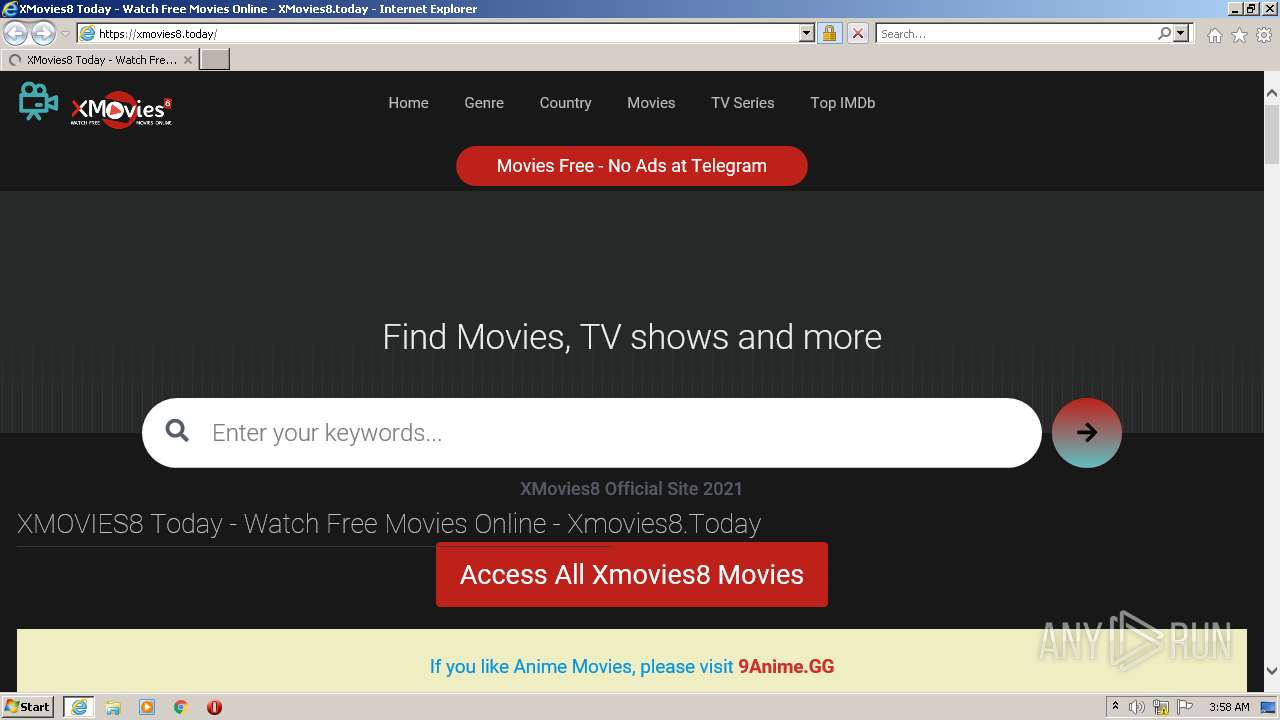
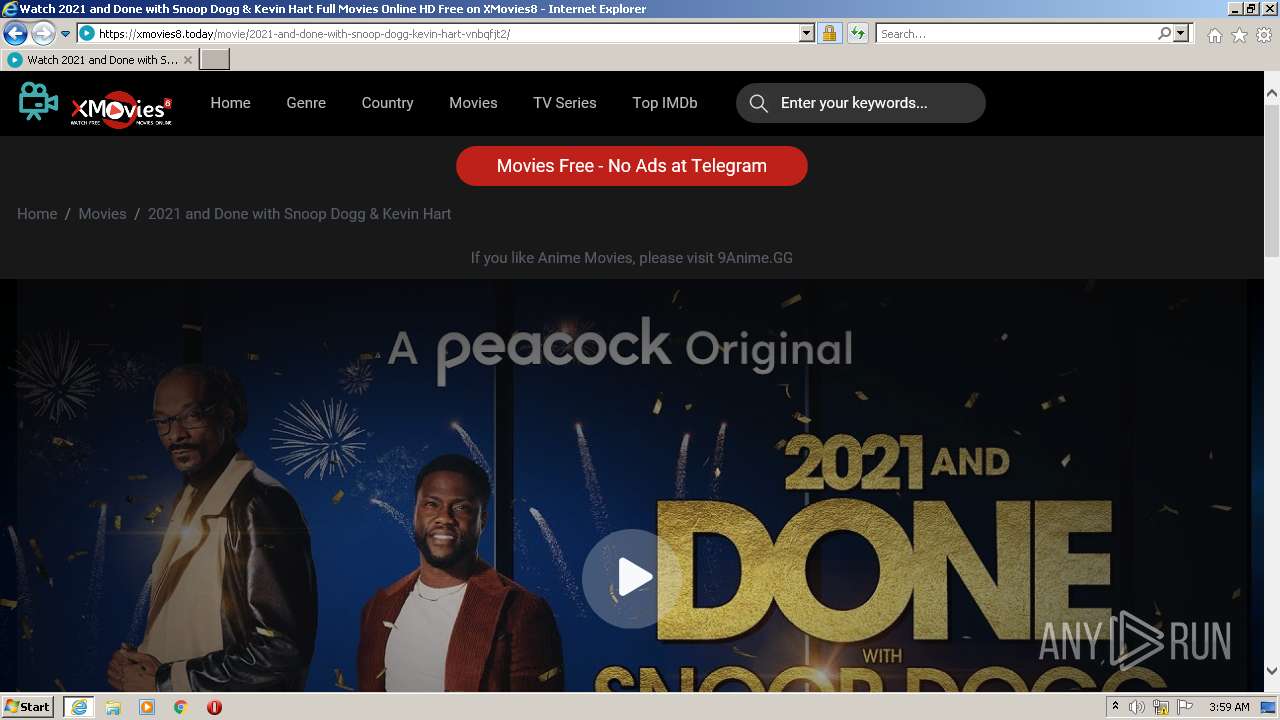
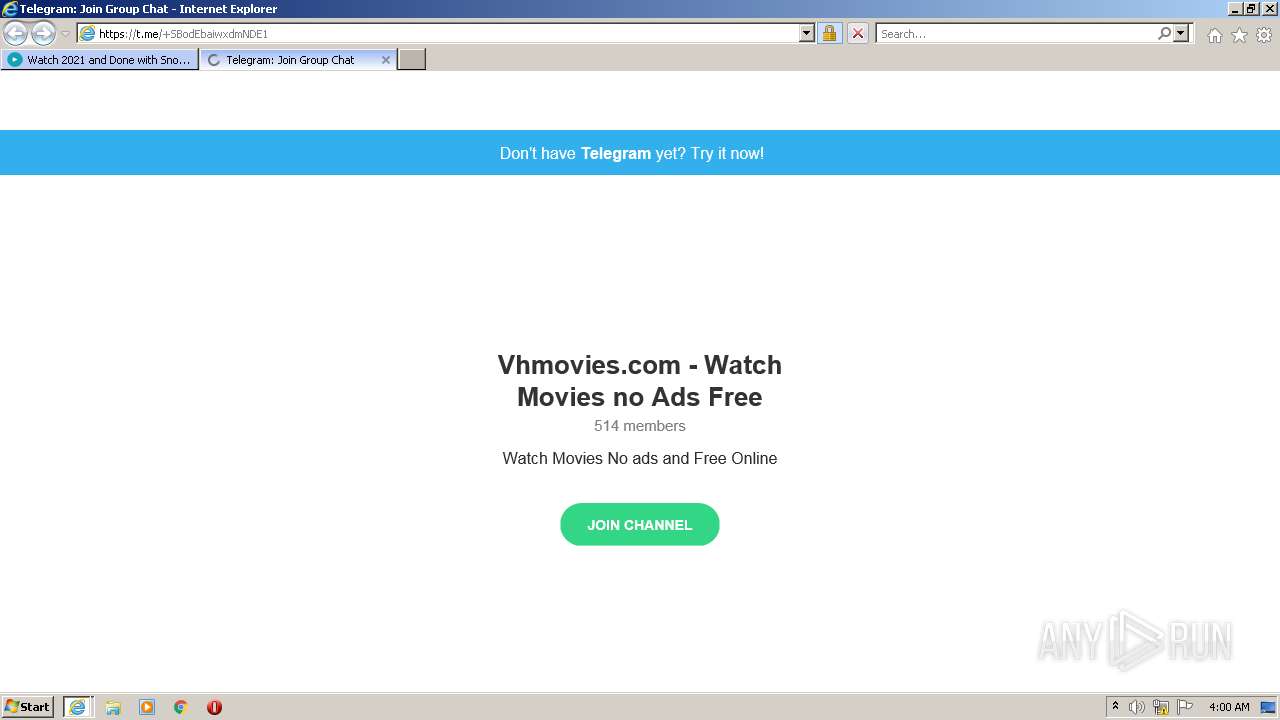
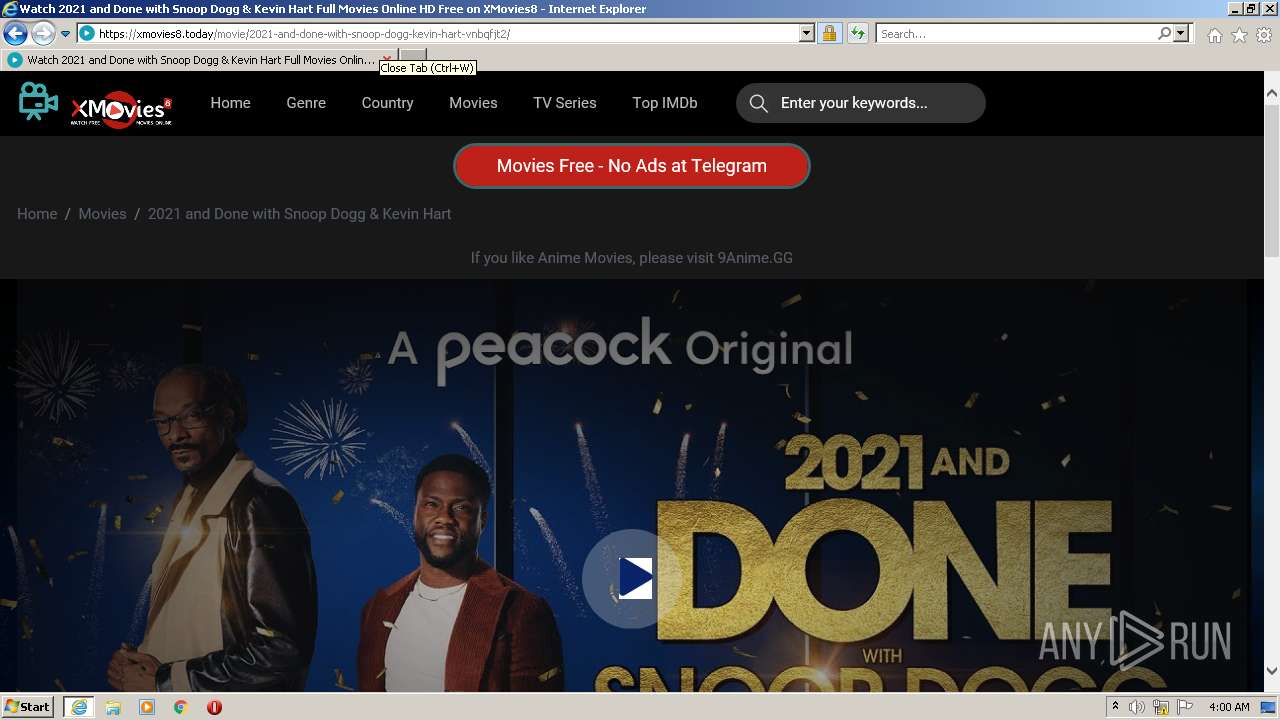
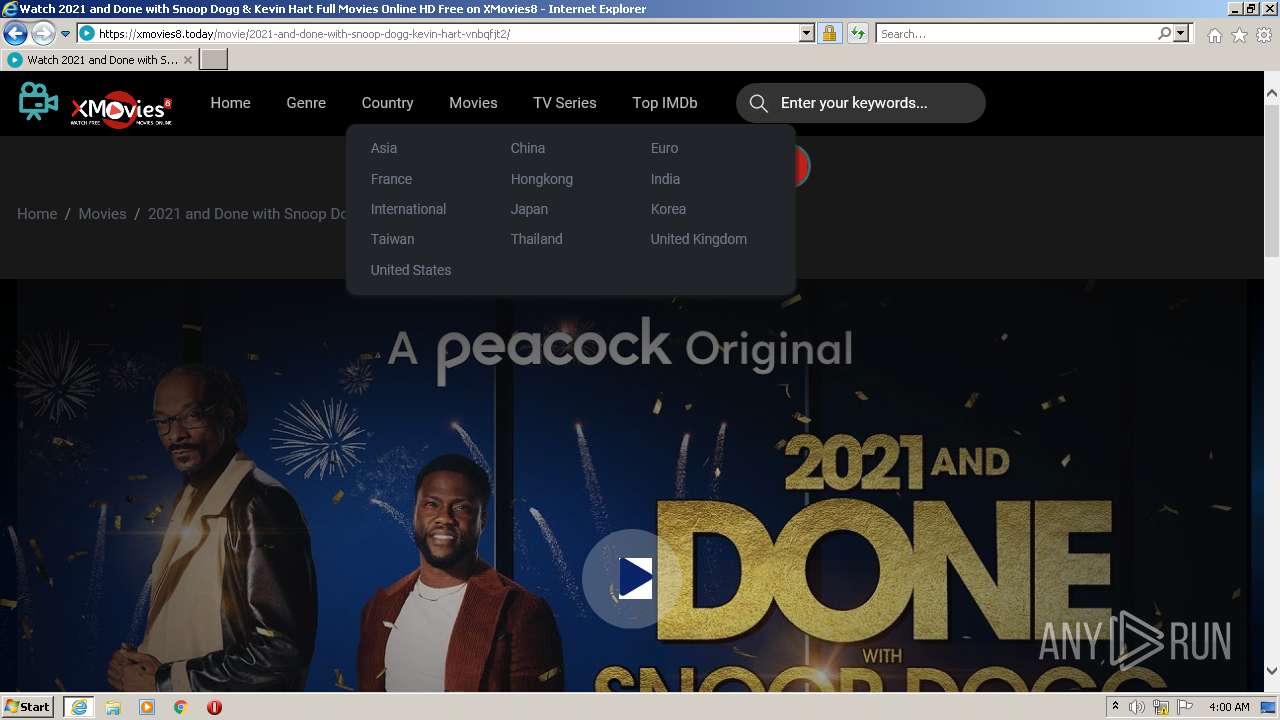
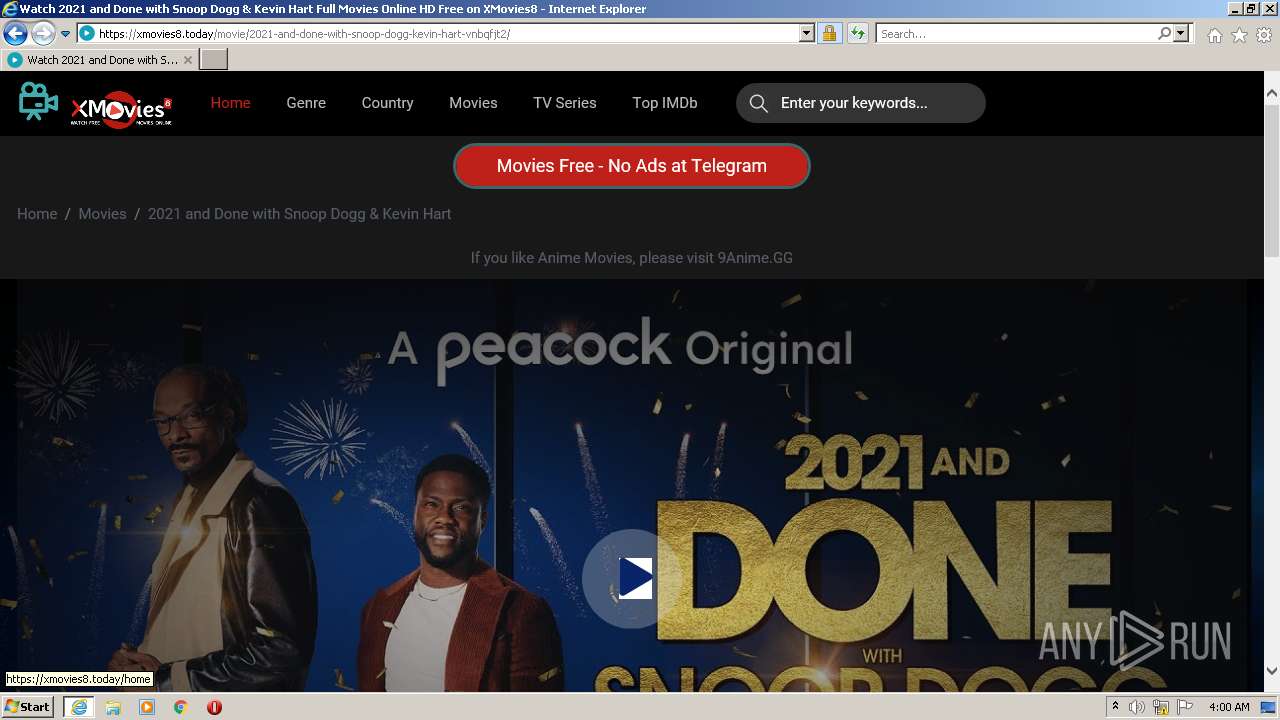
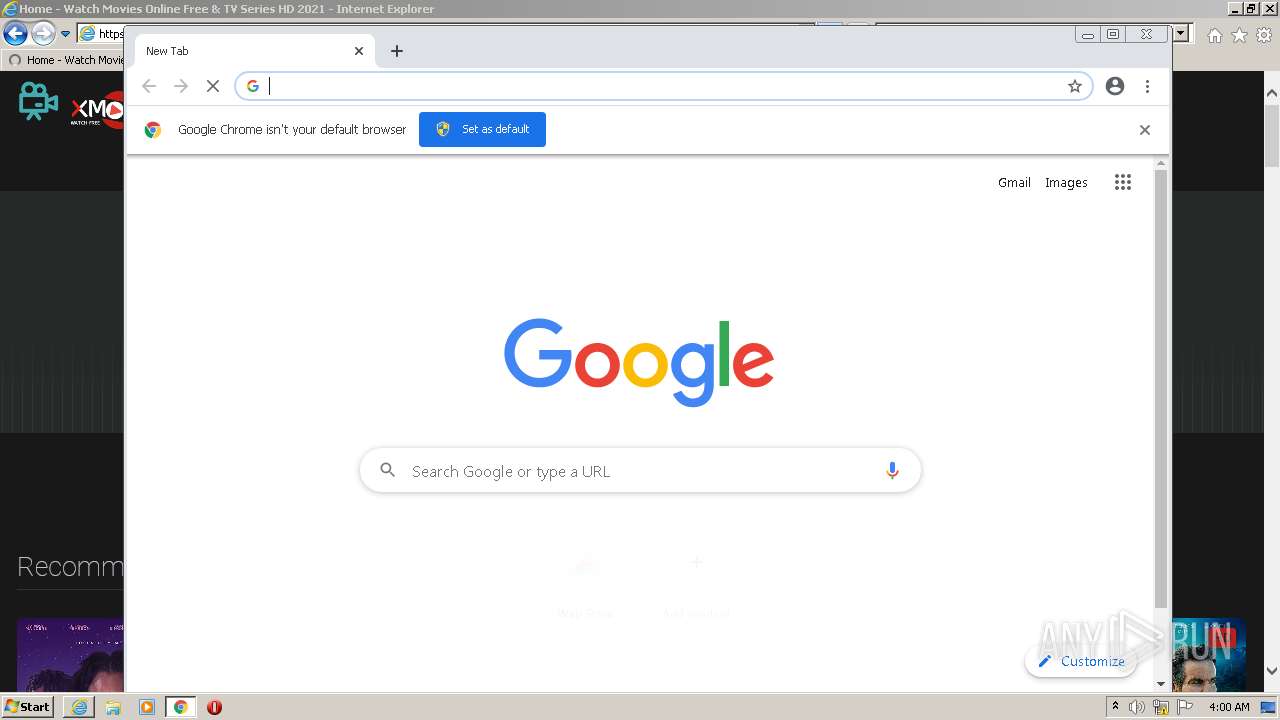
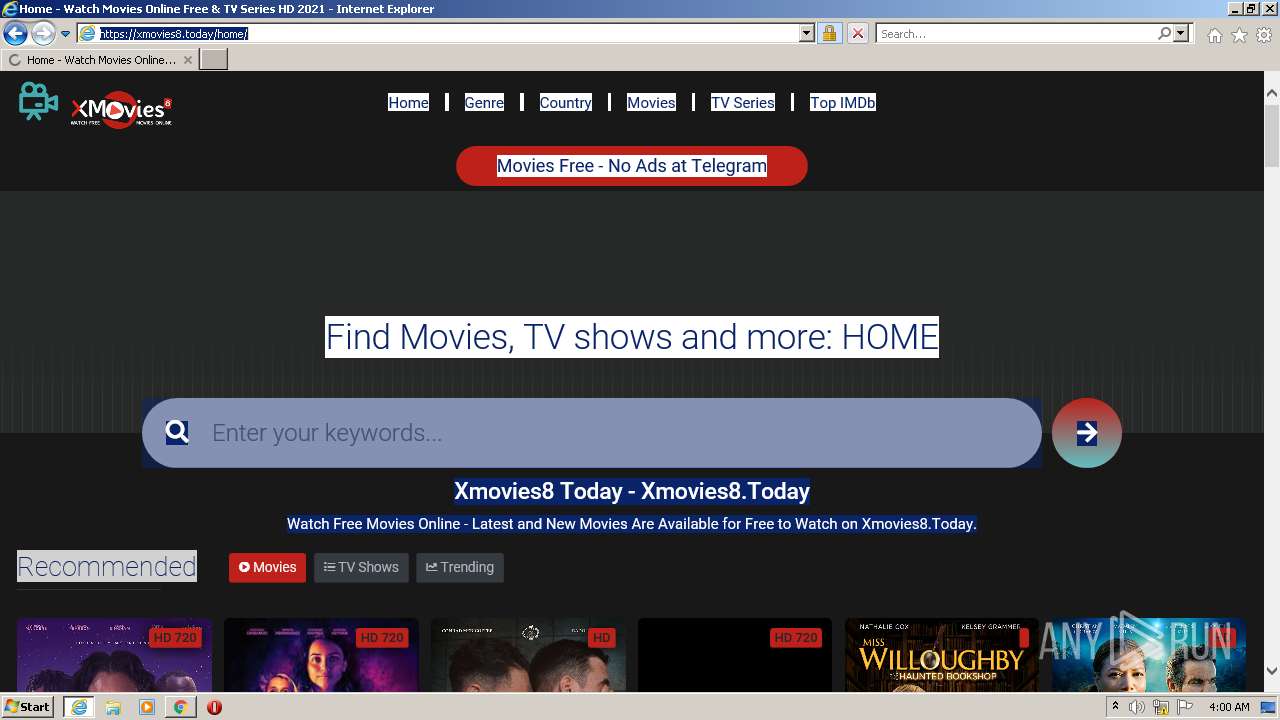
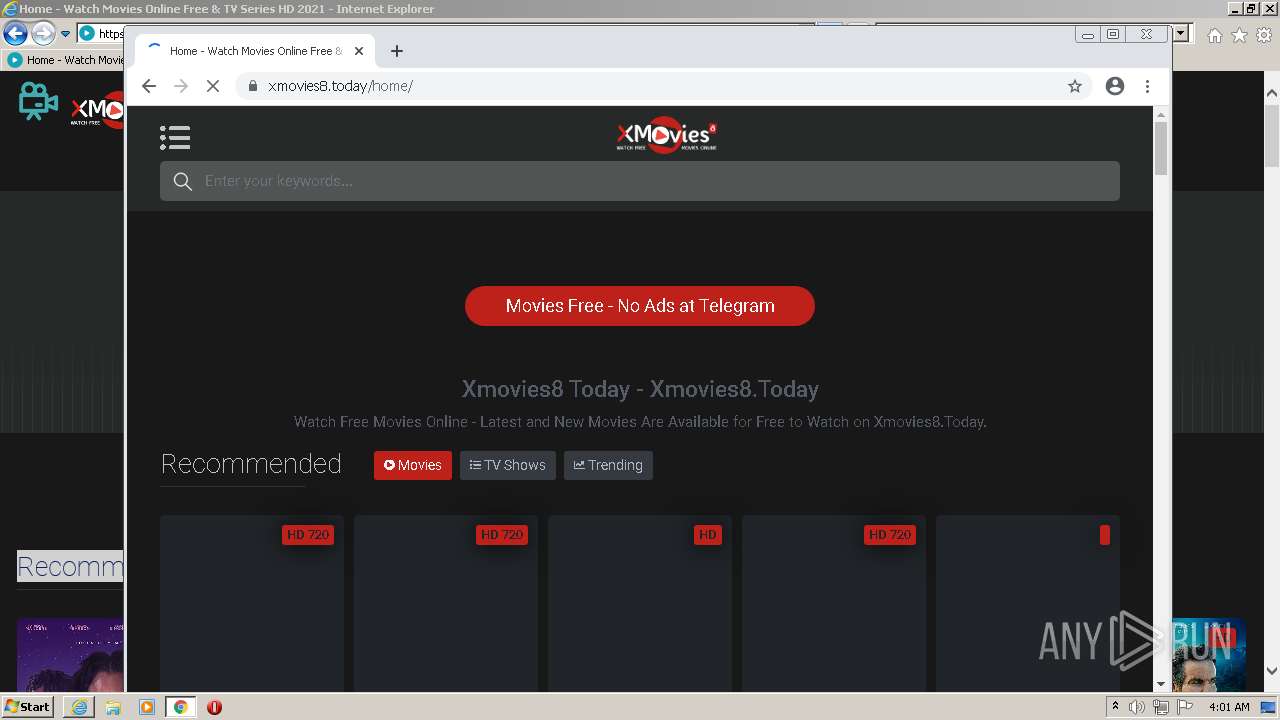
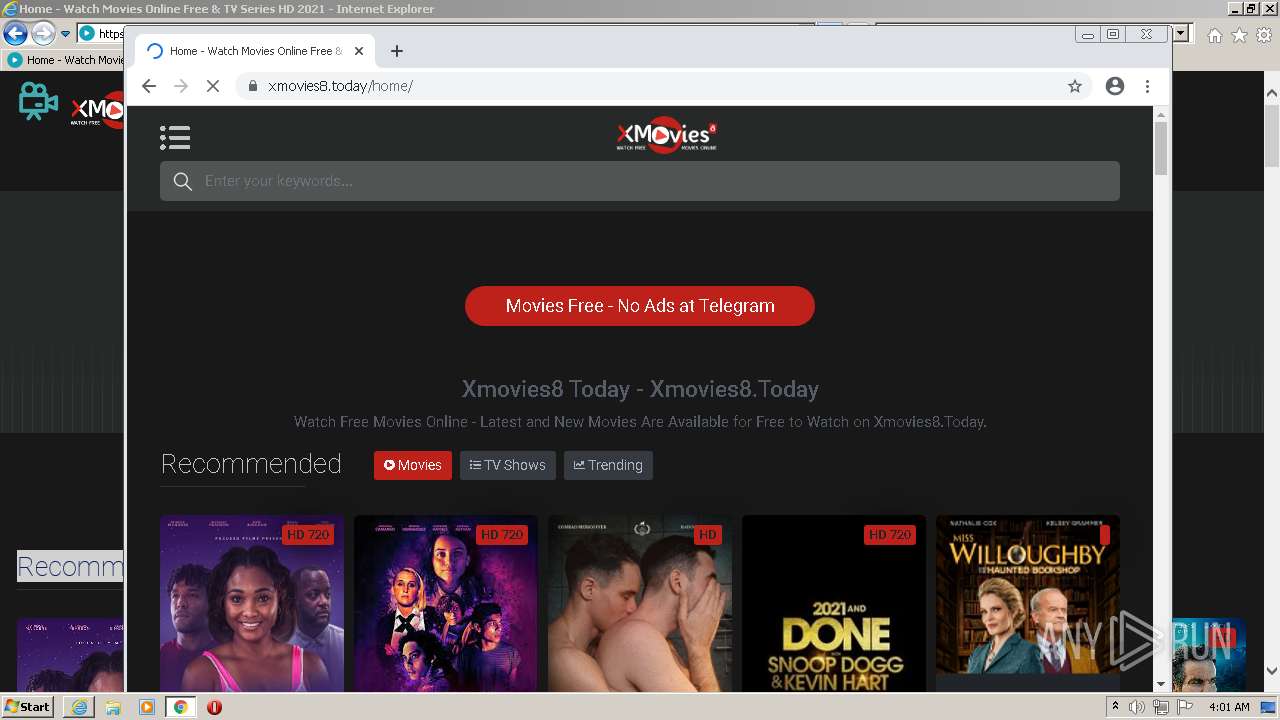
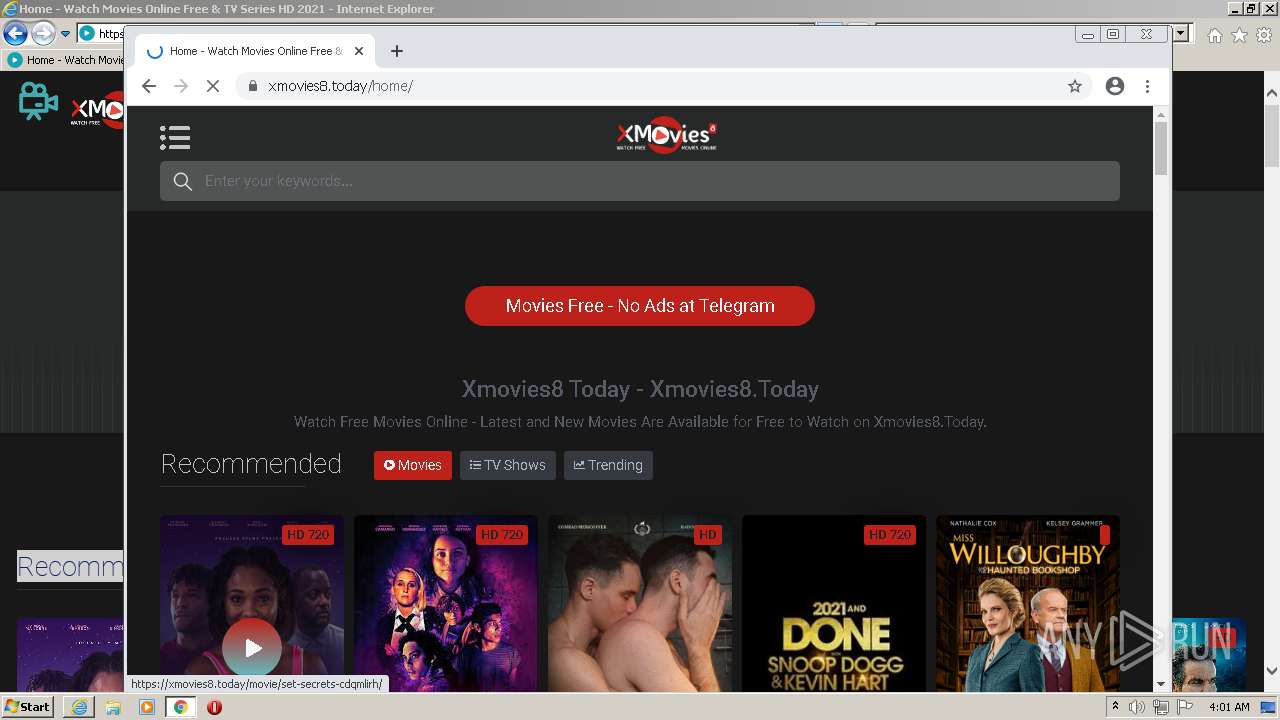
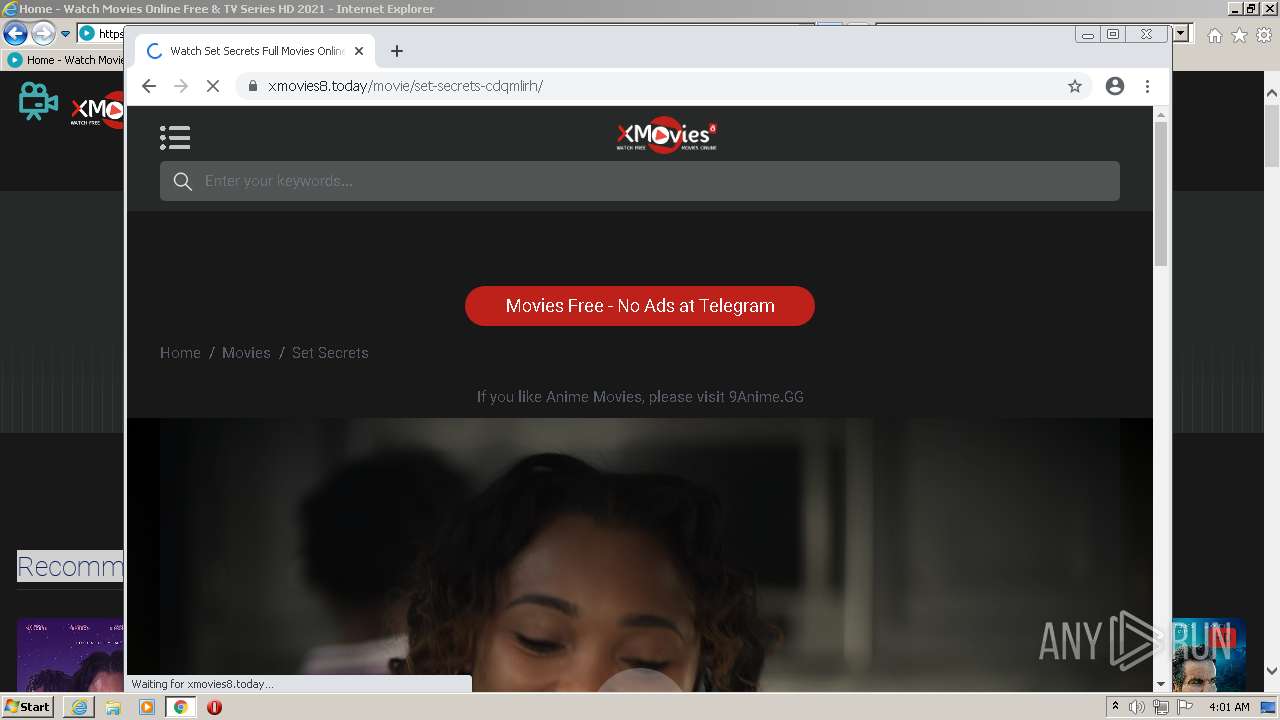
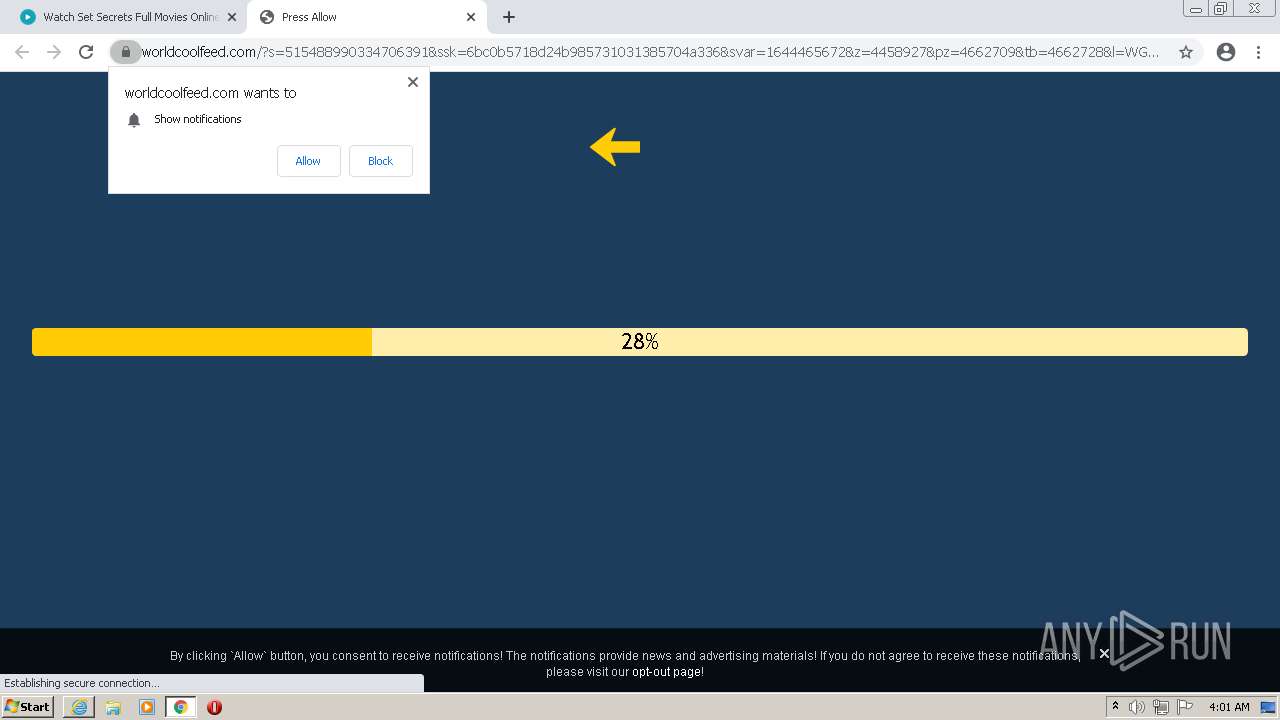
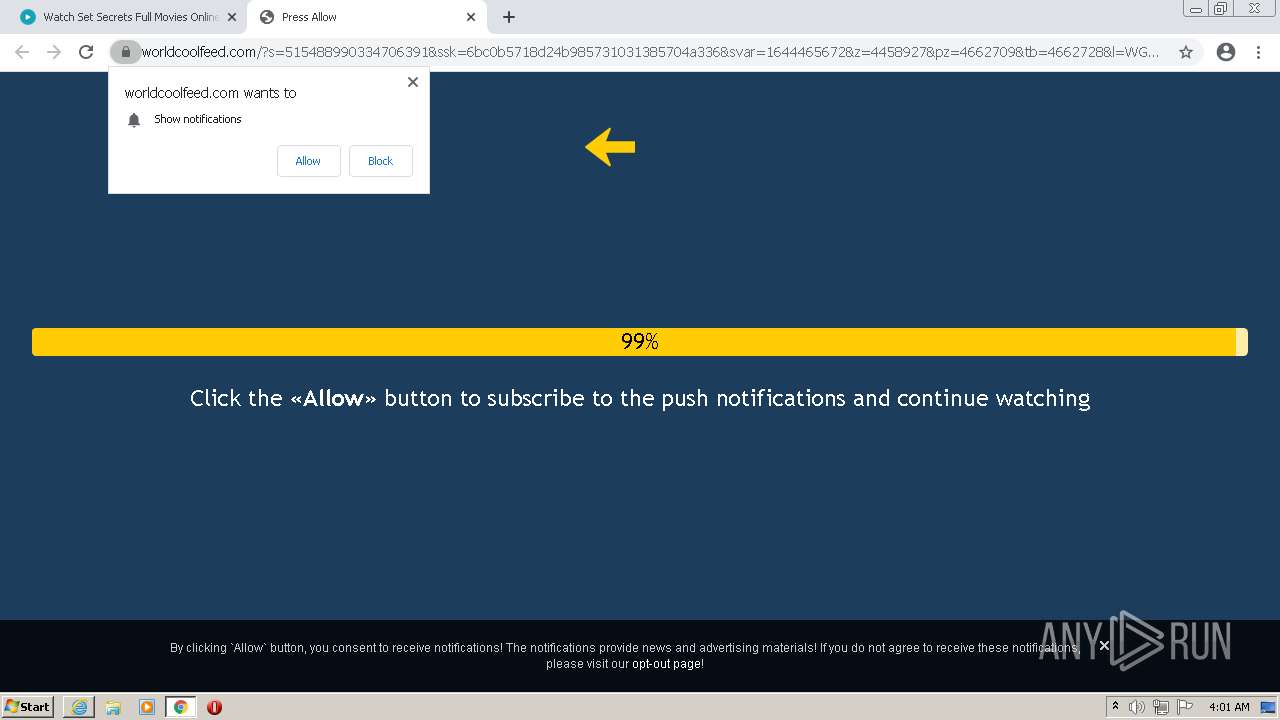
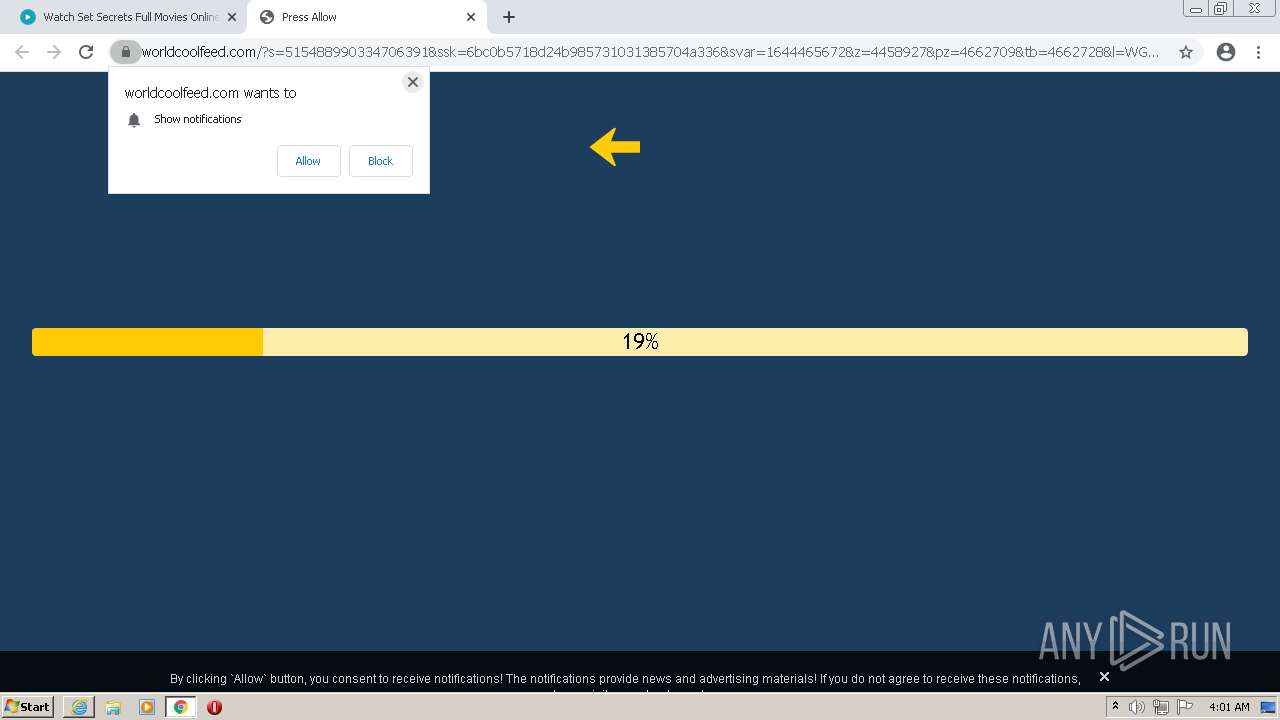
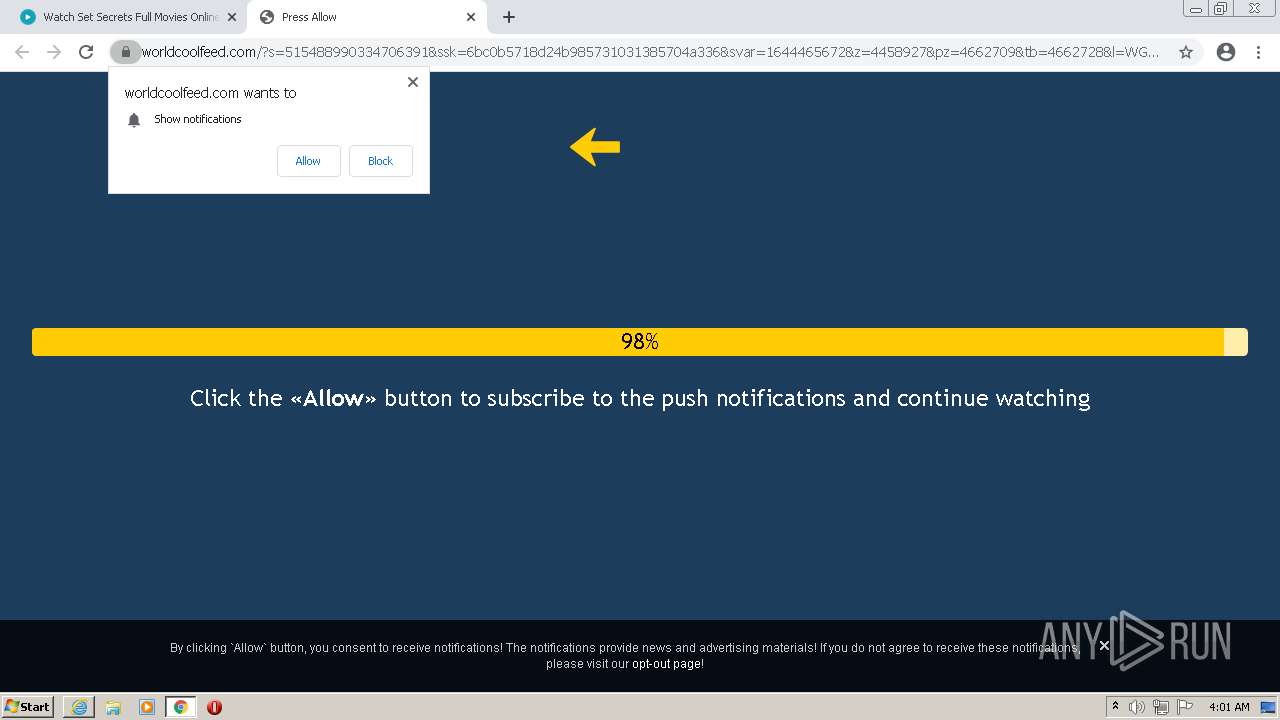
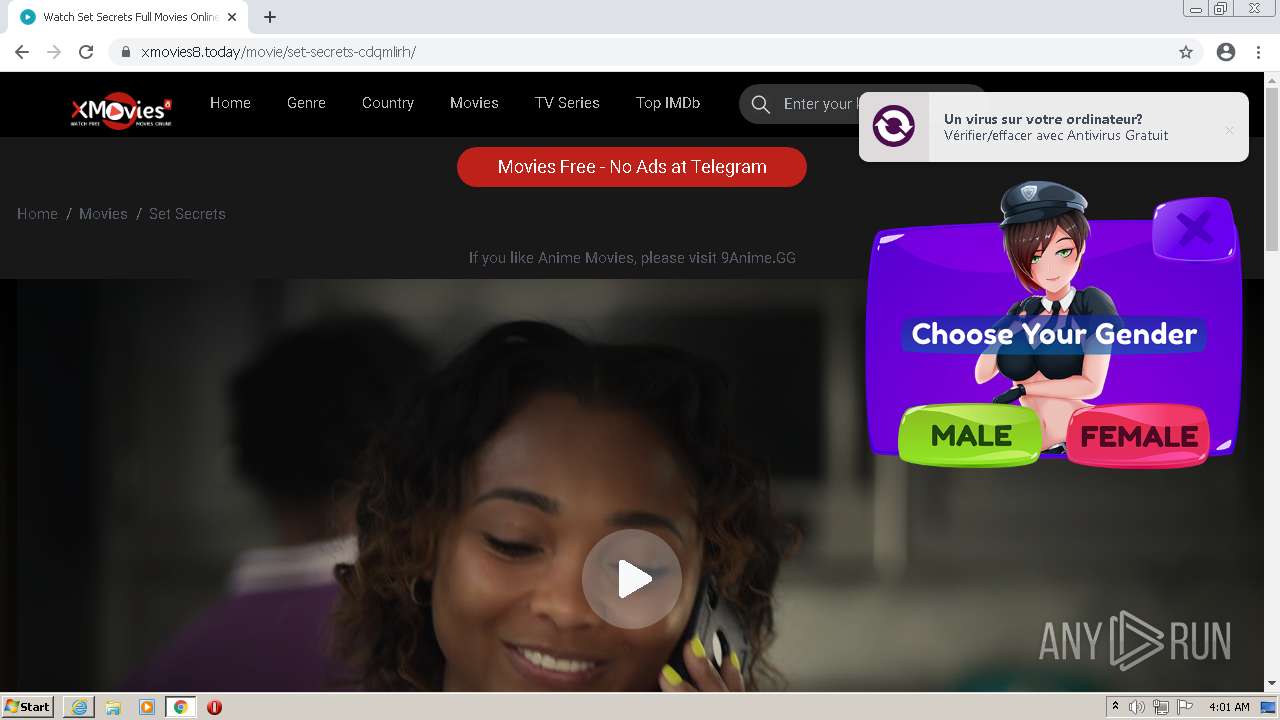
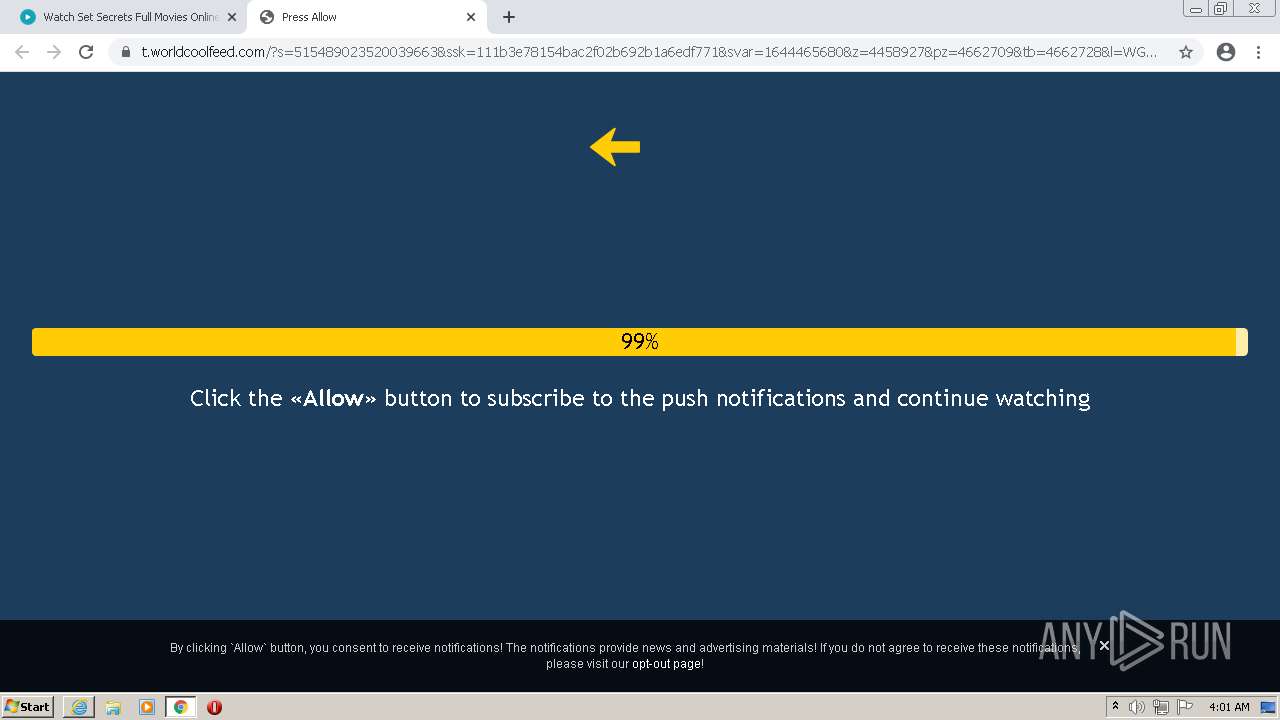
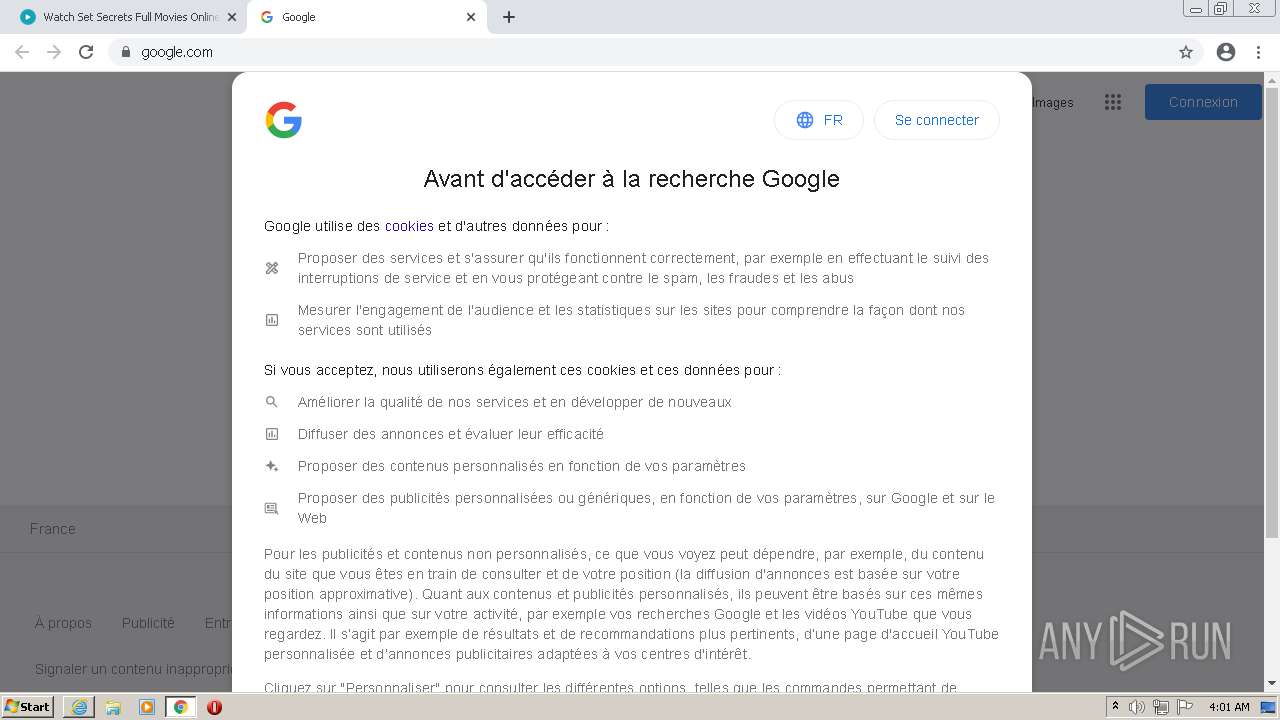
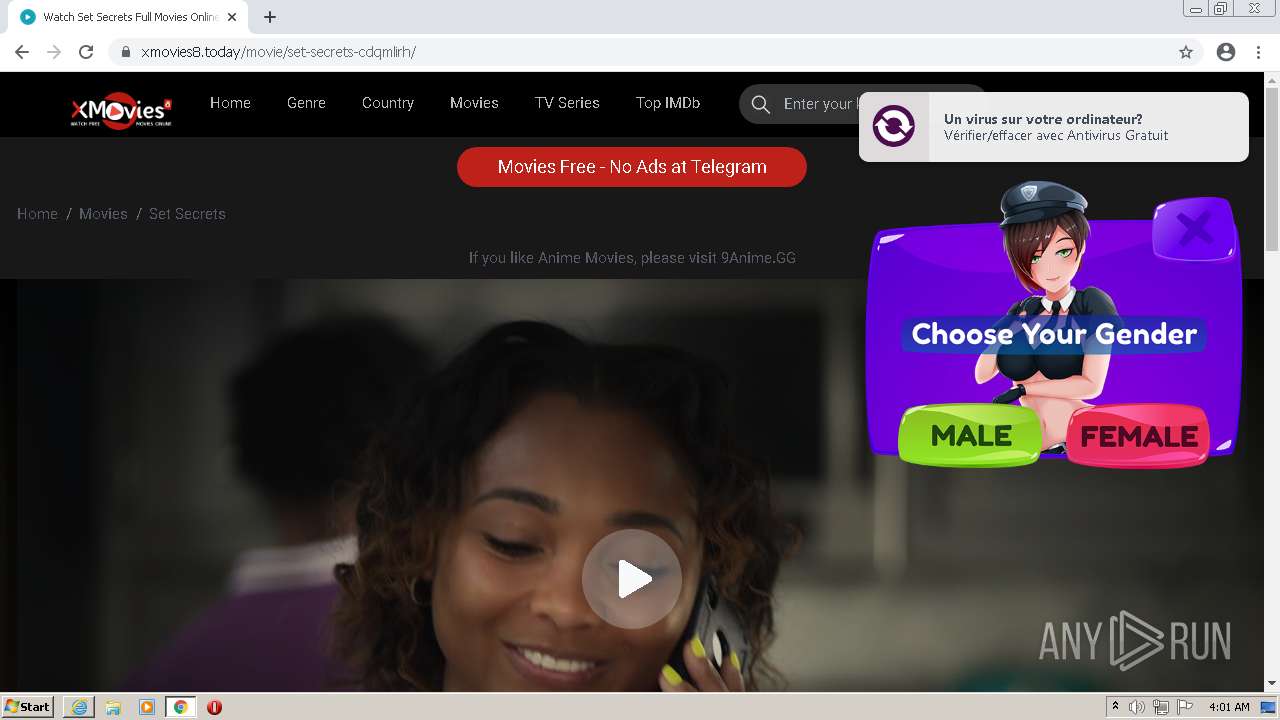
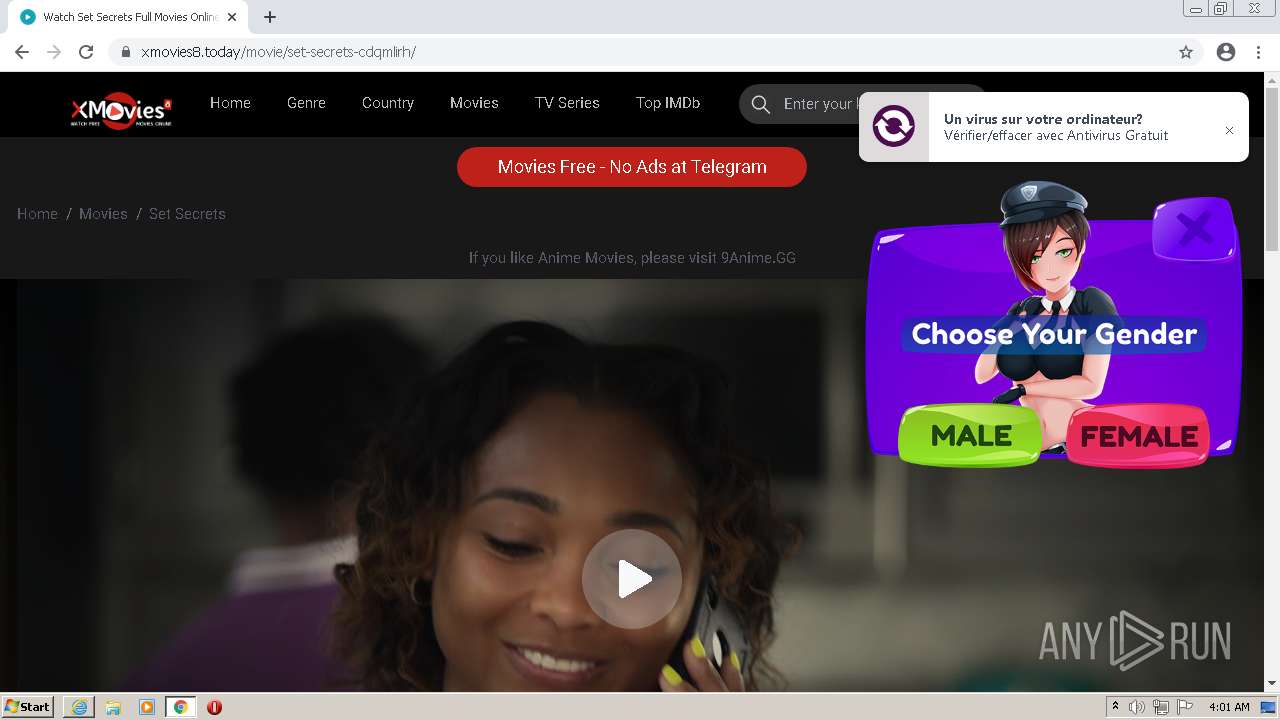
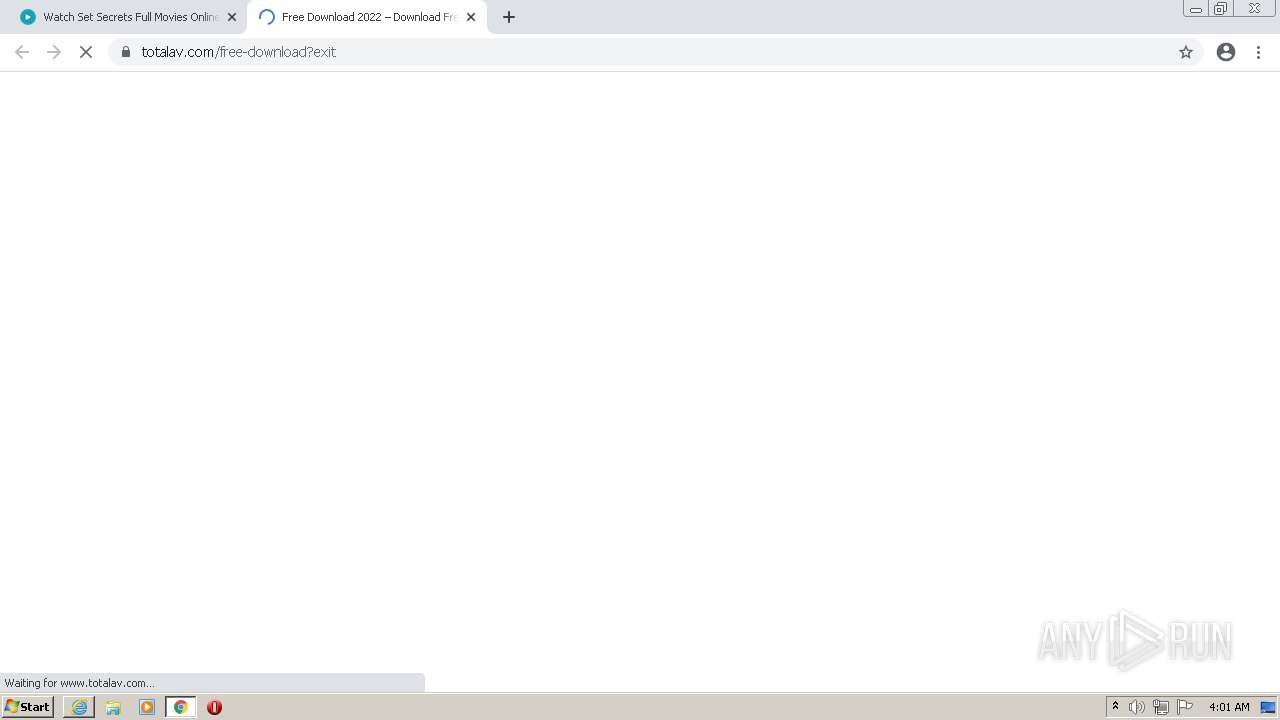
| URL: | http://xmovies8.today |
| Full analysis: | https://app.any.run/tasks/10b19ee6-54dc-4b6d-bacc-8c7653e910ef |
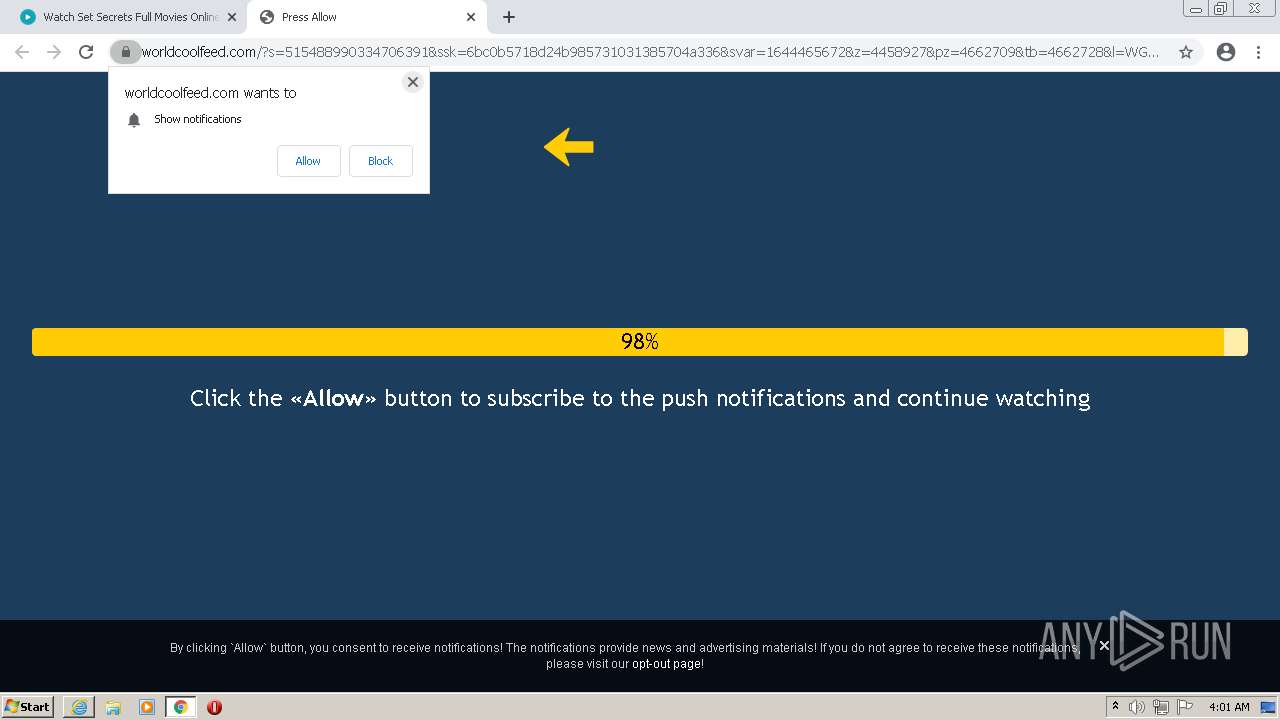
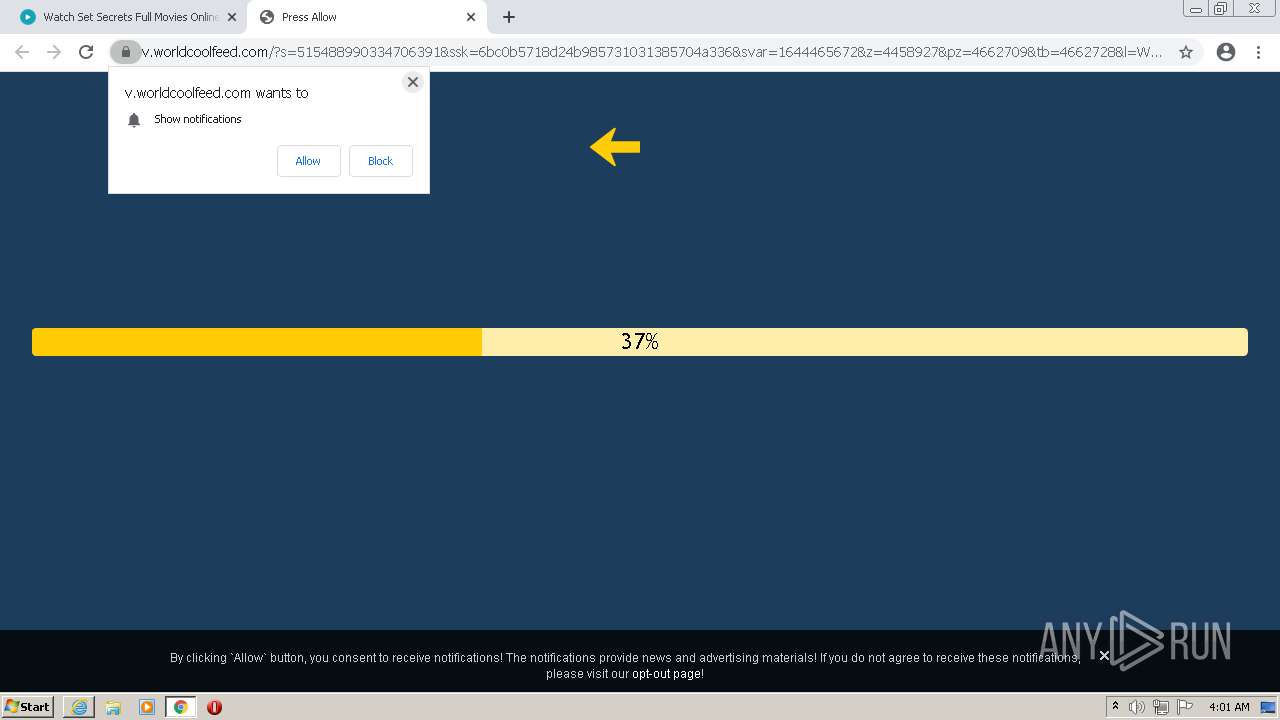
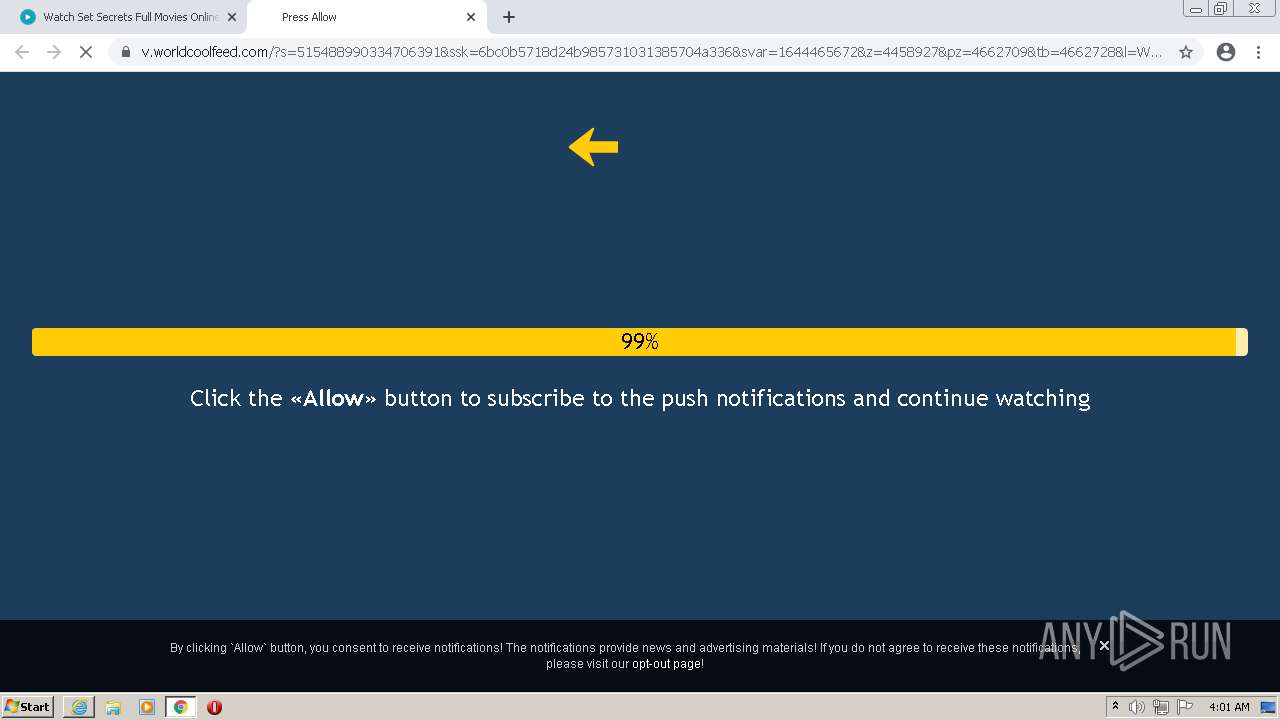
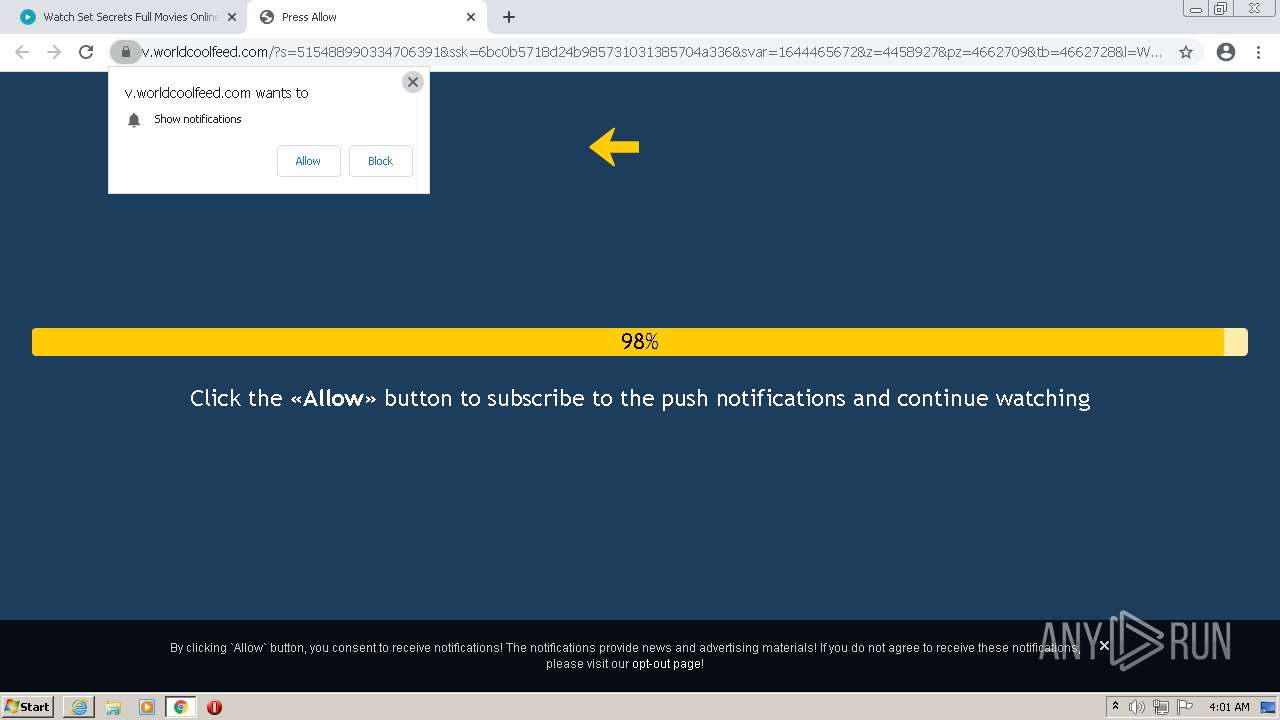
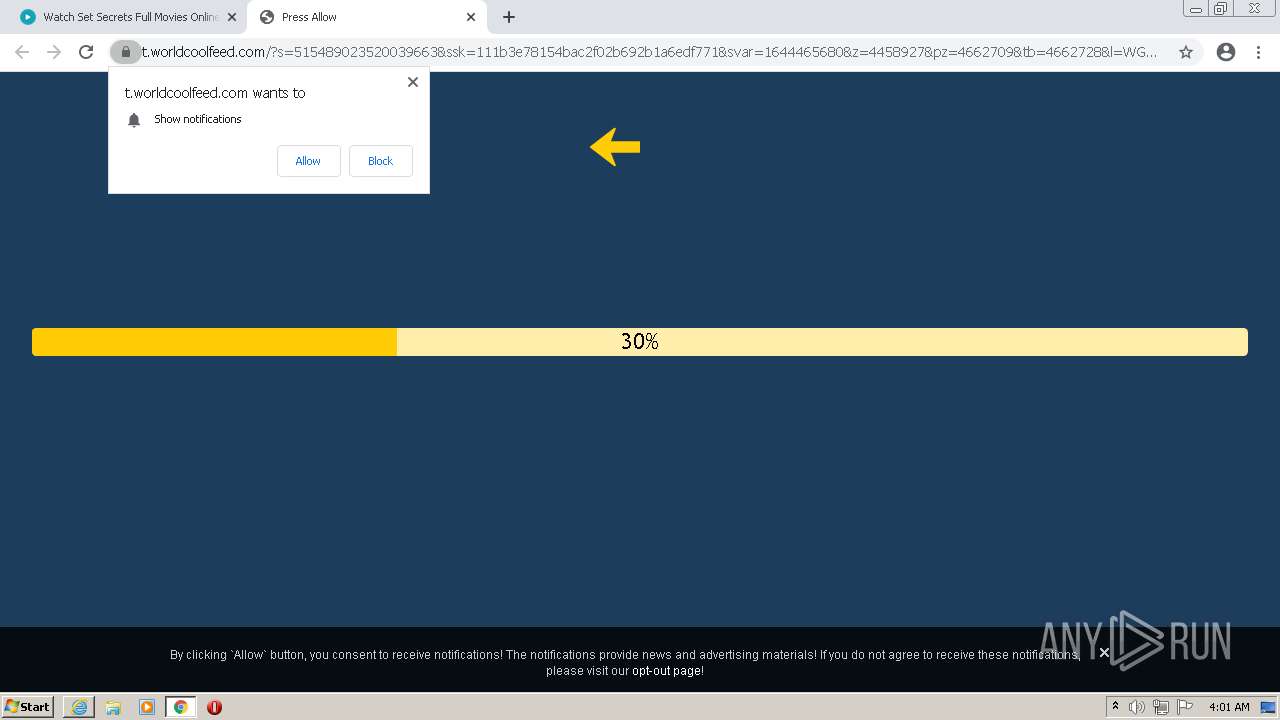
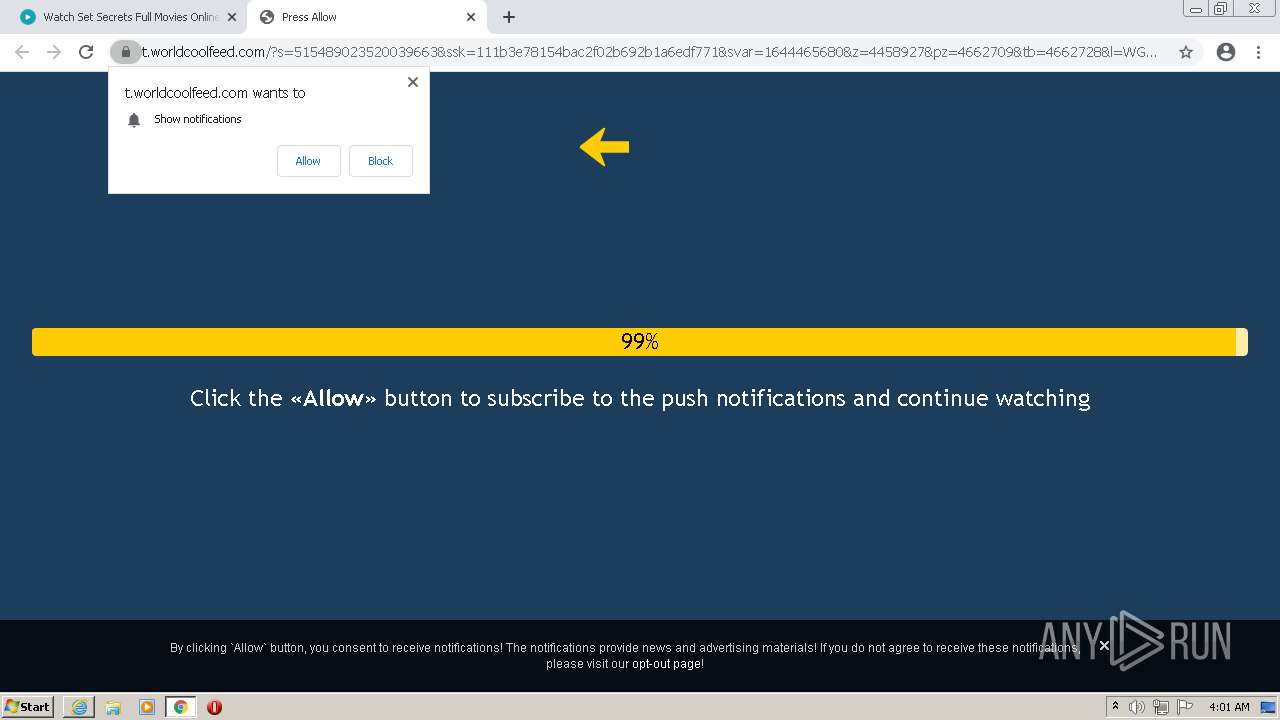
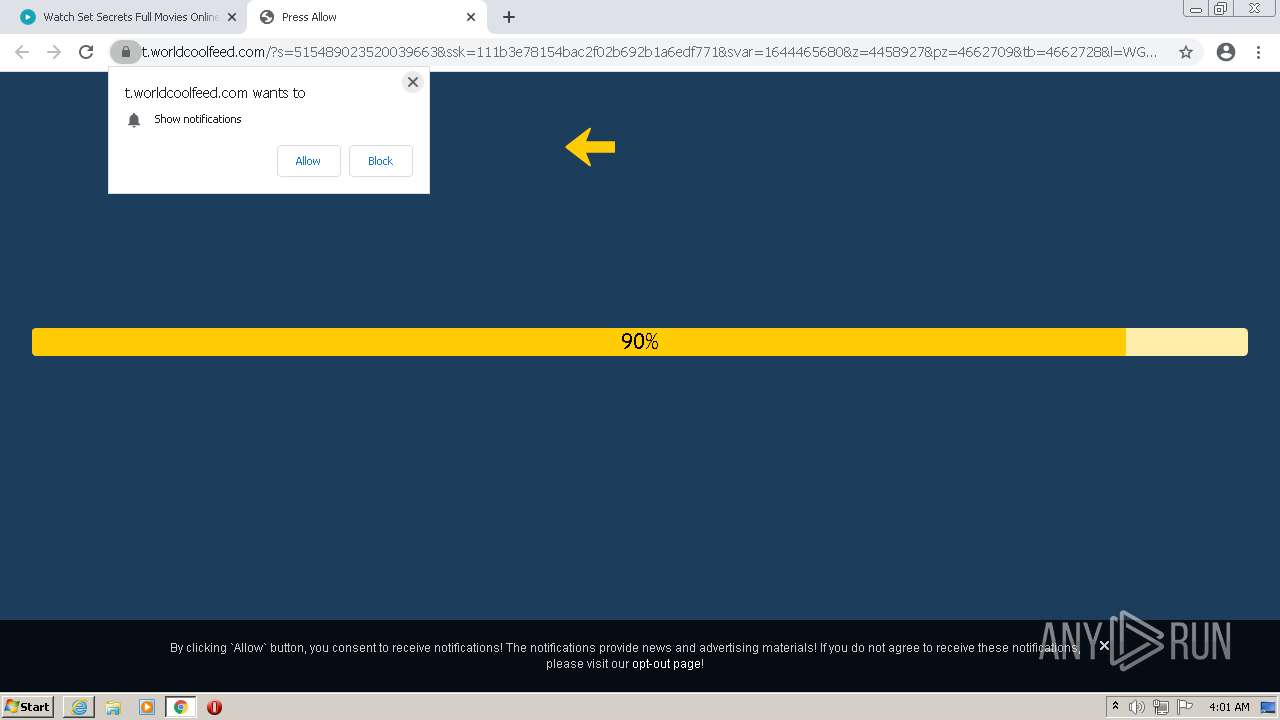
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2022, 03:57:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 64C70D5DF7553731AD513D594C1F7AEE |
| SHA1: | 1156CD5504F8F8133F1F032C683D2995D3EEF68F |
| SHA256: | C8EE943FE62CB15F2CD840AF633F979262E2EC0E7FFEC35261C9B8E277D4CD43 |
| SSDEEP: | 3:N1KGIyn:CGVn |
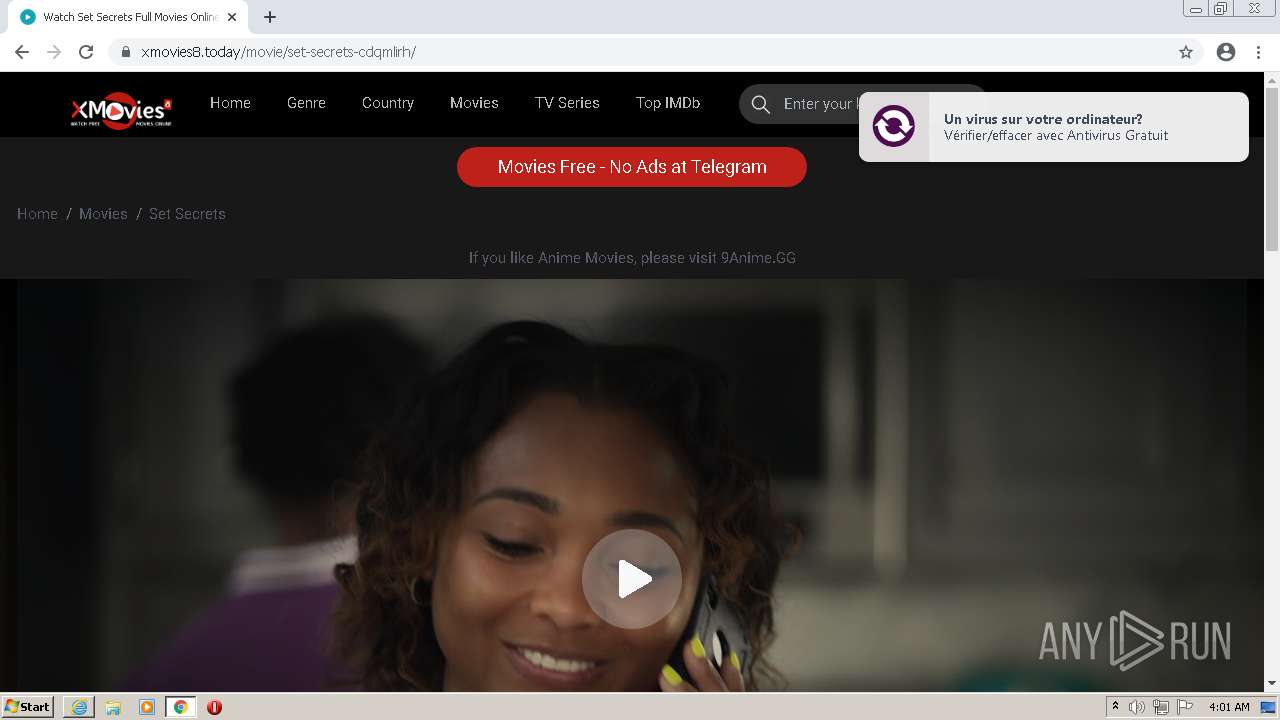
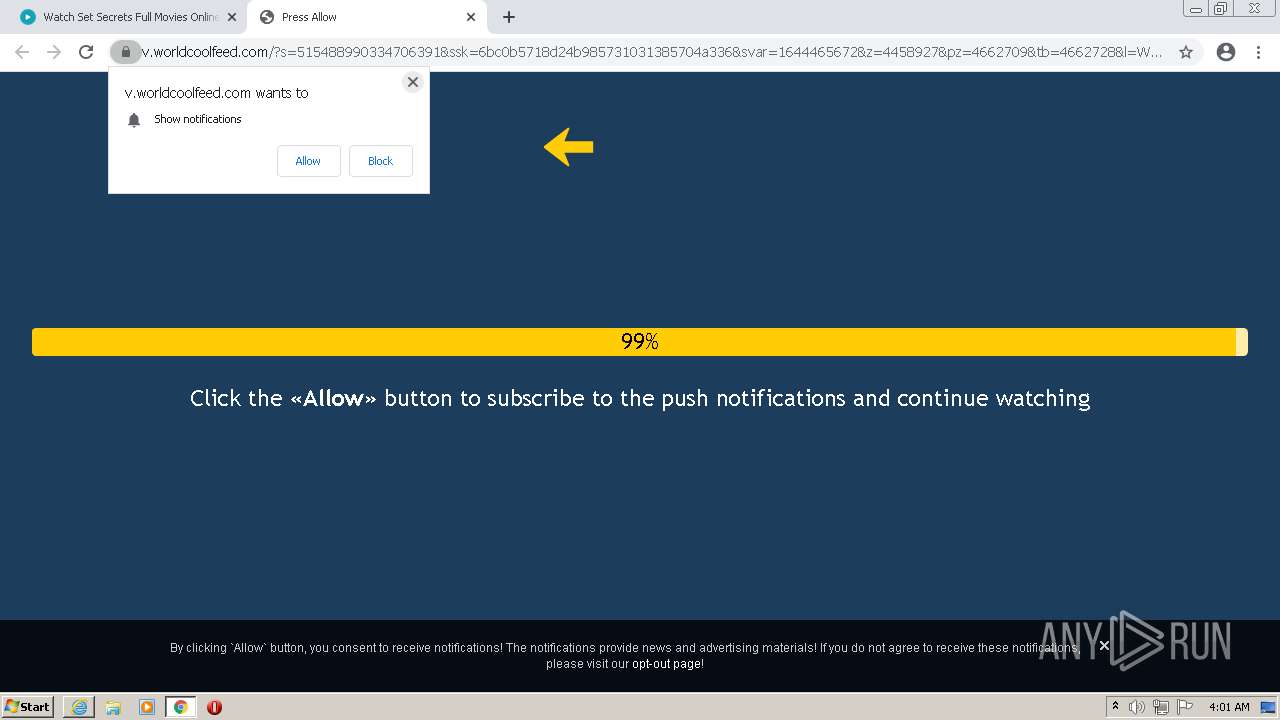
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1960)
- iexplore.exe (PID: 2104)
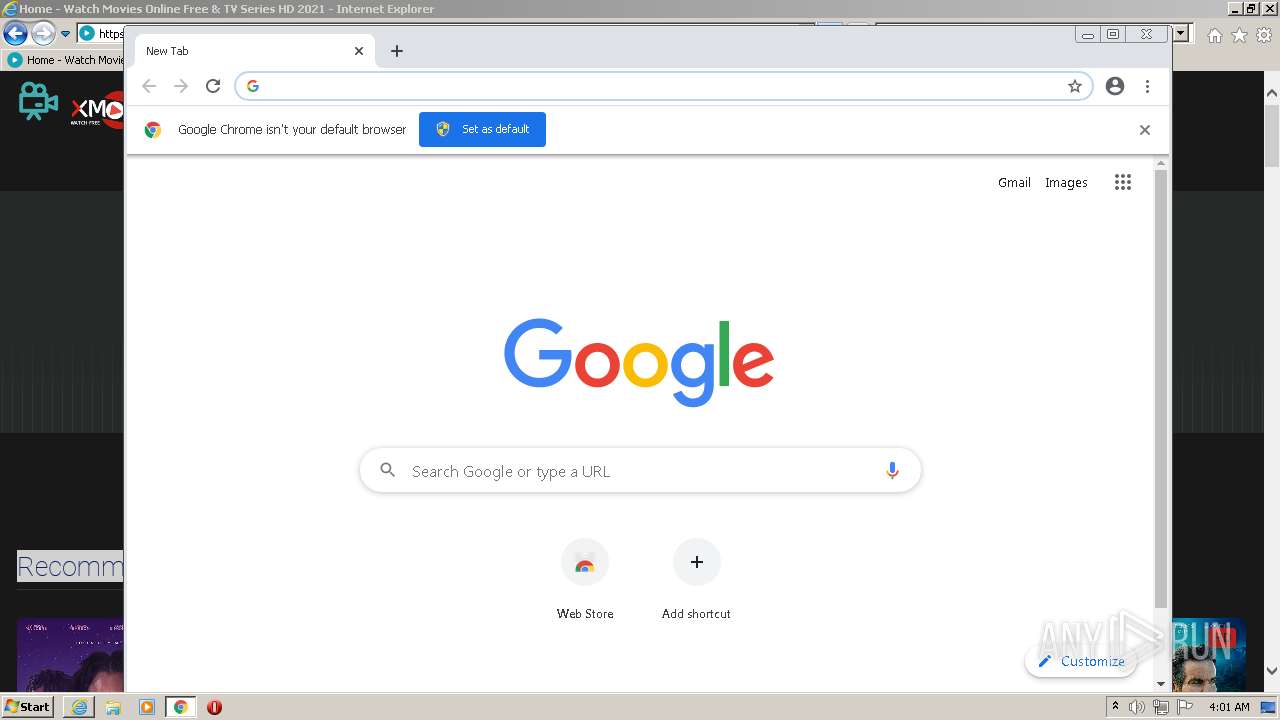
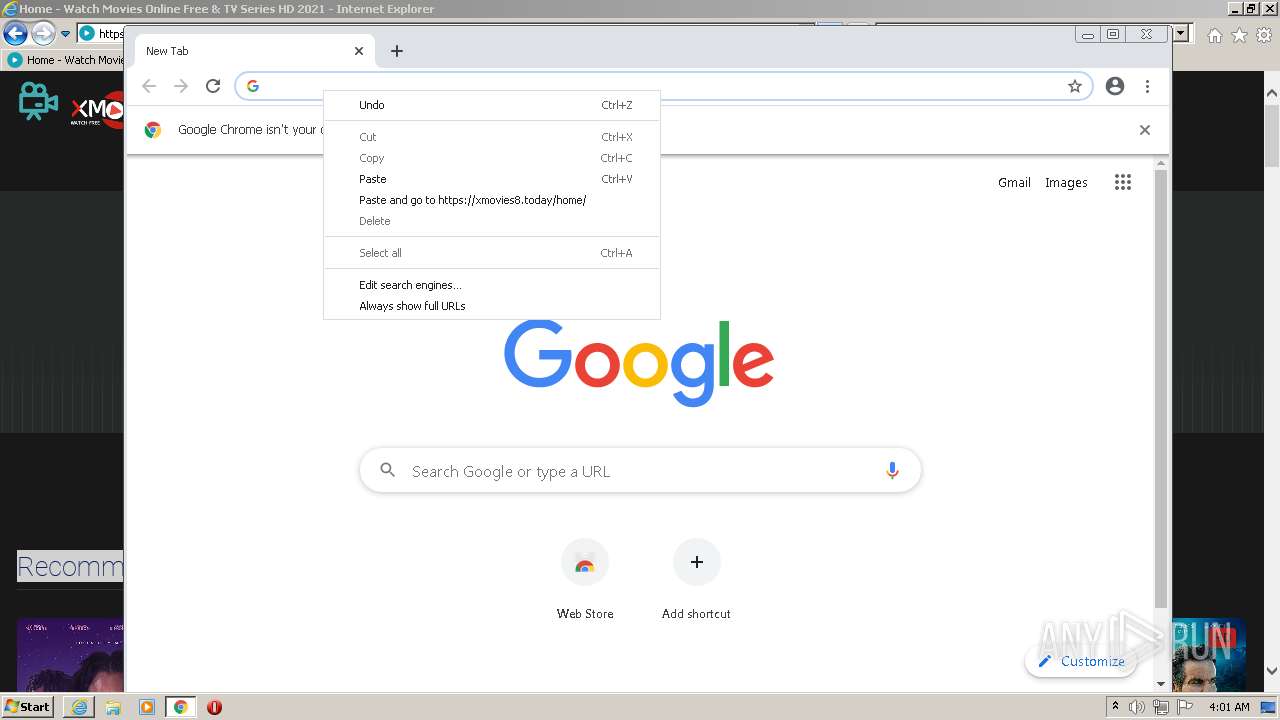
Modifies files in Chrome extension folder
- chrome.exe (PID: 2836)
INFO
Application launched itself
- iexplore.exe (PID: 3740)
- chrome.exe (PID: 2836)
Reads the computer name
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 1960)
- iexplore.exe (PID: 2104)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 2620)
- chrome.exe (PID: 884)
- chrome.exe (PID: 1260)
- chrome.exe (PID: 3464)
- chrome.exe (PID: 588)
- chrome.exe (PID: 1028)
Changes internet zones settings
- iexplore.exe (PID: 3740)
Reads settings of System Certificates
- iexplore.exe (PID: 1960)
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 2104)
- chrome.exe (PID: 2620)
Reads internet explorer settings
- iexplore.exe (PID: 1960)
- iexplore.exe (PID: 2104)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3740)
Checks supported languages
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 1960)
- chrome.exe (PID: 2620)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 2876)
- chrome.exe (PID: 1976)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 884)
- chrome.exe (PID: 1260)
- chrome.exe (PID: 1476)
- chrome.exe (PID: 1436)
- chrome.exe (PID: 2296)
- chrome.exe (PID: 3864)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 1148)
- chrome.exe (PID: 3204)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 3464)
- chrome.exe (PID: 588)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 1536)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 3964)
- chrome.exe (PID: 1028)
- chrome.exe (PID: 2436)
- chrome.exe (PID: 444)
Checks Windows Trust Settings
- iexplore.exe (PID: 1960)
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 2104)
Creates files in the user directory
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 2104)
- chrome.exe (PID: 2836)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3740)
Changes settings of System certificates
- iexplore.exe (PID: 3740)
Reads the hosts file
- chrome.exe (PID: 2836)
- chrome.exe (PID: 2620)
Manual execution by user
- chrome.exe (PID: 2836)
Drops Coronavirus (possible) decoy
- iexplore.exe (PID: 1960)
Reads the date of Windows installation
- chrome.exe (PID: 588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
31
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11207237480022249986,17130876854999192999,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,11207237480022249986,17130876854999192999,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,11207237480022249986,17130876854999192999,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2860 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,11207237480022249986,17130876854999192999,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=980 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11207237480022249986,17130876854999192999,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3332 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,11207237480022249986,17130876854999192999,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3652 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,11207237480022249986,17130876854999192999,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,11207237480022249986,17130876854999192999,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2868 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11207237480022249986,17130876854999192999,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3676 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1960 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3740 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
39 851
Read events
39 559
Write events
288
Delete events
4
Modification events
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30940722 | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30940722 | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
228
Text files
378
Unknown types
48
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:5E8C7157EC14B4BB9710245897CB1A64 | SHA256:1ABB5FFF0C59195D4AD47892B131AA0AC4559049578DB6E7B2E108B14F3783E4 | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:EEB8350F26D81F5B16F1F66C83A1D436 | SHA256:4A9D4DC552EBF649EC654A792E4DF244A47D86748870911C8D7B4DA3235E81F0 | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:58655D806FF01F7F5A66CBC16FBF9992 | SHA256:C710750AE0357EB777595819EF6DBD65C2174F797524383BA05AB32AD7BB2FBF | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\JRHR970M.htm | html | |
MD5:1F00619B34862F5B1879E9D9656BEB4E | SHA256:6923E287969EBA423119A03C8906B9E94A68AD2E362E32C02AE0C39AED9A0236 | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style[1].css | text | |
MD5:17C2A12AB6E082A657EDC72F8520EEC1 | SHA256:DF3069A4A240E2A26B147F9A4EA07EBCFD498F2BC87DF6F39E2A50B3BD1605BC | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\fonts[1].css | text | |
MD5:E94F653CD233A261A049FED215E47145 | SHA256:62270A2AD42F92FE971650731D3B6359953B3106267C7D5564F318C95D8A6D1E | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\jstheme[1].js | text | |
MD5:171148CE55232017A3DFCEAF9ACE7E91 | SHA256:7EB4607B5C03ABD5053133BA3EE509E10FE9667031299B85A885F905E146745E | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\NUFVLZQ1 | text | |
MD5:FDA44910DEB1A460BE4AC5D56D61D837 | SHA256:933B971C6388D594A23FA1559825DB5BEC8ADE2DB1240AA8FC9D0C684949E8C9 | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\all[1].css | text | |
MD5:730B154CCAB17F78ABB14C8648B61317 | SHA256:FAA1553E61EE4718F0EDDD62873C73D406AD2ECD5B5DD93619BFC7D0214C2169 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
166
DNS requests
76
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1960 | iexplore.exe | GET | 301 | 104.21.79.86:80 | http://xmovies8.today/ | US | — | — | suspicious |
1960 | iexplore.exe | GET | 200 | 8.253.95.249:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c7e1f7930a058e5f | US | compressed | 4.70 Kb | whitelisted |
1960 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
1960 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDIRy5Lqyj5dAoAAAABLgV%2F | US | der | 472 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 92.123.195.107:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTN2ywtdRezDJufn8CUN4sXkQ%3D%3D | unknown | der | 503 b | shared |
1960 | iexplore.exe | GET | 200 | 104.89.32.83:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 92.123.195.107:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgM6lB7fAs6LqkDNpVvlzxldAg%3D%3D | unknown | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
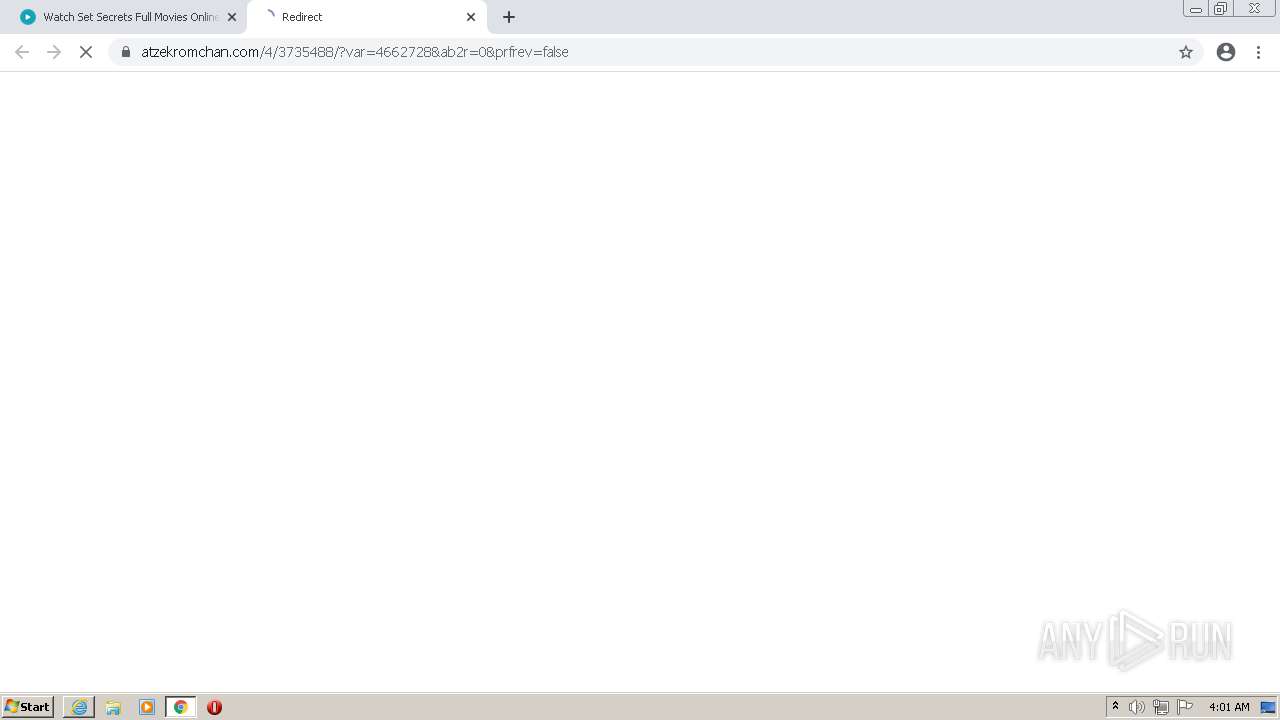
1960 | iexplore.exe | 104.21.79.86:80 | xmovies8.today | Cloudflare Inc | US | unknown |
1960 | iexplore.exe | 104.21.79.86:443 | xmovies8.today | Cloudflare Inc | US | unknown |
1960 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1960 | iexplore.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
1960 | iexplore.exe | 8.253.95.249:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
1960 | iexplore.exe | 139.45.197.239:443 | inpage-push.com | — | US | malicious |
1960 | iexplore.exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
1960 | iexplore.exe | 92.123.195.107:80 | r3.o.lencr.org | Akamai International B.V. | — | suspicious |
3740 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1960 | iexplore.exe | 192.0.77.48:443 | s.w.org | Automattic, Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xmovies8.today |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
thrustlumpypulse.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
lavechefantast.com |
| suspicious |
inpage-push.com |
| suspicious |
fonts.googleapis.com |
| whitelisted |