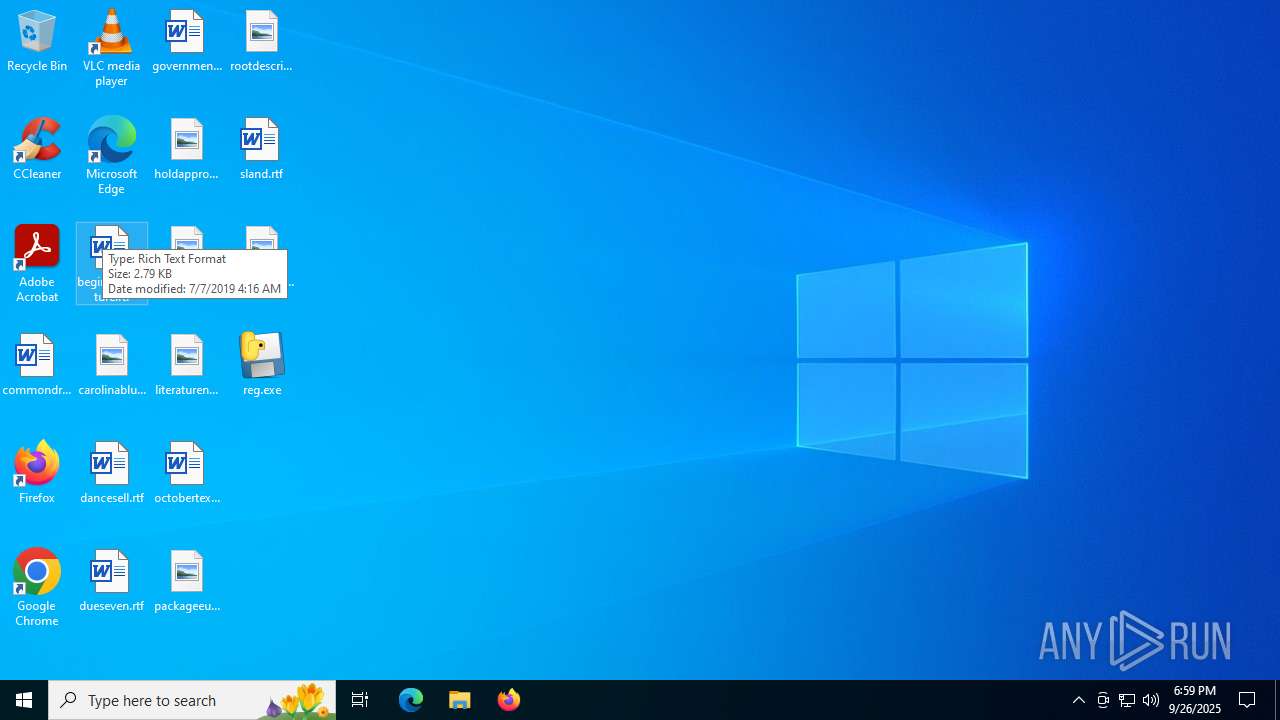
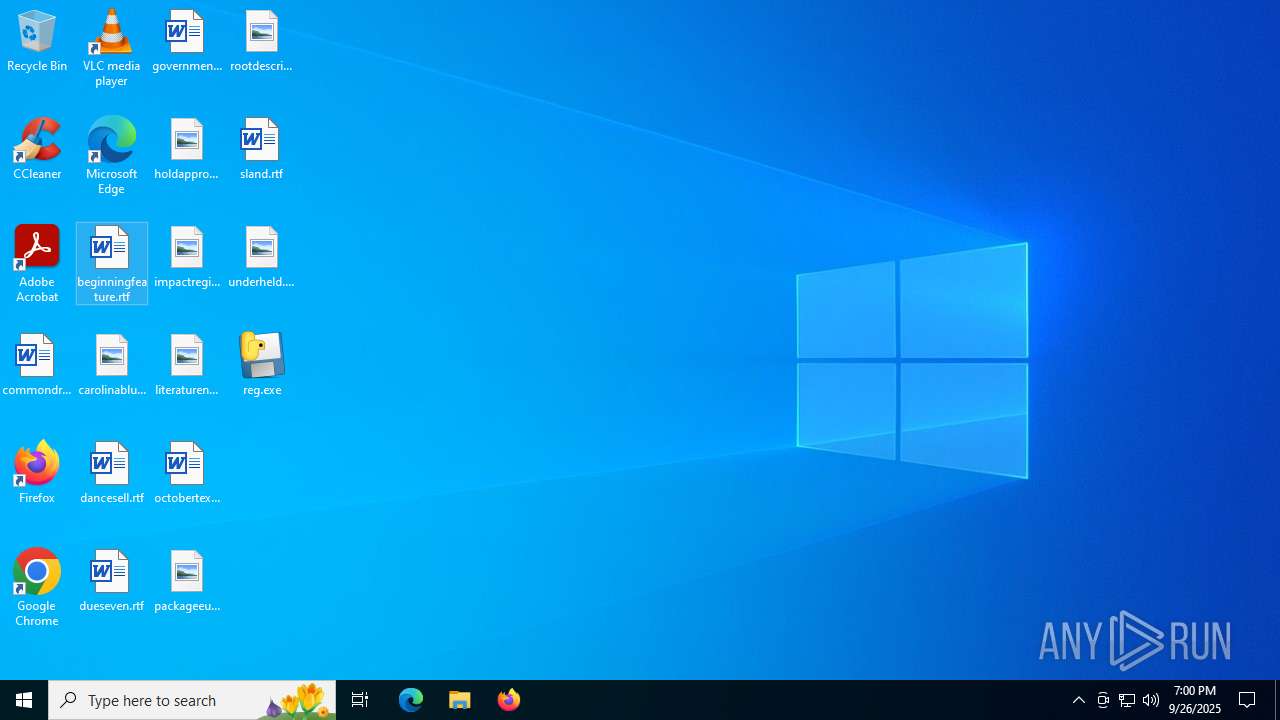
| File name: | reg.exe |
| Full analysis: | https://app.any.run/tasks/662d1a44-c029-4441-9c57-552e92c563a5 |
| Verdict: | Malicious activity |
| Analysis date: | September 26, 2025, 18:58:54 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 1A18043E1415ECDB77A7A25088835311 |
| SHA1: | 0CC441BCCF2AF817EB5DF6A962F4227B8C65DA9B |
| SHA256: | C9CCE8F686A40D8858BD7A38AB0ADFD86C797B161D67864BB9ED0FF6EB46D356 |
| SSDEEP: | 98304:OjHLXJZc5q1Zs3U0t1FWwif9+ZgET/RrBirC278nmOgr3m2/9bHA7/2F2Lq7nAFB:tQgTOnvw30881mwPaB+UsyZ3i7Qq |
MALICIOUS
Uses Task Scheduler to autorun other applications
- Windows-a24997.exe (PID: 4948)
- FateInjector.exe (PID: 2716)
SUSPICIOUS
Process drops python dynamic module
- reg.exe (PID: 6840)
Executable content was dropped or overwritten
- reg.exe (PID: 6840)
- Windows-a24997.exe (PID: 4948)
- reg.exe (PID: 6620)
Loads Python modules
- reg.exe (PID: 6620)
The process drops C-runtime libraries
- reg.exe (PID: 6840)
There is functionality for taking screenshot (YARA)
- reg.exe (PID: 6620)
- reg.exe (PID: 6840)
- FateInjector.exe (PID: 2716)
Process drops legitimate windows executable
- reg.exe (PID: 6840)
Reads security settings of Internet Explorer
- reg.exe (PID: 6620)
Application launched itself
- reg.exe (PID: 6840)
Probably fake Windows Update
- schtasks.exe (PID: 3672)
- schtasks.exe (PID: 4160)
Starts itself from another location
- Windows-a24997.exe (PID: 4948)
Reads the date of Windows installation
- reg.exe (PID: 6620)
Found regular expressions for crypto-addresses (YARA)
- FateInjector.exe (PID: 2716)
Connects to unusual port
- FateInjector.exe (PID: 2716)
INFO
Reads the computer name
- reg.exe (PID: 6840)
- reg.exe (PID: 6620)
- Windows-a24997.exe (PID: 4948)
- FateInjector.exe (PID: 2716)
- FateInjector.exe (PID: 5020)
Create files in a temporary directory
- reg.exe (PID: 6840)
- reg.exe (PID: 6620)
The sample compiled with english language support
- reg.exe (PID: 6840)
PyInstaller has been detected (YARA)
- reg.exe (PID: 6840)
- reg.exe (PID: 6620)
