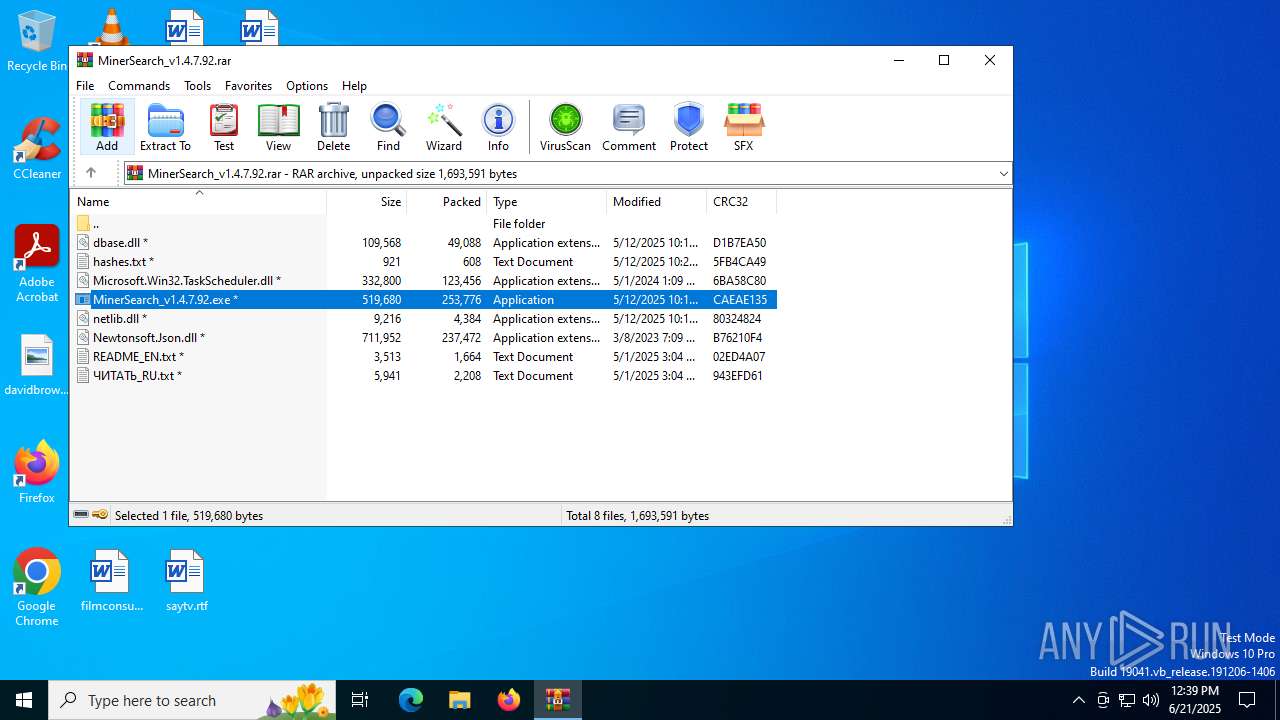
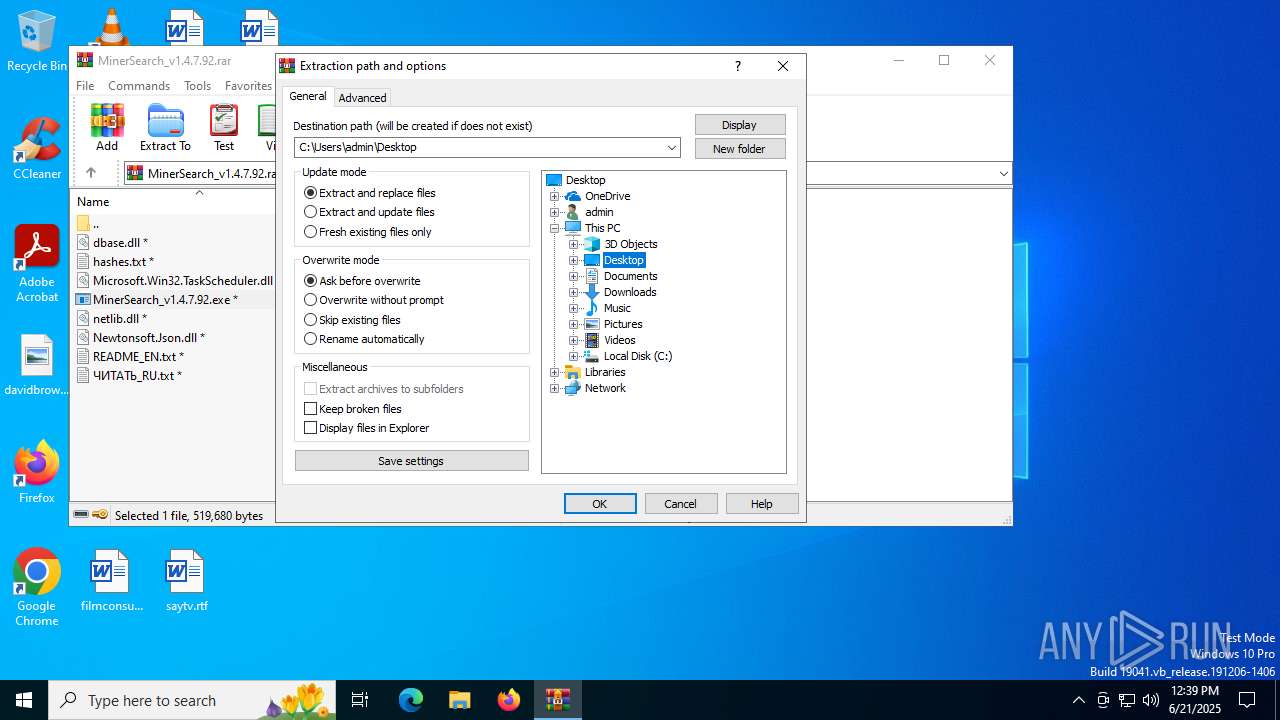
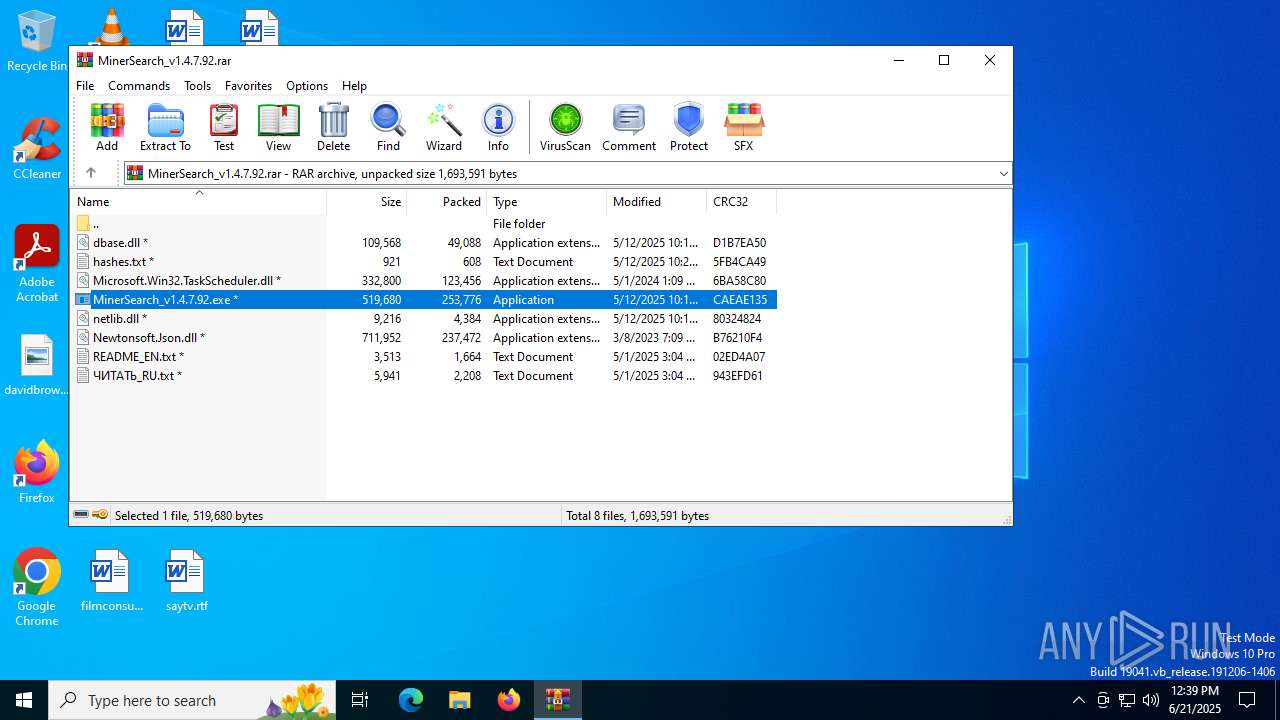
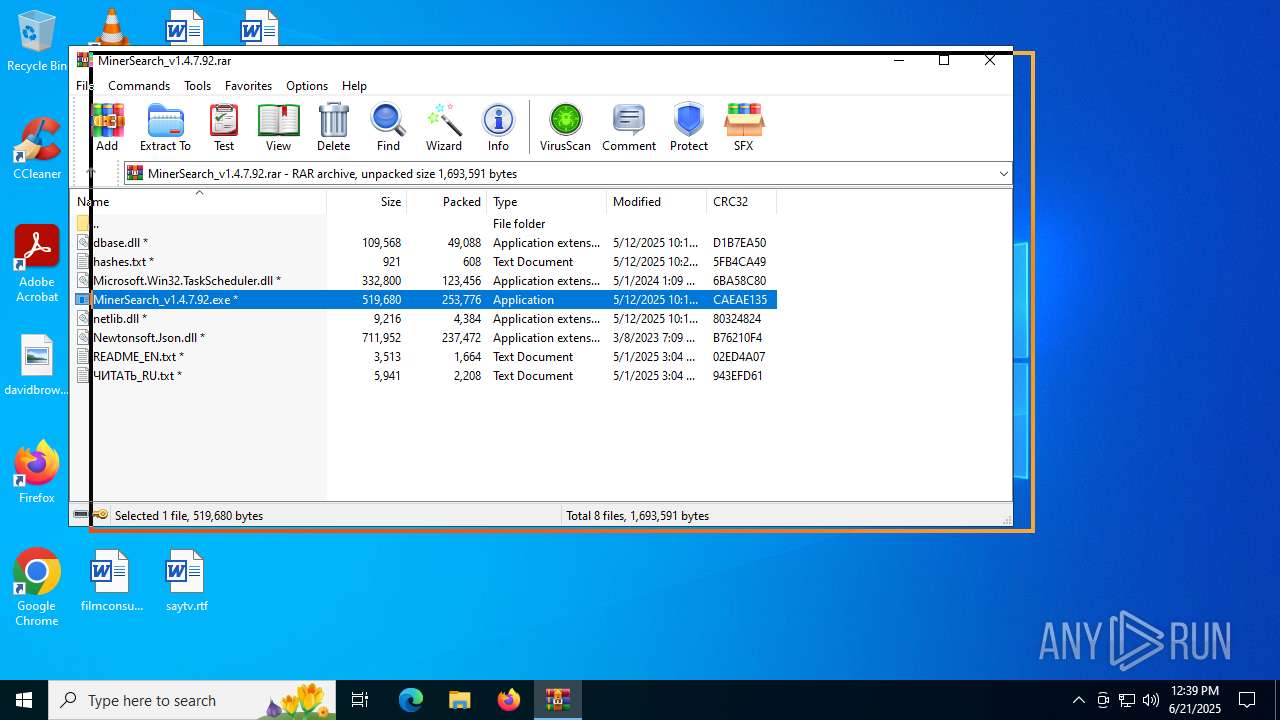
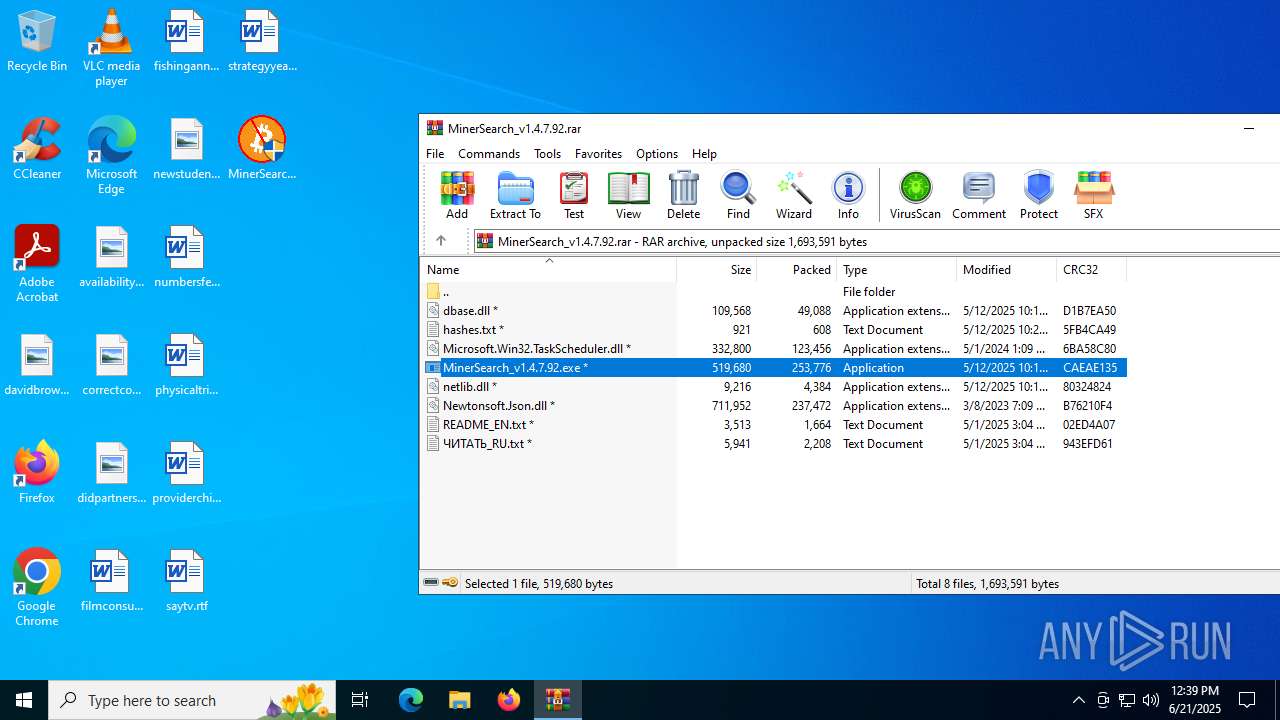
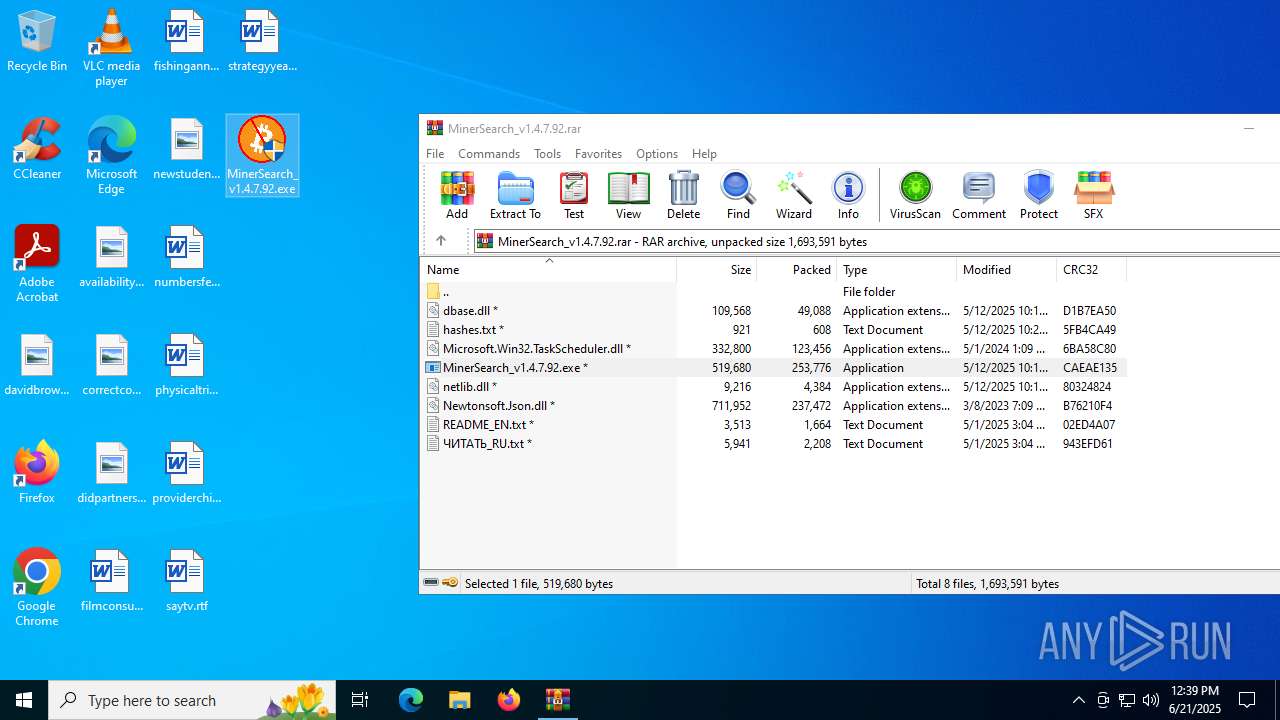
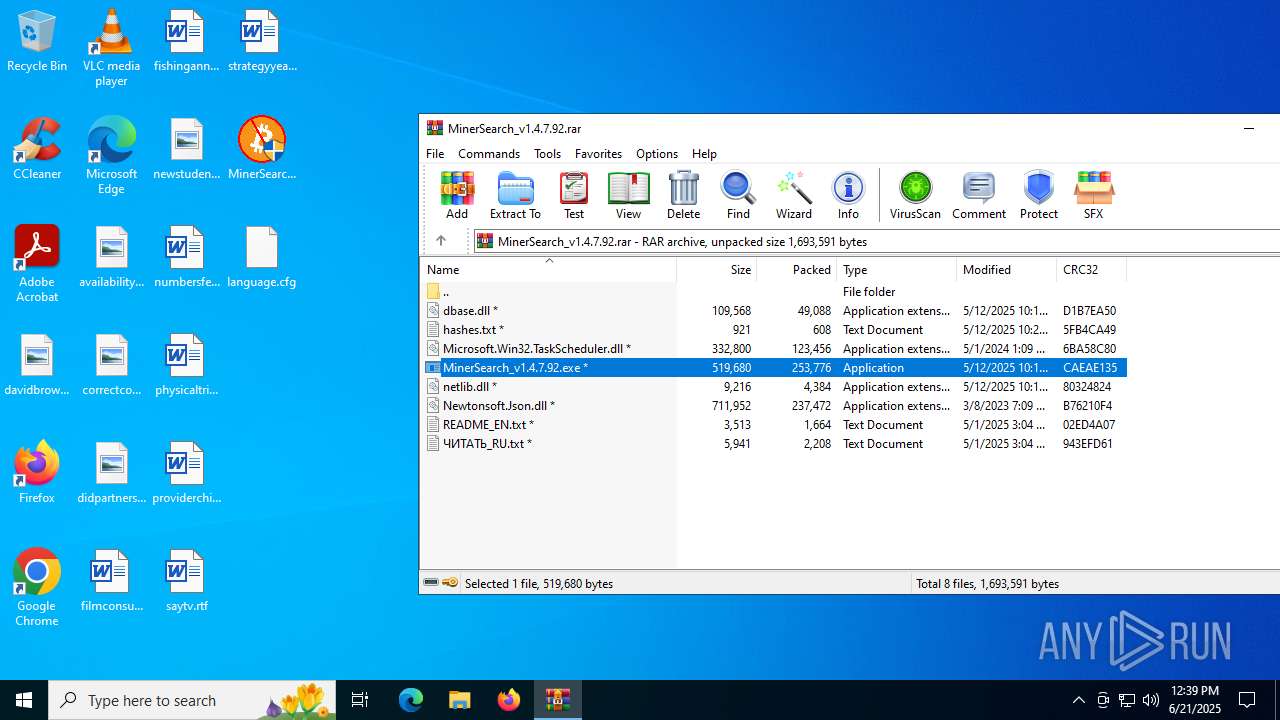
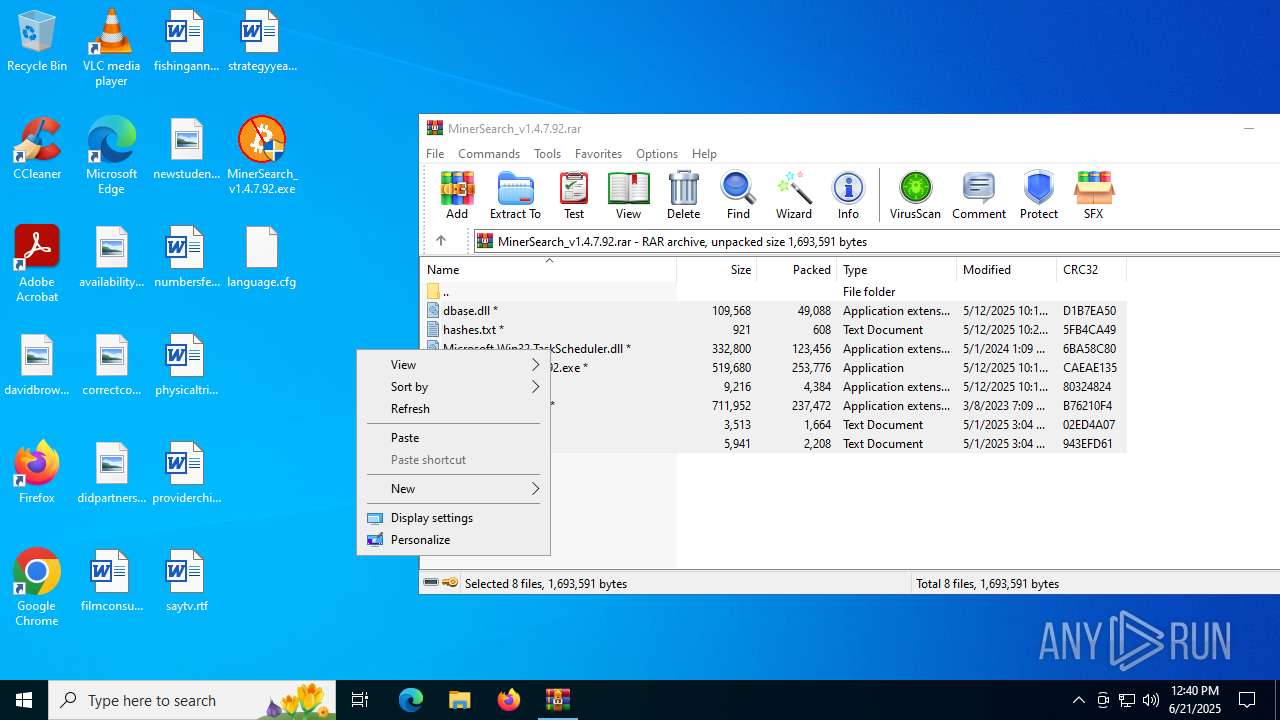
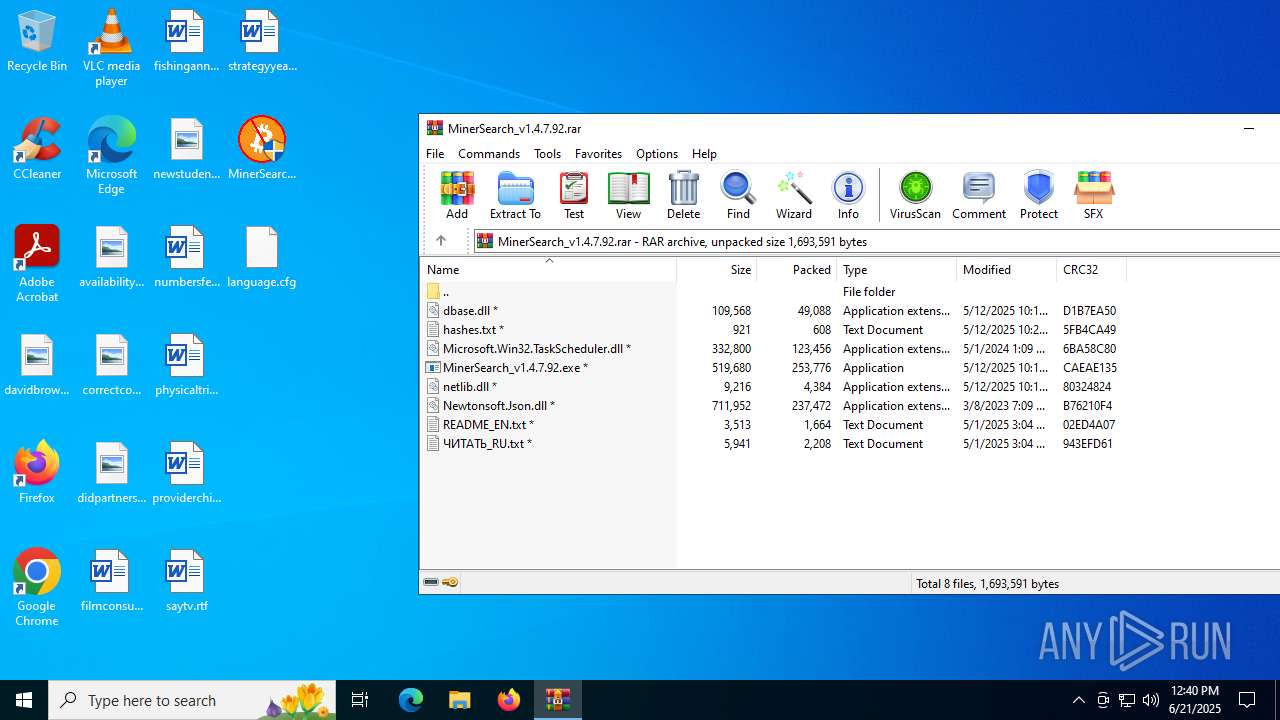
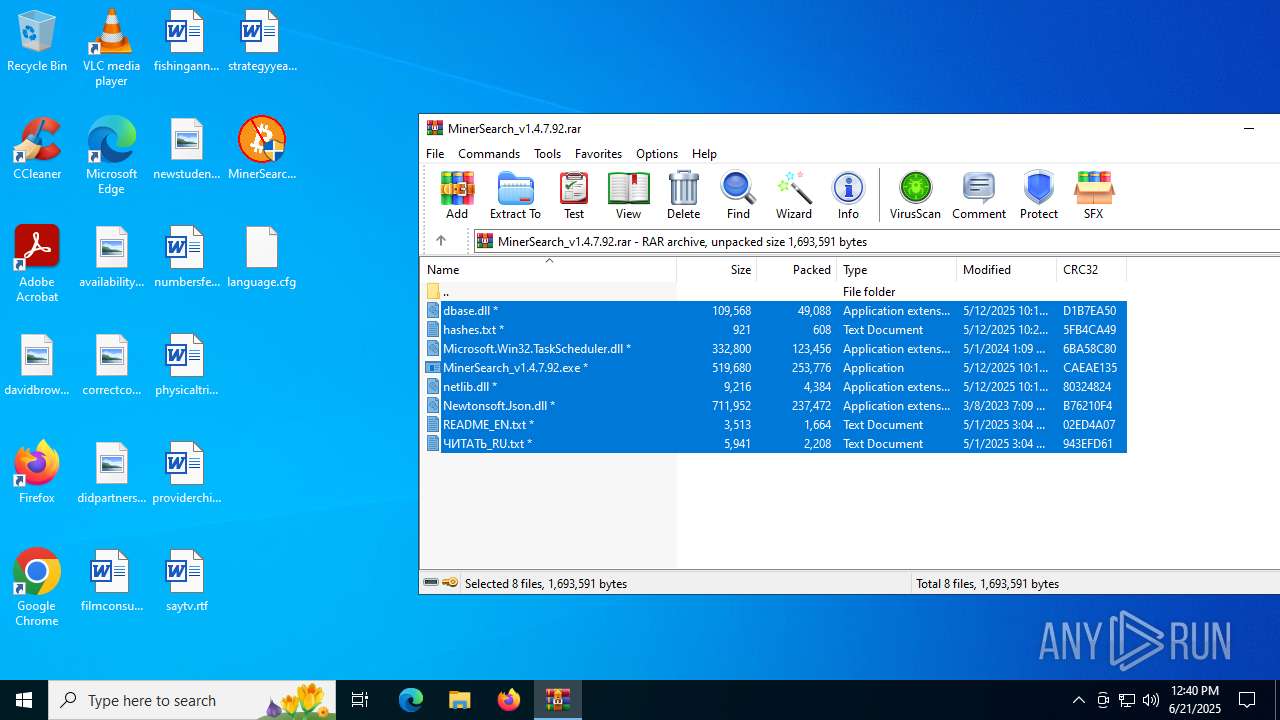
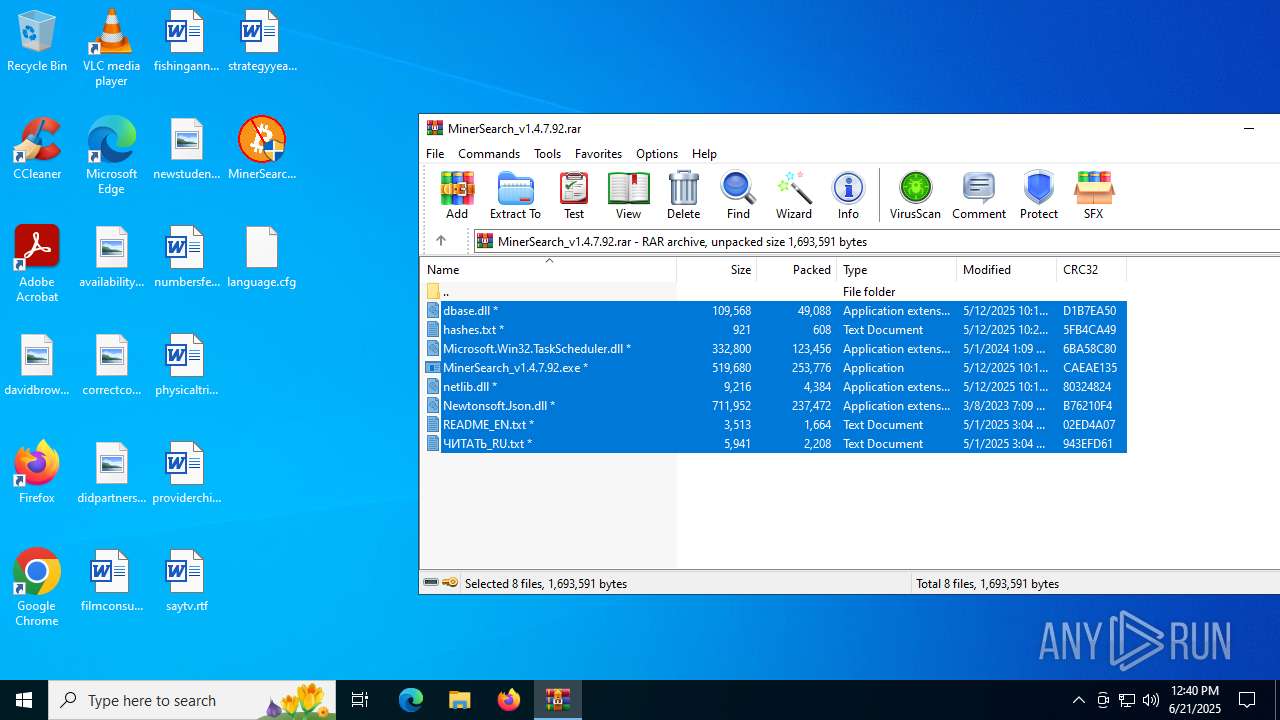
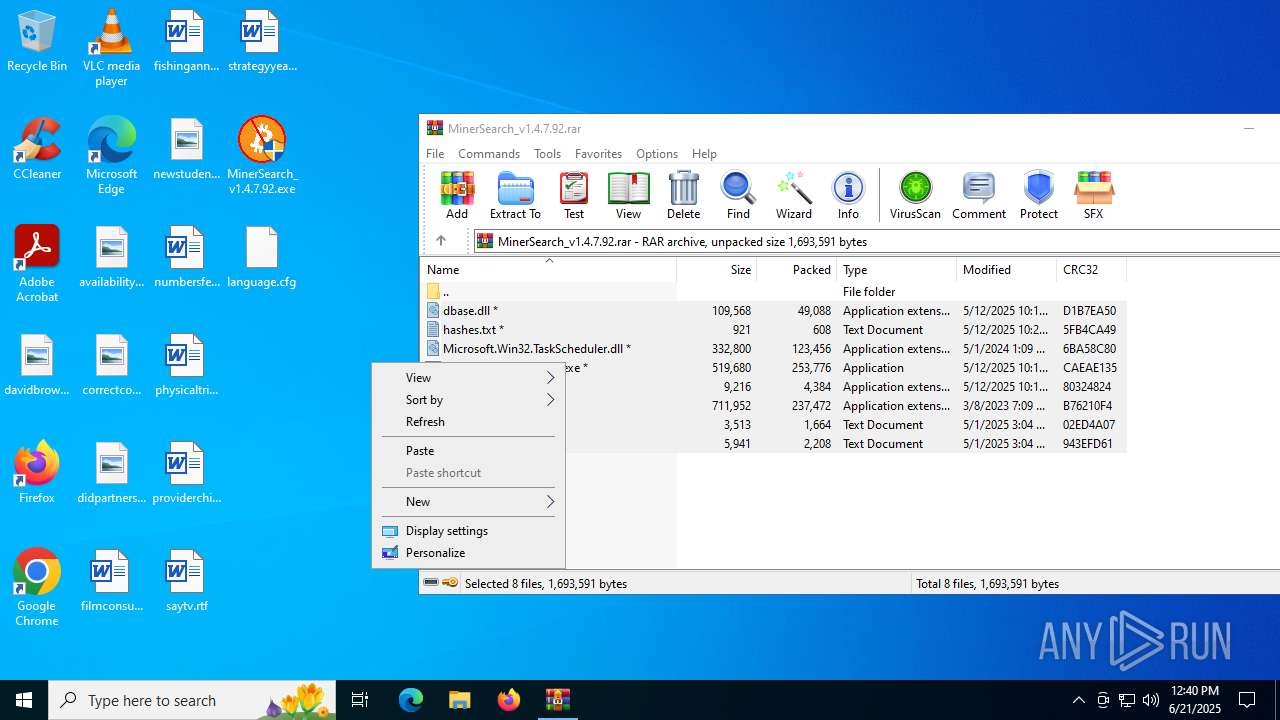
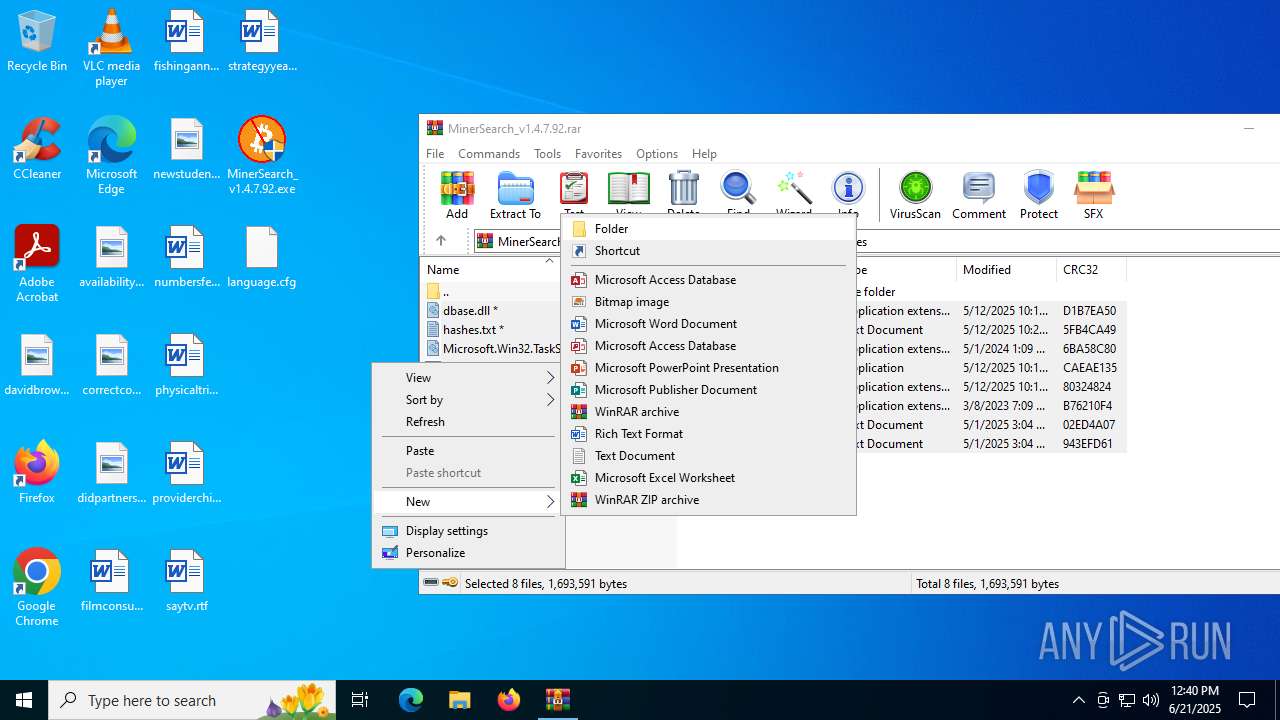
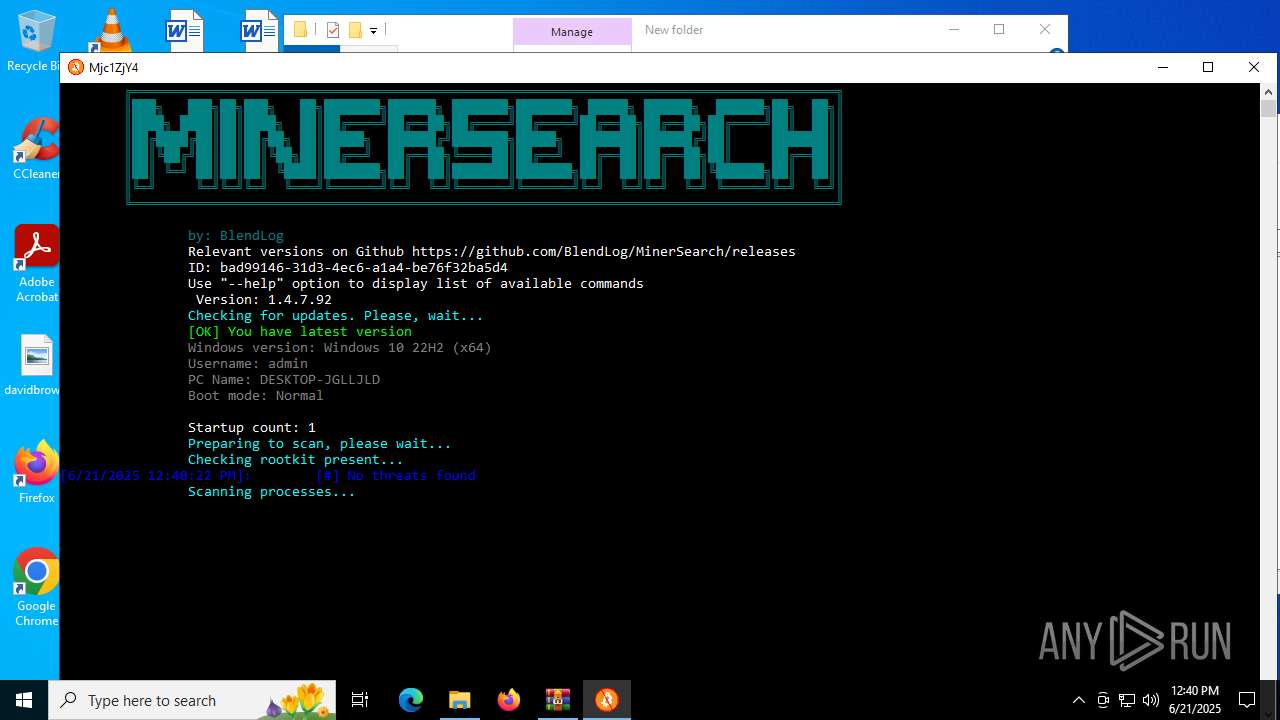
| File name: | MinerSearch_v1.4.7.92.rar |
| Full analysis: | https://app.any.run/tasks/6887d077-d61c-4b2a-ae00-a918124a0e7e |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 12:39:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
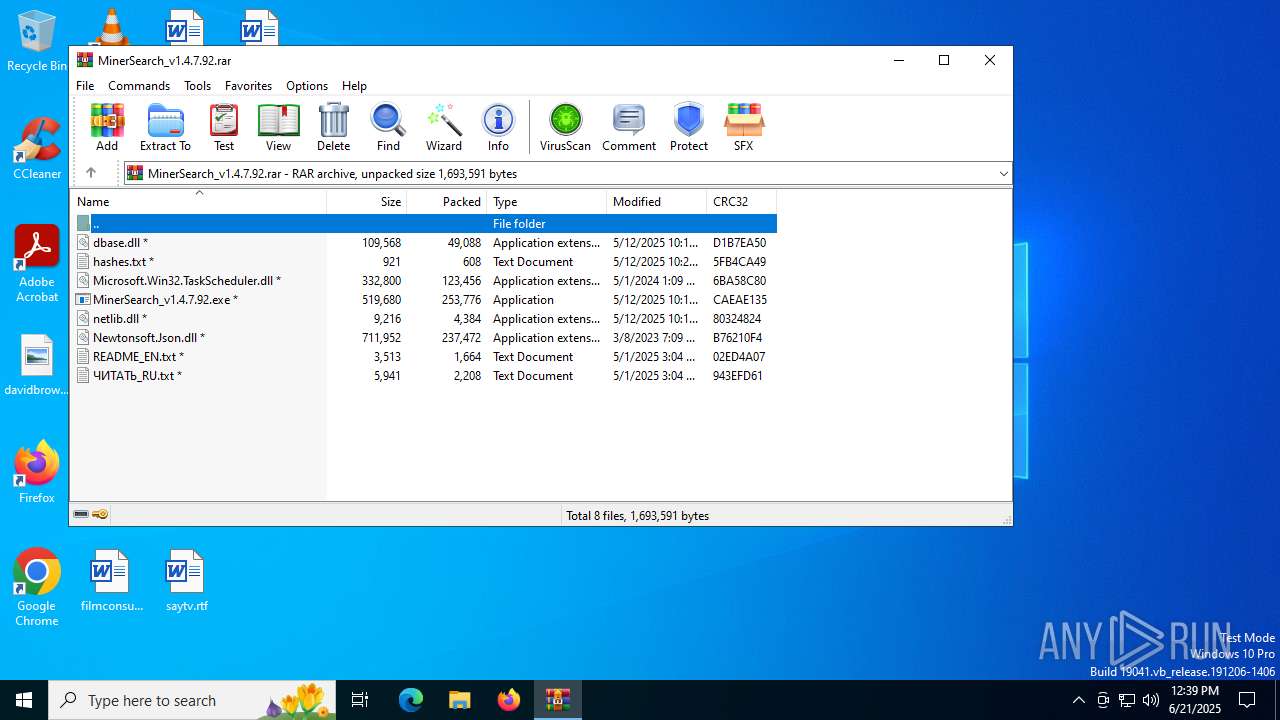
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2E988E4B39FA64EF7C9ADD88B21156C0 |
| SHA1: | 2390C18814698A0D98D0D5E6727276DD0E08D2FC |
| SHA256: | C93E9A4E68E54DEC28983BAAE83AC01AA966981E8119617791BC86BB15E25DB6 |
| SSDEEP: | 24576:DI6E5guYpUtAir1vVC+u1TVi/VbE7I3NmIJ/RJ/s/dzAddBsV0e1IKrpIH6:DI6E5guYpUtAir1vVC+u1TVi9bE7I3N4 |
