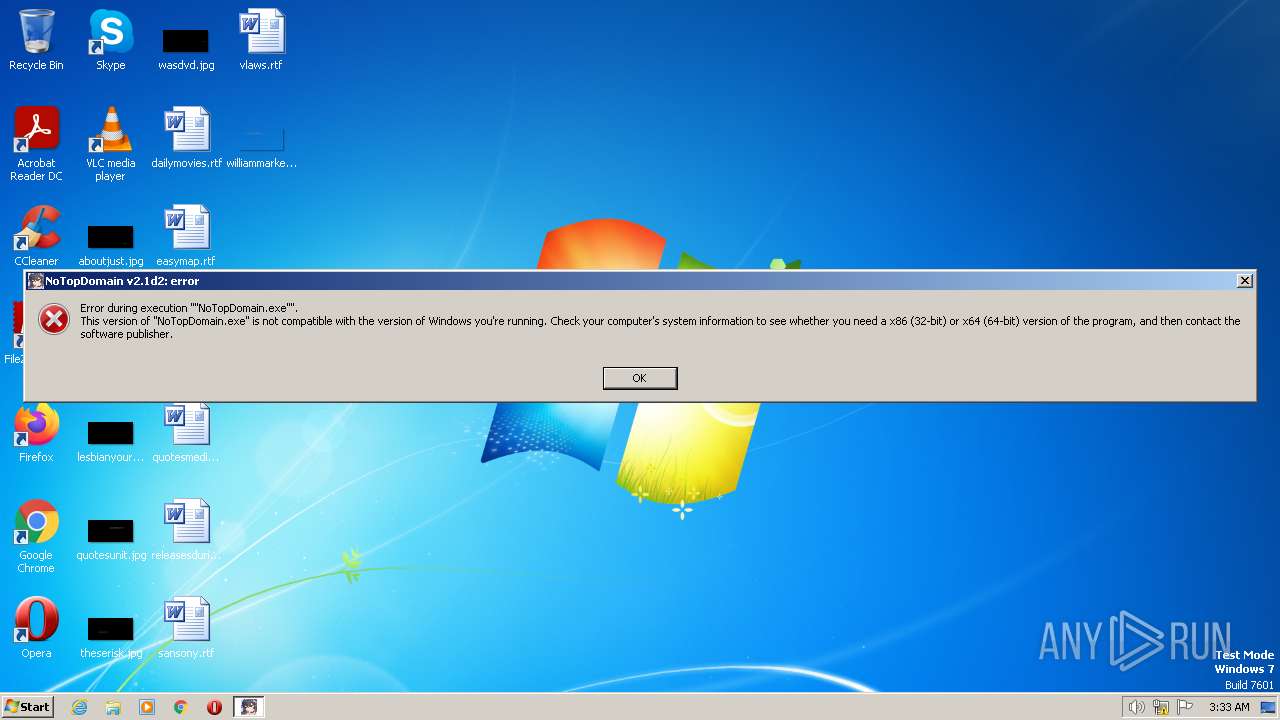
| File name: | NoTopDomain v2.1d2.exe |
| Full analysis: | https://app.any.run/tasks/0388832a-59d1-46c4-b816-f9e67454dc38 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2023, 02:32:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0E271FB927932404AB8D0BD15061B784 |
| SHA1: | 9F2E39AB4877D4DDB6C289A7EFD2B0578CB949B2 |
| SHA256: | C90E006F1FFC22A7CCFFAAB11BE3EE3135C74B8D705AF9EA25AB2A52FA1C5F63 |
| SSDEEP: | 393216:BBsotuKOJcGcY7ndosaAtEgS1IkMrKpzbugrdO524SuQAMYap:3xoc8TdAnT8grdyS9p |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- NoTopDomain v2.1d2.exe (PID: 2732)
Reads the Internet Settings
- NoTopDomain v2.1d2.exe (PID: 2732)
INFO
Checks supported languages
- NoTopDomain v2.1d2.exe (PID: 2732)
Create files in a temporary directory
- NoTopDomain v2.1d2.exe (PID: 2732)
The process checks LSA protection
- NoTopDomain v2.1d2.exe (PID: 2732)
Reads the computer name
- NoTopDomain v2.1d2.exe (PID: 2732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| ProductVersion: | 1.7.1.3901 |
|---|---|
| ProductName: | 7-Zip SFX |
| PrivateBuild: | April 1, 2016 |
| OriginalFileName: | 7ZSfxMod_x86.exe |
| LegalCopyright: | Copyright © 2005-2016 Oleg N. Scherbakov |
| InternalName: | 7ZSfxMod |
| FileVersion: | 1.7.1.3901 |
| FileDescription: | 7z Setup SFX (x86) |
| CompanyName: | Oleg N. Scherbakov |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | Private build |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.7.1.3901 |
| FileVersionNumber: | 1.7.1.3901 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1933f |
| UninitializedDataSize: | - |
| InitializedDataSize: | 48128 |
| CodeSize: | 102400 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2018:05:21 01:48:02+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-May-2018 01:48:02 |
| CompanyName: | Oleg N. Scherbakov |
| FileDescription: | 7z Setup SFX (x86) |
| FileVersion: | 1.7.1.3901 |
| InternalName: | 7ZSfxMod |
| LegalCopyright: | Copyright © 2005-2016 Oleg N. Scherbakov |
| OriginalFilename: | 7ZSfxMod_x86.exe |
| PrivateBuild: | April 1, 2016 |
| ProductName: | 7-Zip SFX |
| ProductVersion: | 1.7.1.3901 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-May-2018 01:48:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00018E9A | 0x00019000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.68813 |
.rdata | 0x0001A000 | 0x00003FDA | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.78584 |
.data | 0x0001E000 | 0x00004AF0 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.32705 |
.rsrc | 0x00023000 | 0x000056E8 | 0x00005800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.11776 |
.reloc | 0x00029000 | 0x00001A96 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.65147 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2112 | 777 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.60602 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.63074 | 488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.3817 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
54 | 6.32101 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.0815 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
ole32.dll |
Total processes
37
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2732 | "C:\Users\admin\AppData\Local\Temp\NoTopDomain v2.1d2.exe" | C:\Users\admin\AppData\Local\Temp\NoTopDomain v2.1d2.exe | explorer.exe | ||||||||||||
User: admin Company: Oleg N. Scherbakov Integrity Level: MEDIUM Description: 7z Setup SFX (x86) Exit code: 0 Version: 1.7.1.3901 Modules
| |||||||||||||||
Total events
761
Read events
753
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2732) NoTopDomain v2.1d2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2732) NoTopDomain v2.1d2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2732) NoTopDomain v2.1d2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2732) NoTopDomain v2.1d2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
45
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2732 | NoTopDomain v2.1d2.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\PyQt5\QtCore.pyd | executable | |
MD5:1DA7B606380B624274E7E3C5F25209BC | SHA256:203BB6236F23F57AD8CDAB5BBF4537A4ABBC0B0879CF2893A8DC930E679DD846 | |||
| 2732 | NoTopDomain v2.1d2.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\select.pyd | executable | |
MD5:4AC28414A1D101E94198AE0AC3BD1EB8 | SHA256:B5D4D5B6DA675376BD3B2824D9CDA957B55FE3D8596D5675381922EF0E64A0F5 | |||
| 2732 | NoTopDomain v2.1d2.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\PyQt5\QtGui.pyd | executable | |
MD5:3A9A1CD6F3A0EFE67B5994B82D7C4E21 | SHA256:2CA28D29EC4F2F50B4CCC70C7D6399B314151BC38852833D2D30097773BB1C00 | |||
| 2732 | NoTopDomain v2.1d2.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\psutil\_psutil_windows.pyd | executable | |
MD5:EBEFBC98D468560B222F2D2D30EBB95C | SHA256:67C17558B635D6027DDBB781EA4E79FC0618BBEC7485BD6D84B0EBCD9EF6A478 | |||
| 2732 | NoTopDomain v2.1d2.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\unicodedata.pyd | executable | |
MD5:2AB7E66DFF1893FEA6F124971221A2A9 | SHA256:A5DB7900ECD5EA5AB1C06A8F94B2885F00DD2E1ADF34BCB50C8A71691A97804F | |||
| 2732 | NoTopDomain v2.1d2.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\PyQt5\QtWidgets.pyd | executable | |
MD5:9E4B668C64D9E7A6C59BEBE4B0D6D7C0 | SHA256:E4A06FE65B02C568DB984771FB9A46EA95A8E4353EA85C942F954CBA02DEC635 | |||
| 2732 | NoTopDomain v2.1d2.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\win32api.pyd | executable | |
MD5:1D6762B494DC9E60CA95F7238AE1FB14 | SHA256:FAE5323E2119A8F678055F4244177B5806C7B6B171B1945168F685631B913664 | |||
| 2732 | NoTopDomain v2.1d2.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\win32gui.pyd | executable | |
MD5:3C81C0CEEBB2B5C224A56C024021EFAD | SHA256:6085BC00A1F157C4D2CC0609E20E1E20D2572FE6498DE3BEC4C9C7BEBCFBB629 | |||
| 2732 | NoTopDomain v2.1d2.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\PyQt5\sip.pyd | executable | |
MD5:AB7A257BD9EB64087D121F9C960DCA5B | SHA256:BB78FC42ADDD319D53AF03D9E6AC0E050698228C70847A3A53A55F398920E8C6 | |||
| 2732 | NoTopDomain v2.1d2.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\win32process.pyd | executable | |
MD5:936B26A67E6C7788C3A5268F478E01B8 | SHA256:0459439EF3EFA0E0FC2B8CA3F0245826E9BBD7E8F3266276398921A4AA899FBD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4004 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |