| File name: | http://tis2-ftp.access-accounts.net/tags/teamviewerqs.exe |
| Full analysis: | https://app.any.run/tasks/11a4a0e7-e646-45b5-89d0-fe6642cc9f5b |
| Verdict: | Malicious activity |
| Analysis date: | September 26, 2019, 07:25:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | AB958EEC3FB498B93010A84AEC8DCB3A |
| SHA1: | D279E9BC9D90C8787FEA23F4CC0A4177B0125F2F |
| SHA256: | C96F9147B9D07A170A207624C3D8DCA5199779245D29E33DC7B045F71981D3C8 |
| SSDEEP: | 393216:feDZyZDA9v85hnsL0BEL+F5B8pkqiCMIshm+T/B:WDM9cE59sgq8kkqipdd |
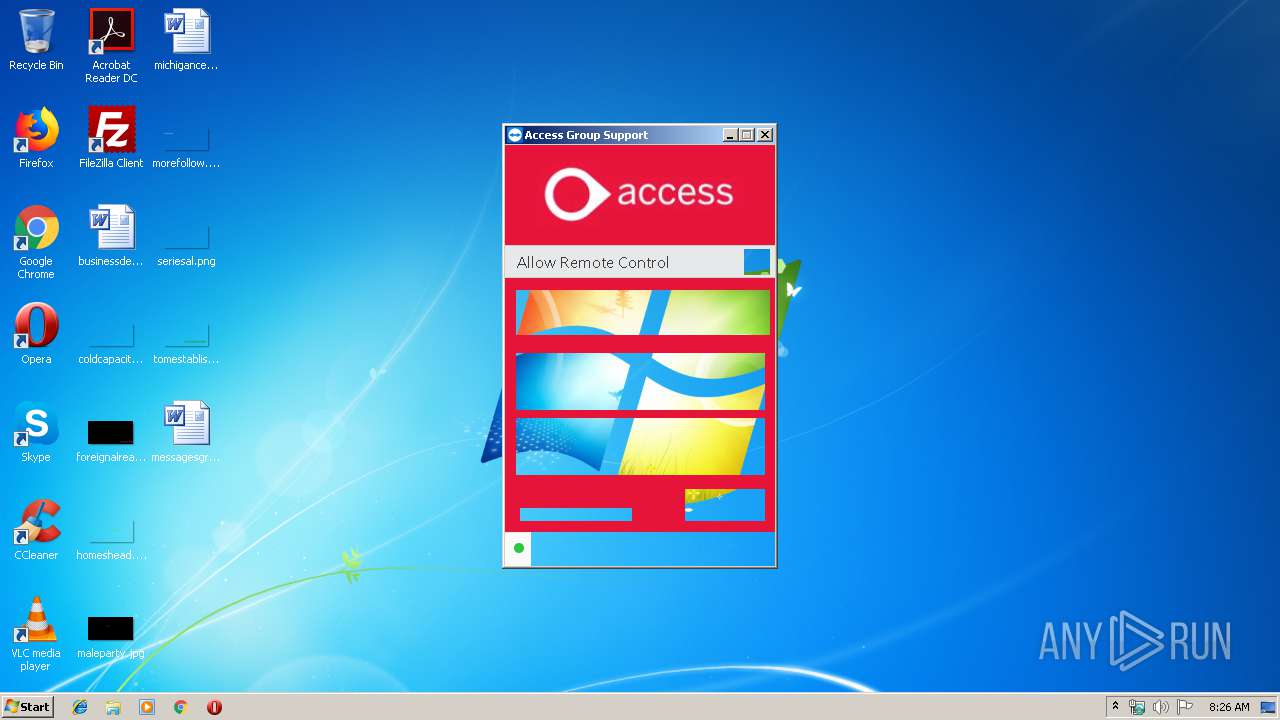
MALICIOUS
Loads dropped or rewritten executable
- teamviewerqs.exe (PID: 3772)
- TeamViewer.exe (PID: 2536)
- TeamViewer.exe (PID: 2720)
- tv_w32.exe (PID: 2688)
Application was dropped or rewritten from another process
- tv_w32.exe (PID: 2688)
SUSPICIOUS
Creates files in the user directory
- TeamViewer.exe (PID: 2536)
Executable content was dropped or overwritten
- teamviewerqs.exe (PID: 3772)
Application launched itself
- TeamViewer.exe (PID: 2536)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:03 22:18:56+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x33b6 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 14.0.13880.0 |
| ProductVersionNumber: | 14.0.13880.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | TeamViewer Remote Control Application |
| CompanyName: | TeamViewer |
| LegalCopyright: | TeamViewer |
| ProductName: | TeamViewer QS |
| ProductVersion: | 14.0.13880.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Apr-2016 20:18:56 |
| Detected languages: |
|
| Comments: | TeamViewer Remote Control Application |
| CompanyName: | TeamViewer |
| LegalCopyright: | TeamViewer |
| ProductName: | TeamViewer QS |
| ProductVersion: | 14.0.13880.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Apr-2016 20:18:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000615D | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45041 |
.rdata | 0x00008000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.163 |
.data | 0x0000A000 | 0x00020338 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.9824 |
.ndata | 0x0002B000 | 0x00019000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00044000 | 0x00047200 | 0x00047200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.81977 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29548 | 1061 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.22479 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.43297 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.39572 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 3.00583 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2536 | "C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer.exe" --configuration 2wwk4f2 | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer.exe | teamviewerqs.exe | ||||||||||||
User: admin Company: TeamViewer GmbH Integrity Level: MEDIUM Description: TeamViewer 14 Exit code: 0 Version: 14.0.13880.0 Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\AppData\Local\Temp\TeamViewer\tv_w32.exe" --action hooks --log C:\Users\admin\AppData\Roaming\TeamViewer\TeamViewer14_Logfile.log | C:\Users\admin\AppData\Local\Temp\TeamViewer\tv_w32.exe | TeamViewer.exe | ||||||||||||
User: SYSTEM Company: TeamViewer GmbH Integrity Level: SYSTEM Description: TeamViewer 14 Exit code: 0 Version: 14.0.13880.0 Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer.exe" --configuration 2wwk4f2 --dre | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer.exe | TeamViewer.exe | ||||||||||||
User: admin Company: TeamViewer GmbH Integrity Level: HIGH Description: TeamViewer 14 Exit code: 0 Version: 14.0.13880.0 Modules
| |||||||||||||||
| 3772 | "C:\Users\admin\AppData\Local\Temp\teamviewerqs.exe" | C:\Users\admin\AppData\Local\Temp\teamviewerqs.exe | explorer.exe | ||||||||||||
User: admin Company: TeamViewer Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
839
Read events
806
Write events
32
Delete events
1
Modification events
| (PID) Process: | (3772) teamviewerqs.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3772) teamviewerqs.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2536) TeamViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: TeamViewer.exe | |||
| (PID) Process: | (2536) TeamViewer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2536) TeamViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2536) TeamViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2720) TeamViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: TeamViewer.exe | |||
| (PID) Process: | (2720) TeamViewer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2720) TeamViewer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TeamViewer\DefaultSettings |
| Operation: | write | Name: | Autostart_GUI |
Value: 0 | |||
| (PID) Process: | (2720) TeamViewer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TeamViewer\Temp |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
48
Suspicious files
0
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3772 | teamviewerqs.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\tvqsfiles.7z | — | |
MD5:— | SHA256:— | |||
| 3772 | teamviewerqs.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer.exe | — | |
MD5:— | SHA256:— | |||
| 3772 | teamviewerqs.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Service.exe | executable | |
MD5:— | SHA256:— | |||
| 3772 | teamviewerqs.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 3772 | teamviewerqs.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\tv_w32.exe | executable | |
MD5:— | SHA256:— | |||
| 3772 | teamviewerqs.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Note.exe | executable | |
MD5:— | SHA256:— | |||
| 3772 | teamviewerqs.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Resource_da.dll | executable | |
MD5:— | SHA256:— | |||
| 3772 | teamviewerqs.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Resource_ar.dll | executable | |
MD5:— | SHA256:— | |||
| 3772 | teamviewerqs.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Resource_bg.dll | executable | |
MD5:— | SHA256:— | |||
| 3772 | teamviewerqs.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\tv_x64.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
6
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
— | — | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/AFE5D244A8D1194230FF479FE2F897BBCD7A8CB4.crt | US | der | 1.46 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
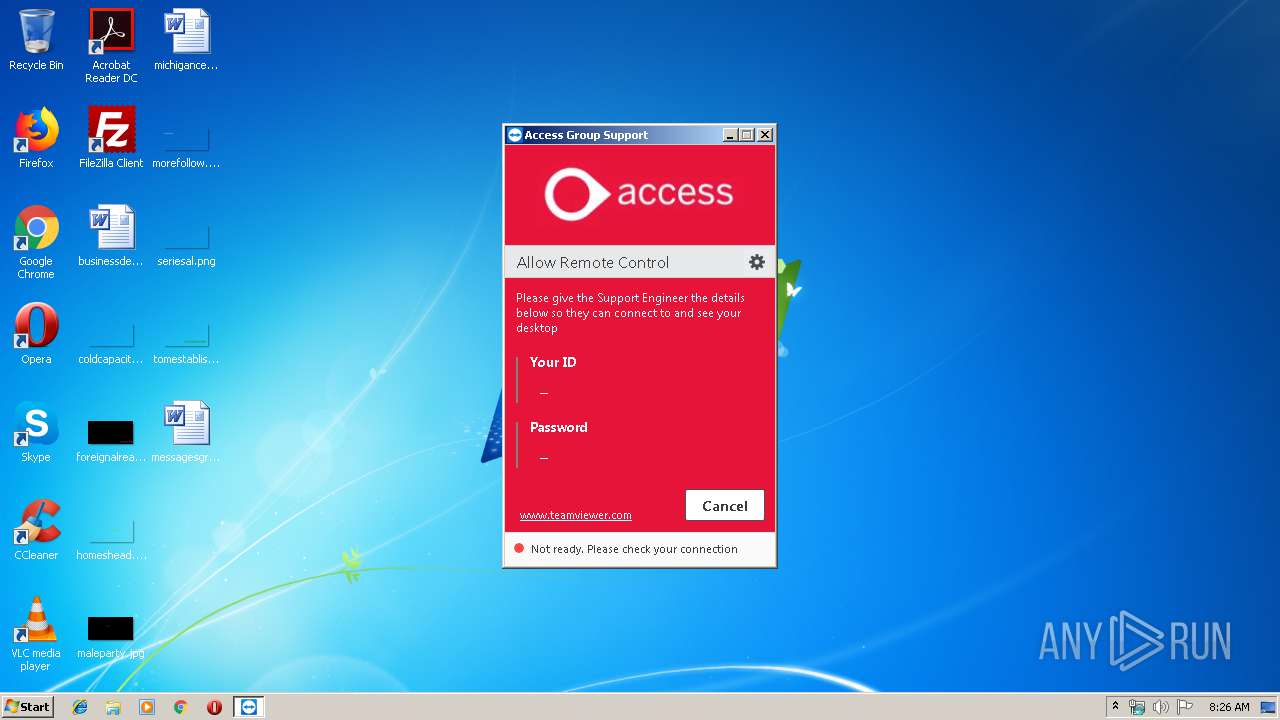
2720 | TeamViewer.exe | 137.117.184.37:443 | configdl.teamviewer.com | Microsoft Corporation | NL | whitelisted |
2720 | TeamViewer.exe | 217.146.13.137:5938 | router8.teamviewer.com | ANEXIA Internetdienstleistungs GmbH | PL | suspicious |
2720 | TeamViewer.exe | 52.168.20.22:443 | client.teamviewer.com | Microsoft Corporation | US | whitelisted |
— | — | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
— | — | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2536 | TeamViewer.exe | 137.117.184.37:443 | configdl.teamviewer.com | Microsoft Corporation | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
configdl.teamviewer.com |
| unknown |
router8.teamviewer.com |
| suspicious |
client.teamviewer.com |
| shared |
crt.comodoca.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2720 | TeamViewer.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TeamViewer connection |
2720 | TeamViewer.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TeamViewer negotiation |
2 ETPRO signatures available at the full report