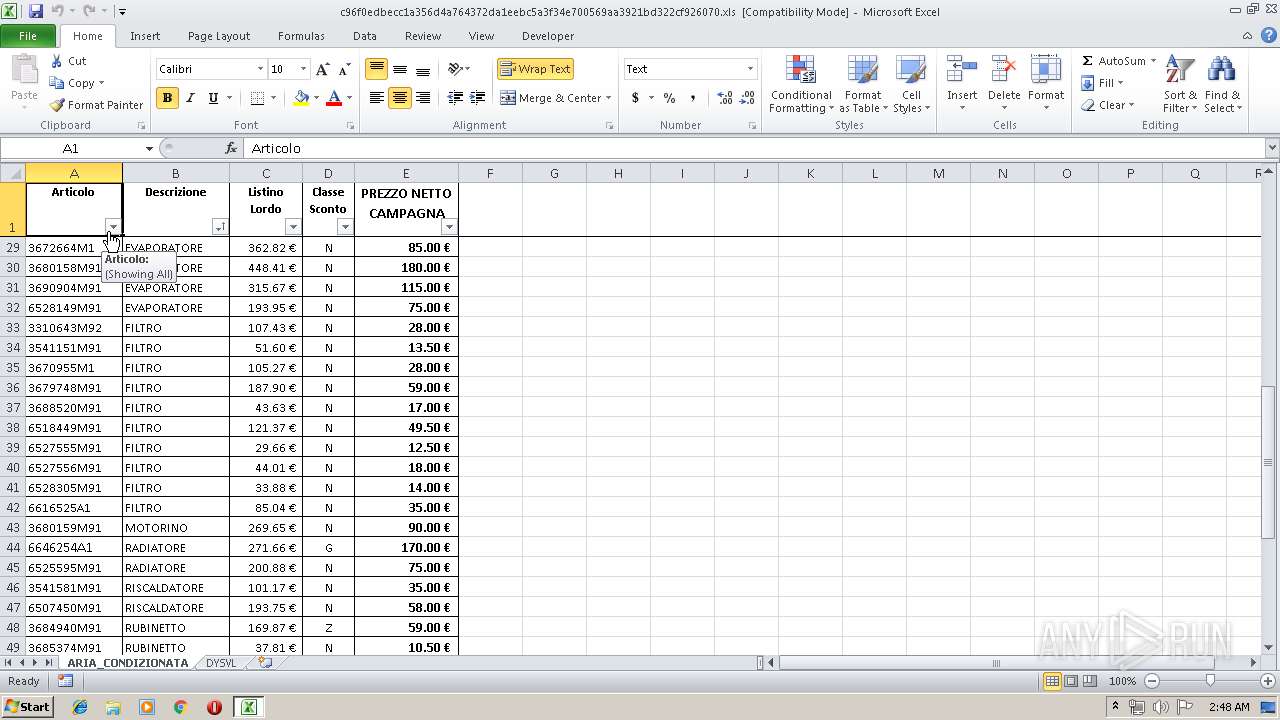
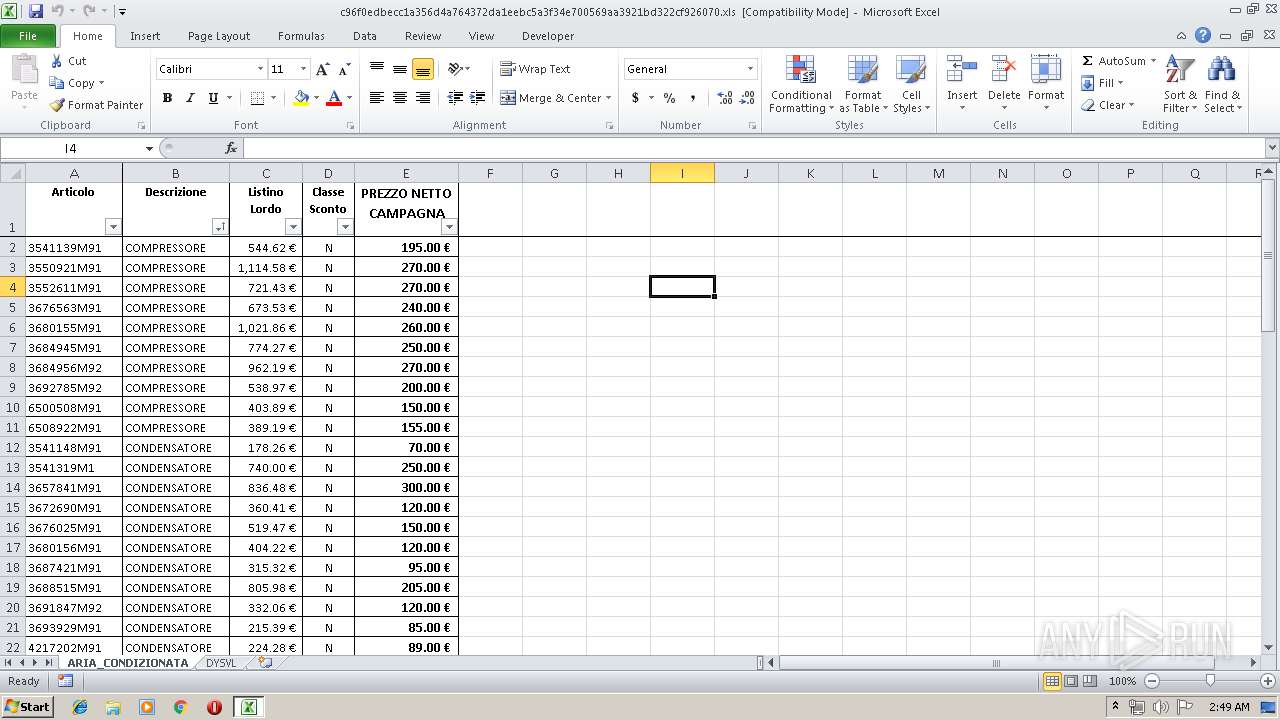
| File name: | c96f0edbecc1a356d4a764372da1eebc5a3f34e700569aa3921bd322cf926070.xls |
| Full analysis: | https://app.any.run/tasks/c74f18e5-aa60-4720-889e-536f046d282f |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 01:48:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/CDFV2 |
| File info: | Composite Document File V2 Document, Can't read directory |
| MD5: | D043ED2F7465DACA8C785195731B6A84 |
| SHA1: | 4824D8A2D31A26E01A1D4F53695F2C02E016FF8F |
| SHA256: | C96F0EDBECC1A356D4A764372DA1EEBC5A3F34E700569AA3921BD322CF926070 |
| SSDEEP: | 1536:3fk3hOdsylKlgryzc4bNhZFGzE+cL2knAiKKLDs3EgD0hBobE4VmI:vk3hOdsylKlgryzc4bNhZFGzE+cL2knt |
MALICIOUS
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 1372)
Application was dropped or rewritten from another process
- pb94a.exe (PID: 2316)
- pb94a.exe (PID: 1332)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1372)
SUSPICIOUS
Starts CMD.EXE for commands execution
- pb94a.exe (PID: 1332)
- cmmon32.exe (PID: 284)
Application launched itself
- pb94a.exe (PID: 1332)
Executable content was dropped or overwritten
- cmd.exe (PID: 1860)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1372)
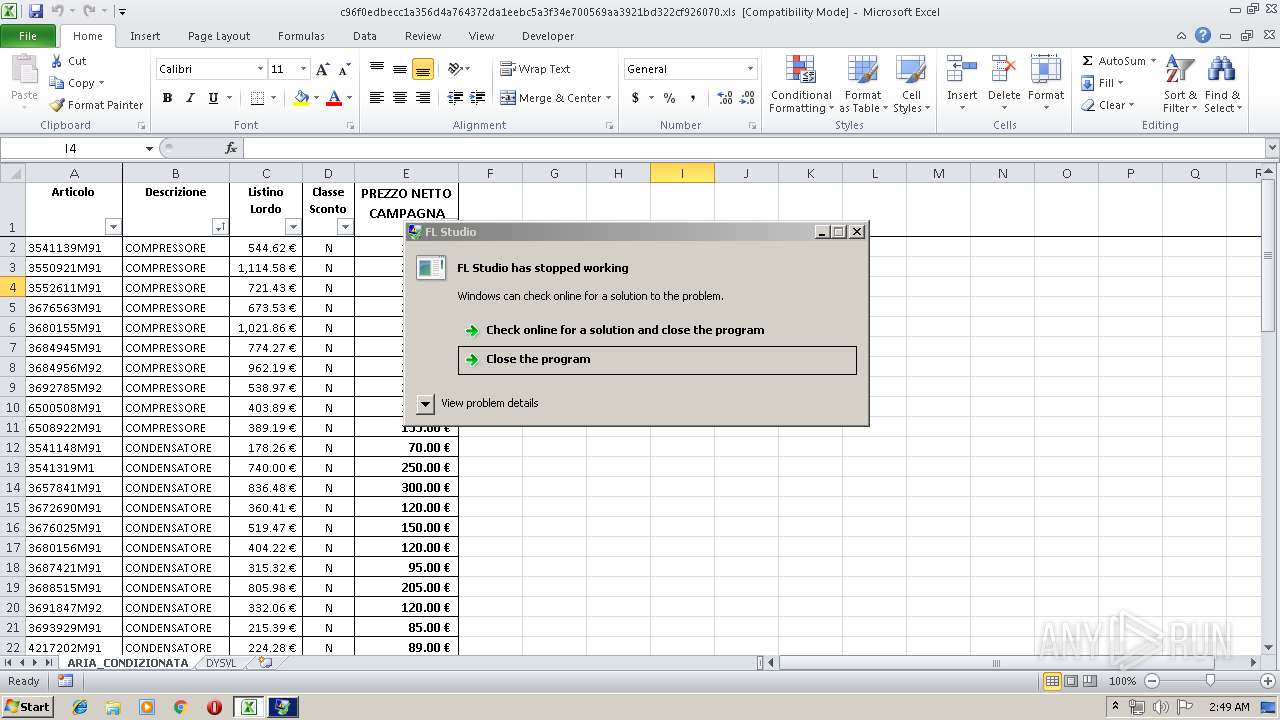
Application was crashed
- pb94a.exe (PID: 1332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
Total processes
46
Monitored processes
8
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Windows\System32\cmmon32.exe" | C:\Windows\System32\cmmon32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Monitor Exit code: 0 Version: 7.02.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | "C:\Users\admin\AppData\Local\Temp\pb94a.exe" | C:\Users\admin\AppData\Local\Temp\pb94a.exe | cmd.exe | ||||||||||||
User: admin Company: Image Line Software nv Integrity Level: MEDIUM Description: FL Studio Exit code: 0 Version: 1.1.48.0 Modules
| |||||||||||||||
| 1372 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1860 | "C:\Windows\System32\cmd.exe" /c ren "C:\Users\admin\AppData\Local\Temp\pb94a.png" "pb94a.exe" &start "" "C:\Users\admin\AppData\Local\Temp\pb94a.exe" | C:\Windows\System32\cmd.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2316 | "C:\Users\admin\AppData\Local\Temp\pb94a.exe" | C:\Users\admin\AppData\Local\Temp\pb94a.exe | — | pb94a.exe | |||||||||||
User: admin Company: Image Line Software nv Integrity Level: MEDIUM Description: FL Studio Exit code: 0 Version: 1.1.48.0 Modules
| |||||||||||||||
| 3260 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\AppData\Local\Temp\pb94a.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | pb94a.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3604 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\AppData\Local\Temp\pb94a.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | pb94a.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4088 | /c del "C:\Users\admin\AppData\Local\Temp\pb94a.exe" | C:\Windows\System32\cmd.exe | — | cmmon32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
699
Read events
657
Write events
35
Delete events
7
Modification events
| (PID) Process: | (1372) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | -'6 |
Value: 2D2736005C050000010000000000000000000000 | |||
| (PID) Process: | (1372) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1372) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1372) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 5C050000A8AB2855C00AD50100000000 | |||
| (PID) Process: | (1372) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | -'6 |
Value: 2D2736005C050000010000000000000000000000 | |||
| (PID) Process: | (1372) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (1372) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (1372) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1372) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1372) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\134412 |
| Operation: | write | Name: | 134412 |
Value: 040000005C0500006600000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0063003900360066003000650064006200650063006300310061003300350036006400340061003700360034003300370032006400610031006500650062006300350061003300660033003400650037003000300035003600390061006100330039003200310062006400330032003200630066003900320036003000370030002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00010000000000000060F74156C00AD501124413001244130000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1372 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR3F8D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1372 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\pb94a.png | — | |
MD5:— | SHA256:— | |||
| 1860 | cmd.exe | C:\Users\admin\AppData\Local\Temp\pb94a.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1372 | EXCEL.EXE | 172.96.184.165:443 | excursiionline.ro | SingleHop, Inc. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
excursiionline.ro |
| suspicious |
www.alltraffic2update.review |
| unknown |
Threats
Process | Message |
|---|---|
pb94a.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
pb94a.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
pb94a.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
pb94a.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
pb94a.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
pb94a.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
pb94a.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
pb94a.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|