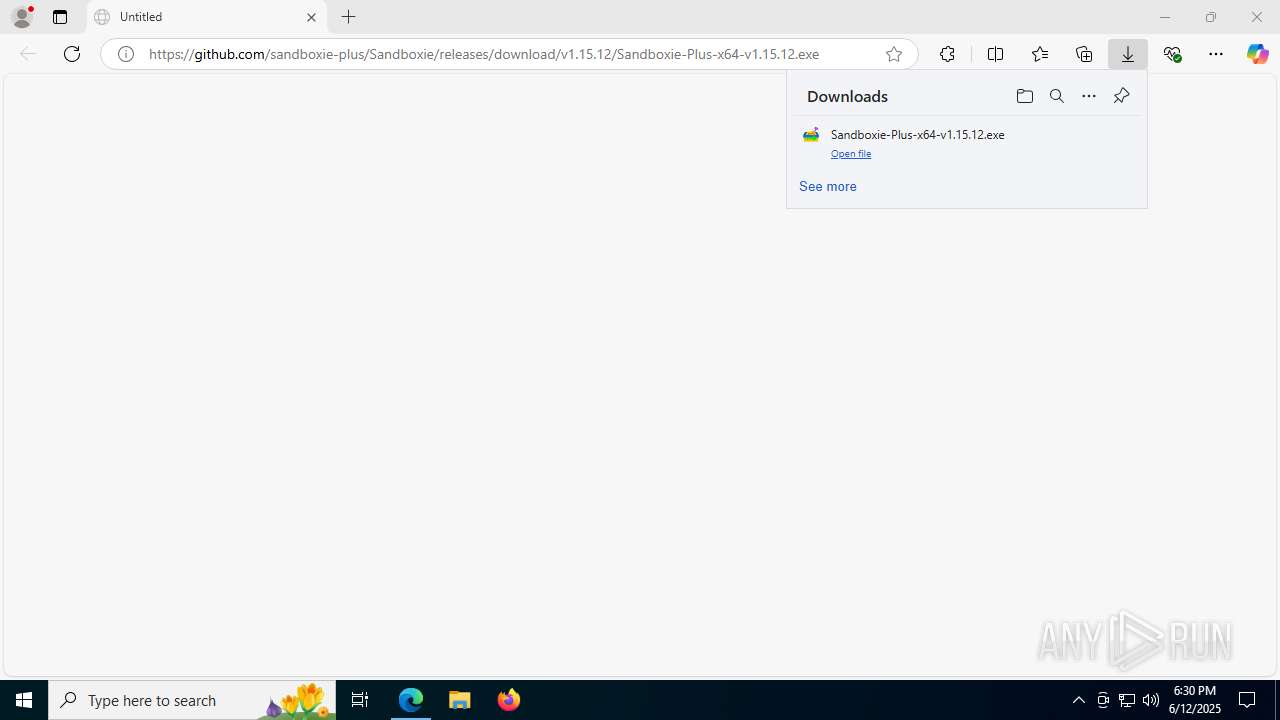
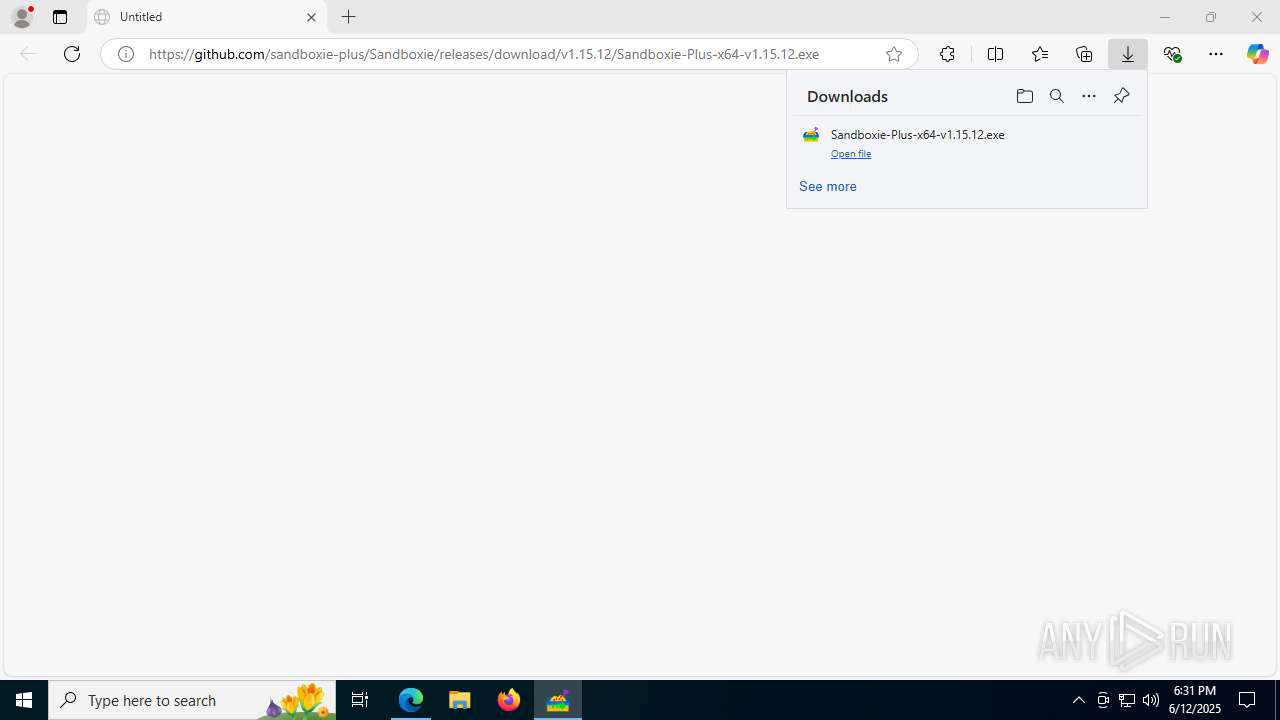
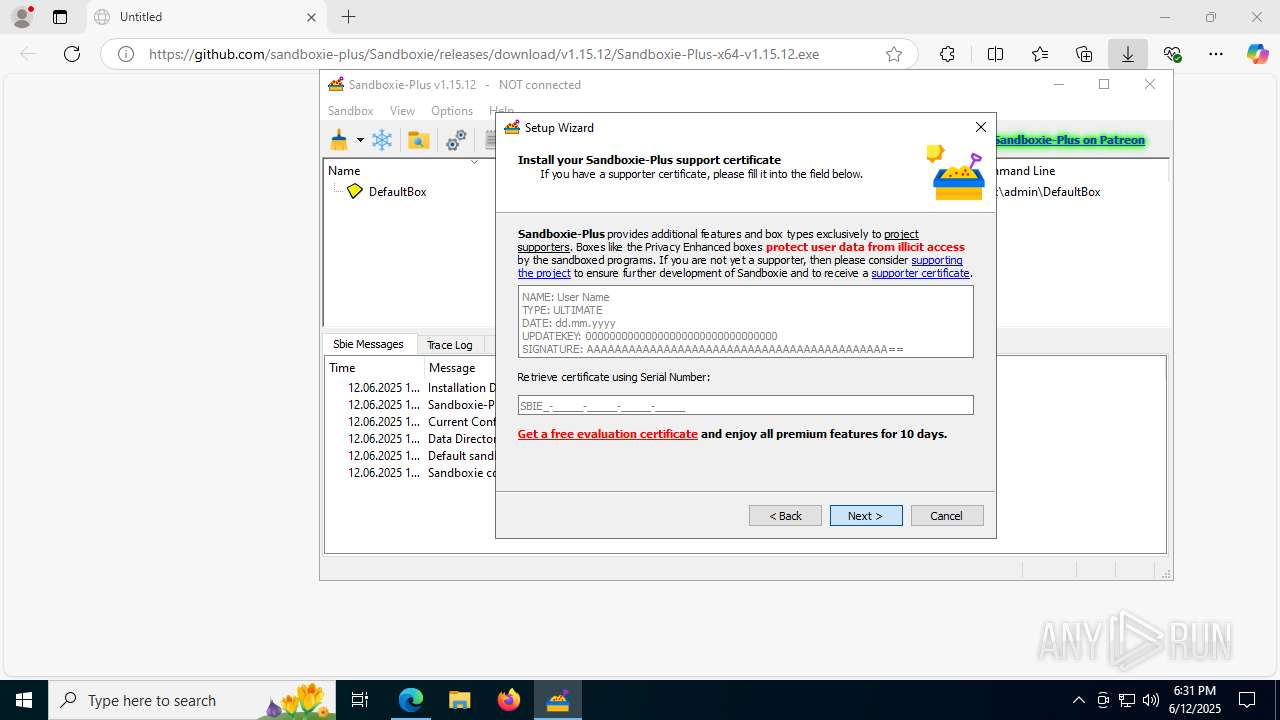
| URL: | https://github.com/sandboxie-plus/Sandboxie/releases/download/v1.15.12/Sandboxie-Plus-x64-v1.15.12.exe |
| Full analysis: | https://app.any.run/tasks/bb7fa012-105e-4076-aed8-21142954f153 |
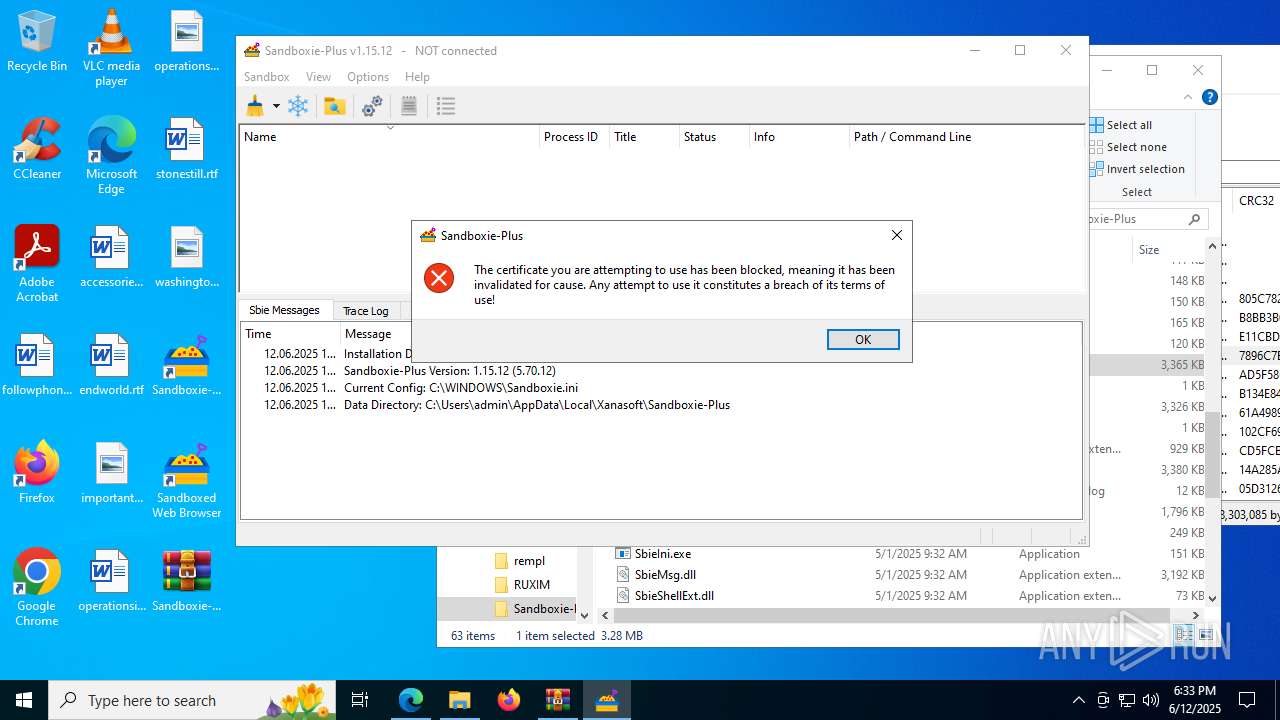
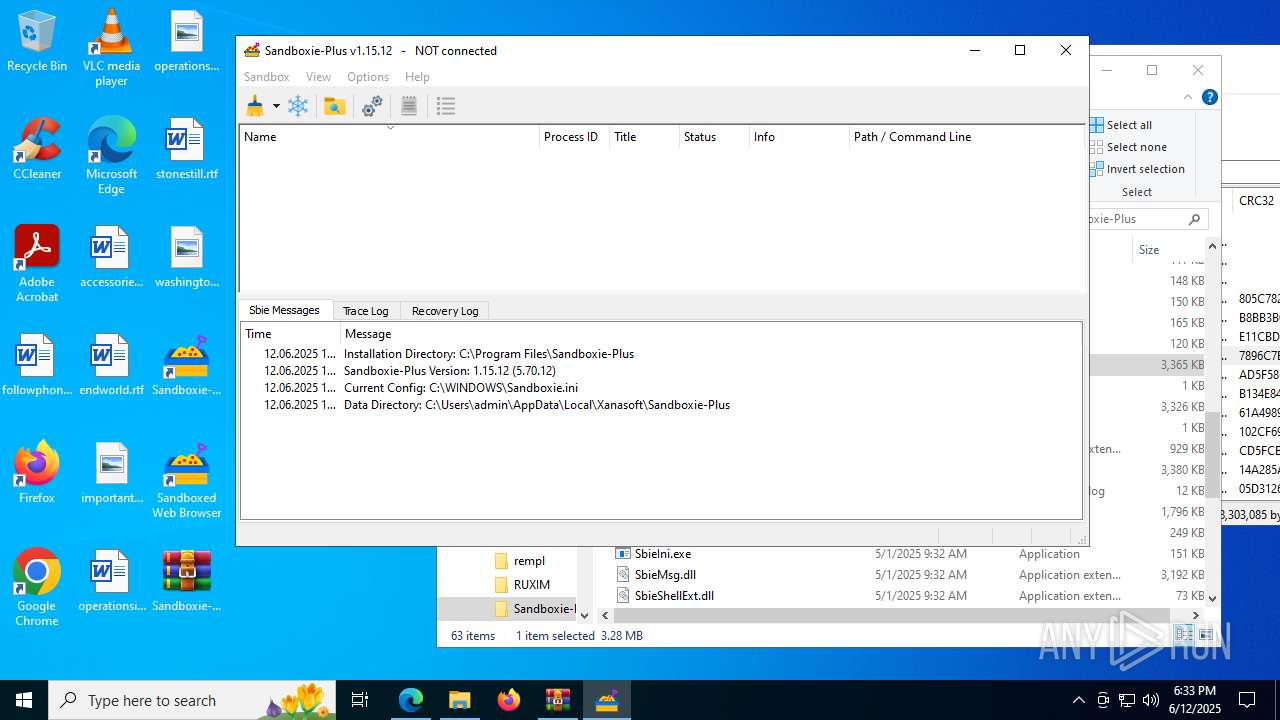
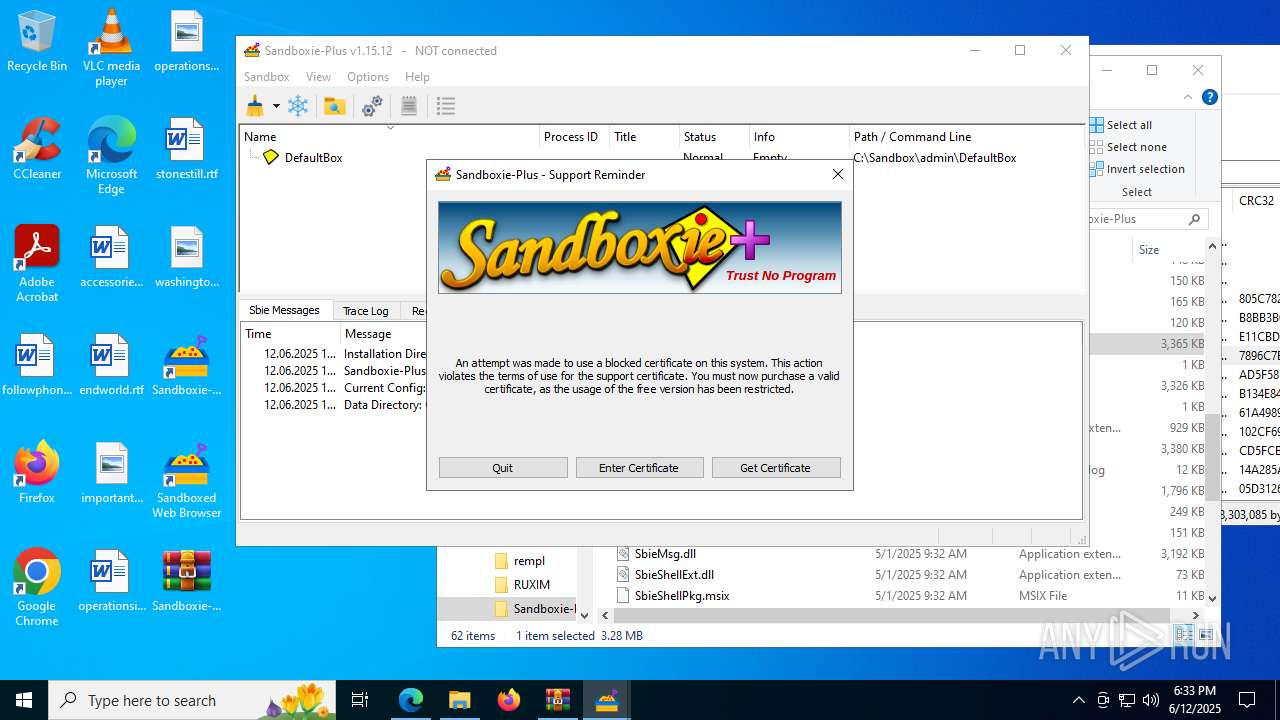
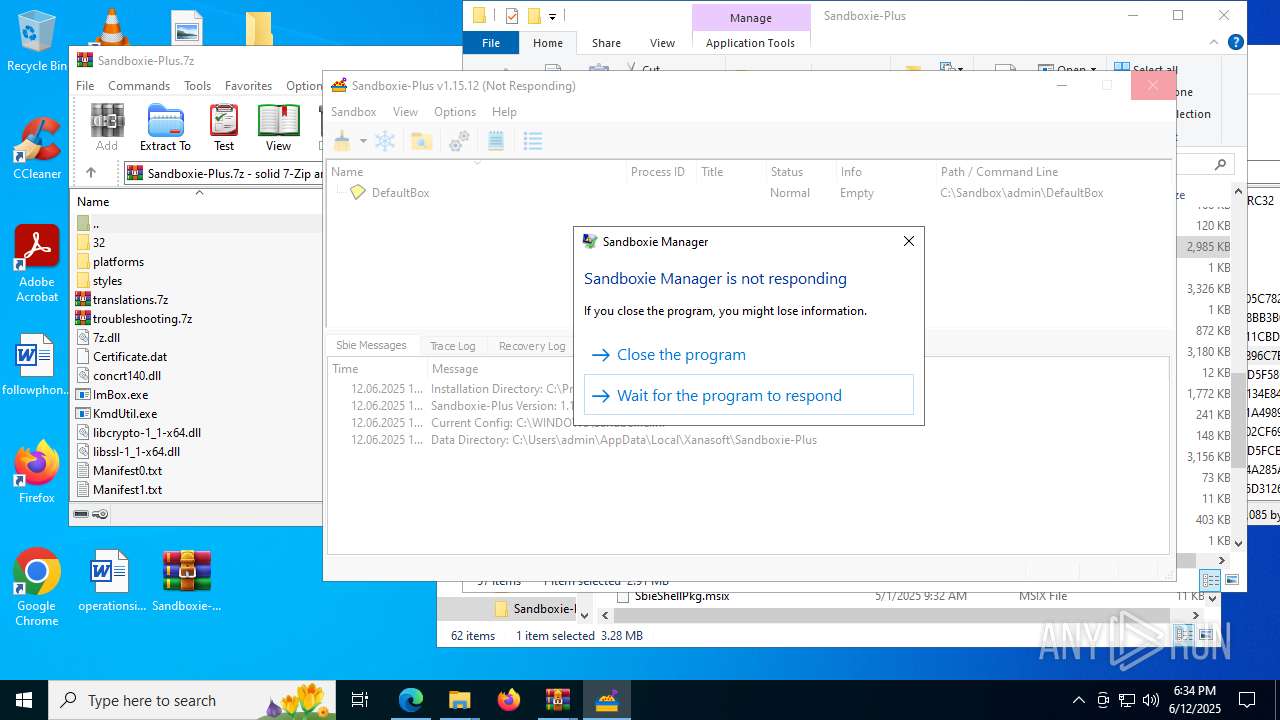
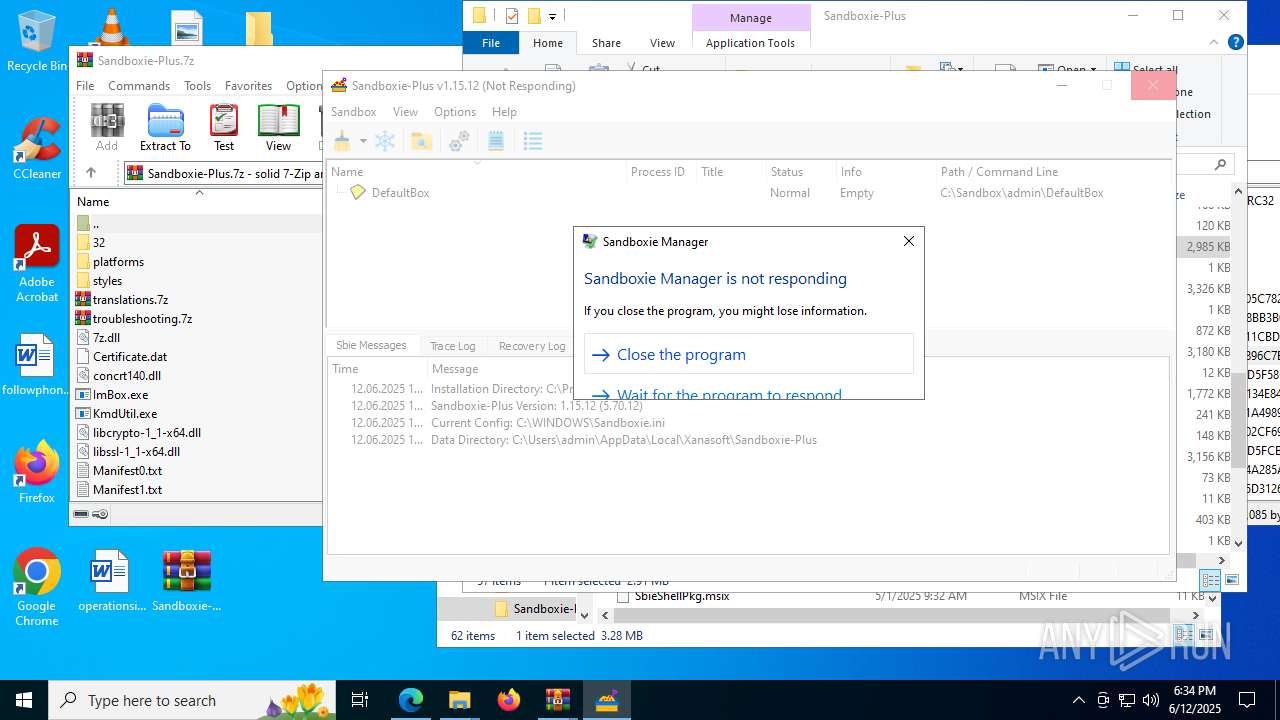
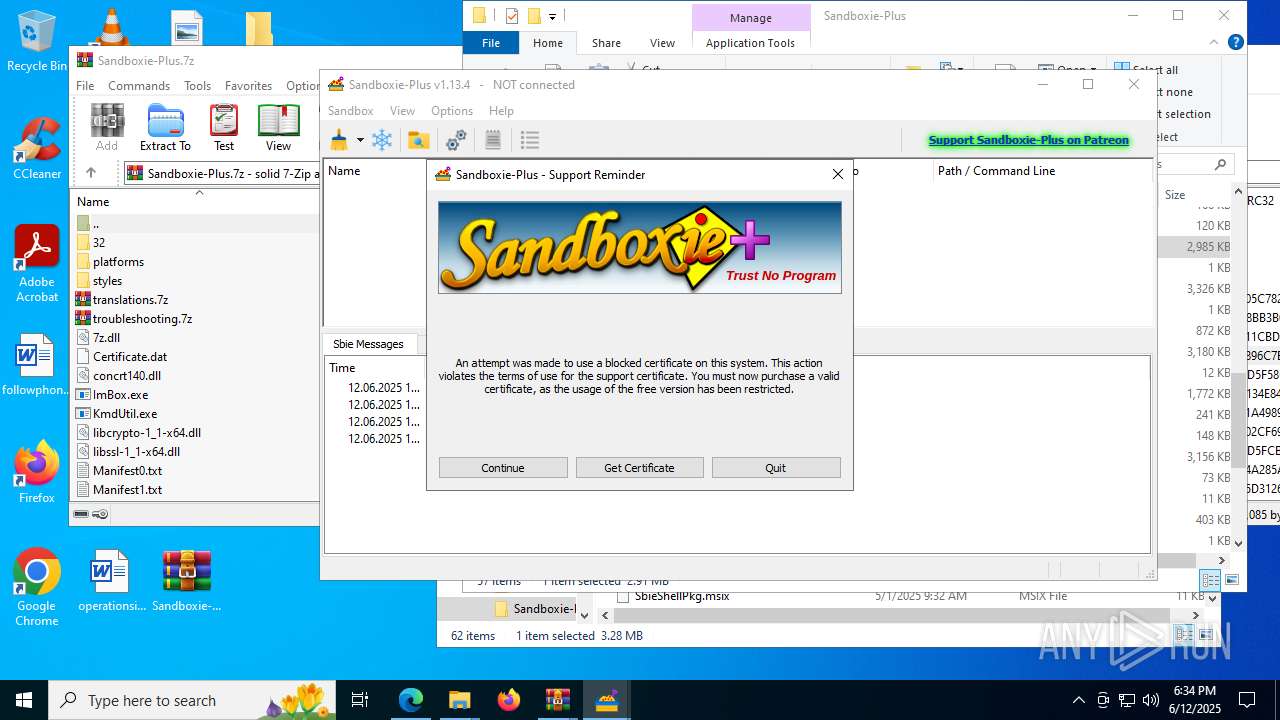
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2025, 18:30:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1B7018602899C84674953FD7E65FCB77 |
| SHA1: | D152757880DA5CF2EB37662287BFAE483DFDC9BC |
| SHA256: | C8A9E4B9229A78E69F99096A2D2336604DF518F43C1F81E501E5B5A71BB4BCDB |
| SSDEEP: | 3:N8tEdmELxKdM674KkCmJLl5pEIndn:2uwi9CFsF7pPd |
MALICIOUS
Changes the autorun value in the registry
- SandMan.exe (PID: 7676)
SUSPICIOUS
Executable content was dropped or overwritten
- Sandboxie-Plus-x64-v1.15.12.exe (PID: 1636)
- Sandboxie-Plus-x64-v1.15.12.exe (PID: 6776)
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- extrac32.exe (PID: 3592)
Reads security settings of Internet Explorer
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 7484)
Reads the Windows owner or organization settings
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
Uses TASKKILL.EXE to kill process
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
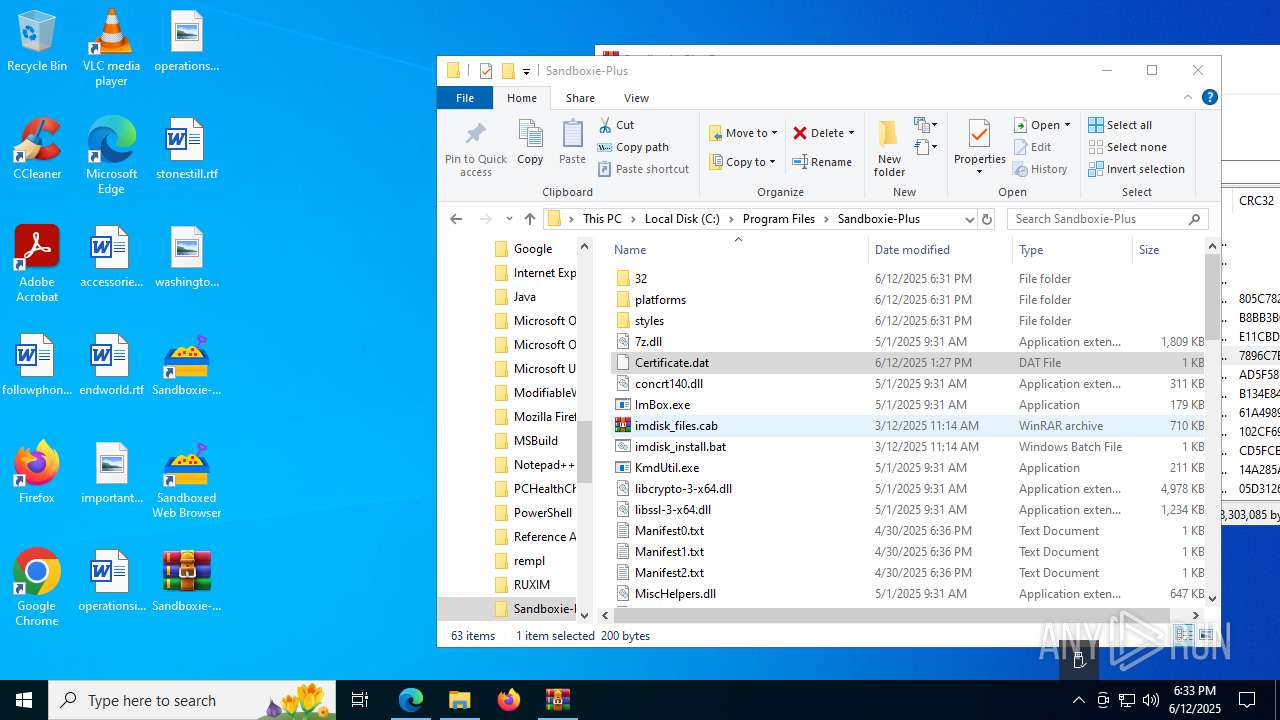
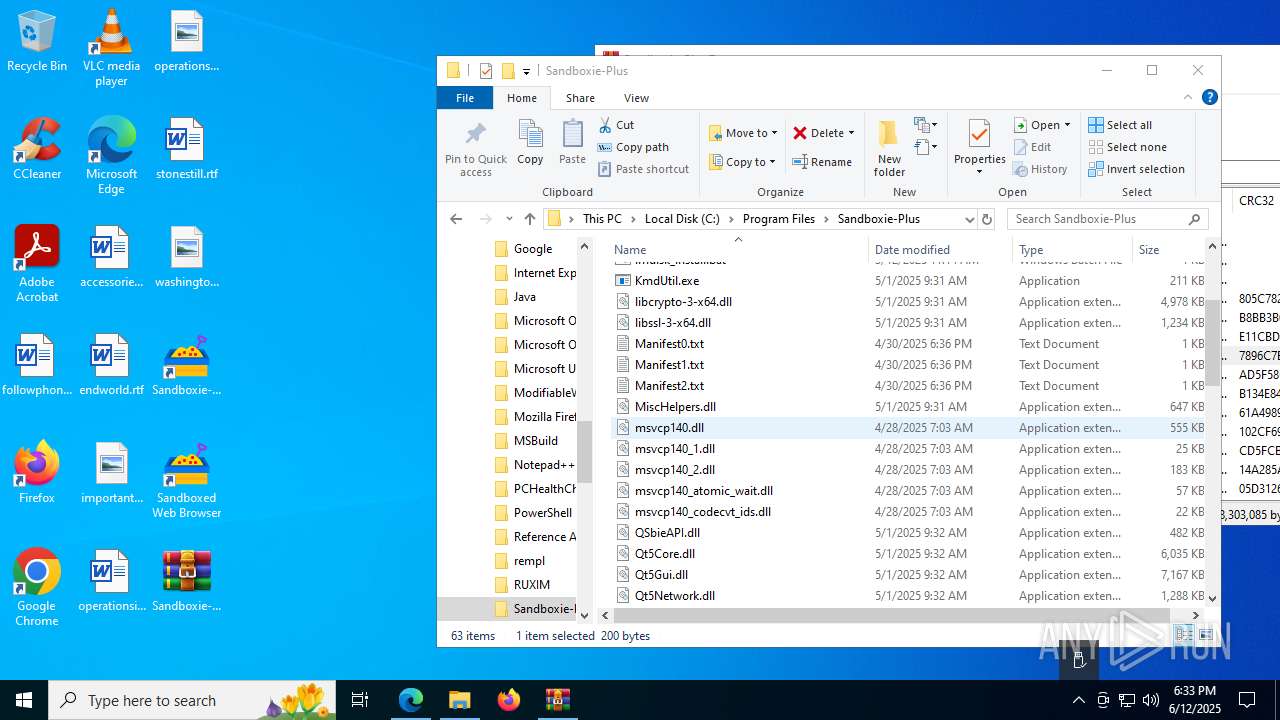
The process drops C-runtime libraries
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
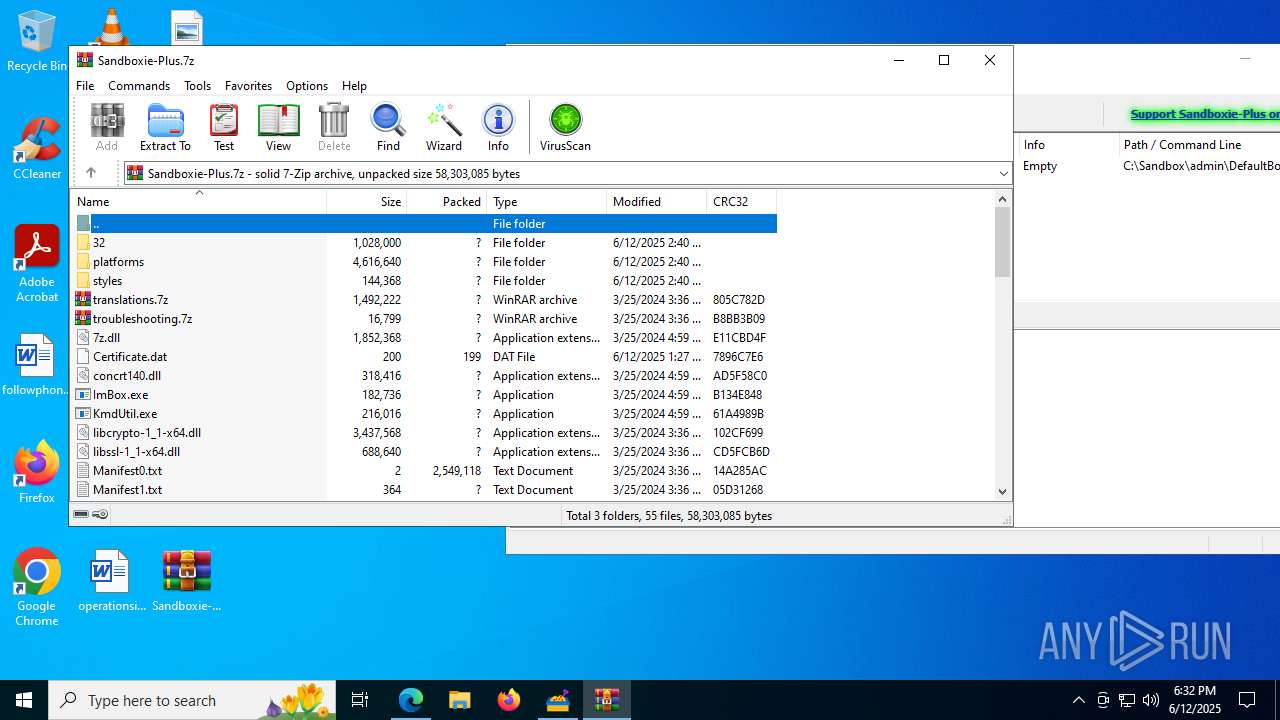
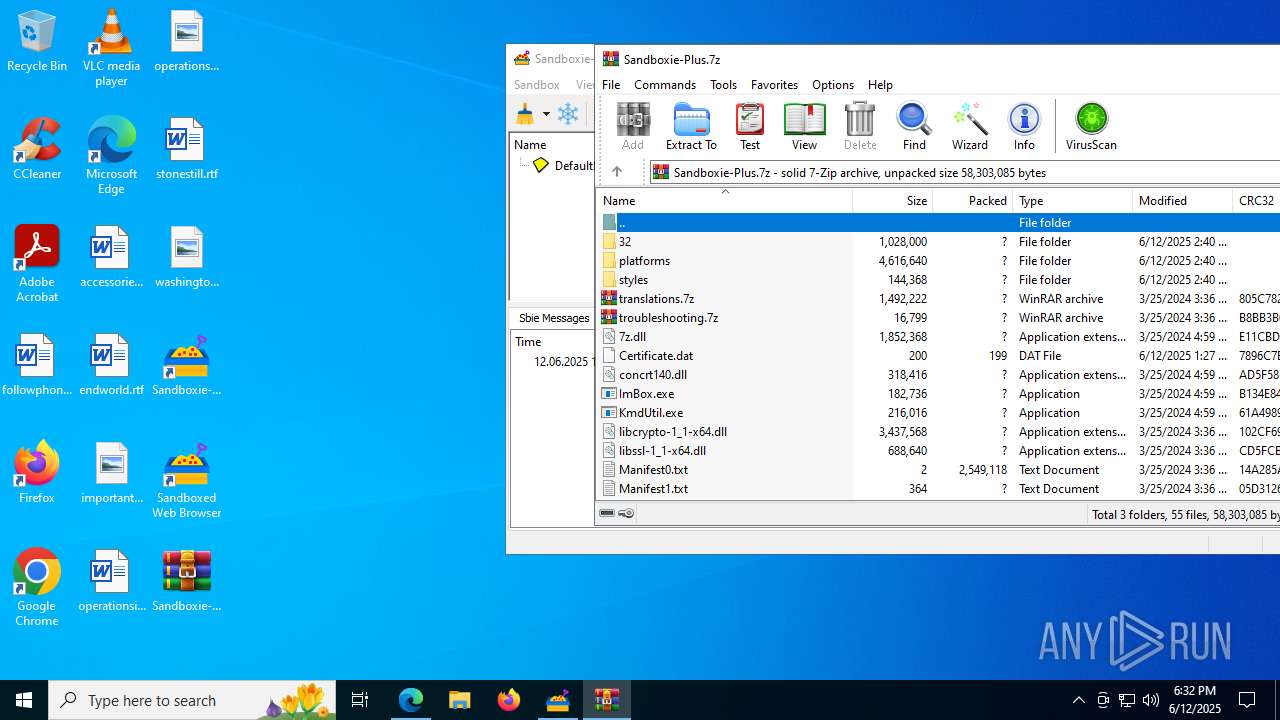
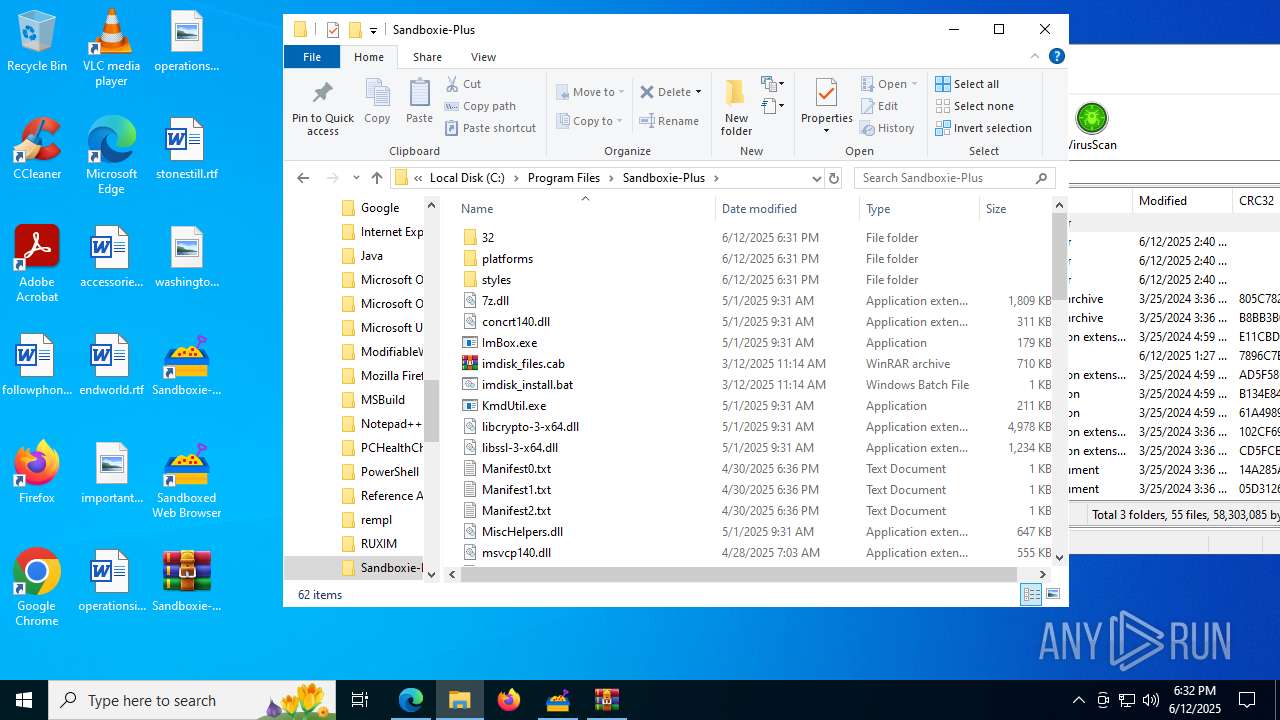
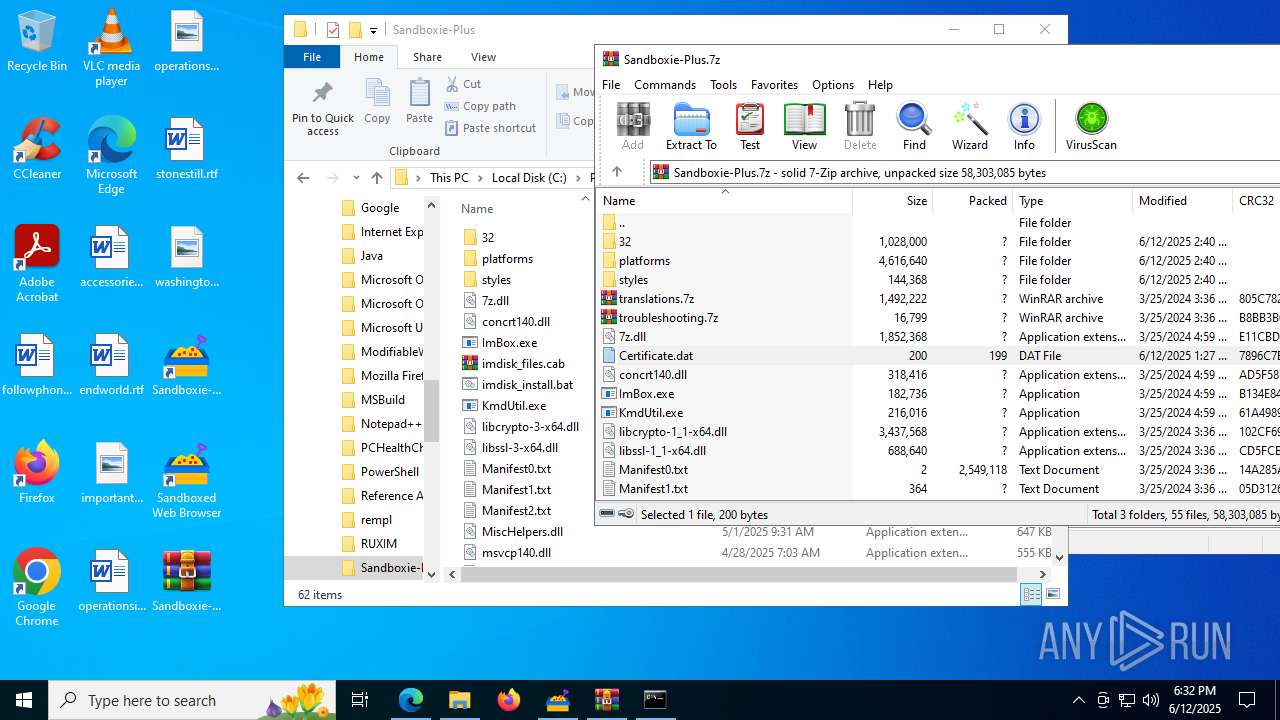
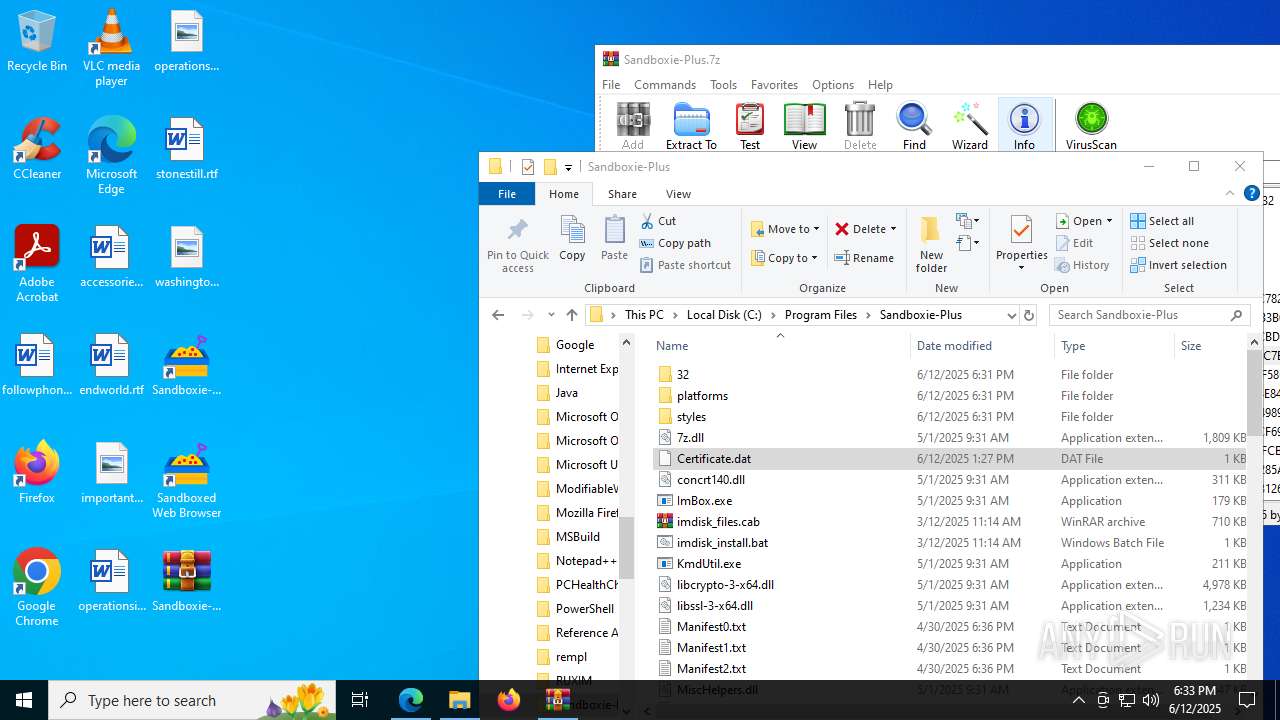
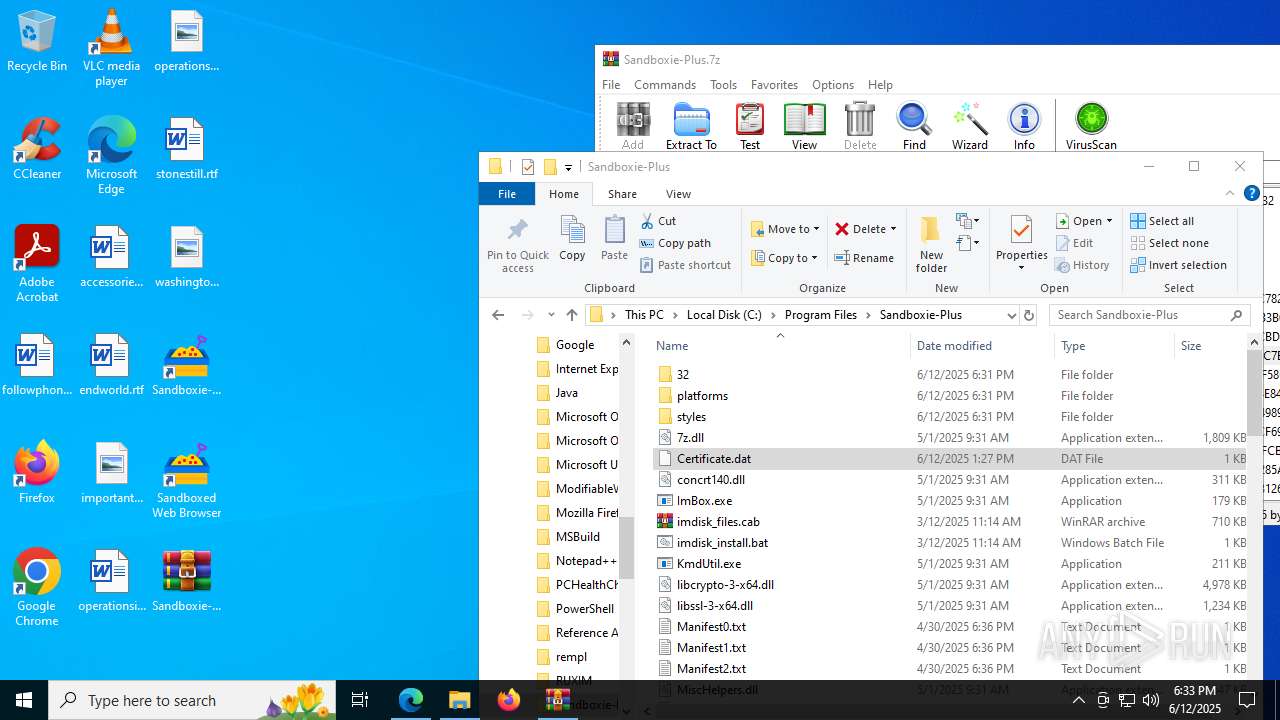
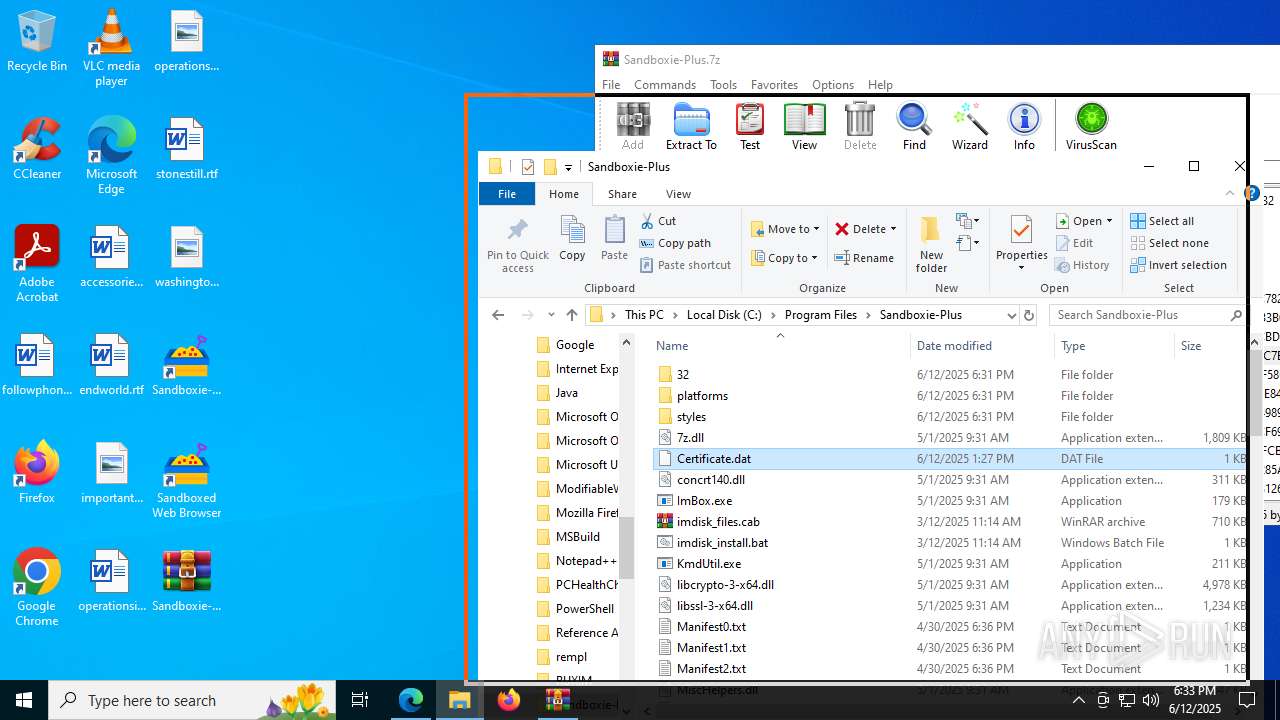
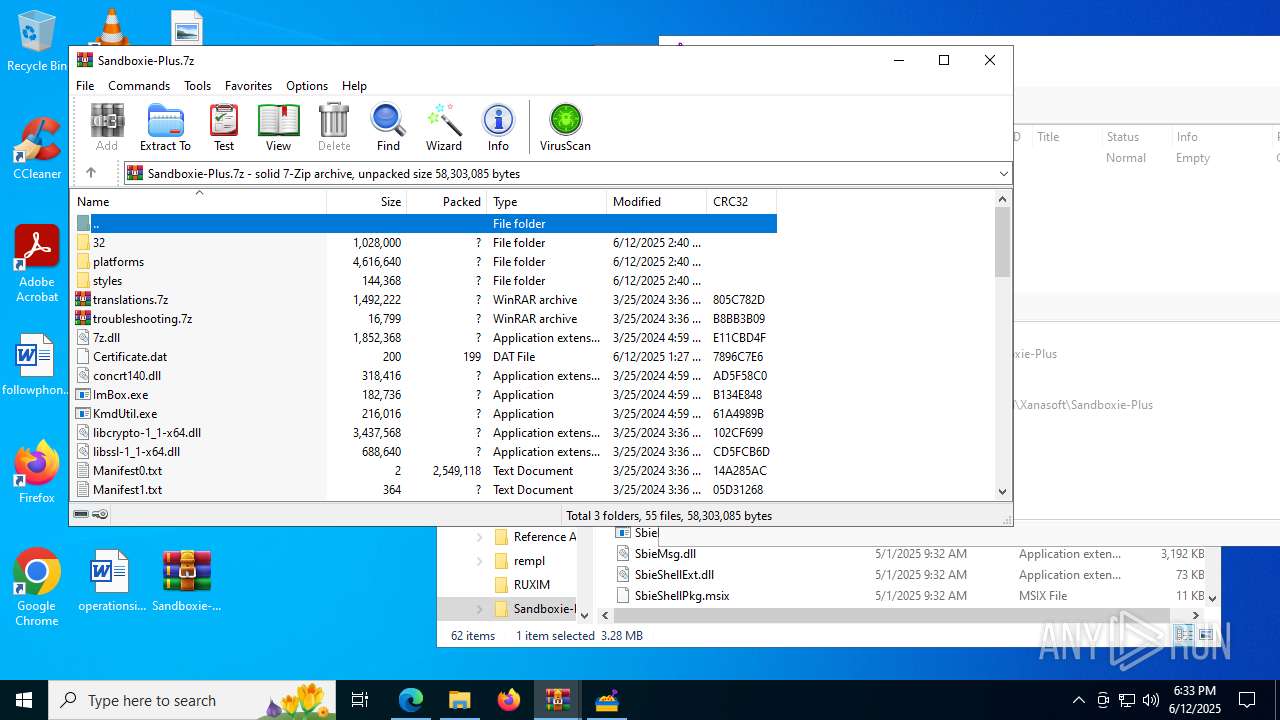
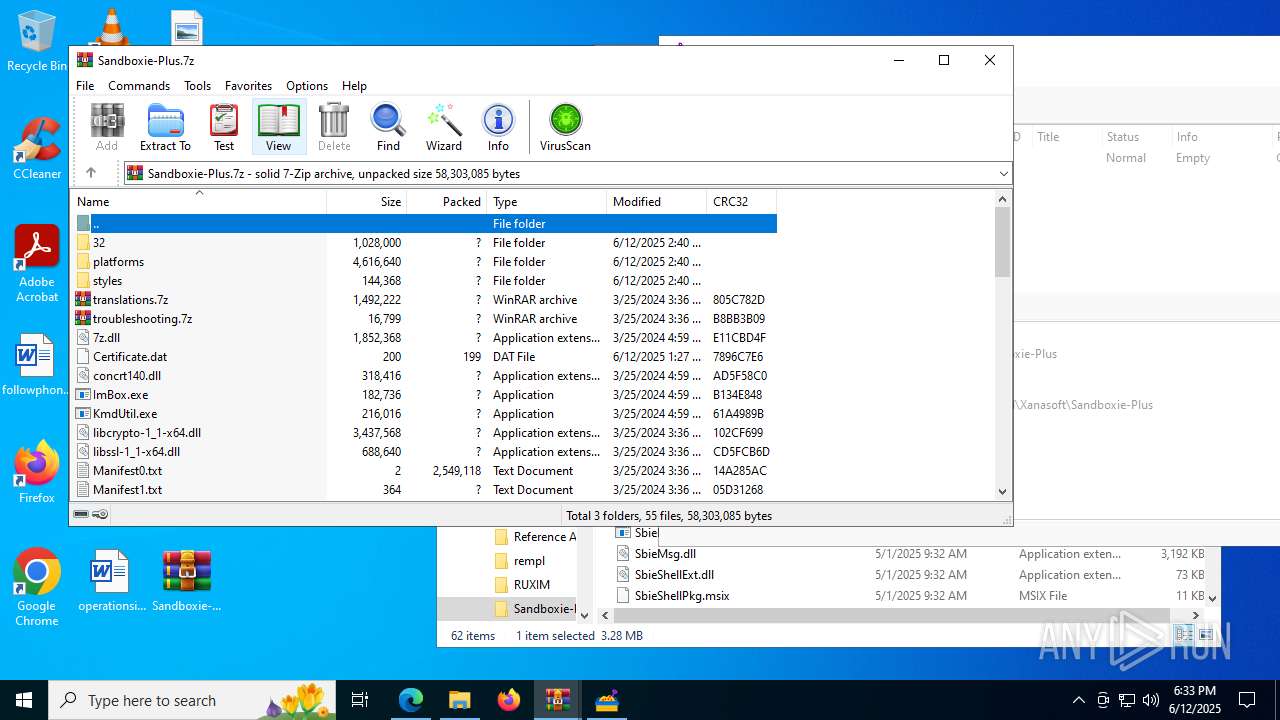
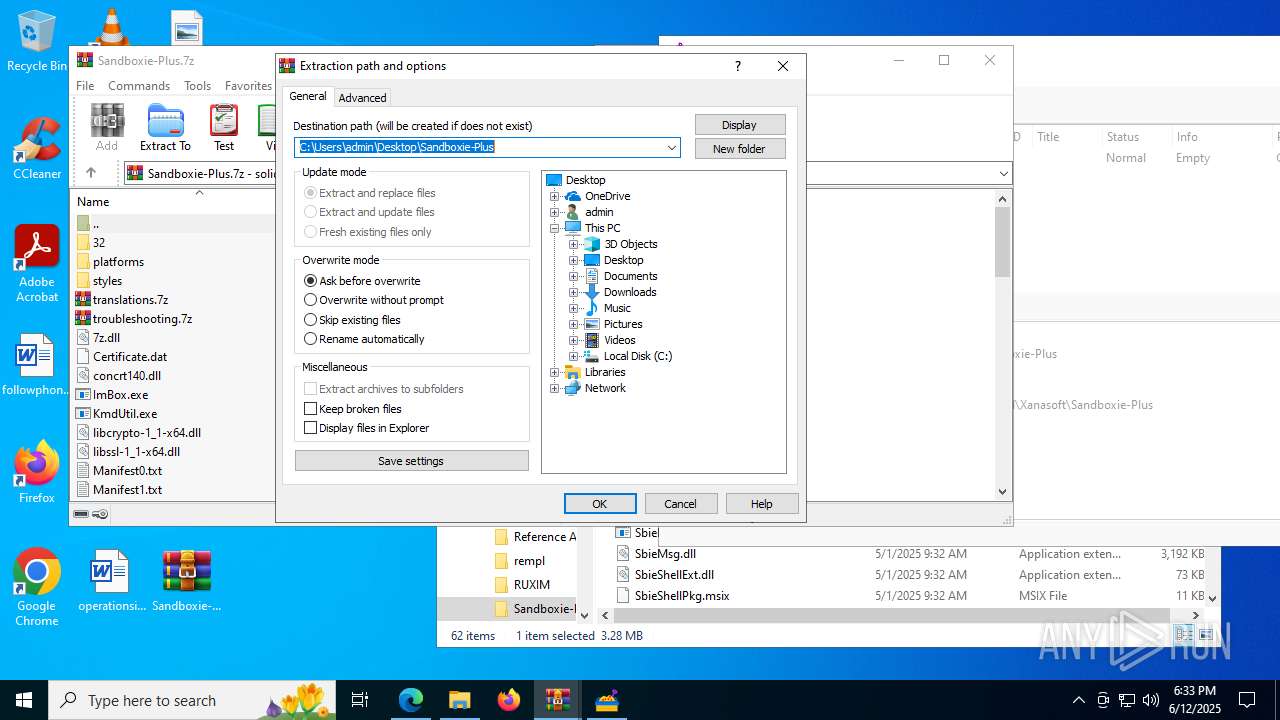
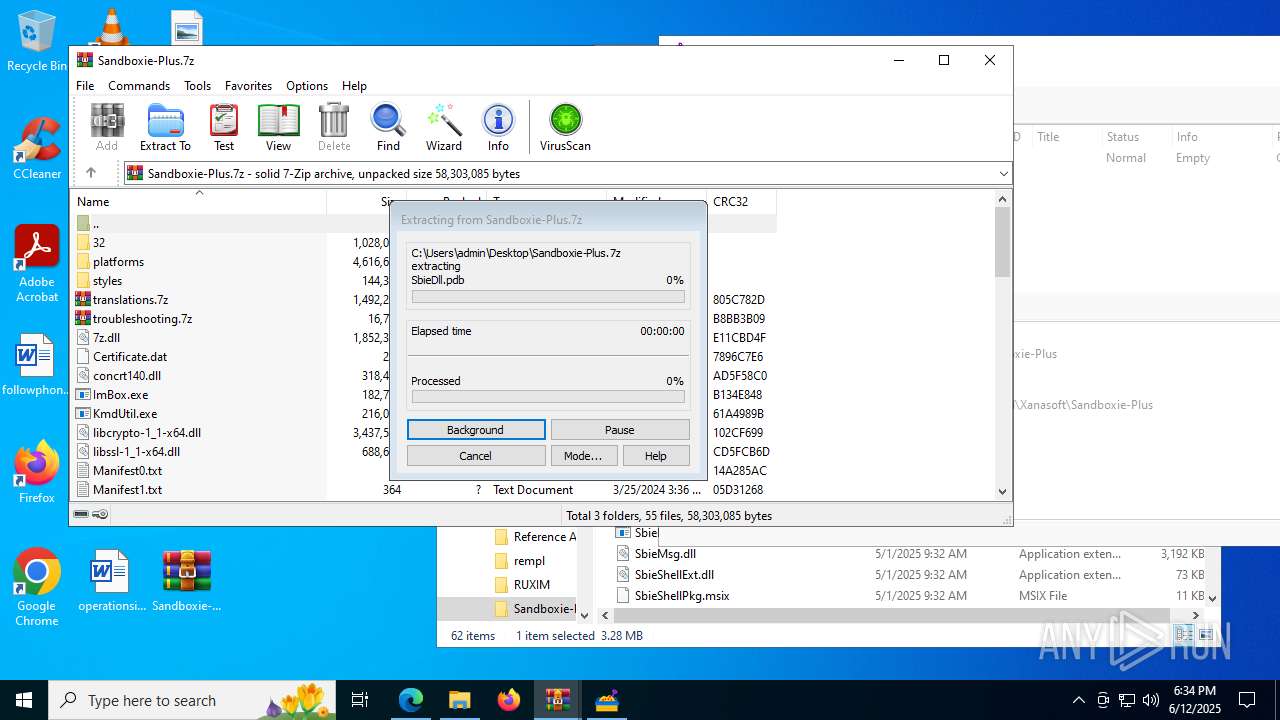
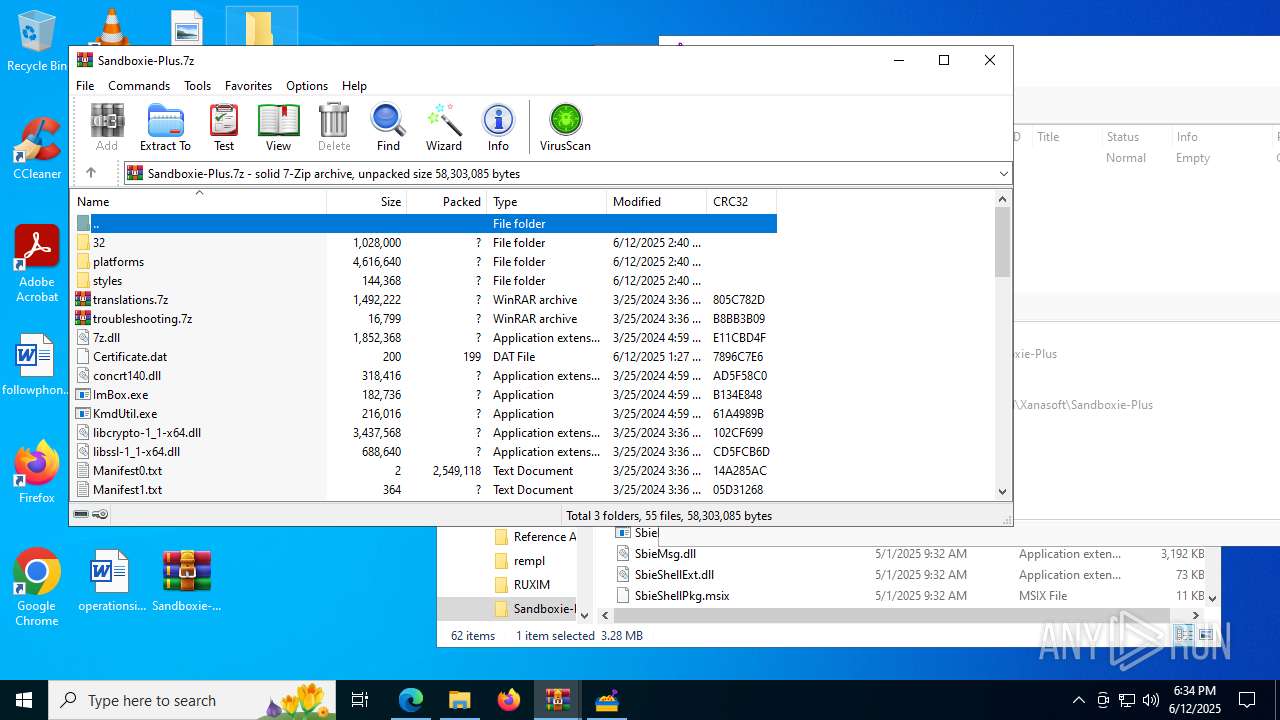
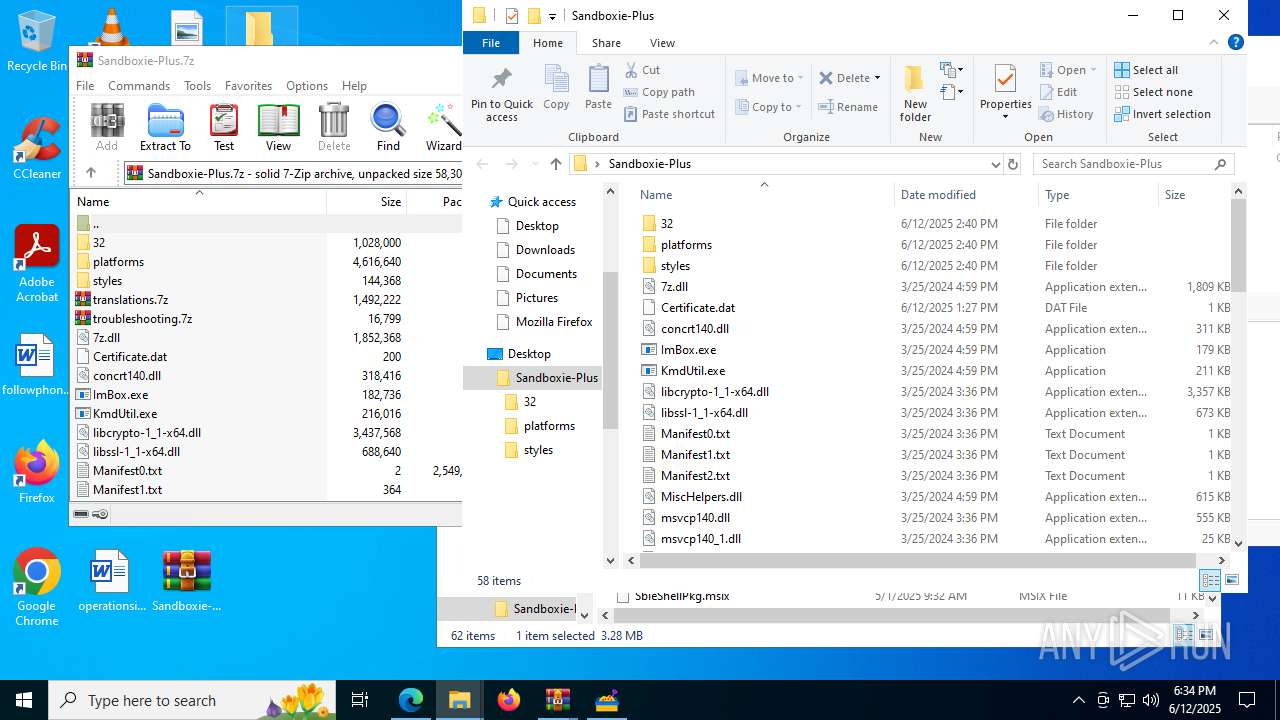
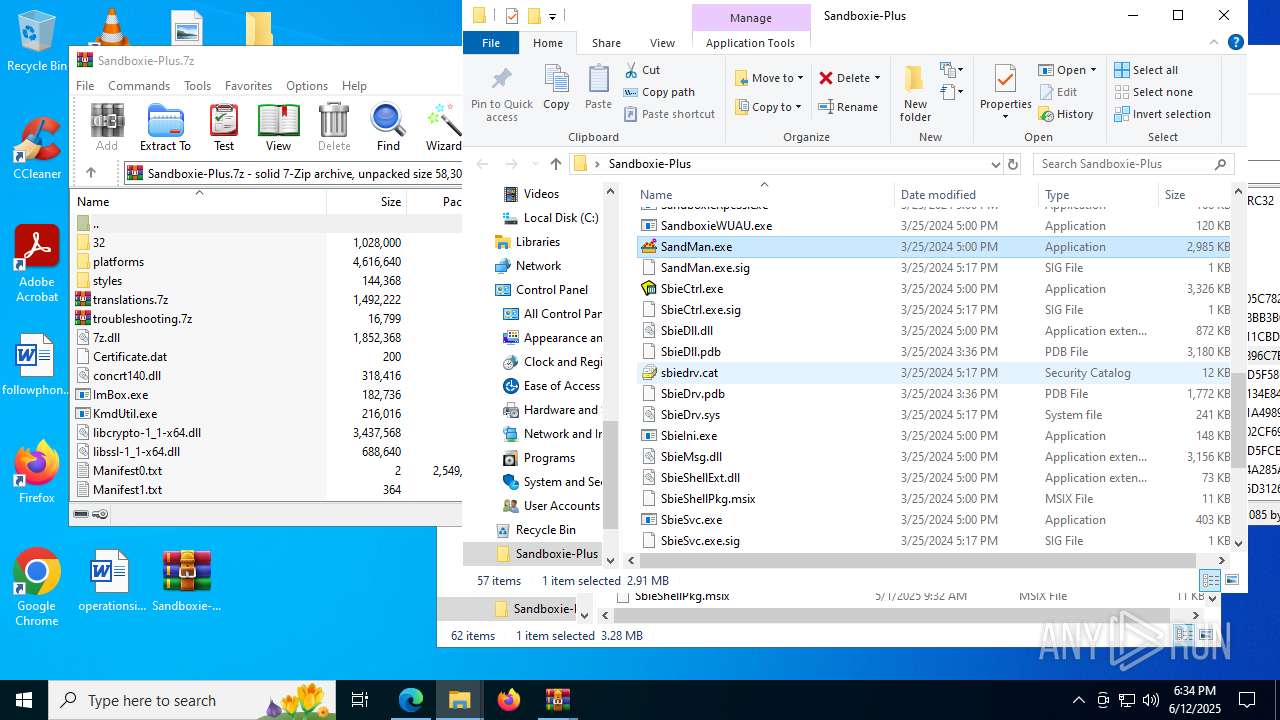
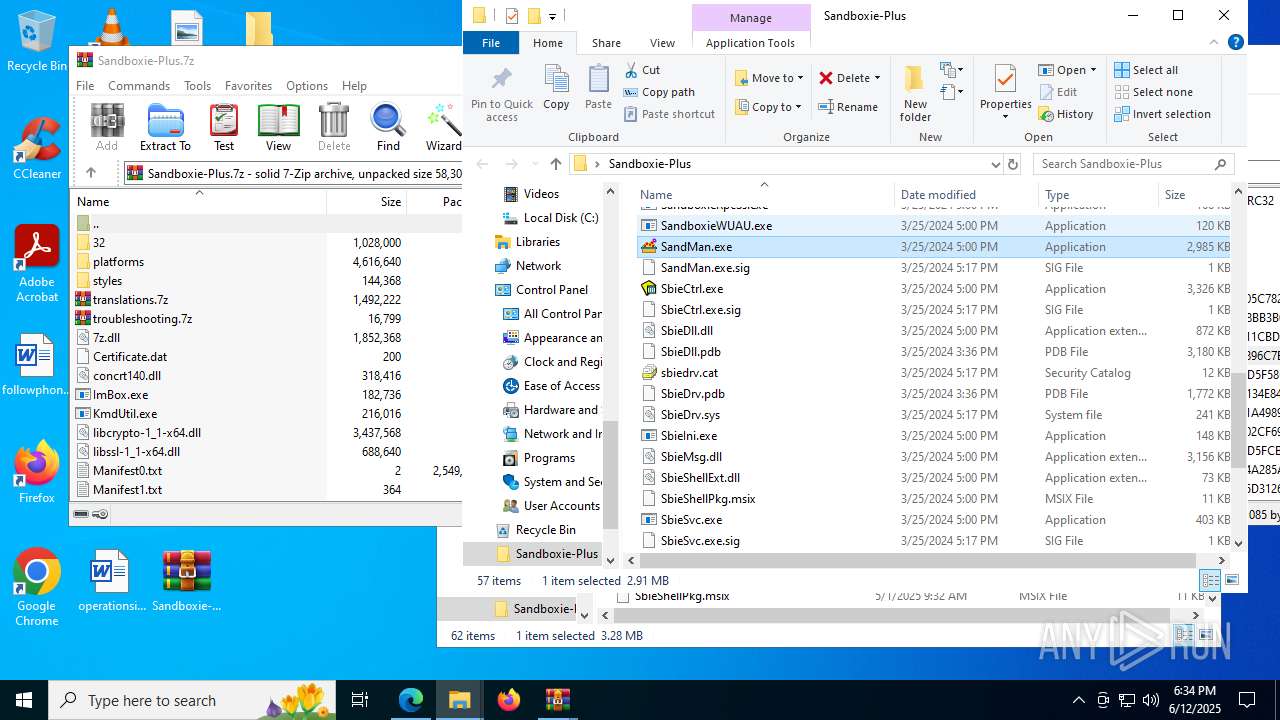
Drops 7-zip archiver for unpacking
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- WinRAR.exe (PID: 5652)
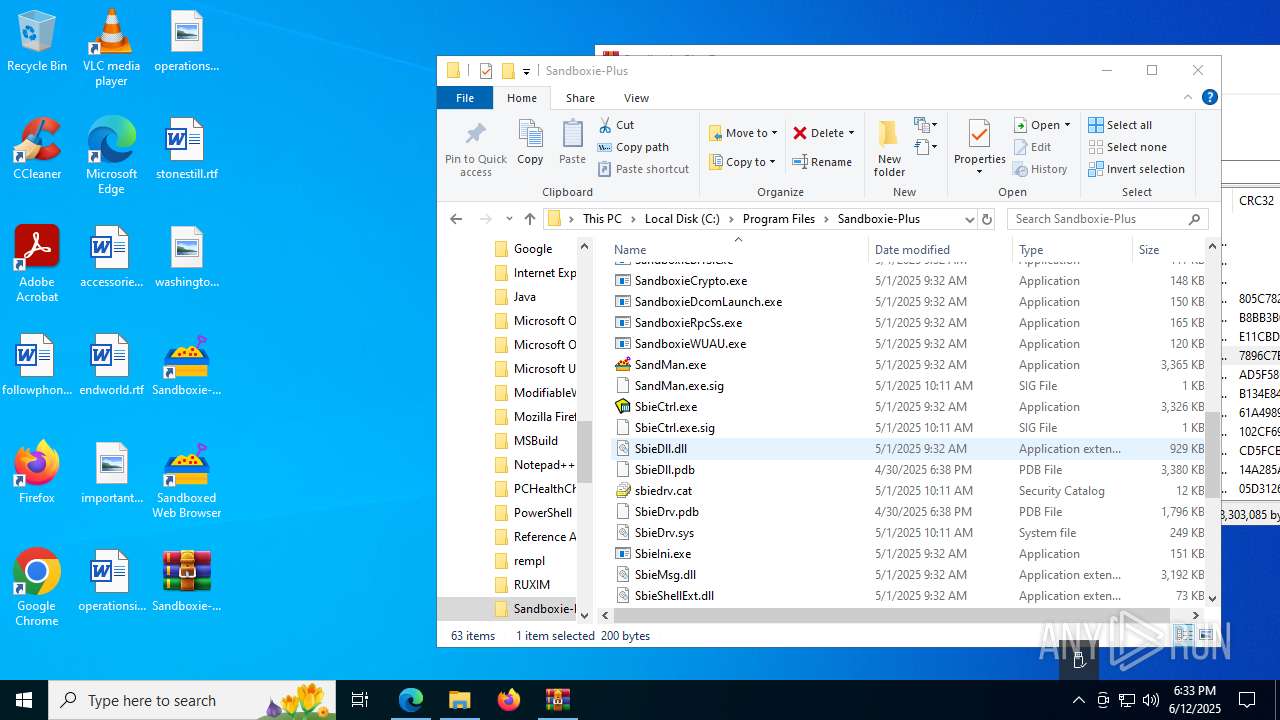
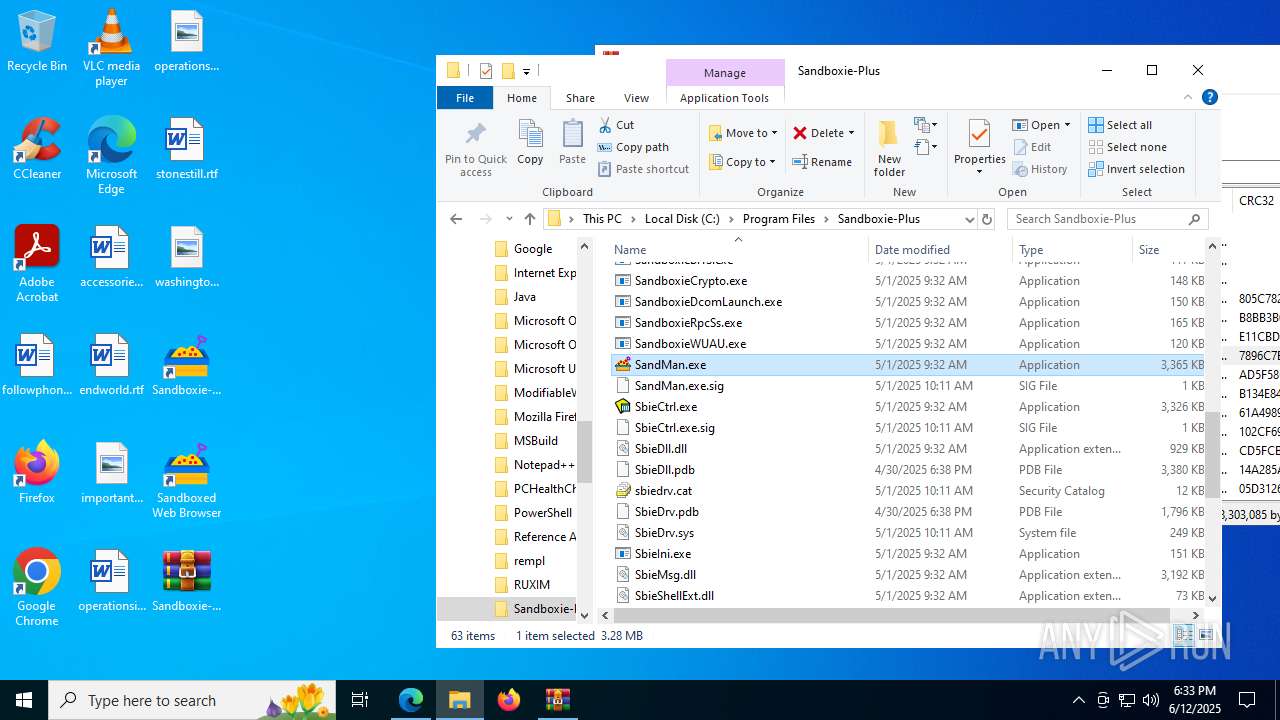
Process drops legitimate windows executable
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- extrac32.exe (PID: 3592)
- WinRAR.exe (PID: 5652)
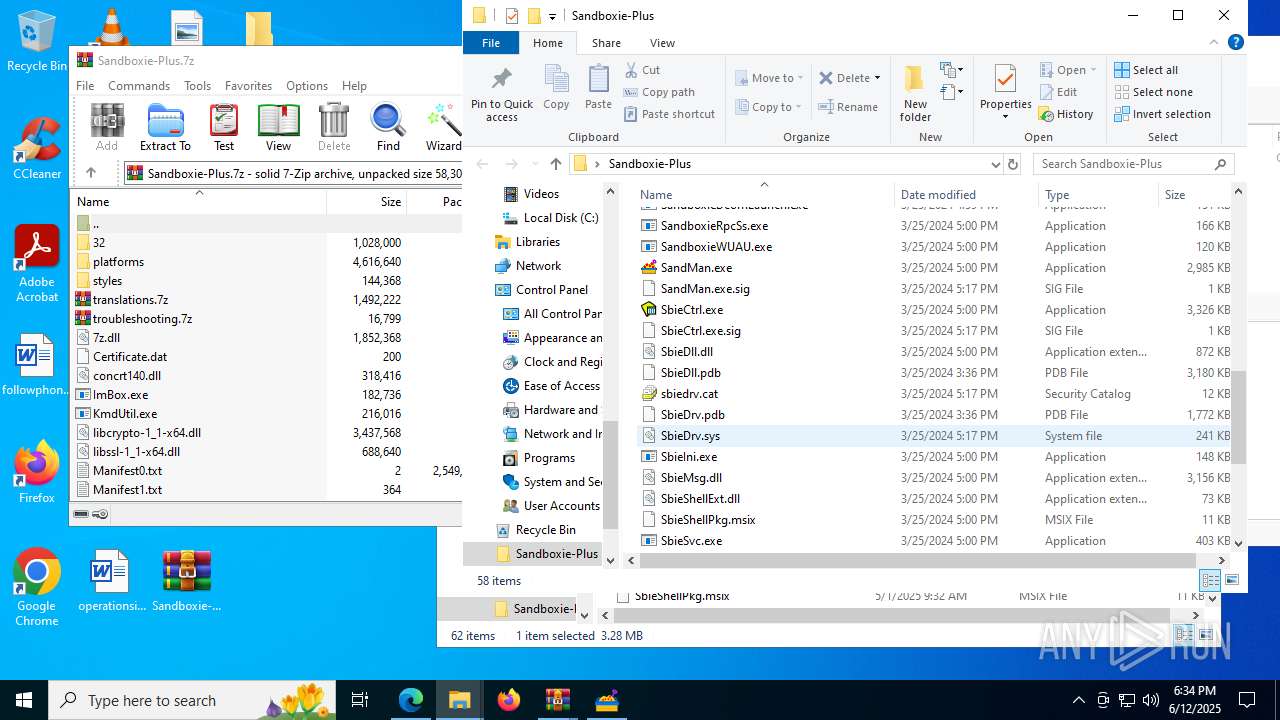
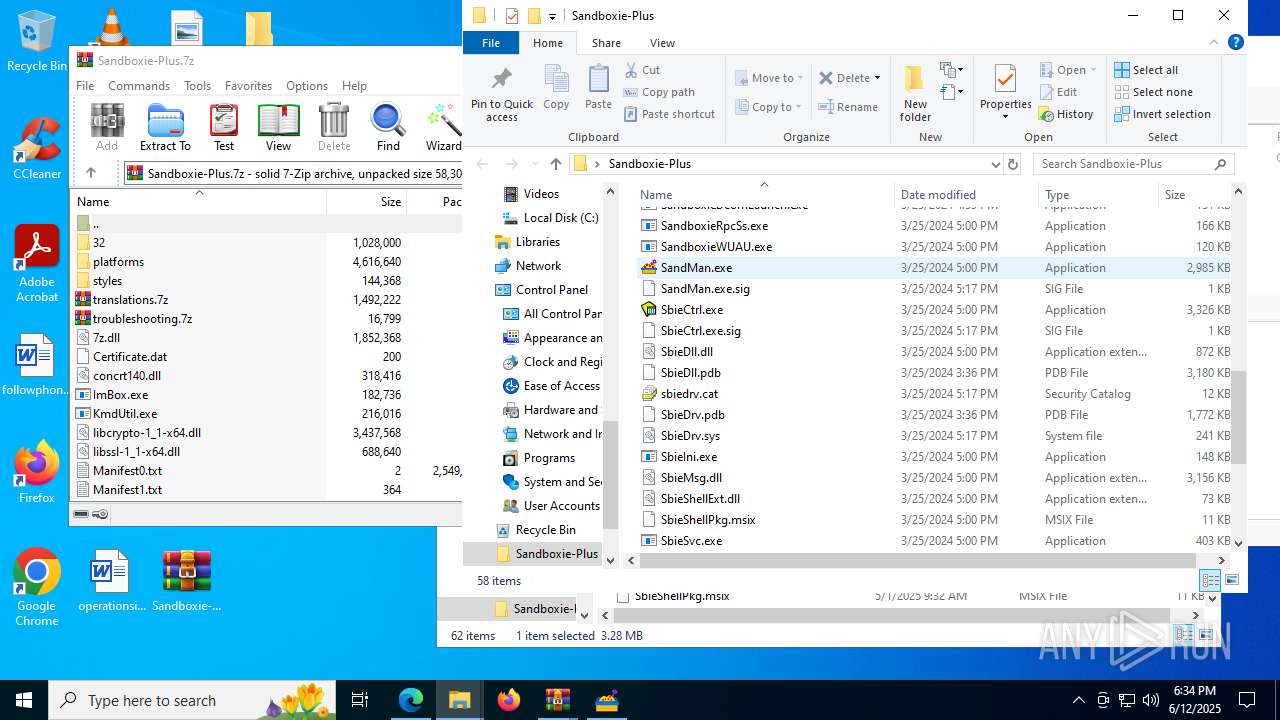
Drops a system driver (possible attempt to evade defenses)
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- extrac32.exe (PID: 3592)
- WinRAR.exe (PID: 5652)
Creates or modifies Windows services
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- KmdUtil.exe (PID: 8168)
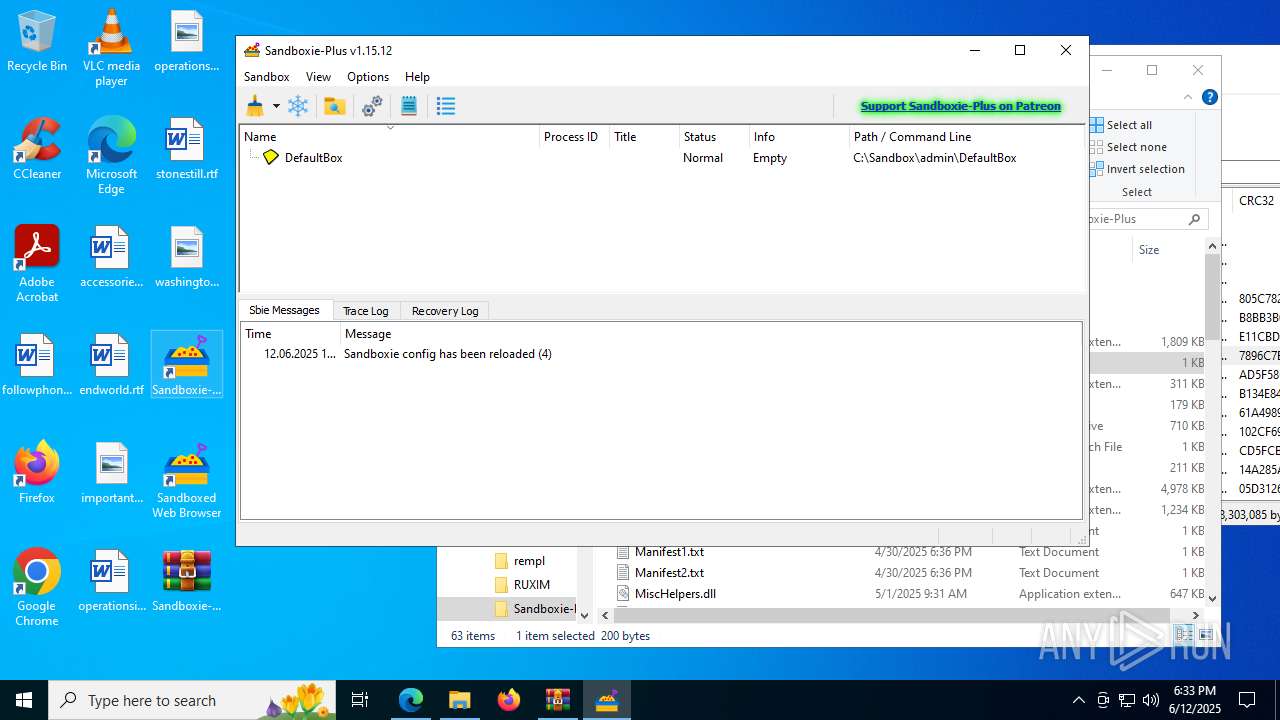
Executes as Windows Service
- SbieSvc.exe (PID: 8144)
There is functionality for taking screenshot (YARA)
- SbieSvc.exe (PID: 8144)
- SandMan.exe (PID: 7676)
- SandMan.exe (PID: 5248)
- SandMan.exe (PID: 5288)
- SandMan.exe (PID: 6036)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3352)
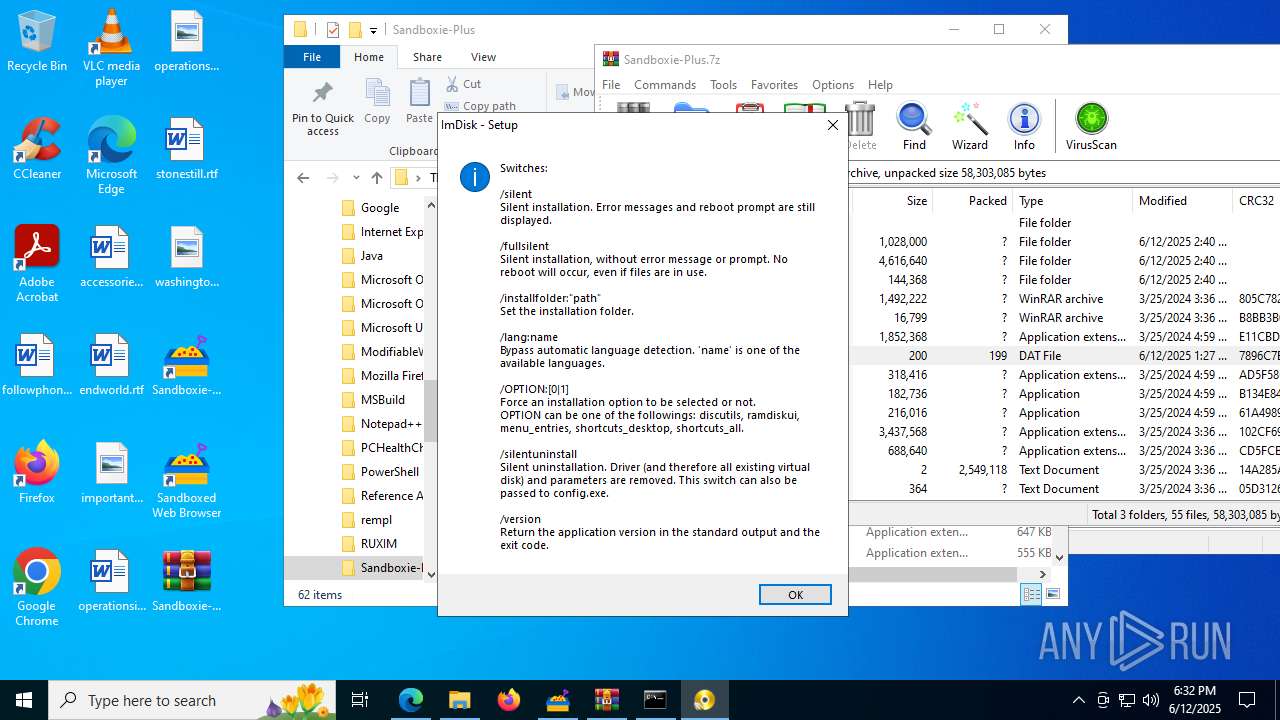
Executing commands from a ".bat" file
- cmd.exe (PID: 3352)
Application launched itself
- cmd.exe (PID: 3352)
The executable file from the user directory is run by the CMD process
- config.exe (PID: 8044)
INFO
Application launched itself
- msedge.exe (PID: 4156)
Executable content was dropped or overwritten
- msedge.exe (PID: 4156)
- msedge.exe (PID: 2680)
- WinRAR.exe (PID: 5652)
Checks supported languages
- identity_helper.exe (PID: 7540)
- Sandboxie-Plus-x64-v1.15.12.exe (PID: 1636)
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 7484)
- Sandboxie-Plus-x64-v1.15.12.exe (PID: 6776)
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- KmdUtil.exe (PID: 8168)
- KmdUtil.exe (PID: 7188)
- SbieSvc.exe (PID: 8144)
- KmdUtil.exe (PID: 8136)
- Start.exe (PID: 7656)
- SandMan.exe (PID: 7676)
Reads the computer name
- identity_helper.exe (PID: 7540)
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 7484)
- Sandboxie-Plus-x64-v1.15.12.exe (PID: 6776)
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- KmdUtil.exe (PID: 8168)
- KmdUtil.exe (PID: 8136)
- SbieSvc.exe (PID: 8144)
- KmdUtil.exe (PID: 7188)
- SandMan.exe (PID: 7676)
Reads Environment values
- identity_helper.exe (PID: 7540)
- SandMan.exe (PID: 7676)
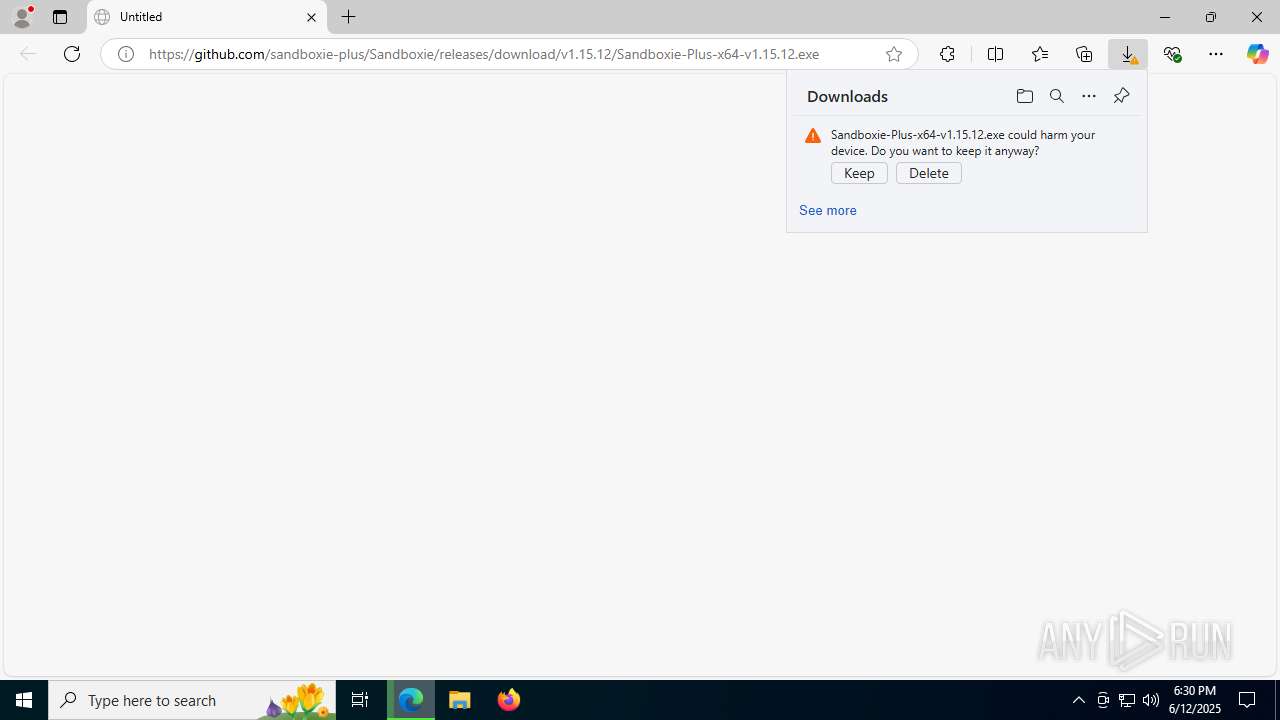
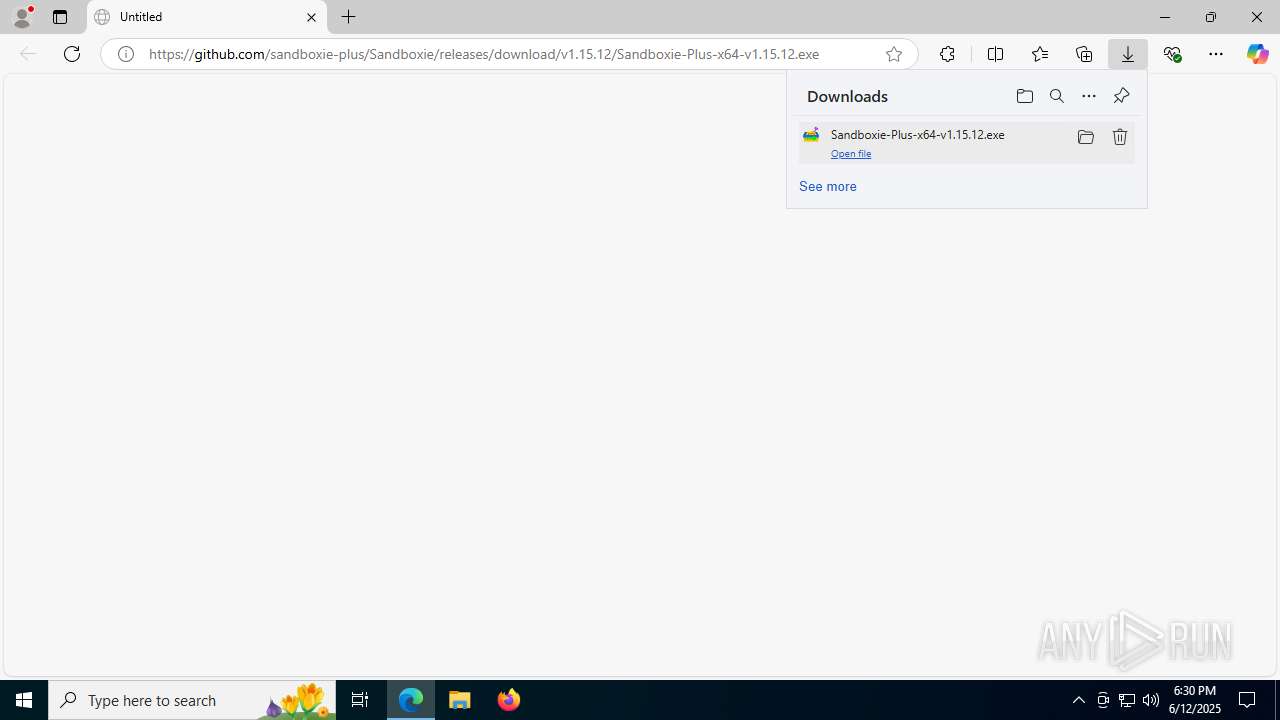
Launching a file from the Downloads directory
- msedge.exe (PID: 4156)
Create files in a temporary directory
- Sandboxie-Plus-x64-v1.15.12.exe (PID: 1636)
- Sandboxie-Plus-x64-v1.15.12.exe (PID: 6776)
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- SandMan.exe (PID: 7676)
Process checks computer location settings
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 7484)
The sample compiled with english language support
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- WinRAR.exe (PID: 5652)
- extrac32.exe (PID: 3592)
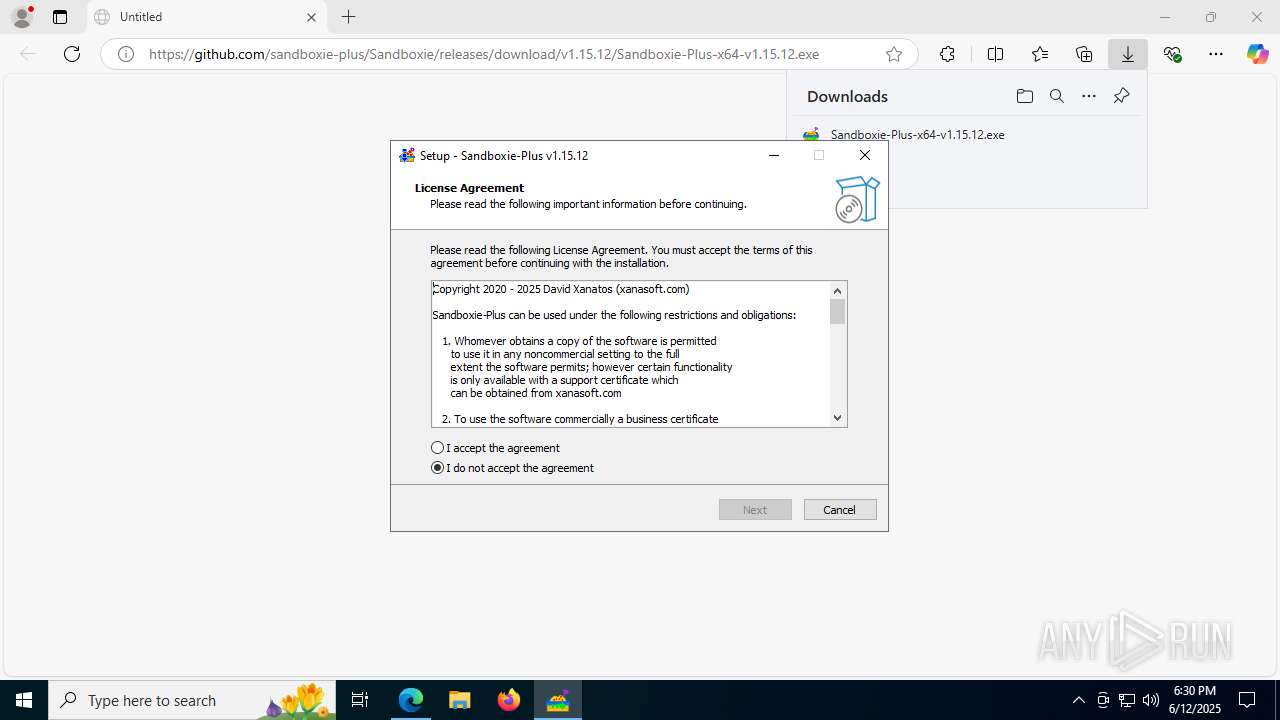
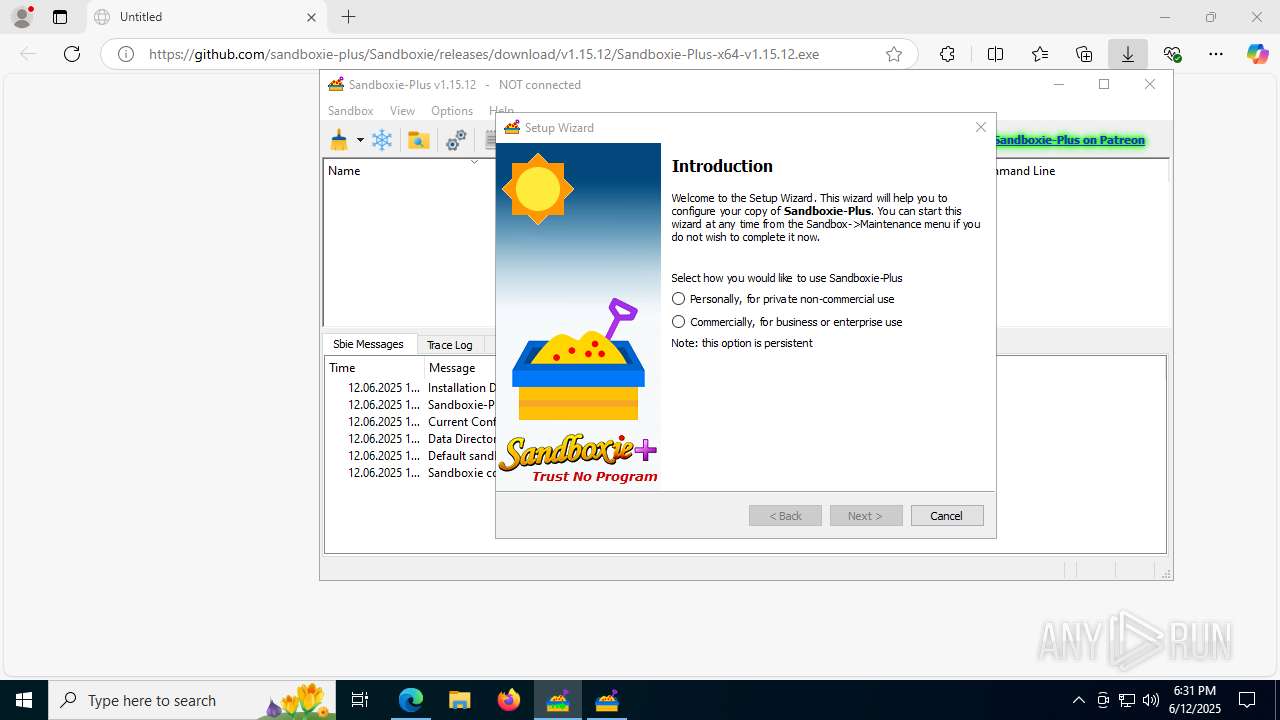
Detects InnoSetup installer (YARA)
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 7484)
- Sandboxie-Plus-x64-v1.15.12.exe (PID: 6776)
- Sandboxie-Plus-x64-v1.15.12.exe (PID: 1636)
Compiled with Borland Delphi (YARA)
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 7484)
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- Sandboxie-Plus-x64-v1.15.12.exe (PID: 6776)
- Sandboxie-Plus-x64-v1.15.12.exe (PID: 1636)
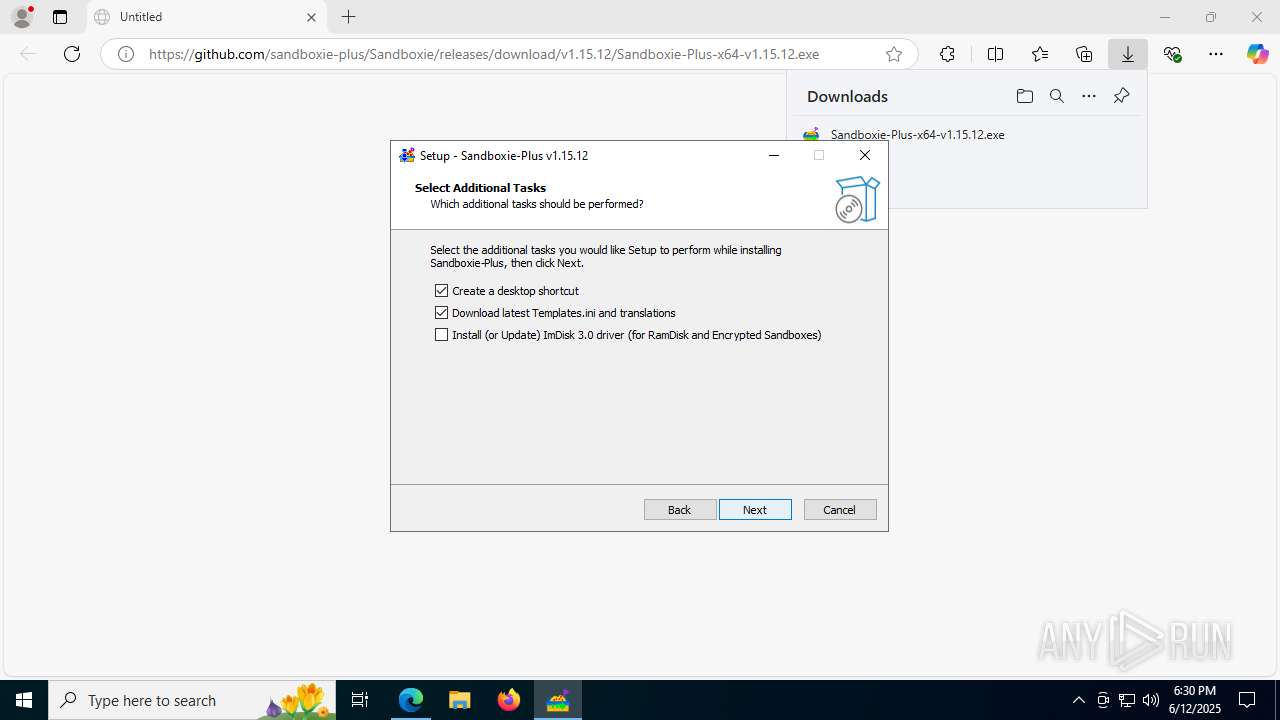
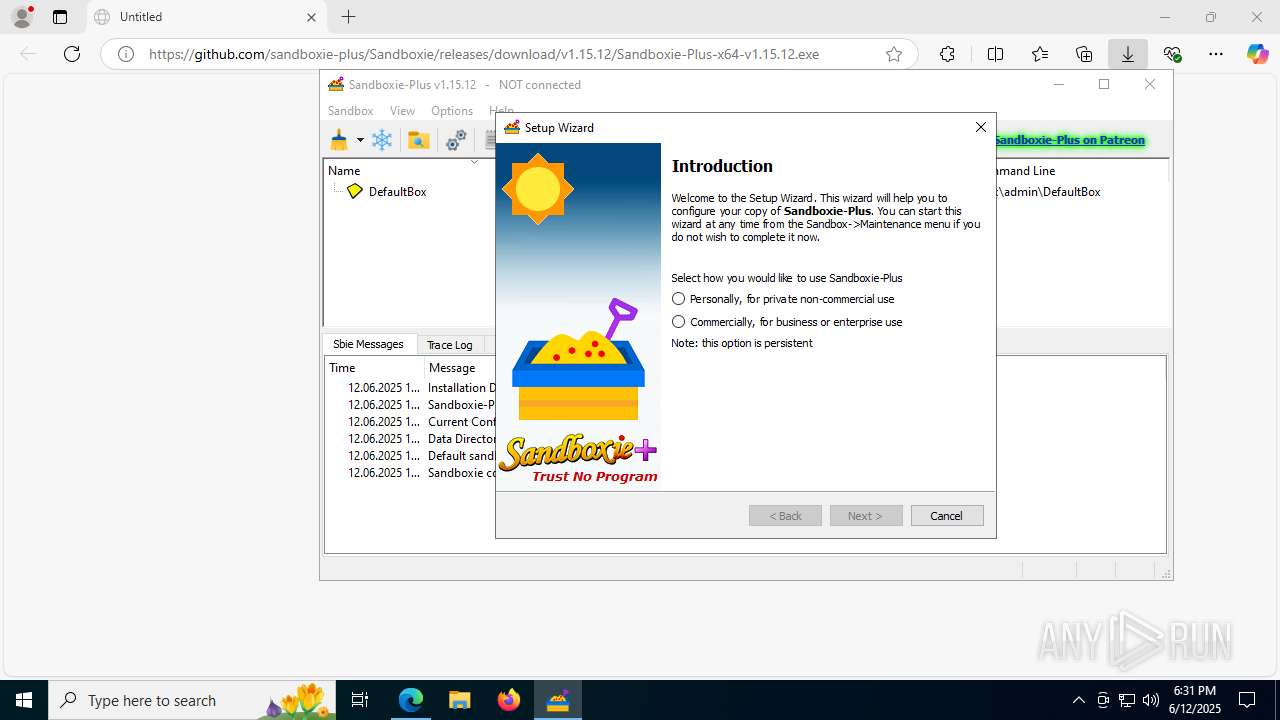
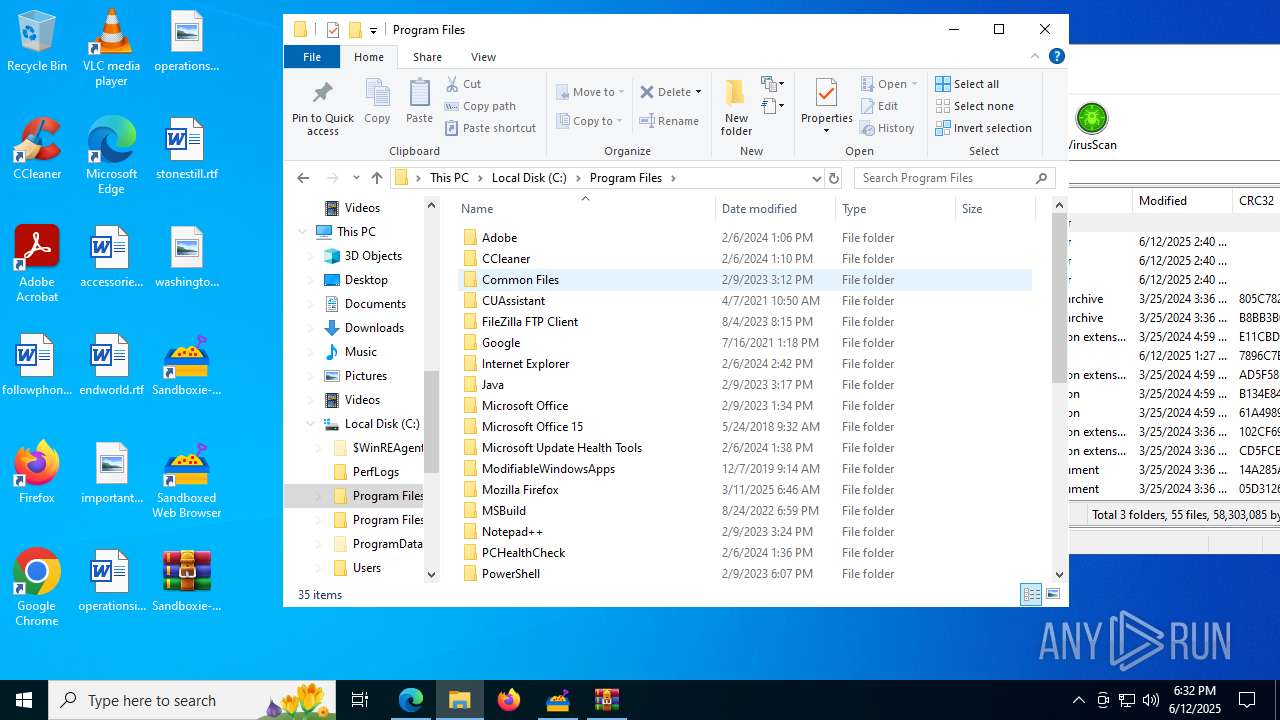
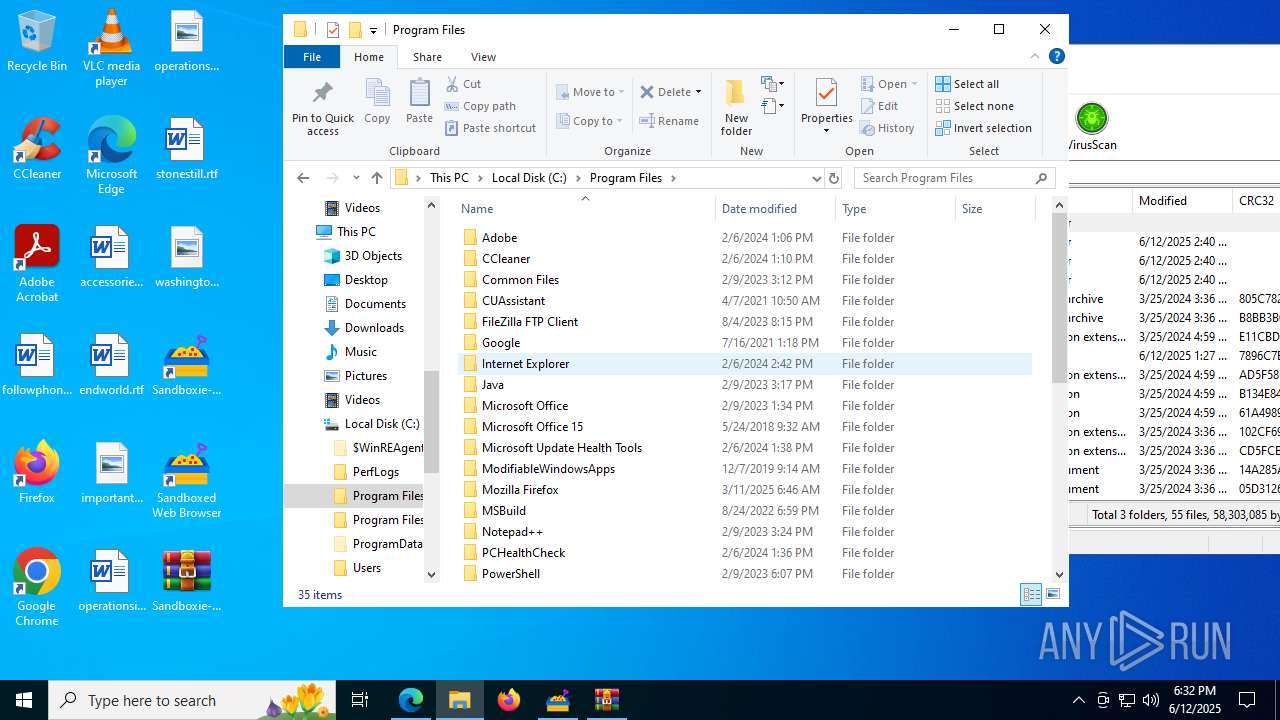
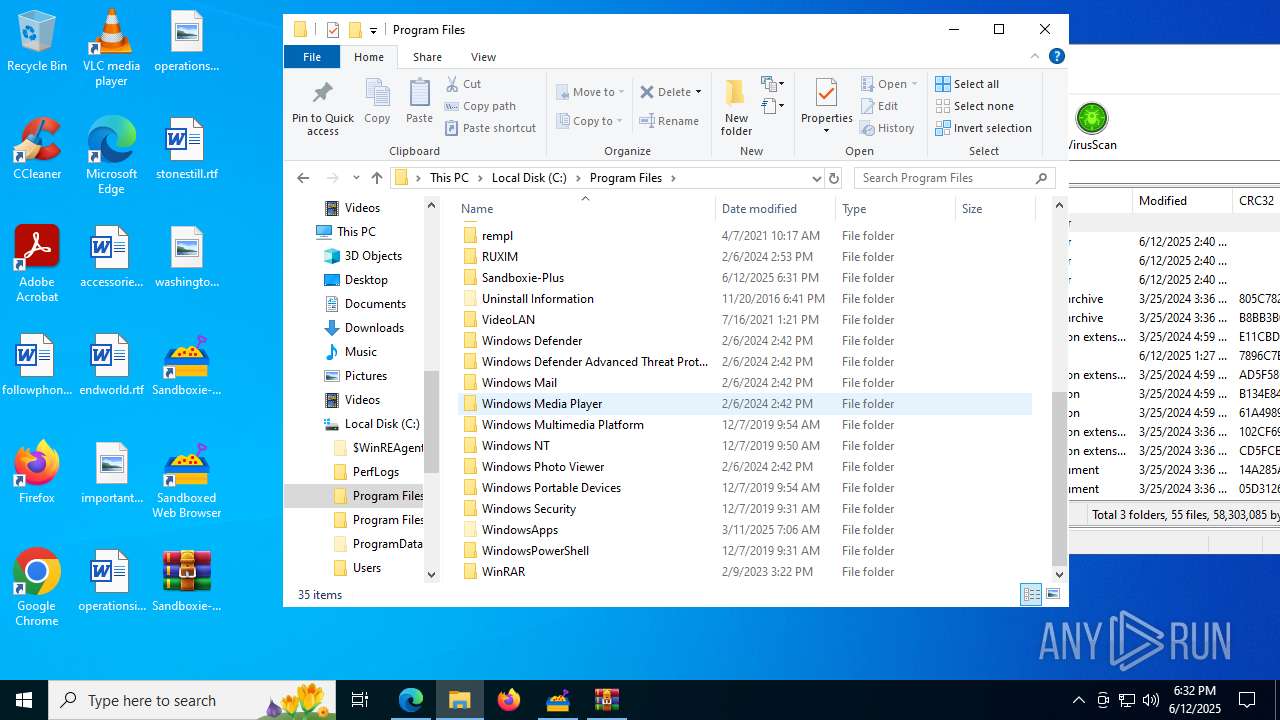
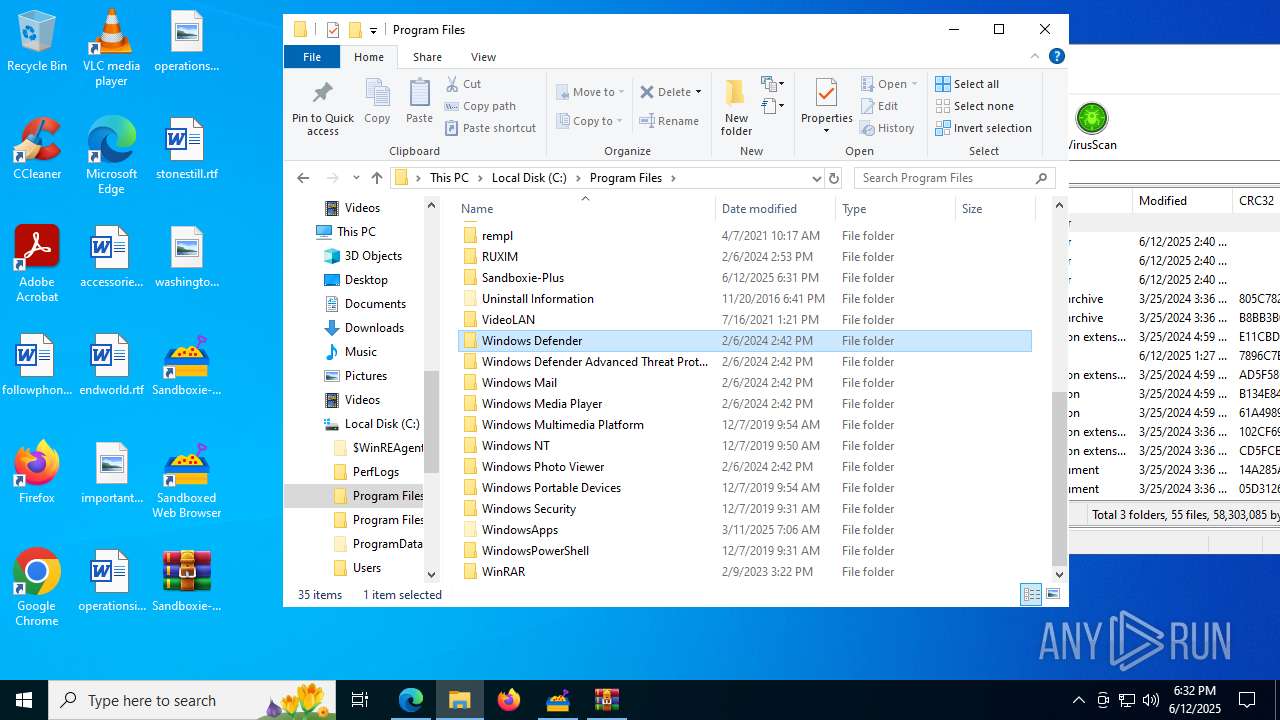
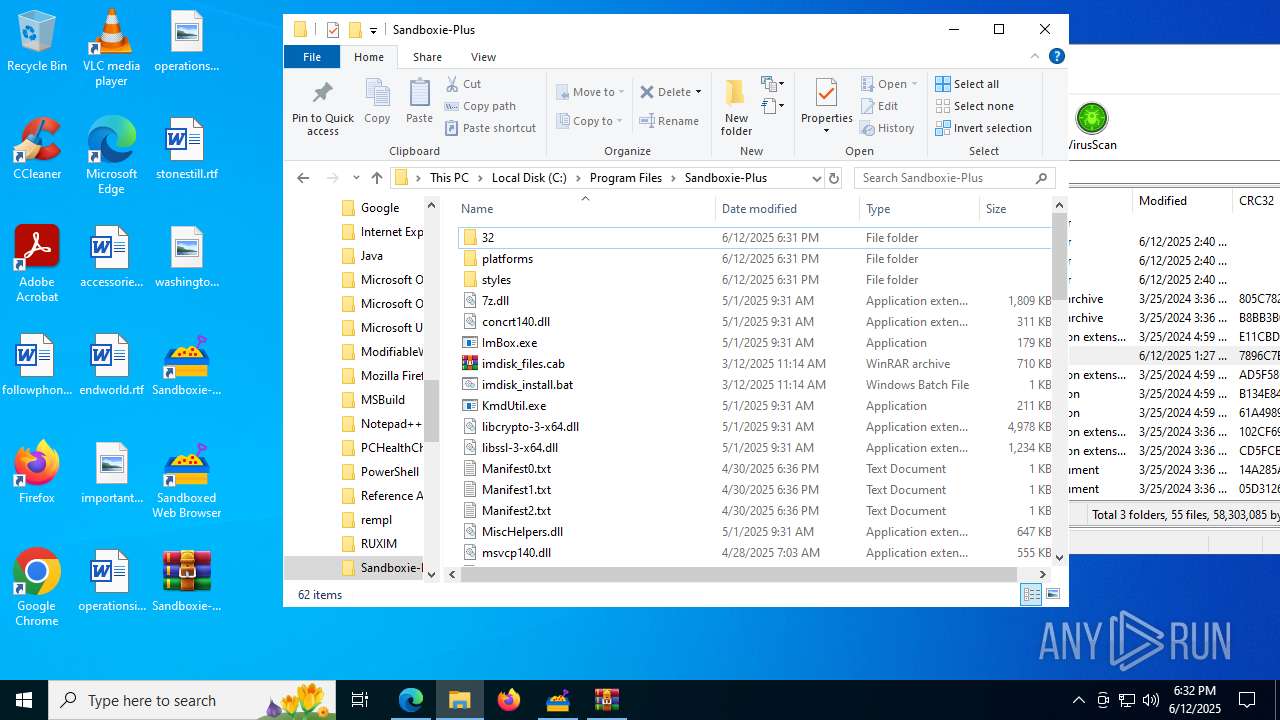
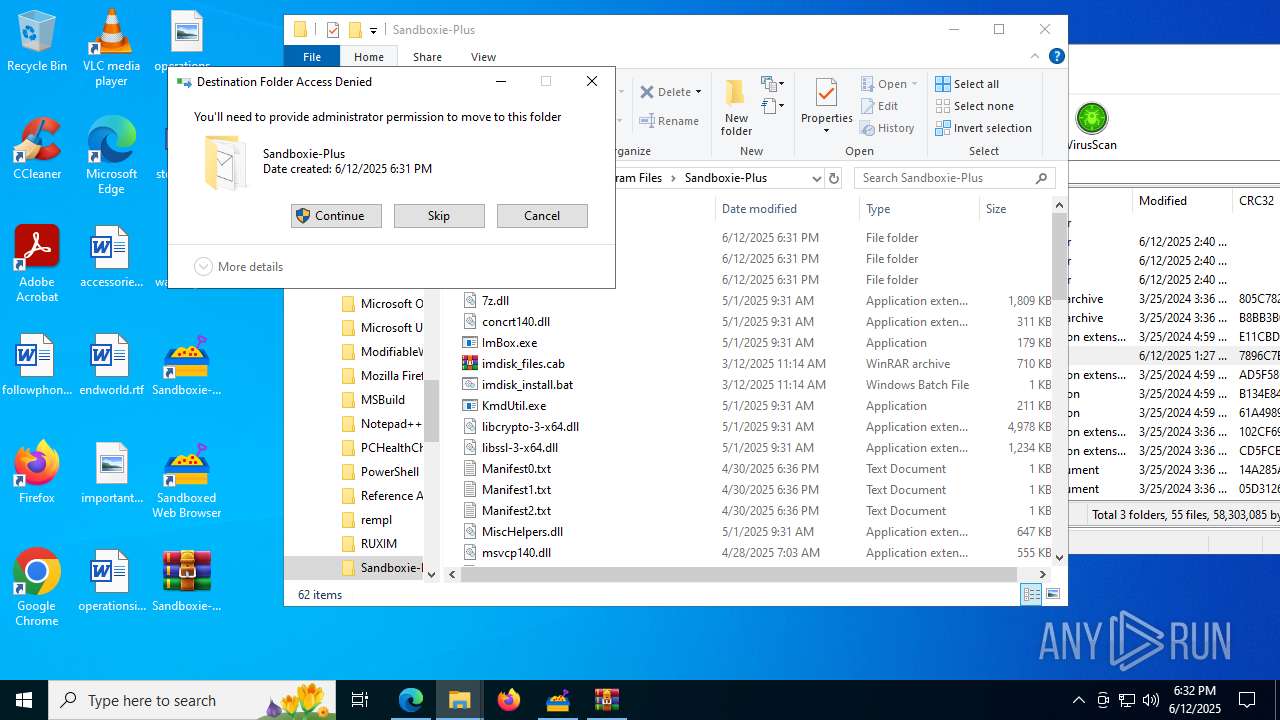
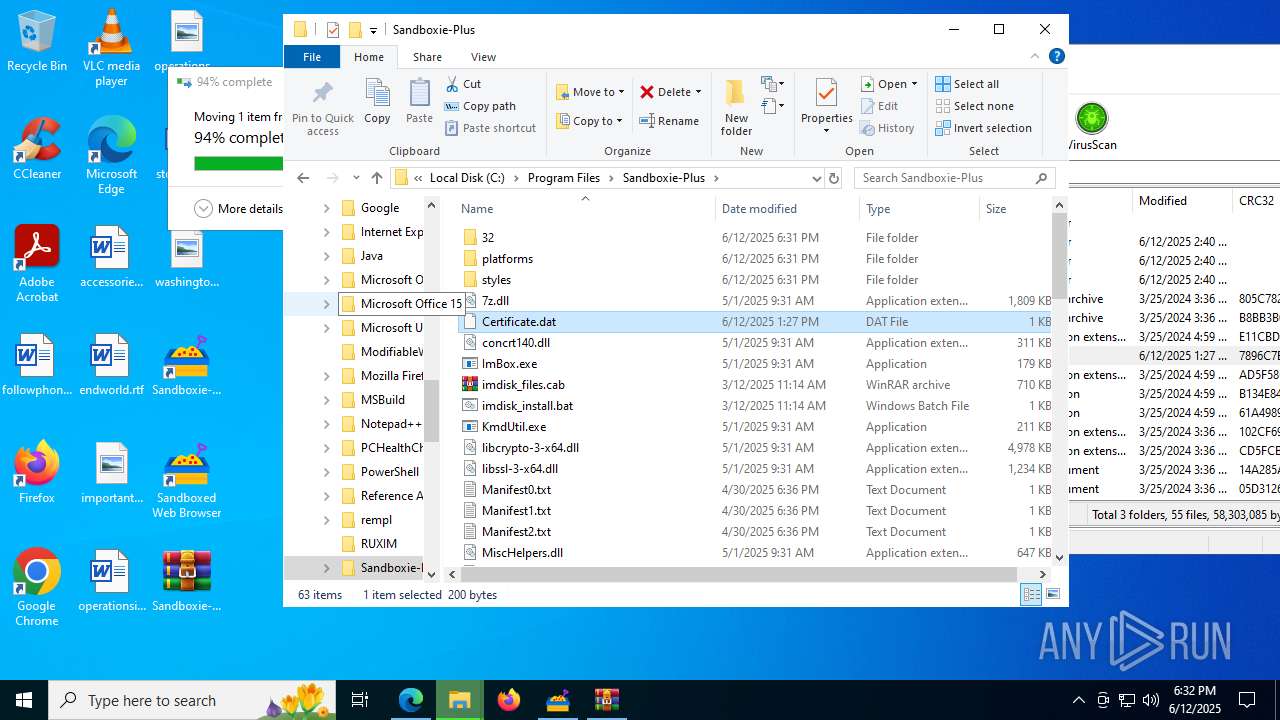
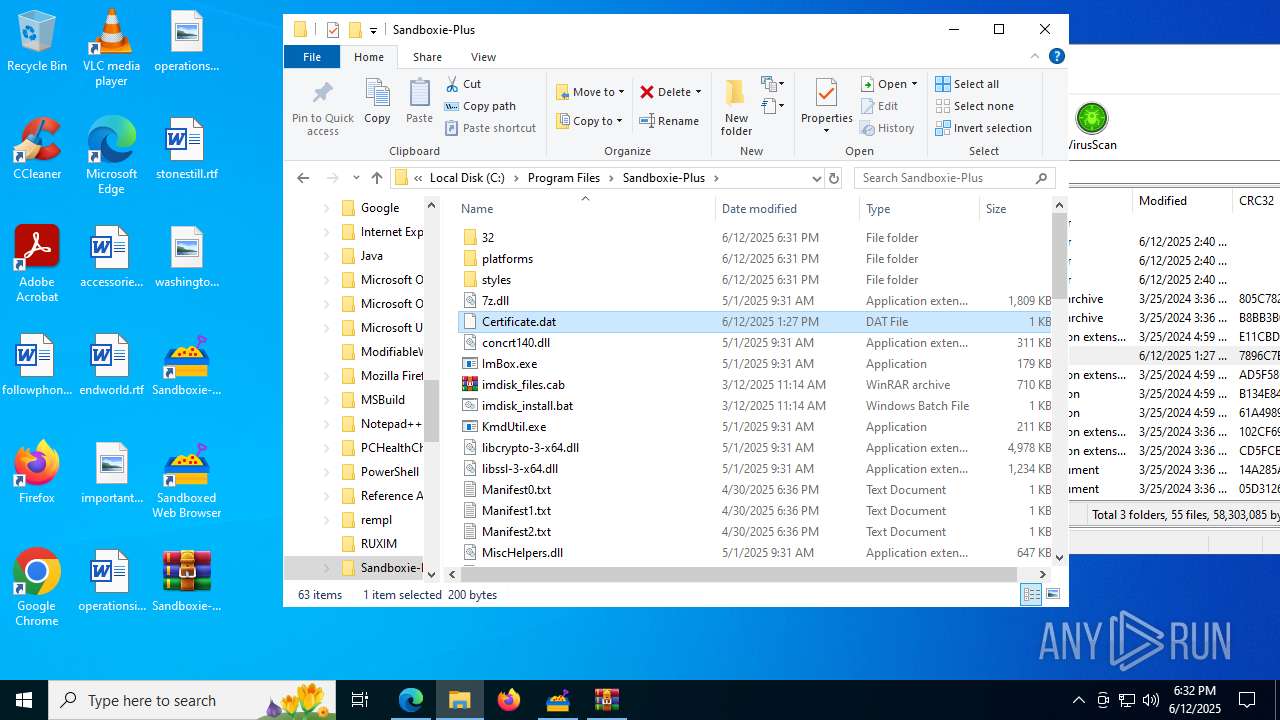
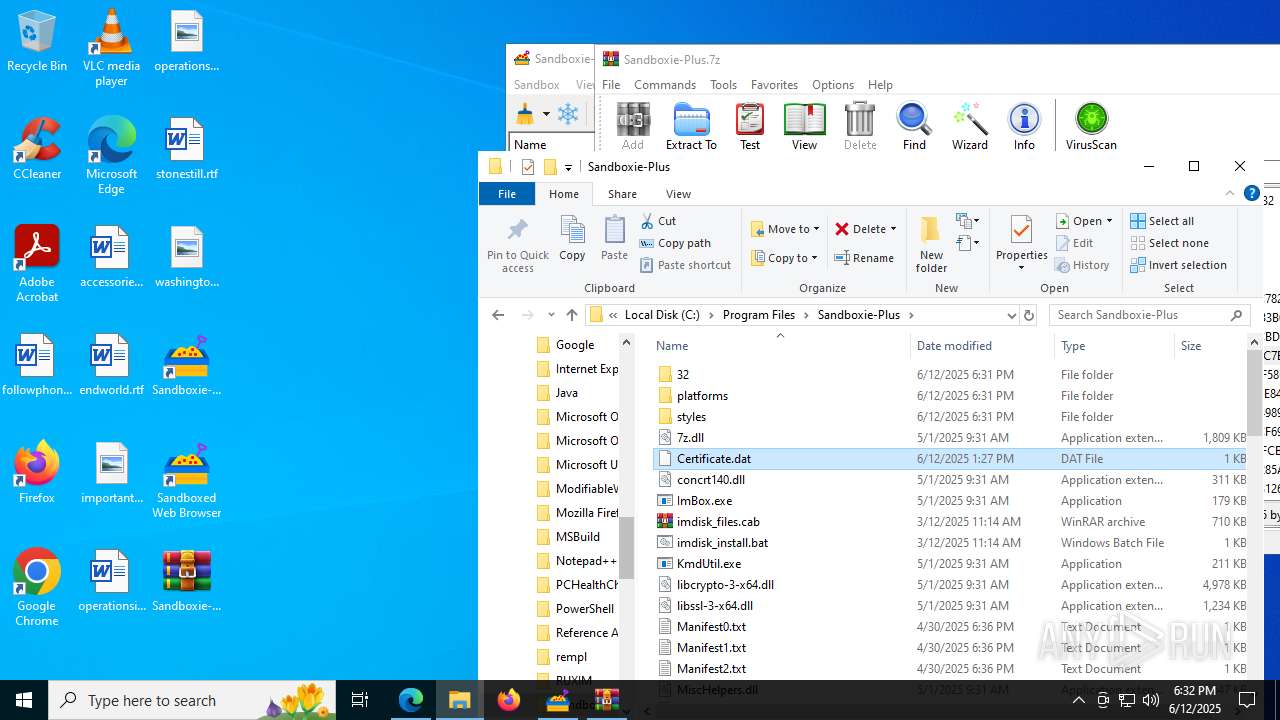
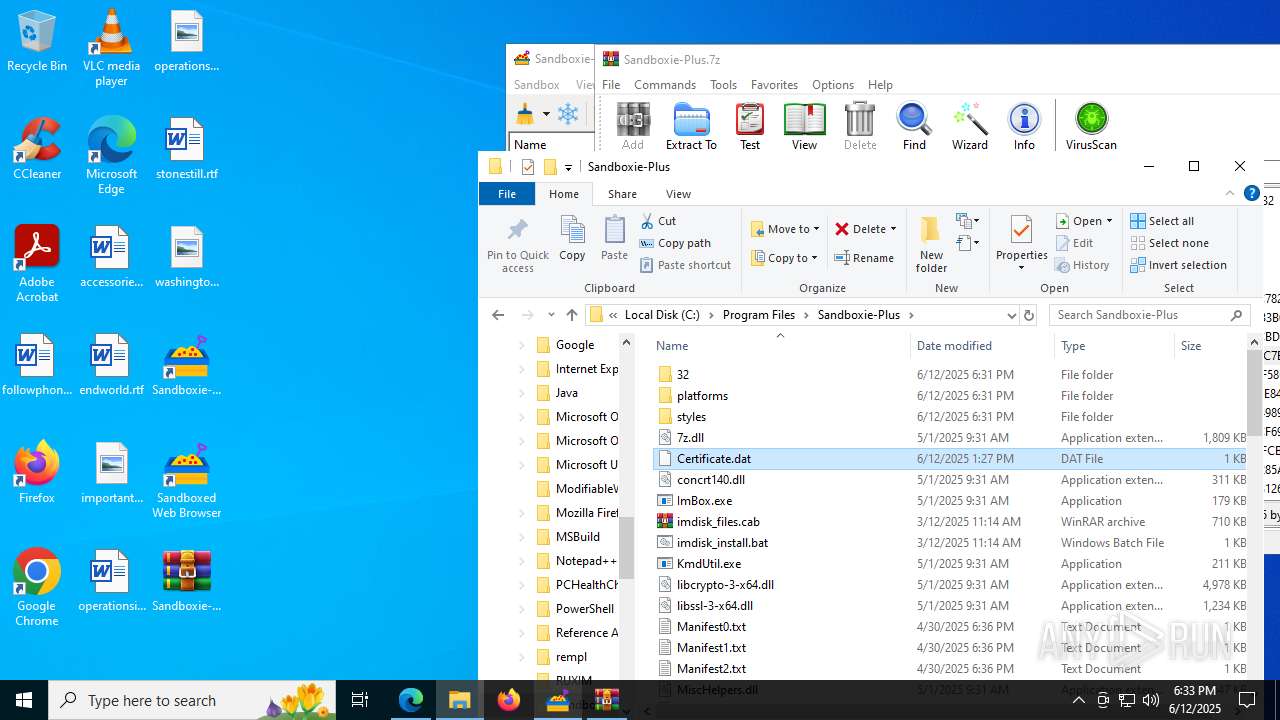
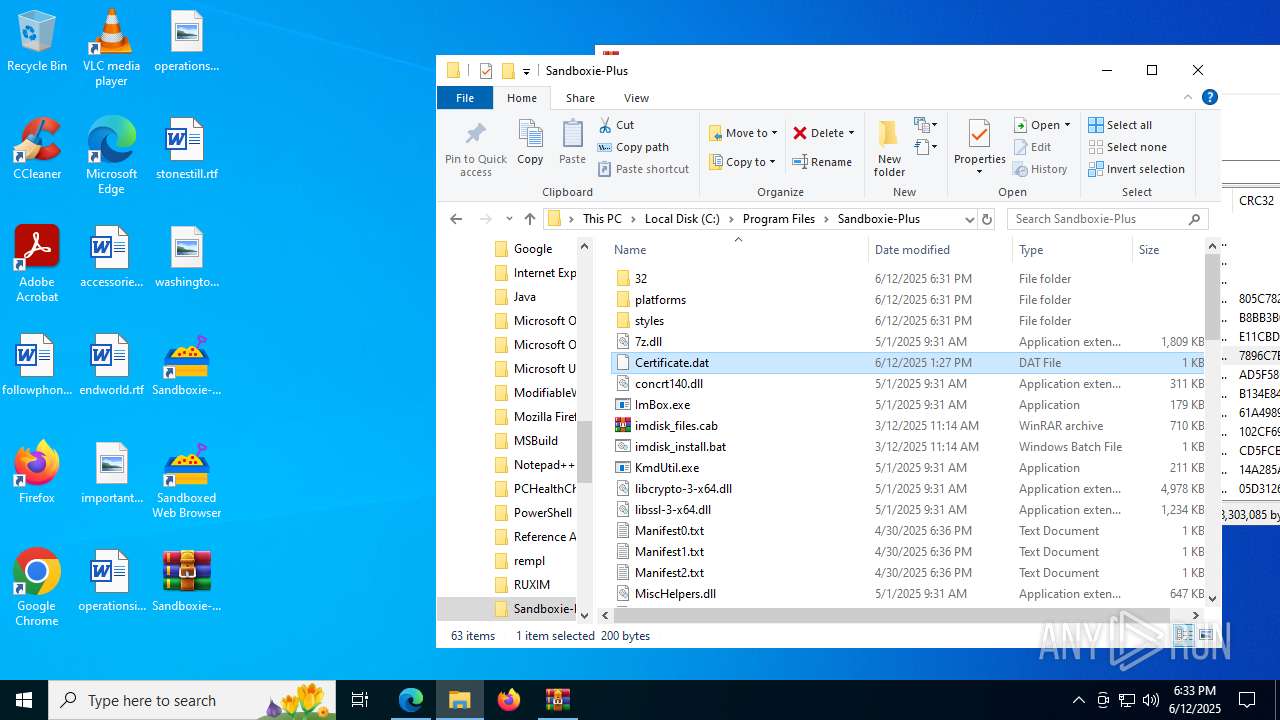
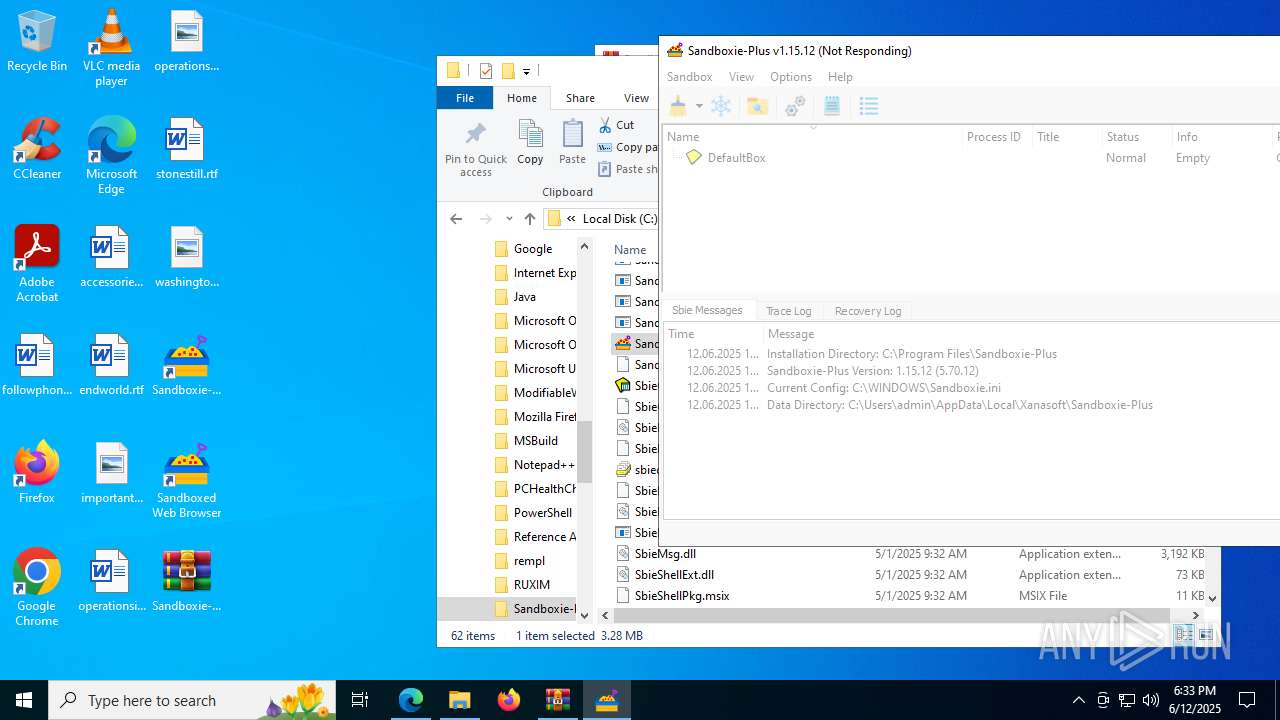
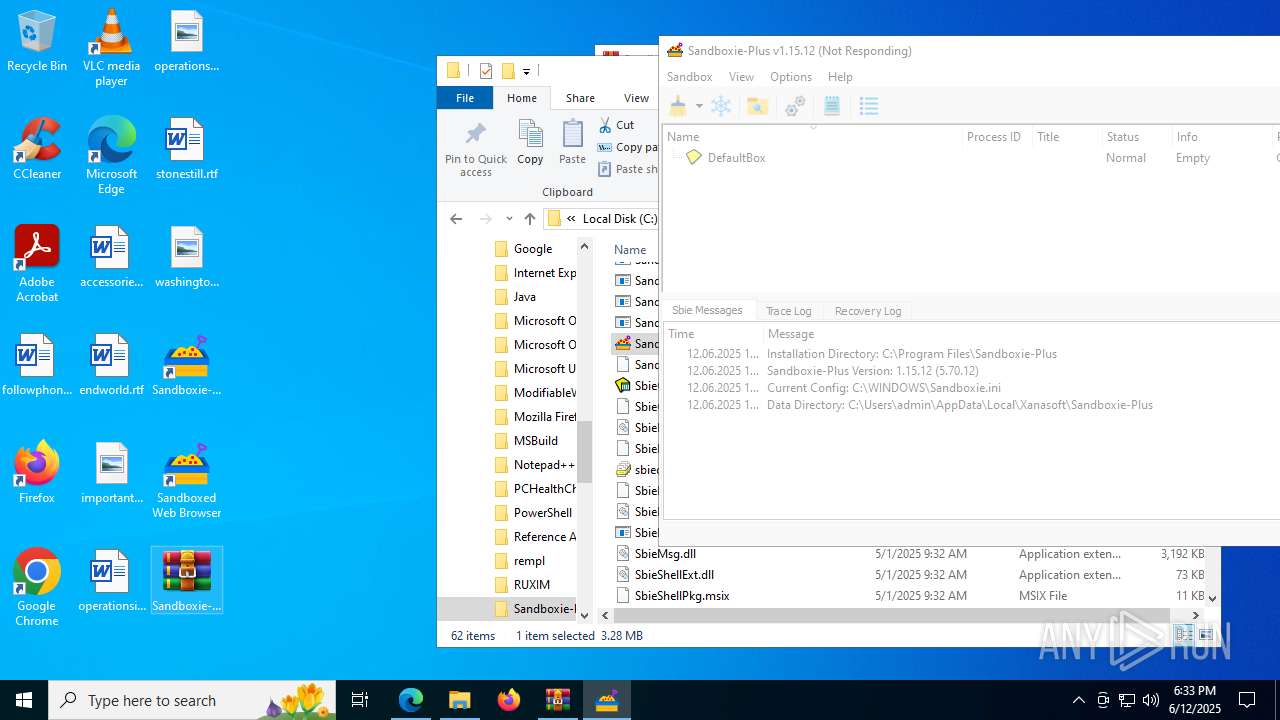
Creates files in the program directory
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
Creates files or folders in the user directory
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
- SandMan.exe (PID: 7676)
Creates a software uninstall entry
- Sandboxie-Plus-x64-v1.15.12.tmp (PID: 2140)
Reads the machine GUID from the registry
- SandMan.exe (PID: 7676)
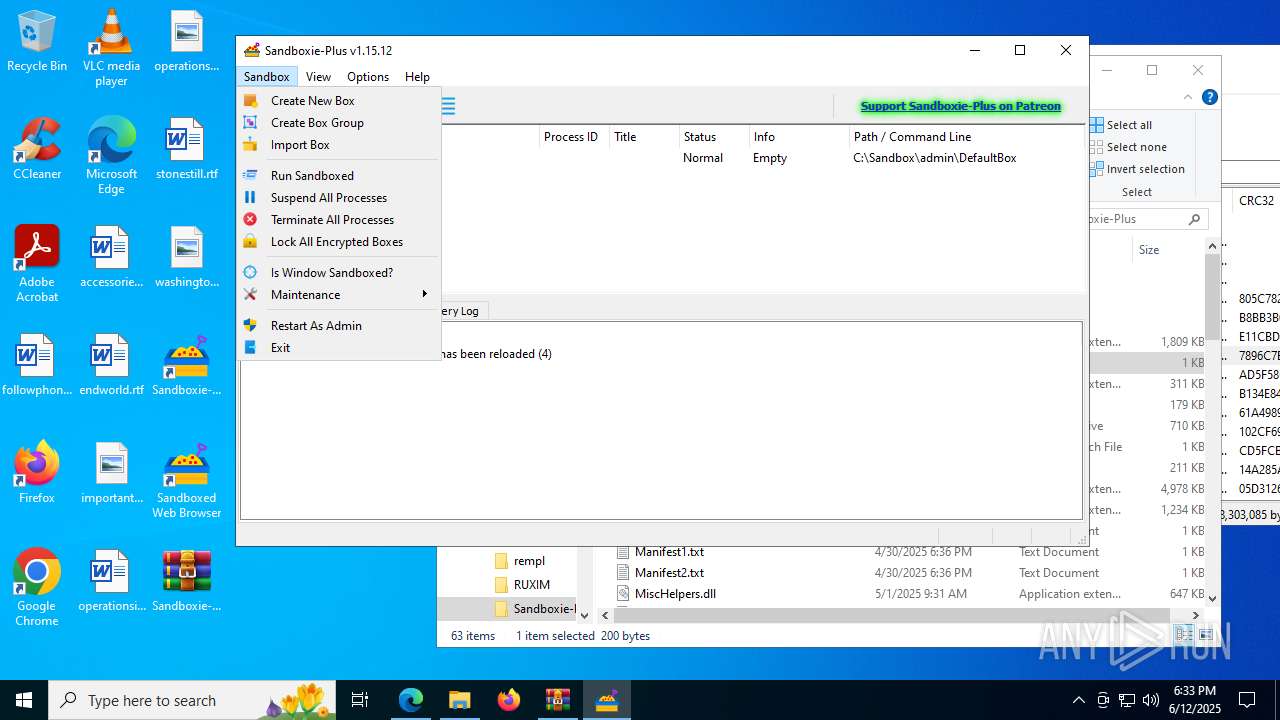
Launching a file from a Registry key
- SandMan.exe (PID: 7676)
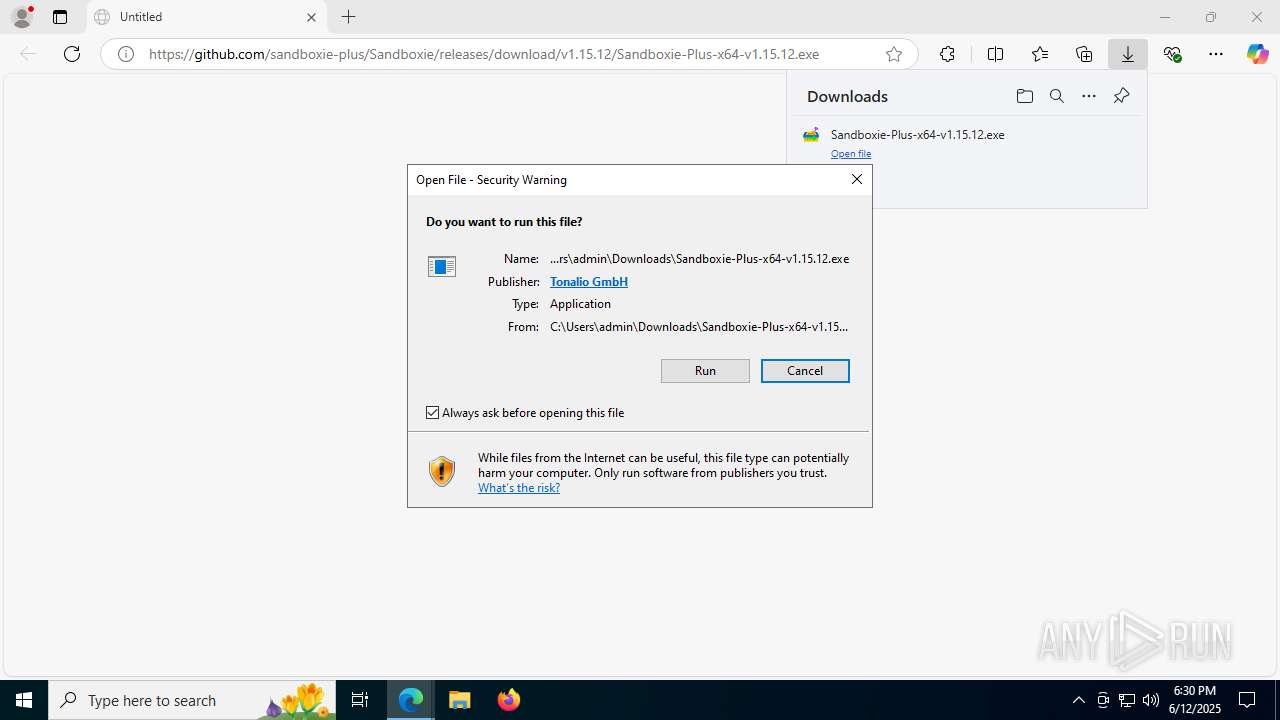
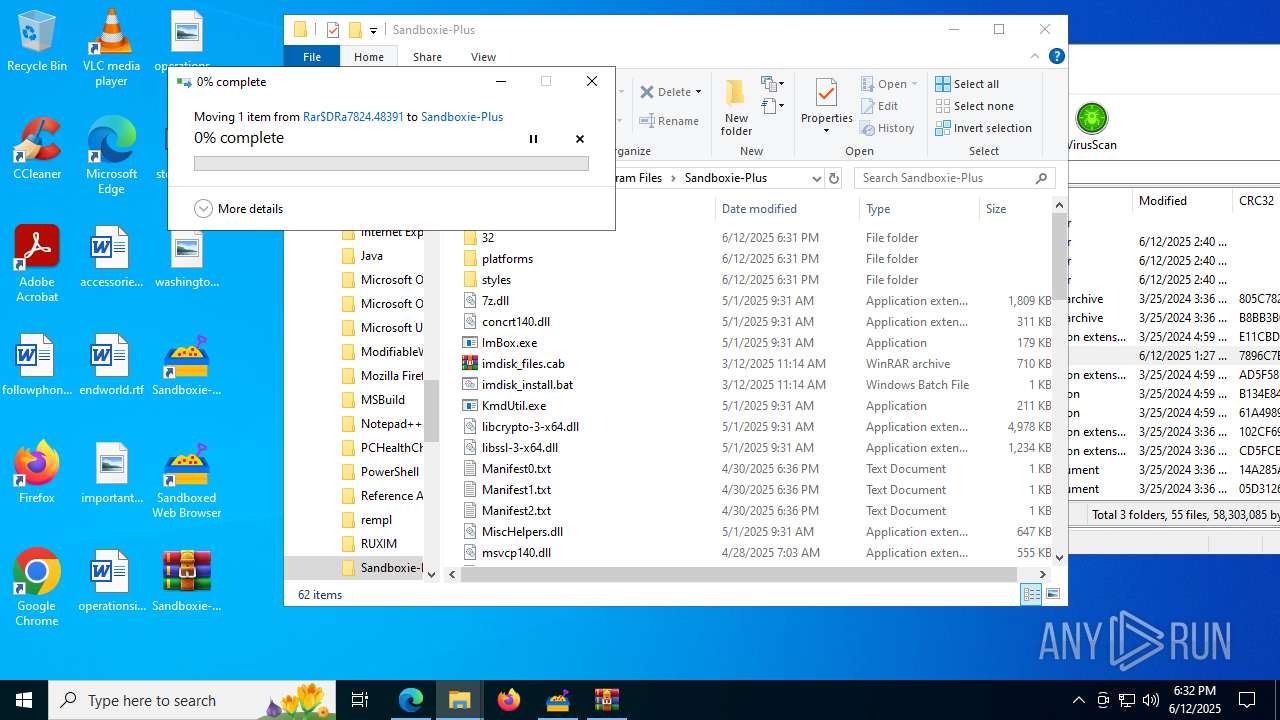
Manual execution by a user
- WinRAR.exe (PID: 7824)
- cmd.exe (PID: 3352)
- SandMan.exe (PID: 2028)
- SandMan.exe (PID: 5248)
- WinRAR.exe (PID: 5652)
- SandMan.exe (PID: 6036)
- SandMan.exe (PID: 5288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
219
Monitored processes
64
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
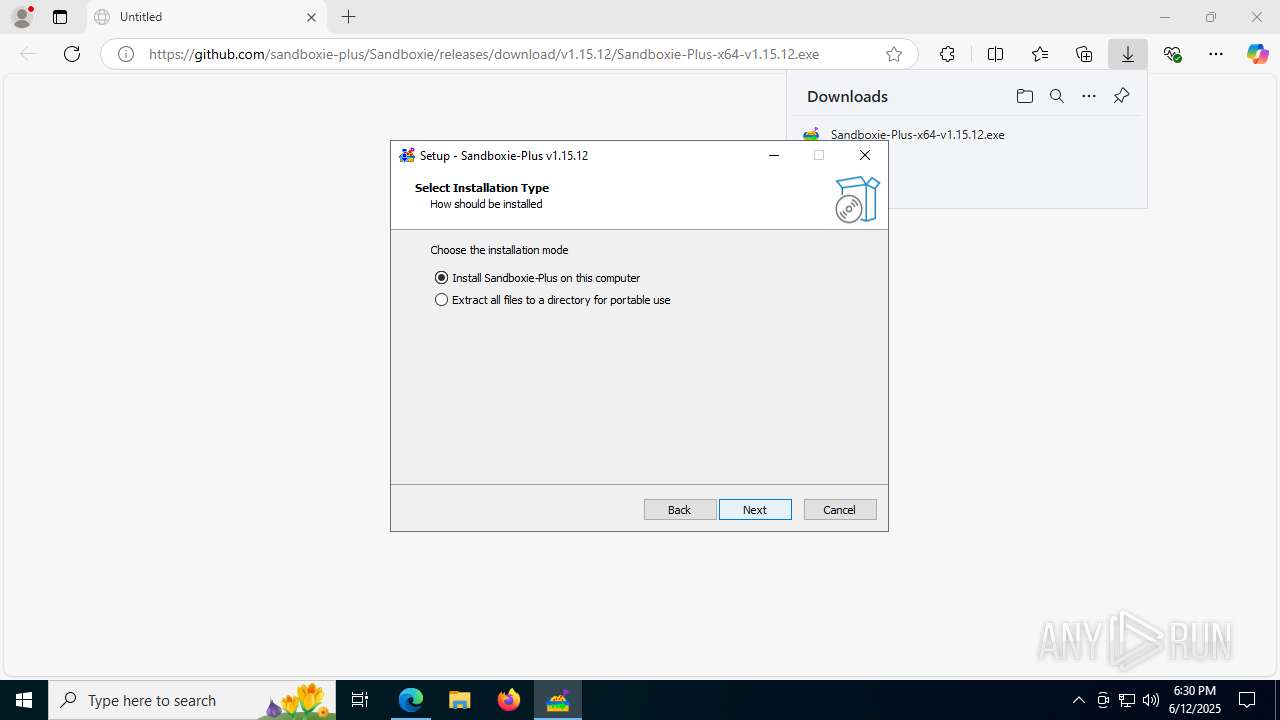
| 1636 | "C:\Users\admin\Downloads\Sandboxie-Plus-x64-v1.15.12.exe" | C:\Users\admin\Downloads\Sandboxie-Plus-x64-v1.15.12.exe | msedge.exe | ||||||||||||
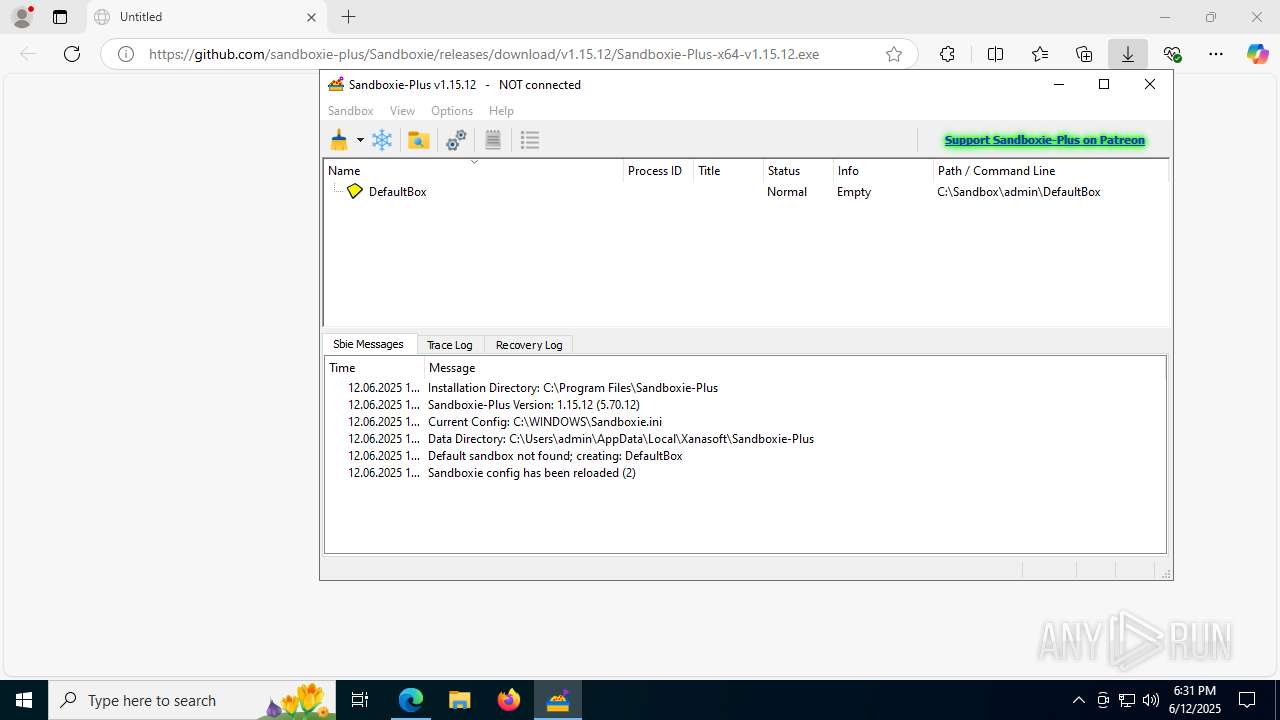
User: admin Company: http://xanasoft.com/ Integrity Level: MEDIUM Description: Sandboxie-Plus Setup Exit code: 0 Version: 1.15.12 Modules
| |||||||||||||||
| 1720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4952,i,8006101993371749143,9626589321302953412,262144 --variations-seed-version --mojo-platform-channel-handle=4904 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
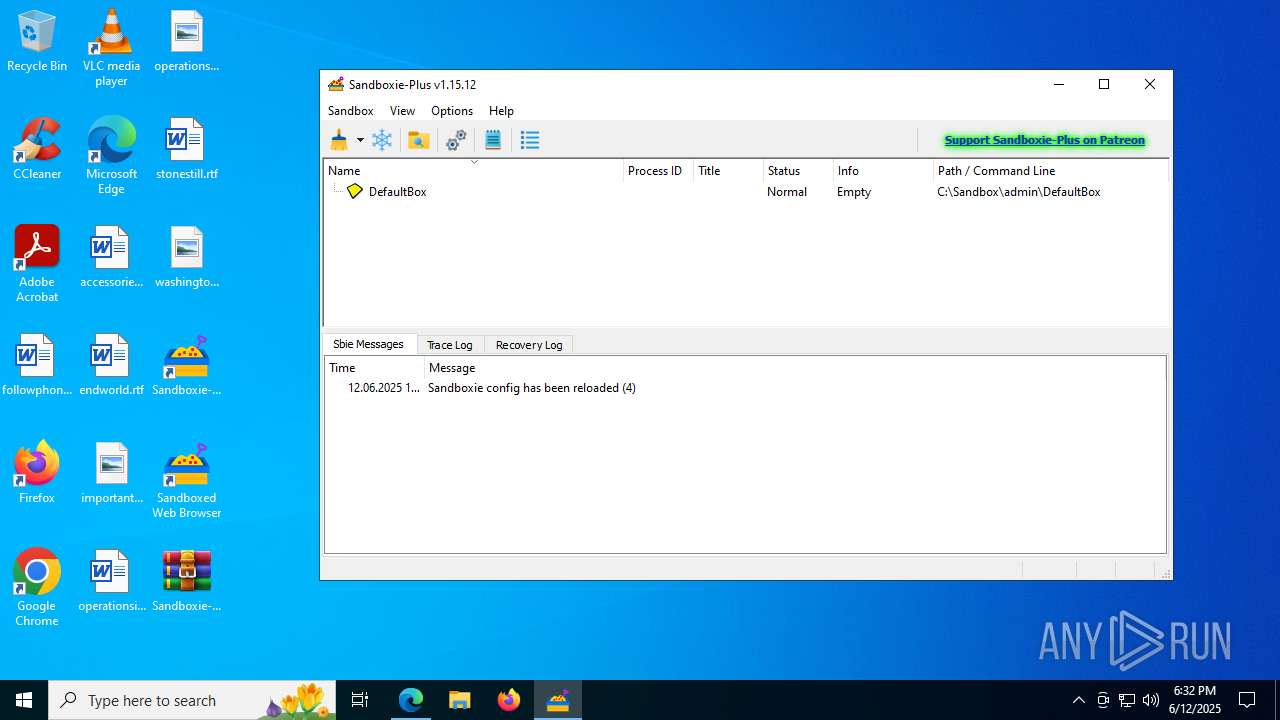
| 2028 | "C:\Program Files\Sandboxie-Plus\SandMan.exe" | C:\Program Files\Sandboxie-Plus\SandMan.exe | — | explorer.exe | |||||||||||
User: admin Company: sandboxie-plus.com Integrity Level: MEDIUM Description: Sandboxie Manager Exit code: 0 Version: 1.15.12 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\Temp\is-G1M9U.tmp\Sandboxie-Plus-x64-v1.15.12.tmp" /SL5="$702E0,22613692,805376,C:\Users\admin\Downloads\Sandboxie-Plus-x64-v1.15.12.exe" /SPAWNWND=$60322 /NOTIFYWND=$C02EA | C:\Users\admin\AppData\Local\Temp\is-G1M9U.tmp\Sandboxie-Plus-x64-v1.15.12.tmp | Sandboxie-Plus-x64-v1.15.12.exe | ||||||||||||
User: admin Company: http://xanasoft.com/ Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4244,i,8006101993371749143,9626589321302953412,262144 --variations-seed-version --mojo-platform-channel-handle=4328 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2264,i,8006101993371749143,9626589321302953412,262144 --variations-seed-version --mojo-platform-channel-handle=2508 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3000 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5744,i,8006101993371749143,9626589321302953412,262144 --variations-seed-version --mojo-platform-channel-handle=4736 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
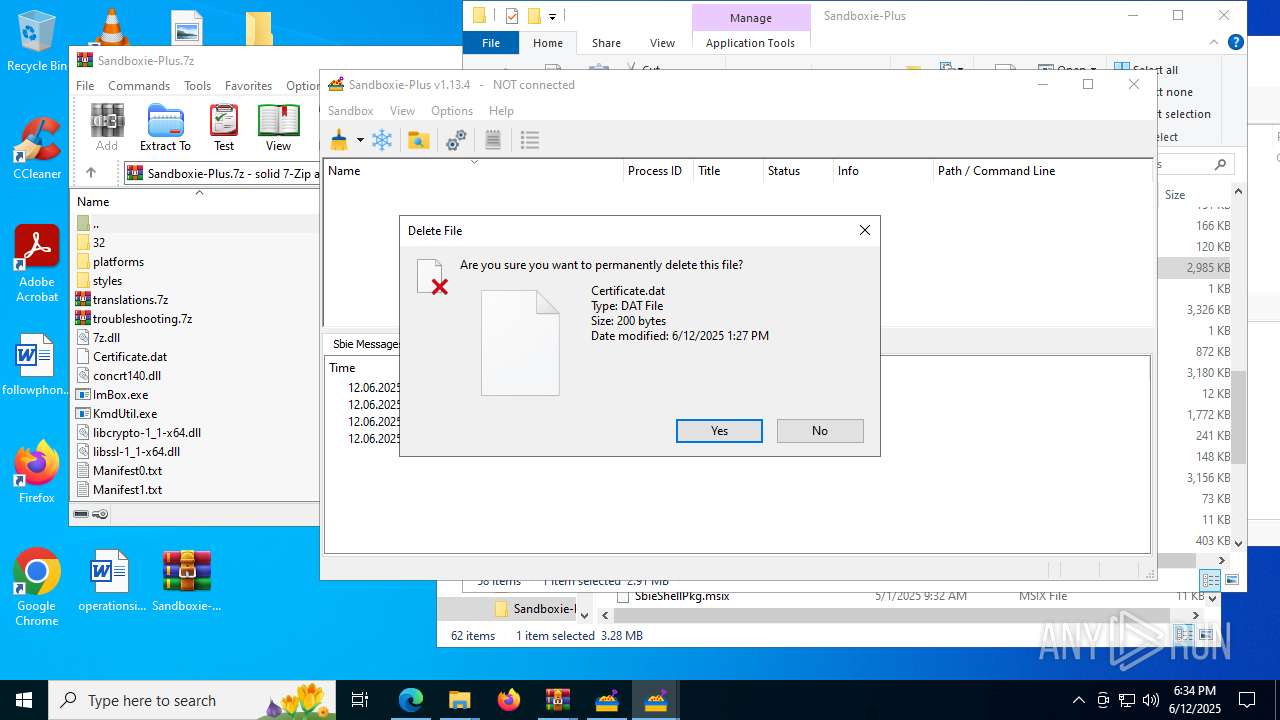
| 3352 | C:\WINDOWS\system32\cmd.exe /c ""C:\Program Files\Sandboxie-Plus\imdisk_install.bat" C:\Users\admin\AppData\Local\Temp\Rar$DRa7824.47847\Certificate.dat" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3592 | extrac32.exe /e /l "C:\Users\admin\AppData\Local\Temp\ImDisk183249.41" "C:\Program Files\Sandboxie-Plus\imdisk_files.cab" | C:\Windows\System32\extrac32.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® CAB File Extract Utility Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 903
Read events
17 792
Write events
94
Delete events
17
Modification events
| (PID) Process: | (5460) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (5460) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (5460) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (5460) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (5460) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 606873362 | |||
| (PID) Process: | (5460) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31185864 | |||
| (PID) Process: | (5460) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5460) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5460) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5460) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
187
Suspicious files
276
Text files
170
Unknown types
57
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1765ed.TMP | — | |
MD5:— | SHA256:— | |||
| 4156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1765ed.TMP | — | |
MD5:— | SHA256:— | |||
| 4156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1765ed.TMP | — | |
MD5:— | SHA256:— | |||
| 4156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1765ed.TMP | — | |
MD5:— | SHA256:— | |||
| 4156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17660d.TMP | — | |
MD5:— | SHA256:— | |||
| 4156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
68
DNS requests
71
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7212 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1750174112&P2=404&P3=2&P4=QhOGFr6MgN0F0MFySqaeTxRfrOsPt703shyVUR9W619hTk0hCCEiiItniFZYiBAc%2b1aazY9YKw2G2dHmMx15sg%3d%3d | unknown | — | — | whitelisted |
7212 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1750170511&P2=404&P3=2&P4=kRE58BksBTqiZp6D9Ee0%2b1K152rXTFm%2fwvK0ONGEzi3DkHpyCCb5gAq%2bLxYbGVJ5AzrgeB88EfdQH7xh%2bDS9%2bA%3d%3d | unknown | — | — | whitelisted |
7212 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1750174112&P2=404&P3=2&P4=QhOGFr6MgN0F0MFySqaeTxRfrOsPt703shyVUR9W619hTk0hCCEiiItniFZYiBAc%2b1aazY9YKw2G2dHmMx15sg%3d%3d | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.16.252.233:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7212 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1750166910&P2=404&P3=2&P4=Y9vv%2buztauIcZcsDQck1PRpwXhqmD8WaDua%2fEO22ay%2ba051hXN%2b%2f0NH4k3oS6dQmGssCAjHGqBA9XcYpIwYcbQ%3d%3d | unknown | — | — | whitelisted |
7212 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/46df2db5-82ac-46a7-9d9e-cf1580d73a96?P1=1750286252&P2=404&P3=2&P4=OfswLU5ddLUPqQXBghDvFsKtJkC1fdfcYrsaZGZ%2bkz%2fDGtBRydwSjNvyY90Xv%2b9HD%2bL%2fMwoljX%2fNvc3kZ60wUQ%3d%3d | unknown | — | — | whitelisted |
7212 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1750166910&P2=404&P3=2&P4=Y9vv%2buztauIcZcsDQck1PRpwXhqmD8WaDua%2fEO22ay%2ba051hXN%2b%2f0NH4k3oS6dQmGssCAjHGqBA9XcYpIwYcbQ%3d%3d | unknown | — | — | whitelisted |
7212 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/46df2db5-82ac-46a7-9d9e-cf1580d73a96?P1=1750286252&P2=404&P3=2&P4=OfswLU5ddLUPqQXBghDvFsKtJkC1fdfcYrsaZGZ%2bkz%2fDGtBRydwSjNvyY90Xv%2b9HD%2bL%2fMwoljX%2fNvc3kZ60wUQ%3d%3d | unknown | — | — | whitelisted |
2680 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:VrvXYxbLLZPfdqg4Vjzrr_DrkaGY3kW7kMeaduF7sHE&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
640 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3924 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2680 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2680 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
2680 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2680 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2680 | msedge.exe | 2.23.227.199:443 | copilot.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
Process | Message |
|---|---|
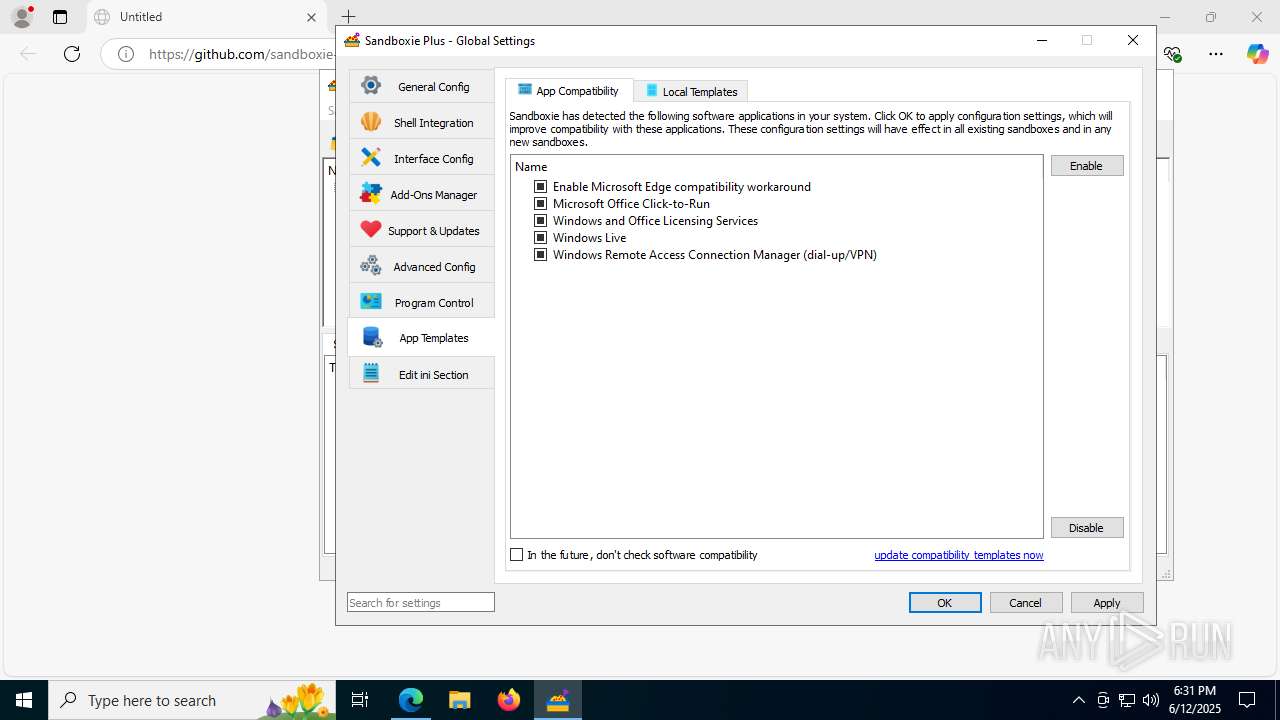
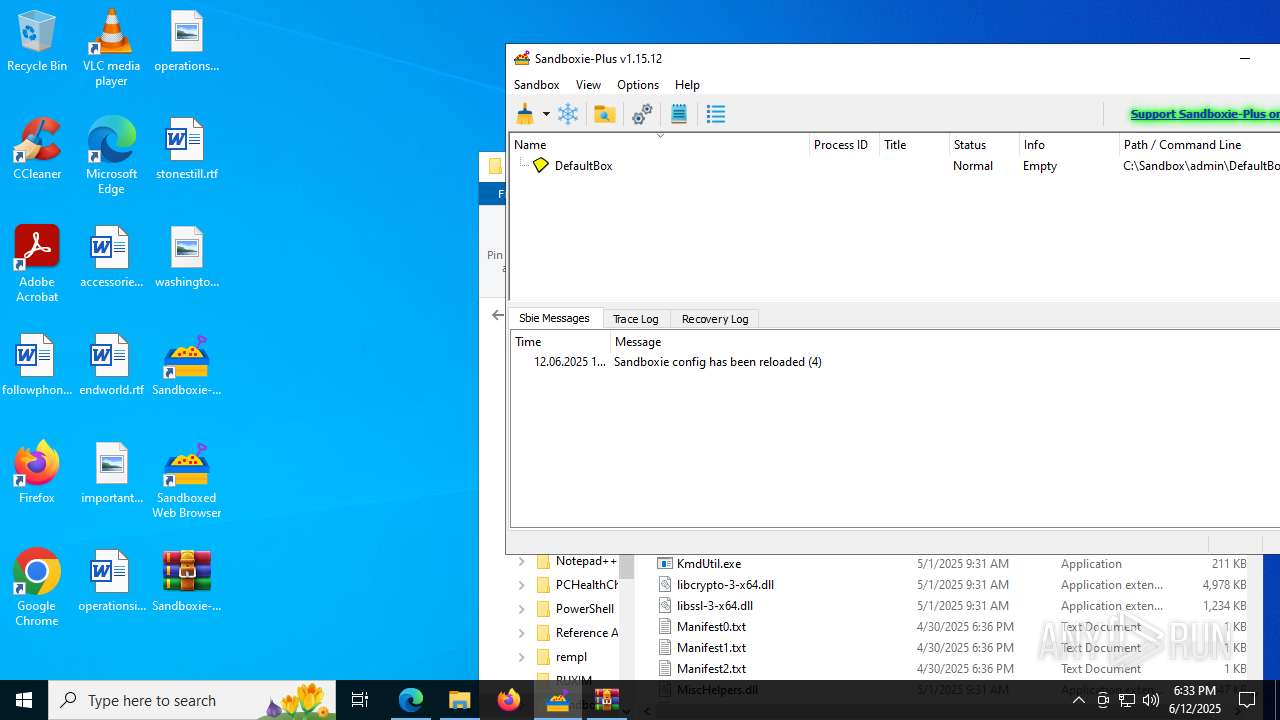
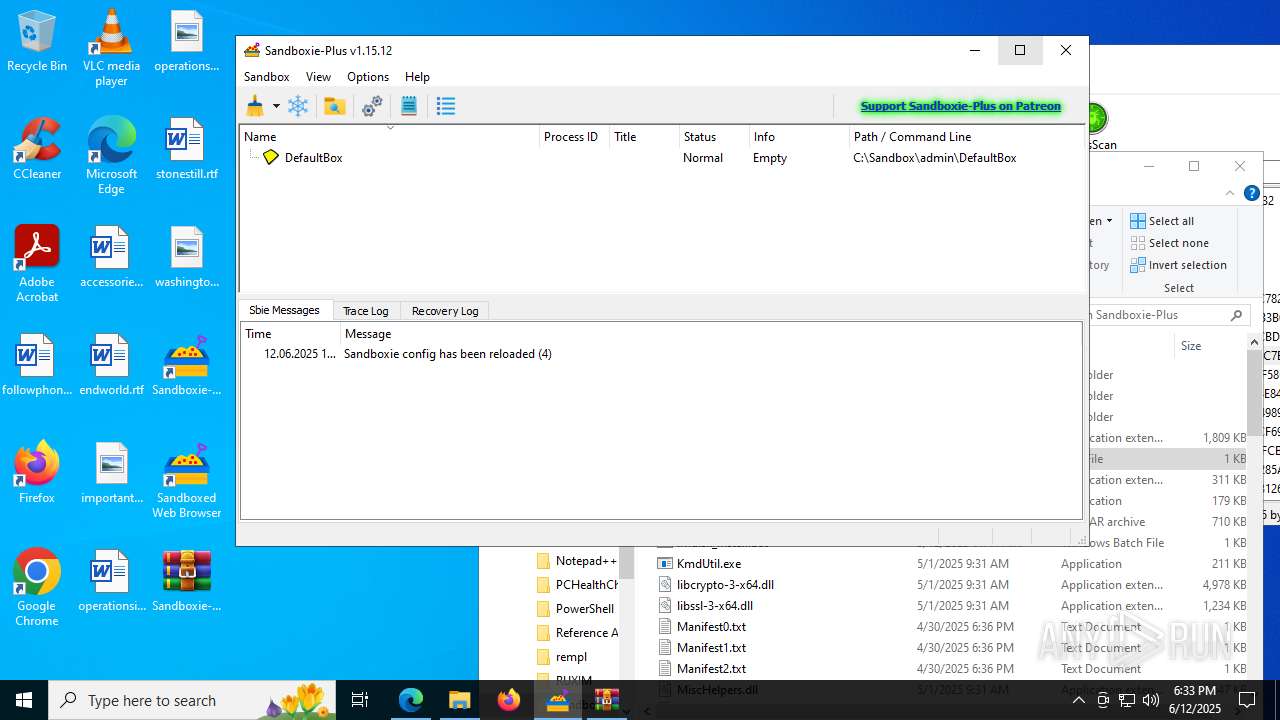
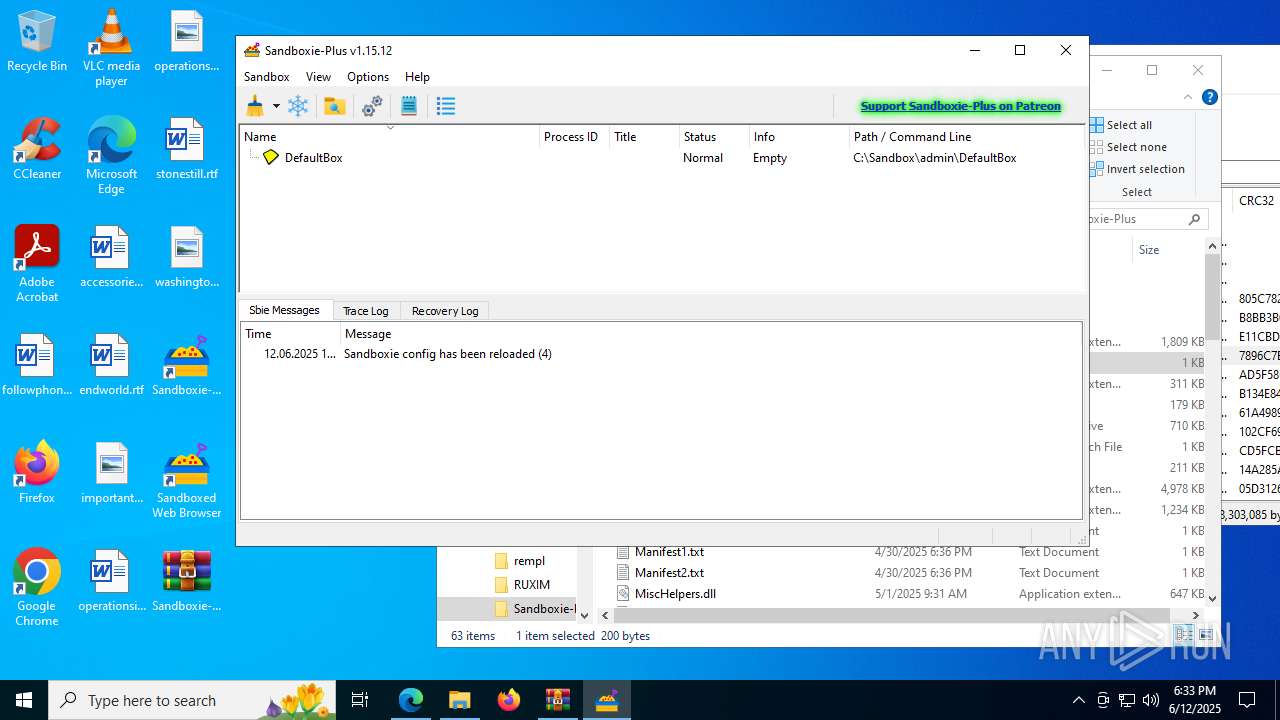
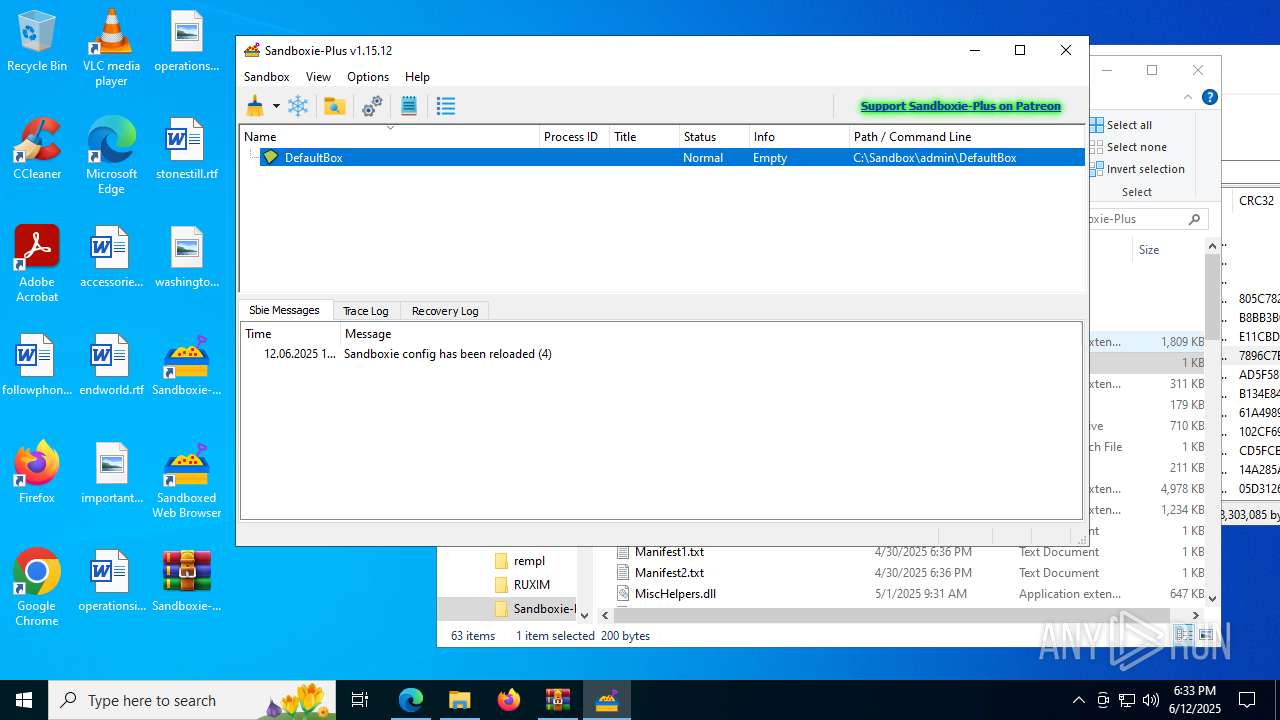
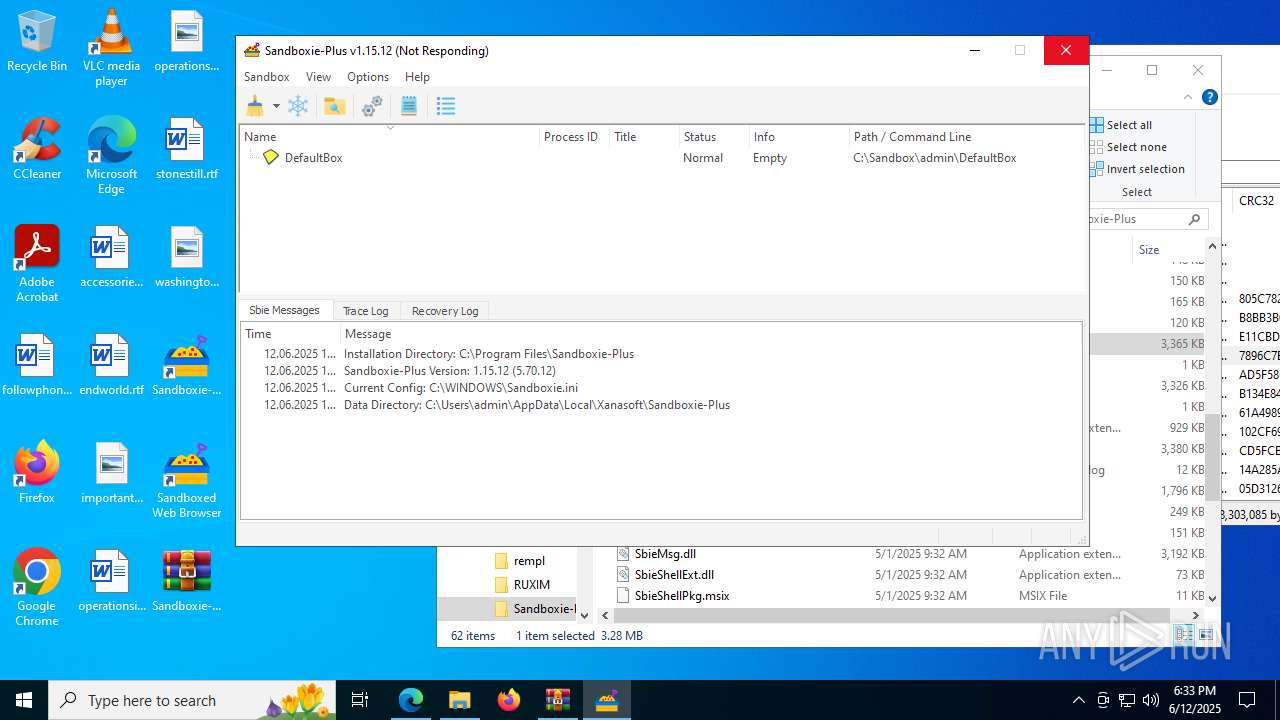
SandMan.exe | Clear took 2.8e-05 s
|
SandMan.exe | QObject::connect: No such slot CSandMan::OnDismissUpdate()
|
SandMan.exe | QFileSystemWatcher::removePath: path is empty
|
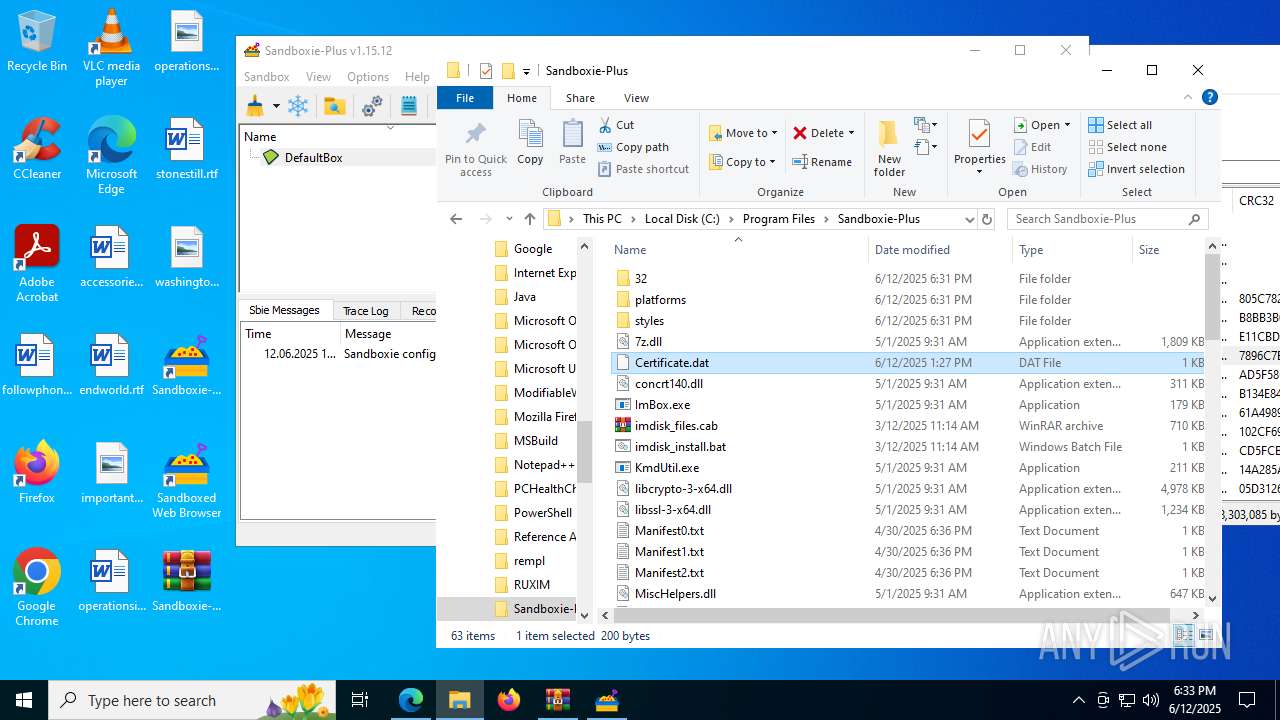
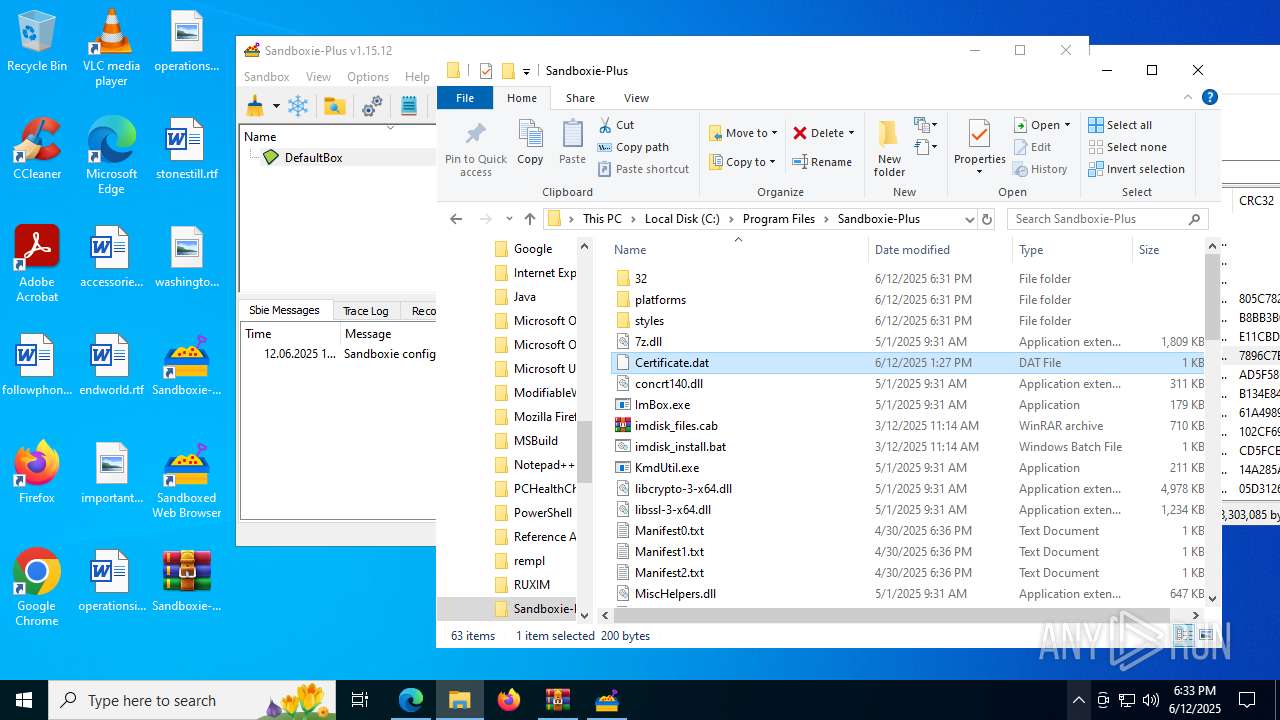
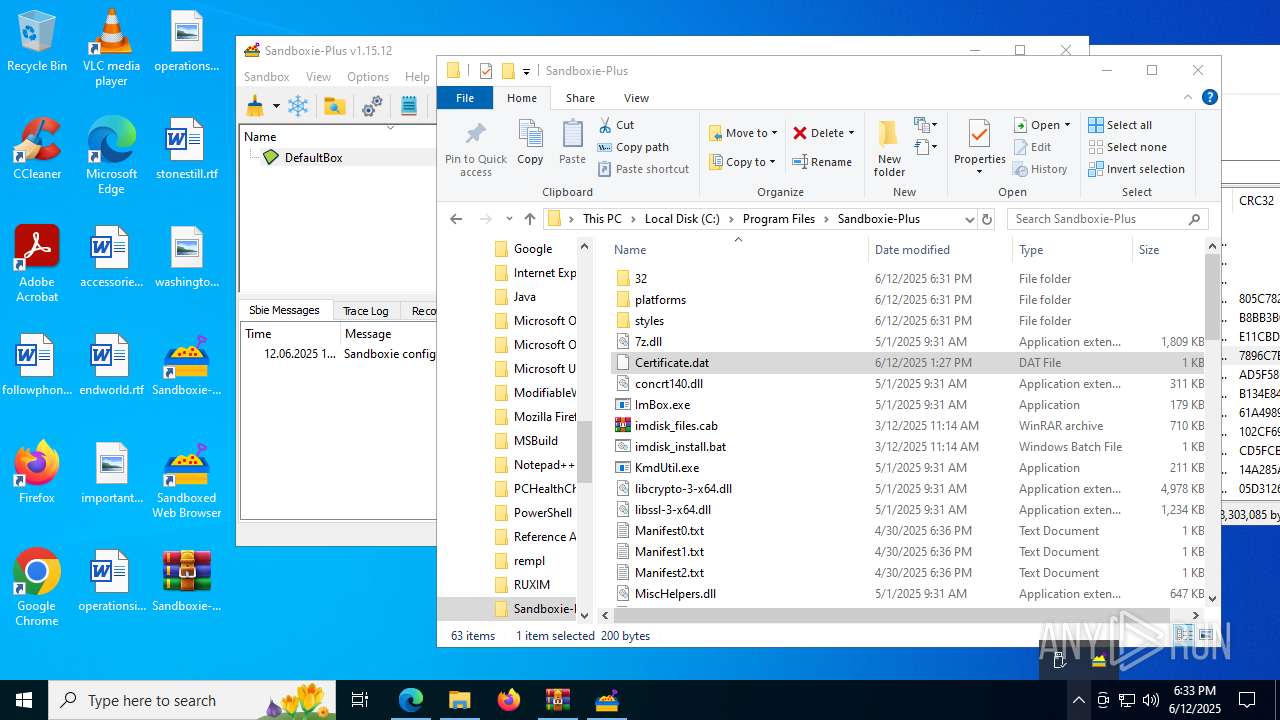
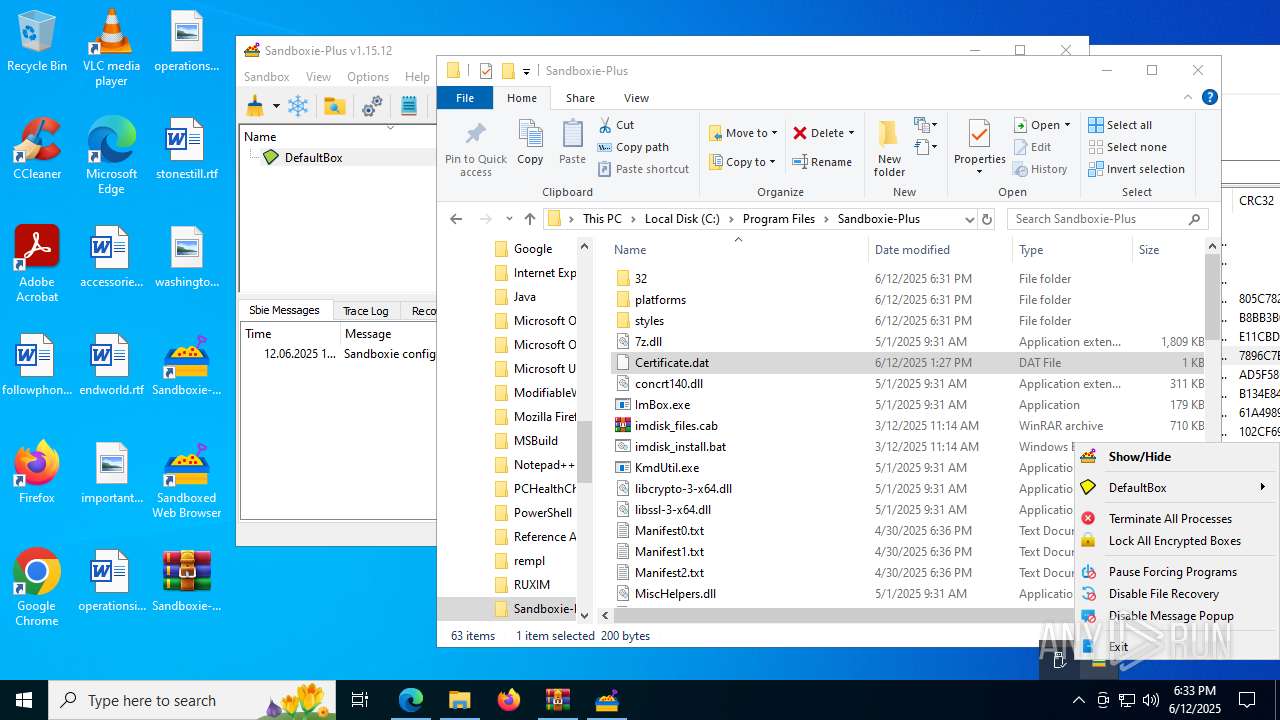
SandMan.exe | Config file: "C:\\WINDOWS\\Sandboxie.ini" (system)
|
SandMan.exe | QString::arg: Argument missing: Sandboxie config has been reloaded,
|
SandMan.exe | QString::arg: Argument missing: Sandboxie config has been reloaded,
|
SandMan.exe | QString::arg: Argument missing: Sandboxie config has been reloaded,
|
SandMan.exe | QString::arg: Argument missing: Sandboxie config has been reloaded,
|
SandMan.exe | QString::arg: Argument missing: Sandboxie config has been reloaded,
|
SandMan.exe | Clear took 1e-05 s
|