| File name: | 872abebdfc932a52ed277e452f706971-wrar561tr.exe |
| Full analysis: | https://app.any.run/tasks/d44e5f13-3d4f-446b-acf3-1f47ae24ac51 |
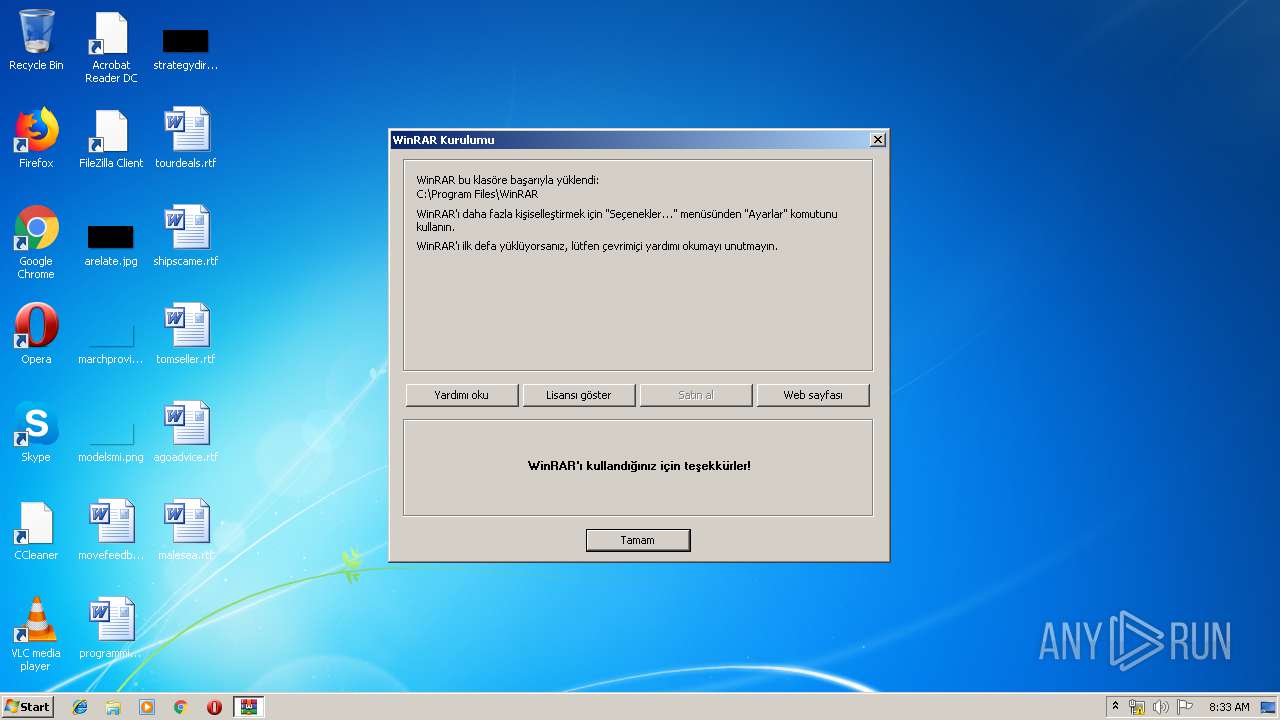
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 07:32:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 872ABEBDFC932A52ED277E452F706971 |
| SHA1: | D768B9E77782BBDC671A81D8FED00AA8A5D7EAC9 |
| SHA256: | C94B26E7842B6726BB7C592F687F38F2DA83453A0979A319DBF83A7C040AD8B2 |
| SSDEEP: | 49152:LxuBfJXAtJYUo3WddOXZYVNkYbNskNfe12PZVzTg6/UdaqnA2RlS0PIkje:UBfKGGdd3VRB/e12PZVzTg6/UdVNcyK |
MALICIOUS
Application was dropped or rewritten from another process
- uninstall.exe (PID: 2648)
- WinRAR.exe (PID: 2176)
- WinRAR.exe (PID: 1208)
SUSPICIOUS
Reads internet explorer settings
- 872abebdfc932a52ed277e452f706971-wrar561tr.exe (PID: 3880)
- hh.exe (PID: 2484)
Modifies the open verb of a shell class
- uninstall.exe (PID: 2648)
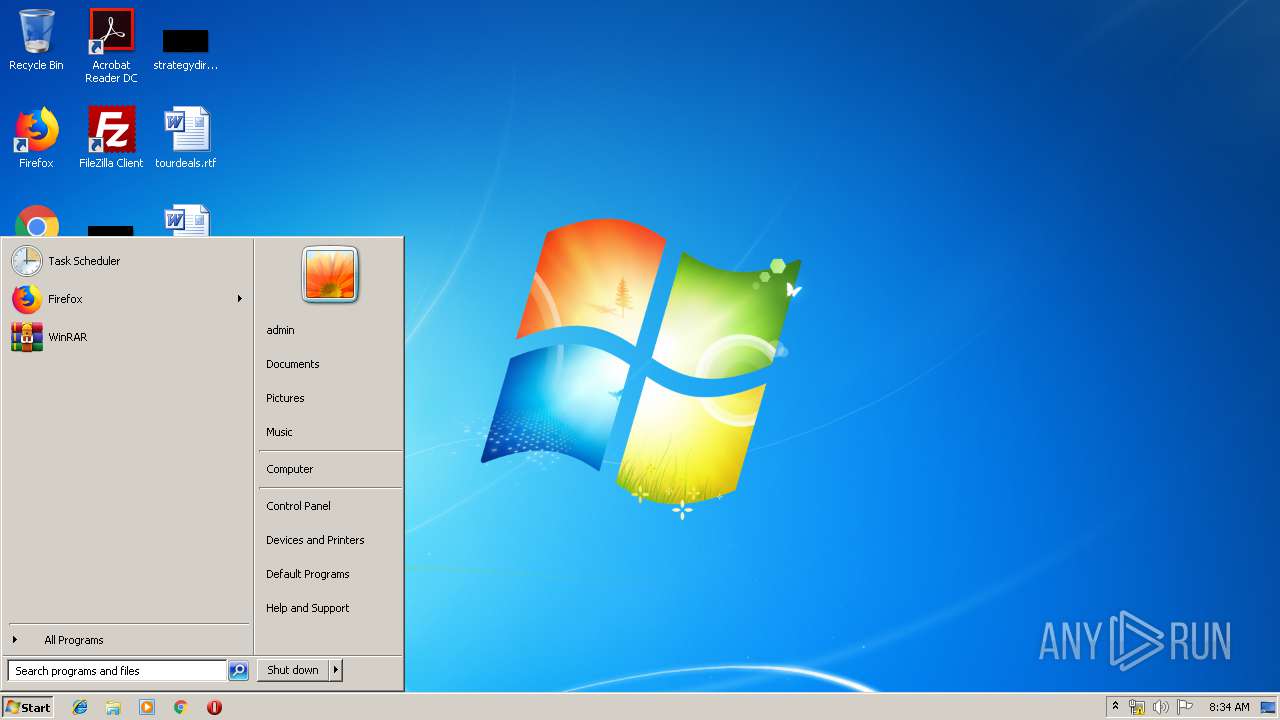
Creates COM task schedule object
- uninstall.exe (PID: 2648)
Creates a software uninstall entry
- uninstall.exe (PID: 2648)
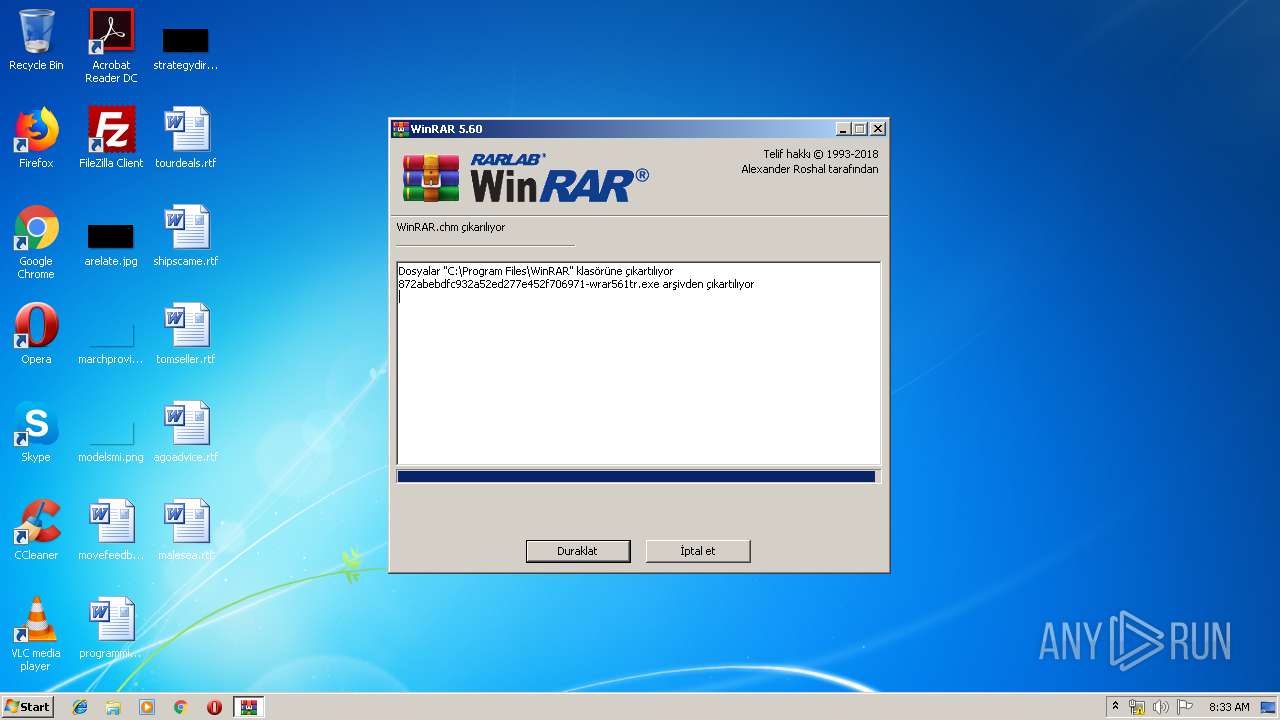
Executable content was dropped or overwritten
- 872abebdfc932a52ed277e452f706971-wrar561tr.exe (PID: 3880)
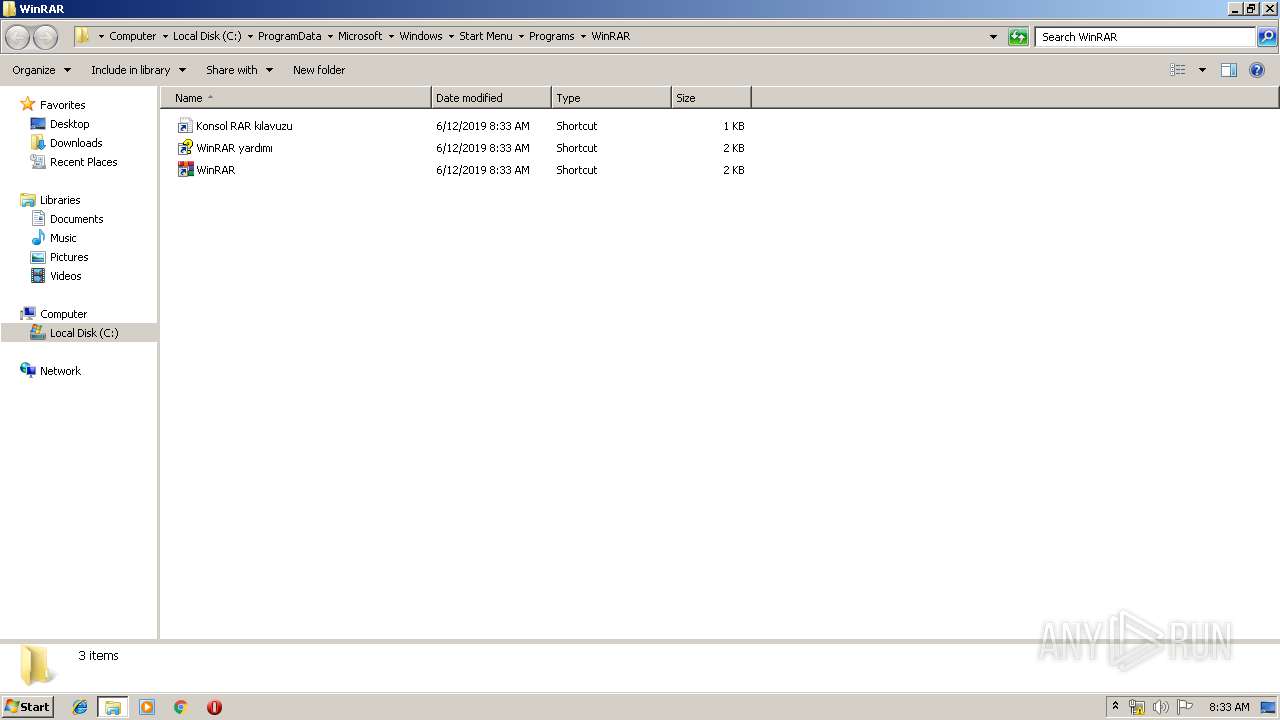
Creates files in the program directory
- 872abebdfc932a52ed277e452f706971-wrar561tr.exe (PID: 3880)
- uninstall.exe (PID: 2648)
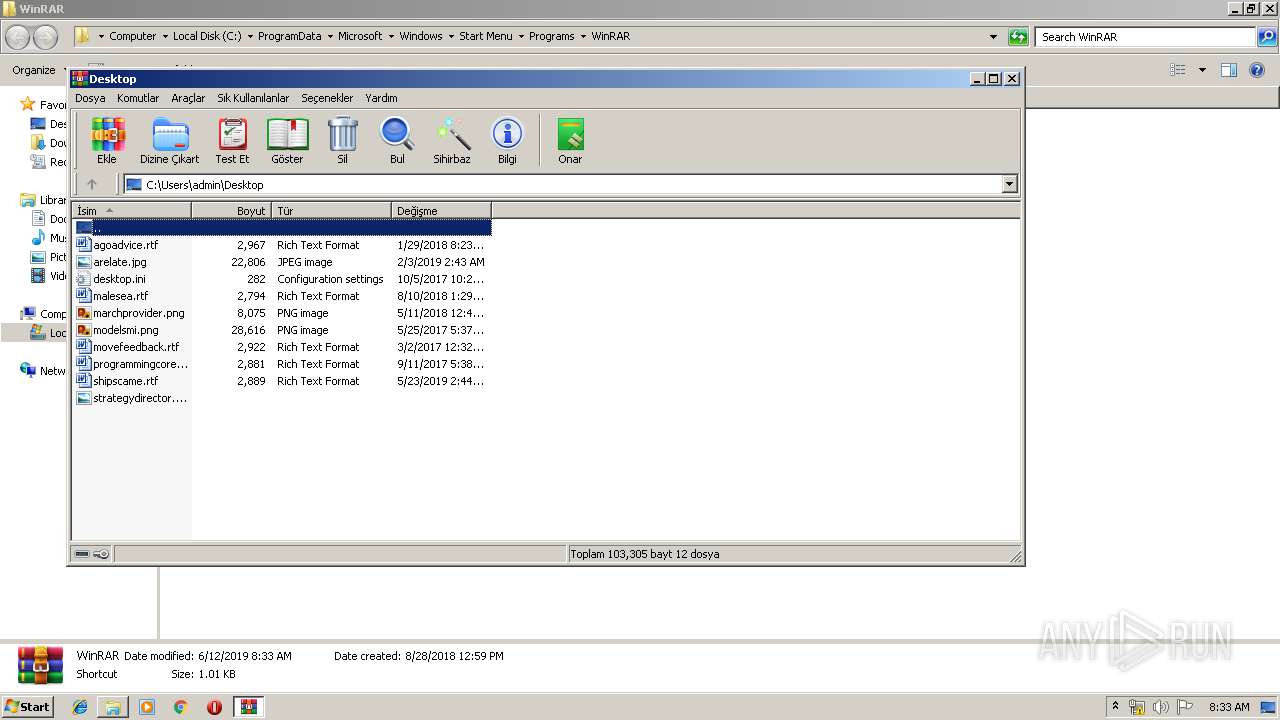
Creates files in the user directory
- uninstall.exe (PID: 2648)
INFO
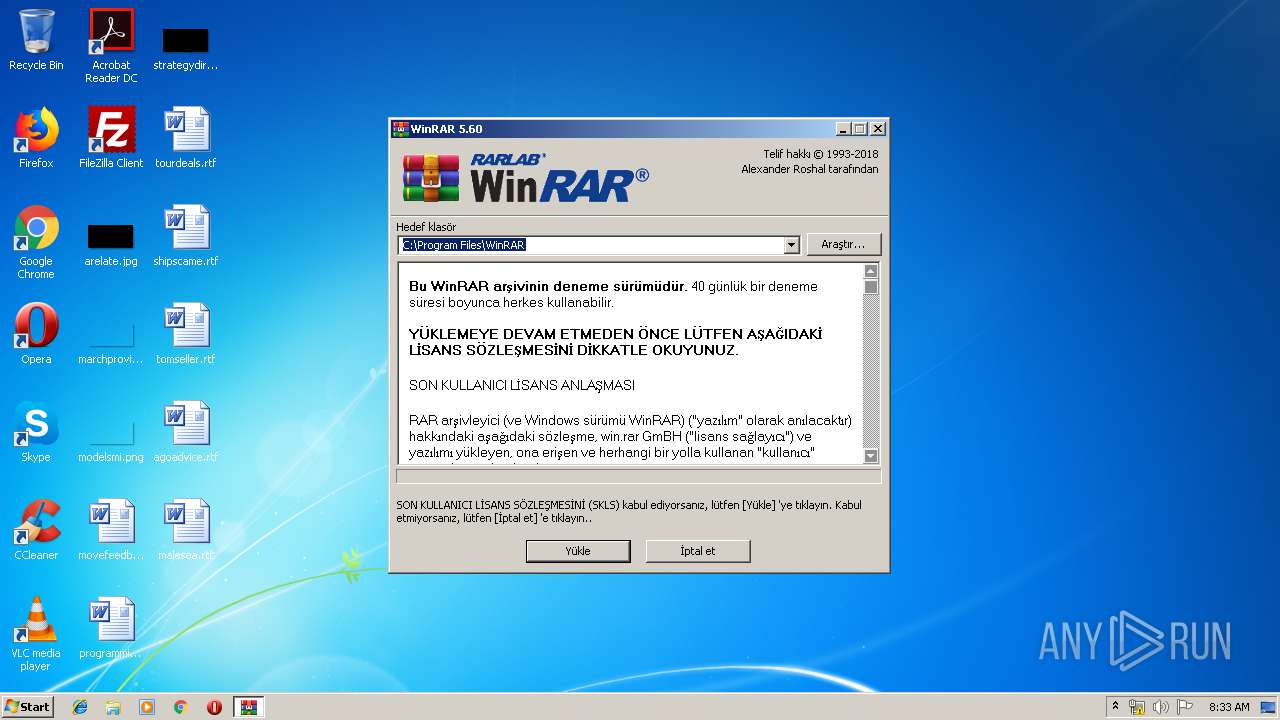
Manual execution by user
- WinRAR.exe (PID: 2176)
- hh.exe (PID: 2484)
- WinRAR.exe (PID: 1208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:30 20:01:57+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 189440 |
| InitializedDataSize: | 304128 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cea9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.61.0.0 |
| ProductVersionNumber: | 5.61.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| ProductName: | WinRAR |
| CompanyName: | Alexander Roshal |
| FileDescription: | WinRAR archiver |
| FileVersion: | 5.61.0 |
| ProductVersion: | 5.61.0 |
| InternalName: | WinRAR |
| LegalCopyright: | Copyright © Alexander Roshal 1993-2018 |
| OriginalFileName: | WinRAR.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Sep-2018 18:01:57 |
| Detected languages: |
|
| Debug artifacts: |
|
| ProductName: | WinRAR |
| CompanyName: | Alexander Roshal |
| FileDescription: | WinRAR archiver |
| FileVersion: | 5.61.0 |
| ProductVersion: | 5.61.0 |
| InternalName: | WinRAR |
| LegalCopyright: | Copyright © Alexander Roshal 1993-2018 |
| OriginalFilename: | WinRAR.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 30-Sep-2018 18:01:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E254 | 0x0002E400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69532 |
.rdata | 0x00030000 | 0x000099DC | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16021 |
.data | 0x0003A000 | 0x00020388 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.19639 |
.gfids | 0x0005B000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.07073 |
.rsrc | 0x0005C000 | 0x0001F000 | 0x0001E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.66682 |
.reloc | 0x0007B000 | 0x00001F88 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.66229 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26297 | 1872 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.03536 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24591 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.57239 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 6.35851 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.9392 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.11482 | 376 | UNKNOWN | English - United States | RT_STRING |
8 | 3.14988 | 436 | UNKNOWN | English - United States | RT_STRING |
9 | 3.16863 | 434 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
gdiplus.dll |
Total processes
43
Monitored processes
6
Malicious processes
3
Suspicious processes
1
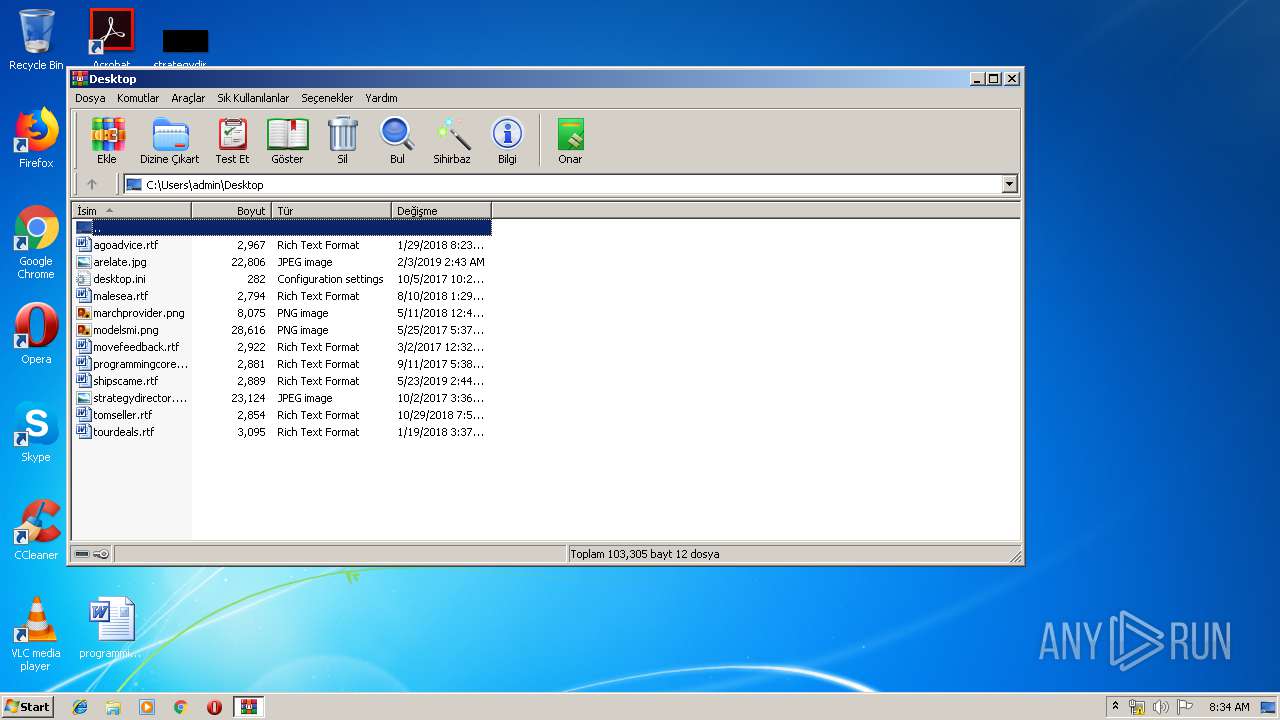
Behavior graph
Click at the process to see the details
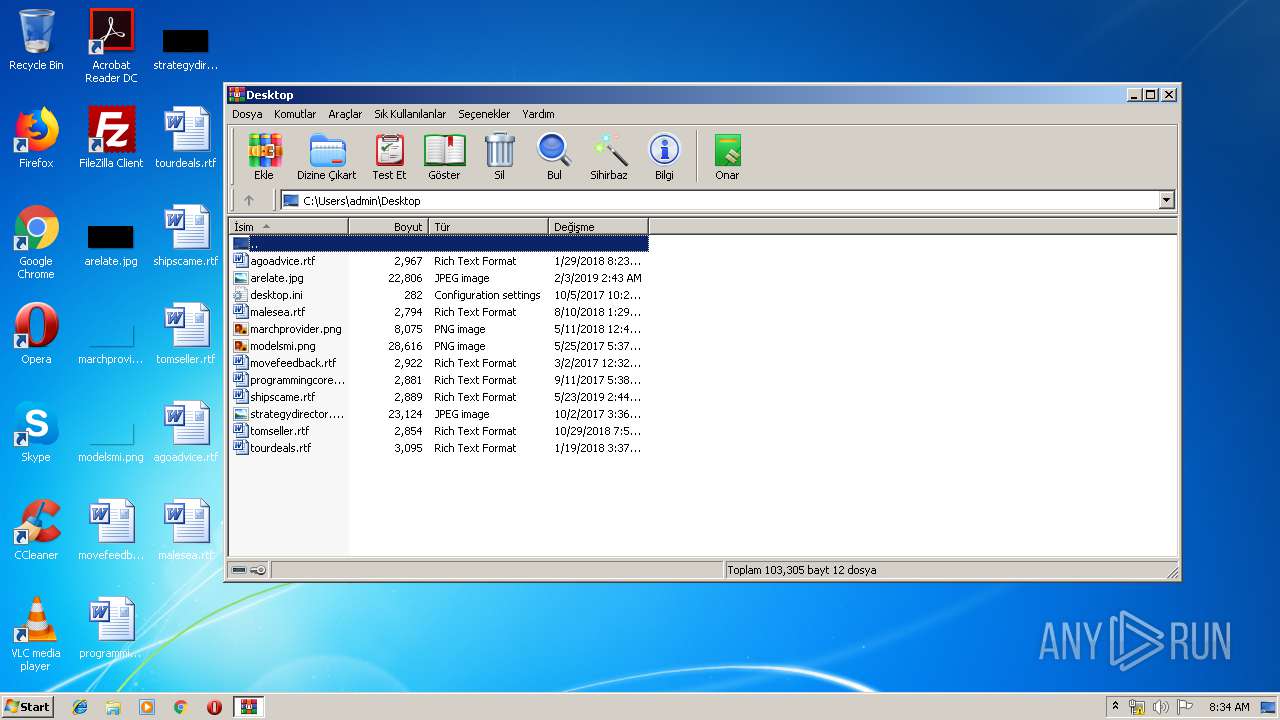
Process information
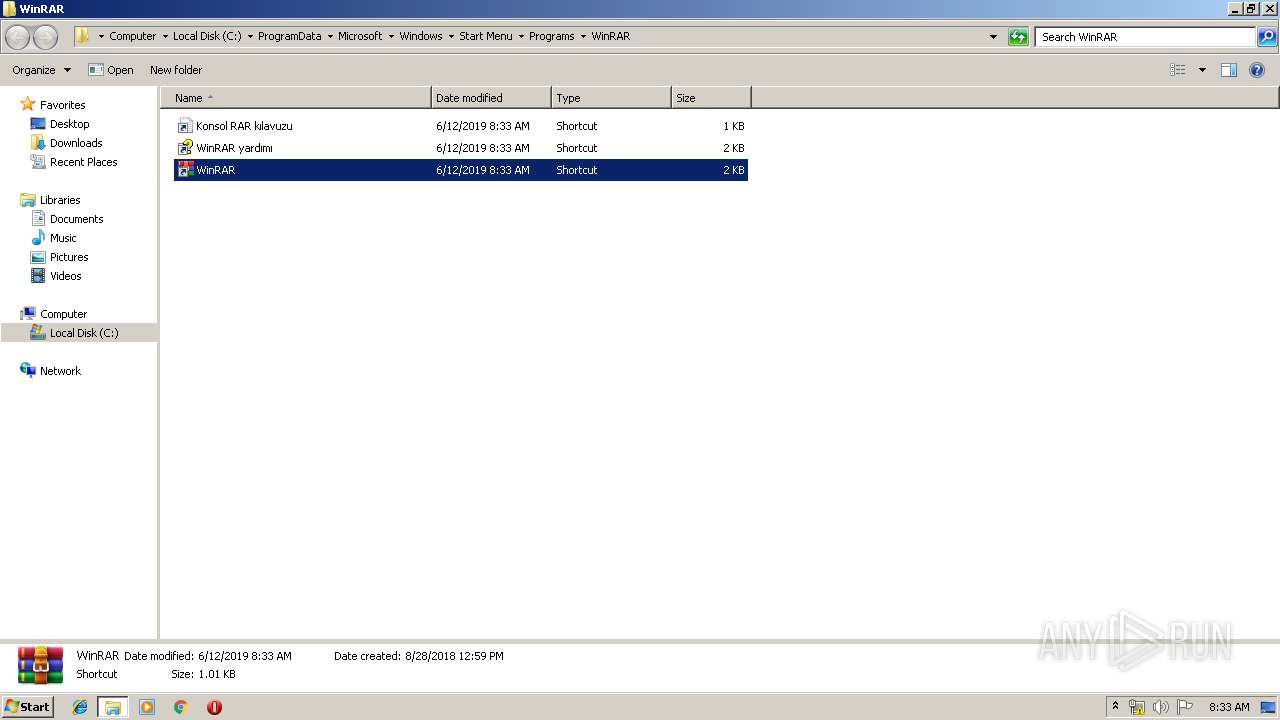
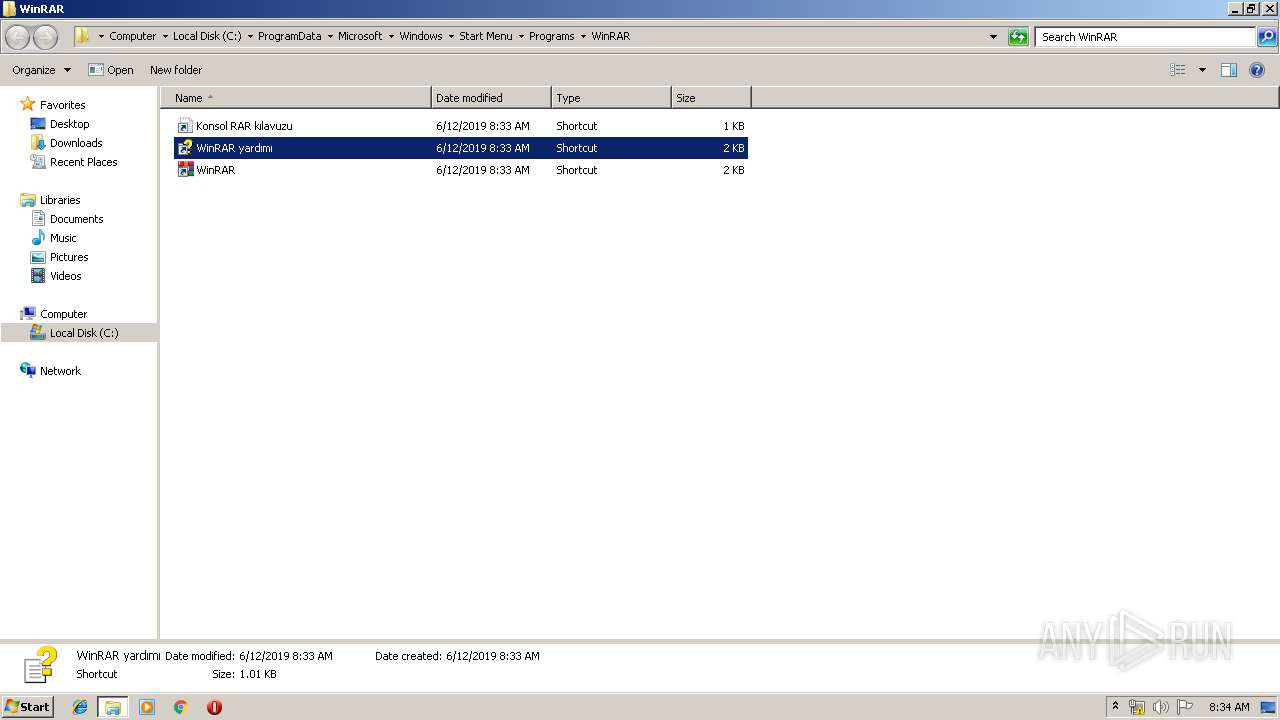
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\Program Files\WinRAR\WinRAR.exe" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.61.0 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\WinRAR\WinRAR.exe" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.61.0 Modules
| |||||||||||||||
| 2484 | "C:\Windows\hh.exe" C:\Program Files\WinRAR\WinRAR.chm | C:\Windows\hh.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2648 | "C:\Program Files\WinRAR\uninstall.exe" /setup | C:\Program Files\WinRAR\uninstall.exe | — | 872abebdfc932a52ed277e452f706971-wrar561tr.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Uninstall WinRAR Exit code: 0 Version: 5.61.0 Modules
| |||||||||||||||
| 3448 | "C:\Users\admin\AppData\Local\Temp\872abebdfc932a52ed277e452f706971-wrar561tr.exe" | C:\Users\admin\AppData\Local\Temp\872abebdfc932a52ed277e452f706971-wrar561tr.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 3221226540 Version: 5.61.0 Modules
| |||||||||||||||
| 3880 | "C:\Users\admin\AppData\Local\Temp\872abebdfc932a52ed277e452f706971-wrar561tr.exe" | C:\Users\admin\AppData\Local\Temp\872abebdfc932a52ed277e452f706971-wrar561tr.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR archiver Exit code: 0 Version: 5.61.0 Modules
| |||||||||||||||
Total events
1 094
Read events
915
Write events
177
Delete events
2
Modification events
| (PID) Process: | (3880) 872abebdfc932a52ed277e452f706971-wrar561tr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3880) 872abebdfc932a52ed277e452f706971-wrar561tr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3880) 872abebdfc932a52ed277e452f706971-wrar561tr.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | C%%Program Files%WinRAR |
Value: C:\Program Files\WinRAR | |||
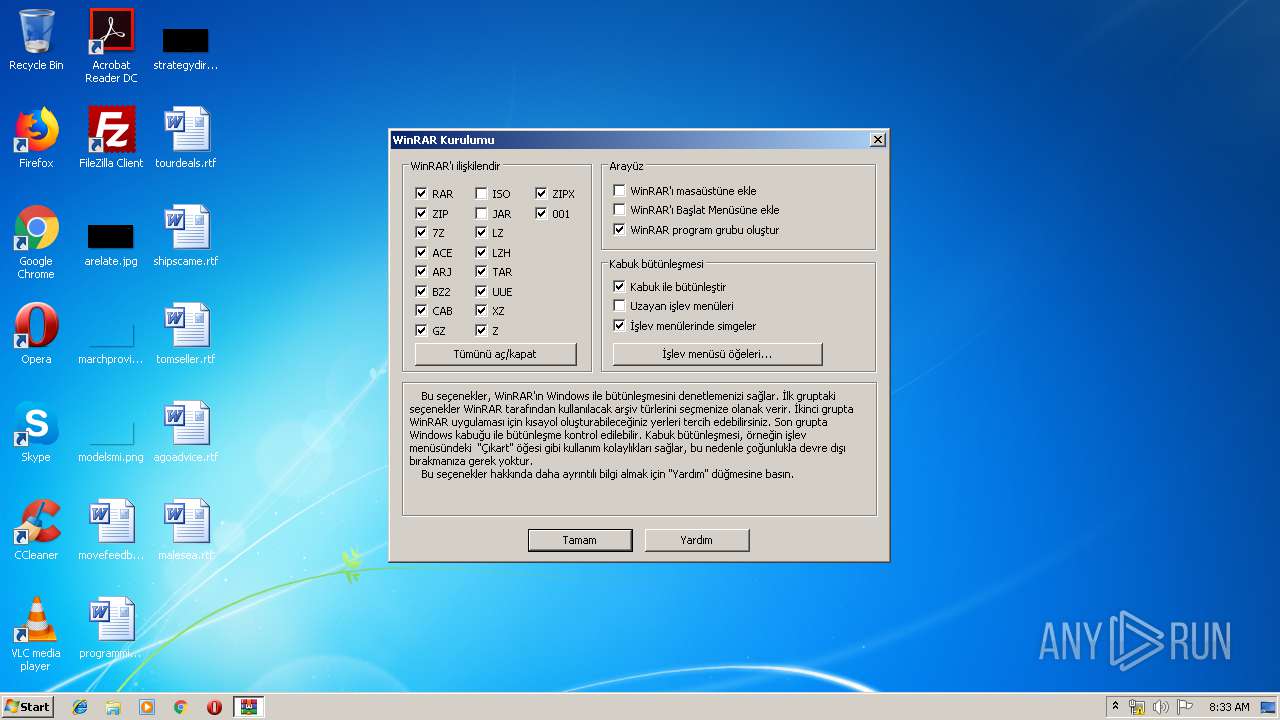
| (PID) Process: | (2648) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Setup\.rar |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (2648) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Setup\.zip |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (2648) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Setup\.cab |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (2648) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Setup\.arj |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (2648) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Setup\.lz |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (2648) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Setup\.lzh |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (2648) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Setup\.ace |
| Operation: | write | Name: | Set |
Value: 1 | |||
Executable files
11
Suspicious files
1
Text files
12
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | 872abebdfc932a52ed277e452f706971-wrar561tr.exe | C:\Program Files\WinRAR\WhatsNew.txt | text | |
MD5:— | SHA256:— | |||
| 3880 | 872abebdfc932a52ed277e452f706971-wrar561tr.exe | C:\Program Files\WinRAR\License.txt | text | |
MD5:715B33385DEF389971A1C74E755A1276 | SHA256:1A96719F0B4244F02C3AD34EB8E82262D604646230EF84CD5E873133CB8CE8F5 | |||
| 3880 | 872abebdfc932a52ed277e452f706971-wrar561tr.exe | C:\Program Files\WinRAR\ReadMe.txt | text | |
MD5:D1996129F4509BB905999C1FE9C1E846 | SHA256:AADB1C5C21E526F0BADC26B155BEF26660CFA62515A11E5CE56CA37C297C6062 | |||
| 3880 | 872abebdfc932a52ed277e452f706971-wrar561tr.exe | C:\Program Files\WinRAR\Rar.txt | text | |
MD5:0FB2565FF4342ACFD592477C504B8EF8 | SHA256:BE15EE8511EF506ED2022C0046C5EA97FB3816C5CBBADE9DF00BAE68550F0206 | |||
| 3880 | 872abebdfc932a52ed277e452f706971-wrar561tr.exe | C:\Program Files\WinRAR\Order.htm | html | |
MD5:B245C18AEC29D07673AB44C5AA7AB454 | SHA256:AF9793B58528839021D59AAC2DFDA28E578FADBCD8E315C2F601CC73A4E0FFC4 | |||
| 3880 | 872abebdfc932a52ed277e452f706971-wrar561tr.exe | C:\Program Files\WinRAR\Rar.exe | executable | |
MD5:33A75BFB1B9038899B9BA5E2A06D5D57 | SHA256:F210868E696B4219F213BC4FE8652380570F60B6F4D5B440F6CF786ADF301778 | |||
| 3880 | 872abebdfc932a52ed277e452f706971-wrar561tr.exe | C:\Program Files\WinRAR\Uninstall.lst | text | |
MD5:A6532D31EE969112CB1B9F43091B2E28 | SHA256:9F414240F7E1BDE5ECCFC439B882D61F2B2CC6CD8B52F3C442F4074BC8660DBA | |||
| 3880 | 872abebdfc932a52ed277e452f706971-wrar561tr.exe | C:\Program Files\WinRAR\RarFiles.lst | text | |
MD5:08EA0309D72A874C182F08CBF9DA2CC3 | SHA256:12787F8204EEDB0B8BDABF5D68D557334FDDB2D70B46E1422510713DDA5E6A01 | |||
| 3880 | 872abebdfc932a52ed277e452f706971-wrar561tr.exe | C:\Program Files\WinRAR\UnRAR.exe | executable | |
MD5:99F5F4642140F01CDAE3B50395826E7D | SHA256:A2EE3D312C4D92346D47C35346276DB10B525452E88C11142BD2EA72A9F035F5 | |||
| 3880 | 872abebdfc932a52ed277e452f706971-wrar561tr.exe | C:\Program Files\WinRAR\Uninstall.exe | executable | |
MD5:2ACA14CC6303CD00028D46F3665CF704 | SHA256:D39A3965755875FF0063501E820CBDAEE98671765A51B986D9DA371A68AA9404 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report