Process checks computer location settings
- reg.exe (PID: 6620)
Checks supported languages
- Windows-a24997.exe (PID: 4948)
- FateInjector.exe (PID: 2716)
- reg.exe (PID: 6840)
- reg.exe (PID: 6620)
- FateInjector.exe (PID: 5020)
Reads Environment values
- Windows-a24997.exe (PID: 4948)
- FateInjector.exe (PID: 2716)
- FateInjector.exe (PID: 5020)
Reads the machine GUID from the registry
- Windows-a24997.exe (PID: 4948)
- FateInjector.exe (PID: 2716)
- FateInjector.exe (PID: 5020)
Reads the software policy settings
- slui.exe (PID: 5988)
Checks proxy server information
- slui.exe (PID: 5988)
Manual execution by a user
- FateInjector.exe (PID: 5020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:09:26 18:58:01+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 179712 |
| InitializedDataSize: | 158208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xda30 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
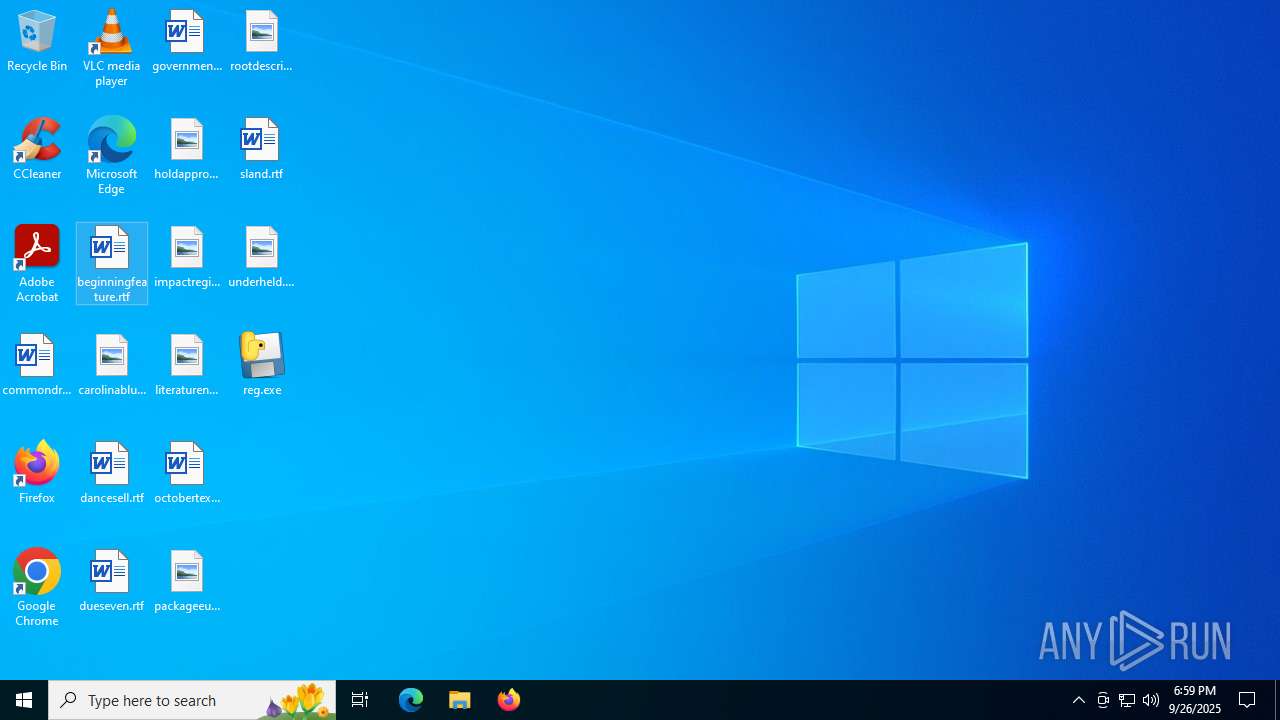
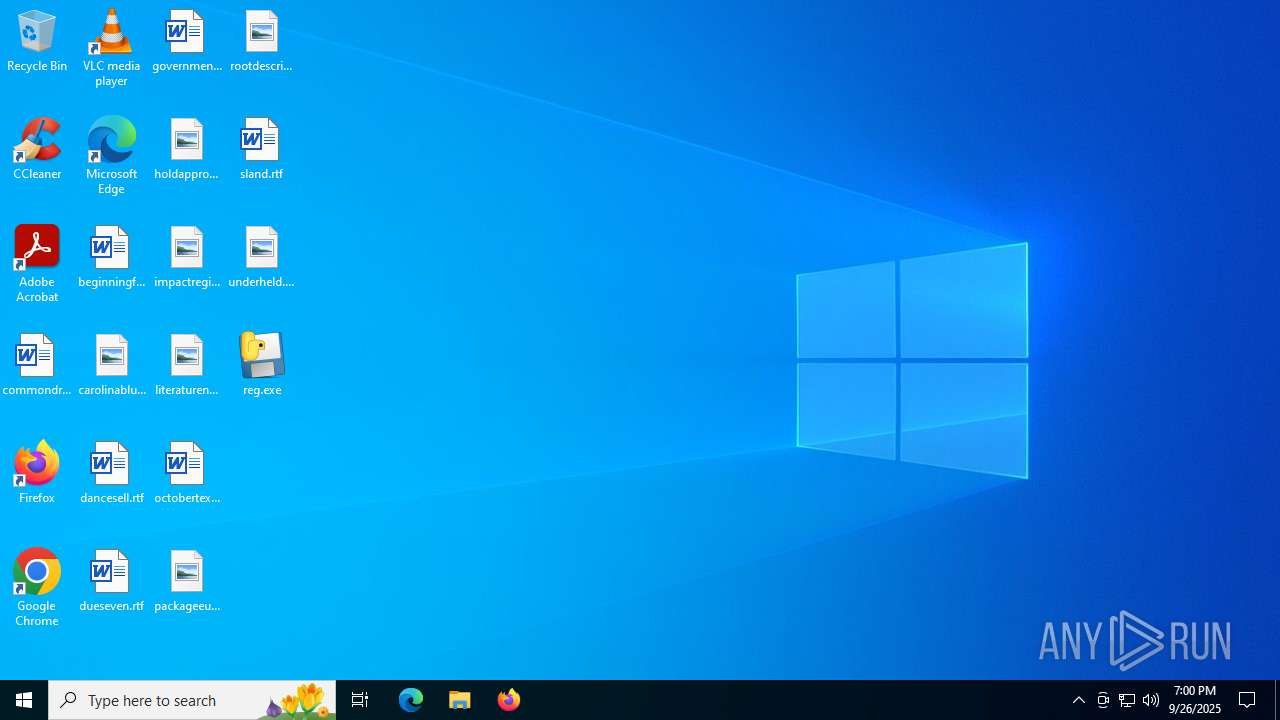
Total processes
143
Monitored processes
11
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1880 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2716 | "C:\WINDOWS\system32\SubDir\FateInjector.exe" | C:\Windows\System32\SubDir\FateInjector.exe | Windows-a24997.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.0.0.0 Modules
| |||||||||||||||
| 3672 | "schtasks" /create /tn "Windows Update" /sc ONLOGON /tr "C:\WINDOWS\system32\SubDir\FateInjector.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | Windows-a24997.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4160 | "schtasks" /create /tn "Windows Update" /sc ONLOGON /tr "C:\WINDOWS\system32\SubDir\FateInjector.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | FateInjector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4948 | "C:\Users\admin\AppData\Local\Temp\Windows\w_a24997\Windows-a24997.exe" | C:\Users\admin\AppData\Local\Temp\Windows\w_a24997\Windows-a24997.exe | reg.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5020 | C:\WINDOWS\system32\SubDir\FateInjector.exe | C:\Windows\System32\SubDir\FateInjector.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5504 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5988 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6620 | "C:\Users\admin\Desktop\reg.exe" | C:\Users\admin\Desktop\reg.exe | reg.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
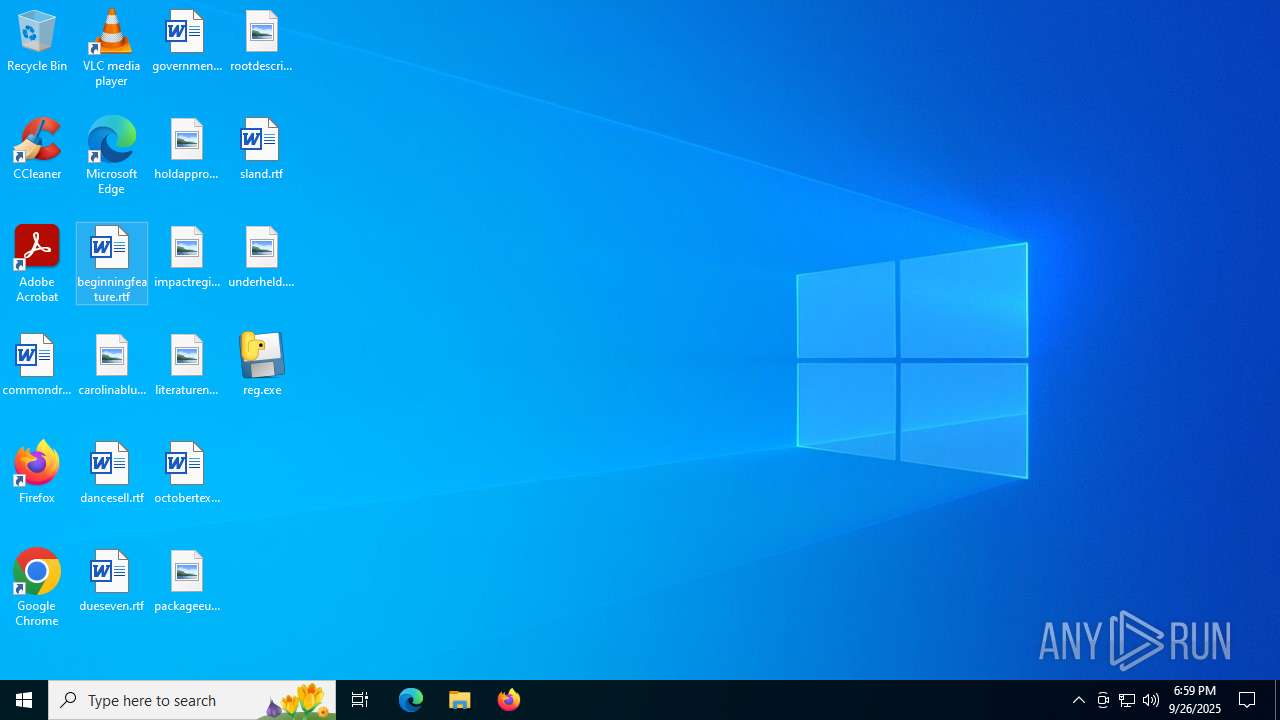
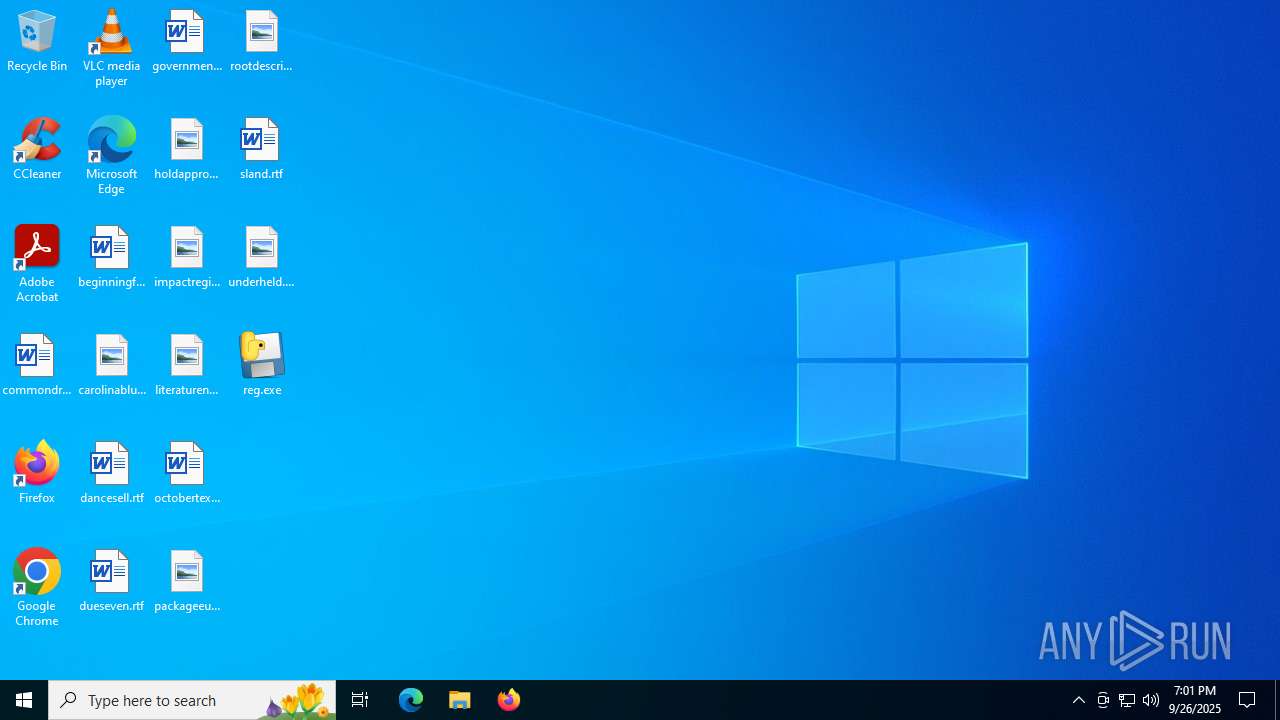
Total events
5 292
Read events
5 292
Write events
0
Delete events
0
Modification events
Executable files
109
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6840 | reg.exe | C:\Users\admin\AppData\Local\Temp\_MEI68402\Crypto\Cipher\_chacha20.pyd | executable | |
MD5:709BE56D3AE0CB50807A6B54A762C875 | SHA256:612B4DA235E04CB9CE0106A13AA31AB7D5F651A0685653EDC9A57E1F93BE5670 | |||
| 6840 | reg.exe | C:\Users\admin\AppData\Local\Temp\_MEI68402\Crypto\Cipher\_Salsa20.pyd | executable | |
MD5:17C99EDF022309BC2C54A732FB8FBF26 | SHA256:34EB9C505180358711D8D6268E3F0E700C58AC9F47B0AD68565ED73BAB5DBD81 | |||
| 6840 | reg.exe | C:\Users\admin\AppData\Local\Temp\_MEI68402\Crypto\Cipher\_raw_arc2.pyd | executable | |
MD5:530BB99610B35527C3B06A22FD92CCEC | SHA256:43BC2F864D062BF7FE940E9CC497EF4FDFCC6EAEAB95FD4D4EE837E4D5DE0437 | |||
| 6840 | reg.exe | C:\Users\admin\AppData\Local\Temp\_MEI68402\Crypto\Cipher\_raw_cast.pyd | executable | |
MD5:C5ECF284E05E75955A40E1276C9B250D | SHA256:3F65302BA35C1FF1F9A9BE9C5C5300A66B1BC4577E444B3EEE738FA7177135D4 | |||
| 6840 | reg.exe | C:\Users\admin\AppData\Local\Temp\_MEI68402\Crypto\Cipher\_raw_aesni.pyd | executable | |
MD5:133B156E060C77AF41B38841A32DA4B6 | SHA256:20005B988FE848983A65F7F4727EC27148E4D0ABEAB9CFD0E58778F812BF7595 | |||
| 6840 | reg.exe | C:\Users\admin\AppData\Local\Temp\_MEI68402\Crypto\Cipher\_ARC4.pyd | executable | |
MD5:EFF0F16D6E853EA2CBC7B3BCAB5E0591 | SHA256:9892A83A3E511BD1024BFCCE460DBDE2690FD2A3C0C449081950C40EFDBA4C7D | |||
| 6840 | reg.exe | C:\Users\admin\AppData\Local\Temp\_MEI68402\Crypto\Cipher\_raw_blowfish.pyd | executable | |
MD5:403A4F70938F58C15DAEB4A63D7ECADB | SHA256:FB407812E3E4D17B2CA981C8B95C716FF1B288A5E4658A831CD067A2837A753B | |||
| 6840 | reg.exe | C:\Users\admin\AppData\Local\Temp\_MEI68402\Crypto\Cipher\_raw_des3.pyd | executable | |
MD5:494239F9453679D80511BECC23C6B621 | SHA256:9C849A1DD641A3143C25B261E18D8F1453B00BB975E324384F15311C1B544F3D | |||
| 6840 | reg.exe | C:\Users\admin\AppData\Local\Temp\_MEI68402\Crypto\Cipher\_raw_eksblowfish.pyd | executable | |
MD5:B6037CEAA162C50FC25F1B361B4250C9 | SHA256:605AECF52ACD7D17B7B1000AEEDEE6C0601D6BC5F753756E7EE70A83F44FCCB2 | |||
| 6840 | reg.exe | C:\Users\admin\AppData\Local\Temp\_MEI68402\Crypto\Cipher\_raw_ecb.pyd | executable | |
MD5:B9F8151C65BDAF81BF9407A32E77959B | SHA256:ED154E6C22235659E57532B0A8B3CD7A081603C6CAE9CB165E436006881C1C74 | |||
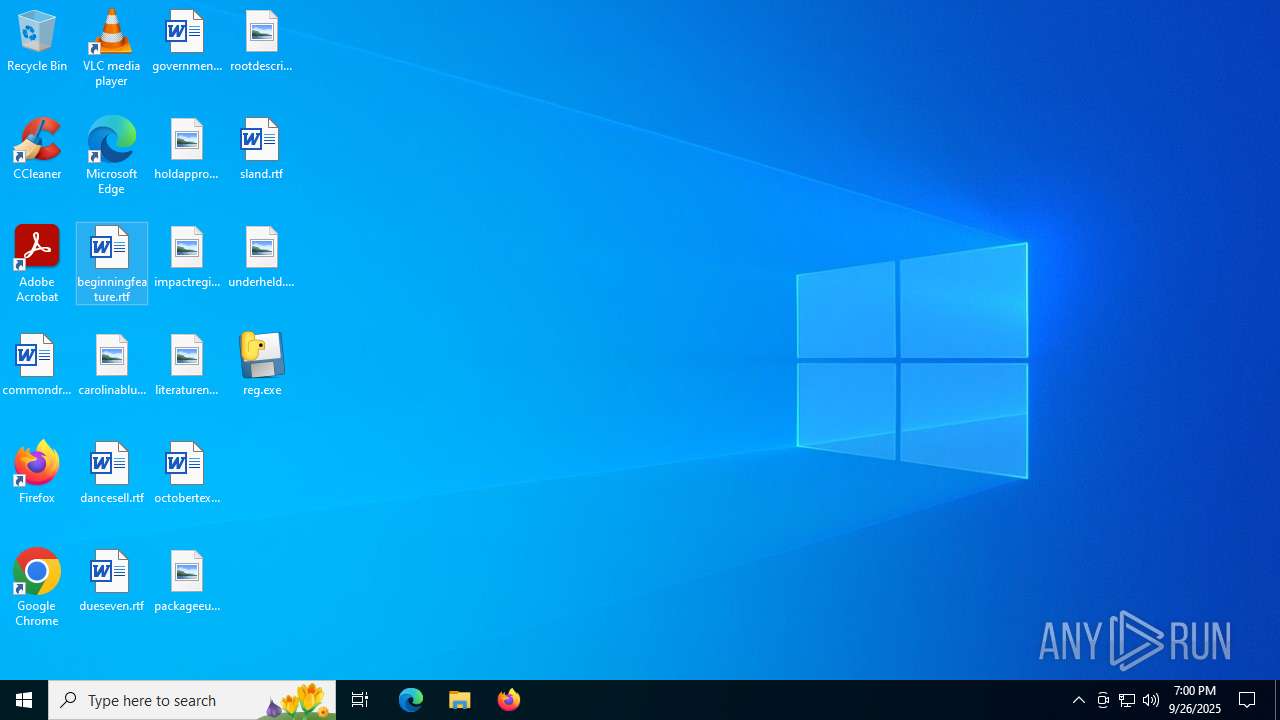
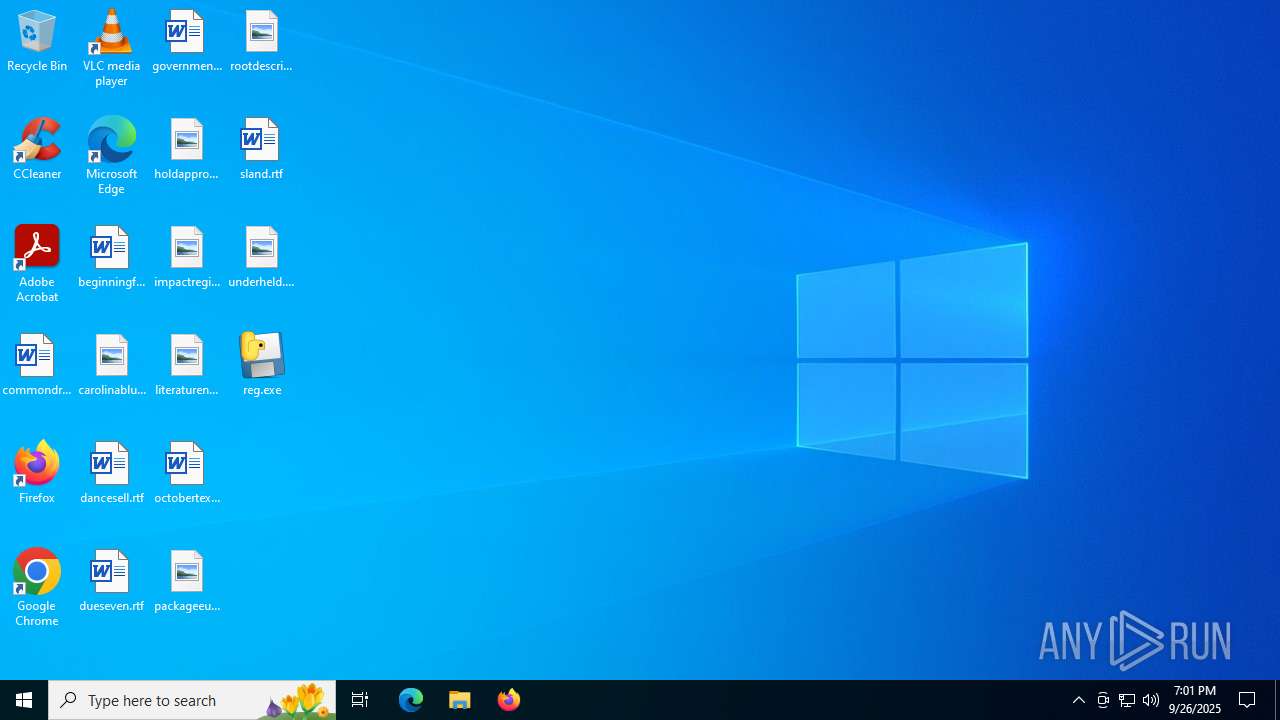
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
61
DNS requests
20
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5504 | RUXIMICS.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 400 | 20.190.160.2:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | unknown |
— | — | POST | 200 | 20.190.160.2:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | unknown |
— | — | POST | 400 | 20.190.160.132:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 204 b | unknown |
— | — | POST | 400 | 40.126.32.68:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | — | 203 b | unknown |
— | — | POST | 400 | 40.126.32.72:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | unknown |
— | — | POST | 400 | 40.126.32.72:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5504 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5504 | RUXIMICS.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5504 | RUXIMICS.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
insurance-scuba.gl.at.ply.gg |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2200 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2200 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2200 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |