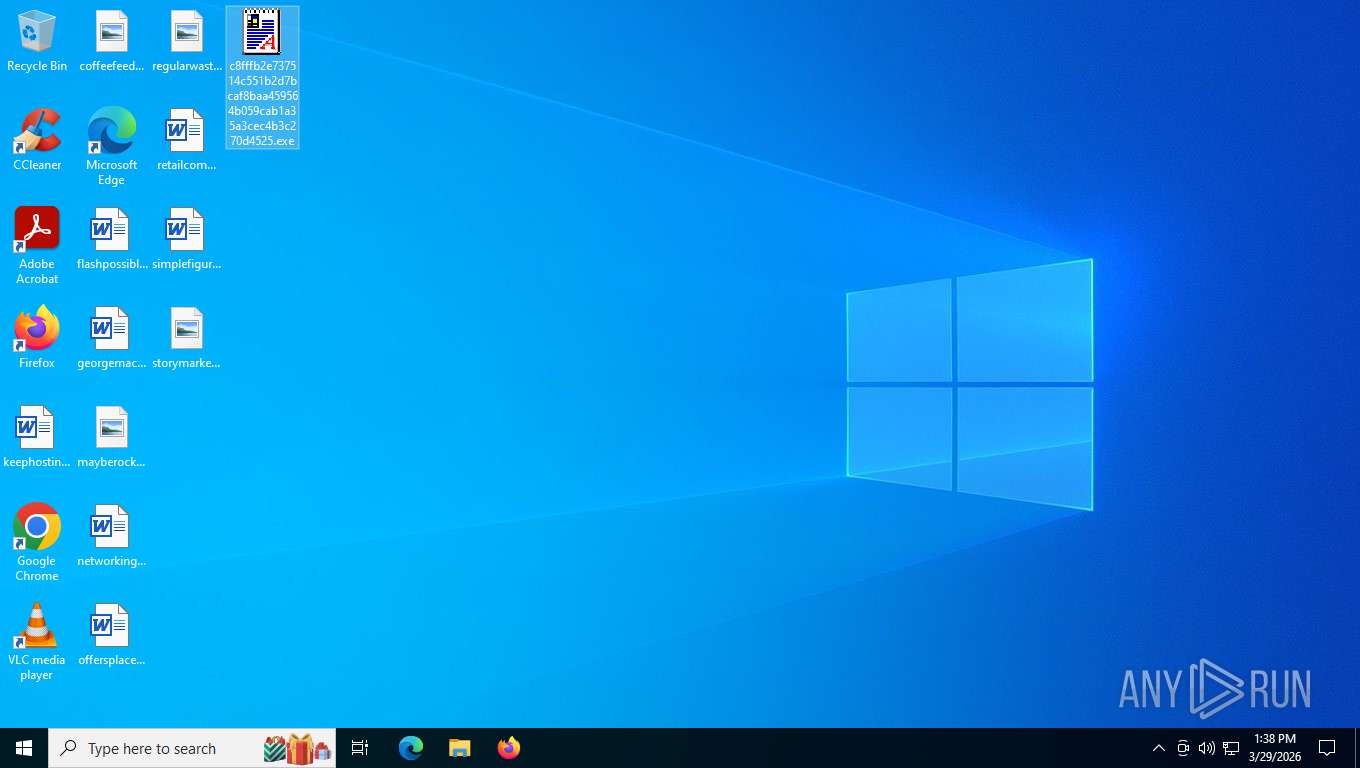
| File name: | c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe |
| Full analysis: | https://app.any.run/tasks/a7234a7f-8aab-48d7-8ab5-de67fa06b796 |
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2026, 17:37:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 3018E99857F31A59E0777396AE634A8F |
| SHA1: | 7031CFE76EE7B2C925F2C00372FB9EF7F983F60C |
| SHA256: | C8FFFB2E737514C551B2D7BCAF8BAA459564B059CAB1A35A3CEC4B3C270D4525 |
| SSDEEP: | 768:vWkliAnUQYkYKzqbjC5RqHjrYReyZx+l0oKriCPRDLk:+ySsz6jGeyZx+l0TRM |
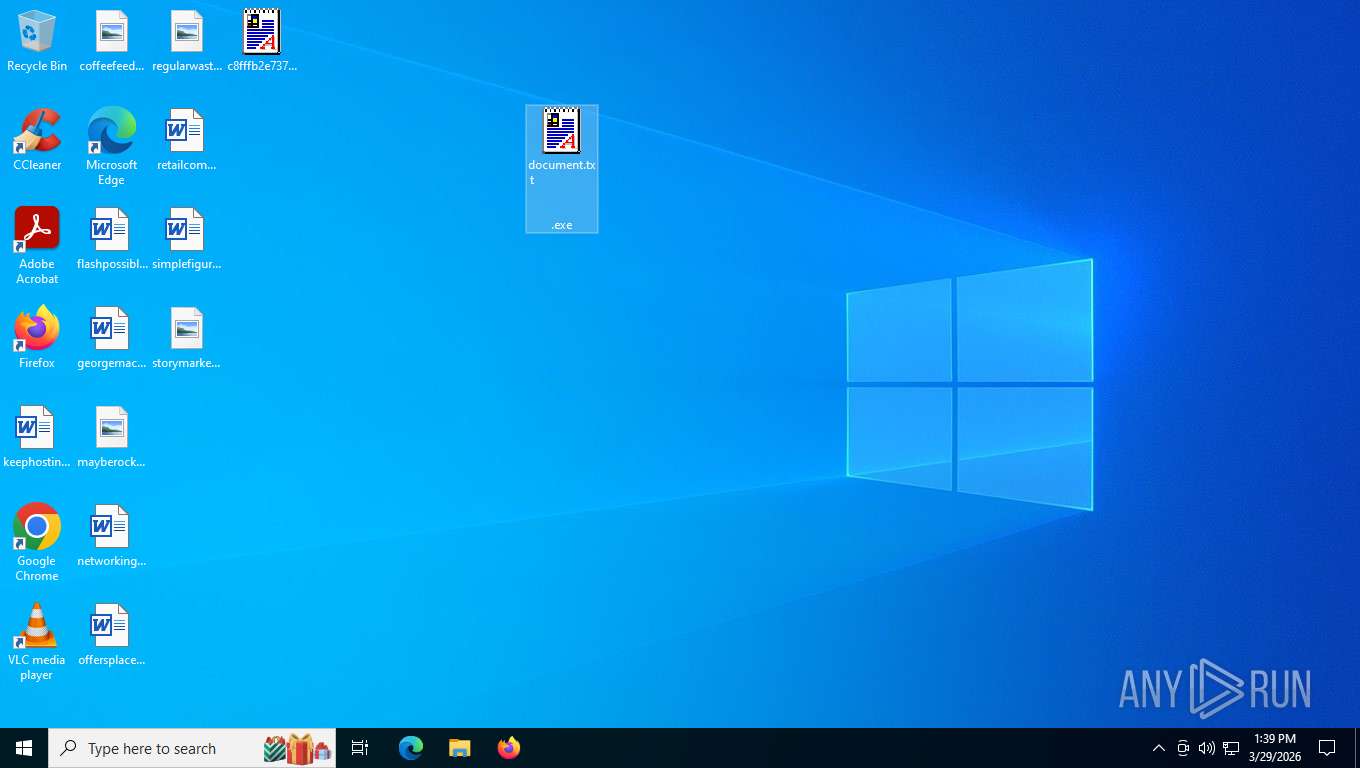
MALICIOUS
SKYBAG mutex has been found
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 3652)
- FVProtect.exe (PID: 1464)
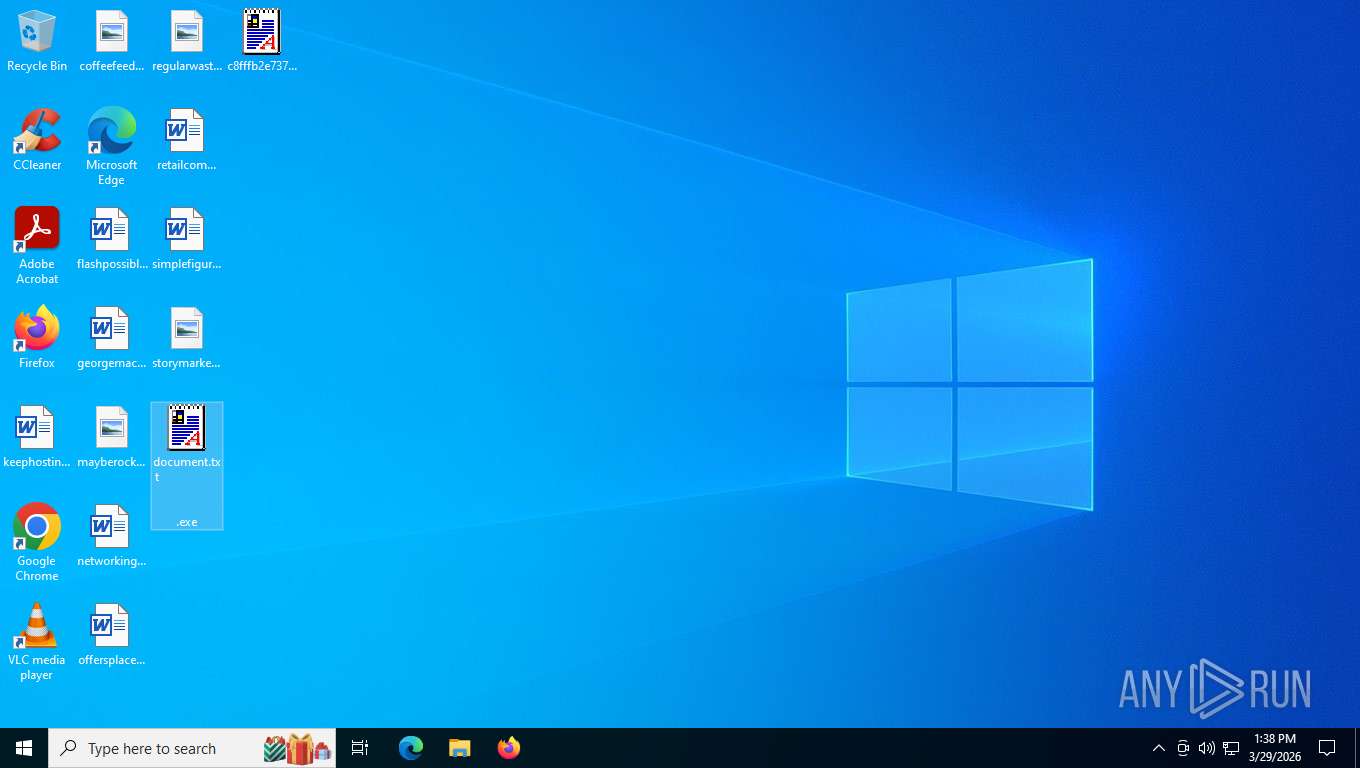
- document.txt .exe (PID: 2424)
- document.txt .exe (PID: 8328)
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 4624)
Changes the autorun value in the registry
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 4624)
SUSPICIOUS
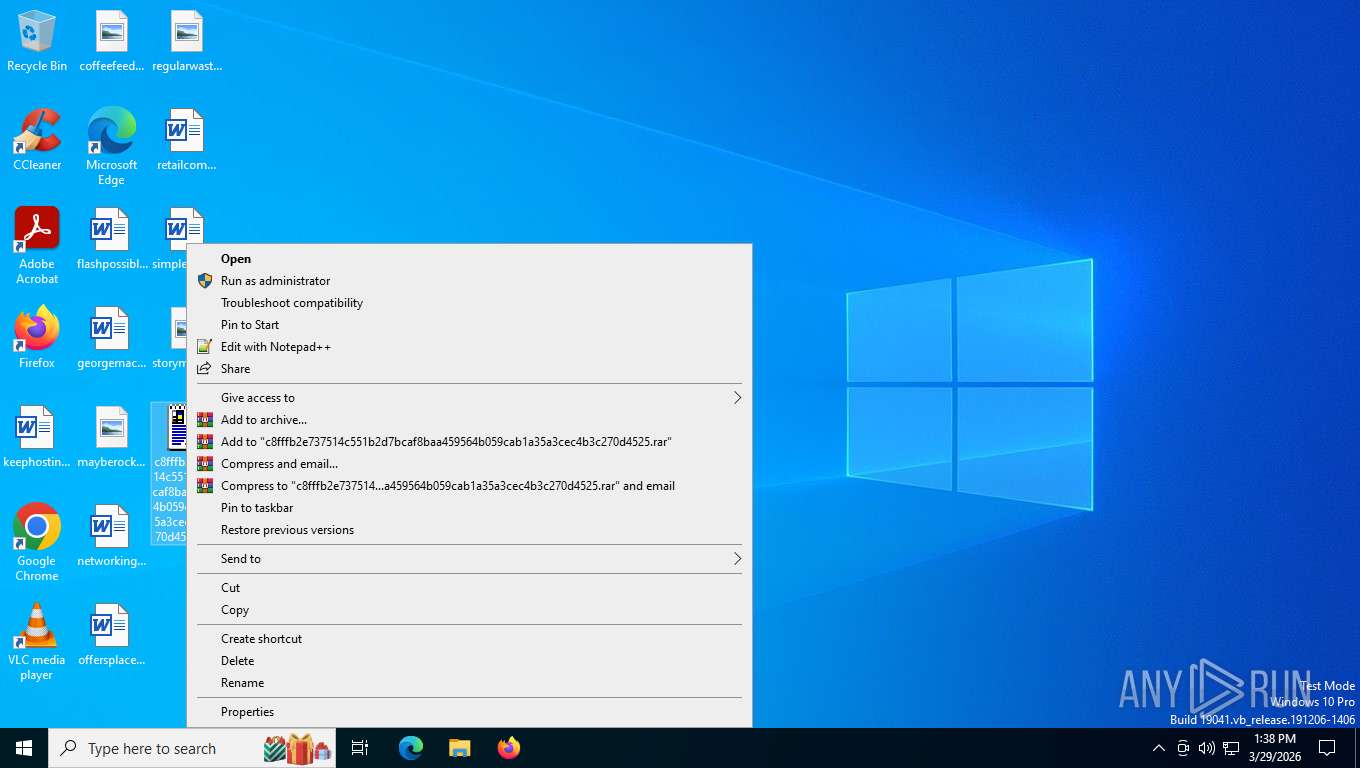
Drops a file with a rarely used extension (PIF)
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 4624)
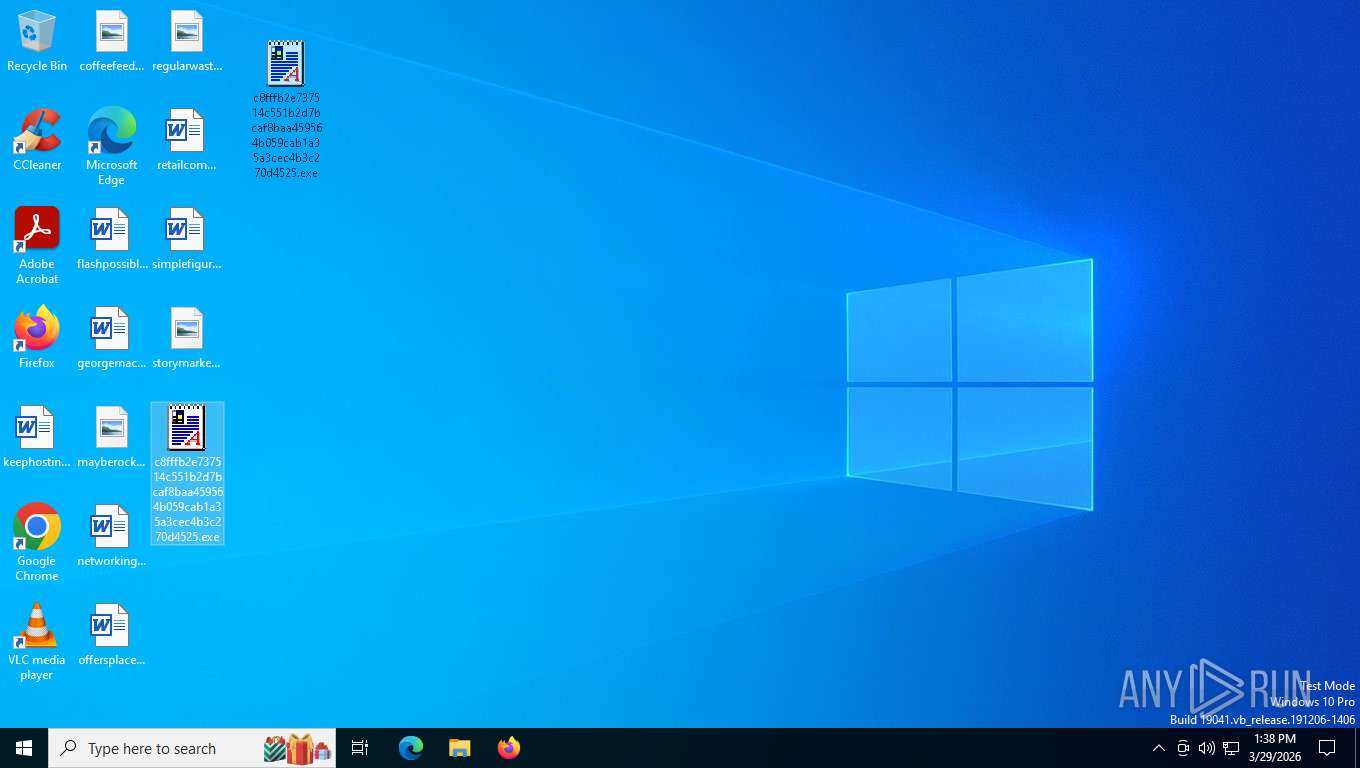
Executable content was dropped or overwritten
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 4624)
Connects to SMTP port
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 4624)
INFO
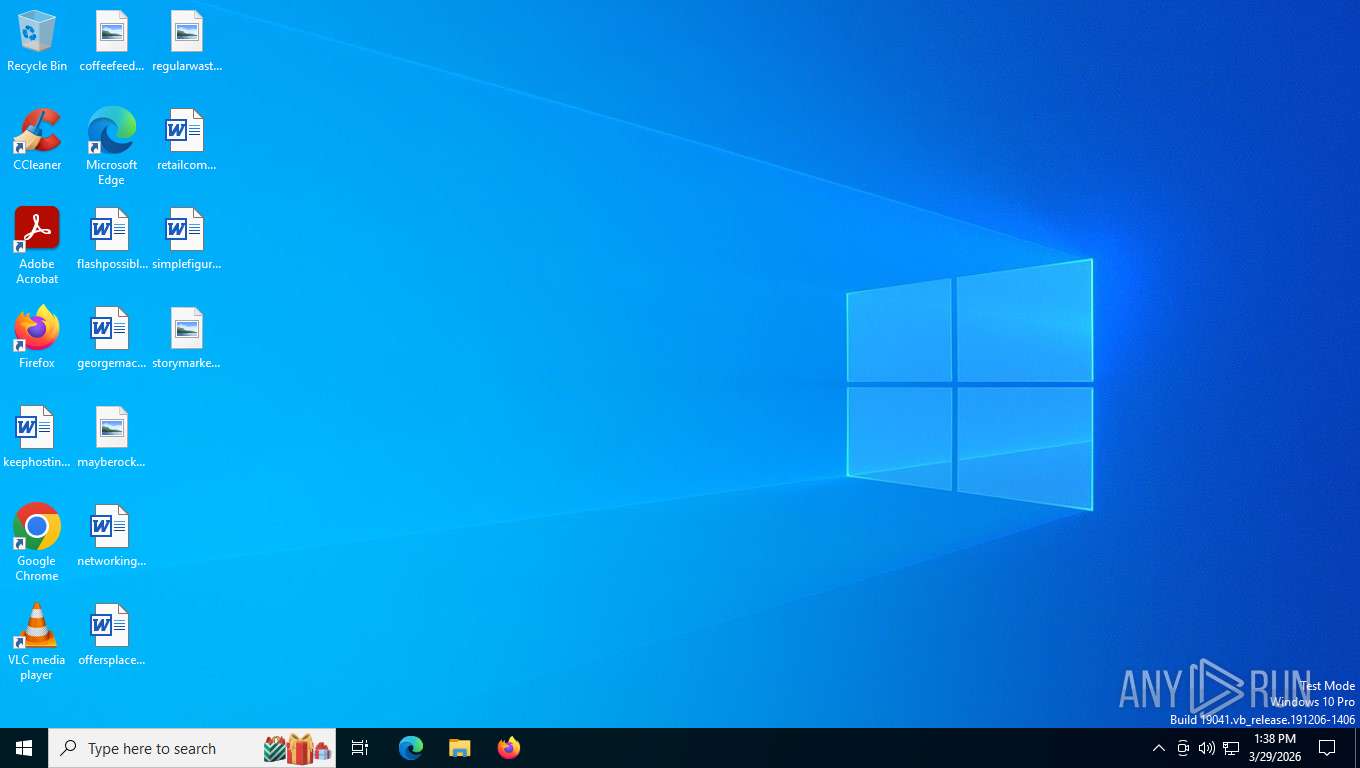
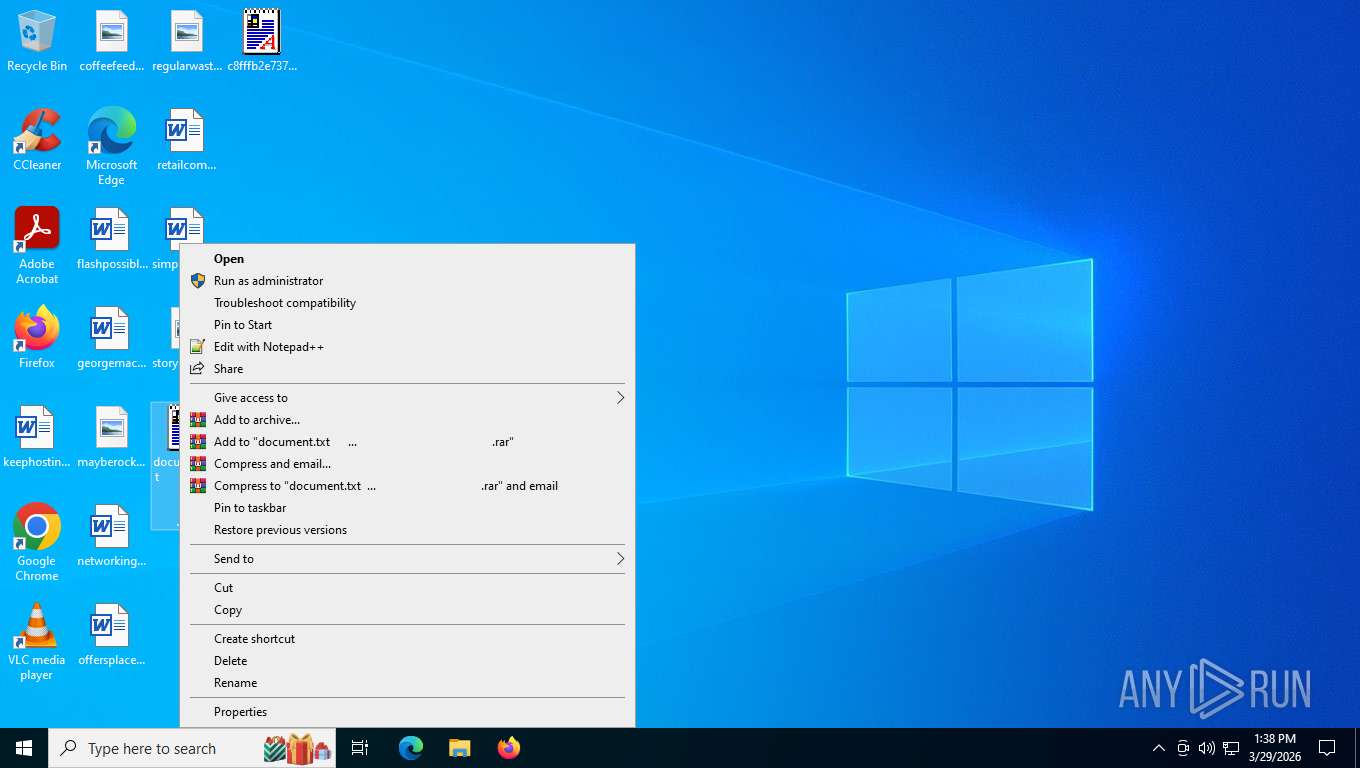
Manual execution by a user
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 4624)
- document.txt .exe (PID: 8328)
- document.txt .exe (PID: 2424)
- FVProtect.exe (PID: 1464)
Failed to create an executable file in Windows directory
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 3652)
Checks supported languages
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 4624)
Reads security settings of Internet Explorer
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 4624)
Creates files or folders in the user directory
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 4624)
Reads the computer name
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 4624)
Launching a file from a Registry key
- c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe (PID: 4624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.7) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.4) |
| .exe | | | DOS Executable Generic (23.4) |
| .vxd | | | VXD Driver (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | - |
| CodeSize: | 1024 |
| InitializedDataSize: | 29184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
166
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1464 | C:\WINDOWS\FVProtect.exe | C:\Windows\FVProtect.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\Desktop\document.txt .exe" | C:\Users\admin\Desktop\document.txt .exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\Desktop\c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe" | C:\Users\admin\Desktop\c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3700 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4624 | "C:\Users\admin\Desktop\c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe" | C:\Users\admin\Desktop\c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7324 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 7828 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8328 | "C:\Users\admin\Desktop\document.txt .exe" | C:\Users\admin\Desktop\document.txt .exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
25 002
Read events
24 976
Write events
1
Delete events
25
Modification events
| (PID) Process: | (4624) c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Norton Antivirus AV |
Value: C:\WINDOWS\FVProtect.exe | |||
| (PID) Process: | (4624) c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (4624) c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (4624) c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | system. |
Value: | |||
| (PID) Process: | (4624) c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | msgsvr32 |
Value: | |||
| (PID) Process: | (4624) c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | au.exe |
Value: | |||
| (PID) Process: | (4624) c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | winupd.exe |
Value: | |||
| (PID) Process: | (4624) c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | direct.exe |
Value: | |||
| (PID) Process: | (4624) c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | direct.exe |
Value: | |||
| (PID) Process: | (4624) c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | jijbl |
Value: | |||
Executable files
4 780
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4624 | c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | C:\Windows\zipped.tmp | compressed | |
MD5:CED3C570320E0323070E60AD6BFC9028 | SHA256:151CAEA7EA3D950236C1EFF1BA87D89B4D6DBE49EDFEDC2FD960D1DA0009EFED | |||
| 4624 | c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | C:\Windows\FVProtect.exe | executable | |
MD5:3018E99857F31A59E0777396AE634A8F | SHA256:C8FFFB2E737514C551B2D7BCAF8BAA459564B059CAB1A35A3CEC4B3C270D4525 | |||
| 4624 | c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | C:\Windows\zip1.tmp | text | |
MD5:C3A3DBDEF6859DEA29AED15BA31C11C6 | SHA256:87D4D22484449FB463D4DA6A9AF536AF784A9AF6A7739FA8D79C7199FFF4F6F5 | |||
| 4624 | c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | C:\Windows\zip3.tmp | text | |
MD5:B89DC7A112A4C7A045B9736BA0710BCD | SHA256:E0BFEB9AD99E538EC6426D50F698A076D2DEC13768BC743FC771C136EB5BDACC | |||
| 4624 | c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | C:\Program Files\Microsoft Office\Updates\Download\PackageFiles\5B9936B4-3789-47CD-A7E1-A479148E7D7F\root\vfs\Windows\assembly\GAC_MSIL\Microsoft.AnalysisServices.SPClient.Interfaces\13.0.0.0__89845DCD8080CC91\Harry Potter e book.doc.exe | executable | |
MD5:3018E99857F31A59E0777396AE634A8F | SHA256:C8FFFB2E737514C551B2D7BCAF8BAA459564B059CAB1A35A3CEC4B3C270D4525 | |||
| 4624 | c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | C:\Program Files\Microsoft Office\Updates\Download\PackageFiles\5B9936B4-3789-47CD-A7E1-A479148E7D7F\root\vfs\Windows\assembly\GAC_MSIL\Microsoft.AnalysisServices.SPClient.Interfaces\13.0.0.0__89845DCD8080CC91\Harry Potter game.exe | executable | |
MD5:3018E99857F31A59E0777396AE634A8F | SHA256:C8FFFB2E737514C551B2D7BCAF8BAA459564B059CAB1A35A3CEC4B3C270D4525 | |||
| 4624 | c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | C:\Windows\zip2.tmp | text | |
MD5:19C51F395FDC8DAC38DF5115887013A0 | SHA256:DC01E55359C12DCB7FF8CA94ADDA3318A3D4A05D14107A9DC46F01DEC5109A13 | |||
| 4624 | c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | C:\Program Files\Microsoft Office\Updates\Download\PackageFiles\5B9936B4-3789-47CD-A7E1-A479148E7D7F\root\vfs\Windows\assembly\GAC_MSIL\Microsoft.AnalysisServices.SPClient.Interfaces\13.0.0.0__89845DCD8080CC91\Britney Spears blowjob.jpg.exe | executable | |
MD5:3018E99857F31A59E0777396AE634A8F | SHA256:C8FFFB2E737514C551B2D7BCAF8BAA459564B059CAB1A35A3CEC4B3C270D4525 | |||
| 4624 | c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | C:\Program Files\Microsoft Office\Updates\Download\PackageFiles\5B9936B4-3789-47CD-A7E1-A479148E7D7F\root\vfs\Windows\assembly\GAC_MSIL\Microsoft.AnalysisServices.SPClient.Interfaces\13.0.0.0__89845DCD8080CC91\Britney Spears Sexy archive.doc.exe | executable | |
MD5:3018E99857F31A59E0777396AE634A8F | SHA256:C8FFFB2E737514C551B2D7BCAF8BAA459564B059CAB1A35A3CEC4B3C270D4525 | |||
| 4624 | c8fffb2e737514c551b2d7bcaf8baa459564b059cab1a35a3cec4b3c270d4525.exe | C:\Windows\base64.tmp | text | |
MD5:FD423C9A5BE3ECD2BCCFC5685D32577C | SHA256:51BDA746AF237BA3EF1B0371D6C8233066903F7D69B4D18B3FEE12B55C97010C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
110
DNS requests
450
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
888 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
356 | svchost.exe | POST | 400 | 20.190.160.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
888 | SIHClient.exe | GET | 200 | 74.178.240.51:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
888 | SIHClient.exe | GET | 200 | 74.179.77.204:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
7228 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7228 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
888 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7228 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7532 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.218:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
356 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7228 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |