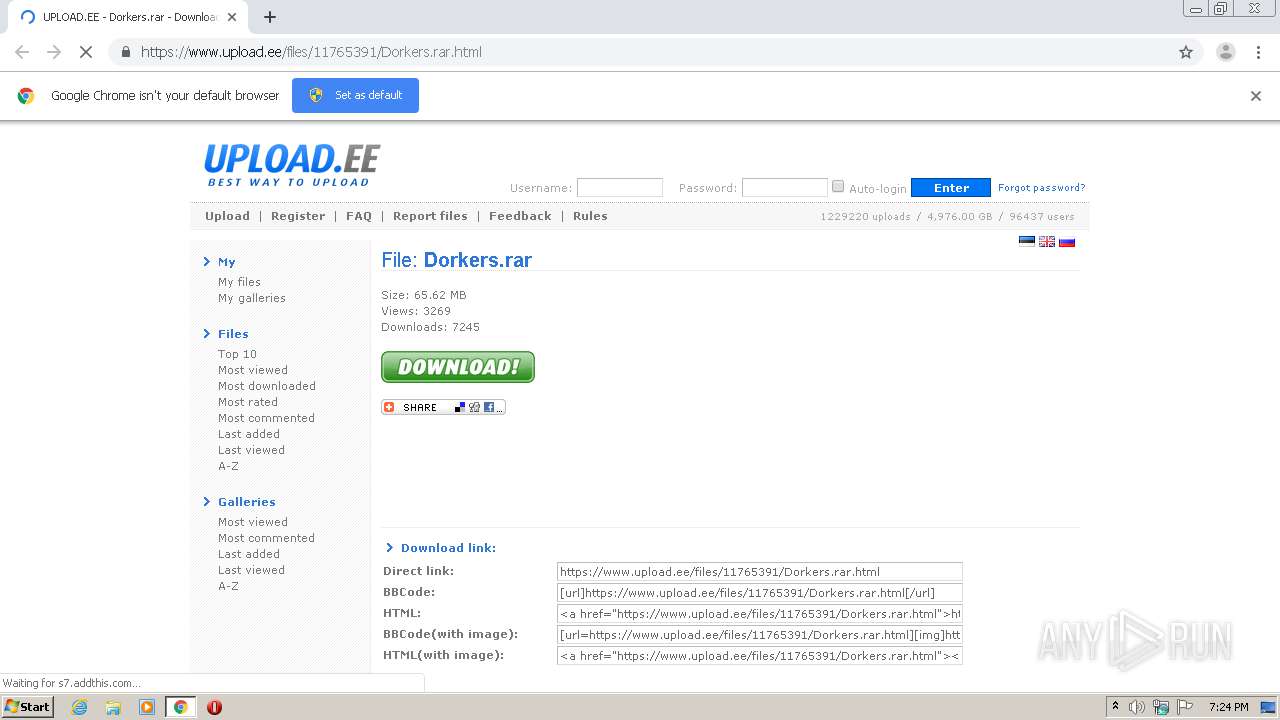
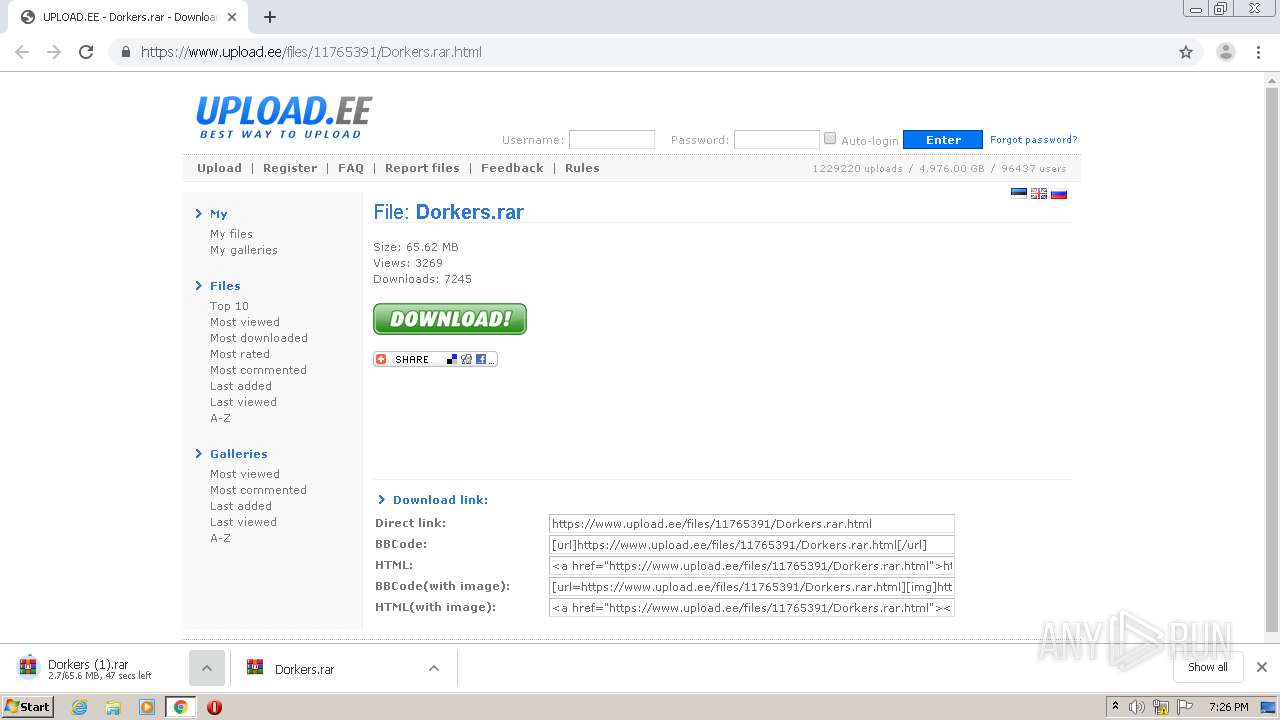
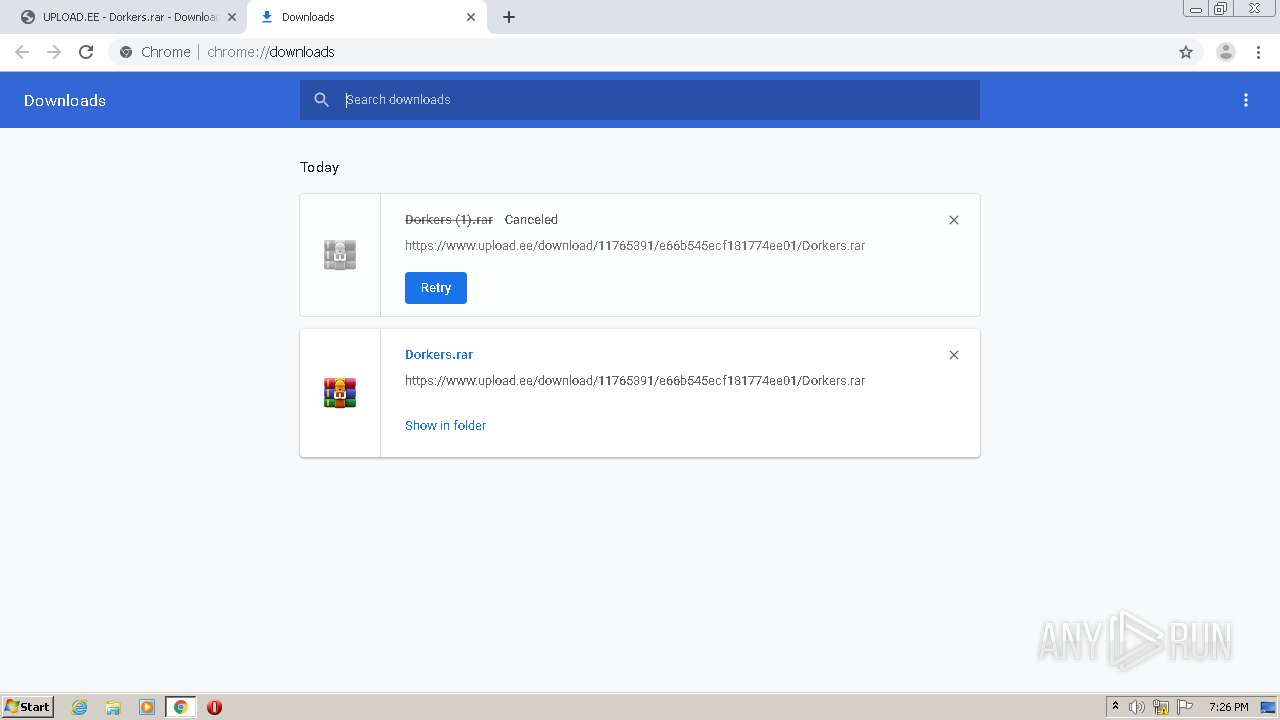
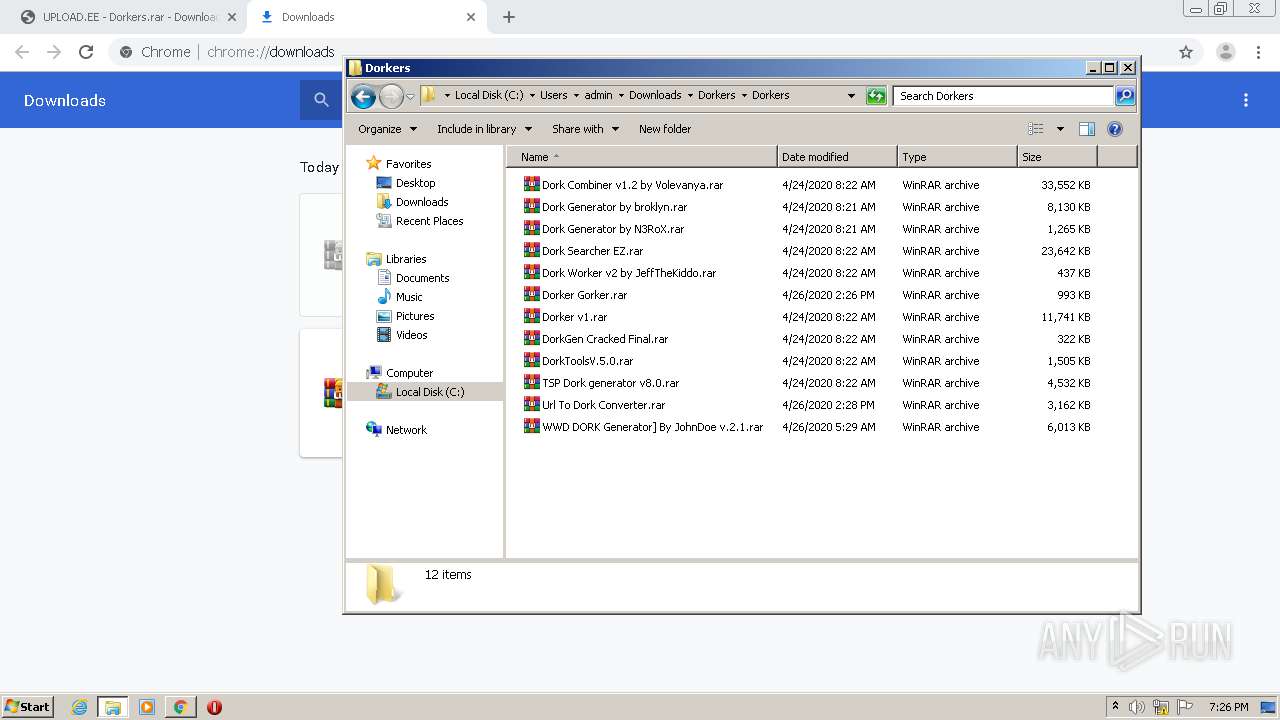
| URL: | https://www.upload.ee/files/11765391/Dorkers.rar.html |
| Full analysis: | https://app.any.run/tasks/d834ebad-87df-482d-be61-ab8ca5045fe7 |
| Verdict: | Malicious activity |
| Analysis date: | June 20, 2020, 18:24:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0CEF52B612CDE0B48E3220F2B6E95B53 |
| SHA1: | 73C7A8542808673C667DE4AFF8C60CB4FDE5519C |
| SHA256: | C9962C0CCD7BC59AE4715D73518316158BE25C98A78912FF29C38ECEC4F115C2 |
| SSDEEP: | 3:N8DSLr7MJmULcW0M+jn:2OLr0EpM+jn |
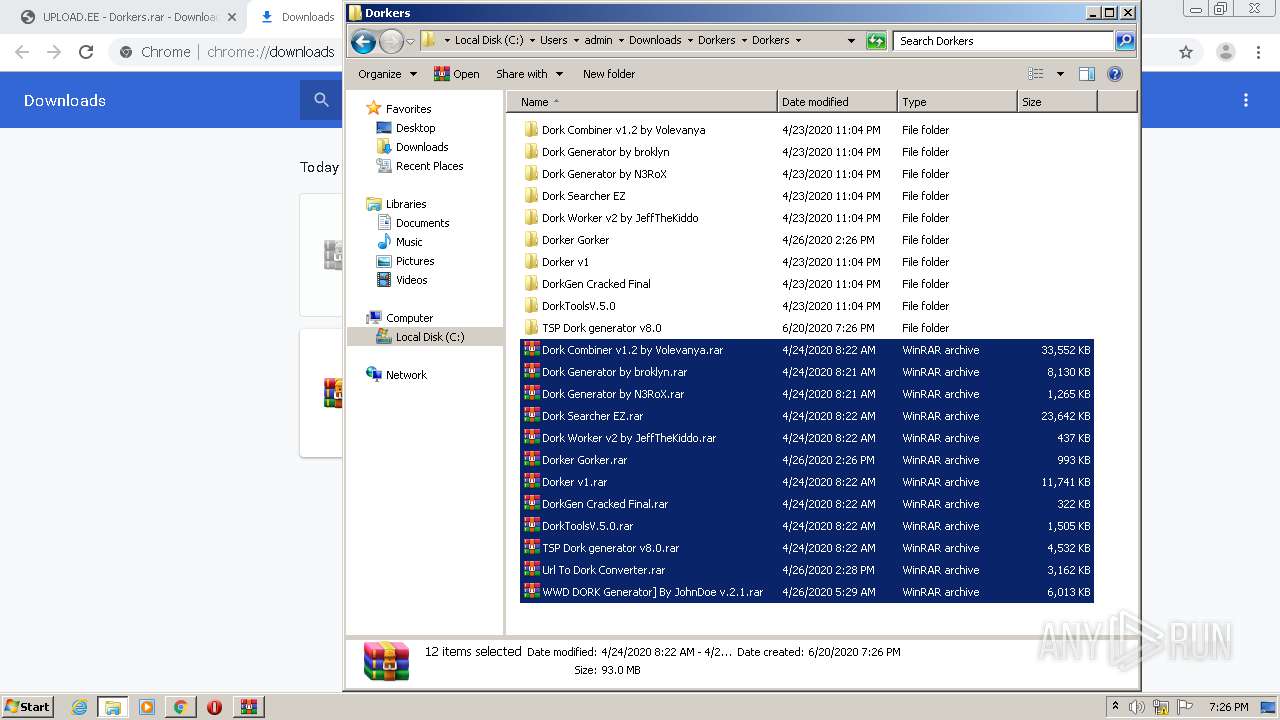
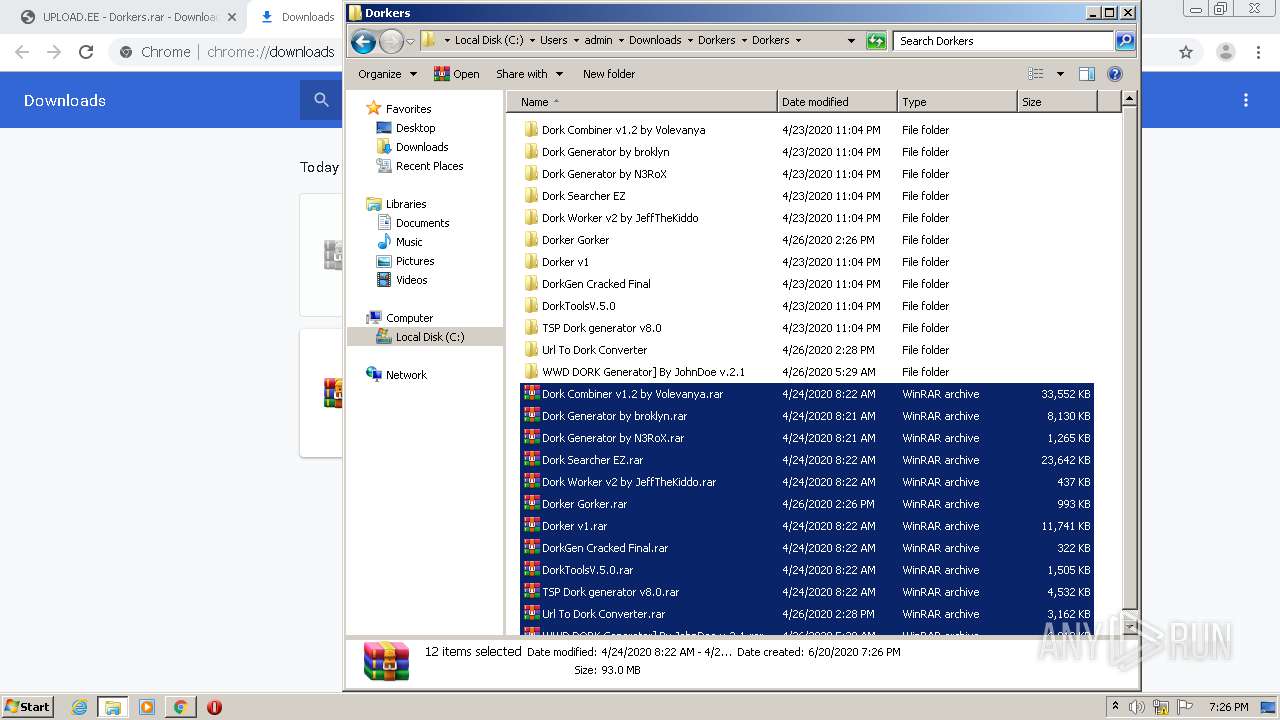
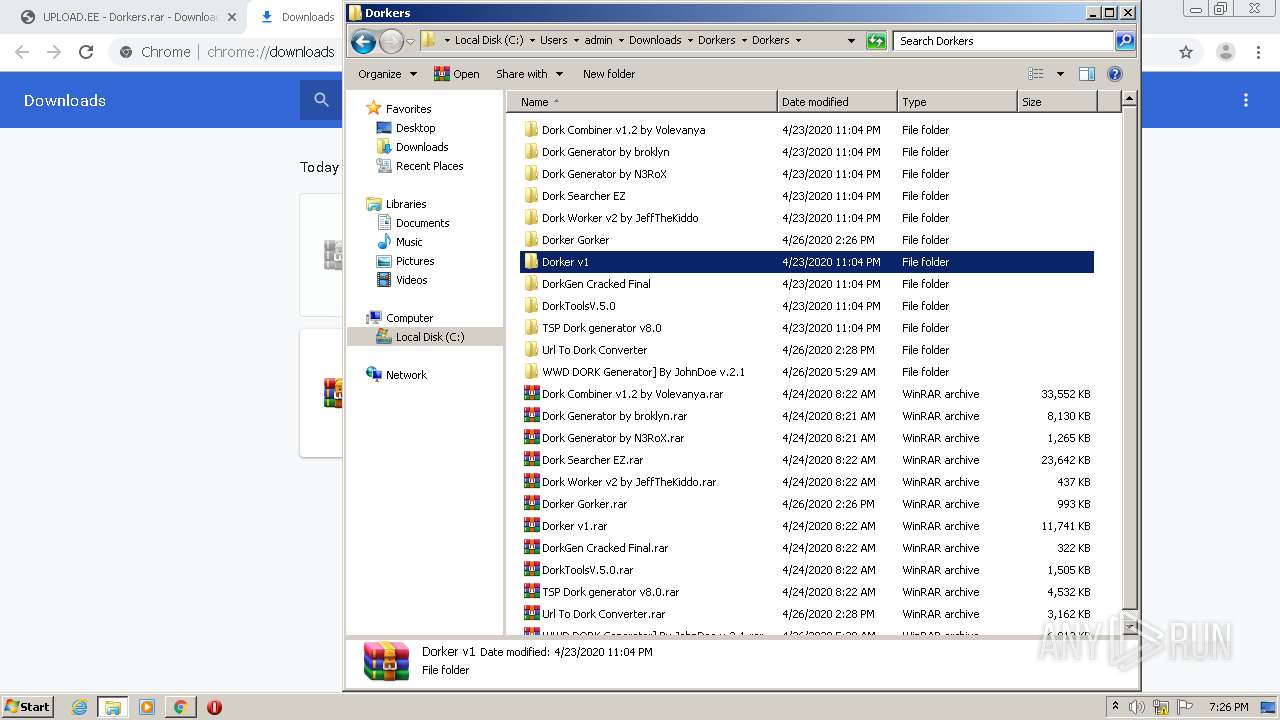
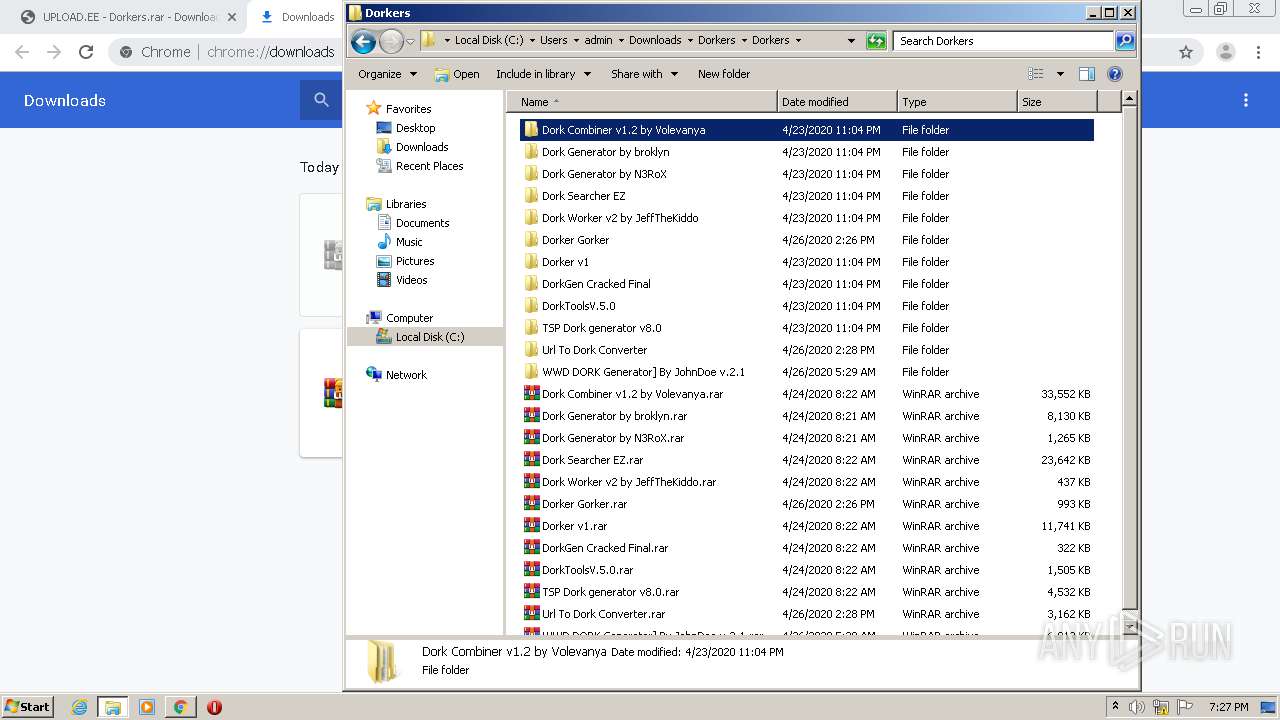
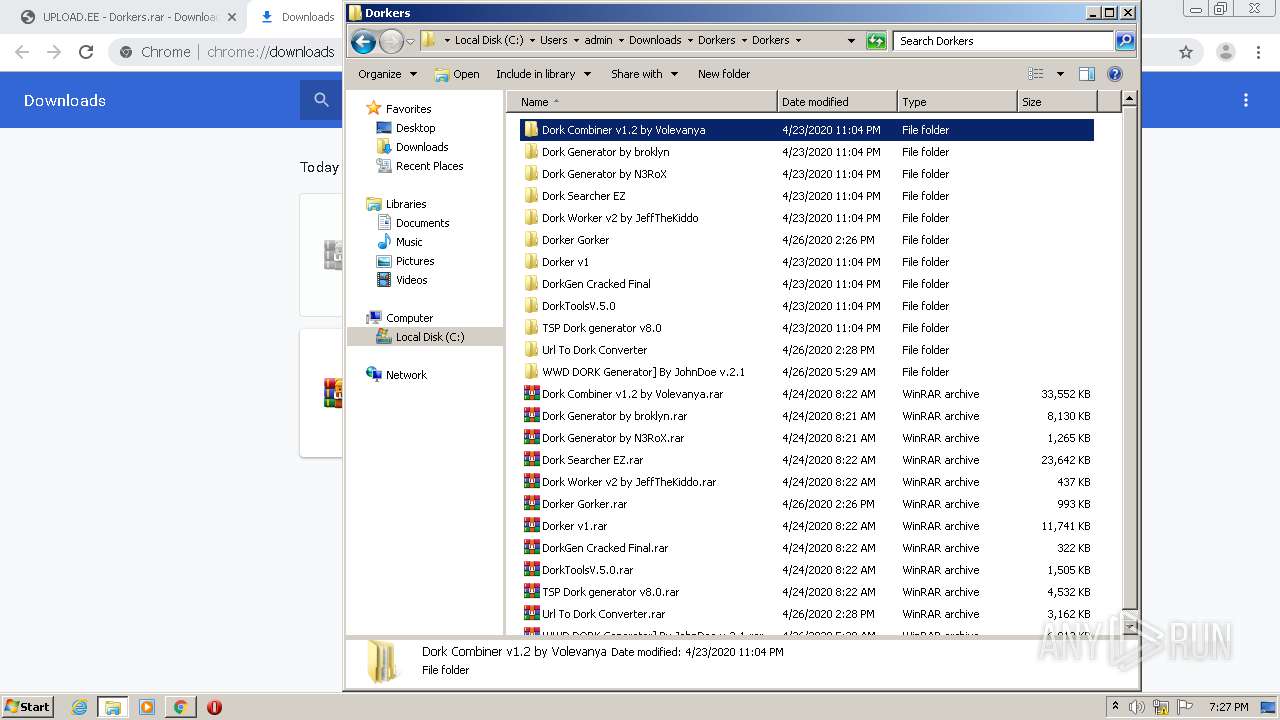
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 888)
- WerFault.exe (PID: 996)
- explorer.exe (PID: 468)
- byZysnet.exe (PID: 3420)
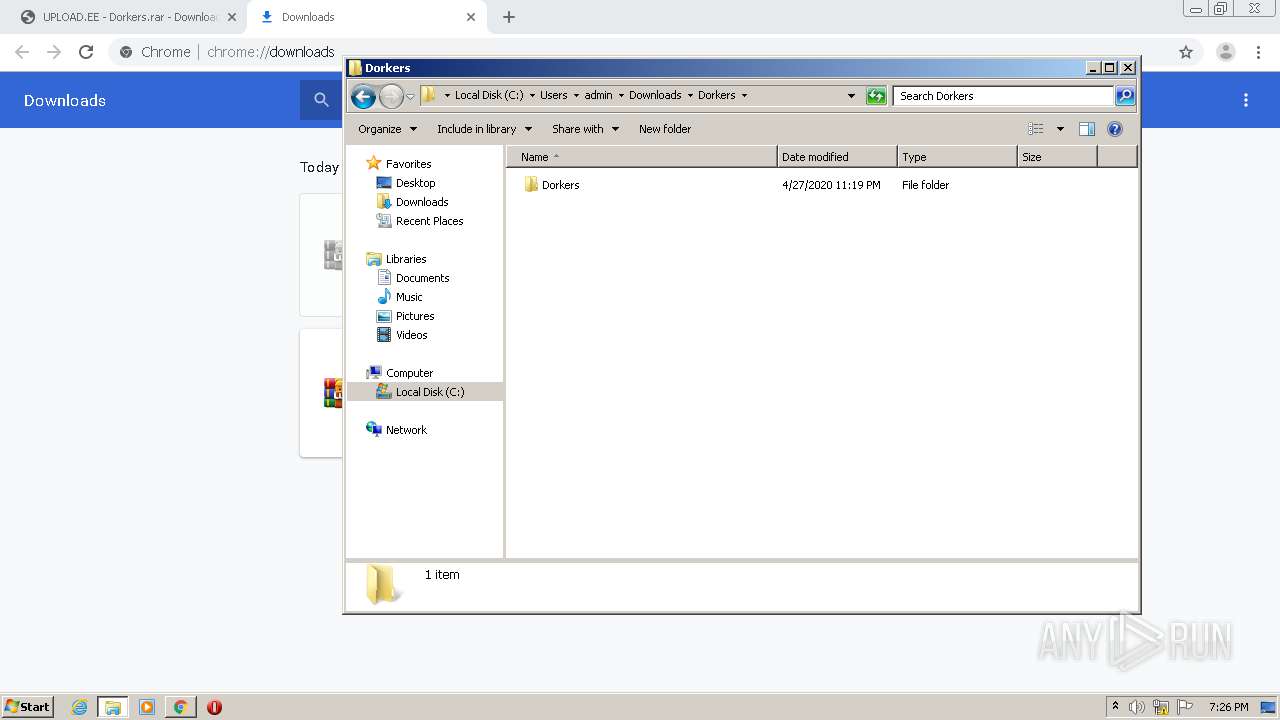
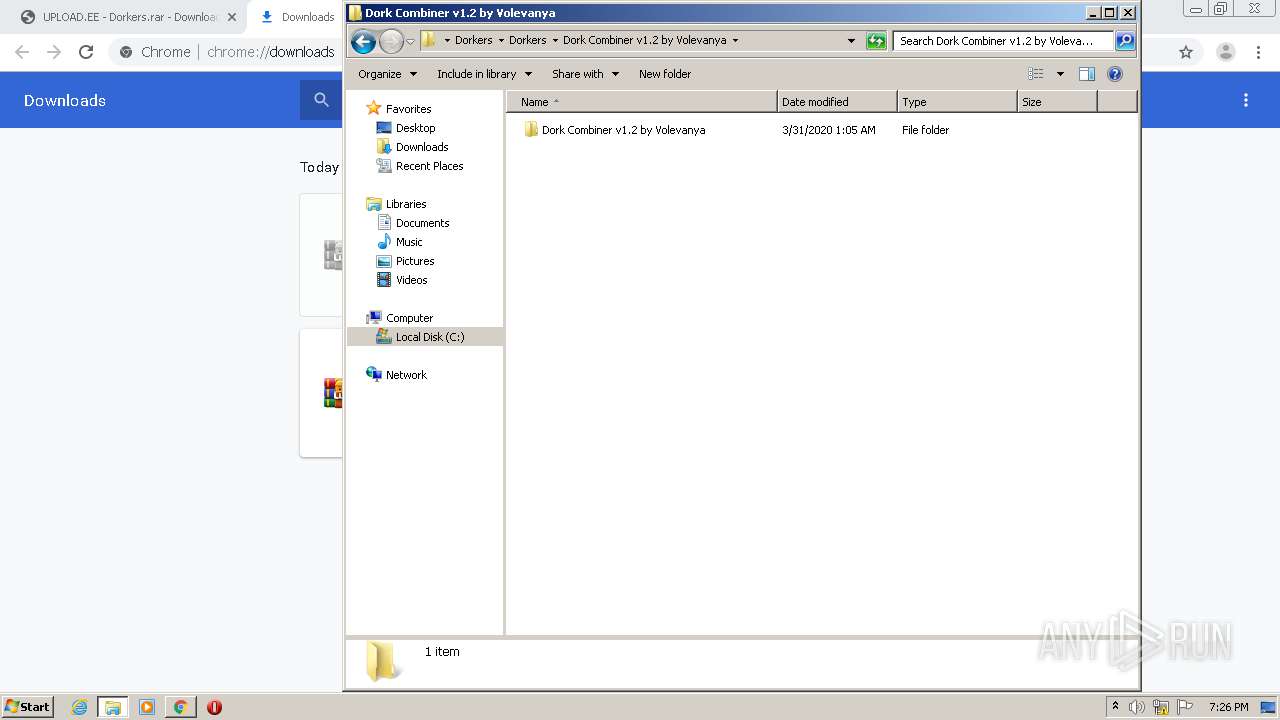
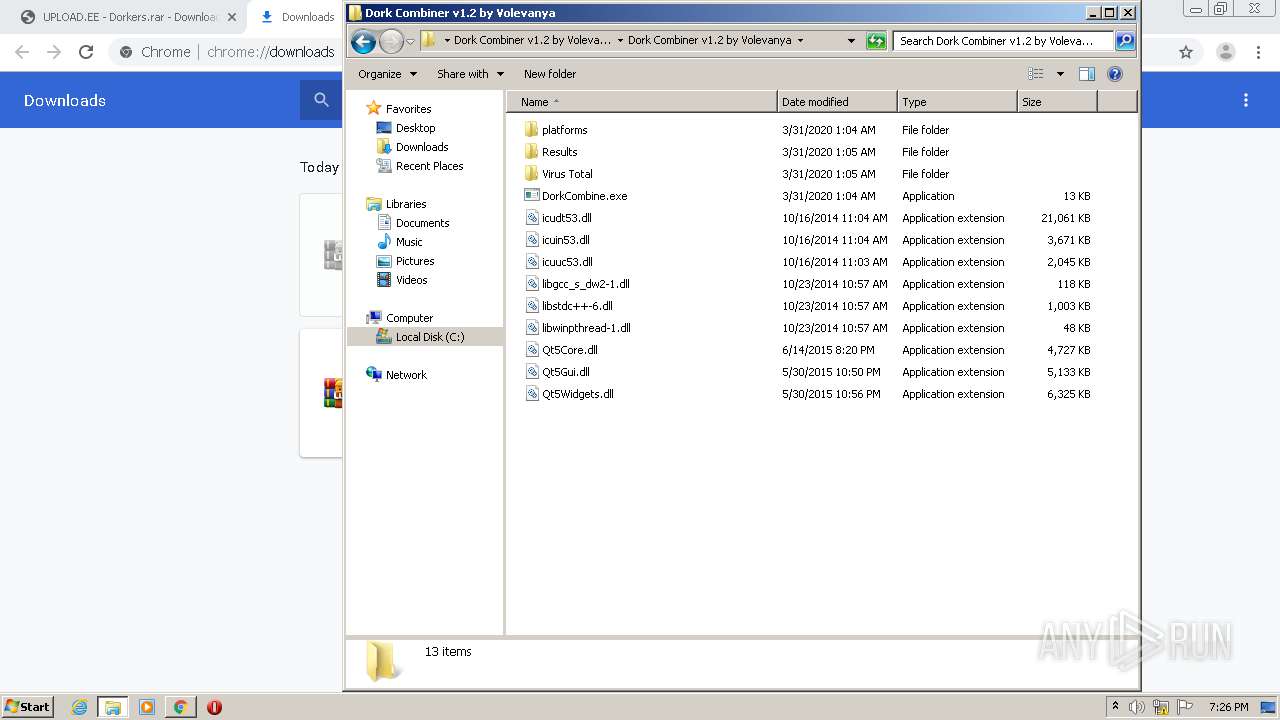
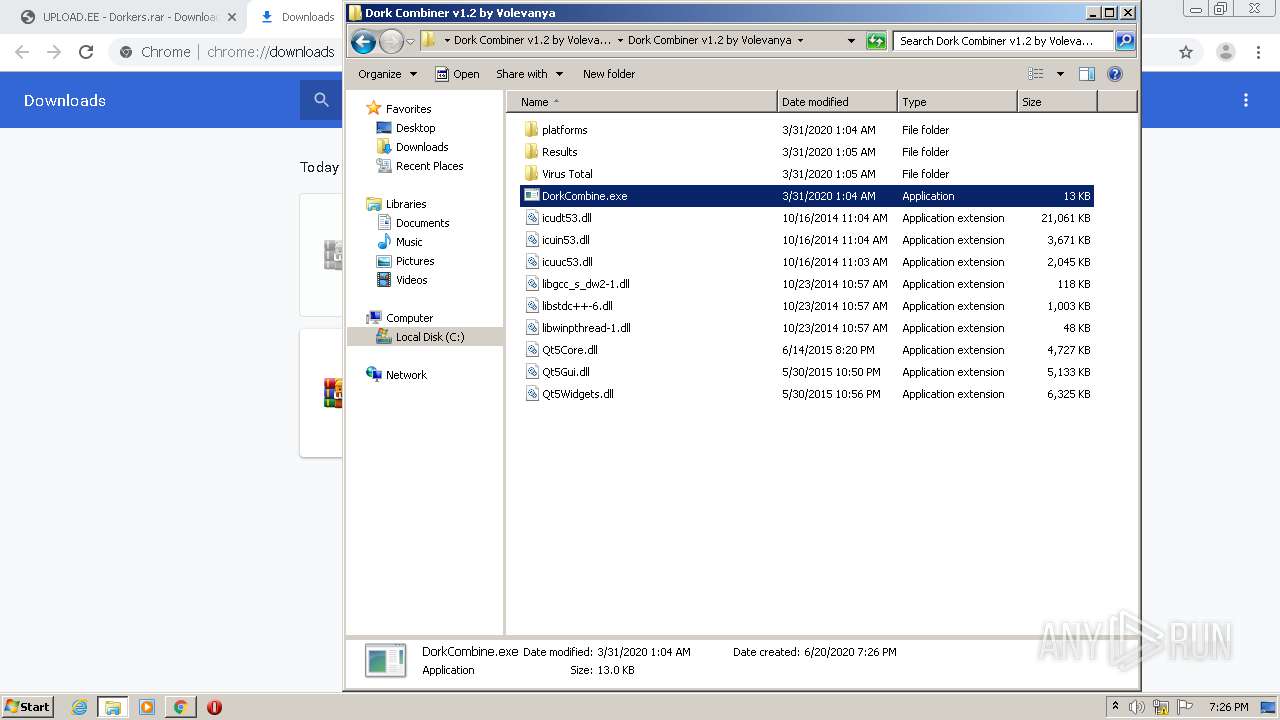
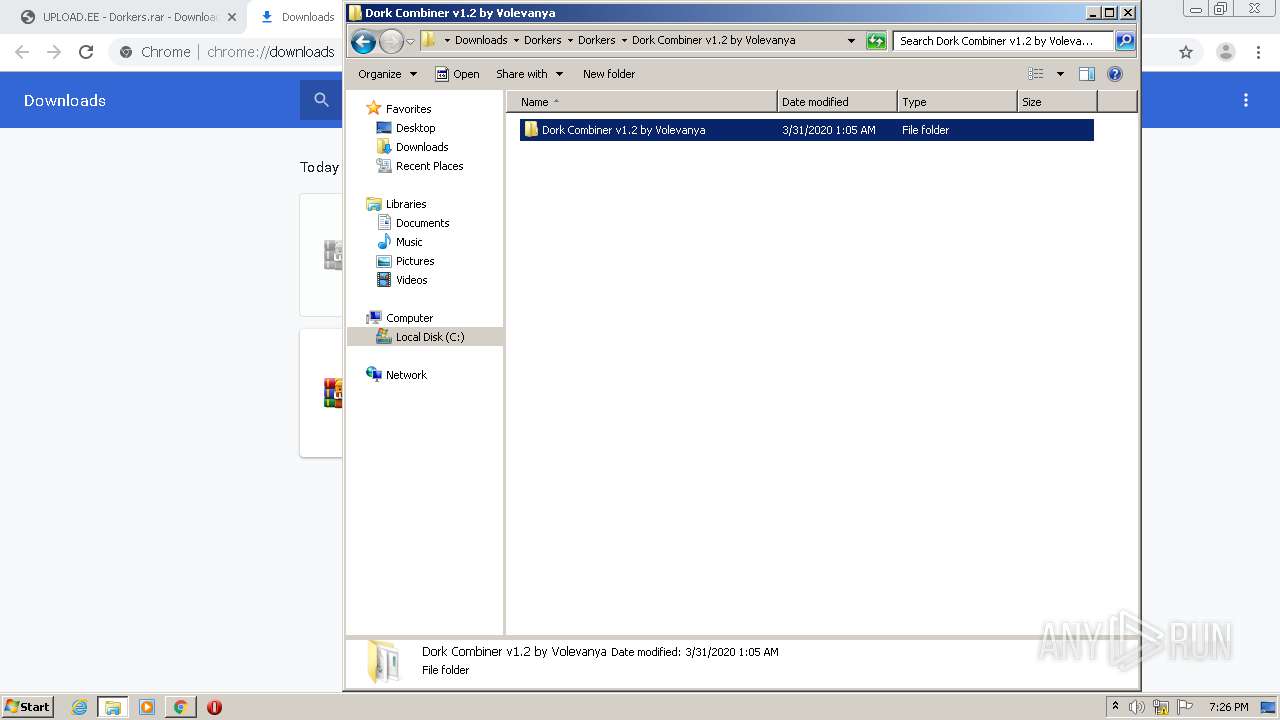
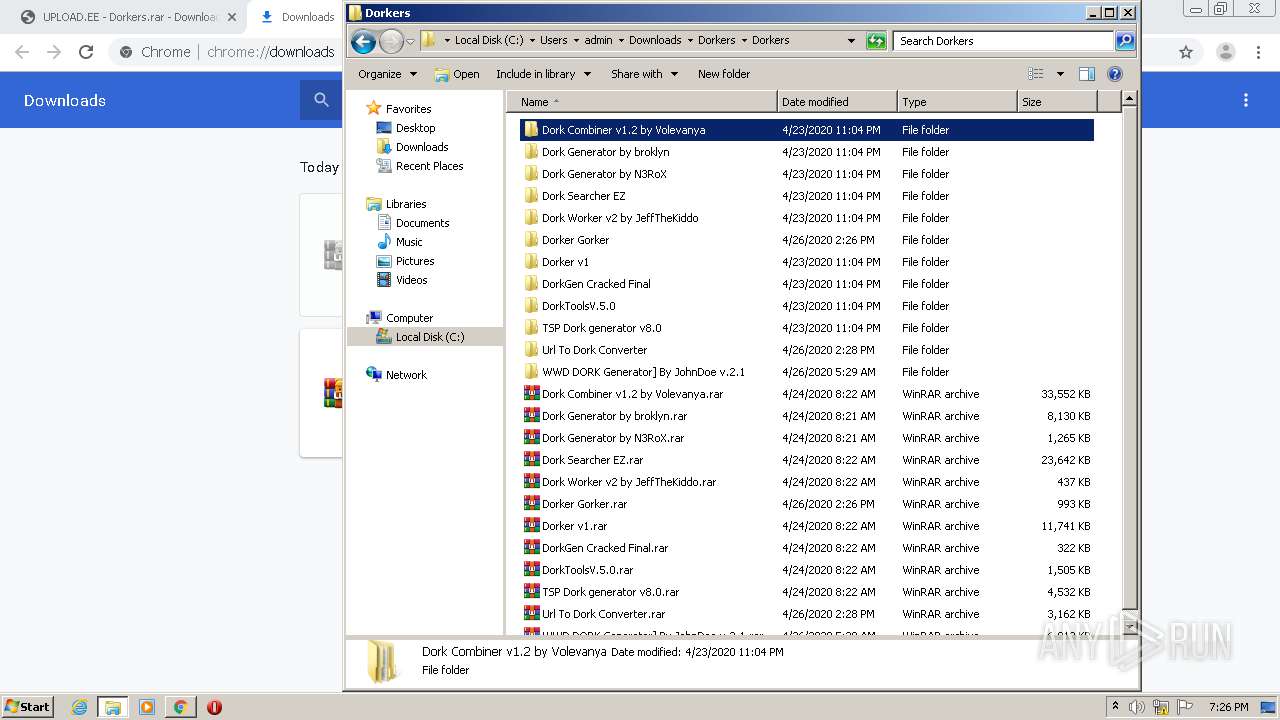
Application was dropped or rewritten from another process
- DorkCombine.exe (PID: 2480)
- Microsoft Windows Protocol Services Host.exe (PID: 1204)
- Microsoft Windows Protocol Monitor.exe (PID: 2332)
- byZysnet.exe (PID: 3420)
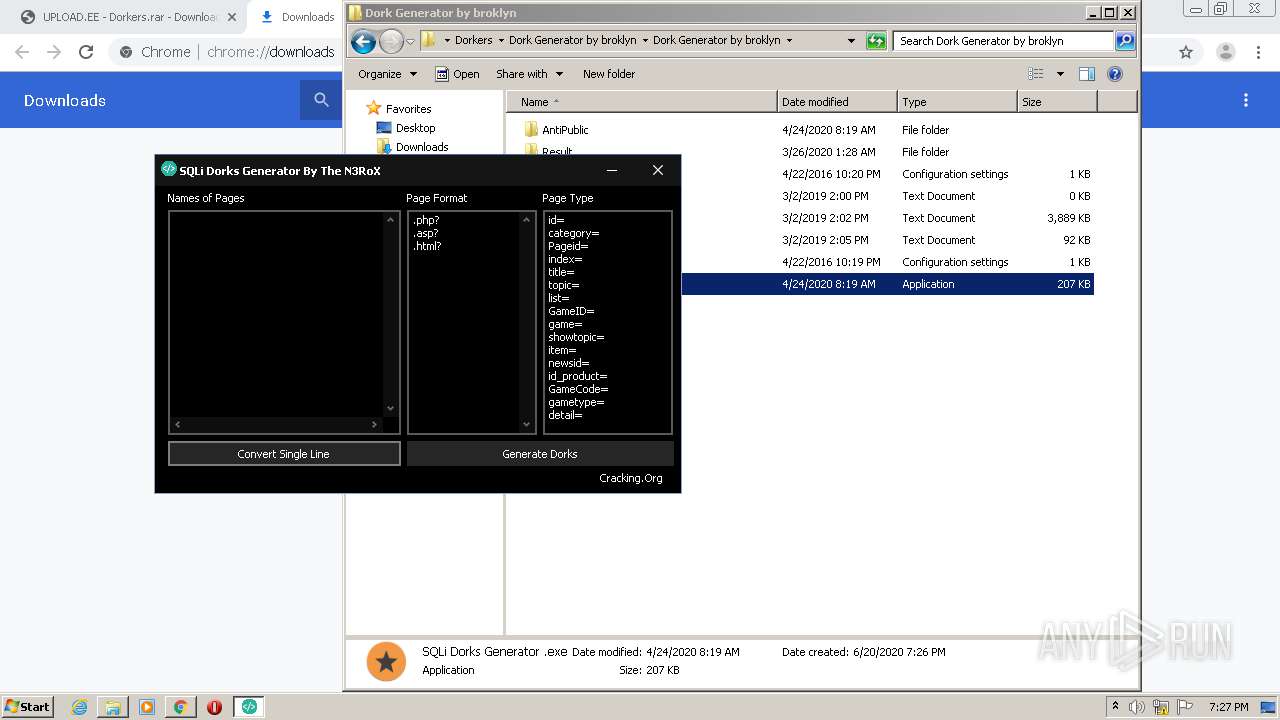
- SQLi Dorks Generator .exe (PID: 2980)
- Gen.exe (PID: 732)
- Microsoft Windows Protocol Services Host.exe (PID: 3768)
Writes to a start menu file
- DorkCombine.exe (PID: 2480)
- SQLi Dorks Generator .exe (PID: 2980)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2712)
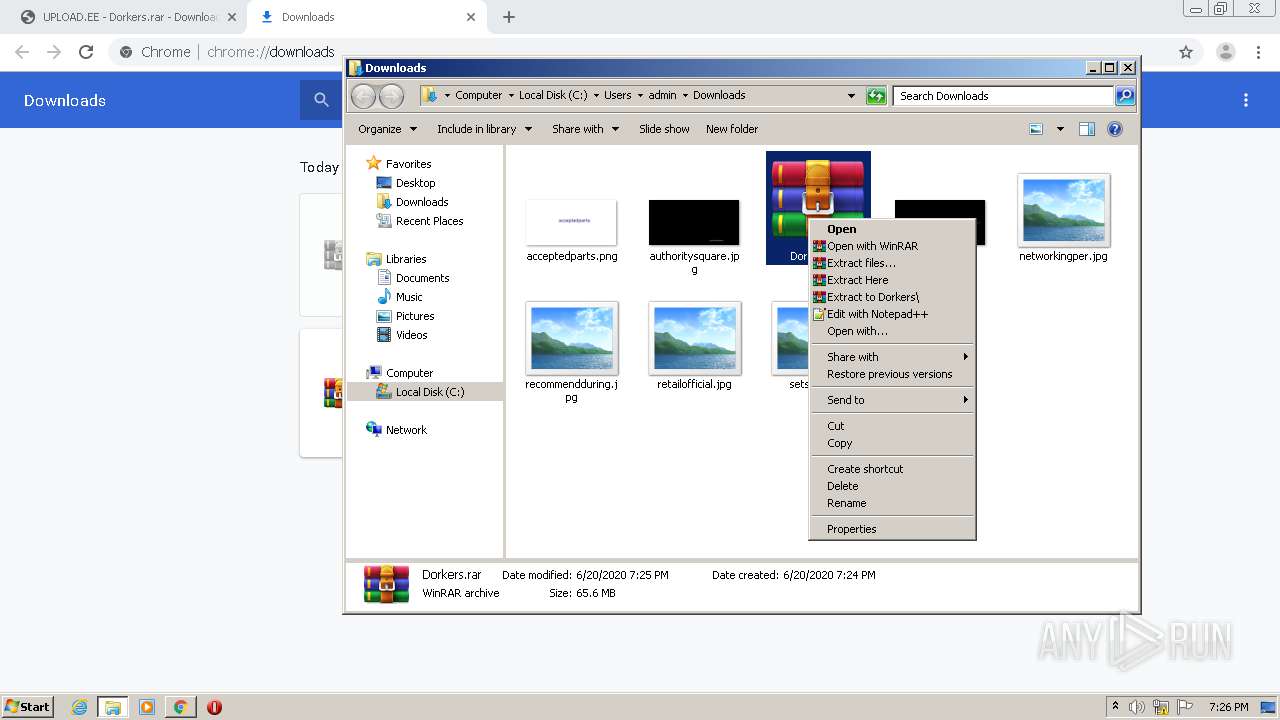
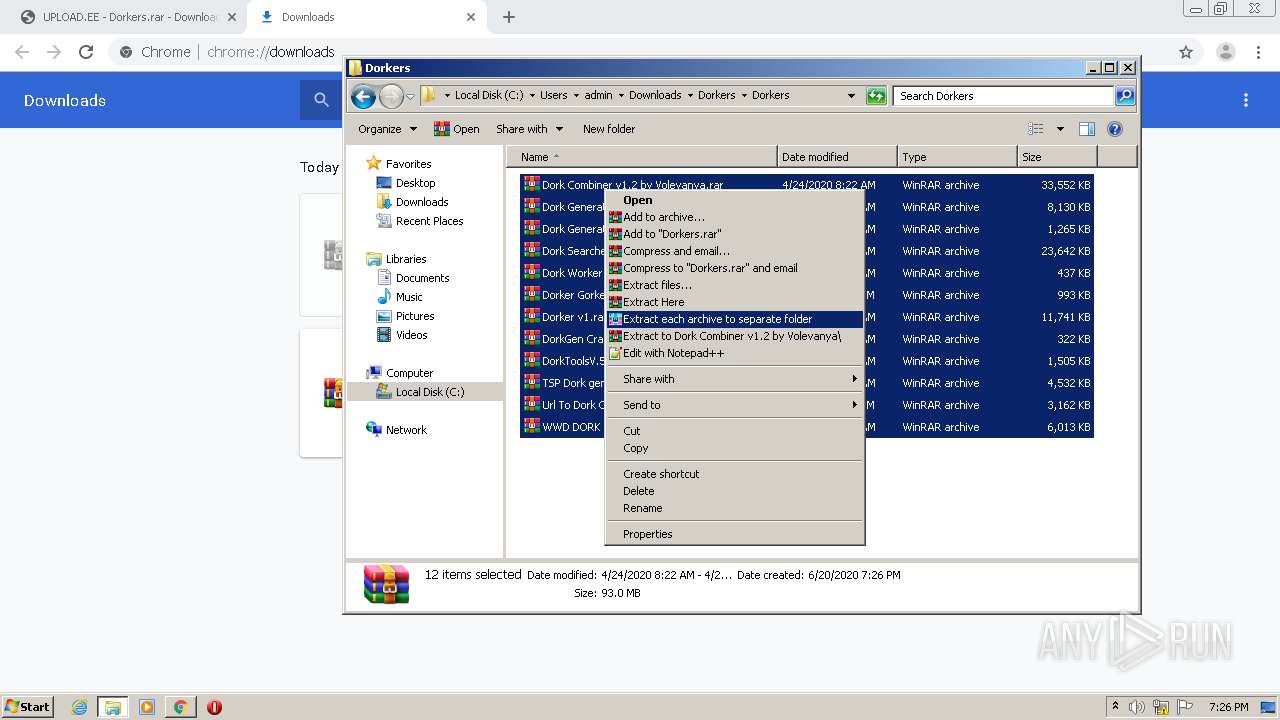
Writes to a desktop.ini file (may be used to cloak folders)
- WinRAR.exe (PID: 2236)
Creates files in the user directory
- explorer.exe (PID: 468)
- DorkCombine.exe (PID: 2480)
Creates files in the program directory
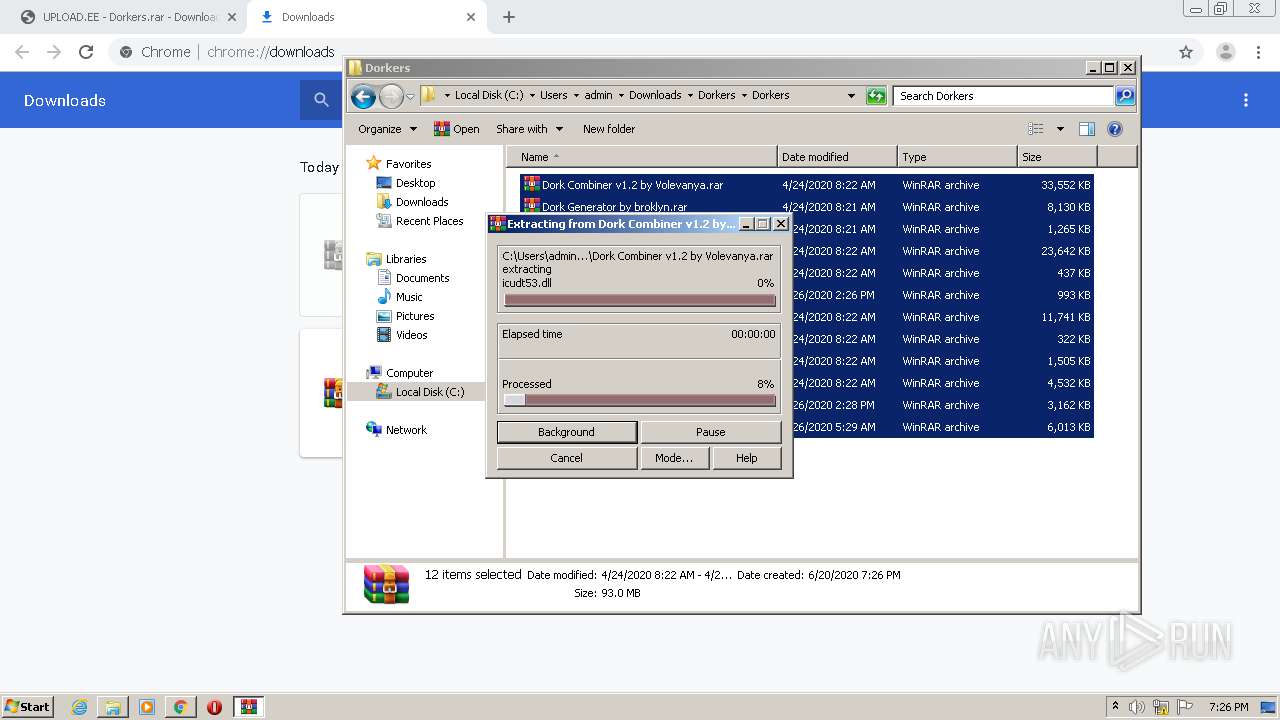
- WinRAR.exe (PID: 2236)
- DorkCombine.exe (PID: 2480)
- WerFault.exe (PID: 996)
- SQLi Dorks Generator .exe (PID: 2980)
Creates files in the Windows directory
- DorkCombine.exe (PID: 2480)
- SQLi Dorks Generator .exe (PID: 2980)
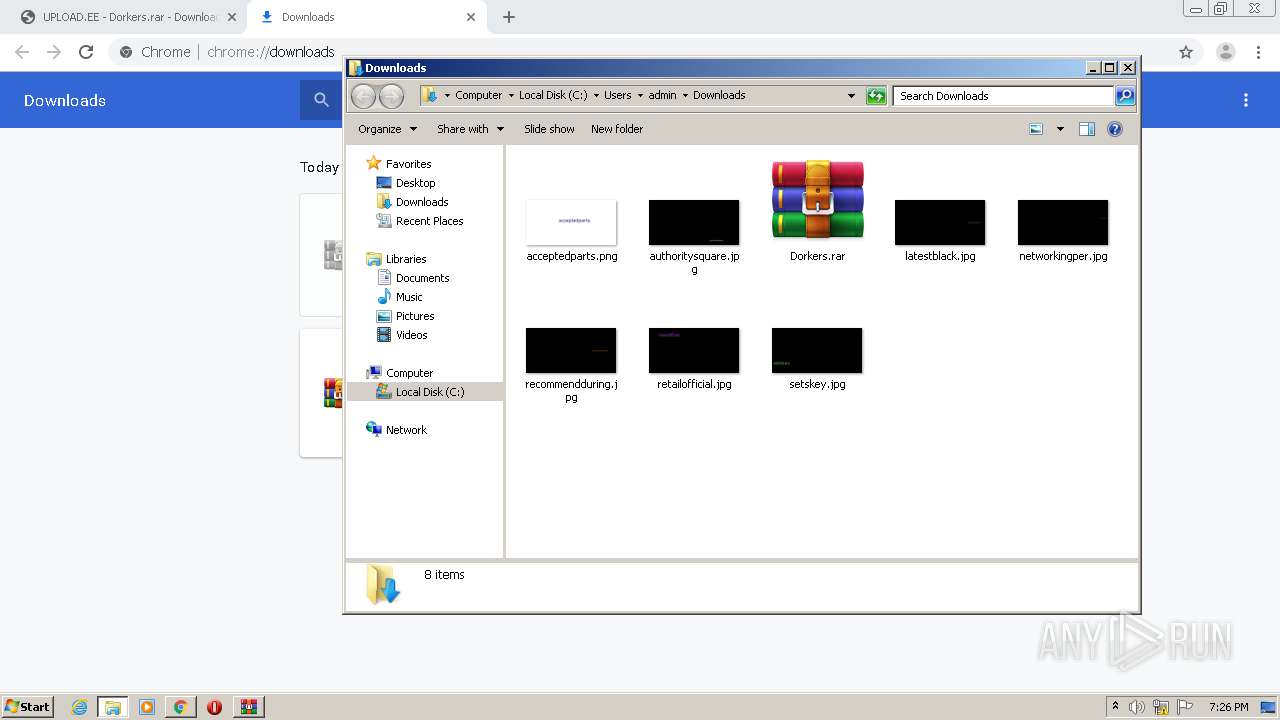
Executable content was dropped or overwritten
- DorkCombine.exe (PID: 2480)
- WinRAR.exe (PID: 2236)
- SQLi Dorks Generator .exe (PID: 2980)
INFO
Reads the hosts file
- chrome.exe (PID: 2712)
- chrome.exe (PID: 2180)
Reads Internet Cache Settings
- chrome.exe (PID: 2712)
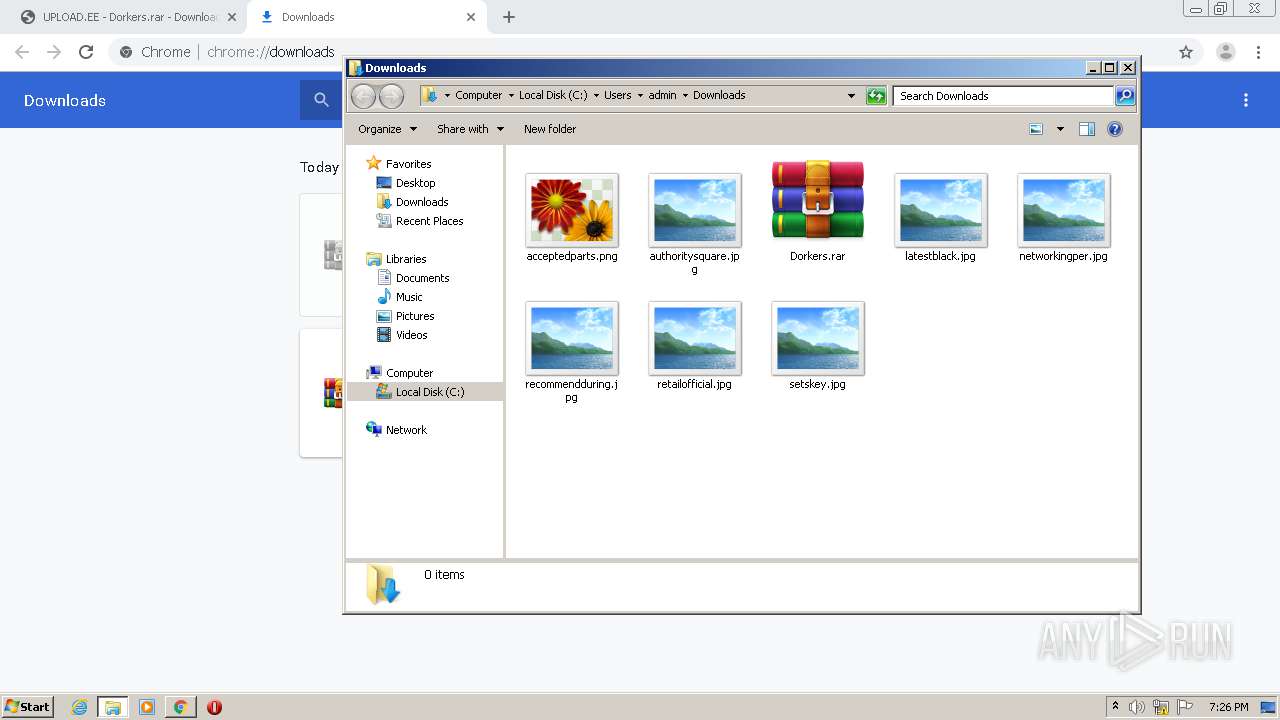
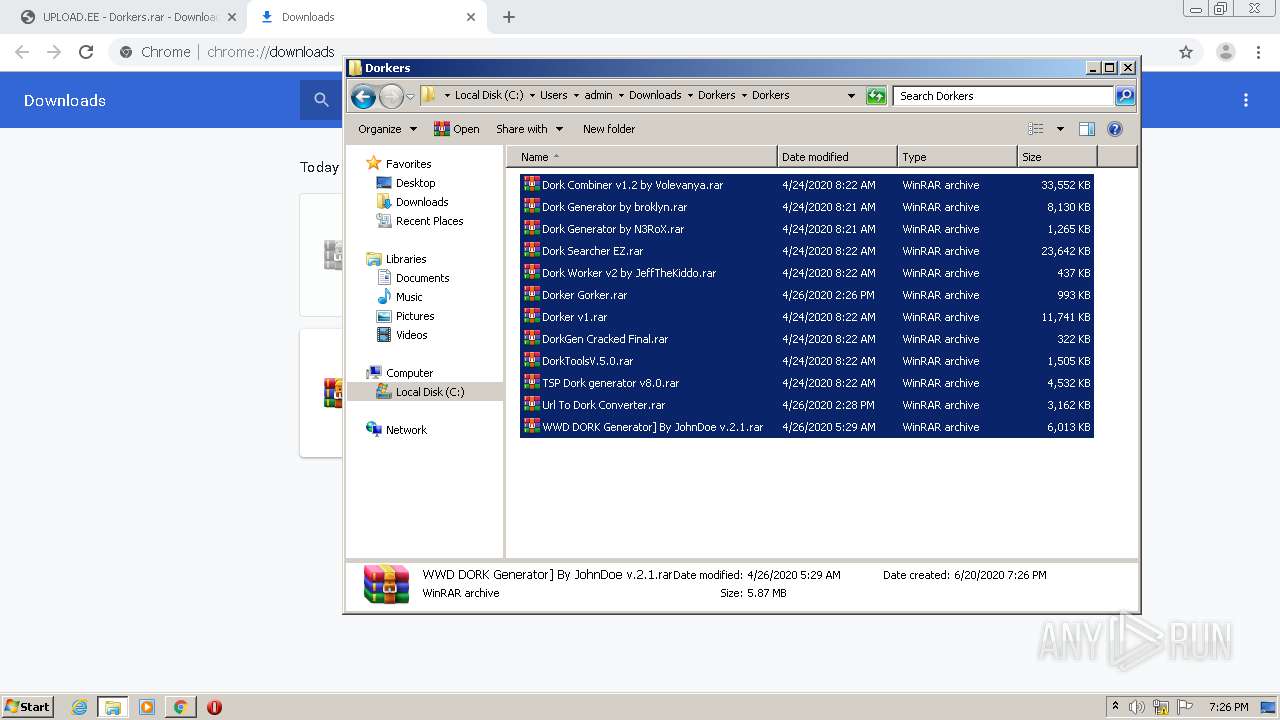
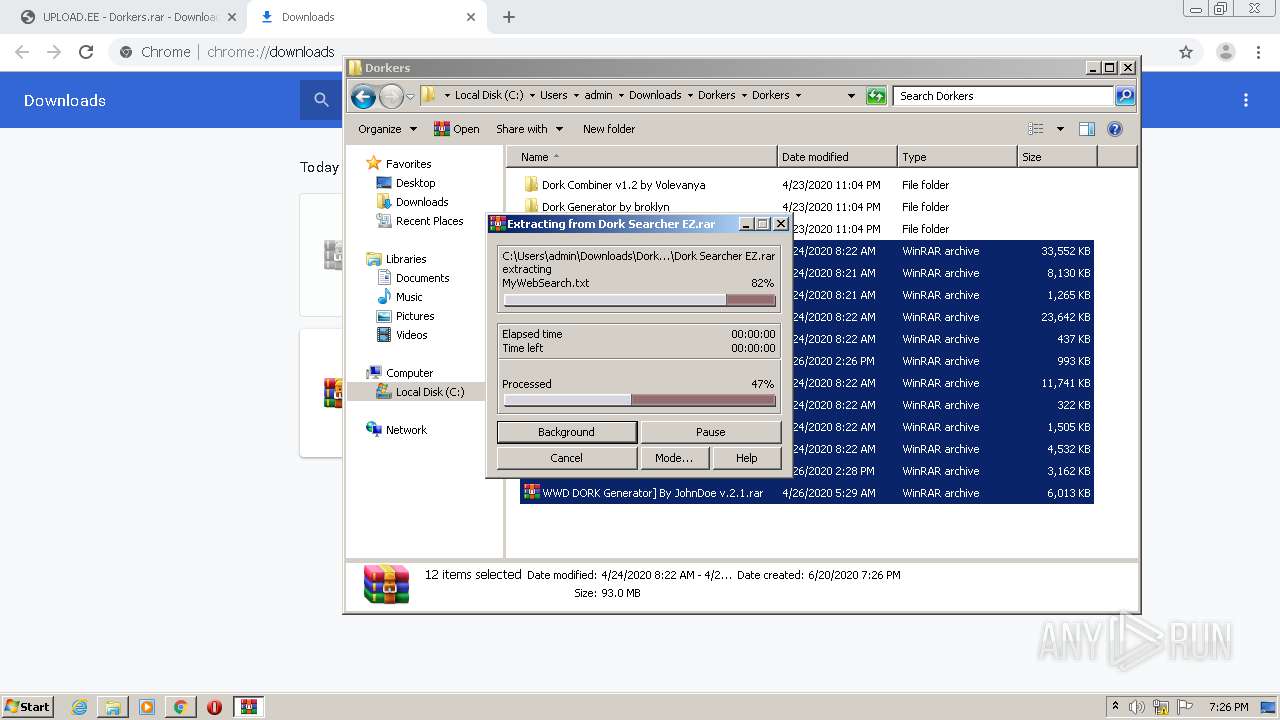
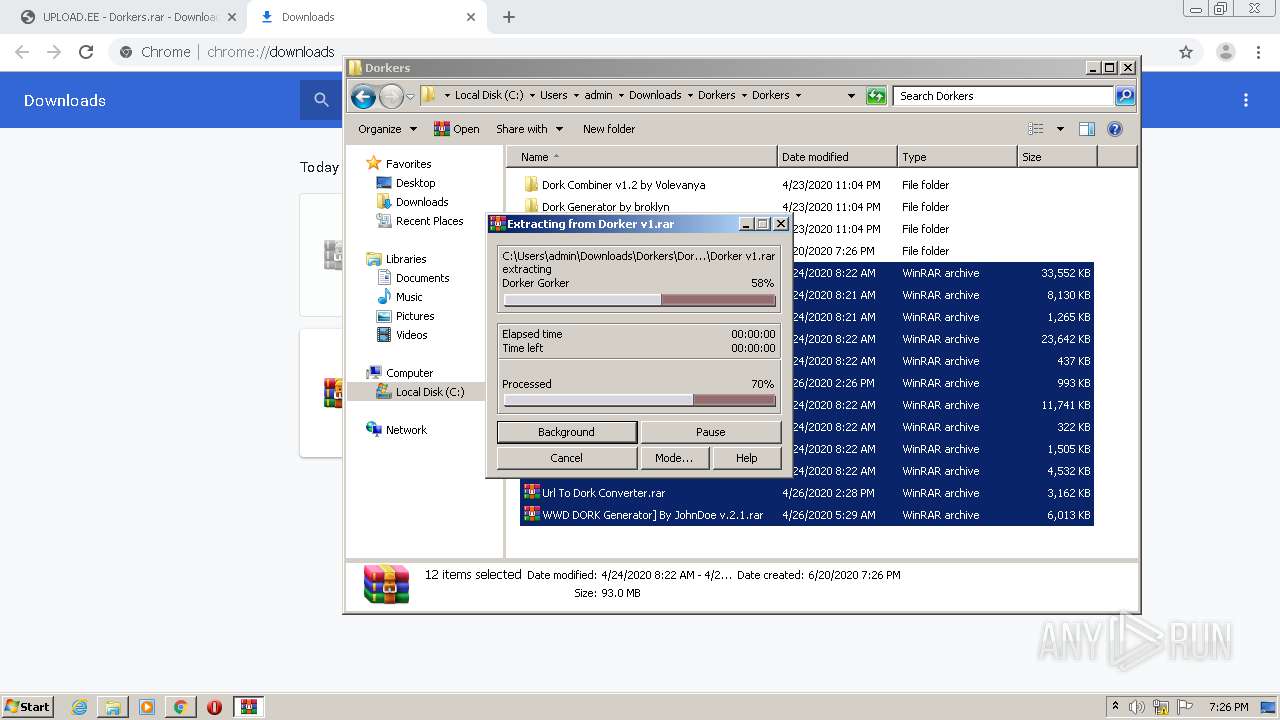
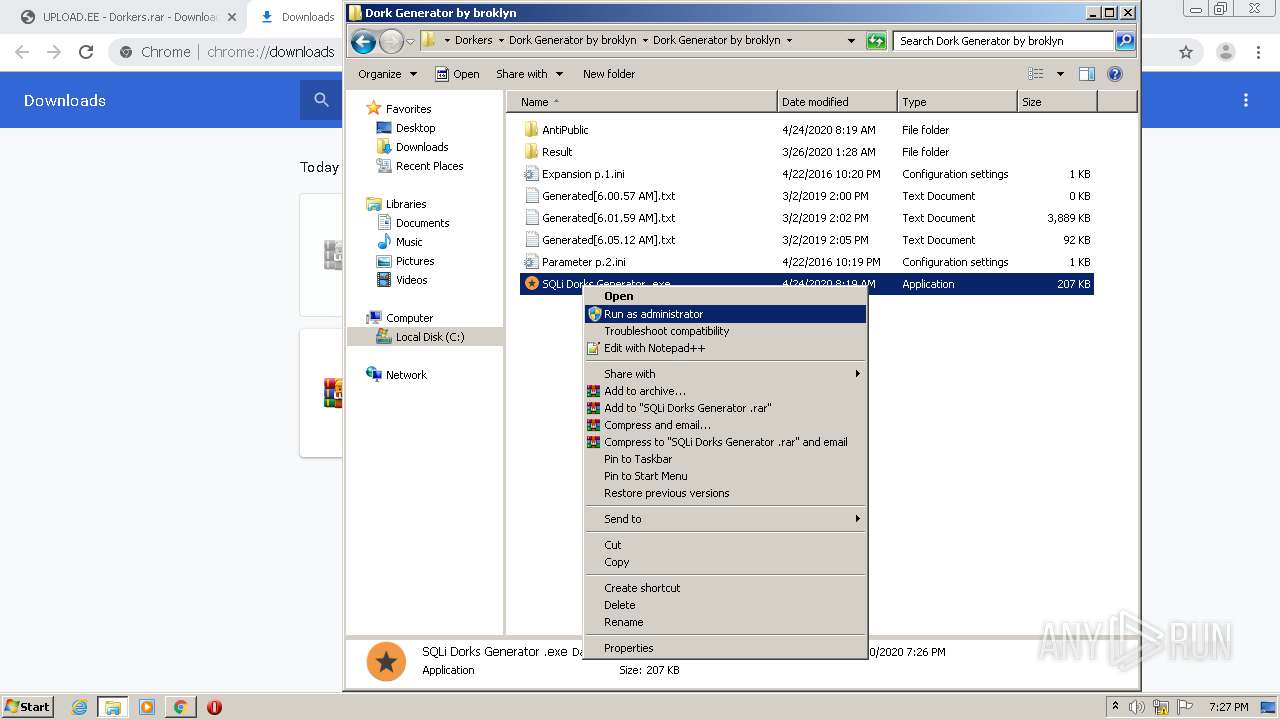
Manual execution by user
- WinRAR.exe (PID: 2236)
- WinRAR.exe (PID: 3520)
- DorkCombine.exe (PID: 2480)
Dropped object may contain TOR URL's
- WinRAR.exe (PID: 2236)
Application launched itself
- chrome.exe (PID: 2712)
Dropped object may contain Bitcoin addresses
- DorkCombine.exe (PID: 2480)
- SQLi Dorks Generator .exe (PID: 2980)
- WinRAR.exe (PID: 2236)
Reads settings of System Certificates
- chrome.exe (PID: 2180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
44
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 468 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 732 | "C:\Users\admin\Downloads\Dorkers\Dorkers\Dork Generator by broklyn\Dork Generator by broklyn\AntiPublic\Gen.exe" {Arguments If Needed} | C:\Users\admin\Downloads\Dorkers\Dorkers\Dork Generator by broklyn\Dork Generator by broklyn\AntiPublic\Gen.exe | — | SQLi Dorks Generator .exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 888 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | C:\Windows\system32\WerFault.exe -u -p 3420 -s 308 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1204 | "C:\Windows\Program Files (x86)\Microsoft Host Interface\platforms\Microsoft Windows Protocol Services Host.exe" {Arguments If Needed} | C:\Windows\Program Files (x86)\Microsoft Host Interface\platforms\Microsoft Windows Protocol Services Host.exe | — | DorkCombine.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Microsoft Windows Protocol Services Host Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,18230838092578954140,5910912474015065565,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10741017154718100374 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,18230838092578954140,5910912474015065565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5546559034233752349 --mojo-platform-channel-handle=1584 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver "-anf=C:\Users\admin\AppData\Local\Temp\Rar$LS468.42661" -scul -- "C:\Users\admin\Downloads\Dorkers\Dorkers\WWD DORK Generator] By JohnDoe v.2.1.rar" C:\Users\admin\Downloads\Dorkers\Dorkers\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,18230838092578954140,5910912474015065565,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7466084264750771418 --mojo-platform-channel-handle=4008 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,18230838092578954140,5910912474015065565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4975570908355702506 --mojo-platform-channel-handle=3976 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
6 279
Read events
5 634
Write events
640
Delete events
5
Modification events
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2712-13237151069599000 |
Value: 259 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
137
Suspicious files
43
Text files
547
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EEE545E-A98.pma | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e0dd0775-3605-4c69-8c3b-ff78fcd1ceae.tmp | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13eab1.TMP | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF13eac1.TMP | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF13ed51.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
40
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2180 | chrome.exe | GET | 200 | 74.125.173.169:80 | http://r4---sn-1gieen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.212.170.83&mm=28&mn=sn-1gieen7e&ms=nvh&mt=1592677451&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
2180 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
2180 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
2180 | chrome.exe | GET | 200 | 74.125.173.166:80 | http://r1---sn-1gieen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.212.170.83&mm=28&mn=sn-1gieen7e&ms=nvh&mt=1592677390&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2180 | chrome.exe | 35.190.74.92:443 | www.tradeadexchange.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
2180 | chrome.exe | 23.210.250.213:443 | z.moatads.com | Akamai International B.V. | NL | whitelisted |
2180 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 35.201.74.235:443 | theonecdn.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 35.190.77.201:443 | commercialvalue.org | Google Inc. | US | unknown |
2180 | chrome.exe | 37.187.167.53:443 | www.upload.ee | OVH SAS | FR | suspicious |
2180 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 35.227.202.173:443 | www.geniusdexchange.com | — | US | unknown |
2180 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.upload.ee |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.geniusdexchange.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.tradeadexchange.com |
| whitelisted |
z.moatads.com |
| whitelisted |
www.google.com |
| malicious |
pagead2.googlesyndication.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
Threats
Process | Message |
|---|---|
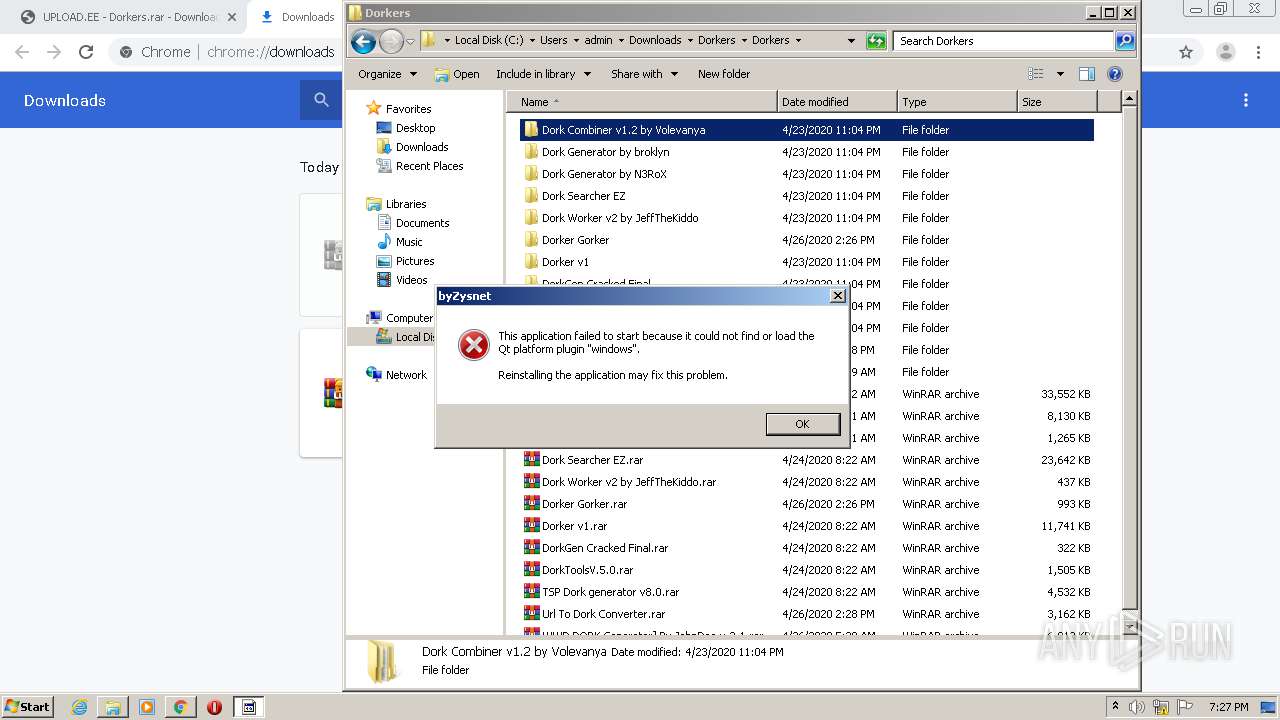
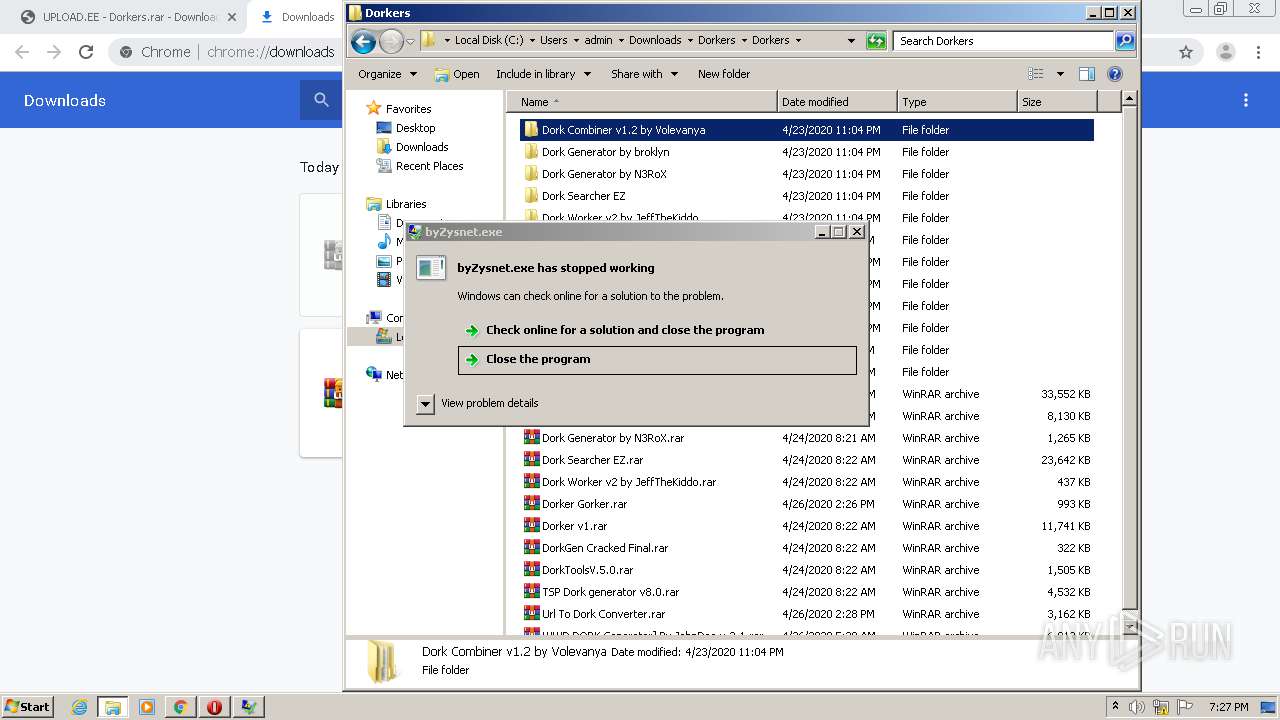
byZysnet.exe | This application failed to start because it could not find or load the Qt platform plugin "windows".
Reinstalling the application may fix this problem.
|
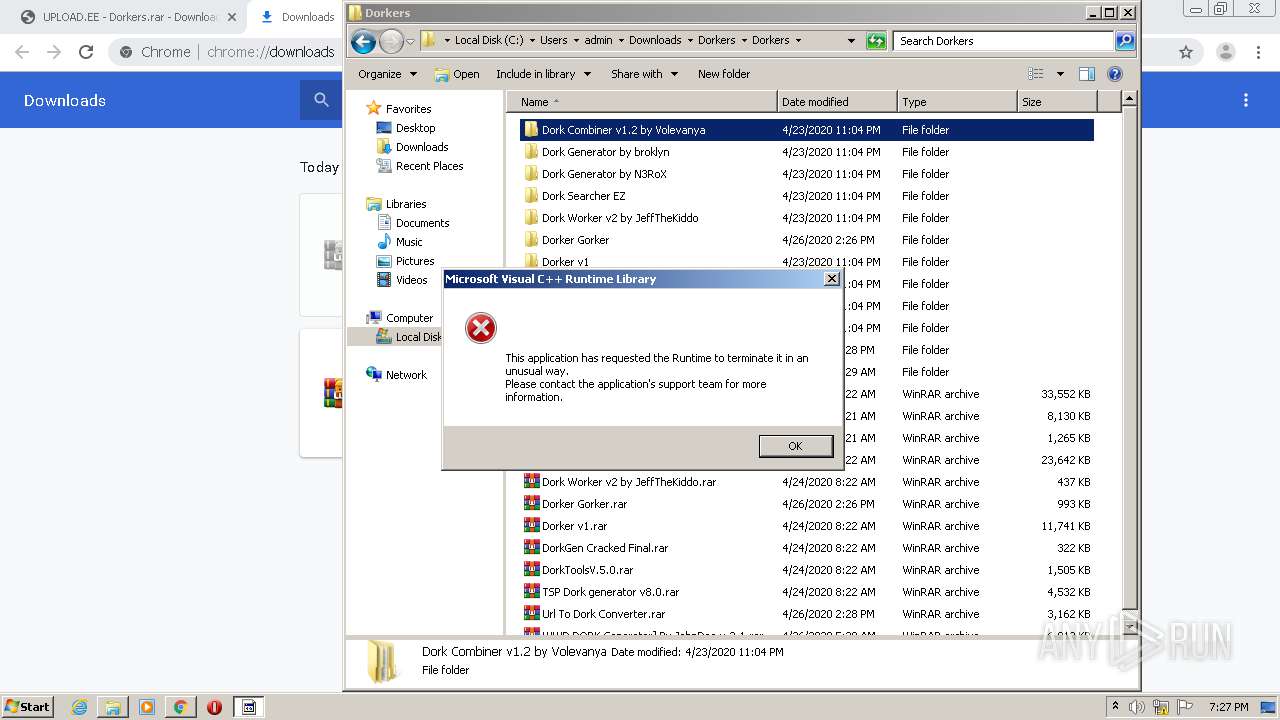
byZysnet.exe | Invalid parameter passed to C runtime function.
|
byZysnet.exe | Invalid parameter passed to C runtime function.
|