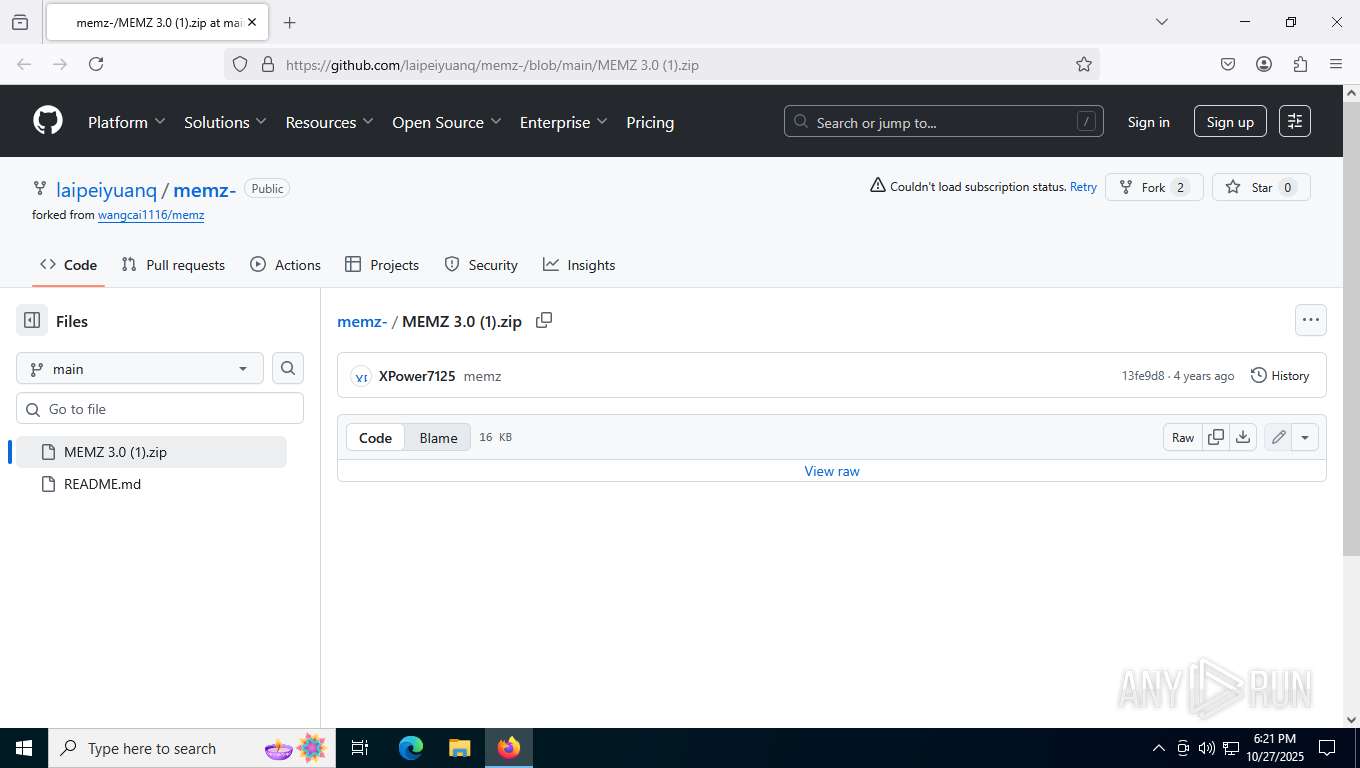
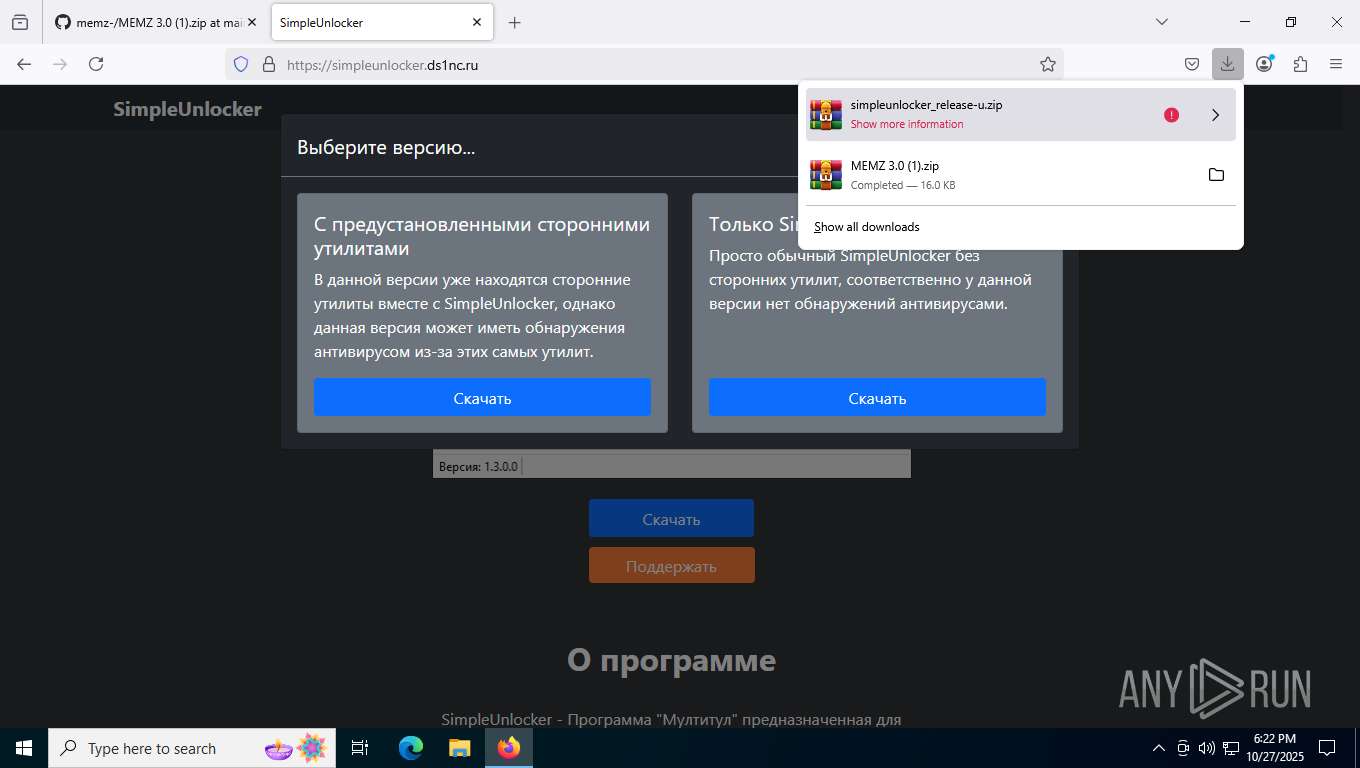
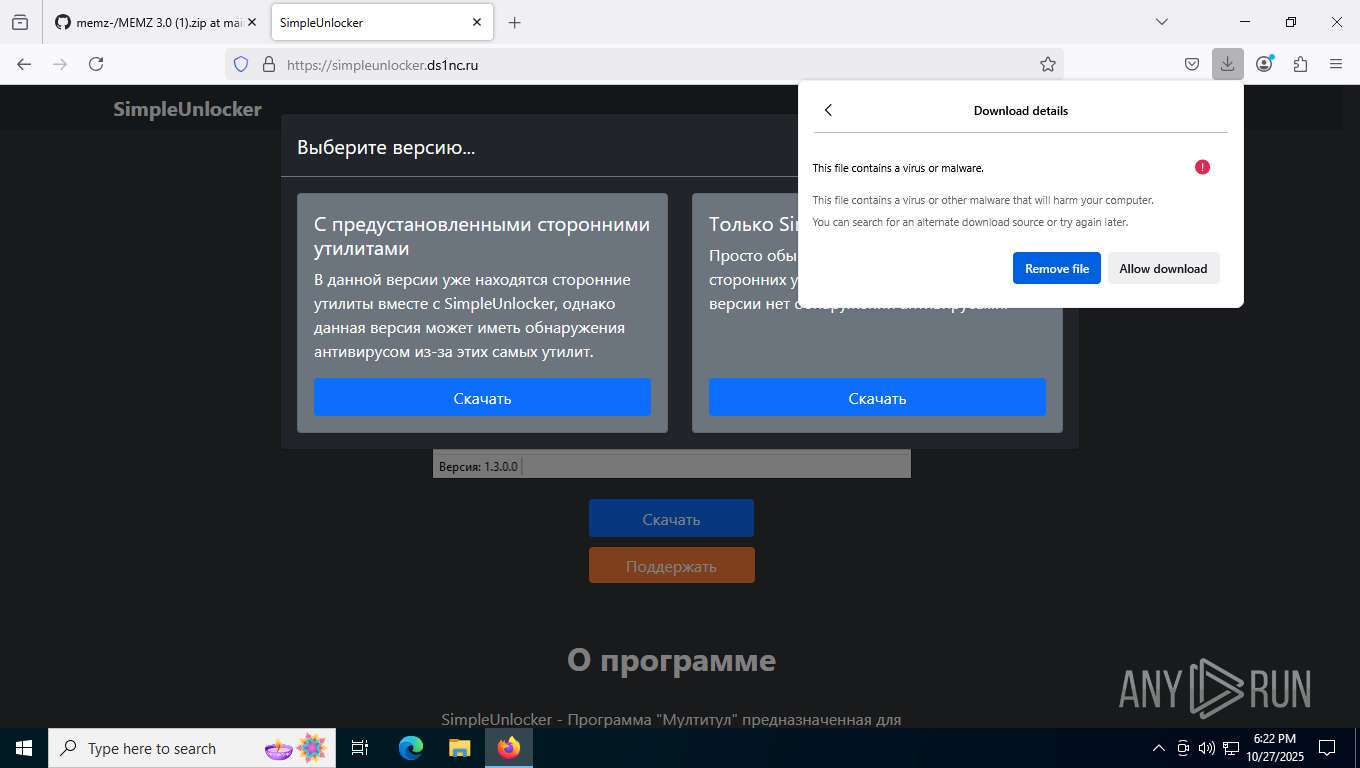
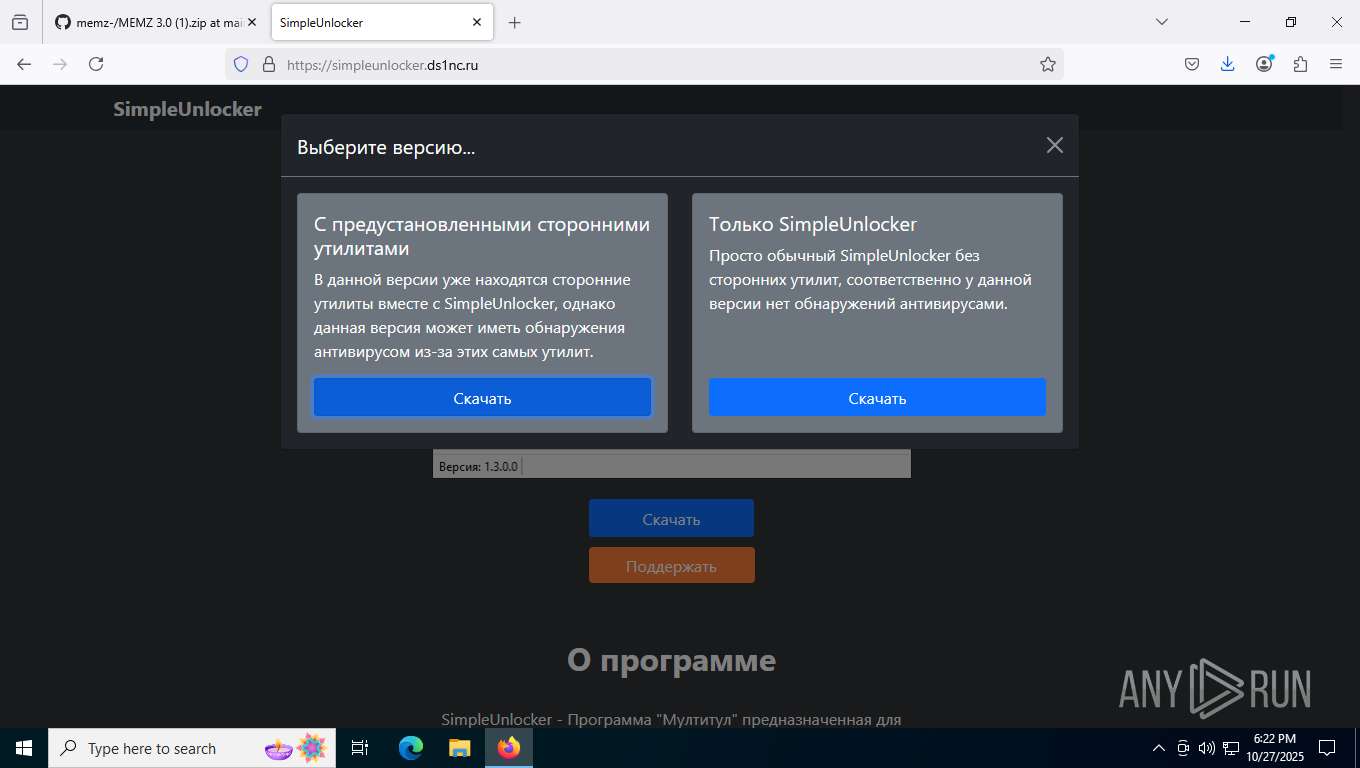
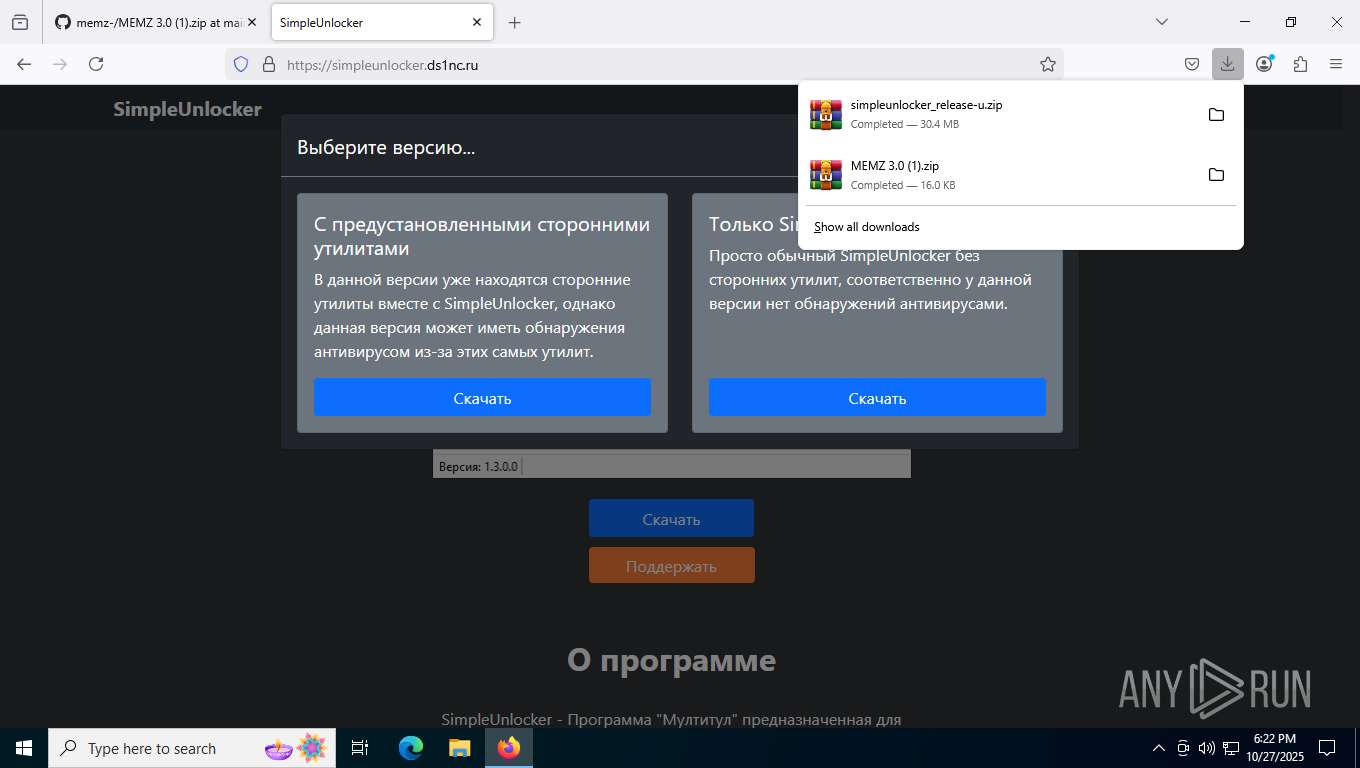
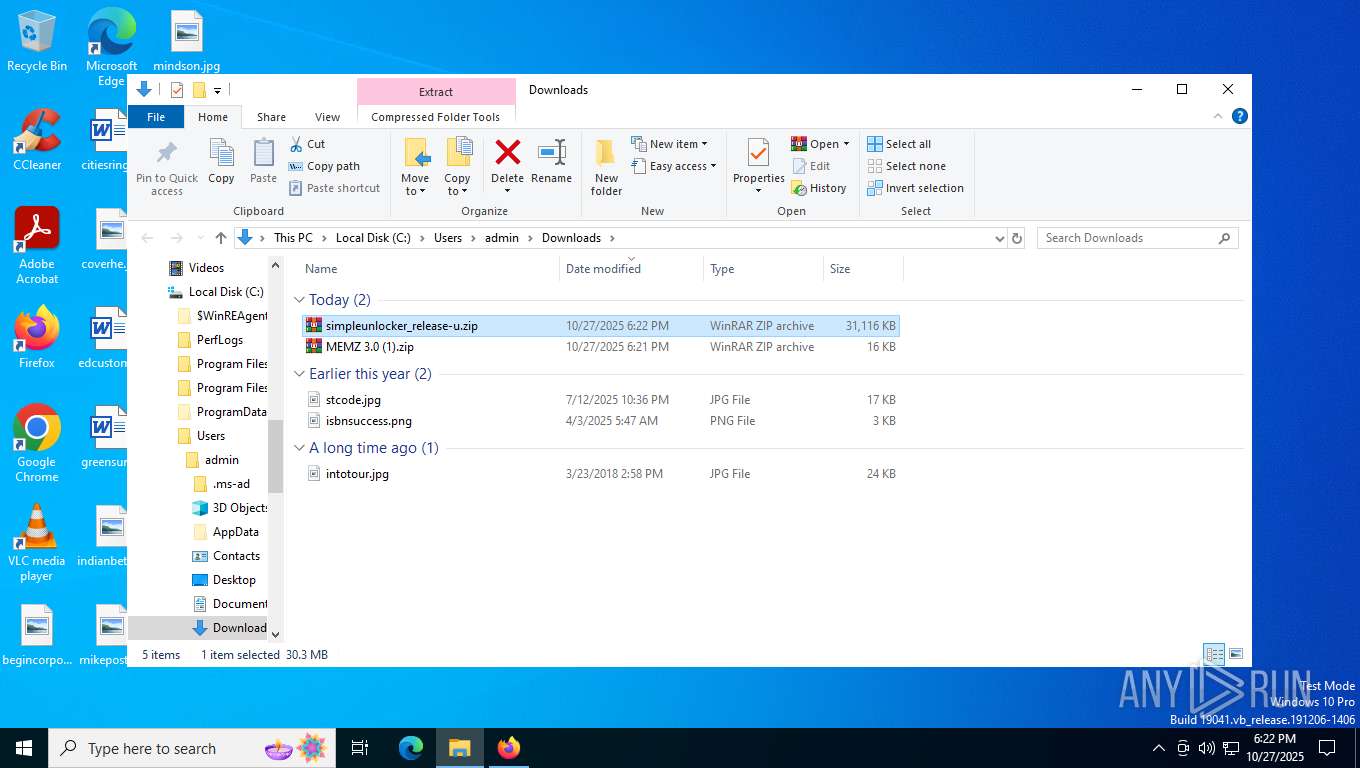
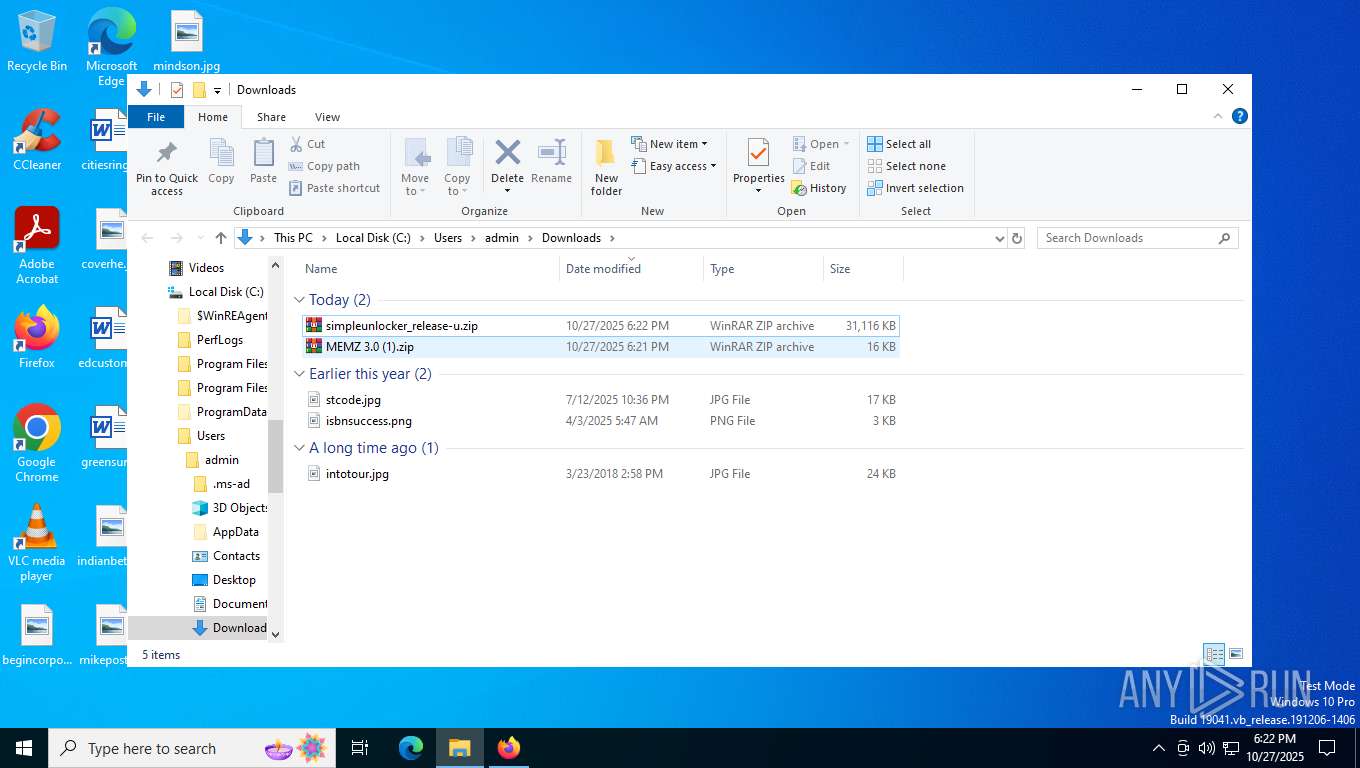
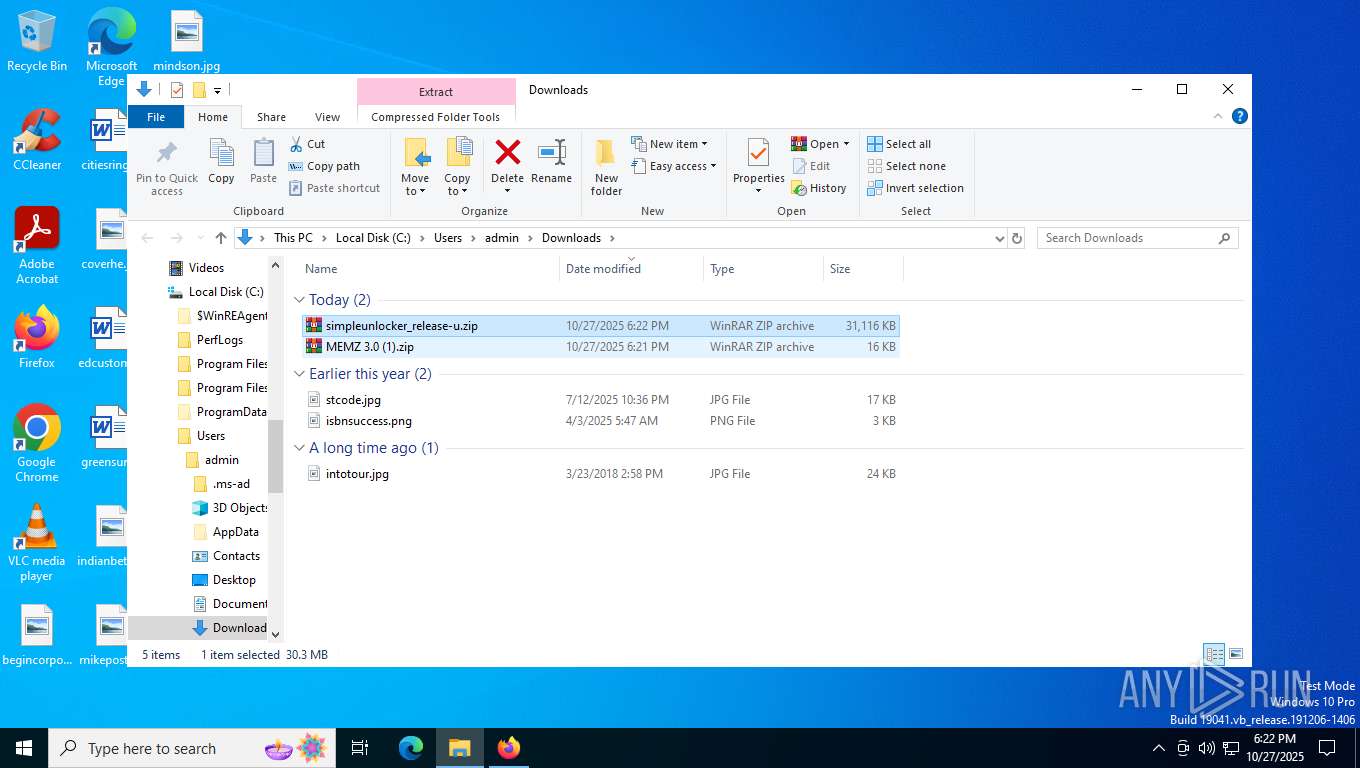
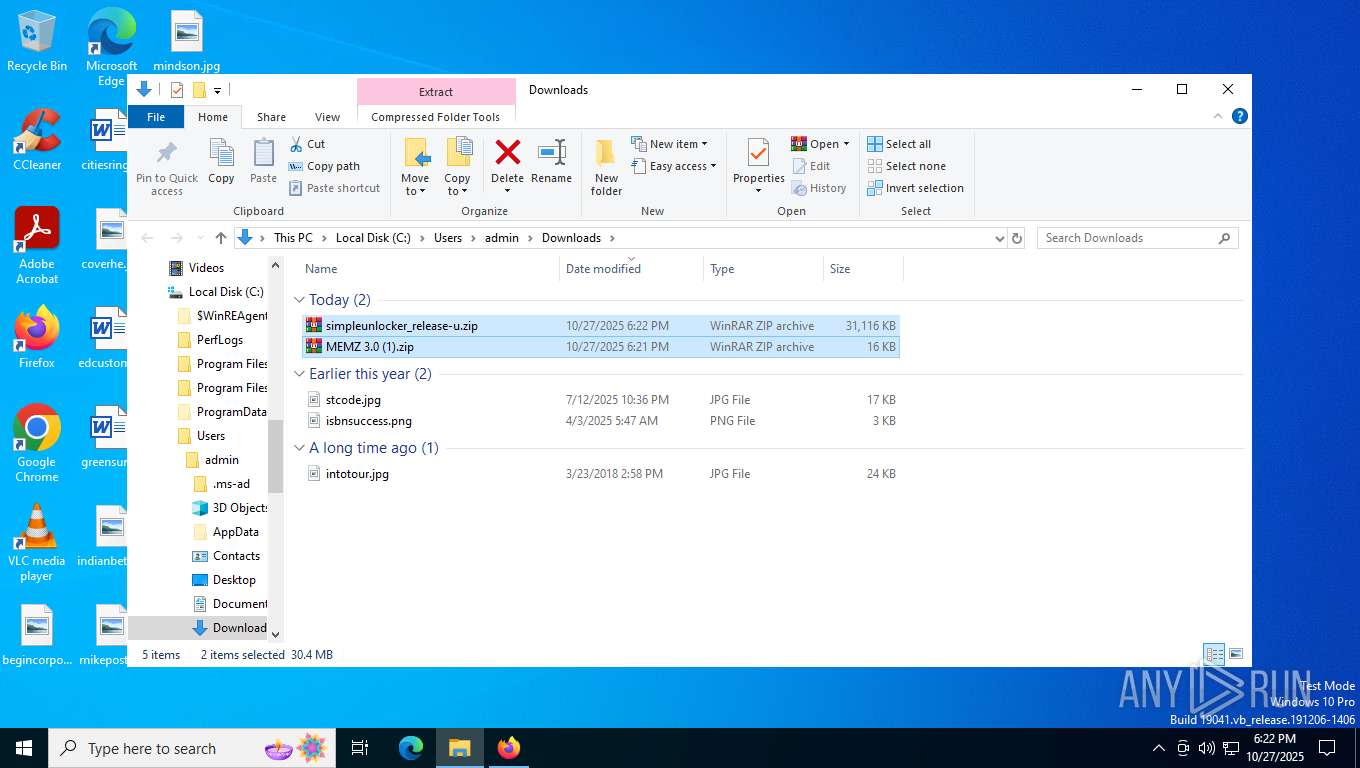
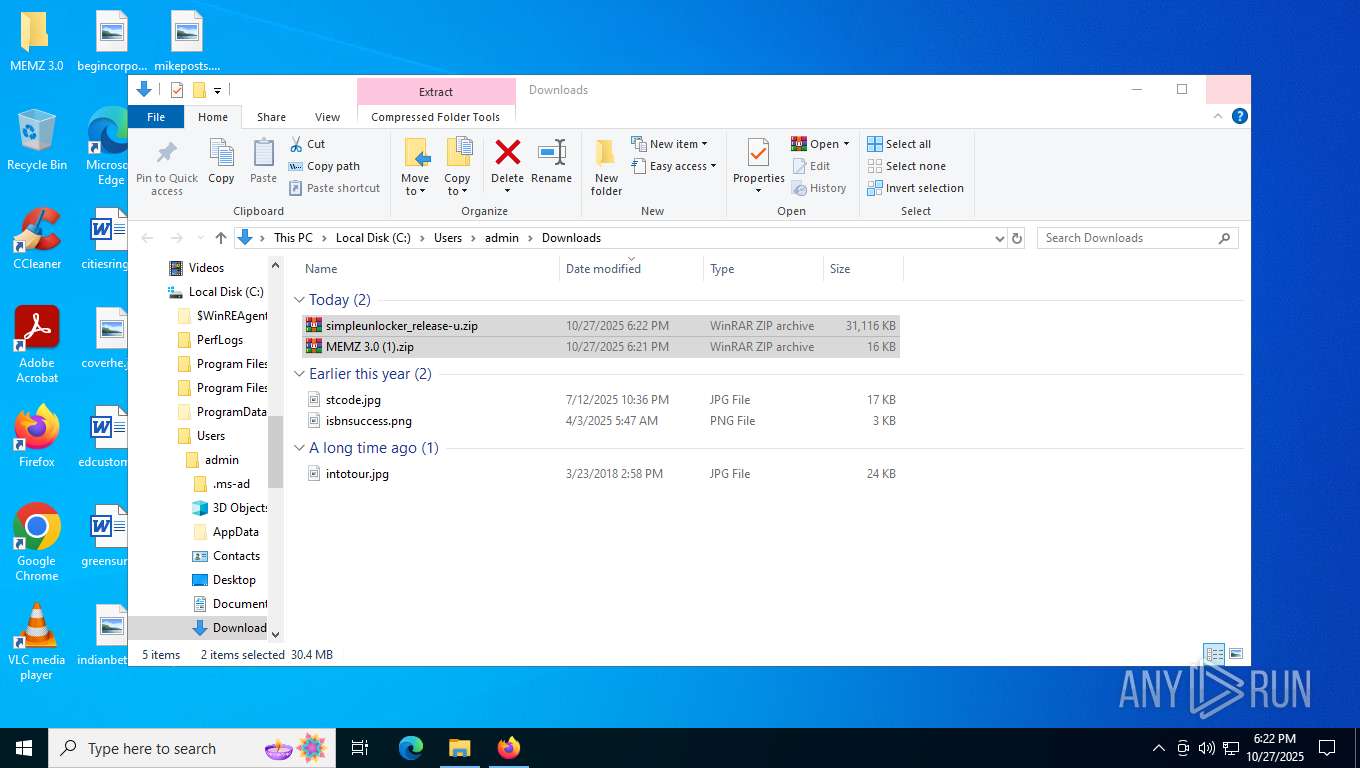
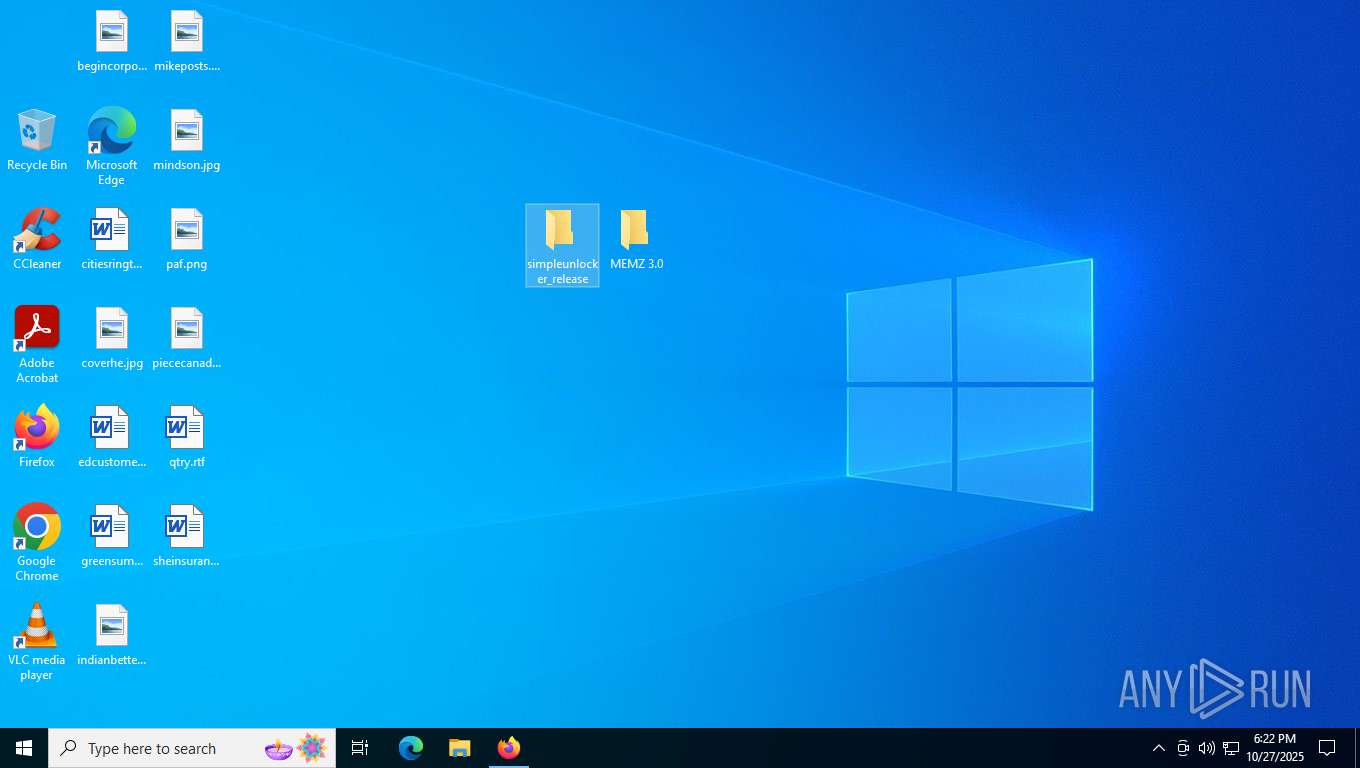
| URL: | github.com/laipeiyuanq/memz-/blob/main/MEMZ%203.0%20(1).zip |
| Full analysis: | https://app.any.run/tasks/92560adc-80d7-46f5-b229-d75b1495ee24 |
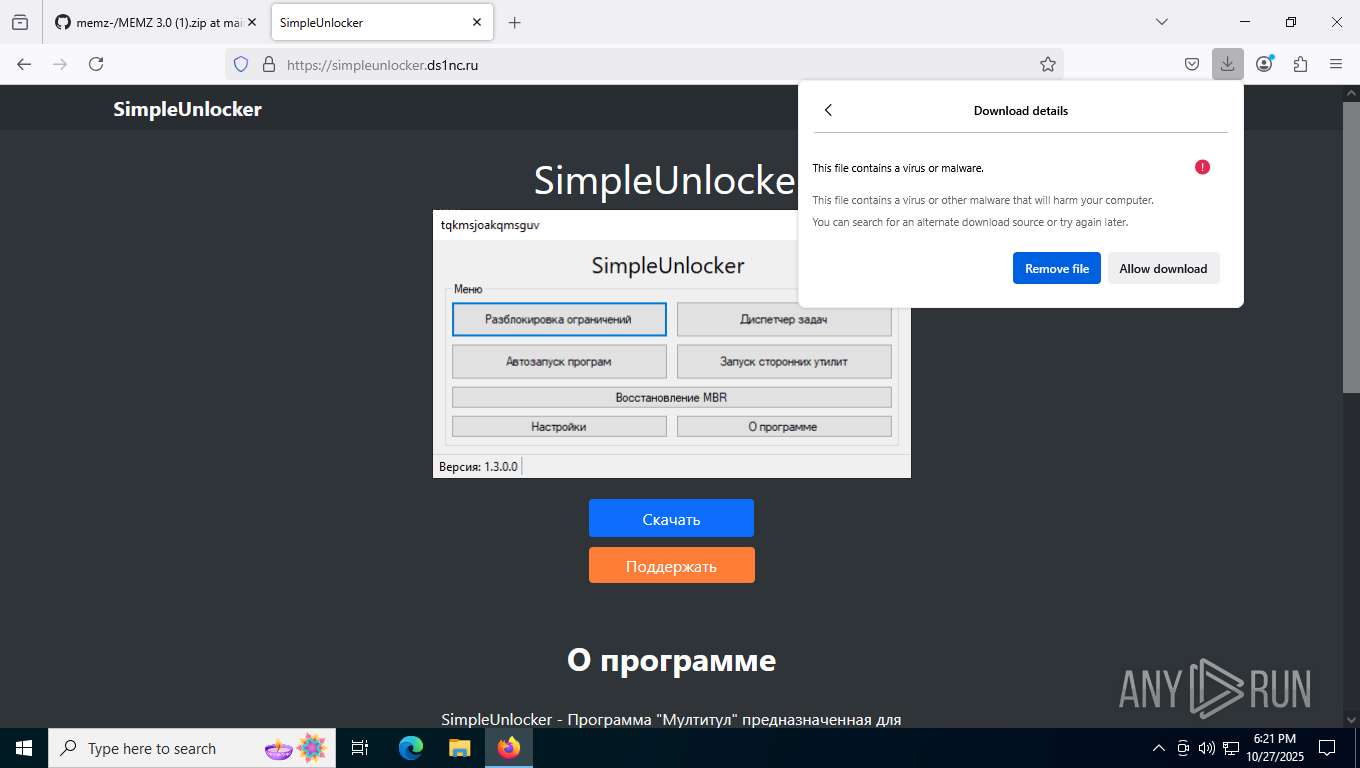
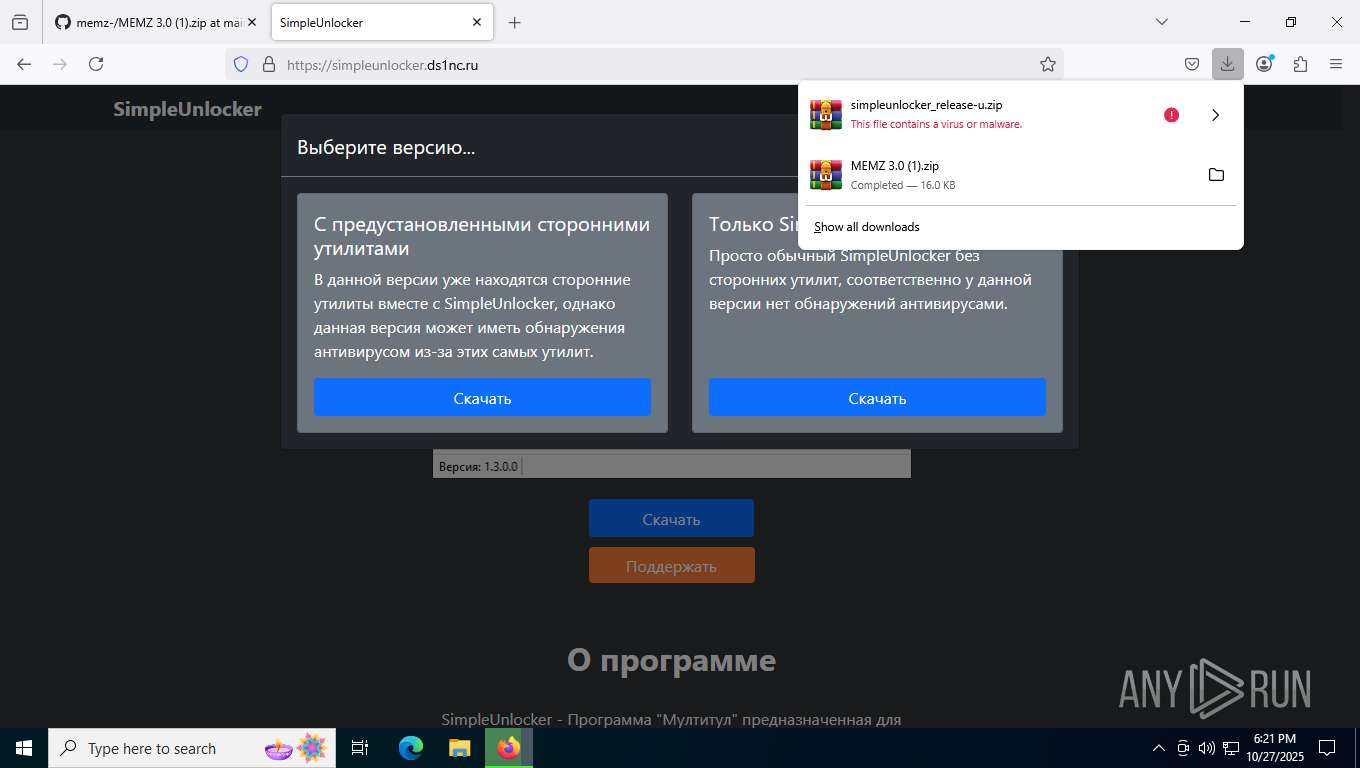
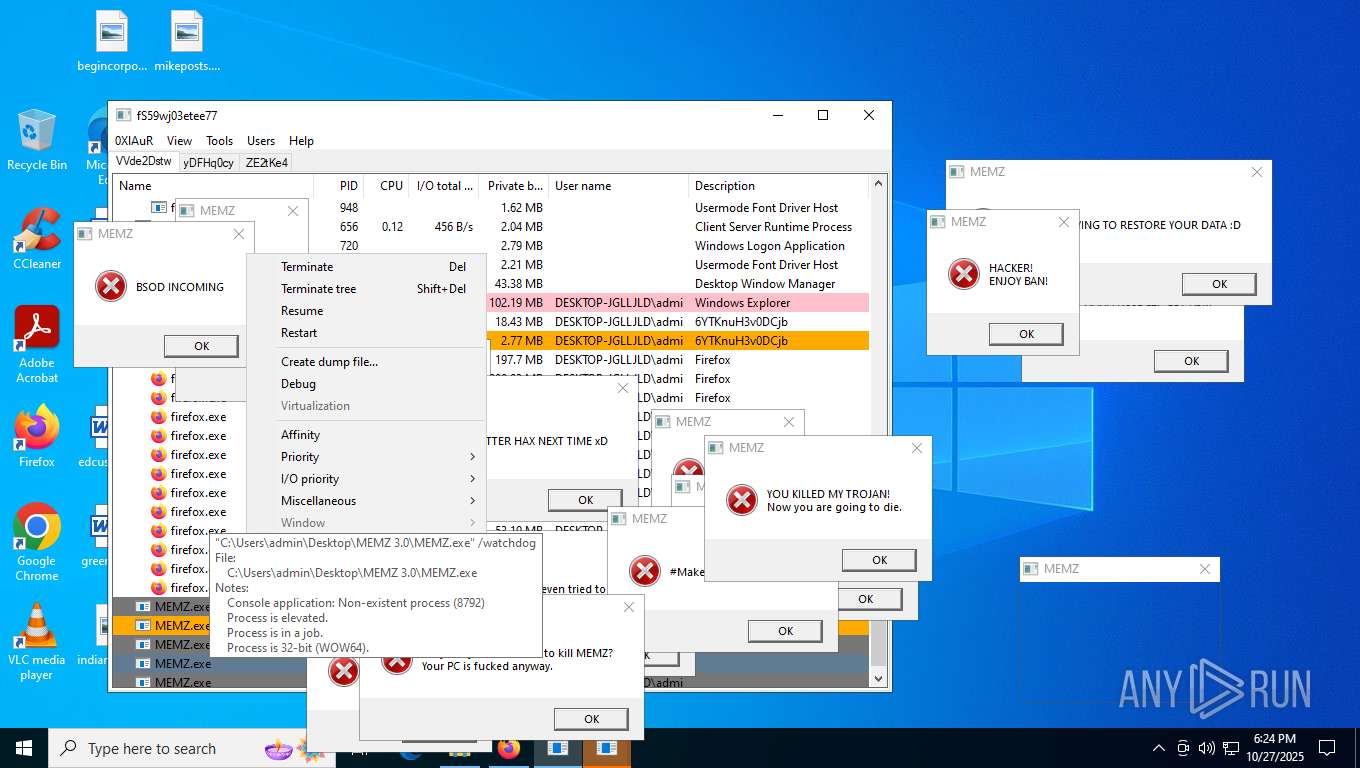
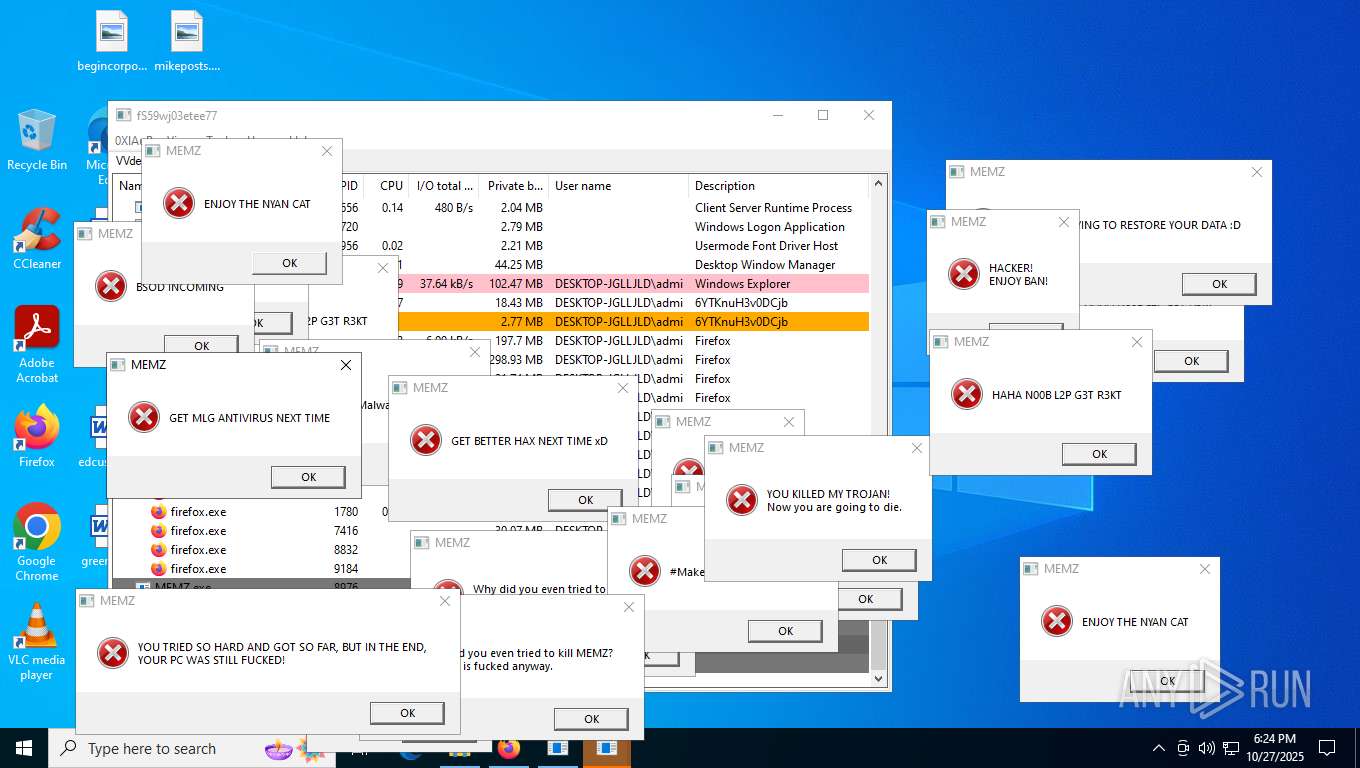
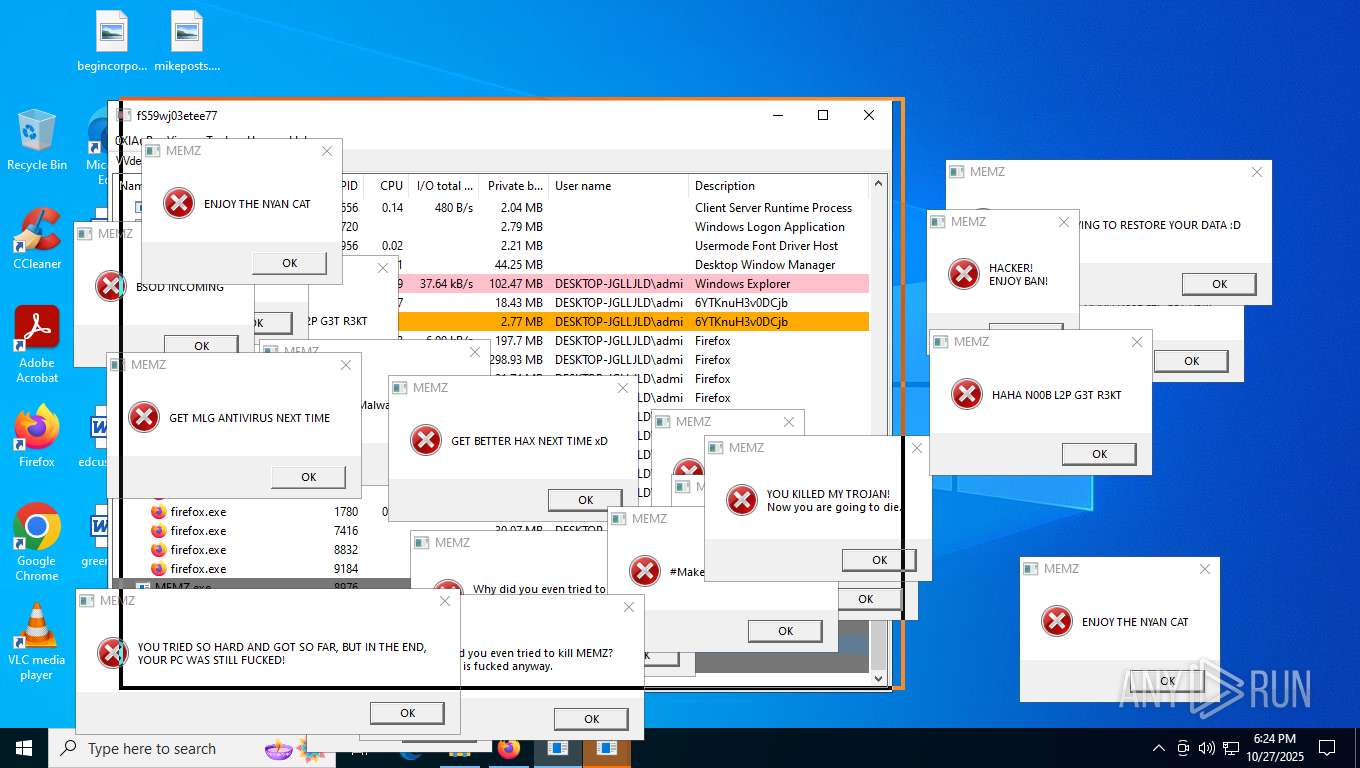
| Verdict: | Malicious activity |
| Analysis date: | October 27, 2025, 18:21:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 50B3ED0049A05886EAFB7CD40232651B |
| SHA1: | 90E08CC9EA10B1521E7A3A25531D098853CCD9FF |
| SHA256: | C8FB3F2AF715922B5FD067524F0F8E627852535ADE5884D8D8C1FDD1BB9242AA |
| SSDEEP: | 3:j4d5EP7If3SERkAXVUA3V4:j4cPMfisJXVUaV4 |
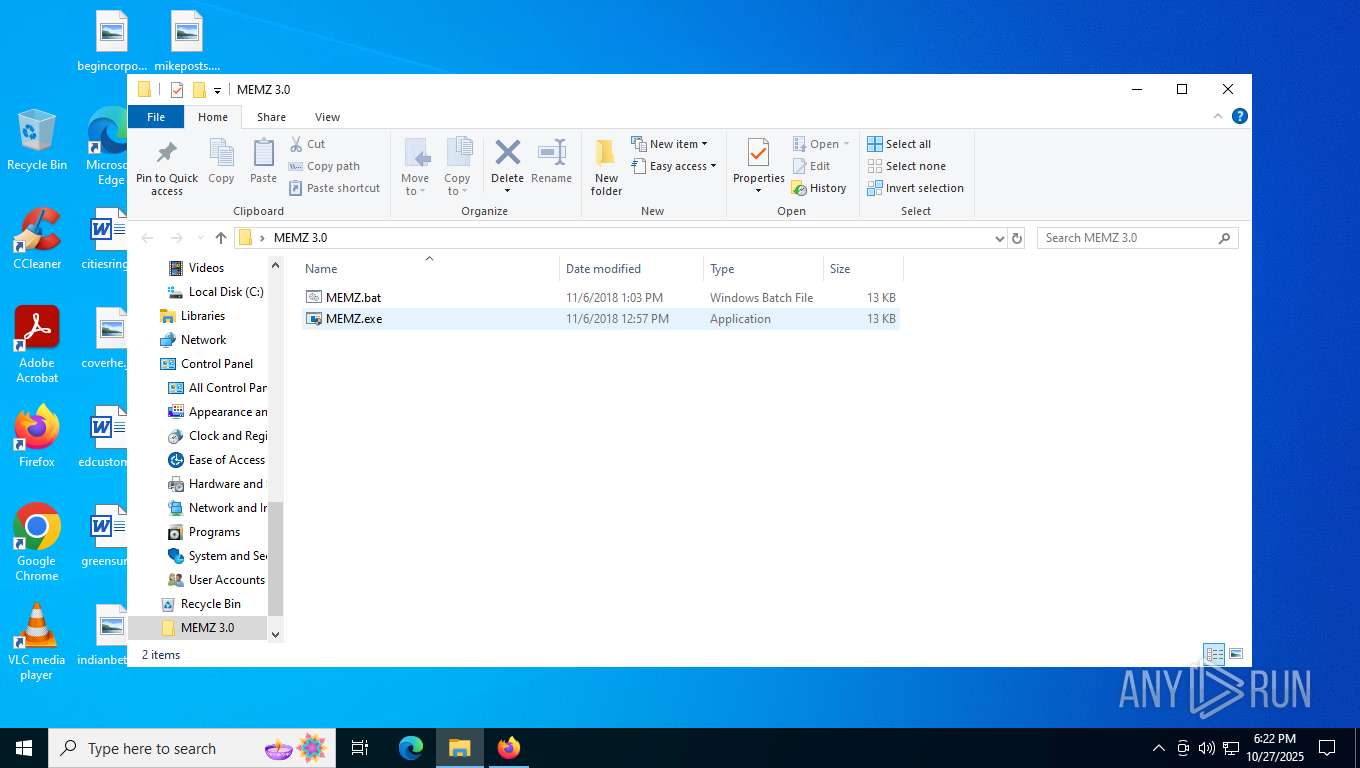
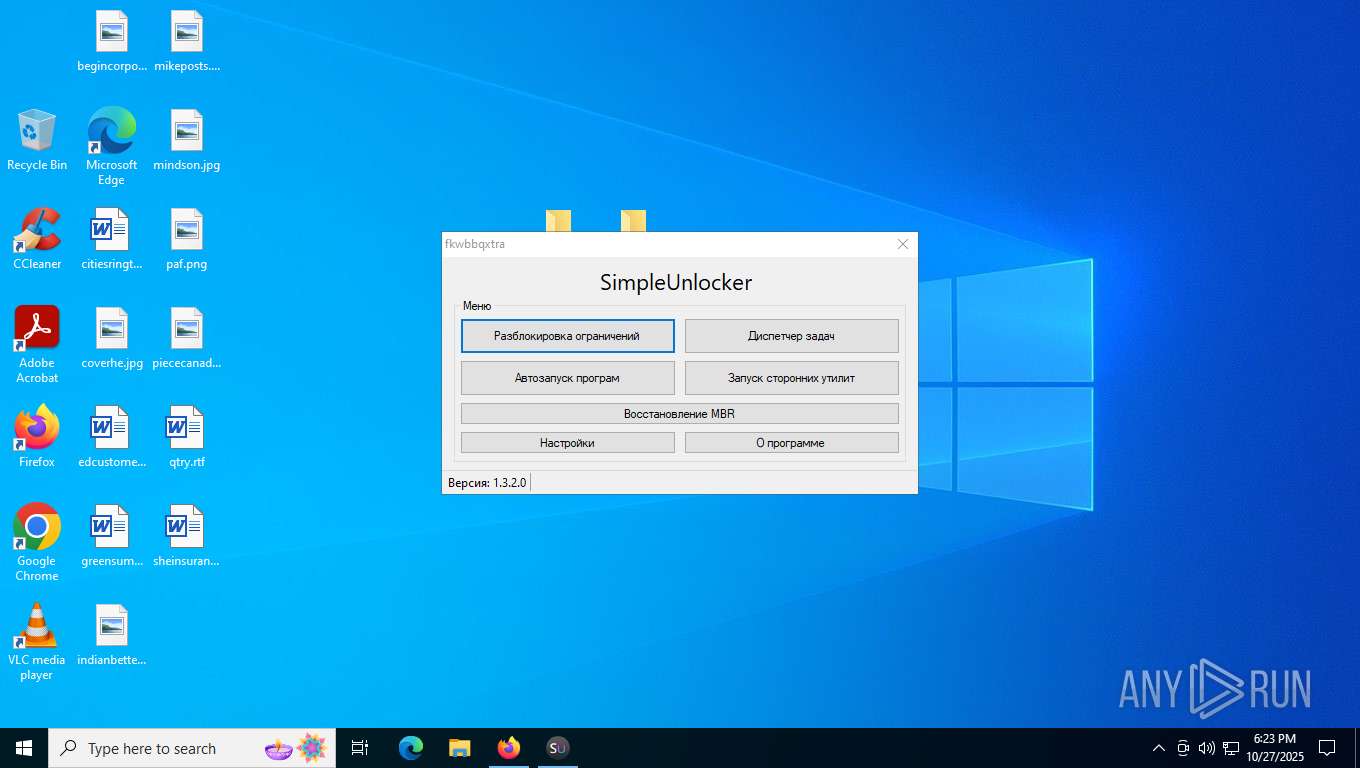
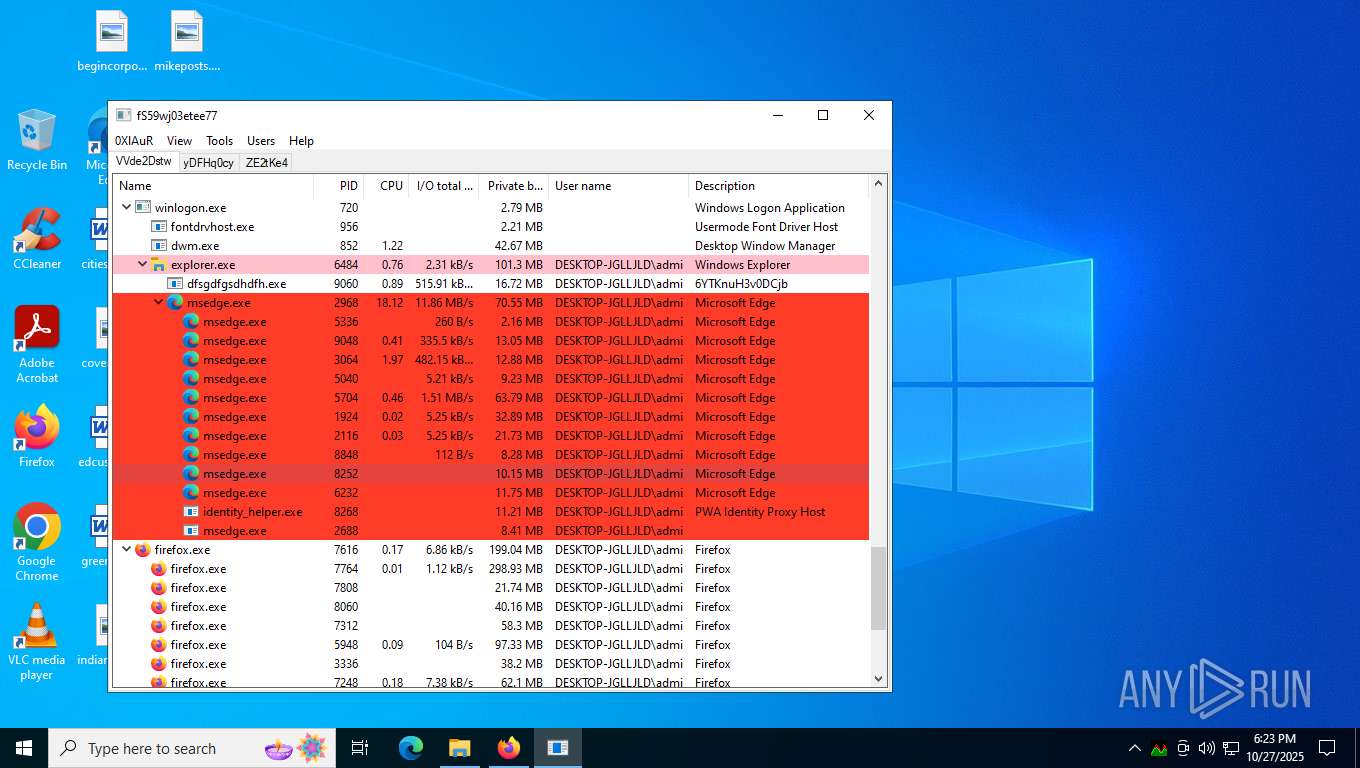
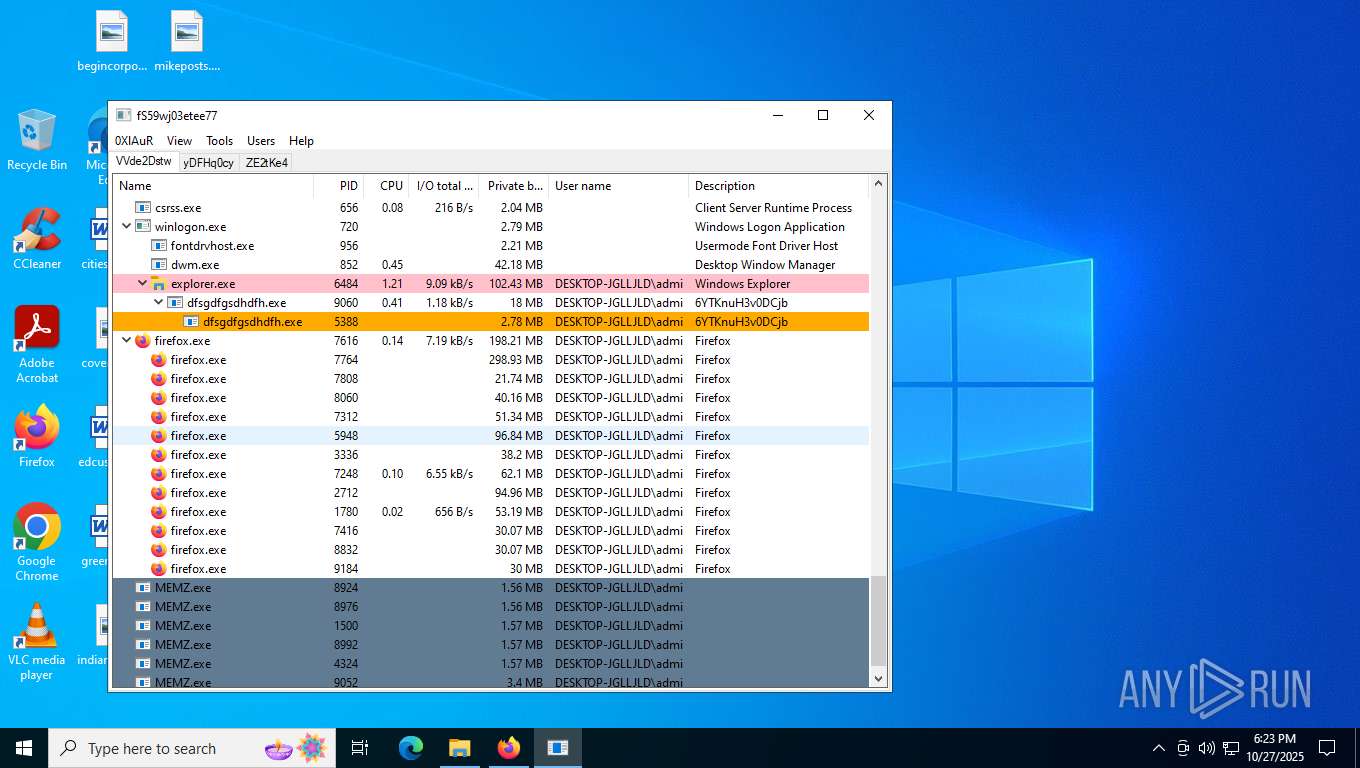
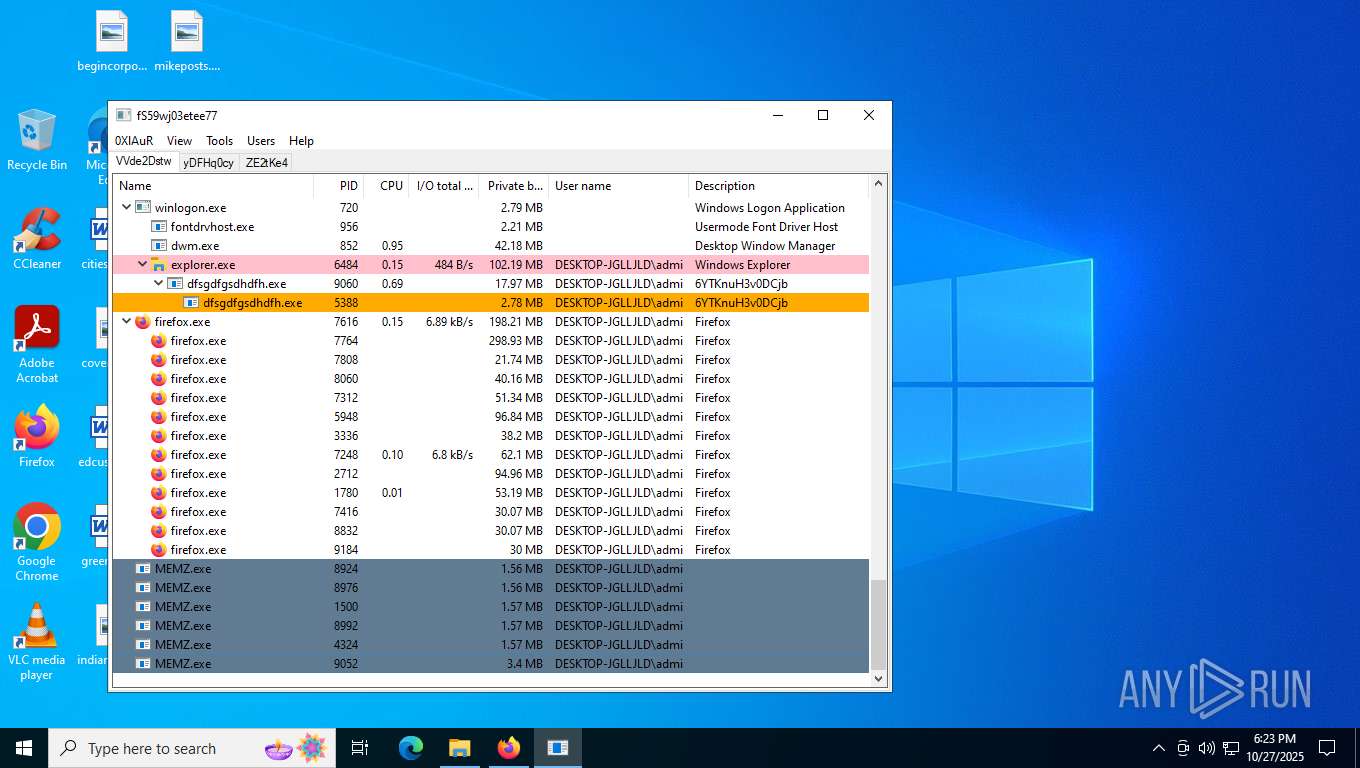
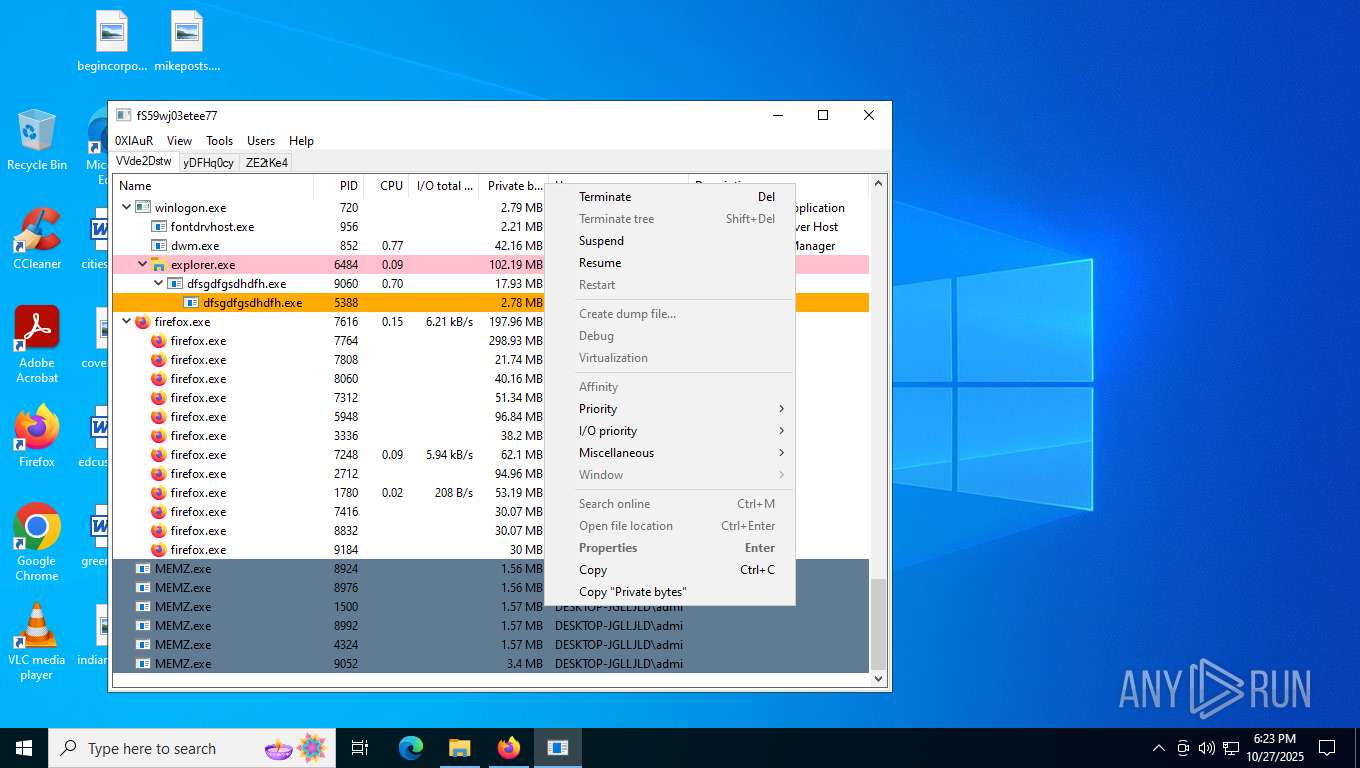
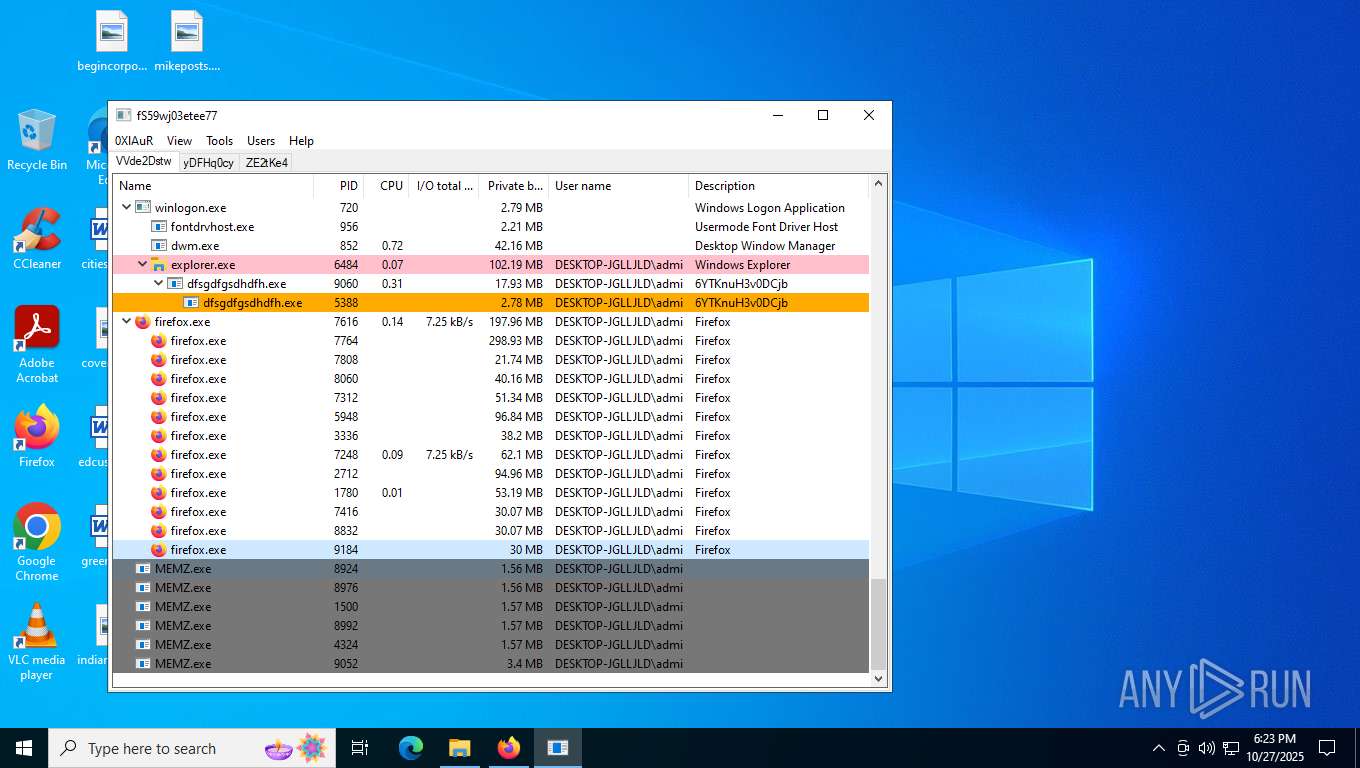
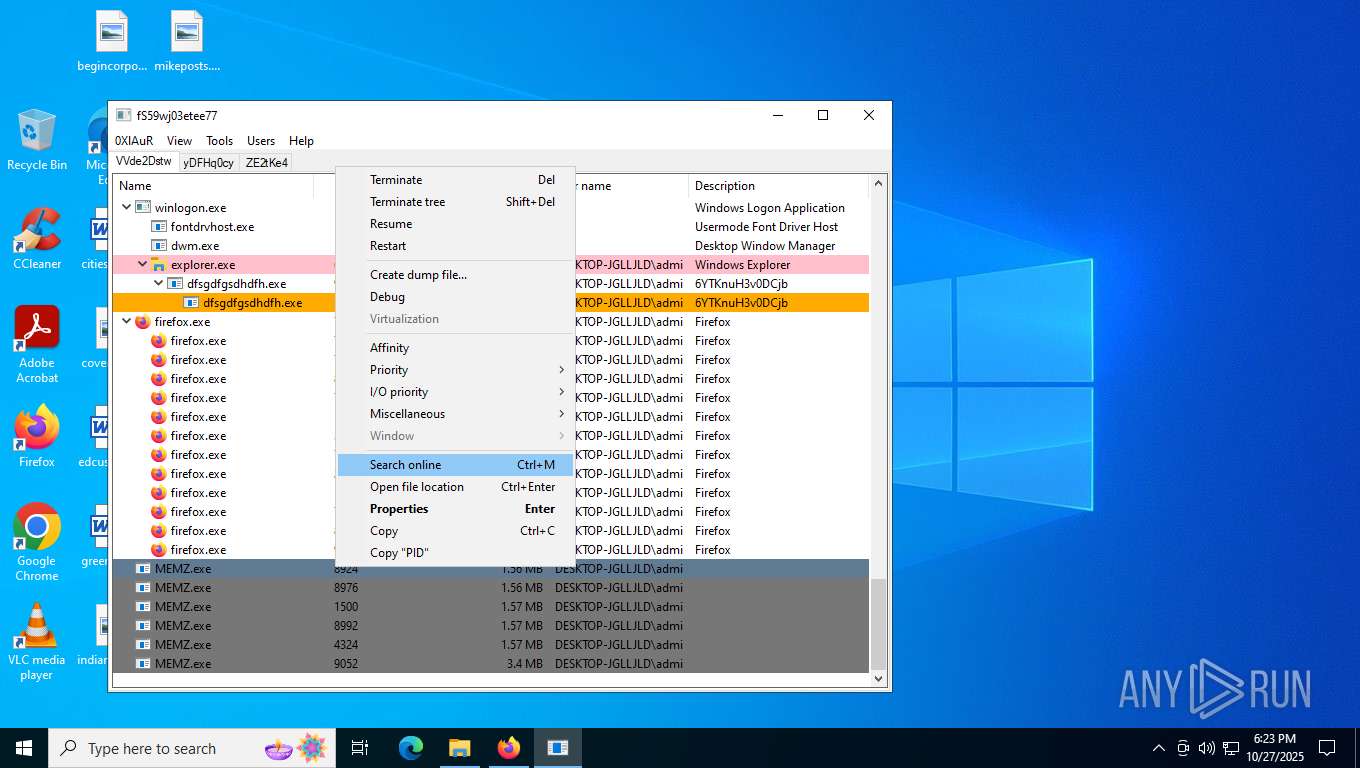
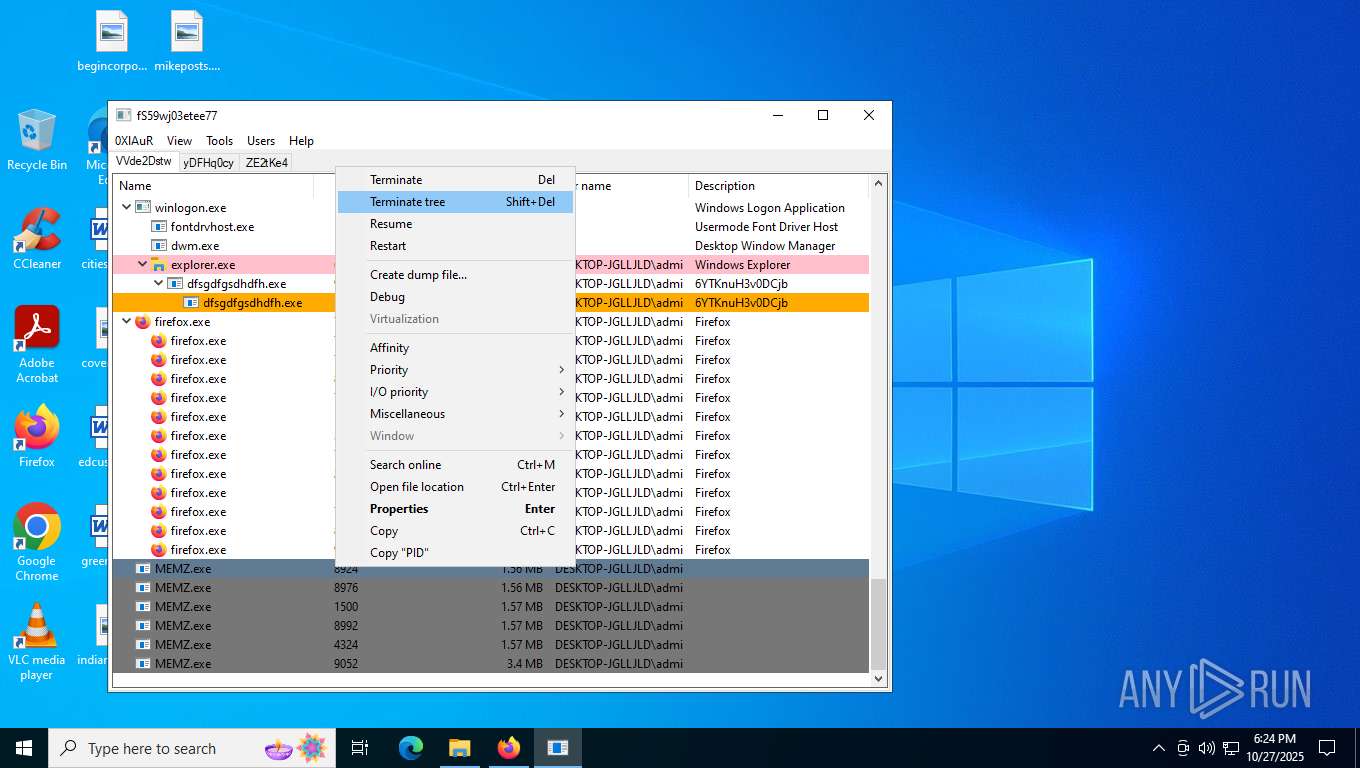
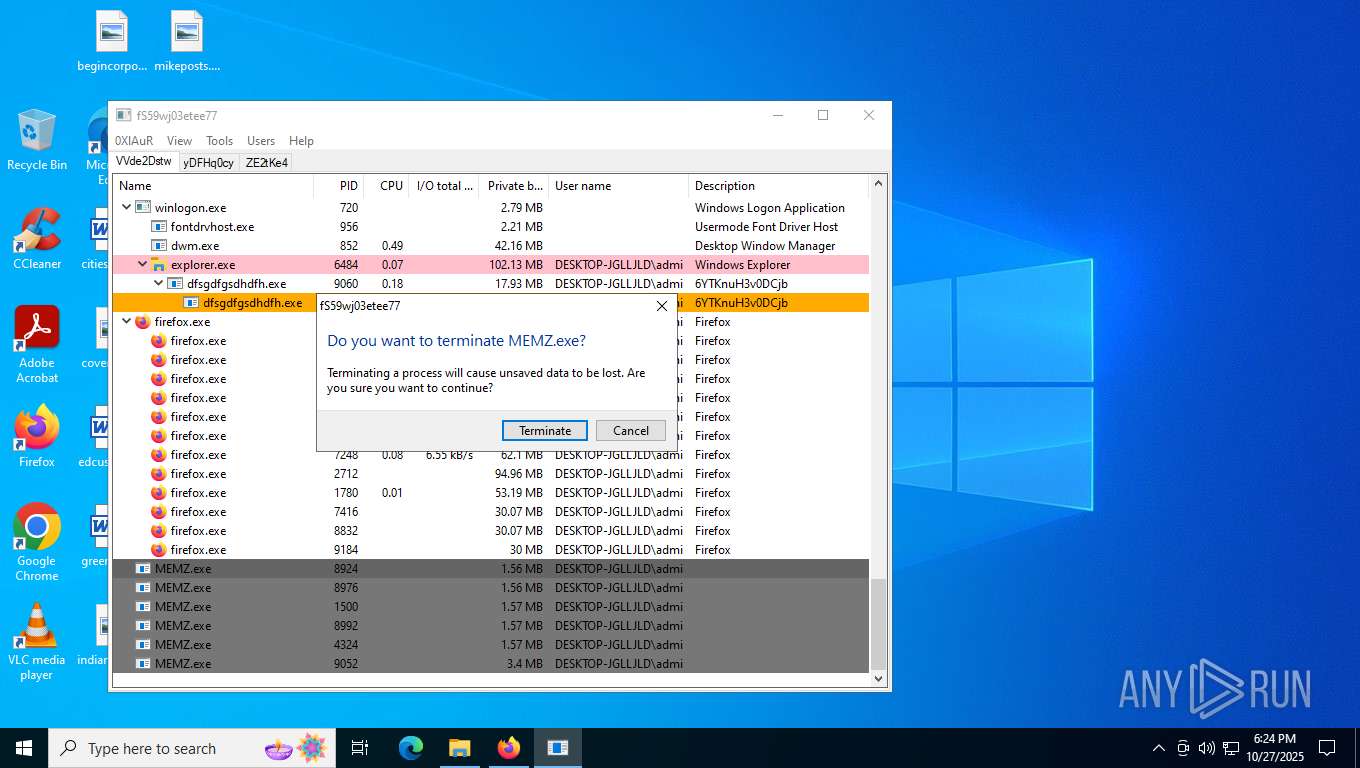
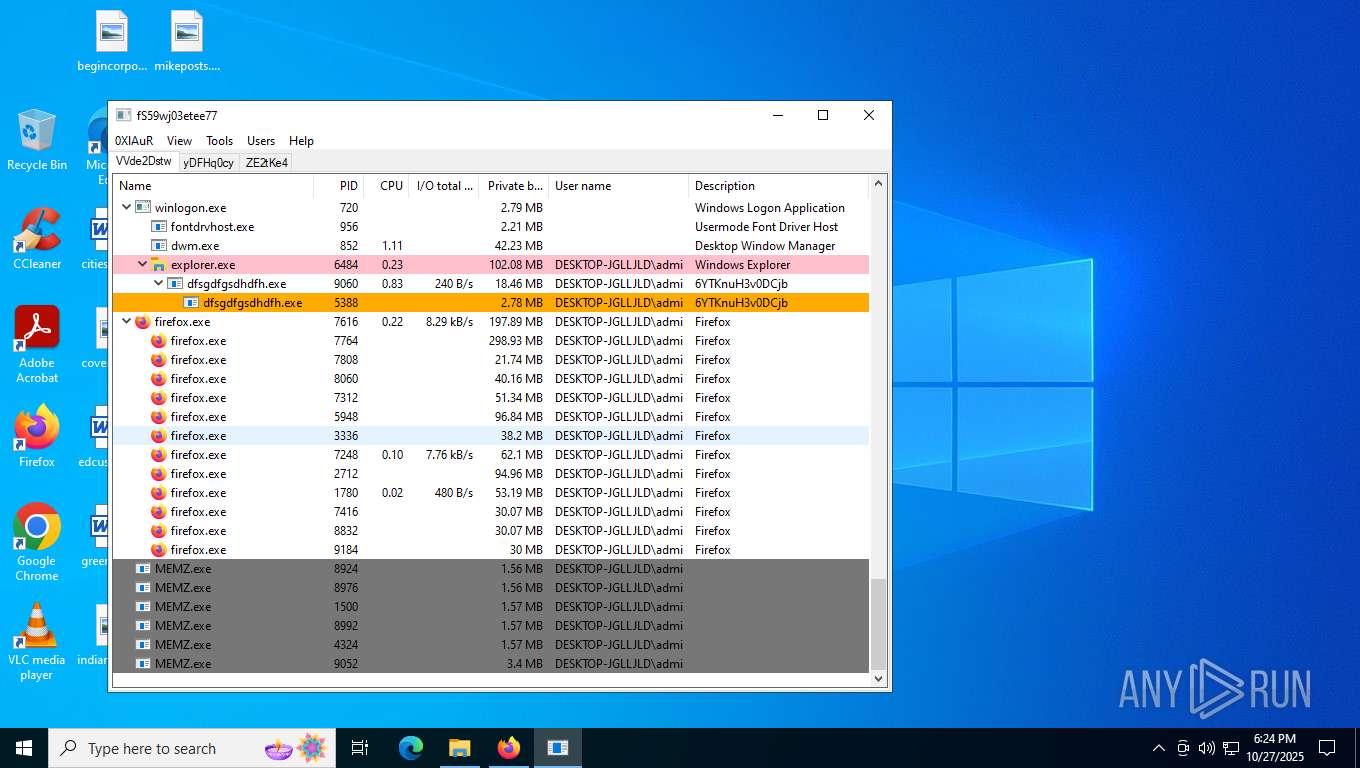
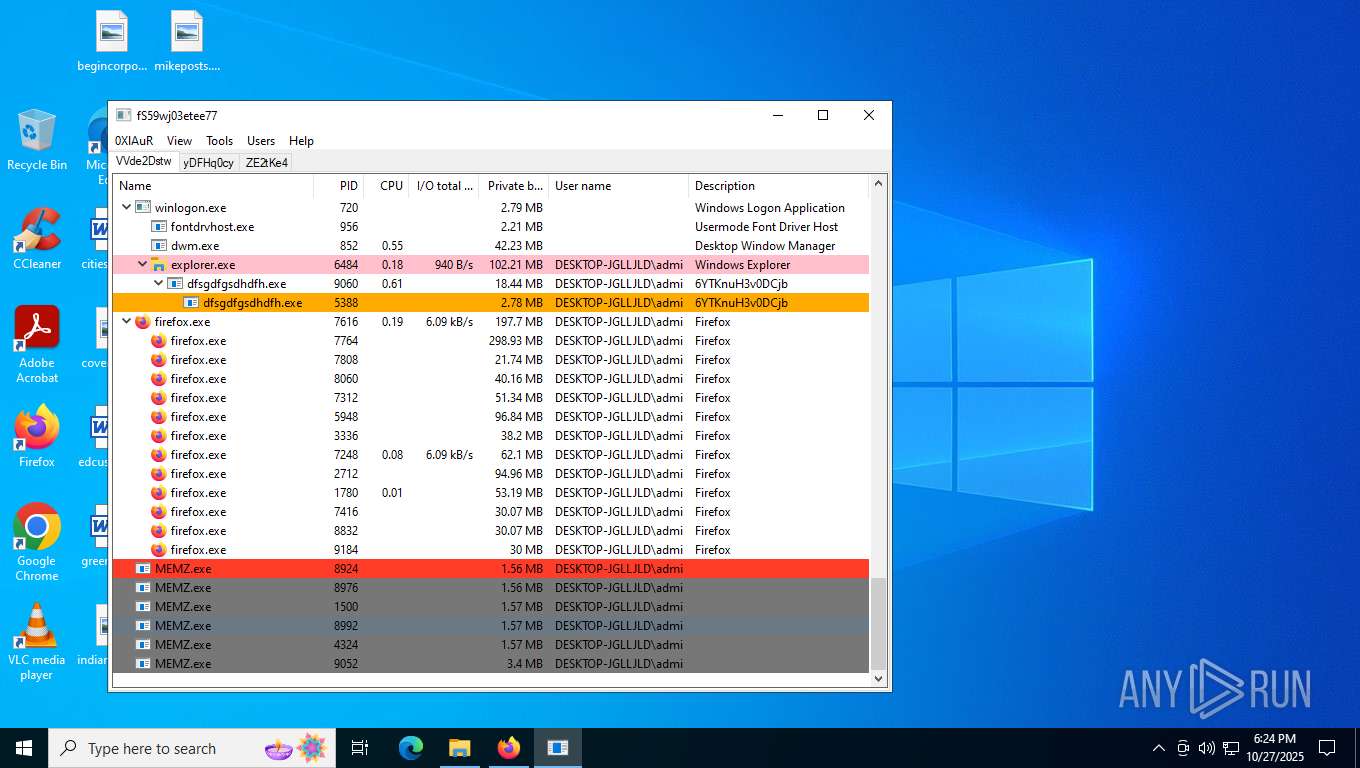
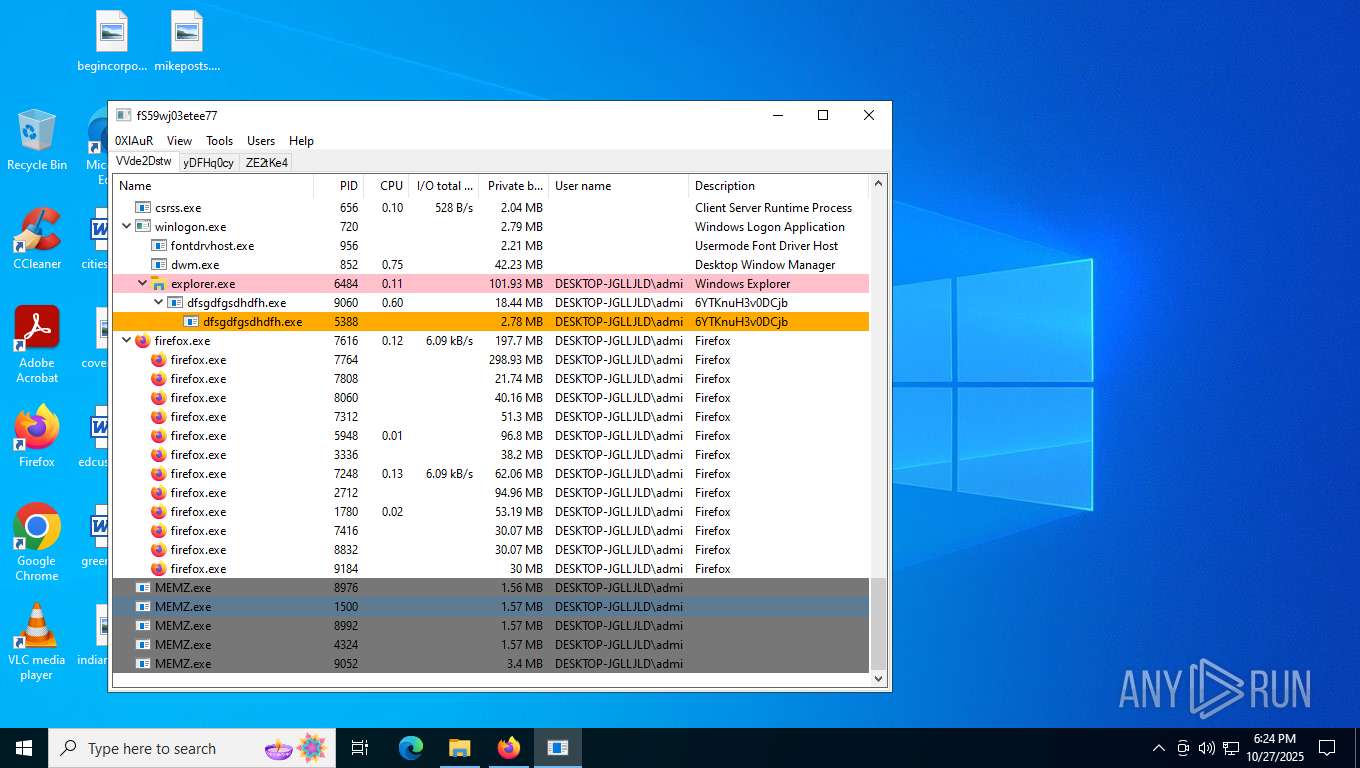
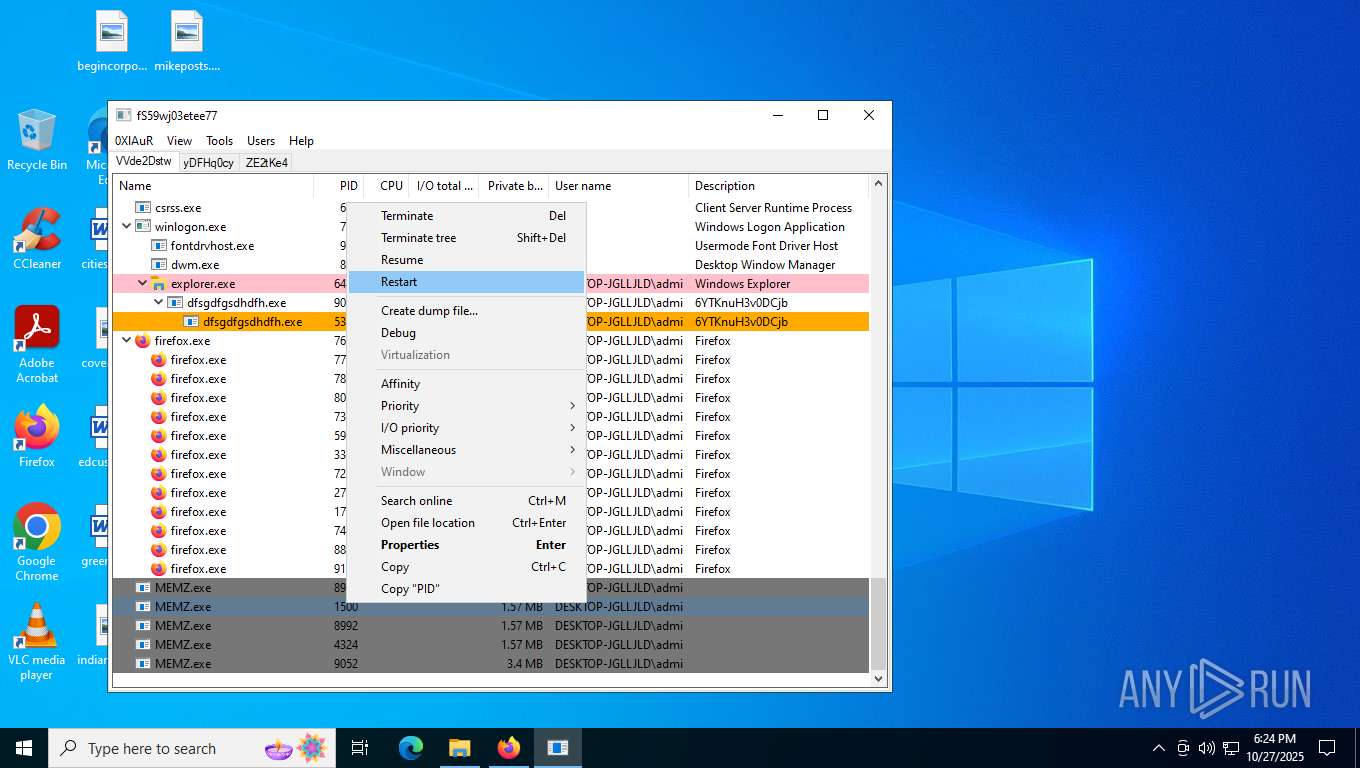
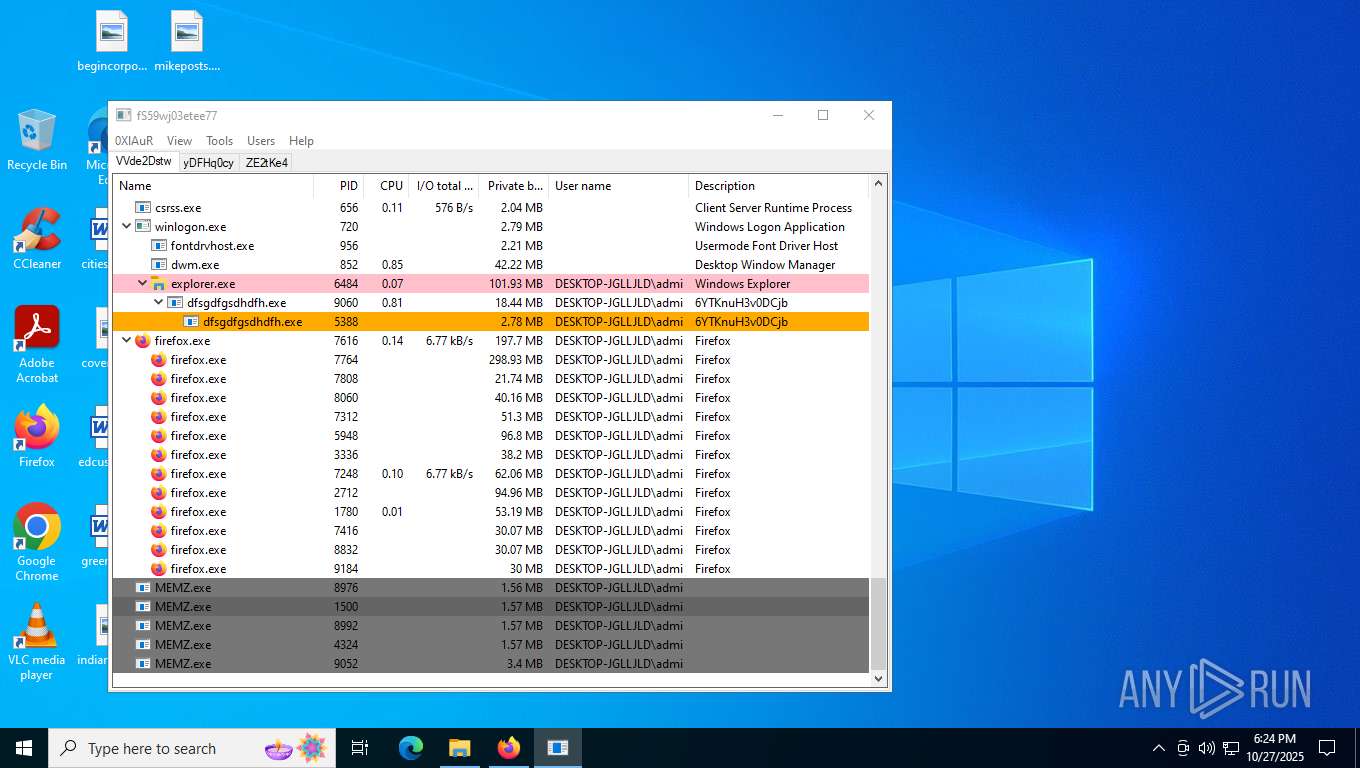
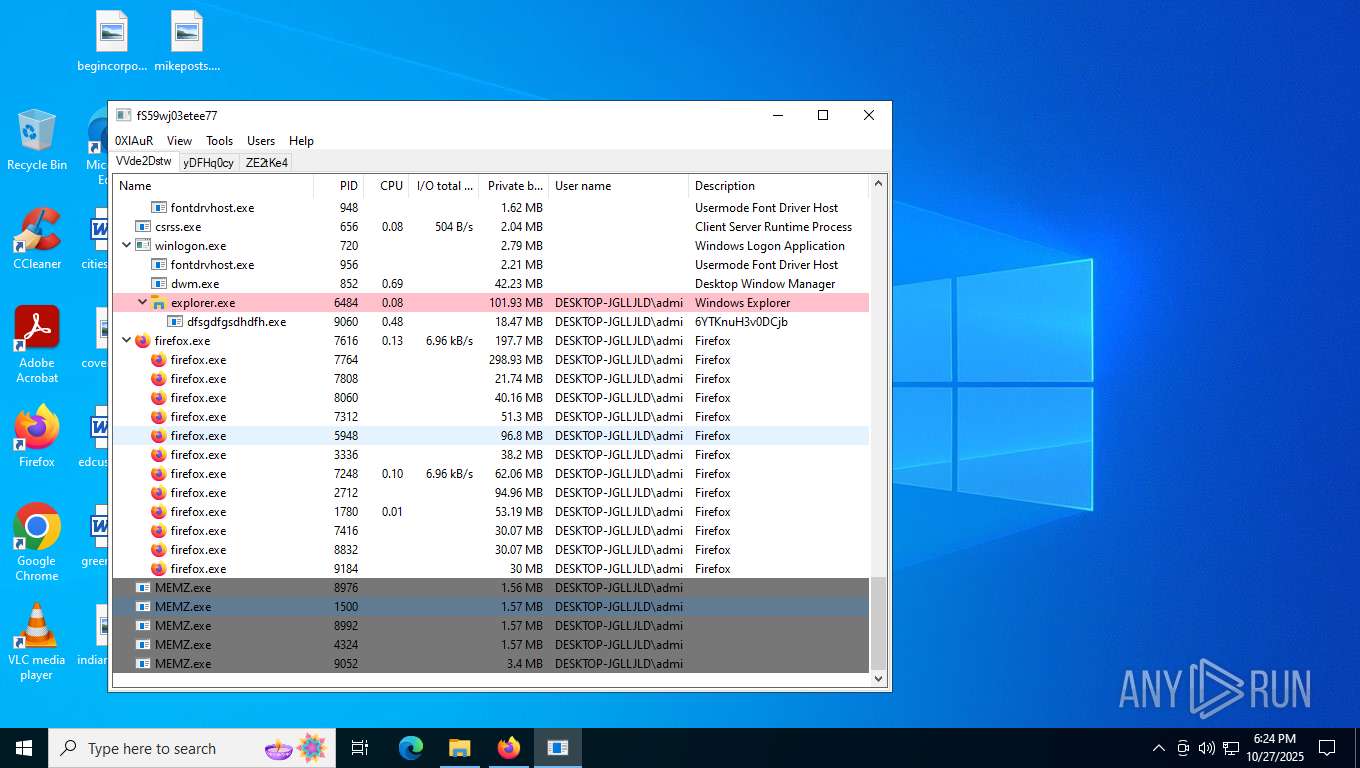
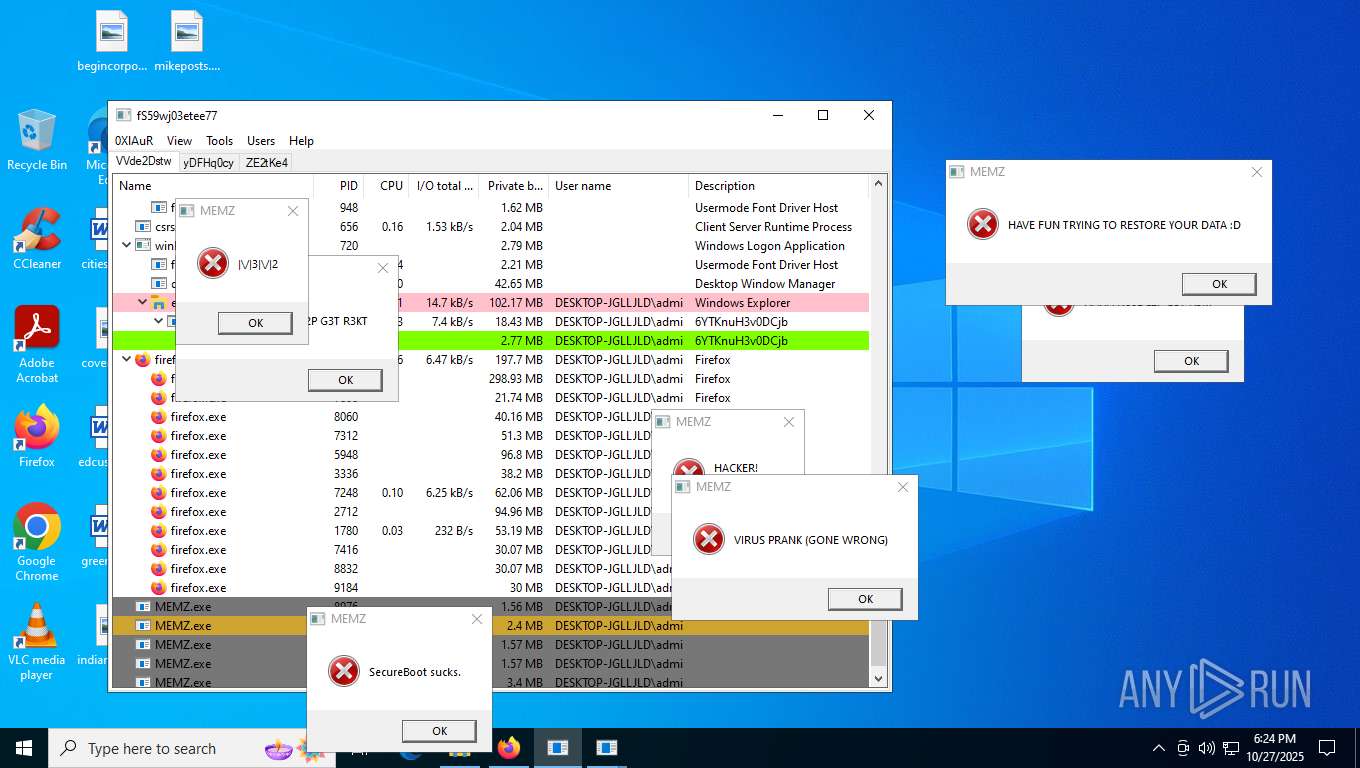
MALICIOUS
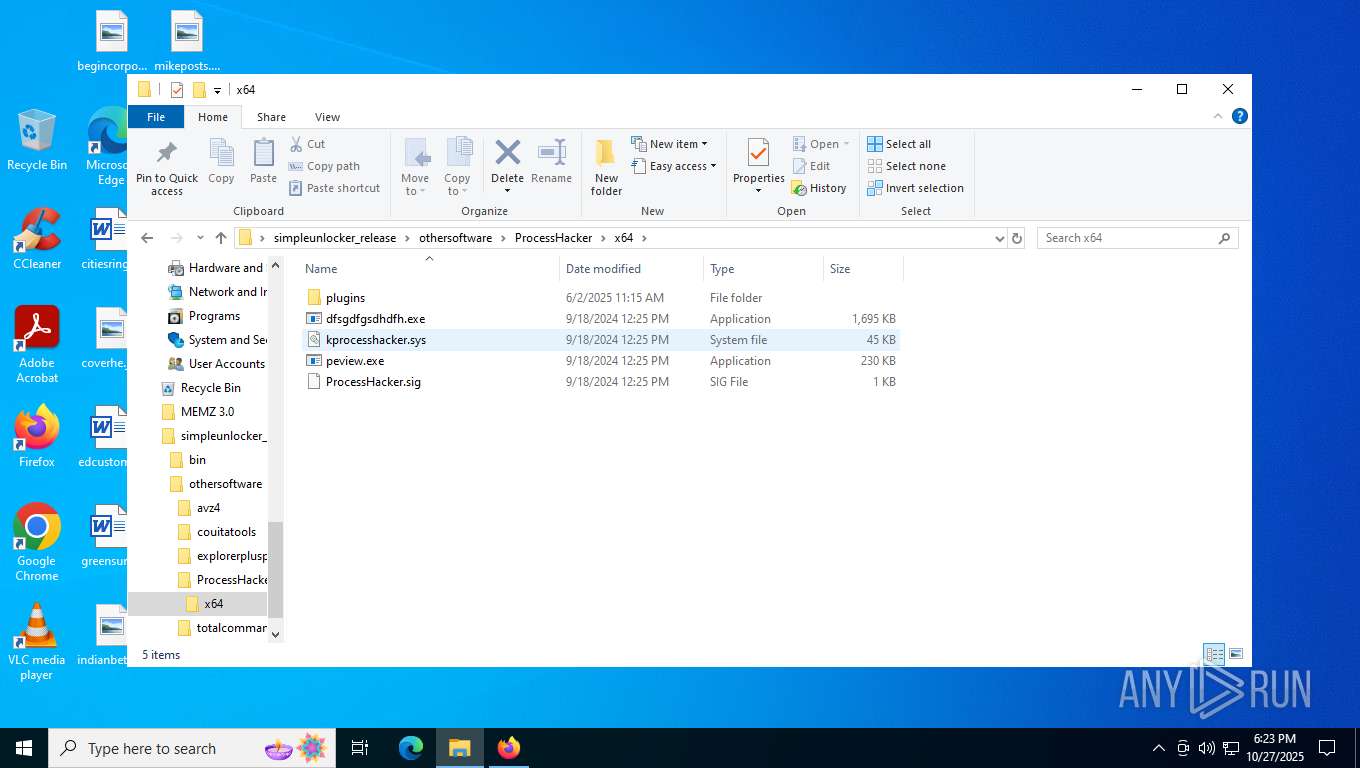
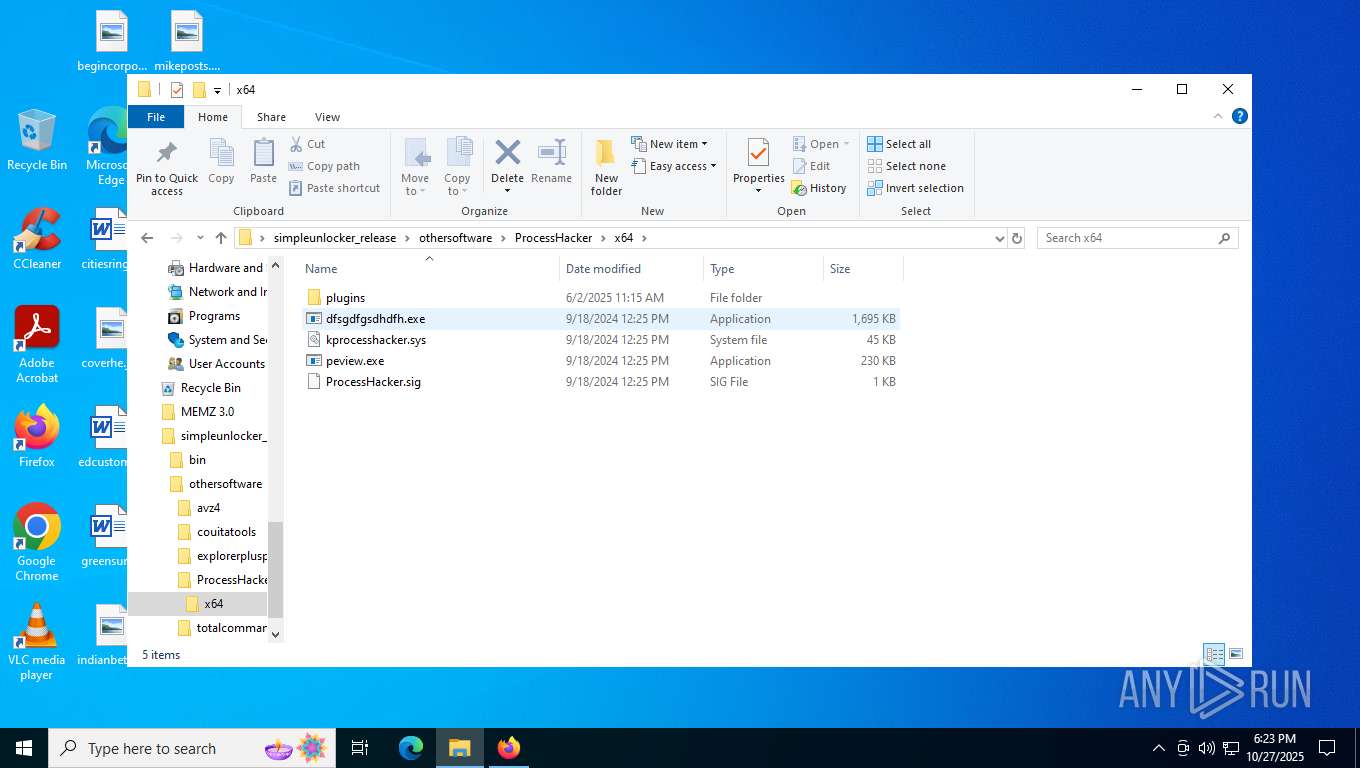
Vulnerable driver has been detected
- WinRAR.exe (PID: 8100)
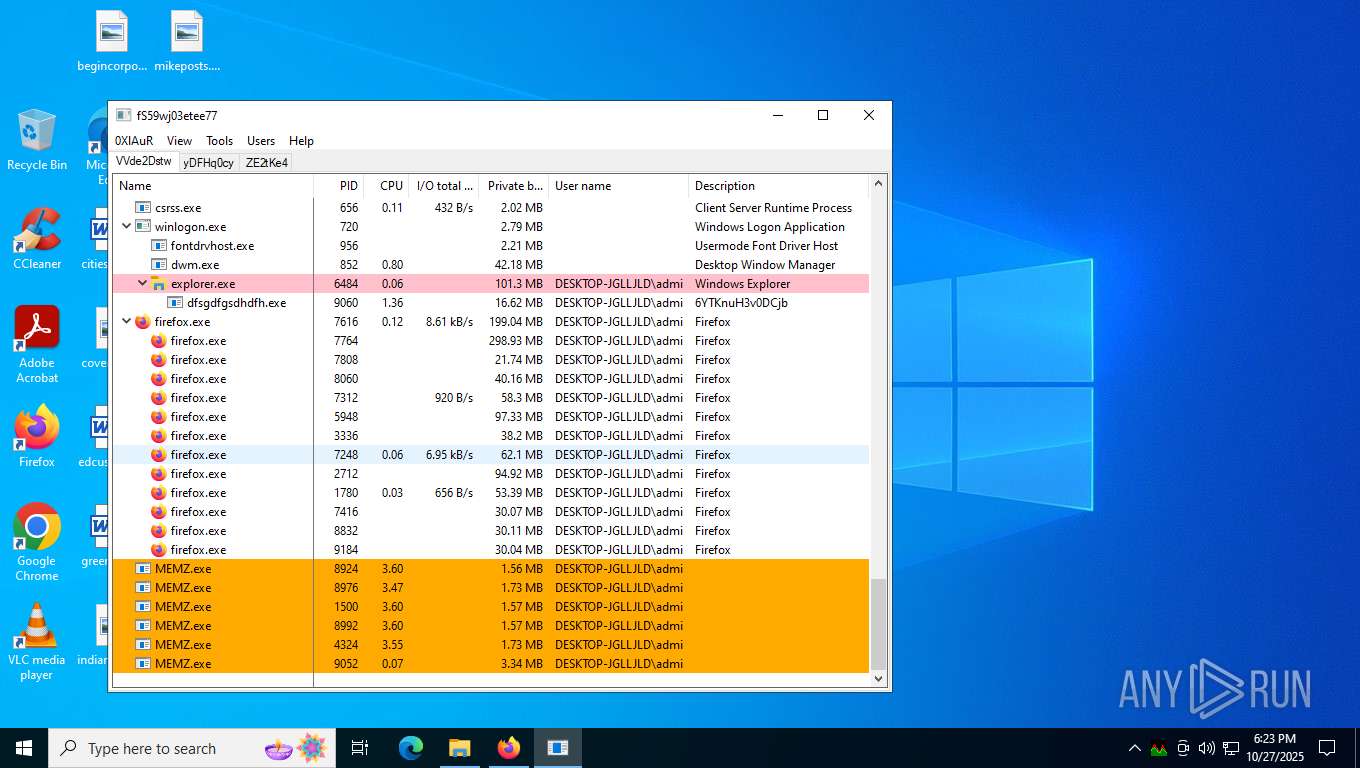
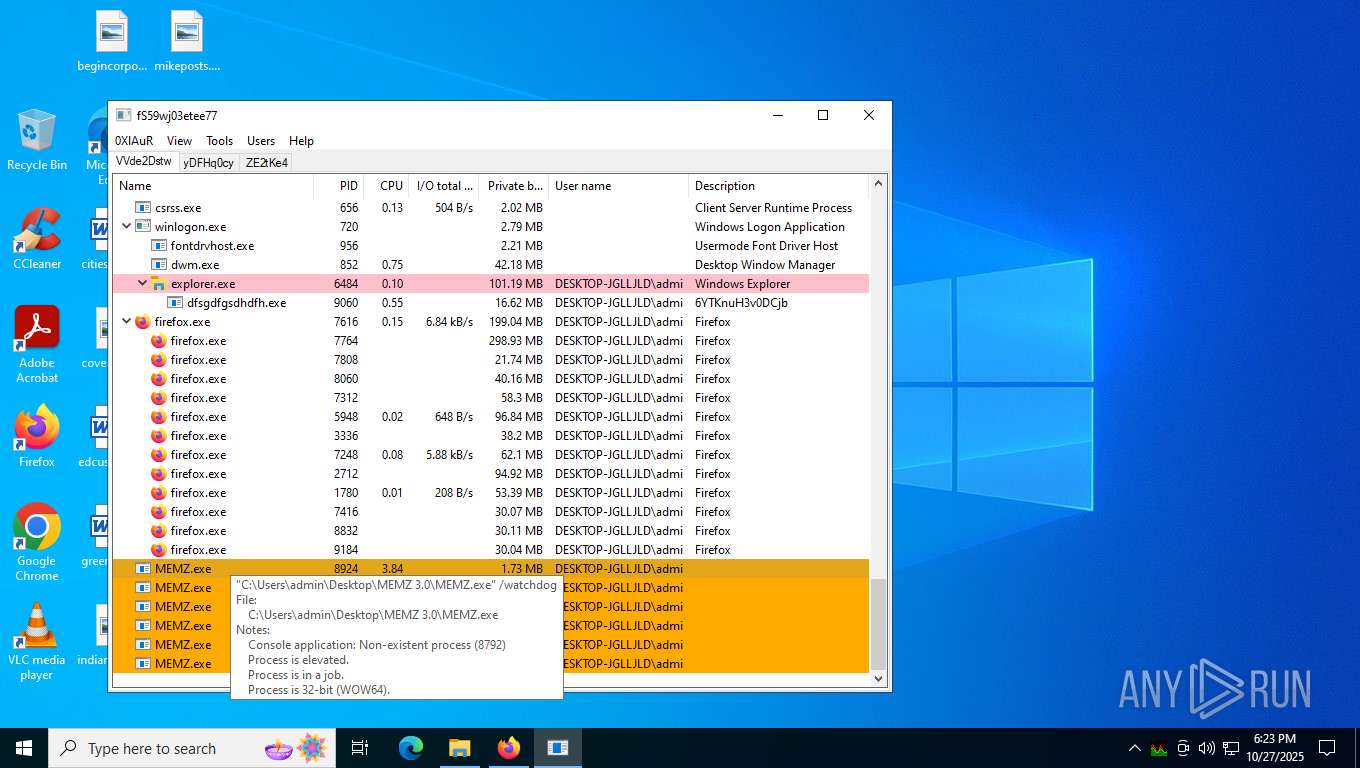
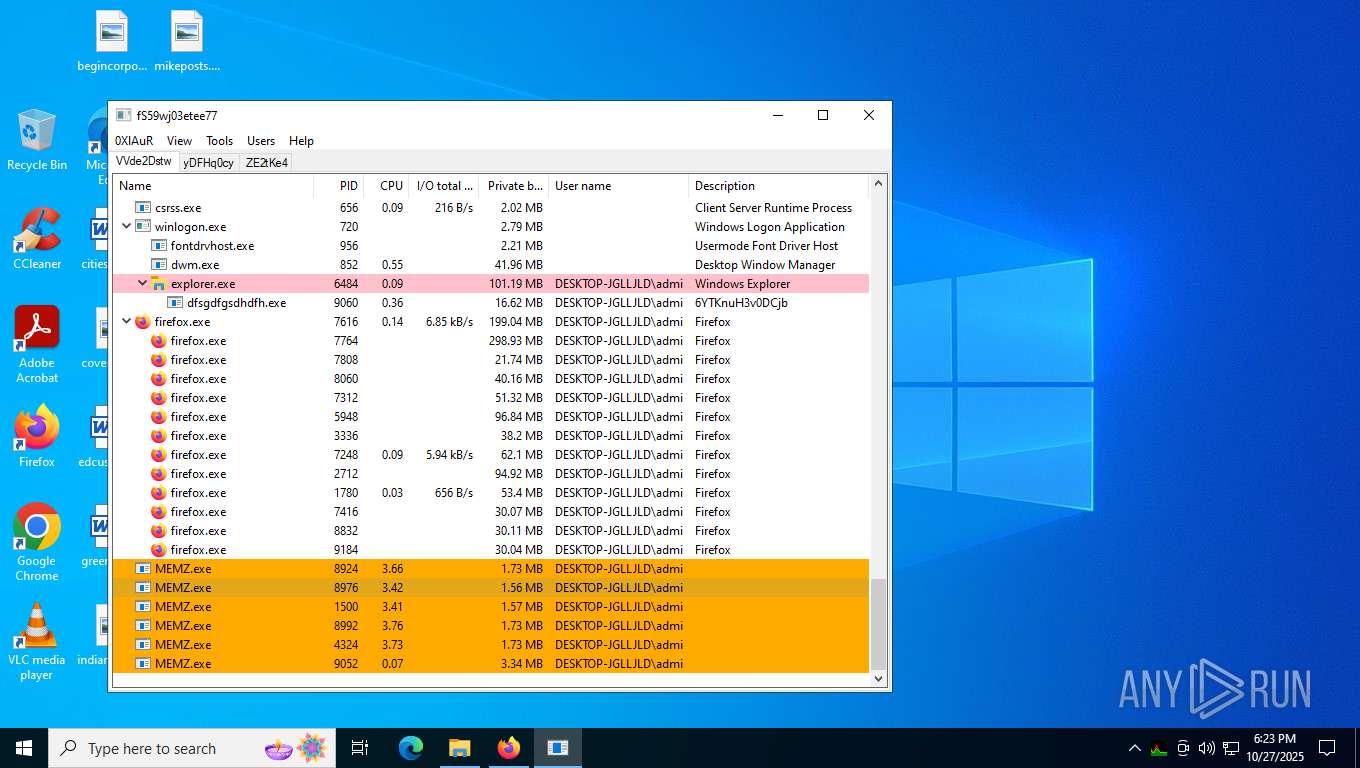
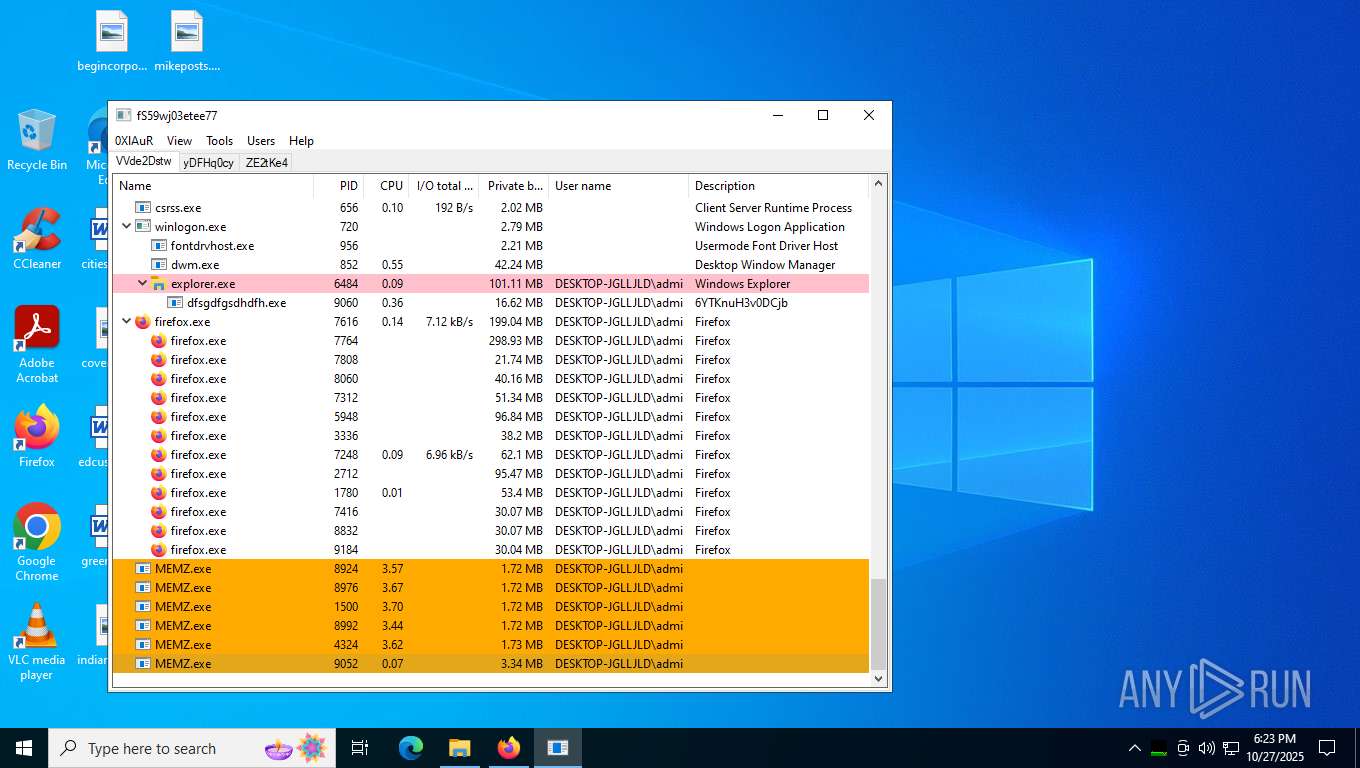
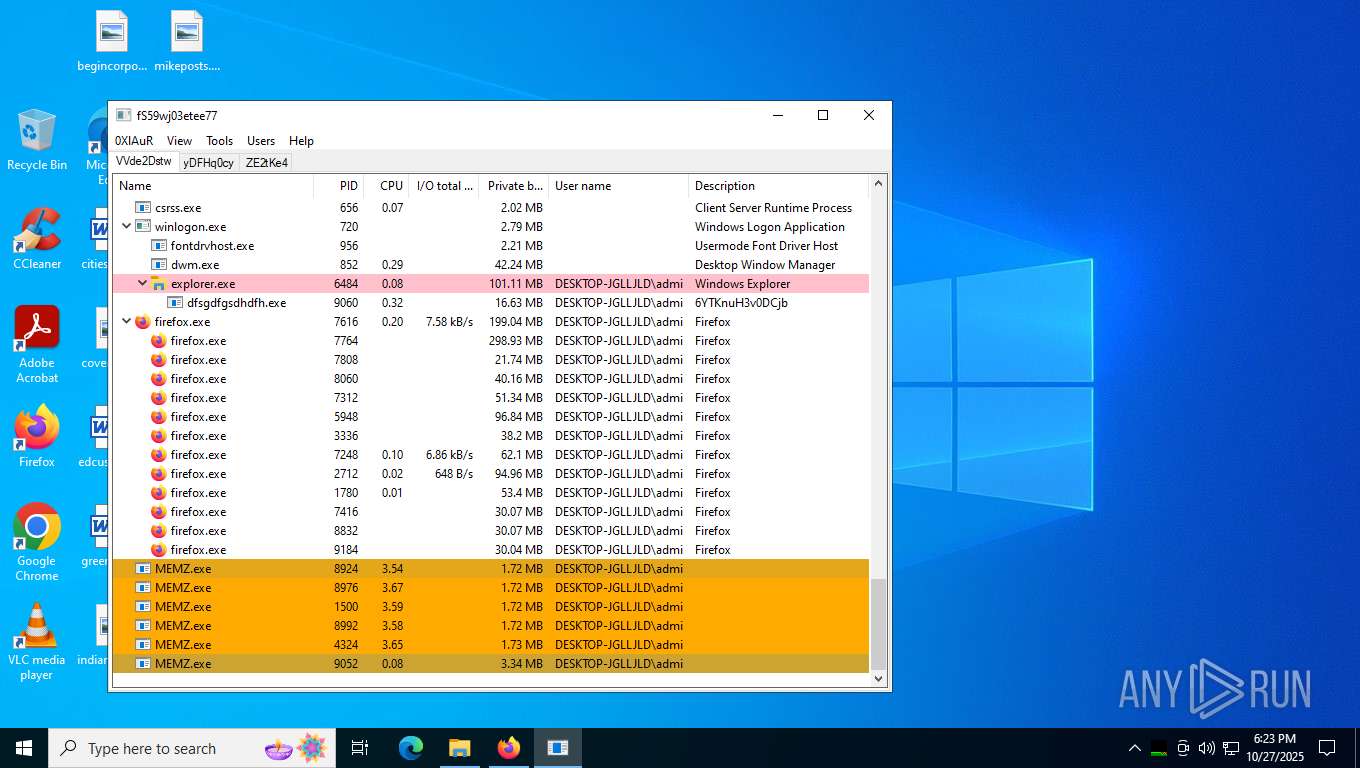
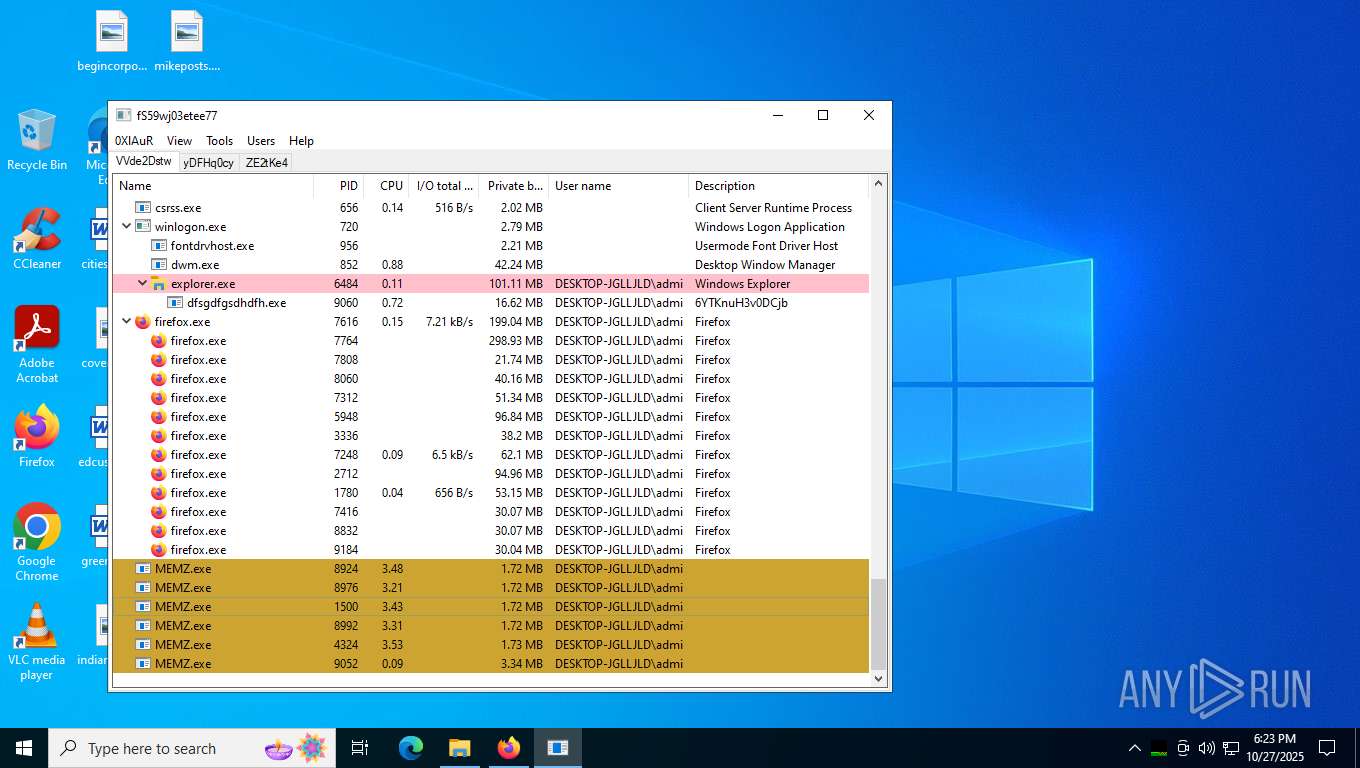
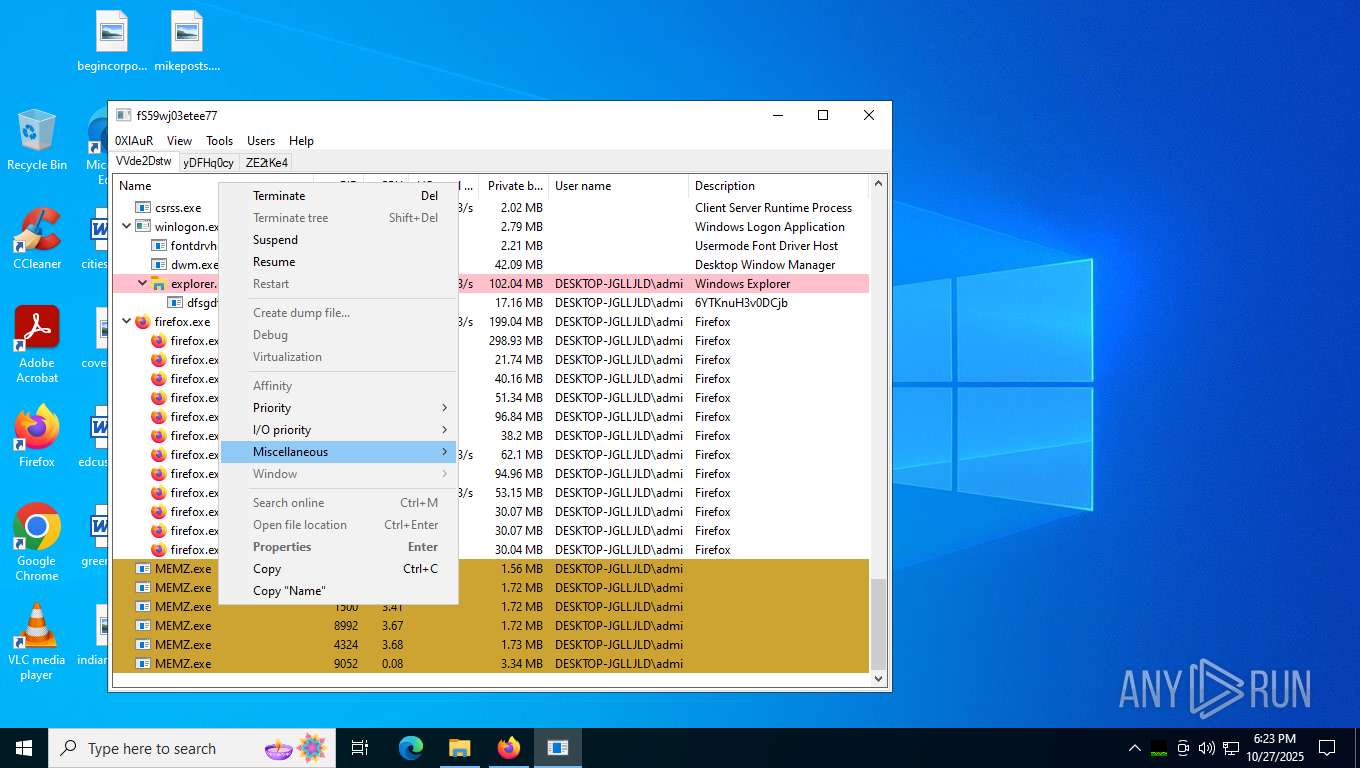
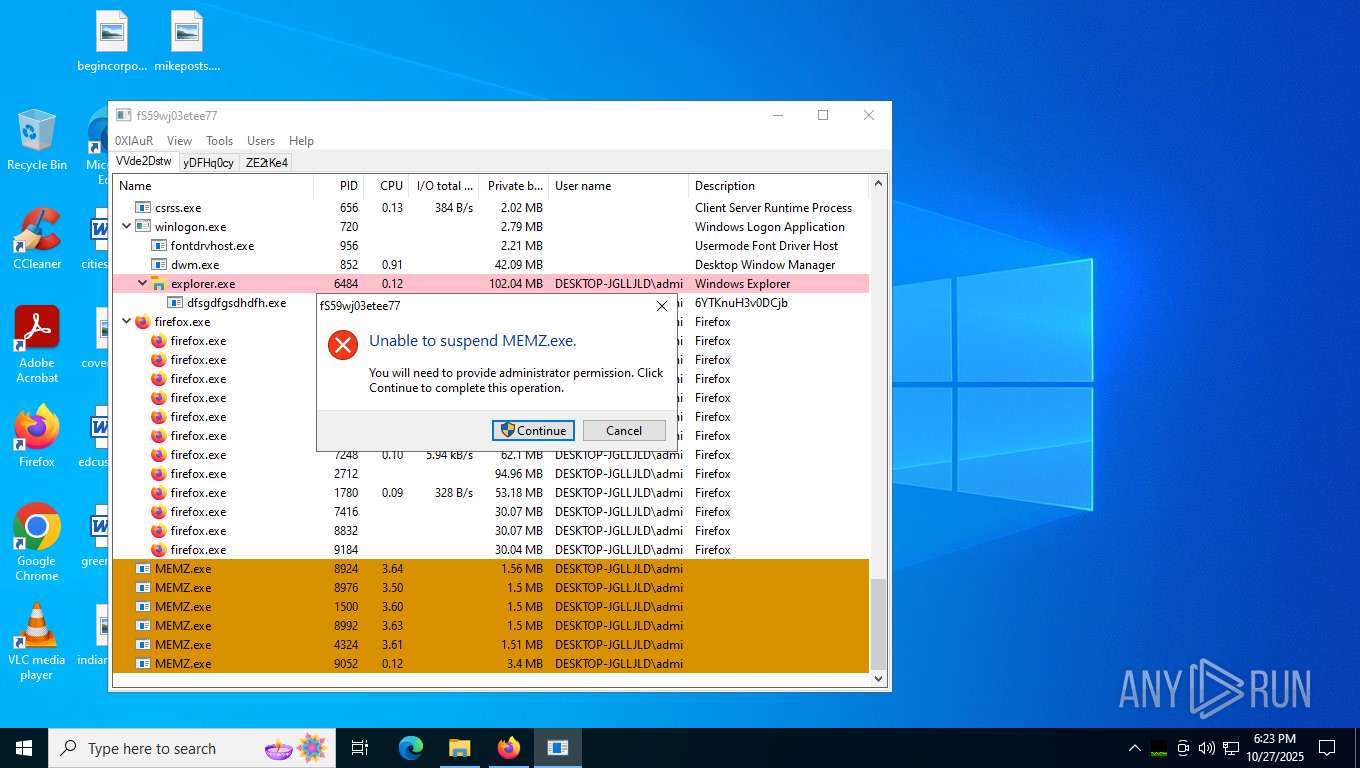
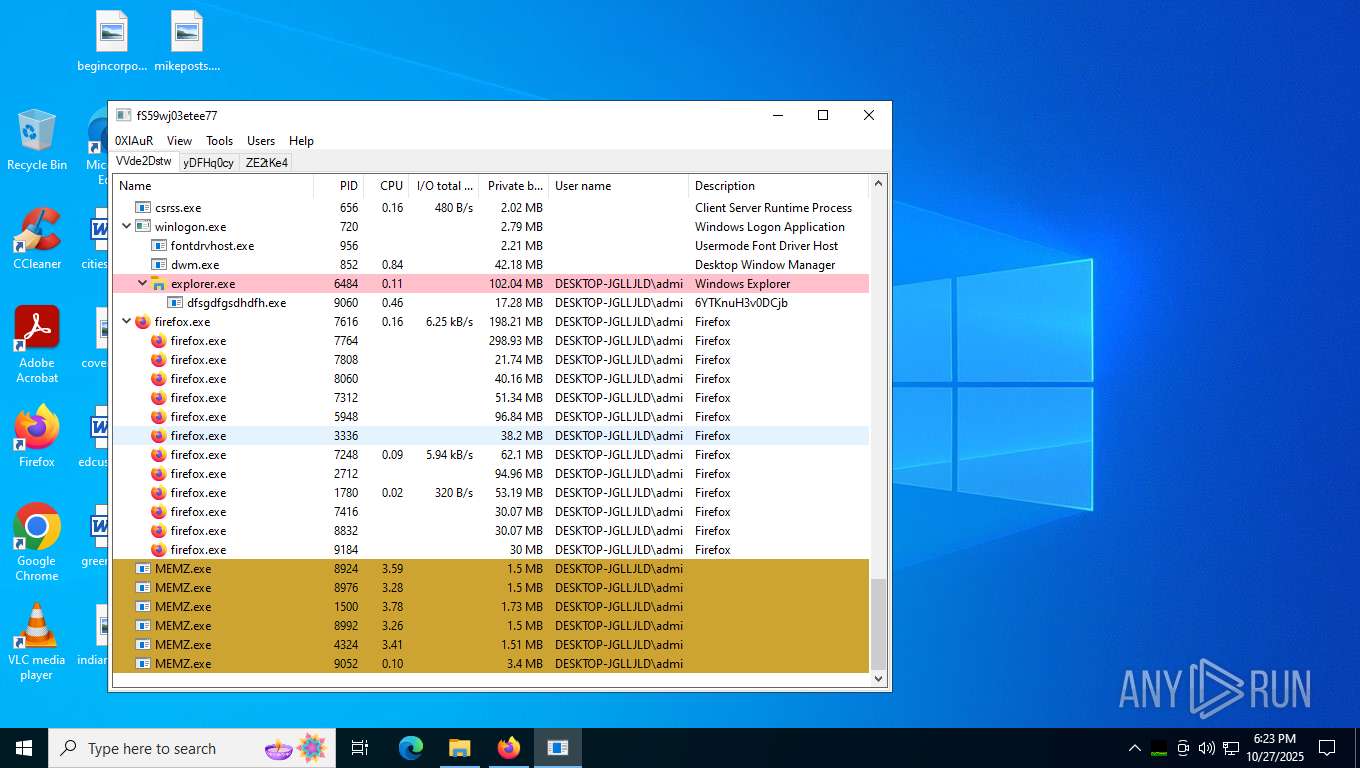
MEMZ has been detected (YARA)
- MEMZ.exe (PID: 8924)
- MEMZ.exe (PID: 1500)
- MEMZ.exe (PID: 4324)
- MEMZ.exe (PID: 8976)
- MEMZ.exe (PID: 9052)
- MEMZ.exe (PID: 8992)
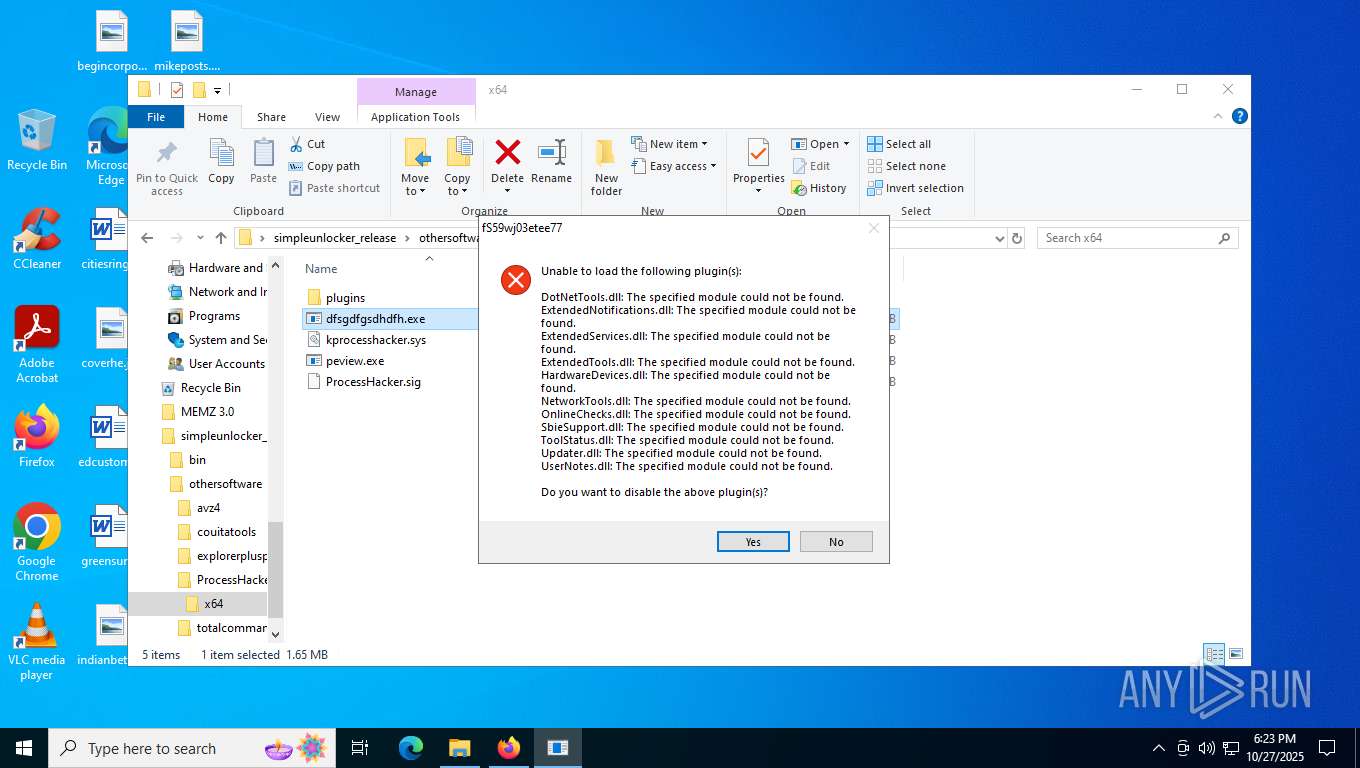
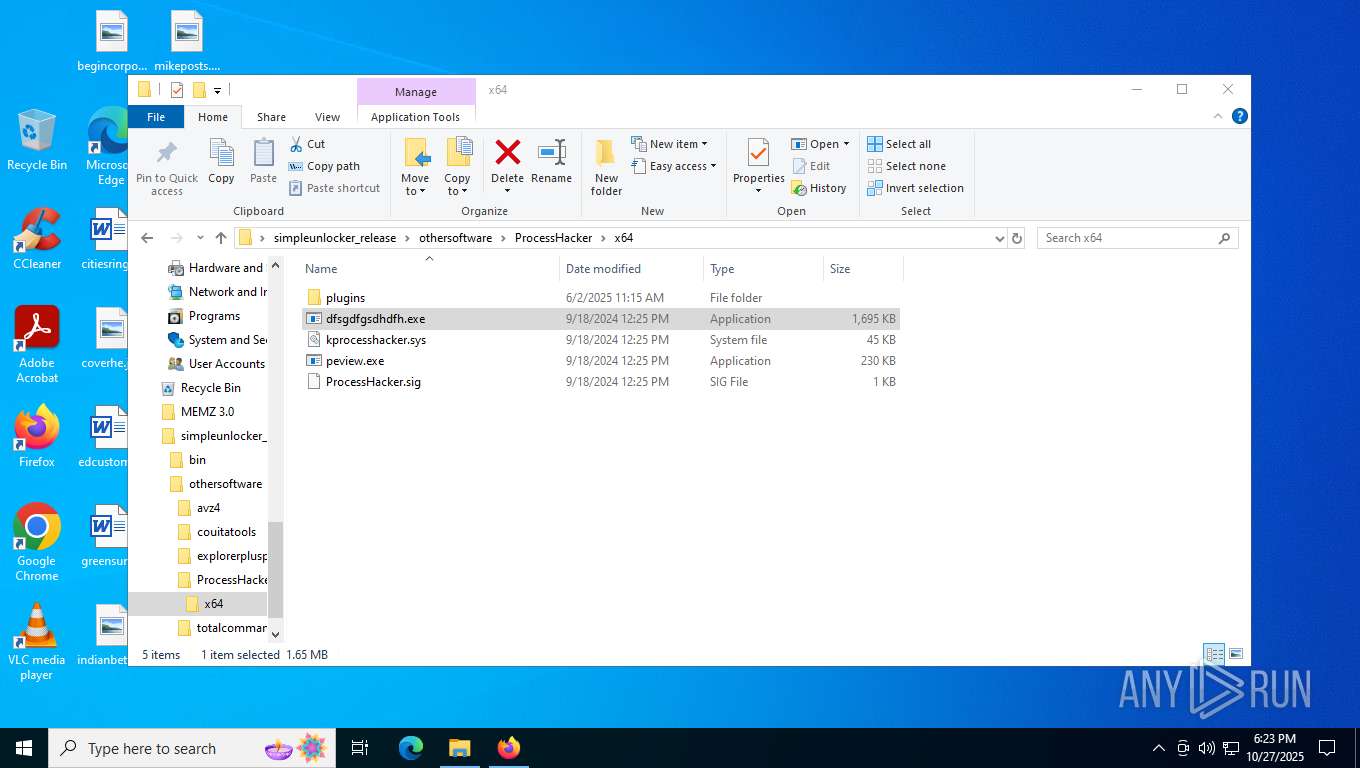
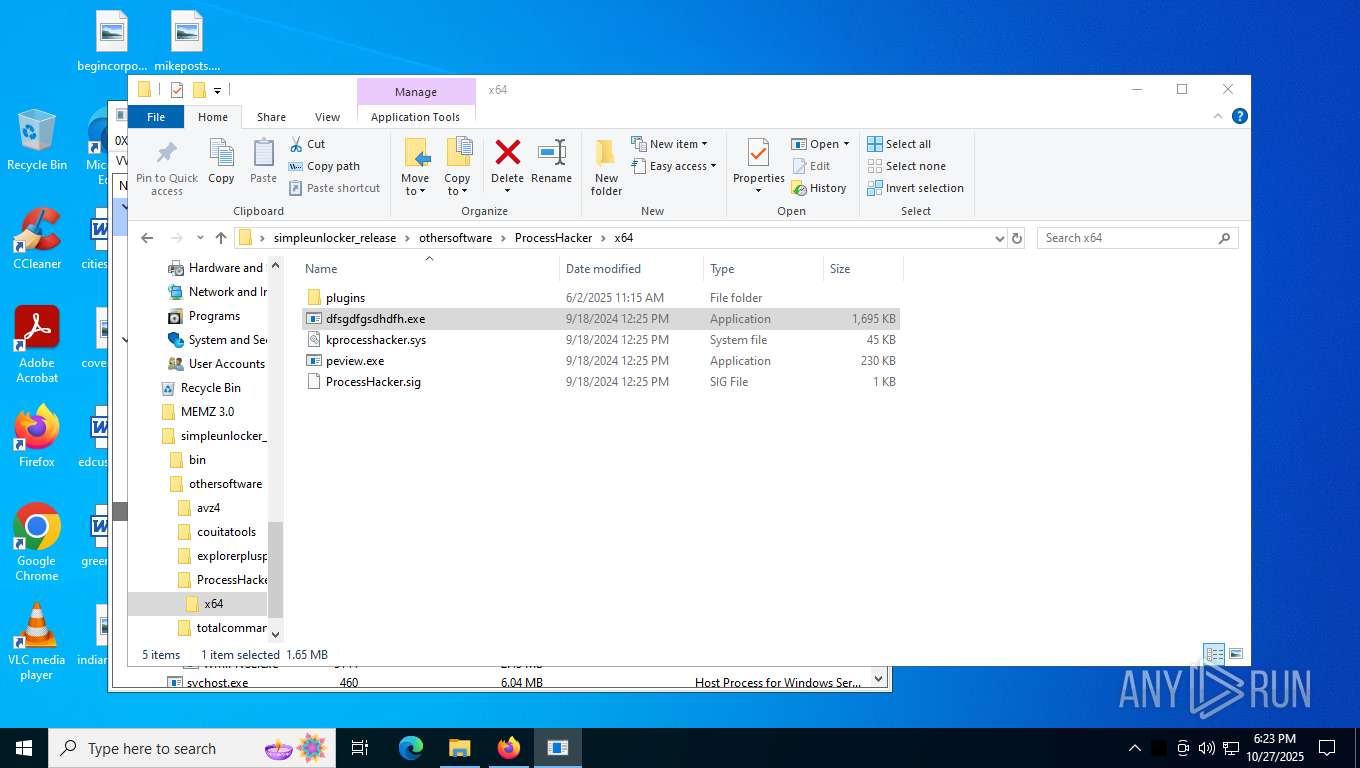
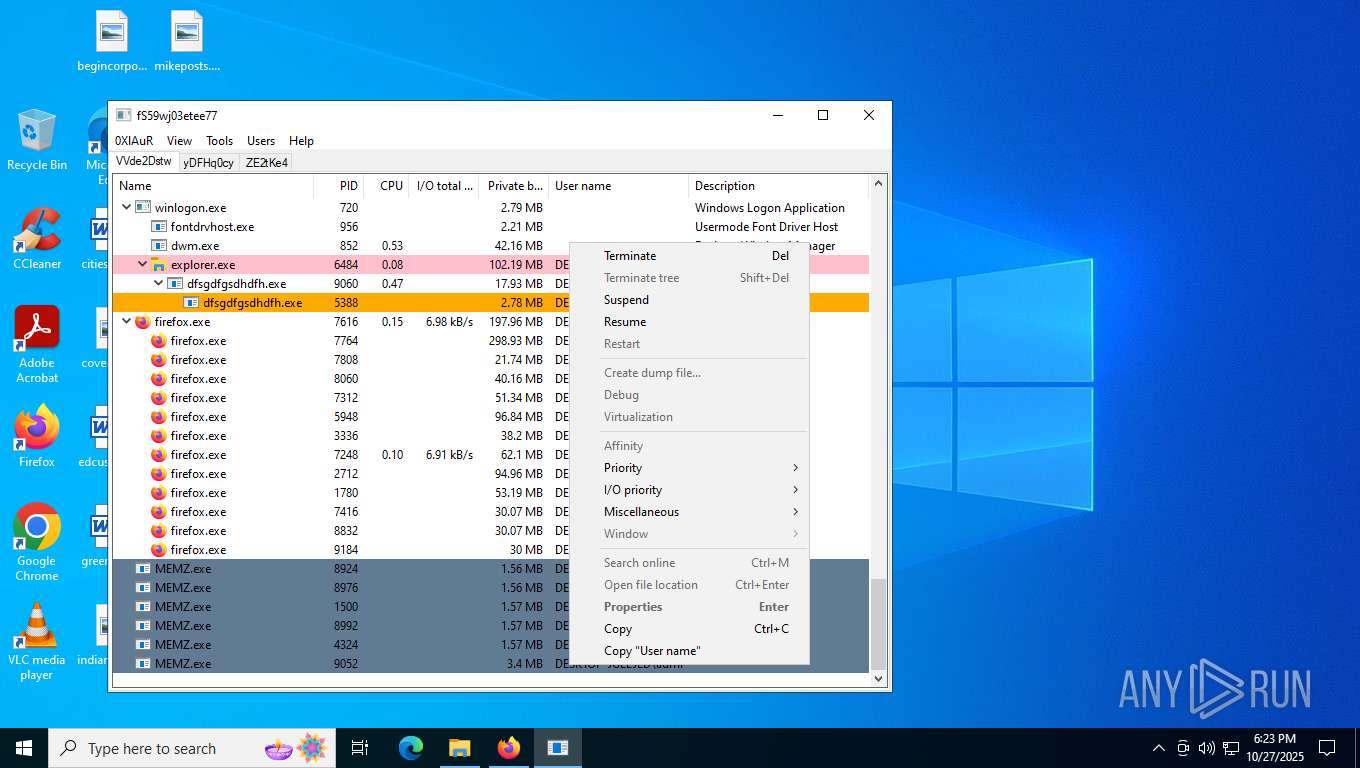
Executing a file with an untrusted certificate
- dfsgdfgsdhdfh.exe (PID: 9060)
- dfsgdfgsdhdfh.exe (PID: 5388)
- dfsgdfgsdhdfh.exe (PID: 9160)
SUSPICIOUS
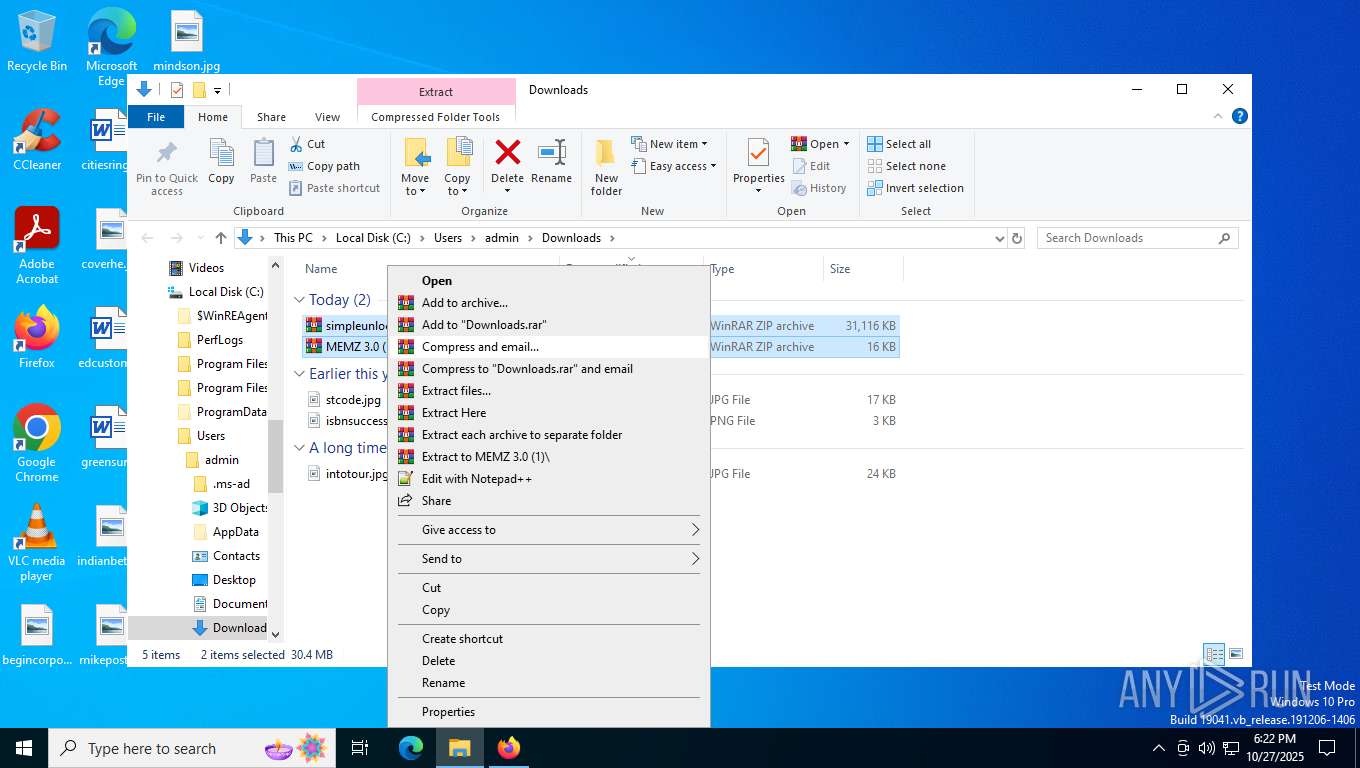
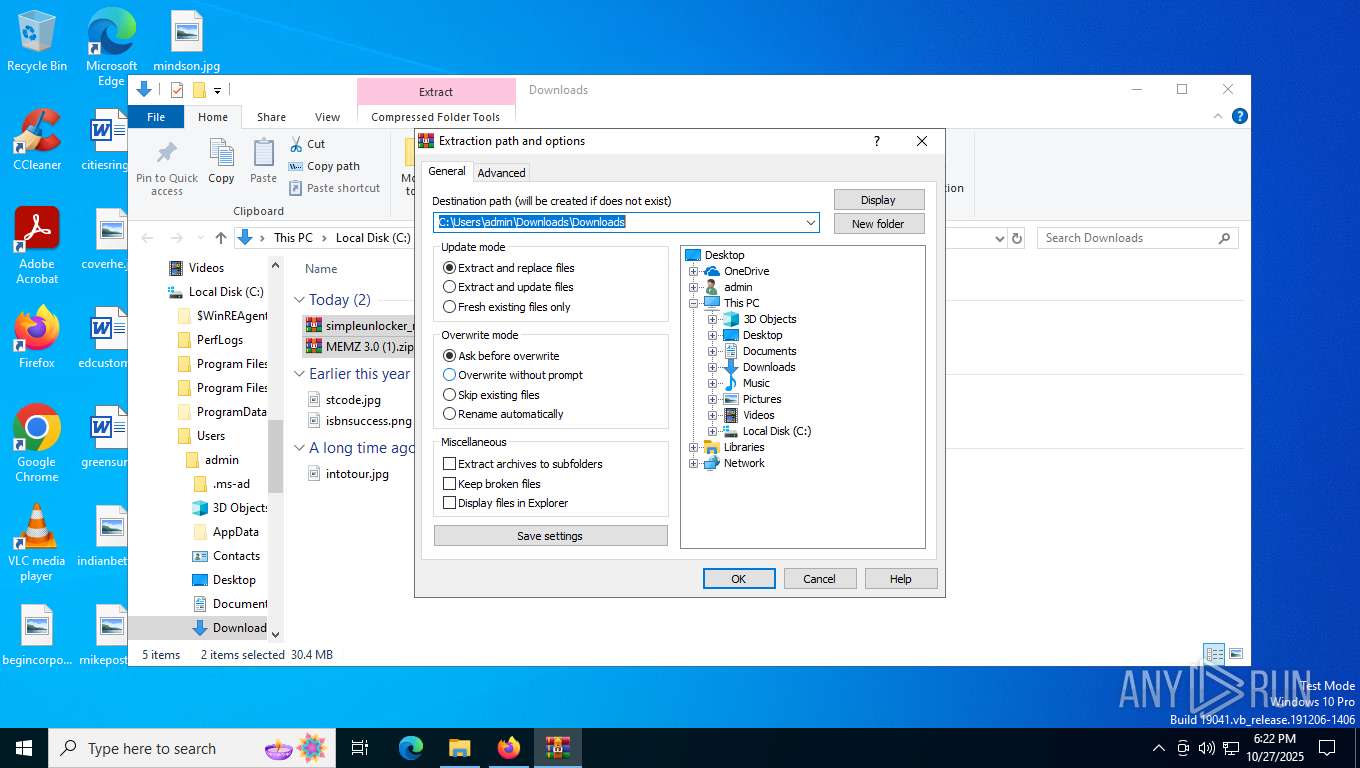
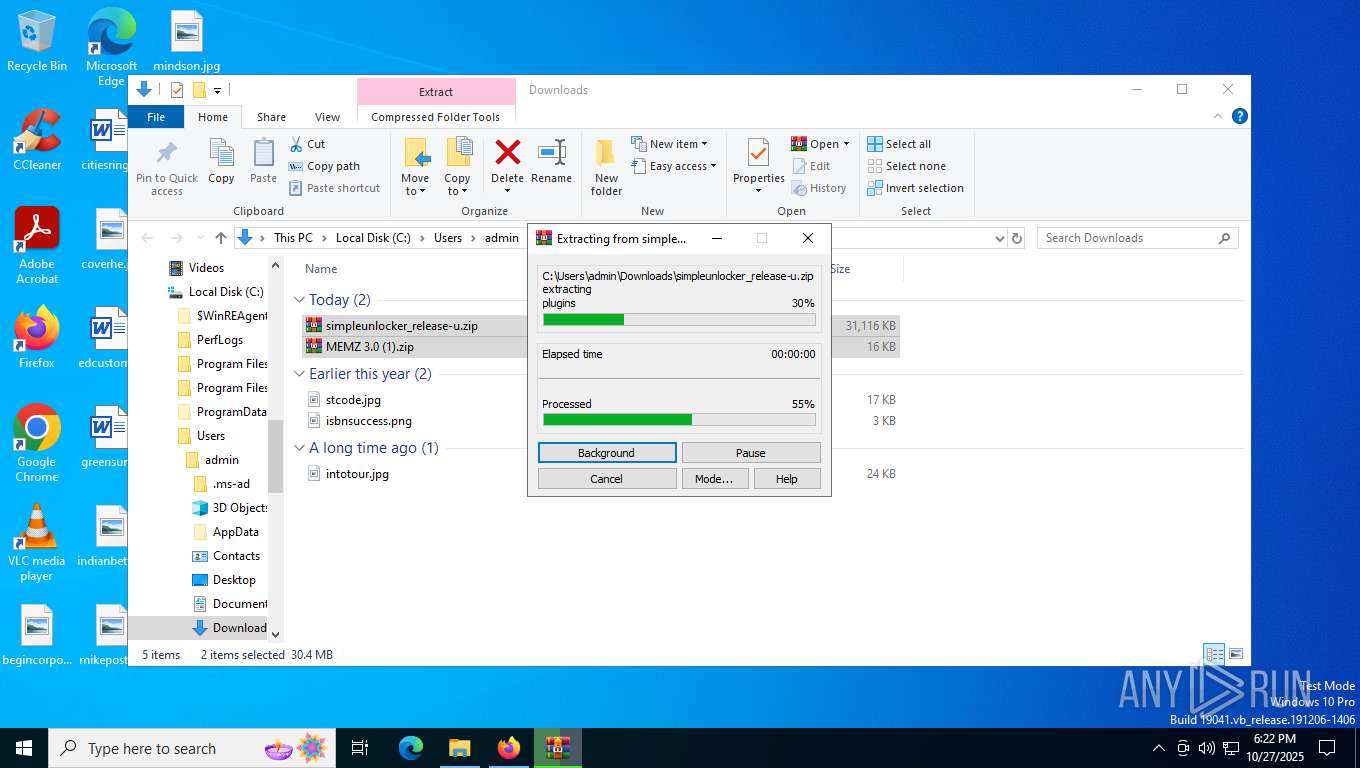
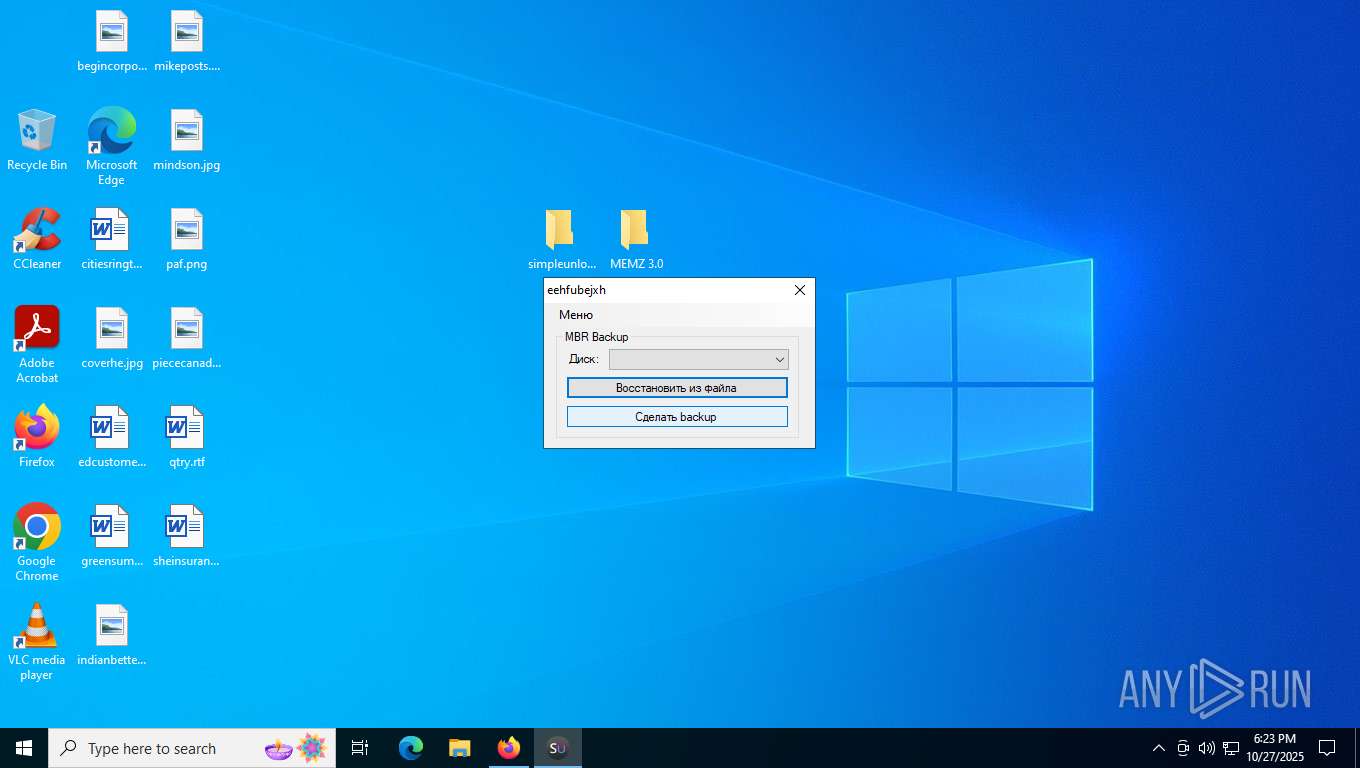
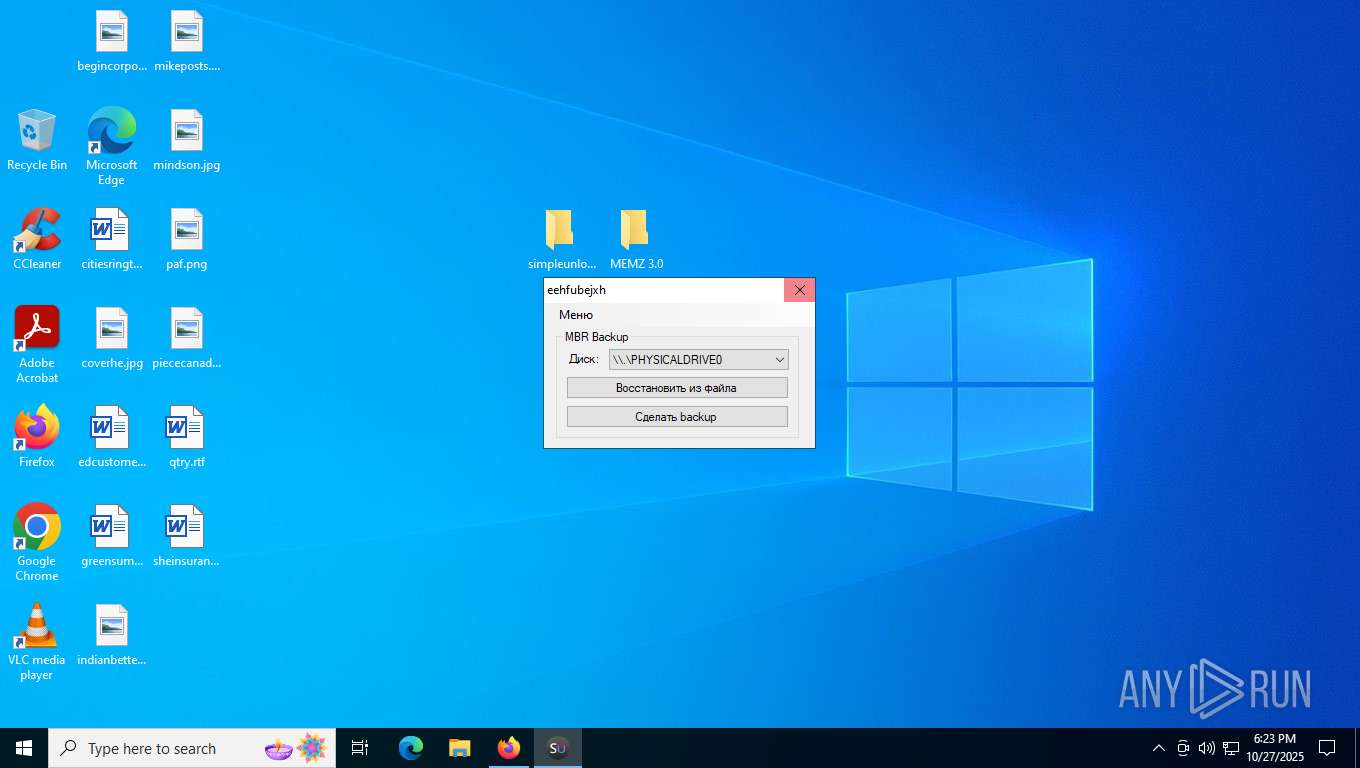
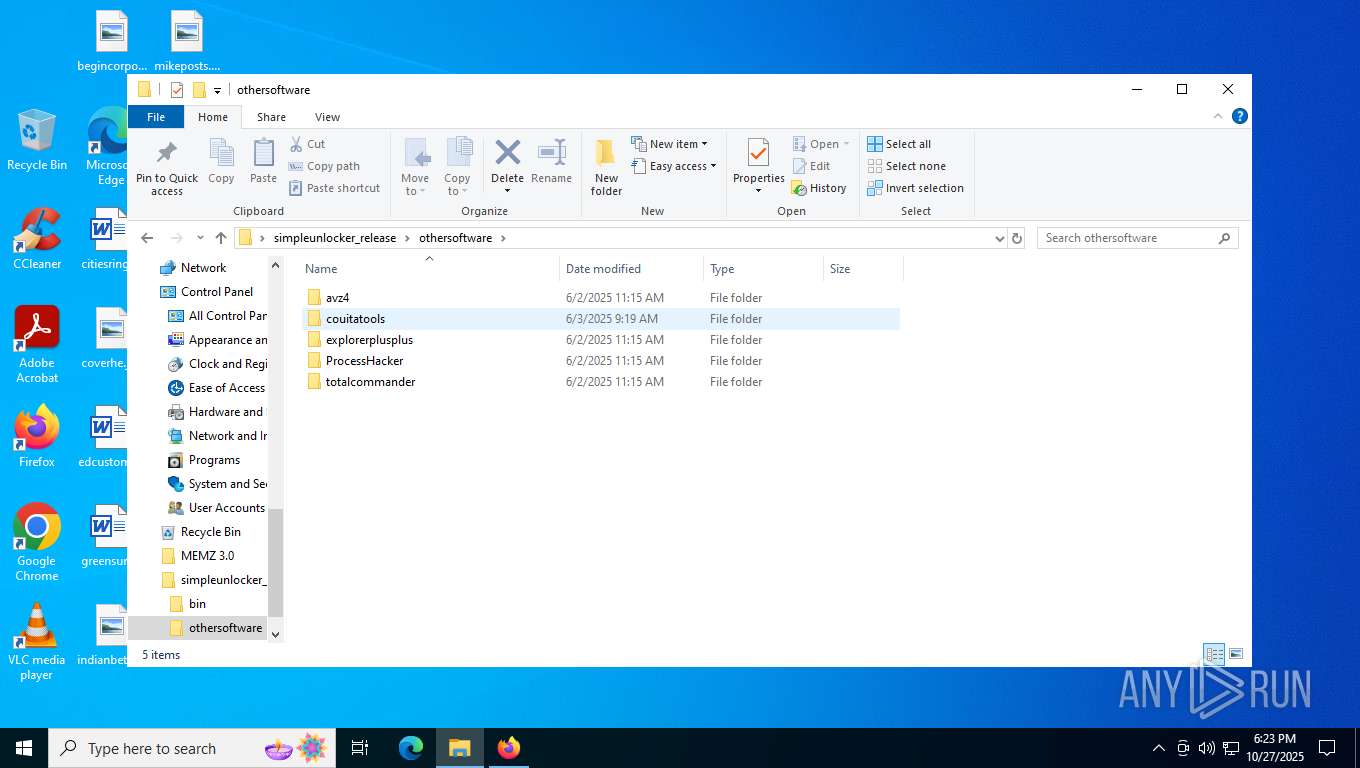
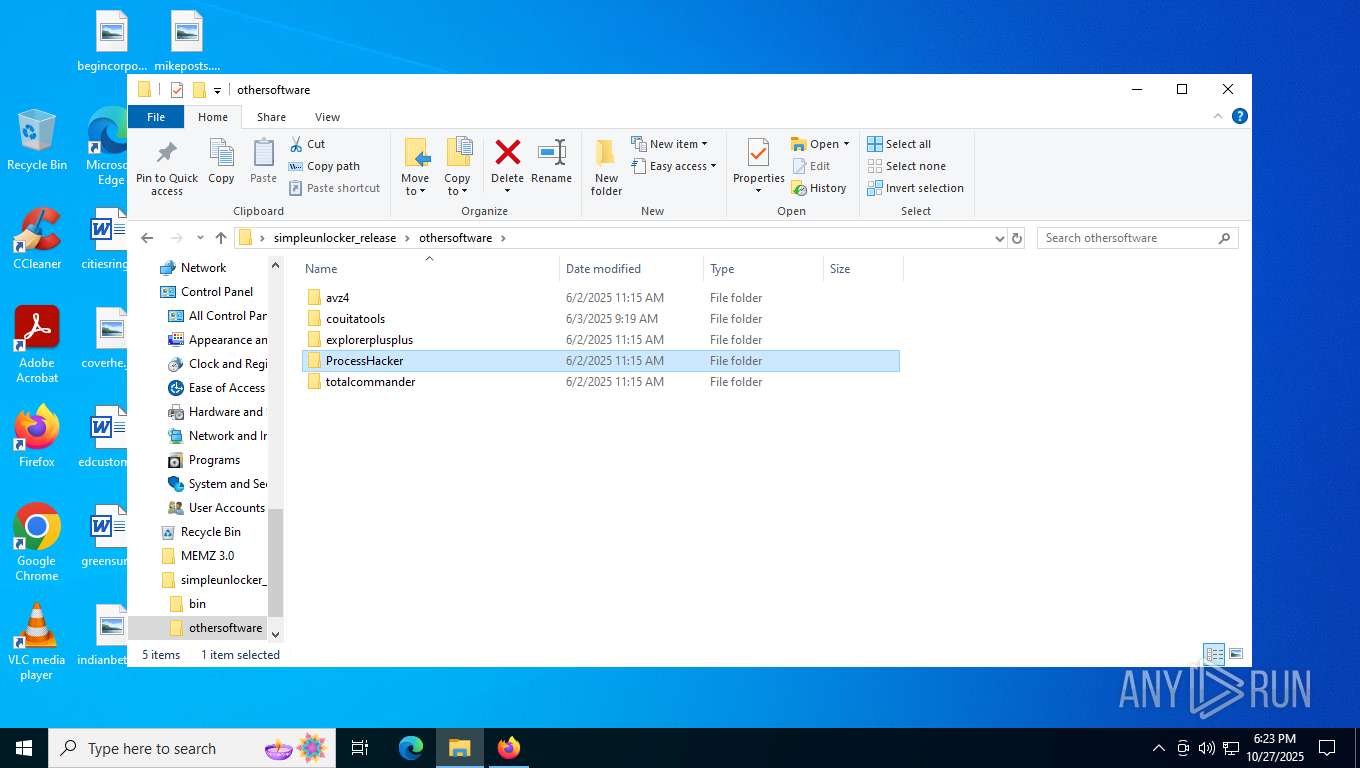
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 8100)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 8100)
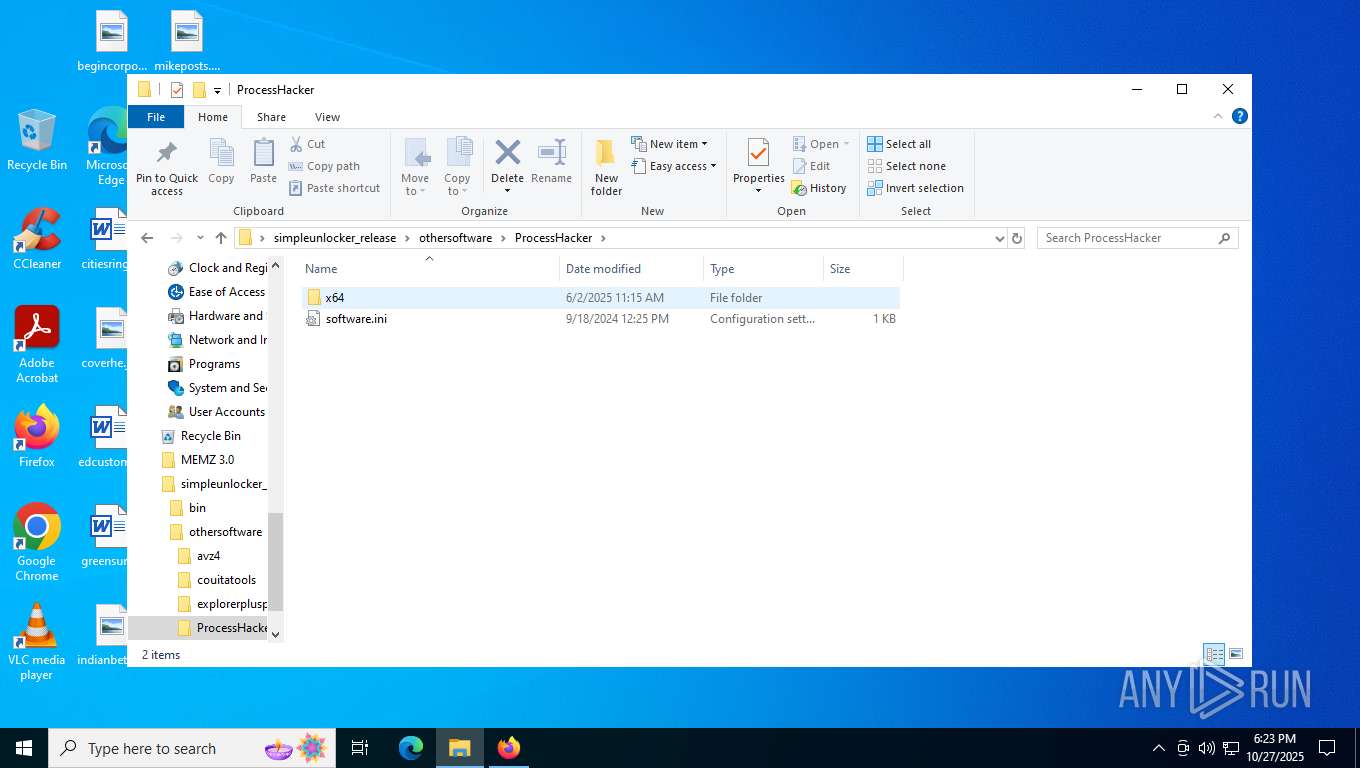
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 8100)
Reads security settings of Internet Explorer
- MEMZ.exe (PID: 8792)
- MEMZ.exe (PID: 9052)
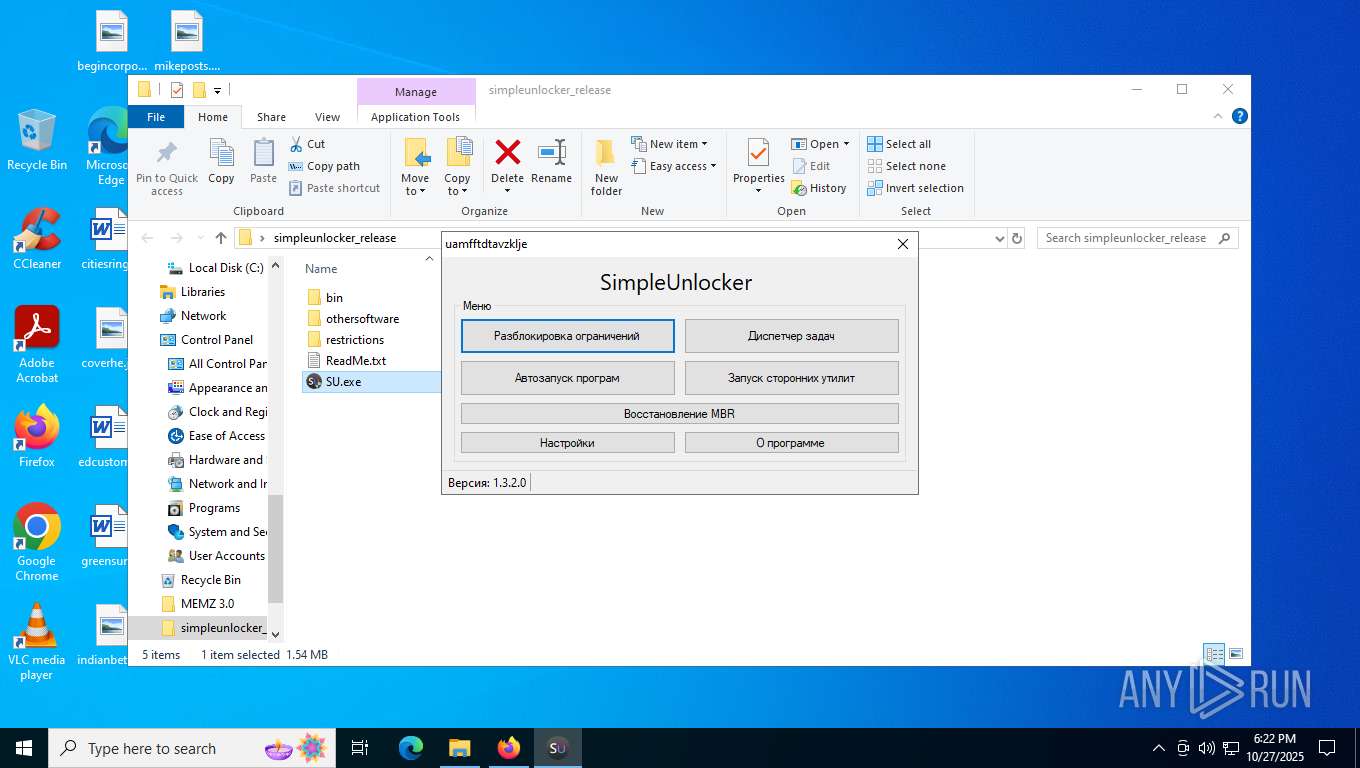
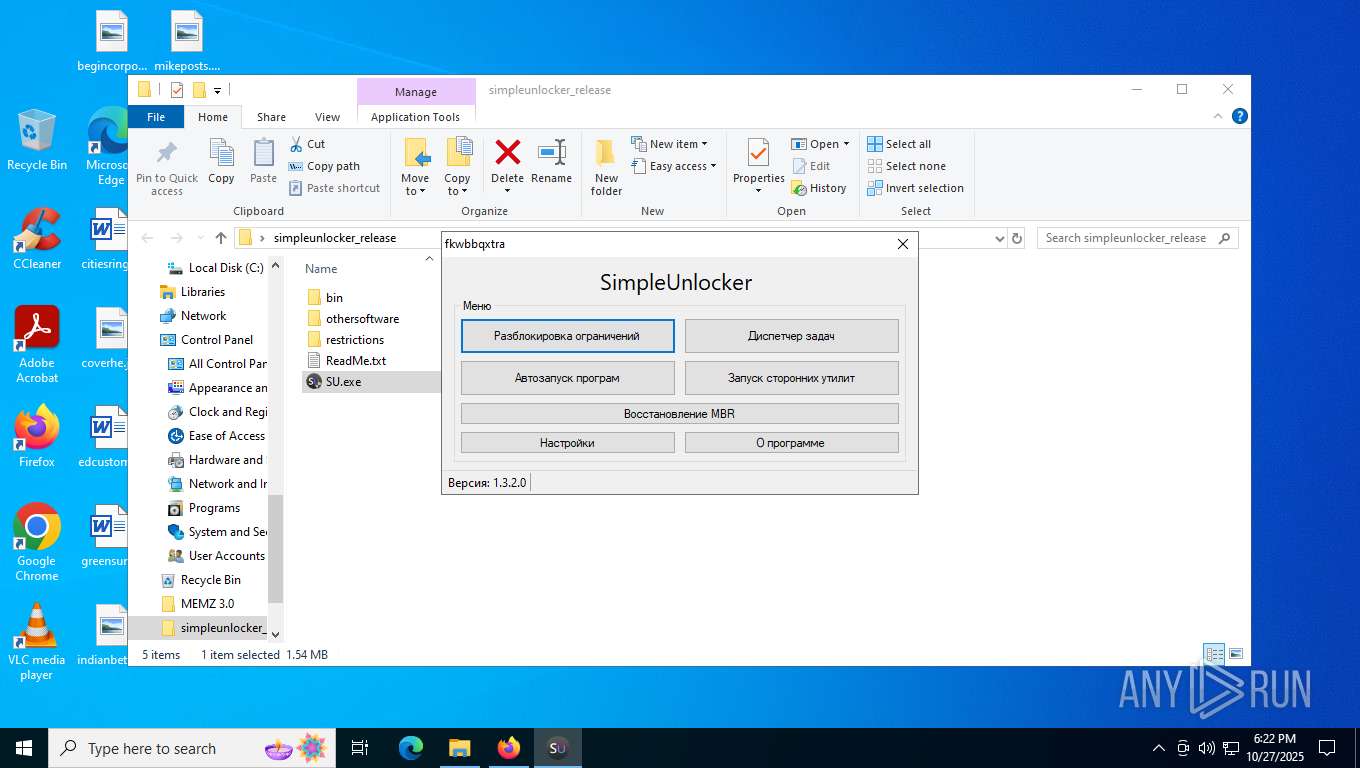
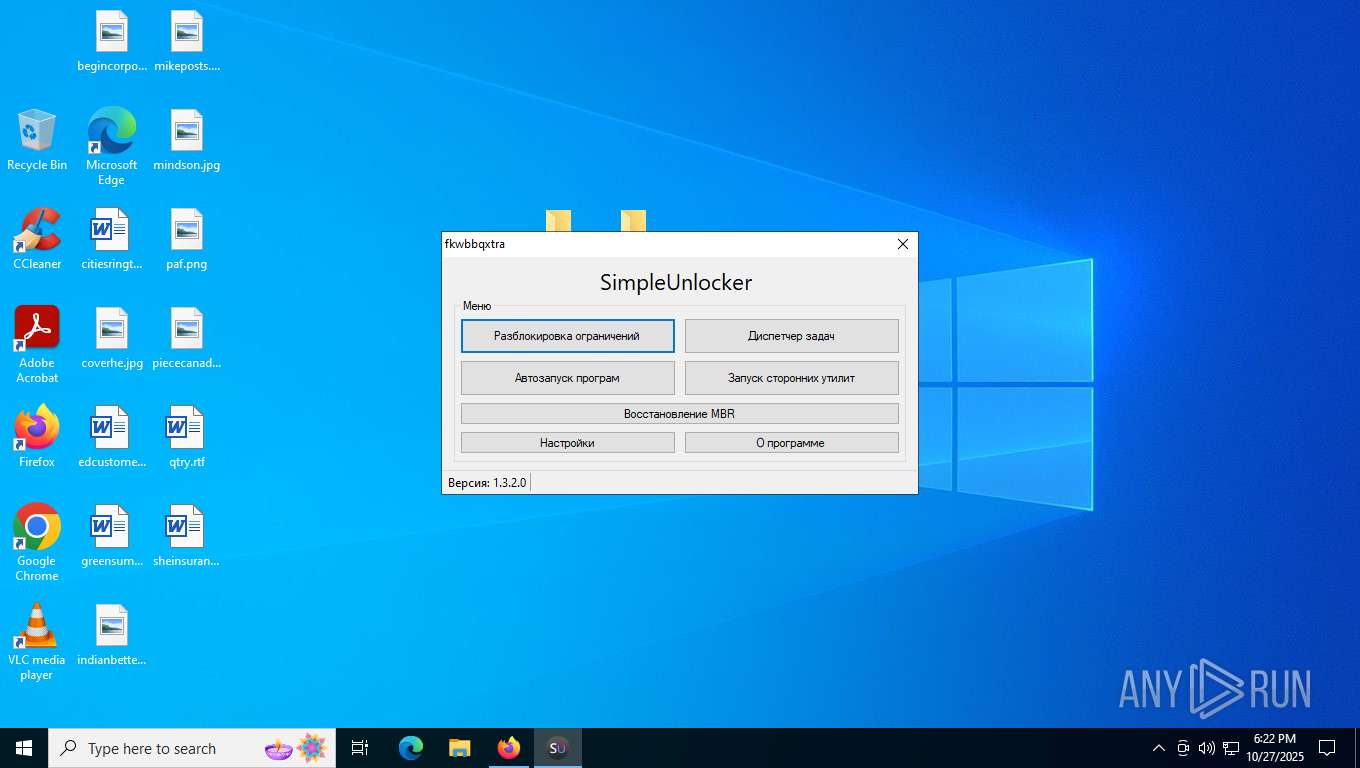
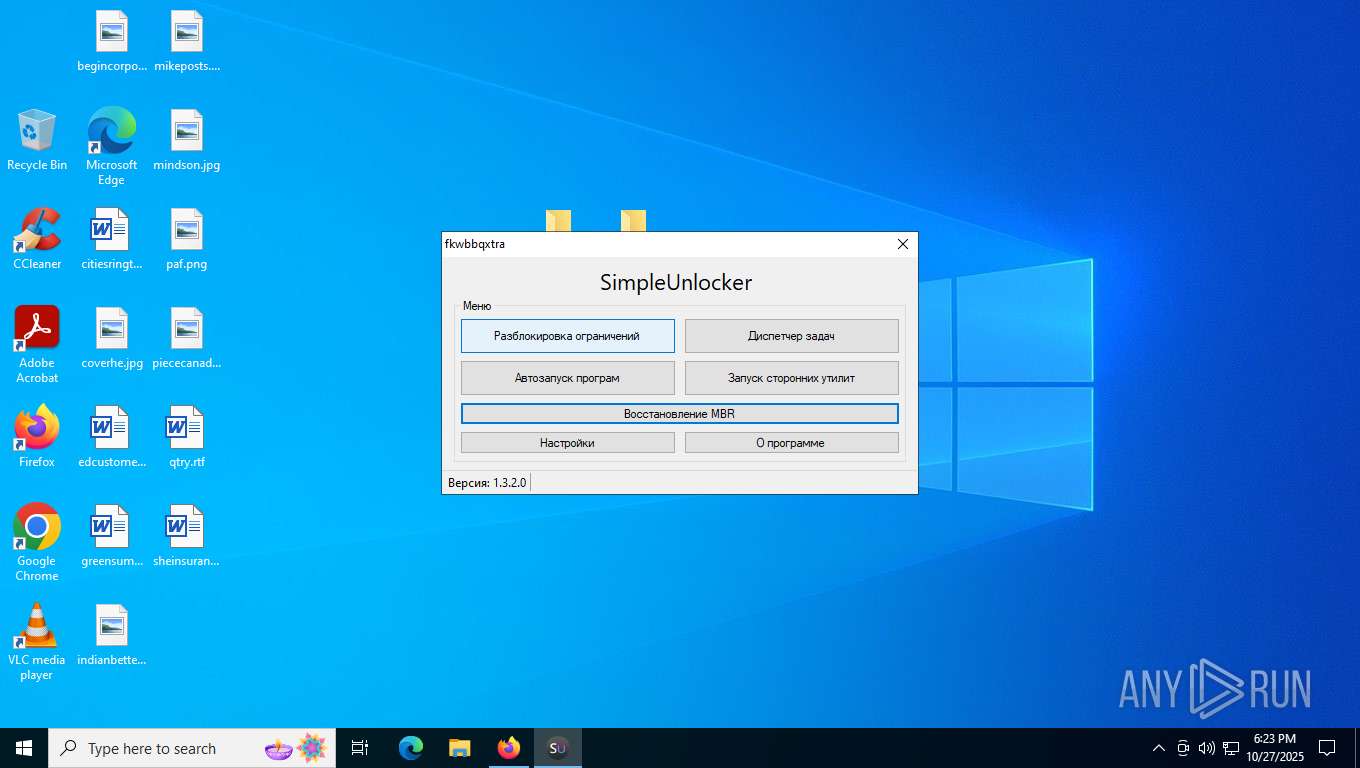
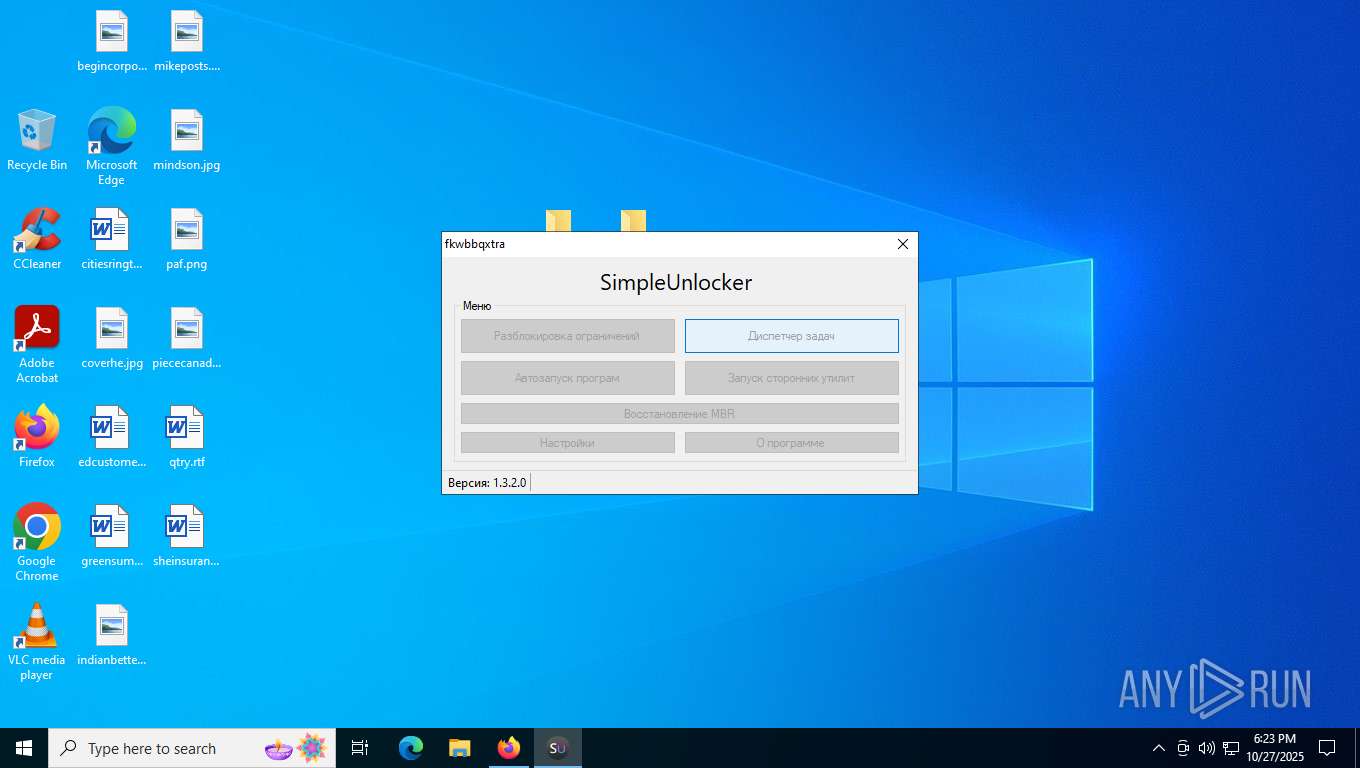
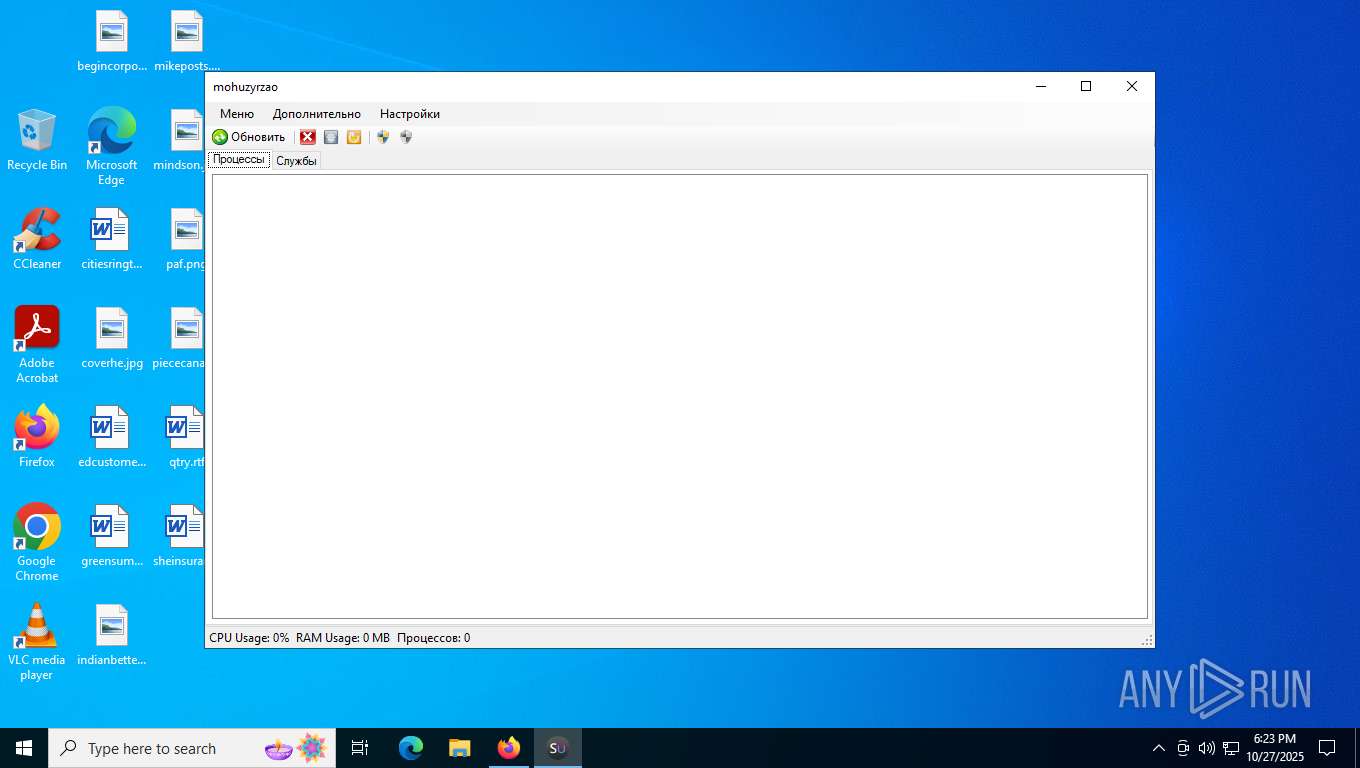
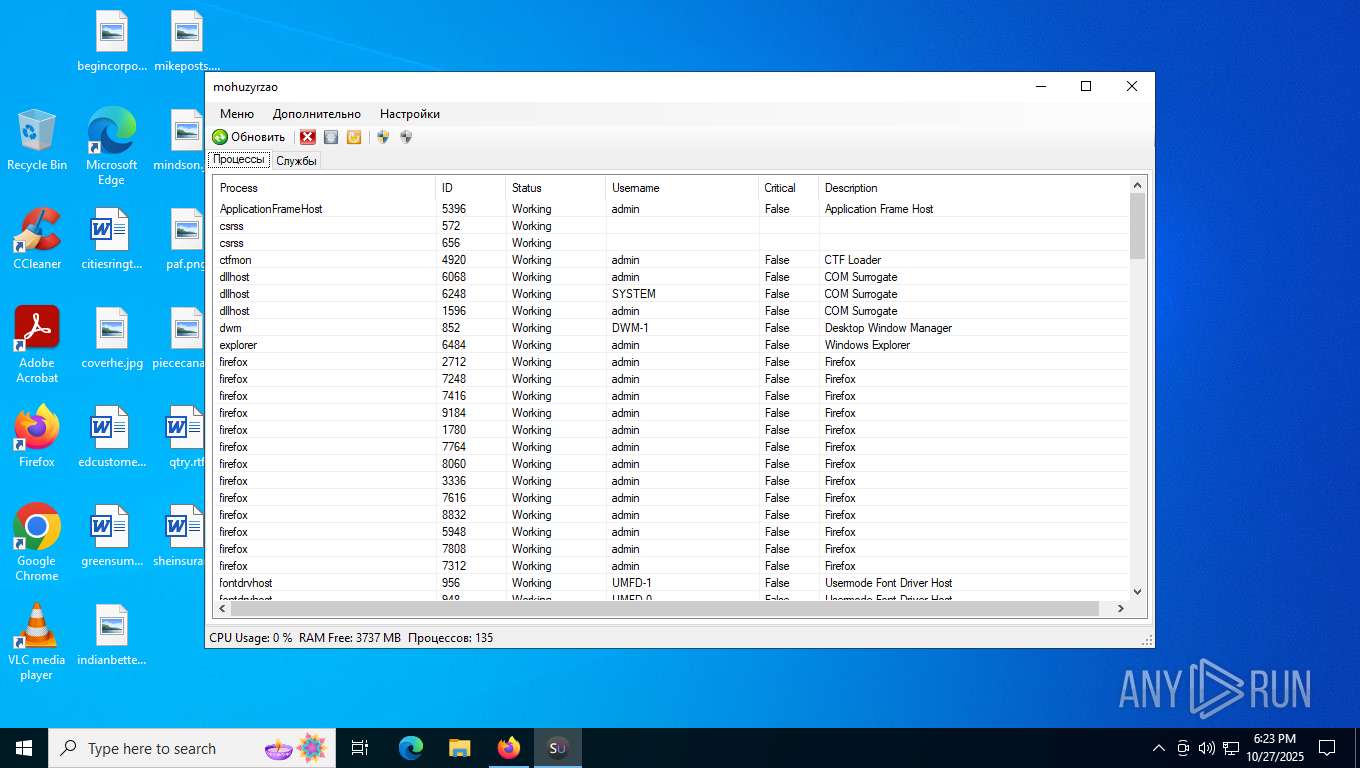
- SU.exe (PID: 8280)
- SU.exe (PID: 7332)
- dfsgdfgsdhdfh.exe (PID: 9060)
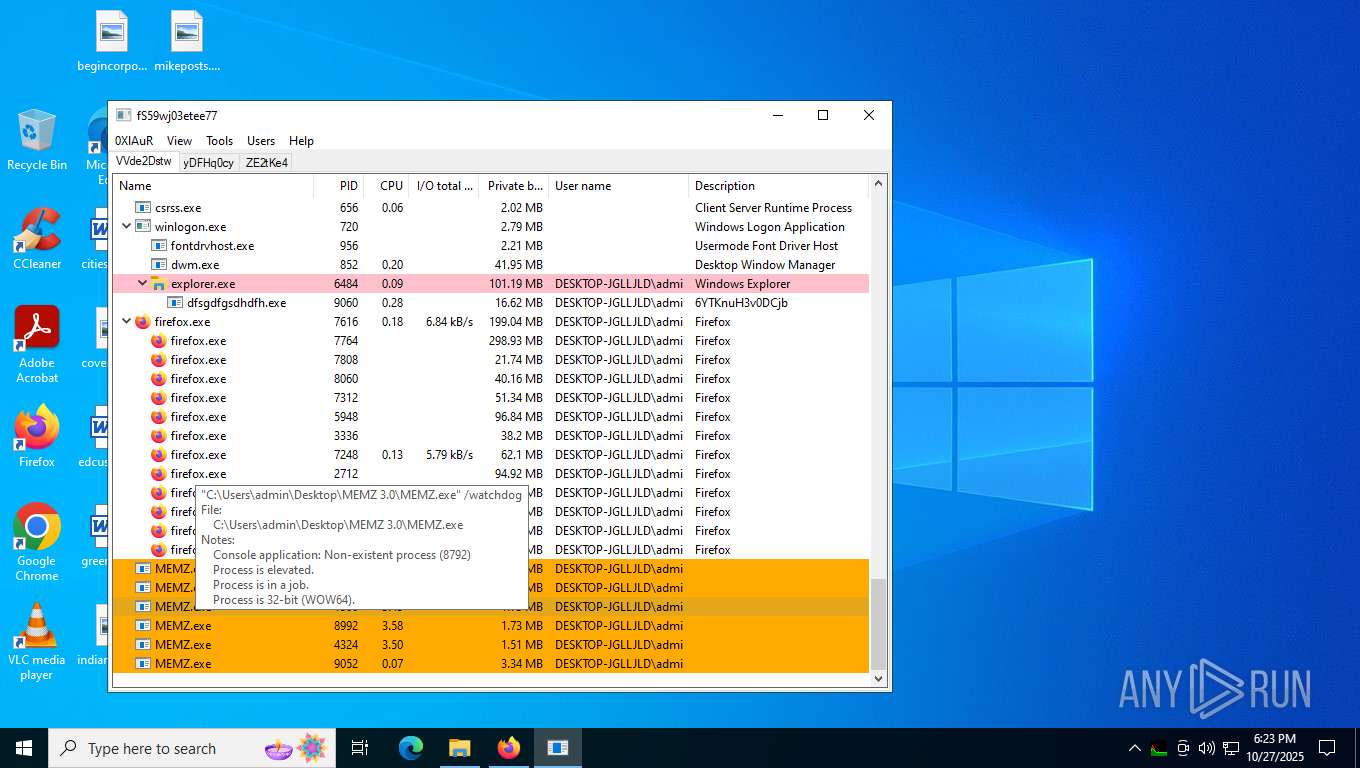
Application launched itself
- MEMZ.exe (PID: 8792)
- dfsgdfgsdhdfh.exe (PID: 9060)
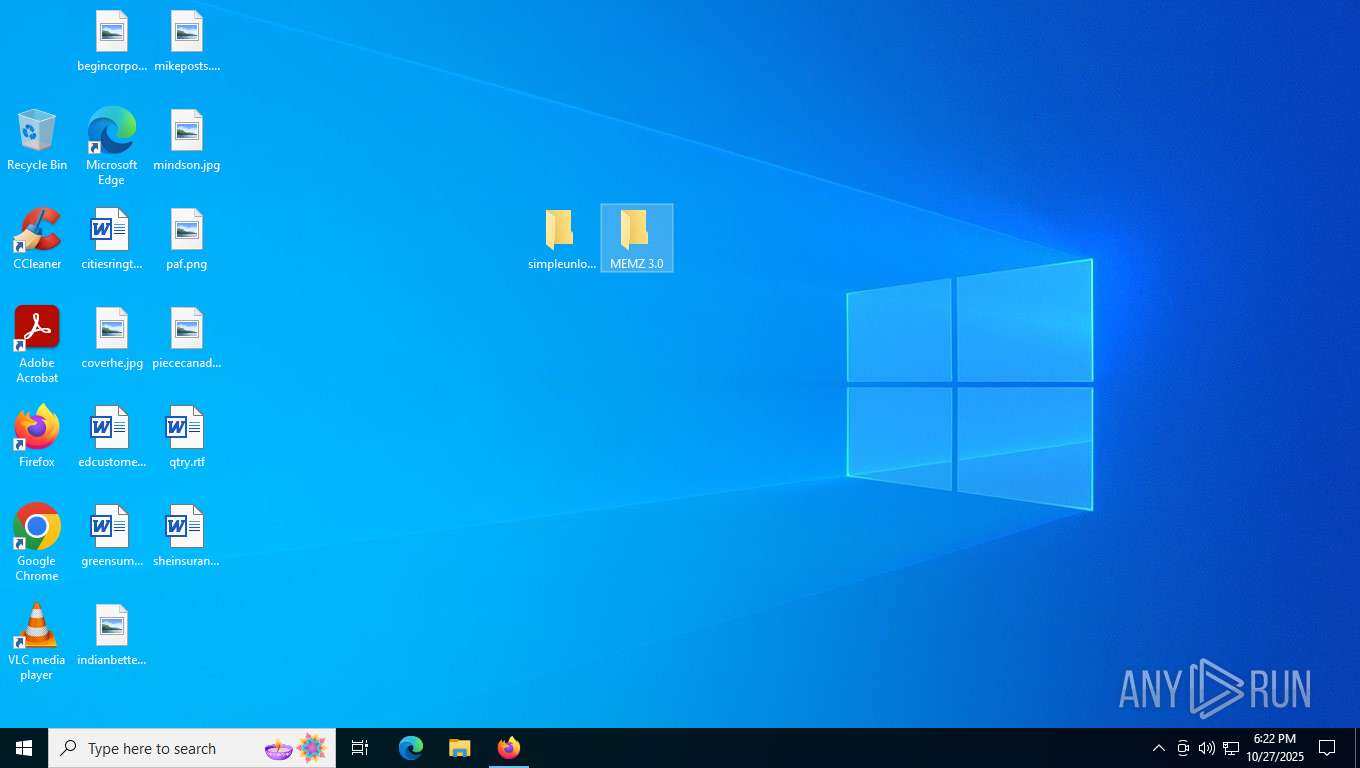
Creates file in the systems drive root
- MEMZ.exe (PID: 9052)
- notepad.exe (PID: 9044)
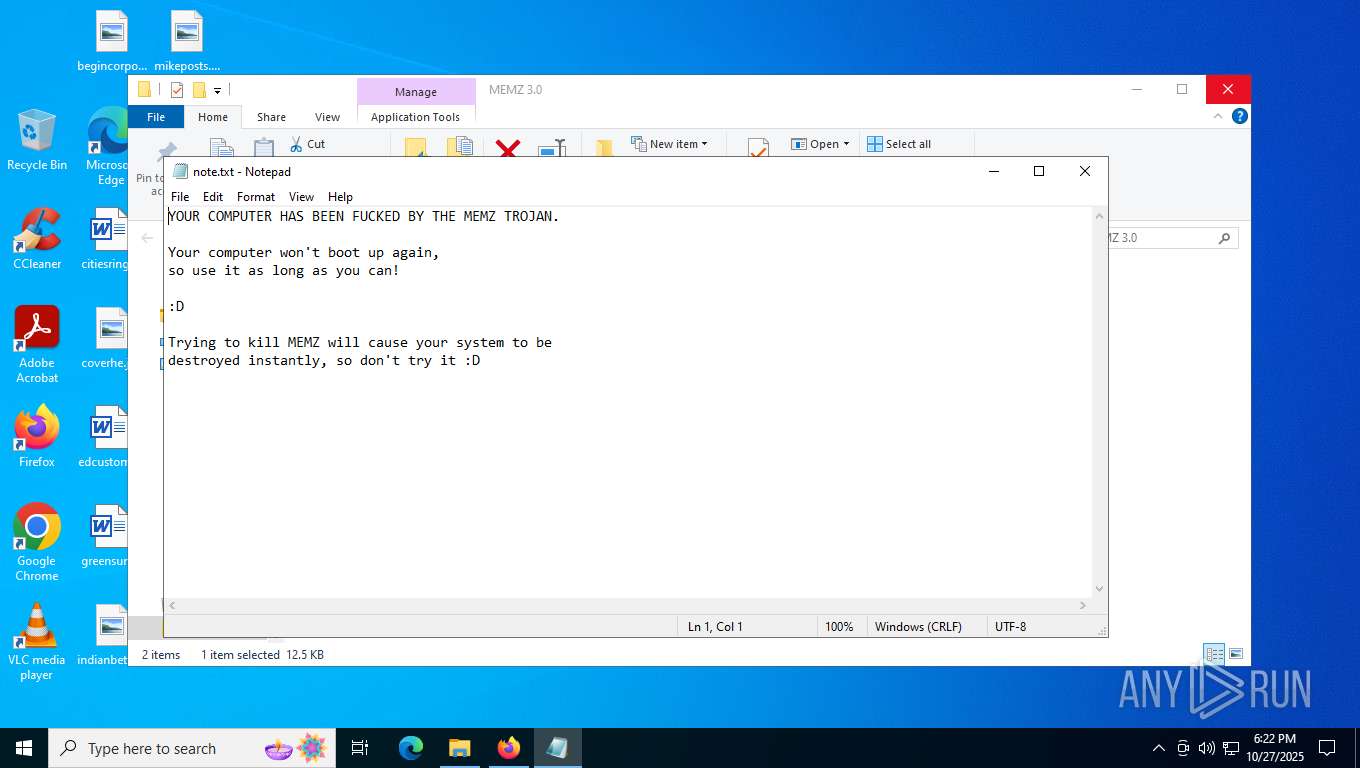
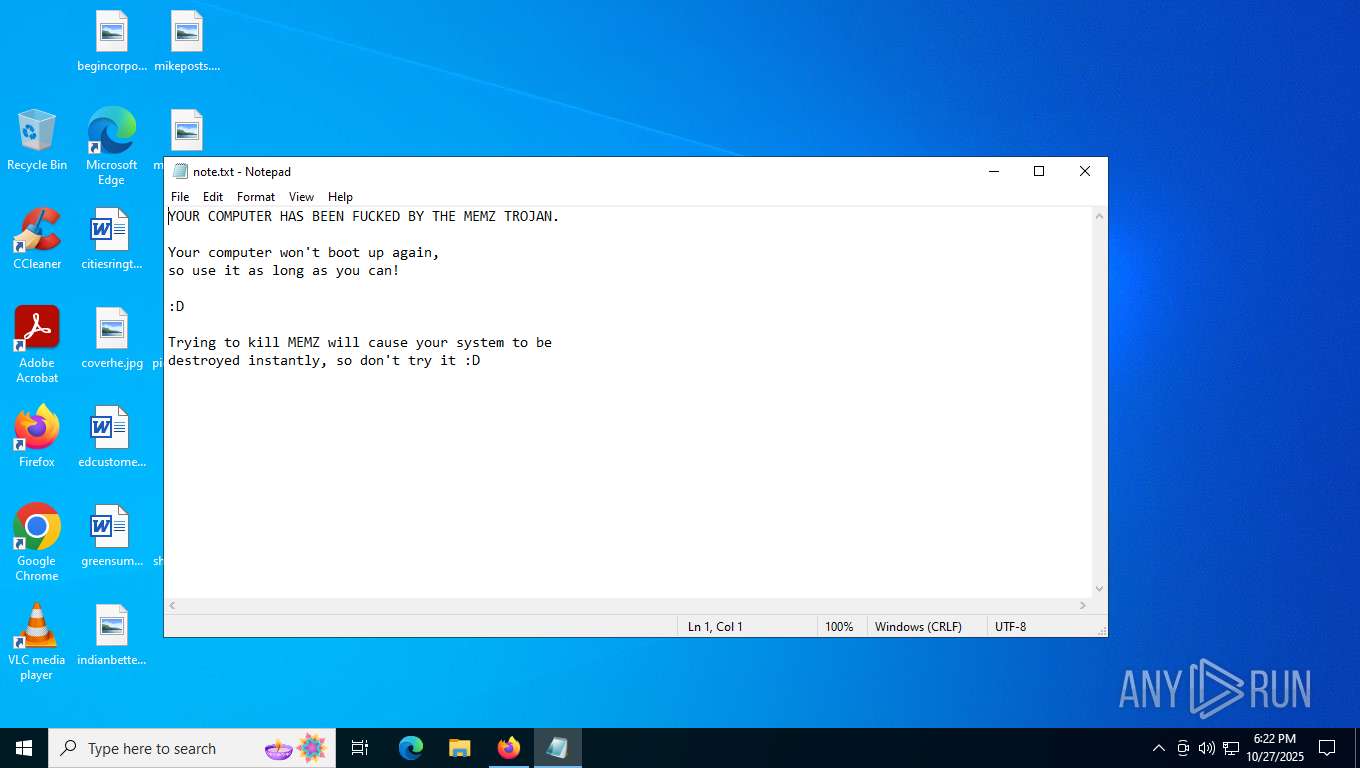
Start notepad (likely ransomware note)
- MEMZ.exe (PID: 9052)
There is functionality for taking screenshot (YARA)
- MEMZ.exe (PID: 8924)
- MEMZ.exe (PID: 1500)
- MEMZ.exe (PID: 8976)
- MEMZ.exe (PID: 4324)
- MEMZ.exe (PID: 8992)
- MEMZ.exe (PID: 9052)
- dfsgdfgsdhdfh.exe (PID: 5388)
- dfsgdfgsdhdfh.exe (PID: 9060)
Check the default browser
- SU.exe (PID: 8280)
Executes as Windows Service
- WmiApSrv.exe (PID: 5864)
Reads the date of Windows installation
- dfsgdfgsdhdfh.exe (PID: 9060)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 8100)
Checks supported languages
- MEMZ.exe (PID: 8792)
- MEMZ.exe (PID: 4324)
- MEMZ.exe (PID: 8976)
- MEMZ.exe (PID: 1500)
- MEMZ.exe (PID: 8924)
- MEMZ.exe (PID: 8992)
- MEMZ.exe (PID: 9052)
- SU.exe (PID: 8280)
- SU.exe (PID: 7332)
- dfsgdfgsdhdfh.exe (PID: 9060)
- identity_helper.exe (PID: 8268)
- dfsgdfgsdhdfh.exe (PID: 5388)
- dfsgdfgsdhdfh.exe (PID: 9160)
Application launched itself
- firefox.exe (PID: 7488)
- firefox.exe (PID: 7616)
- msedge.exe (PID: 8268)
- msedge.exe (PID: 9160)
- msedge.exe (PID: 2968)
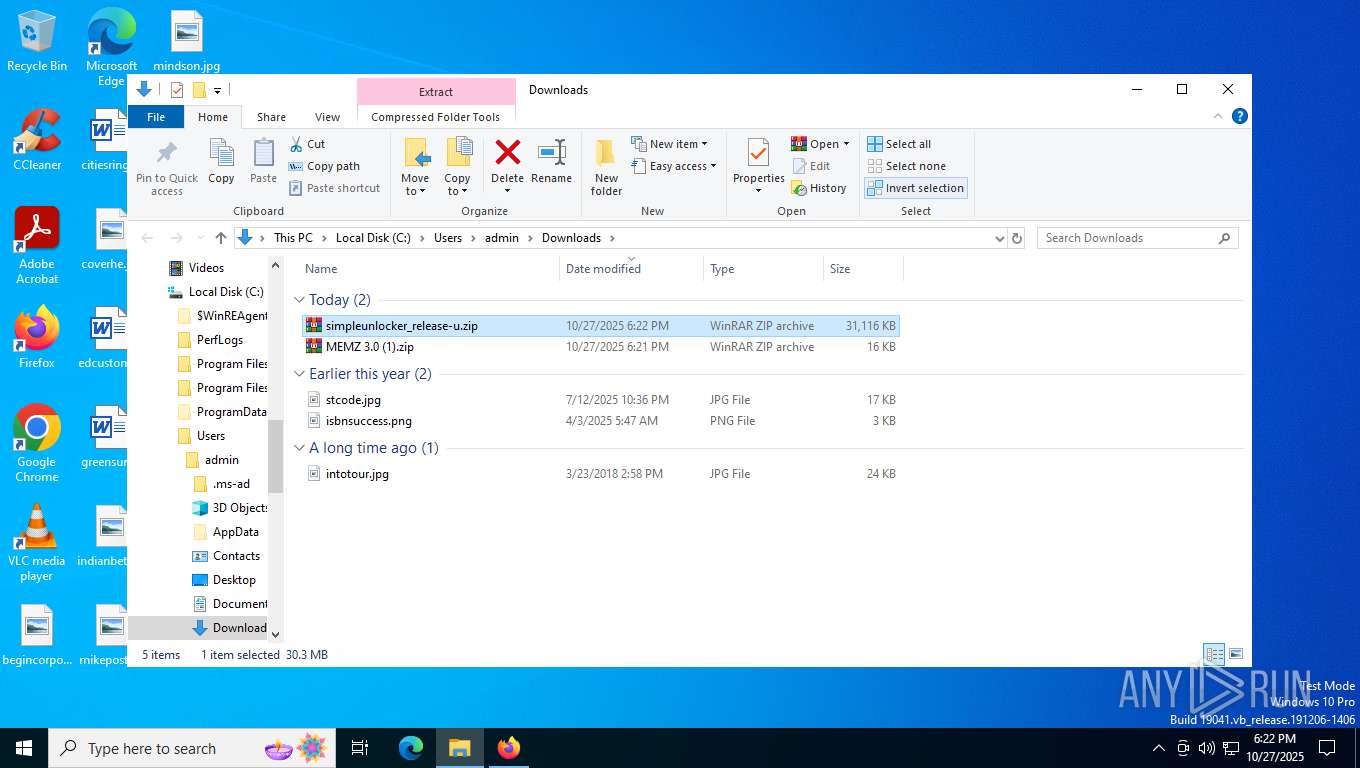
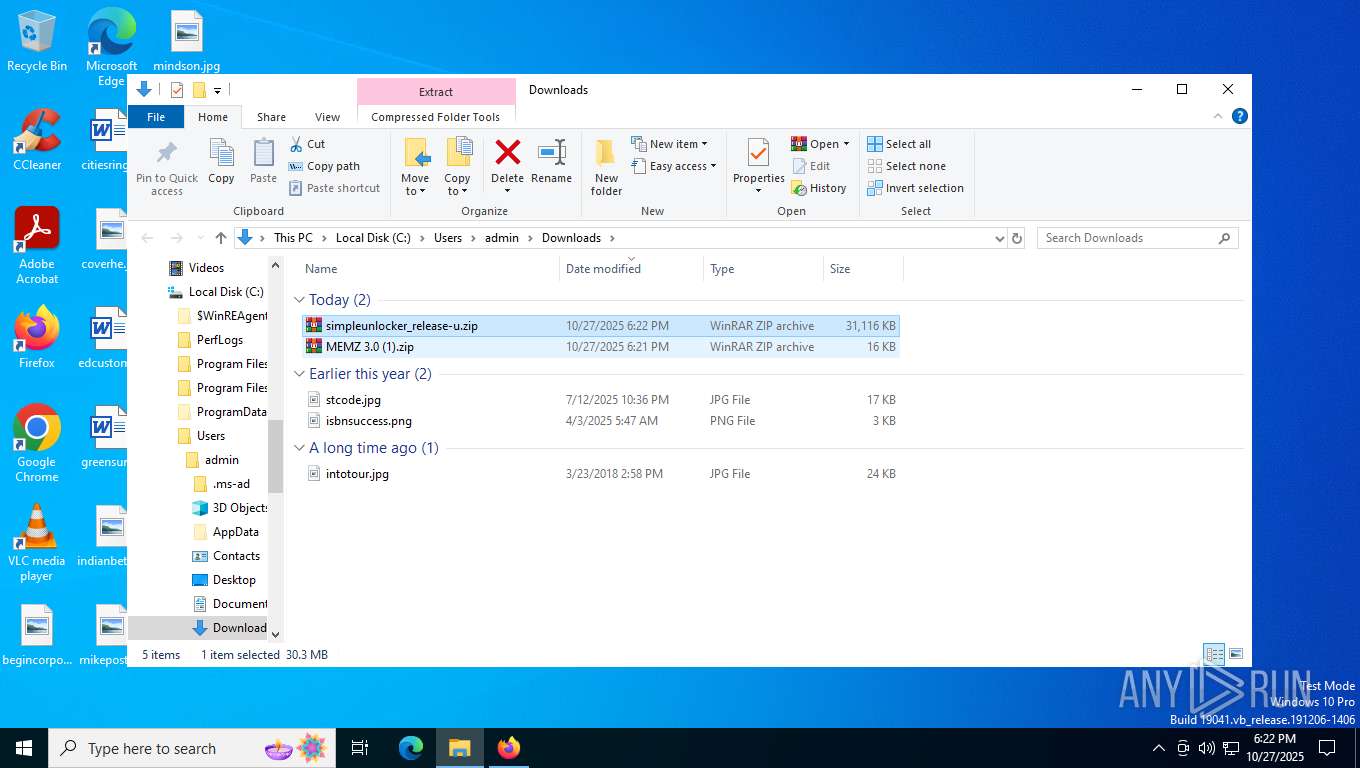
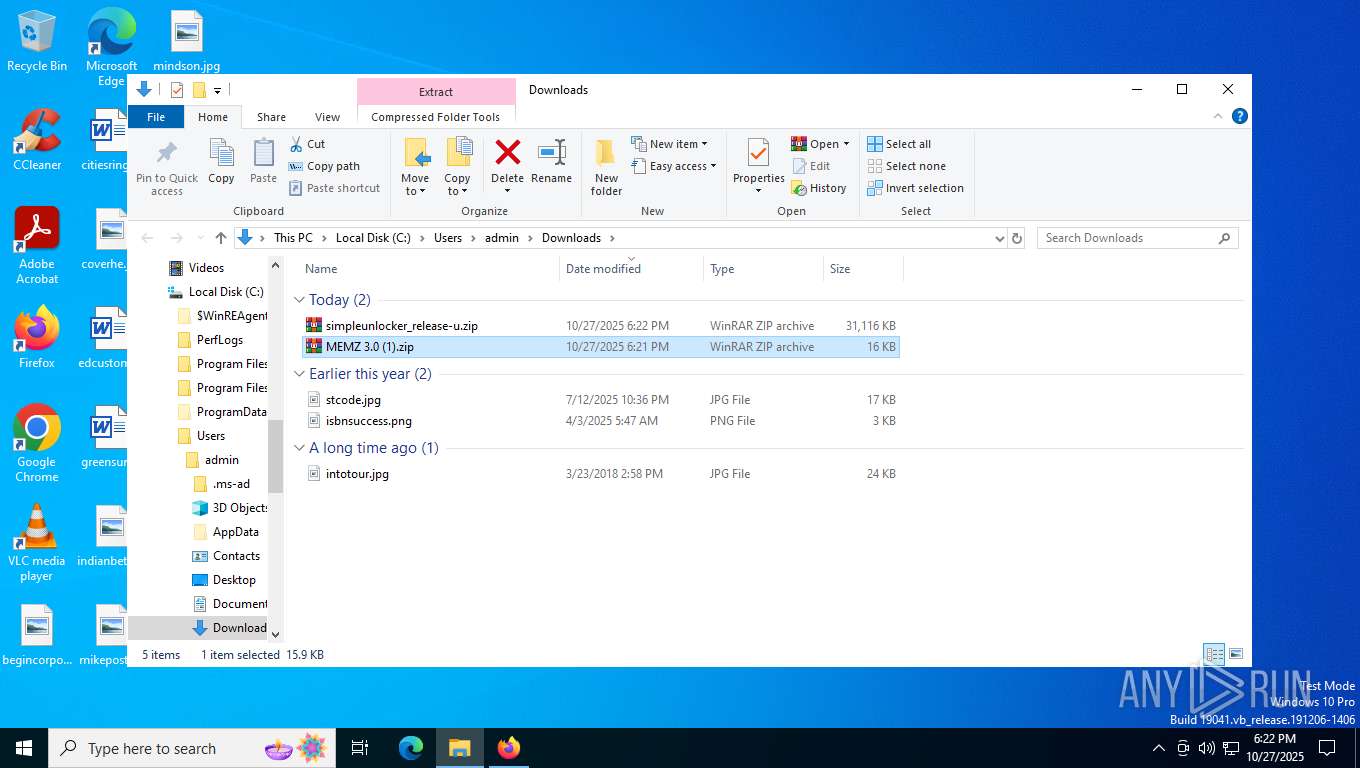
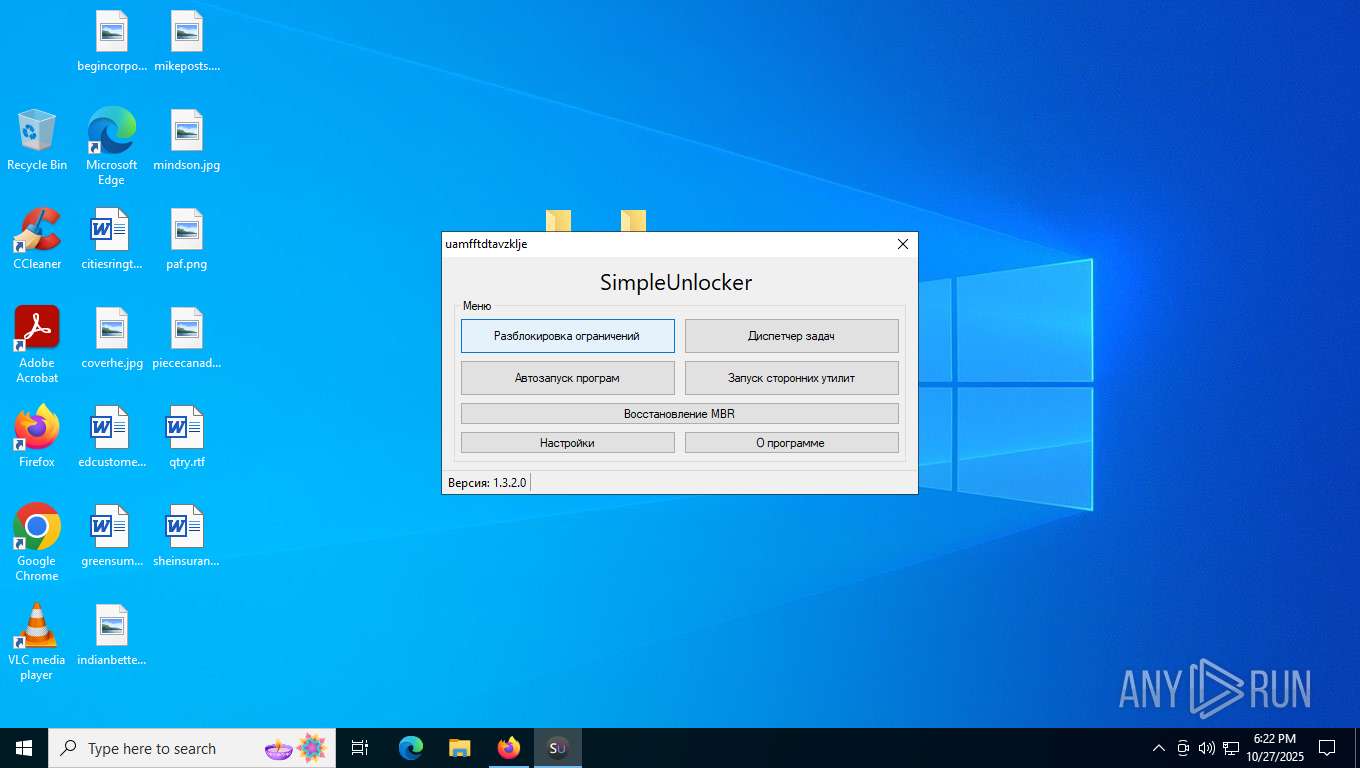
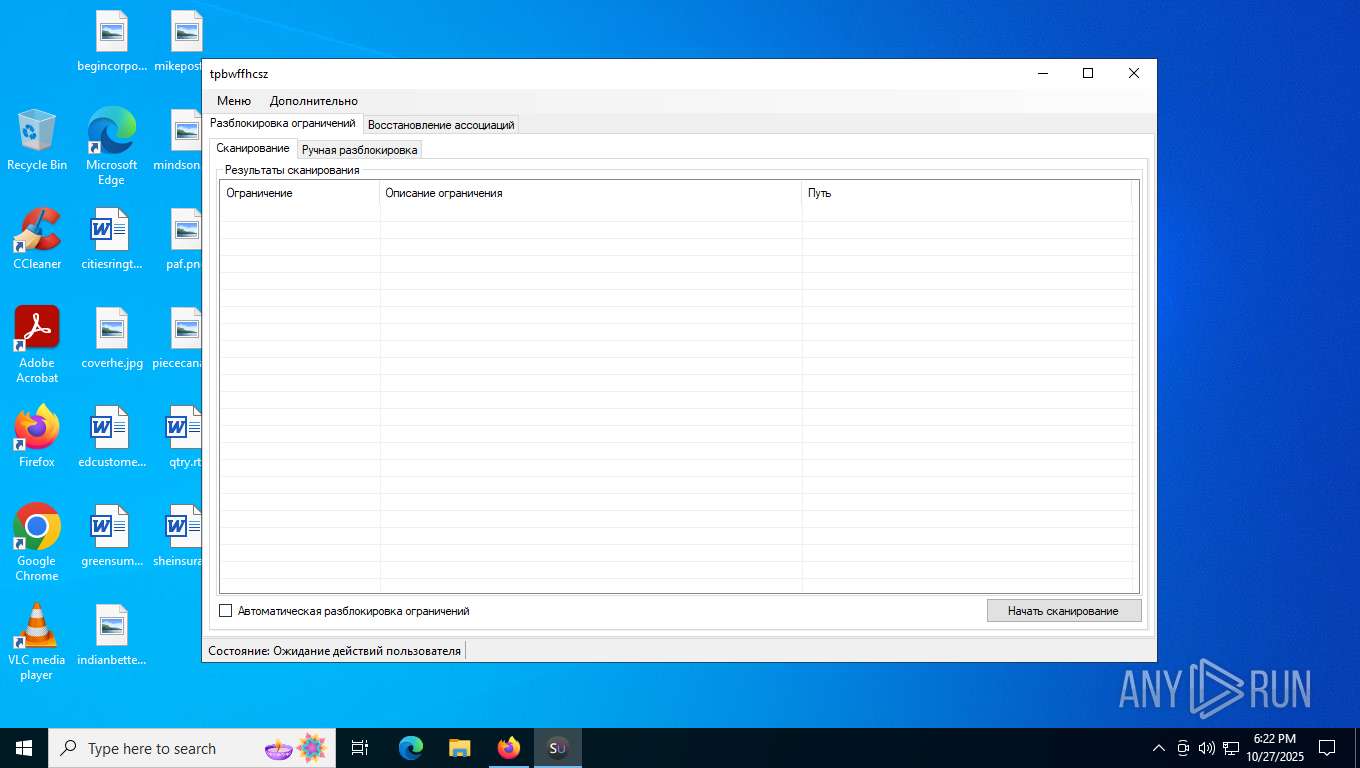
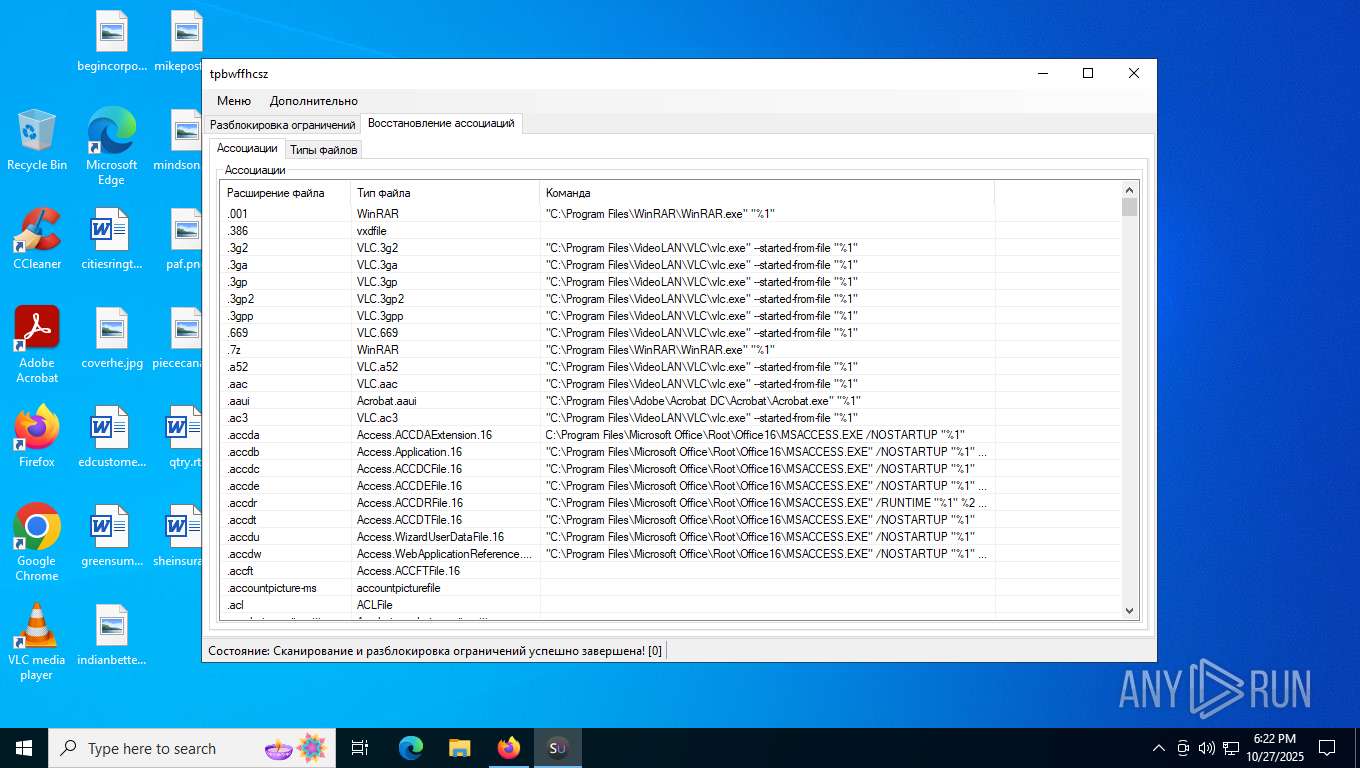
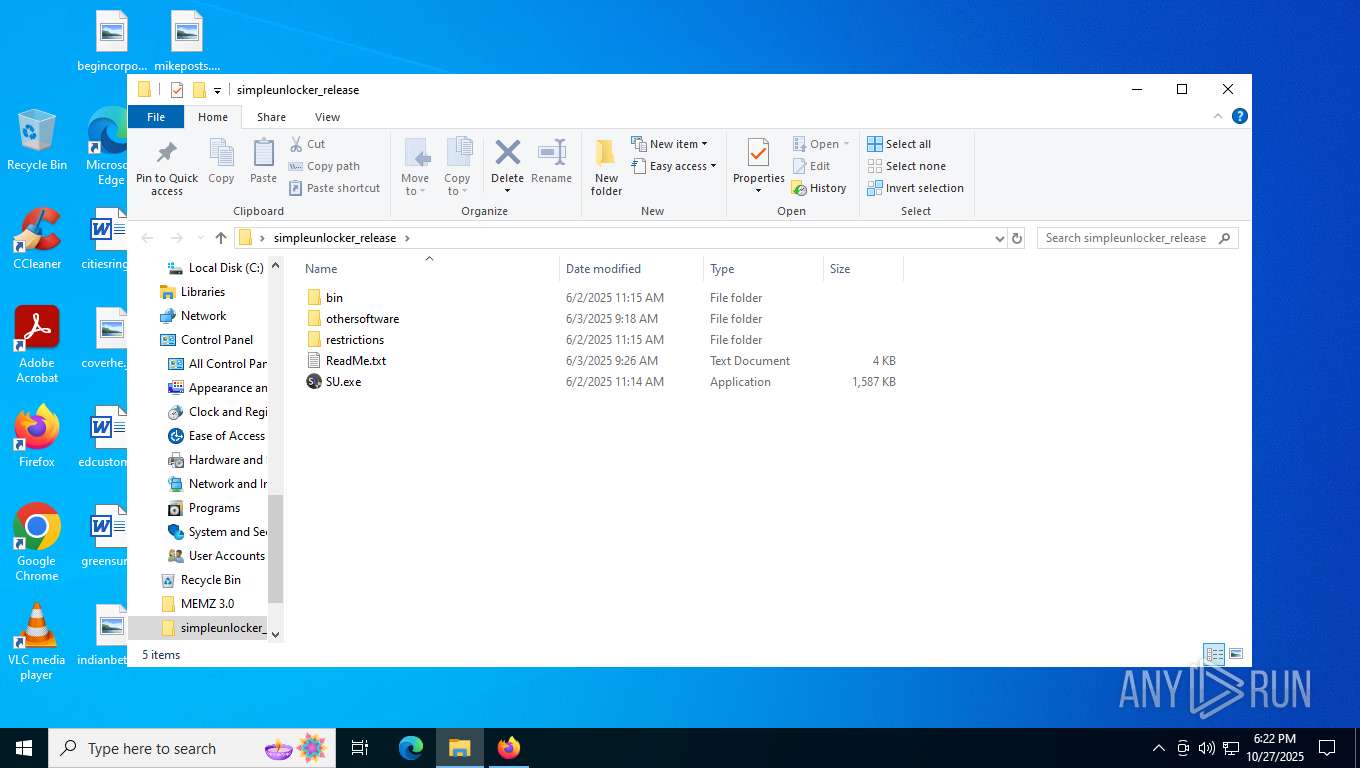
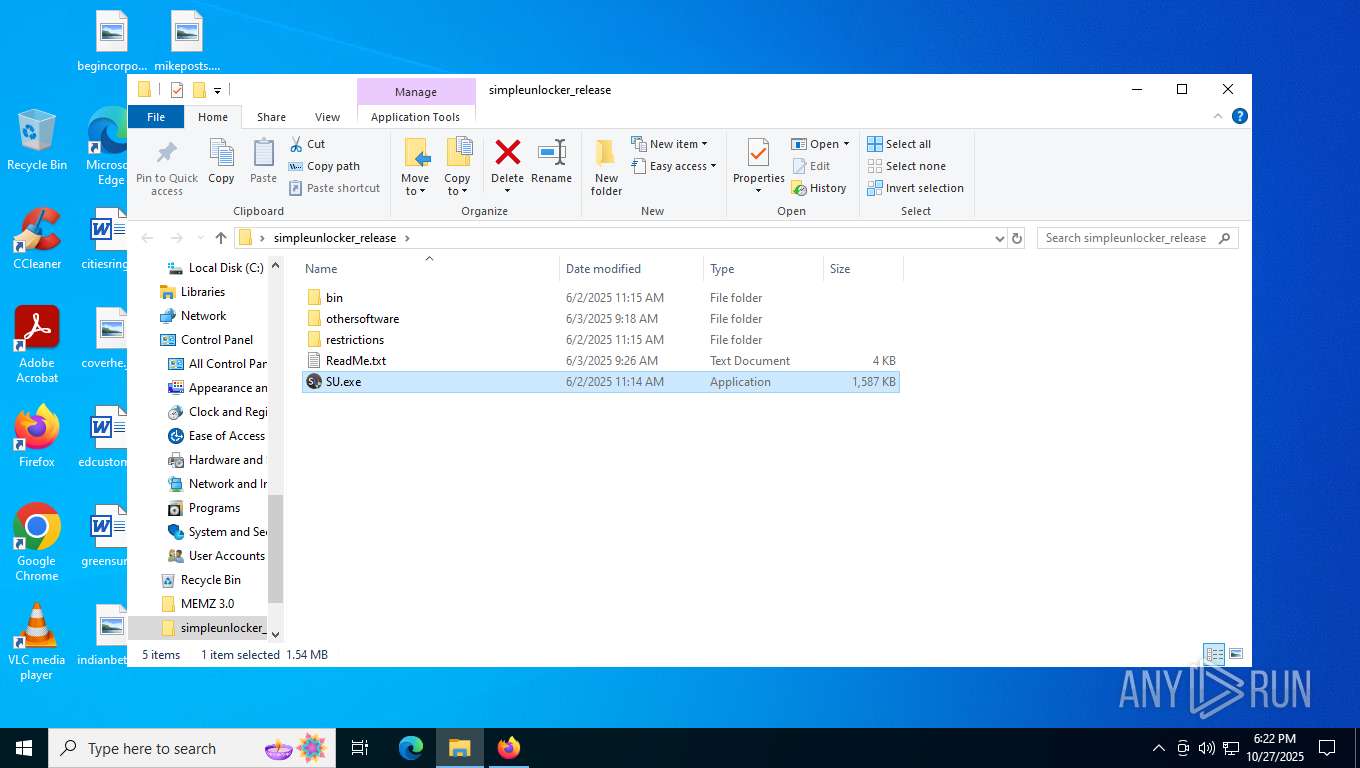
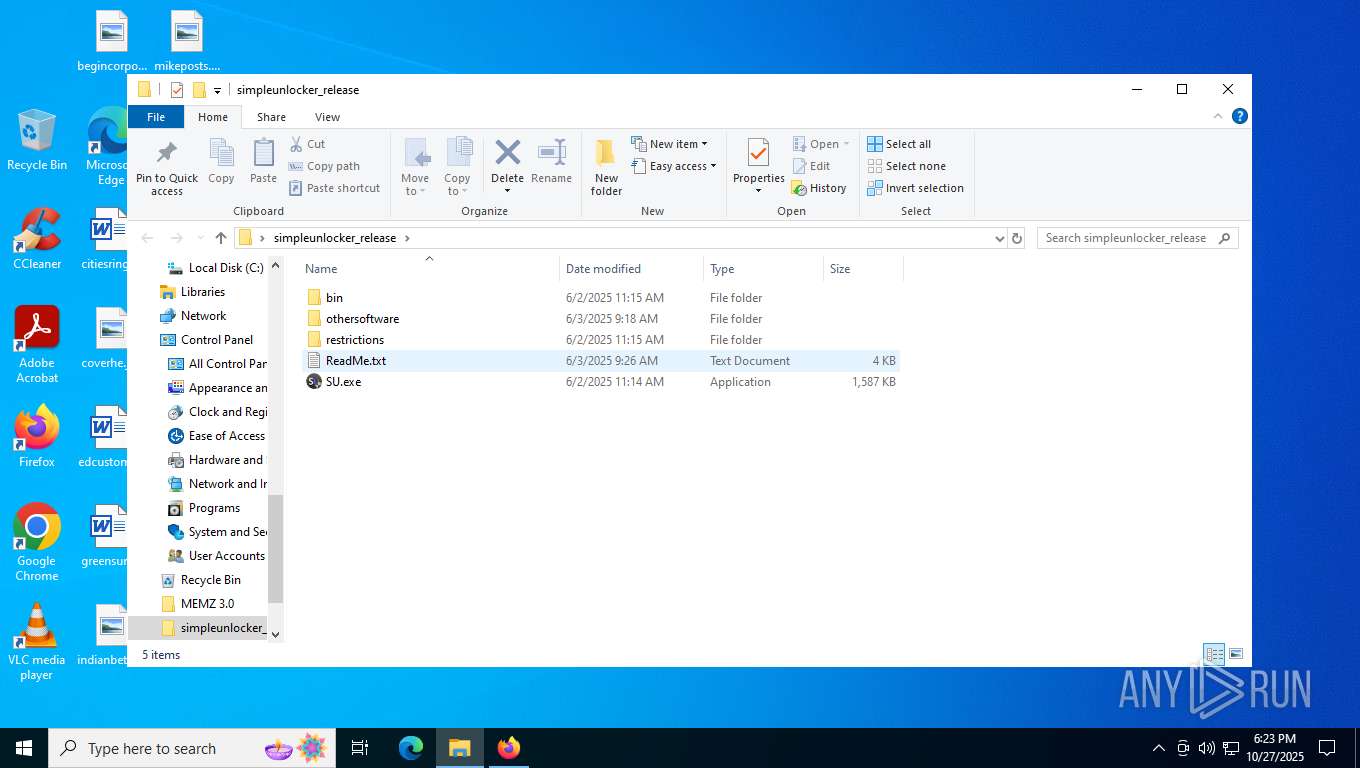
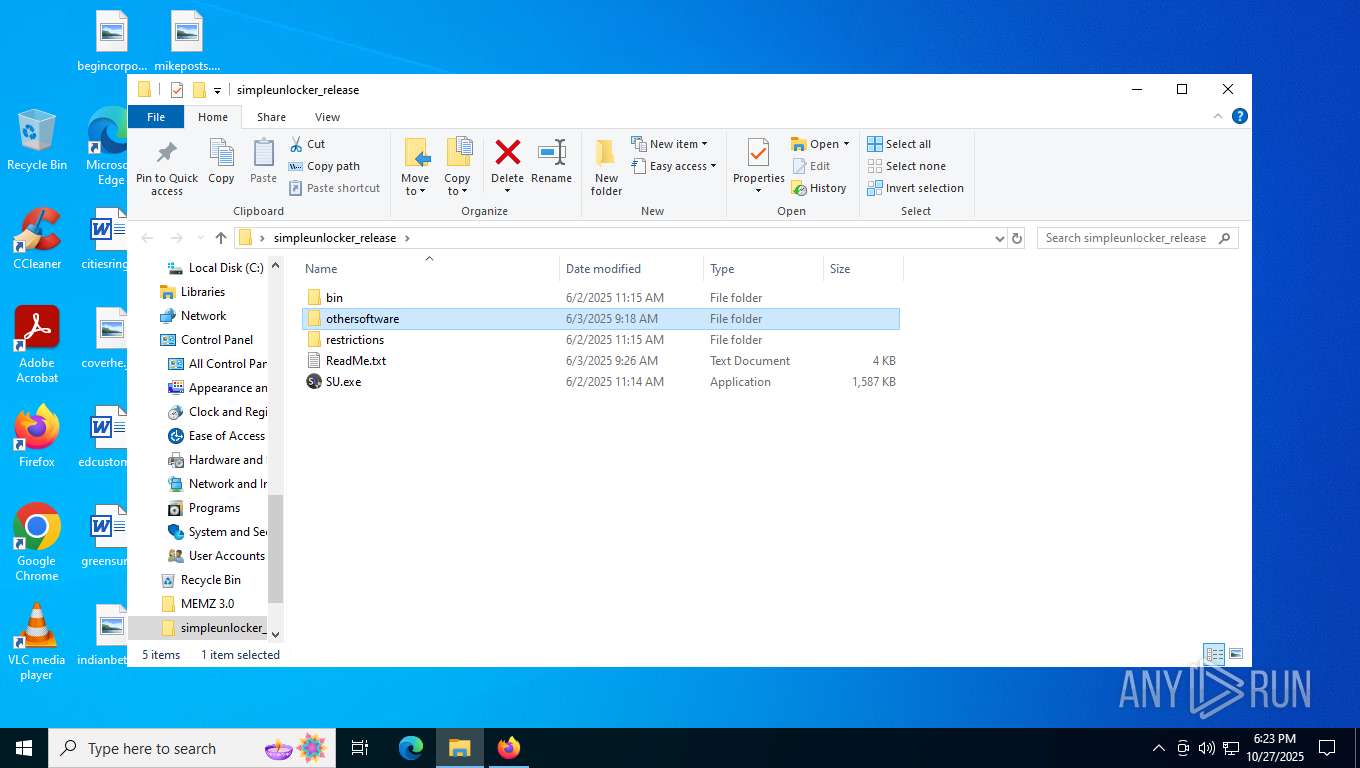
Manual execution by a user
- WinRAR.exe (PID: 8100)
- MEMZ.exe (PID: 1172)
- MEMZ.exe (PID: 8792)
- SU.exe (PID: 9136)
- SU.exe (PID: 8280)
- SU.exe (PID: 7268)
- SU.exe (PID: 7332)
- dfsgdfgsdhdfh.exe (PID: 9060)
- msedge.exe (PID: 2968)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8100)
The sample compiled with russian language support
- firefox.exe (PID: 7616)
- WinRAR.exe (PID: 8100)
The sample compiled with chinese language support
- WinRAR.exe (PID: 8100)
Launching a file from the Downloads directory
- firefox.exe (PID: 7616)
Reads the computer name
- MEMZ.exe (PID: 8792)
- SU.exe (PID: 8280)
- SU.exe (PID: 7332)
- dfsgdfgsdhdfh.exe (PID: 9060)
- identity_helper.exe (PID: 8268)
- MEMZ.exe (PID: 9052)
- MEMZ.exe (PID: 1500)
- dfsgdfgsdhdfh.exe (PID: 9160)
- dfsgdfgsdhdfh.exe (PID: 5388)
Process checks computer location settings
- MEMZ.exe (PID: 8792)
- MEMZ.exe (PID: 9052)
- dfsgdfgsdhdfh.exe (PID: 9060)
The sample compiled with german language support
- WinRAR.exe (PID: 8100)
Reads security settings of Internet Explorer
- notepad.exe (PID: 9044)
- calc.exe (PID: 7796)
- OpenWith.exe (PID: 4556)
Reads the machine GUID from the registry
- SU.exe (PID: 8280)
- SU.exe (PID: 7332)
- MEMZ.exe (PID: 9052)
- MEMZ.exe (PID: 1500)
- dfsgdfgsdhdfh.exe (PID: 9060)
Reads Environment values
- SU.exe (PID: 8280)
- SU.exe (PID: 7332)
- identity_helper.exe (PID: 8268)
Disables trace logs
- SU.exe (PID: 8280)
- SU.exe (PID: 7332)
Checks proxy server information
- SU.exe (PID: 8280)
- slui.exe (PID: 8564)
- SU.exe (PID: 7332)
Reads the software policy settings
- SU.exe (PID: 8280)
- SU.exe (PID: 7332)
- slui.exe (PID: 8564)
- dfsgdfgsdhdfh.exe (PID: 9060)
Reads CPU info
- SU.exe (PID: 7332)
Reads the time zone
- SU.exe (PID: 7332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
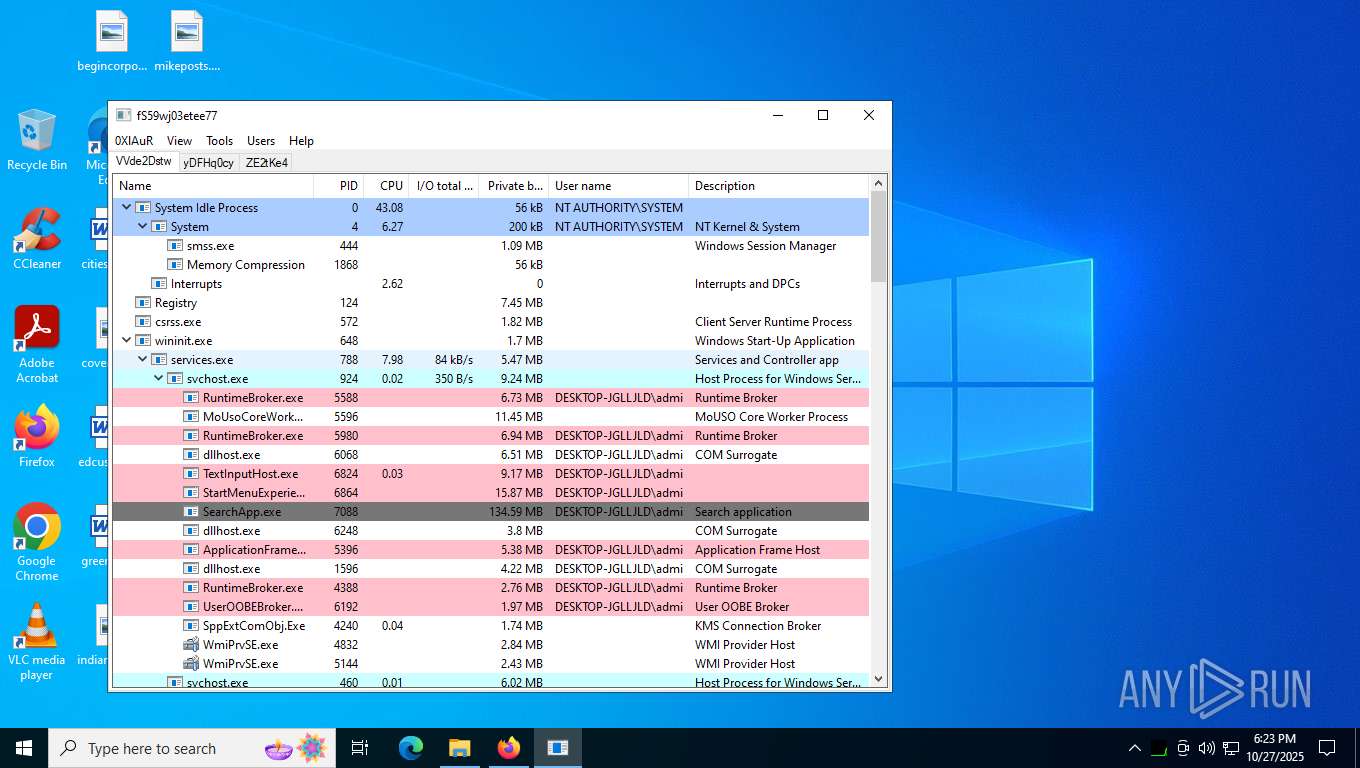
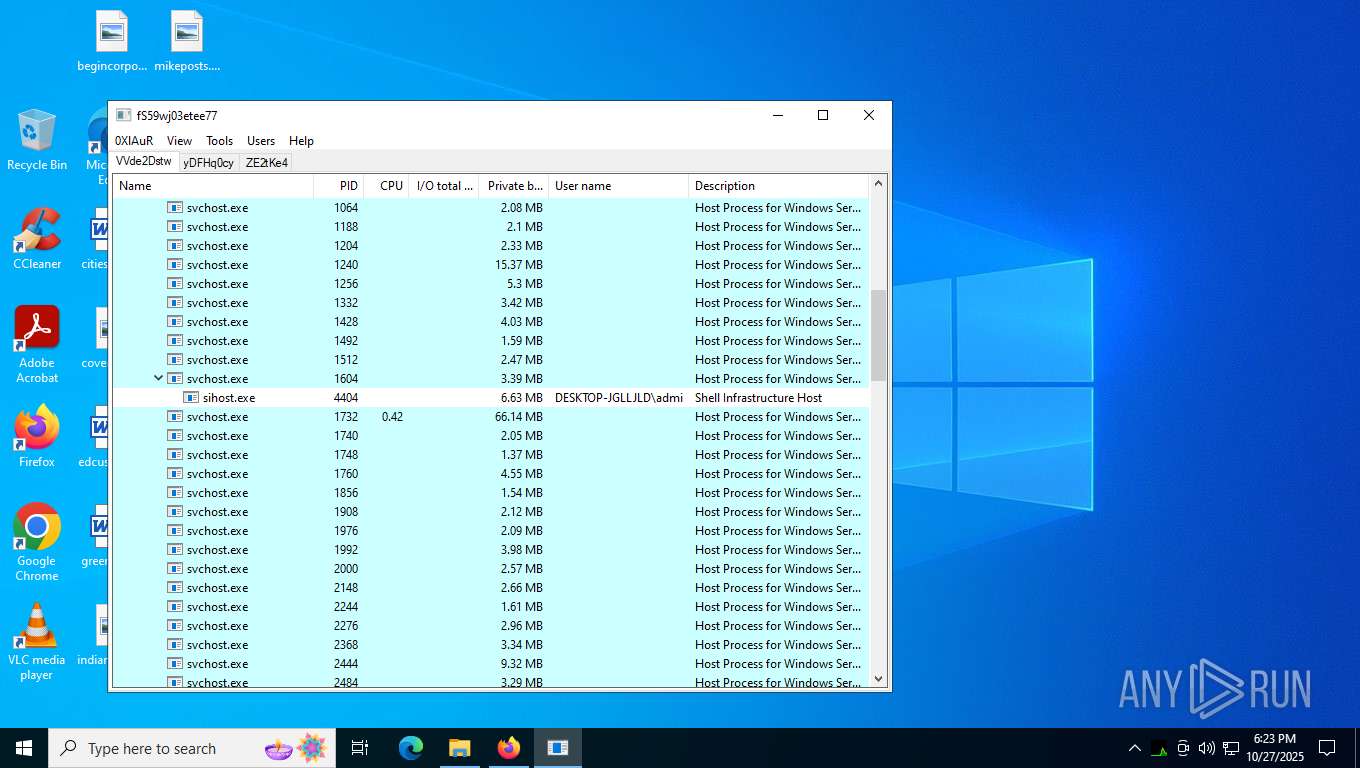
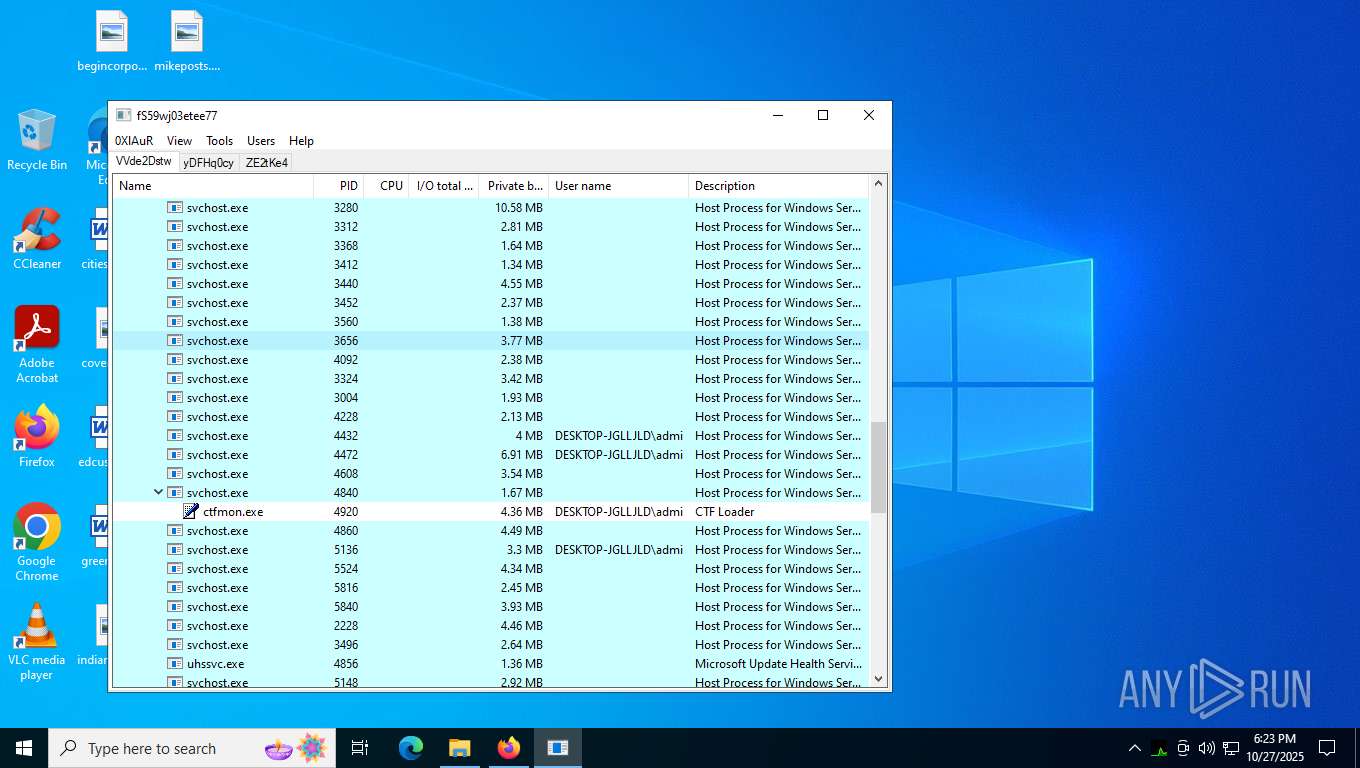
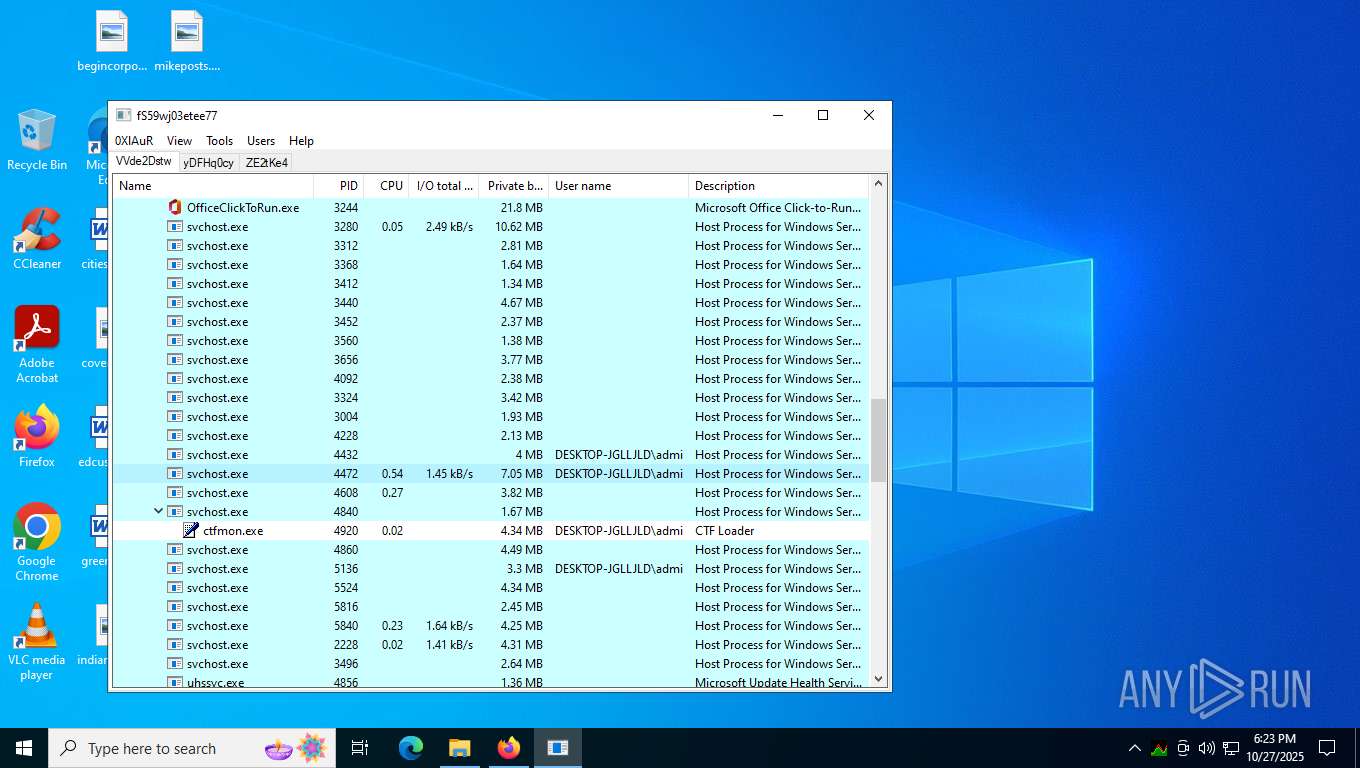
Total processes
203
Monitored processes
60
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
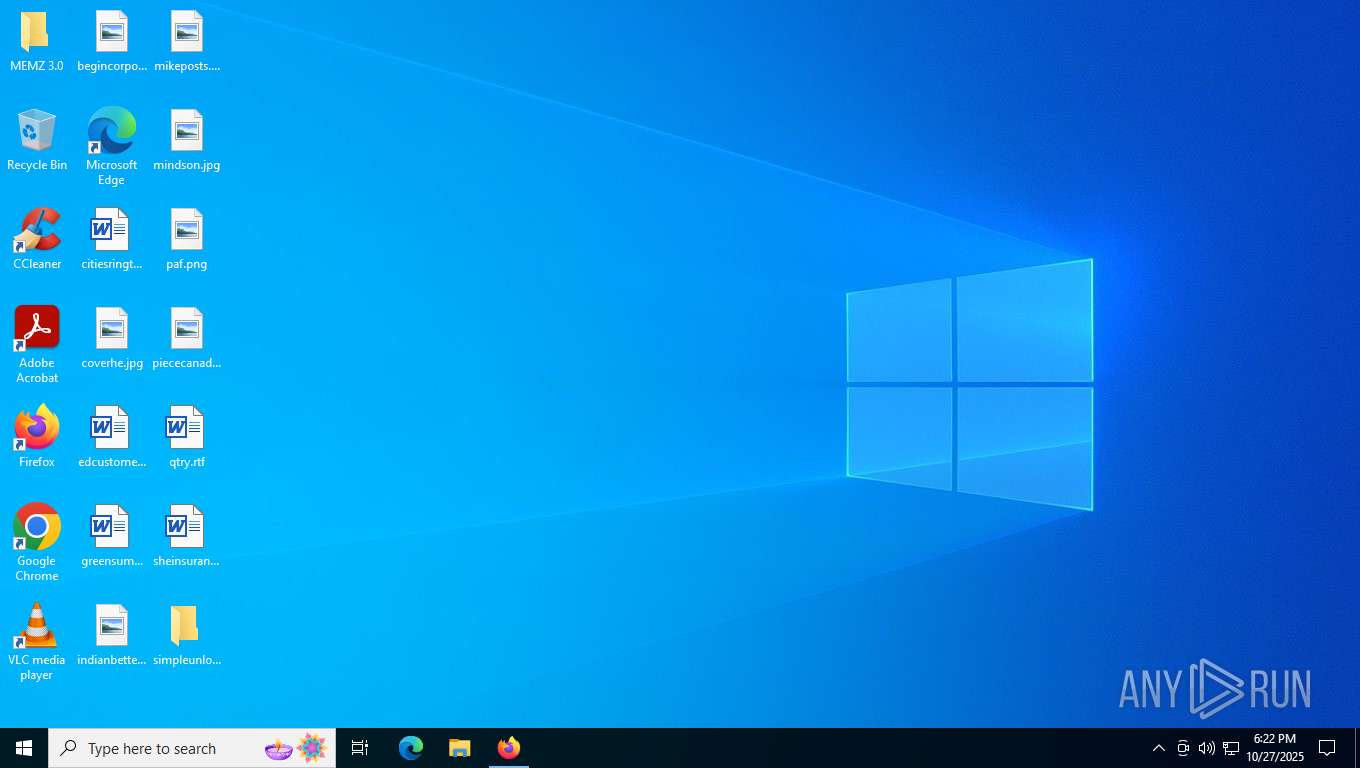
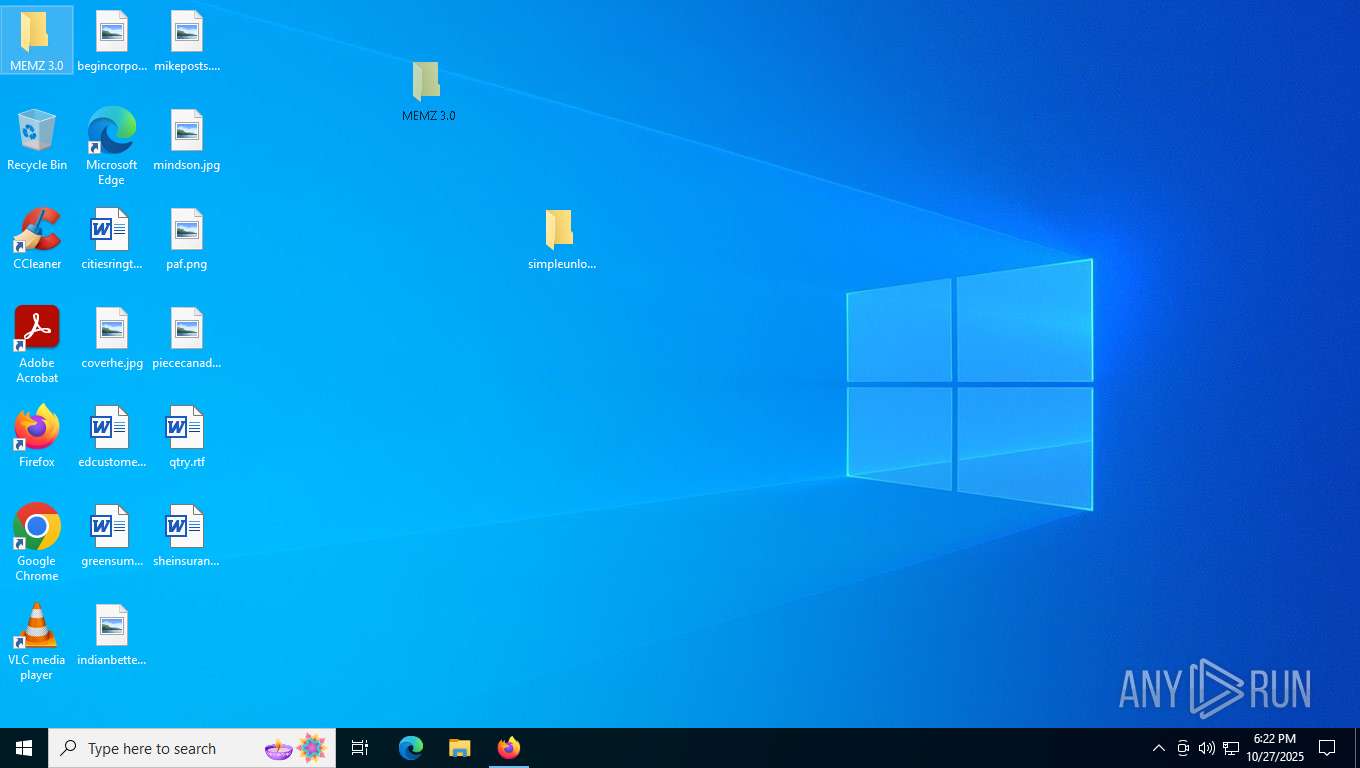
| 1172 | "C:\Users\admin\Desktop\MEMZ 3.0\MEMZ.exe" | C:\Users\admin\Desktop\MEMZ 3.0\MEMZ.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1500 | "C:\Users\admin\Desktop\MEMZ 3.0\MEMZ.exe" /watchdog | C:\Users\admin\Desktop\MEMZ 3.0\MEMZ.exe | MEMZ.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 2276 -prefsLen 39191 -prefMapHandle 4152 -prefMapSize 273045 -jsInitHandle 4140 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4160 -initialChannelId {22503999-d18d-4f45-b7f5-377752a3d820} -parentPid 7616 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7616" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 11 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4216,i,212488927051480104,8082544972910868277,262144 --variations-seed-version --mojo-platform-channel-handle=4204 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=4896,i,212488927051480104,8082544972910868277,262144 --variations-seed-version --mojo-platform-channel-handle=5176 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2276 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2688 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6540,i,212488927051480104,8082544972910868277,262144 --variations-seed-version --mojo-platform-channel-handle=6000 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4880 -prefsLen 39191 -prefMapHandle 4784 -prefMapSize 273045 -jsInitHandle 5052 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4496 -initialChannelId {27ce65e6-5b87-4411-9583-caad391b1935} -parentPid 7616 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7616" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
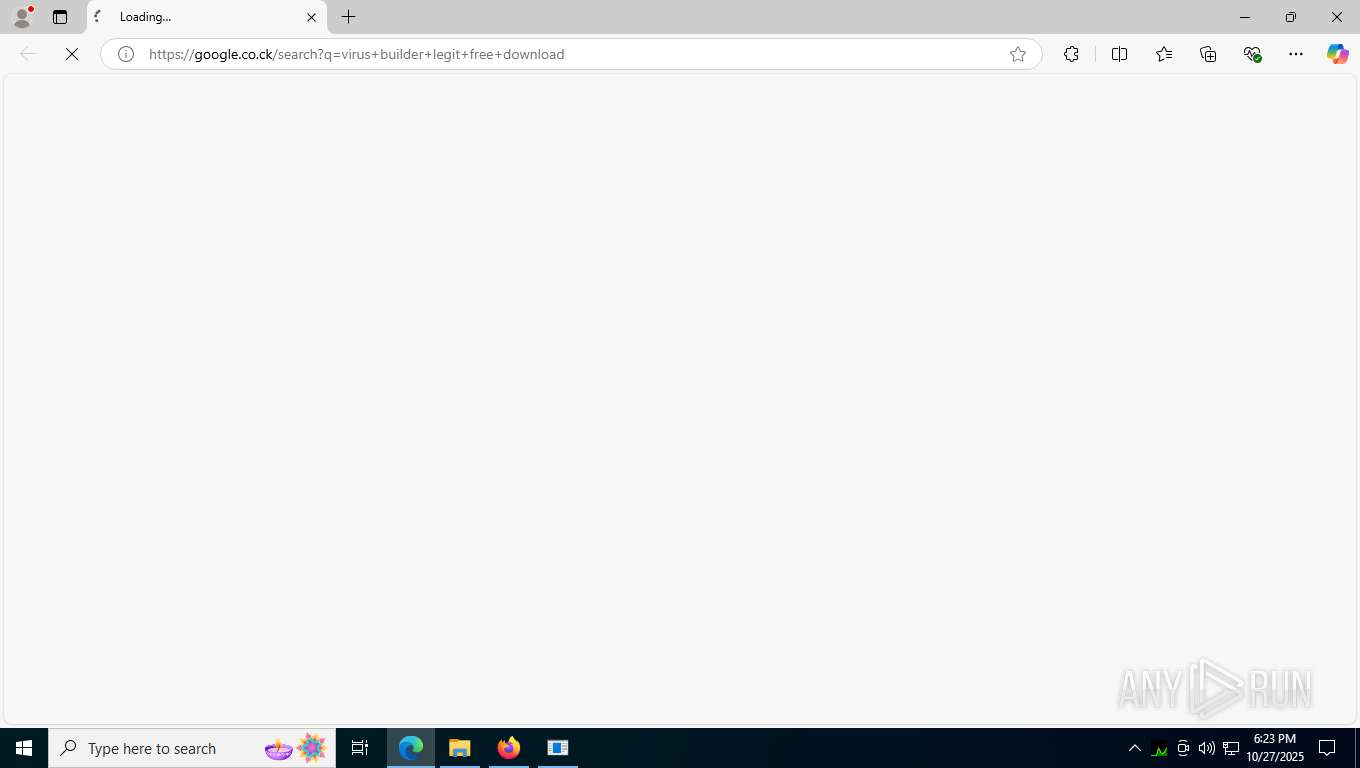
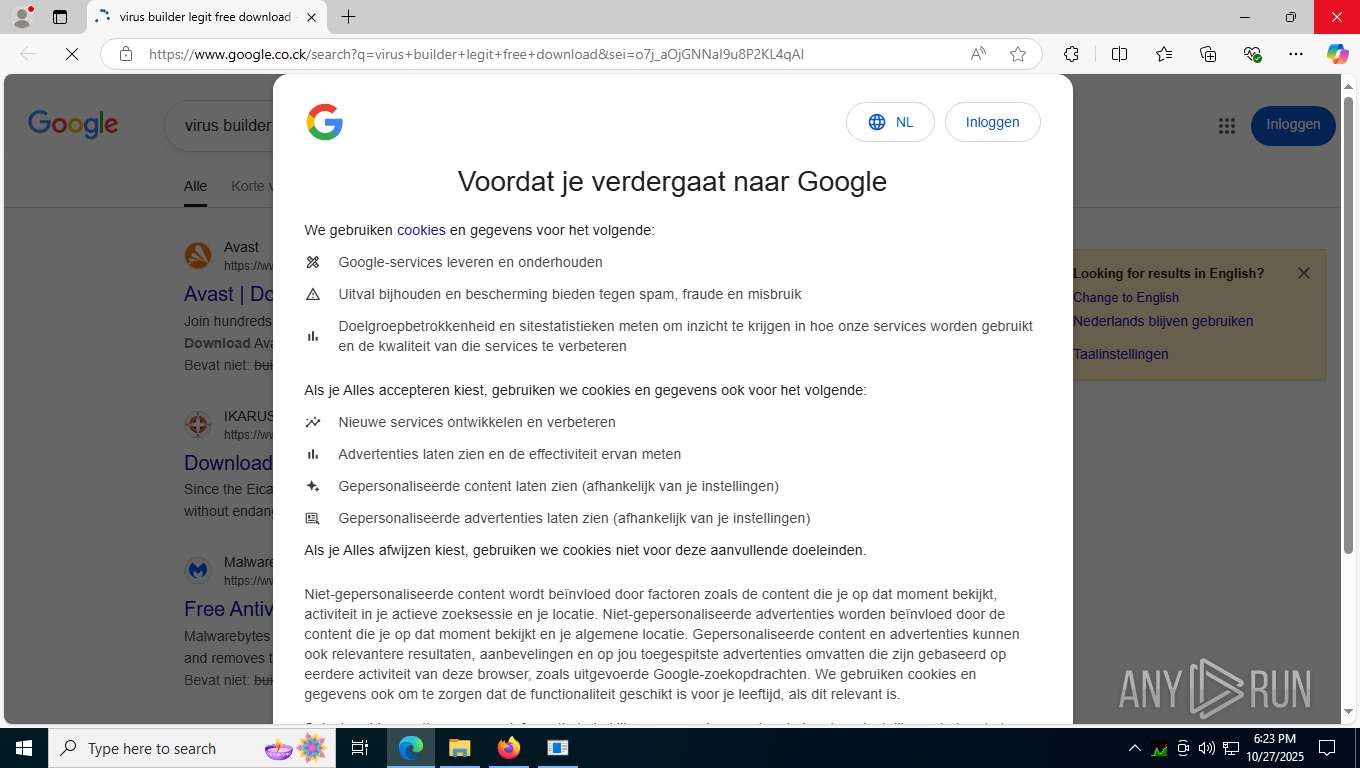
| 2968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --disable-quic --flag-switches-end --do-not-de-elevate --single-argument https://google.co.ck/search?q=virus+builder+legit+free+download | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2264,i,212488927051480104,8082544972910868277,262144 --variations-seed-version --mojo-platform-channel-handle=2504 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
18 734
Read events
18 677
Write events
44
Delete events
13
Modification events
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 11 |
Value: | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 10 |
Value: | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 9 |
Value: | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 8 |
Value: | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 7 |
Value: | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 6 |
Value: | |||
Executable files
128
Suspicious files
702
Text files
218
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7616 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\places.sqlite-wal | binary | |
MD5:55E8DCFA67FAC06E7E00DCF0FE42BDD9 | SHA256:88E65DBED752B8127791C448836591B723F359DEC15E84756A9271DDA4DEDDE6 | |||
| 7616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7616 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.discovery_stream.json.tmp | binary | |
MD5:C06FD646C28265AC2F292ED06003CCC2 | SHA256:3121913917EA1CEC35F18CB52536B7FF108303DE4AC7960F1D368C34F6A2867F | |||
| 7616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:89FDAD2BB592C8A08C49FC82E8E15E67 | SHA256:5C6D6A9AC3ABA09498787939D29135A6386854181E23F9F5C9244794CD8F1498 | |||
| 7616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:04F6805811894B713A32929F7F683509 | SHA256:1DC1231836DE47526CBAA36F00750520B81B72C6E4BF64B086EC42AA5F55CE0C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
146
DNS requests
199
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7616 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7616 | firefox.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
7616 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/s/wr3/25s | unknown | — | — | whitelisted |
7616 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7616 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7616 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7616 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7616 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7616 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7616 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5488 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2328 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7616 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
7616 | firefox.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
7616 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7616 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7616 | firefox.exe | 172.64.149.23:80 | ocsp.sectigo.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
content-signature-chains.prod.autograph.services.mozaws.net |
| whitelisted |
github.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Generic Protocol Command Decode | SURICATA HTTP request field missing colon |
— | — | Generic Protocol Command Decode | SURICATA HTTP URI terminated by non-compliant character |
— | — | Generic Protocol Command Decode | SURICATA HTTP request header invalid |
— | — | Generic Protocol Command Decode | SURICATA HTTP METHOD terminated by non-compliant character |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
— | — | Generic Protocol Command Decode | SURICATA HTTP request field missing colon |