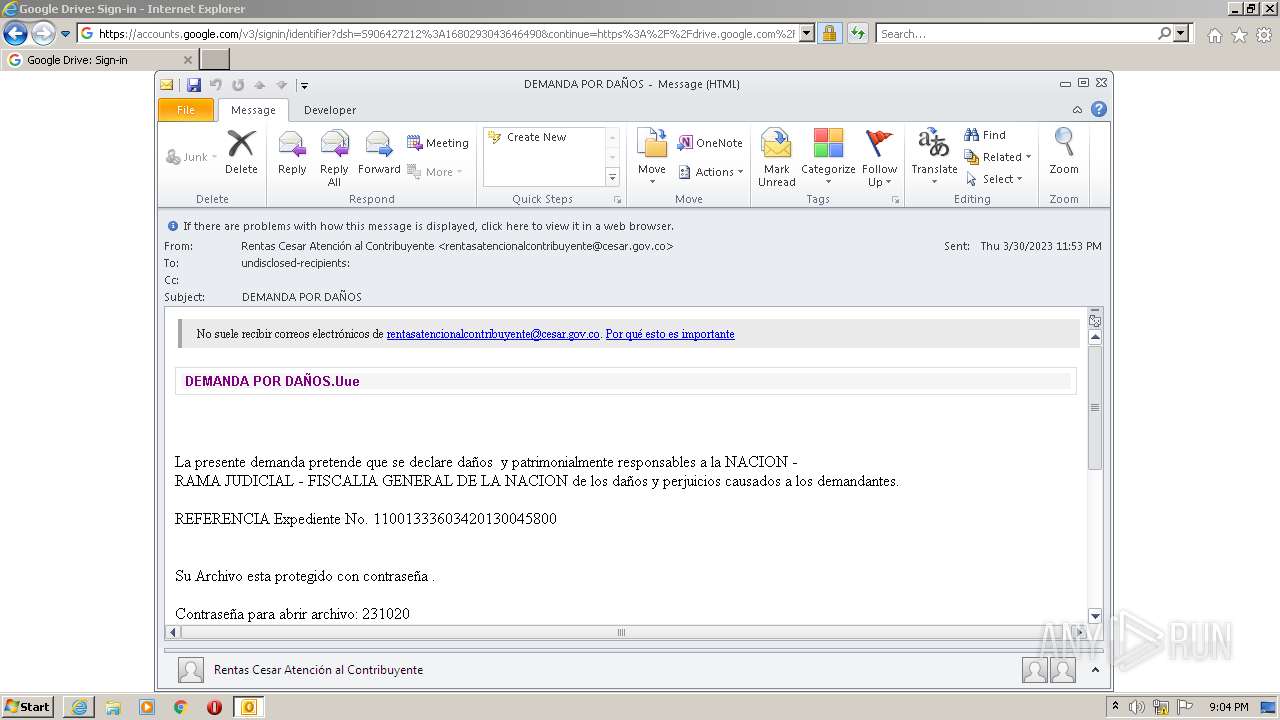
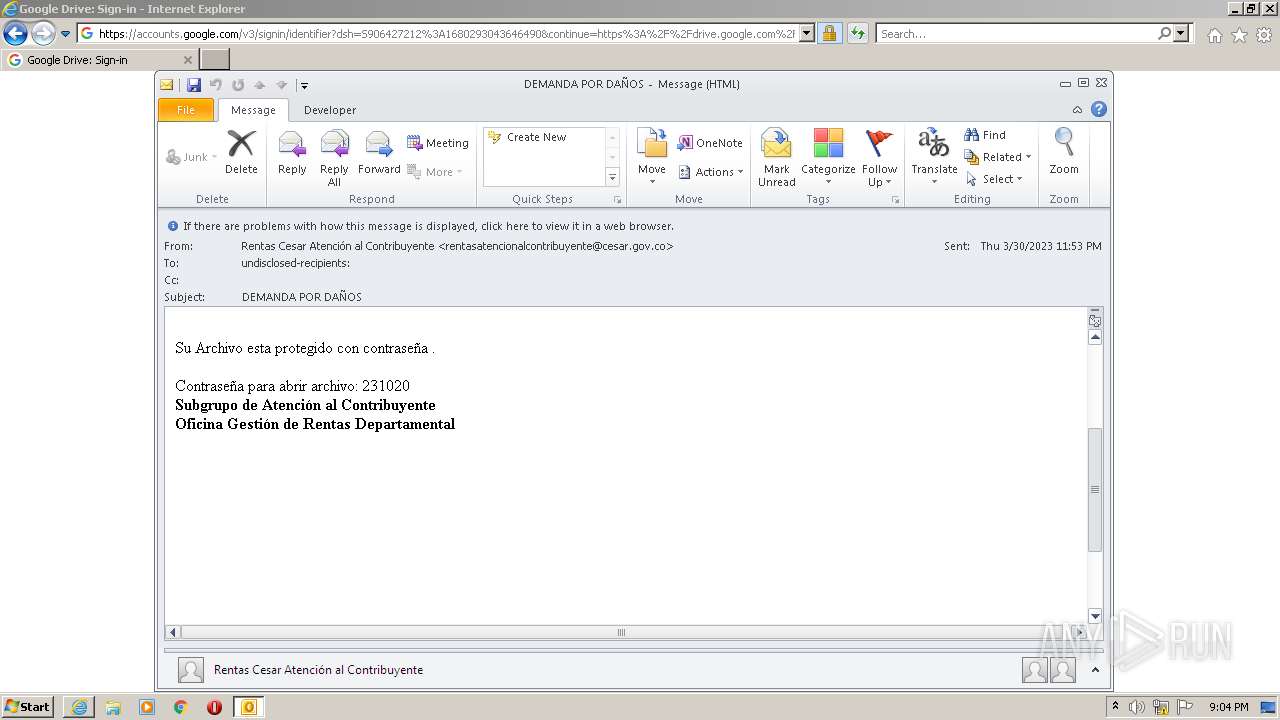
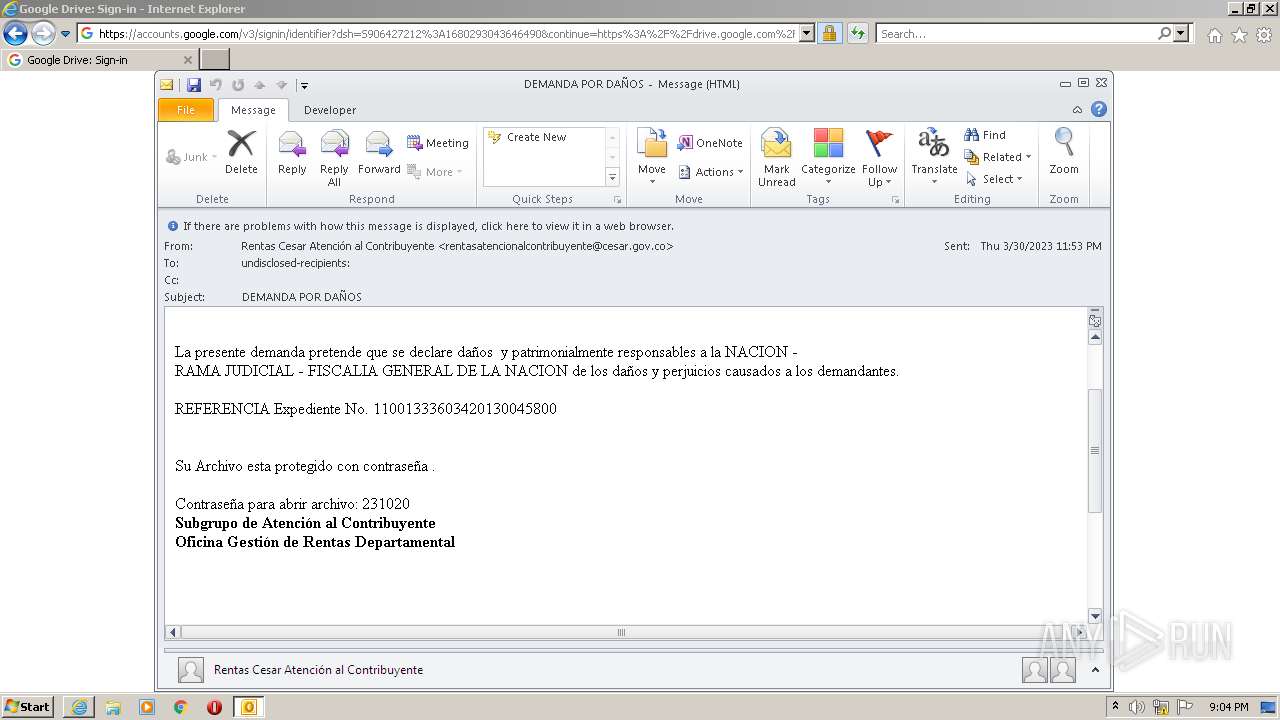
| File name: | DEMANDA POR DAÑOS.eml |
| Full analysis: | https://app.any.run/tasks/0018f74c-c9eb-4de6-9899-621edd10c12f |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2023, 20:02:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 219E703FC56C3023E49DCE3D5D1D8FD7 |
| SHA1: | 8FFC600F801A9D35AF3C8B5CDDDB79765E2E3224 |
| SHA256: | C9EDFC68B49F6C9D303C05E0D8BEB47441FB3783632D9381255FA440BF1D8A6A |
| SSDEEP: | 384:WJmCL1X7zHuDXS2WshPzW+Q9mAmIBwBYGuBAU/GF:WJmCL1X7zSXMAPXQ9m1IBwBiSF |
MALICIOUS
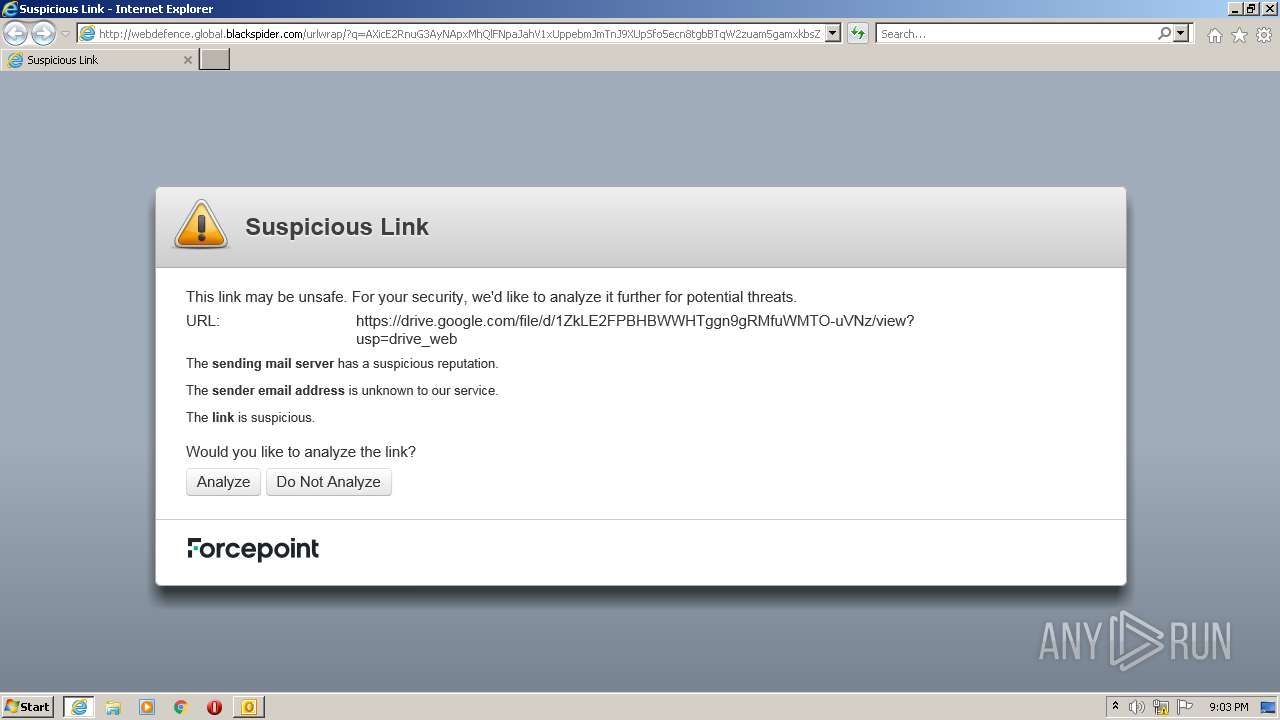
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- OUTLOOK.EXE (PID: 2512)
Searches for installed software
- OUTLOOK.EXE (PID: 2512)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2512)
Checks supported languages
- OUTLOOK.EXE (PID: 2512)
Reads the computer name
- OUTLOOK.EXE (PID: 2512)
The process checks LSA protection
- OUTLOOK.EXE (PID: 2512)
Reads the machine GUID from the registry
- OUTLOOK.EXE (PID: 2512)
Create files in a temporary directory
- OUTLOOK.EXE (PID: 2512)
- iexplore.exe (PID: 2816)
- chrome.exe (PID: 3592)
Process checks computer location settings
- OUTLOOK.EXE (PID: 2512)
Creates files or folders in the user directory
- OUTLOOK.EXE (PID: 2512)
Checks proxy server information
- OUTLOOK.EXE (PID: 2512)
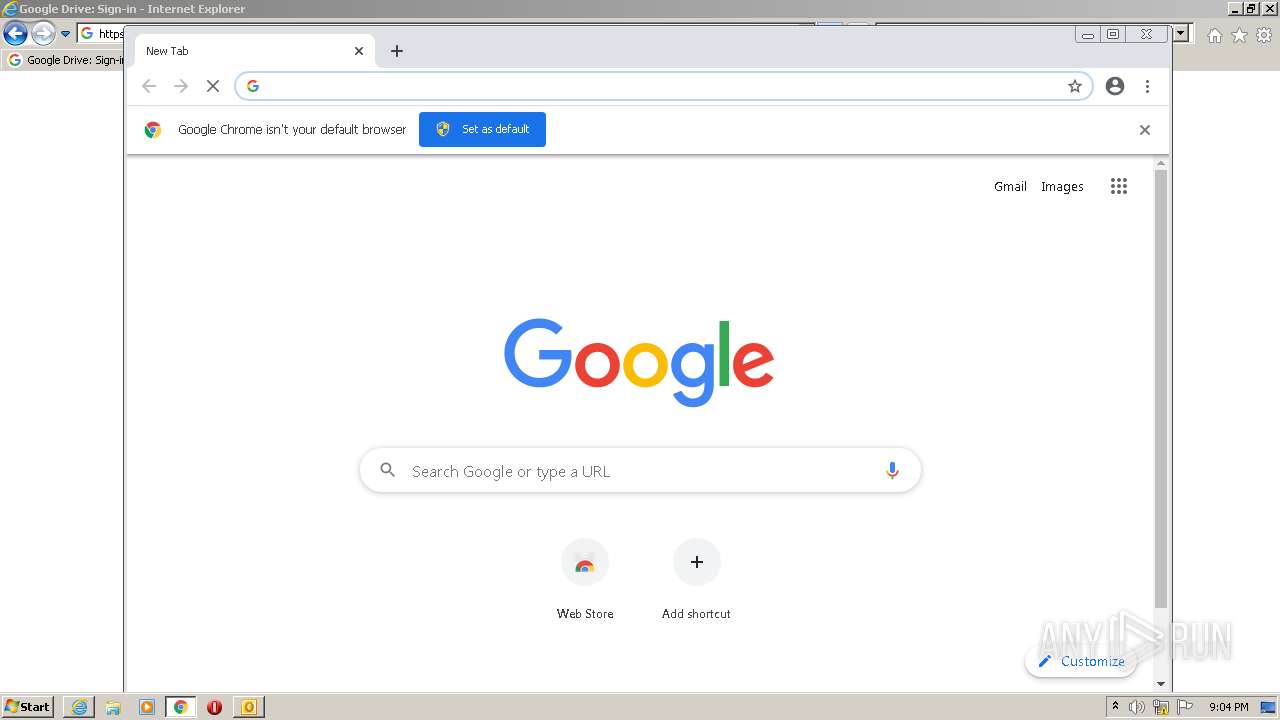
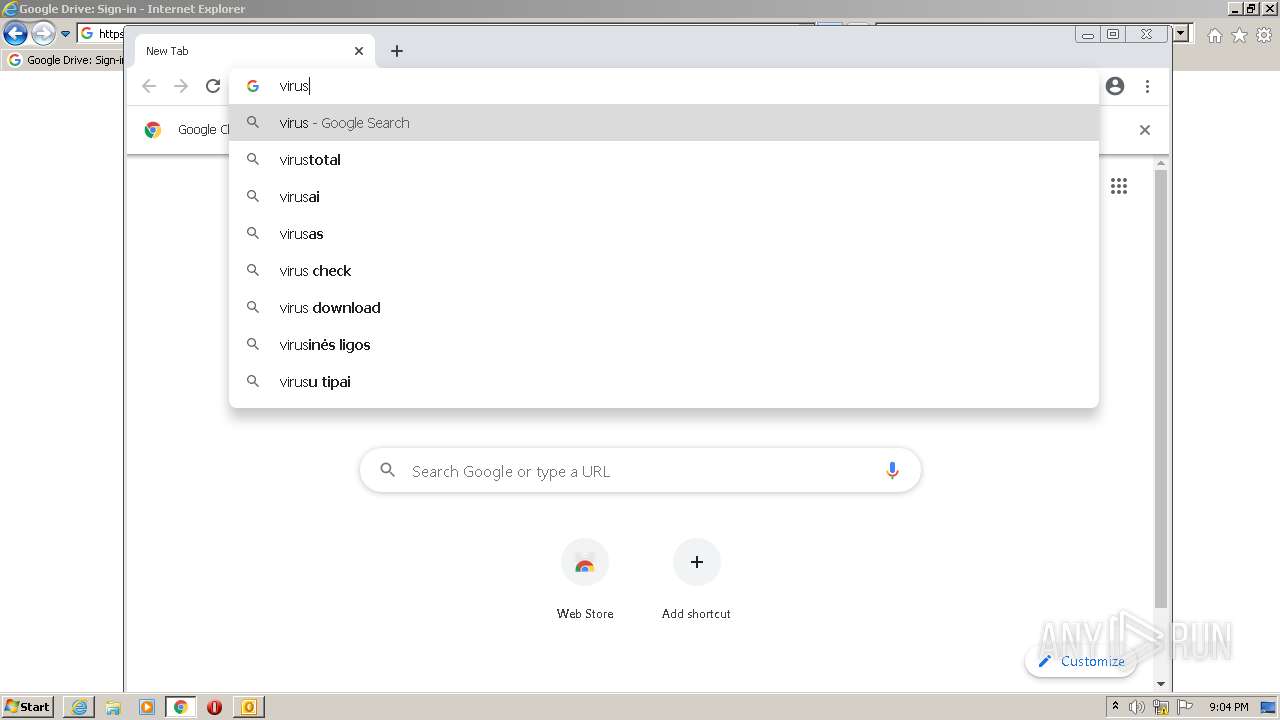
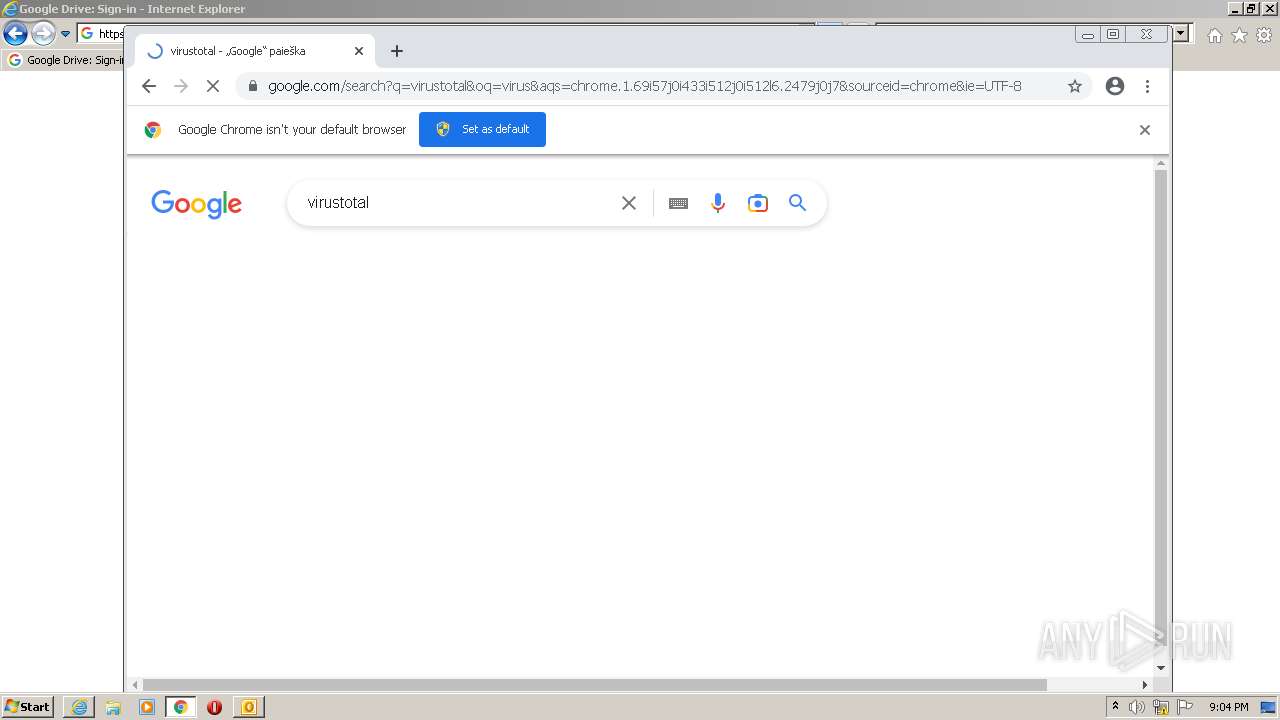
Application launched itself
- iexplore.exe (PID: 2816)
- chrome.exe (PID: 3592)
Manual execution by a user
- chrome.exe (PID: 3592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
78
Monitored processes
38
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,9151389266200122170,17722874836581293664,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4008 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1016,9151389266200122170,17722874836581293664,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2936 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1016,9151389266200122170,17722874836581293664,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2864 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9151389266200122170,17722874836581293664,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2712 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,9151389266200122170,17722874836581293664,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=972 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1016,9151389266200122170,17722874836581293664,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1284 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1016,9151389266200122170,17722874836581293664,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2212 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9151389266200122170,17722874836581293664,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1016,9151389266200122170,17722874836581293664,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3120 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1016,9151389266200122170,17722874836581293664,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3028 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
60 762
Read events
59 534
Write events
1 166
Delete events
62
Modification events
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
0
Suspicious files
352
Text files
376
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF2EC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 2816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{F9526581-F68F-45C6-AB78-657C34B23035}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_0973E0398FC2C346BA8BD3DBF27E1A56.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
84
DNS requests
48
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
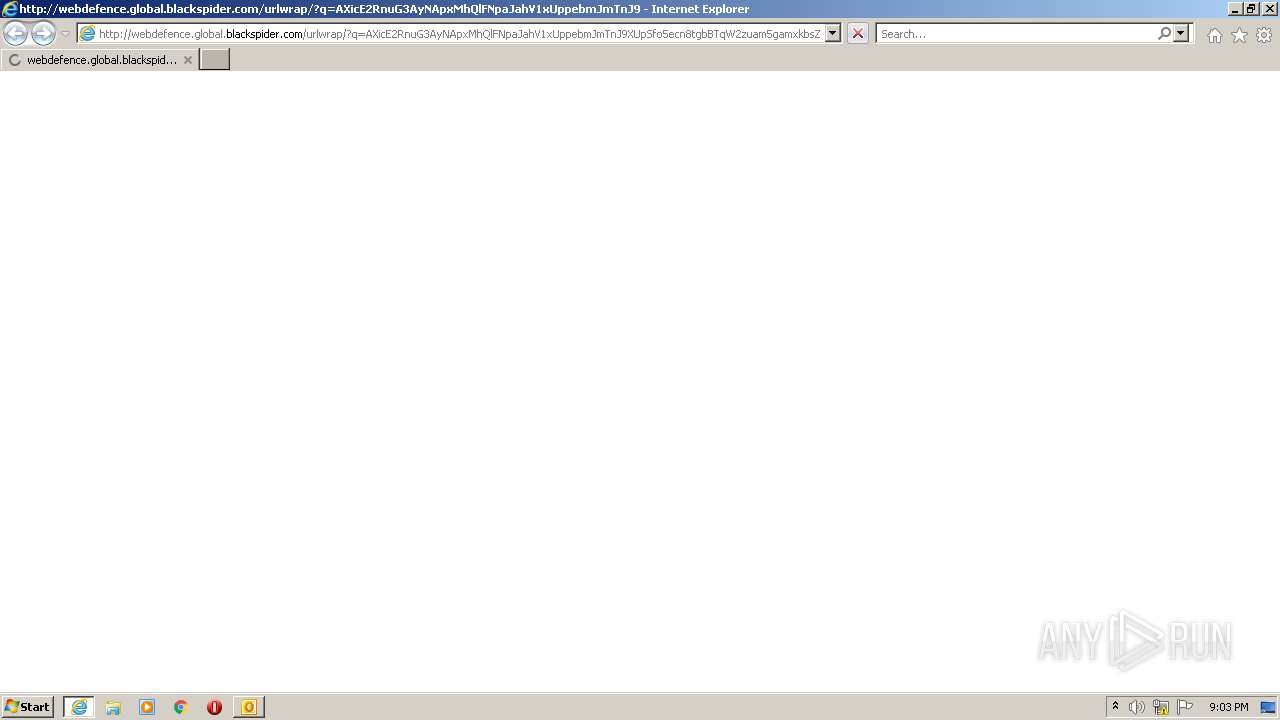
2408 | iexplore.exe | GET | 200 | 85.115.52.220:80 | http://www.mailcontrol.com/http-resources/notification-pages/empty.js | GB | — | — | whitelisted |
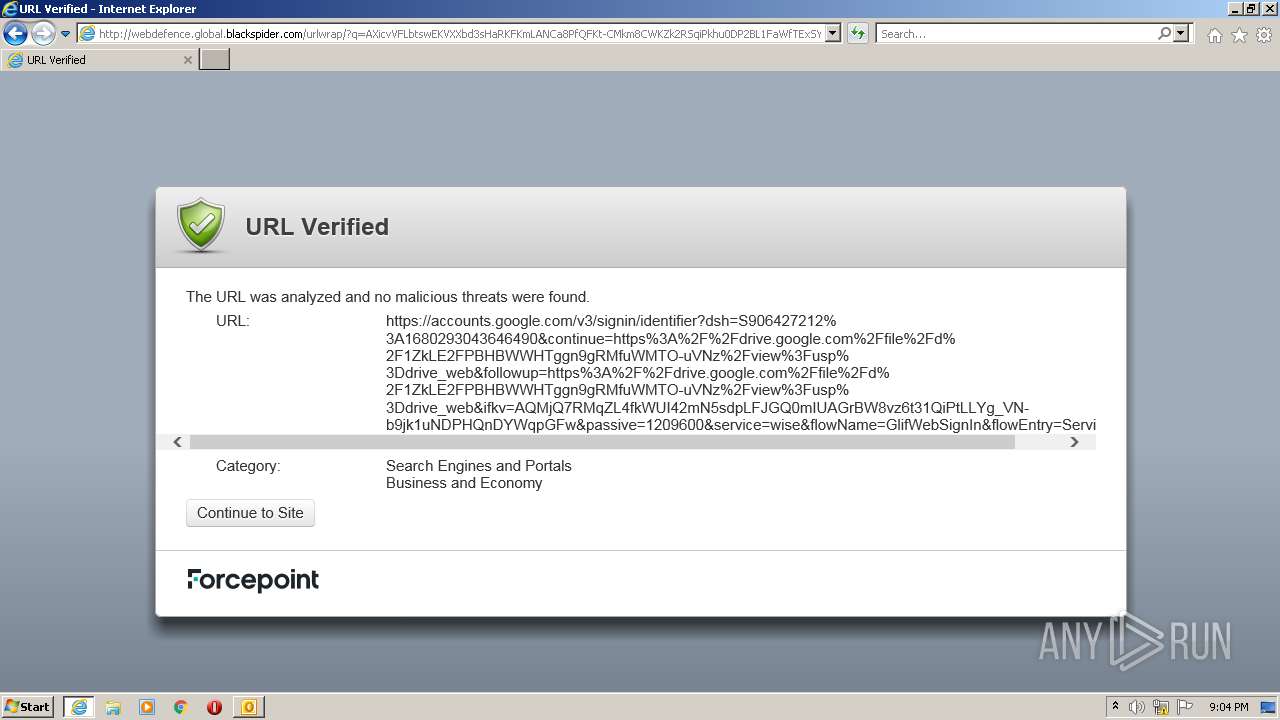
2408 | iexplore.exe | GET | 403 | 116.50.61.180:80 | http://webdefence.global.blackspider.com/urlwrap/?q=AXicE2RnuG3AyNApxMhQlFNpaJahV1xUppebmJmTnJ9XUpSfo5ecn8tgbBTqW2zuam5gamxkbsZQnFpUlpmcma-XnJOZmleS6lCUlAtSB8QMGSUlBcVW-vopRZllqXrp-fnpOakgOf20zJxU_RR9w6hsH1cjtwAnD6fwcI-Q9PQ8y_Qg37TScN8Qf93SML8q_bLM1HL70uICW7AR8eWpSQwMDC9tGRkAn8s4Yw&Z | JP | html | 5.17 Kb | whitelisted |
2816 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2408 | iexplore.exe | GET | 302 | 116.50.61.180:80 | http://webdefence.global.blackspider.com/urlwrap/?q=AXicHYxLDoIwFAAfK9d6D1sEBSUxGhMMC1FjEBI3Rmqt1UJJCzV6A8_oCbyFn8WsZjLtFrxsC54dC5S497wz0sqg4sAFkWWtpEBEFuA621j7oW8PXMf3QFNlOOESEcFpWdOpyotf9wXOdV3pAOOj4oYiJiUT9OfwiQuKj7i3uy5CZ76eRbMsixLGyhHbxKcmi5NVt0mXD2w4vU0aXY3_i_2N5mAEiRaXYJ0mJOgPhp7nArzHFnwA2yk9tw&action=scan | JP | html | 289 b | whitelisted |
2408 | iexplore.exe | GET | 302 | 116.50.61.180:80 | http://webdefence.global.blackspider.com/urlwrap/?q=AXictVBLboJAAB1XXbd3qDthBIViQqw_ihYULULqxuA4jKMjQxg-qTfoGXuC3qLYpkkv0MVLXvJ-ybu9AR-wAd7vGiBjb23tIImslM4RZYgnecaZhPgZqMraFfpEh11V0TUgcFZSRLmEGMVJjh-z3fnqqwEOeZ6KnixHCPEiyYVEOCcMX2V5WnuzCOW0xA4nNOlfN2hSYPM3tc9q7W8kpgzLe7m9OTkTxfKG9jAMbZ-QxCArNy5C11-0imB-kUuKq34h0nt1_F2yrfCuGXPGeFWk_9WfRkLU3Gwr0NAgbP4cg82KCtyk8ak0B0v3uNRXKtGGvIPW8WBrRYuX1rMTbgJoH9TJ9Gmk0Zmjw1Fx6XbQ1LC82UV3sbEI9tHG84WF4NxZvobqGJQM2c6x5wU-6nW6D5qmAvBpNsAXdg6X8Q&action=scan | JP | html | 441 b | whitelisted |
2408 | iexplore.exe | GET | 302 | 116.50.61.180:80 | http://webdefence.global.blackspider.com/urlwrap/?q=AXicvVFLbtswEKVXXbd3sHaRKFKmLANCa8PfQFKt-CMkm8CWKZk2RSqiPkhu0DP2BL1FaWfTExSYt5n35s0M3tcv4DfsgV_feqDi7zY5m6pqzeLAeCpFXUluprIAGO1C5c5cOMDIJUDRqmUpk2bKGRU1_VEdi5tOA5zrulQjyzqkqWxErcxcypzTG2212FIsF0xY7KTnWMZo9f2kzv7Gg8RBLrJRH49tMoTIw9DBxCGOB43bJUw01L97a0UfzXWdKtbSf-x1K2Oc3hgN--UazNB8PVlOkmS5zXPh5U9h1iTh9udDs48-tKZltOvjeaPKPp7e7V47ejQyybnsmvJ_7WPZtfXHcXiJ3afw7SVwsmuyWzmoiAbqVAbzx0UMi9VuvKgmybD9IDW2Y7aug-A5f91HD0fvcrWbaLpexmL6nLyVi3lnlAeltL9vI-gRCI3PyKjfMUWNTL8XHQrqLzjLEnrc6FBW4t6e6dDf_c2nOpA5E6Dl6TK4jNb7bTpyBkNCMAB__B74CwpFuyw&action=allow | JP | compressed | 441 b | whitelisted |
2408 | iexplore.exe | GET | 403 | 116.50.61.180:80 | http://webdefence.global.blackspider.com/urlwrap/?q=AXicvVFLbtswEKVXXbd3sHaRKFKmLANCa8PfQFKt-CMkm8CWKZk2RSqiPkhu0DP2BL1FaWfTExSYt5n35s0M3tcv4DfsgV_feqDi7zY5m6pqzeLAeCpFXUluprIAGO1C5c5cOMDIJUDRqmUpk2bKGRU1_VEdi5tOA5zrulQjyzqkqWxErcxcypzTG2212FIsF0xY7KTnWMZo9f2kzv7Gg8RBLrJRH49tMoTIw9DBxCGOB43bJUw01L97a0UfzXWdKtbSf-x1K2Oc3hgN--UazNB8PVlOkmS5zXPh5U9h1iTh9udDs48-tKZltOvjeaPKPp7e7V47ejQyybnsmvJ_7WPZtfXHcXiJ3afw7SVwsmuyWzmoiAbqVAbzx0UMi9VuvKgmybD9IDW2Y7aug-A5f91HD0fvcrWbaLpexmL6nLyVi3lnlAeltL9vI-gRCI3PyKjfMUWNTL8XHQrqLzjLEnrc6FBW4t6e6dDf_c2nOpA5E6Dl6TK4jNb7bTpyBkNCMAB__B74CwpFuyw&action=scan | JP | html | 5.27 Kb | whitelisted |
2408 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECeWD0WyAbIuCn9a0SESNi4%3D | US | der | 471 b | whitelisted |
2408 | iexplore.exe | GET | 302 | 116.50.61.180:80 | http://webdefence.global.blackspider.com/urlwrap/?q=AXictc1PToNAFAbwYeVa7yA7Gf5YsCSkprGGBWijWBI3hk4f09FhhswwkHoDz9gT9BaWGhMv4OKtvu_7vfMztHct9HVhIcV3Xrh1tOqdpmKcSNEpyR0iGxT4L7mOFpE7CfwoRBpUzwiTDuEMRAe3at2MveOhbde1Osa4IkQa0WmHSkk5jDF-Pu0gk5SJ2Q8CycA02G2lNesh8Xx3GrquPT5nwkDyy23UMf5r1YwD3mDv9SNb-PfLeTovy7SgVEzpU16bMi8er8zq4RP3DIaZ0e1lcHdC3gZY27XkXA6m_Scf9Zyk2Xu8XBUkvp7chGGA0CGx0DfWxXz-&action=scan | JP | html | 5.17 Kb | whitelisted |
2408 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2512 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2408 | iexplore.exe | 116.50.61.180:80 | webdefence.global.blackspider.com | Forcepoint Cloud Ltd | JP | unknown |
2408 | iexplore.exe | 85.115.52.220:80 | www.mailcontrol.com | Forcepoint Cloud Ltd | GB | unknown |
2816 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2816 | iexplore.exe | 23.216.77.44:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | suspicious |
2816 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
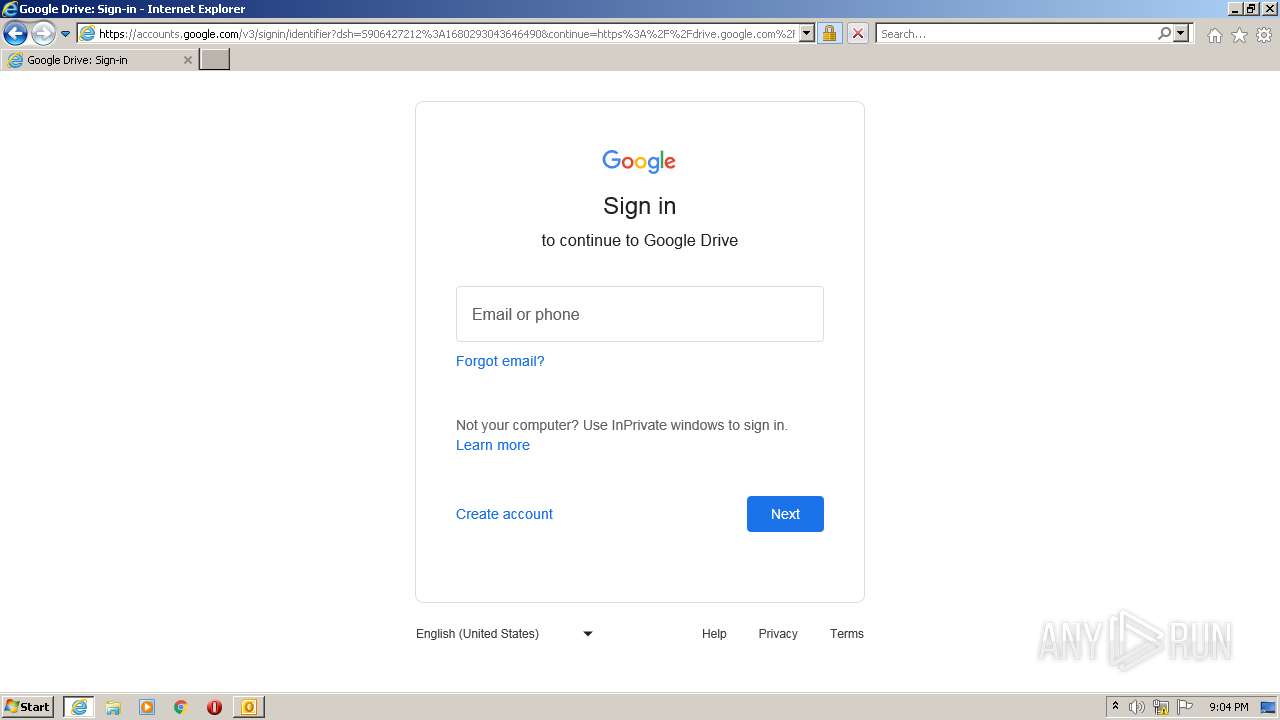
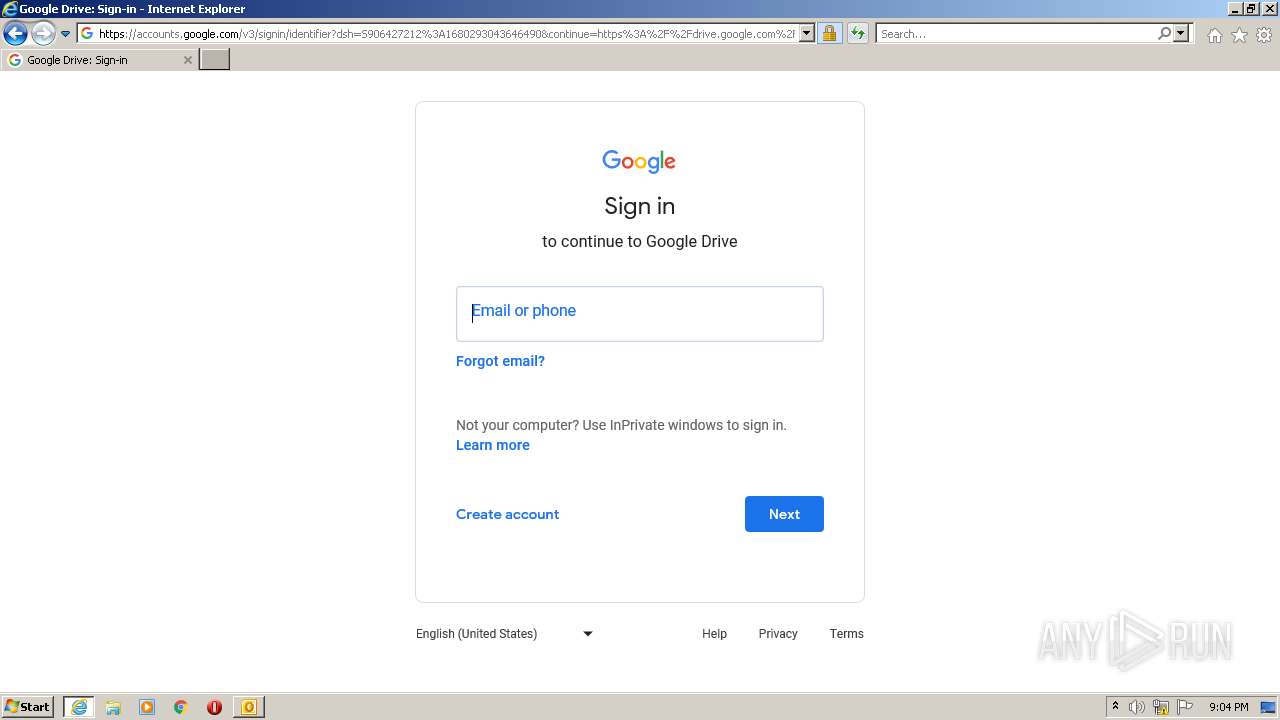
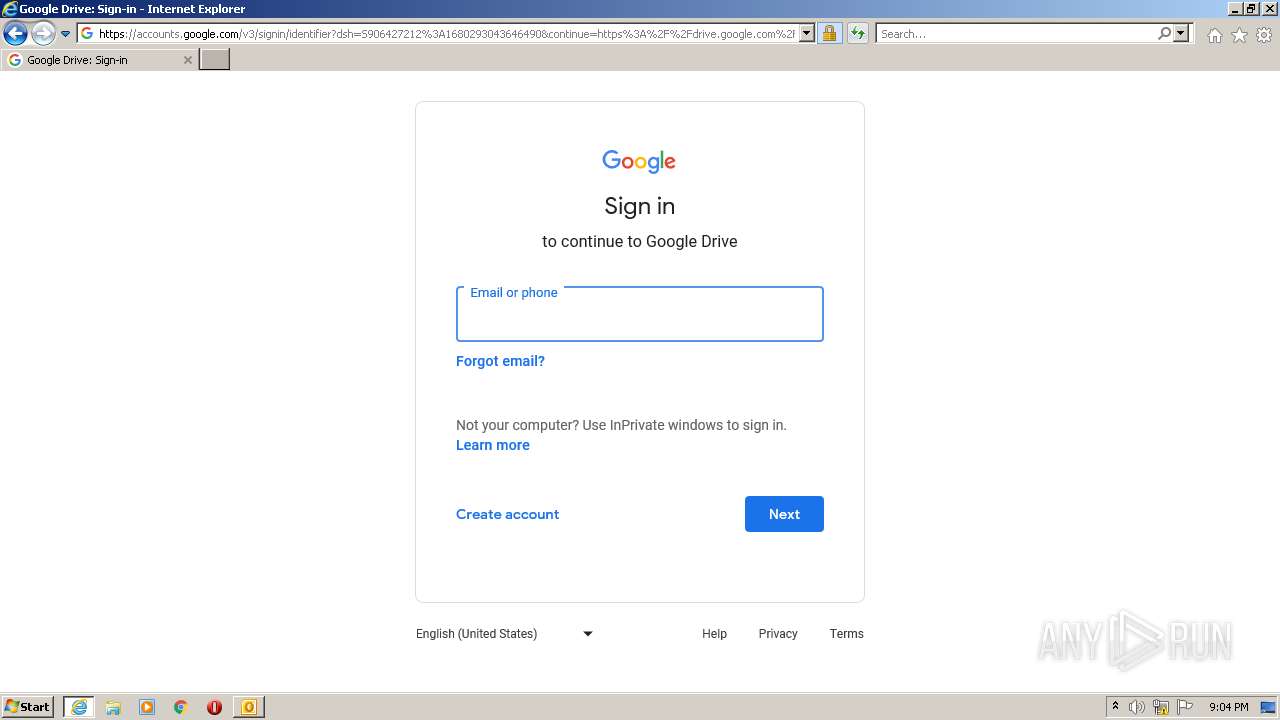
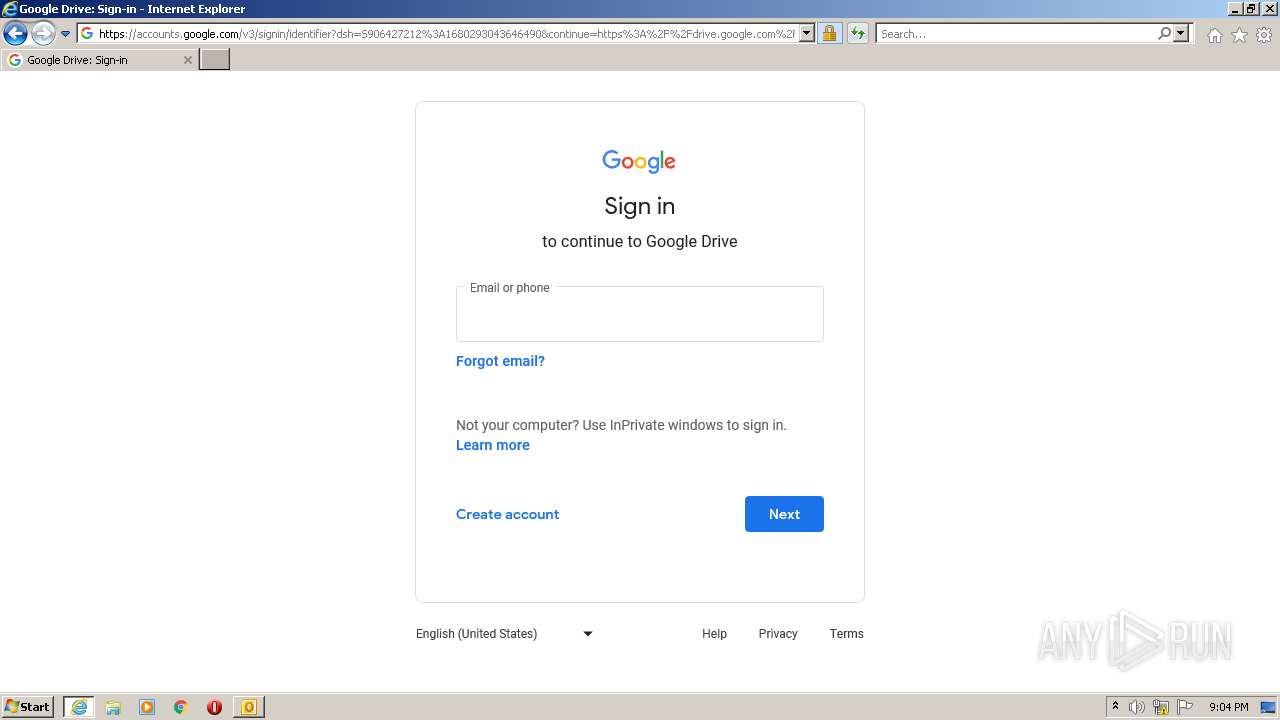
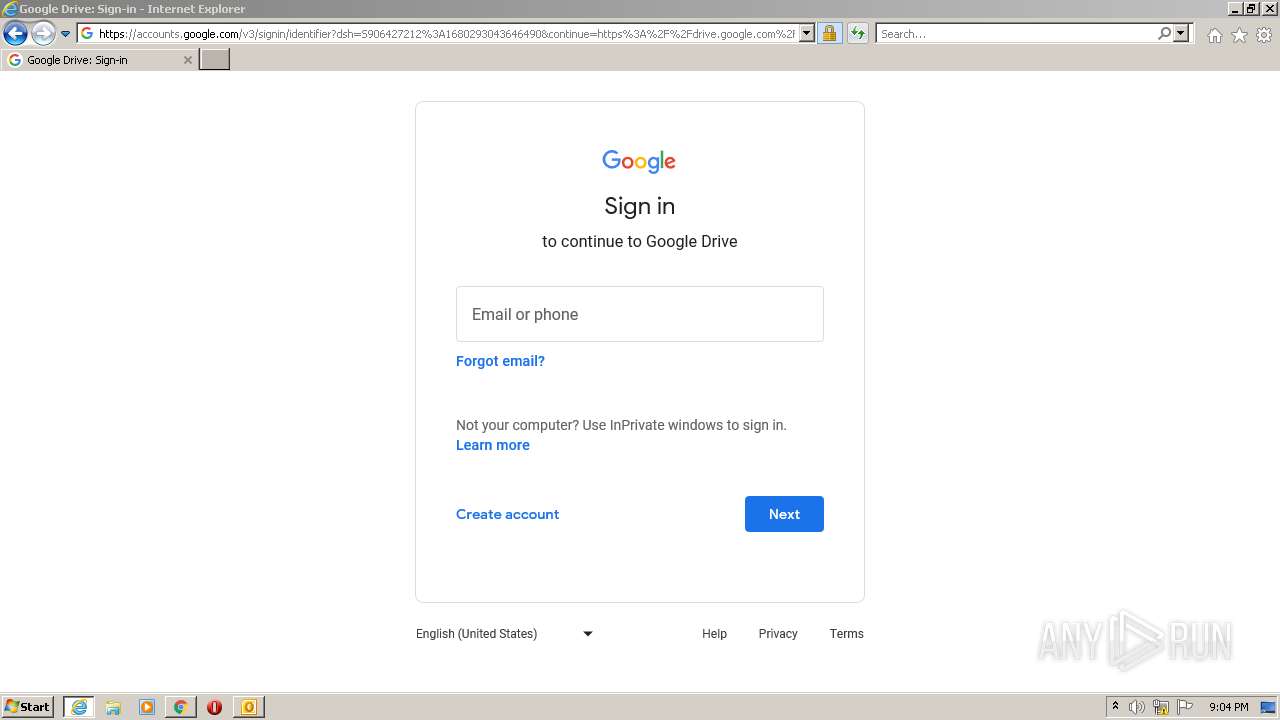
— | — | 142.250.185.109:443 | accounts.google.com | GOOGLE | US | suspicious |
2408 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2408 | iexplore.exe | 142.250.185.195:443 | www.gstatic.com | GOOGLE | US | whitelisted |
2408 | iexplore.exe | 142.250.186.35:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
dns.msftncsi.com |
| shared |
webdefence.global.blackspider.com |
| whitelisted |
www.mailcontrol.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
accounts.google.com |
| shared |
ocsp.pki.goog |
| whitelisted |