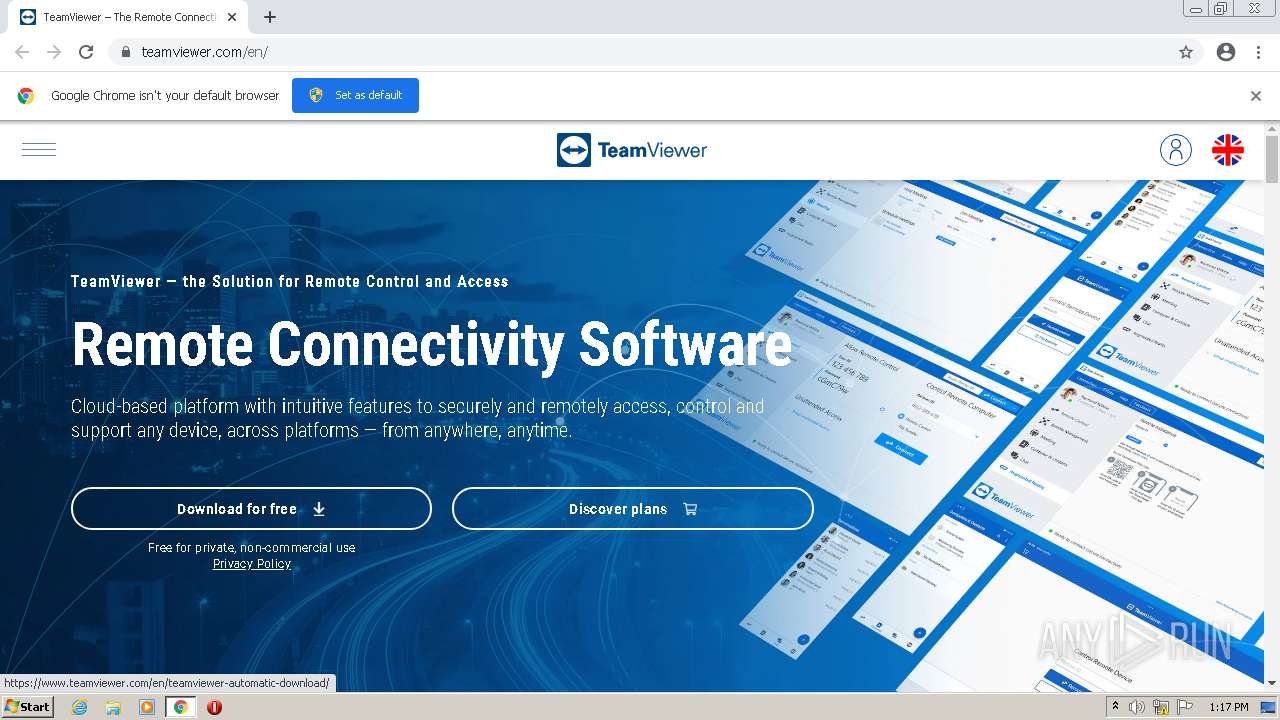
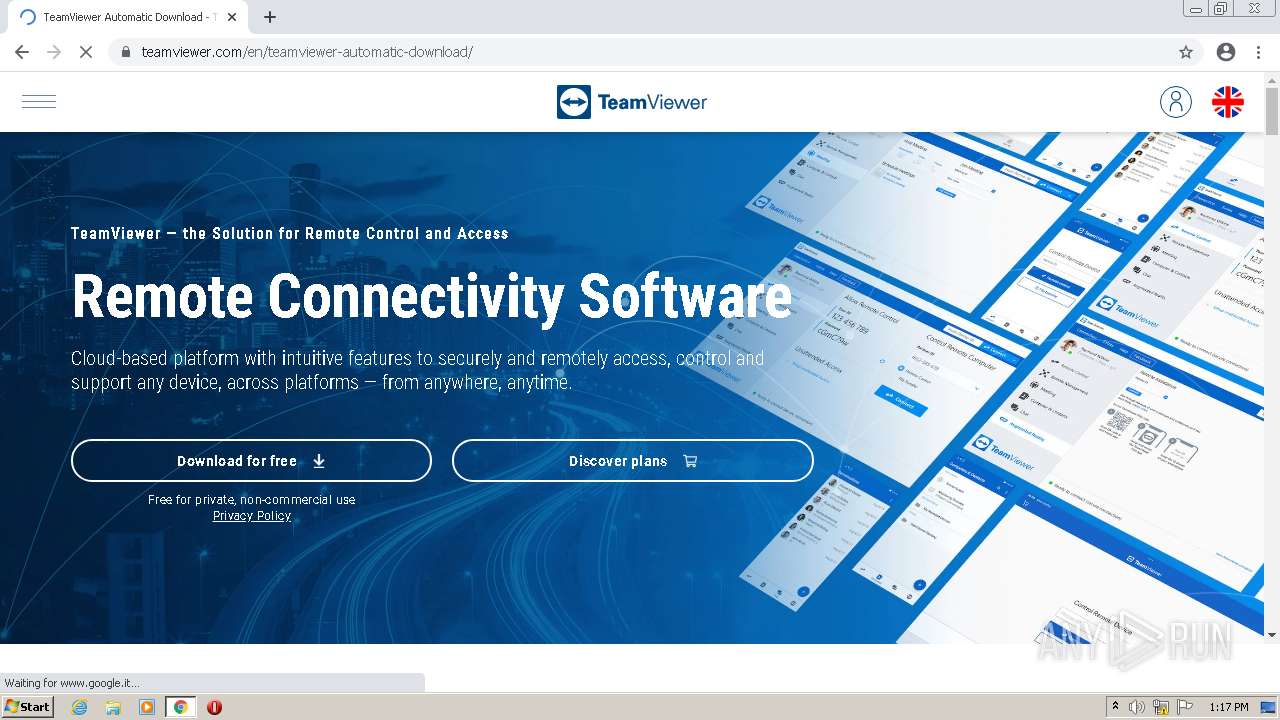
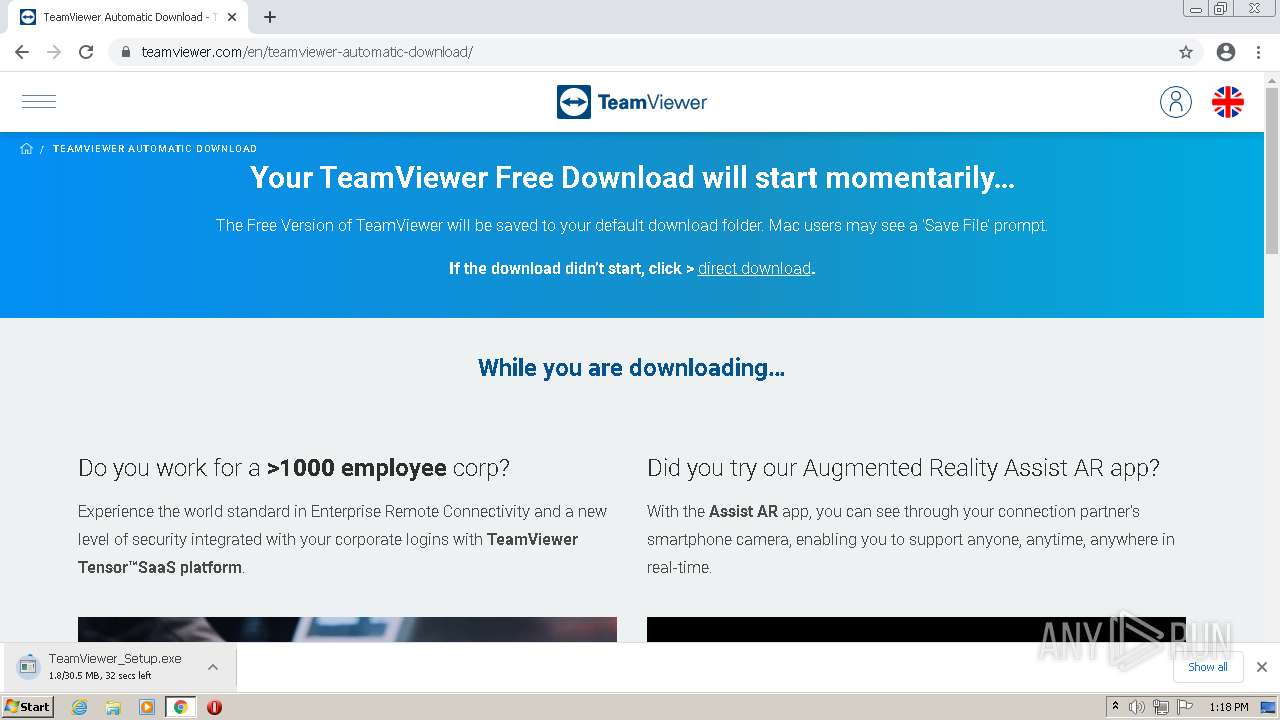
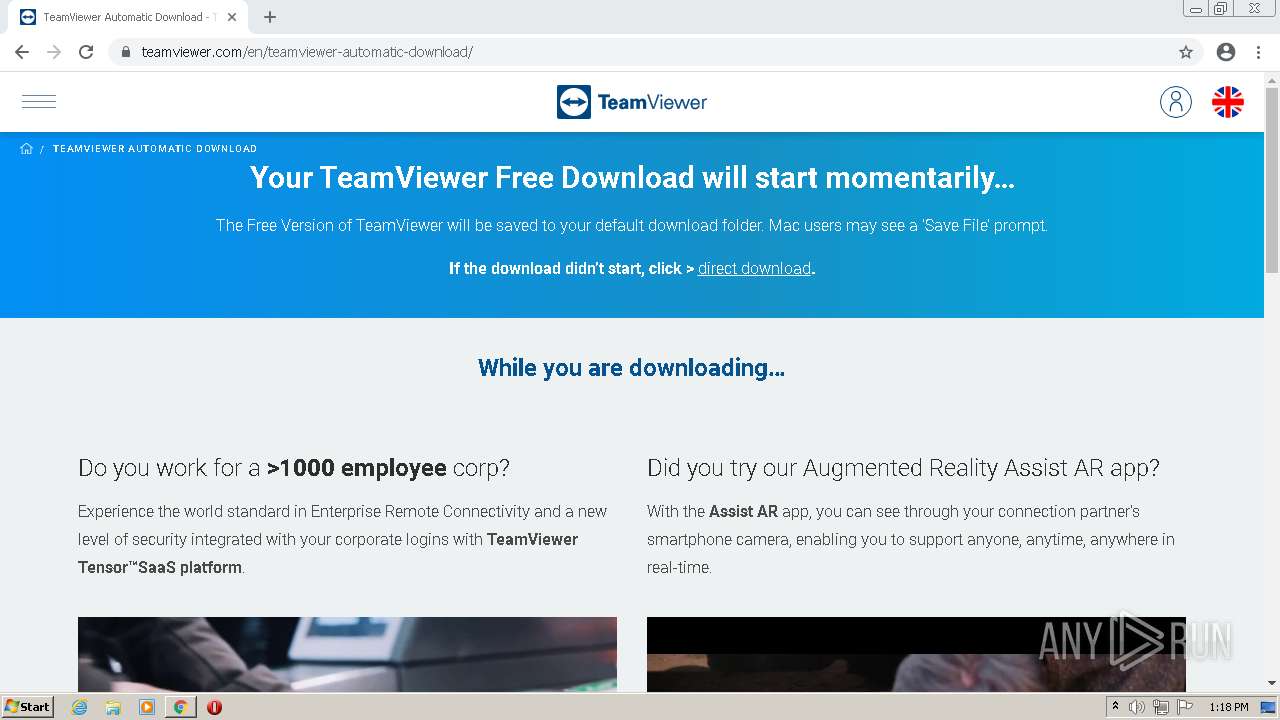
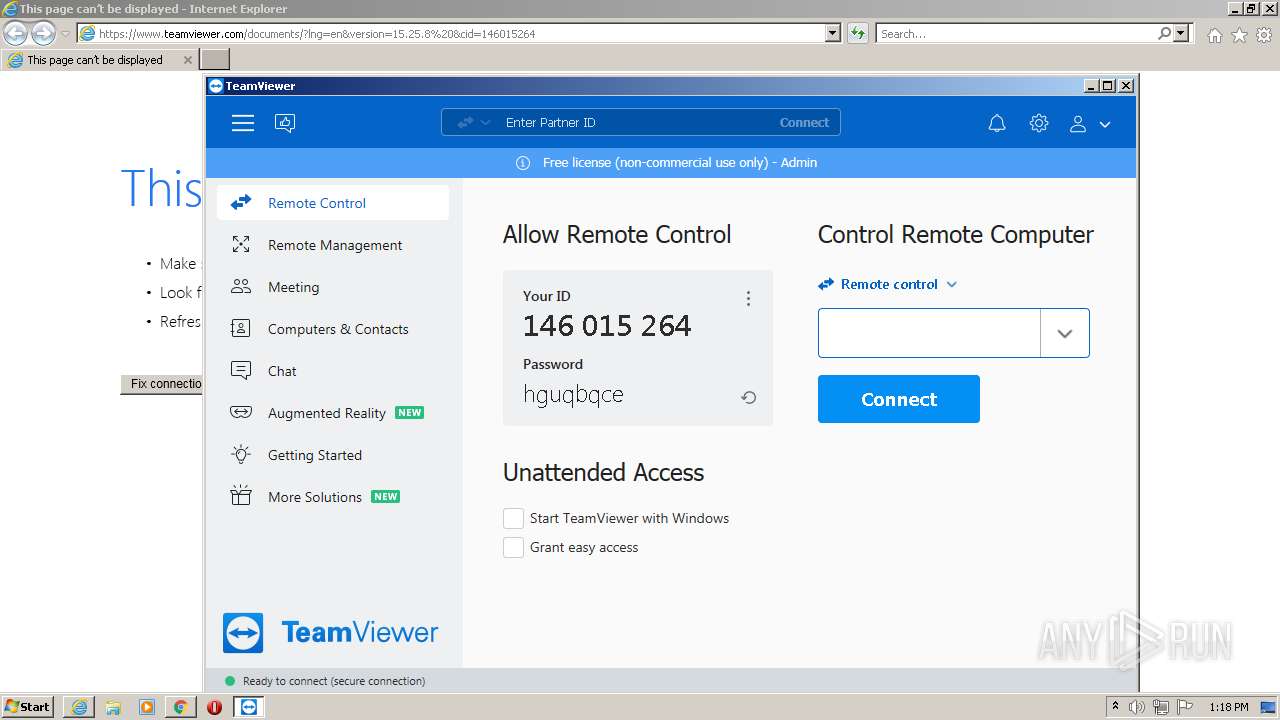
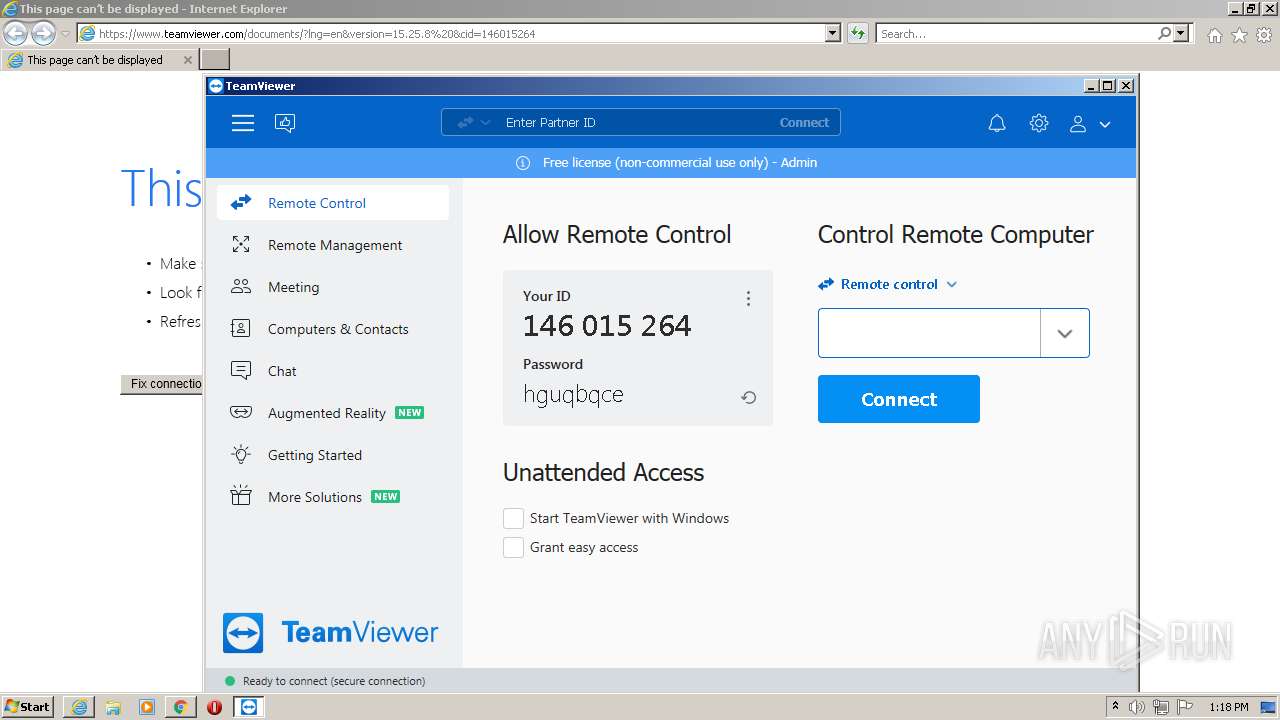
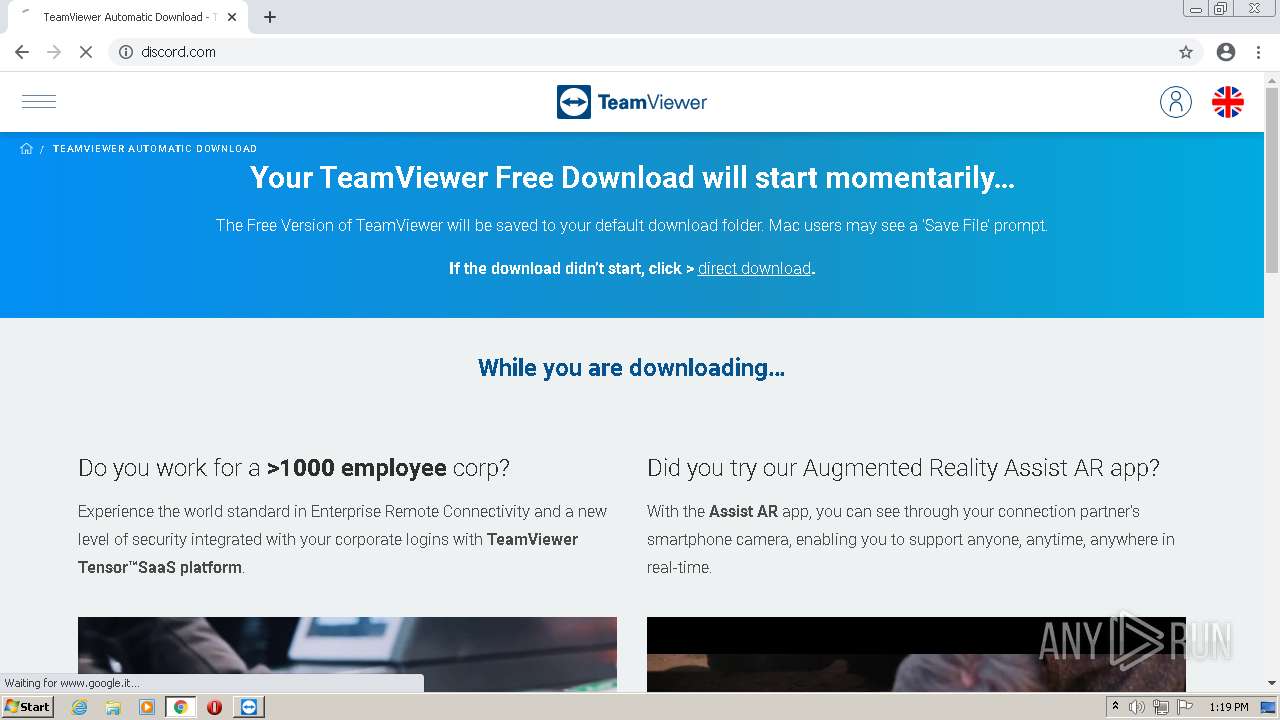
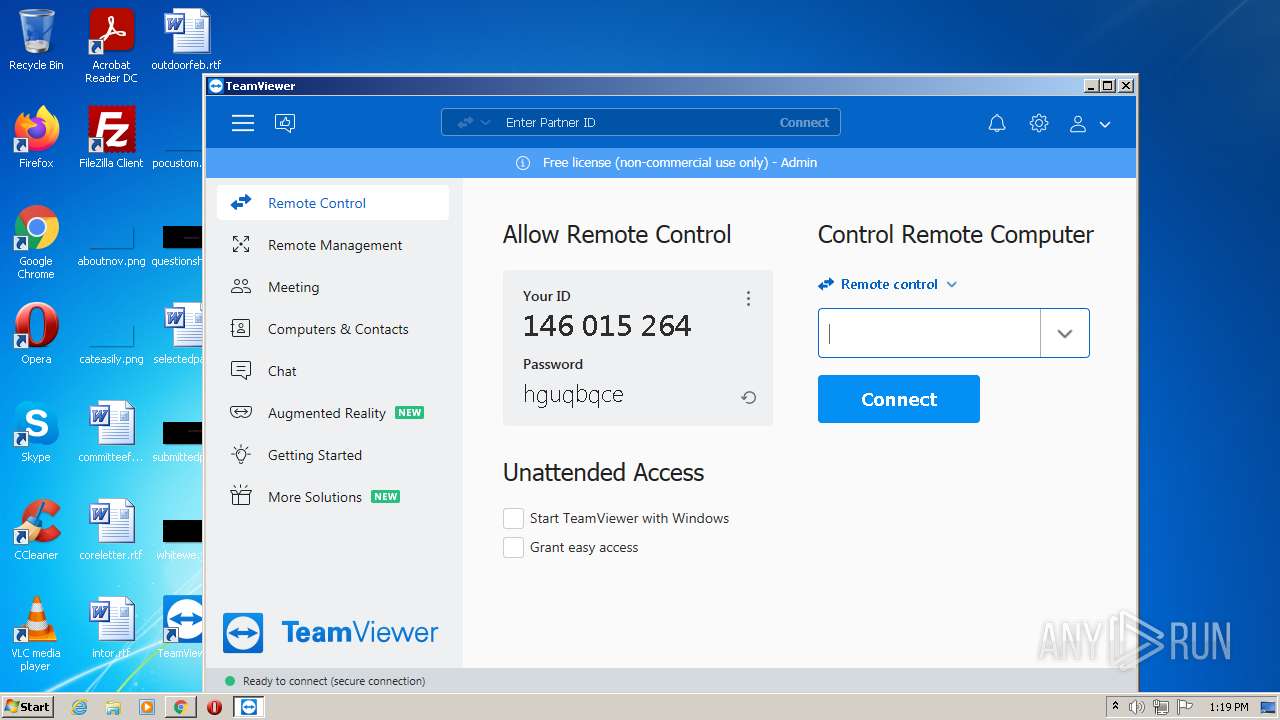
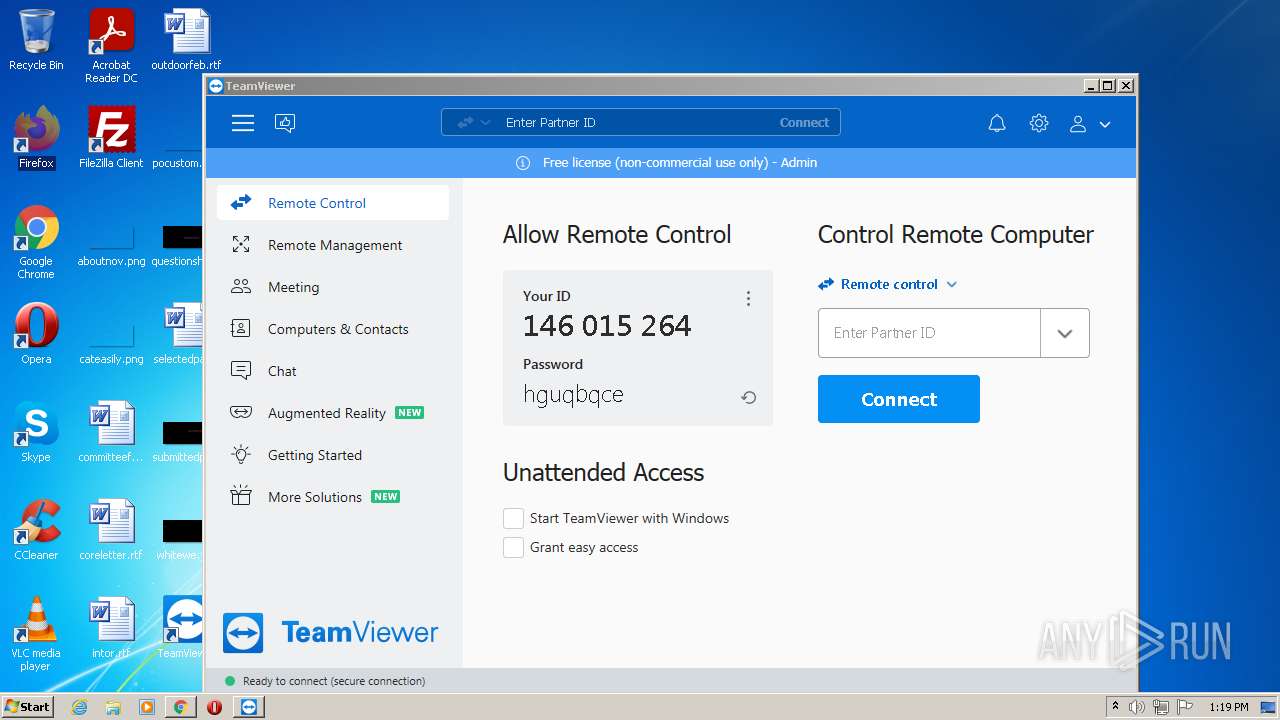
| URL: | https://www.teamviewer.com/en/ |
| Full analysis: | https://app.any.run/tasks/99b474c9-82fa-4d78-ad6f-cc083fe8b4e8 |
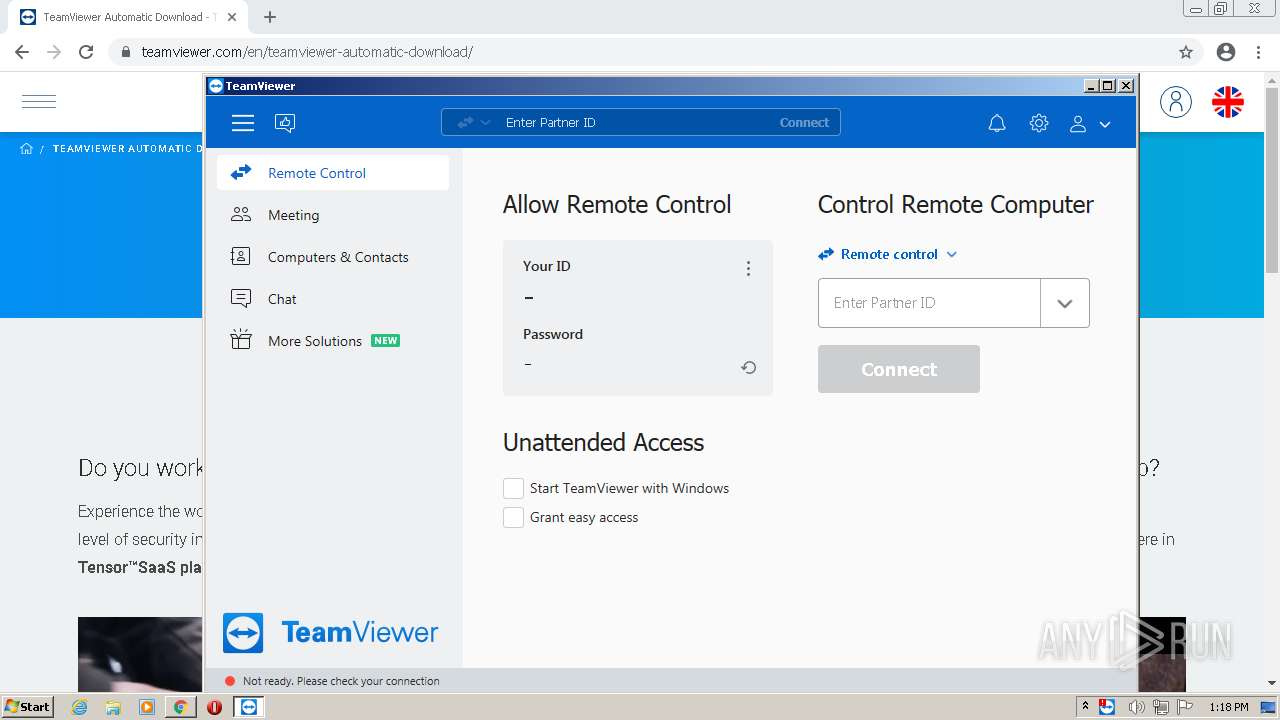
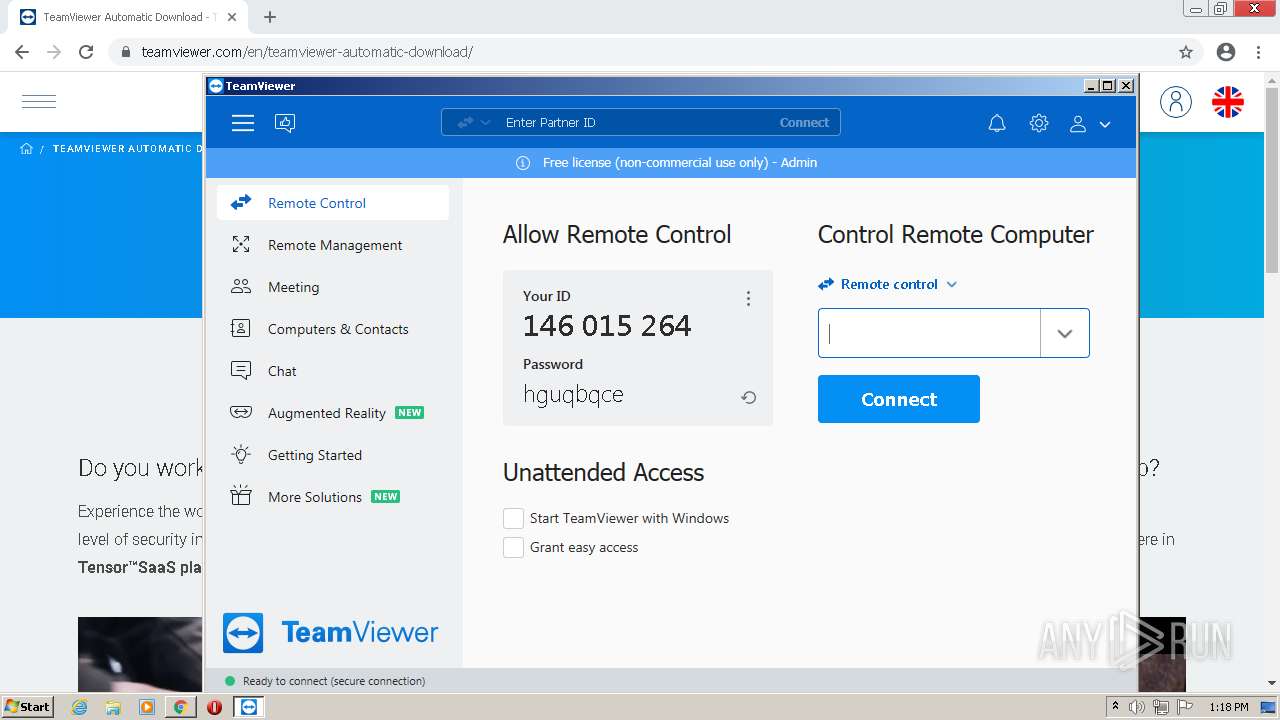
| Verdict: | Malicious activity |
| Analysis date: | December 26, 2021, 13:17:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DF8E2E21613000C46E7CFFBE57518E14 |
| SHA1: | 2A5A544A53545206D1C53D0024E8EA9AC5C67567 |
| SHA256: | C8DD85F9733DEF15AB3A788CB12C00804E19CC6E9C28F48C390CF2FC41C9E253 |
| SSDEEP: | 3:N8DSLaJiun:2OL7un |
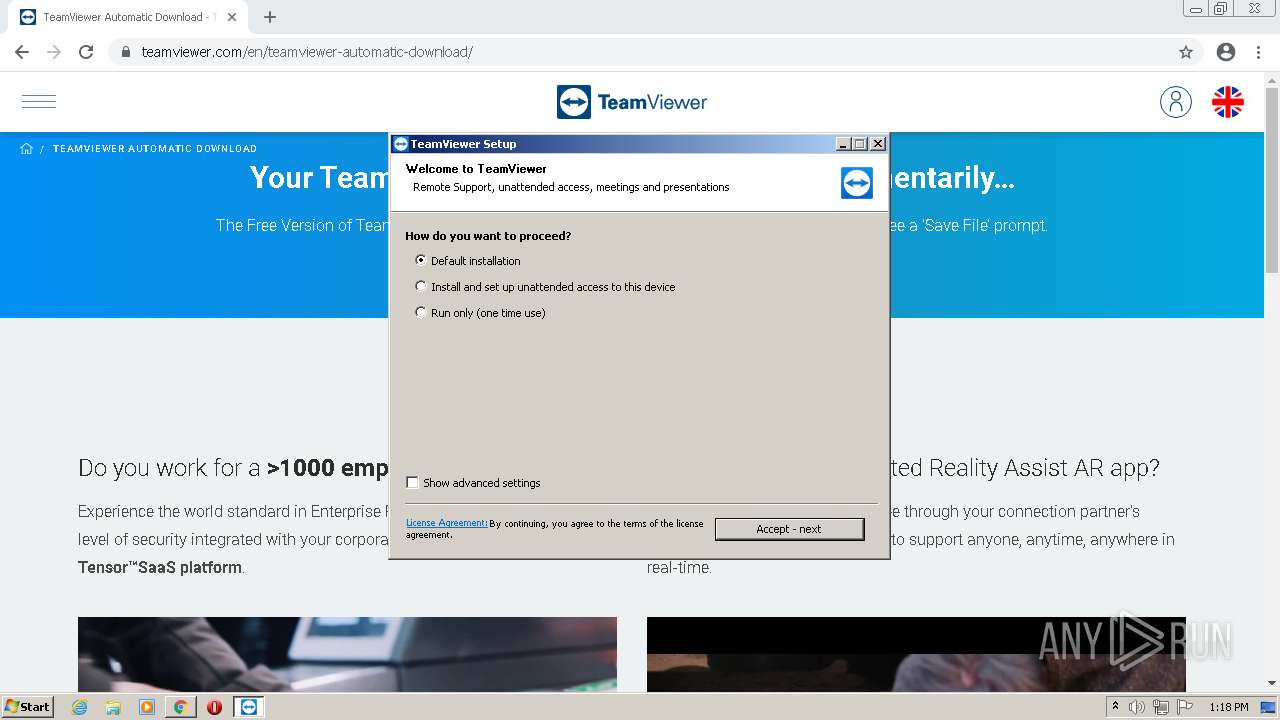
MALICIOUS
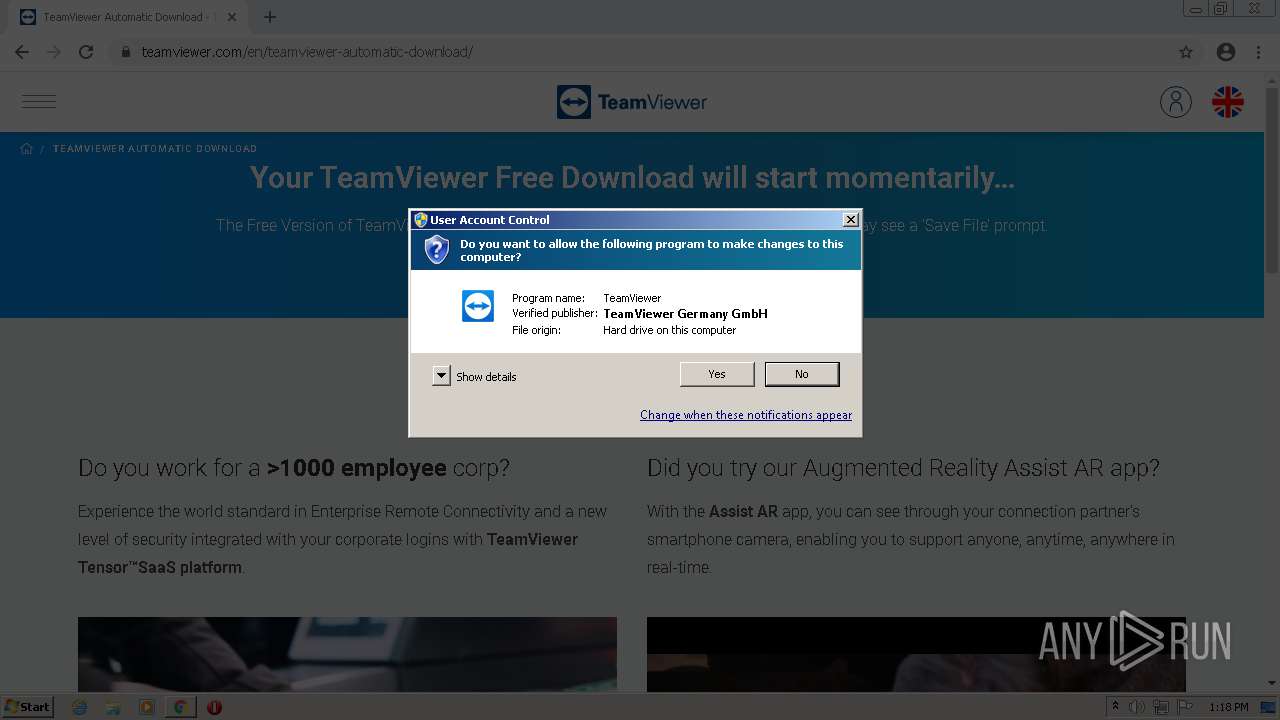
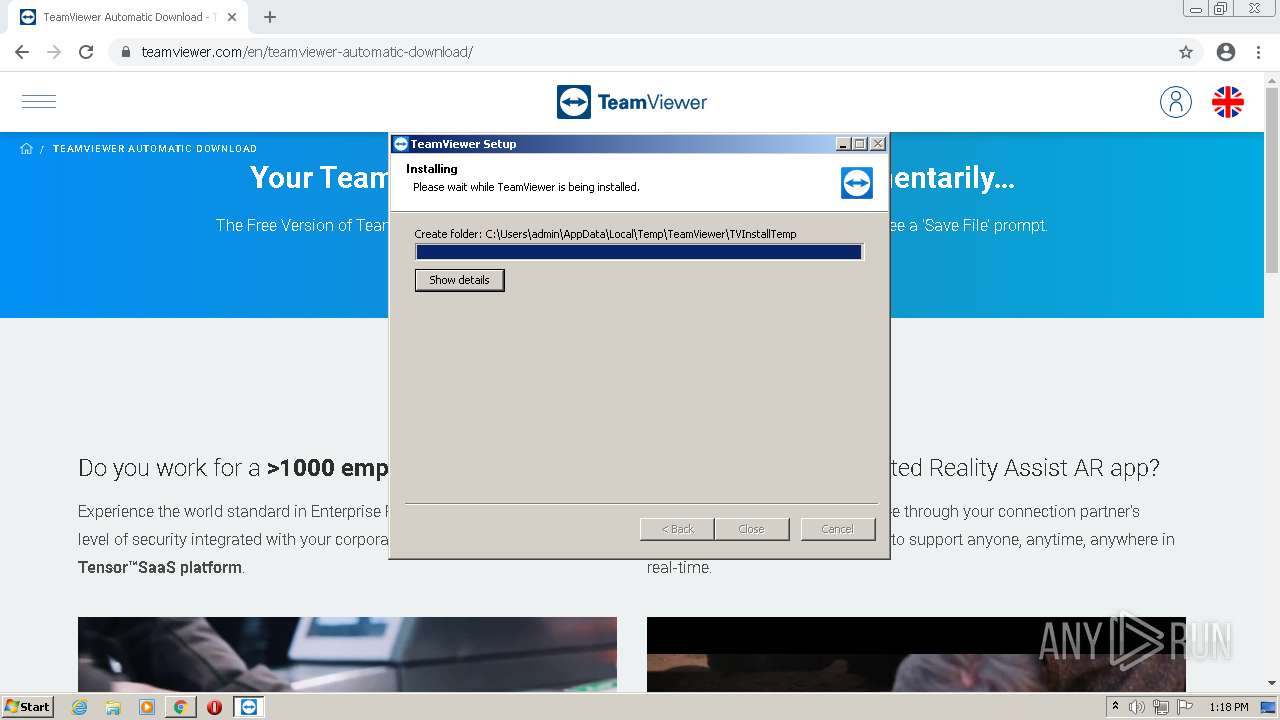
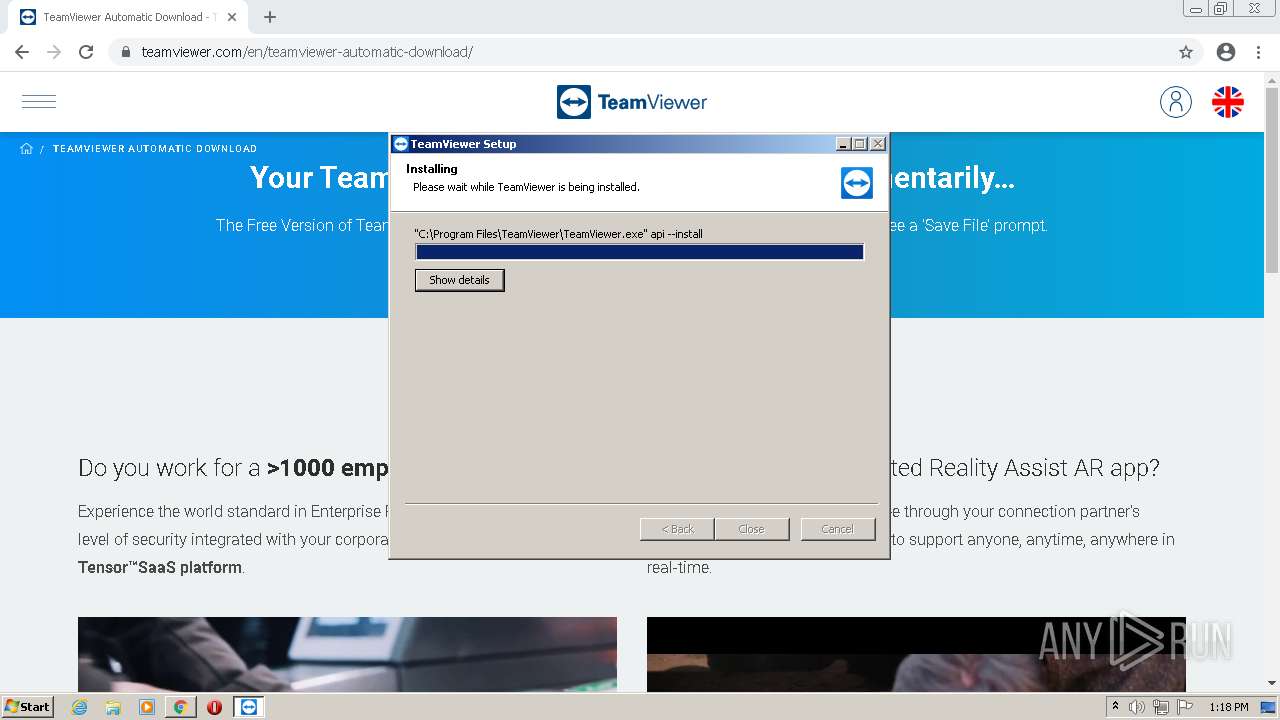
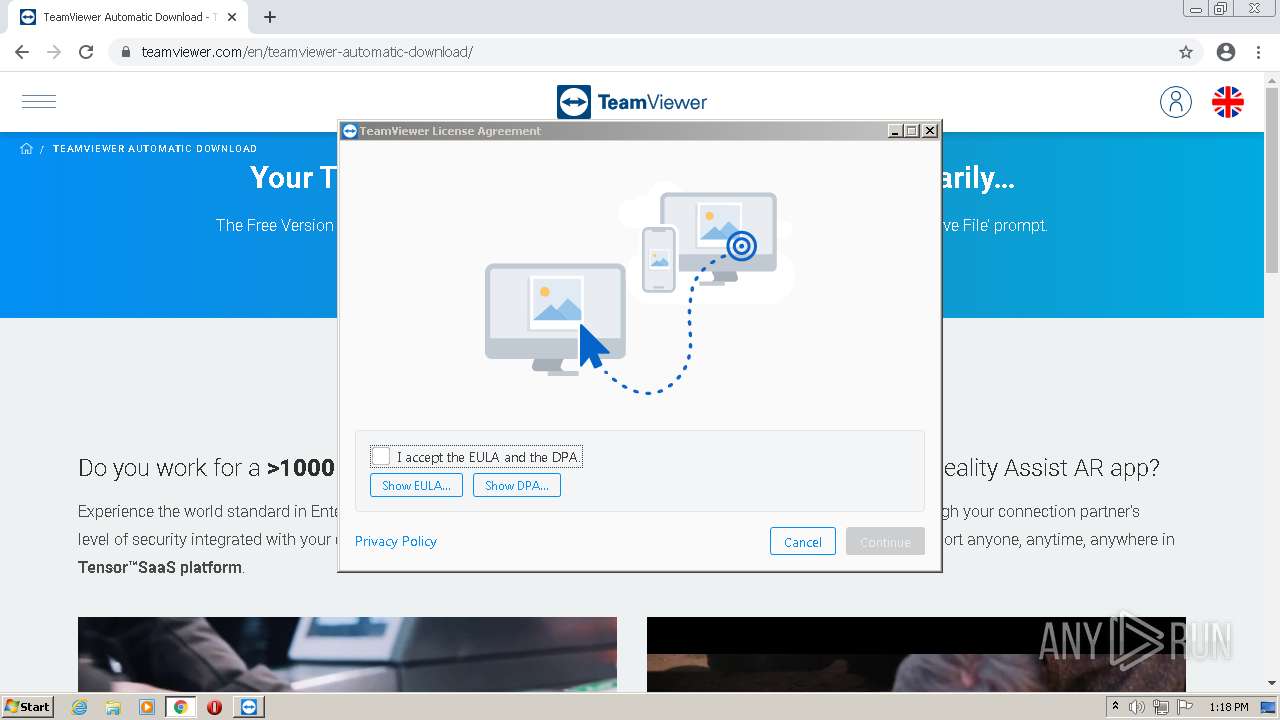
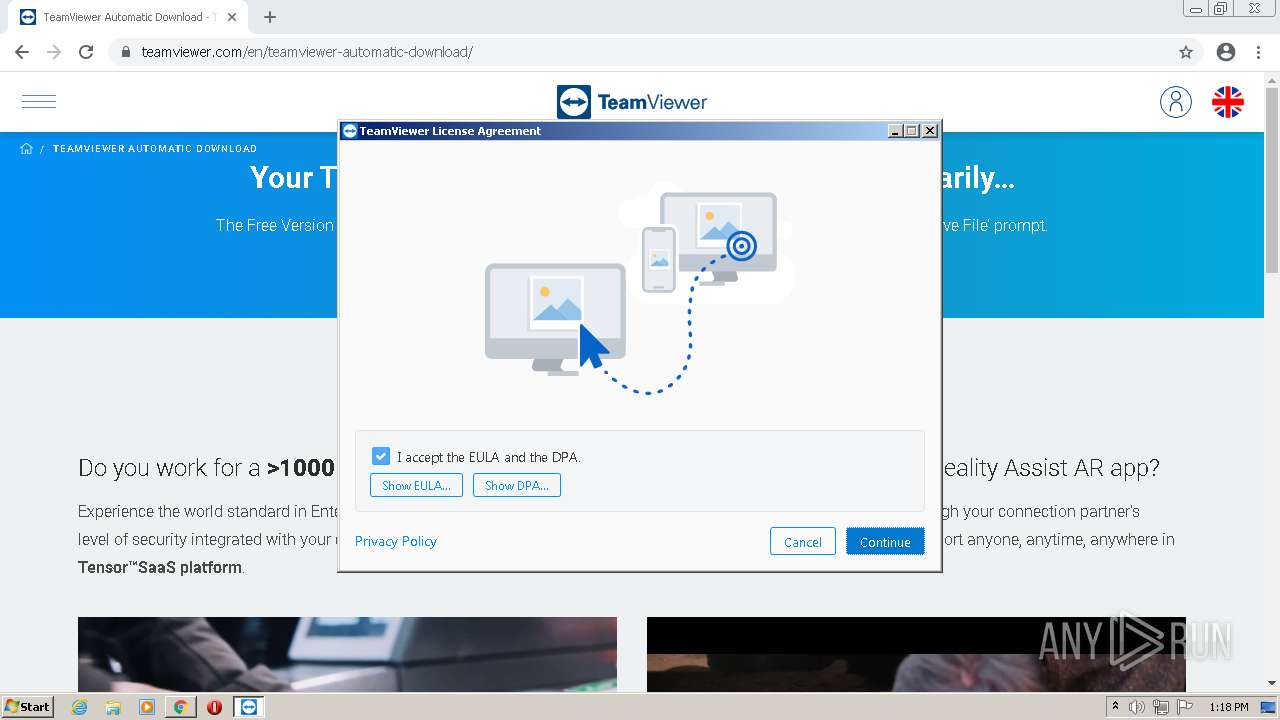
Application was dropped or rewritten from another process
- TeamViewer_Setup.exe (PID: 980)
- TeamViewer_.exe (PID: 3992)
- TeamViewer_.exe (PID: 2060)
- TeamViewer_Service.exe (PID: 2268)
- TeamViewer_Service.exe (PID: 404)
- tv_w32.exe (PID: 2652)
Drops executable file immediately after starts
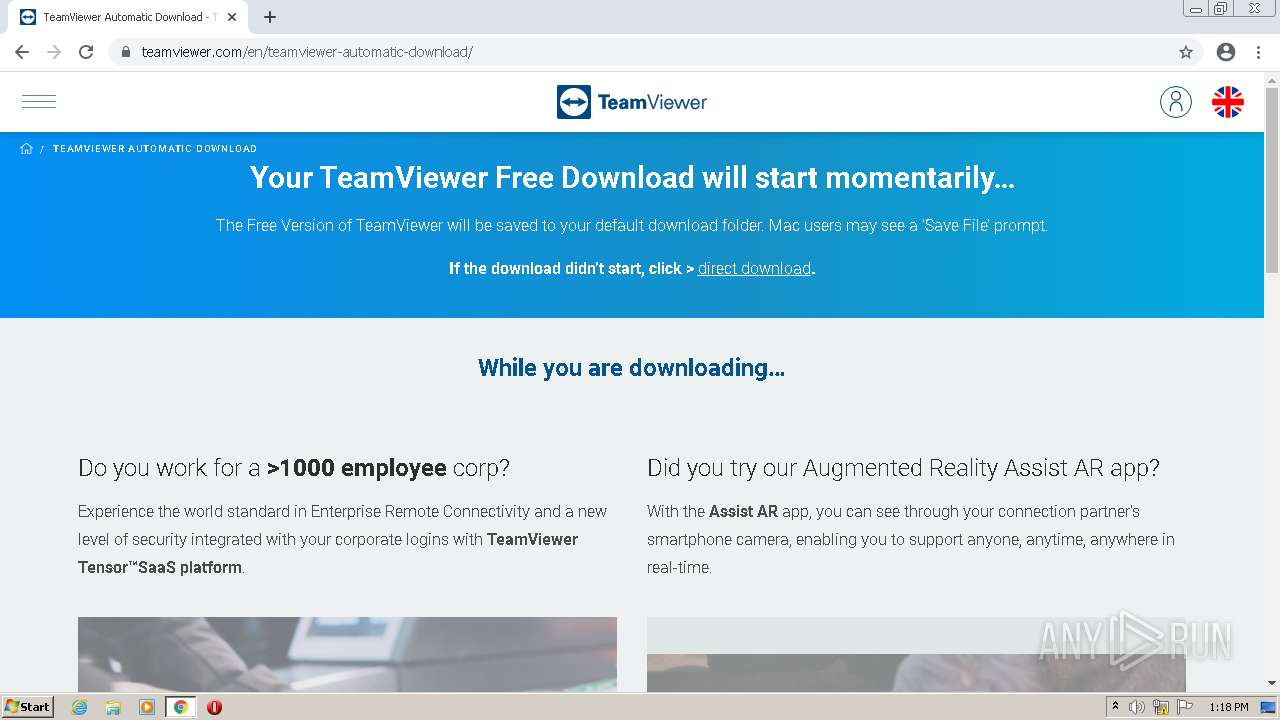
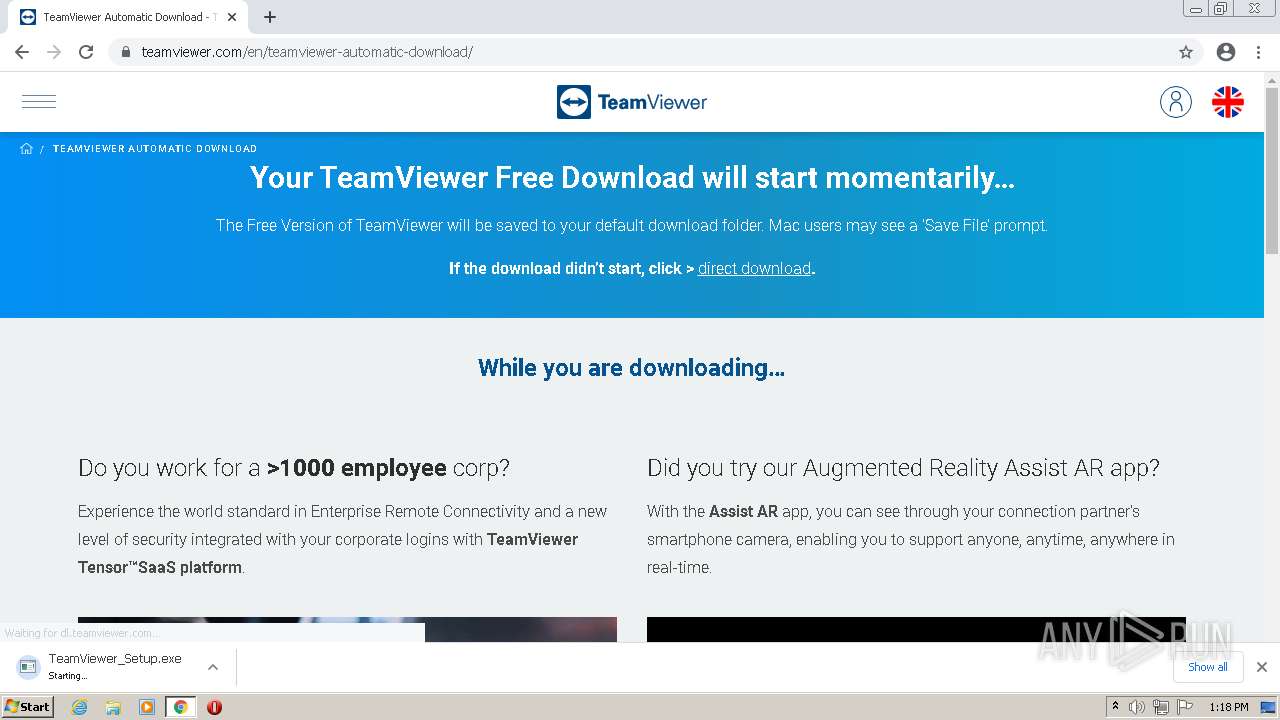
- TeamViewer_Setup.exe (PID: 980)
- TeamViewer_.exe (PID: 3992)
- TeamViewer_.exe (PID: 2060)
- chrome.exe (PID: 4004)
Loads dropped or rewritten executable
- TeamViewer_.exe (PID: 3992)
- TeamViewer_Setup.exe (PID: 980)
- TeamViewer_.exe (PID: 2060)
- tv_w32.exe (PID: 2652)
- TeamViewer.exe (PID: 1068)
Uses Task Scheduler to autorun other applications
- nsCFDC.tmp (PID: 2520)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3416)
- schtasks.exe (PID: 1472)
Registers / Runs the DLL via REGSVR32.EXE
- nsF633.tmp (PID: 3772)
Uses Task Scheduler to run other applications
- nsFD78.tmp (PID: 2412)
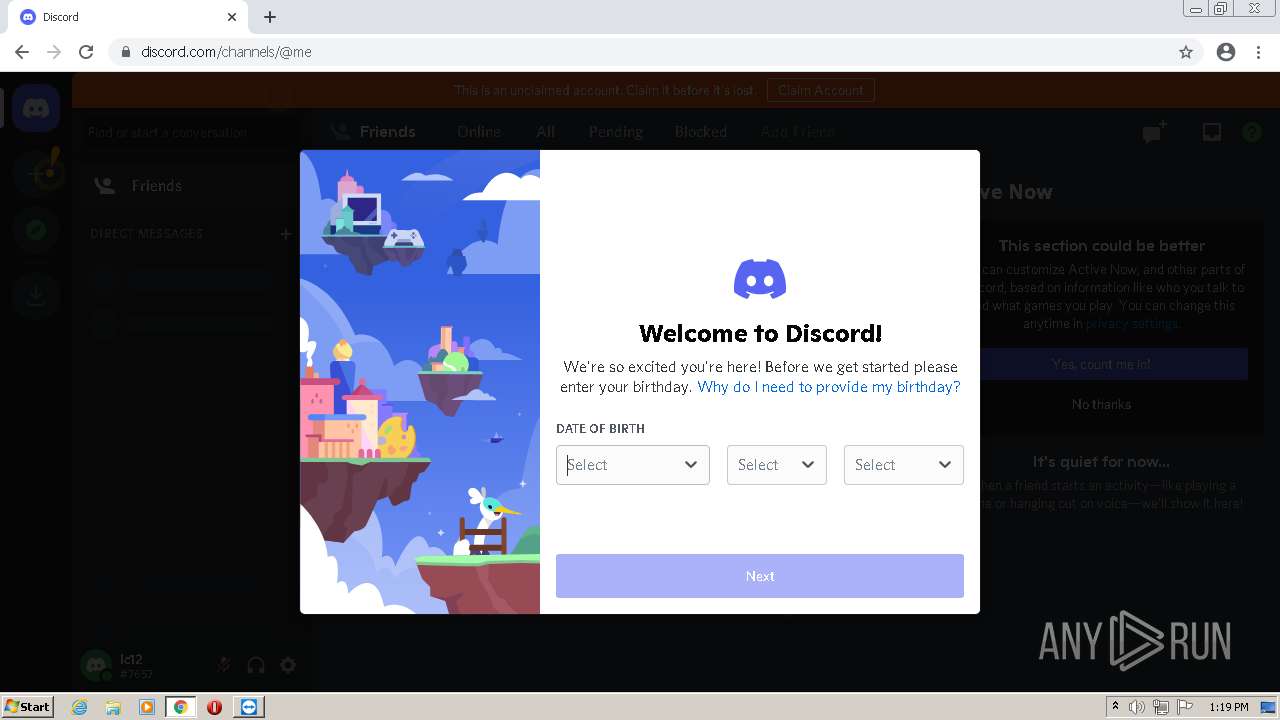
Steals credentials from Web Browsers
- TeamViewer.exe (PID: 1068)
Actions looks like stealing of personal data
- TeamViewer.exe (PID: 1068)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1008)
- TeamViewer_Setup.exe (PID: 980)
- TeamViewer_.exe (PID: 3992)
- TeamViewer_.exe (PID: 2060)
- chrome.exe (PID: 4004)
Checks supported languages
- TeamViewer_Setup.exe (PID: 980)
- TeamViewer_.exe (PID: 3992)
- TeamViewer_.exe (PID: 2060)
- nsCFDC.tmp (PID: 2520)
- nsF1DC.tmp (PID: 3508)
- TeamViewer_Service.exe (PID: 2268)
- nsF633.tmp (PID: 3772)
- nsFD78.tmp (PID: 2412)
- TeamViewer.exe (PID: 2736)
- nsF3A2.tmp (PID: 876)
- TeamViewer_Service.exe (PID: 404)
- TeamViewer.exe (PID: 1068)
- tv_w32.exe (PID: 2652)
Reads the computer name
- TeamViewer_Setup.exe (PID: 980)
- TeamViewer_.exe (PID: 3992)
- TeamViewer_.exe (PID: 2060)
- TeamViewer_Service.exe (PID: 2268)
- TeamViewer.exe (PID: 2736)
- TeamViewer_Service.exe (PID: 404)
- TeamViewer.exe (PID: 1068)
- tv_w32.exe (PID: 2652)
Application launched itself
- TeamViewer_.exe (PID: 3992)
Drops a file with too old compile date
- TeamViewer_.exe (PID: 3992)
- TeamViewer_.exe (PID: 2060)
Starts application with an unusual extension
- TeamViewer_.exe (PID: 2060)
Creates a directory in Program Files
- TeamViewer_.exe (PID: 2060)
Drops a file with a compile date too recent
- TeamViewer_.exe (PID: 2060)
Drops a file that was compiled in debug mode
- TeamViewer_.exe (PID: 2060)
- chrome.exe (PID: 4004)
Creates files in the user directory
- TeamViewer_.exe (PID: 2060)
- TeamViewer_Service.exe (PID: 2268)
Creates files in the program directory
- TeamViewer_.exe (PID: 2060)
- TeamViewer_Service.exe (PID: 404)
Changes default file association
- TeamViewer_.exe (PID: 2060)
Creates a software uninstall entry
- TeamViewer_.exe (PID: 2060)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1536)
Creates files in the Windows directory
- TeamViewer_.exe (PID: 2060)
- TeamViewer_Service.exe (PID: 404)
Executed as Windows Service
- TeamViewer_Service.exe (PID: 404)
Reads Microsoft Outlook installation path
- TeamViewer.exe (PID: 1068)
- iexplore.exe (PID: 3572)
Starts Internet Explorer
- TeamViewer.exe (PID: 1068)
Reads Windows owner or organization settings
- TeamViewer.exe (PID: 1068)
Reads the time zone
- TeamViewer_Service.exe (PID: 404)
Reads the Windows organization settings
- TeamViewer.exe (PID: 1068)
INFO
Checks supported languages
- chrome.exe (PID: 3220)
- chrome.exe (PID: 280)
- chrome.exe (PID: 1008)
- chrome.exe (PID: 452)
- chrome.exe (PID: 768)
- chrome.exe (PID: 3944)
- chrome.exe (PID: 1328)
- chrome.exe (PID: 3332)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 1892)
- chrome.exe (PID: 1116)
- chrome.exe (PID: 880)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 124)
- chrome.exe (PID: 2584)
- schtasks.exe (PID: 3416)
- chrome.exe (PID: 612)
- regsvr32.exe (PID: 1536)
- schtasks.exe (PID: 1472)
- iexplore.exe (PID: 3280)
- iexplore.exe (PID: 3572)
- chrome.exe (PID: 1272)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 3988)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 4032)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 4008)
- chrome.exe (PID: 2300)
- chrome.exe (PID: 2204)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 980)
- chrome.exe (PID: 3732)
- firefox.exe (PID: 2708)
- firefox.exe (PID: 4024)
- firefox.exe (PID: 3516)
- firefox.exe (PID: 2728)
- firefox.exe (PID: 2088)
- firefox.exe (PID: 2624)
- firefox.exe (PID: 2096)
- firefox.exe (PID: 2080)
- chrome.exe (PID: 4004)
Reads the hosts file
- chrome.exe (PID: 280)
- chrome.exe (PID: 1008)
Reads the computer name
- chrome.exe (PID: 1008)
- chrome.exe (PID: 452)
- chrome.exe (PID: 3944)
- chrome.exe (PID: 280)
- chrome.exe (PID: 3332)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 1116)
- chrome.exe (PID: 2584)
- schtasks.exe (PID: 3416)
- chrome.exe (PID: 612)
- schtasks.exe (PID: 1472)
- iexplore.exe (PID: 3280)
- iexplore.exe (PID: 3572)
- chrome.exe (PID: 1272)
- chrome.exe (PID: 980)
- chrome.exe (PID: 3732)
- firefox.exe (PID: 4024)
- firefox.exe (PID: 3516)
- firefox.exe (PID: 2728)
- firefox.exe (PID: 2088)
- firefox.exe (PID: 2096)
- firefox.exe (PID: 2624)
- firefox.exe (PID: 2080)
Application launched itself
- chrome.exe (PID: 1008)
- iexplore.exe (PID: 3280)
- firefox.exe (PID: 2708)
- firefox.exe (PID: 2088)
Reads settings of System Certificates
- chrome.exe (PID: 280)
- chrome.exe (PID: 1008)
- TeamViewer_Service.exe (PID: 2268)
- TeamViewer.exe (PID: 2736)
- TeamViewer_Service.exe (PID: 404)
- TeamViewer.exe (PID: 1068)
- tv_w32.exe (PID: 2652)
- iexplore.exe (PID: 3280)
Checks Windows Trust Settings
- chrome.exe (PID: 1008)
- TeamViewer_Service.exe (PID: 2268)
- TeamViewer.exe (PID: 2736)
- TeamViewer_Service.exe (PID: 404)
- TeamViewer.exe (PID: 1068)
- tv_w32.exe (PID: 2652)
- iexplore.exe (PID: 3280)
Reads Microsoft Office registry keys
- TeamViewer_.exe (PID: 3992)
- TeamViewer_.exe (PID: 2060)
Reads the date of Windows installation
- chrome.exe (PID: 612)
- iexplore.exe (PID: 3280)
Changes internet zones settings
- iexplore.exe (PID: 3280)
Reads internet explorer settings
- iexplore.exe (PID: 3572)
Manual execution by user
- firefox.exe (PID: 2708)
Reads CPU info
- firefox.exe (PID: 2088)
Creates files in the user directory
- firefox.exe (PID: 2088)
Creates files in the program directory
- firefox.exe (PID: 2088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
109
Monitored processes
62
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=1716 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1048,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1244 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 404 | "C:\Program Files\TeamViewer\TeamViewer_Service.exe" | C:\Program Files\TeamViewer\TeamViewer_Service.exe | services.exe | ||||||||||||
User: SYSTEM Company: TeamViewer Germany GmbH Integrity Level: SYSTEM Description: TeamViewer Exit code: 0 Version: 15.25.8.0 Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1052 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3572 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 876 | "C:\Users\admin\AppData\Local\Temp\nsxCEF1.tmp\nsF3A2.tmp" "C:\Program Files\TeamViewer\TeamViewer.exe" api --install | C:\Users\admin\AppData\Local\Temp\nsxCEF1.tmp\nsF3A2.tmp | — | TeamViewer_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3416 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 980 | "C:\Users\admin\Downloads\TeamViewer_Setup.exe" | C:\Users\admin\Downloads\TeamViewer_Setup.exe | chrome.exe | ||||||||||||
User: admin Company: TeamViewer Germany GmbH Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1048,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=2940 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
61 251
Read events
60 021
Write events
1 217
Delete events
13
Modification events
| (PID) Process: | (1008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1008) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
126
Suspicious files
147
Text files
184
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61C86B7B-3F0.pma | — | |
MD5:— | SHA256:— | |||
| 1008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 1008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 1008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0bc7855a-ad4e-41af-a4f8-542bf008e2a4.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19331c.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 1008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF1934f1.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 1008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF19334b.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 1008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
129
DNS requests
154
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6ns375f2pcxjd6lc6gqc772joq_2021.11.28.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2021.11.28.1202_all_adkem2jc7ozcg3aprfifzzq6ee4q.crx3 | US | — | — | whitelisted |
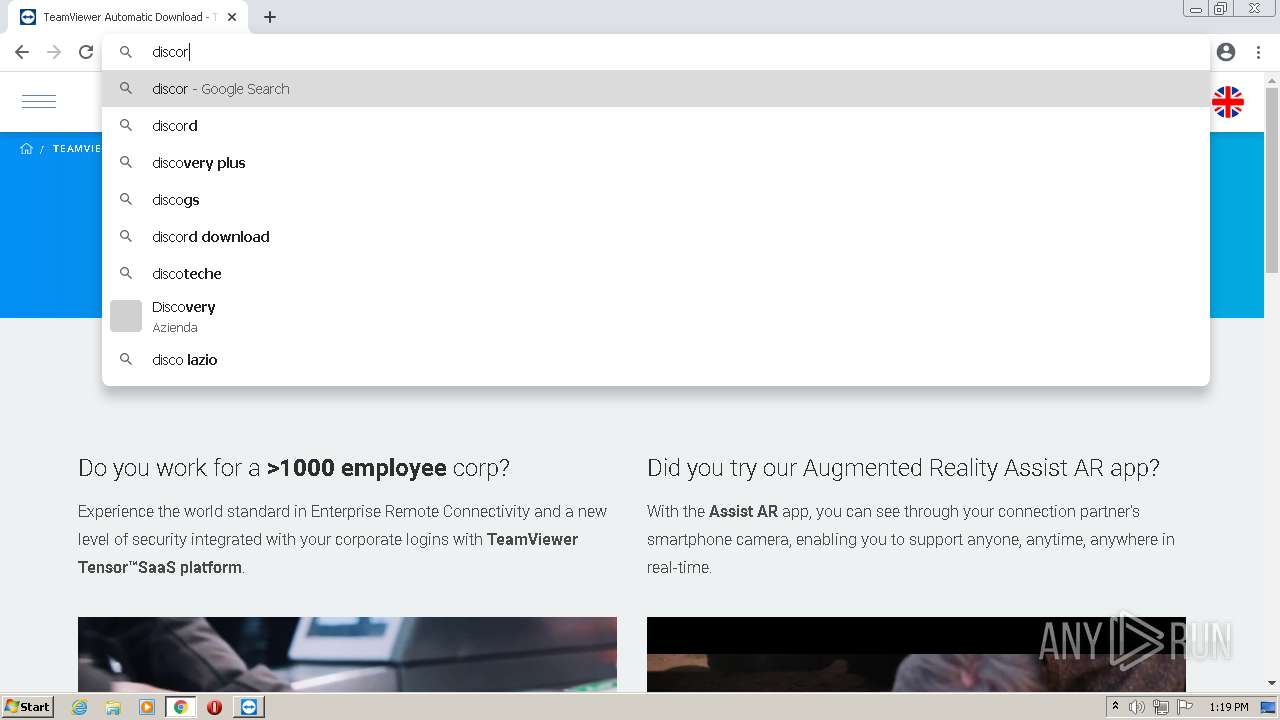
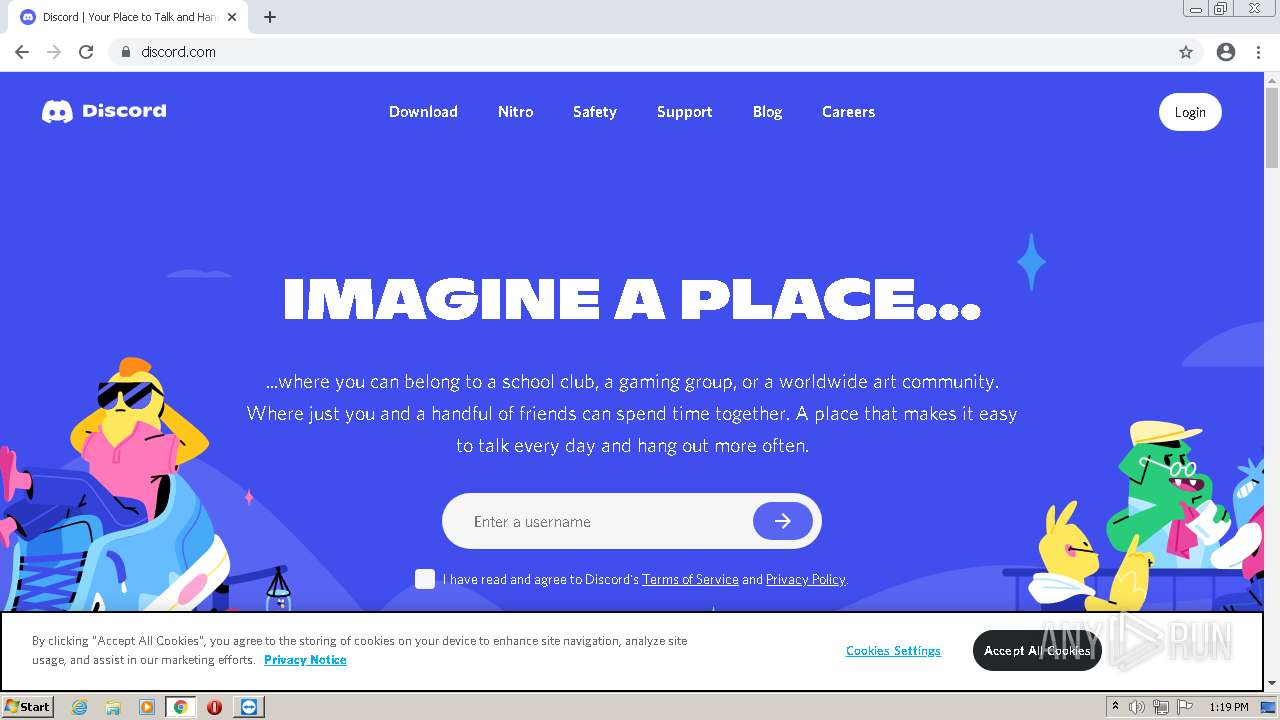
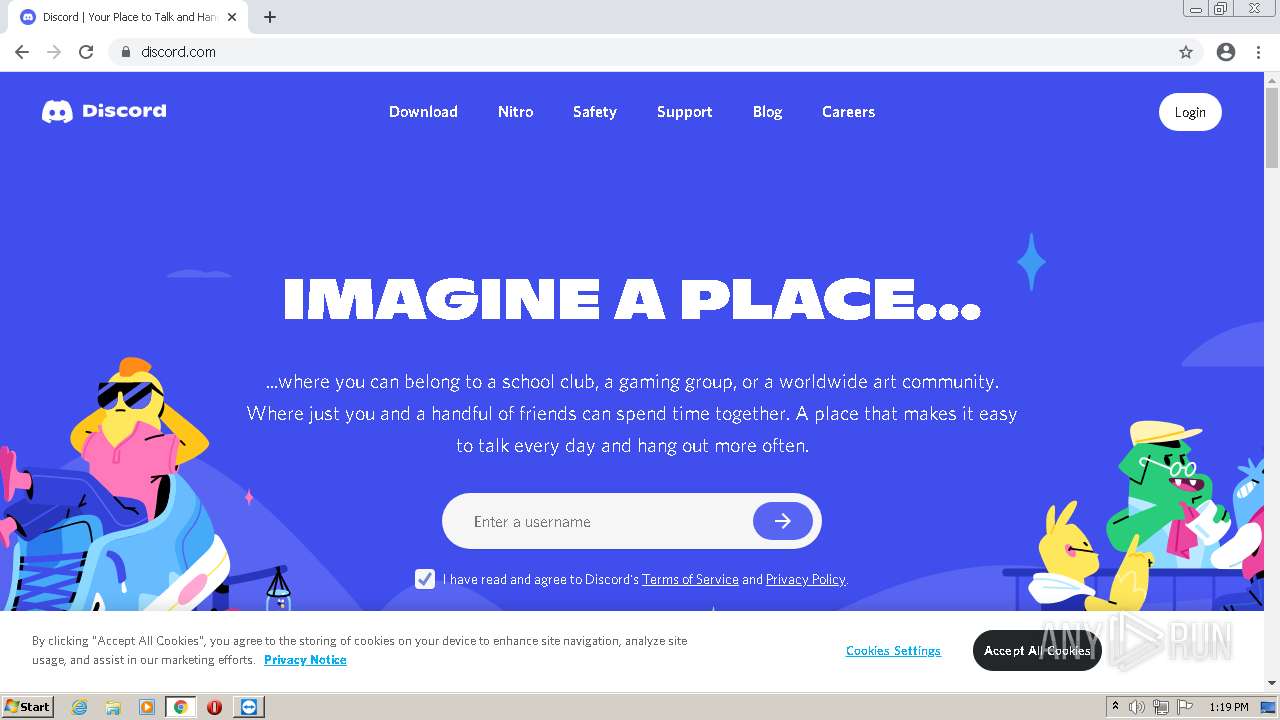
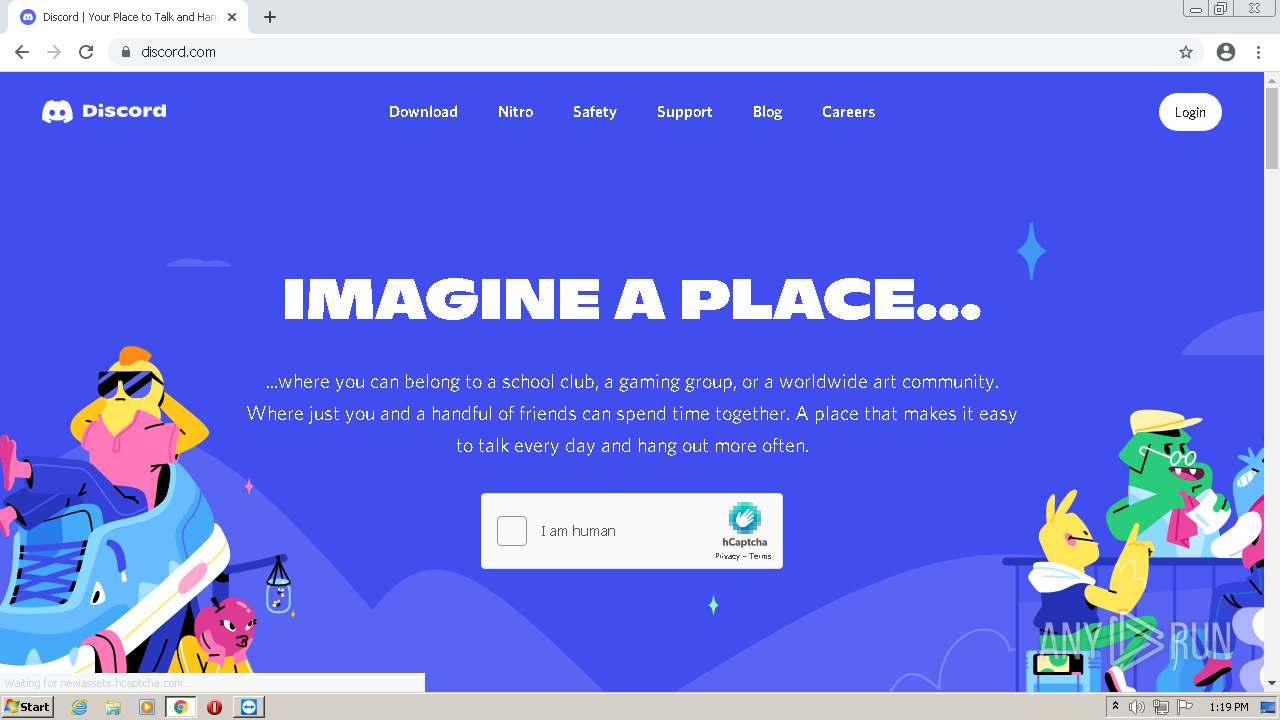
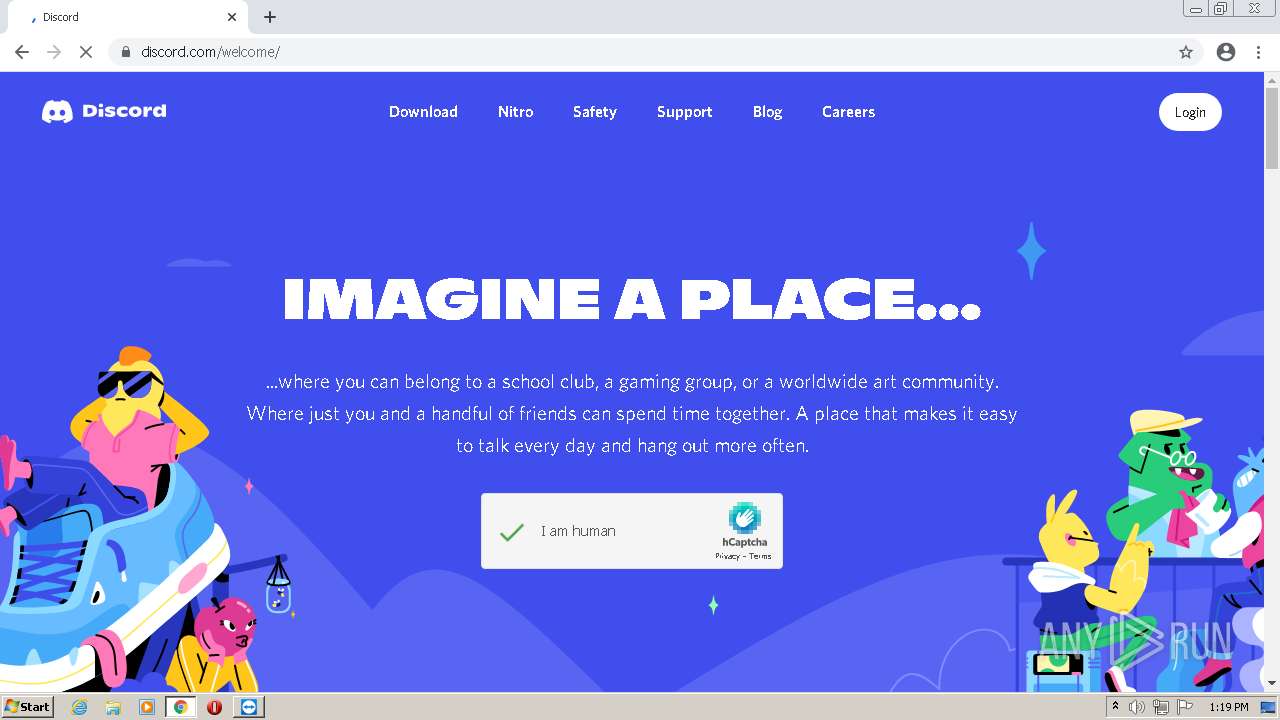
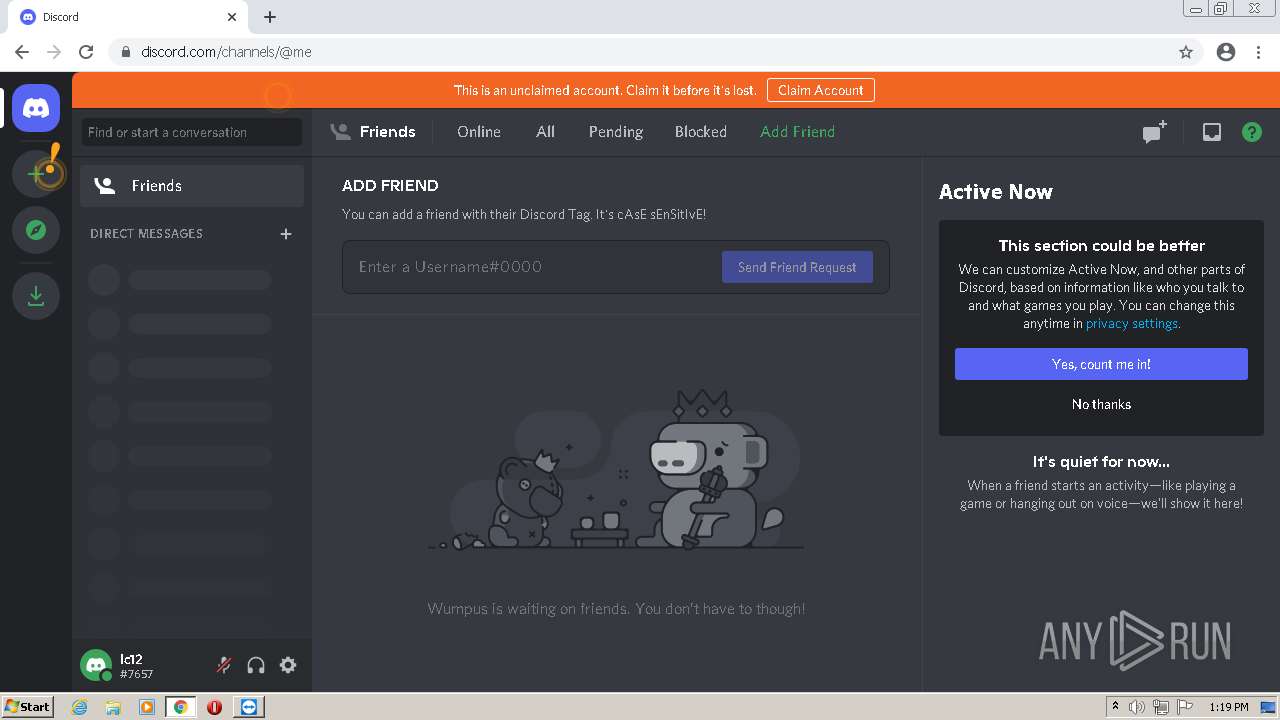
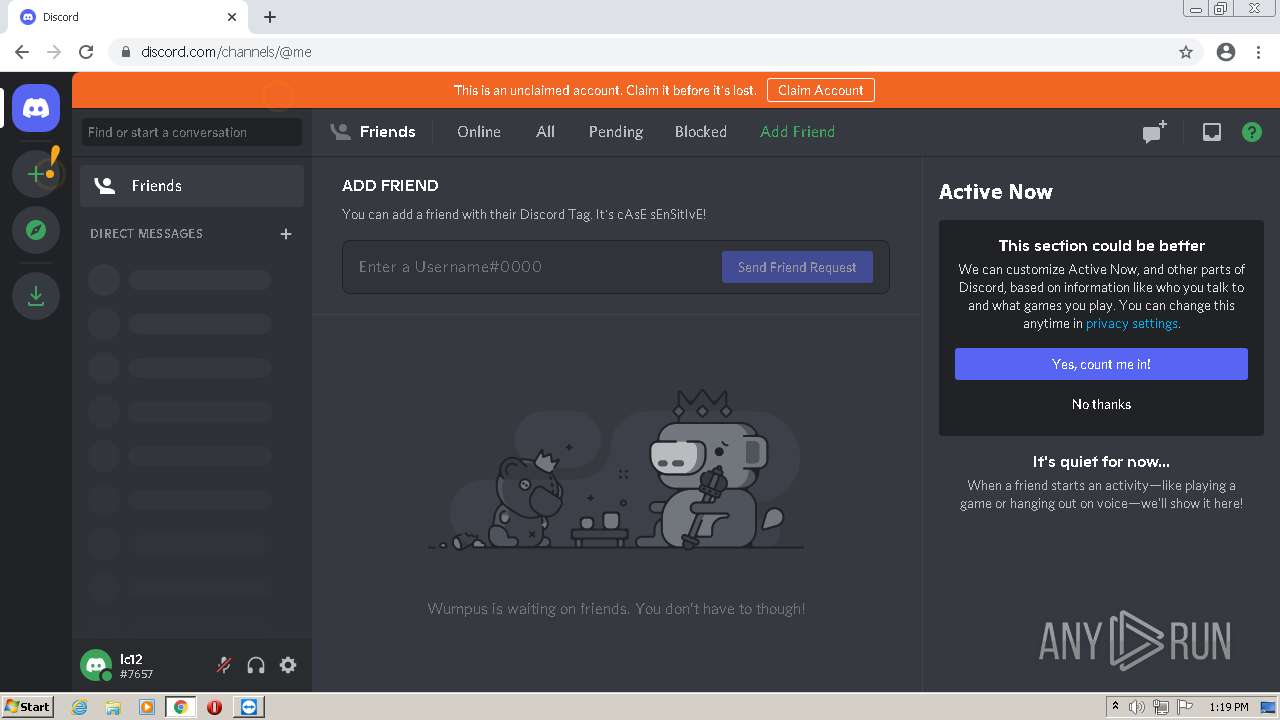
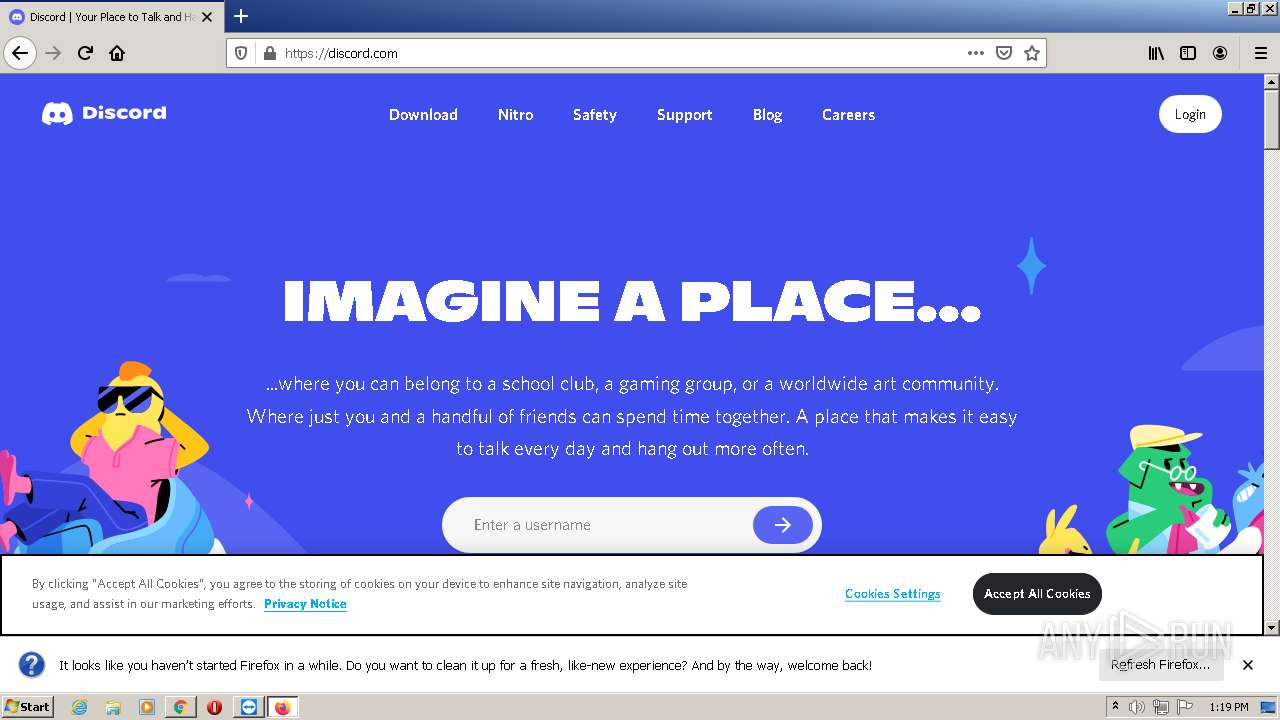
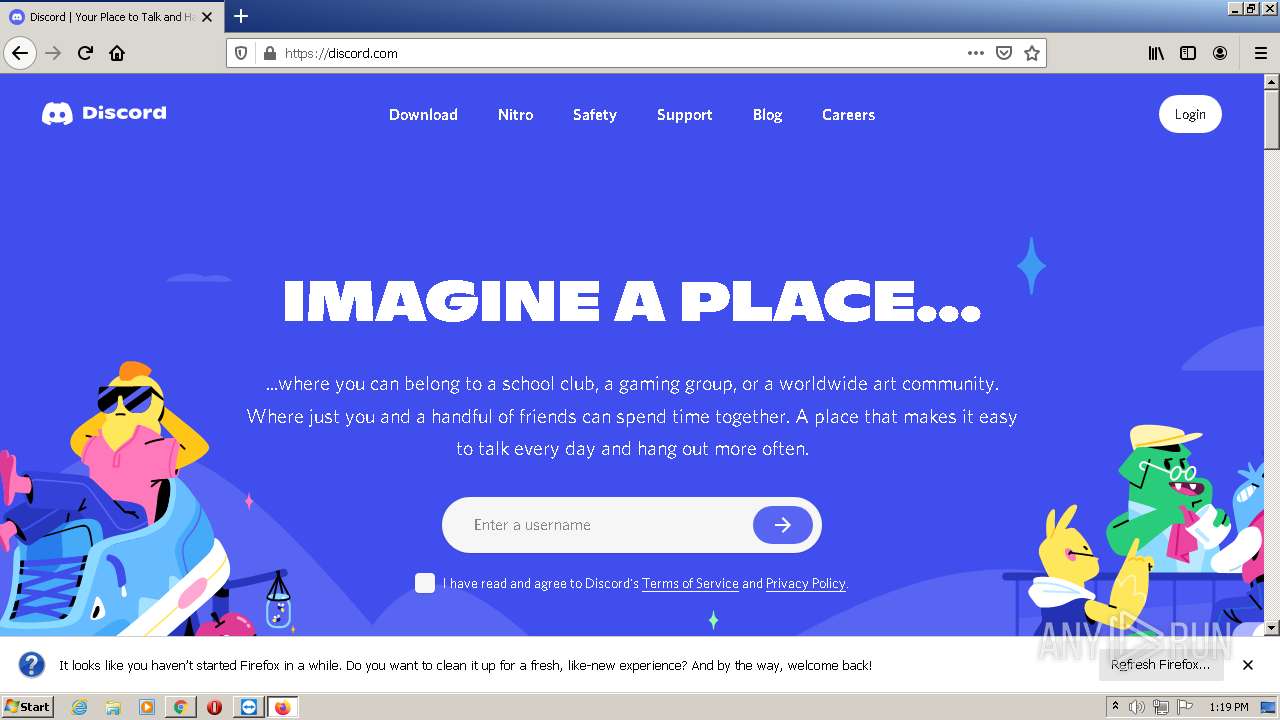
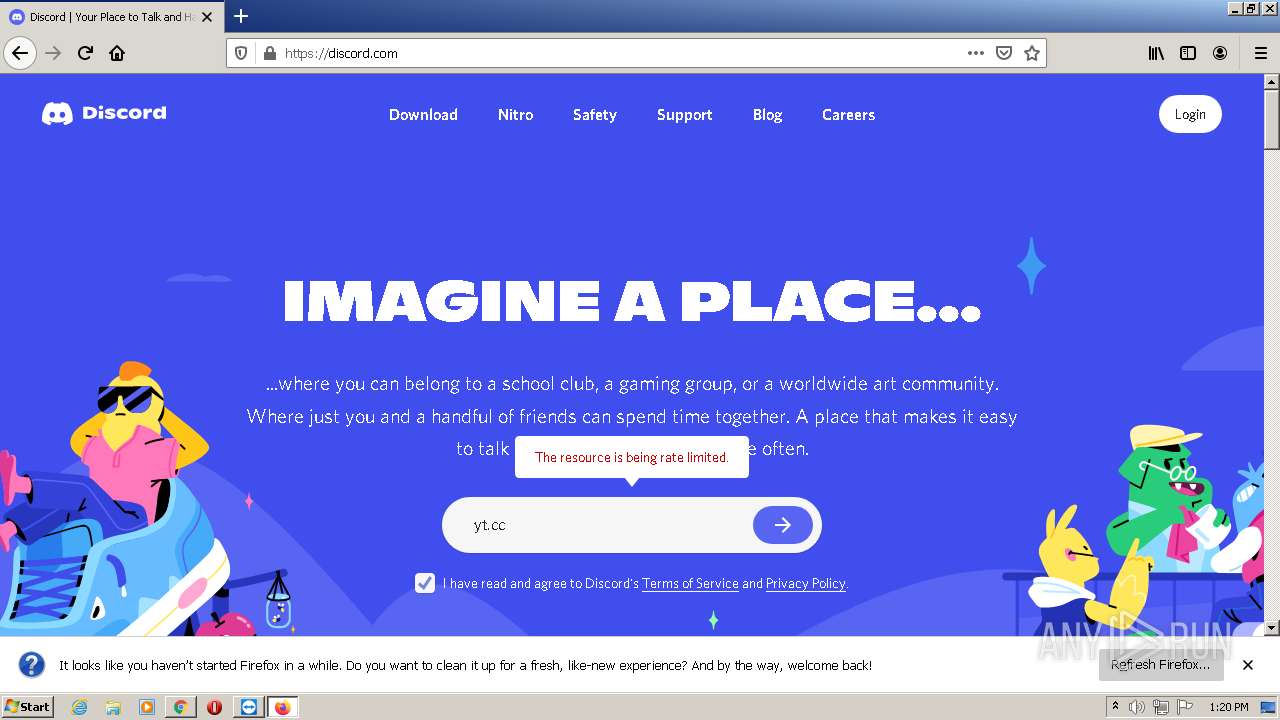
2088 | firefox.exe | GET | 301 | 162.159.135.232:80 | http://discord.com/ | unknown | — | — | whitelisted |
280 | chrome.exe | GET | 301 | 162.159.138.232:80 | http://discord.com/ | unknown | — | — | whitelisted |
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/etfhywtptnfps2qeuyx6p57rsa_47/khaoiebndkojlmppeemjhbpbandiljpe_47_win_eiam27nsc3cmgynazgpf5duaty.crx3 | US | binary | 3.93 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6ns375f2pcxjd6lc6gqc772joq_2021.11.28.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2021.11.28.1202_all_adkem2jc7ozcg3aprfifzzq6ee4q.crx3 | US | binary | 5.62 Kb | whitelisted |
1068 | TeamViewer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAilokbNS1yMg9cCtLurU0k%3D | US | der | 471 b | whitelisted |
2088 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2088 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 279 b | whitelisted |
2088 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
280 | chrome.exe | 104.16.63.16:443 | www.teamviewer.com | Cloudflare Inc | US | shared |
280 | chrome.exe | 151.101.2.217:443 | cdn.speedcurve.com | Fastly | US | suspicious |
280 | chrome.exe | 142.250.185.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
280 | chrome.exe | 104.16.148.64:443 | cdn.cookielaw.org | Cloudflare Inc | US | unknown |
280 | chrome.exe | 104.16.62.16:443 | www.teamviewer.com | Cloudflare Inc | US | shared |
280 | chrome.exe | 142.250.184.234:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
280 | chrome.exe | 143.204.98.80:443 | widget.trustpilot.com | — | US | suspicious |
280 | chrome.exe | 2.16.186.32:443 | snap.licdn.com | Akamai International B.V. | — | whitelisted |
280 | chrome.exe | 157.240.20.19:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
280 | chrome.exe | 151.101.1.131:443 | 06855245974849538a4442f956b93b64.js.ubembed.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.teamviewer.com |
| shared |
cdn.speedcurve.com |
| whitelisted |
static.teamviewer.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
cdn.cookielaw.org |
| whitelisted |
www.google-analytics.com |
| whitelisted |
widget.trustpilot.com |
| shared |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2088 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2088 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |