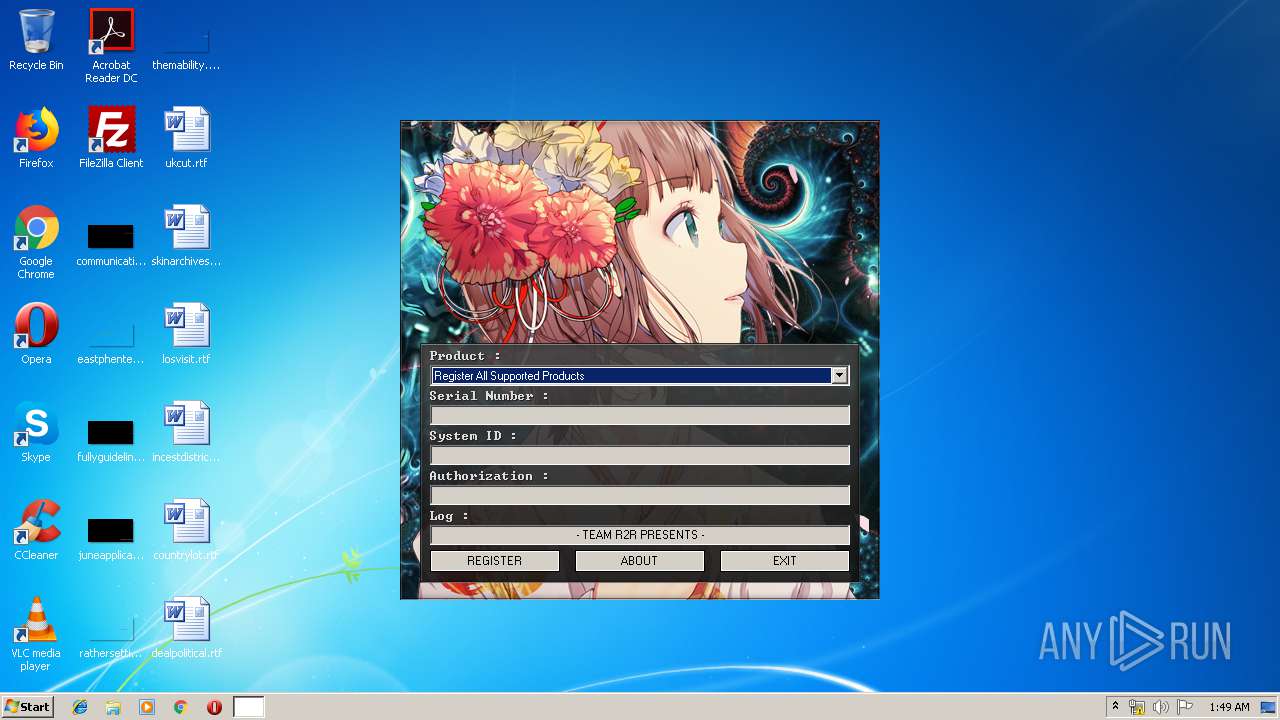
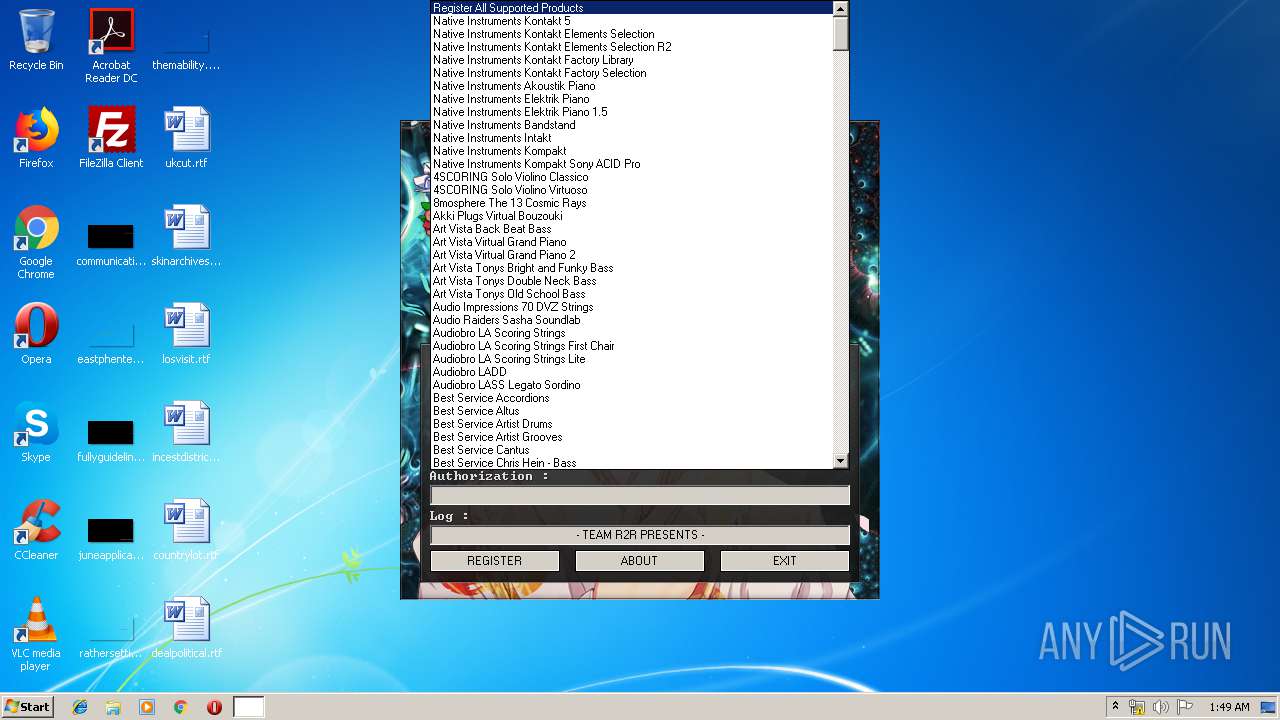
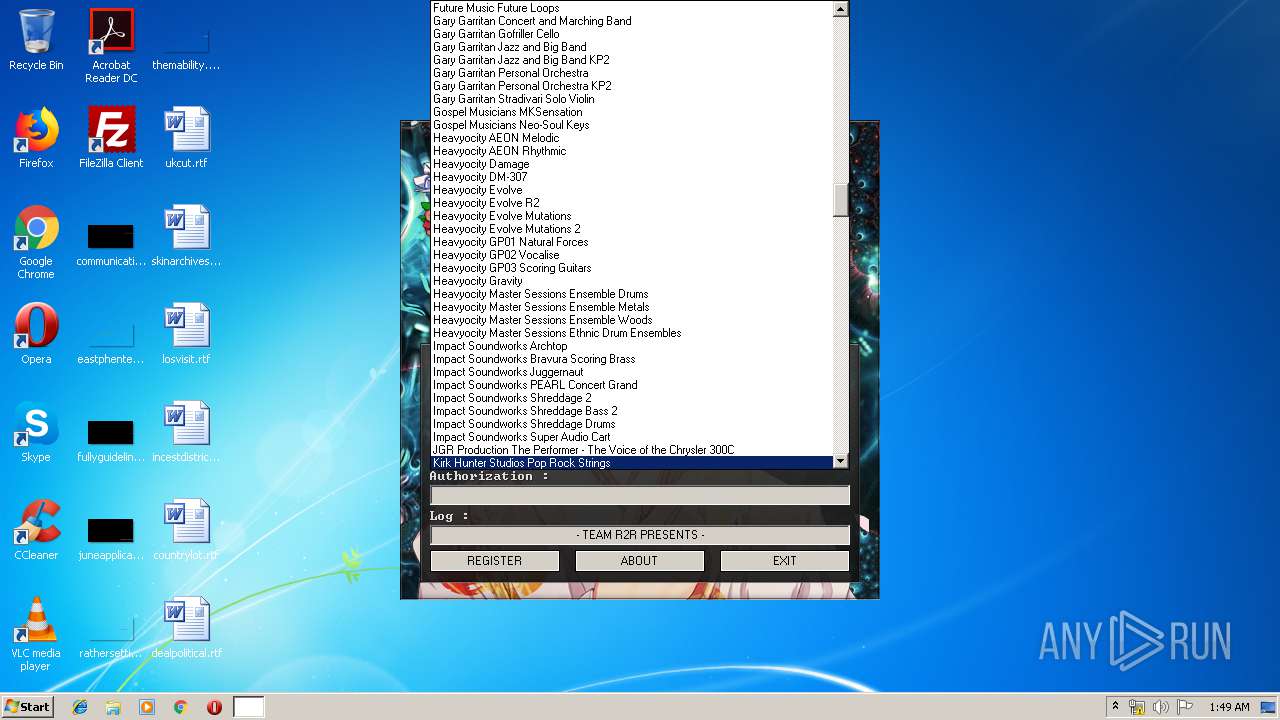
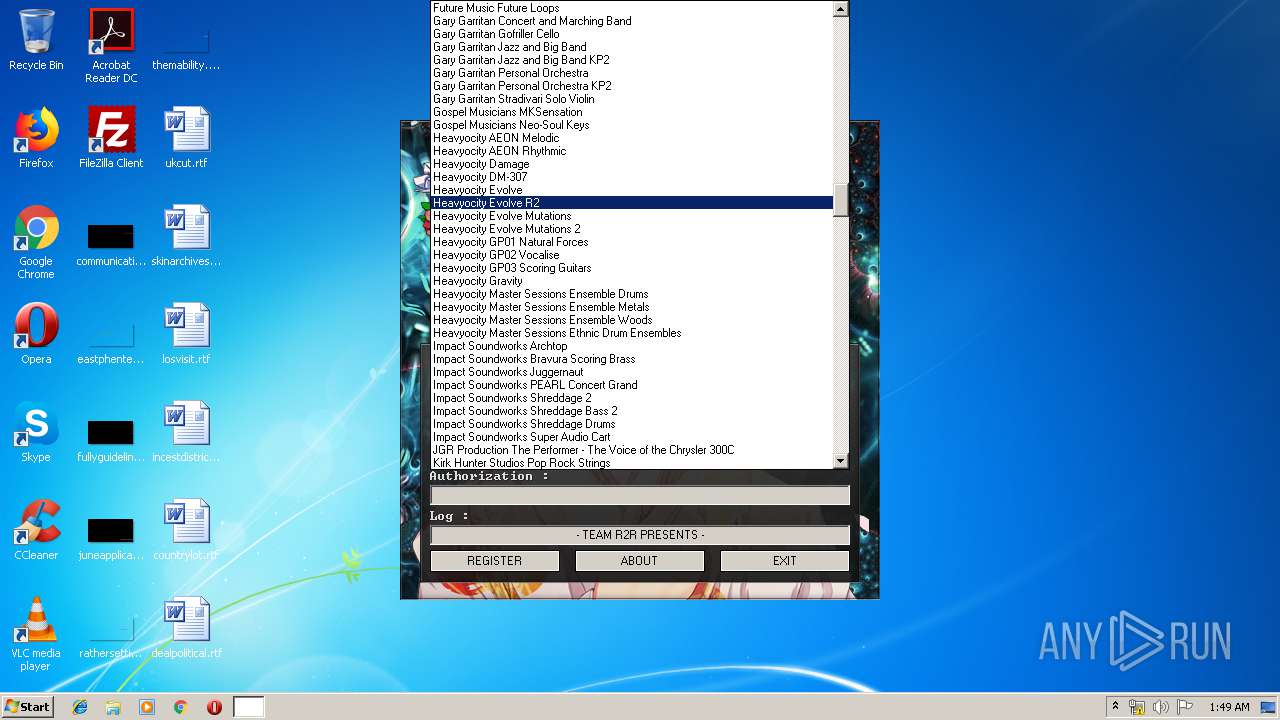
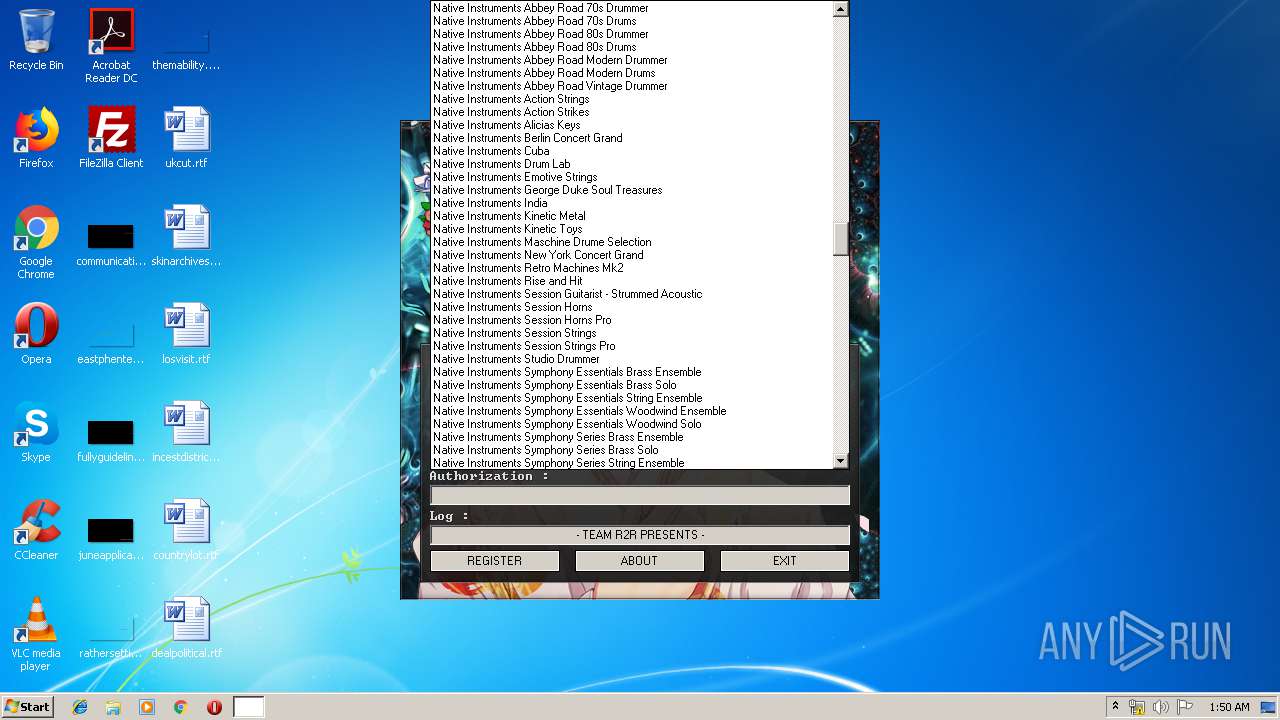
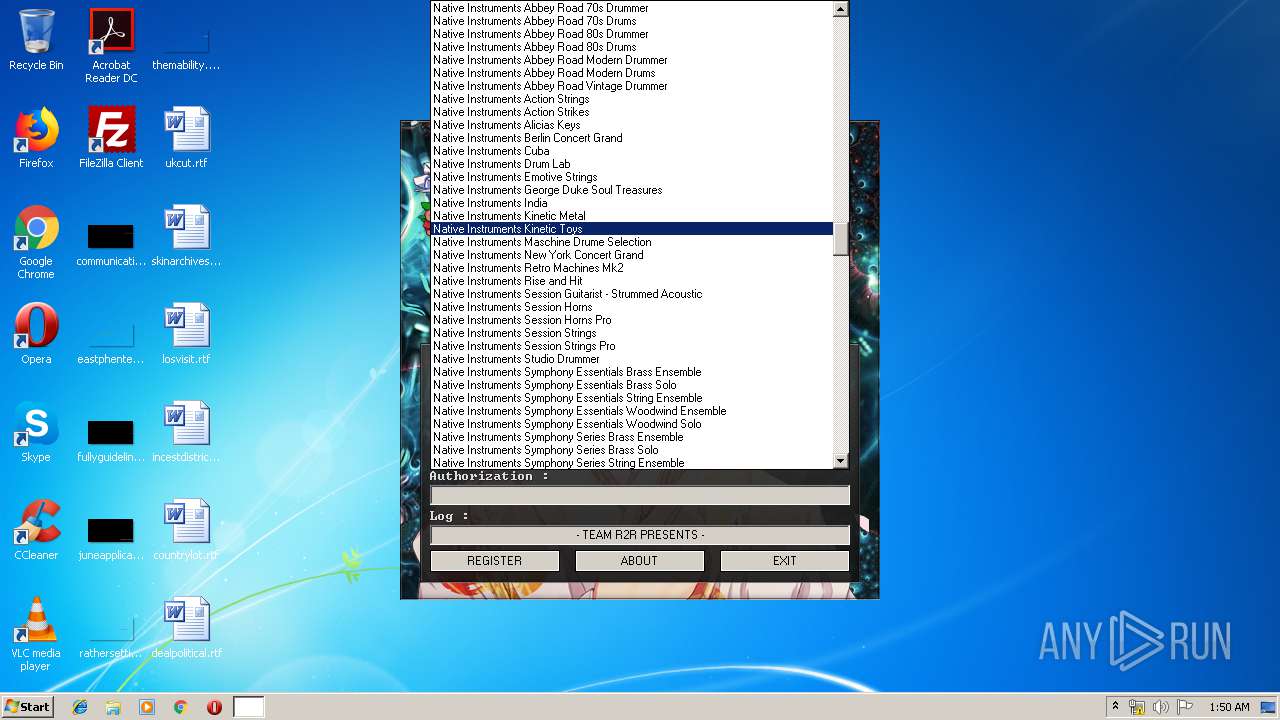
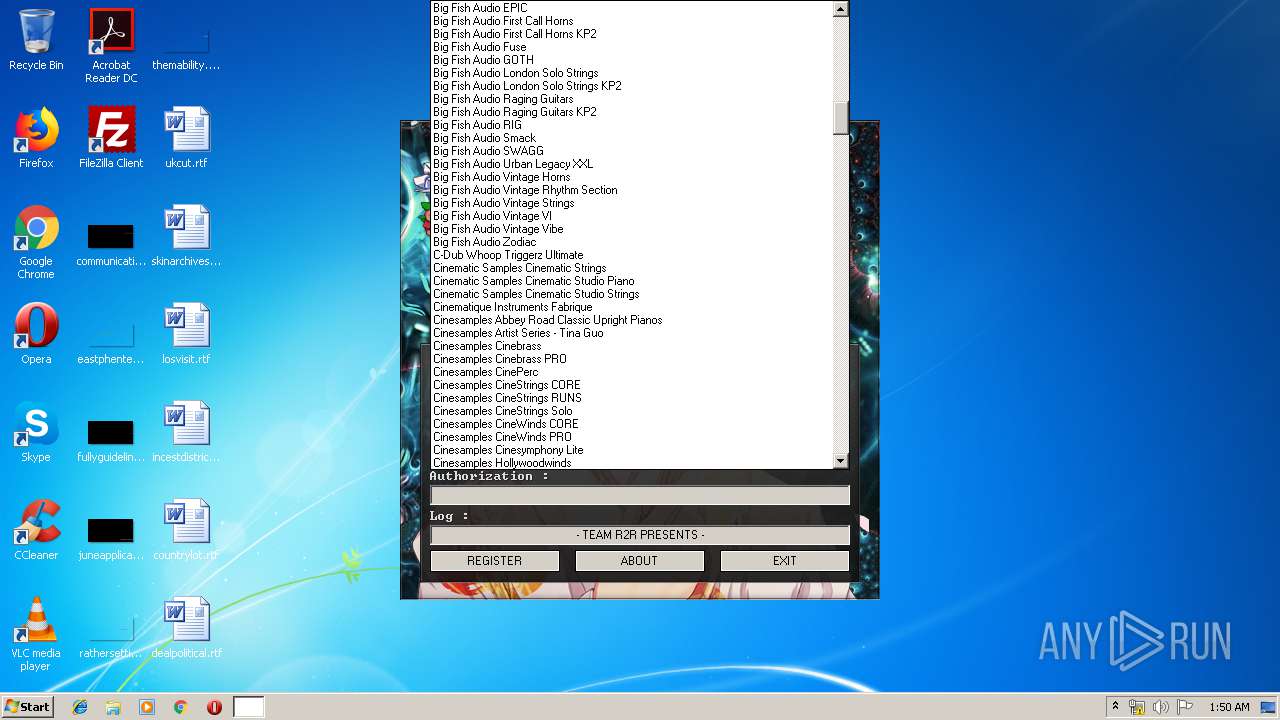
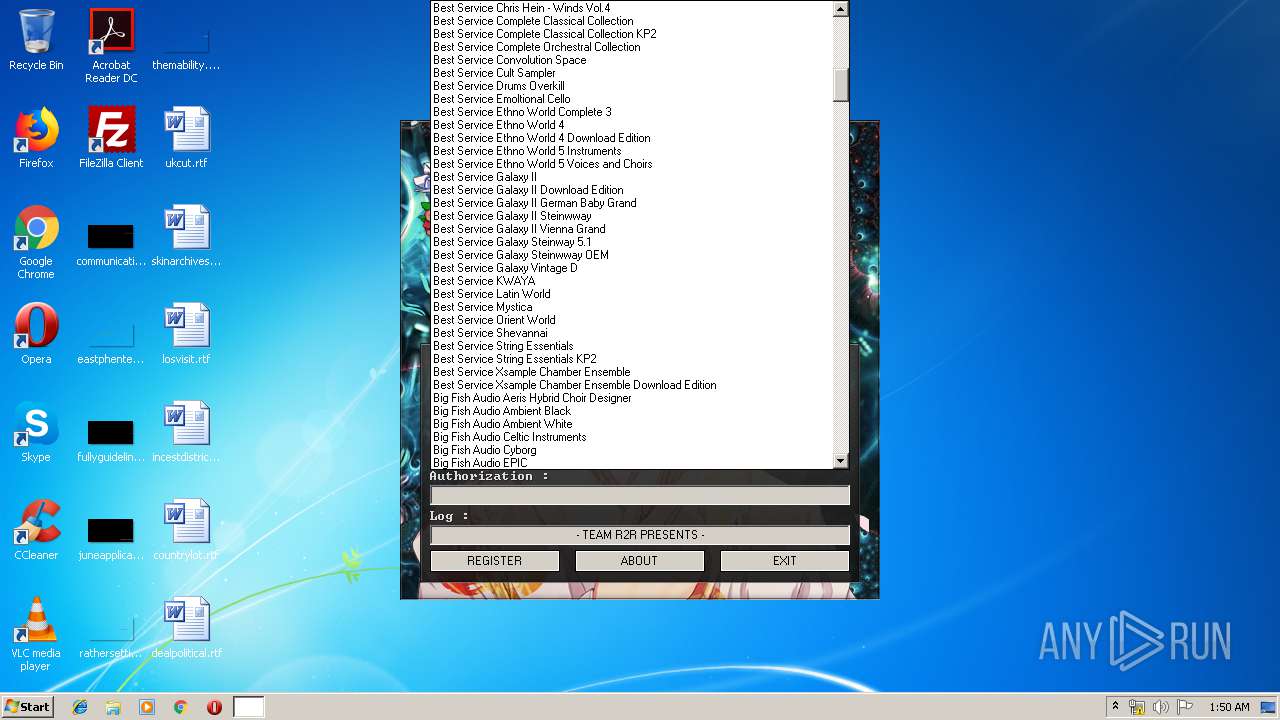
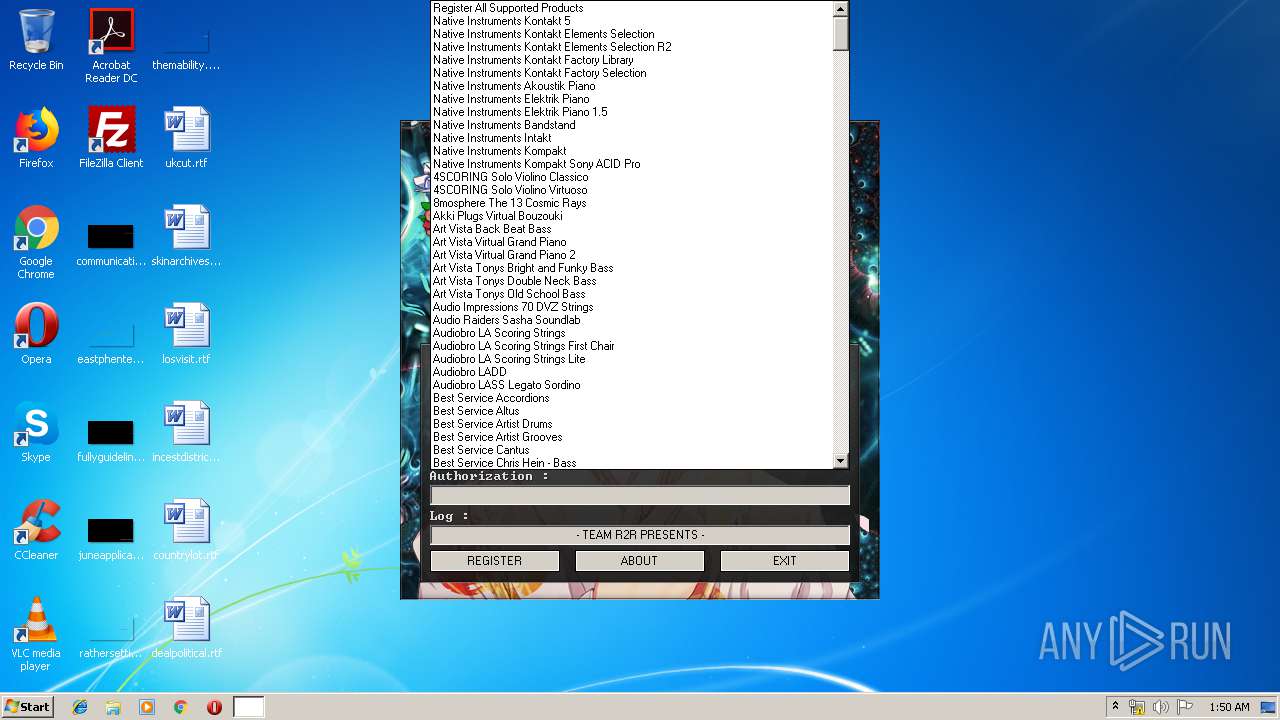
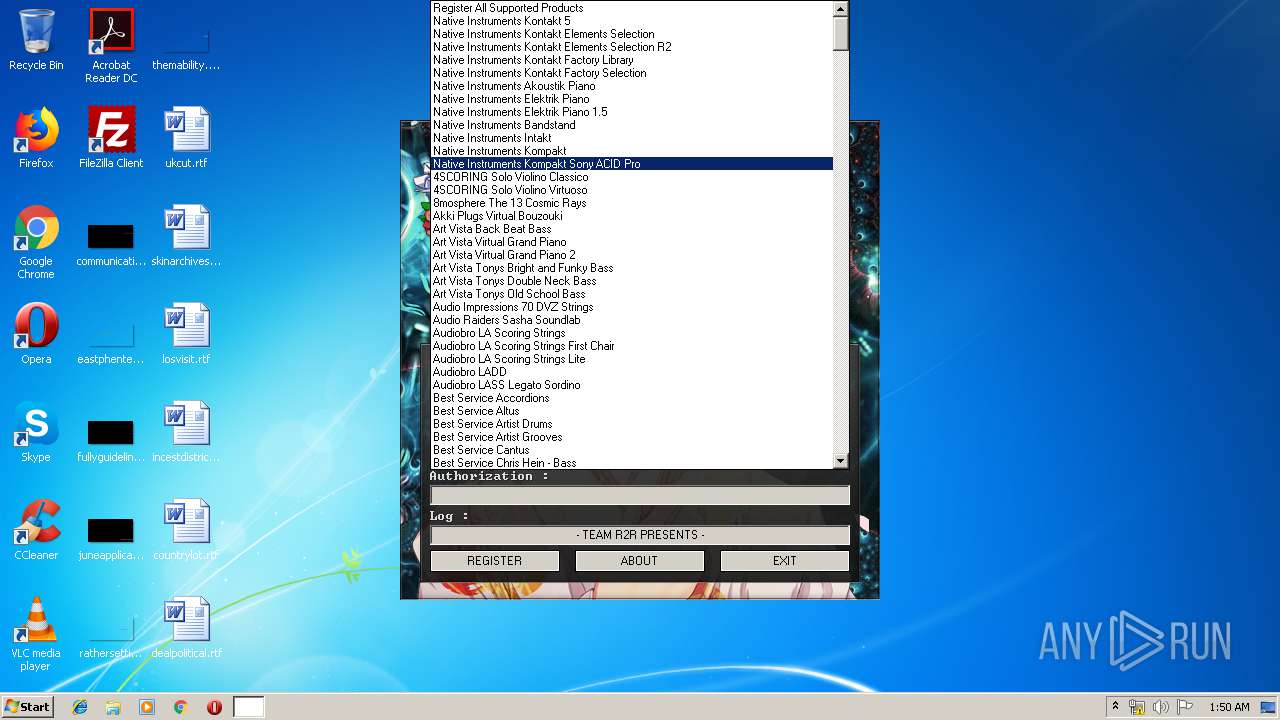
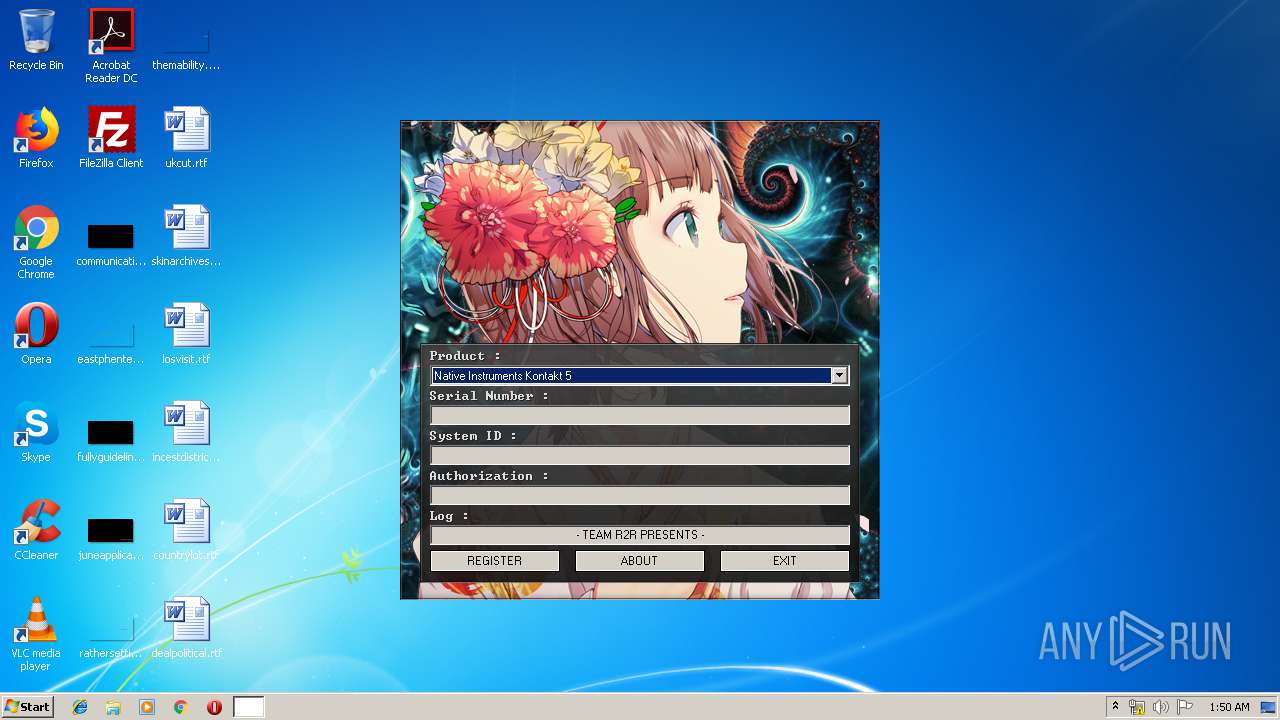
| File name: | Kontakt_Keygen.exe |
| Full analysis: | https://app.any.run/tasks/34e7d480-1733-4e13-974e-76a5fdaf57fe |
| Verdict: | No threats detected |
| Analysis date: | July 09, 2019, 00:49:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 6937503CAF7541886E8814CA4E48DF4B |
| SHA1: | CB372FAB3D49317234EE387D25A17EF625978381 |
| SHA256: | C98A66006EAB6A9A12A5F5AF74D8176AD2074D1F6A1EC6F561ACC6EC6EC5AFB0 |
| SSDEEP: | 24576:UcLjnDzo+Xus+mI26WXo9ssnGK//Umz4Vv8PN51+gZESsanJNNGozOn12XzpjzCV:UAb3o+uuoykUmz2UkgZdpnJN4otzCV |
MALICIOUS
Application was dropped or rewritten from another process
- keygen.exe (PID: 2948)
Loads dropped or rewritten executable
- keygen.exe (PID: 2948)
SUSPICIOUS
Executable content was dropped or overwritten
- Kontakt_Keygen.exe (PID: 3412)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 05:20:09+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x326c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:20:09 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2016 03:20:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C74 | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41039 |
.rdata | 0x00007000 | 0x00001196 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20374 |
.data | 0x00009000 | 0x0001B058 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.13053 |
.ndata | 0x00025000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002D000 | 0x00022898 | 0x00022A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.05877 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19285 | 727 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.92764 | 54264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.51849 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.75617 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 4.93004 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 5.08765 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.8213 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
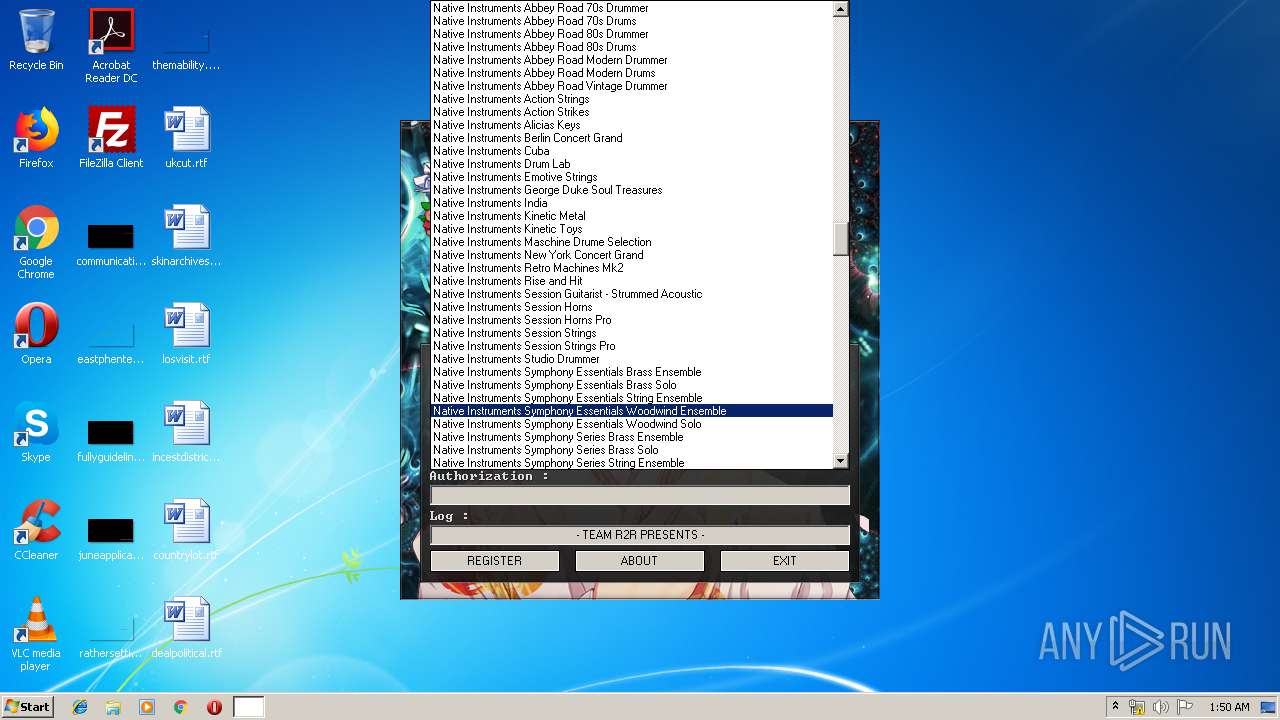
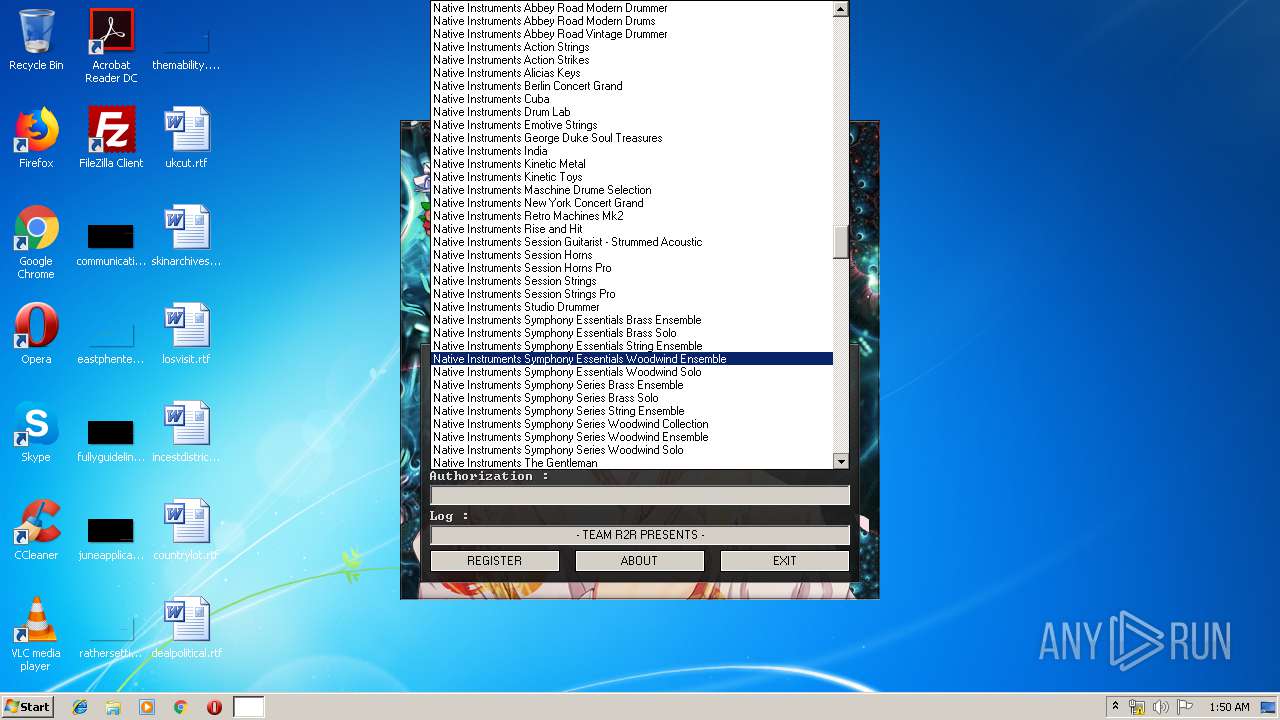
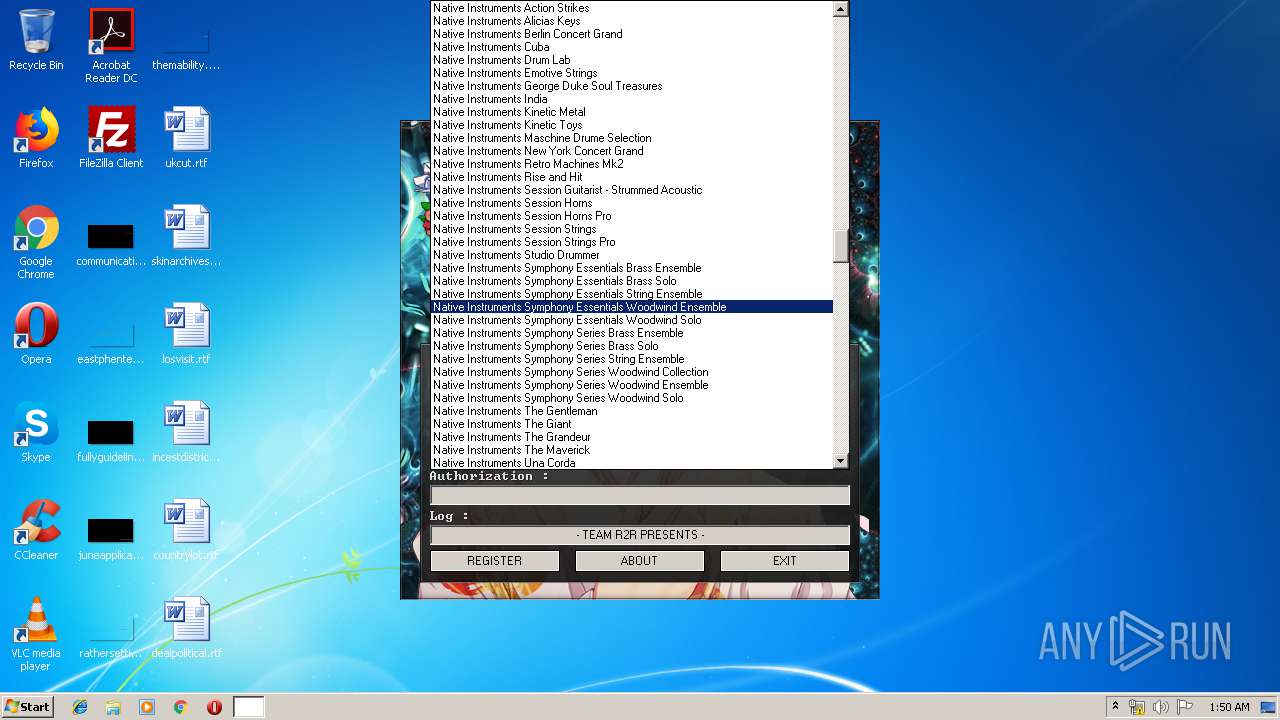
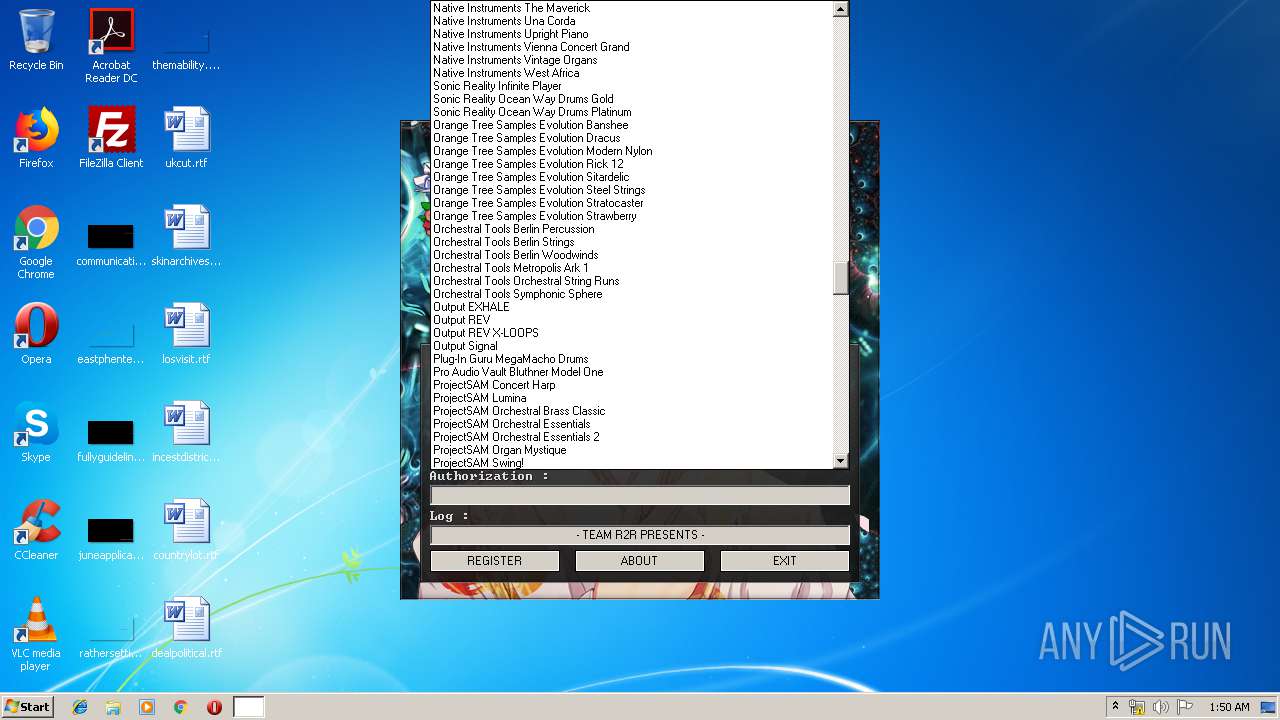
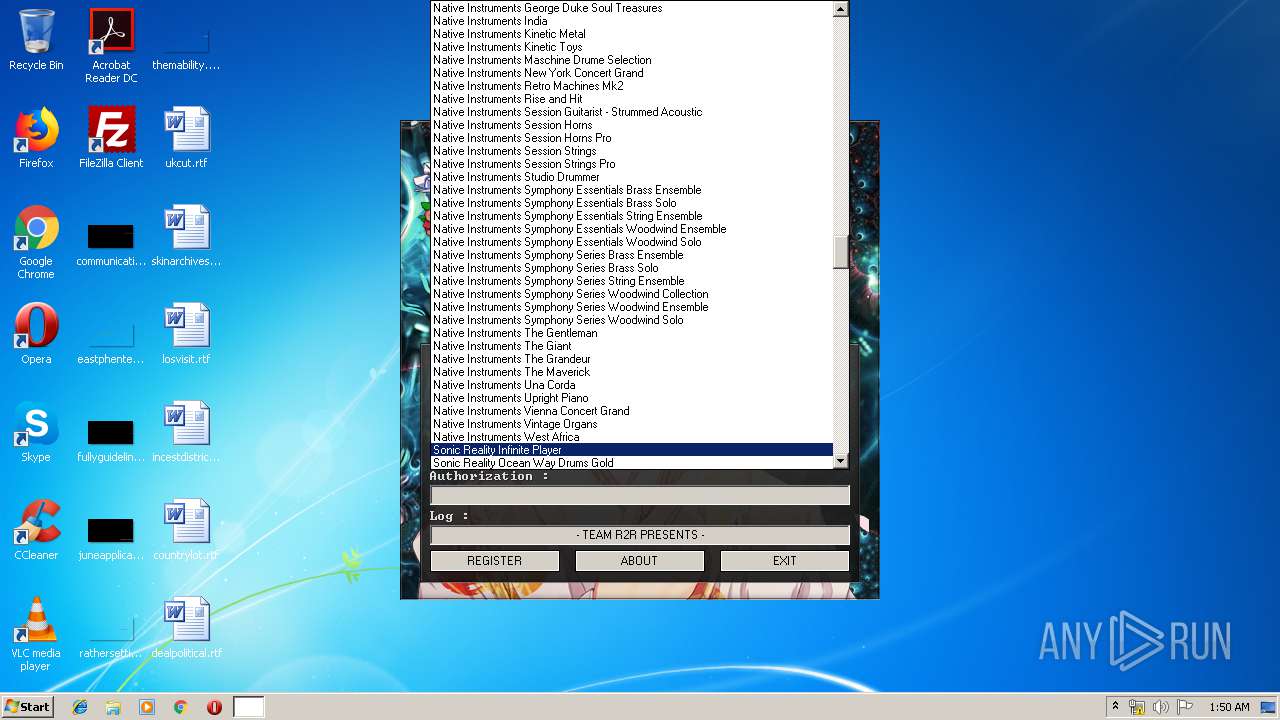
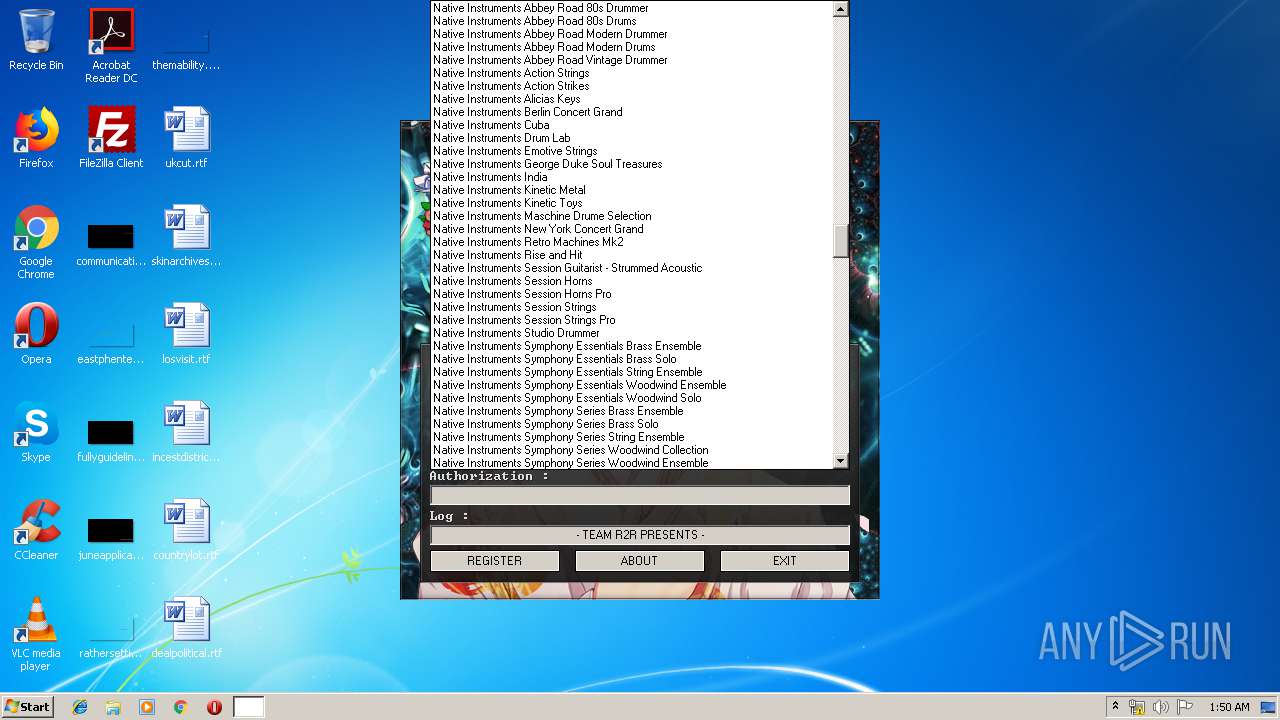
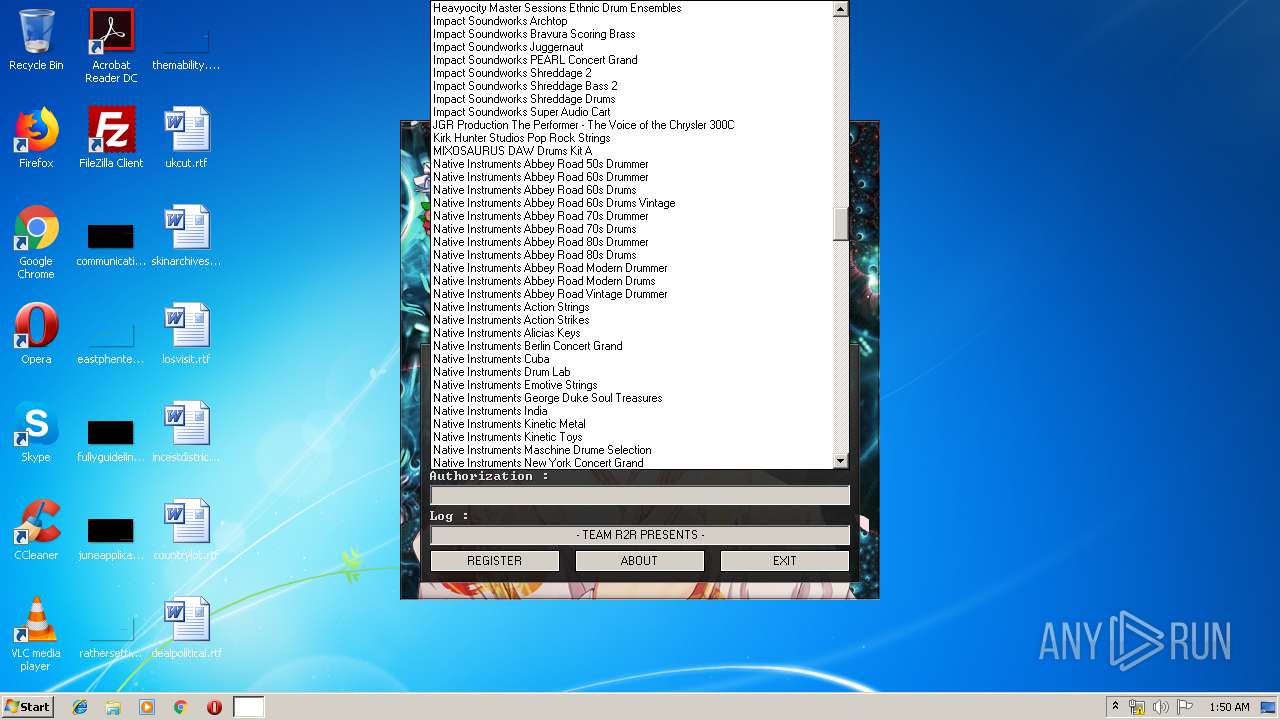
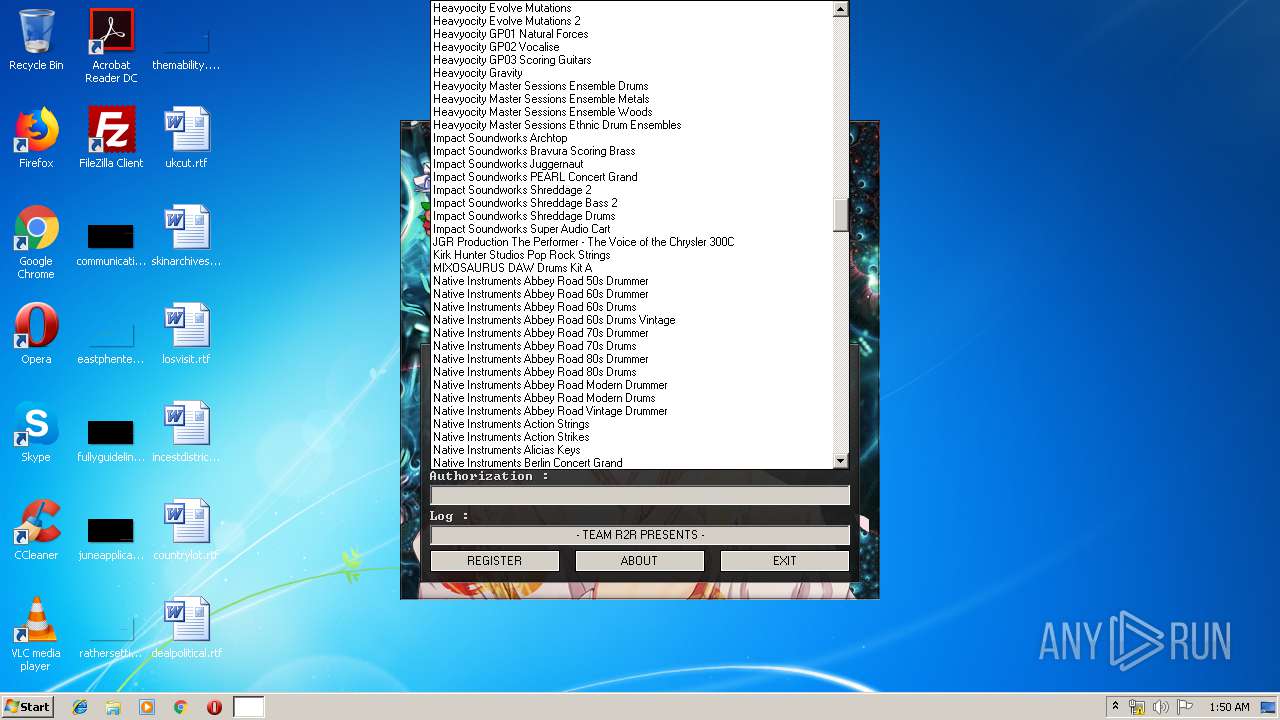
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2948 | C:\Users\admin\AppData\Local\Temp\keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | — | Kontakt_Keygen.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3328 | "C:\Users\admin\AppData\Local\Temp\Kontakt_Keygen.exe" | C:\Users\admin\AppData\Local\Temp\Kontakt_Keygen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3412 | "C:\Users\admin\AppData\Local\Temp\Kontakt_Keygen.exe" | C:\Users\admin\AppData\Local\Temp\Kontakt_Keygen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
351
Read events
348
Write events
3
Delete events
0
Modification events
| (PID) Process: | (2948) keygen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Native Instruments\Kontakt 5 |
| Operation: | write | Name: | SNO |
Value: 32230-79814-11078-99010-19953 | |||
| (PID) Process: | (2948) keygen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Native Instruments\Kontakt 5 |
| Operation: | write | Name: | SYSTEMID |
Value: 62M50HN1WFF4KNK5F1E4WHAM0R0RD59L | |||
| (PID) Process: | (2948) keygen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Native Instruments\Kontakt 5 |
| Operation: | write | Name: | KEY |
Value: DMA1WN5AMQ23N1MAY43B9JP2N9R525S00B6NWMWMQKTQP | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3412 | Kontakt_Keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | executable | |
MD5:— | SHA256:— | |||
| 3412 | Kontakt_Keygen.exe | C:\Users\admin\AppData\Local\Temp\R2RNIKG.dll | executable | |
MD5:— | SHA256:— | |||
| 3412 | Kontakt_Keygen.exe | C:\Users\admin\AppData\Local\Temp\BASSMOD.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 3412 | Kontakt_Keygen.exe | C:\Users\admin\AppData\Local\Temp\bgm.xm | xm | |
MD5:DB5F21FB067C54B97F6FDE240DCC24E3 | SHA256:C1F6465962F4BBA16B30F8A976D1B4F9DAC618C4E977801FE0B3A077AFB16526 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report