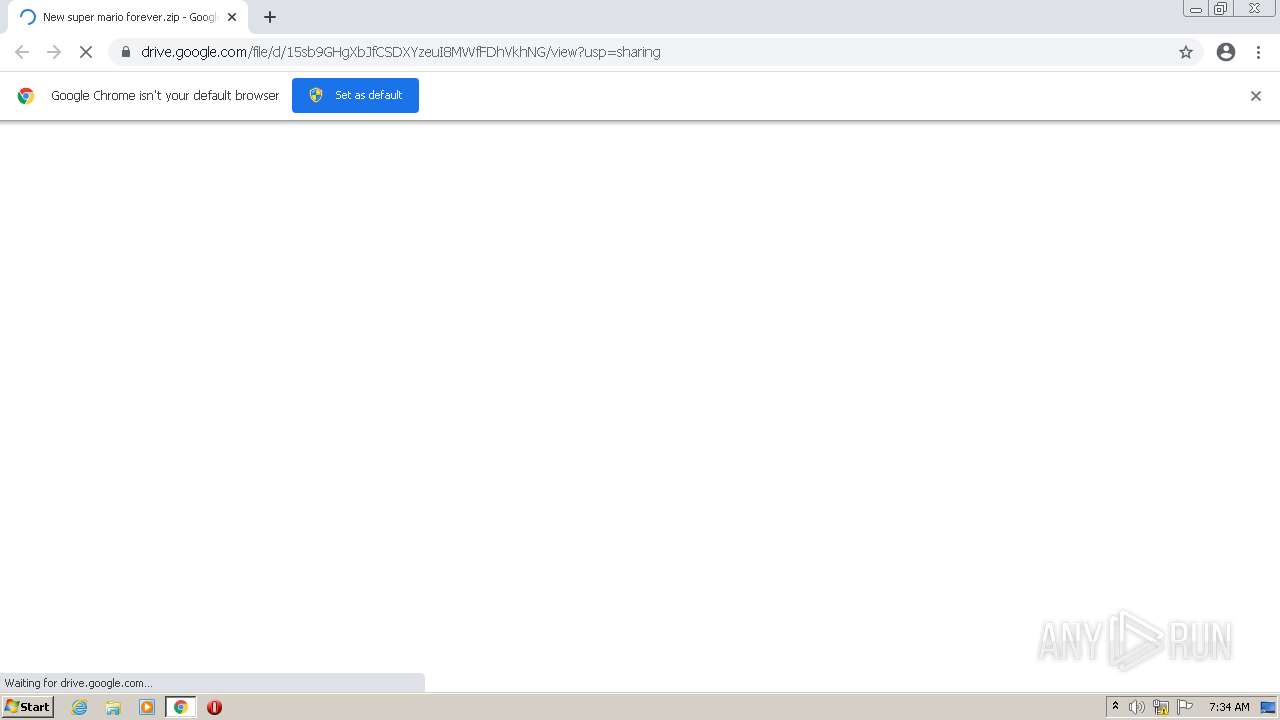
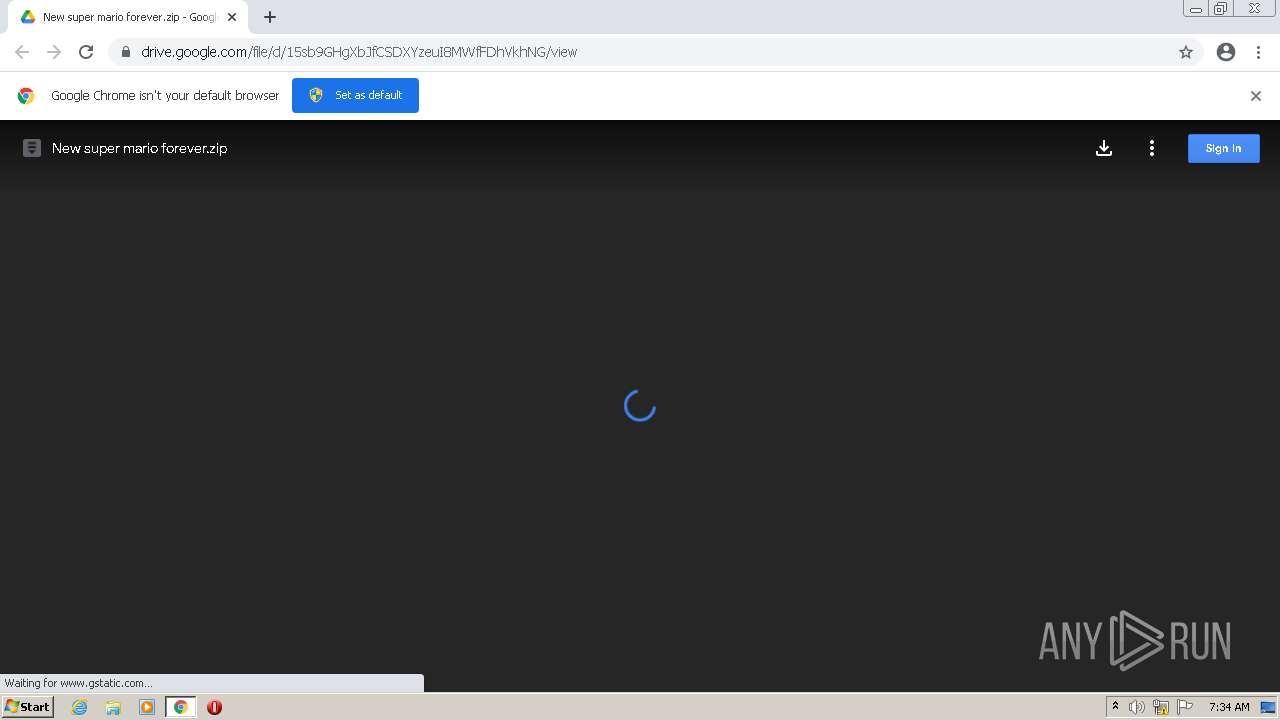
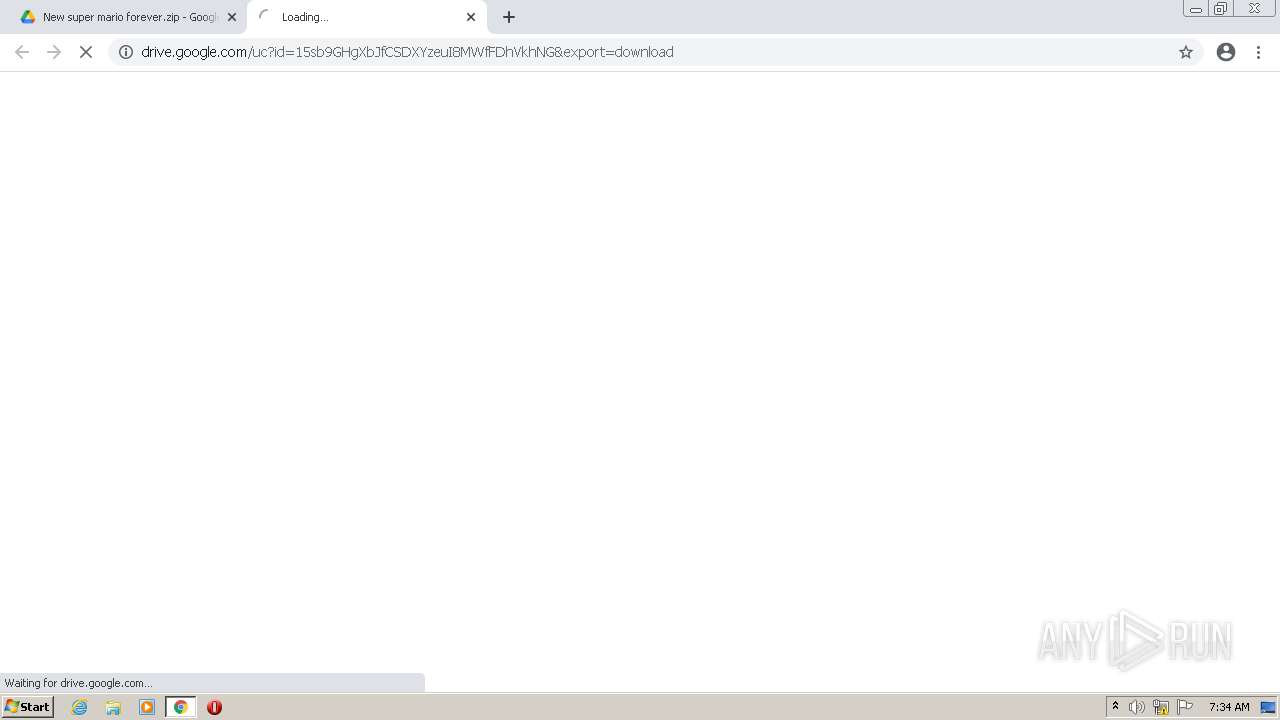
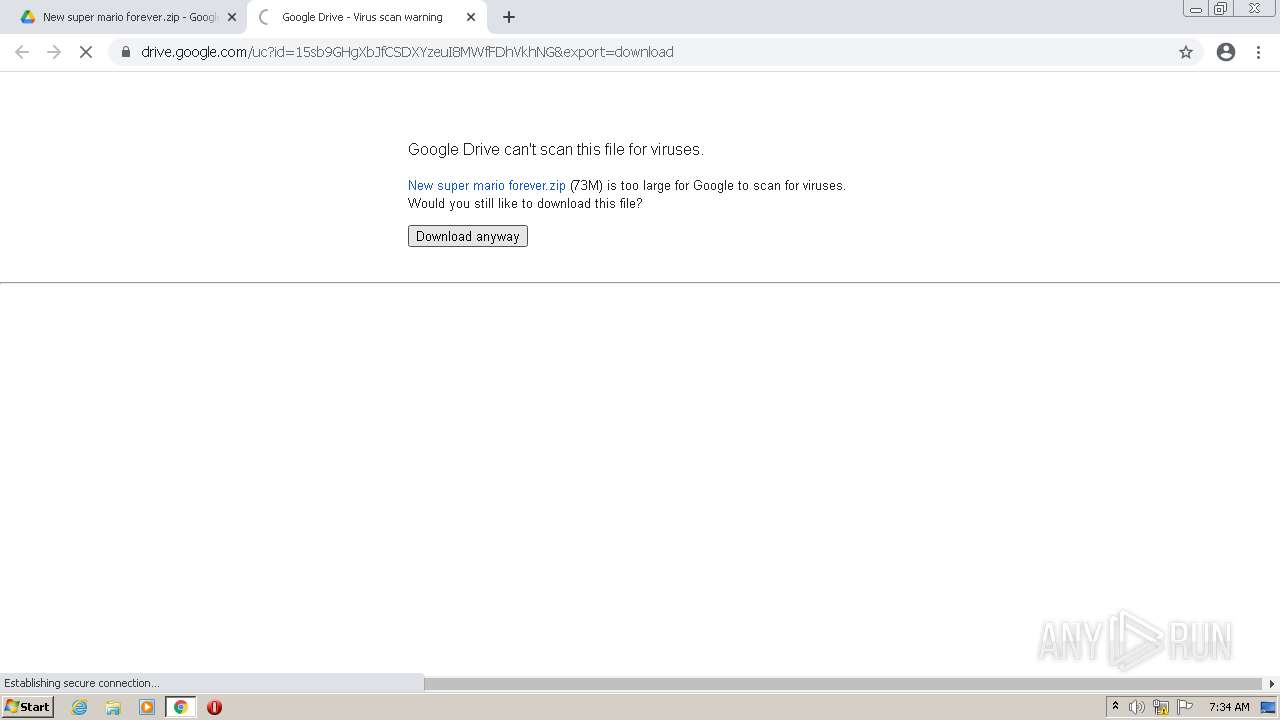
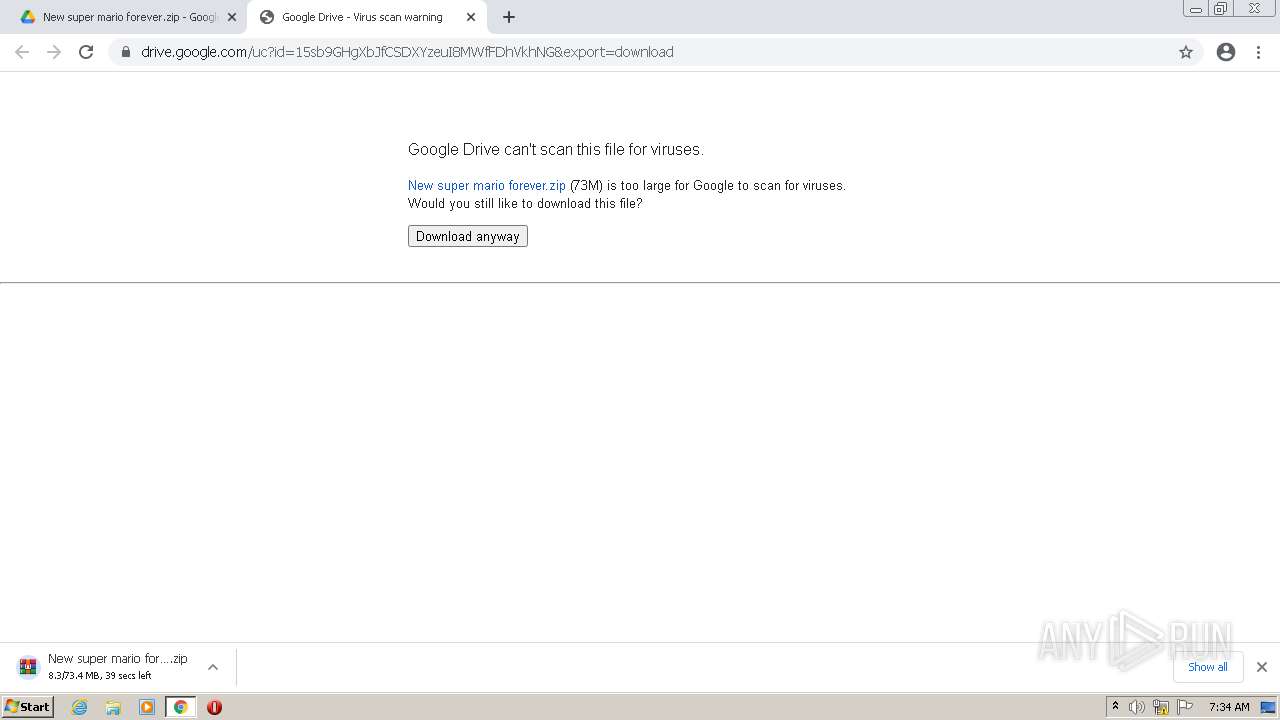
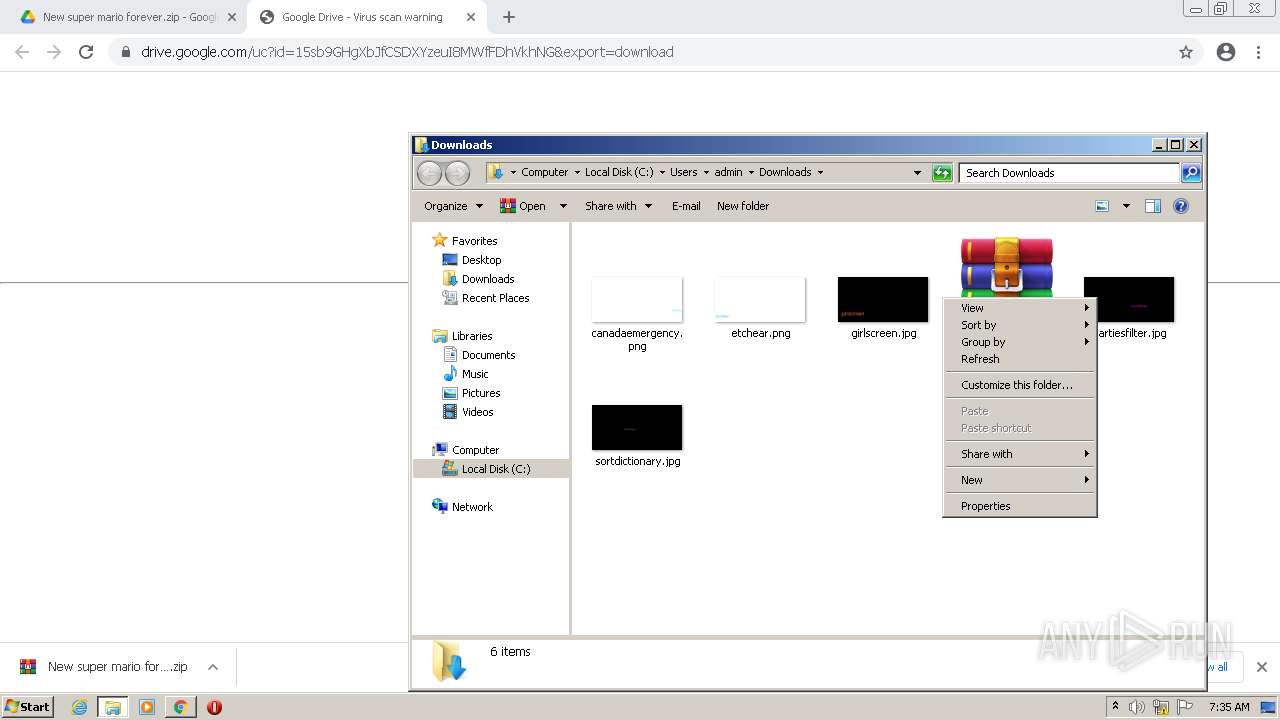
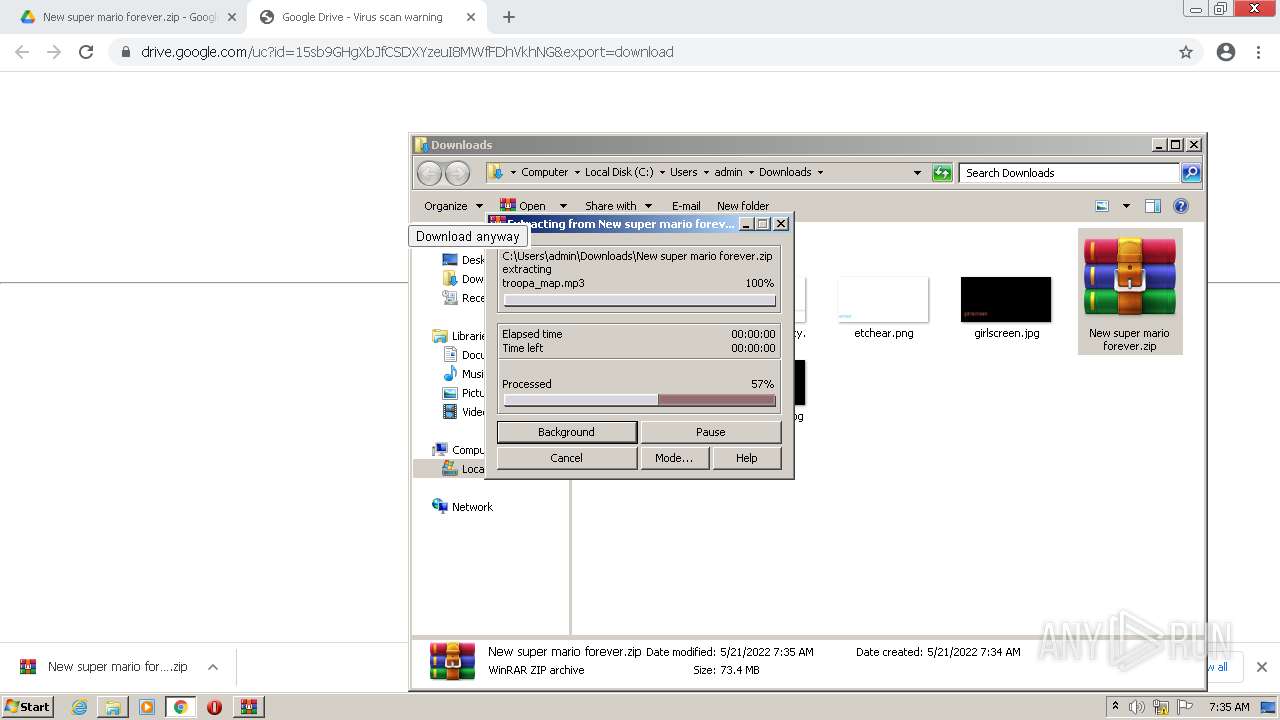
| URL: | https://drive.google.com/file/d/15sb9GHgXbJfCSDXYzeuI8MWfFDhVkhNG/view?usp=sharing |
| Full analysis: | https://app.any.run/tasks/36d26a49-6adc-475d-a43f-0fceadf61420 |
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | May 21, 2022, 06:34:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B6A2DF96BC54627E5714BC1D9E3C2944 |
| SHA1: | 24E5CDF1A93D91070F0653BCF20590AB0D127314 |
| SHA256: | C9478166058F8881EF805008E485D2BA129EA8BCF483824E1226D62830B0EDE4 |
| SSDEEP: | 3:N8PMMtZJulotHTMd3ihMApJZC:2A73iL7ZC |
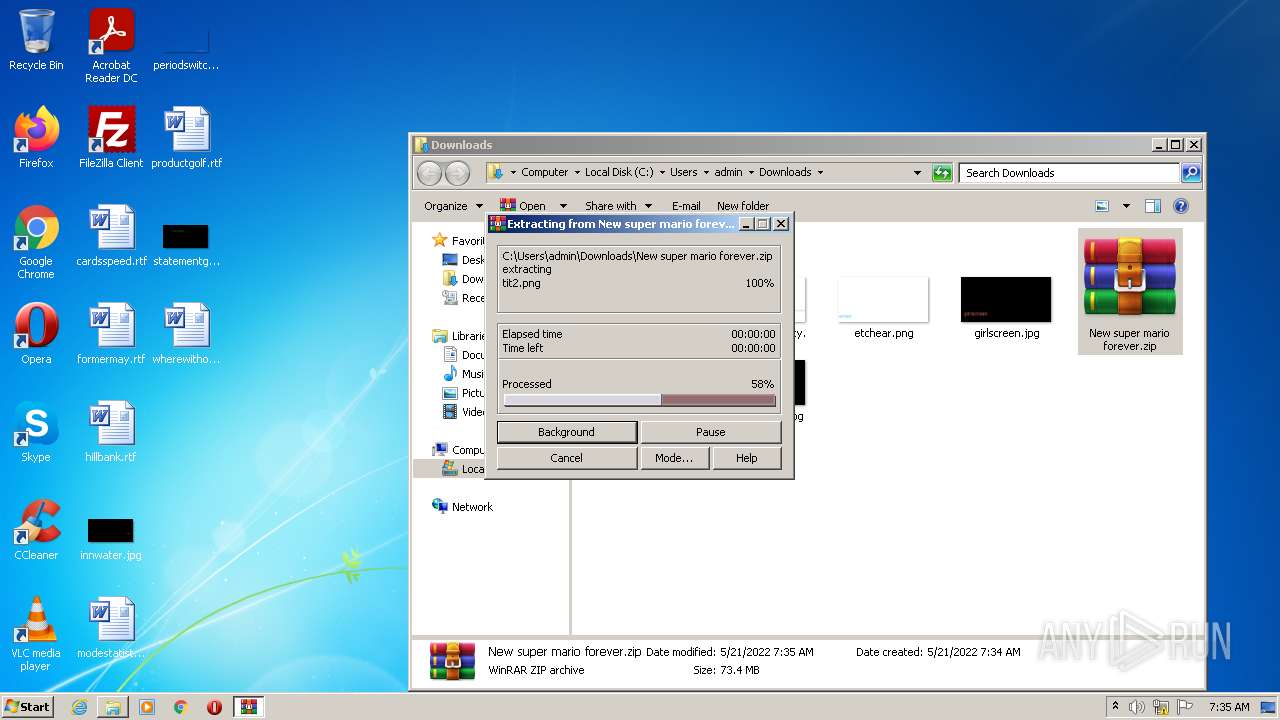
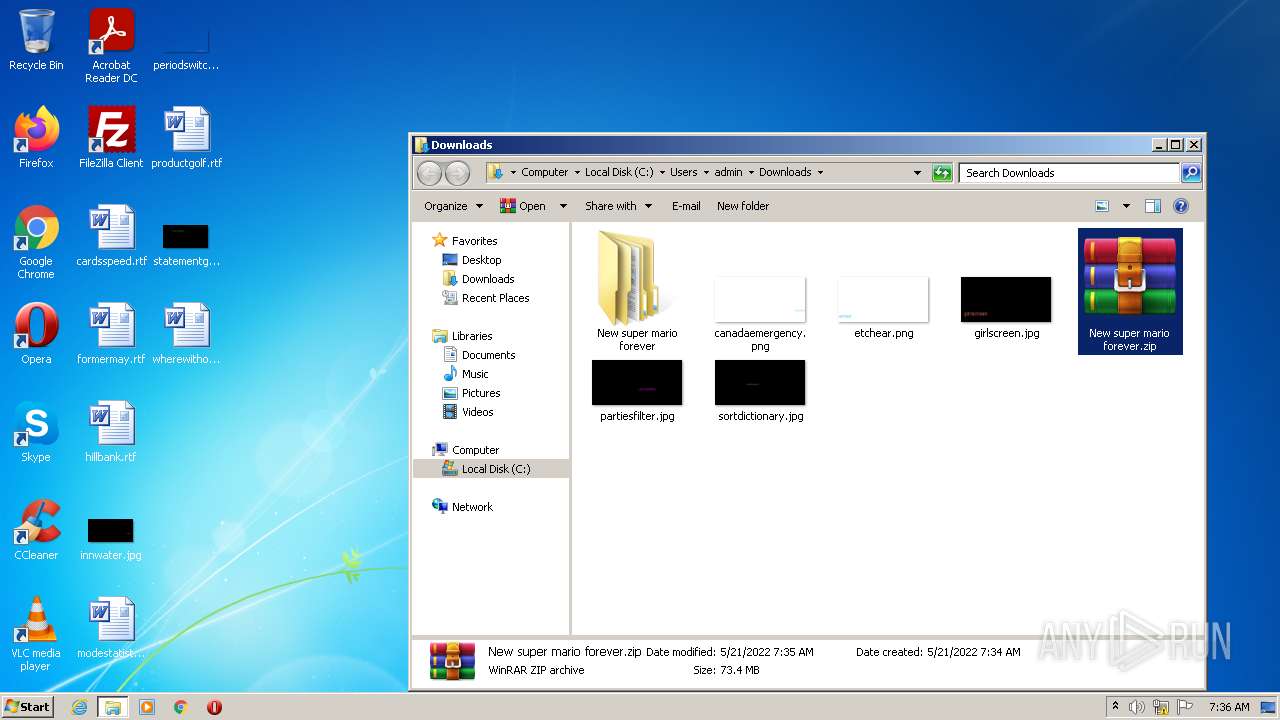
MALICIOUS
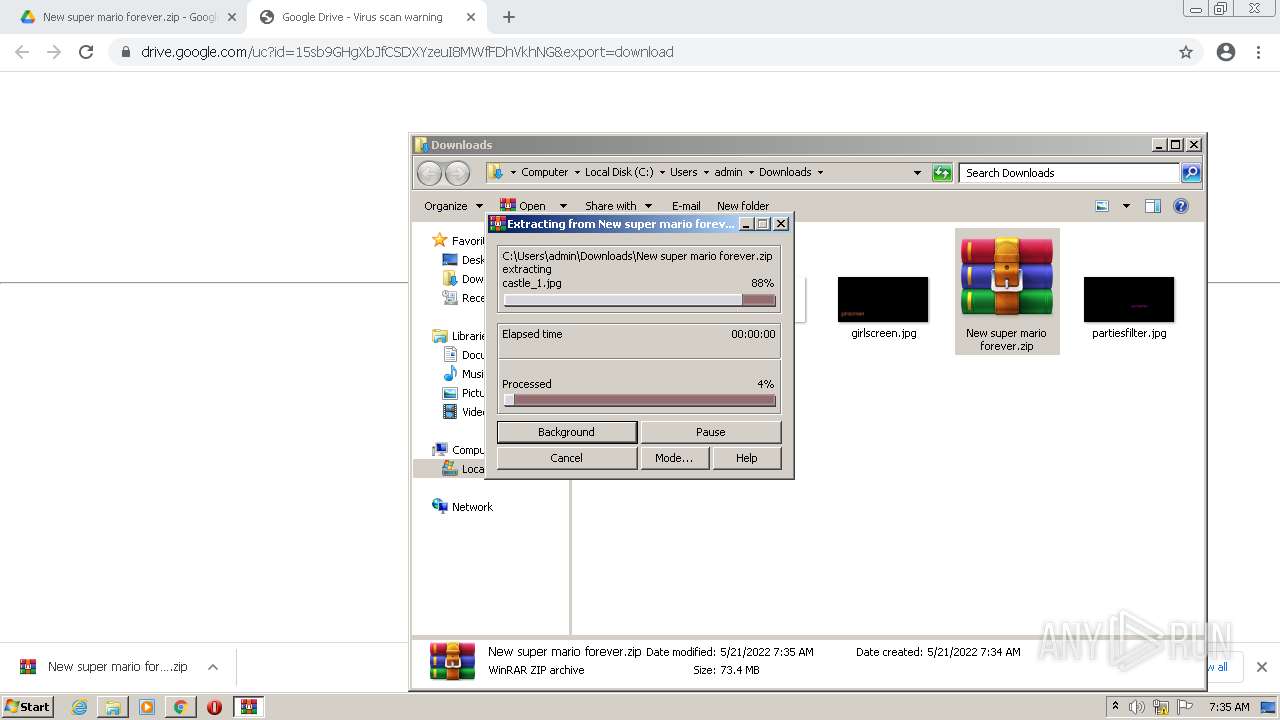
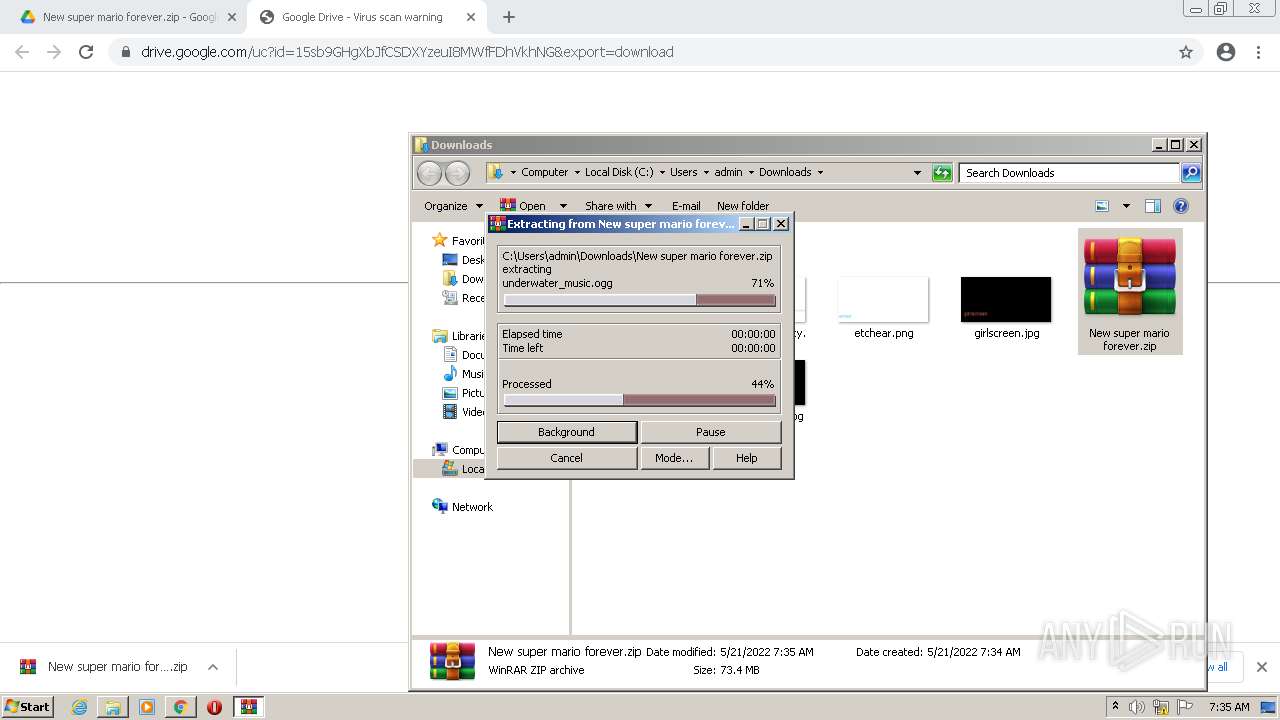
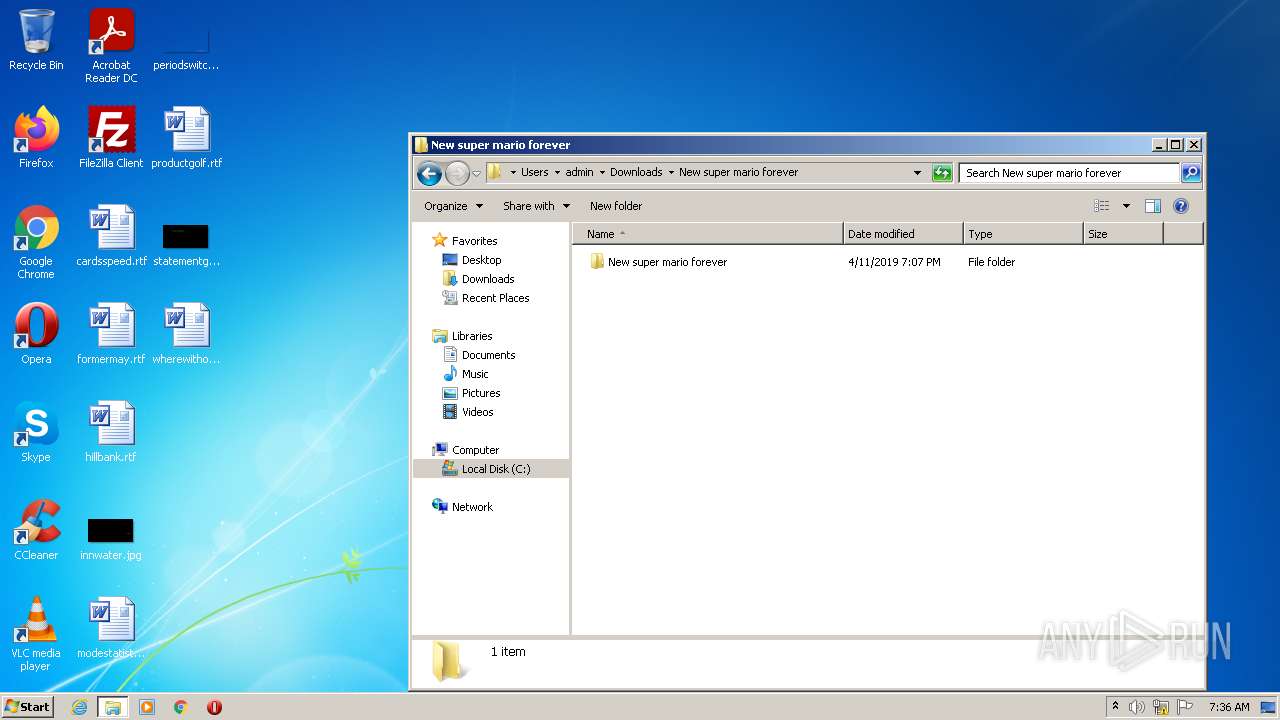
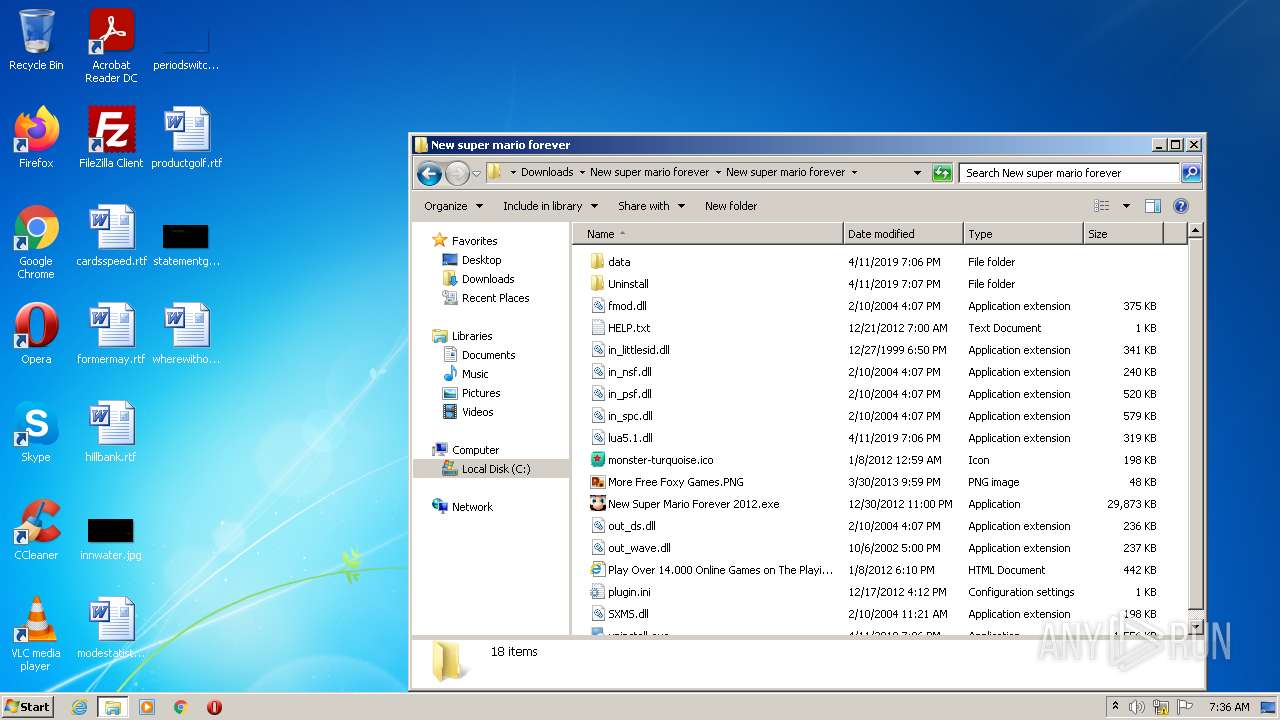
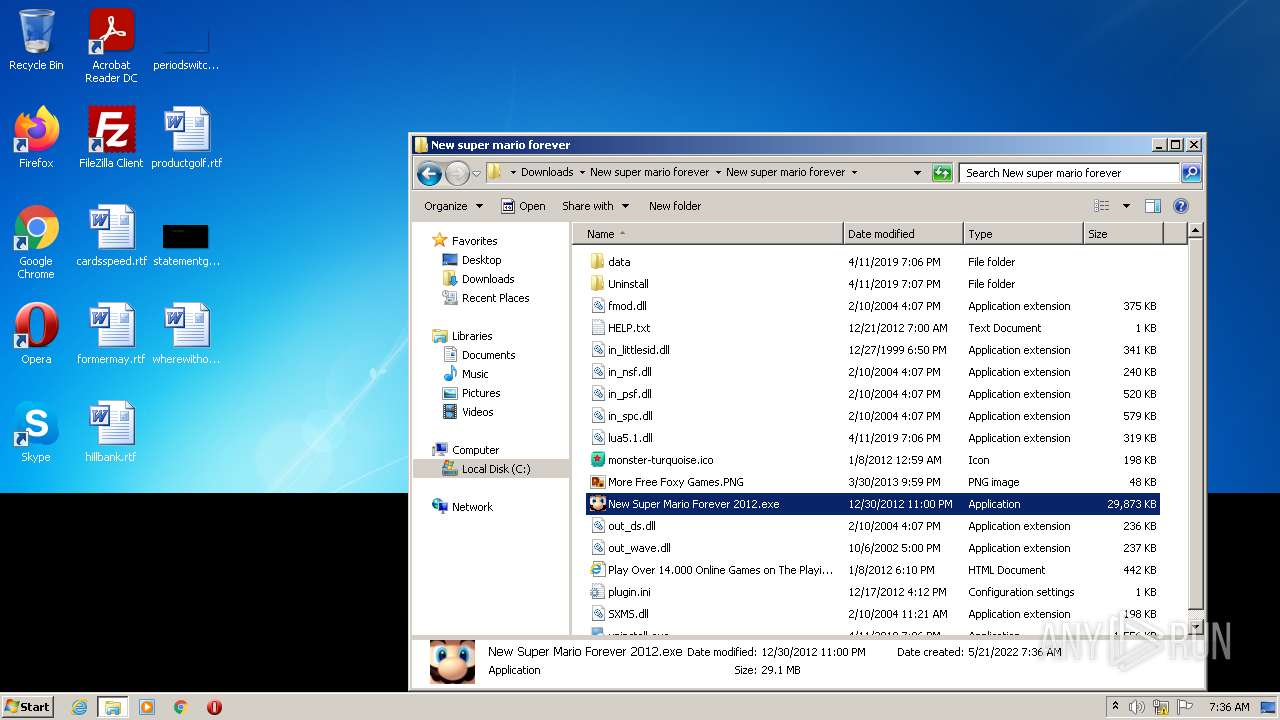
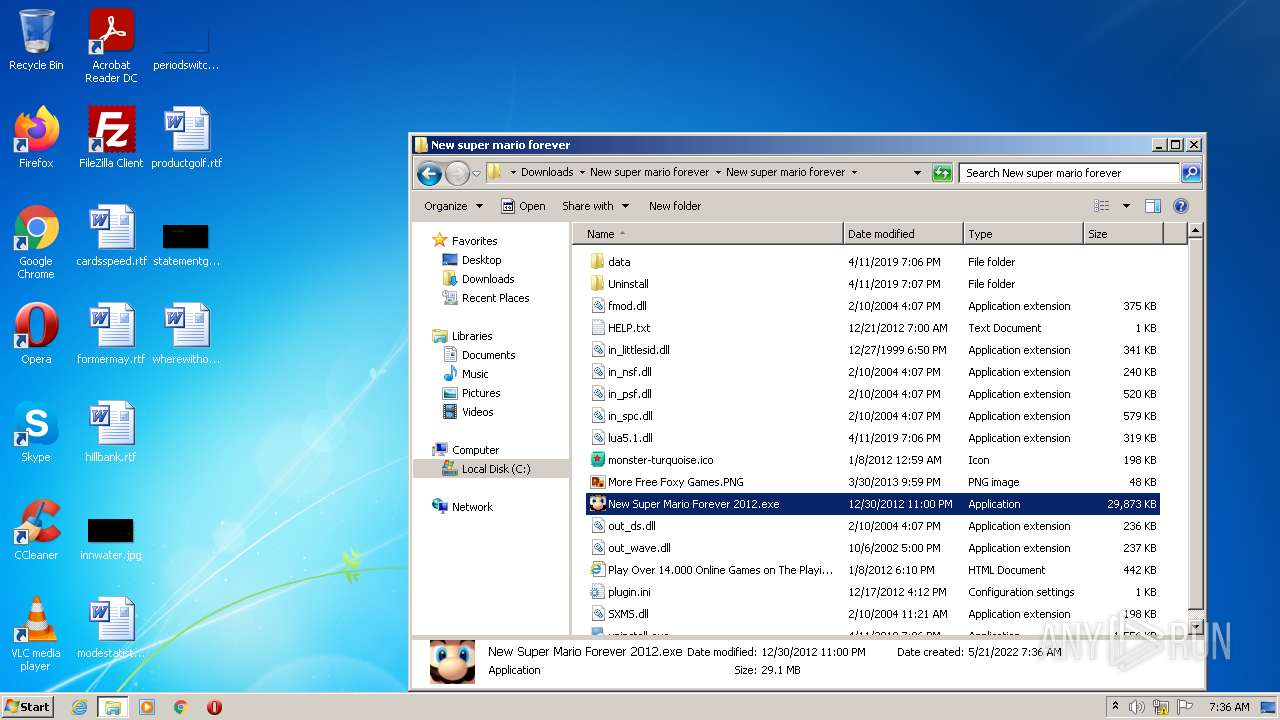
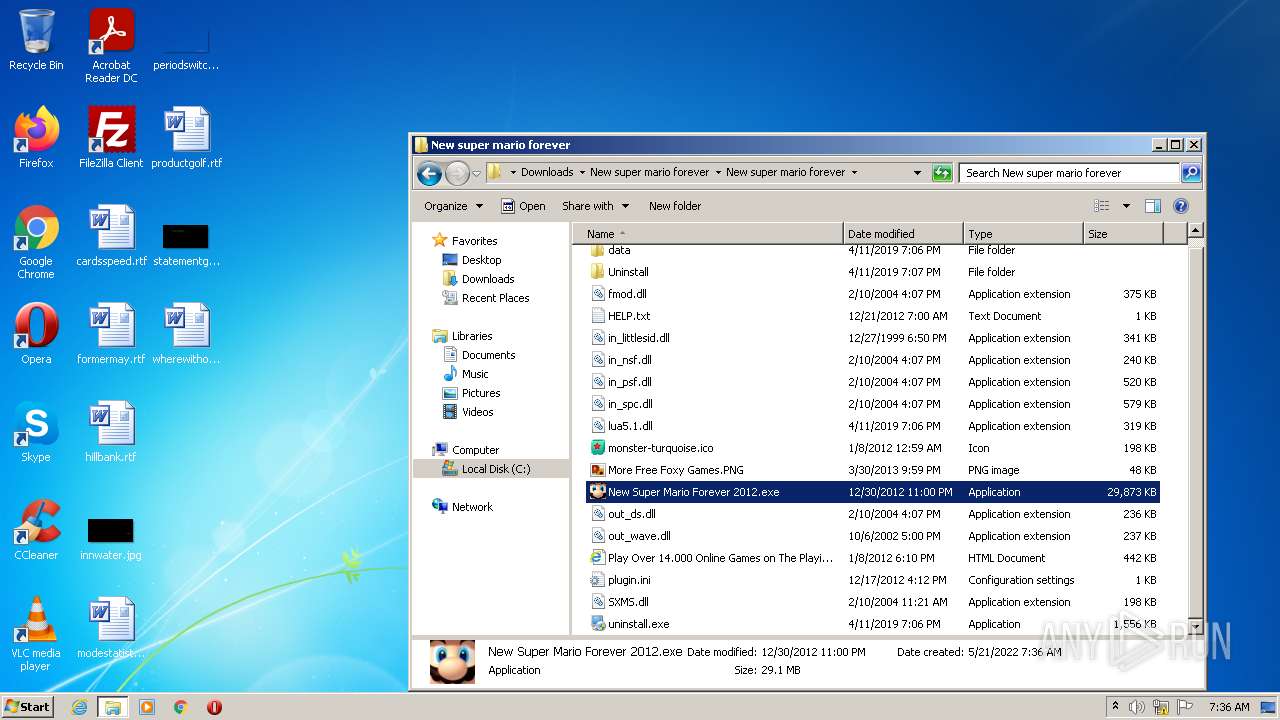
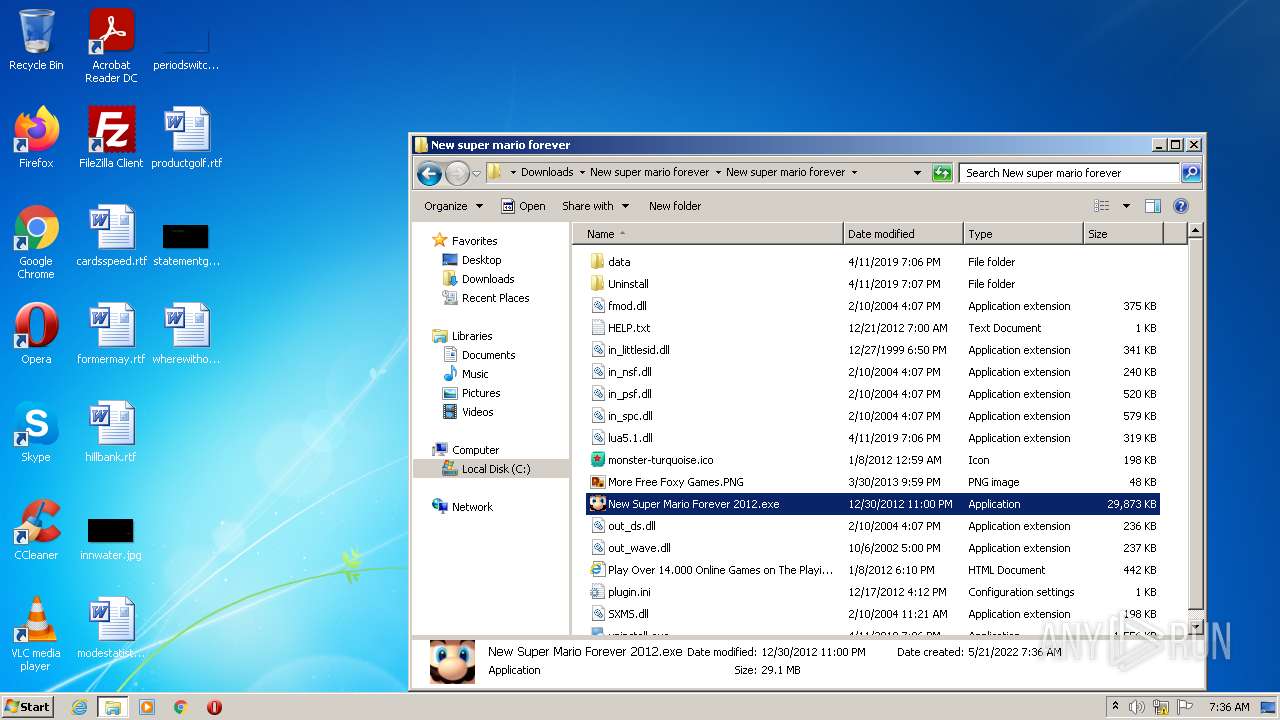
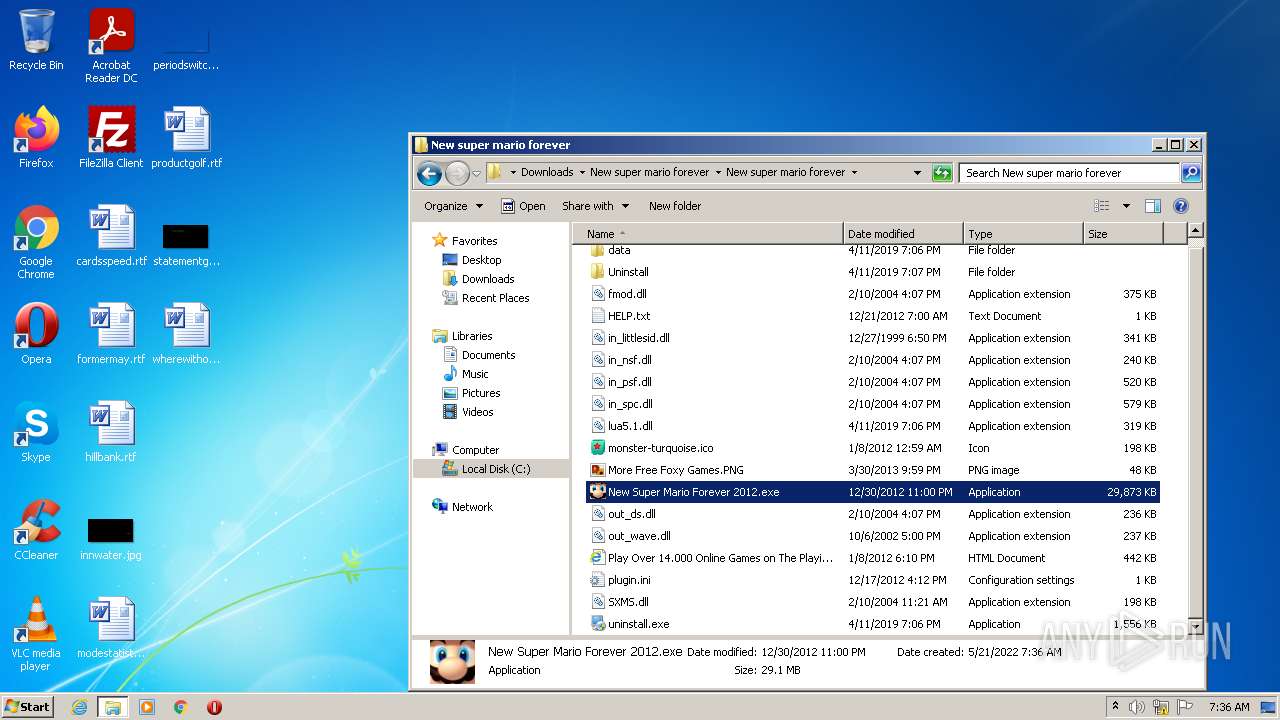
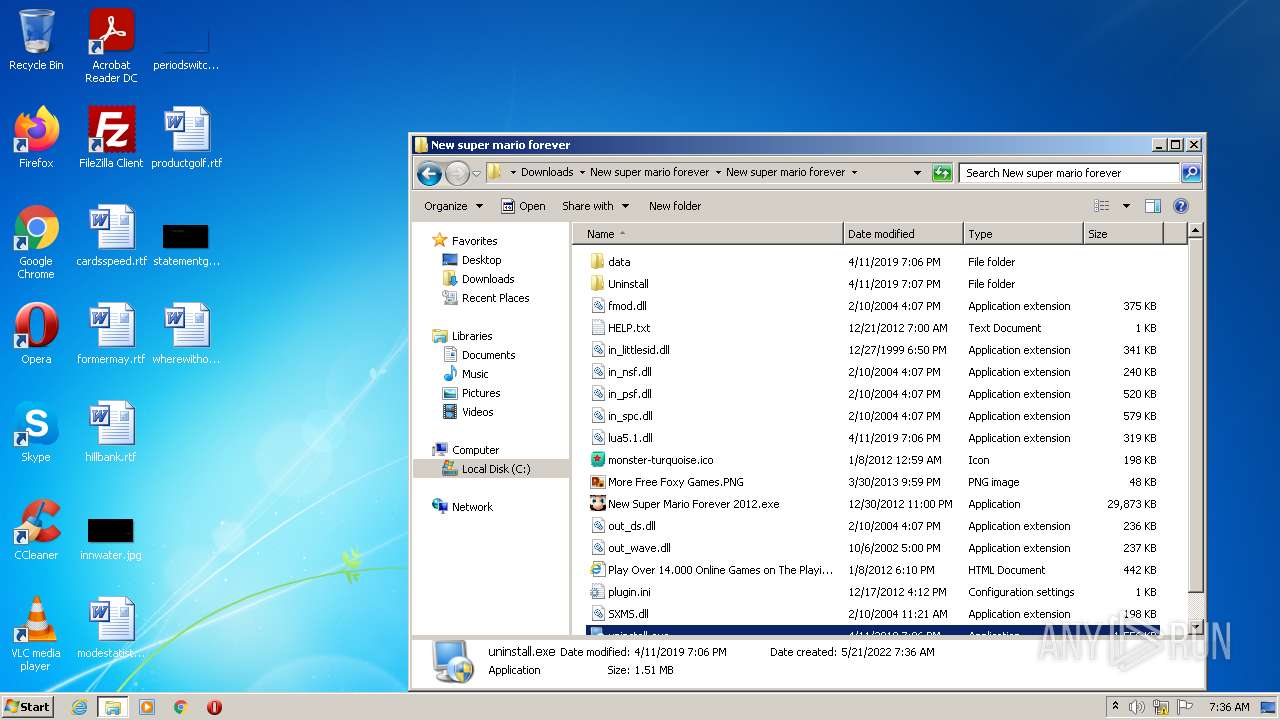
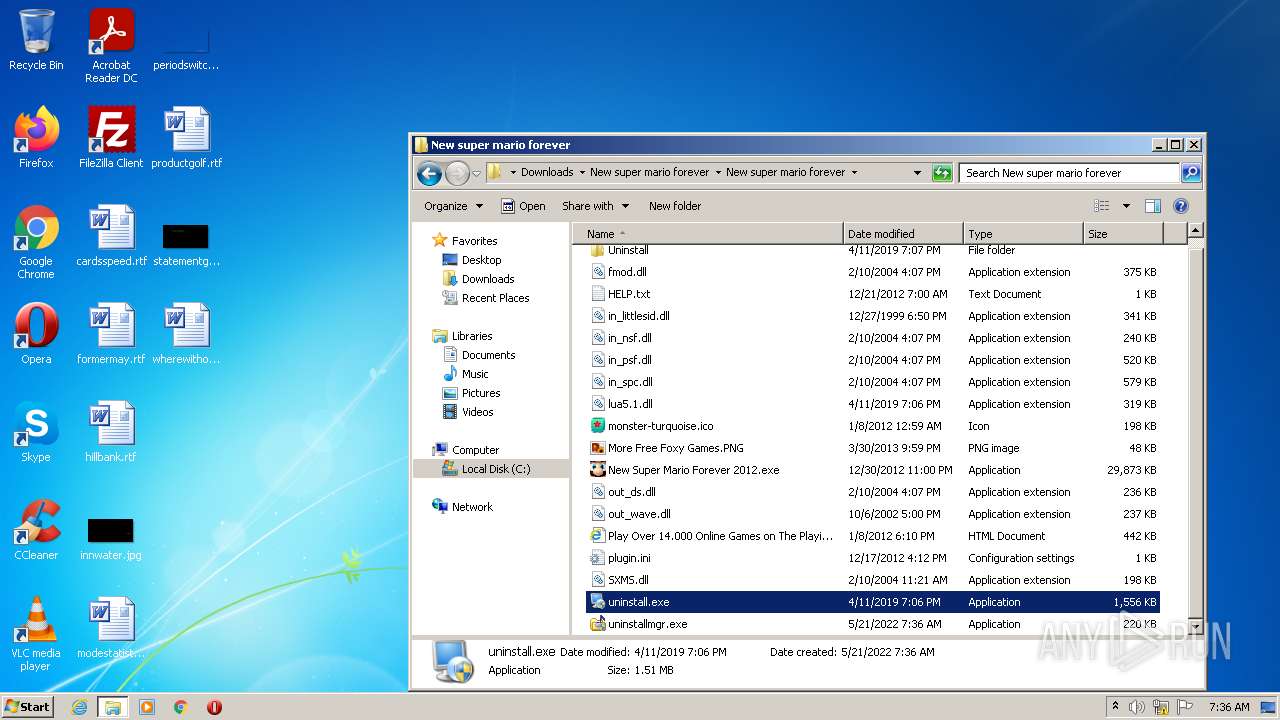
Drops executable file immediately after starts
- WinRAR.exe (PID: 1432)
- New Super Mario Forever 2012.exe (PID: 3336)
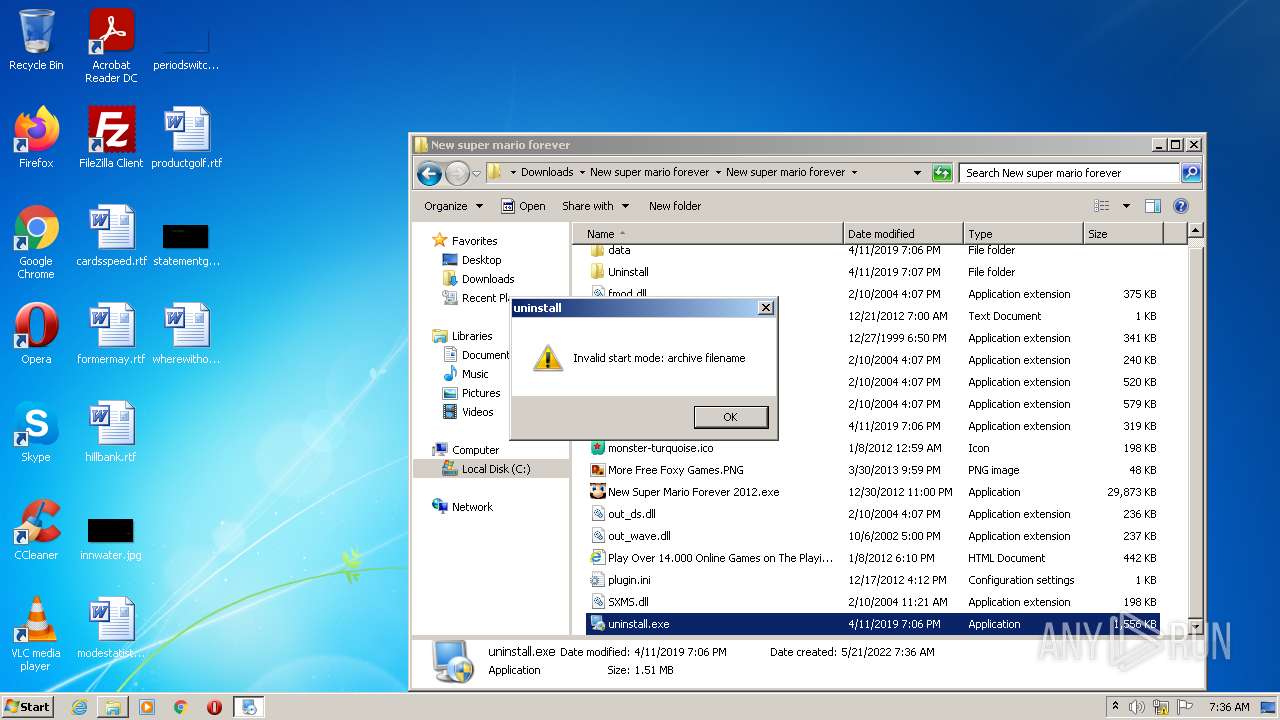
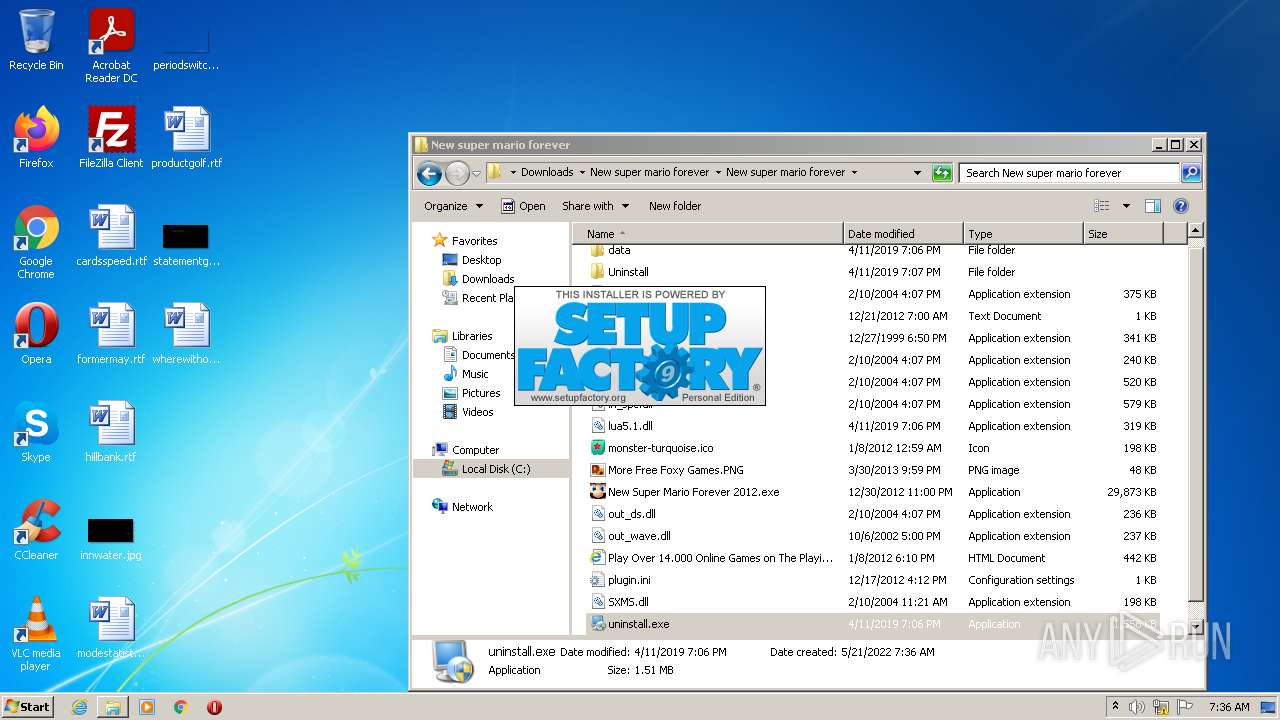
- uninstall.exe (PID: 924)
- iexplore.exe (PID: 3360)
Loads dropped or rewritten executable
- New Super Mario Forever 2012.exe (PID: 3336)
- SearchProtocolHost.exe (PID: 2496)
- uninstall.exe (PID: 924)
Application was dropped or rewritten from another process
- New Super Mario Forever 2012.exe (PID: 3336)
- uninstall.exe (PID: 4024)
- uninstall.exe (PID: 924)
- uninstallmgr.exe (PID: 3744)
Writes to a start menu file
- iexplore.exe (PID: 3360)
Application was injected by another process
- smss.exe (PID: 260)
- lsass.exe (PID: 484)
- csrss.exe (PID: 344)
- csrss.exe (PID: 388)
- winlogon.exe (PID: 436)
- svchost.exe (PID: 592)
- wininit.exe (PID: 380)
- svchost.exe (PID: 1880)
- svchost.exe (PID: 672)
- services.exe (PID: 476)
- lsm.exe (PID: 492)
- svchost.exe (PID: 1084)
- Explorer.EXE (PID: 1172)
- svchost.exe (PID: 1352)
- SearchIndexer.exe (PID: 2176)
- svchost.exe (PID: 1264)
- svchost.exe (PID: 760)
- svchost.exe (PID: 828)
- svchost.exe (PID: 972)
- svchost.exe (PID: 800)
- IMEDICTUPDATE.EXE (PID: 1424)
- svchost.exe (PID: 3172)
- spoolsv.exe (PID: 1236)
- ctfmon.exe (PID: 1372)
- taskeng.exe (PID: 284)
- svchost.exe (PID: 868)
- Dwm.exe (PID: 552)
- SearchFilterHost.exe (PID: 2532)
- DllHost.exe (PID: 3848)
- DllHost.exe (PID: 3272)
Runs injected code in another process
- iexplore.exe (PID: 3424)
RAMNIT was detected
- iexplore.exe (PID: 3360)
Connects to CnC server
- iexplore.exe (PID: 3360)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 696)
Creates files in the Windows directory
- svchost.exe (PID: 828)
Checks supported languages
- WinRAR.exe (PID: 1432)
- New Super Mario Forever 2012.exe (PID: 3336)
- uninstall.exe (PID: 924)
- uninstallmgr.exe (PID: 3744)
- svchost.exe (PID: 800)
Creates or modifies windows services
- services.exe (PID: 476)
Reads the computer name
- WinRAR.exe (PID: 1432)
- New Super Mario Forever 2012.exe (PID: 3336)
- uninstallmgr.exe (PID: 3744)
- csrss.exe (PID: 388)
- uninstall.exe (PID: 924)
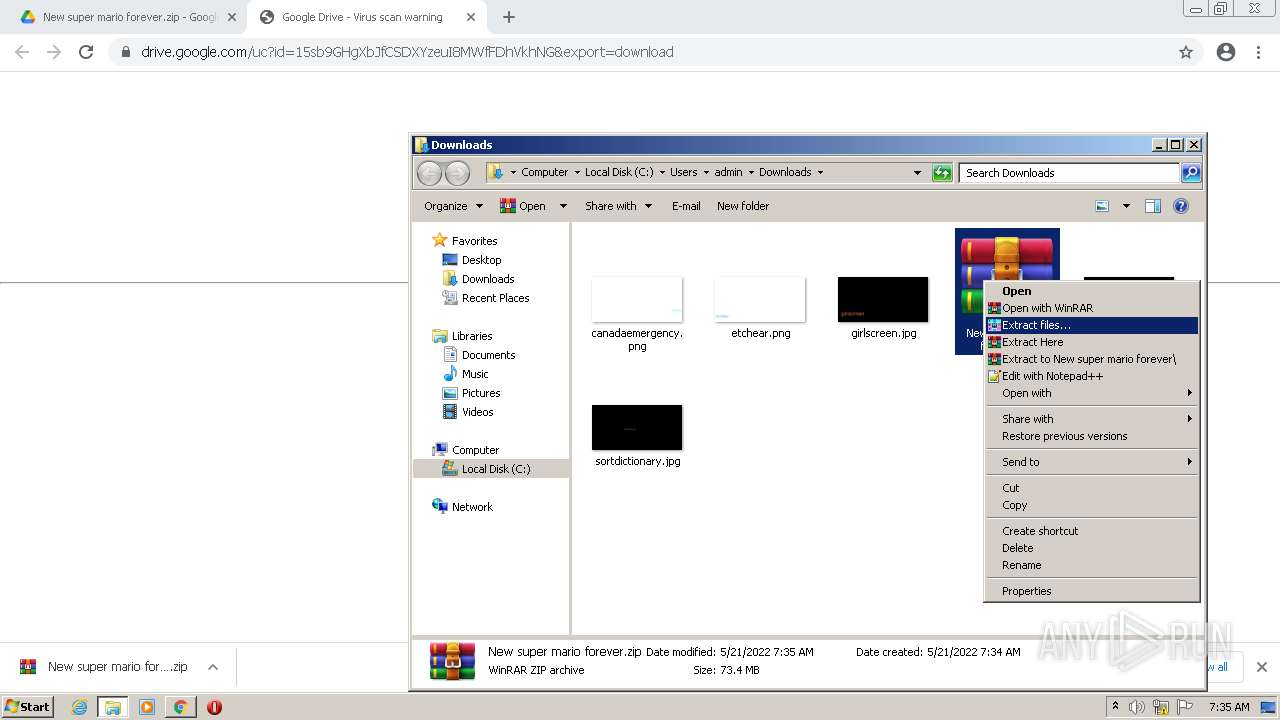
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1432)
- New Super Mario Forever 2012.exe (PID: 3336)
- uninstall.exe (PID: 924)
- iexplore.exe (PID: 3360)
Creates files in the program directory
- SearchIndexer.exe (PID: 2176)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1432)
- New Super Mario Forever 2012.exe (PID: 3336)
- iexplore.exe (PID: 3360)
- uninstall.exe (PID: 924)
Starts Internet Explorer
- uninstallmgr.exe (PID: 3744)
Searches for installed software
- svchost.exe (PID: 800)
INFO
Reads the hosts file
- chrome.exe (PID: 696)
- chrome.exe (PID: 2512)
Application launched itself
- chrome.exe (PID: 696)
Checks supported languages
- chrome.exe (PID: 3840)
- chrome.exe (PID: 856)
- chrome.exe (PID: 2512)
- chrome.exe (PID: 696)
- chrome.exe (PID: 1836)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 3372)
- chrome.exe (PID: 304)
- chrome.exe (PID: 3964)
- svchost.exe (PID: 3172)
- chrome.exe (PID: 1664)
- svchost.exe (PID: 868)
- DllHost.exe (PID: 3848)
- DllHost.exe (PID: 3272)
- iexplore.exe (PID: 3360)
- iexplore.exe (PID: 3424)
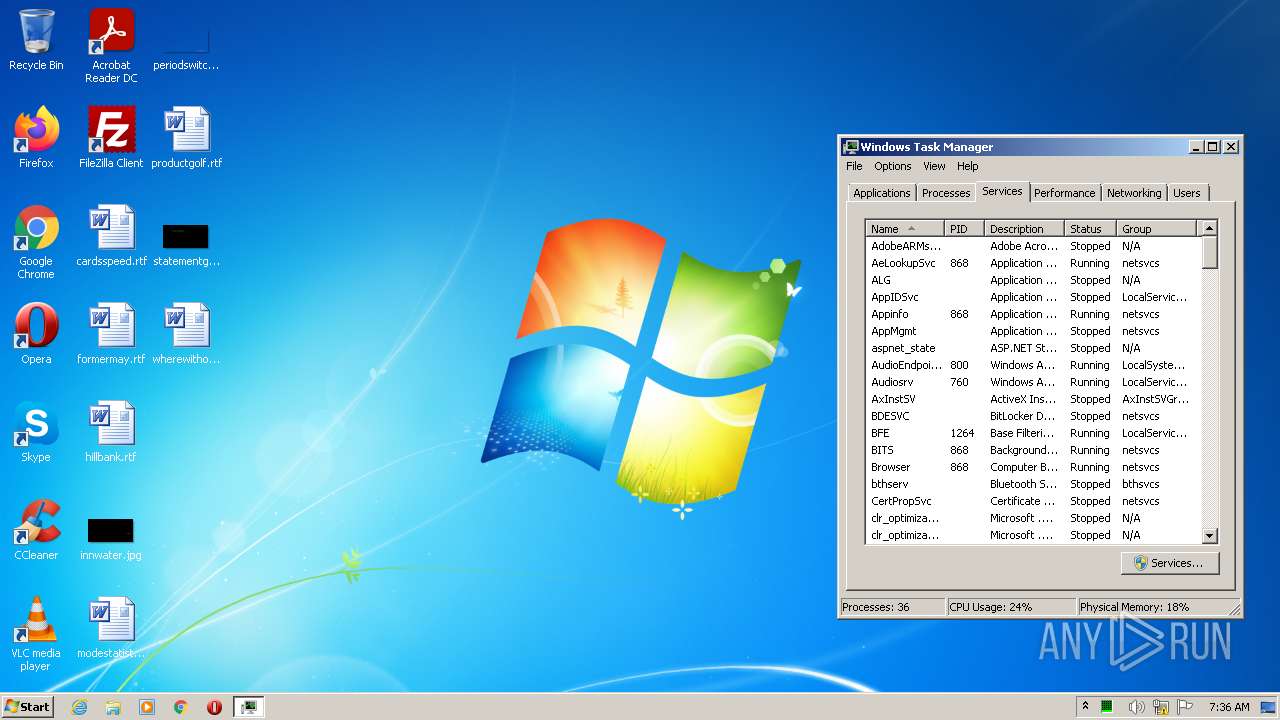
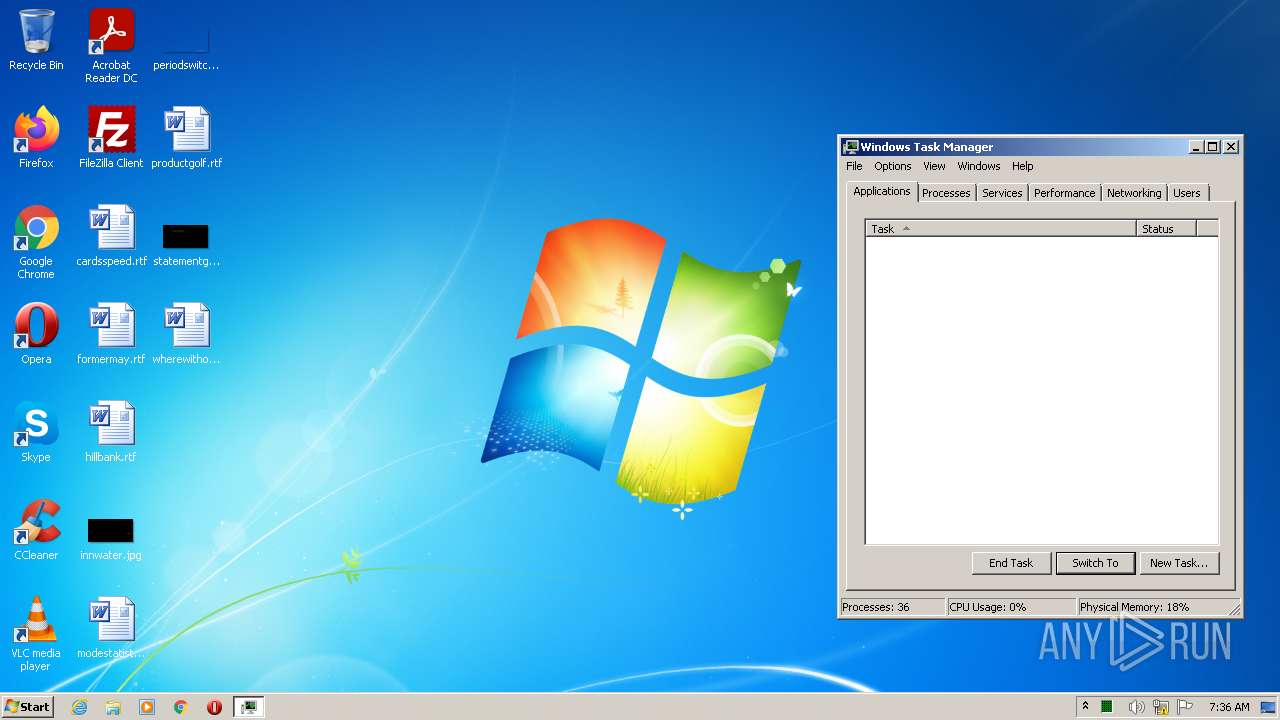
- taskmgr.exe (PID: 2480)
Reads the computer name
- chrome.exe (PID: 696)
- chrome.exe (PID: 2512)
- chrome.exe (PID: 856)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 3372)
- chrome.exe (PID: 3964)
- chrome.exe (PID: 1664)
- svchost.exe (PID: 3172)
- DllHost.exe (PID: 3848)
- DllHost.exe (PID: 3272)
- iexplore.exe (PID: 3424)
- taskmgr.exe (PID: 2480)
- iexplore.exe (PID: 3360)
Reads settings of System Certificates
- chrome.exe (PID: 2512)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 696)
Reads the date of Windows installation
- chrome.exe (PID: 3372)
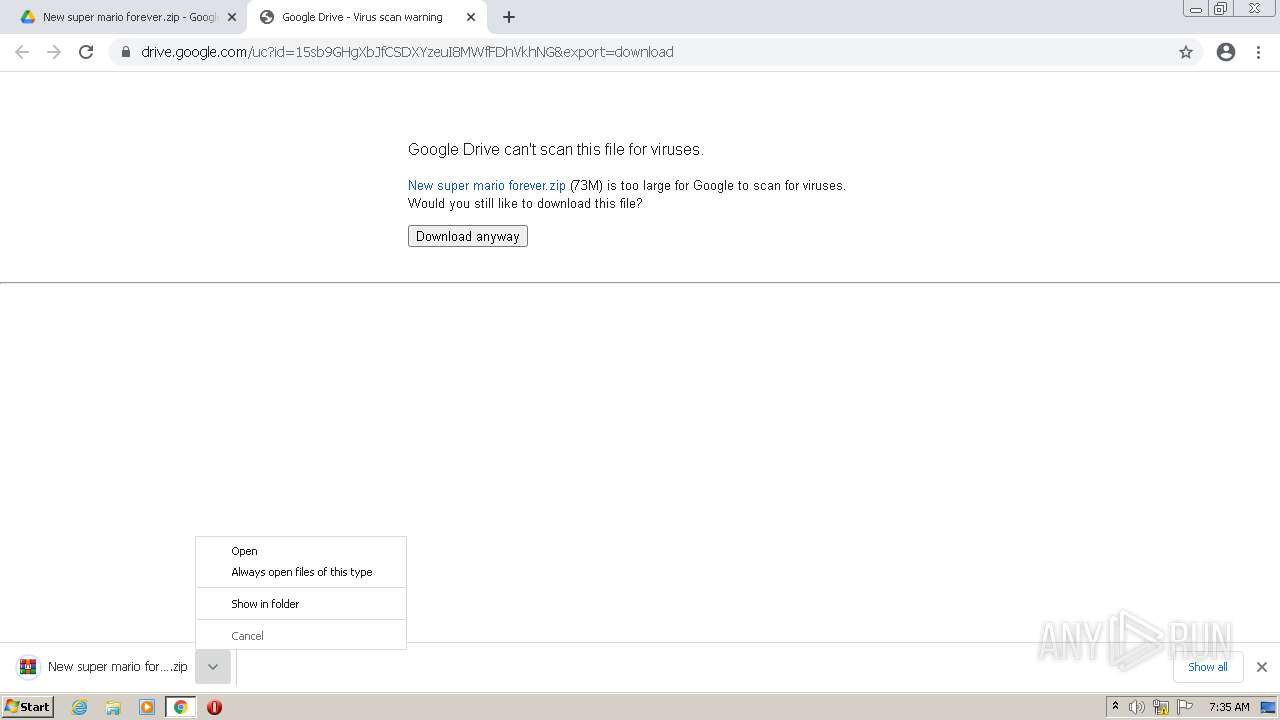
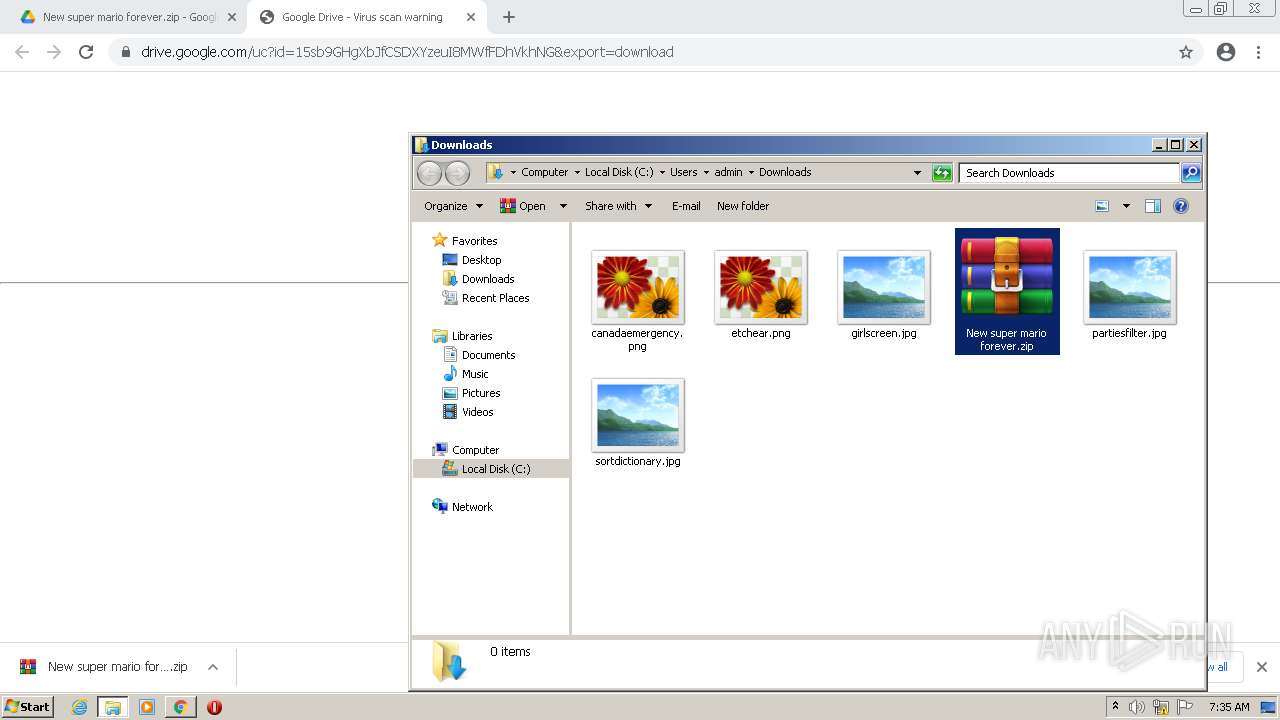
Manual execution by user
- WinRAR.exe (PID: 1432)
- uninstall.exe (PID: 924)
- New Super Mario Forever 2012.exe (PID: 3336)
- uninstall.exe (PID: 4024)
- taskmgr.exe (PID: 2480)
Creates files in the user directory
- iexplore.exe (PID: 3360)
Creates files in the program directory
- iexplore.exe (PID: 3360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
55
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 260 | \SystemRoot\System32\smss.exe | \SystemRoot\System32\smss.exe | System | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 284 | taskeng.exe {676F38EF-2AEC-4A4B-BA70-4C8C7218D1B1} | C:\Windows\system32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=1060,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1592 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 344 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\system32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 380 | wininit.exe | C:\Windows\system32\wininit.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Start-Up Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\system32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 436 | winlogon.exe | C:\Windows\system32\winlogon.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Logon Application Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 476 | C:\Windows\system32\services.exe | C:\Windows\system32\services.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 484 | C:\Windows\system32\lsass.exe | C:\Windows\system32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Exit code: 0 Version: 6.1.7601.24545 (win7sp1_ldr_escrow.200102-1707) Modules
| |||||||||||||||
| 492 | C:\Windows\system32\lsm.exe | C:\Windows\system32\lsm.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Session Manager Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
29 986
Read events
29 580
Write events
406
Delete events
0
Modification events
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
19
Suspicious files
436
Text files
140
Unknown types
302
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62888803-2B8.pma | — | |
MD5:— | SHA256:— | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bd4030b1-8d31-45e2-b2ab-083077e5788c.tmp | text | |
MD5:— | SHA256:— | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RFf9cd3.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 3840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RFf9b2d.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RFfa08c.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFf99b6.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFf9a91.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
25
DNS requests
33
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 5.67 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 9.74 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 9.73 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 9.73 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 43.5 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 20.9 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 88.5 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | pgc | 178 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 358 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2512 | chrome.exe | 142.250.184.238:443 | drive.google.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 142.250.184.237:443 | accounts.google.com | Google Inc. | US | suspicious |
2512 | chrome.exe | 142.250.186.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 142.250.184.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 142.250.181.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 172.217.23.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 142.250.185.234:443 | content.googleapis.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 142.250.186.74:443 | blobcomments-pa.clients6.google.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 142.250.181.234:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
drive.google.com |
| shared |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
content.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3360 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3360 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3360 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |