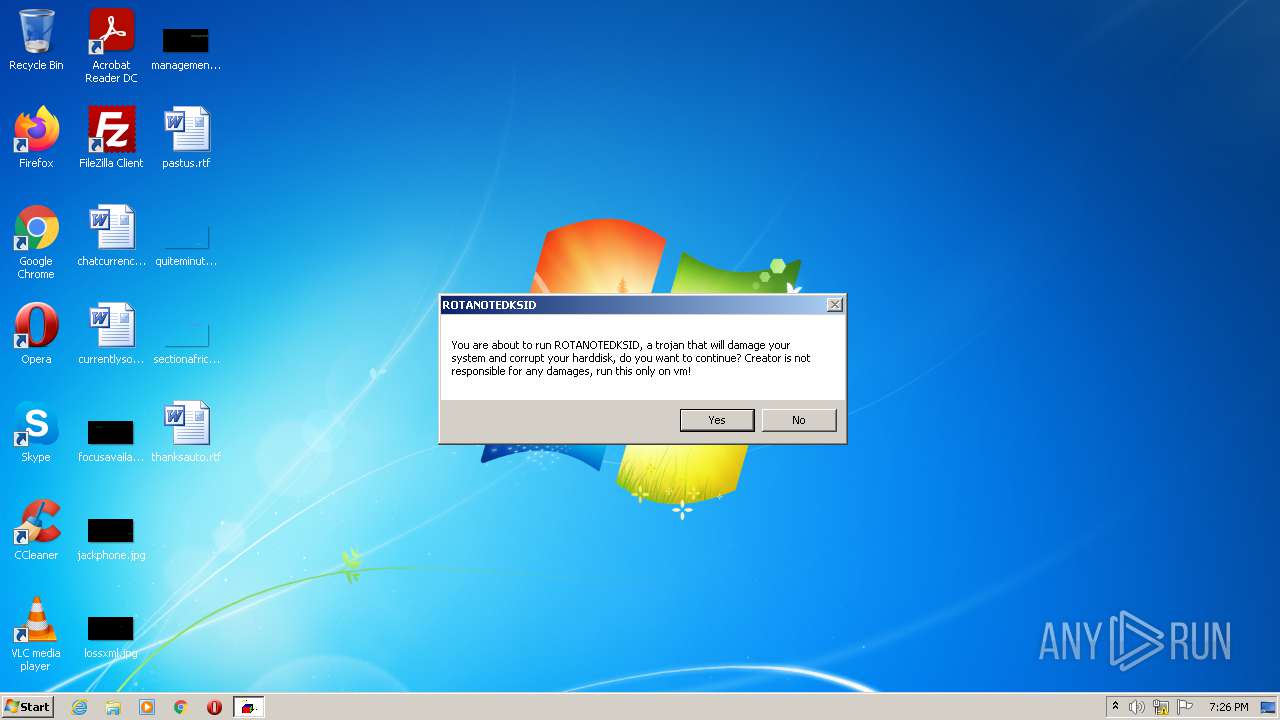
| download: | ROTANOTEDKSID-Destructive.exe |
| Full analysis: | https://app.any.run/tasks/f99b2bd3-c989-4fc8-ab2f-16b058e8a1fe |
| Verdict: | Malicious activity |
| Analysis date: | October 13, 2021, 18:26:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8B93E46A7E9E681B2124FFE7647BBBA1 |
| SHA1: | DEE59152E78DE697F1D23B350CD0F1E14B648960 |
| SHA256: | C9B88B16D87992287EF72834BAE3AC45DB9EBA4E32DCC8DB4756BF6349D97A25 |
| SSDEEP: | 393216:3bAOuHdROJY4gVM5RdxEK1iLXXEhkrzu2WXJcC8d9SkdOt:3sOg0Y4qM5RXEKWNjWKCc/o |
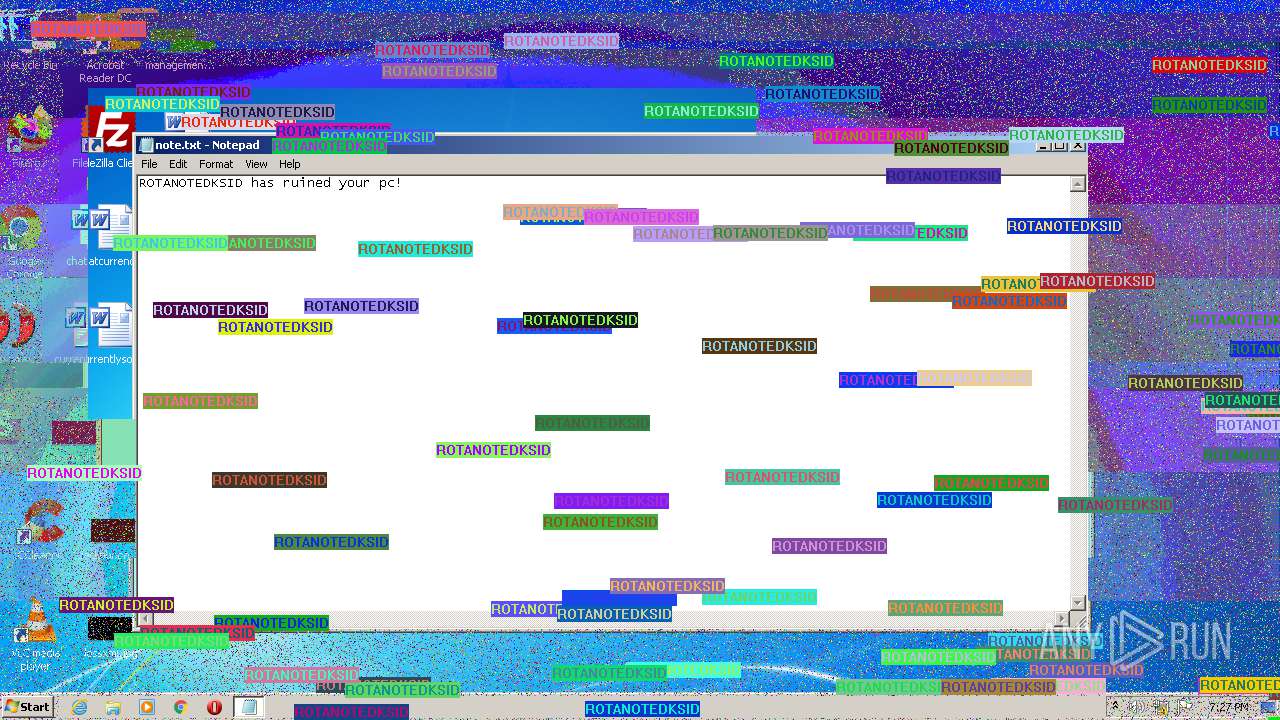
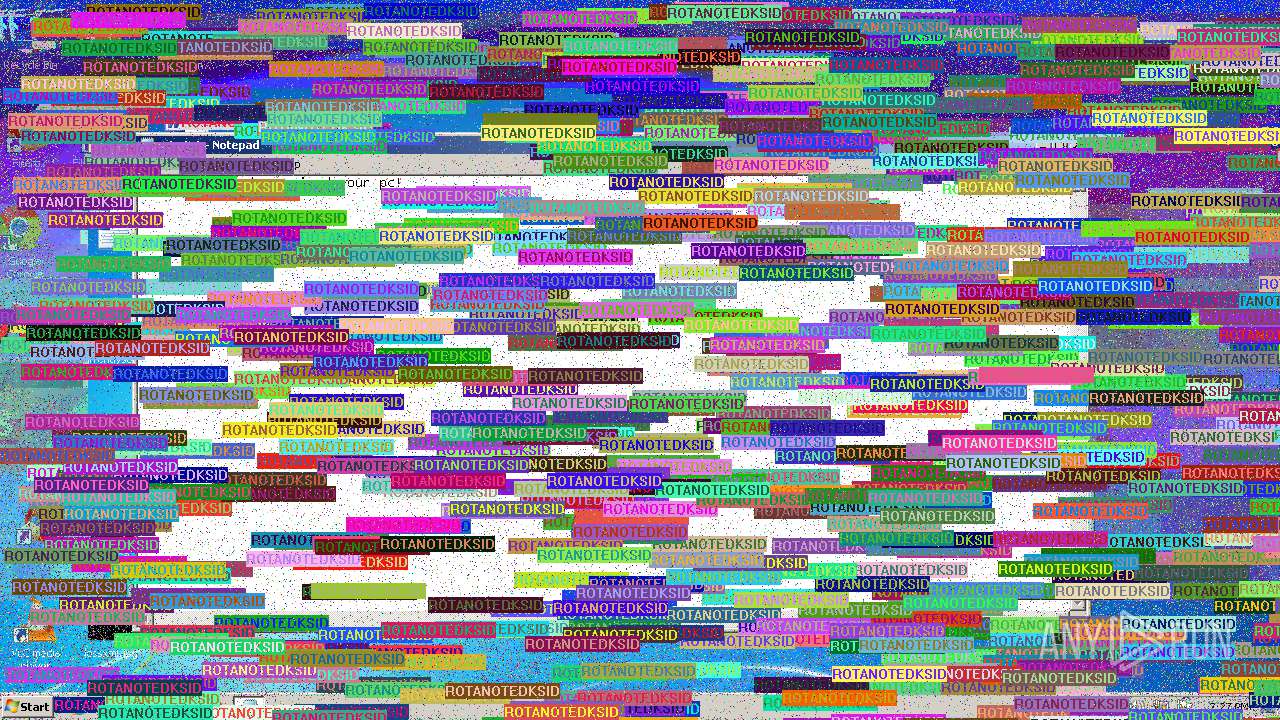
MALICIOUS
Drops executable file immediately after starts
- ROTANOTEDKSID-Destructive.exe (PID: 3220)
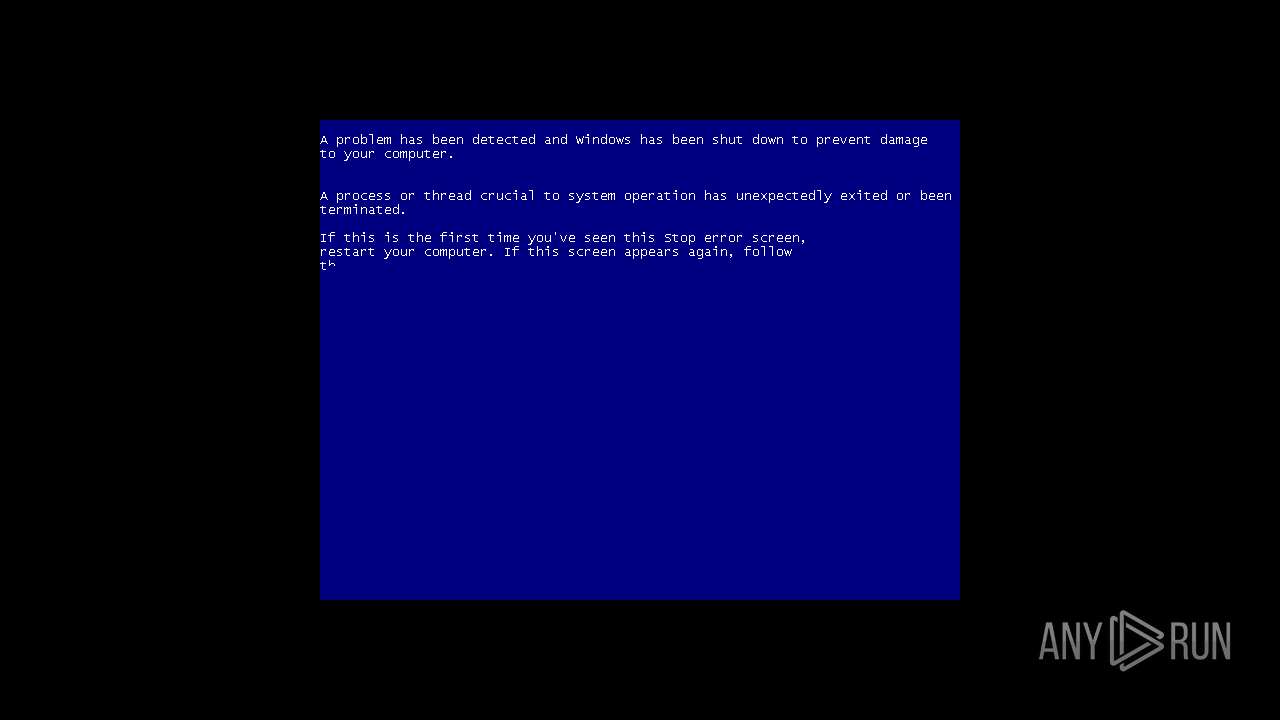
Application was dropped or rewritten from another process
- WipeMBR.exe (PID: 2644)
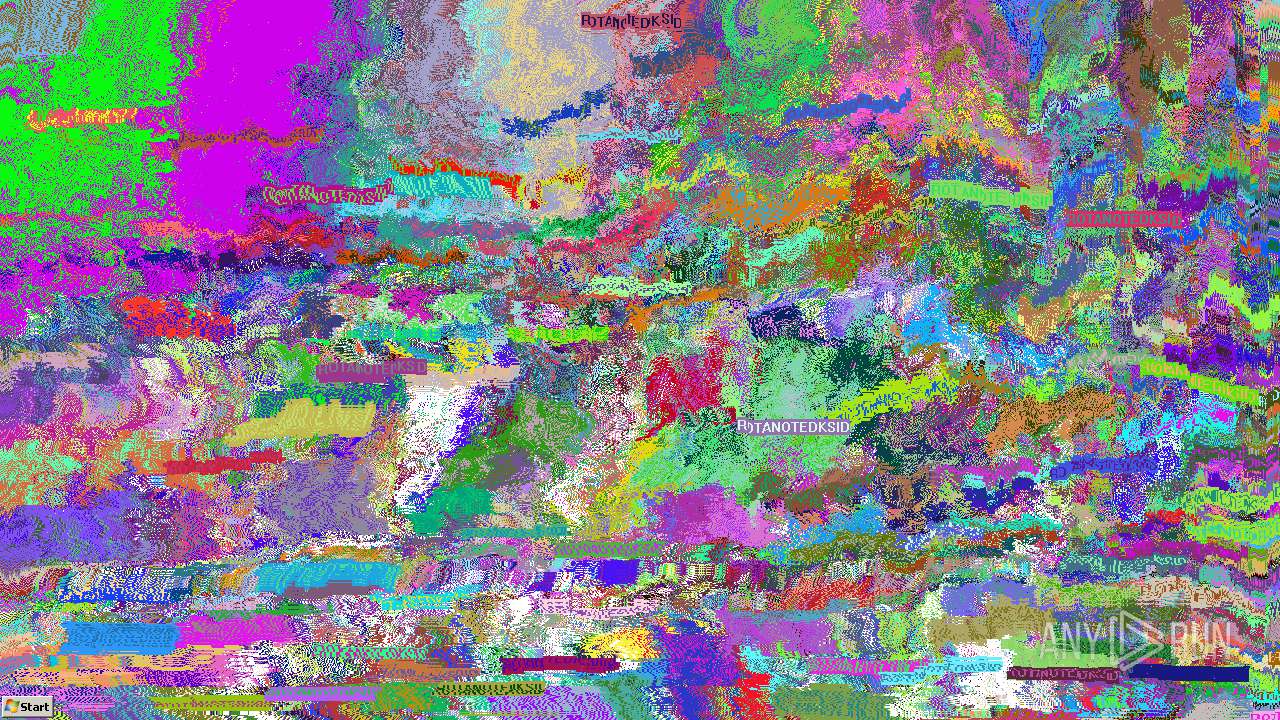
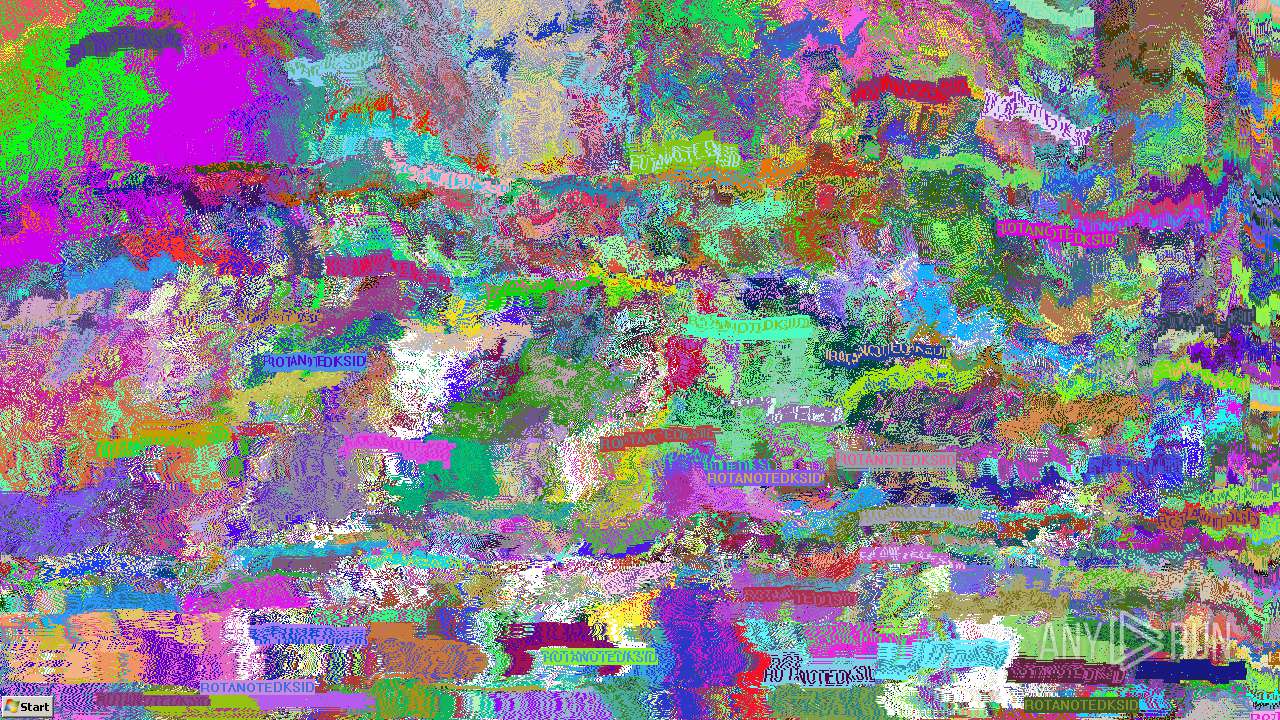
- MouseDraw.exe (PID: 2740)
- pixels.exe (PID: 1740)
- gl.exe (PID: 2756)
- TextOut.exe (PID: 3360)
- masher.exe (PID: 1316)
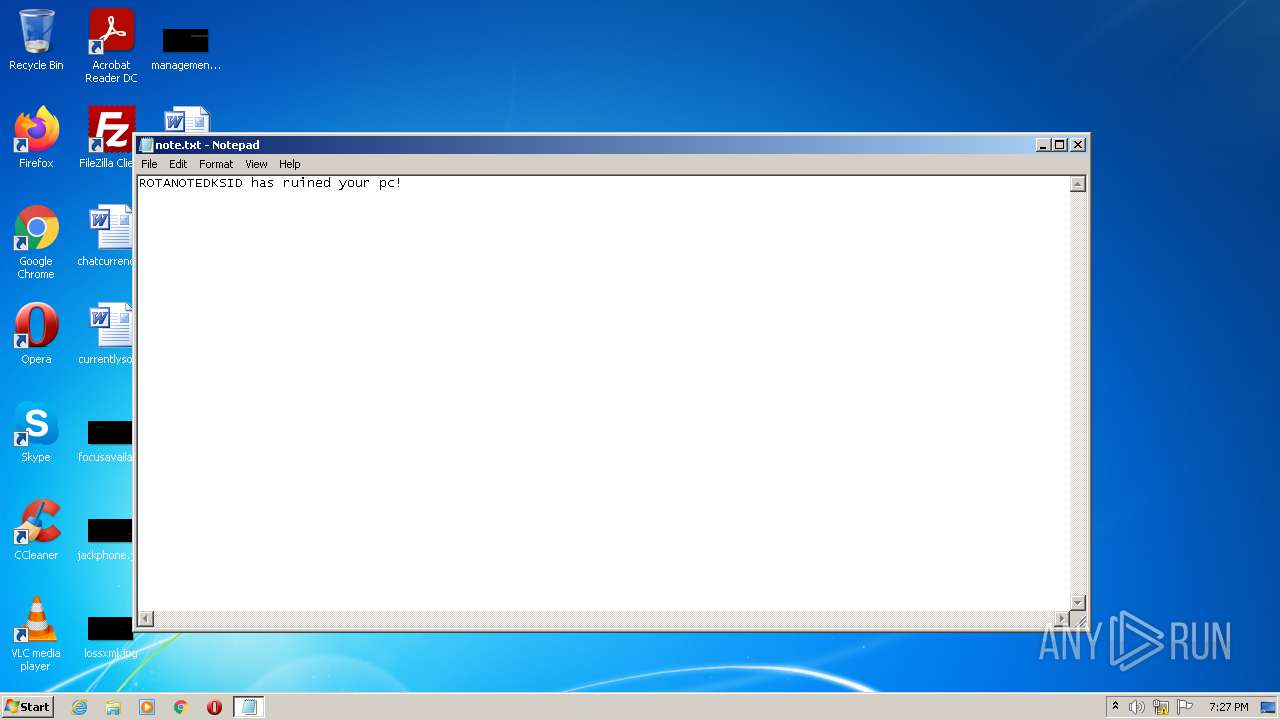
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 1560)
SUSPICIOUS
Checks supported languages
- ROTANOTEDKSID-Destructive.exe (PID: 3220)
- cmd.exe (PID: 2076)
- WipeMBR.exe (PID: 2644)
- wscript.exe (PID: 3488)
- WScript.exe (PID: 3788)
- MouseDraw.exe (PID: 2740)
- pixels.exe (PID: 1740)
- masher.exe (PID: 1316)
- gl.exe (PID: 2756)
- TextOut.exe (PID: 3360)
Drops a file that was compiled in debug mode
- ROTANOTEDKSID-Destructive.exe (PID: 3220)
Reads the computer name
- ROTANOTEDKSID-Destructive.exe (PID: 3220)
- wscript.exe (PID: 3488)
- WScript.exe (PID: 3788)
- cmd.exe (PID: 2076)
Executable content was dropped or overwritten
- ROTANOTEDKSID-Destructive.exe (PID: 3220)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3488)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2076)
Drops a file with a compile date too recent
- ROTANOTEDKSID-Destructive.exe (PID: 3220)
Executes scripts
- ROTANOTEDKSID-Destructive.exe (PID: 3220)
- cmd.exe (PID: 2076)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2076)
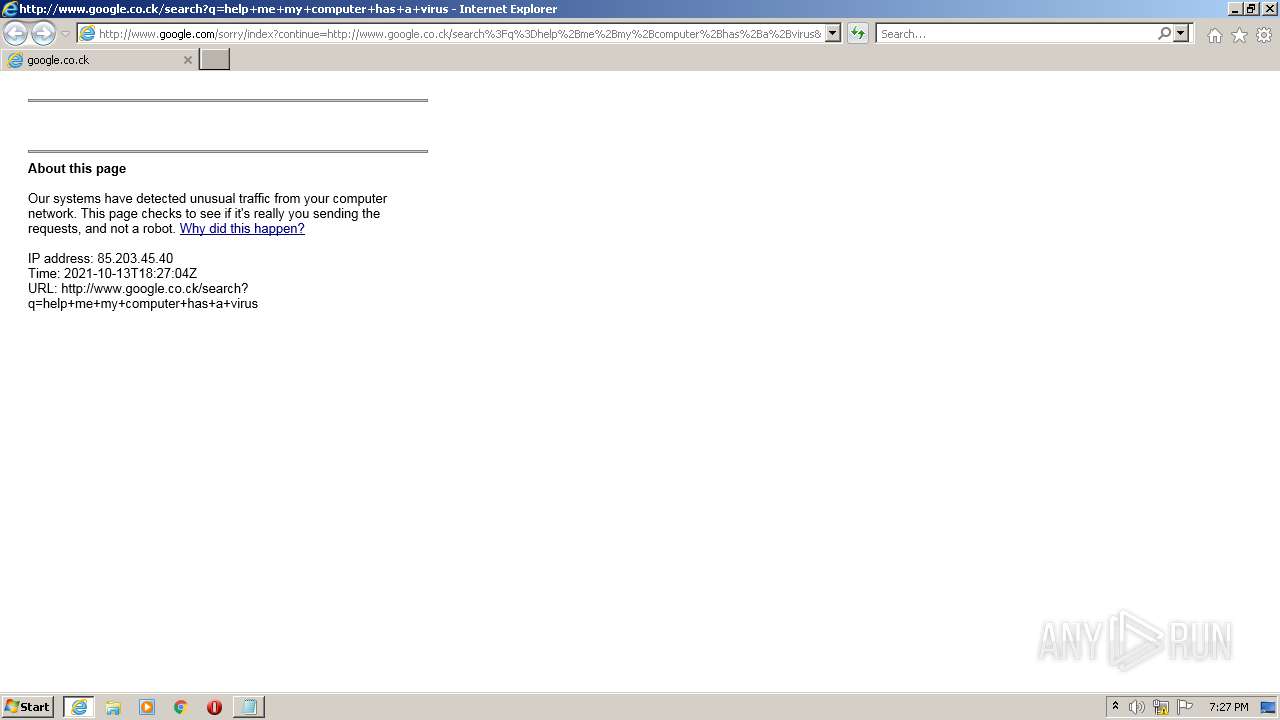
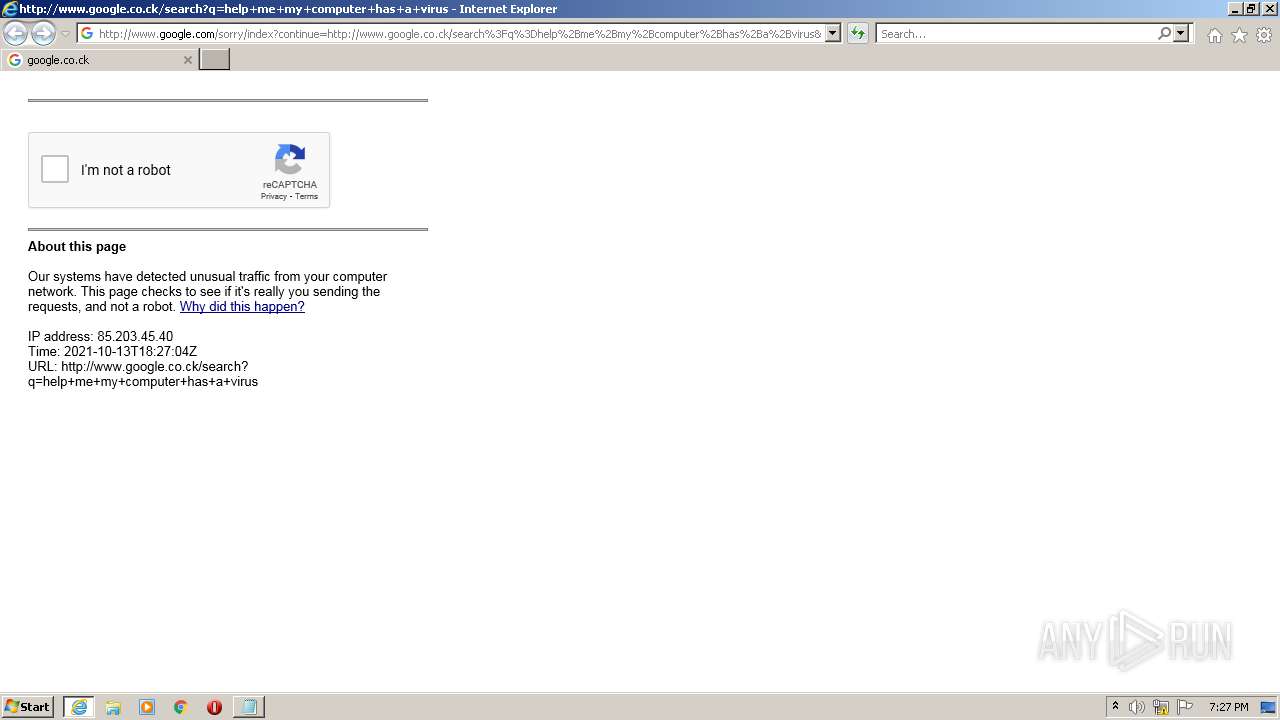
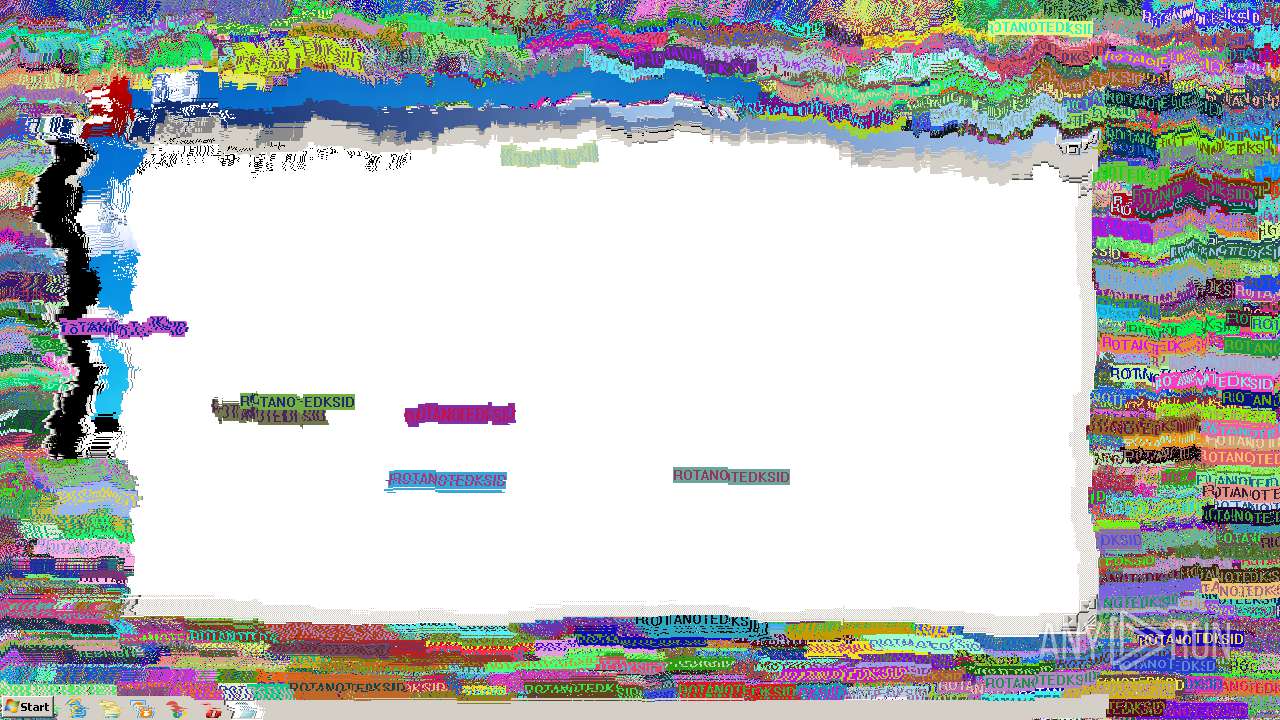
Starts Internet Explorer
- cmd.exe (PID: 2076)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3148)
INFO
Reads the computer name
- taskkill.exe (PID: 2304)
- iexplore.exe (PID: 3684)
- iexplore.exe (PID: 3148)
Checks Windows Trust Settings
- wscript.exe (PID: 3488)
- WScript.exe (PID: 3788)
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3684)
Checks supported languages
- taskkill.exe (PID: 2304)
- reg.exe (PID: 1560)
- timeout.exe (PID: 3544)
- iexplore.exe (PID: 3684)
- NOTEPAD.EXE (PID: 2260)
- timeout.exe (PID: 2832)
- iexplore.exe (PID: 3148)
- timeout.exe (PID: 3348)
- timeout.exe (PID: 2820)
- timeout.exe (PID: 3276)
- timeout.exe (PID: 1800)
Application launched itself
- iexplore.exe (PID: 3684)
Reads internet explorer settings
- iexplore.exe (PID: 3148)
Changes internet zones settings
- iexplore.exe (PID: 3684)
Creates files in the user directory
- iexplore.exe (PID: 3148)
Reads settings of System Certificates
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3684)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3148)
Reads the date of Windows installation
- iexplore.exe (PID: 3684)
Changes settings of System certificates
- iexplore.exe (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 21:46:09+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 66048 |
| InitializedDataSize: | 18661888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2018 20:46:09 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Feb-2018 20:46:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x00003345 | 0x00003400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.58167 |
.text | 0x00005000 | 0x0000CC42 | 0x0000CE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56946 |
.rdata | 0x00012000 | 0x000033A0 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11024 |
.data | 0x00016000 | 0x00001704 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.29594 |
.rsrc | 0x00018000 | 0x011C7DAC | 0x011C7E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99062 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08821 | 672 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.01545 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.26093 | 488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.35033 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.65918 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.97154 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.9218 | 1736 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 4.65982 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 4.91782 | 270376 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 4.99817 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
67
Monitored processes
22
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1316 | masher.exe | C:\Users\admin\AppData\Local\Temp\866B.tmp\masher.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1560 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1740 | pixels.exe | C:\Users\admin\AppData\Local\Temp\866B.tmp\pixels.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1800 | timeout 15 /nobreak | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\866B.tmp\s.cmd" " | C:\Windows\system32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
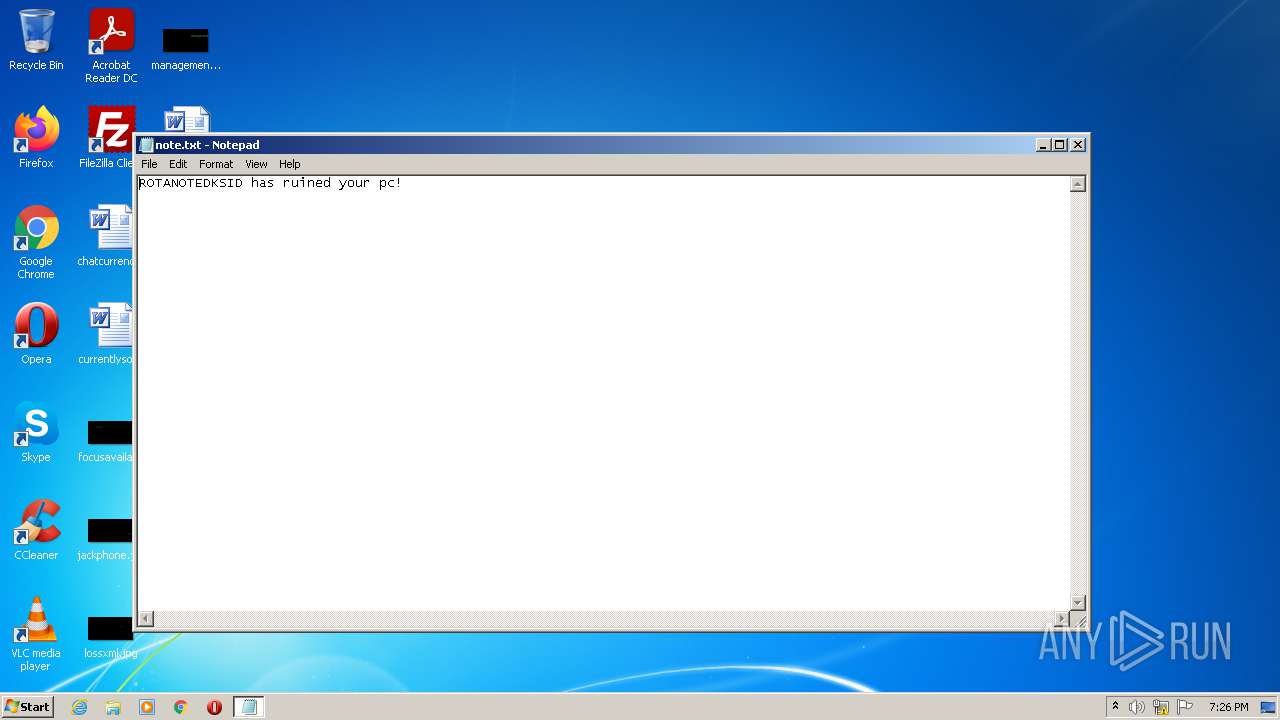
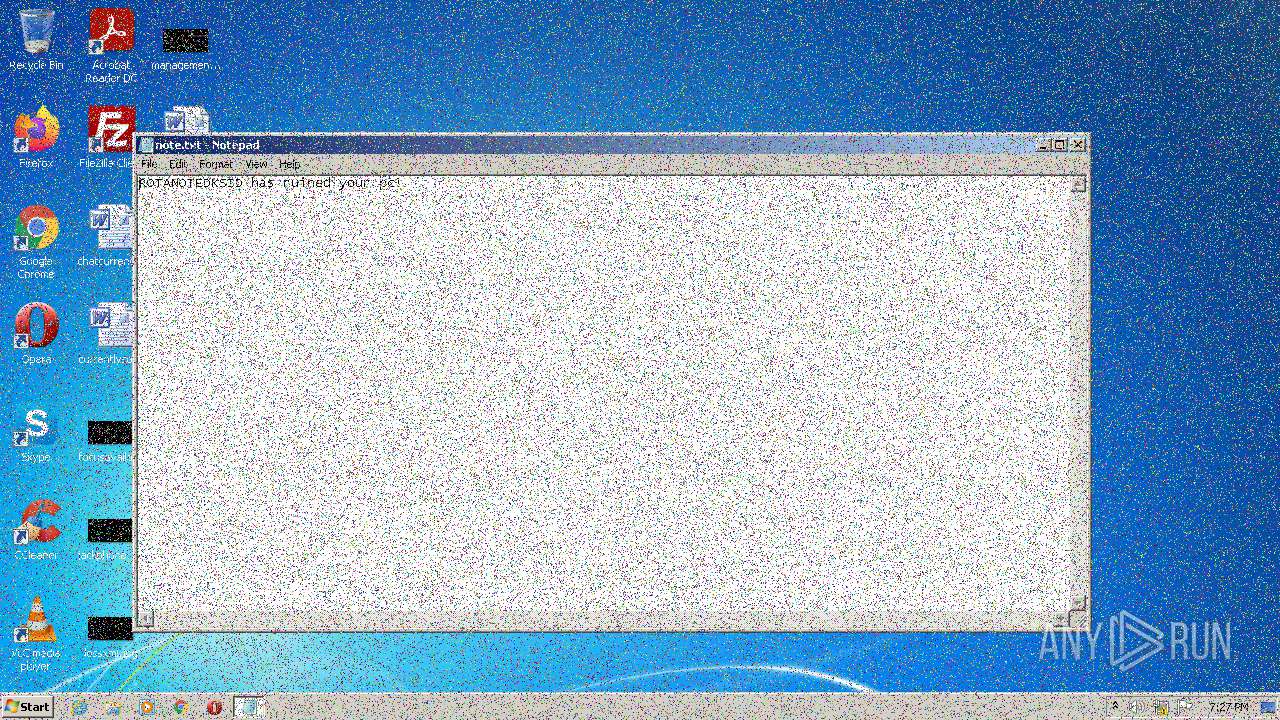
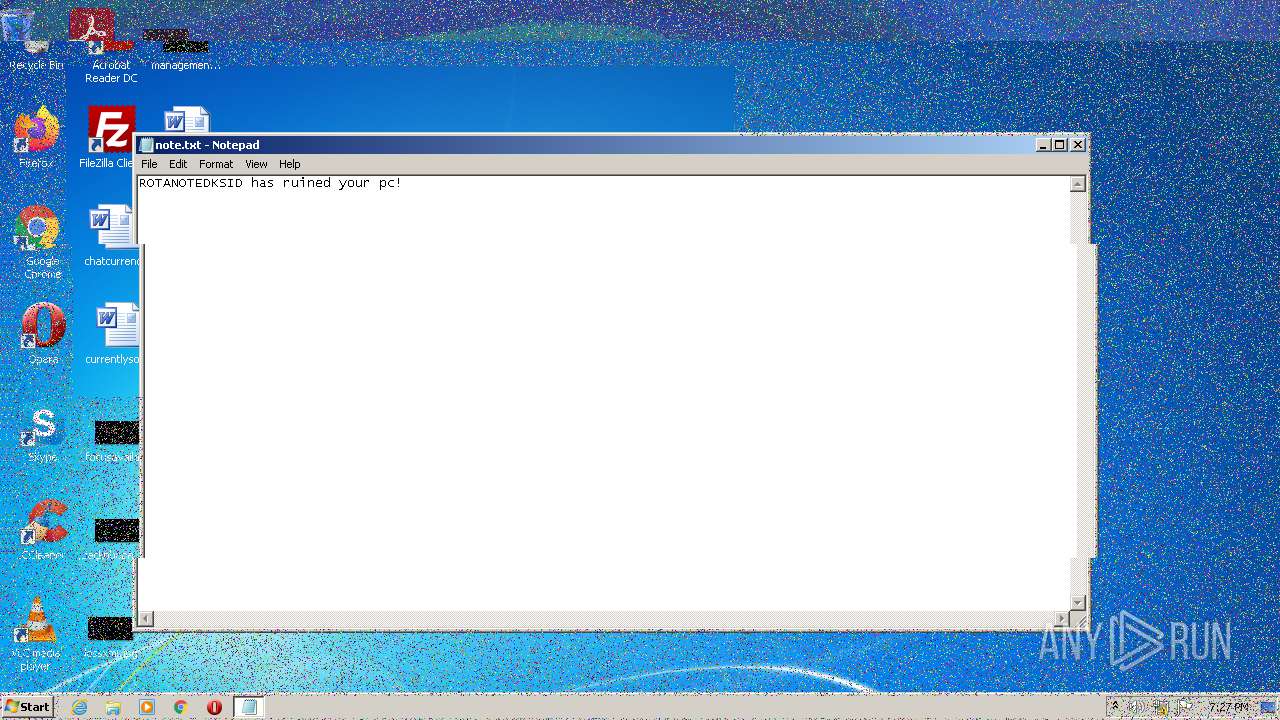
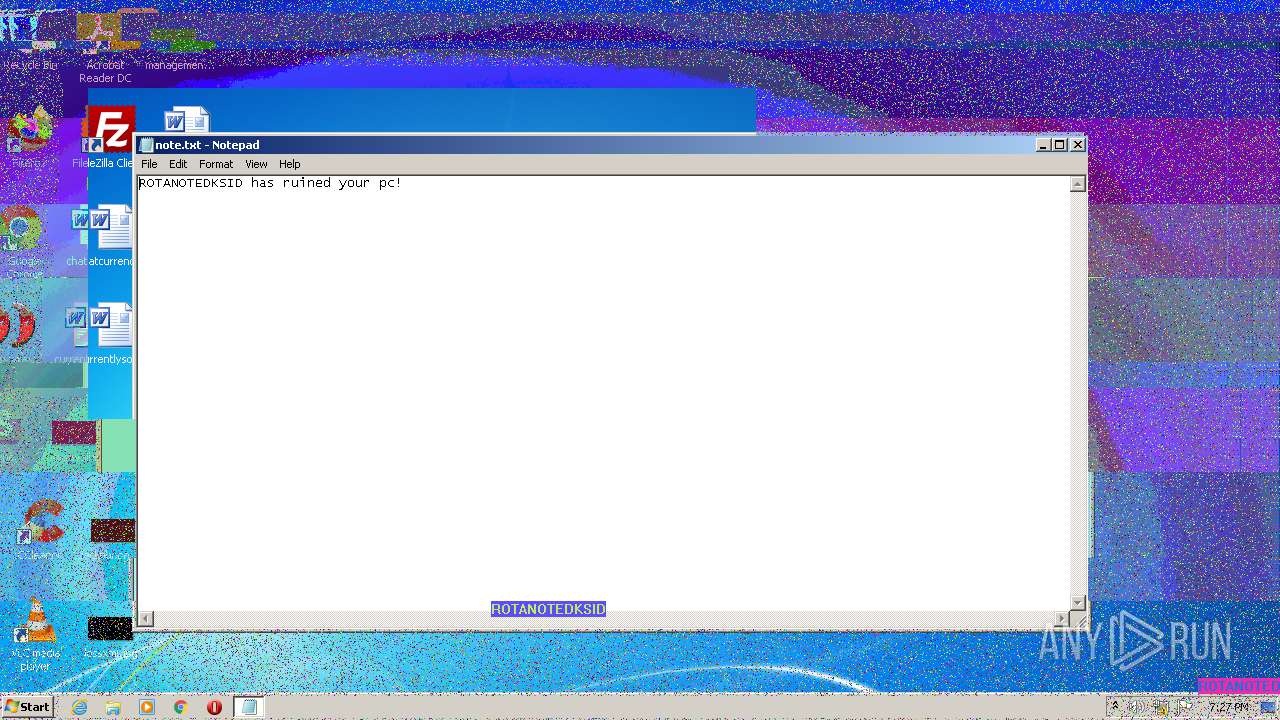
| 2260 | "C:\Windows\system32\NOTEPAD.EXE" C:\note.txt | C:\Windows\system32\NOTEPAD.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | taskkill /f /im taskmgr.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\AppData\Local\Temp\ROTANOTEDKSID-Destructive.exe" | C:\Users\admin\AppData\Local\Temp\ROTANOTEDKSID-Destructive.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2644 | WipeMBR.exe | C:\Users\admin\AppData\Local\Temp\866B.tmp\WipeMBR.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2740 | MouseDraw.exe | C:\Users\admin\AppData\Local\Temp\866B.tmp\MouseDraw.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
18 188
Read events
18 031
Write events
156
Delete events
1
Modification events
| (PID) Process: | (3220) ROTANOTEDKSID-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3220) ROTANOTEDKSID-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3220) ROTANOTEDKSID-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3220) ROTANOTEDKSID-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3488) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3488) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3488) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3488) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1560) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (2076) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
6
Suspicious files
14
Text files
15
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3220 | ROTANOTEDKSID-Destructive.exe | C:\Users\admin\AppData\Local\Temp\866B.tmp\boom.wav | — | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:EF06F47CCA4BC9FC4BDF86DA850F7D0D | SHA256:39D3D14623B9830B2B251B1EA44FBE95A9B8341FA3D09388FC546CF6728A08EE | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:64E9B8BB98E2303717538CE259BEC57D | SHA256:76BD459EC8E467EFC3E3FB94CB21B9C77A2AA73C9D4C0F3FAF823677BE756331 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F07644E38ED7C9F37D11EEC6D4335E02_3674EE7A36D4FCEB1723FF65E35B9E6F | binary | |
MD5:FA95908EC4DA8827046EBCDDE4569221 | SHA256:5BF4852EA727C6A8AD2BDA2156F3DFBE3E3C4F7F84109CD9076EEFD274B33C7E | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\api[1].js | text | |
MD5:35DAE7881DDC5181CE1C971ABEE8EFAF | SHA256:323918625ED889CC03E90584B2E4D6B680222EA1C2CD7572E1E2EA4BA7F993BE | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:E225F1E0BC64C115B295BDE08974B553 | SHA256:3B535805EDB7EAC3213564623B2AF748152B5AD99B43ECE36A732226C380745D | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_3674EE7A36D4FCEB1723FF65E35B9E6F | der | |
MD5:4E11B1B2303D57AED42BAD725833059E | SHA256:8BB4A811AA735403D8EF53C15C3B6361DDA0F2A26A12A47E214B585CB44B0A10 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\PIZJE3EC.txt | text | |
MD5:9C8692AAD81EA2BBBF62615CF5E6AA8F | SHA256:00FB75A7E8384333BB934B9C2AC7B8CD7DE5933152F17B632B7F321CDF971BB9 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:597A65A59E0AD2053CA897434297DF8F | SHA256:E4427A42D0AF6248543CFB804B1579CC4A304B273853C42B0C33E76FED7B1186 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:153055876892B8CA8F94EEA6BB863DA1 | SHA256:43E53AF48979708806CF6663BCE27670753DE312C699C93A8F6FF08875520B10 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
17
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | iexplore.exe | GET | 302 | 172.217.23.99:80 | http://www.google.co.ck/search?q=help+me+my+computer+has+a+virus | US | html | 371 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCrHFBqOLe78goAAAAA%2F2QG | US | der | 472 b | whitelisted |
3684 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECRXdf7EU7SwCgAAAAD%2FZgs%3D | US | der | 471 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3148 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?dff286358656e4a4 | US | compressed | 4.70 Kb | whitelisted |
3148 | iexplore.exe | GET | 429 | 142.250.185.228:80 | http://www.google.com/sorry/index?continue=http://www.google.co.ck/search%3Fq%3Dhelp%2Bme%2Bmy%2Bcomputer%2Bhas%2Ba%2Bvirus&q=EgRVyy0oGPjJnIsGIhDZ8JE9FjGz-qx5ur2HVXTuMgFy | US | html | 2.83 Kb | malicious |
3148 | iexplore.exe | GET | 200 | 142.250.185.228:80 | http://www.google.com/favicon.ico | US | image | 1.46 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3148 | iexplore.exe | 172.217.23.99:80 | www.google.co.ck | Google Inc. | US | whitelisted |
3148 | iexplore.exe | 142.250.185.228:80 | www.google.com | Google Inc. | US | whitelisted |
3148 | iexplore.exe | 142.250.185.228:443 | www.google.com | Google Inc. | US | whitelisted |
3148 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3148 | iexplore.exe | 142.250.184.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3148 | iexplore.exe | 142.250.186.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3684 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3684 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3148 | iexplore.exe | 142.250.186.67:443 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.co.ck |
| whitelisted |
www.google.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
iecvlist.microsoft.com |
| whitelisted |