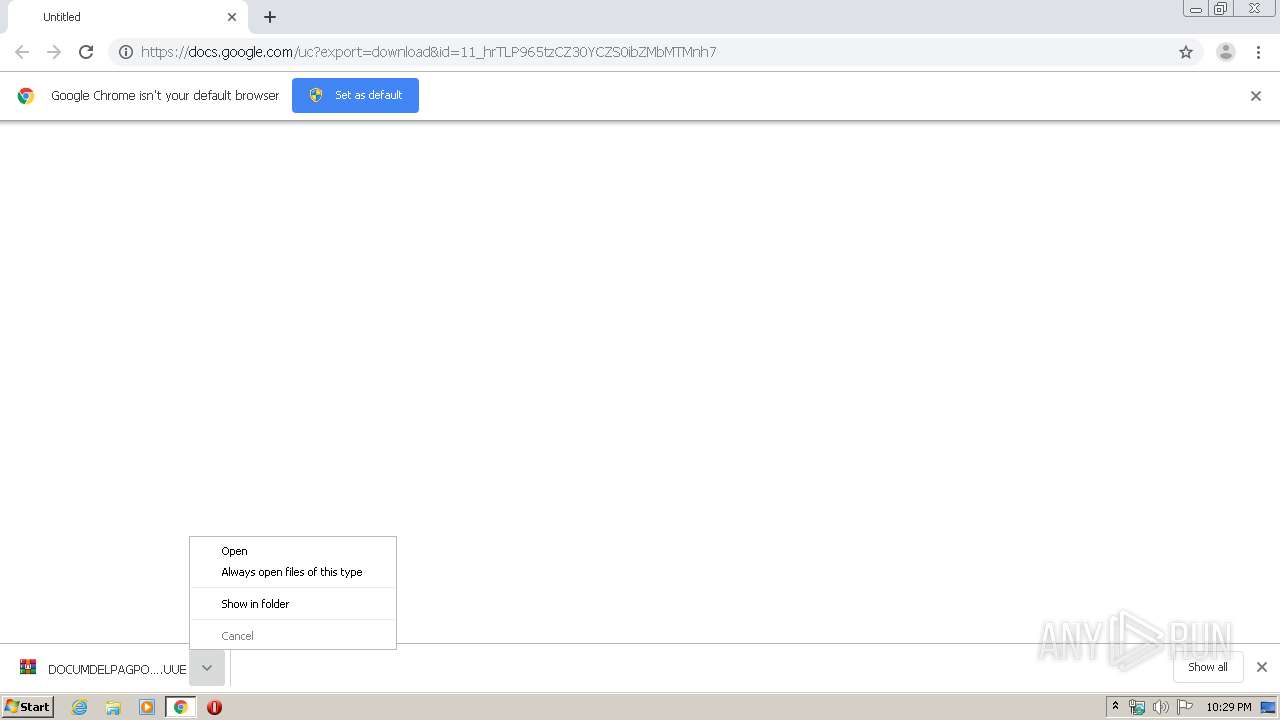
| URL: | https://docs.google.com/uc?export=download&id=11_hrTLP965tzCZ30YCZS0ibZMbMTMnh7 |
| Full analysis: | https://app.any.run/tasks/56417f41-6a17-4677-94a0-69c620f7ad7d |
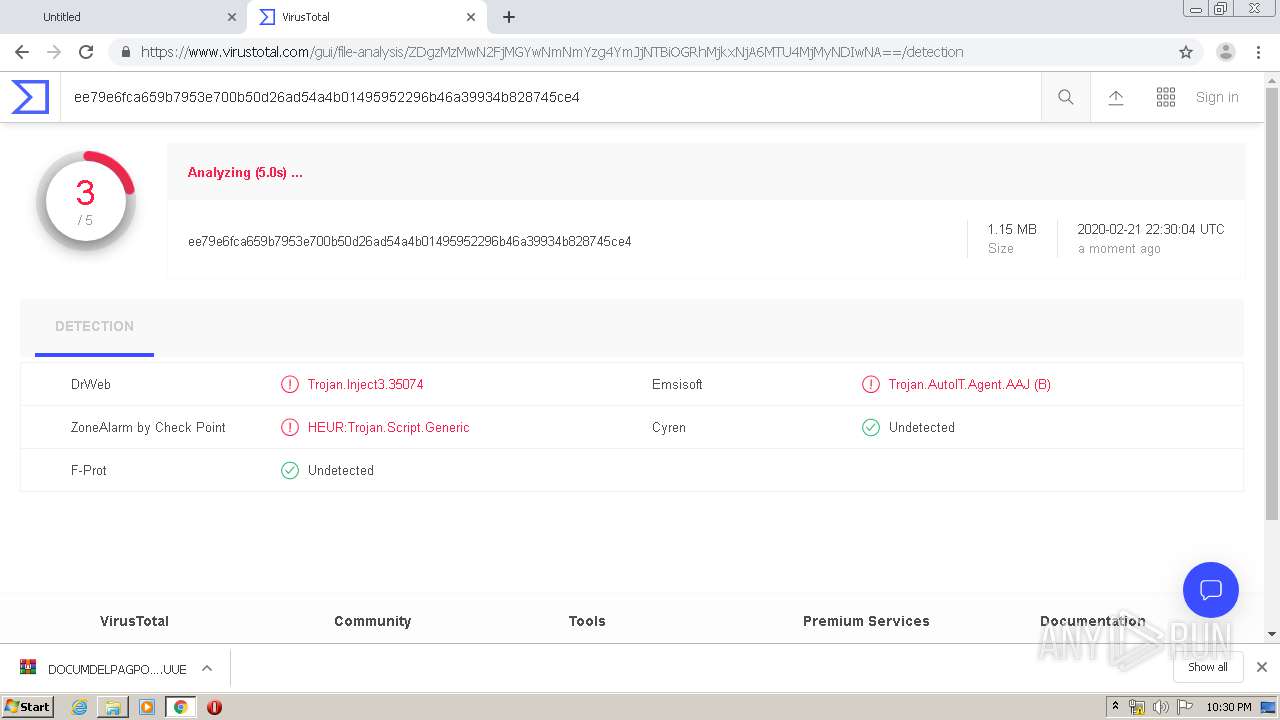
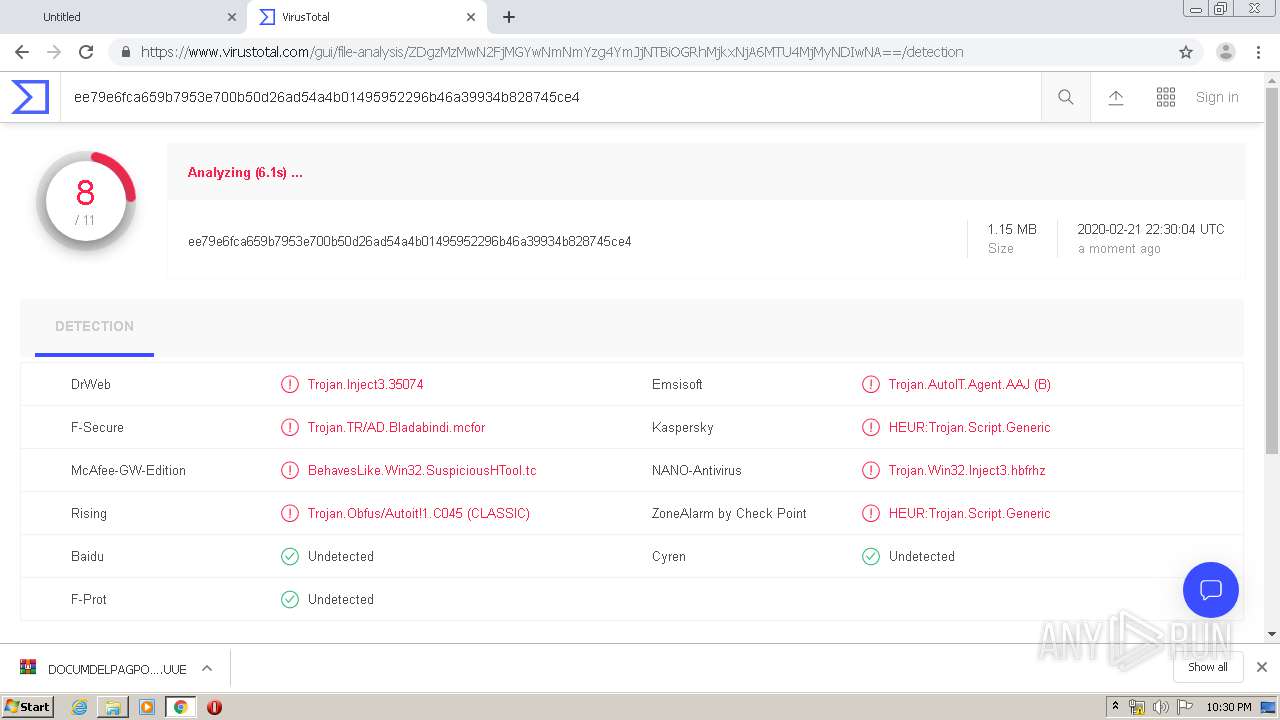
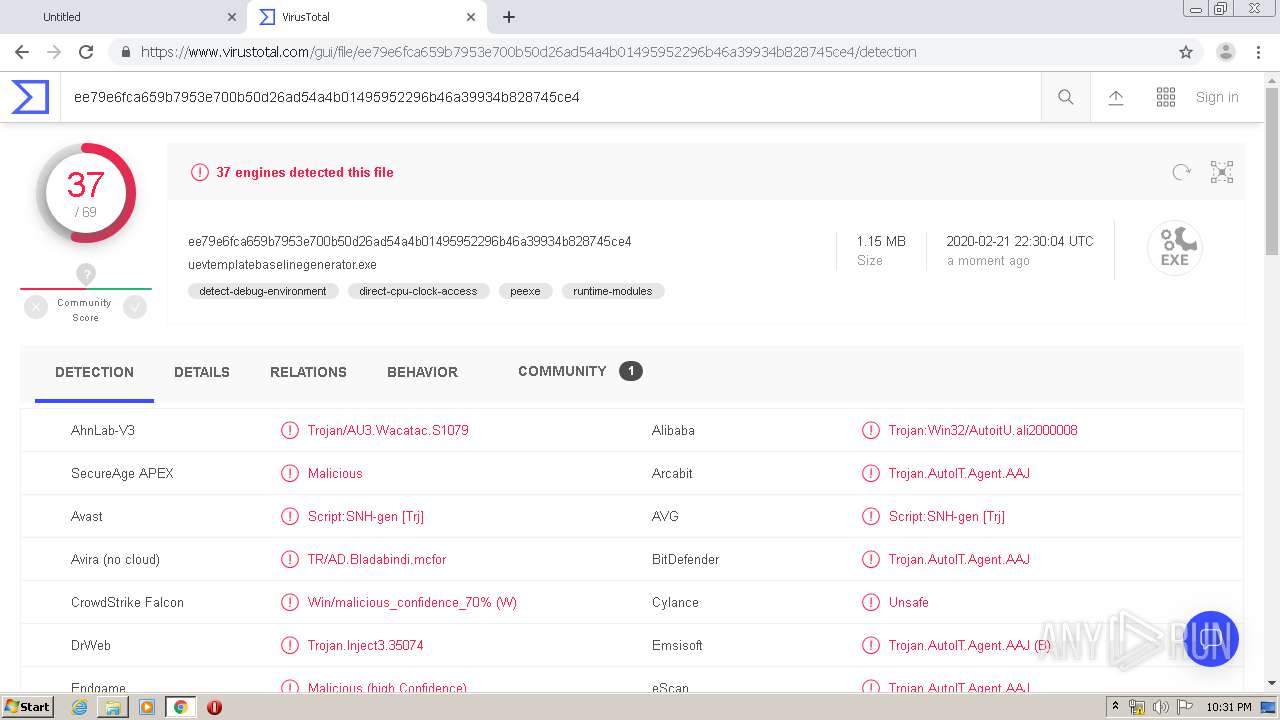
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 22:28:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
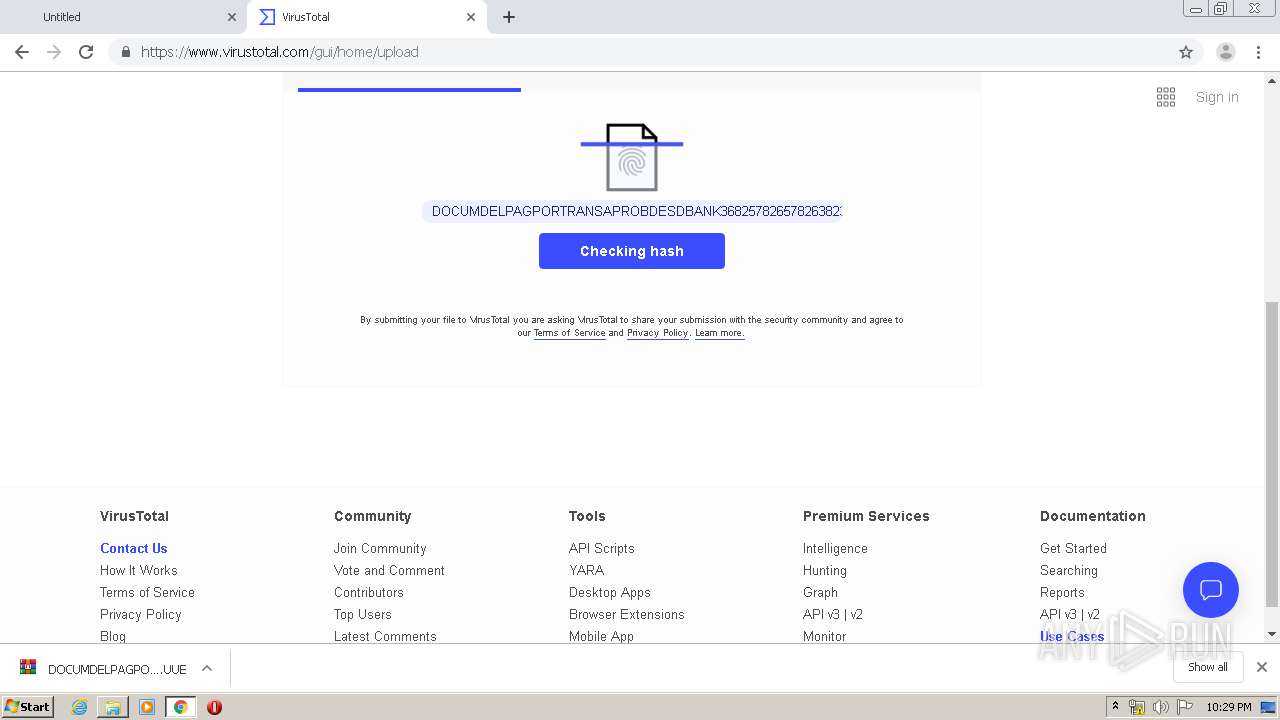
| MD5: | 788776290C19C75CD4CE2D93003E047F |
| SHA1: | 759C65FF4BEC5268AA3707895438D4147536B061 |
| SHA256: | C95F56C5E1E035A02F24D59297B14A1982EDF25B5D1EE68008C65518674162F8 |
| SSDEEP: | 3:N8SP3u2NAaBrC2jN/WNS8Iy1MWAn:2Sm2BB+25WNPIolAn |
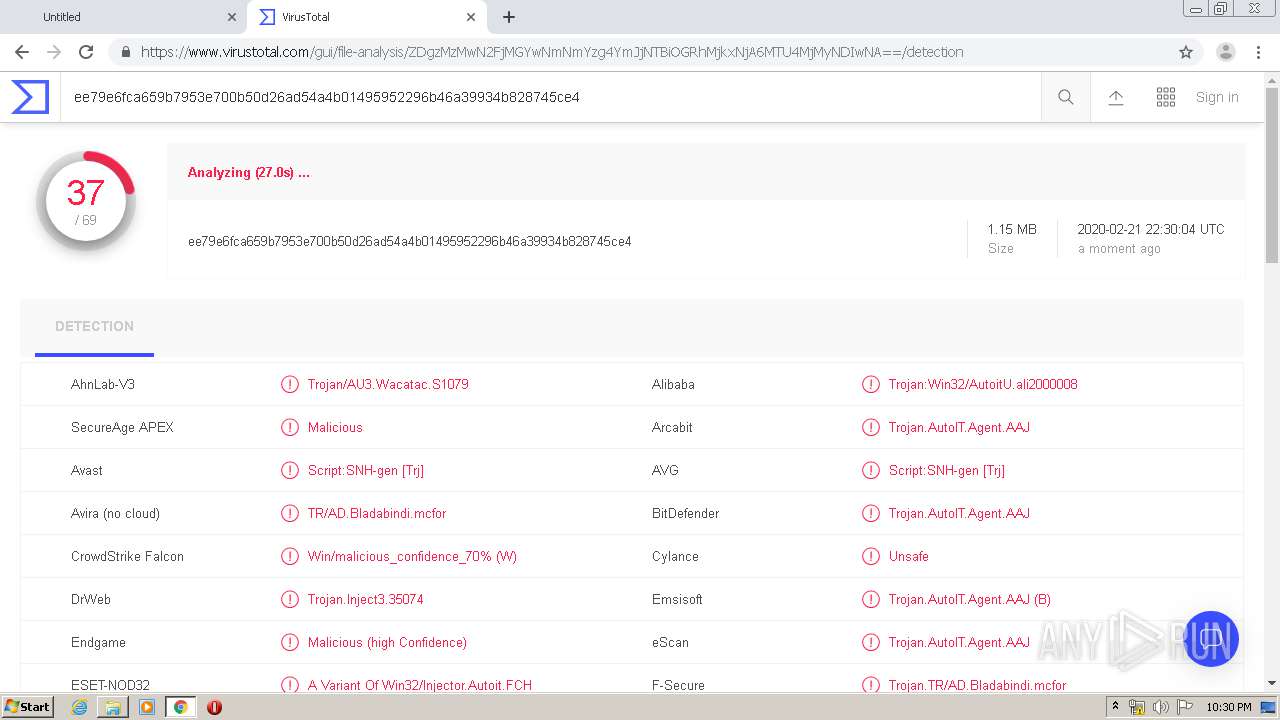
MALICIOUS
Writes to a start menu file
- DOCUMDELPAGPORTRANSAPROBDESDBANK368257826578263823600003 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360004 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360005.exe (PID: 1024)
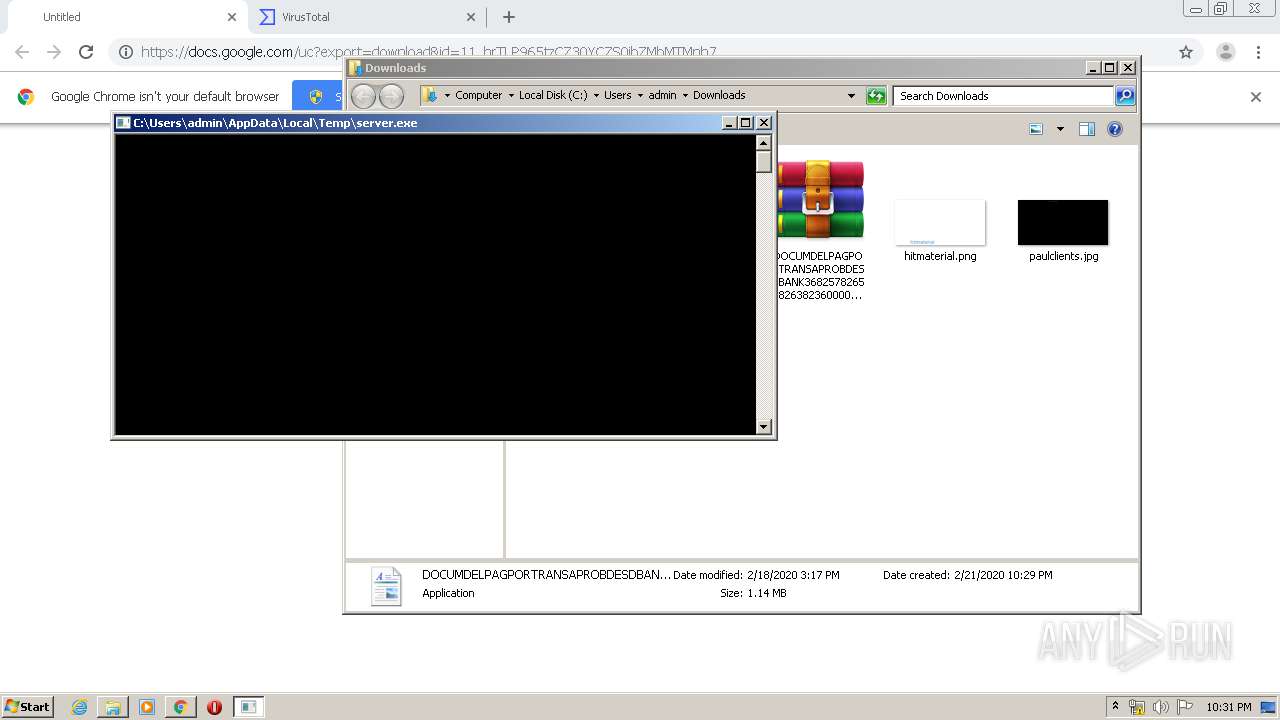
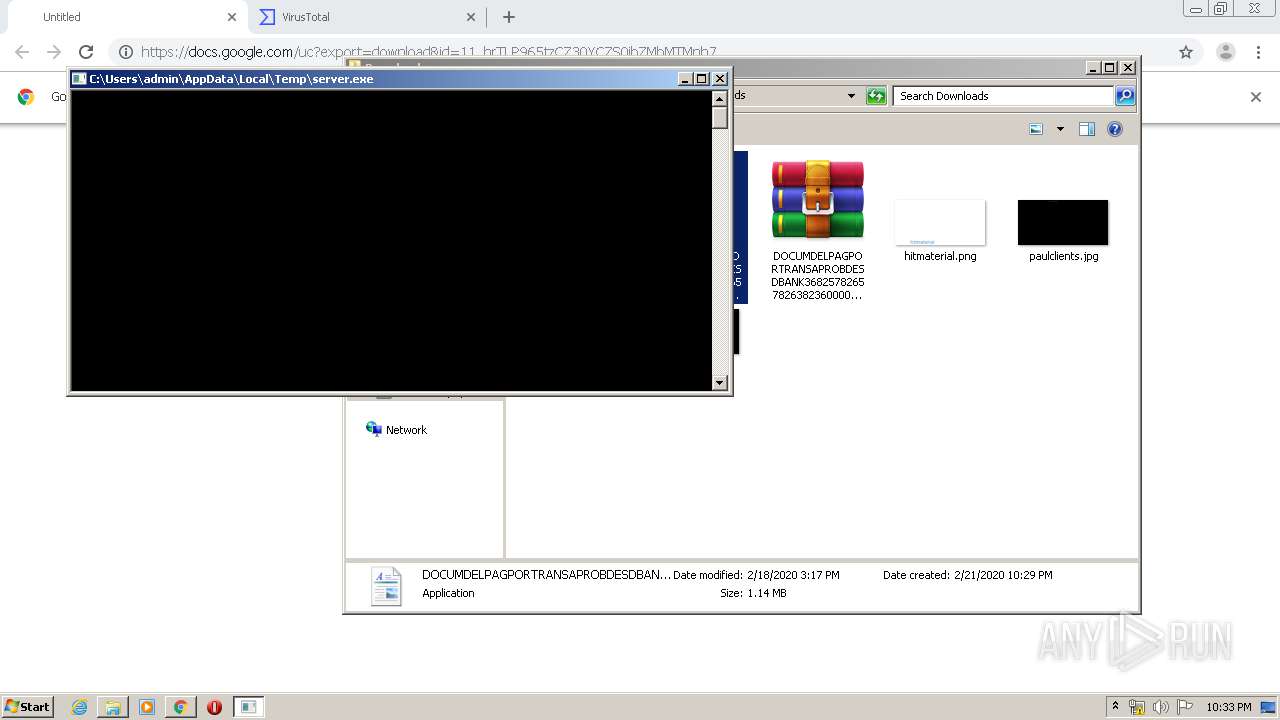
Application was dropped or rewritten from another process
- RegSvcs.exe (PID: 2676)
- DOCUMDELPAGPORTRANSAPROBDESDBANK368257826578263823600003 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360004 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360005.exe (PID: 1024)
