| File name: | TomMarslandResume.docm |
| Full analysis: | https://app.any.run/tasks/ea82e2f6-46b7-4392-9272-aaf5bc868f4b |
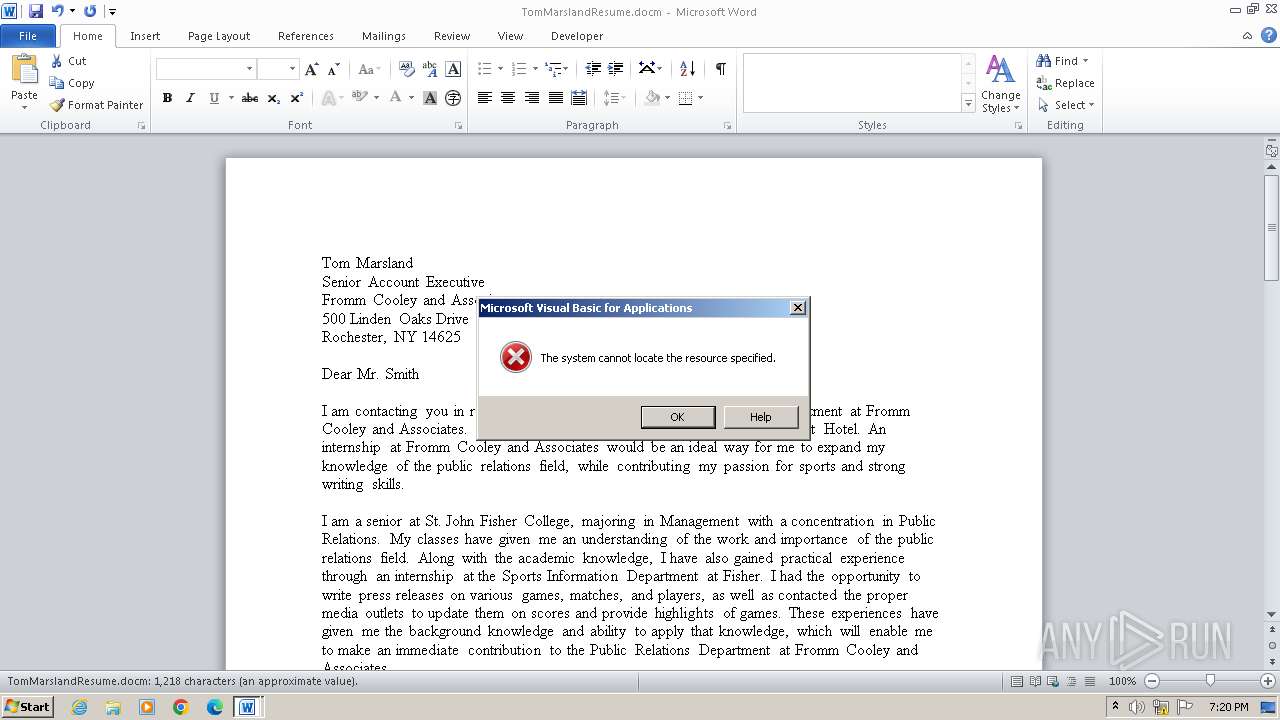
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2024, 18:19:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 9559A9EED09C11CBA30E4743CF7974CD |
| SHA1: | 52279F70194B2E4F89BDDE1F403B41194DFEC67D |
| SHA256: | C97A6B93B33D0DFC9685AAABC673756BC0329DE8D2F9F088CCE7C70B76C66489 |
| SSDEEP: | 384:UmA7zSZweORo0rhhFL/ulWsboTp0RBfk/VBCUNfde9I0ZkZY:UlWOxdhFLGlWsbm0bfW7nhIZkW |
MALICIOUS
Opens an HTTP connection (SCRIPT)
- WINWORD.EXE (PID: 3964)
Sends HTTP request (SCRIPT)
- WINWORD.EXE (PID: 3964)
Creates internet connection object (SCRIPT)
- WINWORD.EXE (PID: 3964)
SUSPICIOUS
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- WINWORD.EXE (PID: 3964)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x91fc8a0b |
| ZipCompressedSize: | 401 |
| ZipUncompressedSize: | 1586 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | cents |
|---|
XML
| LastModifiedBy: | Solanki, Chance Y Finance |
|---|---|
| RevisionNumber: | 12 |
| CreateDate: | 2022:07:04 00:29:00Z |
| ModifyDate: | 2023:01:16 06:22:00Z |
| Template: | Normal |
| TotalEditTime: | 3.1 hours |
| Pages: | 2 |
| Words: | 220 |
| Characters: | 1258 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 10 |
| Paragraphs: | 2 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | ARGENTS |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1476 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
34
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3964 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n C:\Users\admin\AppData\Local\Temp\TomMarslandResume.docm | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
6 881
Read events
6 474
Write events
163
Delete events
244
Modification events
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %>? |
Value: 253E3F007C0F0000010000000000000000000000 | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3964) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3E05.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:D27D307C9620F0F2B78519B6F5CB7294 | SHA256:8A5E3EC0A17A150FA69946625208F77546C15E5247A4A318EE1F7ADA644FFCF5 | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\mso4384.tmp | image | |
MD5:ED3C1C40B68BA4F40DB15529D5443DEC | SHA256:039FE79B74E6D3D561E32D4AF570E6CA70DB6BB3718395BE2BF278B9E601279A | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$mMarslandResume.docm | pgc | |
MD5:364A57E7569CB042247F0F4ABDE8885C | SHA256:3125099063FB0FDFF87AA75EE9036CD72E29C03E16243E4FC4A740184EAF355C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3964 | WINWORD.EXE | 9.53.99.47:80 | — | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |