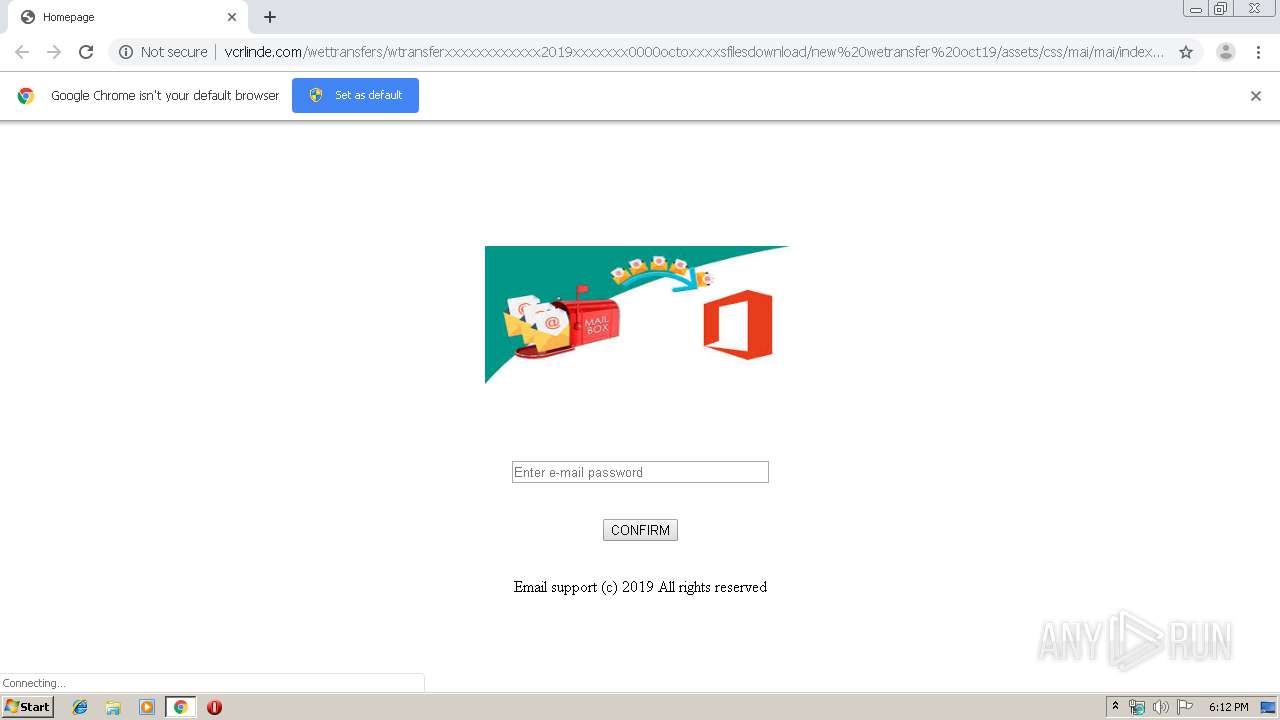
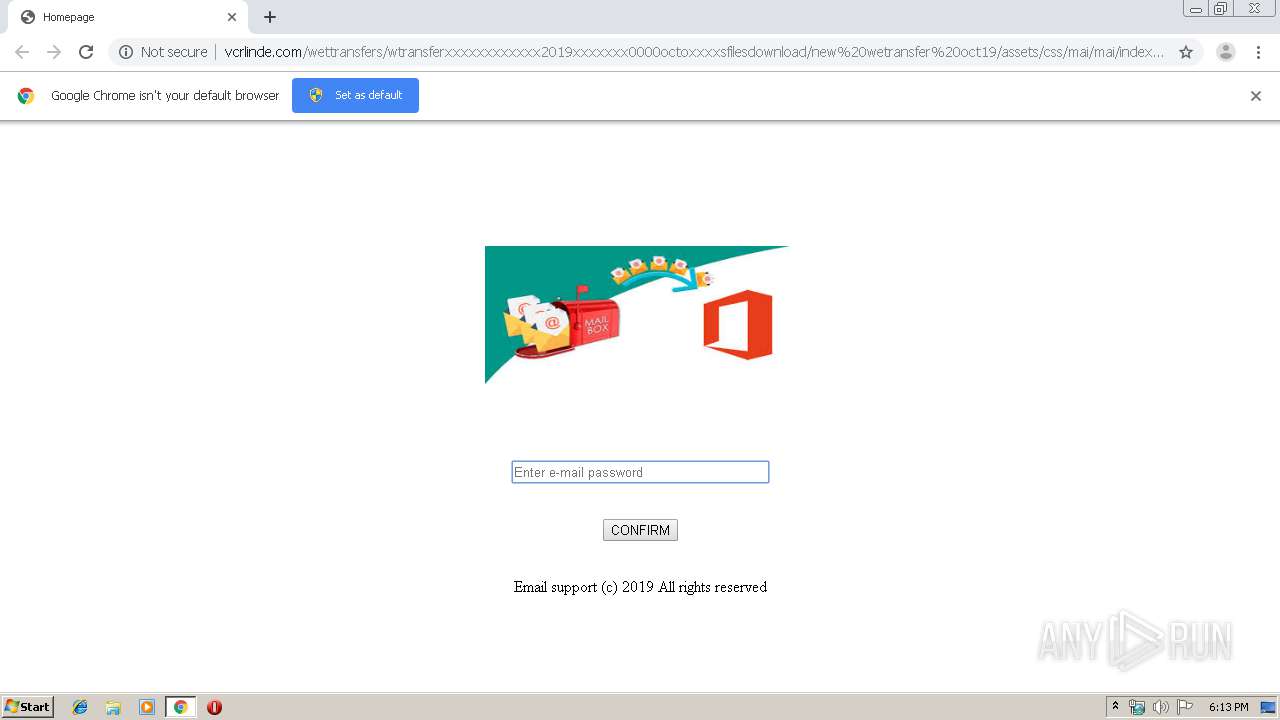
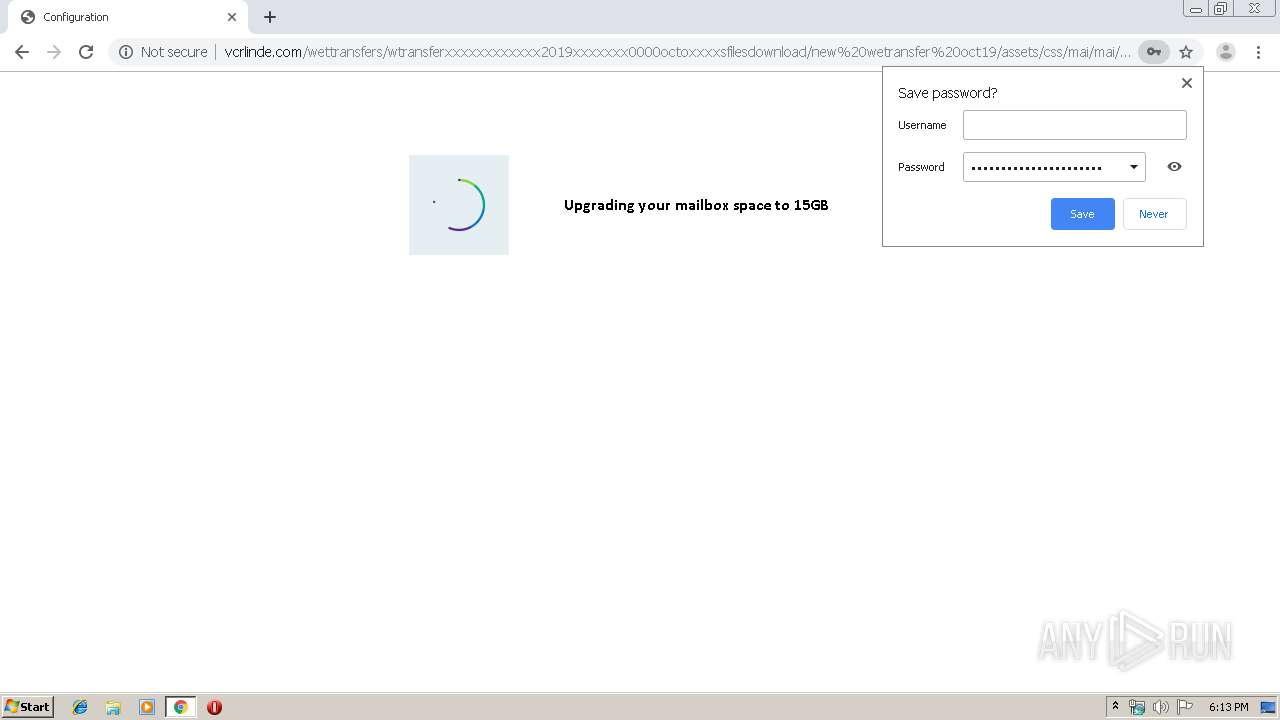
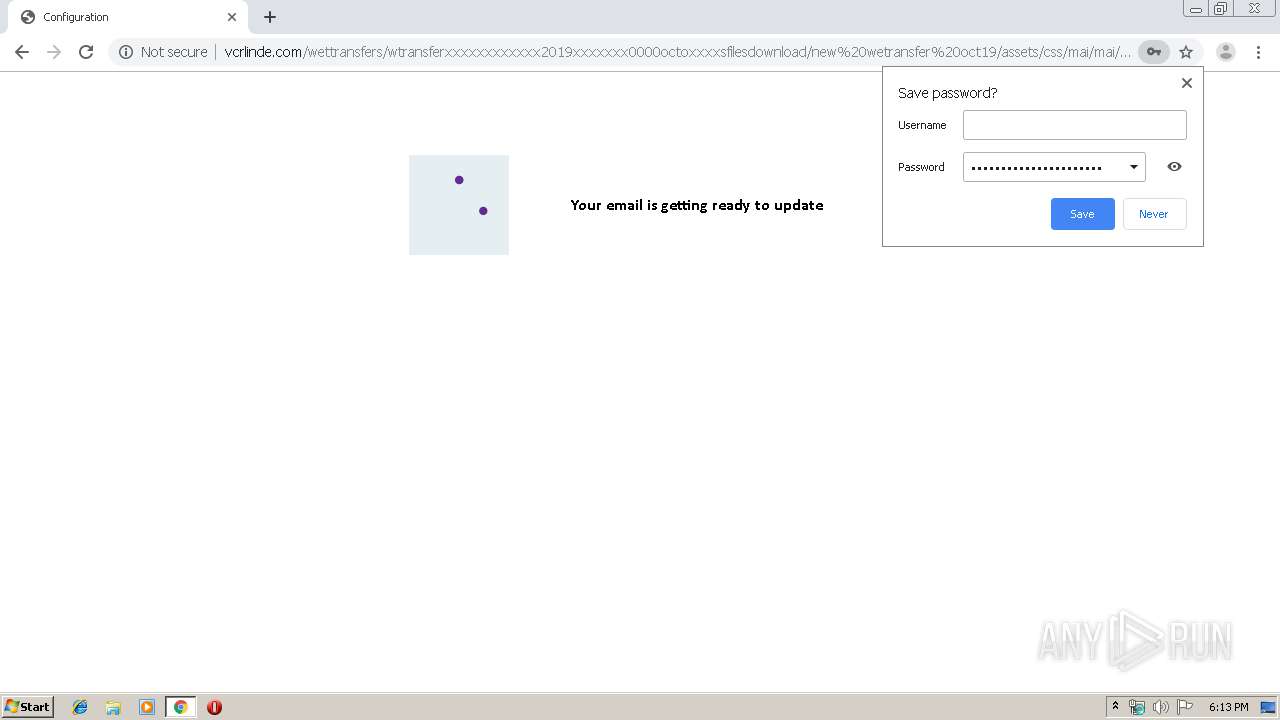
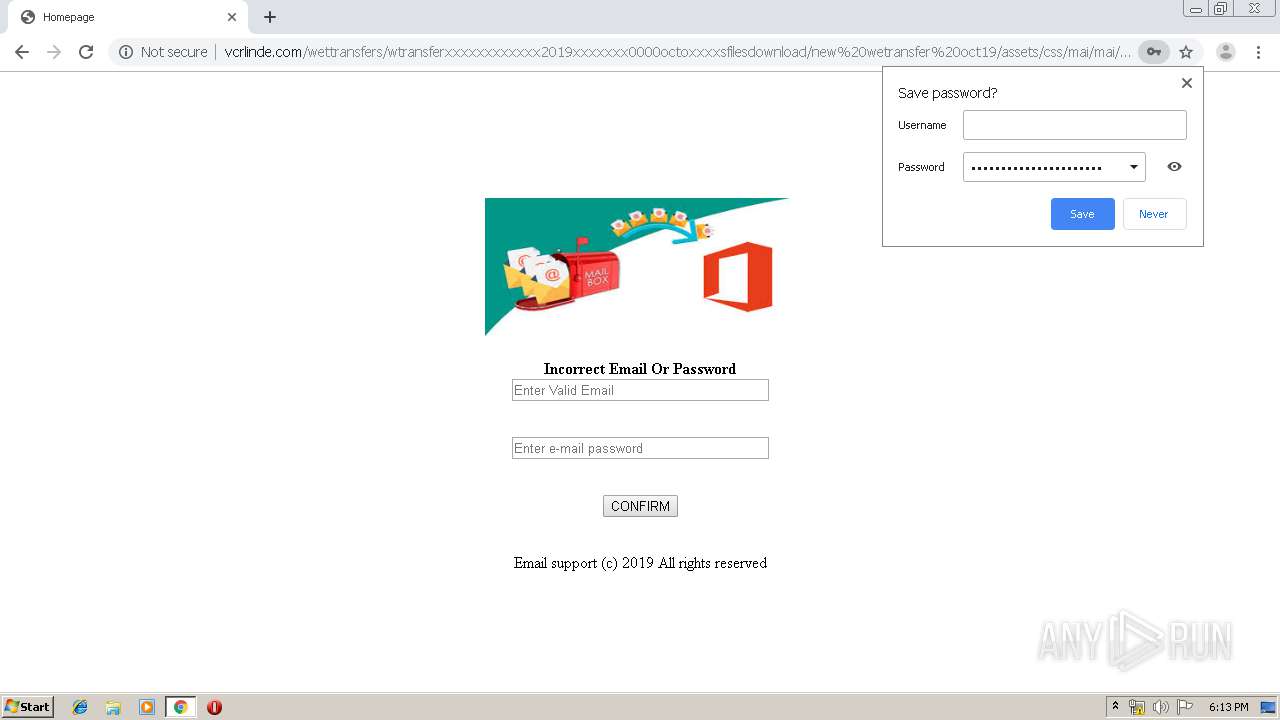
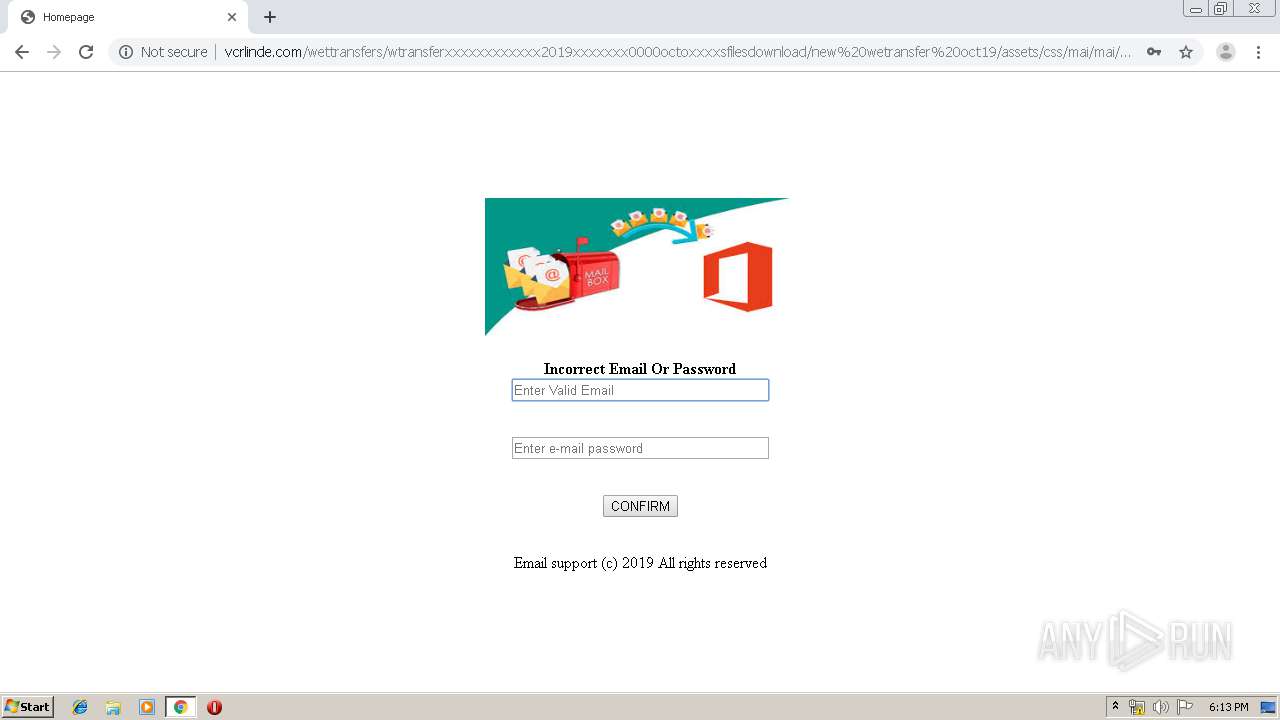
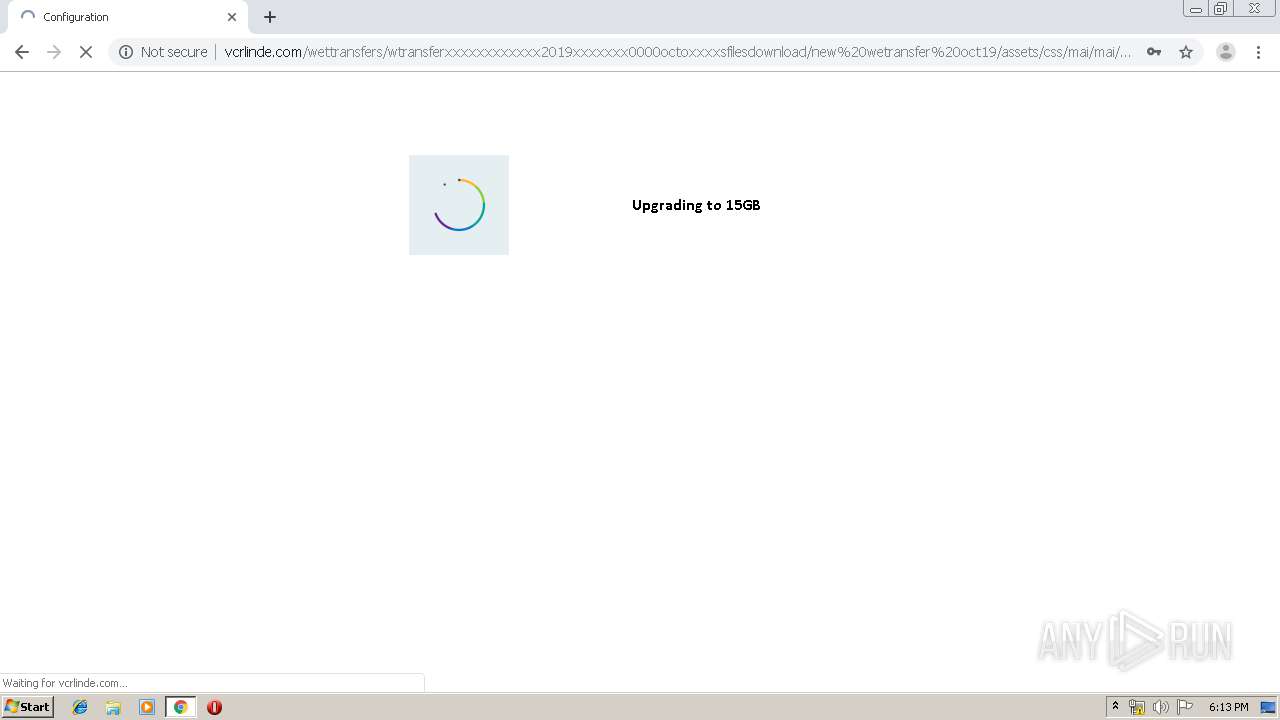
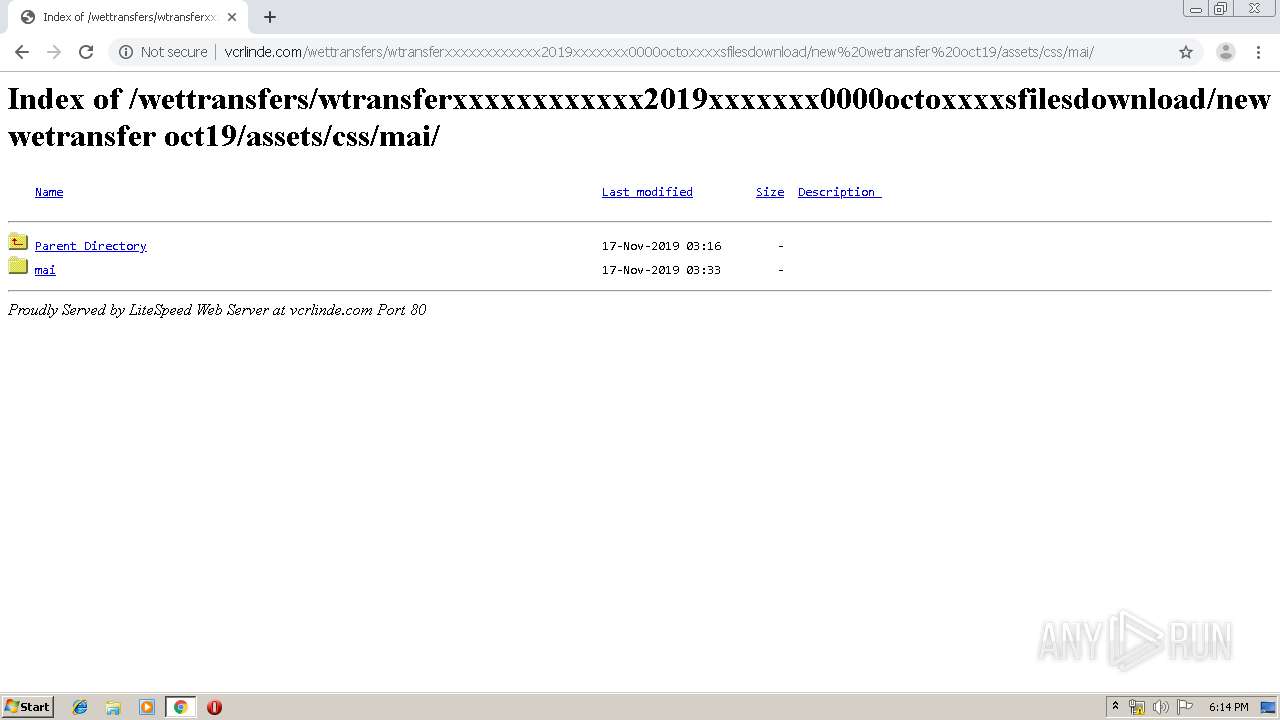
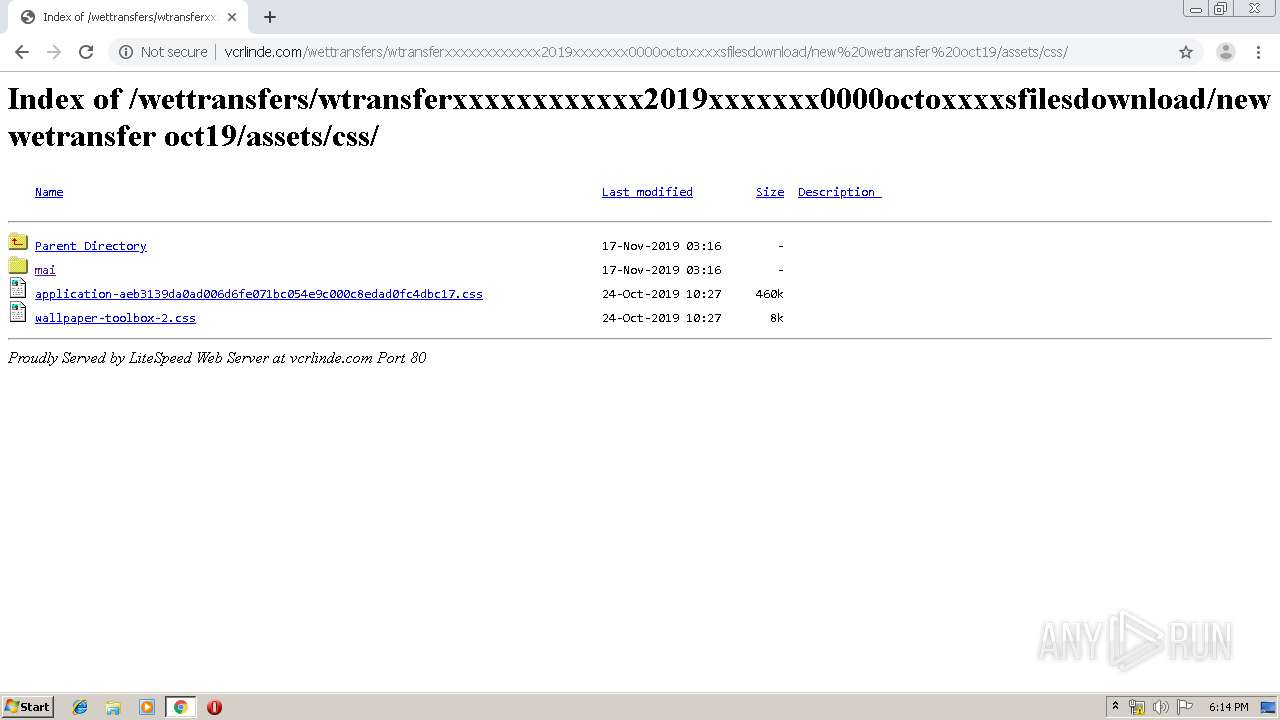
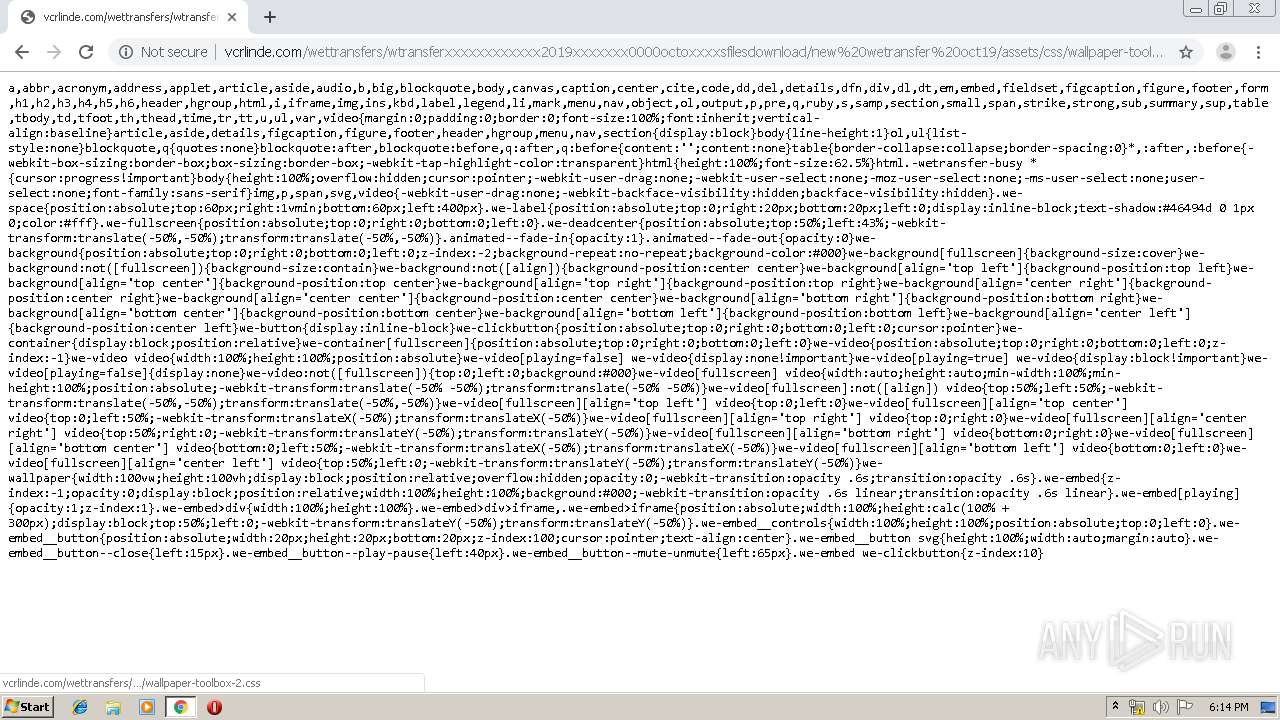
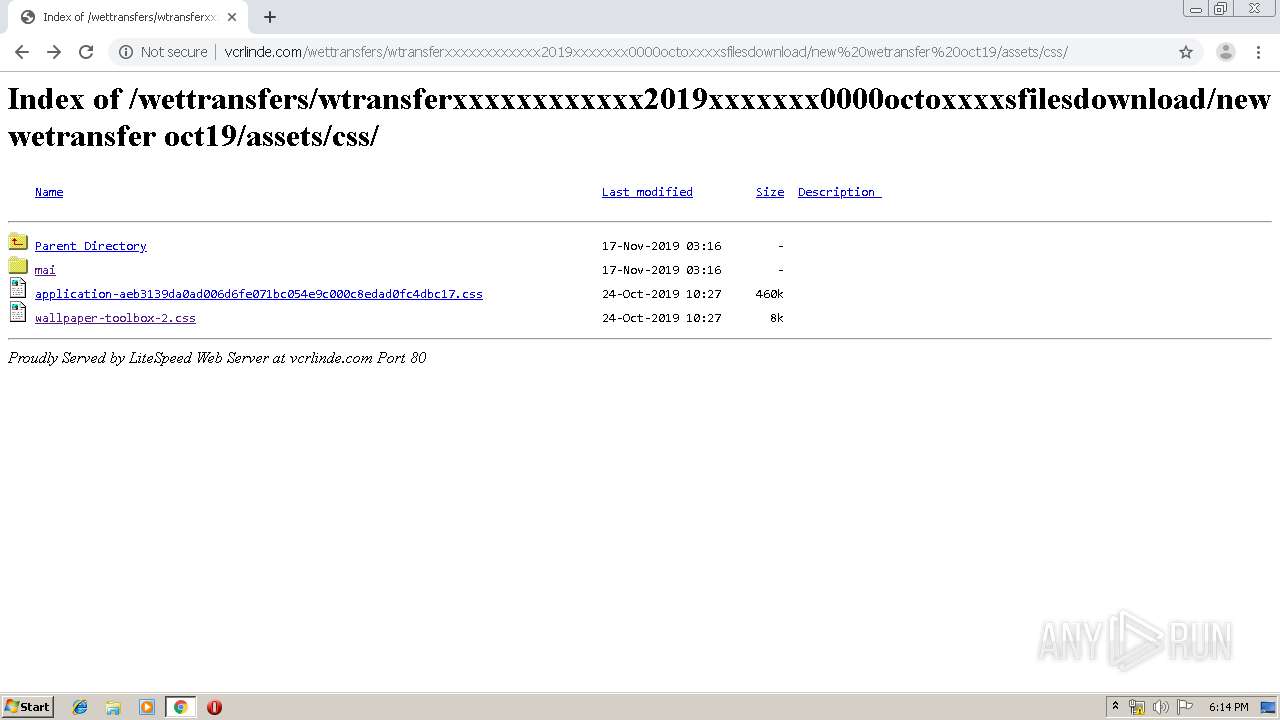
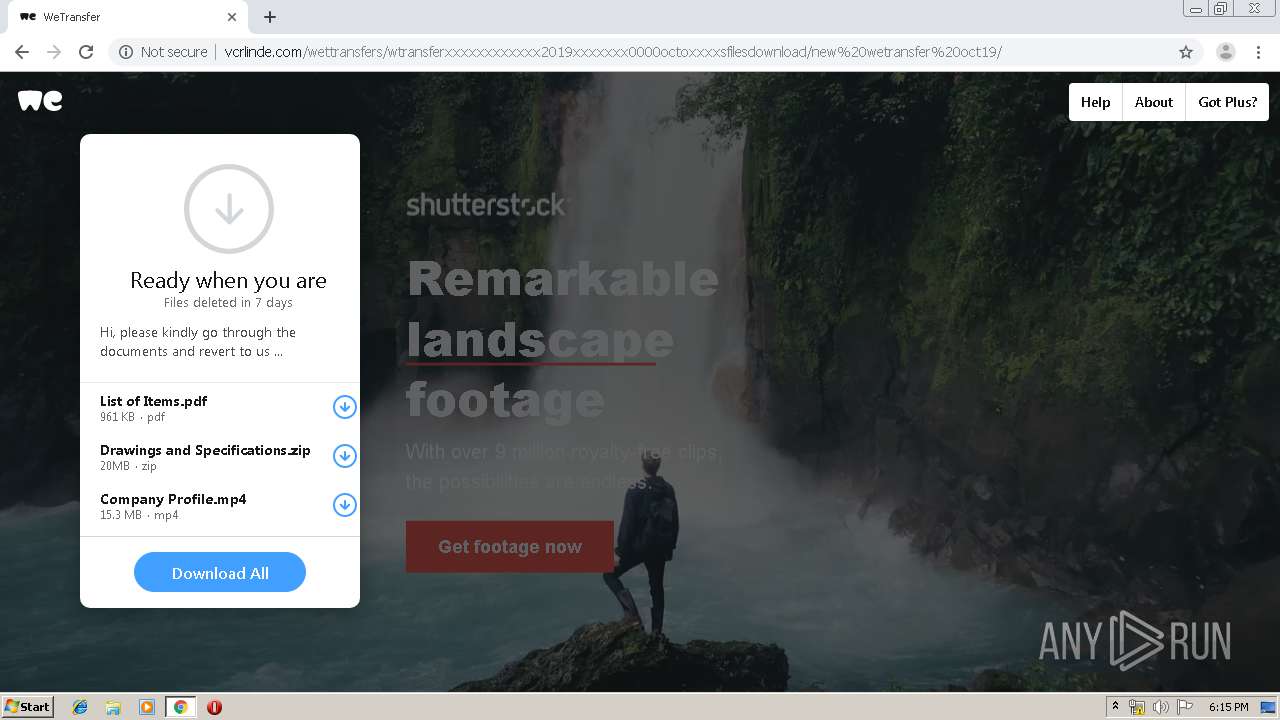
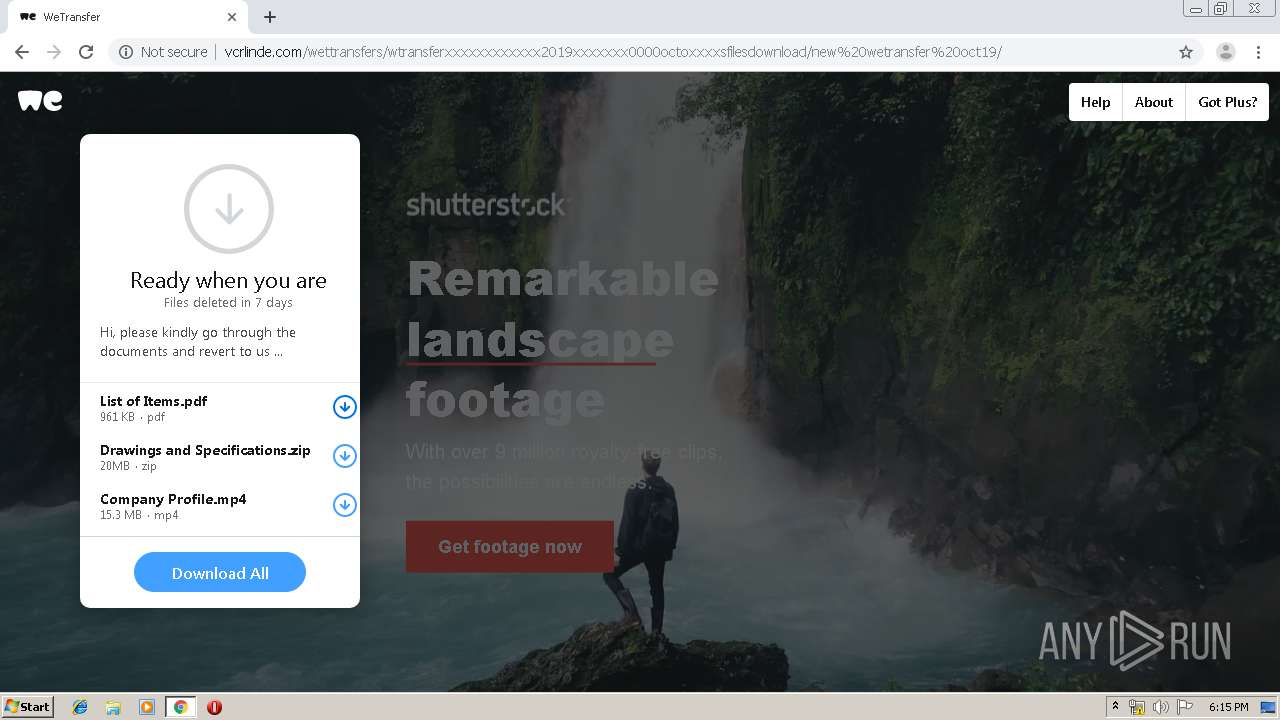
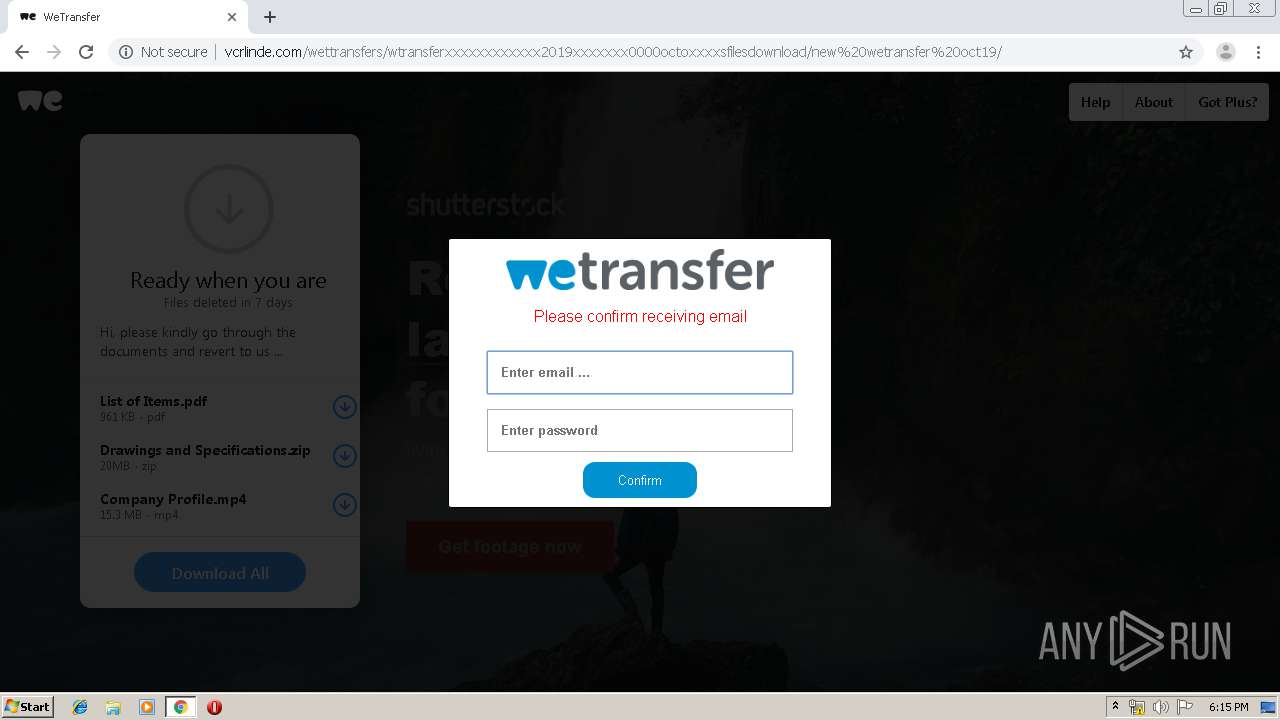
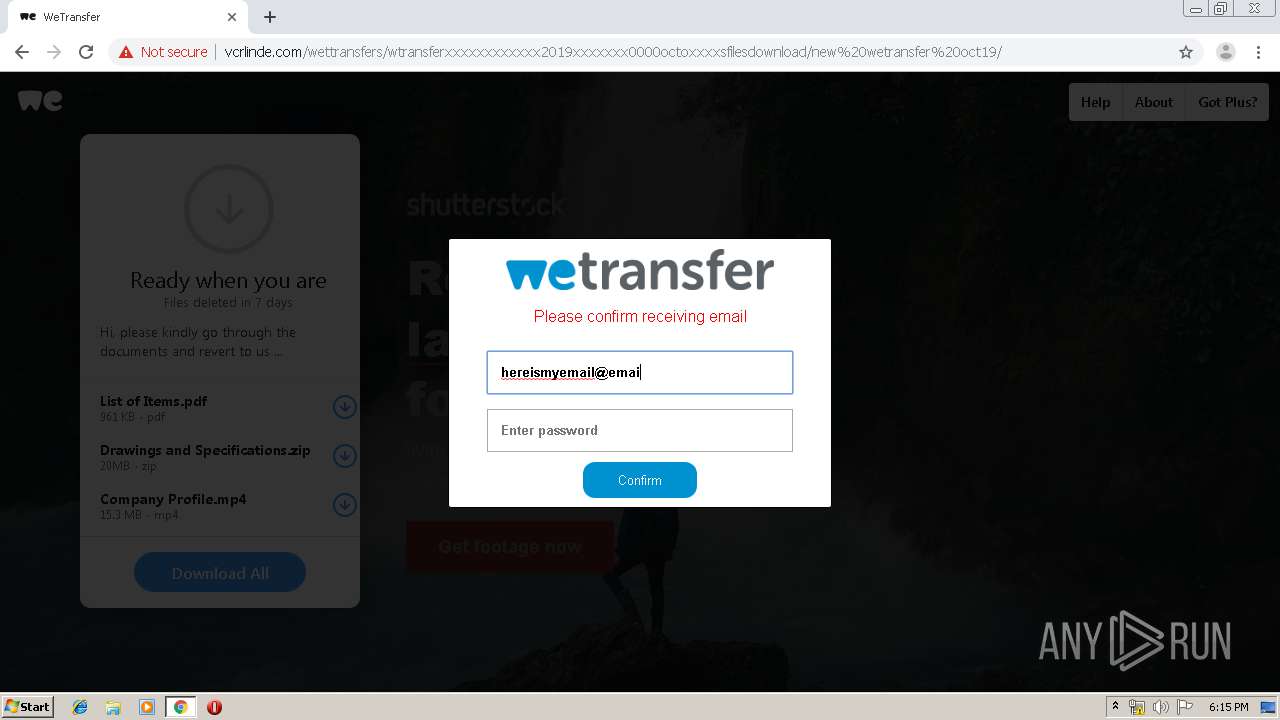
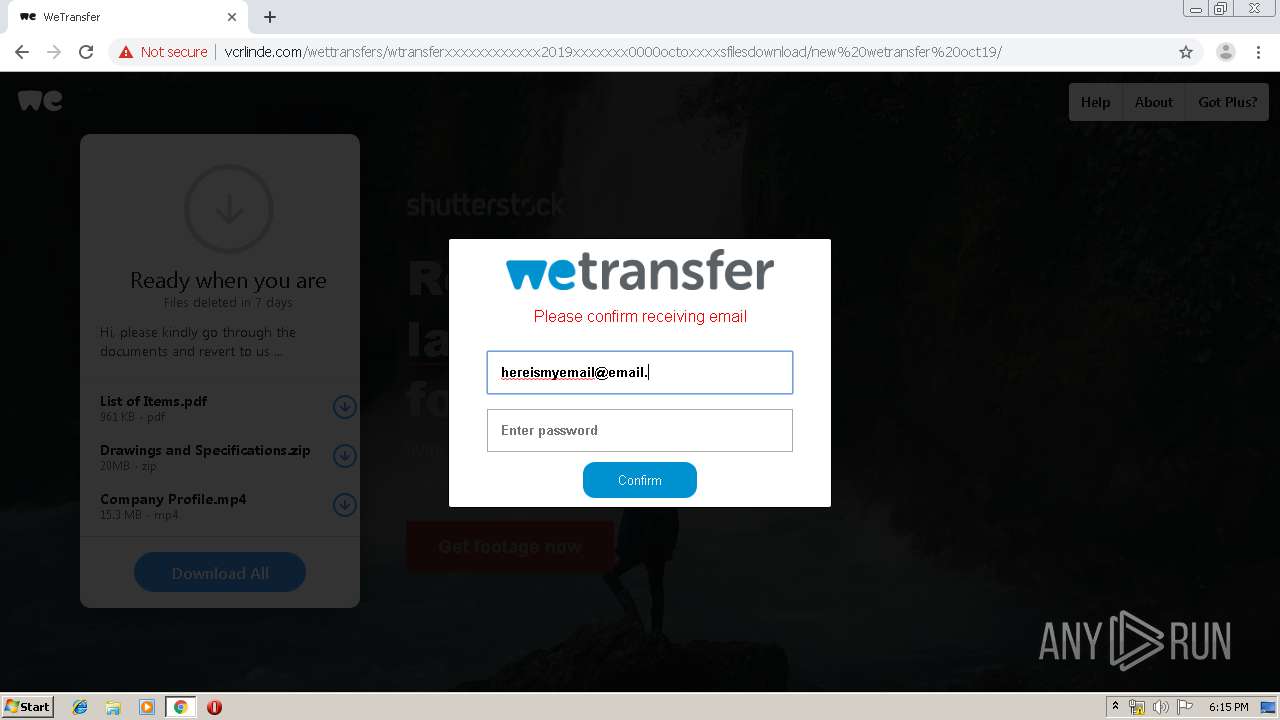
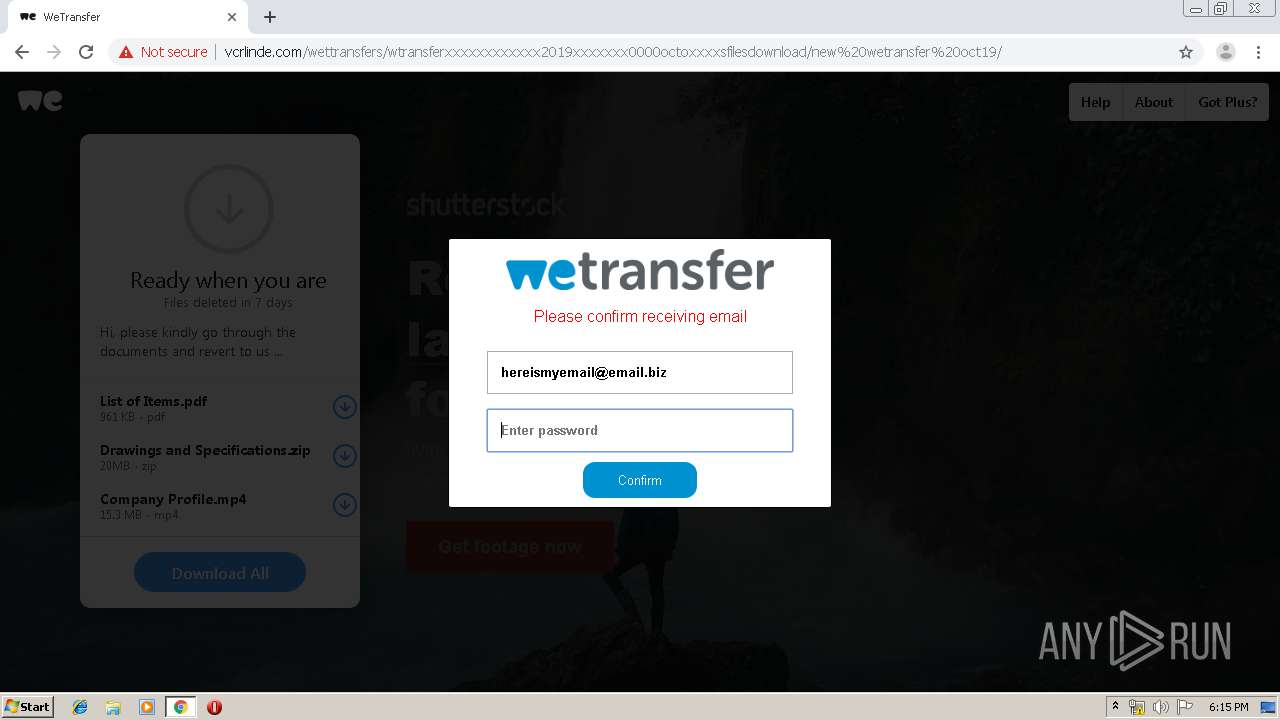
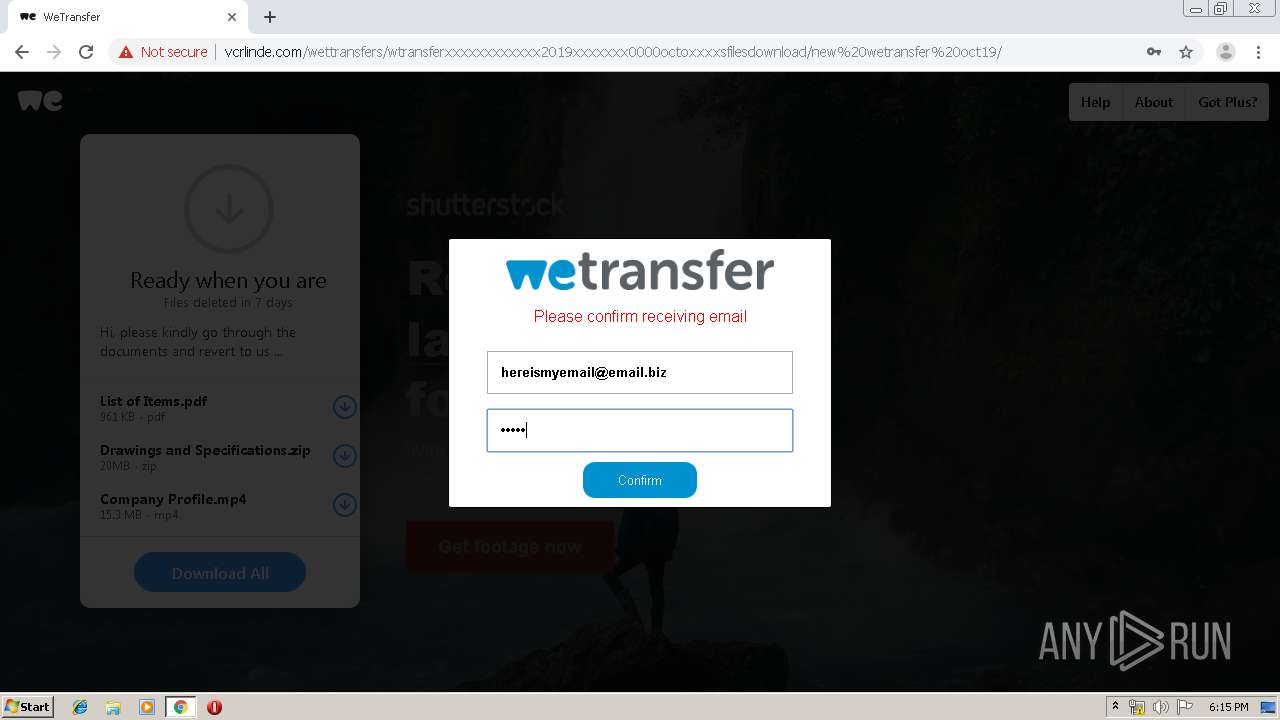
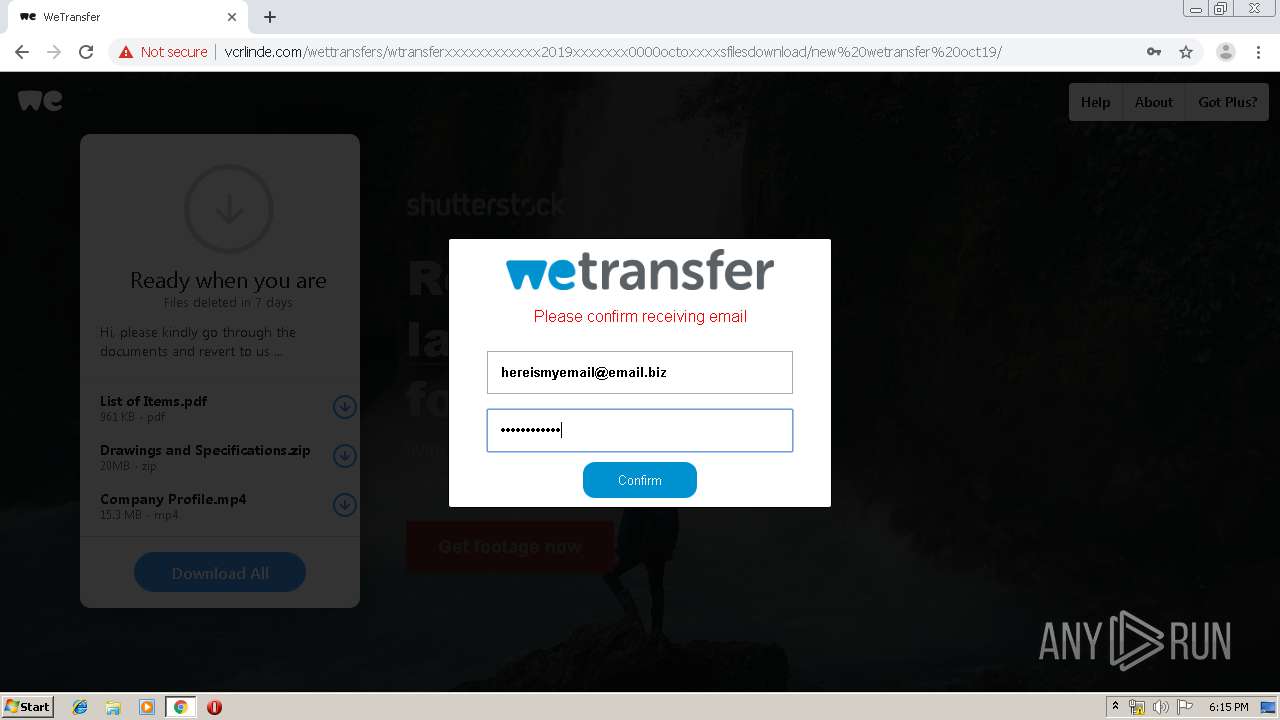
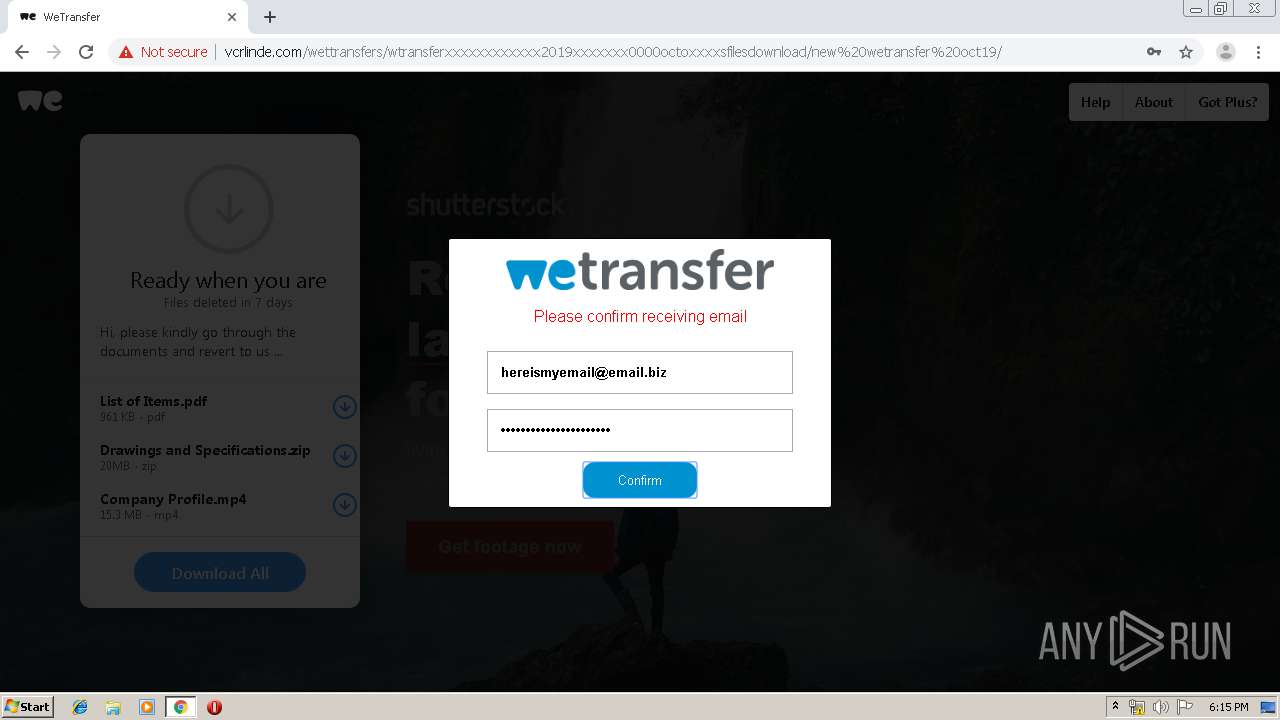
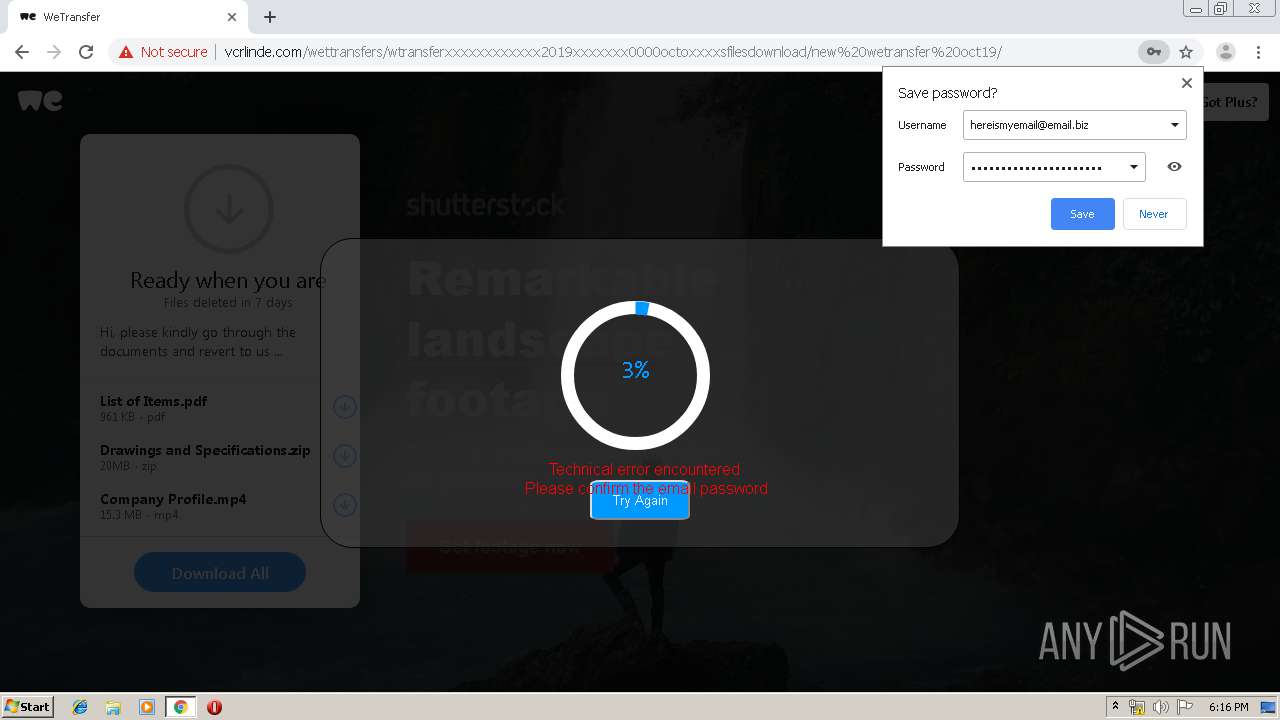
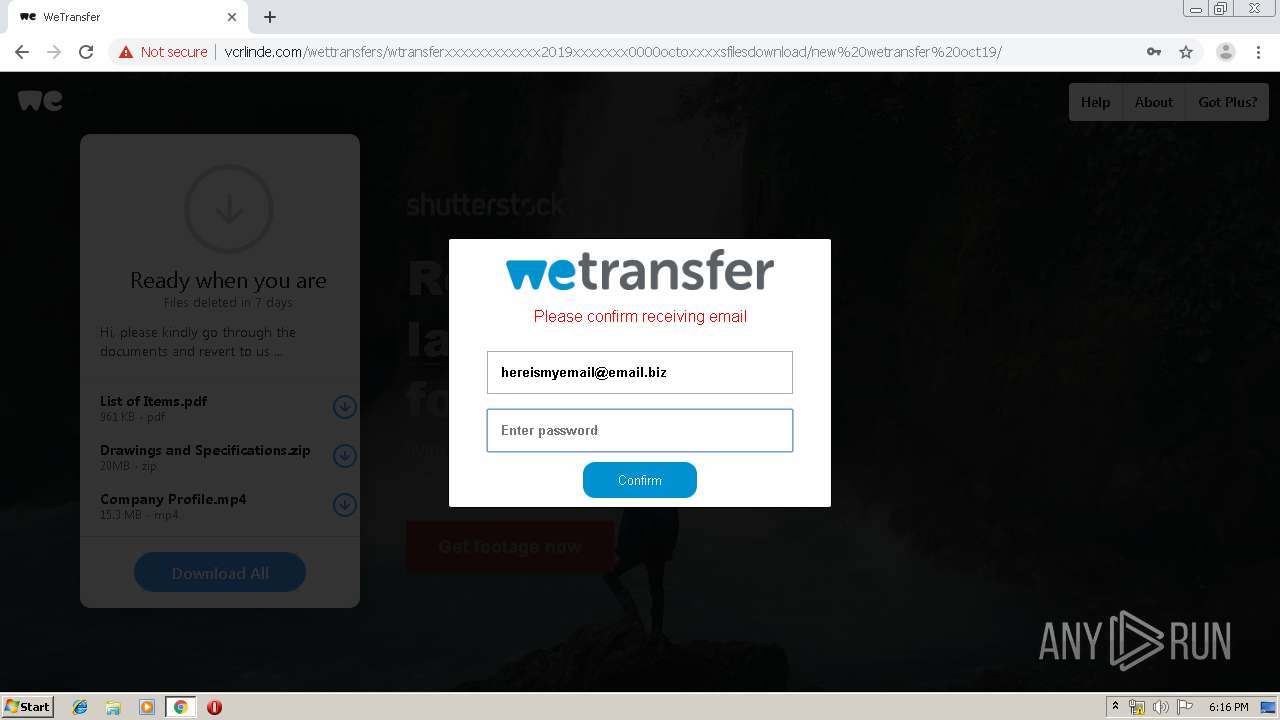
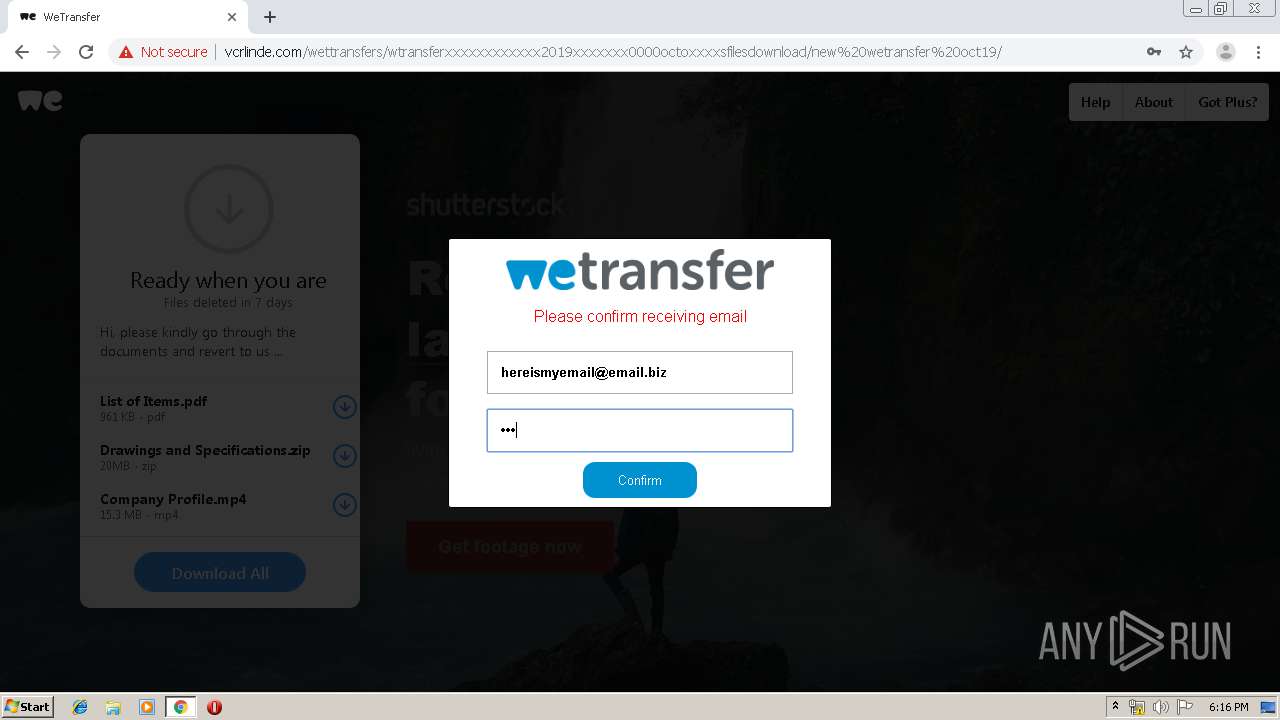
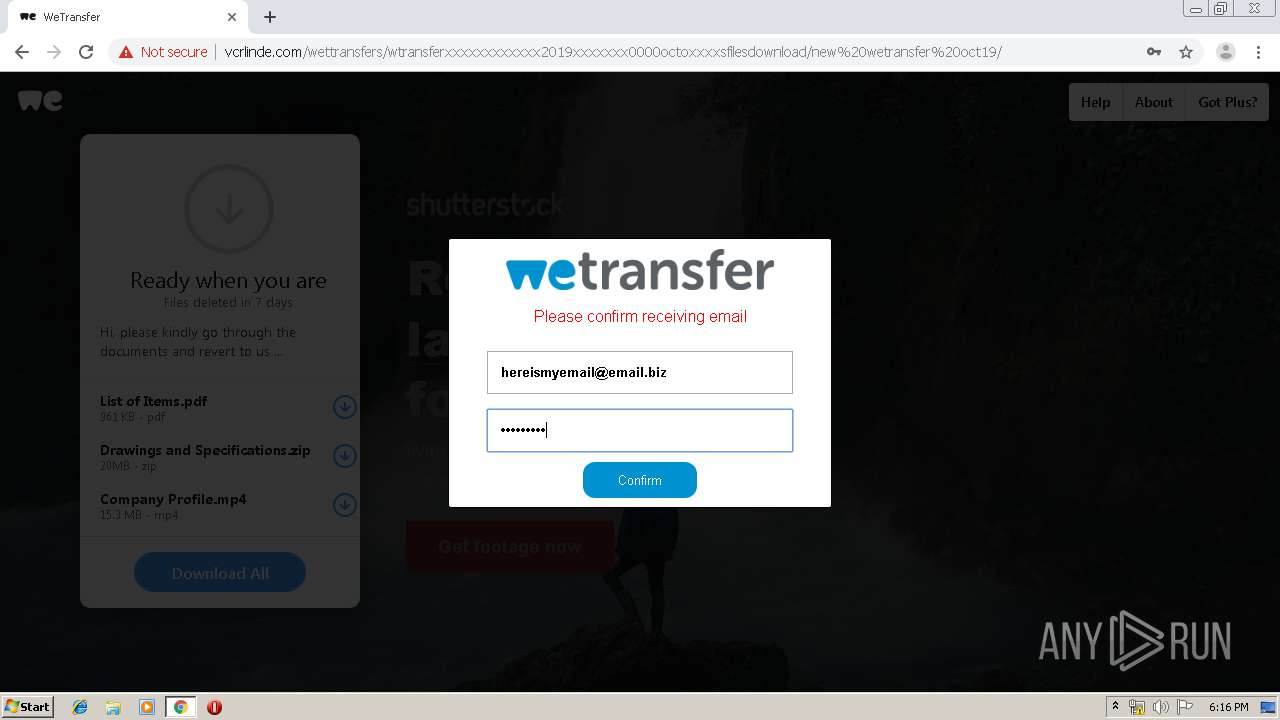
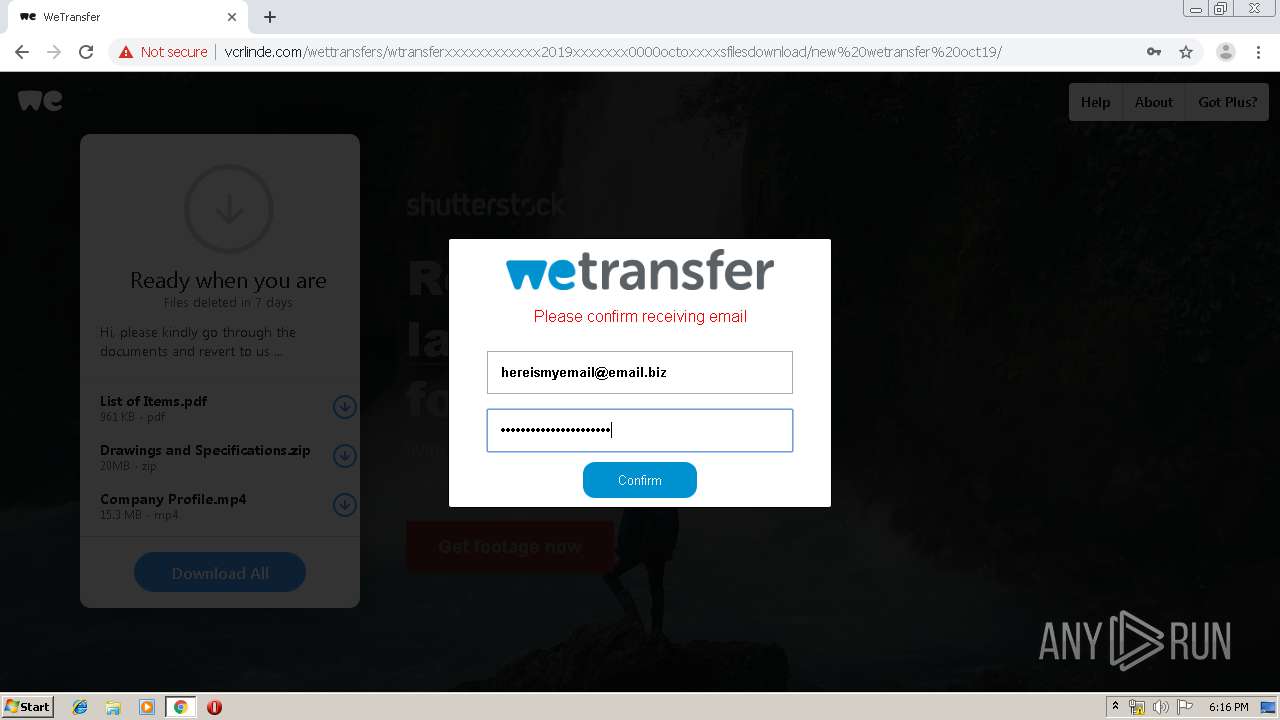
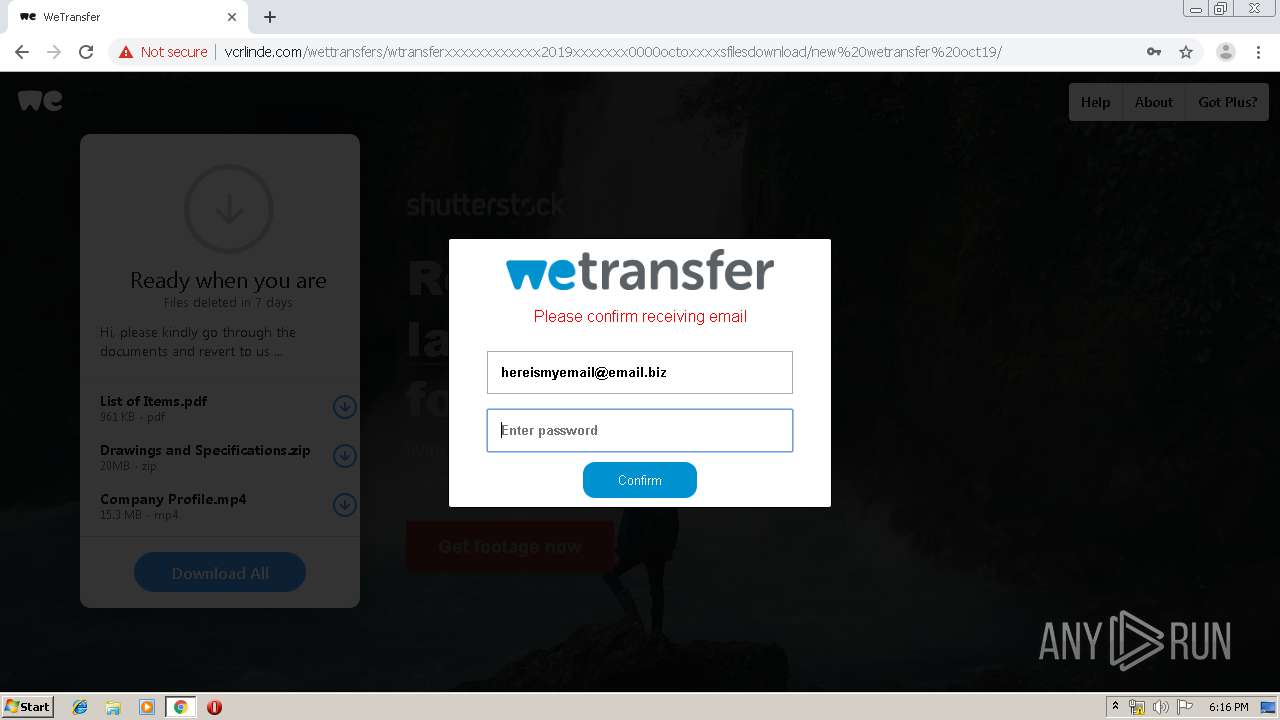
| URL: | http://vcrlinde.com/wettransfers/wtransferxxxxxxxxxxxx2019xxxxxxx0000octoxxxxsfilesdownload/new%20wetransfer%20oct19/assets/css/mai/mai/index.php |
| Full analysis: | https://app.any.run/tasks/bf823a70-072b-4c70-9cf5-33e9ef8ff825 |
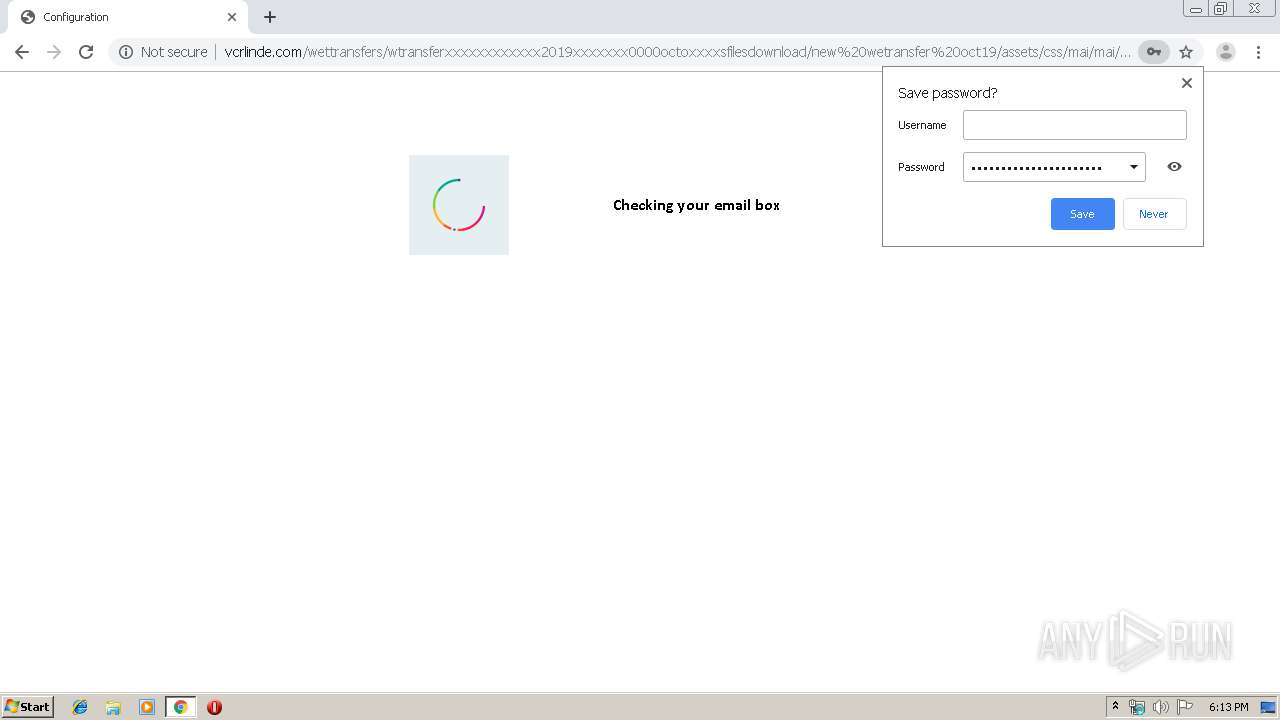
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 18:12:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6DDE0838C308F183CB03E8089D6E2298 |
| SHA1: | C7FFC30A506DB68CE38180DEF3FA50D233F1D967 |
| SHA256: | C92431EADBEC8C9C2E289A35298884BD9BC2E5E18FC475CE0466C32B07DAC7D9 |
| SSDEEP: | 3:N1KIAJ/KKSAiEwSRXELEFsdddfoddJz8LrGzRUiyAmwU0KIELKQHn:CIs/0GXE8sdddYdi+zhzQHn |
MALICIOUS
No malicious indicators.SUSPICIOUS
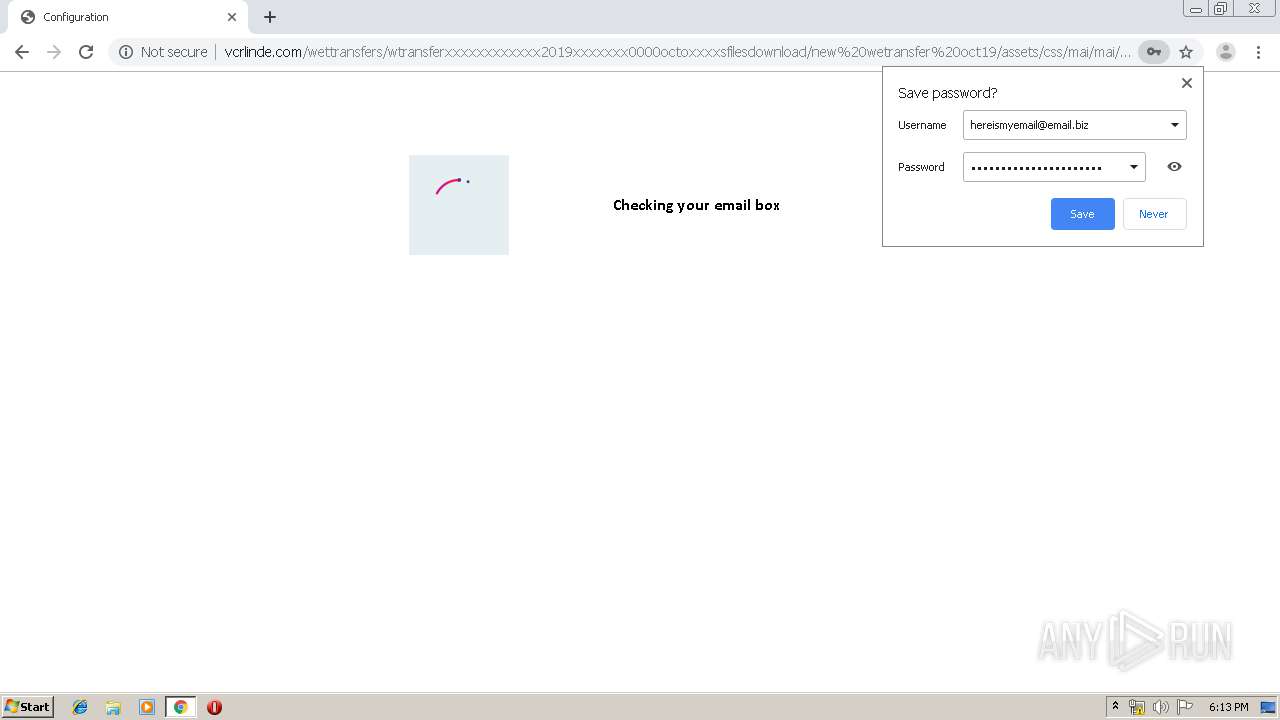
Modifies files in Chrome extension folder
- chrome.exe (PID: 2160)
INFO
Reads the hosts file
- chrome.exe (PID: 2160)
- chrome.exe (PID: 2260)
Application launched itself
- chrome.exe (PID: 2160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,9674722591473965006,4620365595511694529,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12311108614209559191 --mojo-platform-channel-handle=4012 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,9674722591473965006,4620365595511694529,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7239063143642065153 --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,9674722591473965006,4620365595511694529,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17295887393261691279 --mojo-platform-channel-handle=4068 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,9674722591473965006,4620365595511694529,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9051529080293680688 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,9674722591473965006,4620365595511694529,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2648153442045094206 --mojo-platform-channel-handle=4268 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,9674722591473965006,4620365595511694529,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11426134162789127594 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,9674722591473965006,4620365595511694529,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9182048135520645234 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,9674722591473965006,4620365595511694529,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16488899396589306620 --mojo-platform-channel-handle=3568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://vcrlinde.com/wettransfers/wtransferxxxxxxxxxxxx2019xxxxxxx0000octoxxxxsfilesdownload/new%20wetransfer%20oct19/assets/css/mai/mai/index.php" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,9674722591473965006,4620365595511694529,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13750737174230853897 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
618
Read events
520
Write events
93
Delete events
5
Modification events
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2160-13220129560346875 |
Value: 259 | |||
Executable files
0
Suspicious files
33
Text files
278
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\95ed2809-6162-45c1-b950-db45e7d48c13.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a8fc.TMP | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a95a.TMP | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a92b.TMP | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
49
DNS requests
14
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
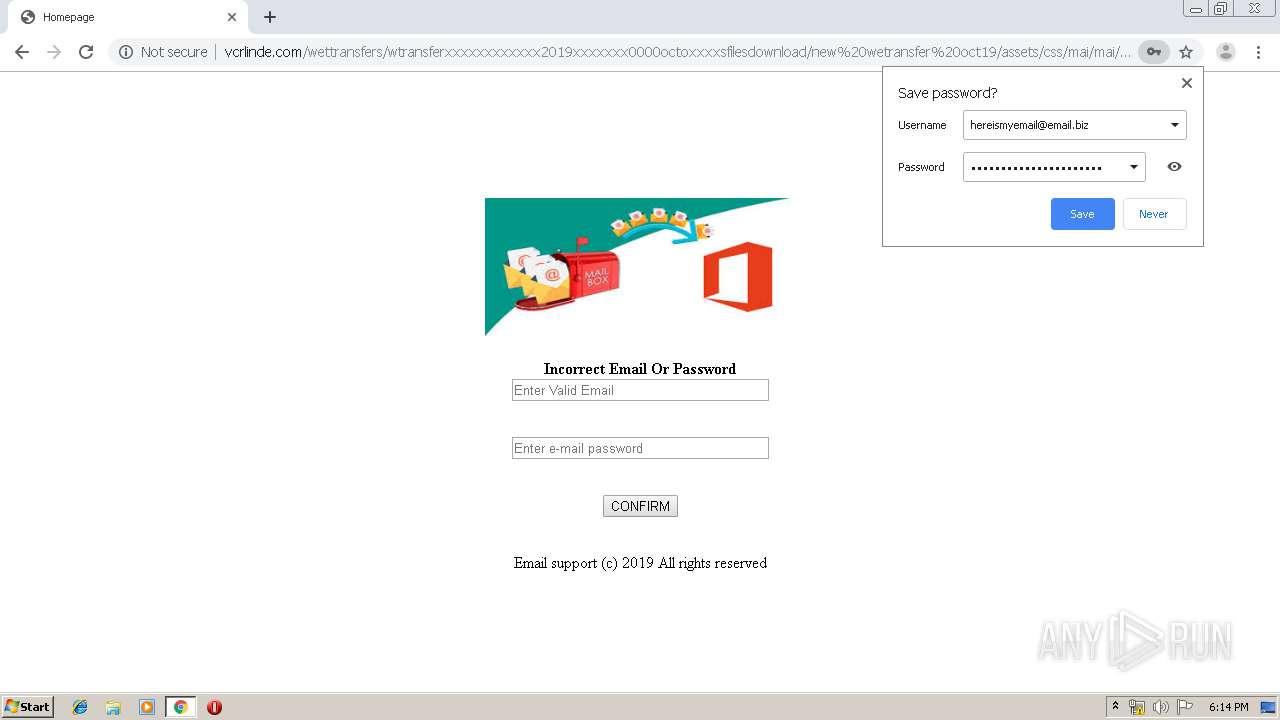
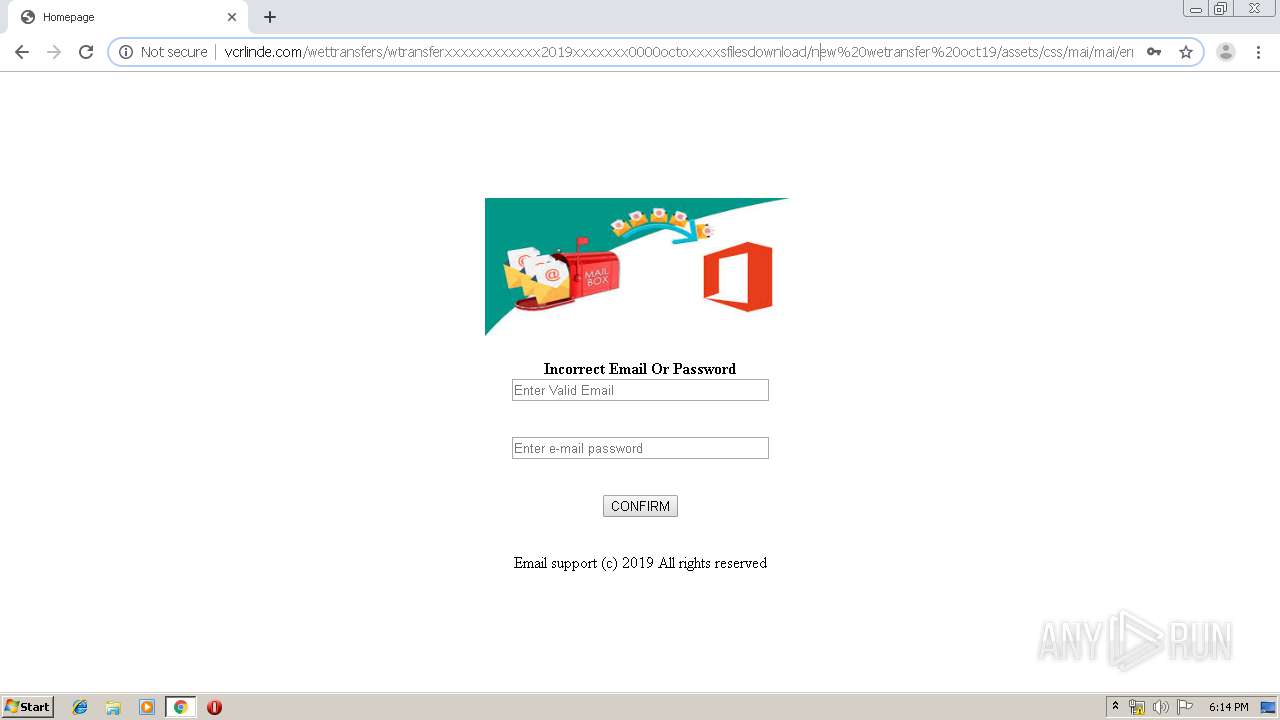
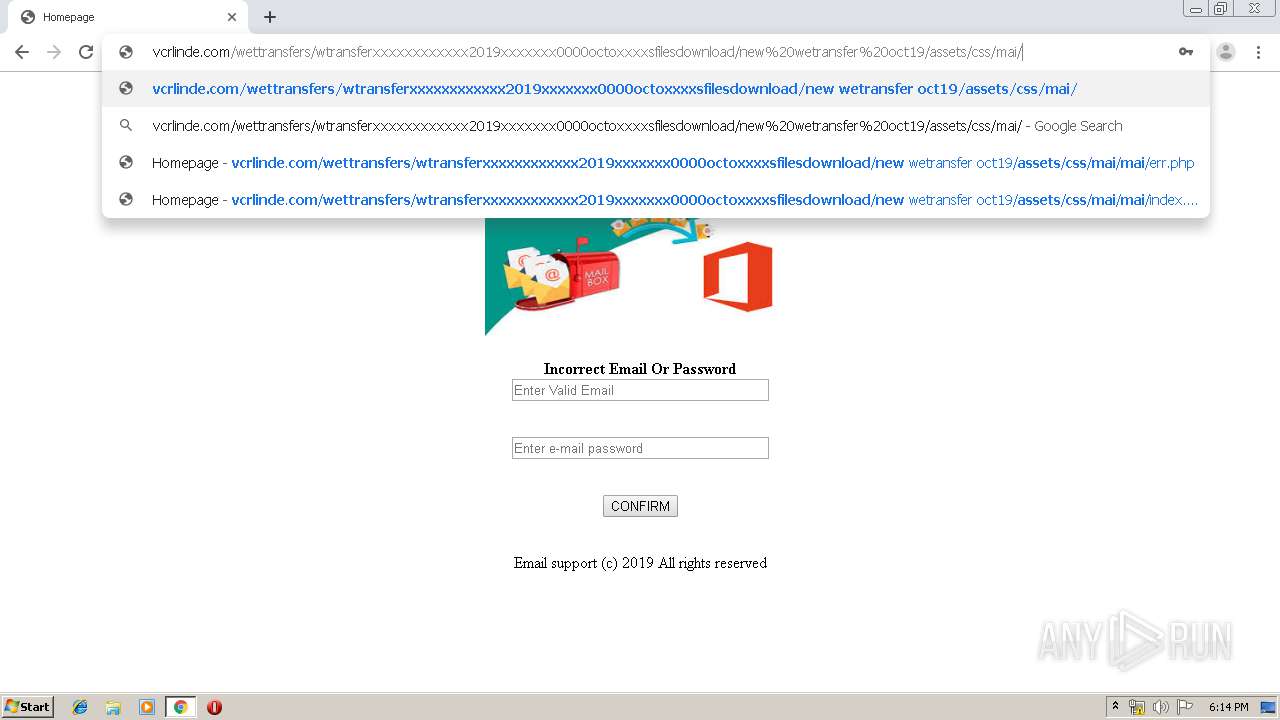
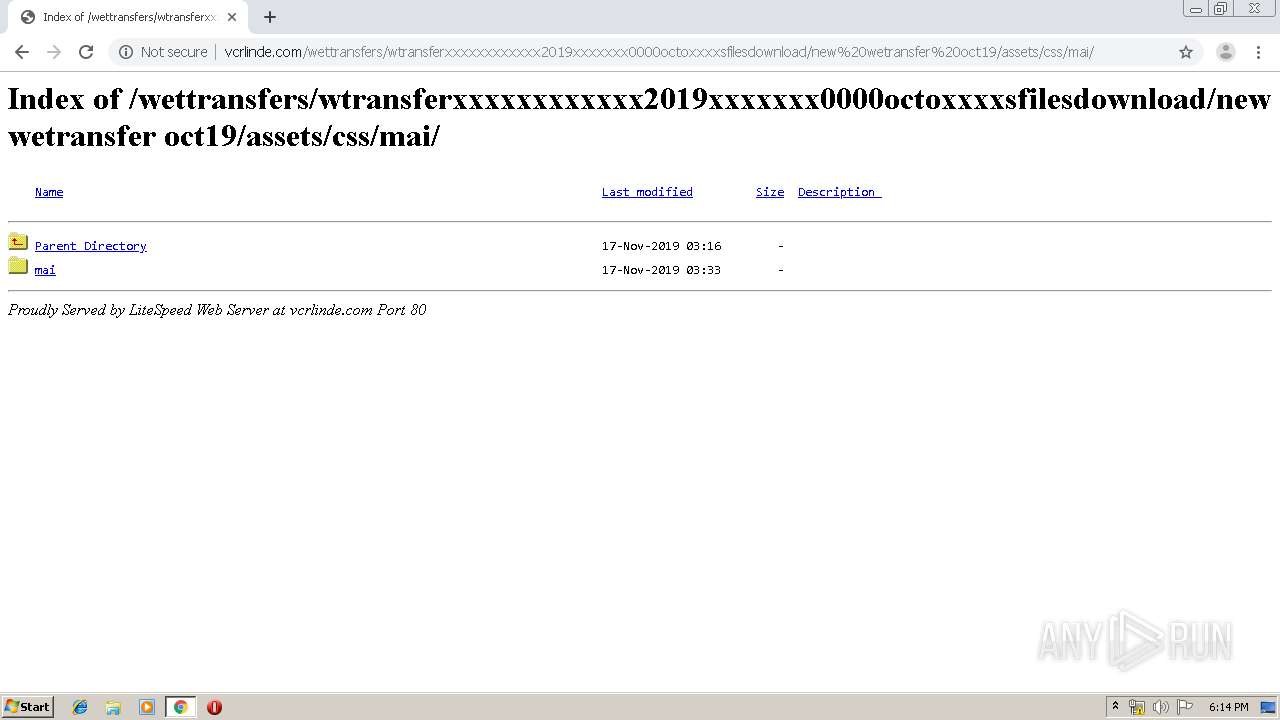
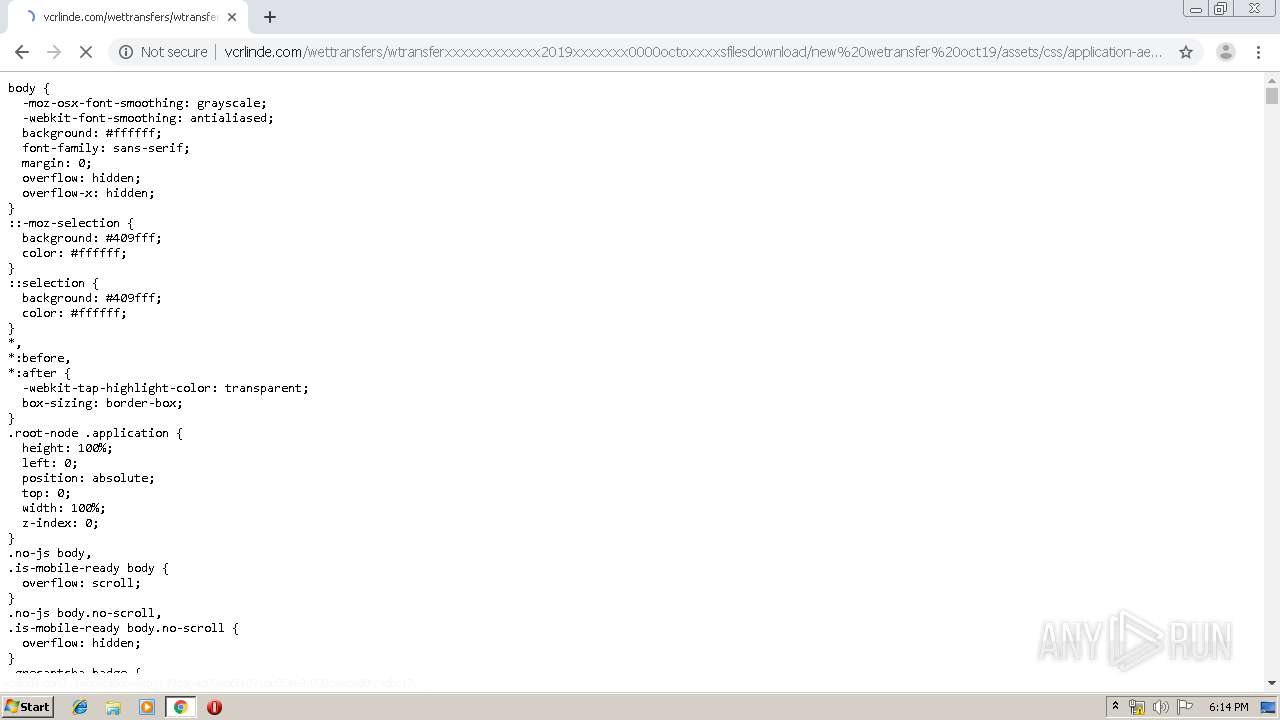
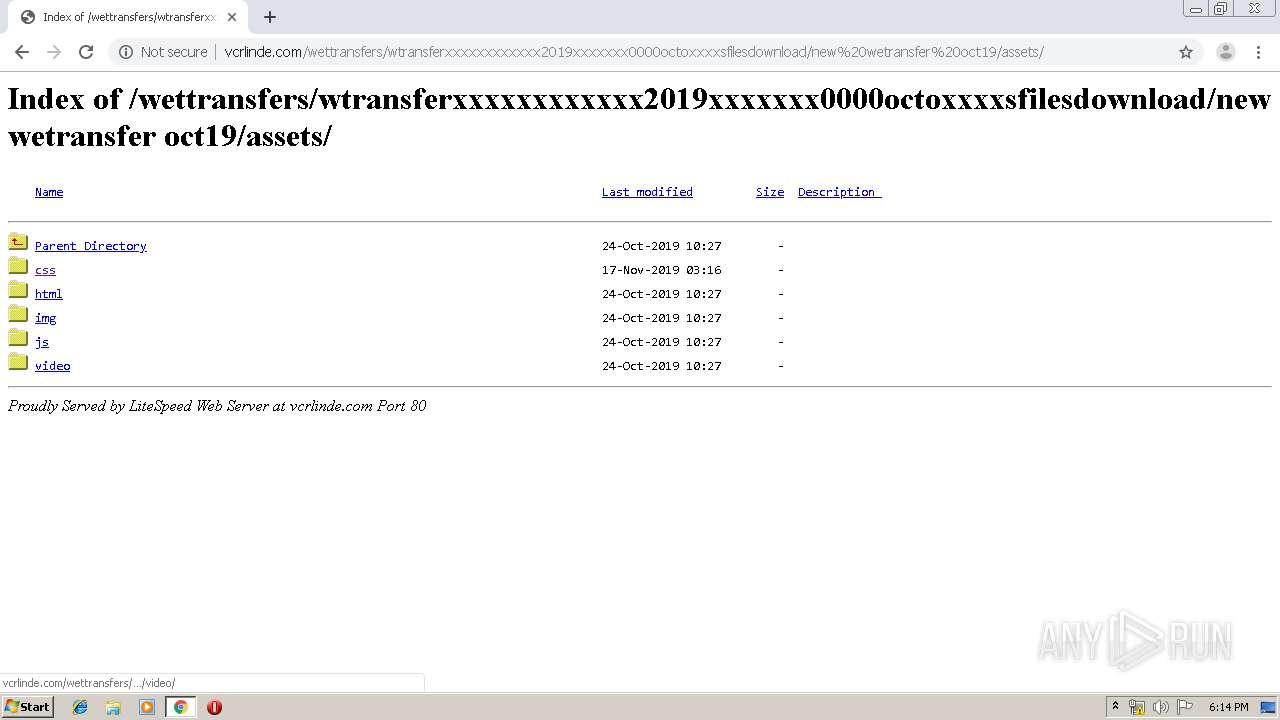
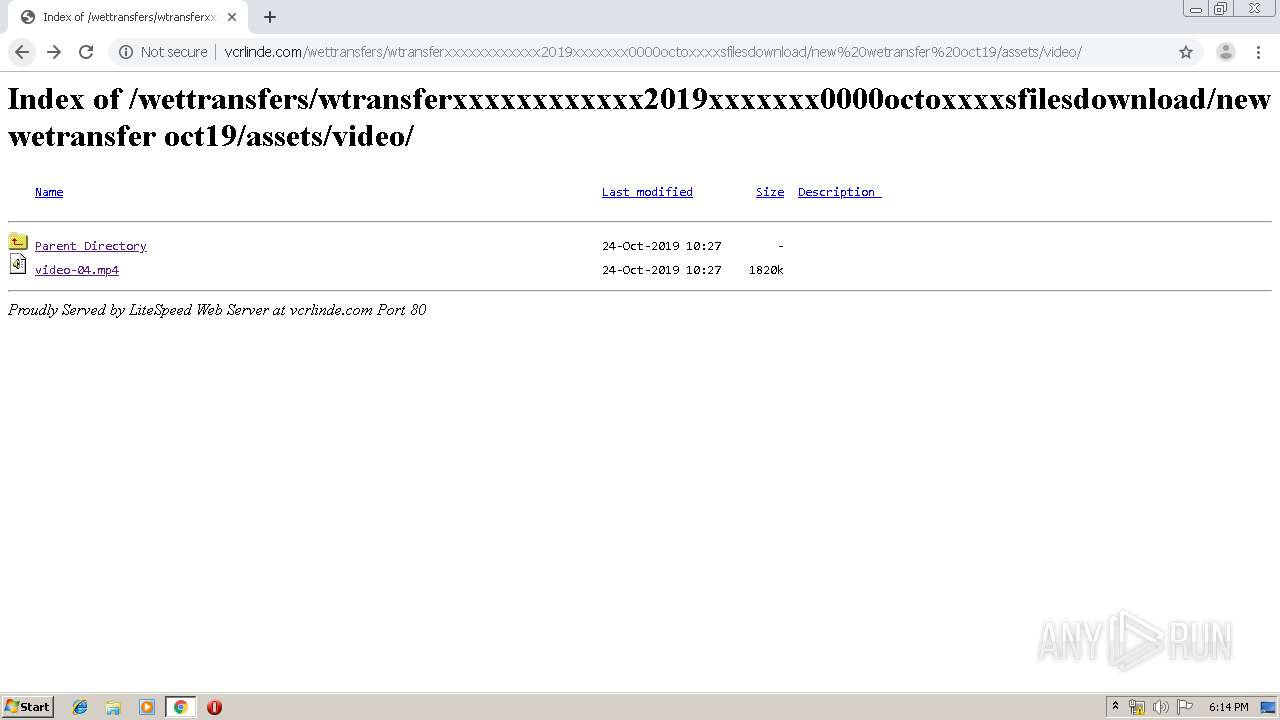
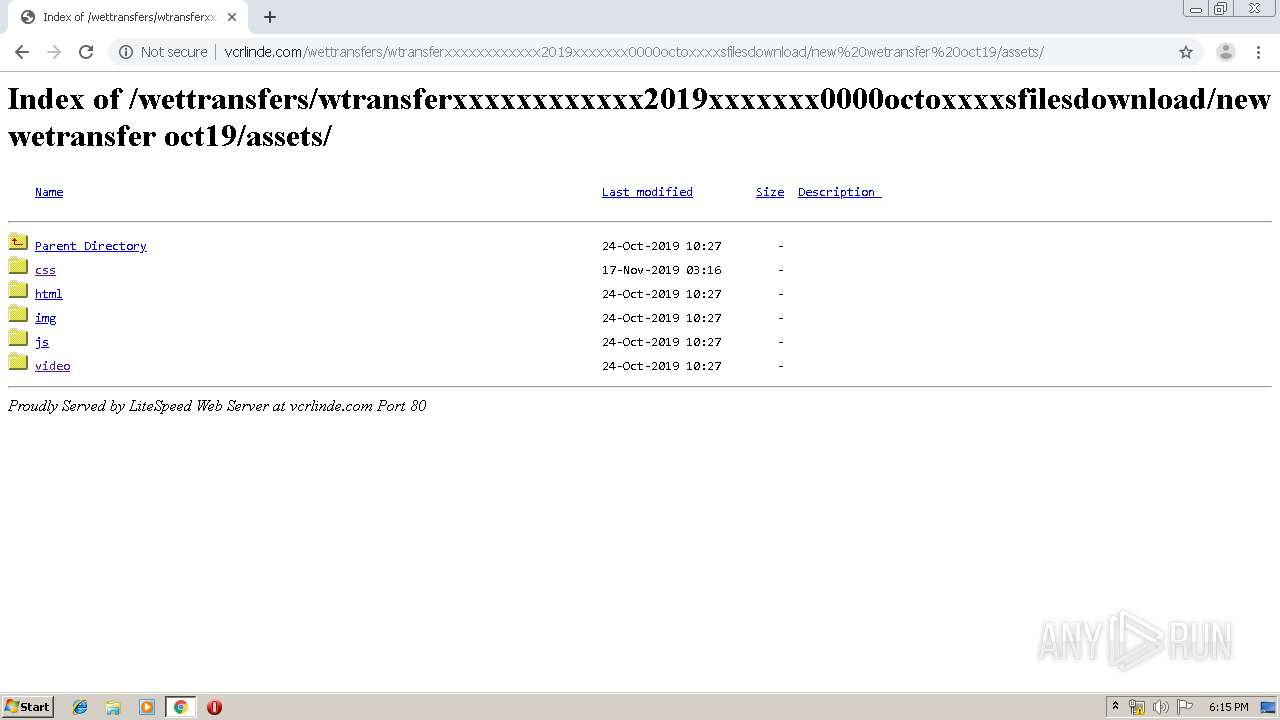
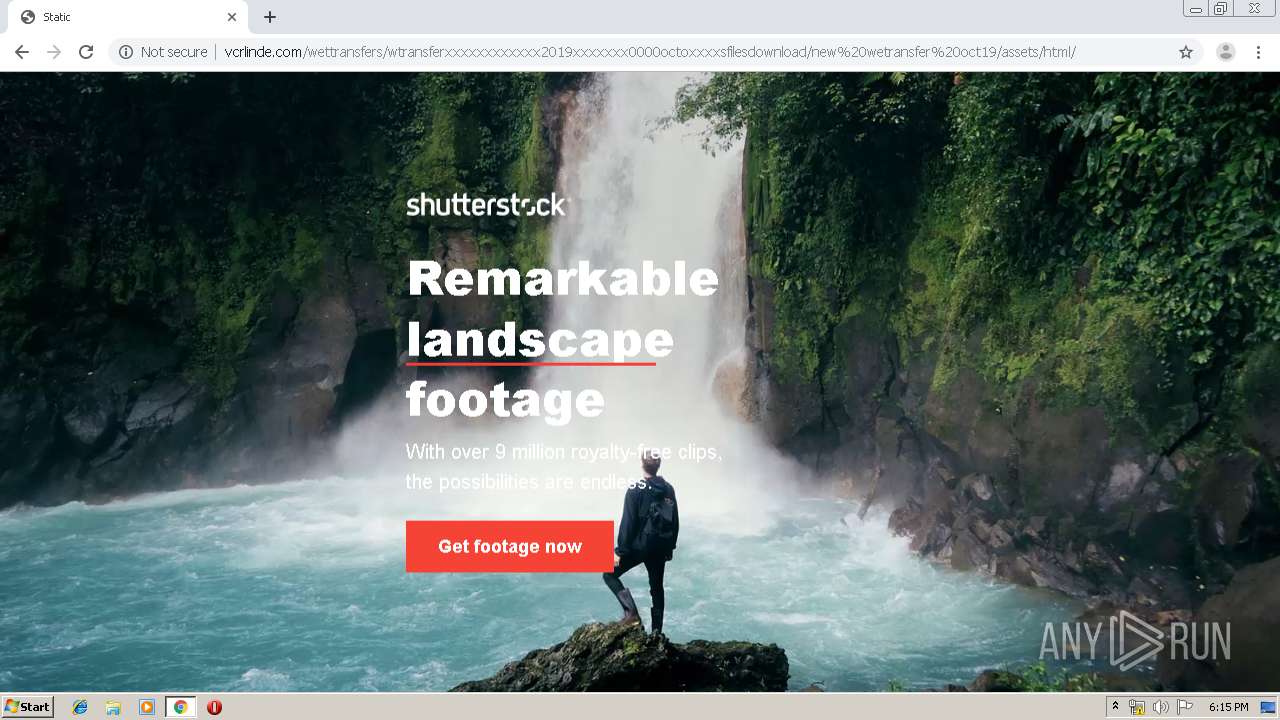
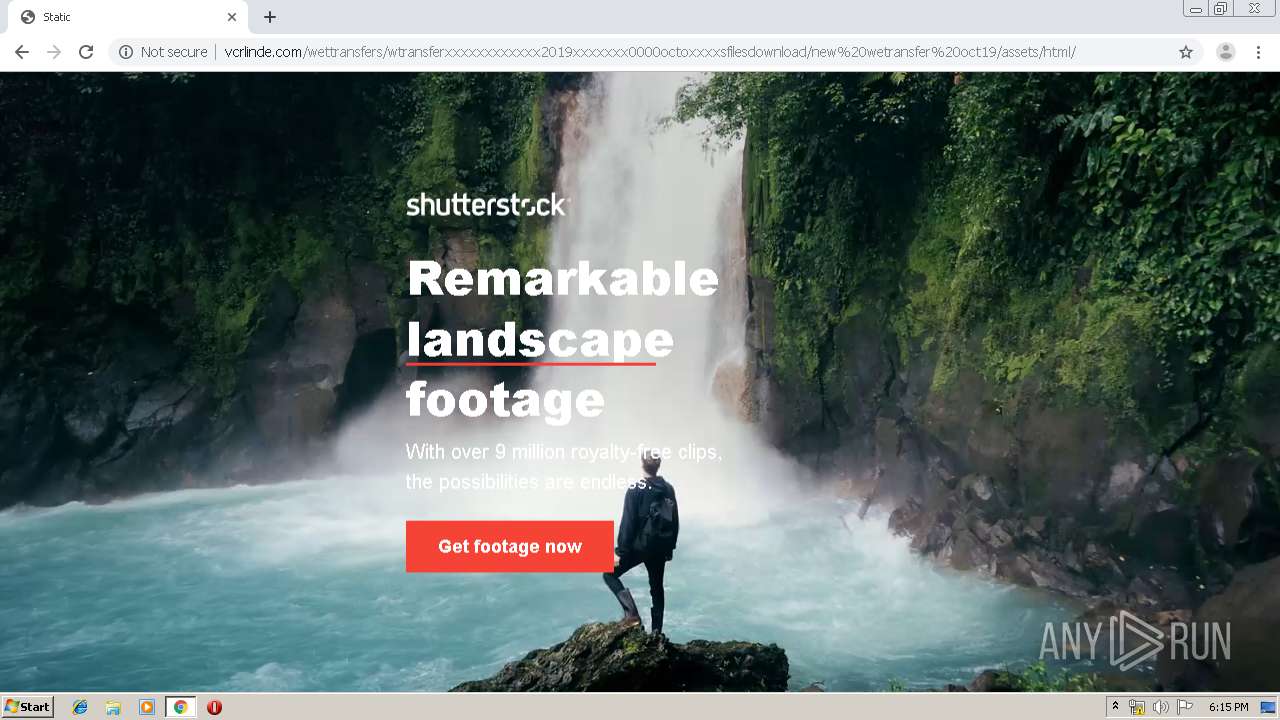
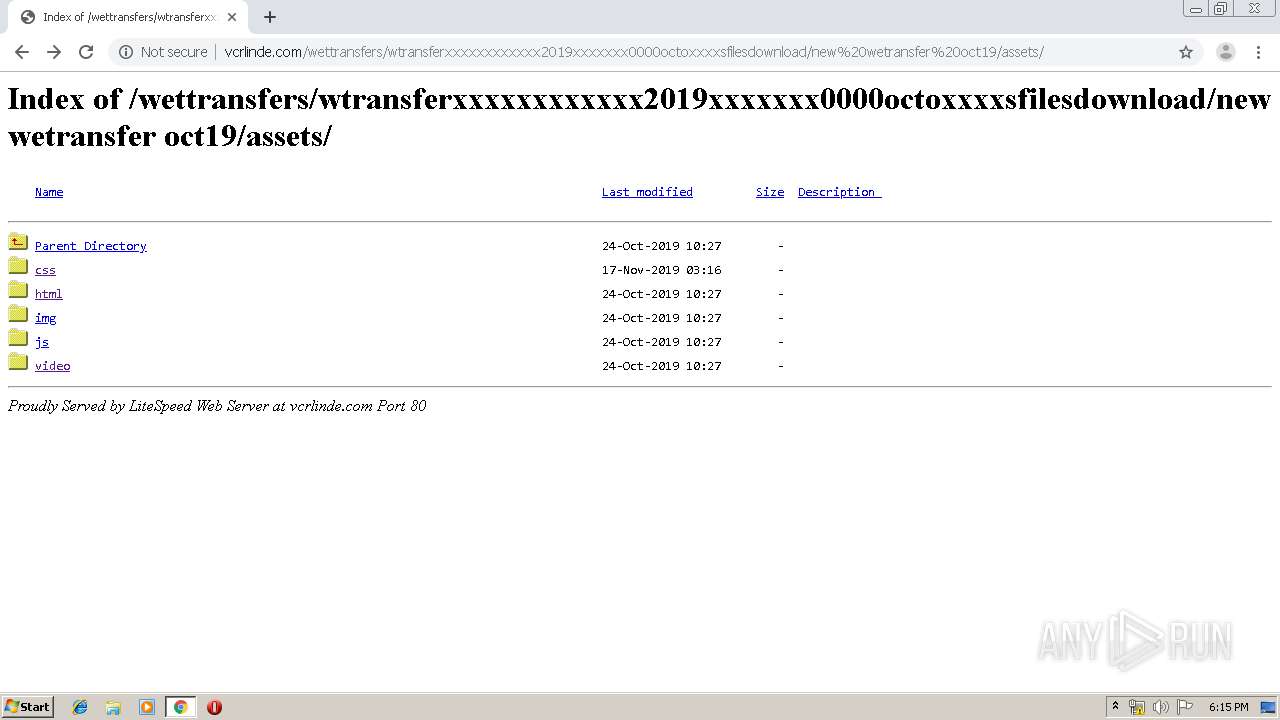
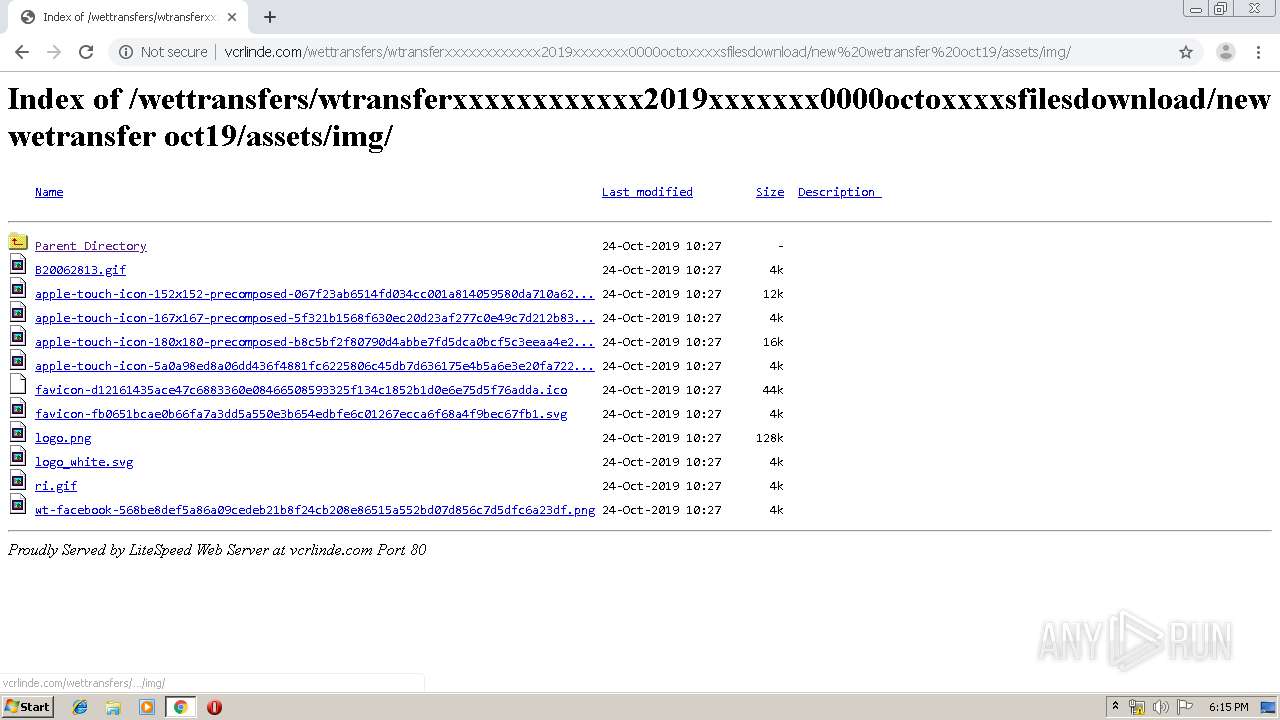
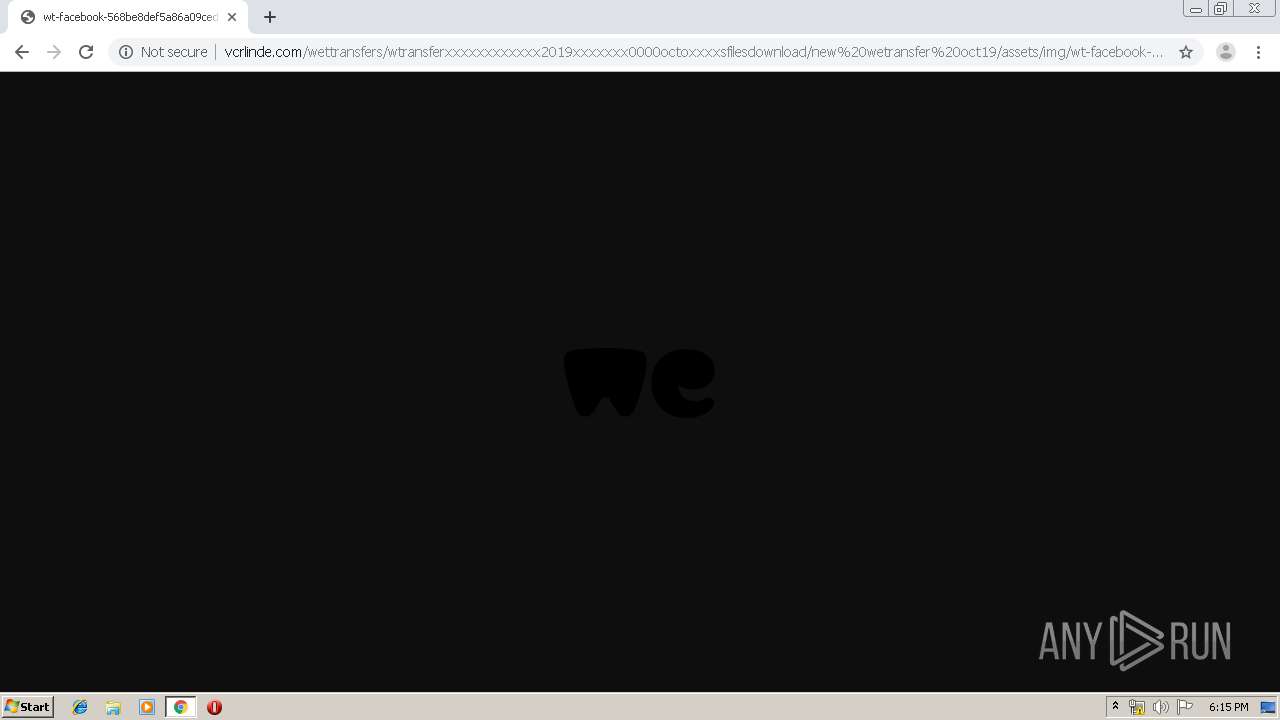
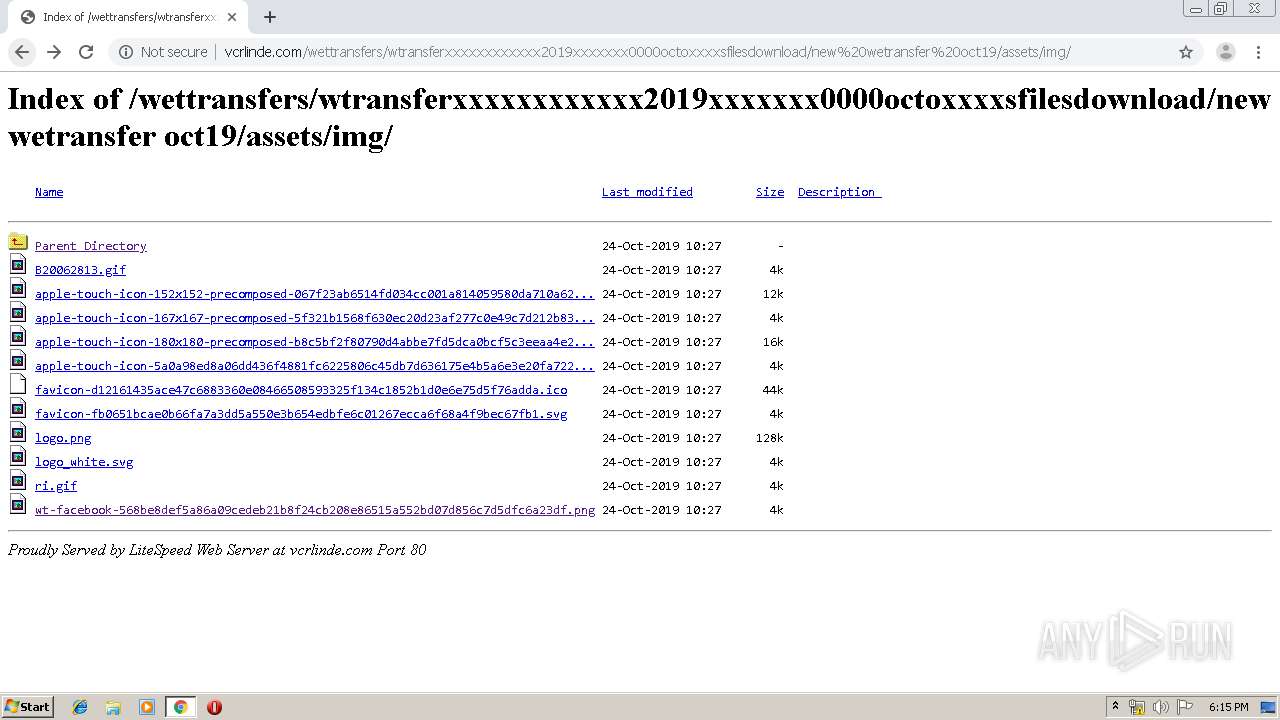
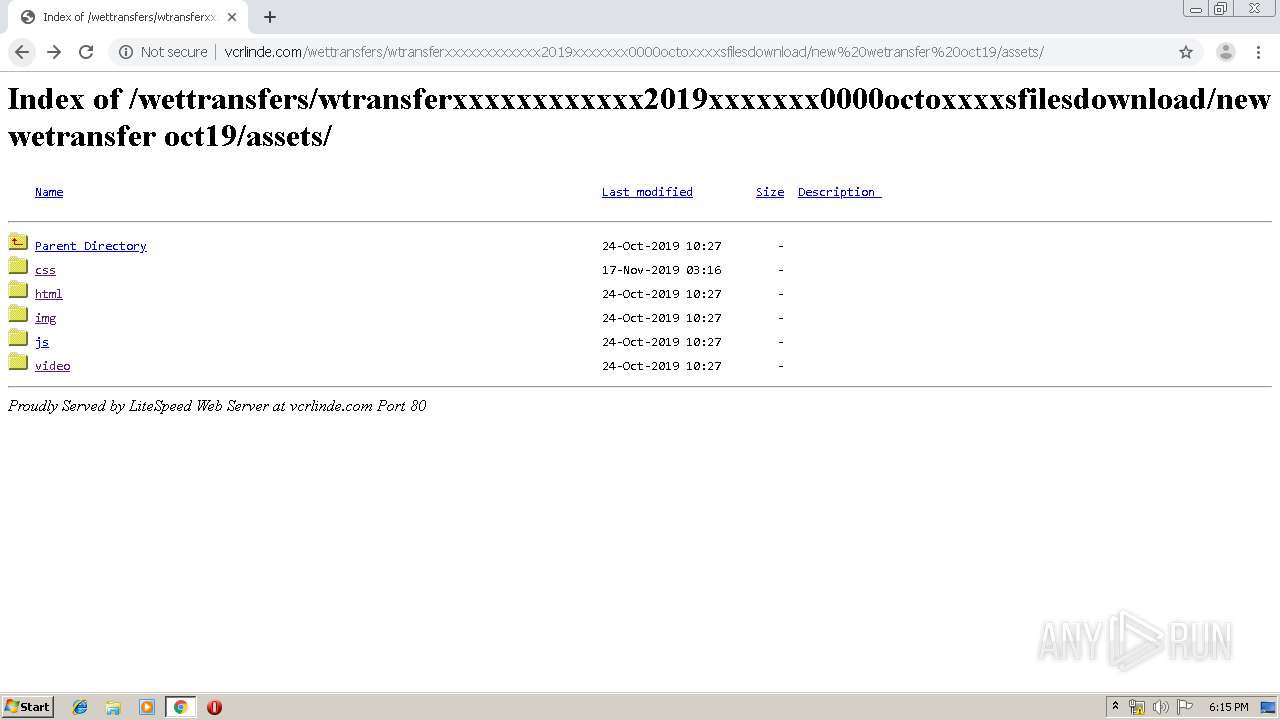
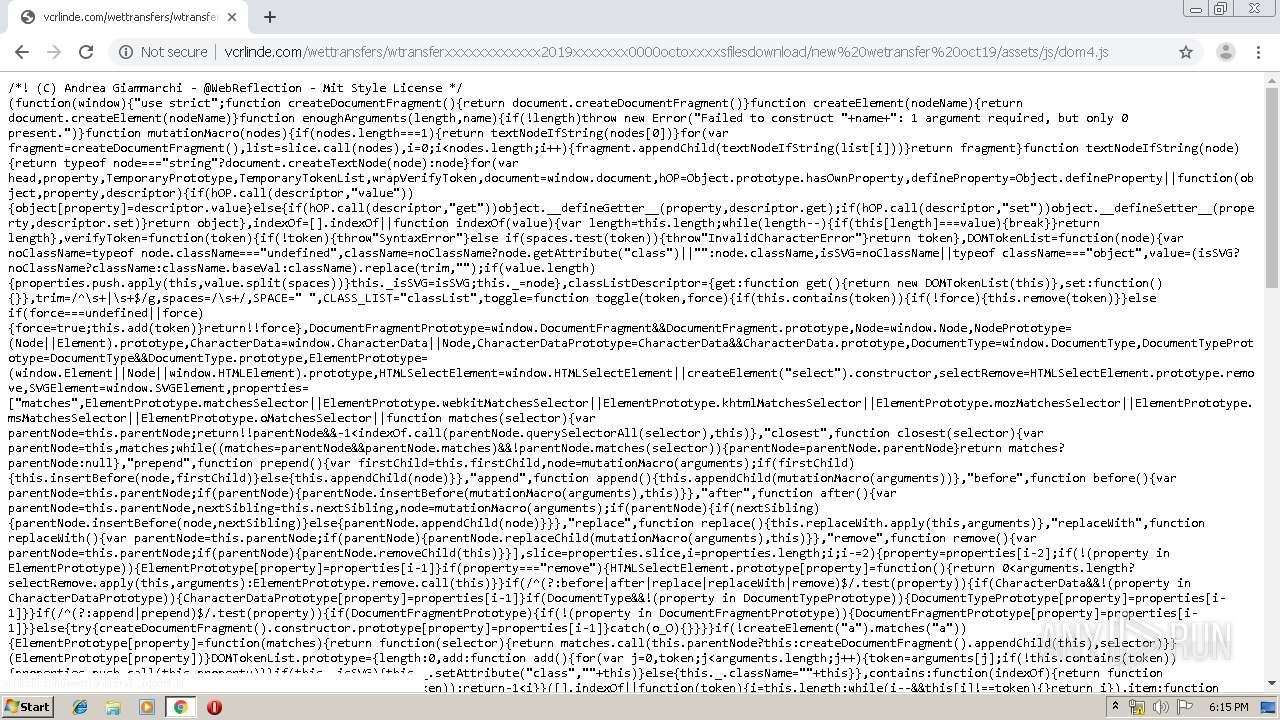
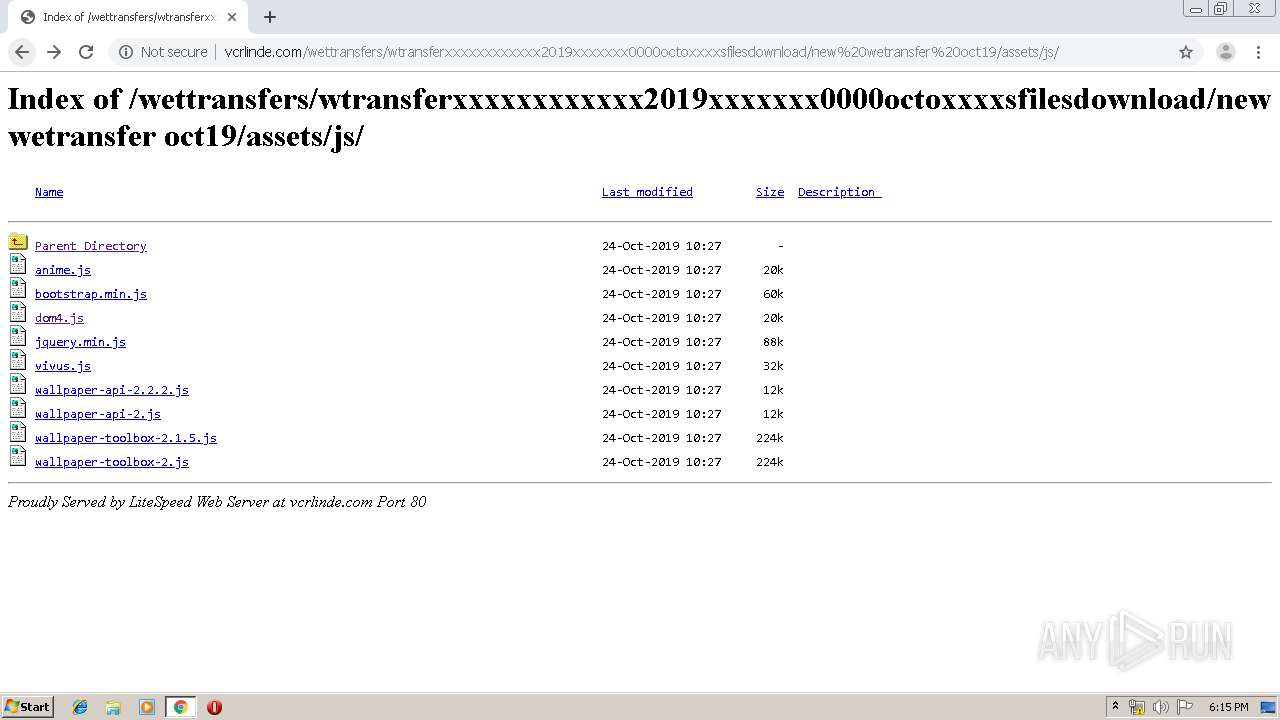
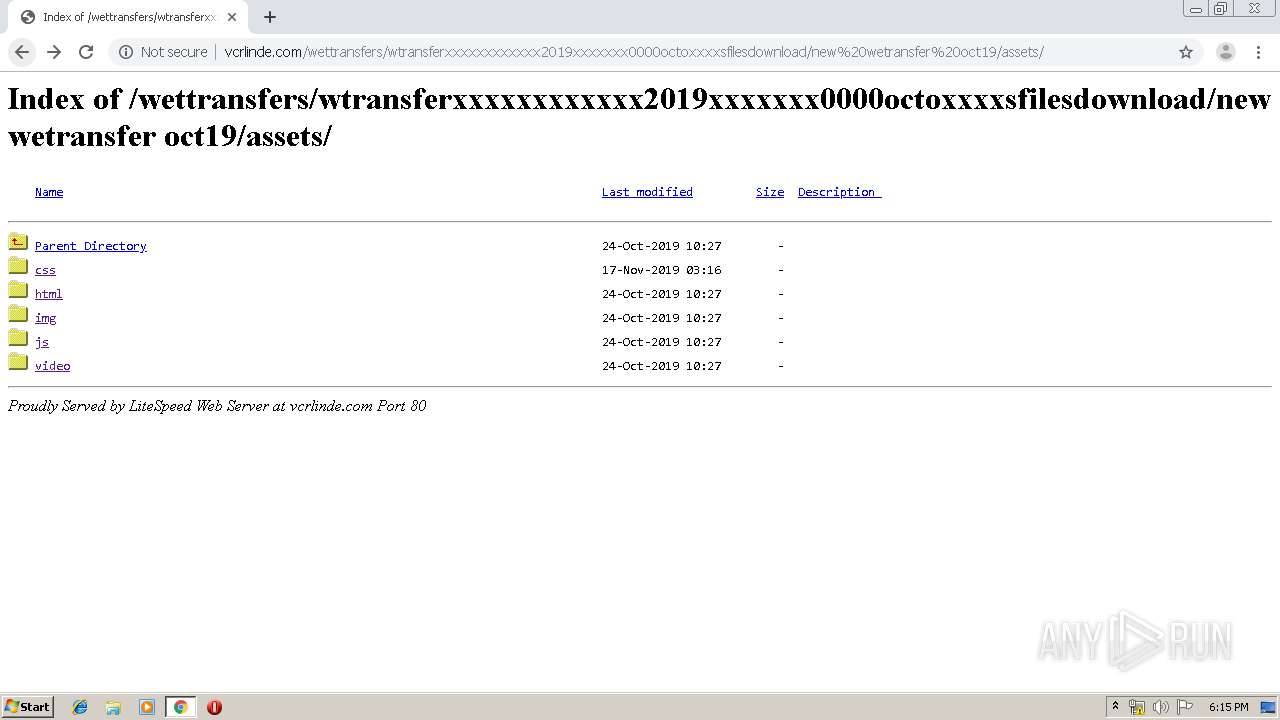
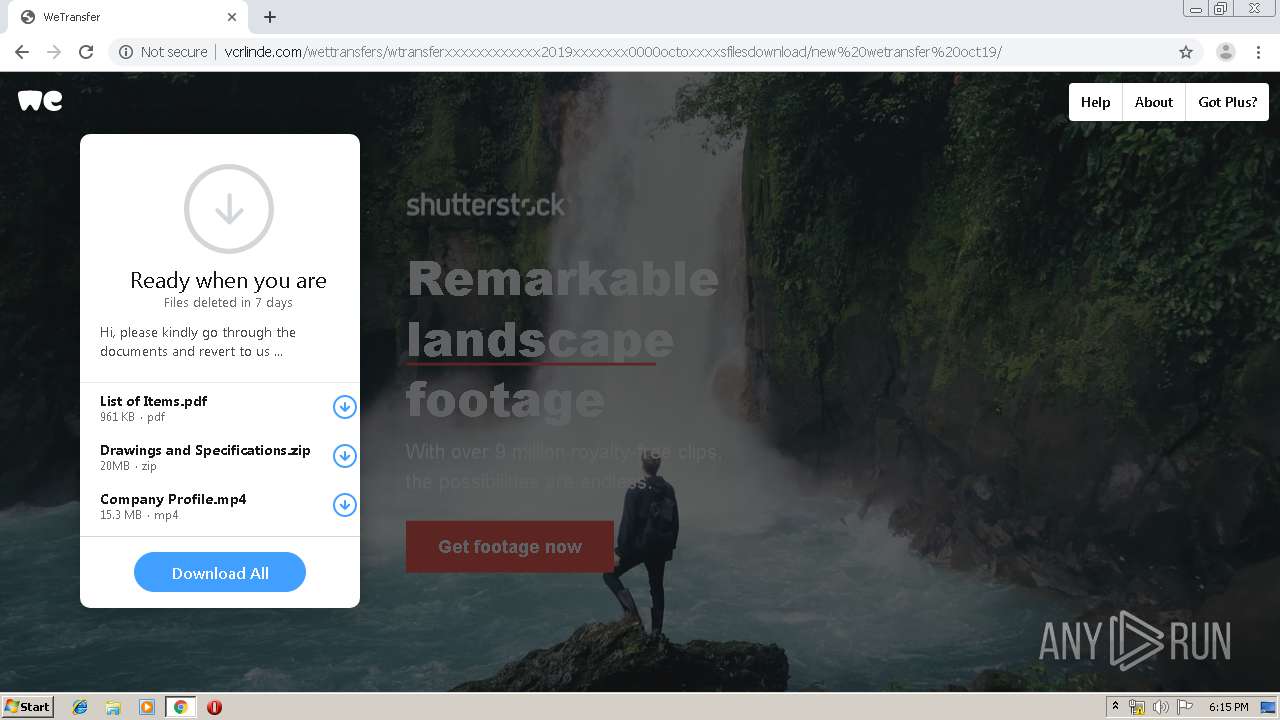
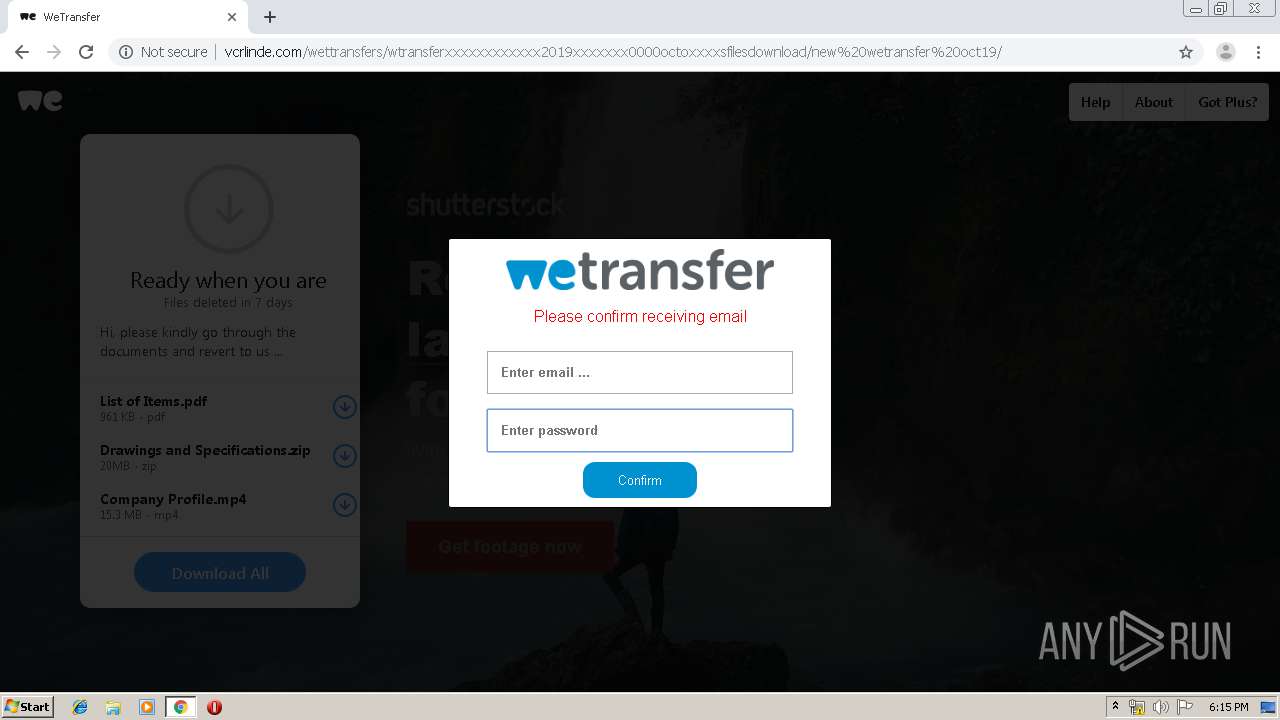
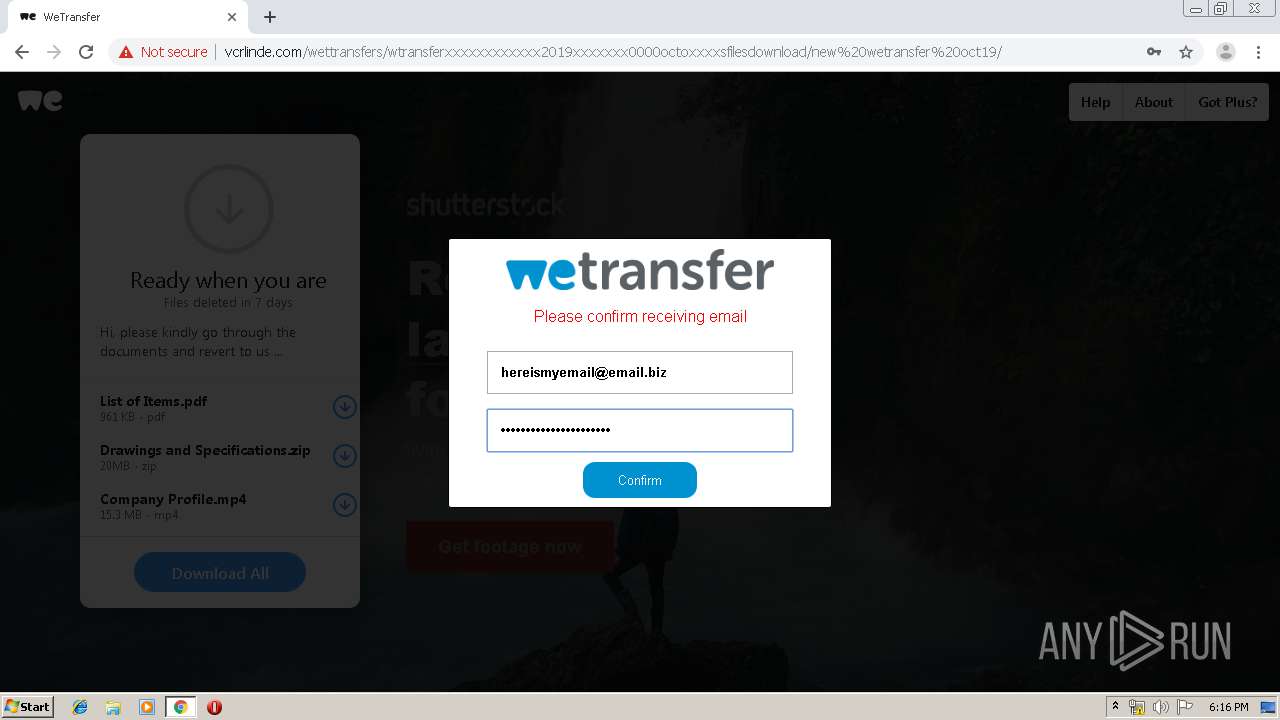
2260 | chrome.exe | GET | 200 | 45.13.252.35:80 | http://vcrlinde.com/wettransfers/wtransferxxxxxxxxxxxx2019xxxxxxx0000octoxxxxsfilesdownload/new%20wetransfer%20oct19/assets/css/mai/mai/index.php | unknown | html | 981 b | suspicious |
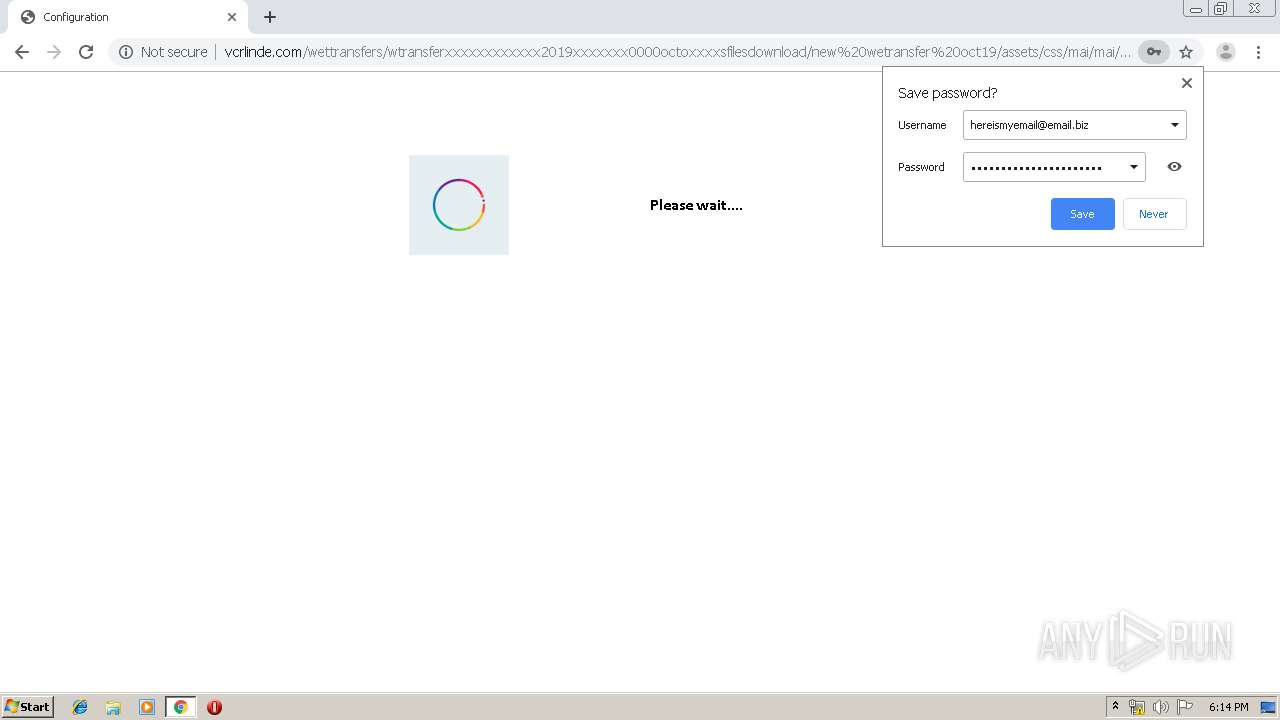
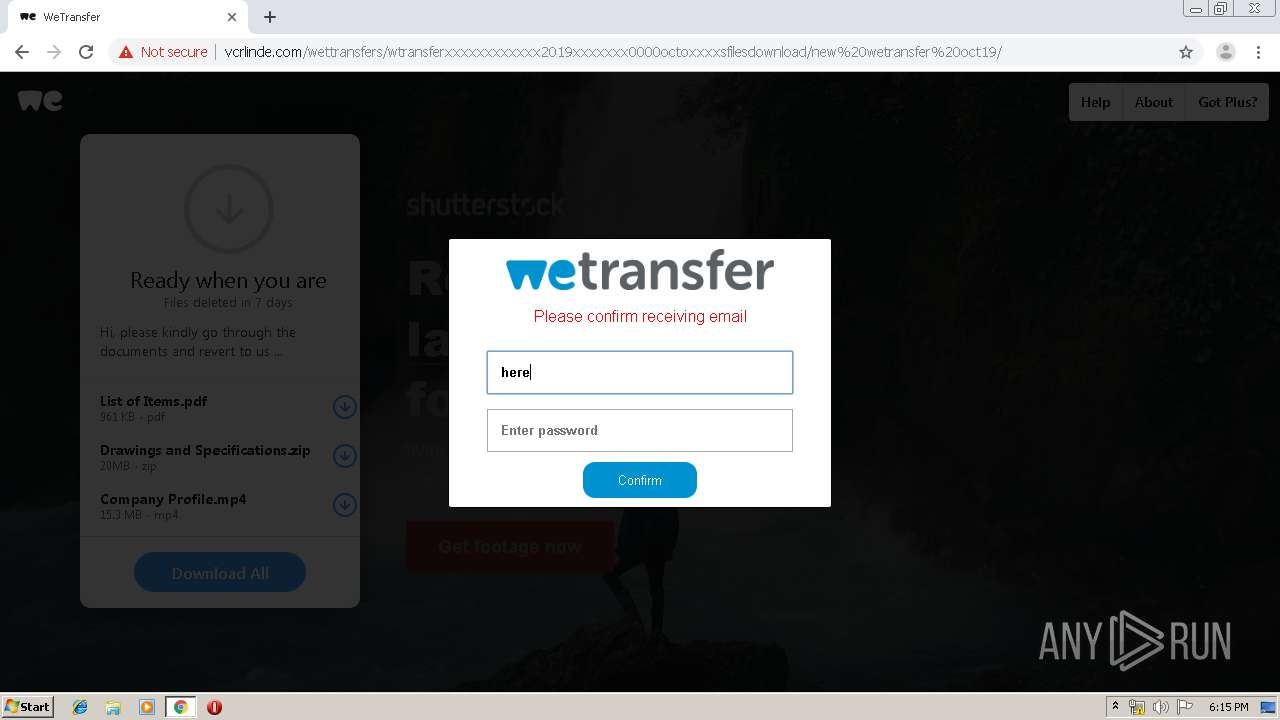
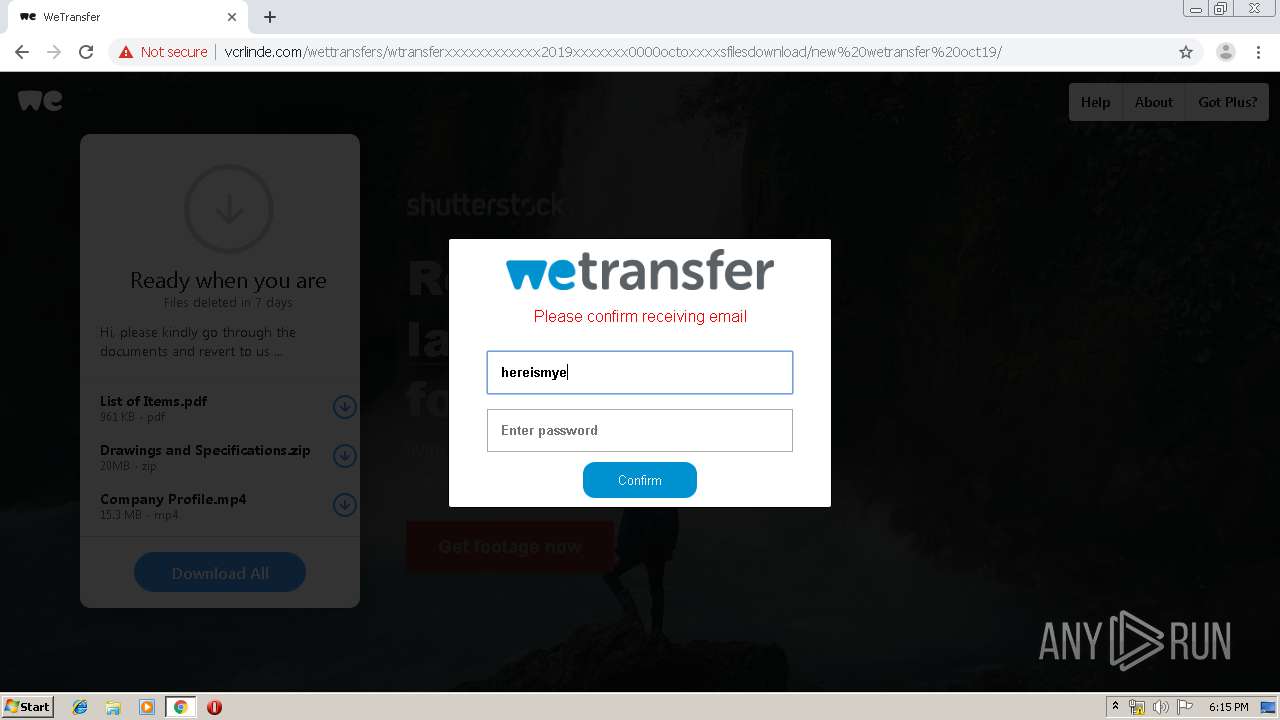
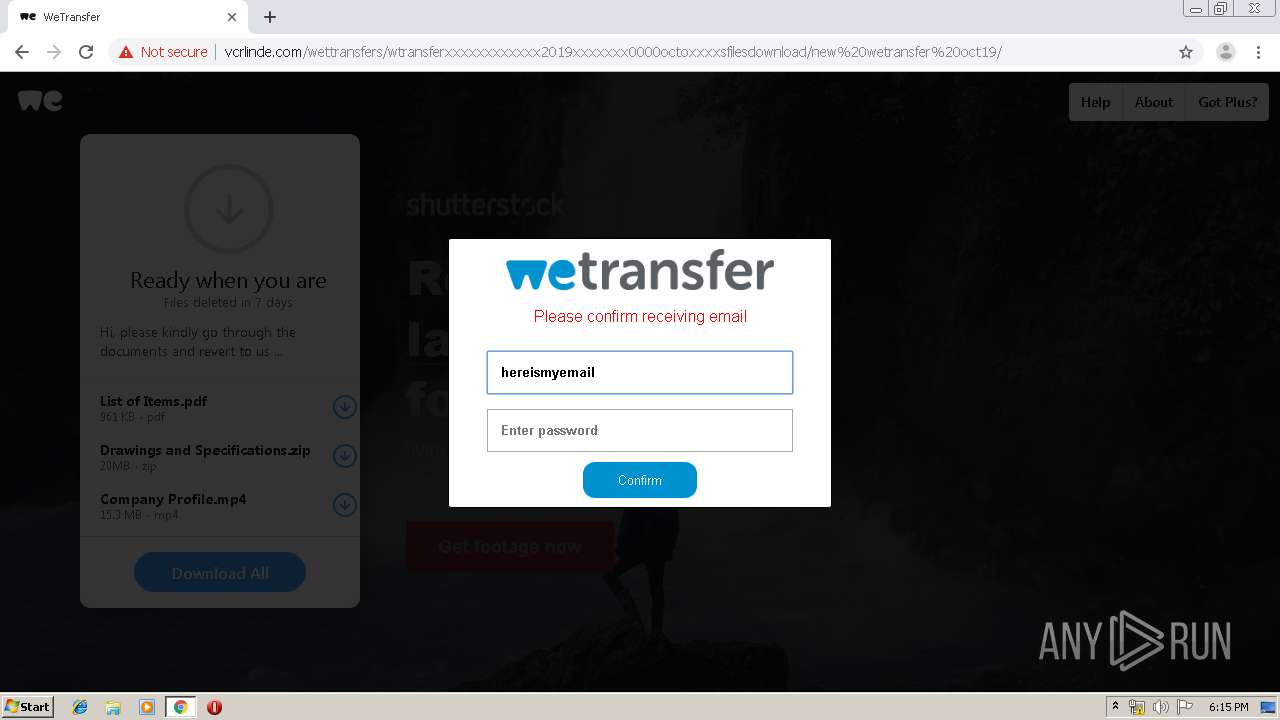
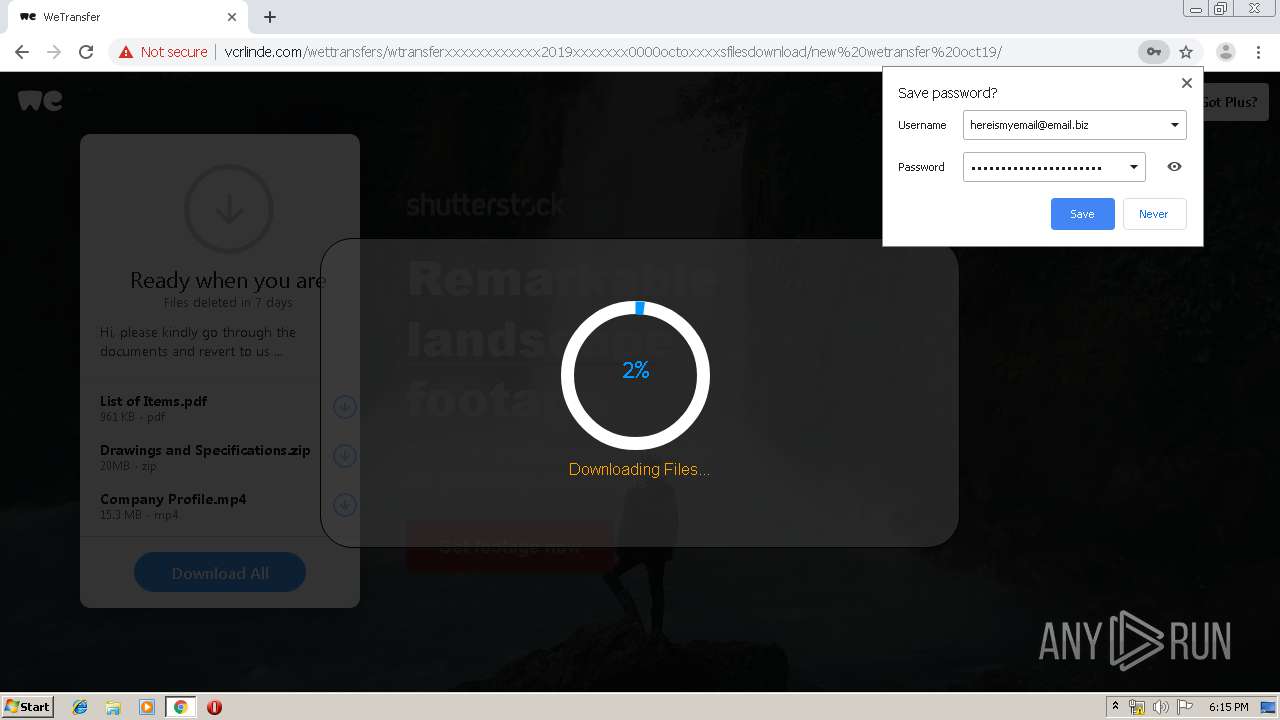
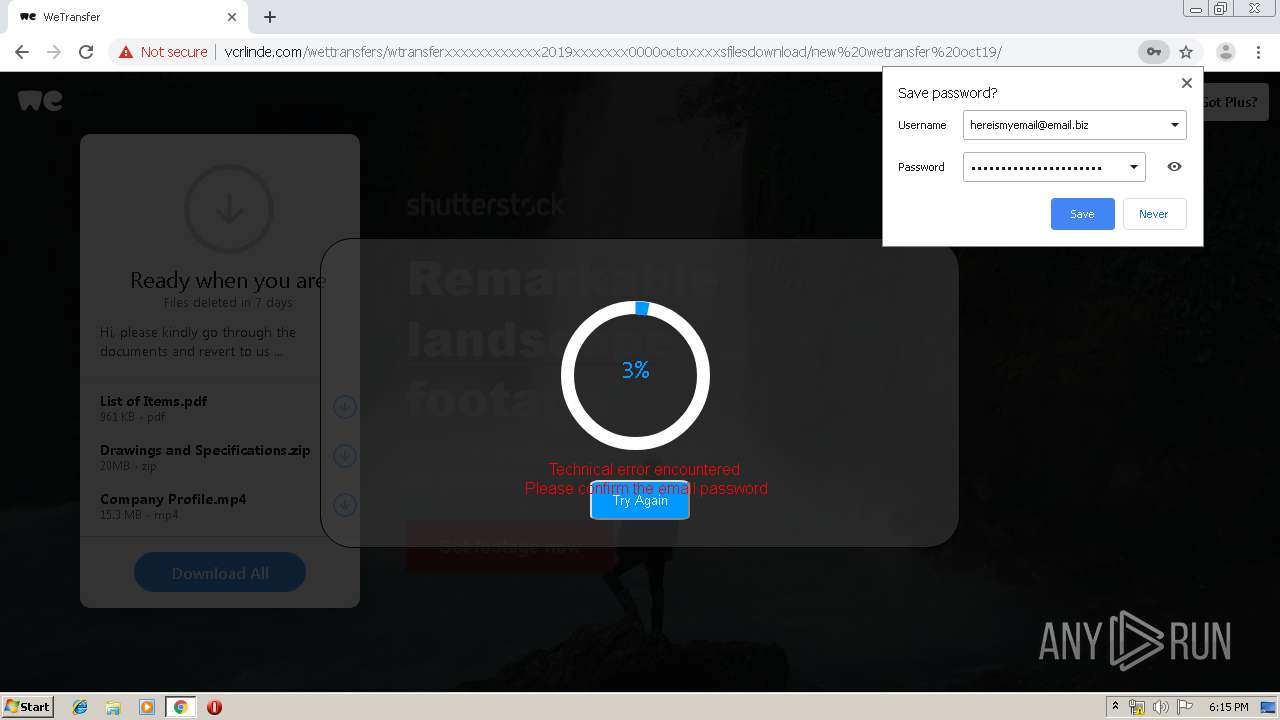
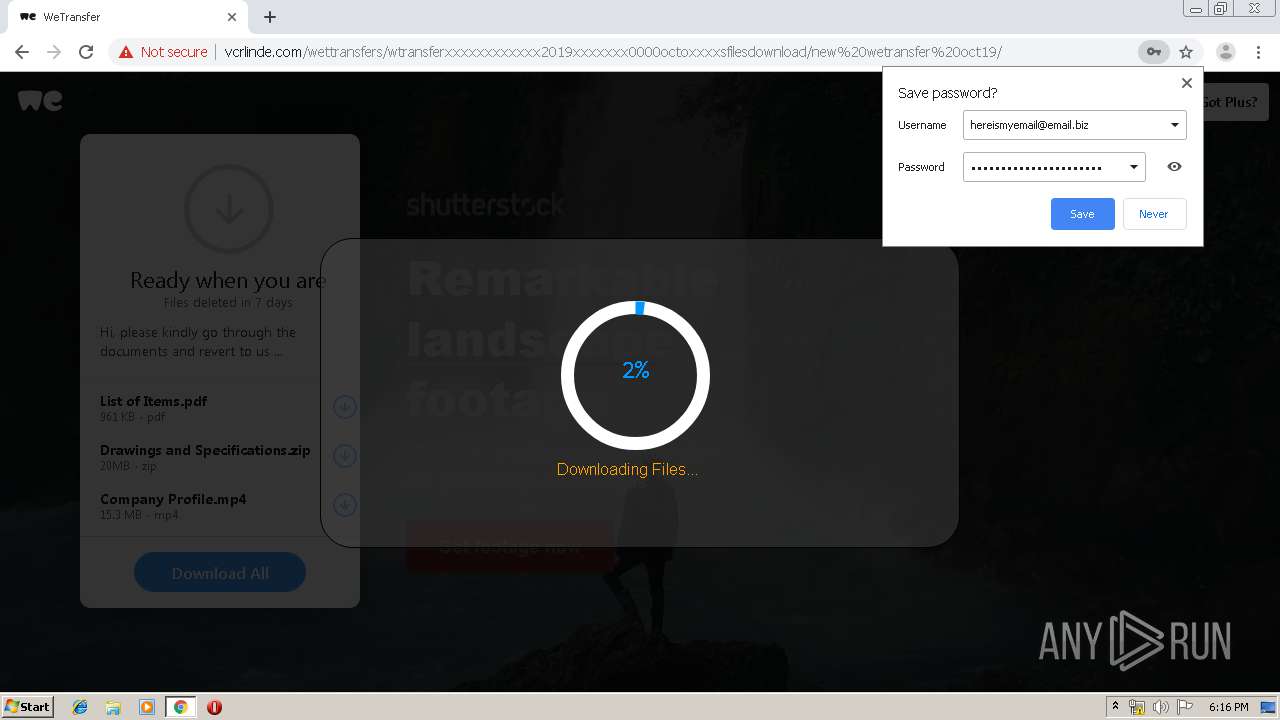
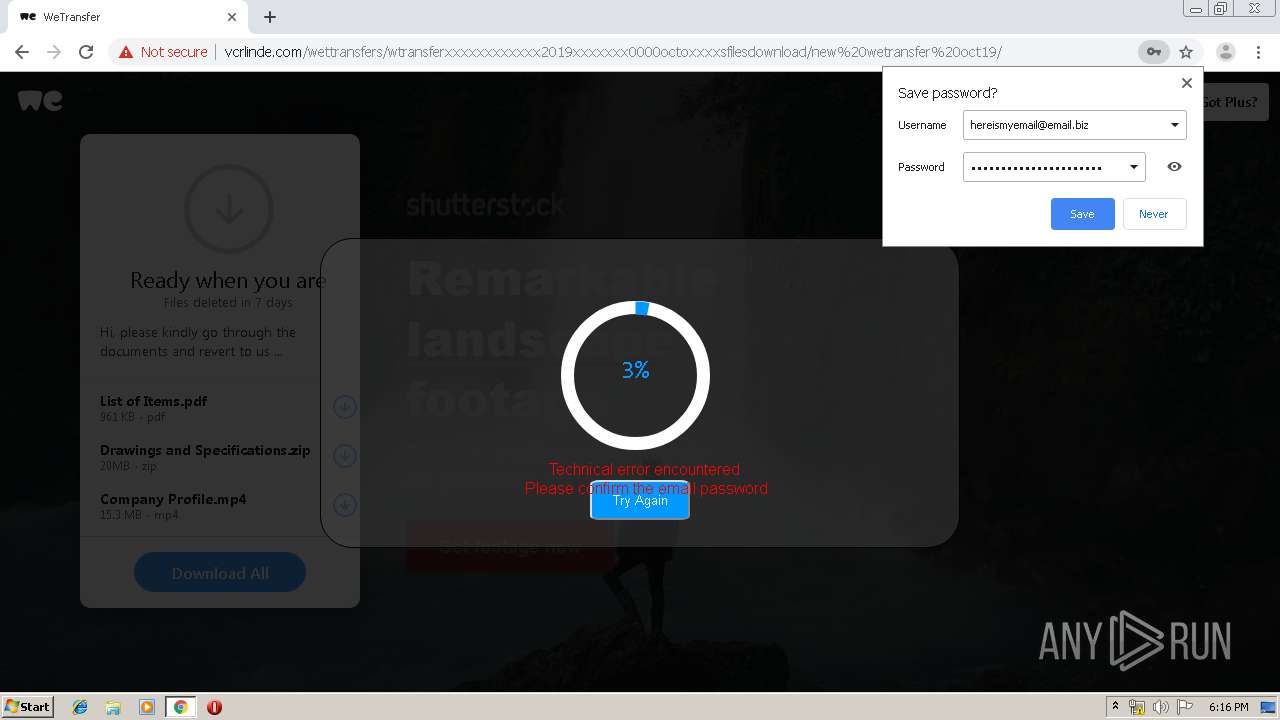
2260 | chrome.exe | POST | 302 | 45.13.252.35:80 | http://vcrlinde.com/wettransfers/wtransferxxxxxxxxxxxx2019xxxxxxx0000octoxxxxsfilesdownload/new%20wetransfer%20oct19/assets/css/mai/mai/login.php | unknown | — | — | suspicious |
2260 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 507 b | whitelisted |
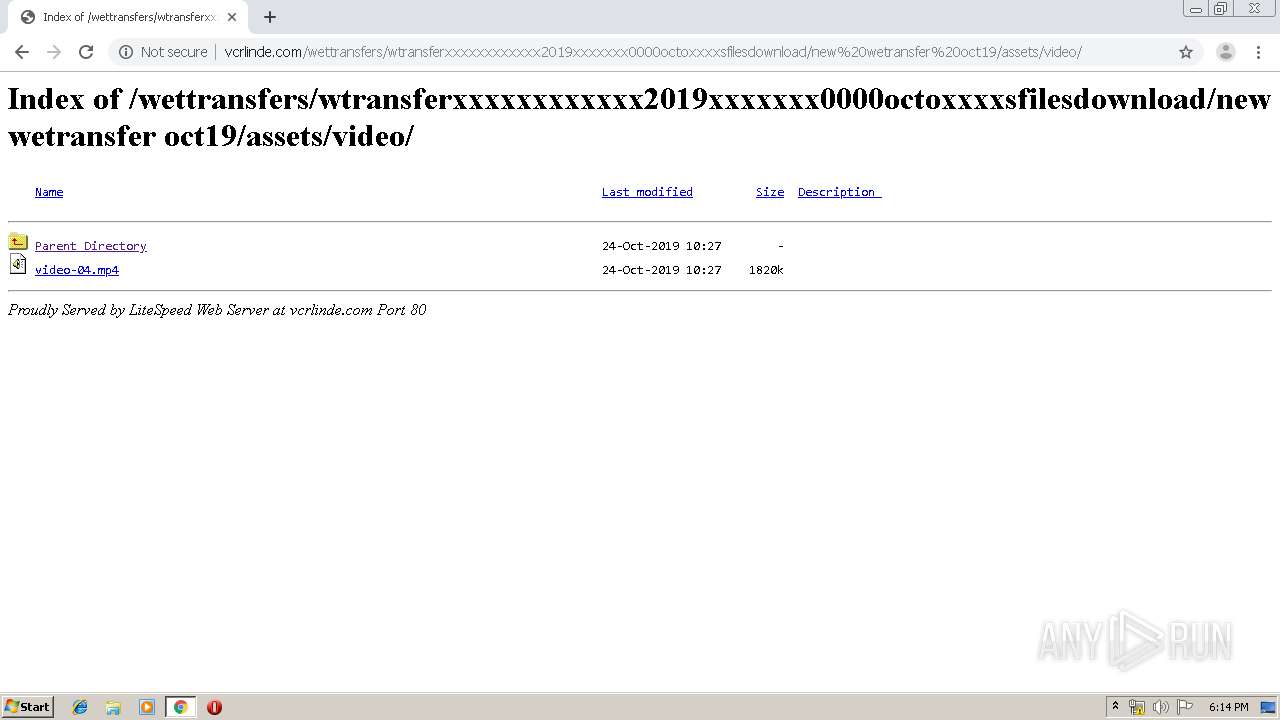
2260 | chrome.exe | GET | 200 | 45.13.252.35:80 | http://vcrlinde.com/wettransfers/wtransferxxxxxxxxxxxx2019xxxxxxx0000octoxxxxsfilesdownload/new%20wetransfer%20oct19/assets/css/mai/mai/mailbox.jpg | unknown | image | 9.12 Kb | suspicious |
2260 | chrome.exe | POST | 302 | 45.13.252.35:80 | http://vcrlinde.com/wettransfers/wtransferxxxxxxxxxxxx2019xxxxxxx0000octoxxxxsfilesdownload/new%20wetransfer%20oct19/assets/css/mai/mai/login.php | unknown | — | — | suspicious |
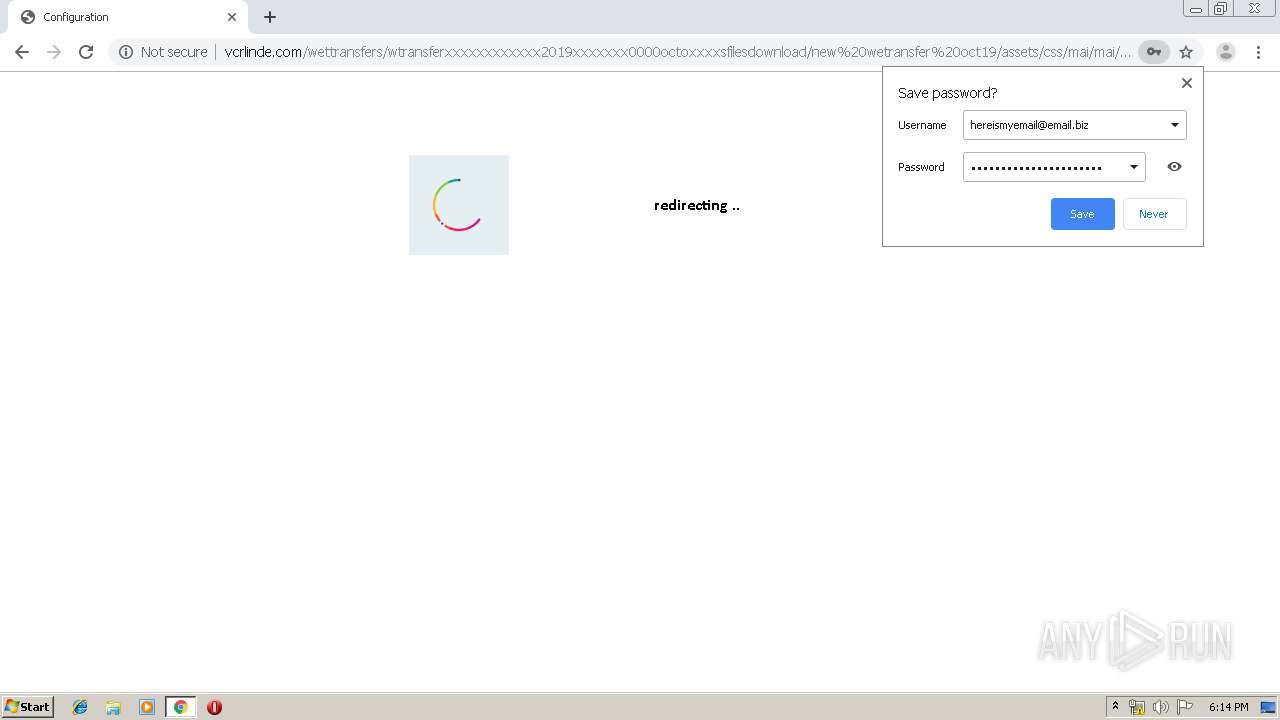
2260 | chrome.exe | GET | 200 | 45.13.252.35:80 | http://vcrlinde.com/wettransfers/wtransferxxxxxxxxxxxx2019xxxxxxx0000octoxxxxsfilesdownload/new%20wetransfer%20oct19/assets/css/mai/mai/updated.php | unknown | html | 1.72 Kb | suspicious |
2260 | chrome.exe | GET | 403 | 185.176.43.92:80 | http://2019-up-da-te-938383.eu5.net/loginmodule.css | BG | html | 121 b | malicious |
2260 | chrome.exe | GET | 200 | 173.194.7.57:80 | http://r3---sn-p5qlsnsr.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qlsnsr&ms=nvh&mt=1575655879&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2260 | chrome.exe | GET | 403 | 185.176.43.92:80 | http://2019-up-da-te-938383.eu5.net/images/40.ico | BG | html | 121 b | malicious |
2260 | chrome.exe | GET | 403 | 185.176.43.92:80 | http://2019-up-da-te-938383.eu5.net/abstract.simplenet.com/point2.html | BG | html | 121 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2260 | chrome.exe | 216.58.206.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 45.13.252.35:80 | vcrlinde.com | — | — | suspicious |
2260 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 185.176.43.92:80 | 2019-up-da-te-938383.eu5.net | Zetta Hosting Solutions LLC. | BG | malicious |
2260 | chrome.exe | 172.217.18.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
— | — | 45.13.252.35:80 | vcrlinde.com | — | — | suspicious |
2260 | chrome.exe | 172.217.135.6:80 | r1---sn-p5qlsndk.gvt1.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 172.217.22.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 173.194.7.57:80 | r3---sn-p5qlsnsr.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vcrlinde.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
2019-up-da-te-938383.eu5.net |
| malicious |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-p5qlsndk.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2260 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |
2260 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
2260 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |
2260 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |
2260 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
2260 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |
2260 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |
4 ETPRO signatures available at the full report