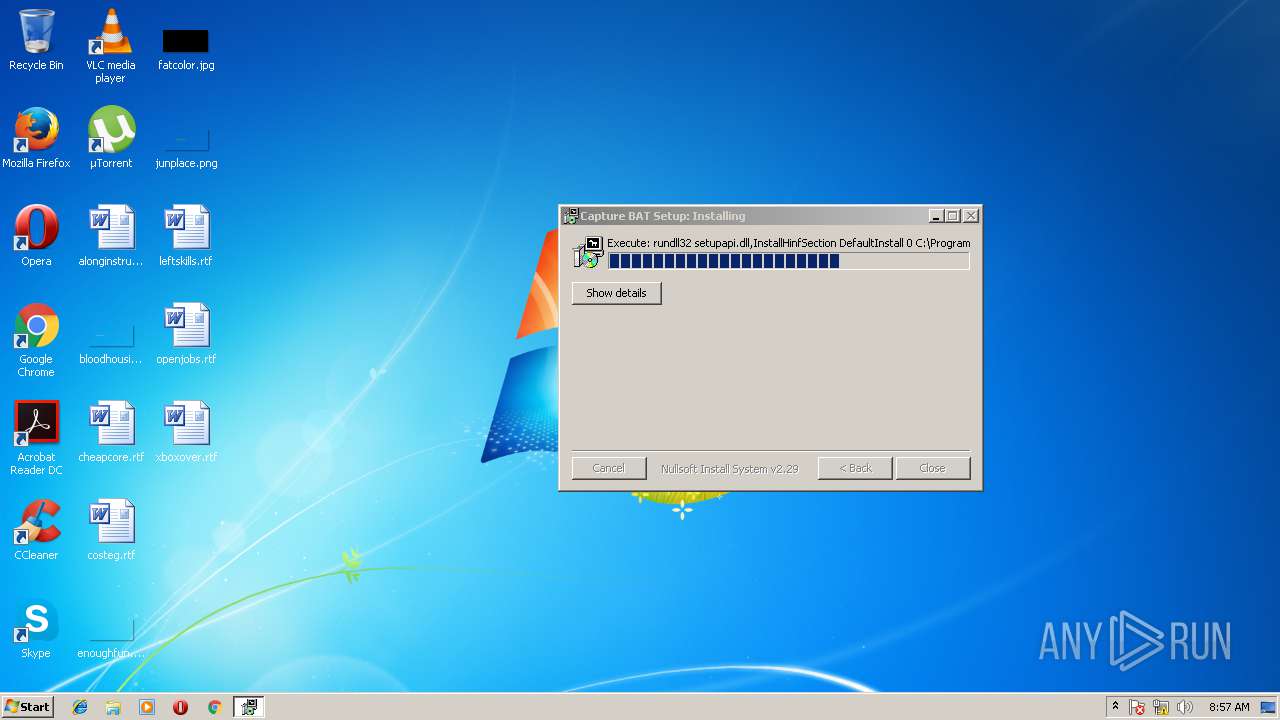
| File name: | CaptureBAT-Setup-2.0.0-5574.exe |
| Full analysis: | https://app.any.run/tasks/85d87af2-0b07-4931-8904-1e722fc45109 |
| Verdict: | Malicious activity |
| Analysis date: | March 16, 2018, 08:57:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | C1894E46FFE89BE6CA35729D9DAB6145 |
| SHA1: | C507C1FEA3C550DC32D4B0238DF47115AB4CD8DE |
| SHA256: | C91E50A921F07EB7CE510441761DAF38F3E4E6340CF9FAF67E660A3D13BD88E8 |
| SSDEEP: | 12288:v6Tgc+jrhgvYeaRBlfOKYvS0z8TRAPa9NGgqdKbqAzbsABd:0gCwxj4VvSPyiyMb |
MALICIOUS
Changes the autorun value in the registry
- rundll32.exe (PID: 3612)
- rundll32.exe (PID: 2280)
SUSPICIOUS
Modifies files in the system directory
- rundll32.exe (PID: 3612)
- rundll32.exe (PID: 2280)
Creates files in the Windows directory
- rundll32.exe (PID: 3612)
- rundll32.exe (PID: 2280)
Creates files in the program directory
- CaptureBAT-Setup-2.0.0-5574.exe (PID: 3112)
Removes files from Windows directory
- rundll32.exe (PID: 2280)
Creates files in the driver directory
- rundll32.exe (PID: 2280)
Creates or modifies windows services
- rundll32.exe (PID: 2280)
Creates a software uninstall entry
- CaptureBAT-Setup-2.0.0-5574.exe (PID: 3112)
INFO
Dropped object may contain URL's
- CaptureBAT-Setup-2.0.0-5574.exe (PID: 3112)
Loads rich edit control libraries
- CaptureBAT-Setup-2.0.0-5574.exe (PID: 3112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:07:14 17:12:54+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fb |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jul-2007 15:12:54 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 14-Jul-2007 15:12:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005B0C | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46412 |
.rdata | 0x00007000 | 0x00001286 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04312 |
.data | 0x00009000 | 0x00025CD8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.16525 |
.ndata | 0x0002F000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00037000 | 0x000007B0 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.19719 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.50665 | 744 | UNKNOWN | English - United States | RT_ICON |
102 | 2.74309 | 184 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
46
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
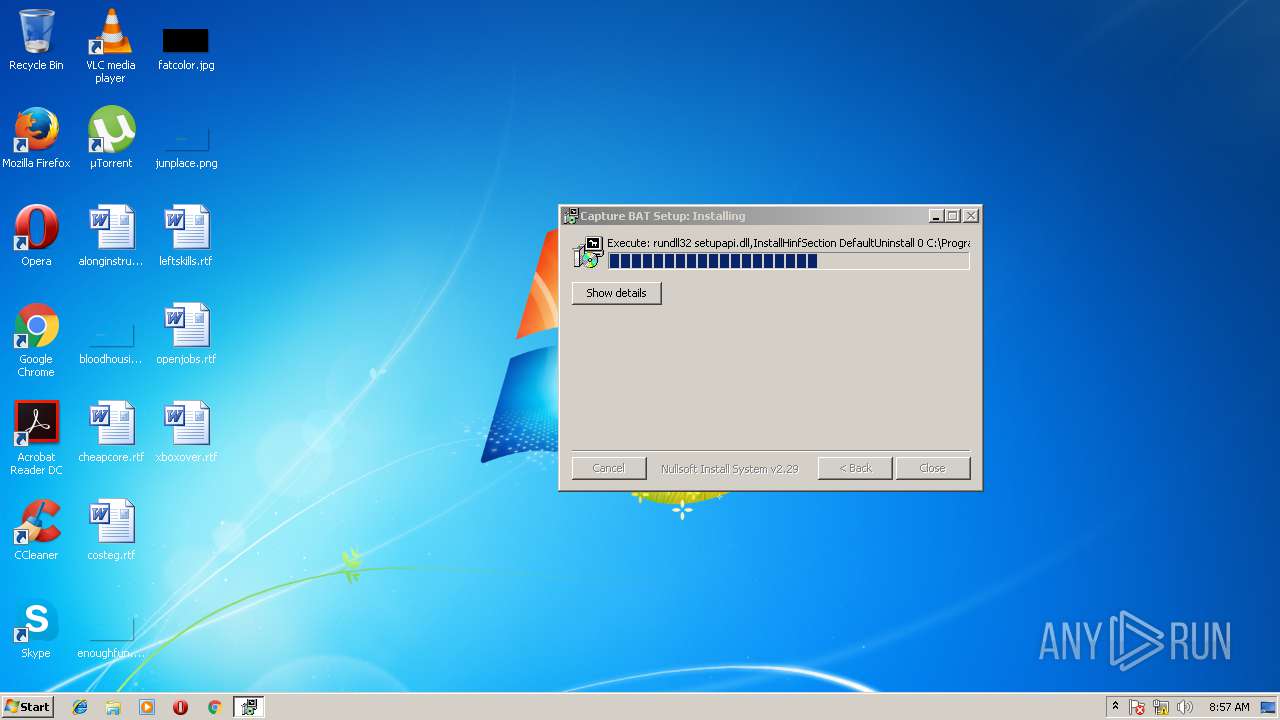
| 2280 | rundll32 setupapi.dll,InstallHinfSection DefaultInstall 0 C:\Program Files\Capture\FileMonitorInstallation.inf | C:\Windows\system32\rundll32.exe | CaptureBAT-Setup-2.0.0-5574.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2388 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\system32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2600 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2900 | "C:\Users\admin\AppData\Local\Temp\CaptureBAT-Setup-2.0.0-5574.exe" | C:\Users\admin\AppData\Local\Temp\CaptureBAT-Setup-2.0.0-5574.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3008 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\AppData\Local\Temp\CaptureBAT-Setup-2.0.0-5574.exe" | C:\Users\admin\AppData\Local\Temp\CaptureBAT-Setup-2.0.0-5574.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 3612 | rundll32 setupapi.dll,InstallHinfSection DefaultUninstall 0 C:\Program Files\Capture\FileMonitorInstallation.inf | C:\Windows\system32\rundll32.exe | CaptureBAT-Setup-2.0.0-5574.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3624 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\system32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
102
Read events
81
Write events
19
Delete events
2
Modification events
| (PID) Process: | (2388) runonce.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | GrpConv |
Value: grpconv -o | |||
| (PID) Process: | (3612) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (3612) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | GrpConv |
Value: grpconv -o | |||
| (PID) Process: | (2280) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\GroupOrderList |
| Operation: | write | Name: | FSFilter Activity Monitor |
Value: 020000000100000002000000 | |||
| (PID) Process: | (2280) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\CaptureFileMonitor\Instances |
| Operation: | write | Name: | DefaultInstance |
Value: Capture - Top Instance | |||
| (PID) Process: | (2280) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\CaptureFileMonitor\Instances\Capture - Top Instance |
| Operation: | write | Name: | Altitude |
Value: 385000 | |||
| (PID) Process: | (2280) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\CaptureFileMonitor\Instances\Capture - Top Instance |
| Operation: | write | Name: | Flags |
Value: 0 | |||
| (PID) Process: | (2280) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | GrpConv |
Value: grpconv -o | |||
| (PID) Process: | (3624) runonce.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | GrpConv |
Value: grpconv -o | |||
| (PID) Process: | (2388) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
7
Suspicious files
1
Text files
22
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2280 | rundll32.exe | C:\Windows\system32\DRIVERS\SETBA6F.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | rundll32.exe | C:\Windows\INF\setupapi.app.log | text | |
MD5:— | SHA256:— | |||
| 3612 | rundll32.exe | C:\Windows\INF\setupapi.app.log | text | |
MD5:— | SHA256:— | |||
| 3112 | CaptureBAT-Setup-2.0.0-5574.exe | C:\Program Files\Capture\ProcessMonitor.exl | text | |
MD5:2EC9BE16BEEAC6AFAA115B2A9EEC5258 | SHA256:E91BB5871E840777B45691643105F6F015A9ADFF215EA7F82287148D451B71AE | |||
| 3112 | CaptureBAT-Setup-2.0.0-5574.exe | C:\Program Files\Capture\FileMonitor.exl | text | |
MD5:9F3139343EA67CBB703E8271B131FA78 | SHA256:69DA0C07B6A9D41CBF32372AA6513D0D0902764D35FA0103F84E6F3556B996C1 | |||
| 3112 | CaptureBAT-Setup-2.0.0-5574.exe | C:\Program Files\Capture\Readme.txt | text | |
MD5:DFF6E78B6E49AD370A083601BABD735B | SHA256:C60B4D4C4A3B0E8BC438CAD5DE28625B1271088429FBDE40BCF85F2B8B5F27B1 | |||
| 3112 | CaptureBAT-Setup-2.0.0-5574.exe | C:\Program Files\Capture\RegistryMonitor.exl | text | |
MD5:2E3F309CFA5C53CA4473CCF34C13E2A5 | SHA256:635A8489CCA2000A2208183BDCA3091D465B53563F9CD5EB152B80CA2C53A55C | |||
| 3112 | CaptureBAT-Setup-2.0.0-5574.exe | C:\Program Files\Capture\CaptureProcessMonitor.sys | executable | |
MD5:A6F0F372910D8114B65775CABF165ACB | SHA256:2F42C45EA02A2E606B6696B2A287148483A0D020ED0CD4CB2D1E3789B494BBA8 | |||
| 3112 | CaptureBAT-Setup-2.0.0-5574.exe | C:\Program Files\Capture\CaptureFileMonitor.sys | executable | |
MD5:D70F8AFF620E1203C45680DC827A6B3E | SHA256:B2E6F2062B2F81CD0F3E1F2503F387AE824A84A8DD77ED55CF92DA03FDEEC130 | |||
| 3112 | CaptureBAT-Setup-2.0.0-5574.exe | C:\Program Files\Capture\FileMonitorInstallation.inf | binary | |
MD5:C2D8DFE752F2257DC12B983B82558566 | SHA256:219ABB4A859D8E62EFFC584BFE113D373C9FF471EA893B97449952E38C816270 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report