| File name: | Geofiltering.exe |
| Full analysis: | https://app.any.run/tasks/dbc2e81a-d7da-4ee5-a628-a5d2d17a0c1a |
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2022, 16:39:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | A92EA185EDDCD153048454AF61CF285C |
| SHA1: | 410160B529B3FB3B457AE12E9073E235CC19E339 |
| SHA256: | C98A60E5D0390BA4AD784B76EC0CE3602272452FFB44CE73DBB849906F2CFF4D |
| SSDEEP: | 384:6ABp1ujCZv9zuB1TPBHzLeA0EX0jJQdIJMh7mmd:L1uGZvQHzLx0EX2QOMh7Hd |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- Geofiltering.exe (PID: 3416)
Reads the computer name
- Geofiltering.exe (PID: 3416)
Checks for external IP
- Geofiltering.exe (PID: 3416)
INFO
Reads settings of System Certificates
- Geofiltering.exe (PID: 3416)
Checks Windows Trust Settings
- Geofiltering.exe (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x1d05 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 7680 |
| CodeSize: | 6656 |
| LinkerVersion: | 14.29 |
| PEType: | PE32 |
| TimeStamp: | 2022:03:15 17:39:02+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 15-Mar-2022 16:39:02 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Mar-2022 16:39:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000018A2 | 0x00001A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.16423 |
.rdata | 0x00003000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75805 |
.data | 0x00005000 | 0x00000400 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.75857 |
.rsrc | 0x00006000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.6976 |
.reloc | 0x00007000 | 0x00000290 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.87103 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
MSVCP140.dll |
VCRUNTIME140.dll |
api-ms-win-crt-heap-l1-1-0.dll |
api-ms-win-crt-locale-l1-1-0.dll |
api-ms-win-crt-math-l1-1-0.dll |
api-ms-win-crt-runtime-l1-1-0.dll |
api-ms-win-crt-stdio-l1-1-0.dll |
urlmon.dll |
Total processes
36
Monitored processes
1
Malicious processes
0
Suspicious processes
0
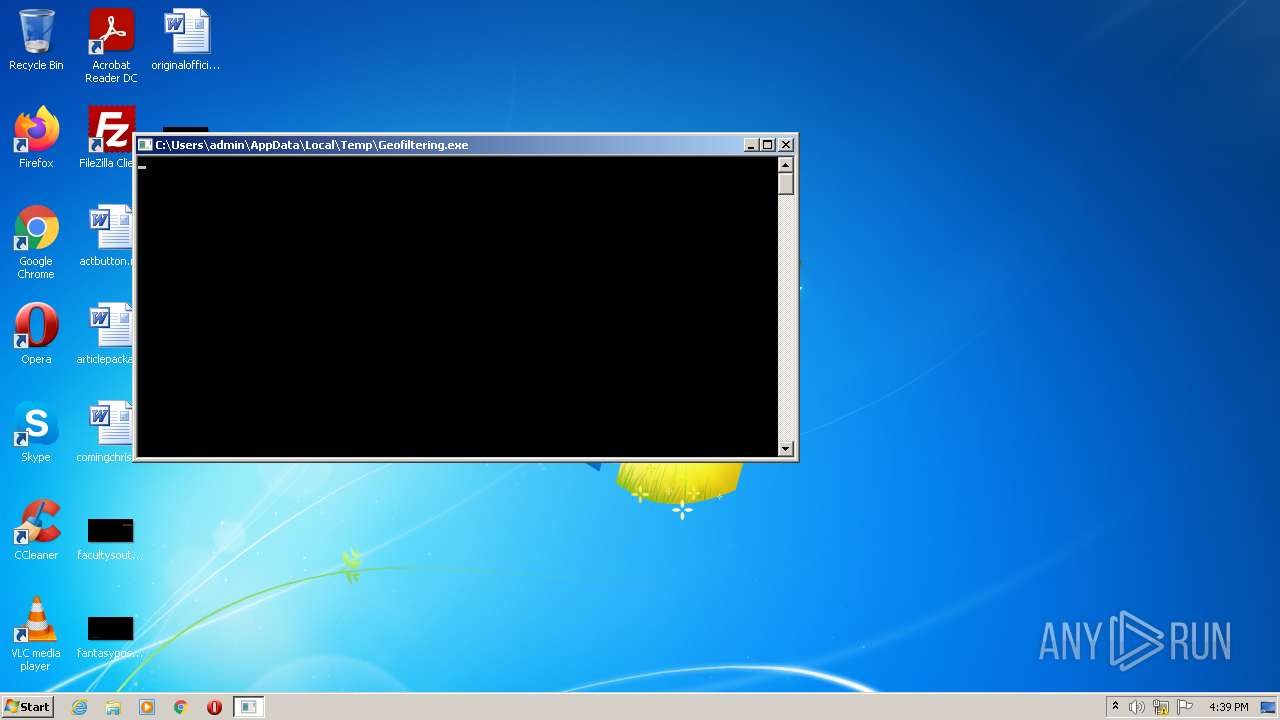
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3416 | "C:\Users\admin\AppData\Local\Temp\Geofiltering.exe" | C:\Users\admin\AppData\Local\Temp\Geofiltering.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 558
Read events
3 514
Write events
44
Delete events
0
Modification events
| (PID) Process: | (3416) Geofiltering.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3416) Geofiltering.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3416) Geofiltering.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3416) Geofiltering.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3416) Geofiltering.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3416) Geofiltering.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3416) Geofiltering.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3416) Geofiltering.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3416) Geofiltering.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3416) Geofiltering.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | Geofiltering.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | binary | |
MD5:6BAE72618F5BC454101AA8AD1EA5959E | SHA256:C5232FB61885F0B5AB184317795A7D1B5556A209046AA27E25A9F7E33ED332A5 | |||
| 3416 | Geofiltering.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5B0C23469FA29FAE1790BFE68671F4AD_AA05EE845923167FCC6028DA473A681E | der | |
MD5:7BE0555355E93D6DE4307F674F0635EB | SHA256:ACEDB3A43864292D39EDA89B23CE8F6C789FE18951EEB56248D4A22DE1CFED1B | |||
| 3416 | Geofiltering.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\ip[1].txt | text | |
MD5:F83F7420D03273E78E525A6EC1F41131 | SHA256:A8A3FBEE320C43939F25C6F3E9AC0808B7B903856CFF9C14490BC4CD81B608D3 | |||
| 3416 | Geofiltering.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | der | |
MD5:34615E035F22E0F62ABB877EF4E65B52 | SHA256:77DA562E421B1004406EBDA1A1E2576B3B04D6D6E62BBDFF40B8C67E0A3C6486 | |||
| 3416 | Geofiltering.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5B0C23469FA29FAE1790BFE68671F4AD_AA05EE845923167FCC6028DA473A681E | binary | |
MD5:62F87286E9C23EFD59D504F4ECED3A86 | SHA256:27D41D830A8CF6413864445345661228934D2BAA34403254EB93DAE449853F87 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3416 | Geofiltering.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | US | der | 724 b | whitelisted |
3416 | Geofiltering.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/s/gts1d4/onU6DY8-7YM/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEQC6RuMyEp3KUxIAAAAAAlG%2B | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3416 | Geofiltering.exe | 142.250.184.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3416 | Geofiltering.exe | 142.250.186.163:80 | crl.pki.goog | Google Inc. | US | whitelisted |
3416 | Geofiltering.exe | 34.117.59.81:443 | ifconfig.me | — | US | whitelisted |
3416 | Geofiltering.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ifconfig.me |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
crl.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3416 | Geofiltering.exe | Potentially Bad Traffic | ET POLICY External IP Lookup SSL/TLS Certificate (ifconfig .me) |