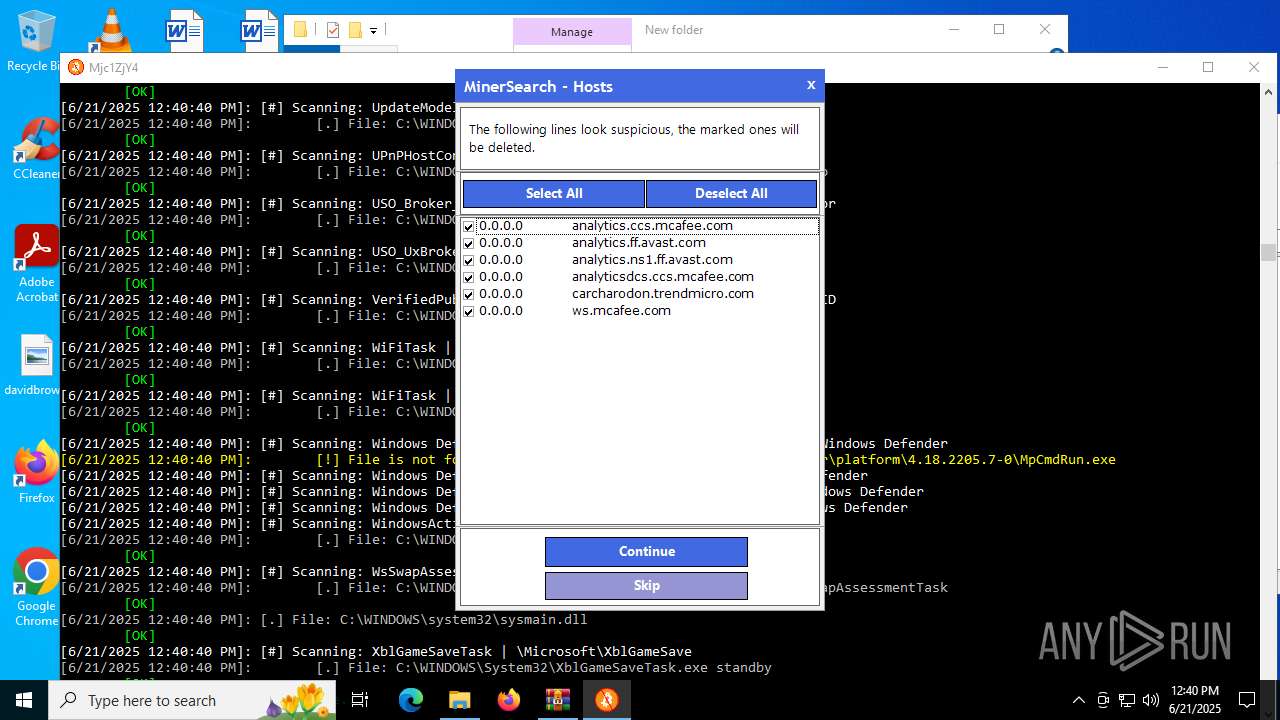
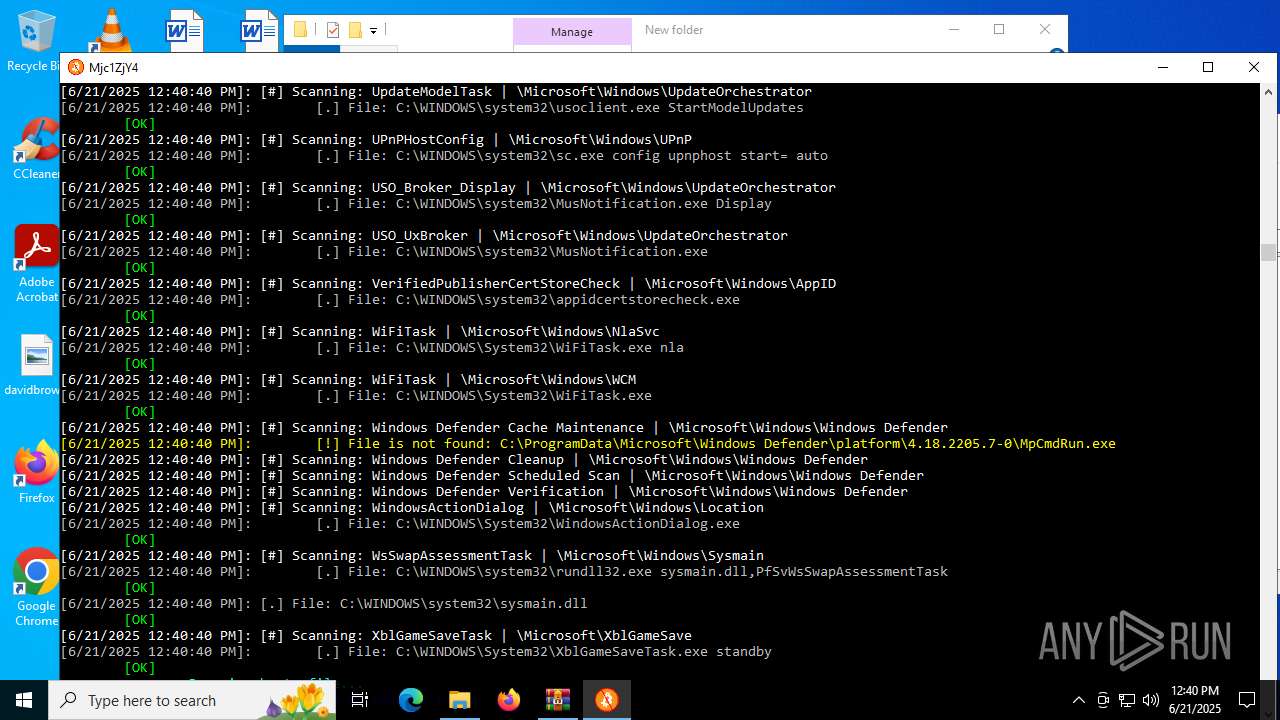
MALICIOUS
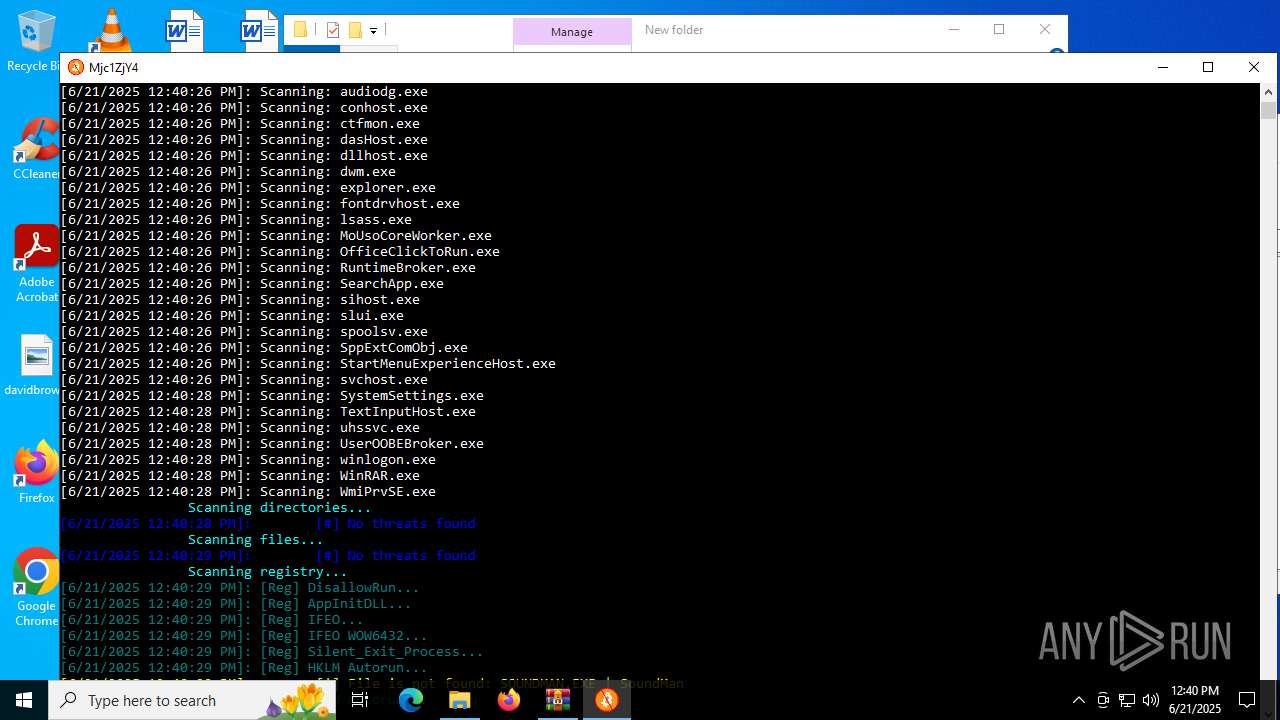
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6612)
- MinerSearch_v1.4.7.92.exe (PID: 5896)
Adds/modifies Windows certificates
- MinerSearch_v1.4.7.92.exe (PID: 5896)
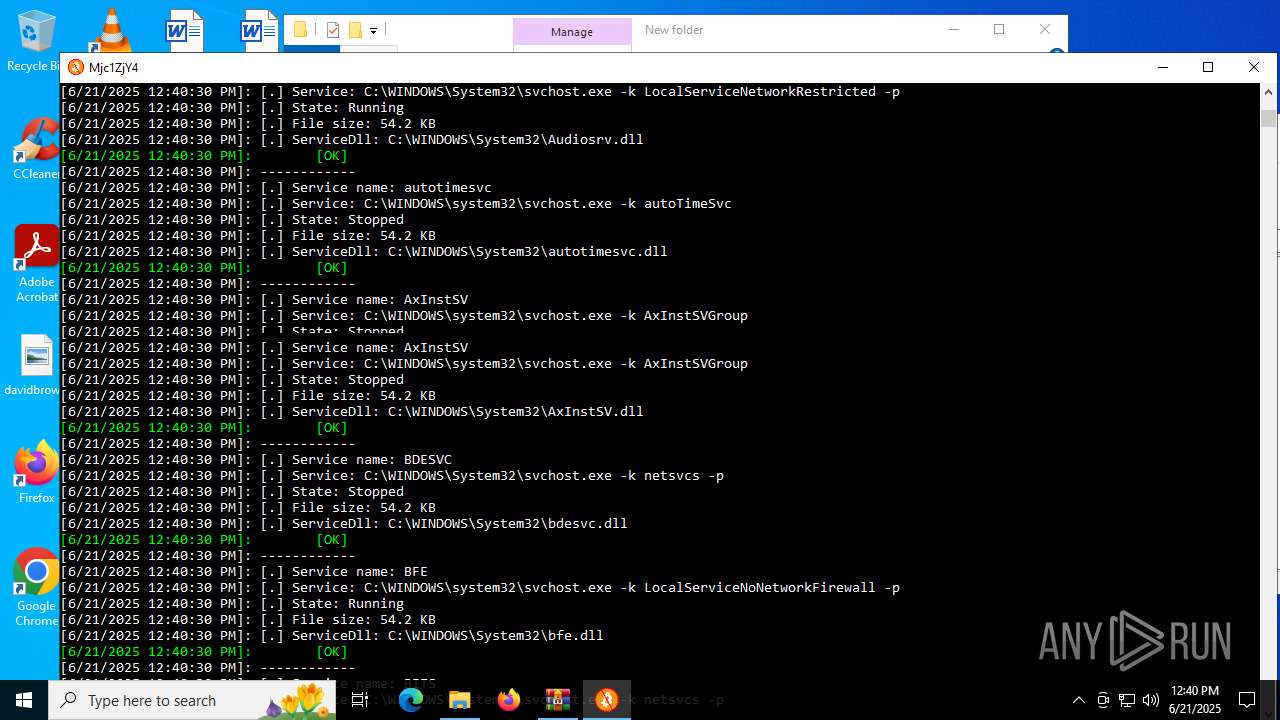
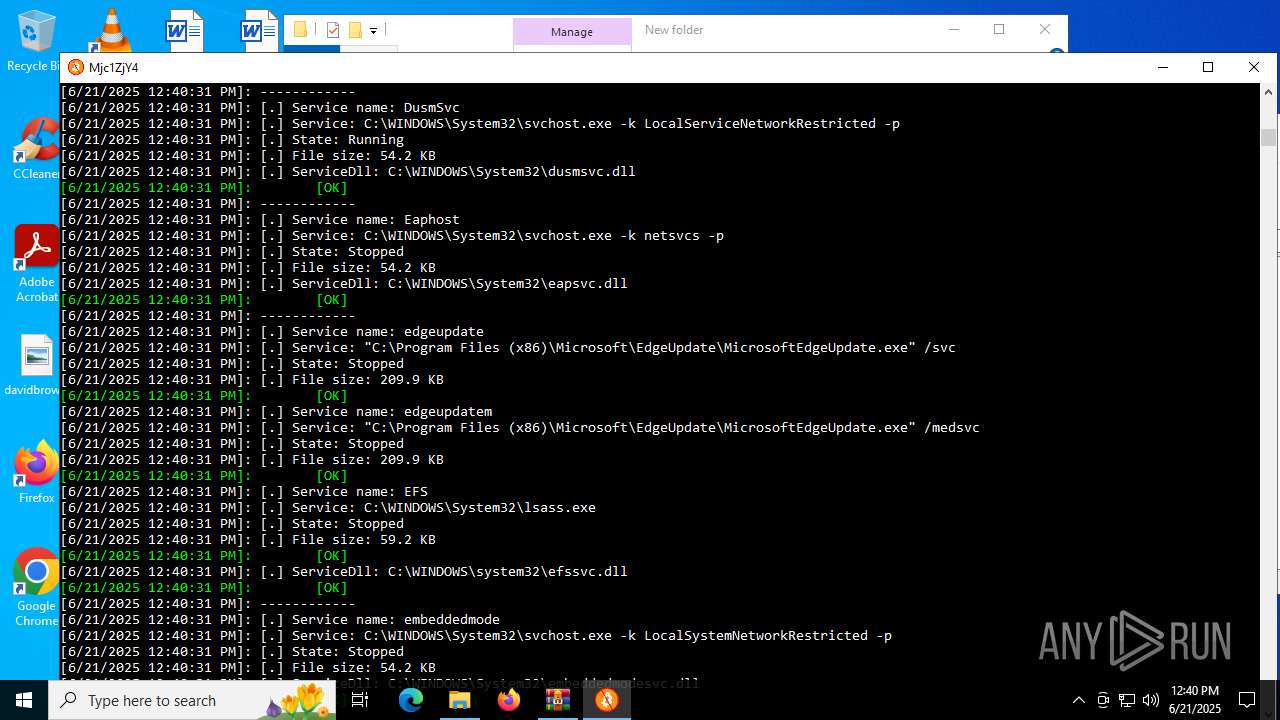
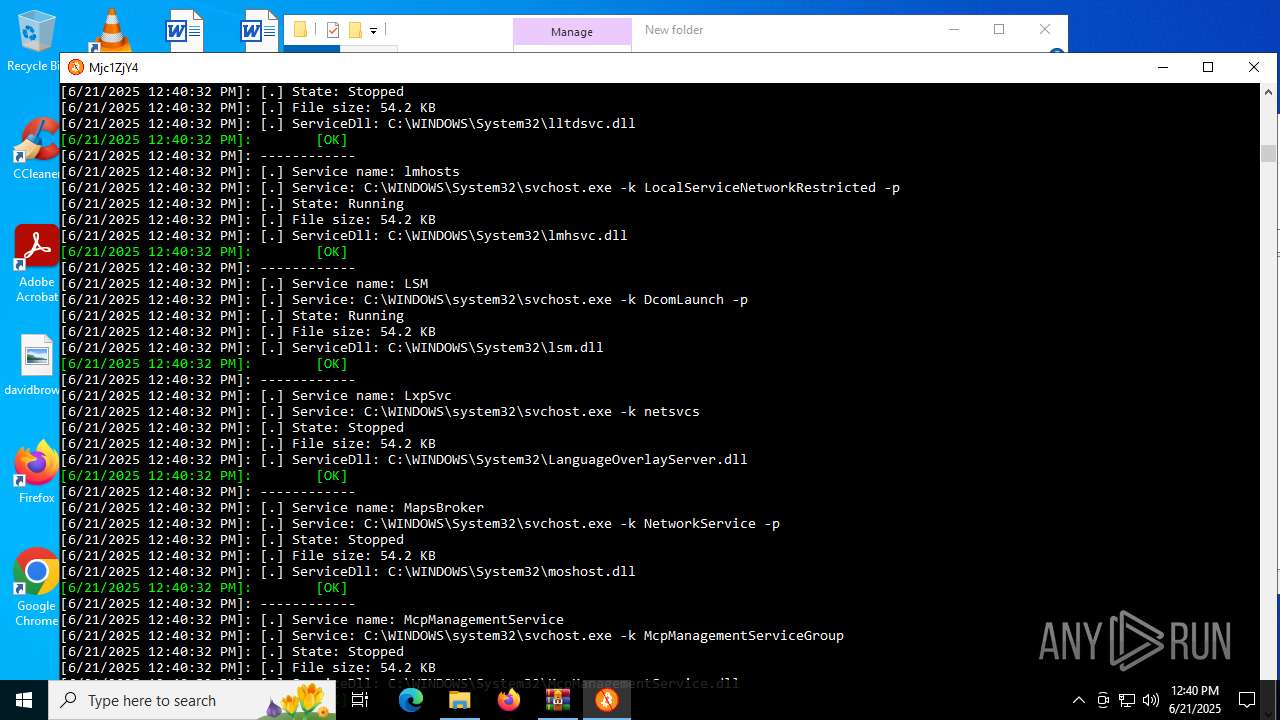
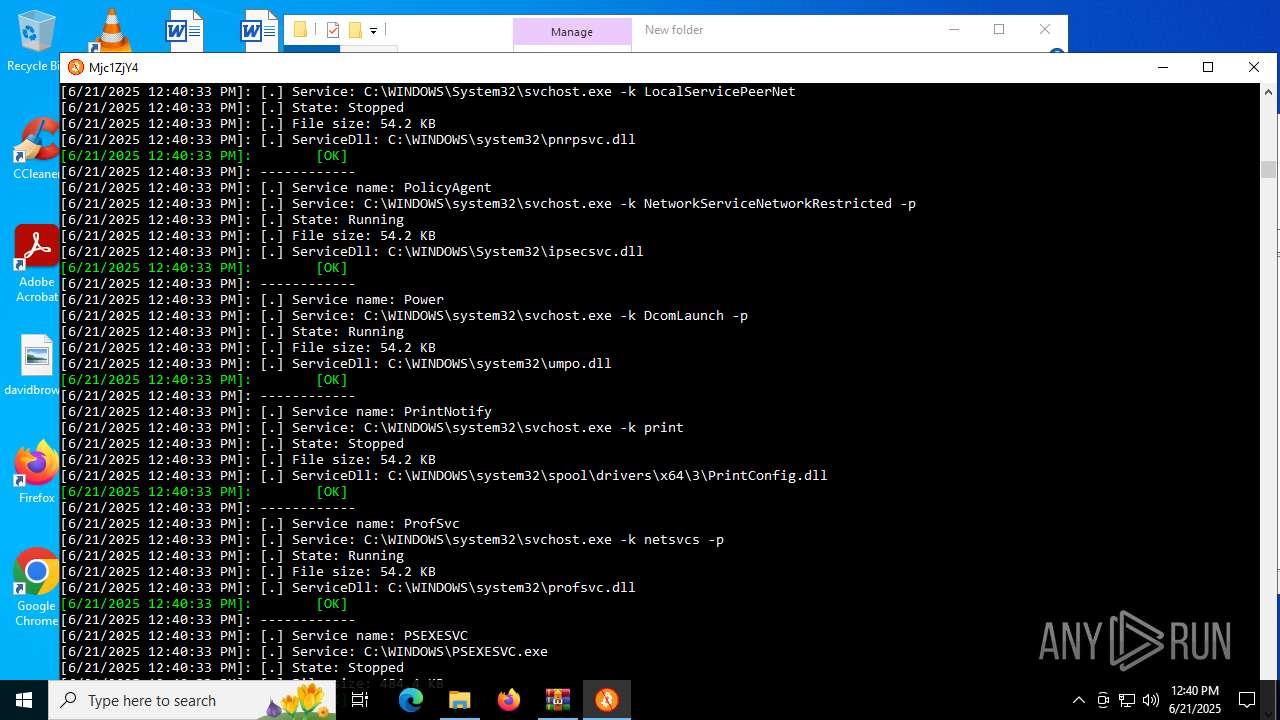
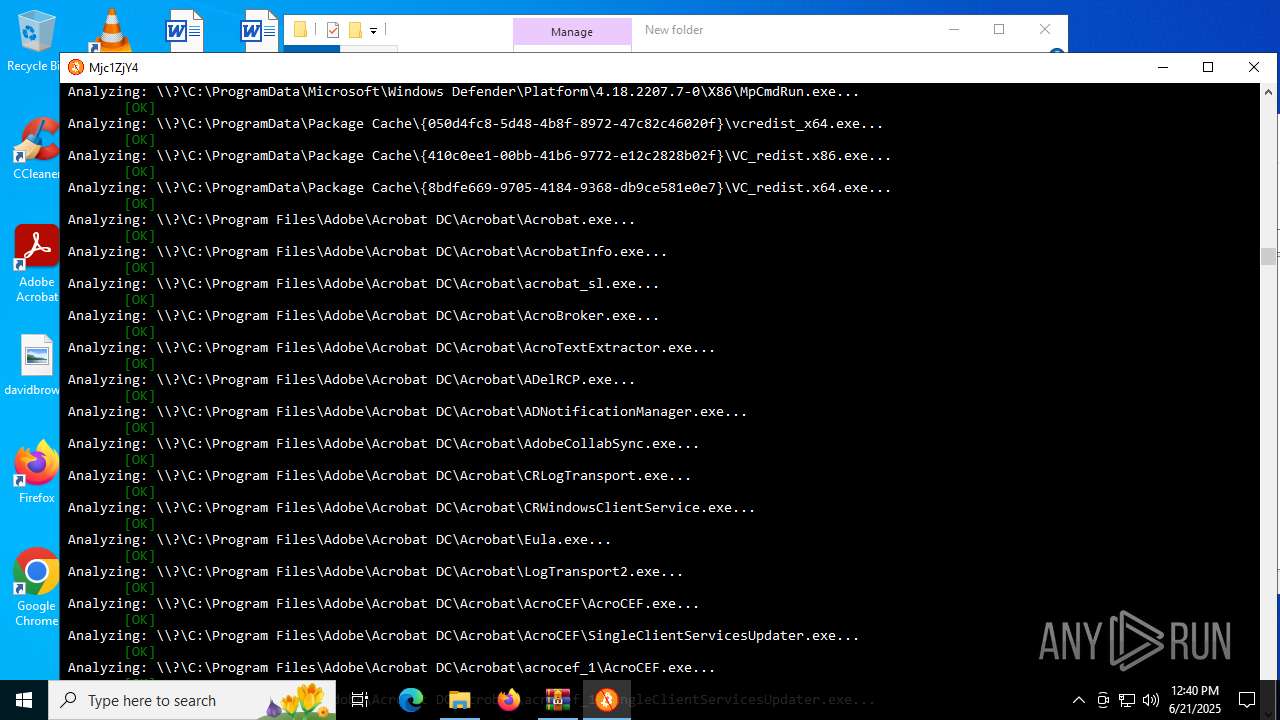
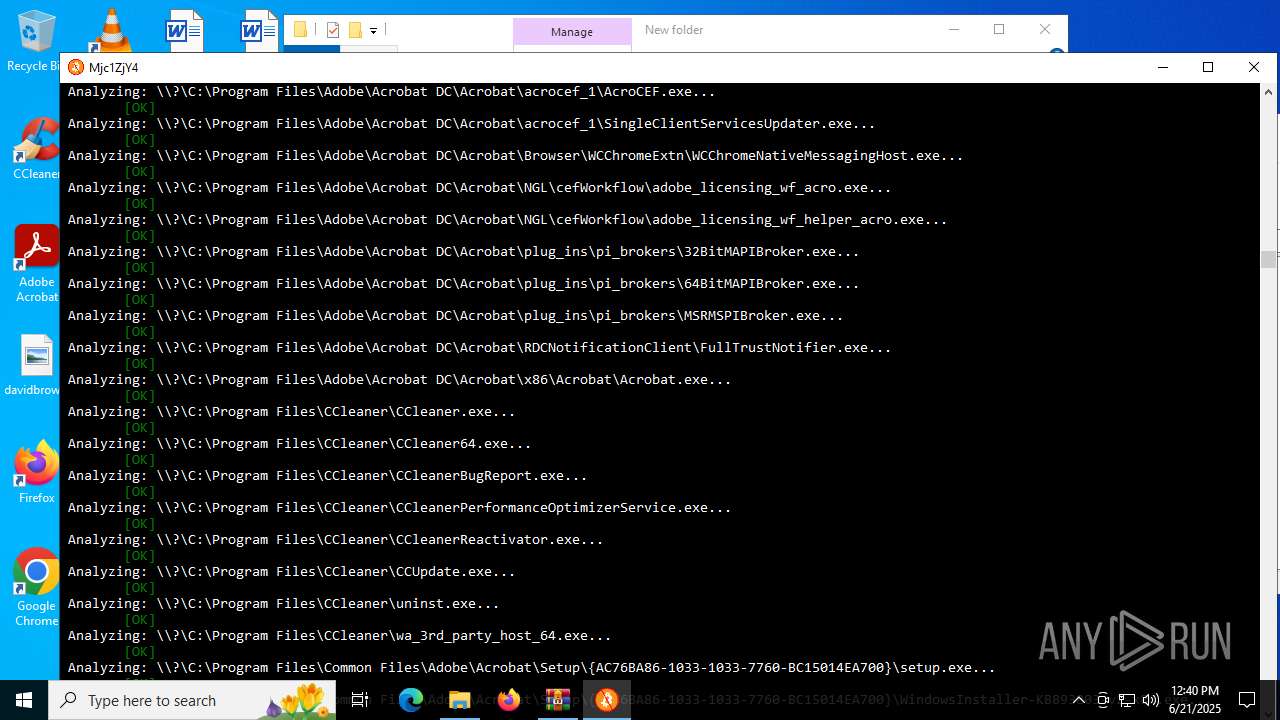
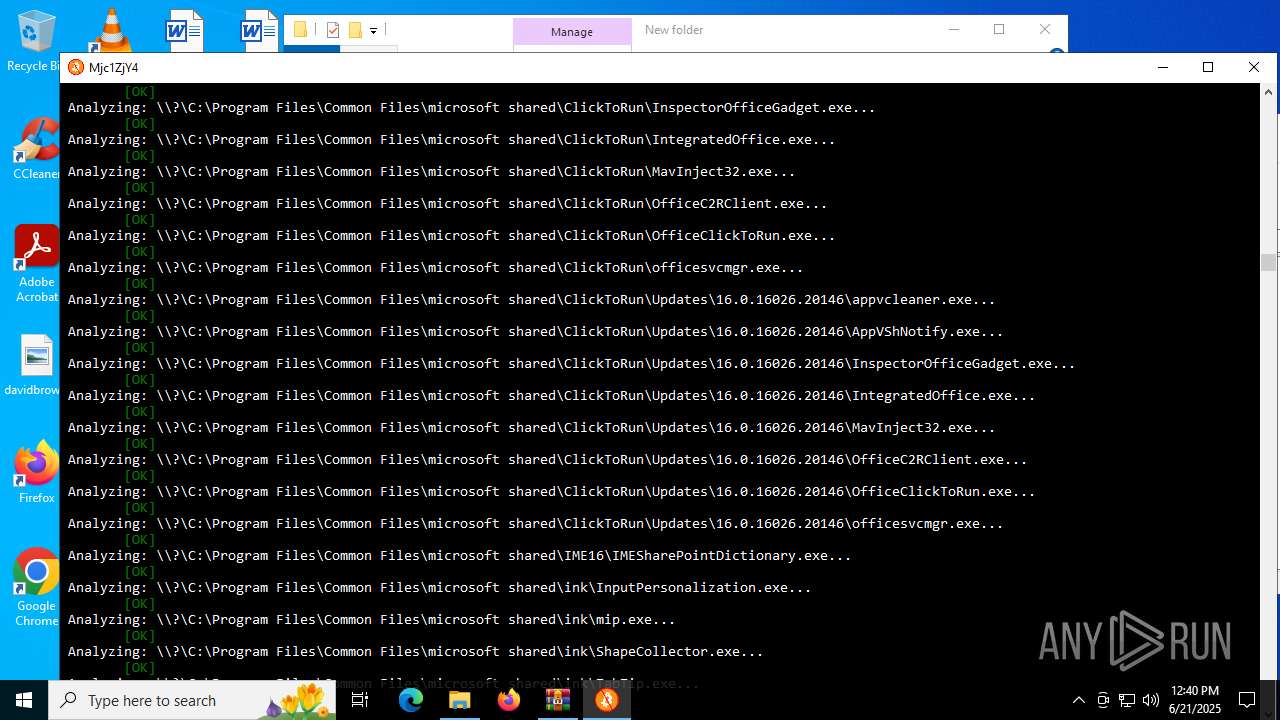
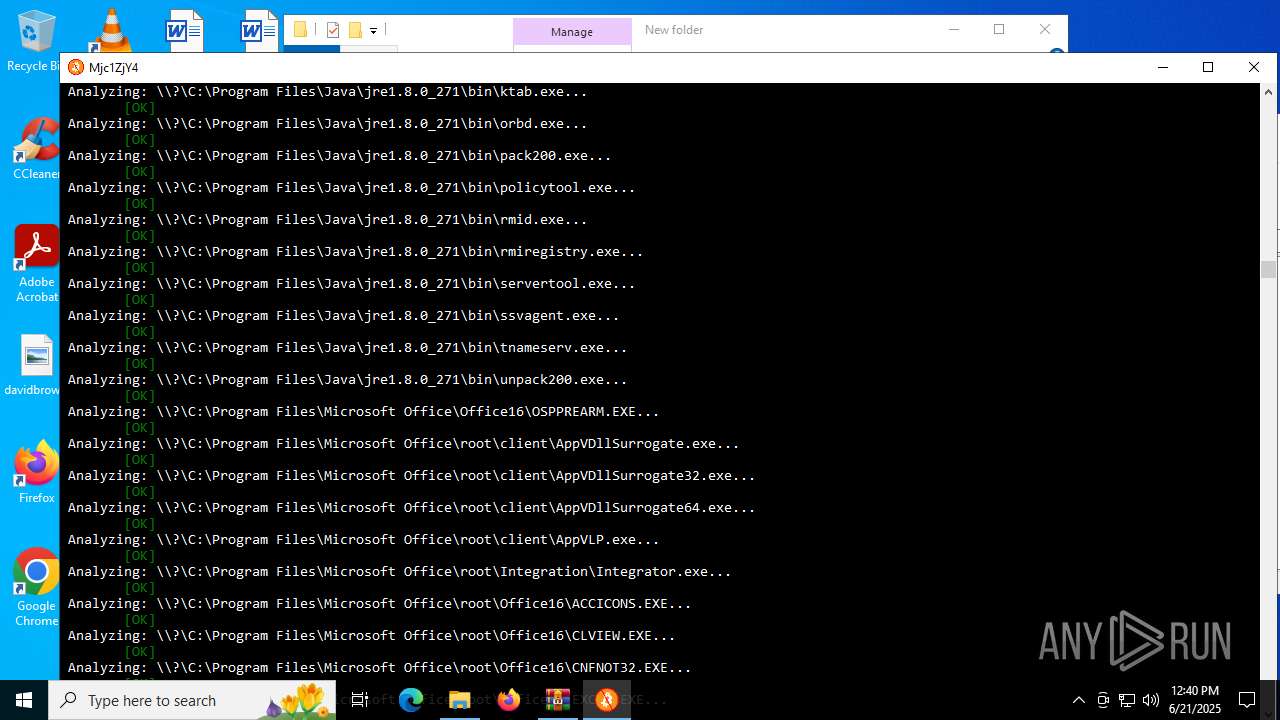
The process verifies whether the antivirus software is installed
- MinerSearch_v1.4.7.92.exe (PID: 5896)
Detected use of reserved device names
- MinerSearch_v1.4.7.92.exe (PID: 5896)
INFO
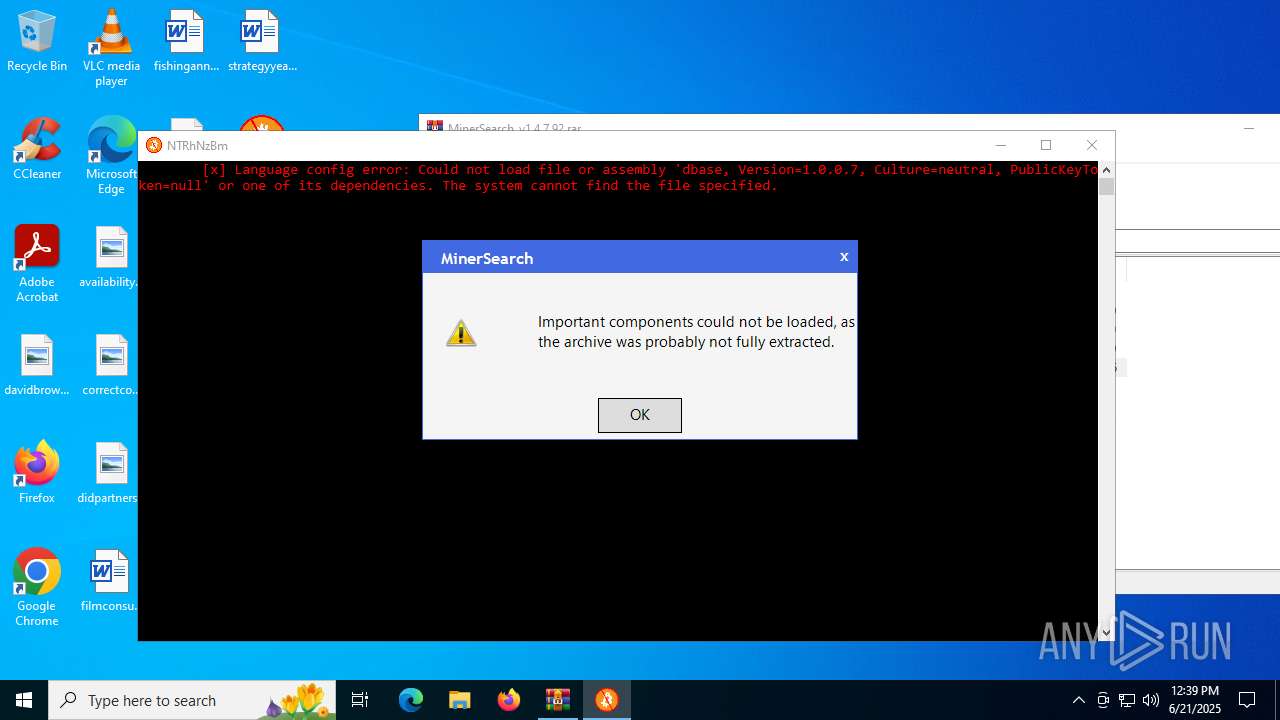
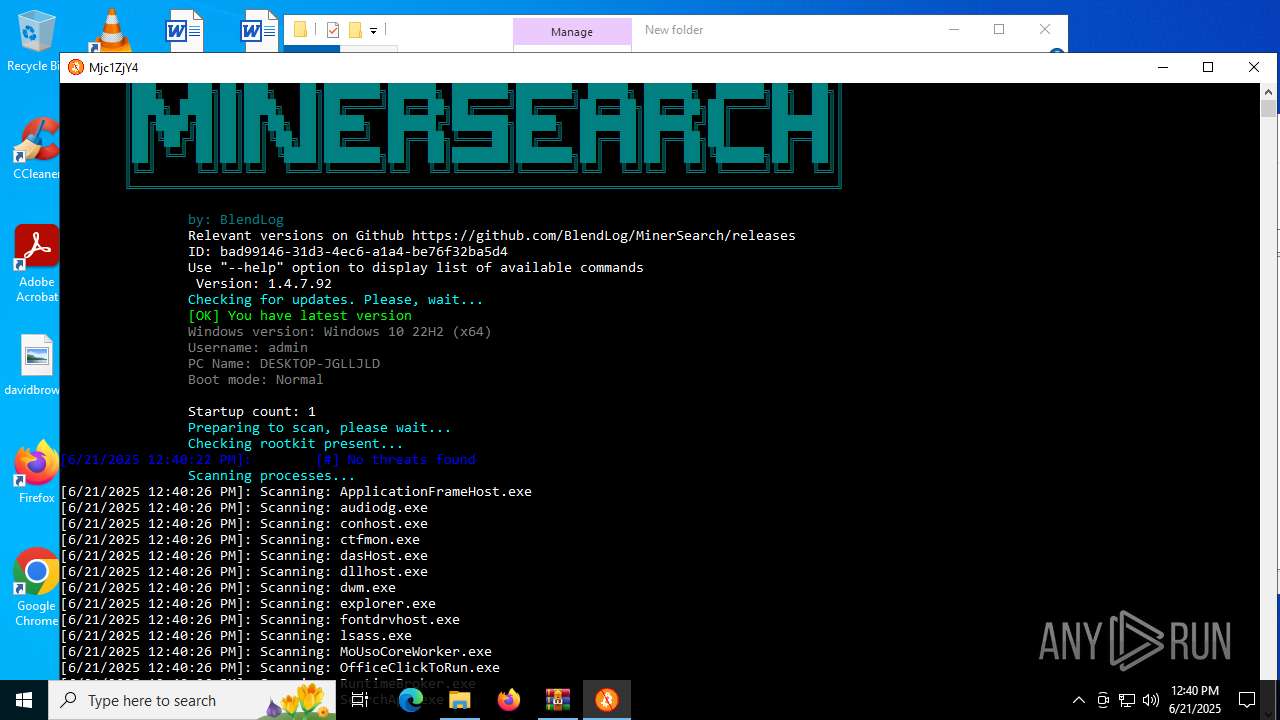
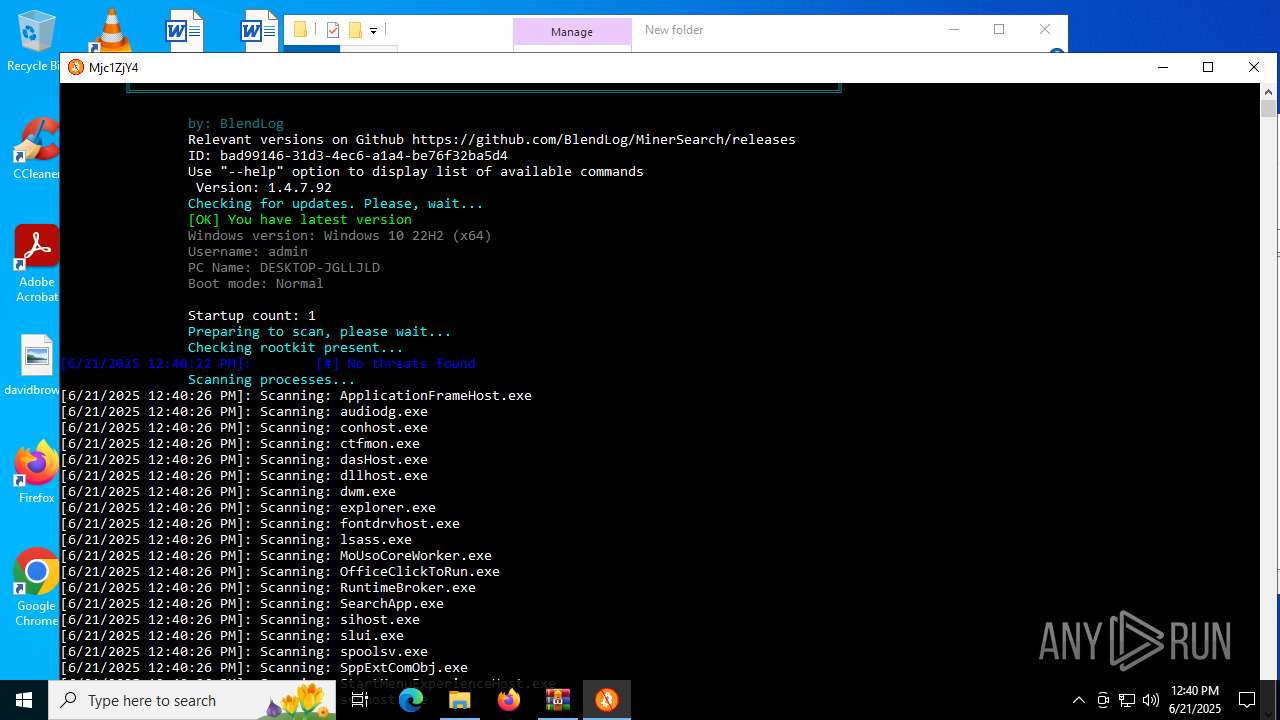
Checks supported languages
- MinerSearch_v1.4.7.92.exe (PID: 3948)
- MinerSearch_v1.4.7.92.exe (PID: 5896)
- MinerSearch_v1.4.7.92.exe (PID: 4216)
Reads the computer name
- MinerSearch_v1.4.7.92.exe (PID: 3948)
- MinerSearch_v1.4.7.92.exe (PID: 5896)
- MinerSearch_v1.4.7.92.exe (PID: 4216)
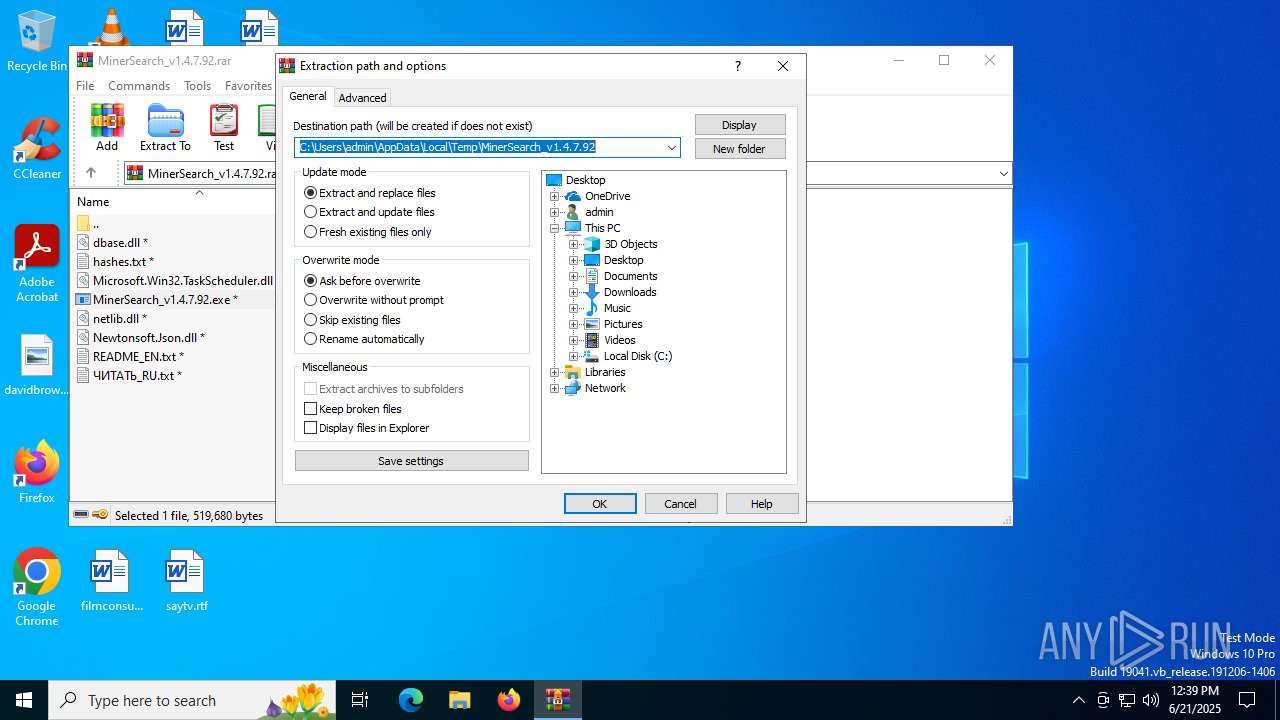
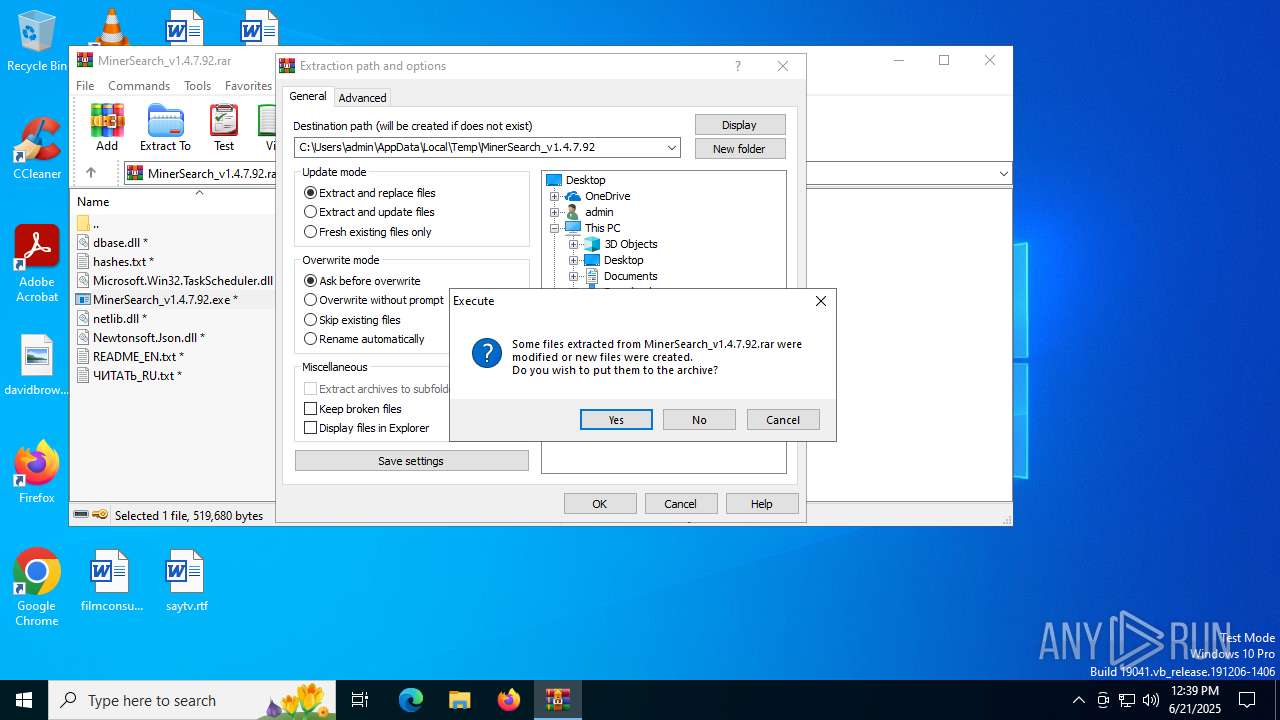
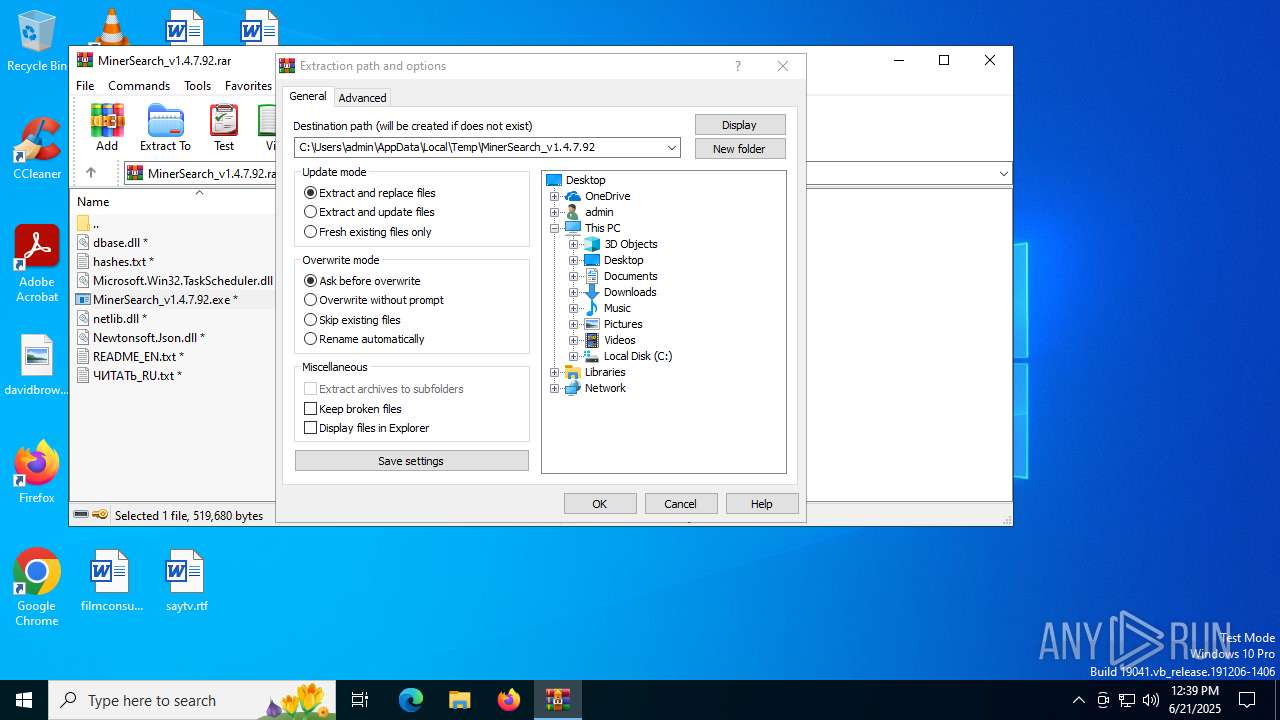
Create files in a temporary directory
- MinerSearch_v1.4.7.92.exe (PID: 3948)
- MinerSearch_v1.4.7.92.exe (PID: 5896)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6612)
Reads the machine GUID from the registry
- MinerSearch_v1.4.7.92.exe (PID: 4216)
- MinerSearch_v1.4.7.92.exe (PID: 5896)
- MinerSearch_v1.4.7.92.exe (PID: 3948)
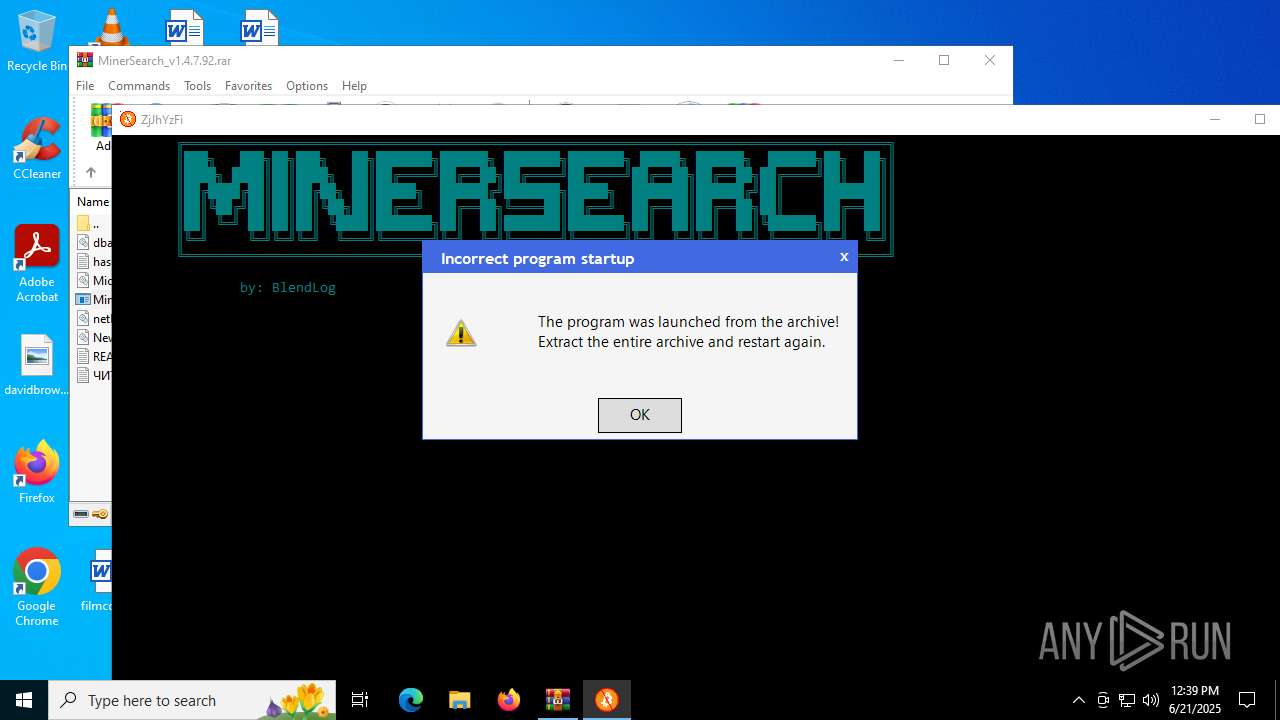
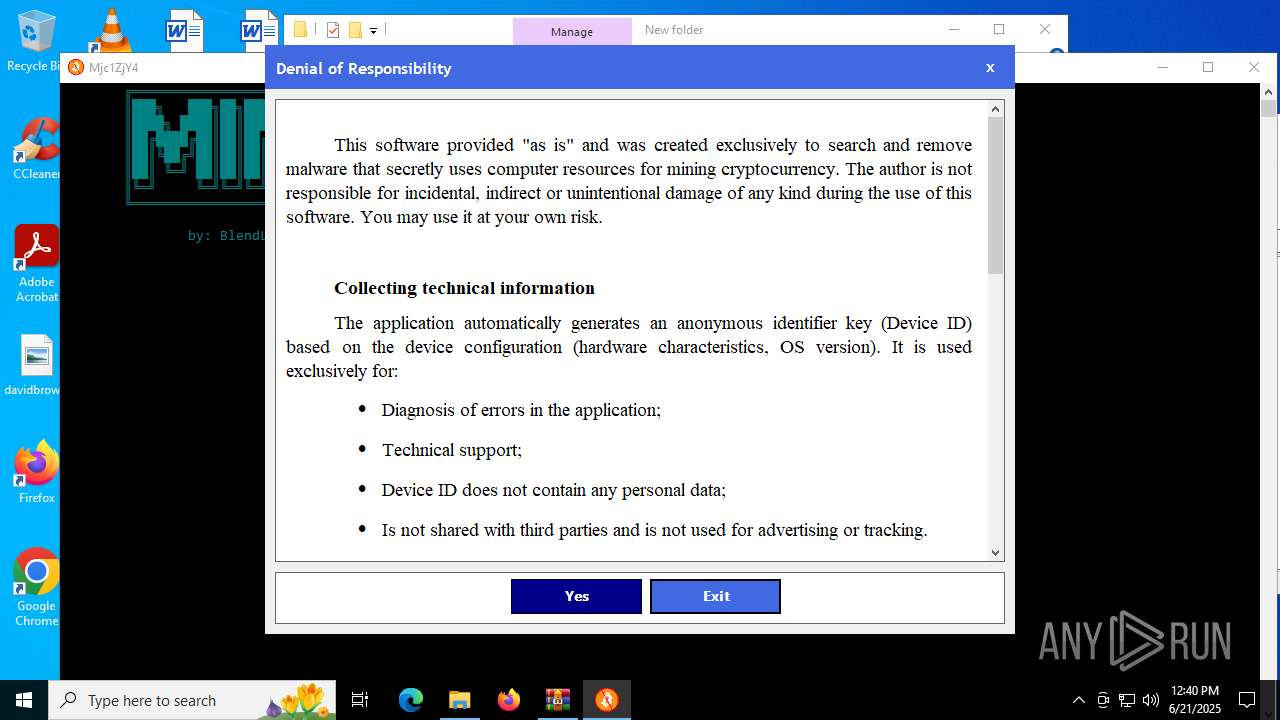
Manual execution by a user
- MinerSearch_v1.4.7.92.exe (PID: 5896)
- MinerSearch_v1.4.7.92.exe (PID: 3672)
- MinerSearch_v1.4.7.92.exe (PID: 4216)
- MinerSearch_v1.4.7.92.exe (PID: 4664)
Reads Environment values
- MinerSearch_v1.4.7.92.exe (PID: 5896)
Checks proxy server information
- MinerSearch_v1.4.7.92.exe (PID: 5896)
Creates files or folders in the user directory
- MinerSearch_v1.4.7.92.exe (PID: 5896)
Disables trace logs
- MinerSearch_v1.4.7.92.exe (PID: 5896)
Reads the software policy settings
- MinerSearch_v1.4.7.92.exe (PID: 5896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
151
Monitored processes
12
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1156 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1964 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | MinerSearch_v1.4.7.92.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
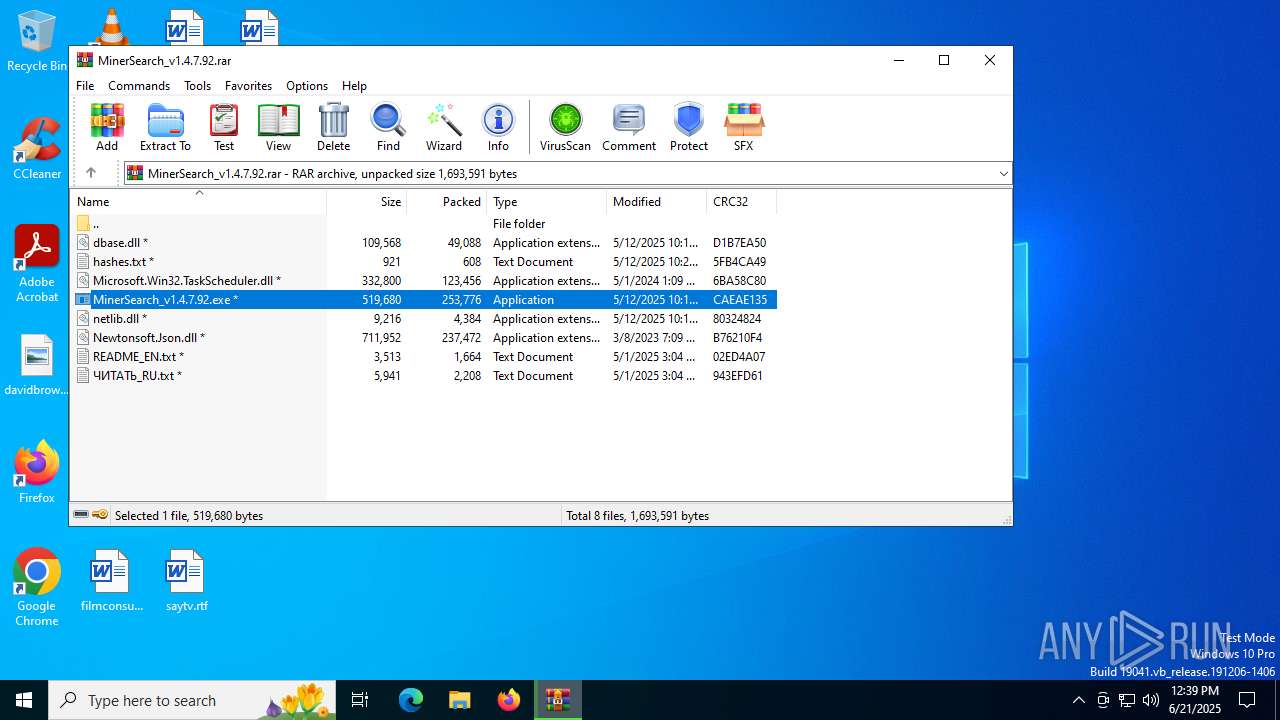
| 3672 | "C:\Users\admin\Desktop\MinerSearch_v1.4.7.92.exe" | C:\Users\admin\Desktop\MinerSearch_v1.4.7.92.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.4.7.92 Modules
| |||||||||||||||
| 3936 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3948 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\MinerSearch_v1.4.7.92.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\MinerSearch_v1.4.7.92.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Version: 1.4.7.92 Modules
| |||||||||||||||
| 4216 | "C:\Users\admin\Desktop\MinerSearch_v1.4.7.92.exe" | C:\Users\admin\Desktop\MinerSearch_v1.4.7.92.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Version: 1.4.7.92 Modules
| |||||||||||||||
| 4512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | MinerSearch_v1.4.7.92.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
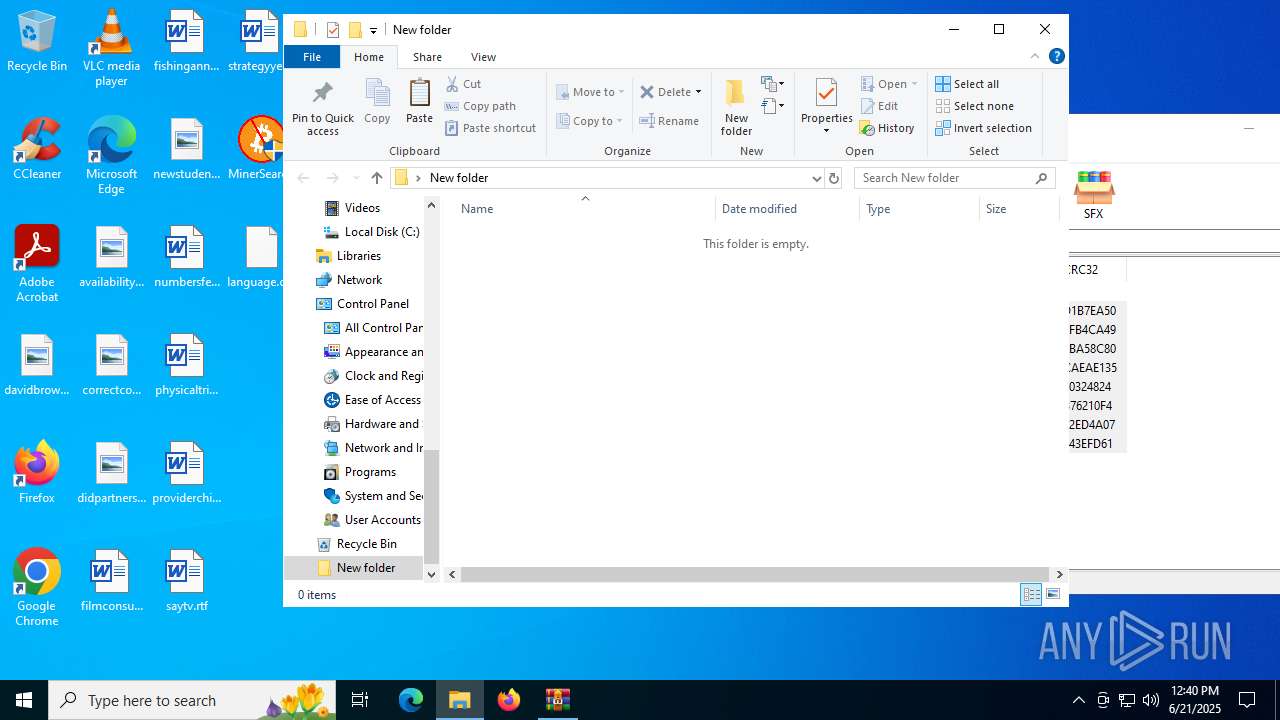
| 4664 | "C:\Users\admin\Desktop\New folder\MinerSearch_v1.4.7.92.exe" | C:\Users\admin\Desktop\New folder\MinerSearch_v1.4.7.92.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.4.7.92 Modules
| |||||||||||||||
| 5504 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | MinerSearch_v1.4.7.92.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5612 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\MinerSearch_v1.4.7.92.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\MinerSearch_v1.4.7.92.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.4.7.92 Modules
| |||||||||||||||
Total events
40 566
Read events
40 515
Write events
33
Delete events
18
Modification events
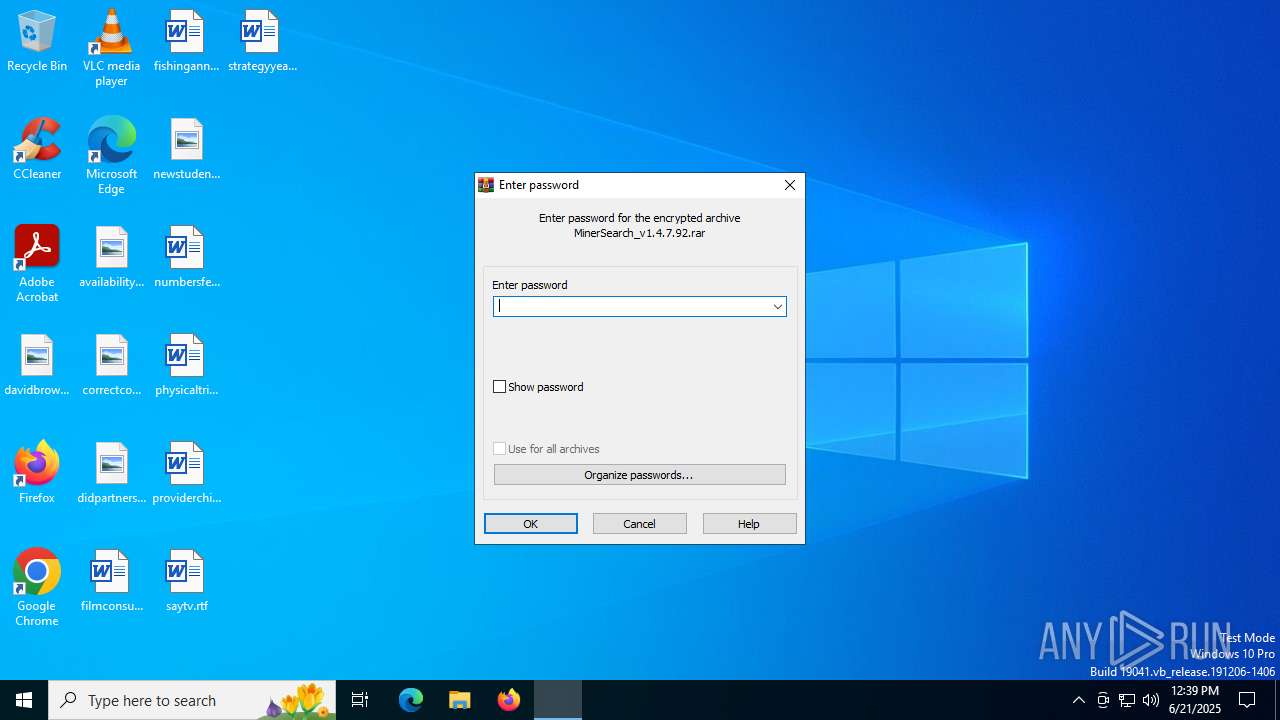
| (PID) Process: | (6612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MinerSearch_v1.4.7.92.rar | |||
| (PID) Process: | (6612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
Executable files
16
Suspicious files
107
Text files
15
Unknown types
0
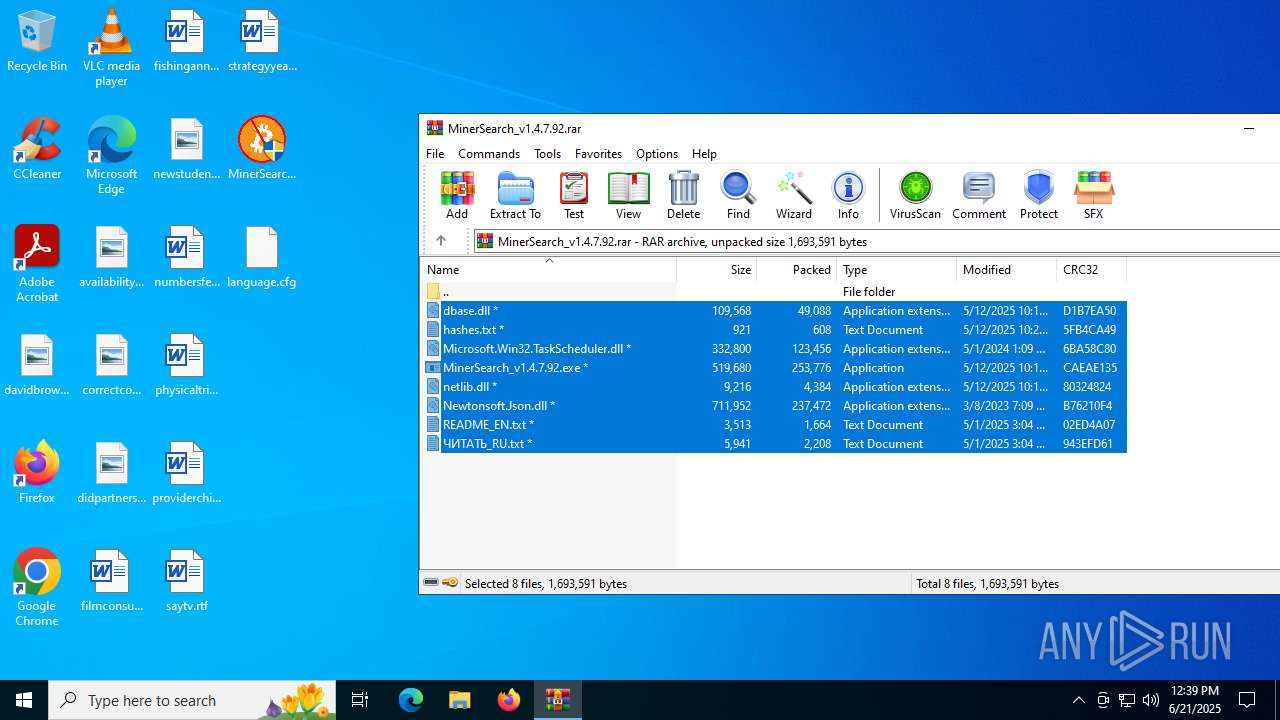
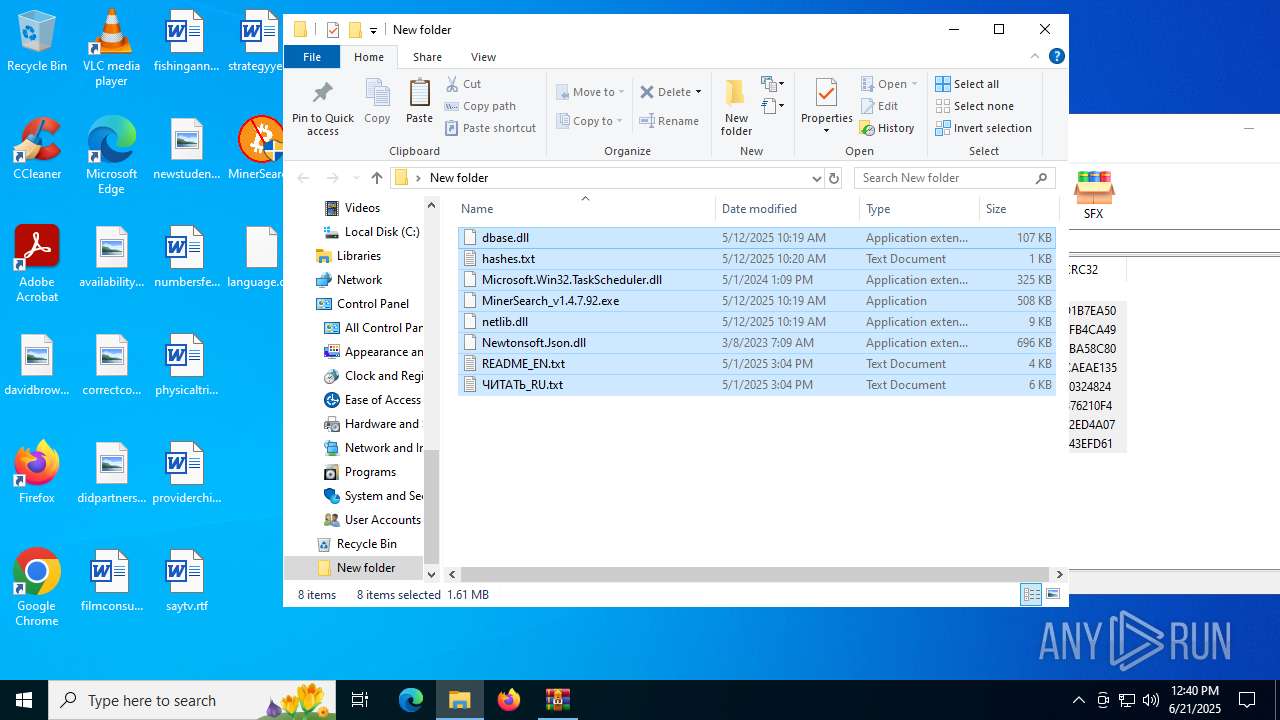
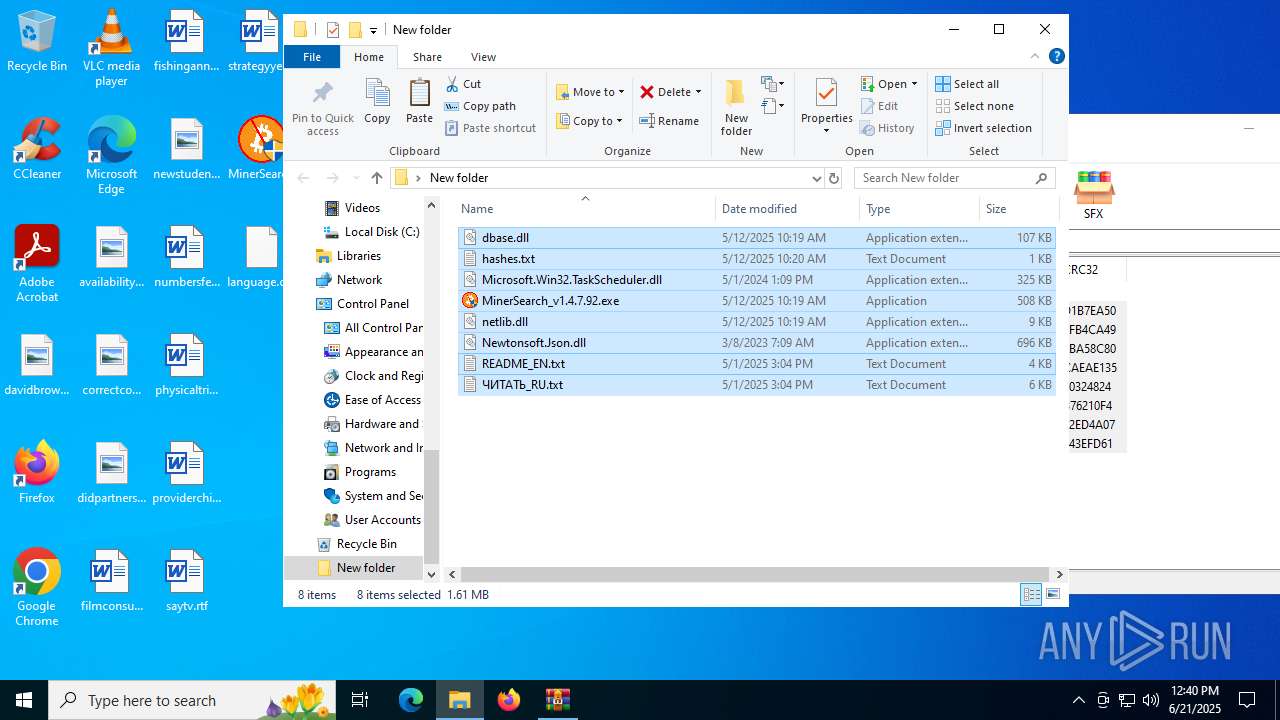
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
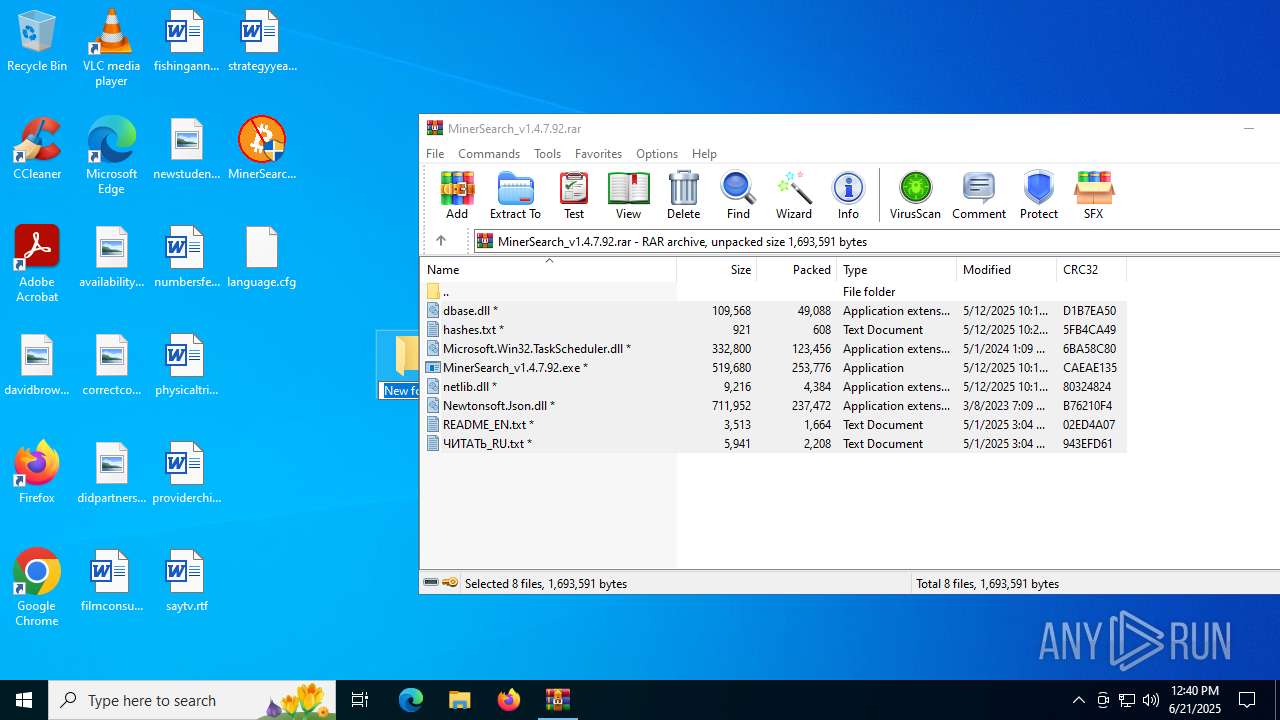
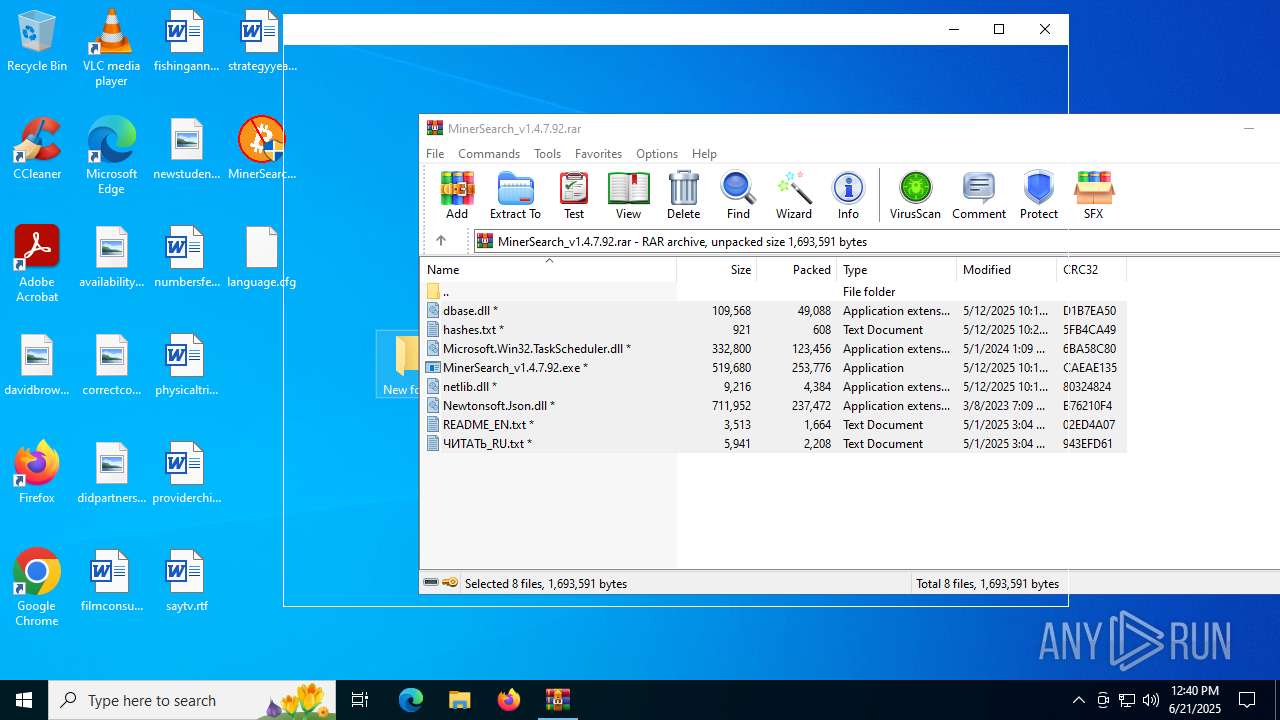
| 6612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\hashes.txt | text | |
MD5:AA77D510E830A7B6458D2BE5EC01786A | SHA256:F5D2A9836C9B8C34D9A4DDDCAF2AE7885B4AB6D041A90E689C84A104D94B28FE | |||
| 6612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\Microsoft.Win32.TaskScheduler.dll | executable | |
MD5:0616EA42B68A8F5F2F01BCD985BDCBC7 | SHA256:EA27C65491119EEE5C8E87CE3D470783580DB8FC5BD141C496768D7D0CCE779A | |||
| 6612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\netlib.dll | executable | |
MD5:73D9917B2F80BA39BE6FDB4F14385E31 | SHA256:5B40204B7210465020BF6DAF50D7CB8E3DD1FDD04664CD4D8D58EBAC27512F60 | |||
| 6612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\README_EN.txt | text | |
MD5:1EB9809AE2D11B34E3E8E5EEB28CD222 | SHA256:E494BEBA042F9723A532F4D40B9605D979162A8919492B0963A5928C9DC71F67 | |||
| 6612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\MinerSearch_v1.4.7.92.exe | executable | |
MD5:58062228F5E6019E49DA9AD901D36505 | SHA256:F82A89AD4FE38A780D308D26AC994445CD38EC58B5937F8BB034EF85128DA1F8 | |||
| 6612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
| 6612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\dbase.dll | executable | |
MD5:99CFCC6EDBD535BF6C971EA894288C6A | SHA256:23108B64B3D269F44549E18EB2670314FFF544289B13BFCFA8DEA9CEA7A2727C | |||
| 4216 | MinerSearch_v1.4.7.92.exe | C:\_MinerSearchLogs\MinerSearch_6_21_2025_12-39-56_PM.log | text | |
MD5:147AABBF0F65A7AAAF326C8E310FD2B6 | SHA256:D26BFD96D8D7C71F554DC302FDF44AEFE5B17139795D029D17E97FB233674FBB | |||
| 6612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6612.41043\dbase.dll | executable | |
MD5:99CFCC6EDBD535BF6C971EA894288C6A | SHA256:23108B64B3D269F44549E18EB2670314FFF544289B13BFCFA8DEA9CEA7A2727C | |||
| 6612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6612.39068\ЧИТАТЬ_RU.txt | text | |
MD5:B308D8633D1ED8A129A4C63C238E3AC4 | SHA256:5F8166625B4155BB0A00C75C6E0E4B59324CFCD16D90FDA407AFE6726FBDD509 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
70
TCP/UDP connections
37
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2464 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6876 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6876 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5896 | MinerSearch_v1.4.7.92.exe | GET | 200 | 184.24.77.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5896 | MinerSearch_v1.4.7.92.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
5896 | MinerSearch_v1.4.7.92.exe | GET | 200 | 184.24.77.14:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_2010-07-06.crl | unknown | — | — | whitelisted |
5896 | MinerSearch_v1.4.7.92.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | — | — | whitelisted |
5896 | MinerSearch_v1.4.7.92.exe | GET | 200 | 184.24.77.14:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3584 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2464 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2464 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 184.24.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |