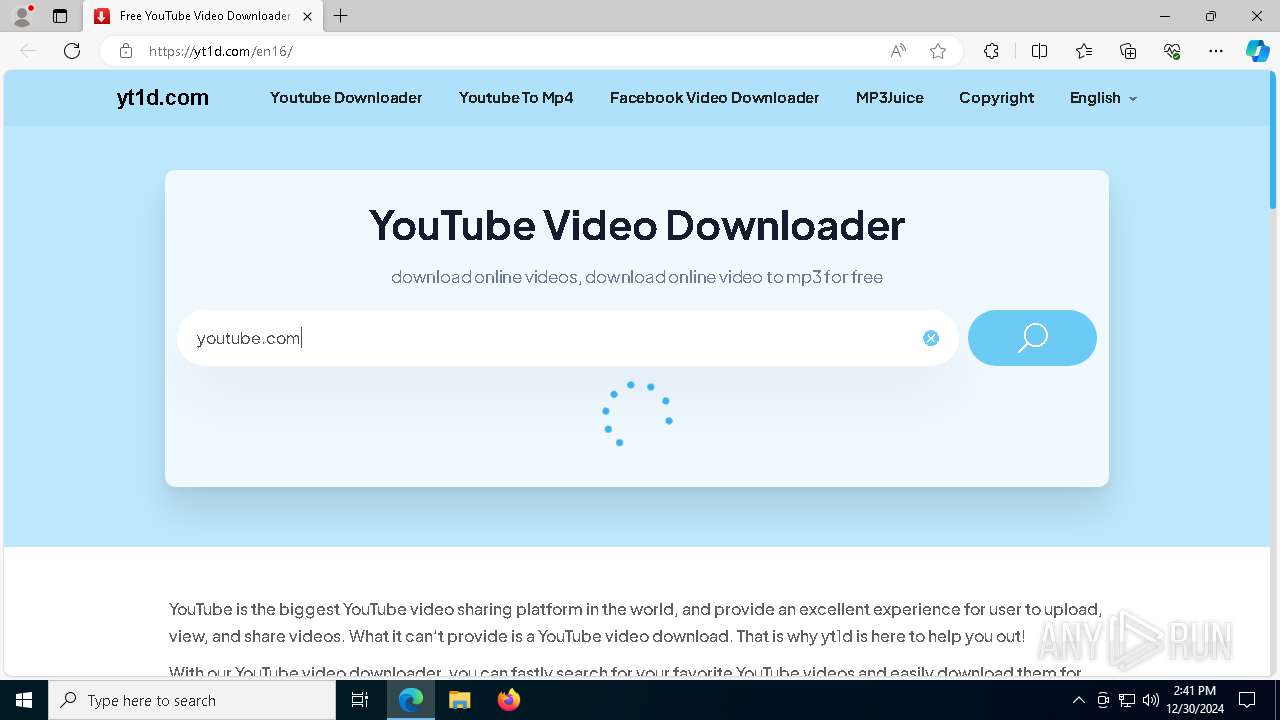
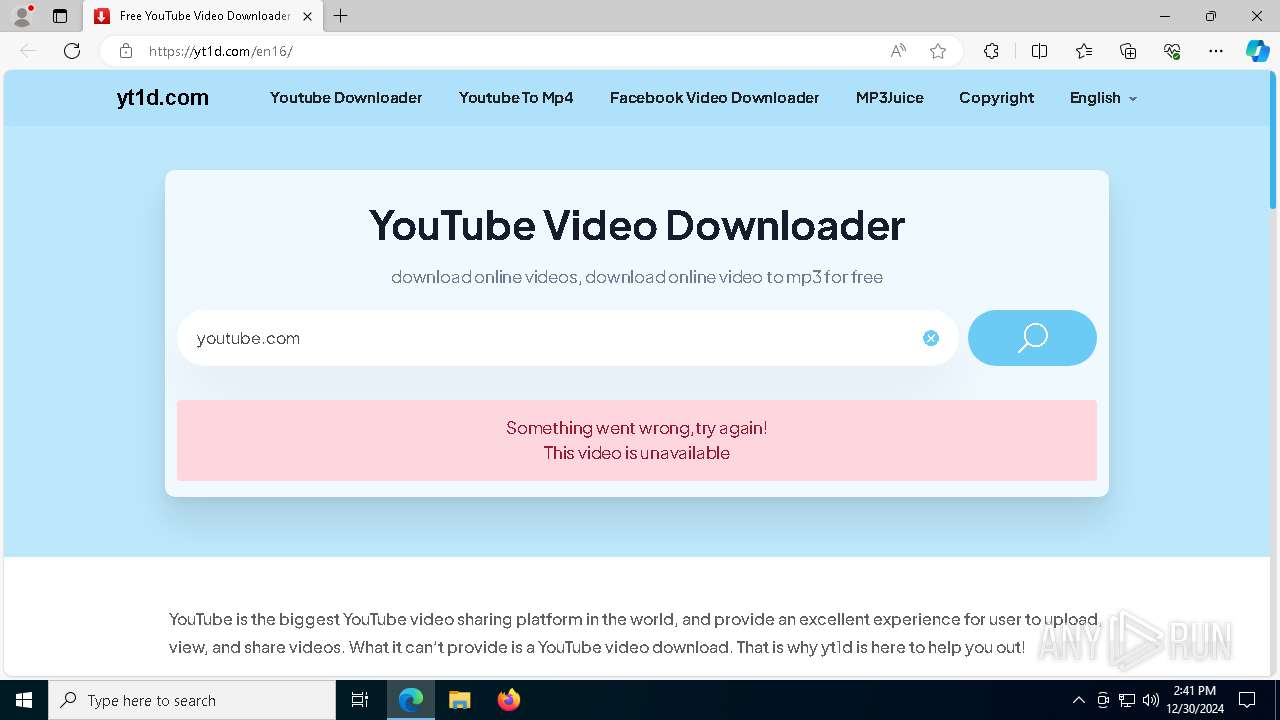
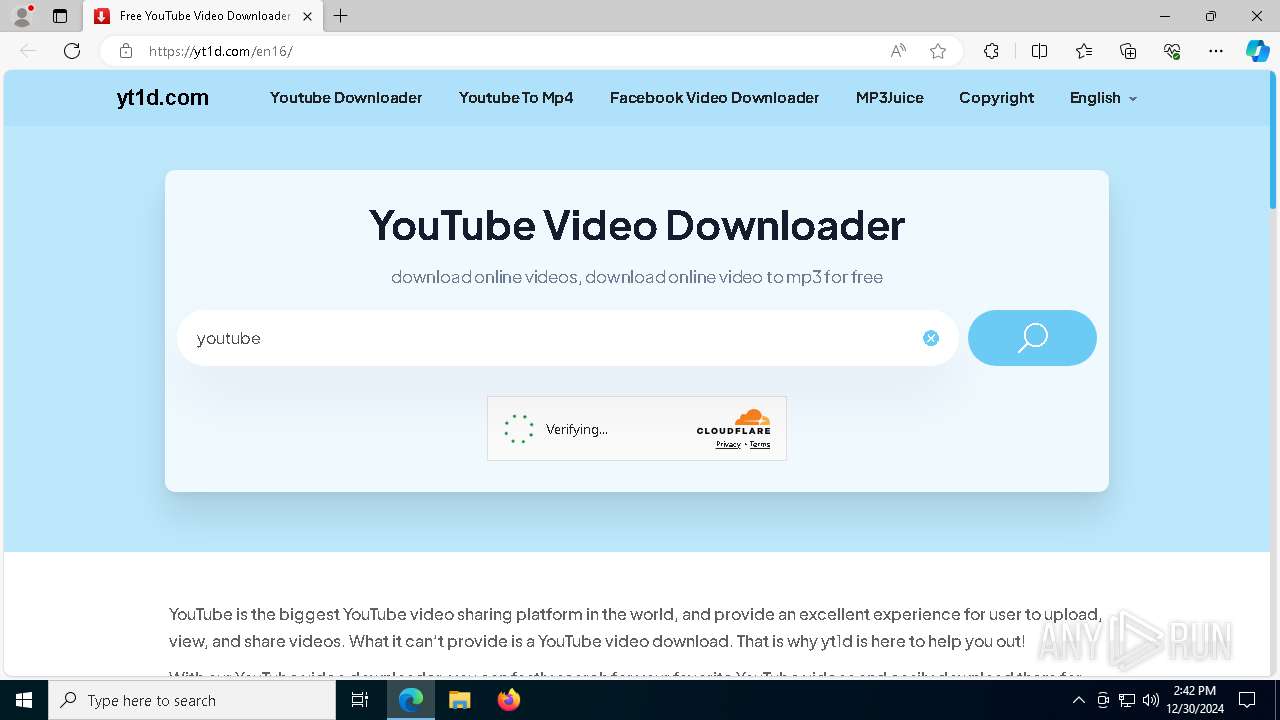
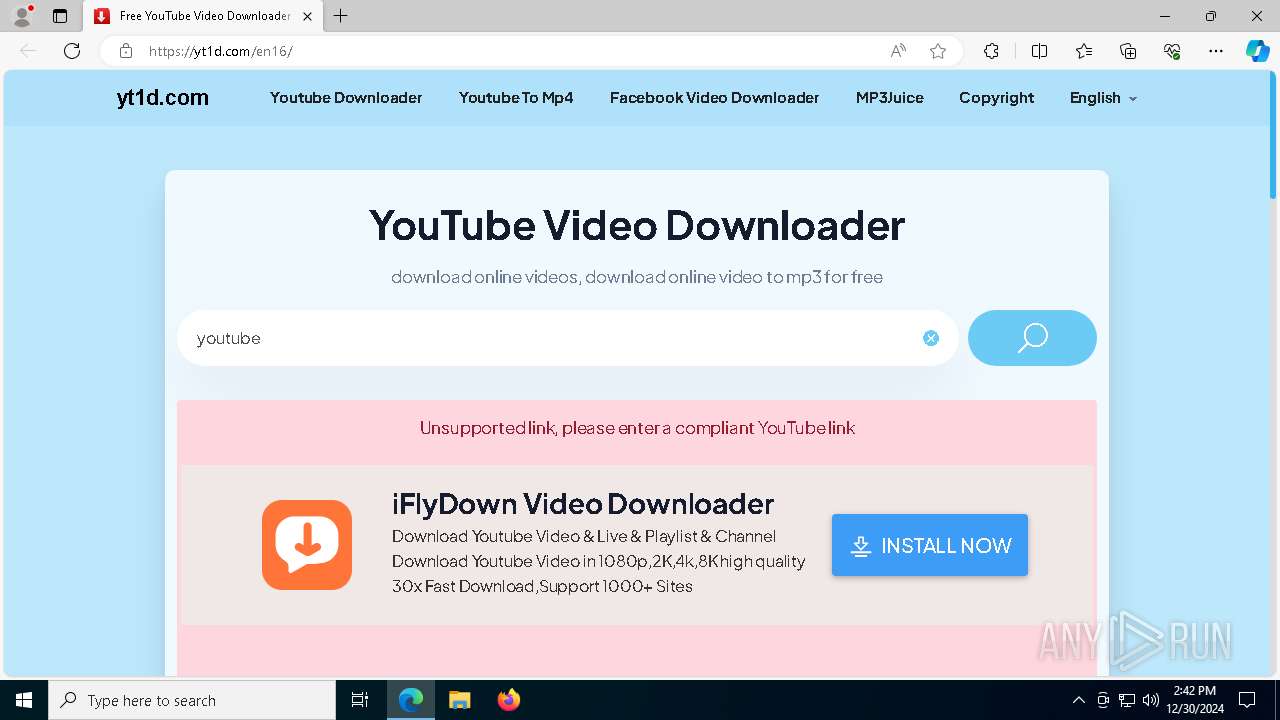
| URL: | https://yt1d.com/en16/ |
| Full analysis: | https://app.any.run/tasks/ded3666a-224e-4b28-b25f-ed63fb44cc96 |
| Verdict: | Malicious activity |
| Analysis date: | December 30, 2024, 14:41:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 2CC766499E4A37E19FB1DAFA34411ABE |
| SHA1: | 66657BF762DBD57A753AD8E2CFB1E9F47842CD7C |
| SHA256: | C9AE63DC8405805E6D91743D053F6AF1E68C844B65D3BEA13141133390D5AA2D |
| SSDEEP: | 3:N8XkwGn:20wG |
MALICIOUS
No malicious indicators.SUSPICIOUS
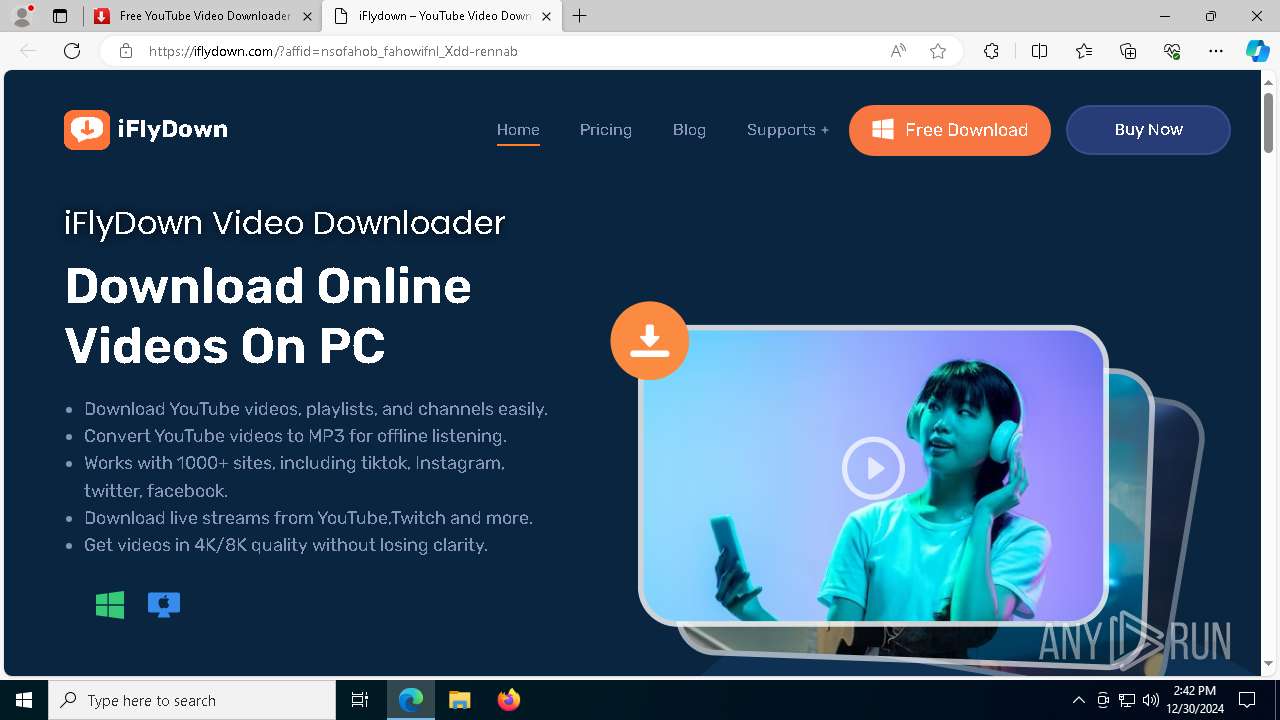
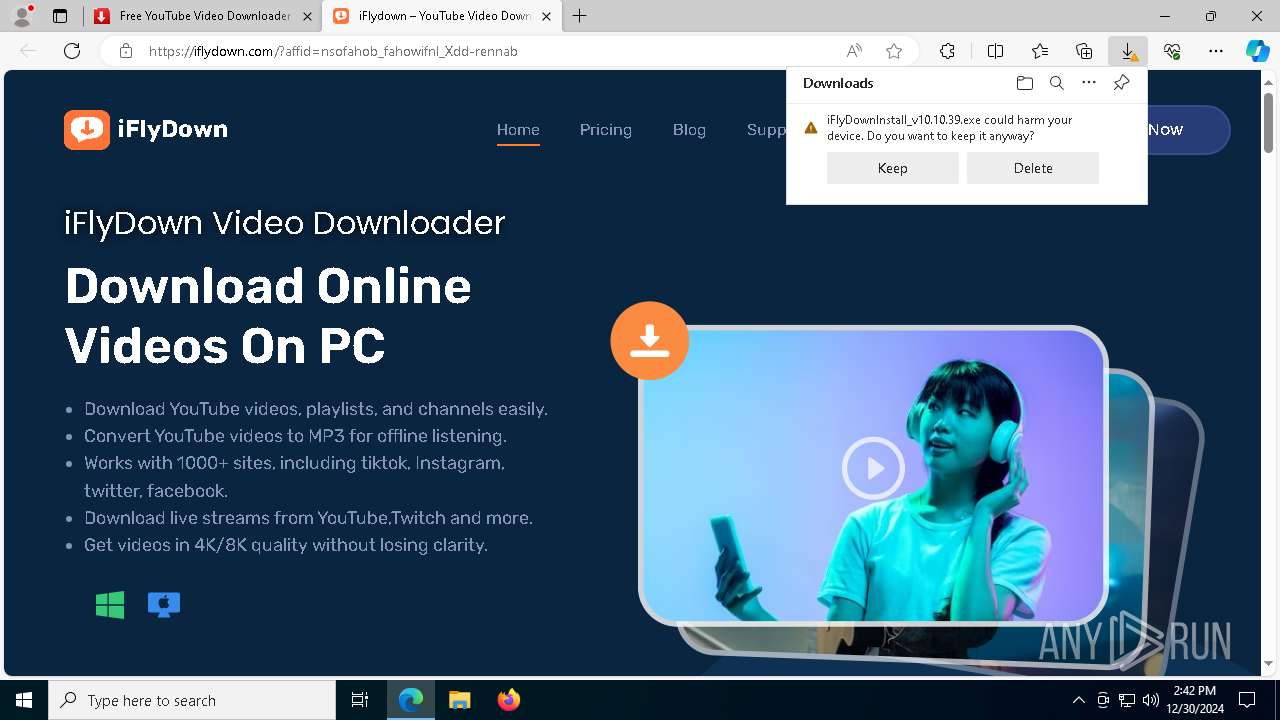
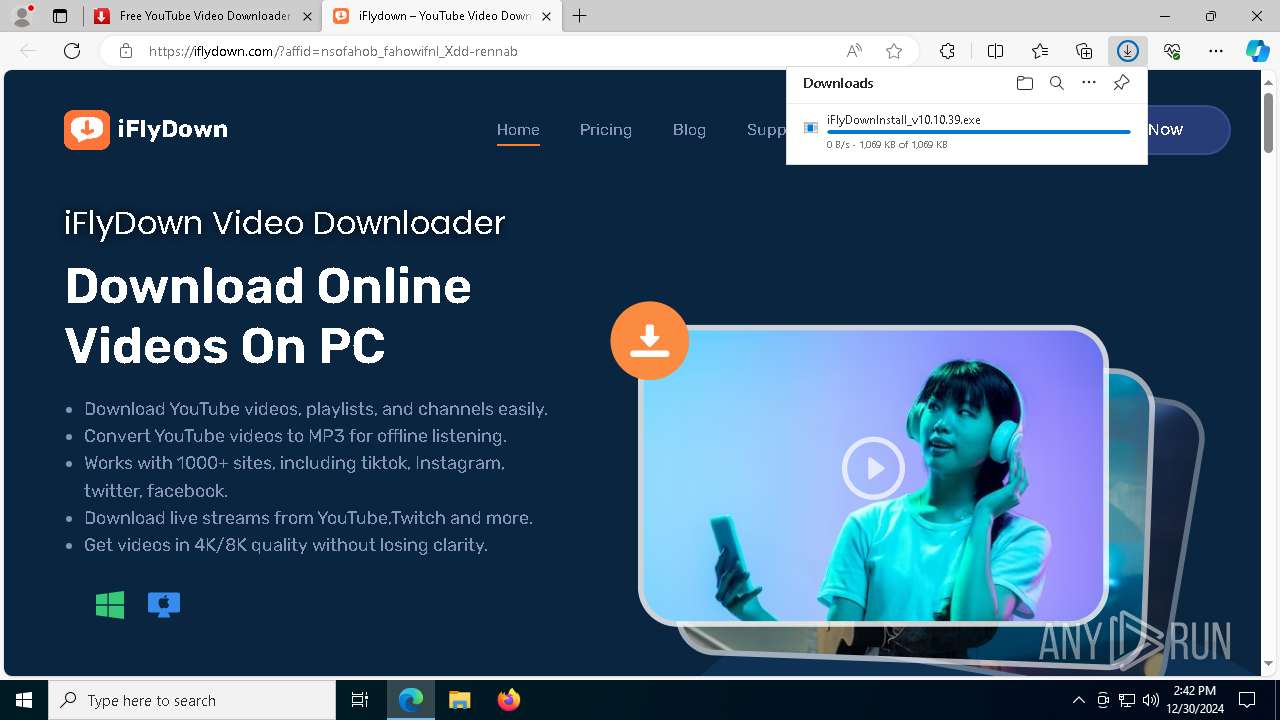
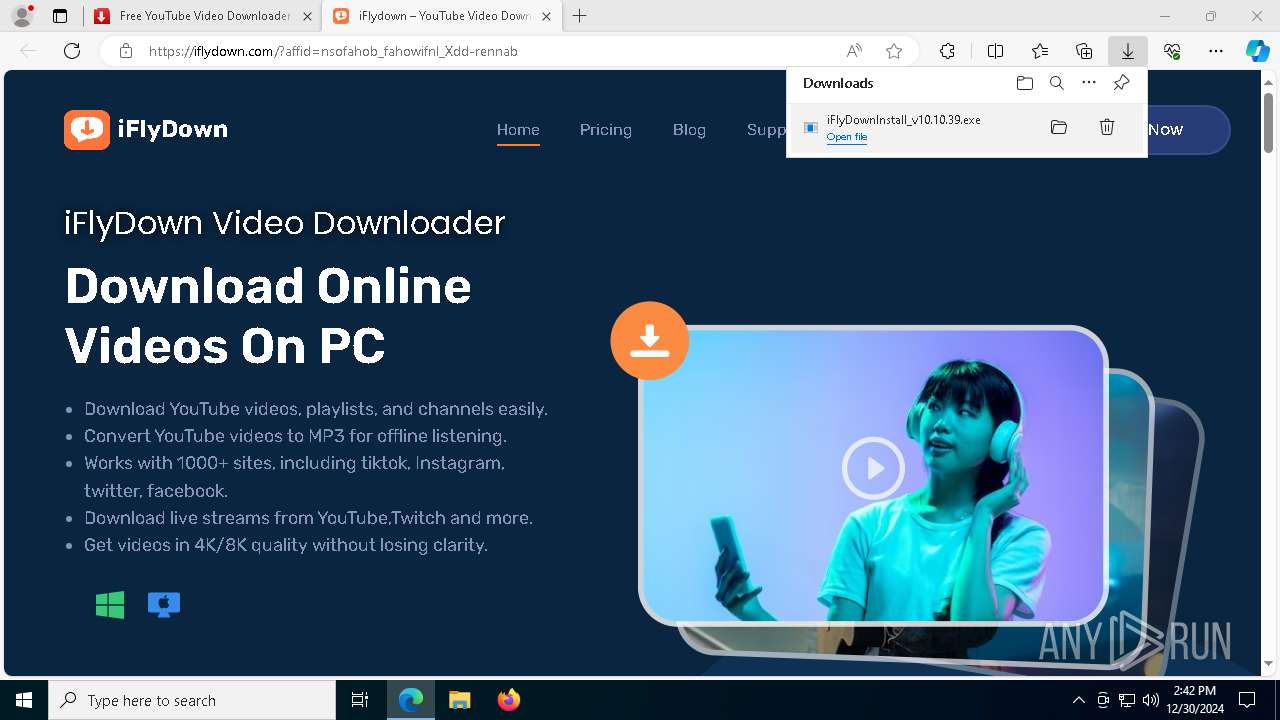
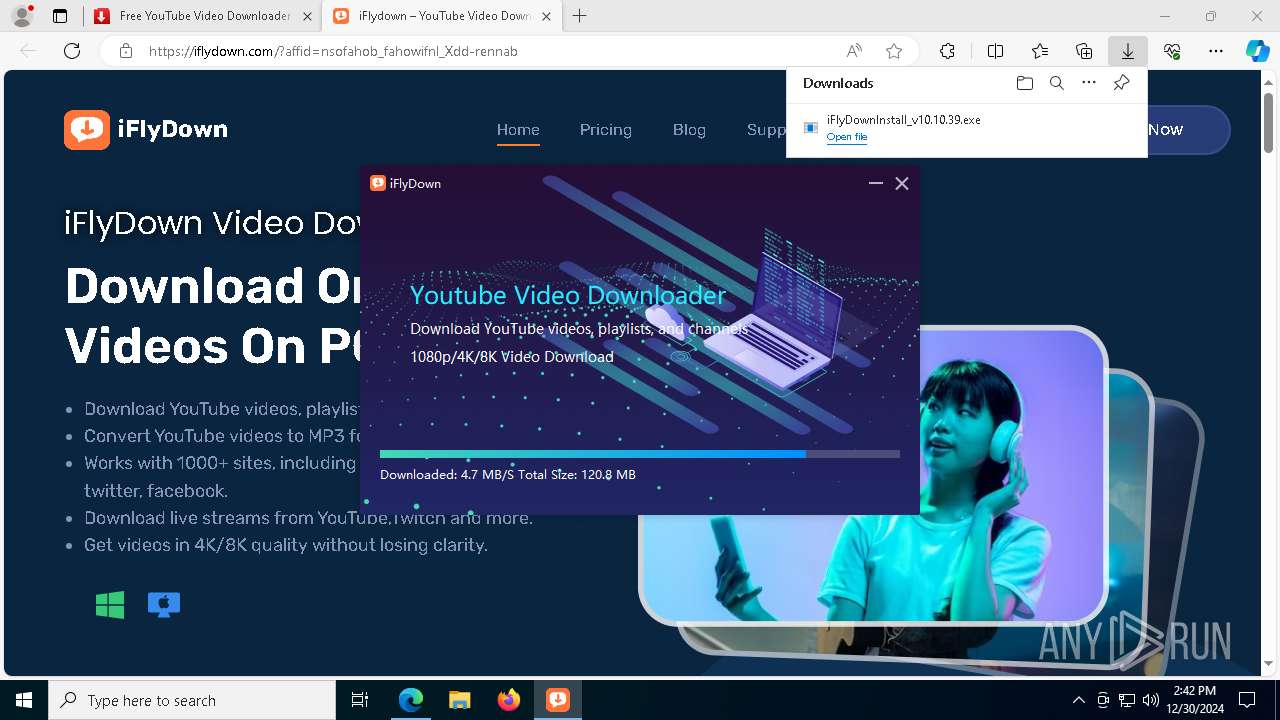
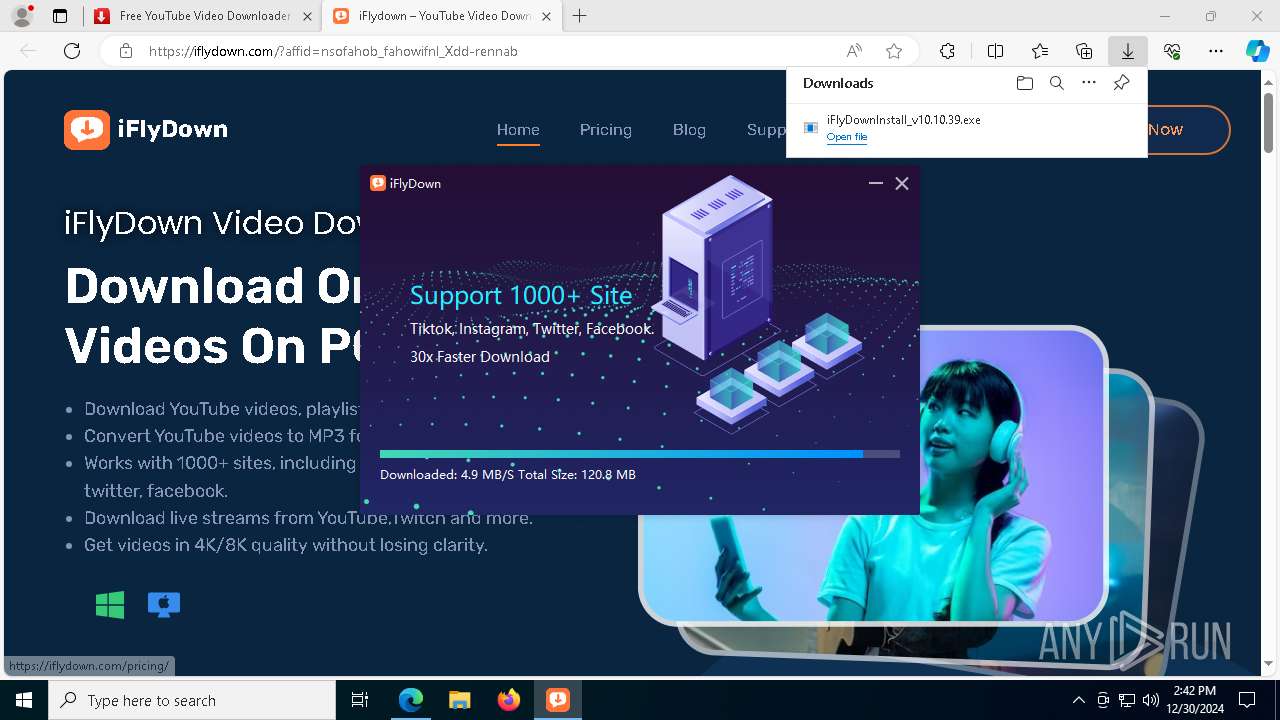
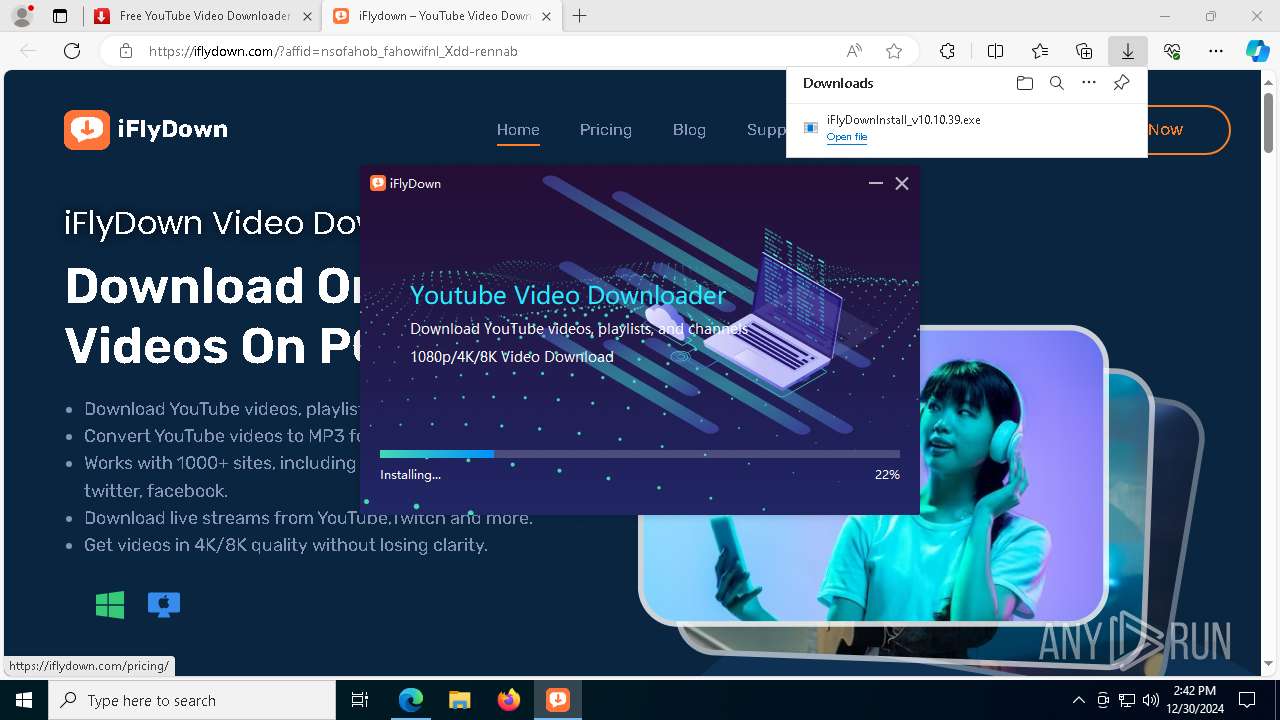
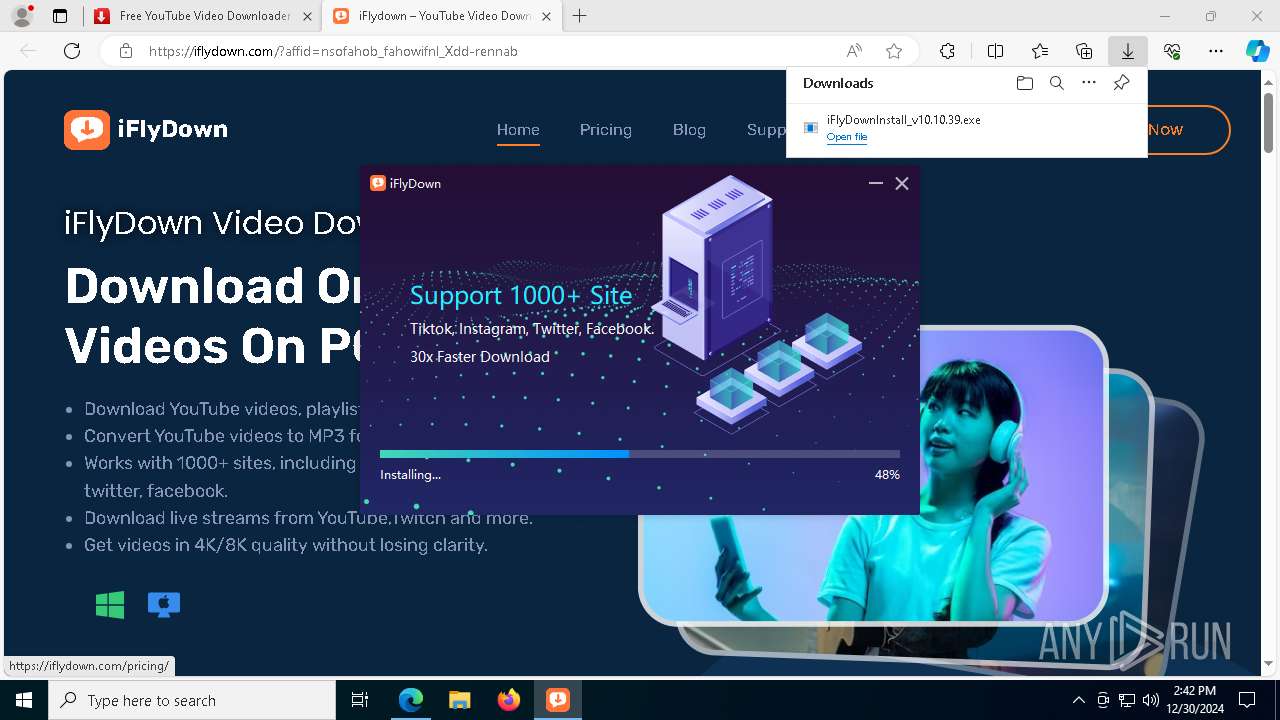
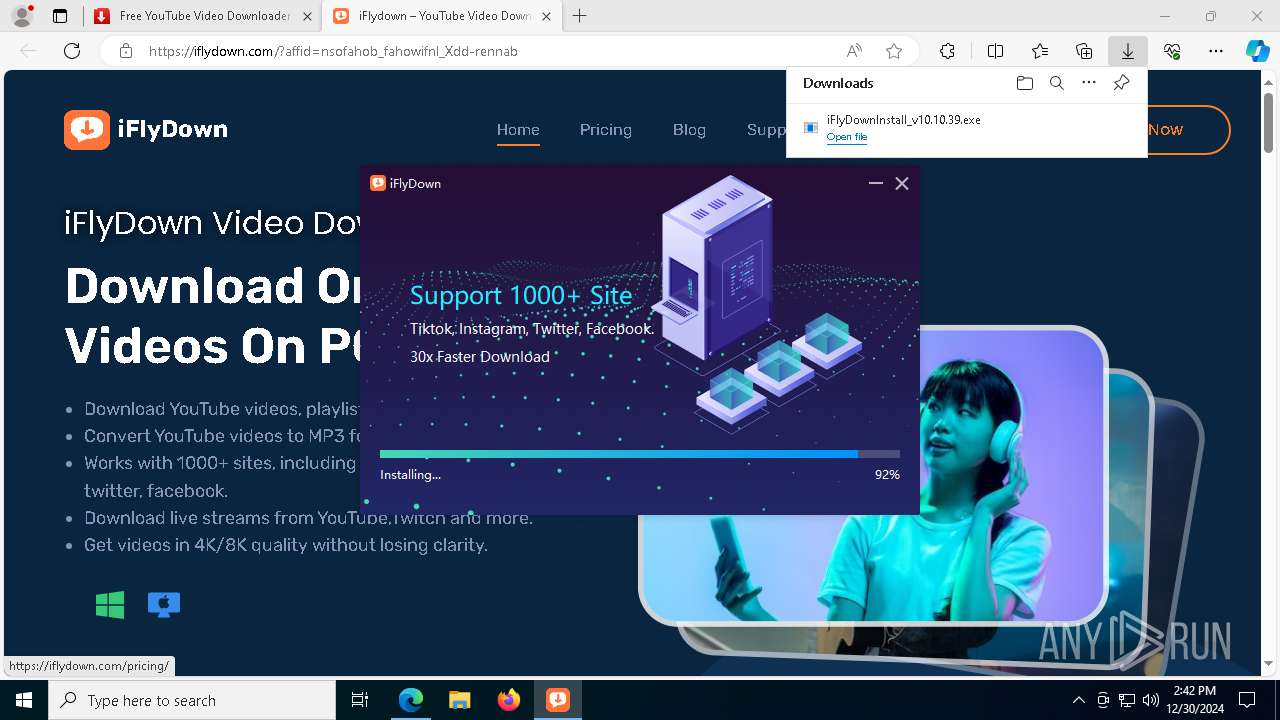
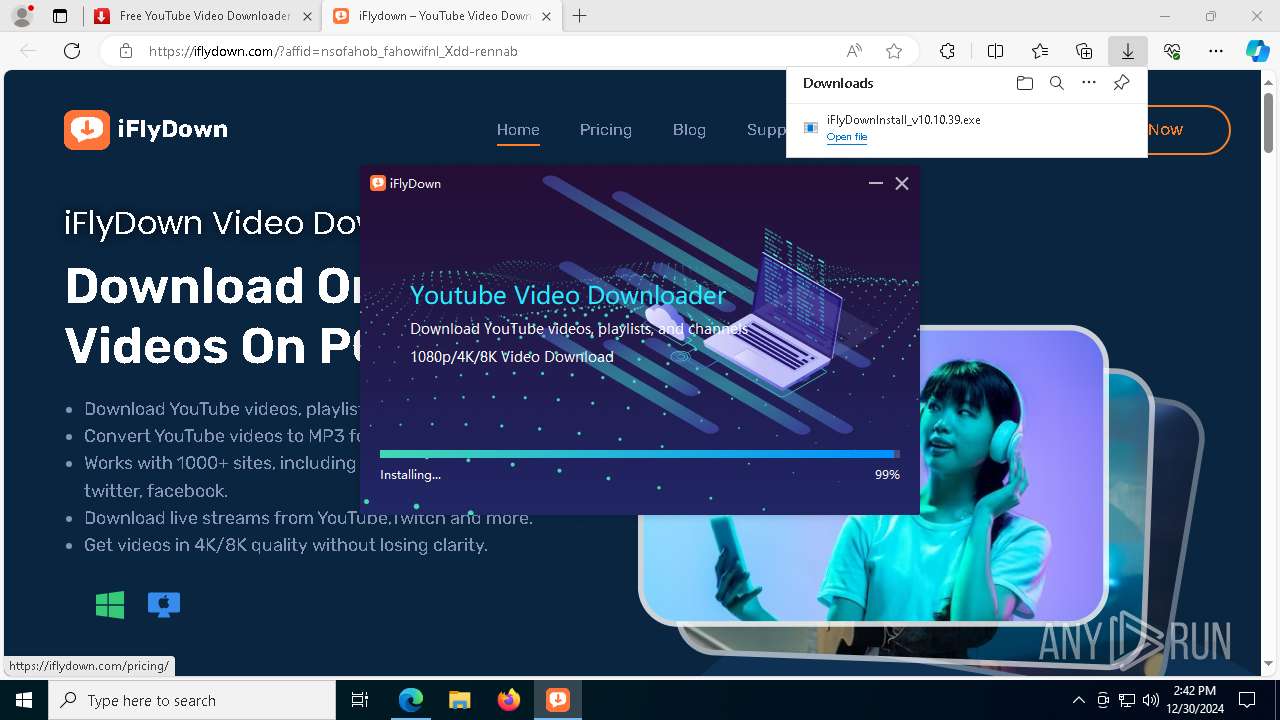
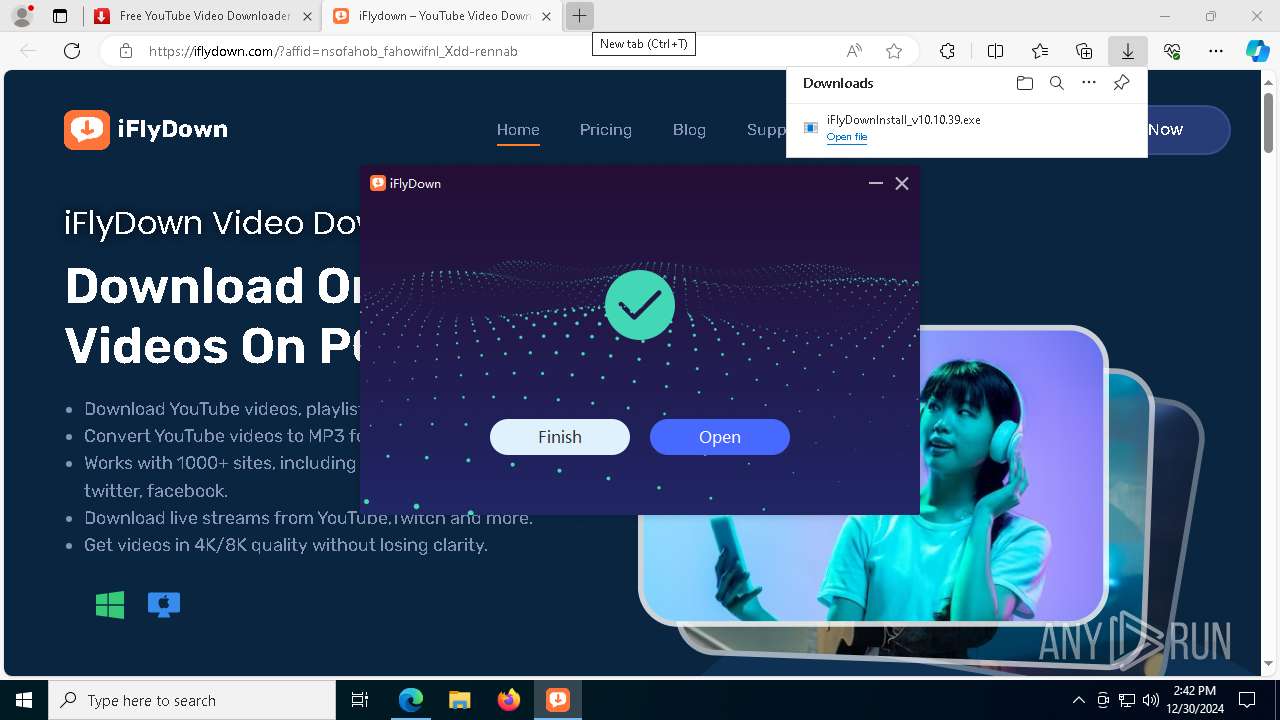
Executable content was dropped or overwritten
- iFlyDownInstall_v10.10.39.exe (PID: 4308)
- yt-dlp.exe (PID: 5160)
Process drops legitimate windows executable
- iFlyDownInstall_v10.10.39.exe (PID: 4308)
- yt-dlp.exe (PID: 5160)
Drops 7-zip archiver for unpacking
- iFlyDownInstall_v10.10.39.exe (PID: 4308)
Malware-specific behavior (creating "System.dll" in Temp)
- iFlyDownInstall_v10.10.39.exe (PID: 4308)
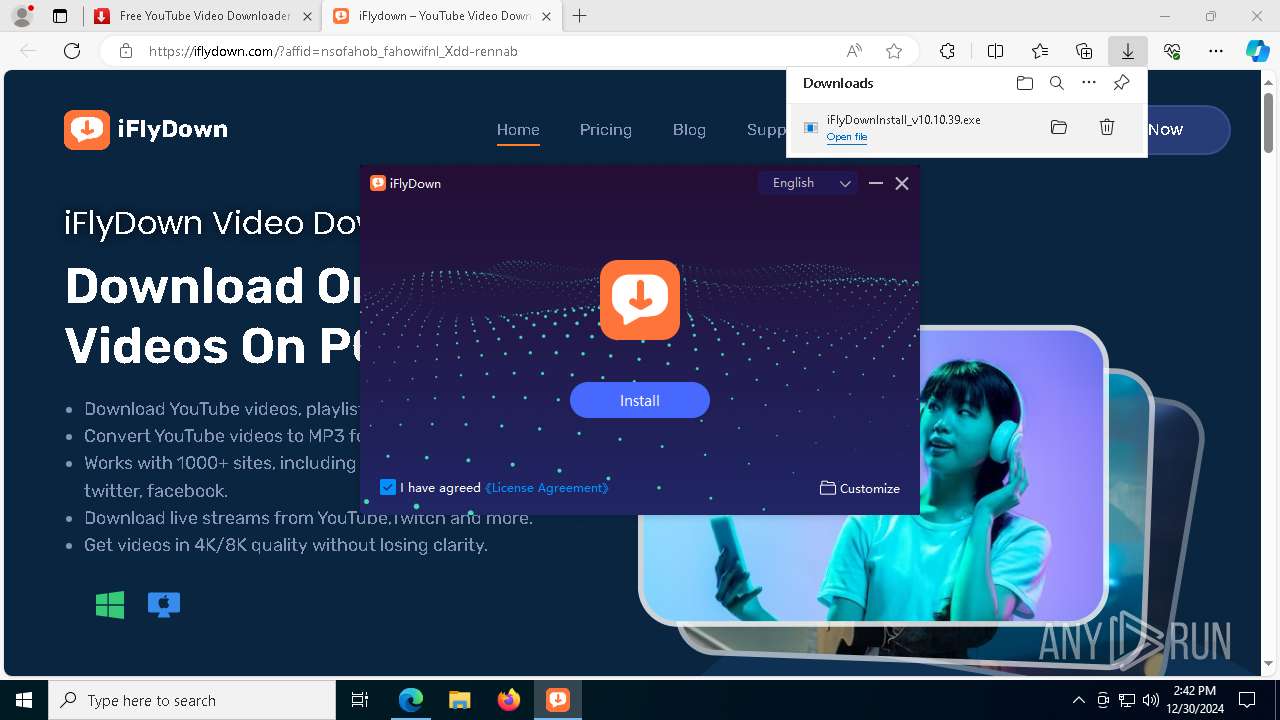
Creates a software uninstall entry
- iFlyDownInstall_v10.10.39.exe (PID: 4308)
Application launched itself
- iFlyDown.exe (PID: 7432)
- yt-dlp.exe (PID: 5160)
Starts application with an unusual extension
- cmd.exe (PID: 7604)
- cmd.exe (PID: 4516)
Starts CMD.EXE for commands execution
- iFlyDown.exe (PID: 1512)
- yt-dlp.exe (PID: 748)
Process drops python dynamic module
- yt-dlp.exe (PID: 5160)
The process drops C-runtime libraries
- yt-dlp.exe (PID: 5160)
Loads Python modules
- yt-dlp.exe (PID: 748)
INFO
Reads the computer name
- identity_helper.exe (PID: 7844)
- iFlyDown.exe (PID: 7432)
- iFlyDown.exe (PID: 6224)
- iFlyDown.exe (PID: 7040)
- yt-dlp.exe (PID: 5160)
- yt-dlp.exe (PID: 748)
The process uses the downloaded file
- msedge.exe (PID: 4708)
Reads Environment values
- identity_helper.exe (PID: 7844)
- iFlyDown.exe (PID: 1512)
Application launched itself
- msedge.exe (PID: 4708)
Checks supported languages
- identity_helper.exe (PID: 7844)
- iFlyDown.exe (PID: 7432)
- iFlyDown.exe (PID: 7912)
- iFlyDown.exe (PID: 6224)
- iFlyDown.exe (PID: 8104)
- iFlyDown.exe (PID: 1512)
- iFlyDown.exe (PID: 2456)
- iFlyDown.exe (PID: 3488)
- iFlyDown.exe (PID: 7004)
- iFlyDown.exe (PID: 7040)
- chcp.com (PID: 6976)
- iFlyDown.exe (PID: 6272)
- iFlyDown.exe (PID: 4336)
- yt-dlp.exe (PID: 5160)
- yt-dlp.exe (PID: 748)
- chcp.com (PID: 3564)
- iFlyDown.exe (PID: 6460)
The sample compiled with chinese language support
- iFlyDownInstall_v10.10.39.exe (PID: 4308)
Executable content was dropped or overwritten
- msedge.exe (PID: 4708)
- msedge.exe (PID: 6596)
The sample compiled with english language support
- msedge.exe (PID: 4708)
- msedge.exe (PID: 6596)
- iFlyDownInstall_v10.10.39.exe (PID: 4308)
- yt-dlp.exe (PID: 5160)
Sends debugging messages
- iFlyDownInstall_v10.10.39.exe (PID: 4308)
Create files in a temporary directory
- iFlyDownInstall_v10.10.39.exe (PID: 4308)
- iFlyDown.exe (PID: 7432)
- yt-dlp.exe (PID: 5160)
Creates files in the program directory
- iFlyDownInstall_v10.10.39.exe (PID: 4308)
Manual execution by a user
- iFlyDown.exe (PID: 7432)
Creates files or folders in the user directory
- iFlyDown.exe (PID: 7912)
- iFlyDown.exe (PID: 7432)
- iFlyDown.exe (PID: 6224)
Reads the machine GUID from the registry
- iFlyDown.exe (PID: 7432)
- yt-dlp.exe (PID: 748)
Process checks computer location settings
- iFlyDown.exe (PID: 1512)
- iFlyDown.exe (PID: 6460)
- iFlyDown.exe (PID: 7004)
- iFlyDown.exe (PID: 3488)
- iFlyDown.exe (PID: 4336)
Reads product name
- iFlyDown.exe (PID: 1512)
Changes the display of characters in the console
- cmd.exe (PID: 4516)
- cmd.exe (PID: 7604)
Checks operating system version
- yt-dlp.exe (PID: 748)
Checks proxy server information
- yt-dlp.exe (PID: 748)
- iFlyDown.exe (PID: 7432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
207
Monitored processes
75
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7080 --field-trial-handle=2340,i,4569595705337358665,11515769480000297281,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
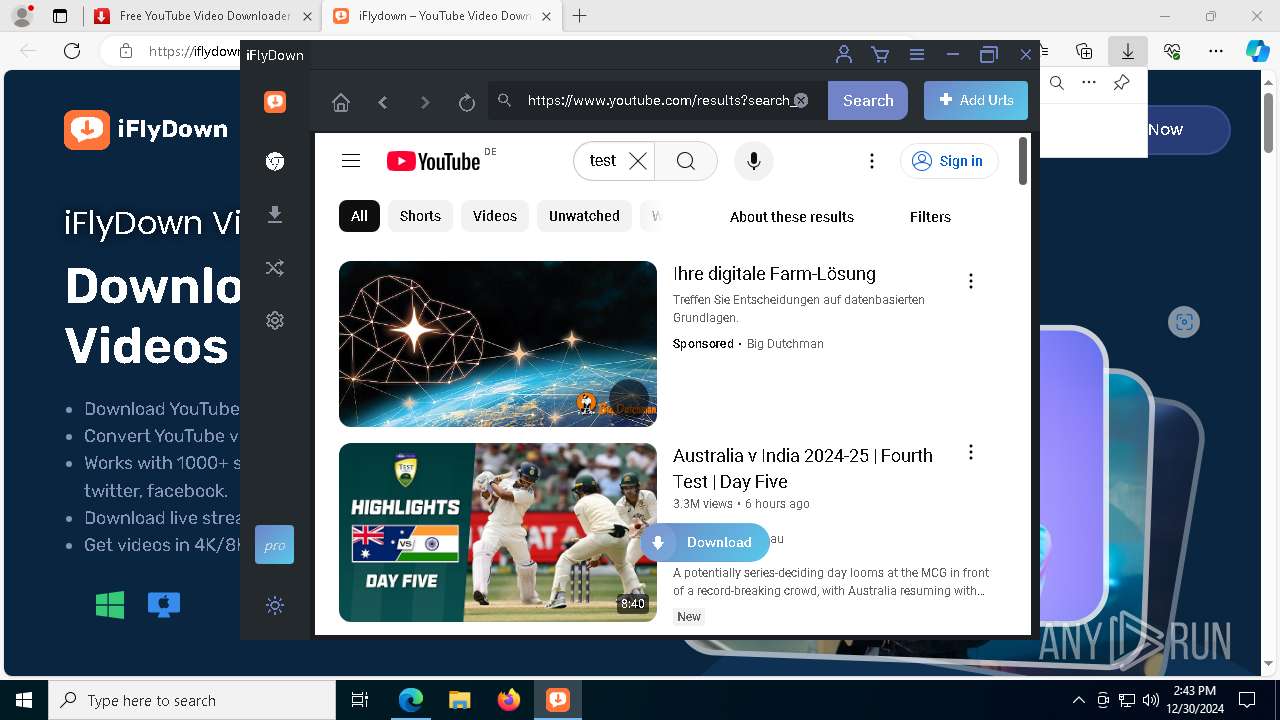
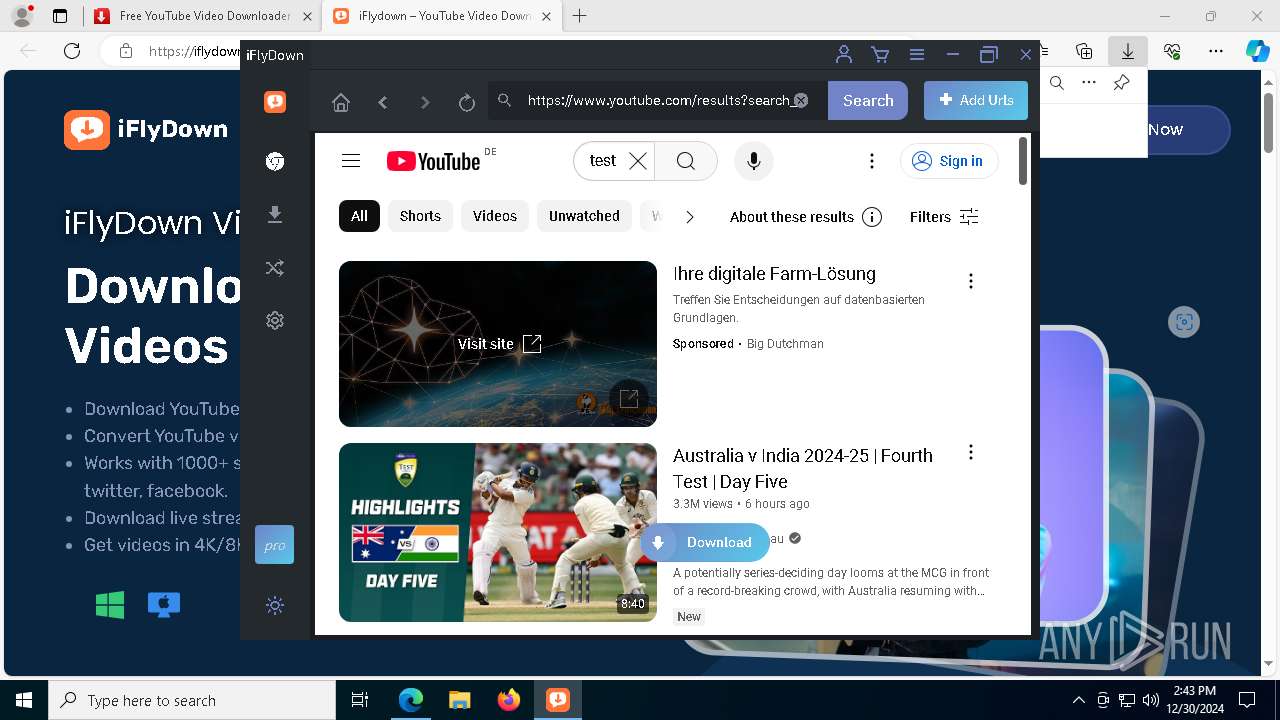
| 748 | "C:\Program Files\iFlyDown\resources\app.asar.unpacked\bin\yt-dlp.exe" -J --no-warnings --flat-playlist --extractor-args "youtube:lang=en" "https://www.bigdutchman.com/de/produkte/legehennenhaltung/bfn-fusion/bfn-fusion/?gad_source=2&gclid=EAIaIQobChMIsP_jq93PigMViQY6Ah0RwC6MEAEYASAAEgJtnvD_BwE" | C:\Program Files\iFlyDown\resources\app.asar.unpacked\bin\yt-dlp.exe | yt-dlp.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1200 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | "C:\Program Files\iFlyDown\iFlyDown.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\iFlyDown" --standard-schemes --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --service-worker-schemes --streaming-schemes --app-user-model-id=iFlyDown --app-path="C:\Program Files\iFlyDown\resources\app.asar" --enable-sandbox --enable-blink-features --disable-blink-features --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=4400 --field-trial-handle=1488,i,17370568339036461076,18242735071282201345,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Program Files\iFlyDown\iFlyDown.exe | — | iFlyDown.exe | |||||||||||
User: admin Company: iFlyDown Integrity Level: LOW Description: iFlyDown Exit code: 0 Version: 10.10.39 Modules
| |||||||||||||||
| 1400 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | yt-dlp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1448 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4200 --field-trial-handle=2340,i,4569595705337358665,11515769480000297281,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\iFlyDown\iFlyDown.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\iFlyDown" --standard-schemes --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --service-worker-schemes --streaming-schemes --app-path="C:\Program Files\iFlyDown\resources\app.asar" --no-sandbox --no-zygote --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2332 --field-trial-handle=1488,i,17370568339036461076,18242735071282201345,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Program Files\iFlyDown\iFlyDown.exe | — | iFlyDown.exe | |||||||||||
User: admin Company: iFlyDown Integrity Level: MEDIUM Description: iFlyDown Version: 10.10.39 Modules
| |||||||||||||||
| 1580 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5704 --field-trial-handle=2340,i,4569595705337358665,11515769480000297281,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\iFlyDown\iFlyDown.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\iFlyDown" --standard-schemes --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --service-worker-schemes --streaming-schemes --app-user-model-id=iFlyDown --app-path="C:\Program Files\iFlyDown\resources\app.asar" --enable-sandbox --enable-blink-features --disable-blink-features --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3816 --field-trial-handle=1488,i,17370568339036461076,18242735071282201345,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Program Files\iFlyDown\iFlyDown.exe | — | iFlyDown.exe | |||||||||||
User: admin Company: iFlyDown Integrity Level: LOW Description: iFlyDown Version: 10.10.39 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\iFlyDown\iFlyDown.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\iFlyDown" --standard-schemes --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --service-worker-schemes --streaming-schemes --app-user-model-id=iFlyDown --app-path="C:\Program Files\iFlyDown\resources\app.asar" --enable-sandbox --enable-blink-features --disable-blink-features --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3364 --field-trial-handle=1488,i,17370568339036461076,18242735071282201345,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Program Files\iFlyDown\iFlyDown.exe | — | iFlyDown.exe | |||||||||||
User: admin Company: iFlyDown Integrity Level: LOW Description: iFlyDown Exit code: 0 Version: 10.10.39 Modules
| |||||||||||||||
Total events
10 635
Read events
10 537
Write events
43
Delete events
55
Modification events
| (PID) Process: | (4708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4708) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0999061814892F00 | |||
| (PID) Process: | (4708) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6FB30E1814892F00 | |||
| (PID) Process: | (4708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {10E75C3C-0115-44C8-B76A-60E790D85504} | |||
| (PID) Process: | (4708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8828756F-8268-4458-ACE0-8758C308540D} | |||
| (PID) Process: | (4708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {91116153-F3D8-4446-820B-F308FD8A0368} | |||
| (PID) Process: | (4708) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6AFB501814892F00 | |||
Executable files
141
Suspicious files
745
Text files
114
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135651.TMP | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135641.TMP | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135641.TMP | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135670.TMP | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135670.TMP | — | |
MD5:— | SHA256:— | |||
| 4708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
144
DNS requests
162
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5764 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5308 | svchost.exe | HEAD | 200 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cc2ce8d1-e7f6-418e-9395-ac64ee9b4dcb?P1=1735943038&P2=404&P3=2&P4=FW%2fwKx2NJwWp3dagZiwhCfnEtHboEcpj8beaiGSY4TkVIALFtjmM%2fd7kwnIKjT93FgEZ5Iy%2bQ2iJkrg3PfoQVw%3d%3d | unknown | — | — | whitelisted |
5308 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cc2ce8d1-e7f6-418e-9395-ac64ee9b4dcb?P1=1735943038&P2=404&P3=2&P4=FW%2fwKx2NJwWp3dagZiwhCfnEtHboEcpj8beaiGSY4TkVIALFtjmM%2fd7kwnIKjT93FgEZ5Iy%2bQ2iJkrg3PfoQVw%3d%3d | unknown | — | — | whitelisted |
5308 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cc2ce8d1-e7f6-418e-9395-ac64ee9b4dcb?P1=1735943038&P2=404&P3=2&P4=FW%2fwKx2NJwWp3dagZiwhCfnEtHboEcpj8beaiGSY4TkVIALFtjmM%2fd7kwnIKjT93FgEZ5Iy%2bQ2iJkrg3PfoQVw%3d%3d | unknown | — | — | whitelisted |
5308 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cc2ce8d1-e7f6-418e-9395-ac64ee9b4dcb?P1=1735943038&P2=404&P3=2&P4=FW%2fwKx2NJwWp3dagZiwhCfnEtHboEcpj8beaiGSY4TkVIALFtjmM%2fd7kwnIKjT93FgEZ5Iy%2bQ2iJkrg3PfoQVw%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5308 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cc2ce8d1-e7f6-418e-9395-ac64ee9b4dcb?P1=1735943038&P2=404&P3=2&P4=FW%2fwKx2NJwWp3dagZiwhCfnEtHboEcpj8beaiGSY4TkVIALFtjmM%2fd7kwnIKjT93FgEZ5Iy%2bQ2iJkrg3PfoQVw%3d%3d | unknown | — | — | whitelisted |
5308 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cc2ce8d1-e7f6-418e-9395-ac64ee9b4dcb?P1=1735943038&P2=404&P3=2&P4=FW%2fwKx2NJwWp3dagZiwhCfnEtHboEcpj8beaiGSY4TkVIALFtjmM%2fd7kwnIKjT93FgEZ5Iy%2bQ2iJkrg3PfoQVw%3d%3d | unknown | — | — | whitelisted |
6304 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5764 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6596 | msedge.exe | 104.18.95.41:443 | challenges.cloudflare.com | — | — | whitelisted |
6596 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4708 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6596 | msedge.exe | 172.67.191.182:443 | yt1d.com | — | — | unknown |
6596 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6596 | msedge.exe | 142.250.185.138:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
6596 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6596 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
yt1d.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
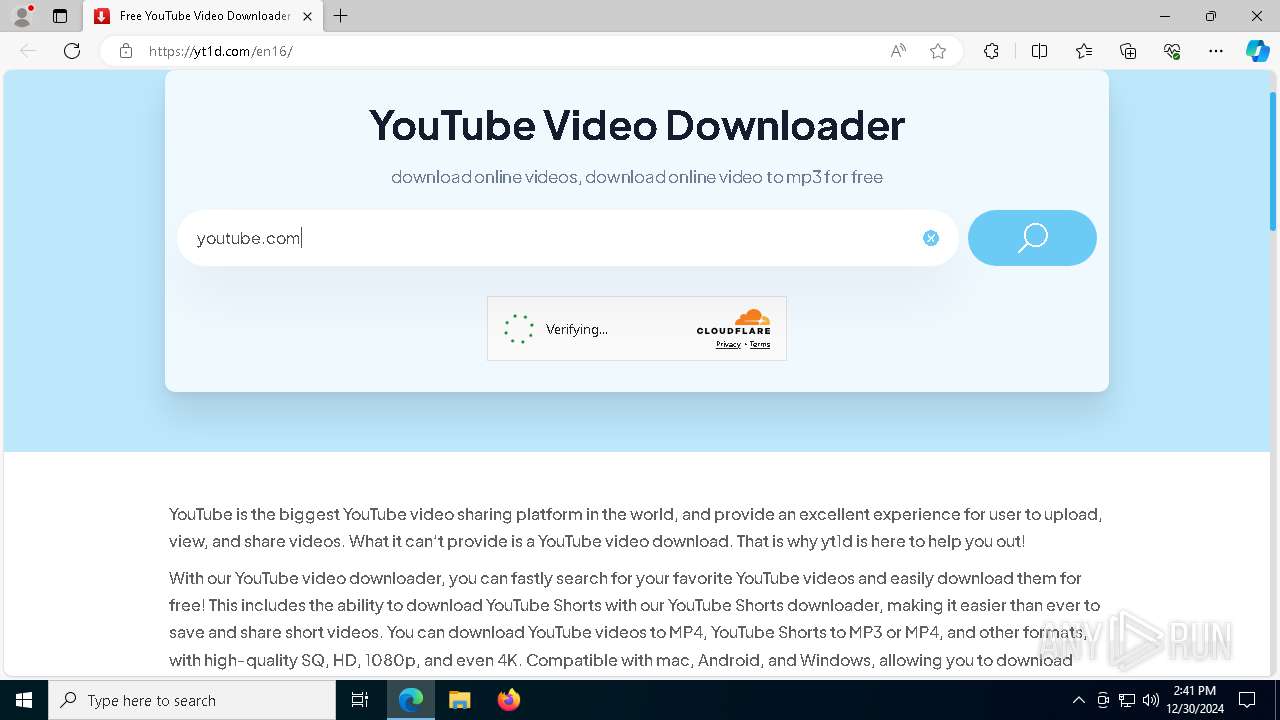
6596 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6596 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6596 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6596 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6224 | iFlyDown.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6224 | iFlyDown.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
iFlyDownInstall_v10.10.39.exe | Window, shadowimage, images/shadow.png
|
iFlyDownInstall_v10.10.39.exe | Window, size, 560,350
|
iFlyDownInstall_v10.10.39.exe | Window, sizebox, 0,0,0,0
|
iFlyDownInstall_v10.10.39.exe | Window, showshadow, true
|
iFlyDownInstall_v10.10.39.exe | Window, caption, 0,0,0,560
|
iFlyDownInstall_v10.10.39.exe | Window, roundcorner, 3,3
|
iFlyDownInstall_v10.10.39.exe | ControlUI, padding, 240,95,0,0
|
iFlyDownInstall_v10.10.39.exe | Window, shadowsize, 14
|
iFlyDownInstall_v10.10.39.exe | Window, shadowcorner, 14,14,14,14
|
iFlyDownInstall_v10.10.39.exe | ControlUI, width, 80
|