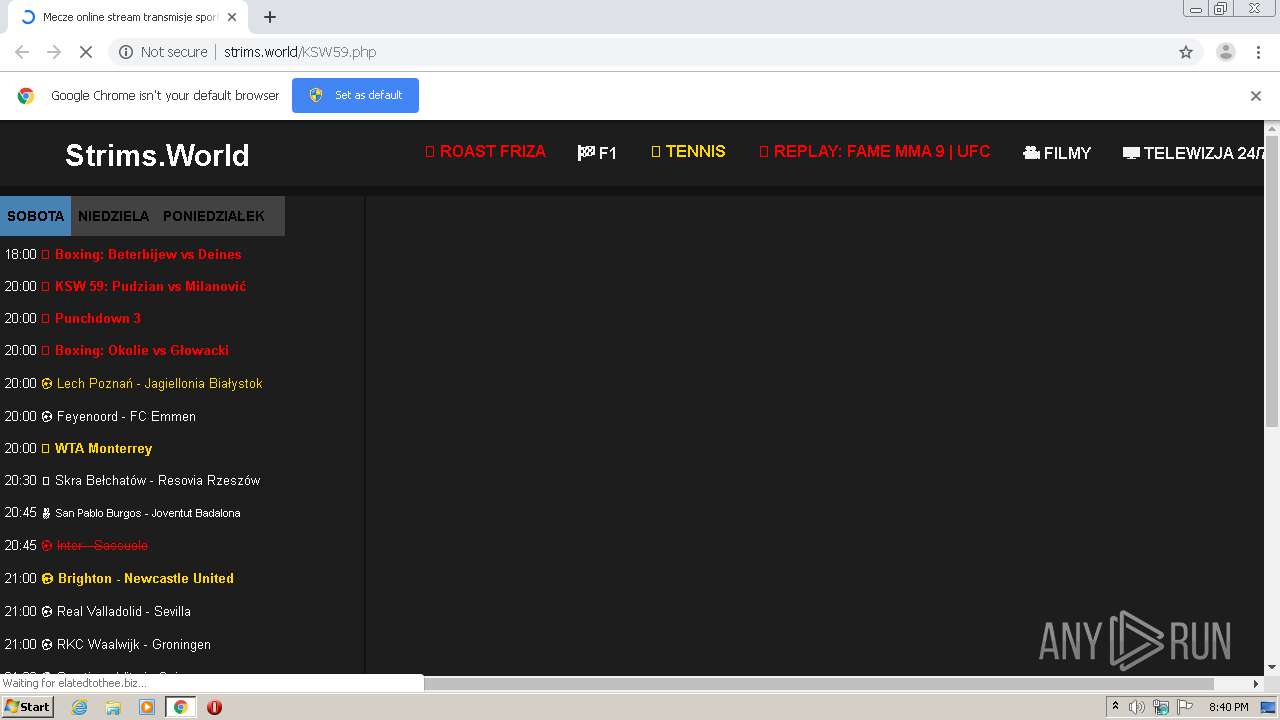
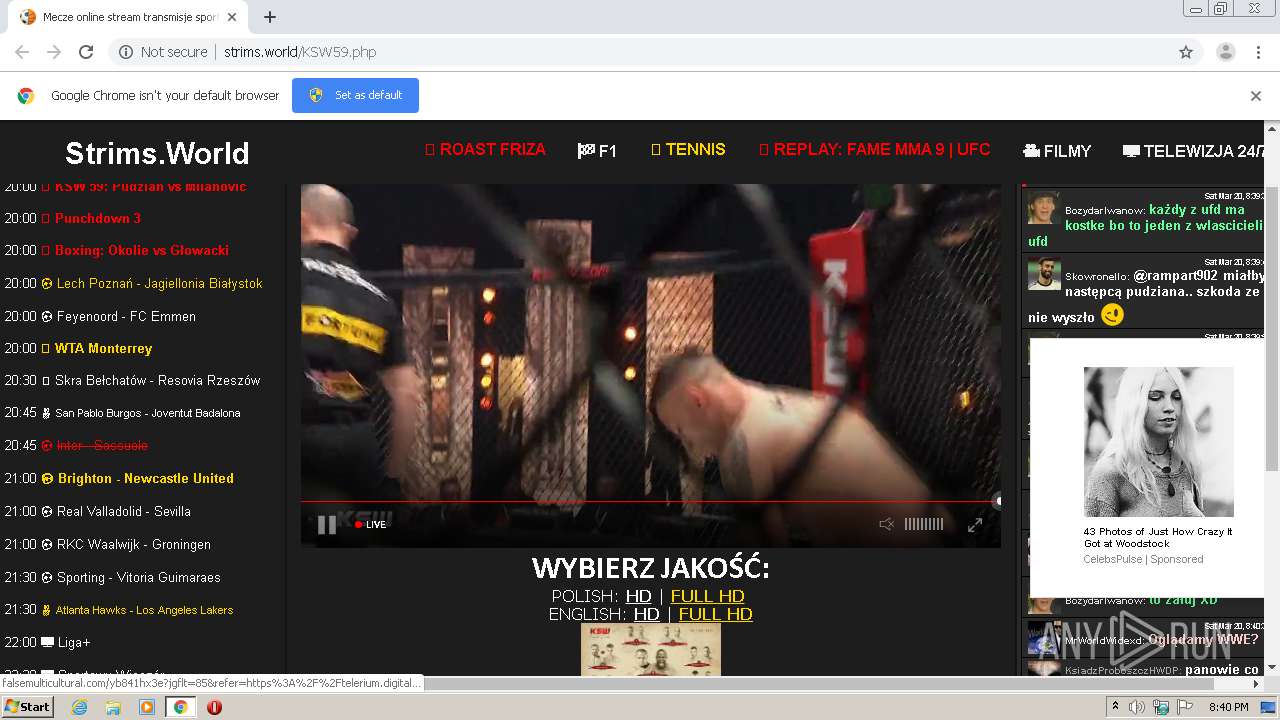
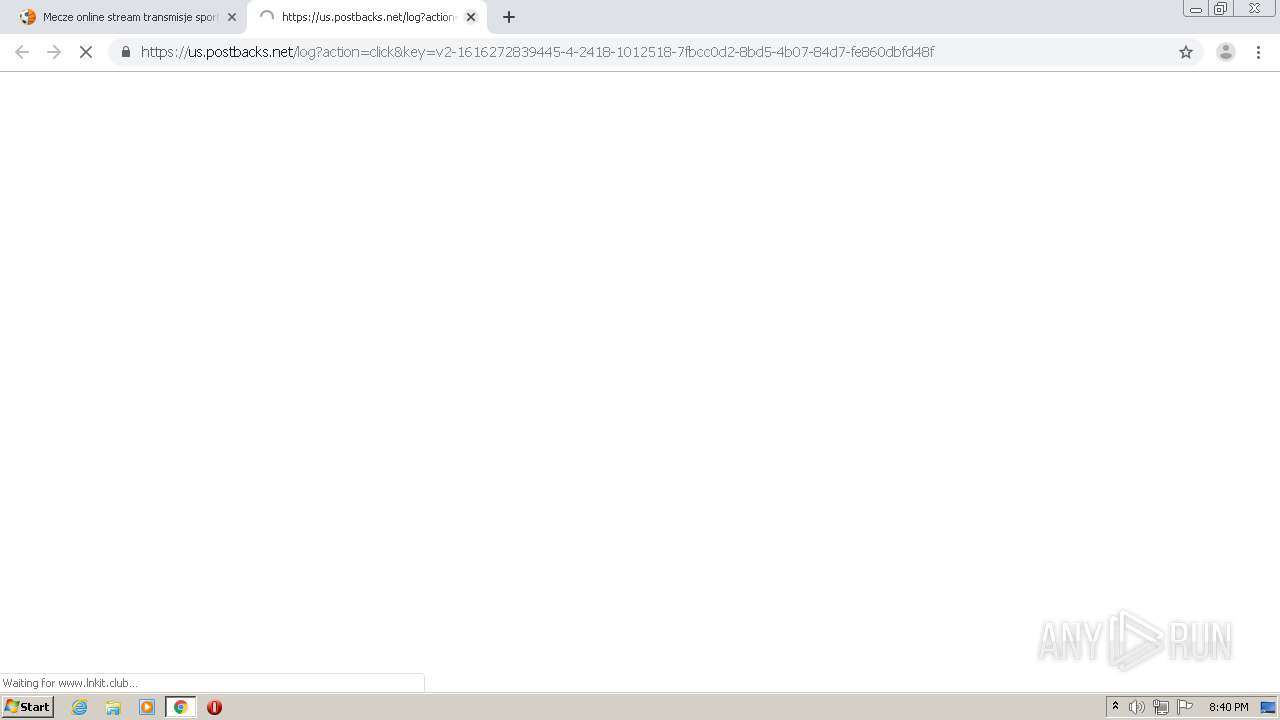
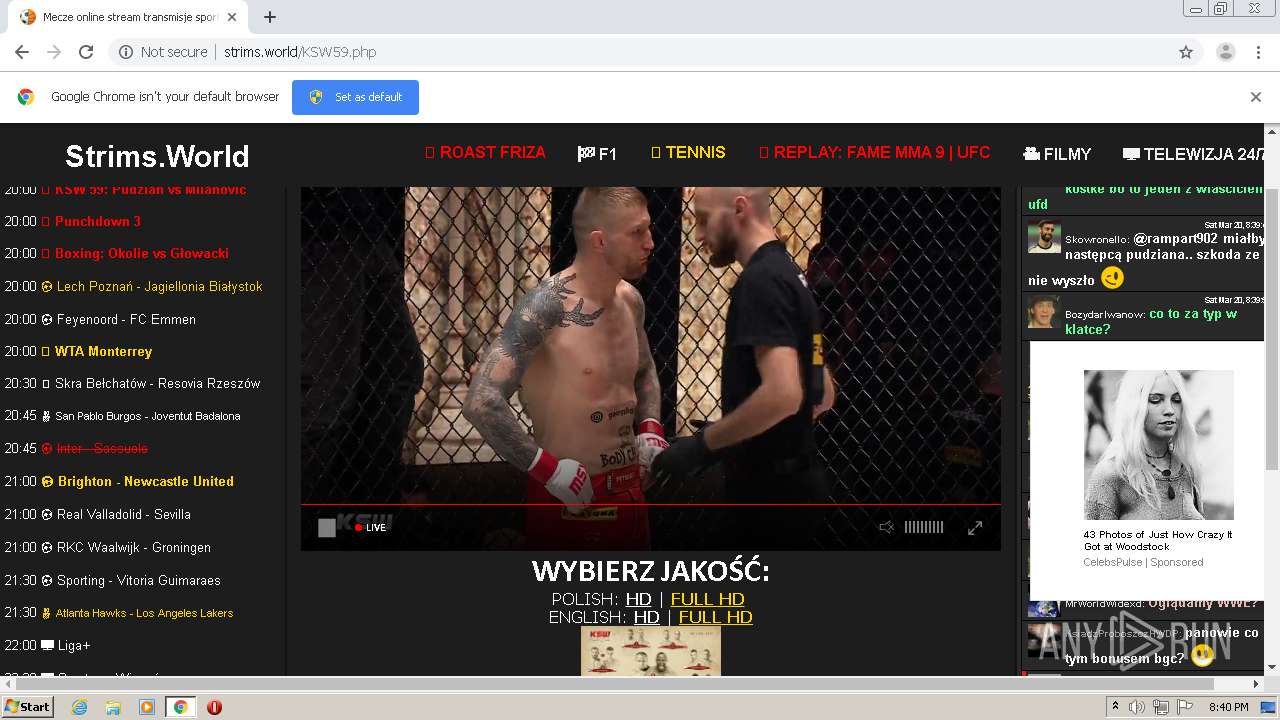
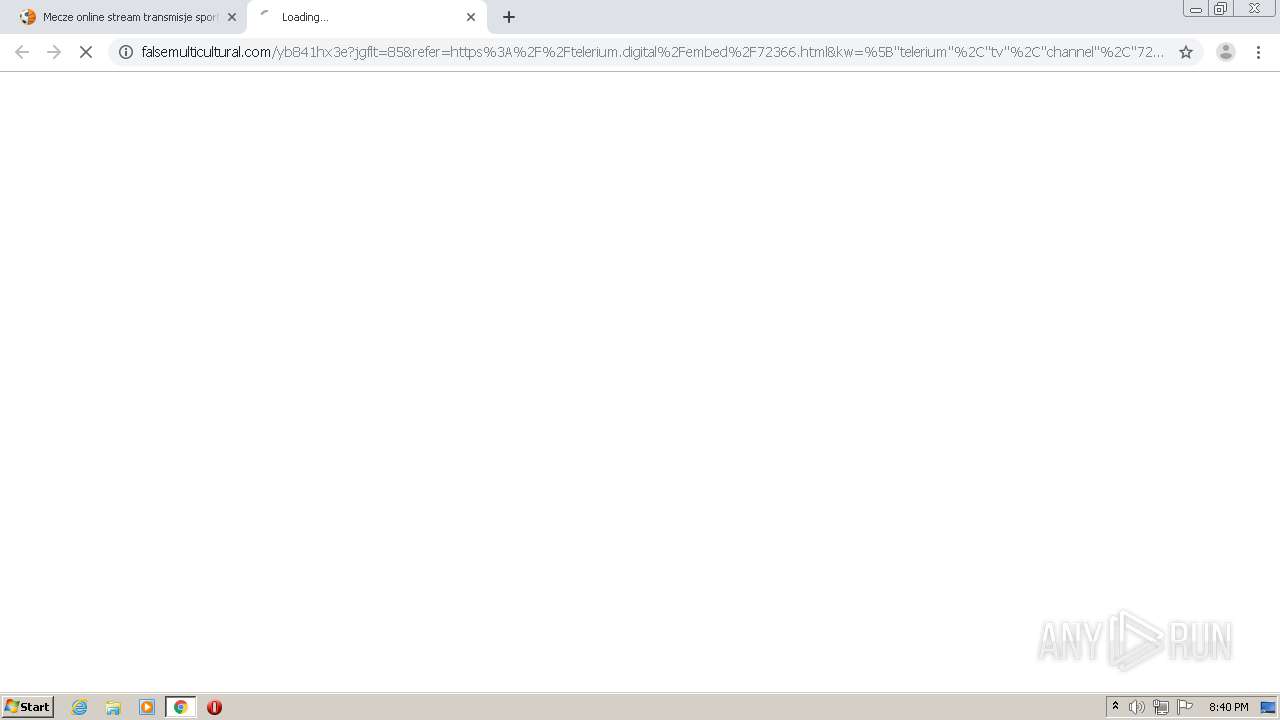
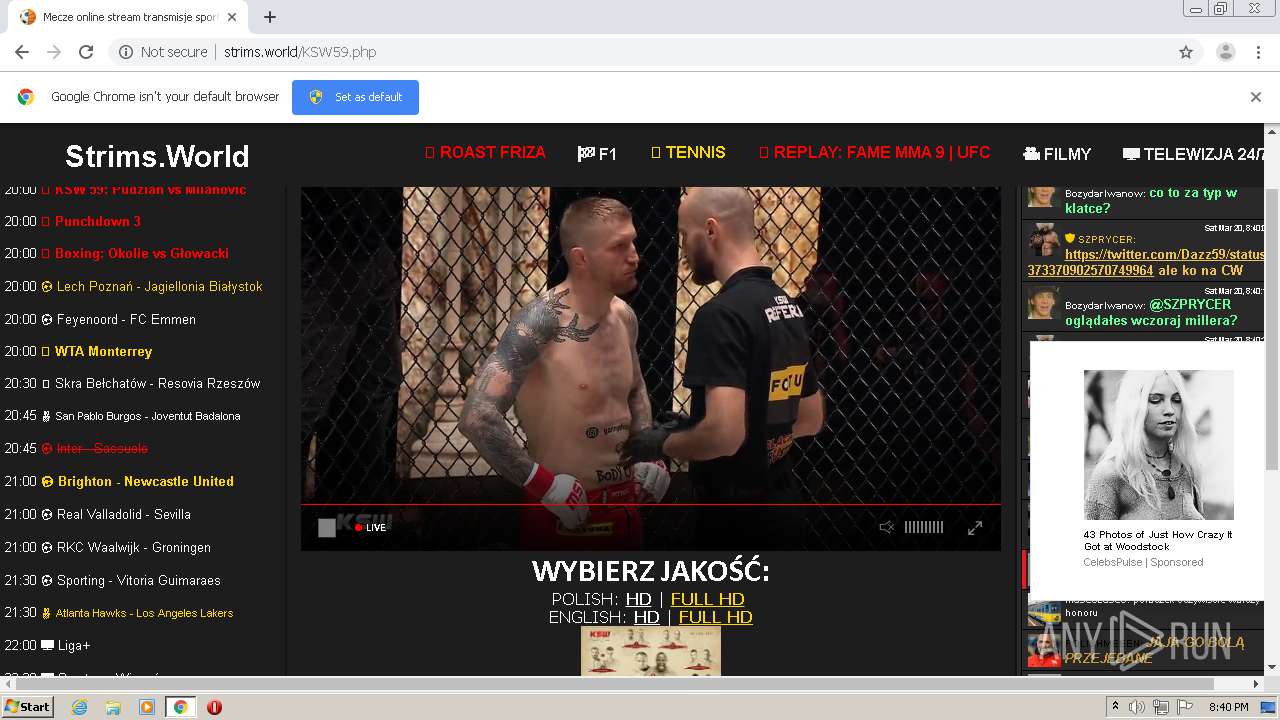
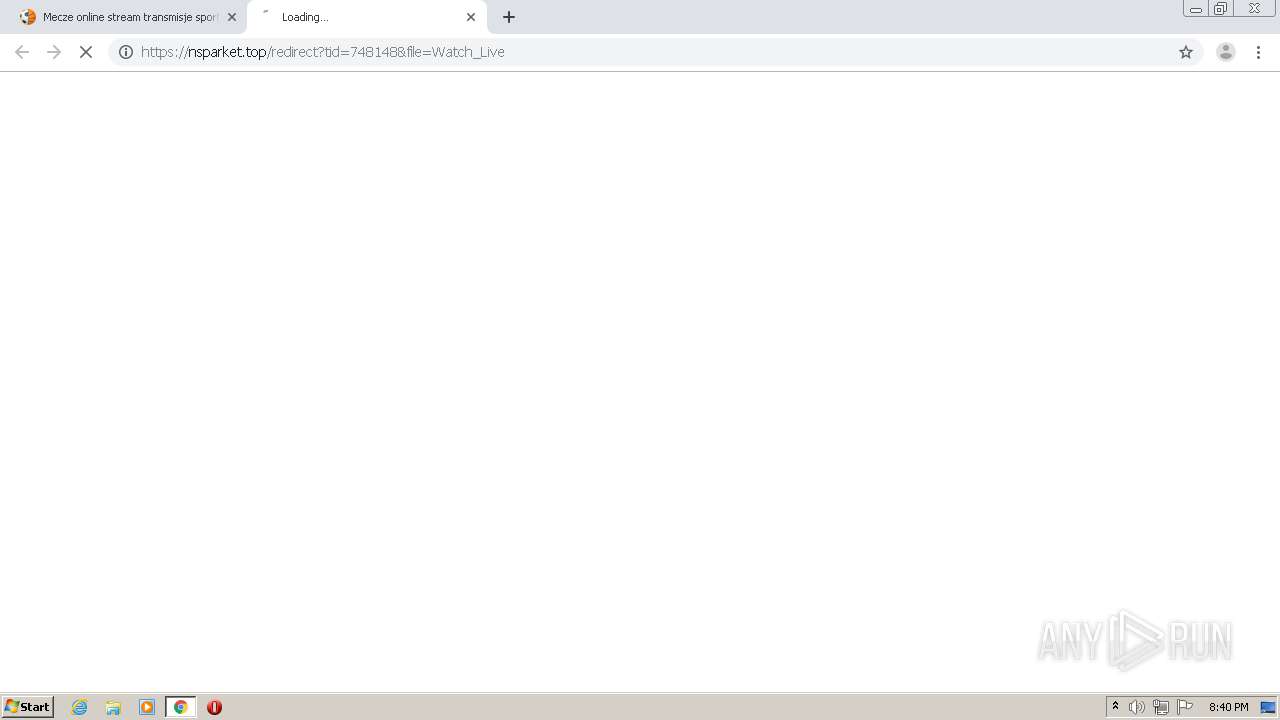
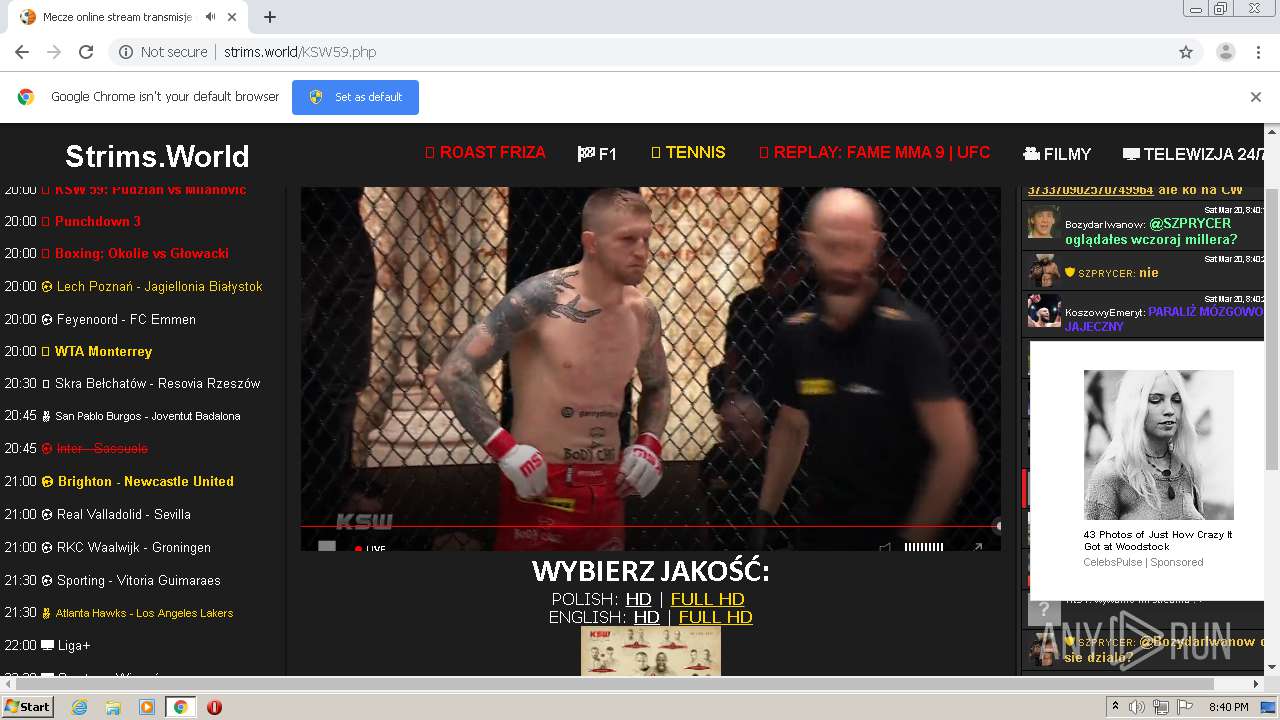
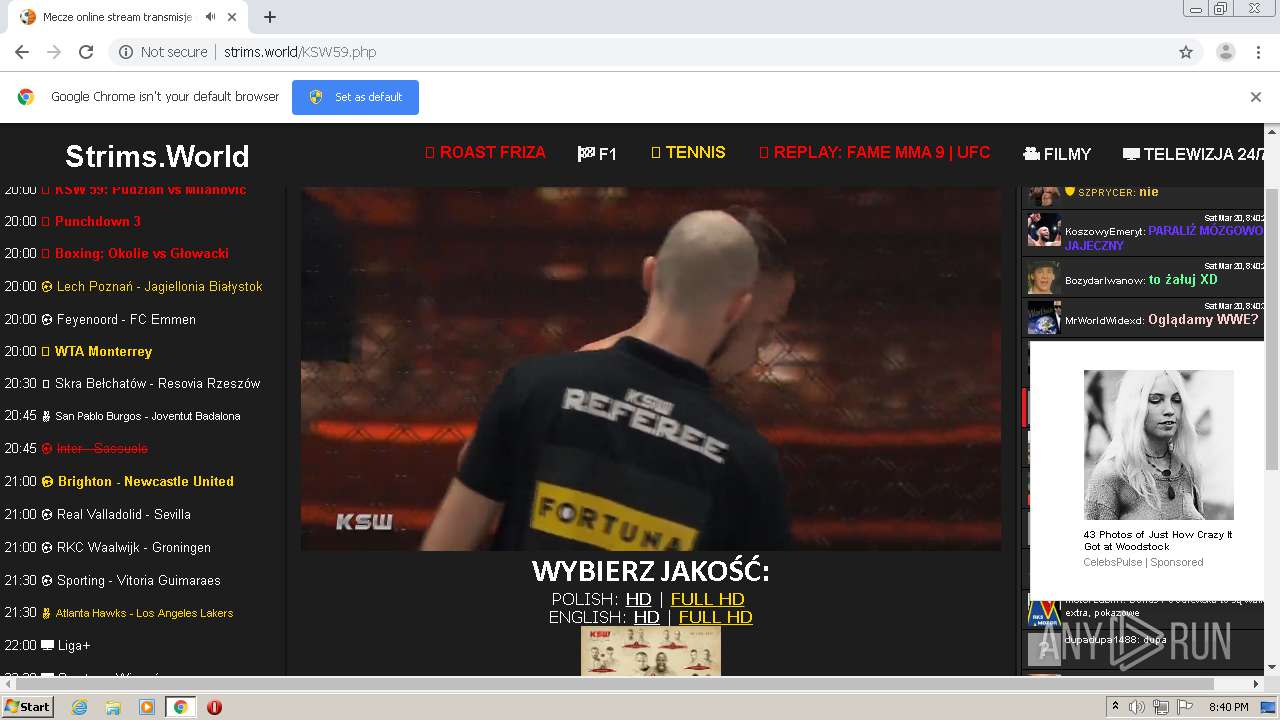
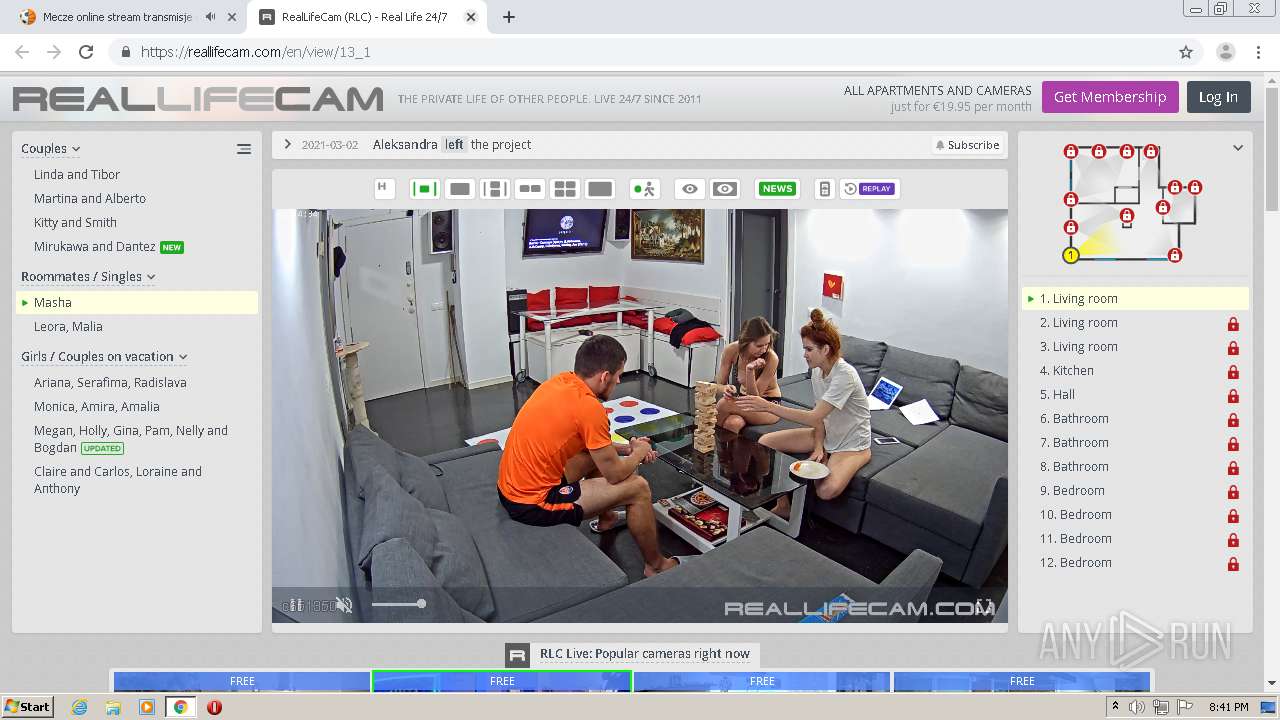
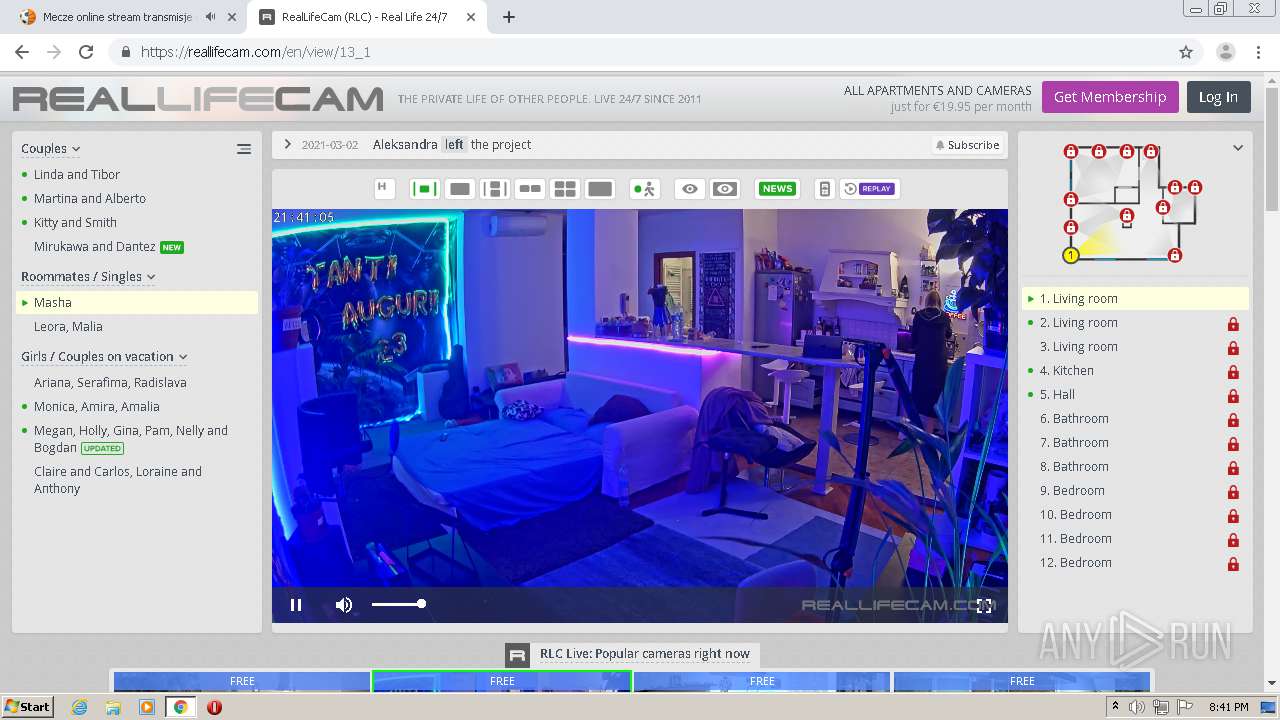
| URL: | http://strims.world/KSW59.php |
| Full analysis: | https://app.any.run/tasks/586049fc-f0e6-4877-b699-7785c416bdcb |
| Verdict: | Malicious activity |
| Analysis date: | March 20, 2021, 20:40:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EB615D283996B90A467D0580F203E876 |
| SHA1: | A26B260FC2F34A3B3FCCB323B5F34C565D21441D |
| SHA256: | C9DD5399FF30CEB540B412C9D03FBC6C334531CE86BDC44B0BA56100A2657432 |
| SSDEEP: | 3:N1KNR5WLcu7VHn:CFWT7Vn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2560)
Reads the hosts file
- chrome.exe (PID: 3964)
- chrome.exe (PID: 2560)
Creates files in the user directory
- chrome.exe (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1261982281044543278,5877926172767696434,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=889841527973869916 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1261982281044543278,5877926172767696434,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1302790601094560138 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1261982281044543278,5877926172767696434,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6260934335237458423 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3720 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,1261982281044543278,5877926172767696434,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9996737667994952335 --mojo-platform-channel-handle=1056 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1261982281044543278,5877926172767696434,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10543574544997679320 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1261982281044543278,5877926172767696434,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6020866356545937790 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1261982281044543278,5877926172767696434,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2219452948379614397 --mojo-platform-channel-handle=3596 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1261982281044543278,5877926172767696434,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4856243932316619488 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1261982281044543278,5877926172767696434,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9239540222217302667 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1261982281044543278,5877926172767696434,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6856314963880751479 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4092 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
664
Read events
586
Write events
75
Delete events
3
Modification events
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2560-13260746423980000 |
Value: 259 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
51
Text files
63
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60565DB8-A00.pma | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3ae8dc64-4116-46b9-aa8c-ff8cdda1f8da.tmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFcfd51.TMP | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFcff74.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
140
DNS requests
89
Threats
206
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3964 | chrome.exe | GET | 403 | 192.243.59.13:80 | http://allegianceenableselfish.com/a82271eaeede182919b6f1f1e8868825/invoke.js | US | — | — | malicious |
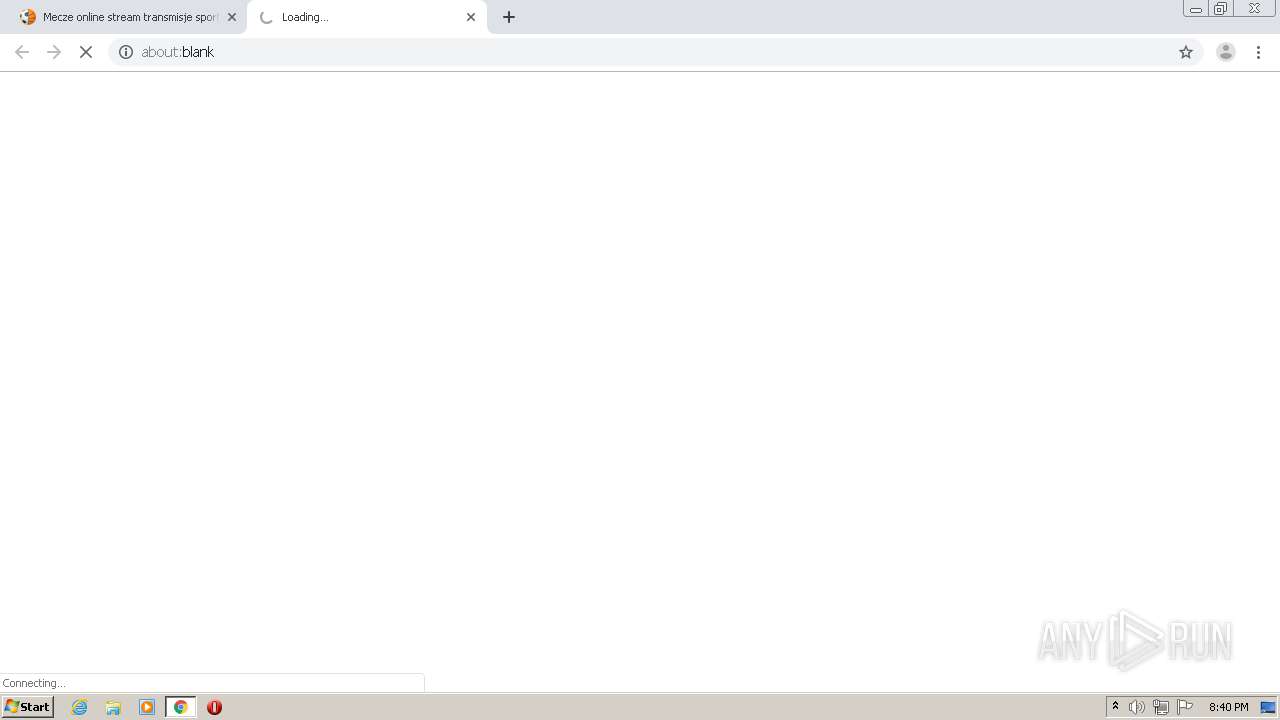
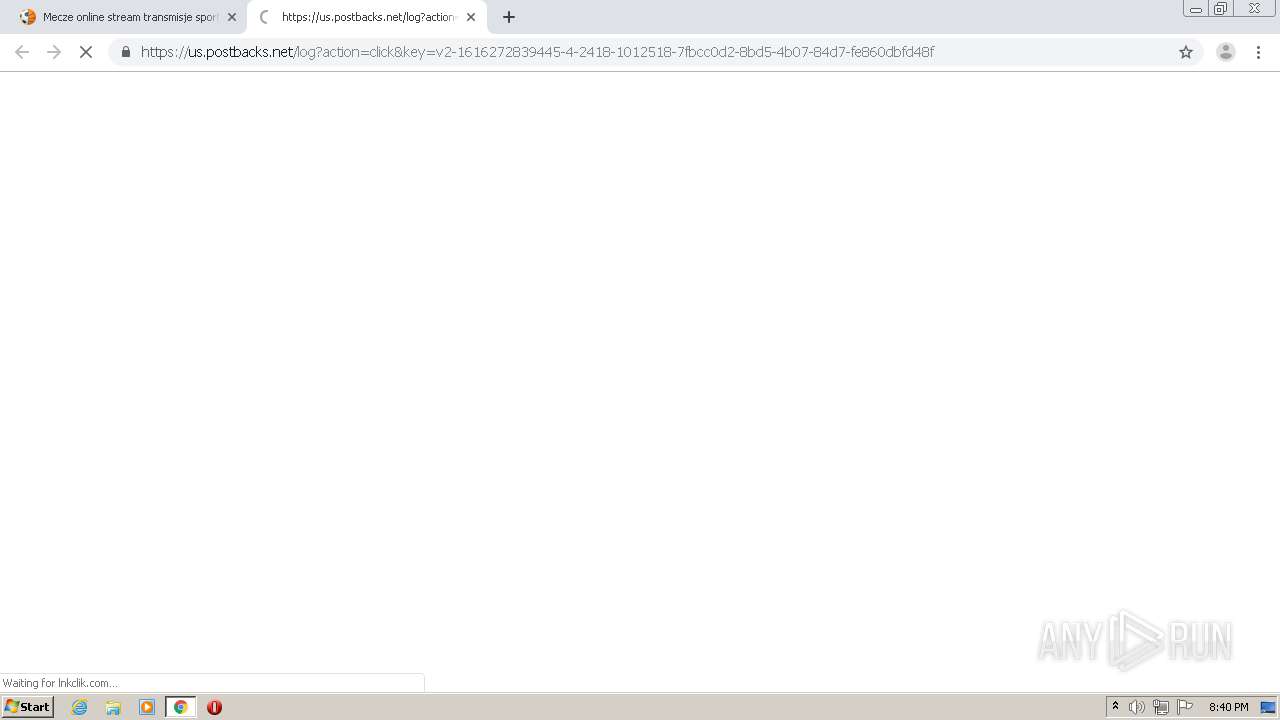
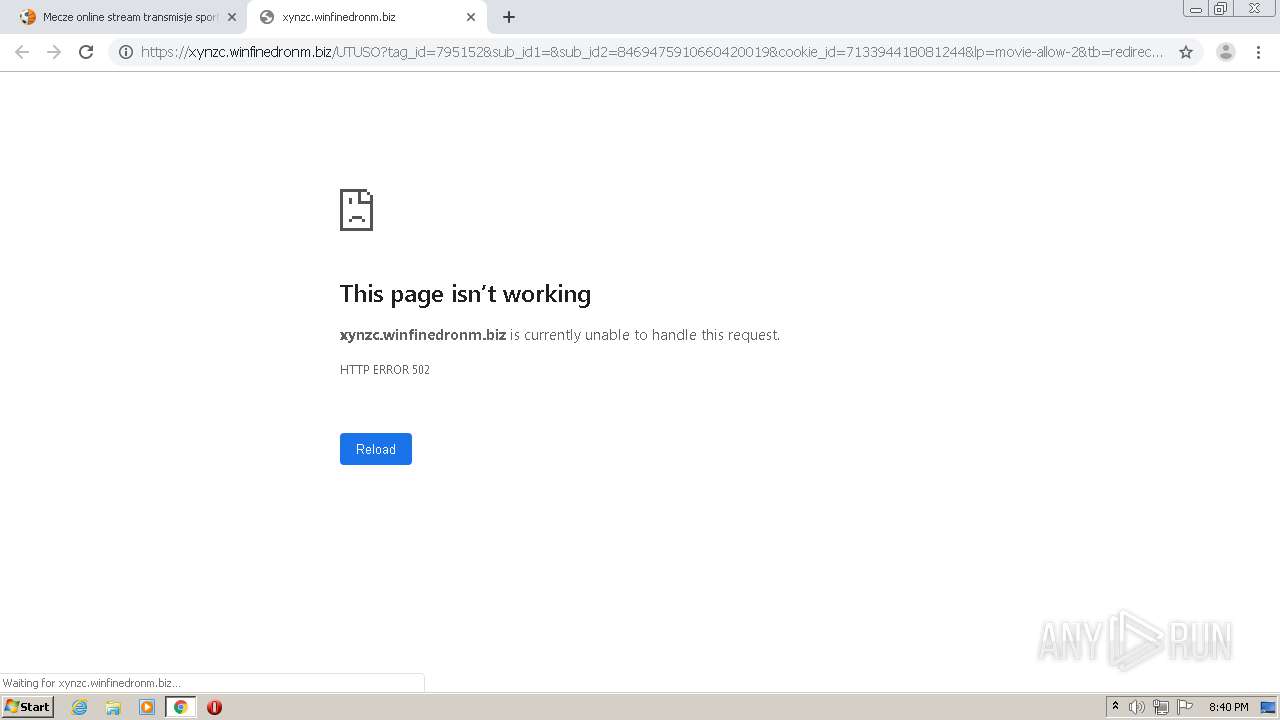
3964 | chrome.exe | GET | 301 | 104.21.88.55:80 | http://lnkclik.com/9JdI | US | — | — | suspicious |
3964 | chrome.exe | GET | 403 | 192.243.59.13:80 | http://allegianceenableselfish.com/976b1e62e885faae5585915805615ed0/invoke.js | US | — | — | malicious |
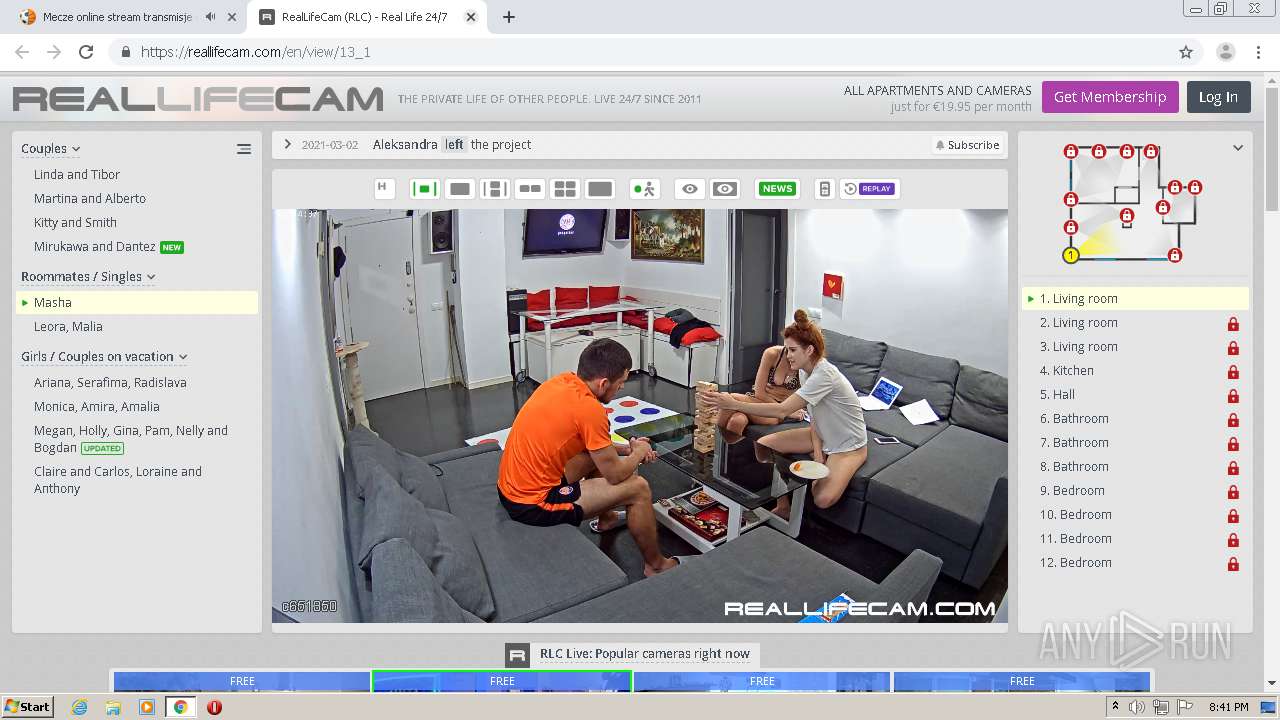
3964 | chrome.exe | GET | 200 | 45.148.121.138:80 | http://strims.world/layout/style.css?v=04012021 | unknown | text | 875 b | malicious |
3964 | chrome.exe | GET | 200 | 45.148.121.138:80 | http://strims.world/live/ramka.php | unknown | html | 490 b | malicious |
3964 | chrome.exe | GET | 200 | 65.9.67.61:80 | http://d36zfztxfflmqo.cloudfront.net/pWFNmcHI7PAgWTSw6Ak1FYWZXRUB+ORUfHChuLkYHKWs/IwEMdRIKFmVjQBwTNjRbVhc2MFtBVDk3BE1GficWHxllMQkeGy04EB8FMXUTEU81PBwZHjQyQ0I0bX1WVUBoexEZHDw8EQNXamMIBFdqY1BeQ3F2VEATKCMKFQU9MQ0ZBn1hIEVBb31VRldqY0-4bGiw+ClVAG3ZUQB4xOANVQGg0AxMZN3pDQkI7OxQfHz12VDZFbX1WXkFvZFZeQ2hjQ0JCKzIAEQAxdlQ2R2tkSENEfiZb | US | text | 607 b | whitelisted |
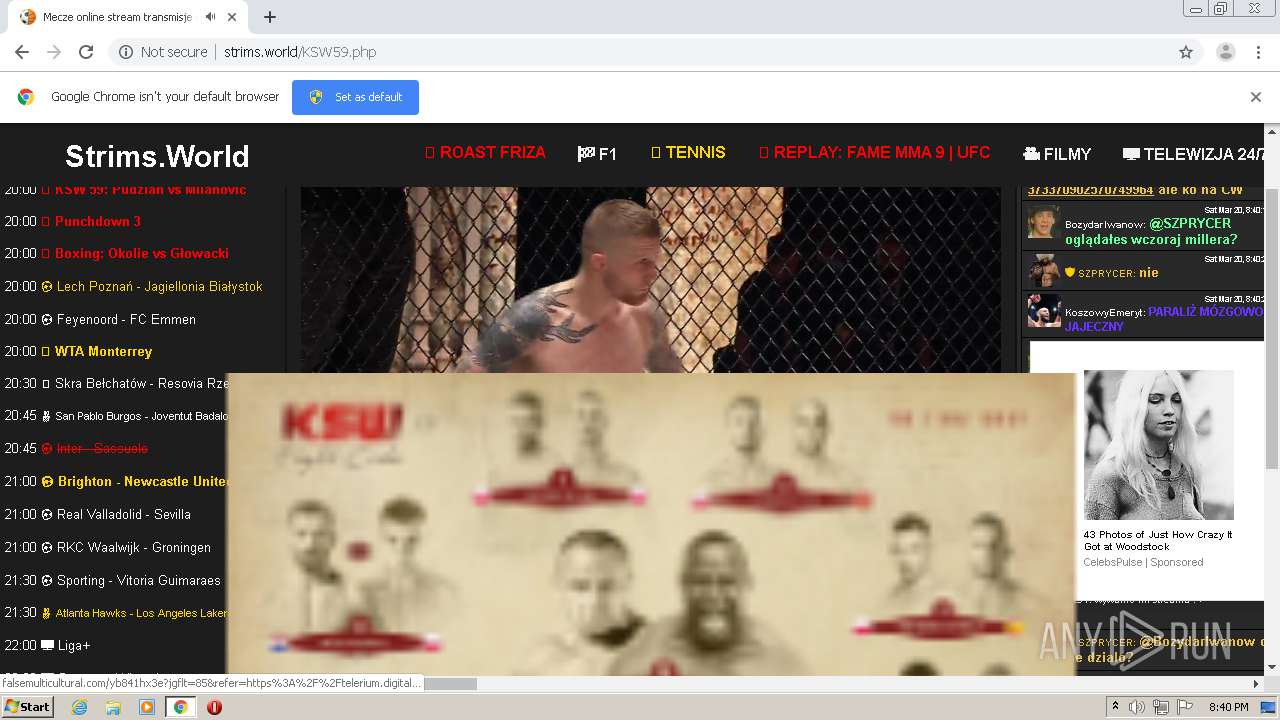
3964 | chrome.exe | GET | 200 | 192.243.59.13:80 | http://falsemulticultural.com/favicon.ico | US | compressed | 1.34 Kb | malicious |
3964 | chrome.exe | GET | 200 | 45.148.121.138:80 | http://strims.world/layout/chat.php | unknown | html | 1.86 Kb | malicious |
3964 | chrome.exe | GET | 200 | 99.84.158.89:80 | http://elatedtothee.biz/SEVGT3EpJyUiTil4JGkEOil7akMOYHQJFXtzPCkLPD0gKR0lNClhEiQqMysXOiooO18mIDJqQw4EIxgrJRMTIBALFCE1FRl1Fg4cIDwXGTsdHCh6FwwHE3k7CSkkAiUrfAIOBnANPH9UegcMGjAgCAR+Ex4rCyI2CSIELjY/JgUOJycgd3c5CS8ifCUdBBIBOSsQBR0GcA8uGjkZdyUCJQ0tESw5IA8SJzRwDwR/Ow0WHDkieRwPBiZxCRAjM38gdw01HgITPTIaHA0CNXgmBA5BcBUqNyQBAgR6JSMtEBZDcQkQJEVtdwQGFngJBSEzfAotASQSFh8eNRloCDgUDS4EDgsRLQAkSAwfdSAQDC0XeTswPQIZMwZ8EgoZHyB1Iz4dExx4FHgpER5DLHMFKBIJCwIoIBl0FxsXeDUUHDYSfR43PypjLDweJjV7GBM/MCwVOz8CBQ | US | compressed | 1.16 Kb | suspicious |
3964 | chrome.exe | GET | 200 | 65.9.67.61:80 | http://d36zfztxfflmqo.cloudfront.net/AeWZmVUoaCQgzdQ0PAmhyQVJUYn5fDBU6JAlbMTc9DAw8Hz0+JUAhMB1bVnMmGAgBaGwcCAVoe18HAjd3TUATNHcUCRw8JhUHQ2cMTEhWcHhJThE8JB0JESZvS1YIIW9LVlB7e1BDVGUrCRYKMD0cBA08PlxUIGB5TkhVY29LVk4+Ig0LCnB4OkNUZSYQDQ-NweEkBAzYhFk9DZ3oaDhQ6JxxDVBN9TEhWe3lOUVZ7e0lWQ2d6CgcANDgQQ1QTf0pRSGZ8XxNb | US | text | 187 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3964 | chrome.exe | 45.148.121.138:80 | strims.world | — | — | malicious |
3964 | chrome.exe | 142.250.185.202:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3964 | chrome.exe | 142.250.74.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3964 | chrome.exe | 142.250.185.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3964 | chrome.exe | 151.101.12.193:443 | i.imgur.com | Fastly | US | malicious |
3964 | chrome.exe | 151.101.2.109:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
3964 | chrome.exe | 65.9.67.61:80 | d36zfztxfflmqo.cloudfront.net | AT&T Services, Inc. | US | suspicious |
3964 | chrome.exe | 99.84.158.89:80 | elatedtothee.biz | AT&T Services, Inc. | US | suspicious |
3964 | chrome.exe | 65.9.58.120:80 | providentsopport.site | AT&T Services, Inc. | US | whitelisted |
3964 | chrome.exe | 67.199.248.10:443 | bit.ly | Bitly Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
strims.world |
| malicious |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
malinesmanses.com |
| suspicious |
d36zfztxfflmqo.cloudfront.net |
| whitelisted |
i.imgur.com |
| malicious |
cdn.jsdelivr.net |
| whitelisted |
bit.ly |
| shared |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .world TLD |
3964 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
3964 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
1040 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3964 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
3964 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
1040 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3964 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3964 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3964 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |