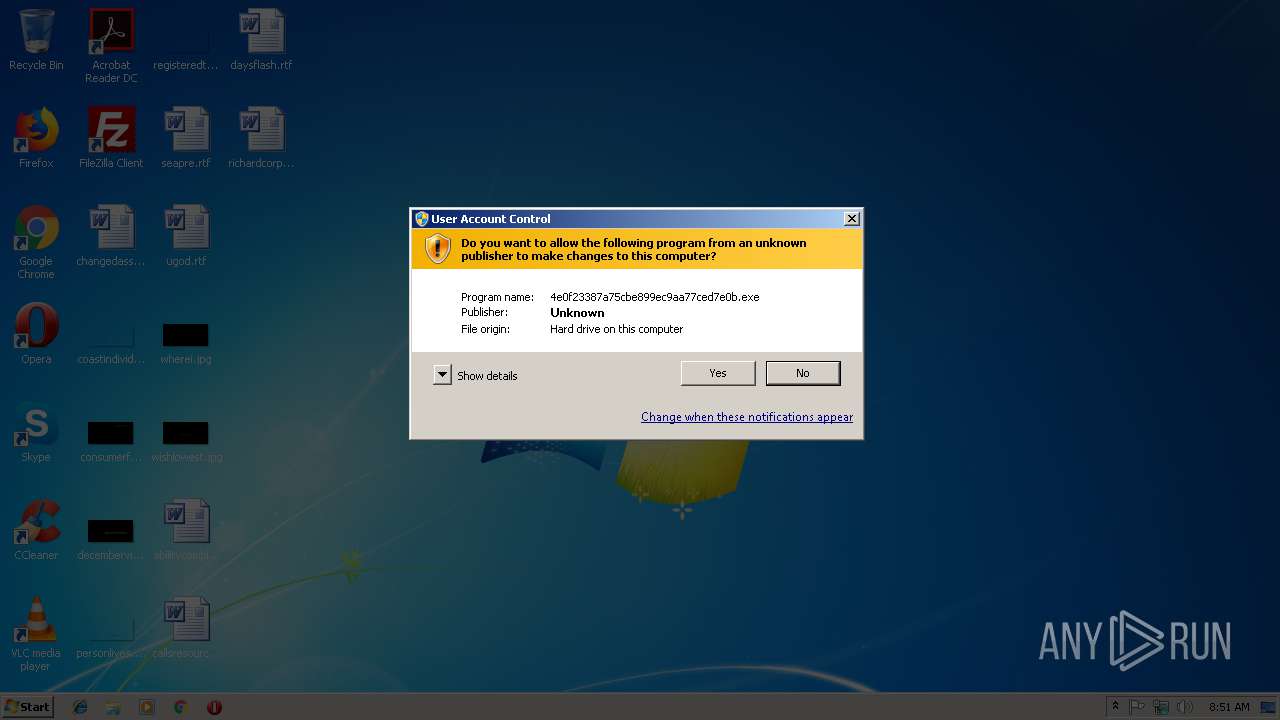
| File name: | 4e0f23387a75cbe899ec9aa77ced7e0b |
| Full analysis: | https://app.any.run/tasks/af7693ab-39d2-4943-a23e-edeaf41d932c |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 08:51:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4E0F23387A75CBE899EC9AA77CED7E0B |
| SHA1: | E74BFACCDE2362A7679F01ABB0AE9E7B2FCD33D3 |
| SHA256: | C9A31509CAE2434A0F4884880ADA28105A0CA7F9F801EEB6D97231E790B3D09B |
| SSDEEP: | 98304:V1v8/6qM8Dty8xhHDzzSgQcZFiCsX6mpgQxLhiIA:V1v8/6qr7zfSxcmC+6mD/A |
MALICIOUS
Application was dropped or rewritten from another process
- 7za.exe (PID: 3464)
- nssm.exe (PID: 3680)
- nssm.exe (PID: 3672)
- nssm.exe (PID: 3004)
- update.exe (PID: 988)
- nssm.exe (PID: 2452)
SUSPICIOUS
Executable content was dropped or overwritten
- 4e0f23387a75cbe899ec9aa77ced7e0b.exe (PID: 3432)
- cmd.exe (PID: 2636)
- 7za.exe (PID: 3464)
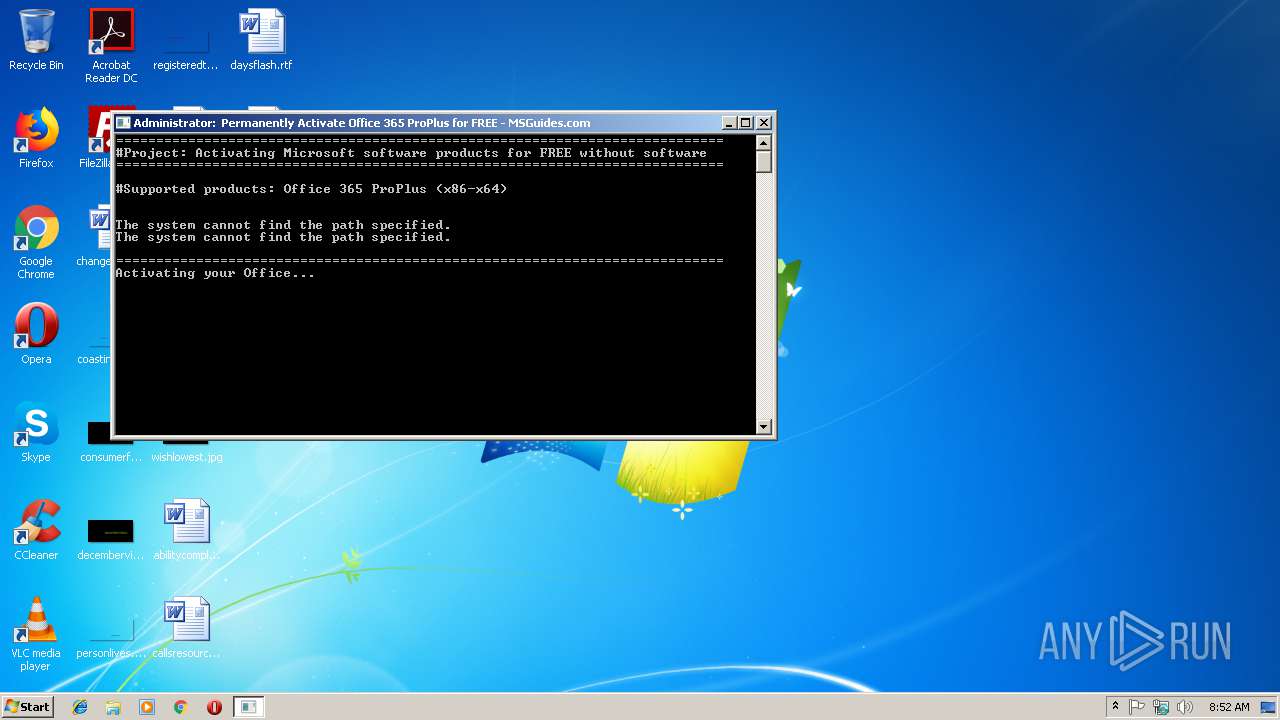
Starts CMD.EXE for commands execution
- 4e0f23387a75cbe899ec9aa77ced7e0b.exe (PID: 3432)
- update.exe (PID: 988)
- cmd.exe (PID: 2700)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2636)
Writes to a desktop.ini file (may be used to cloak folders)
- 7za.exe (PID: 3464)
Reads CPU info
- reg.exe (PID: 2336)
Application launched itself
- cmd.exe (PID: 2700)
- chrmstp.exe (PID: 2728)
Creates files in the Windows directory
- chrome.exe (PID: 2472)
- chrmstp.exe (PID: 2728)
- chrmstp.exe (PID: 3132)
- chrome.exe (PID: 3024)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2636)
Executes scripts
- cmd.exe (PID: 2700)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3024)
Removes files from Windows directory
- chrome.exe (PID: 3024)
Creates files in the program directory
- chrmstp.exe (PID: 2728)
INFO
Application launched itself
- chrome.exe (PID: 3024)
Changes settings of System certificates
- chrome.exe (PID: 3024)
Adds / modifies Windows certificates
- chrome.exe (PID: 3024)
Connects to unusual port
- chrome.exe (PID: 3024)
Reads settings of System Certificates
- chrome.exe (PID: 3024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (30.9) |
| .scr | | | Windows screen saver (14.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.3) |
| .exe | | | Win32 Executable (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:06:15 18:06:28+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 37376 |
| InitializedDataSize: | 3723264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jun-2015 16:06:28 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Jun-2015 16:06:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x00001C51 | 0x00001E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.33053 |
.text | 0x00003000 | 0x0000735A | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57446 |
.rdata | 0x0000B000 | 0x0000065E | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.24362 |
.data | 0x0000C000 | 0x00001838 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.00167 |
.rsrc | 0x0000E000 | 0x0038B340 | 0x0038B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.90909 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09999 | 668 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
B | 5.37391 | 2064 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
D | 3.46772 | 14 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
F | 7.90923 | 3712644 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
I | 4.07782 | 32 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
N | 3.26395 | 48 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
O | 0.650022 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
130
Monitored processes
94
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,9037479585346319953,15506158610924691332,131072 --lang=en-US --no-sandbox --service-request-channel-token=7436480185E0D1ACB9FB60553D79B7F4 --mojo-platform-channel-handle=788 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: SYSTEM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,9037479585346319953,15506158610924691332,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6EFCCA48CED689A62DB003AC8ADDE086 --mojo-platform-channel-handle=5076 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 956 | cscript //nologo ospp.vbs /unpkey:DRTFM | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 988 | C:\Perform\update.exe | C:\Perform\update.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,9037479585346319953,15506158610924691332,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7DD9435D376EB0F12F968CA79FDC8620 --mojo-platform-channel-handle=2392 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,9037479585346319953,15506158610924691332,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2B5982539B0704199330F52B49186E0E --mojo-platform-channel-handle=2952 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,9037479585346319953,15506158610924691332,131072 --disable-gpu-compositing --service-pipe-token=85F696CE8325EB4BE7C0635745E1BD7F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=85F696CE8325EB4BE7C0635745E1BD7F --renderer-client-id=30 --mojo-platform-channel-handle=4852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,9037479585346319953,15506158610924691332,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=EEE16EFFB5AFD7A2E5F8AB48ECF483D3 --mojo-platform-channel-handle=5960 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,9037479585346319953,15506158610924691332,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3649D67E199D37136E3D0CD15DAEA7E4 --mojo-platform-channel-handle=4596 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,9037479585346319953,15506158610924691332,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=381C4EA42F3CB6B67B10A09C210683A7 --mojo-platform-channel-handle=5936 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 150
Read events
1 018
Write events
128
Delete events
4
Modification events
| (PID) Process: | (3432) 4e0f23387a75cbe899ec9aa77ced7e0b.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3432) 4e0f23387a75cbe899ec9aa77ced7e0b.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3672) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\NSSM |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Perform\nssm.exe | |||
| (PID) Process: | (3672) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\NSSM |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
| (PID) Process: | (3672) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Advanced Systemcare Security\Parameters |
| Operation: | write | Name: | Application |
Value: C:\Program Files\Google\Chrome\Application\chrome.exe | |||
| (PID) Process: | (3672) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Advanced Systemcare Security\Parameters |
| Operation: | write | Name: | AppParameters |
Value: http://www.0day-xmr.com.br/ | |||
| (PID) Process: | (3672) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Advanced Systemcare Security\Parameters |
| Operation: | write | Name: | AppDirectory |
Value: C:\Program Files\Google\Chrome\Application | |||
| (PID) Process: | (3672) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Advanced Systemcare Security\Parameters\AppExit |
| Operation: | write | Name: | |
Value: Restart | |||
| (PID) Process: | (3680) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\NSSM |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Perform\nssm.exe | |||
| (PID) Process: | (3680) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\NSSM |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
Executable files
8
Suspicious files
36
Text files
656
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\First Run | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
28
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3024 | chrome.exe | GET | 200 | 216.58.215.243:80 | http://www.0day-xmr.com.br/ | US | html | 10.3 Kb | suspicious |
3024 | chrome.exe | GET | 200 | 173.194.160.71:80 | http://r2---sn-1gi7znes.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYzU3QUFWbnlGT3kzQWtjM3lqNzVJallBUQ/1.0.0.4_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.212.170.95&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1544777431&mv=m&pl=24&shardbypass=yes | US | crx | 184 Kb | whitelisted |
3024 | chrome.exe | GET | 302 | 172.217.168.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYzU3QUFWbnlGT3kzQWtjM3lqNzVJallBUQ/1.0.0.4_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 500 b | whitelisted |
3024 | chrome.exe | GET | 302 | 172.217.168.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZDI3QUFWdDJLbzhIMFNCY21HWi04QmFaZw/6818.528.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 505 b | whitelisted |
3024 | chrome.exe | GET | 200 | 173.194.160.70:80 | http://r1---sn-1gi7znes.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZDI3QUFWdDJLbzhIMFNCY21HWi04QmFaZw/6818.528.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.212.170.95&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1544777431&mv=m&pl=24&shardbypass=yes | US | crx | 826 Kb | whitelisted |
3024 | chrome.exe | GET | 200 | 94.31.29.128:80 | http://cdn.popcash.net/pop.js | GB | text | 25.7 Kb | whitelisted |
3024 | chrome.exe | GET | 200 | 172.217.168.34:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 27.5 Kb | whitelisted |
3024 | chrome.exe | GET | 200 | 216.58.215.233:80 | http://www.blogblog.com/1kt/simple/body_gradient_tile_light.png | US | image | 95 b | whitelisted |
3024 | chrome.exe | GET | 200 | 216.58.215.233:80 | http://www.blogblog.com/1kt/simple/gradients_light.png | US | image | 403 b | whitelisted |
3024 | chrome.exe | GET | 200 | 216.58.215.243:80 | http://www.0day-xmr.com.br/b/stats?style=BLACK_TRANSPARENT&timeRange=ALL_TIME&token=APq4FmB4QuHr-mKKbCvByxUaF_mq9J5u4xvOuEAtIFwR2O4zF7Ssvv5EFajW46FRiQc74THJ0otDF9o7AxmNEWMfw-O_0OIU1Q | US | text | 209 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3024 | chrome.exe | 216.58.215.243:80 | www.0day-xmr.com.br | Google Inc. | US | whitelisted |
3024 | chrome.exe | 172.217.168.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 172.217.168.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 172.217.168.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 216.58.215.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 173.194.160.71:80 | r2---sn-1gi7znes.gvt1.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 172.217.168.14:443 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 216.58.215.233:443 | www.blogger.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 173.194.160.70:80 | r1---sn-1gi7znes.gvt1.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 94.16.113.104:443 | ethtrader.de | netcup GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.0day-xmr.com.br |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
redirector.gvt1.com |
| whitelisted |
r2---sn-1gi7znes.gvt1.com |
| whitelisted |
www.blogger.com |
| shared |
apis.google.com |
| whitelisted |
r1---sn-1gi7znes.gvt1.com |
| whitelisted |