- RegSvcs.exe (PID: 528)
- server.exe (PID: 3376)
- server.exe (PID: 1676)
- RegSvcs.exe (PID: 3884)
- server.exe (PID: 1392)
- RegSvcs.exe (PID: 820)
- RegSvcs.exe (PID: 2108)
- server.exe (PID: 1444)
- server.exe (PID: 2636)
- RegSvcs.exe (PID: 3836)
- RegSvcs.exe (PID: 3508)
- server.exe (PID: 1888)
- RegSvcs.exe (PID: 3132)
- server.exe (PID: 3860)
- server.exe (PID: 1636)
- server.exe (PID: 1544)
- RegSvcs.exe (PID: 3636)
- server.exe (PID: 3832)
- server.exe (PID: 2900)
- server.exe (PID: 3740)
- RegSvcs.exe (PID: 1508)
- RegSvcs.exe (PID: 2076)
- server.exe (PID: 2912)
- RegSvcs.exe (PID: 2540)
- RegSvcs.exe (PID: 3796)
- server.exe (PID: 3840)
- RegSvcs.exe (PID: 2280)
- server.exe (PID: 2700)
- RegSvcs.exe (PID: 780)
- server.exe (PID: 3480)
- RegSvcs.exe (PID: 3196)
- RegSvcs.exe (PID: 2396)
- RegSvcs.exe (PID: 1228)
- server.exe (PID: 3704)
SUSPICIOUS
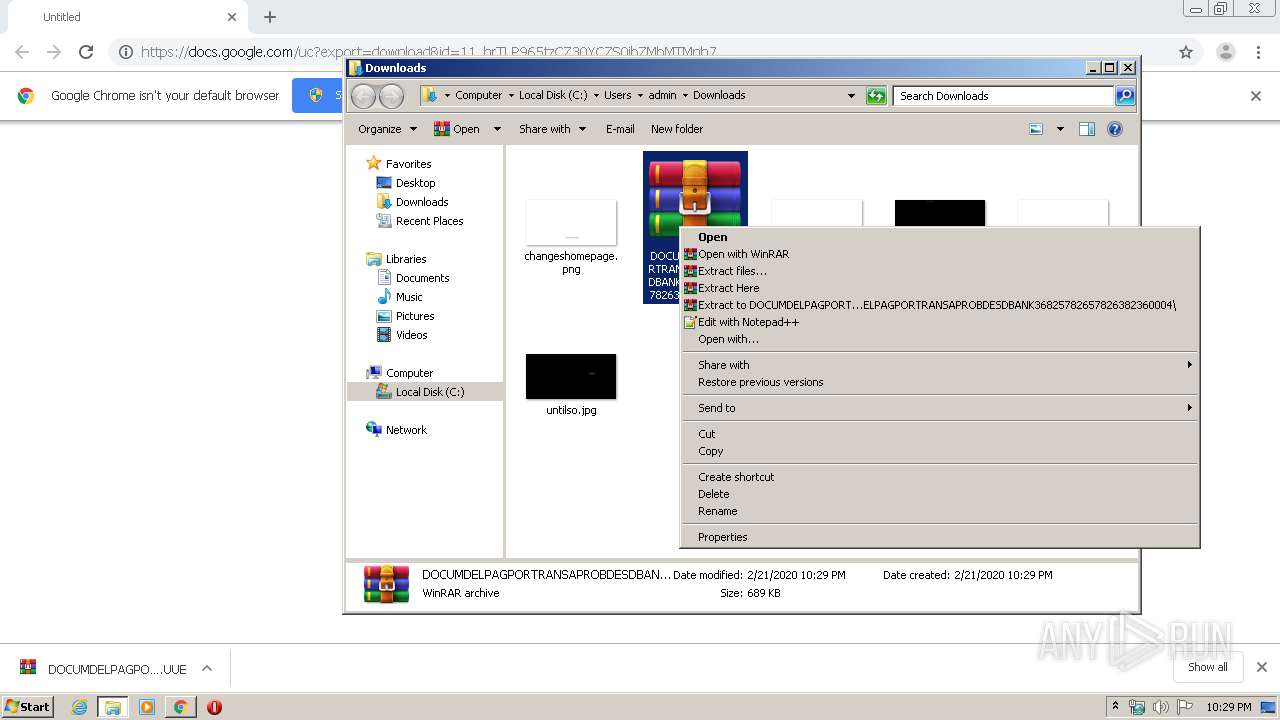
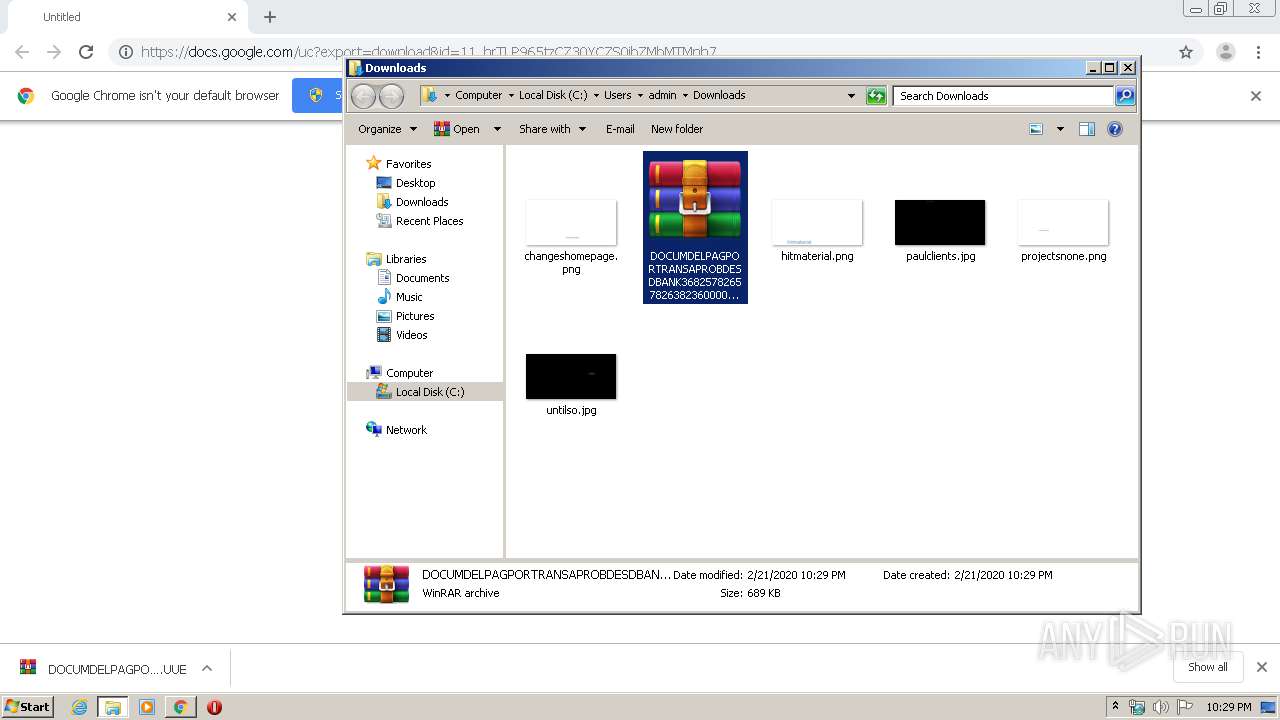
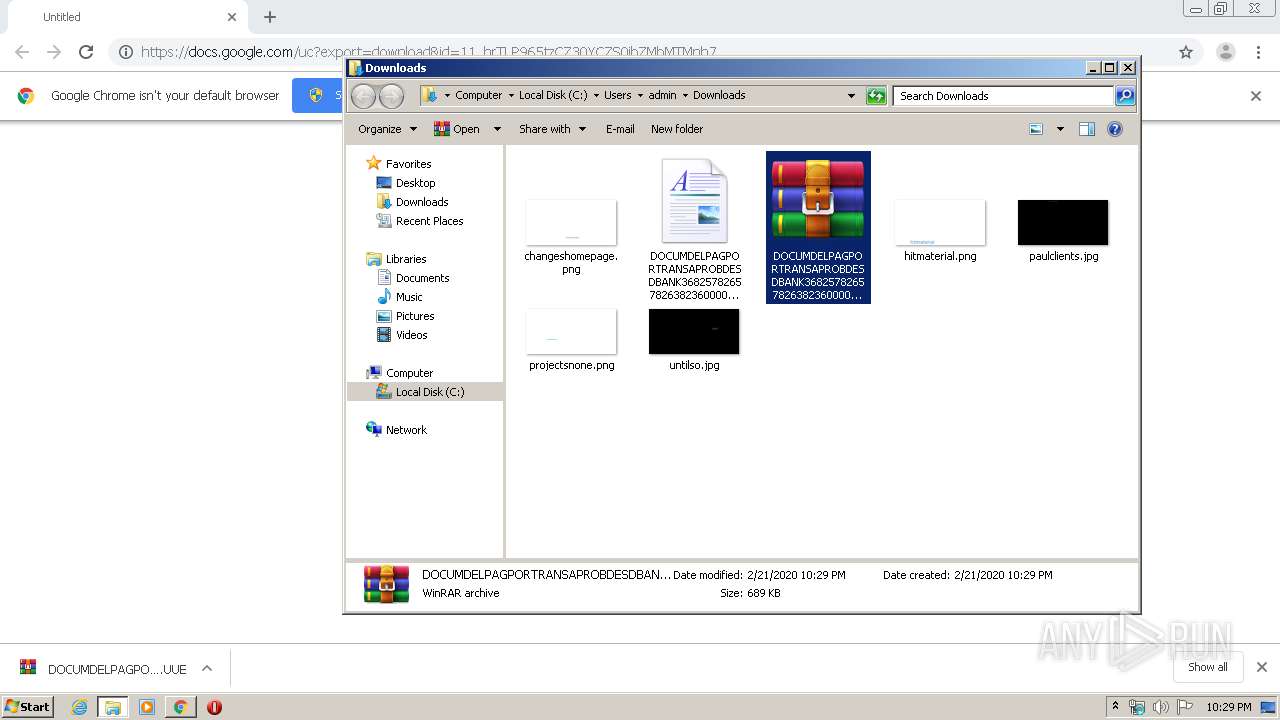
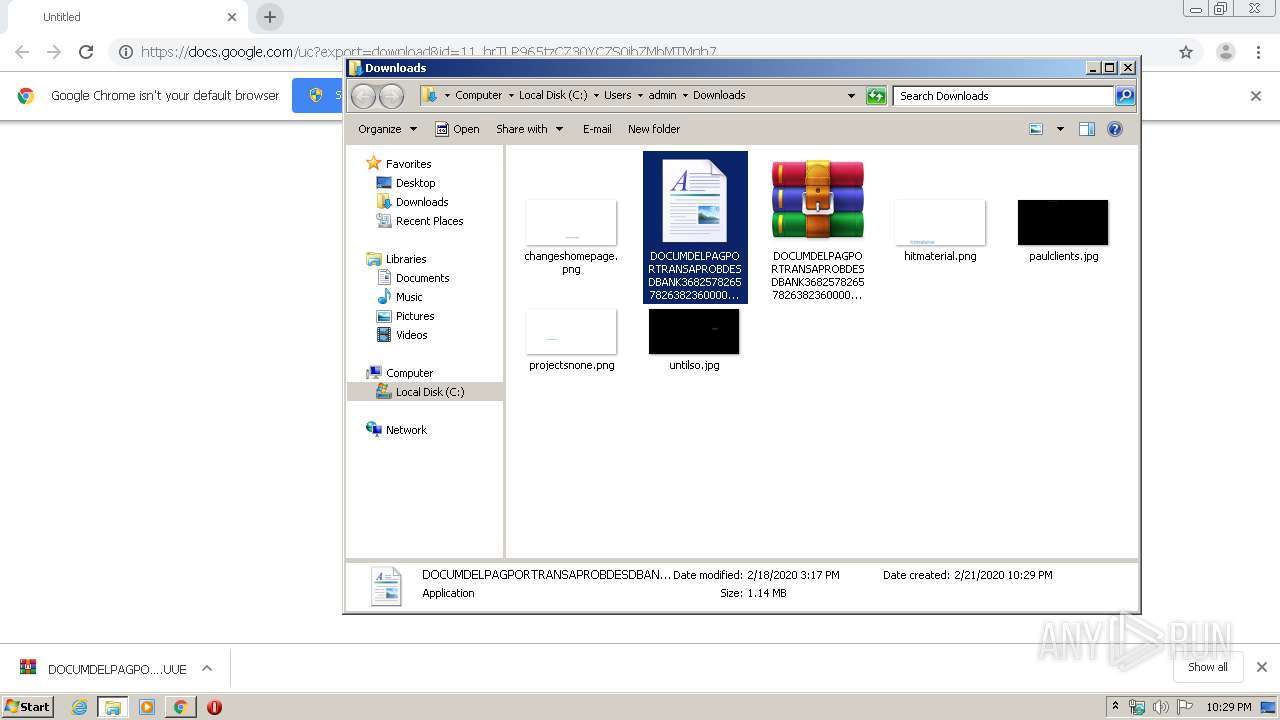
Executable content was dropped or overwritten
- WinRAR.exe (PID: 916)
- DOCUMDELPAGPORTRANSAPROBDESDBANK368257826578263823600003 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360004 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360005.exe (PID: 1024)
- RegSvcs.exe (PID: 2676)
- RegSvcs.exe (PID: 528)
- RegSvcs.exe (PID: 820)
- RegSvcs.exe (PID: 3132)
- RegSvcs.exe (PID: 2108)
- RegSvcs.exe (PID: 3836)
- RegSvcs.exe (PID: 3508)
- RegSvcs.exe (PID: 1228)
- RegSvcs.exe (PID: 3636)
- RegSvcs.exe (PID: 2540)
- RegSvcs.exe (PID: 2076)
- RegSvcs.exe (PID: 1508)
- RegSvcs.exe (PID: 3796)
- RegSvcs.exe (PID: 2280)
- RegSvcs.exe (PID: 780)
- RegSvcs.exe (PID: 3196)
- RegSvcs.exe (PID: 3884)
Starts itself from another location
- RegSvcs.exe (PID: 2676)
- RegSvcs.exe (PID: 528)
- RegSvcs.exe (PID: 3884)
- RegSvcs.exe (PID: 3132)
- RegSvcs.exe (PID: 3836)
- RegSvcs.exe (PID: 820)
- RegSvcs.exe (PID: 2108)
- RegSvcs.exe (PID: 3508)
- RegSvcs.exe (PID: 1228)
- RegSvcs.exe (PID: 3636)
- RegSvcs.exe (PID: 2540)
- RegSvcs.exe (PID: 3796)
- RegSvcs.exe (PID: 2076)
- RegSvcs.exe (PID: 780)
- RegSvcs.exe (PID: 2280)
- RegSvcs.exe (PID: 3196)
- RegSvcs.exe (PID: 1508)
Creates files in the user directory
- DOCUMDELPAGPORTRANSAPROBDESDBANK368257826578263823600003 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360004 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360005.exe (PID: 1024)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3596)
INFO
Reads the hosts file
- chrome.exe (PID: 3596)
- chrome.exe (PID: 2744)
Reads Internet Cache Settings
- chrome.exe (PID: 3596)
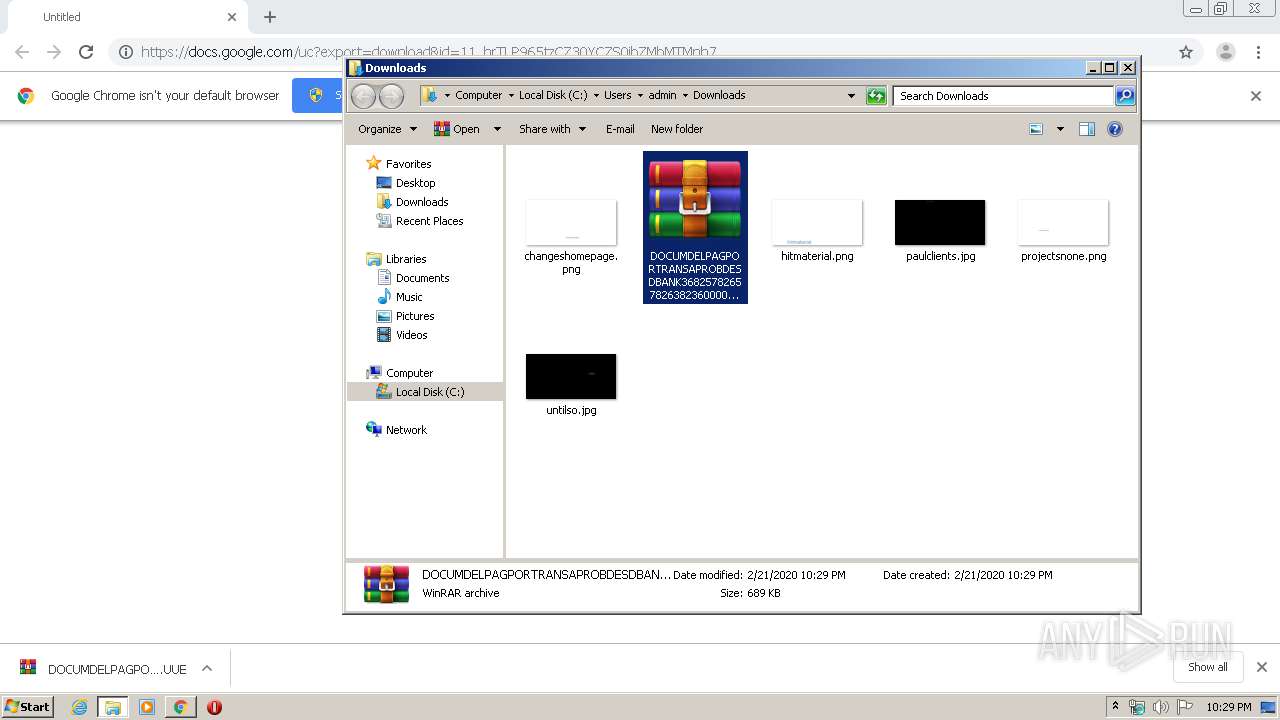
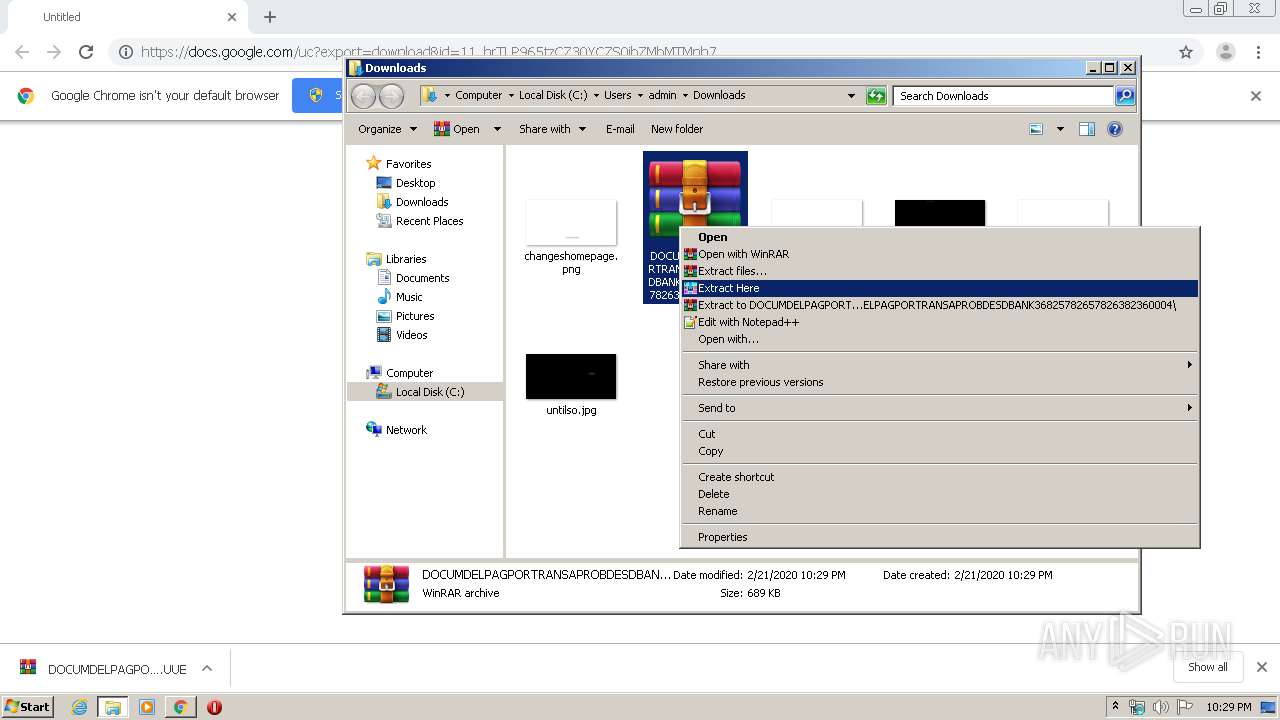
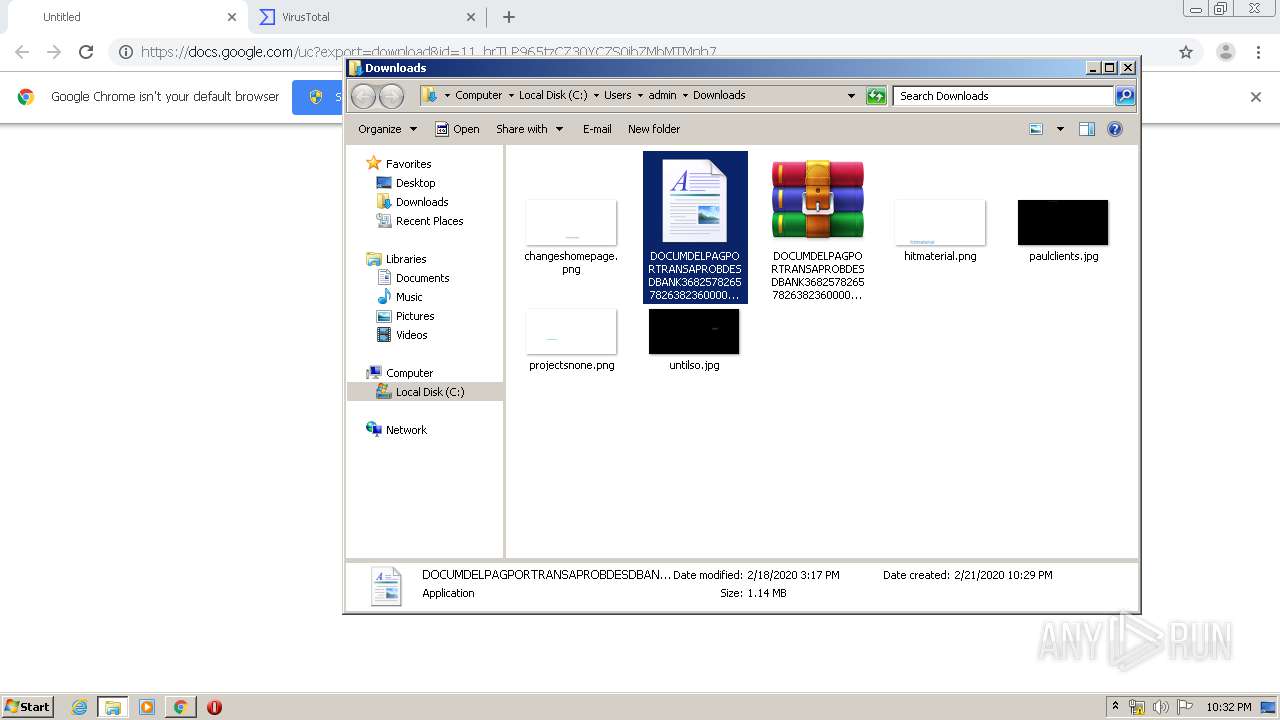
Manual execution by user
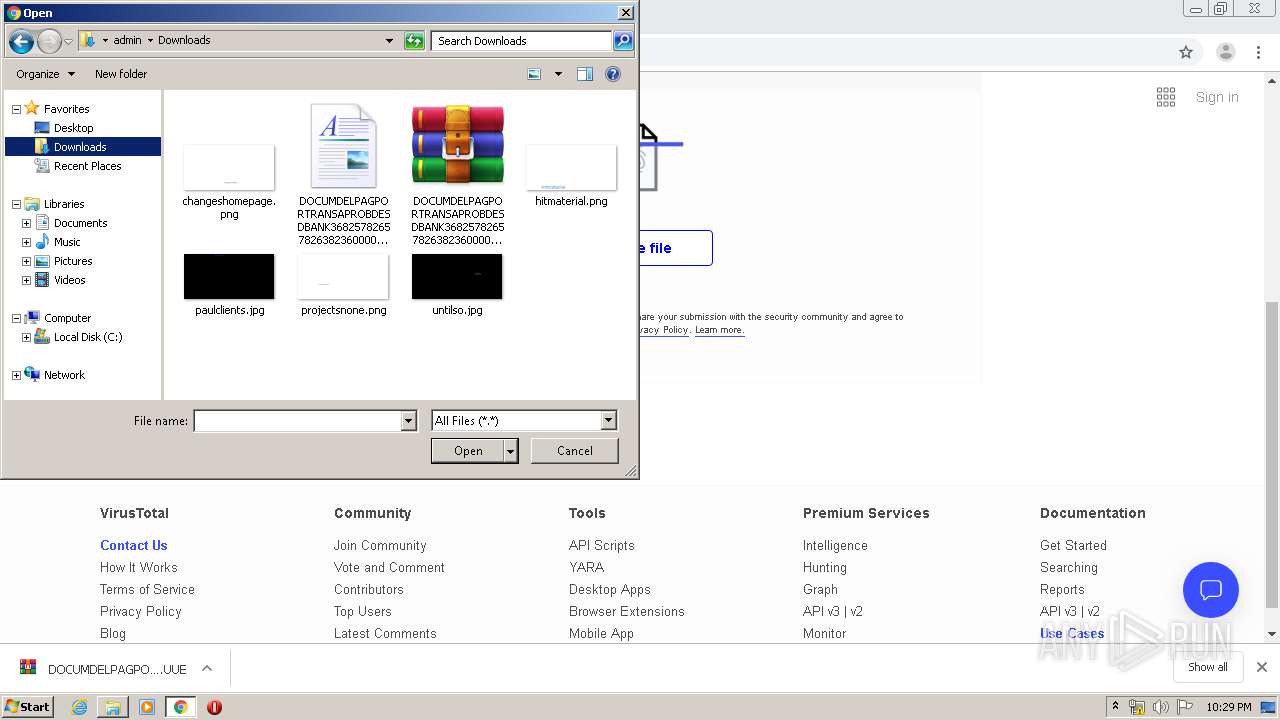
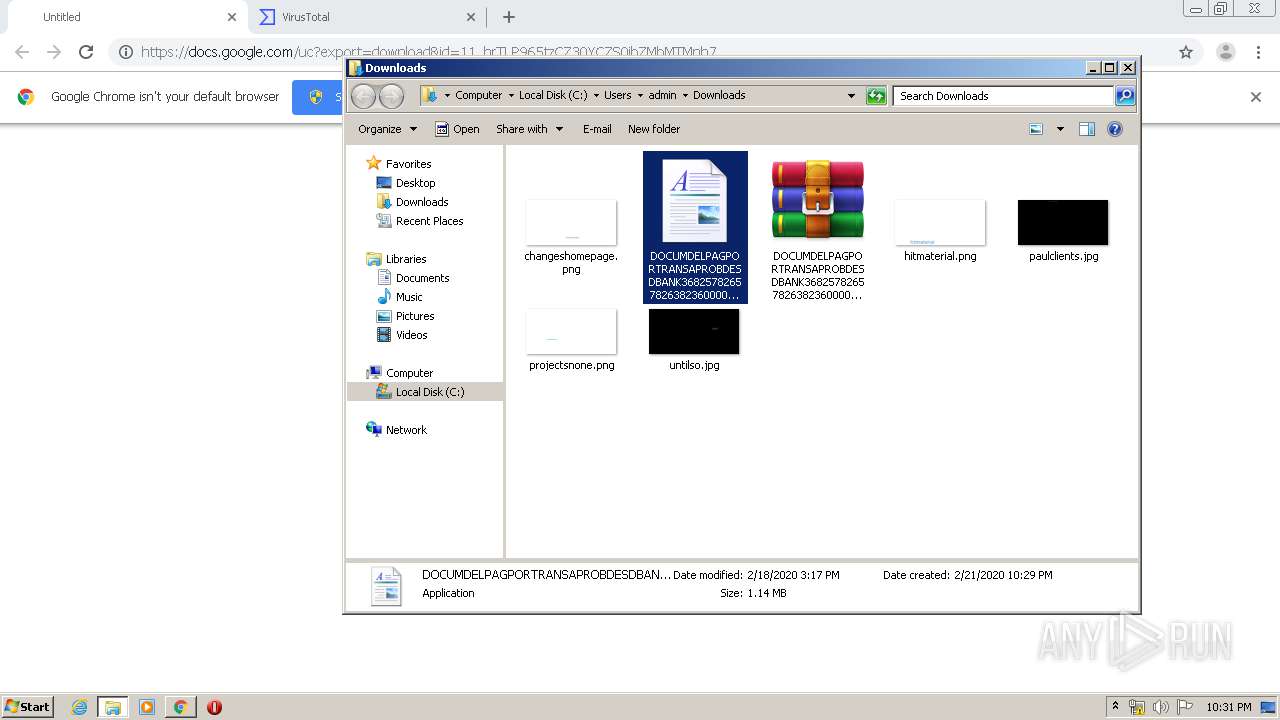
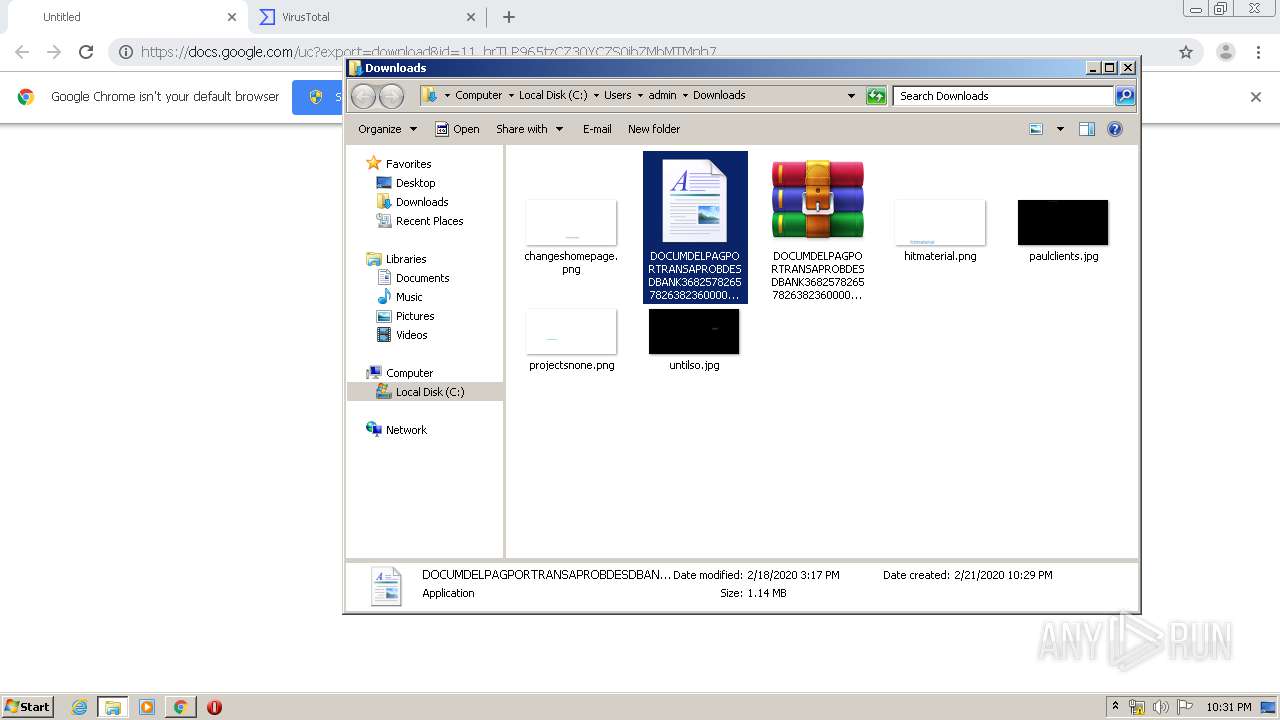
- WinRAR.exe (PID: 916)
- DOCUMDELPAGPORTRANSAPROBDESDBANK368257826578263823600003 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360004 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360005.exe (PID: 1024)
Application launched itself
- chrome.exe (PID: 3596)
Reads settings of System Certificates
- chrome.exe (PID: 2744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
129
Monitored processes
71
Malicious processes
1
Suspicious processes
17
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v4.0.30319\\\\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | DOCUMDELPAGPORTRANSAPROBDESDBANK368257826578263823600003 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360004 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360005.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,5838647780629058313,16134911156175760992,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1125496368457211476 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v4.0.30319\\\\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | DOCUMDELPAGPORTRANSAPROBDESDBANK368257826578263823600003 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360004 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360005.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 820 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v4.0.30319\\\\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | DOCUMDELPAGPORTRANSAPROBDESDBANK368257826578263823600003 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360004 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360005.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 916 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\DOCUMDELPAGPORTRANSAPROBDESDBANK368257826578263823600003 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360004.UUE" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,5838647780629058313,16134911156175760992,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12568074013715503161 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,5838647780629058313,16134911156175760992,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10137070896257432437 --mojo-platform-channel-handle=2544 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Users\admin\Downloads\DOCUMDELPAGPORTRANSAPROBDESDBANK368257826578263823600003 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360004 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360005.exe" | C:\Users\admin\Downloads\DOCUMDELPAGPORTRANSAPROBDESDBANK368257826578263823600003 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360004 DOCUMDELPAGPORTRANSAPROBDESDBANK36825782657826382360005.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,5838647780629058313,16134911156175760992,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8397324919951157832 --mojo-platform-channel-handle=2992 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,5838647780629058313,16134911156175760992,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18274267437975344870 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
7 869
Read events
7 586
Write events
277
Delete events
6
Modification events
| (PID) Process: | (3596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3596-13226797736610875 |
Value: 259 | |||
| (PID) Process: | (3596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3596) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3596) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
19
Suspicious files
75
Text files
276
Unknown types
6
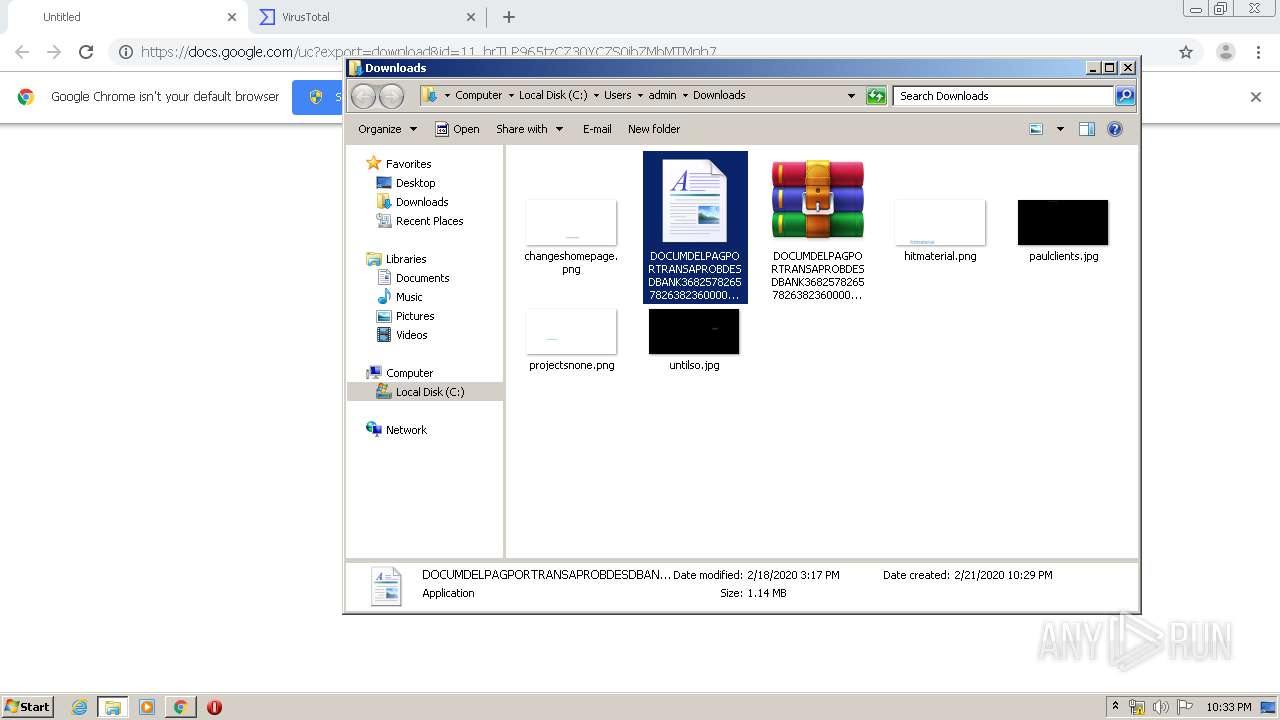
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E5059A8-E0C.pma | — | |
MD5:— | SHA256:— | |||
| 3596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa671cd.TMP | — | |
MD5:— | SHA256:— | |||
| 3596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e02d400e-4314-4cac-a1ee-6fef7ff4d2dd.tmp | — | |
MD5:— | SHA256:— | |||
| 3596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa6718e.TMP | text | |
MD5:— | SHA256:— | |||
| 3596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa671ec.TMP | text | |
MD5:— | SHA256:— | |||
| 3596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3596 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa67373.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
34
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2744 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
2744 | chrome.exe | GET | 200 | 195.95.178.206:80 | http://r3---sn-pouxga5o-vu2l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=45.41.138.204&mm=28&mn=sn-pouxga5o-vu2l&ms=nvh&mt=1582324212&mv=m&mvi=2&pl=24&shardbypass=yes | RO | crx | 293 Kb | whitelisted |
2744 | chrome.exe | GET | 200 | 195.95.178.175:80 | http://r4---sn-pouxga5o-vu2s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=45.41.138.204&mm=28&mn=sn-pouxga5o-vu2s&ms=nvh&mt=1582324212&mv=m&mvi=3&pl=24&shardbypass=yes | RO | crx | 862 Kb | whitelisted |
2744 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2744 | chrome.exe | 172.217.16.206:443 | docs.google.com | Google Inc. | US | whitelisted |
2744 | chrome.exe | 172.217.18.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
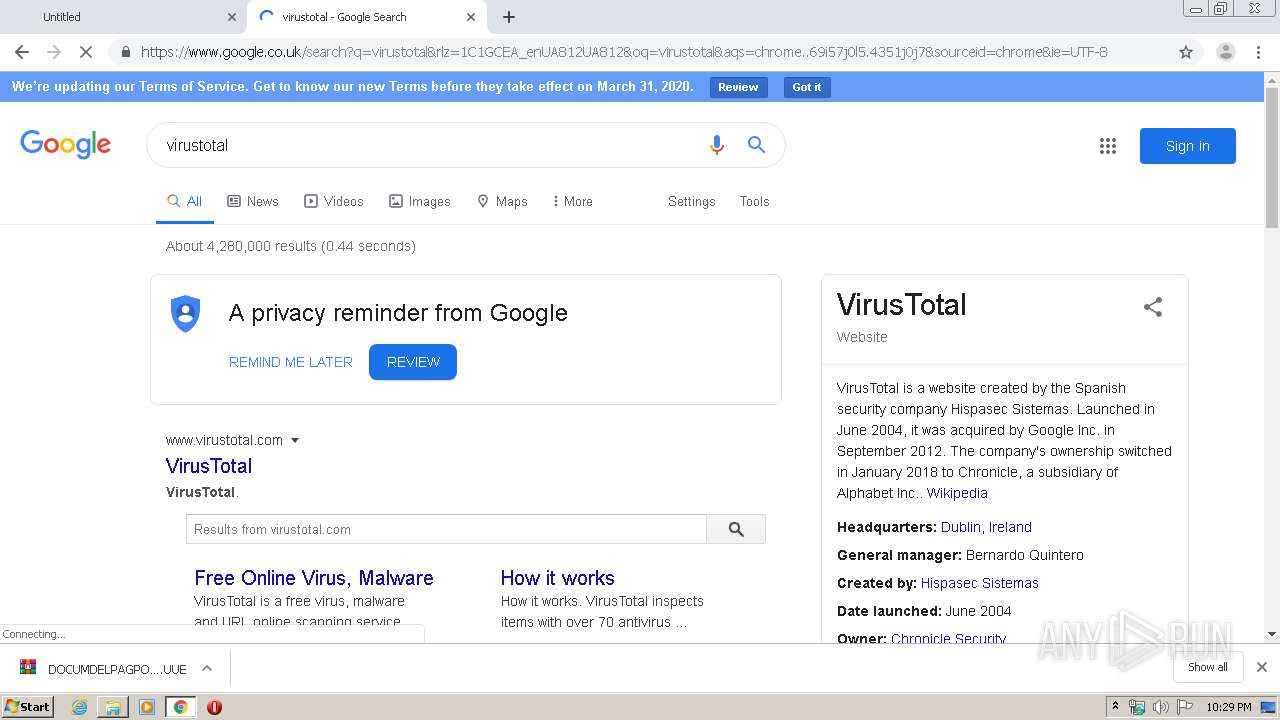
2744 | chrome.exe | 172.217.23.131:443 | www.google.co.uk | Google Inc. | US | whitelisted |
2744 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2744 | chrome.exe | 172.217.23.161:443 | doc-04-8s-docs.googleusercontent.com | Google Inc. | US | whitelisted |
2744 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2744 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
2744 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2744 | chrome.exe | 151.139.237.11:443 | cdn.rawgit.com | netDNA | US | suspicious |
2744 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
docs.google.com |
| shared |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
doc-04-8s-docs.googleusercontent.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.google.co.uk |
| whitelisted |
fonts.googleapis.com |
| whitelisted |