| URL: | https://flowcode.com/p/m7i5gemhy |
| Full analysis: | https://app.any.run/tasks/f4701d99-c0d8-4437-a934-e2977f10afe0 |
| Verdict: | Malicious activity |
| Analysis date: | March 06, 2024, 05:11:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2B37275C67F975BD127241420A579114 |
| SHA1: | 23A6F8FB11F0FBC8F5E66B5E26AA478B53F011D5 |
| SHA256: | C93A773F37CB5C0CF025CA2E039C9A9A54E75909F0576ABEAFF2463484EA02D6 |
| SSDEEP: | 3:N8O15VKUdO:2k+P |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3652 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://flowcode.com/p/m7i5gemhy" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3892 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3652 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
21 374
Read events
21 236
Write events
95
Delete events
43
Modification events
| (PID) Process: | (3652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31092612 | |||
| (PID) Process: | (3652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31092612 | |||
| (PID) Process: | (3652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
17
Text files
10
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:3CCD6C3C962B5CEB29C5E3126F97D43C | SHA256:275EBBB63332B4F0979A98354EFFE85F5BA10461BA8EB49C71AED9233788DCC0 | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | der | |
MD5:5AE8478AF8DD6EEC7AD4EDF162DD3DF1 | SHA256:FE42AC92EAE3B2850370B73C3691CCF394C23AB6133DE39F1697A6EBAC4BEDCA | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFAED.tmp | cat | |
MD5:DD73CEAD4B93366CF3465C8CD32E2796 | SHA256:A6752B7851B591550E4625B832A393AABCC428DE18D83E8593CD540F7D7CAE22 | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:2C71A6F8EAEA91770C510F060A0228FA | SHA256:DFEF9396F1A986D5D8441601C03483AE14B7B352F517B07071F351B5025A85F5 | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\cx.vb[1].htm | html | |
MD5:D107C08CA1C0F063078932B0D16B44C6 | SHA256:C1180B2B0F55C86AC82D233007B0E3109CC813785EB154E83AD61A58C4FF297C | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFAEA.tmp | compressed | |
MD5:753DF6889FD7410A2E9FE333DA83A429 | SHA256:B42DC237E44CBC9A43400E7D3F9CBD406DBDEFD62BFE87328F8663897D69DF78 | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:6F6DCD1D4CB2E712C3B1FF4D72289855 | SHA256:60325860832079B7E72B92ADFA82F0ADCB304706CA1FCF738BE53F97DAB2BF1E | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:3416A7E9276515A5E899EBD477EA0F95 | SHA256:748EB1E10710A0E792DBF28BE7F24989EEA0E6685BD69B9C46DAEC08F5F26038 | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:D480D43D8178C6571BD07C164334130C | SHA256:5CEB65109B728185DD7D50759EEA68D0A7AC0100D35586FAE9A698ED6F9C446C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
32
DNS requests
18
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3892 | iexplore.exe | GET | 304 | 87.248.204.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bd117e088266f0f9 | unknown | — | — | unknown |
3892 | iexplore.exe | GET | 304 | 87.248.204.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | unknown | — | — | unknown |
3892 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
3892 | iexplore.exe | GET | 200 | 87.248.204.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a08f35fbea17b647 | unknown | compressed | 67.5 Kb | unknown |
3892 | iexplore.exe | GET | 200 | 87.248.204.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b150b552b216e1f4 | unknown | compressed | 67.5 Kb | unknown |
3892 | iexplore.exe | GET | 200 | 23.35.209.170:80 | http://x2.c.lencr.org/ | unknown | binary | 299 b | unknown |
3892 | iexplore.exe | GET | 200 | 23.35.209.170:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
3892 | iexplore.exe | GET | 200 | 23.200.147.9:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQpb30u8dVcEqSAiIX%2FRhQWLg%3D%3D | unknown | binary | 503 b | unknown |
3652 | iexplore.exe | GET | 304 | 87.248.204.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?96c8eb5dfc595a04 | unknown | — | — | unknown |
3892 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | binary | 1.42 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3892 | iexplore.exe | 104.18.42.158:443 | flowcode.com | CLOUDFLARENET | — | shared |
3892 | iexplore.exe | 87.248.204.0:80 | ctldl.windowsupdate.com | LLNW | US | unknown |
3892 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
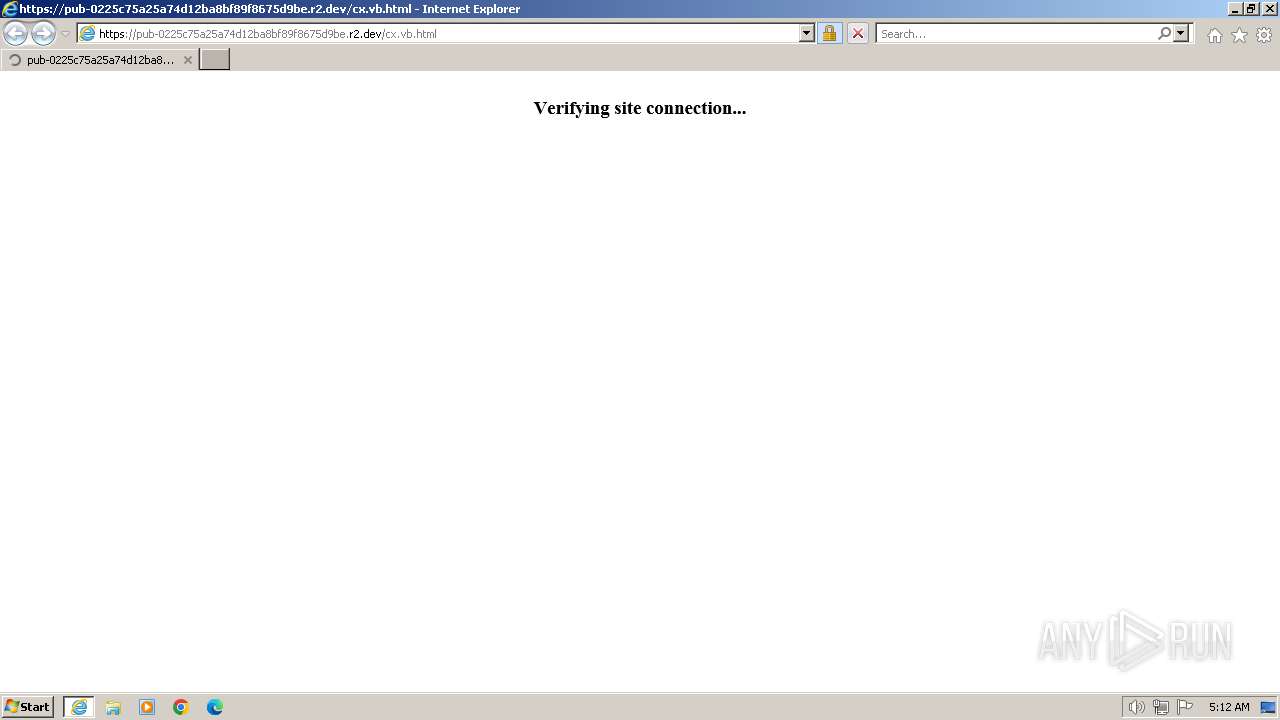
3892 | iexplore.exe | 104.18.2.35:443 | pub-0225c75a25a74d12ba8bf89f8675d9be.r2.dev | CLOUDFLARENET | — | unknown |
3892 | iexplore.exe | 23.35.209.170:80 | x1.c.lencr.org | AKAMAI-AS | CA | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3892 | iexplore.exe | 104.17.2.184:443 | challenges.cloudflare.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
flowcode.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
pub-0225c75a25a74d12ba8bf89f8675d9be.r2.dev |
| unknown |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
seofty.com |
| unknown |
r3.o.lencr.org |
| shared |
code.jquery.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3892 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Public R2.dev Bucket Abuse to Phishing in TLS (Greatness) |
3892 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
3892 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
3892 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |