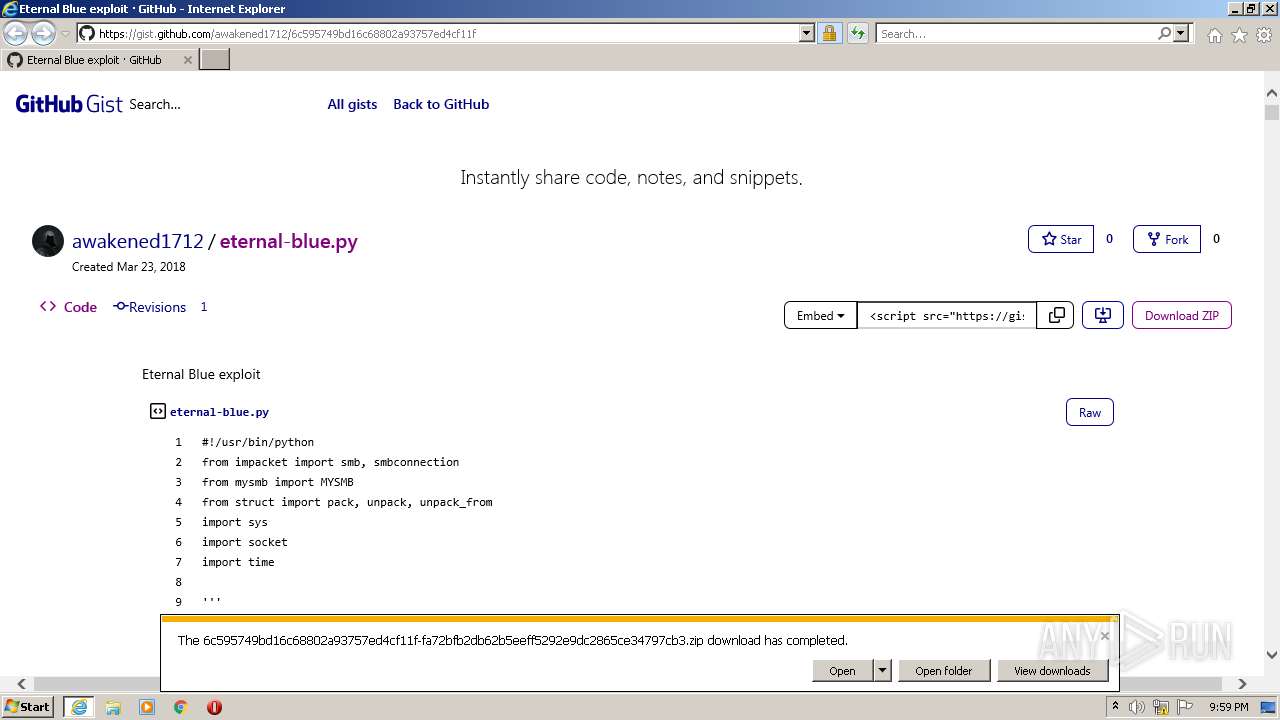
| URL: | https://www.bing.com/ck/a?!&&p=3fed2d82b0618f8dd3ed99040d3b5ee0fad5b5b9d9b0d0018a9e783c200b45dcJmltdHM9MTY1MzA4MDMyNyZpZ3VpZD1mYzlkMzFjNy0wYWI1LTQ3YTMtOGU1NC0yMjY4YTJhYmVhYjkmaW5zaWQ9NTMzOQ&ptn=3&fclid=a445abf2-d87f-11ec-8c74-12a6b2db7071&u=a1aHR0cHM6Ly9naXN0LmdpdGh1Yi5jb20vYXdha2VuZWQxNzEyLzZjNTk1NzQ5YmQxNmM2ODgwMmE5Mzc1N2VkNGNmMTFm&ntb=1 |
| Full analysis: | https://app.any.run/tasks/40d3835b-0d49-4add-87e0-5250f07b5fe0 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 20:59:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 39FB5914C287C64C047AE958A1B98C39 |
| SHA1: | B8A8BDA38D5A753F0187249D4C77470F6ECE0B6C |
| SHA256: | C8B04A3A3DCA889580B4A05444B01F04E111AE94C0176C191B1C380123979B99 |
| SSDEEP: | 6:2OLsRermktRCVJQLGGQJLdPhcrOWjqbODP3chl7eYrbAIxpCtzLMZ:2OBMJQWk5jVrMhxB/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3100)
Reads the computer name
- WinRAR.exe (PID: 1320)
Executed via COM
- DllHost.exe (PID: 2308)
Checks supported languages
- WinRAR.exe (PID: 1320)
INFO
Reads the computer name
- iexplore.exe (PID: 2060)
- iexplore.exe (PID: 3100)
- DllHost.exe (PID: 2308)
Changes internet zones settings
- iexplore.exe (PID: 2060)
Application launched itself
- iexplore.exe (PID: 2060)
Reads settings of System Certificates
- iexplore.exe (PID: 3100)
- iexplore.exe (PID: 2060)
Checks supported languages
- iexplore.exe (PID: 2060)
- iexplore.exe (PID: 3100)
- DllHost.exe (PID: 2308)
Checks Windows Trust Settings
- iexplore.exe (PID: 3100)
- iexplore.exe (PID: 2060)
Reads internet explorer settings
- iexplore.exe (PID: 3100)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3100)
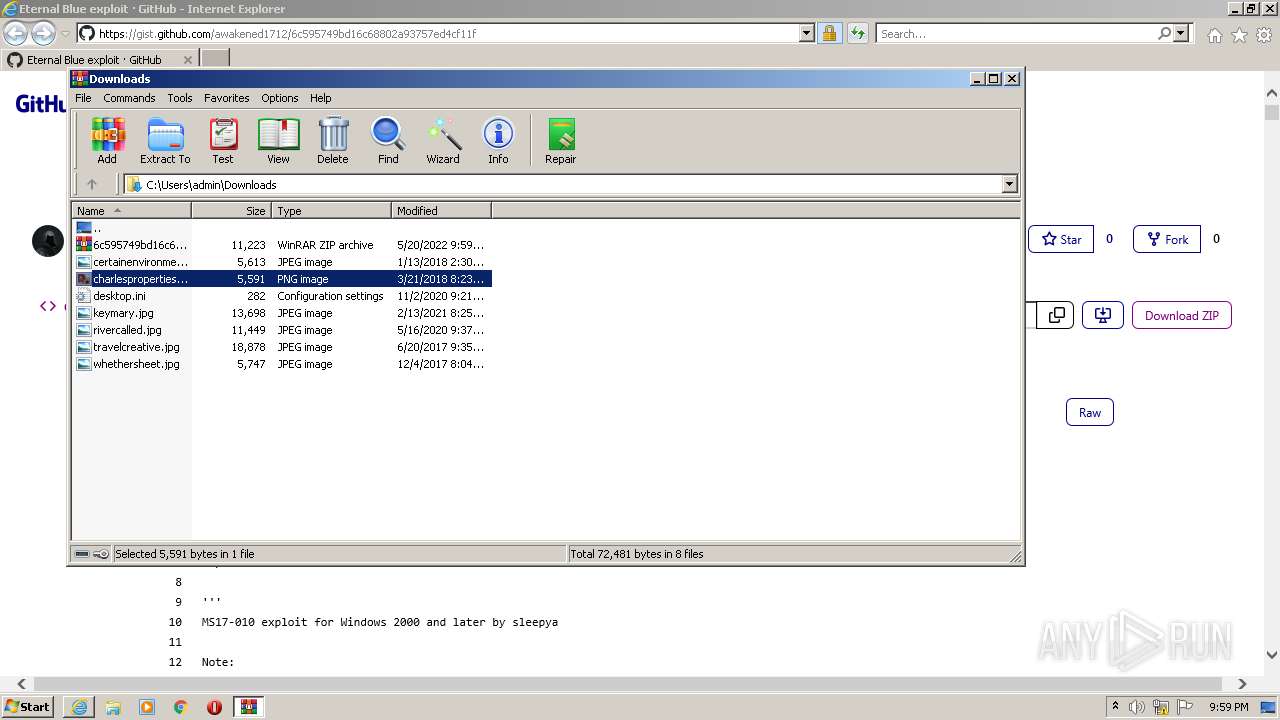
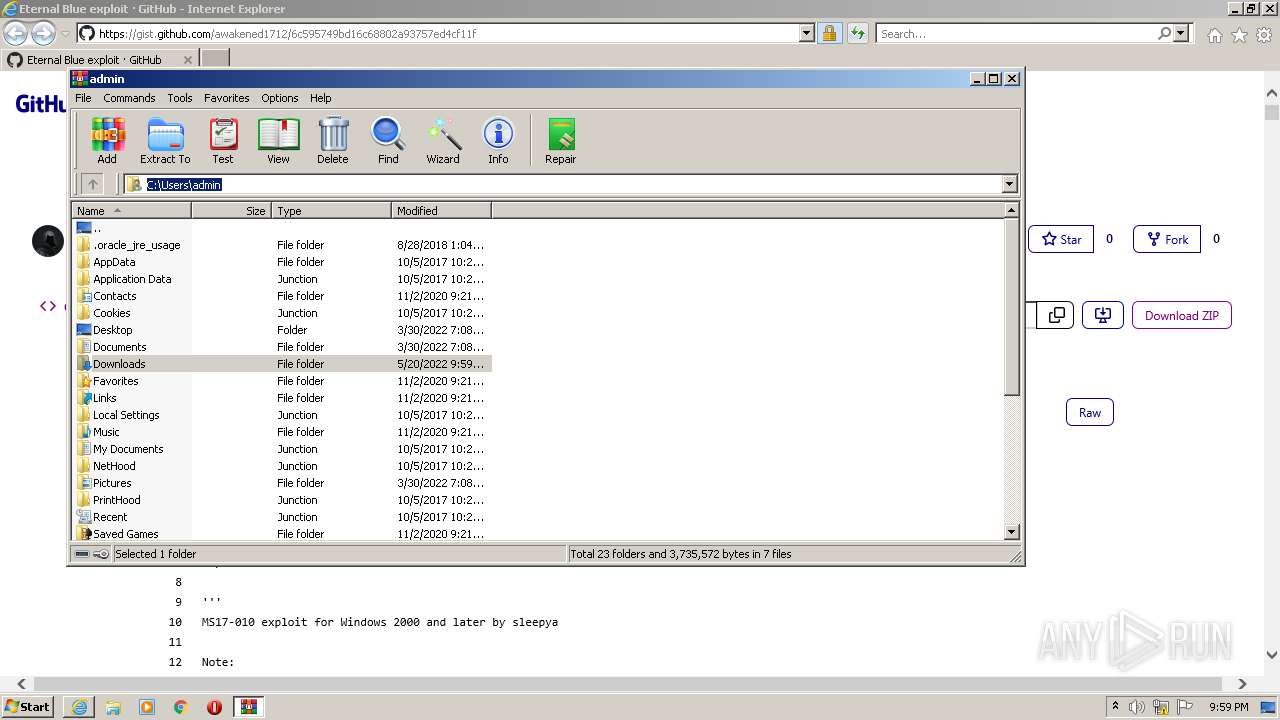
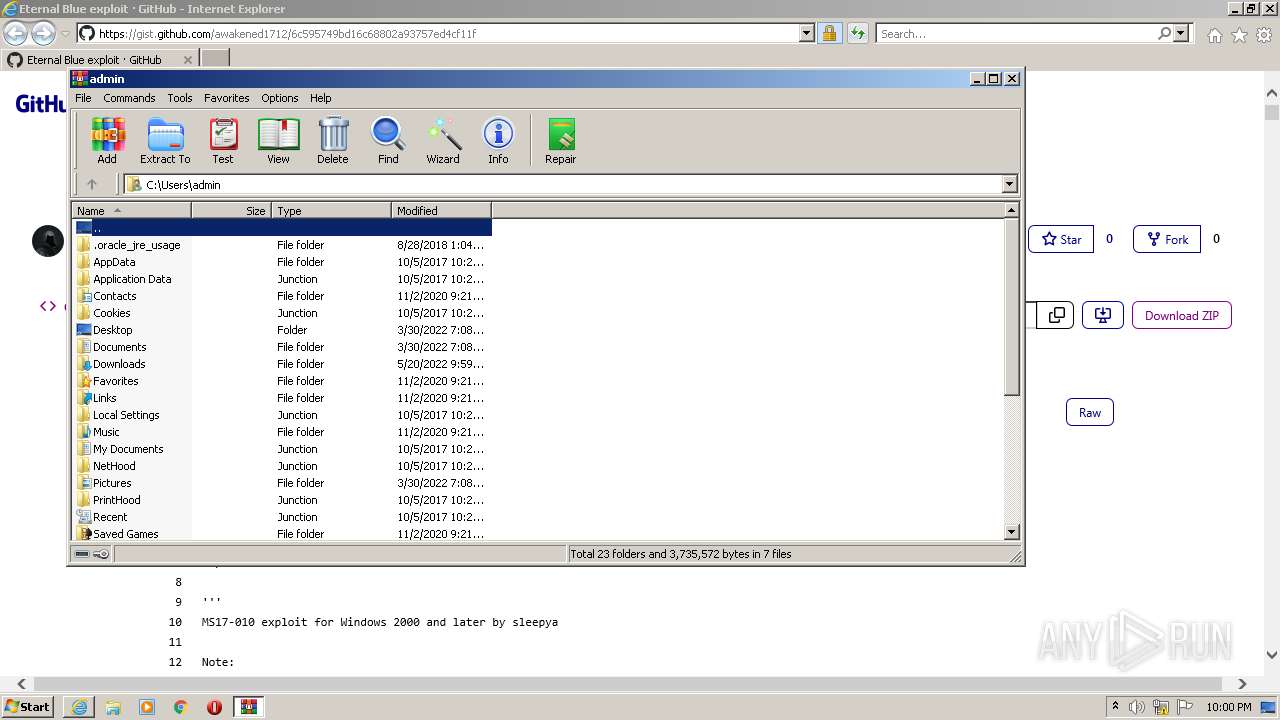
Creates files in the user directory
- iexplore.exe (PID: 3100)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
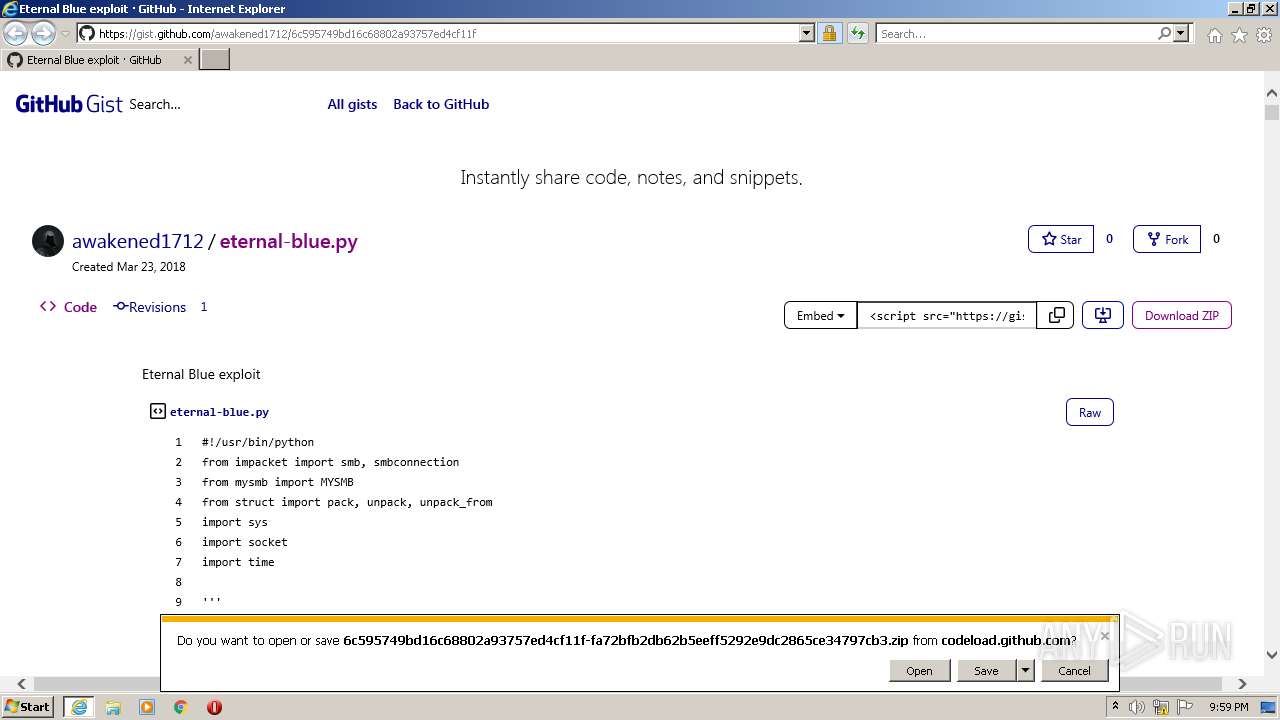
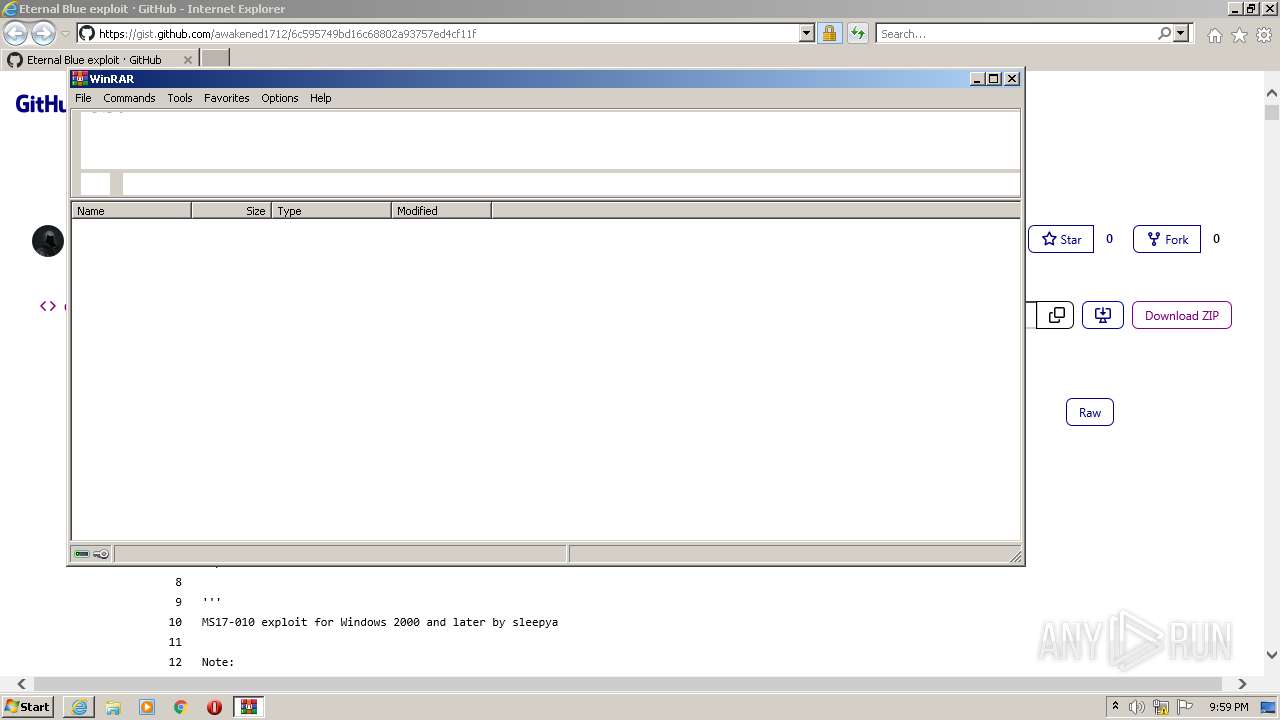
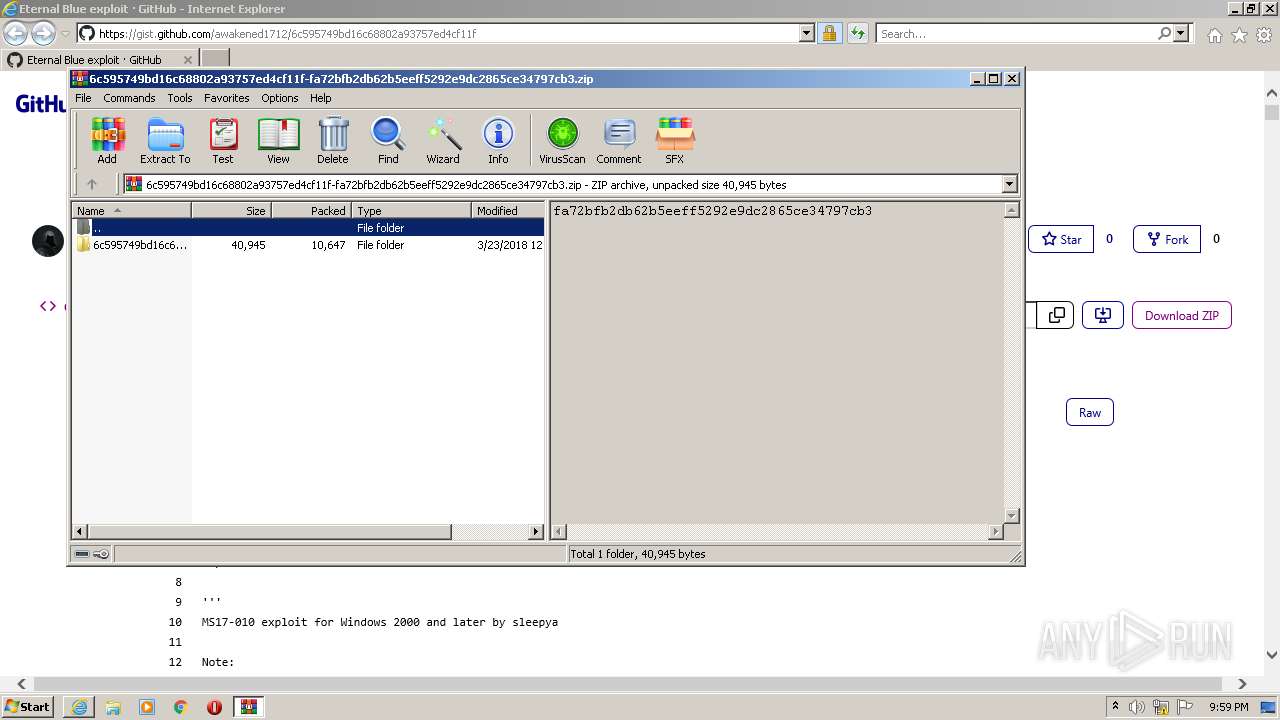
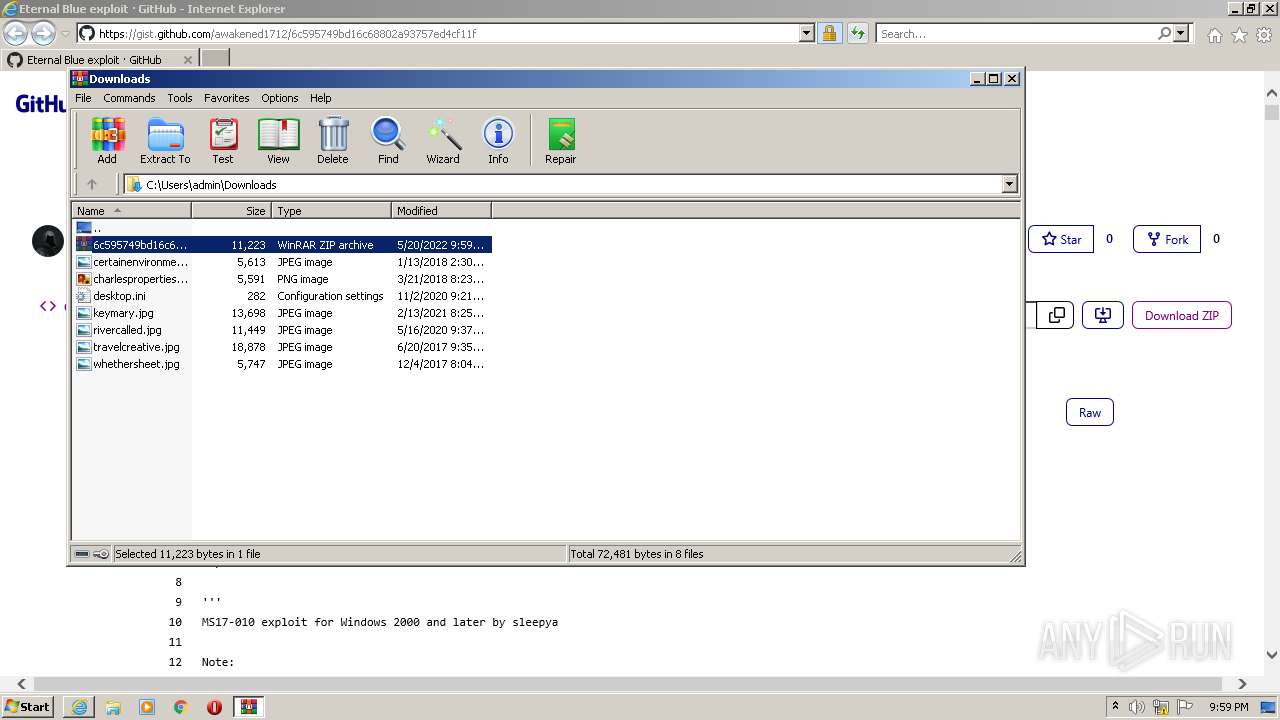
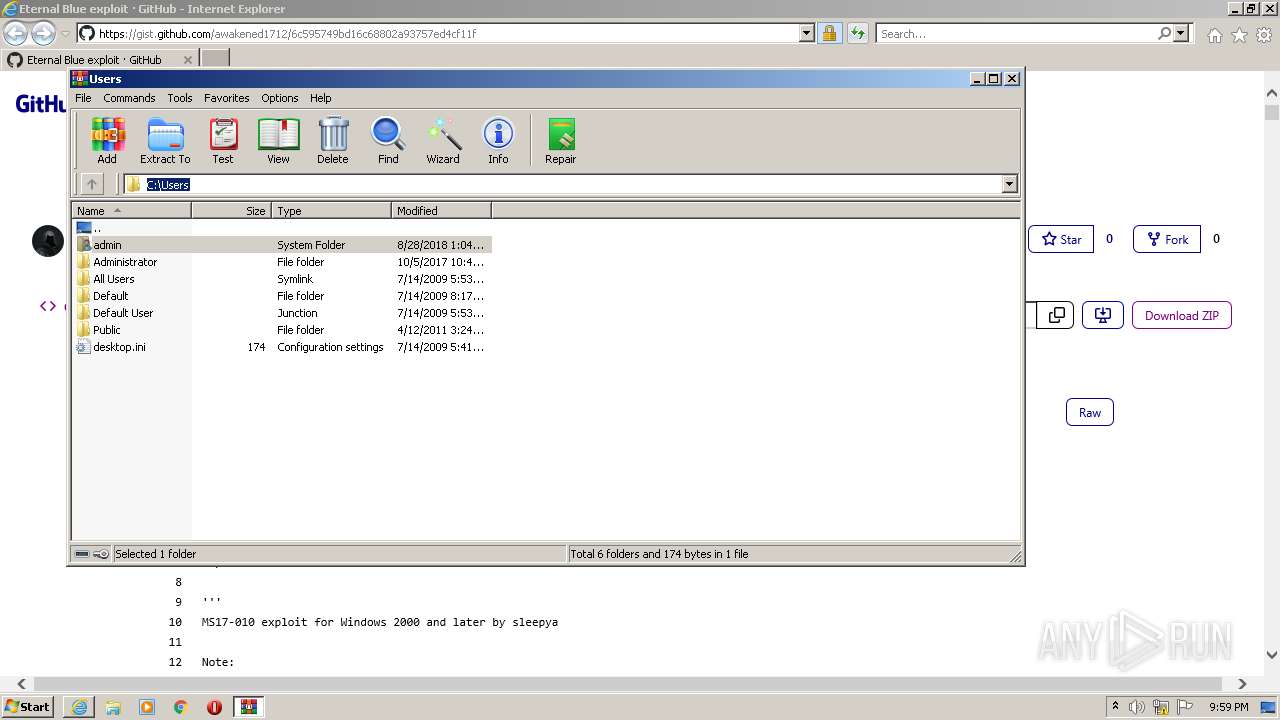
| 1320 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\6c595749bd16c68802a93757ed4cf11f-fa72bfb2db62b5eeff5292e9dc2865ce34797cb3.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.bing.com/ck/a?!&&p=3fed2d82b0618f8dd3ed99040d3b5ee0fad5b5b9d9b0d0018a9e783c200b45dcJmltdHM9MTY1MzA4MDMyNyZpZ3VpZD1mYzlkMzFjNy0wYWI1LTQ3YTMtOGU1NC0yMjY4YTJhYmVhYjkmaW5zaWQ9NTMzOQ&ptn=3&fclid=a445abf2-d87f-11ec-8c74-12a6b2db7071&u=a1aHR0cHM6Ly9naXN0LmdpdGh1Yi5jb20vYXdha2VuZWQxNzEyLzZjNTk1NzQ5YmQxNmM2ODgwMmE5Mzc1N2VkNGNmMTFm&ntb=1" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2308 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3100 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2060 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
18 302
Read events
18 159
Write events
143
Delete events
0
Modification events
| (PID) Process: | (2060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960780 | |||
| (PID) Process: | (2060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960780 | |||
| (PID) Process: | (2060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
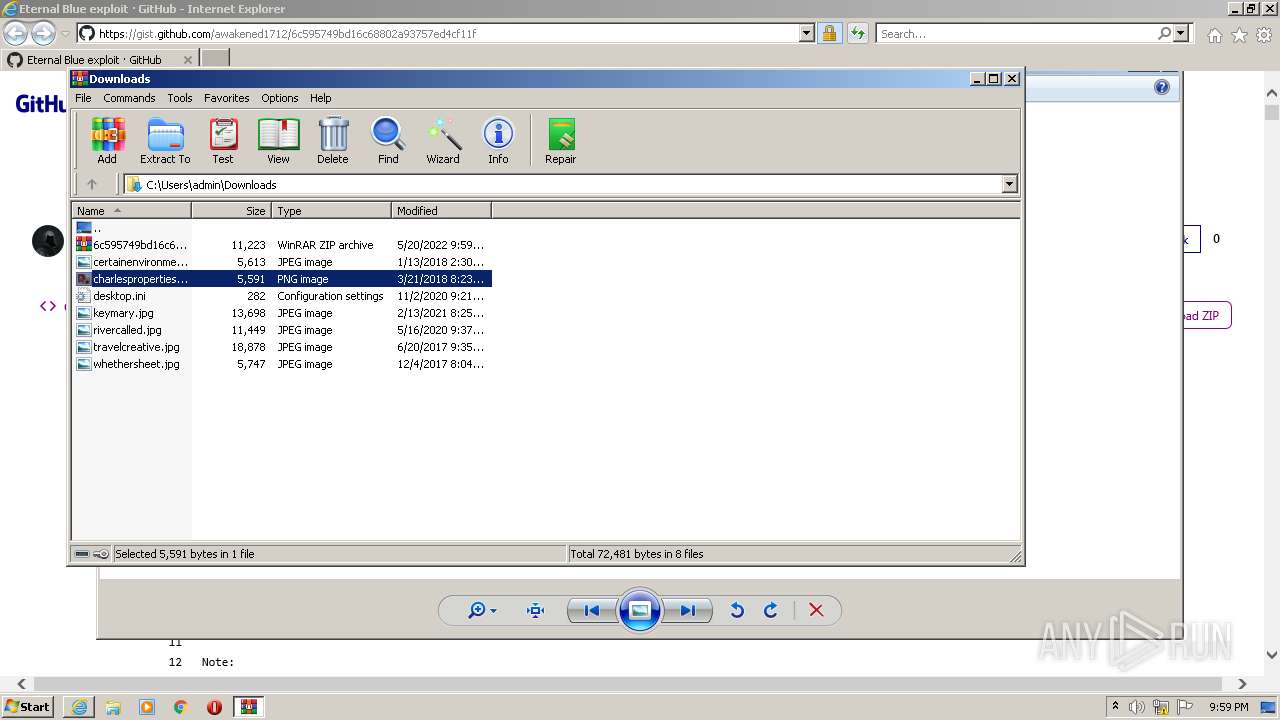
Executable files
0
Suspicious files
12
Text files
40
Unknown types
5
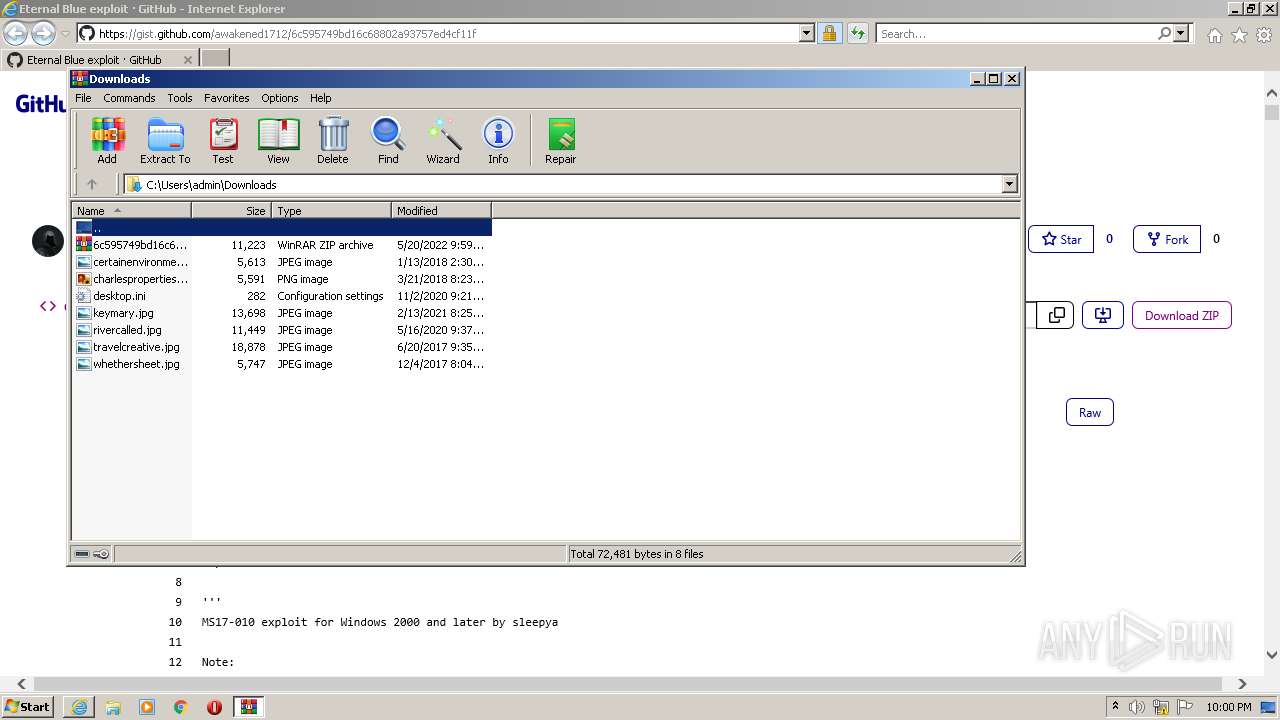
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
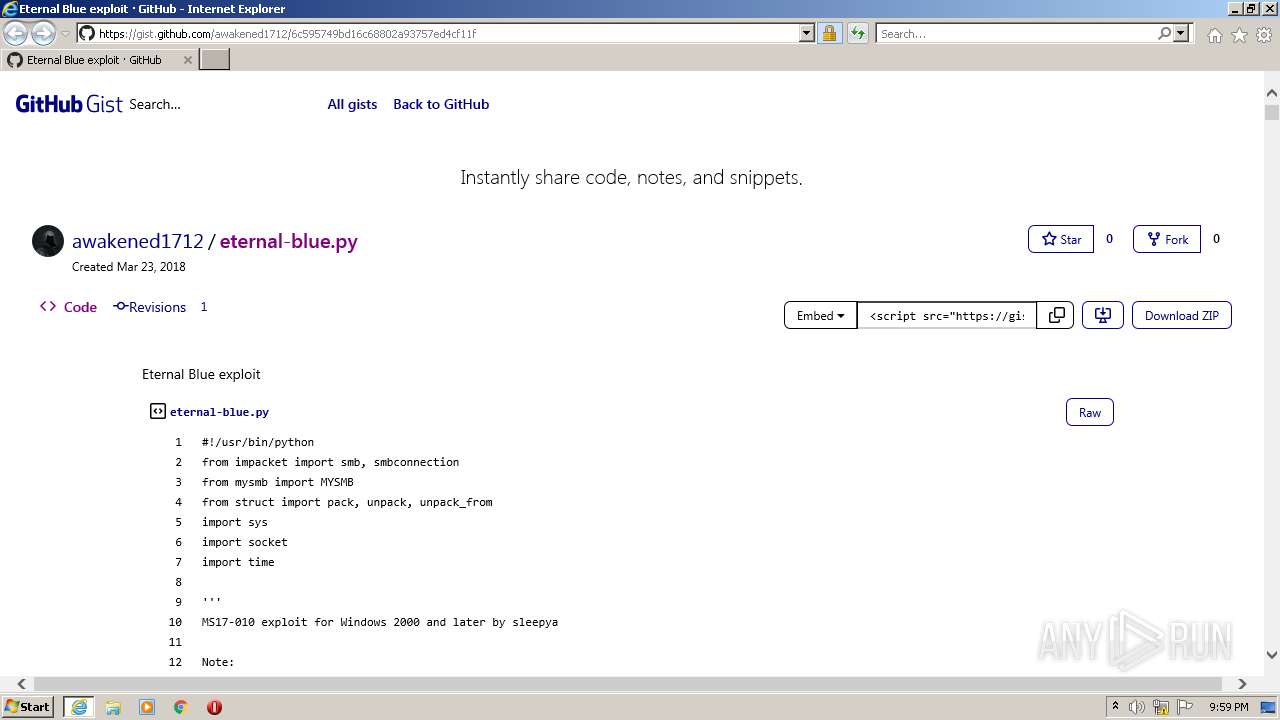
| 3100 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\6c595749bd16c68802a93757ed4cf11f[1].htm | html | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\a[1].htm | html | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_4CCA8700E795CC7BD2FDBA29220FEB7C | der | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | der | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\50CD3D75D026C82E2E718570BD6F44D0_4CCA8700E795CC7BD2FDBA29220FEB7C | binary | |
MD5:— | SHA256:— | |||
| 2060 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\imagestore\f7ruq93\imagestore.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
30
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3100 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2060 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3100 | iexplore.exe | GET | 200 | 8.253.207.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0d6970c7831bbe12 | US | compressed | 4.70 Kb | whitelisted |
3100 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
3100 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3100 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAJ0h%2FSC0Hyw6EHPCik1fps%3D | US | der | 312 b | whitelisted |
3100 | iexplore.exe | GET | 200 | 8.253.207.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?32cb6d1774e283a0 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3100 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3100 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2060 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3100 | iexplore.exe | 185.199.109.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
3100 | iexplore.exe | 185.199.109.133:443 | avatars.githubusercontent.com | GitHub, Inc. | NL | malicious |
2060 | iexplore.exe | 185.199.109.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
3100 | iexplore.exe | 140.82.121.9:443 | codeload.github.com | — | US | suspicious |
2060 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2060 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2060 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
gist.github.com |
| suspicious |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
codeload.github.com |
| whitelisted |