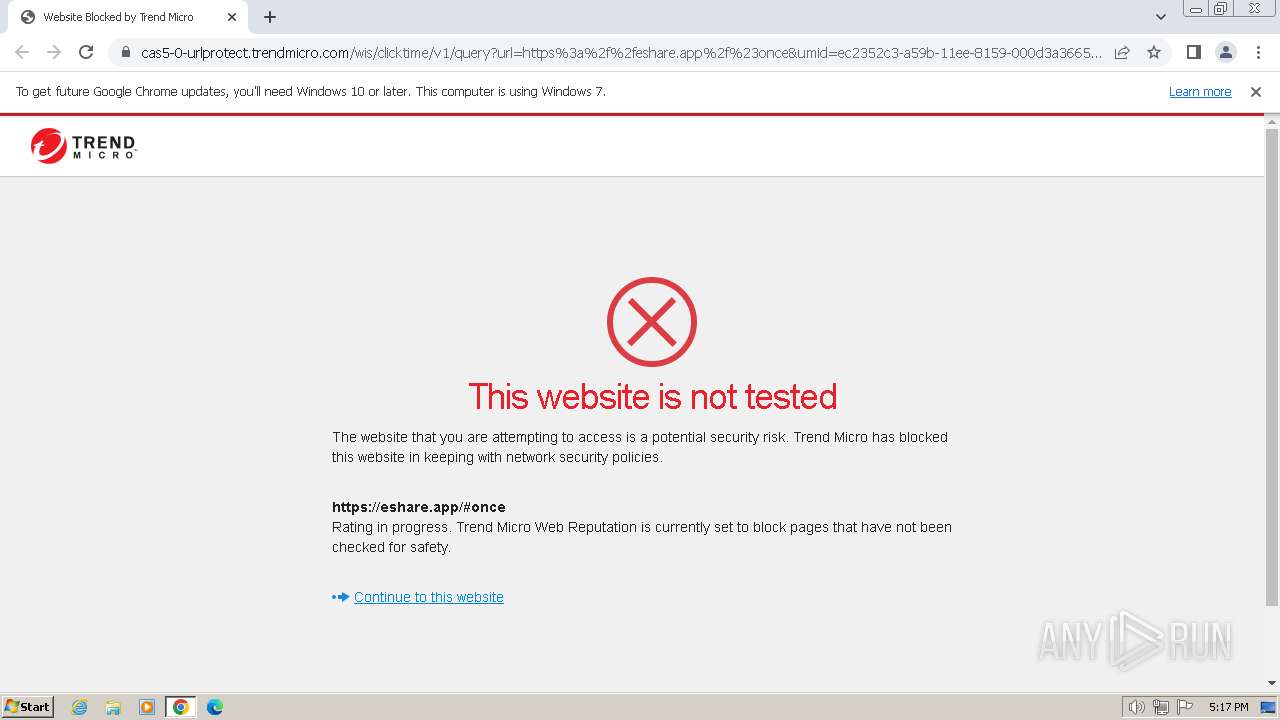
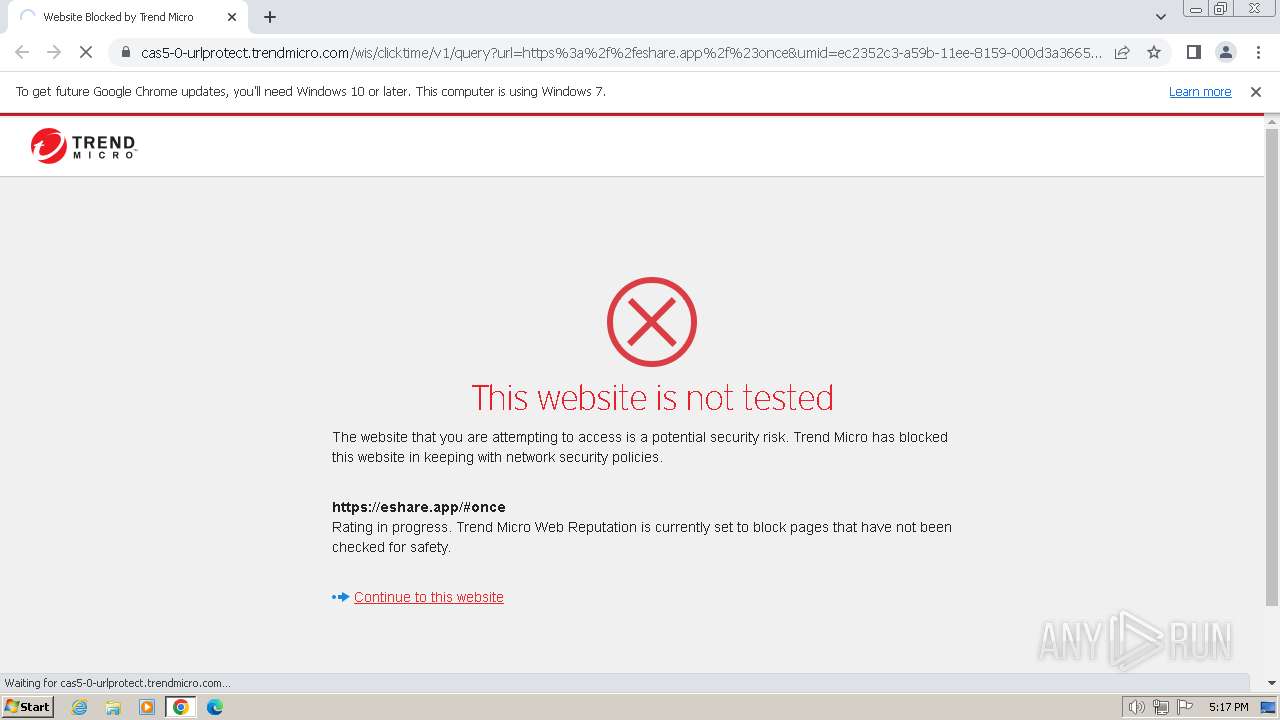
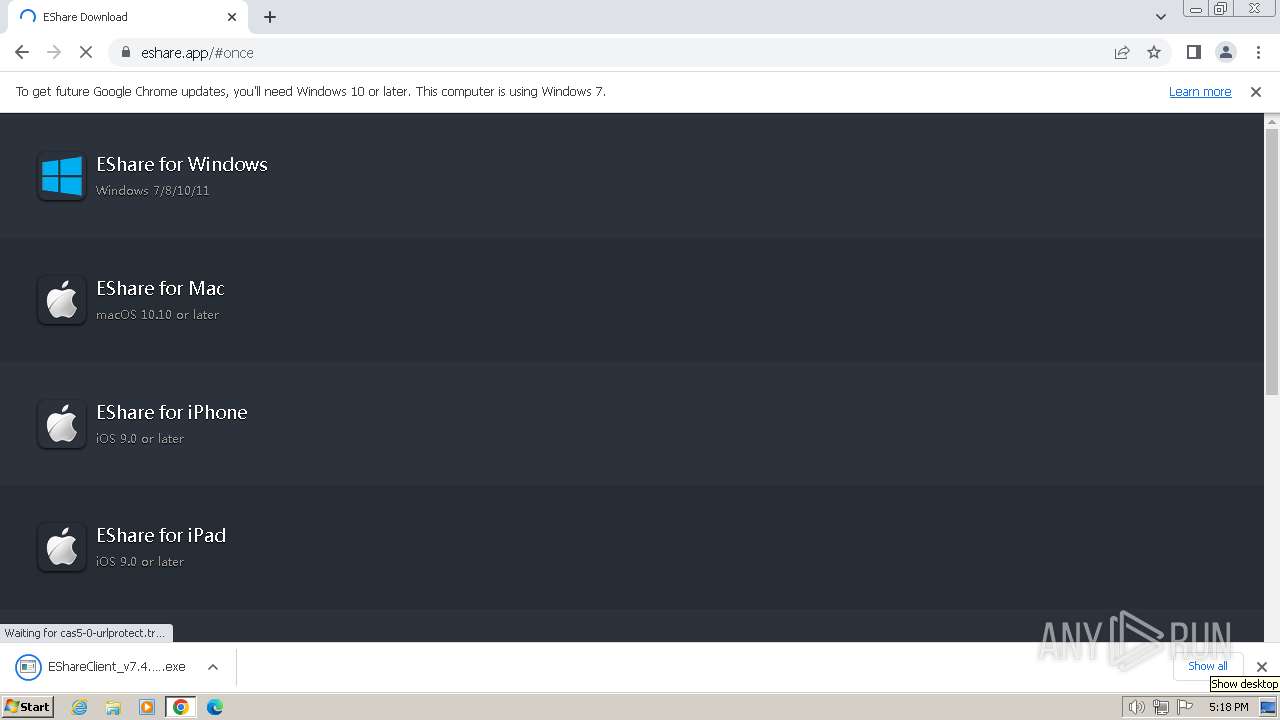
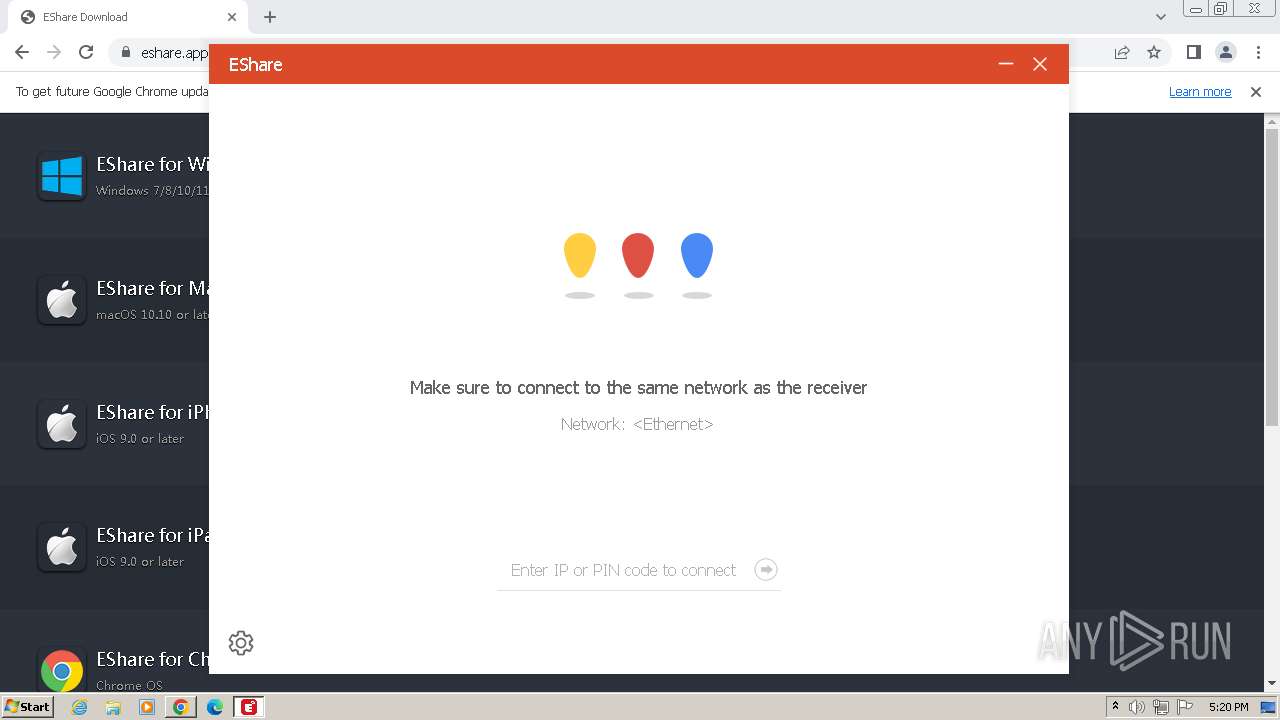
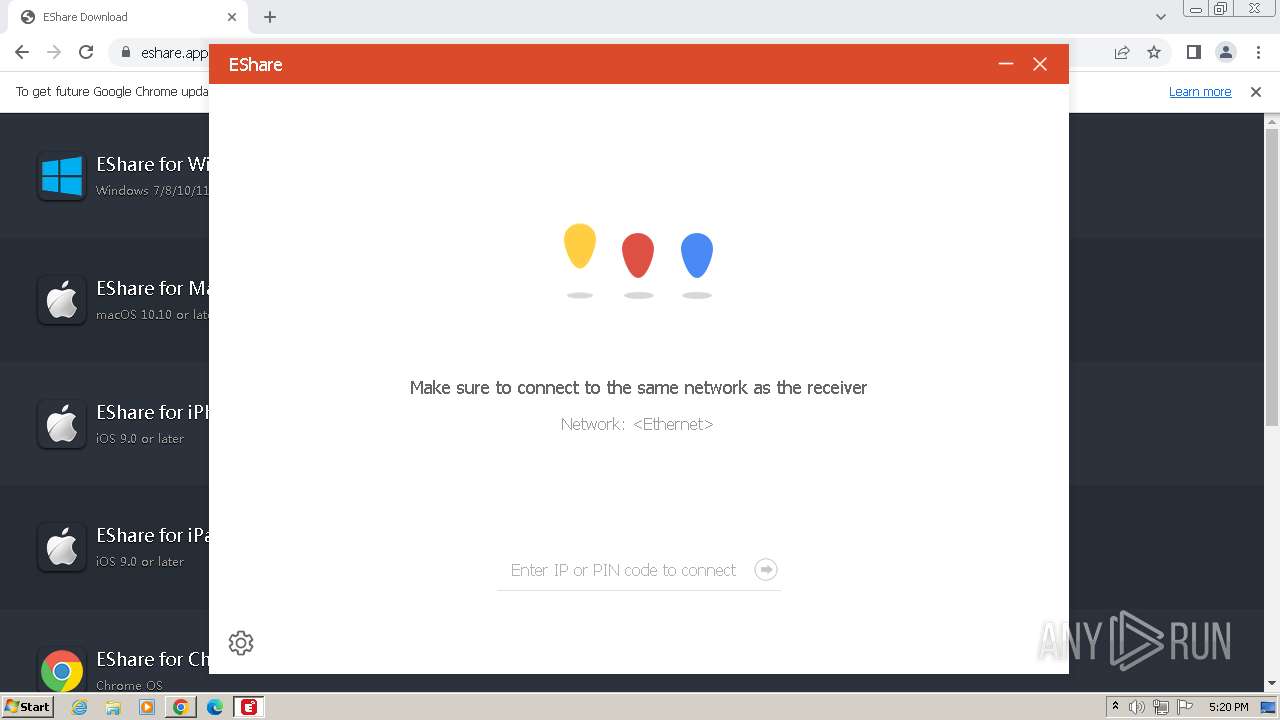
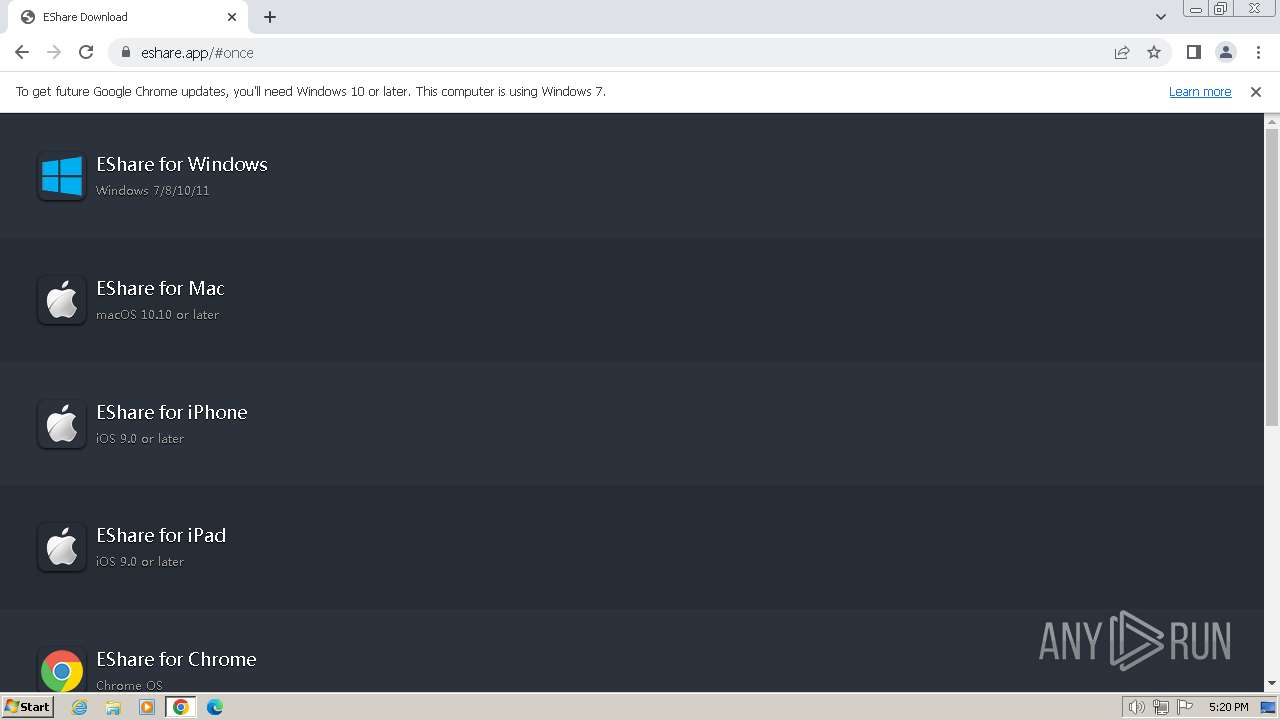
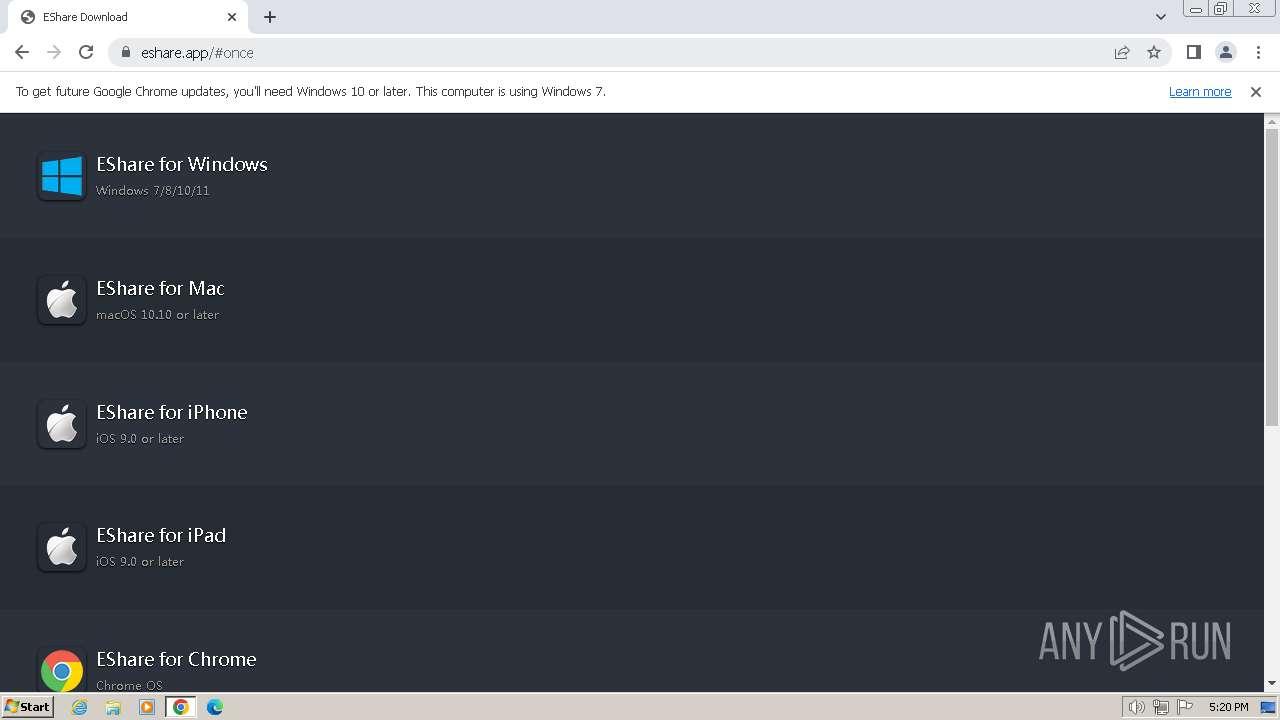
| URL: | https://cas5-0-urlprotect.trendmicro.com/wis/clicktime/v1/query?url=https%3a%2f%2feshare.app%2f%23once&umid=ec2352c3-a59b-11ee-8159-000d3a366586&auth=e9e5c1e4a5adcfd4da7a9063c2c1dfb6dcdb48c7-6d11f961cc300ad4683fff029a1e67a17de289c7 |
| Full analysis: | https://app.any.run/tasks/14408288-7f01-4607-b86e-a9e245fcb6d9 |
| Verdict: | Malicious activity |
| Analysis date: | December 28, 2023, 17:16:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4137F7CB279915DFA99B58ED719D660A |
| SHA1: | BD5CB374638B167BB4B87E97686386C5E7D23F39 |
| SHA256: | C8A91B39BDDBAD5F33D0C9BD39EE9A2FAE7FDECA897433AA86F67003D17224A4 |
| SSDEEP: | 6:2oER4fKMZsdnGMT+ryFvz+NOLo3VTR5NcFn:2oRPKGM7zhMTe |
MALICIOUS
No malicious indicators.SUSPICIOUS
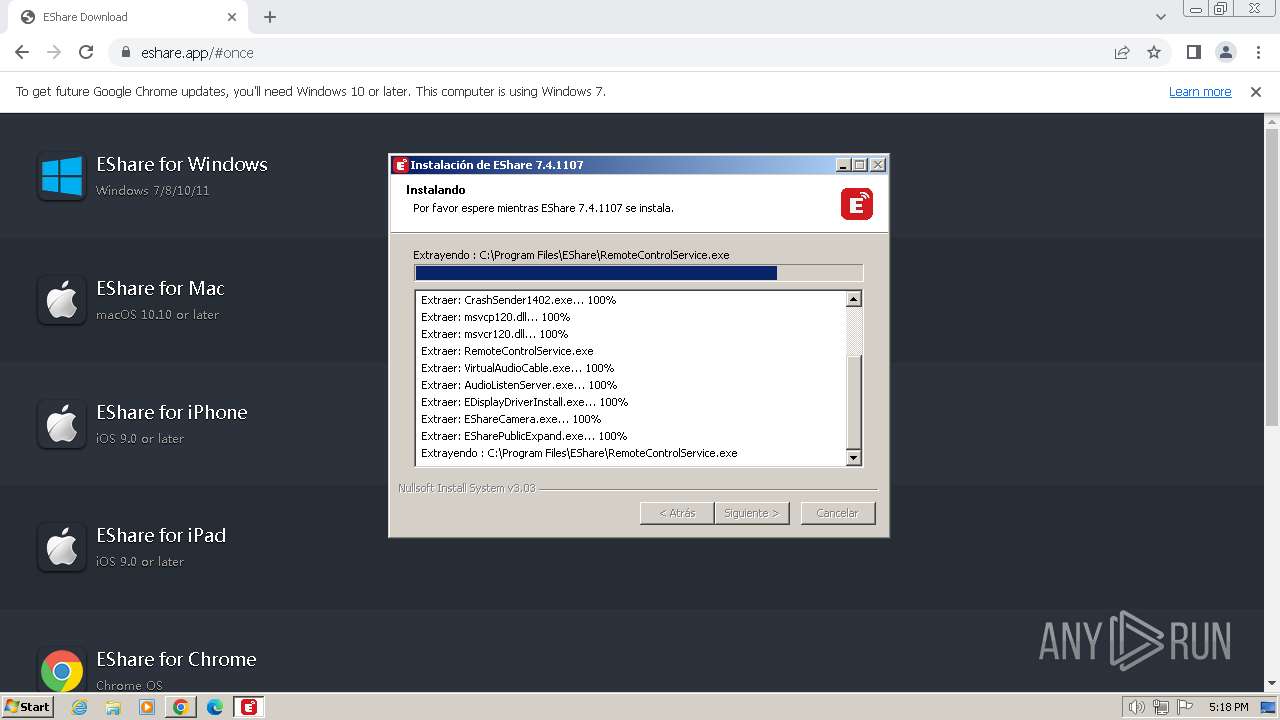
The process creates files with name similar to system file names
- EShareClient_v7.4.1107.exe (PID: 3312)
- EDisplayDriverInstall.exe (PID: 3656)
Starts application with an unusual extension
- EShareClient_v7.4.1107.exe (PID: 3312)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- ns8E10.tmp (PID: 3744)
Uses NETSH.EXE to add a firewall rule or allowed programs
- ns8F0B.tmp (PID: 1020)
Starts CMD.EXE for commands execution
- EShare.exe (PID: 3776)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4024)
- cmd.exe (PID: 632)
- cmd.exe (PID: 1016)
- cmd.exe (PID: 1388)
INFO
Application launched itself
- chrome.exe (PID: 2040)
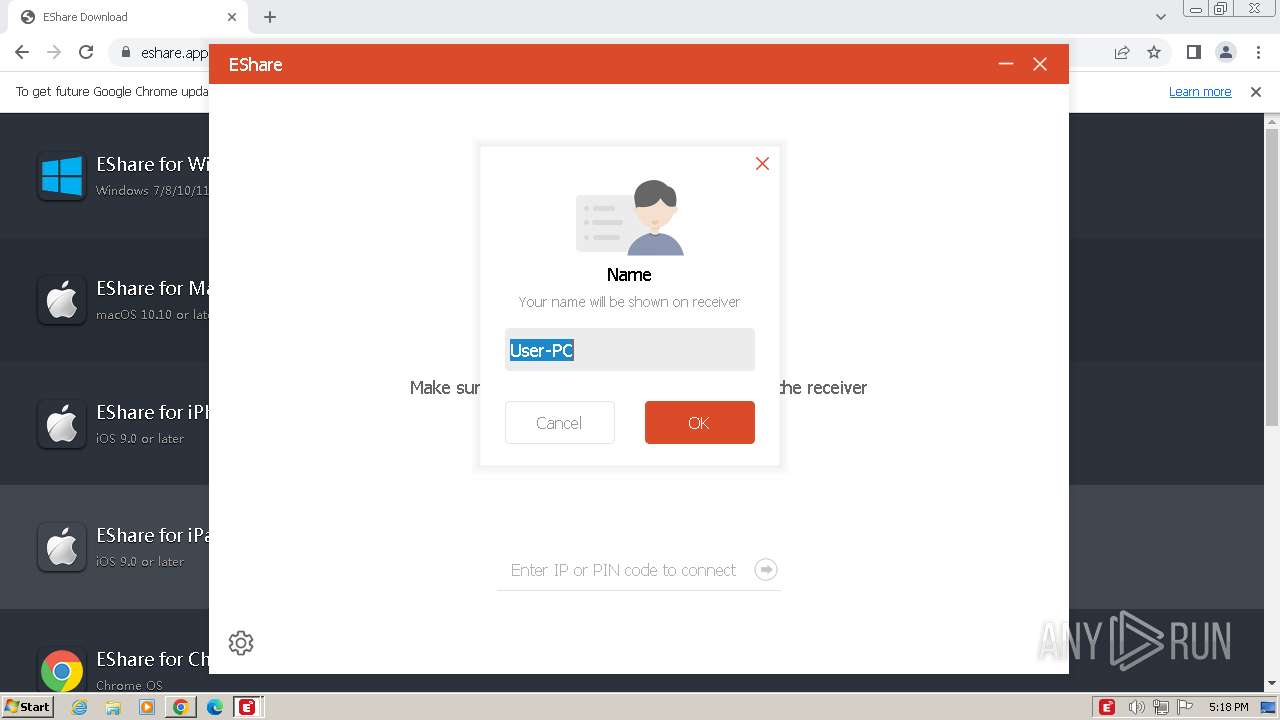
Reads the computer name
- EShareClient_v7.4.1107.exe (PID: 3312)
- msiexec.exe (PID: 3428)
- RemoteControlService.exe (PID: 3536)
- ESystemRemoteService.exe (PID: 3528)
- EDisplayDriverInstall.exe (PID: 3656)
- EShare.exe (PID: 3776)
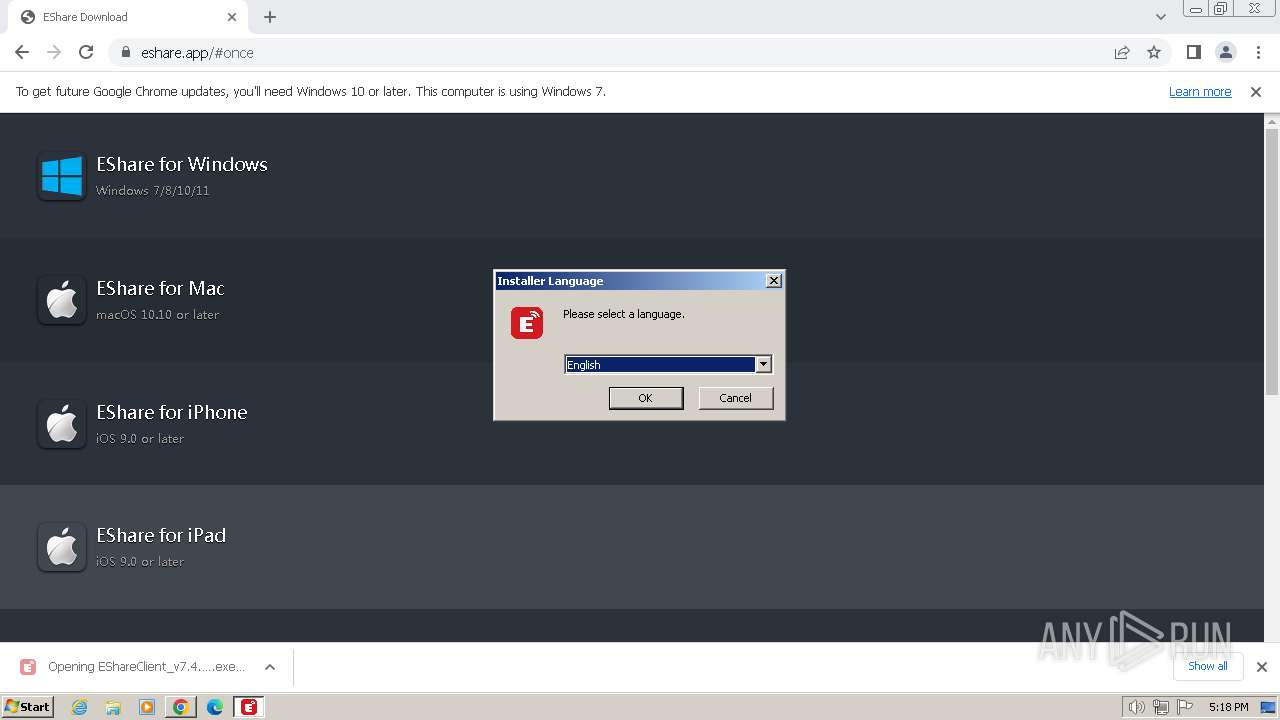
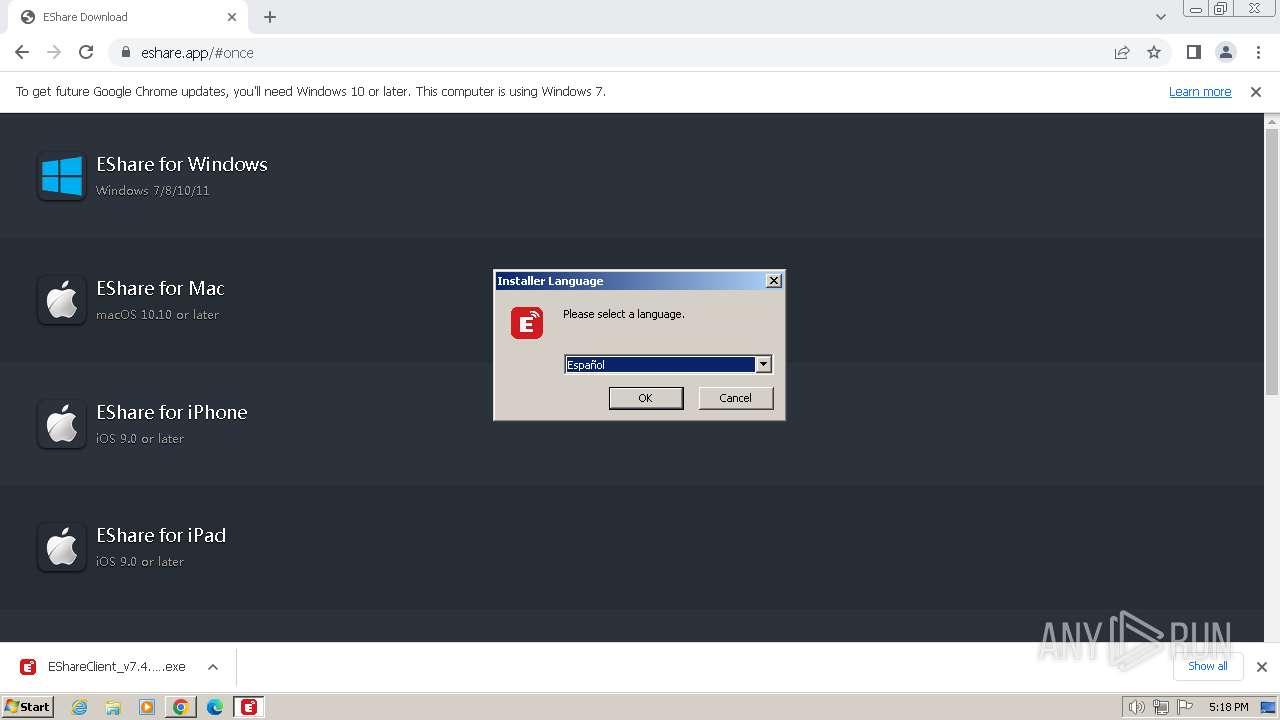
Checks supported languages
- EShareClient_v7.4.1107.exe (PID: 3312)
- msiexec.exe (PID: 3428)
- RemoteControlService.exe (PID: 3536)
- ESystemRemoteService.exe (PID: 3528)
- EDesktop.exe (PID: 3652)
- EDesktopUAC.exe (PID: 3680)
- EDisplayDriverInstall.exe (PID: 3656)
- EShare.exe (PID: 3776)
- ns8E10.tmp (PID: 3744)
- ns8F0B.tmp (PID: 1020)
Drops the executable file immediately after the start
- chrome.exe (PID: 2040)
- EShareClient_v7.4.1107.exe (PID: 3312)
- RemoteControlService.exe (PID: 3536)
- EDisplayDriverInstall.exe (PID: 3656)
- chrome.exe (PID: 2304)
The process uses the downloaded file
- chrome.exe (PID: 2968)
- chrome.exe (PID: 2040)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3428)
- EShare.exe (PID: 3776)
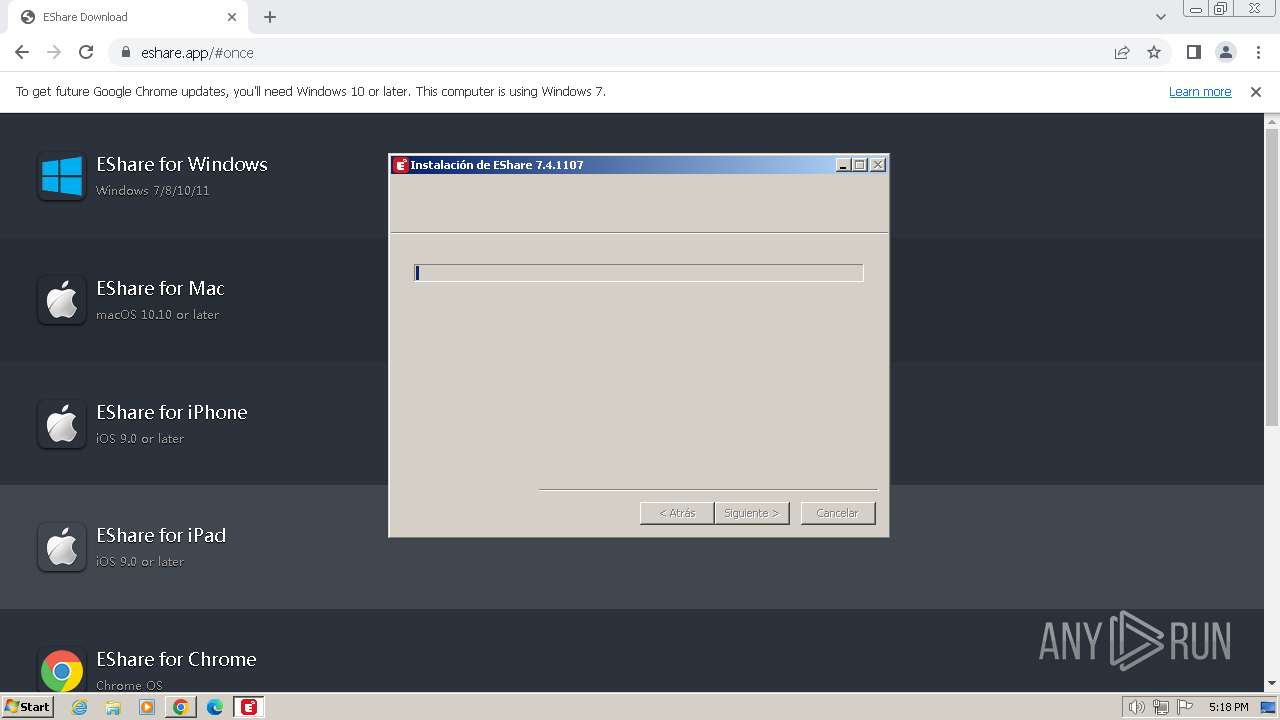
Create files in a temporary directory
- EShareClient_v7.4.1107.exe (PID: 3312)
- RemoteControlService.exe (PID: 3536)
- EDisplayDriverInstall.exe (PID: 3656)
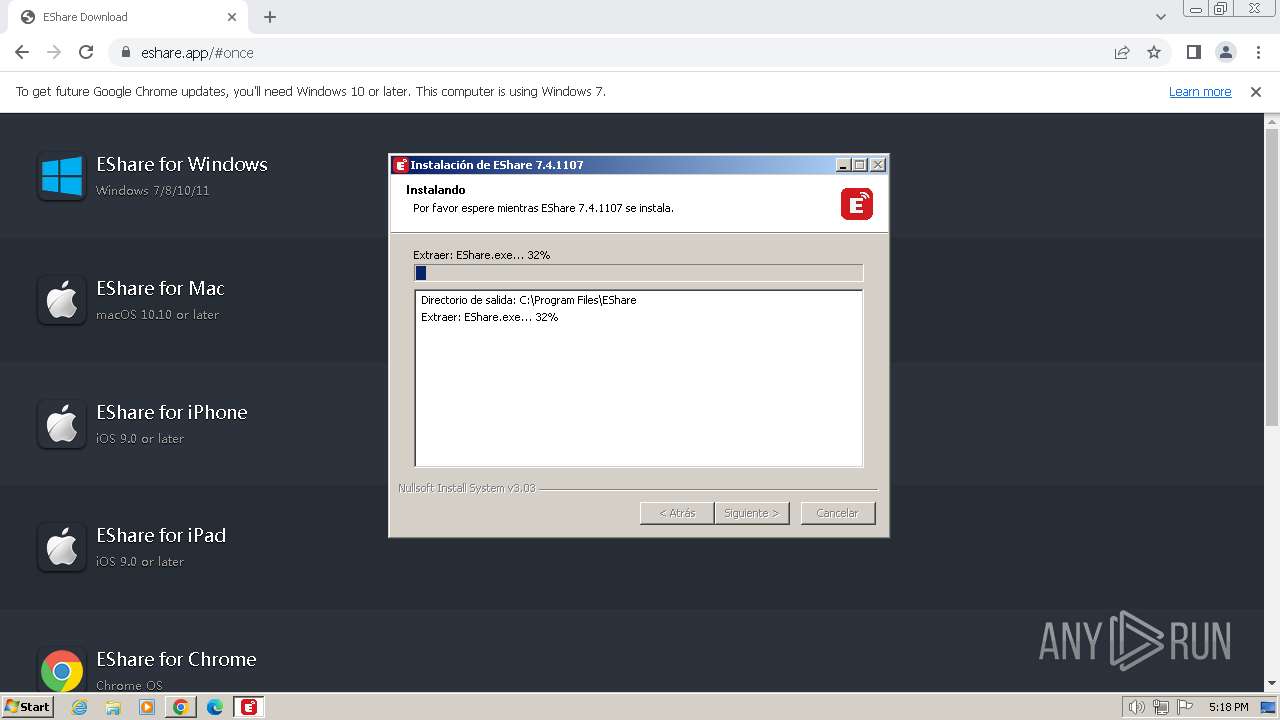
Creates files in the program directory
- EShareClient_v7.4.1107.exe (PID: 3312)
- EDisplayDriverInstall.exe (PID: 3656)
- RemoteControlService.exe (PID: 3536)
The process drops C-runtime libraries
- EShareClient_v7.4.1107.exe (PID: 3312)
Process drops legitimate windows executable
- EShareClient_v7.4.1107.exe (PID: 3312)
- EDisplayDriverInstall.exe (PID: 3656)
Malware-specific behavior (creating "System.dll" in Temp)
- EShareClient_v7.4.1107.exe (PID: 3312)
- EDisplayDriverInstall.exe (PID: 3656)
Executes as Windows Service
- ESystemRemoteService.exe (PID: 3528)
Creates files or folders in the user directory
- EShare.exe (PID: 3776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
92
Monitored processes
47
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | netstat -aon | C:\Windows\System32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1096 --field-trial-handle=812,i,1013283864133590013,9274797999949499544,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 492 | findstr 51030 | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1348 --field-trial-handle=812,i,1013283864133590013,9274797999949499544,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 560 | findstr 51030 | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 632 | cmd /c "netstat -aon|findstr 51030" | C:\Windows\System32\cmd.exe | — | EShare.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3372 --field-trial-handle=812,i,1013283864133590013,9274797999949499544,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1016 | cmd /c "netstat -aon|findstr 51040" | C:\Windows\System32\cmd.exe | — | EShare.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\AppData\Local\Temp\nsc58F5.tmp\ns8F0B.tmp" netsh advfirewall firewall add rule name="EShare" profile=private,public,domain dir=in program="C:\Program Files\EShare\EShare.exe" action=allow | C:\Users\admin\AppData\Local\Temp\nsc58F5.tmp\ns8F0B.tmp | — | EShareClient_v7.4.1107.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1512 --field-trial-handle=812,i,1013283864133590013,9274797999949499544,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
10 246
Read events
10 055
Write events
190
Delete events
1
Modification events
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
34
Suspicious files
184
Text files
37
Unknown types
114
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFdf9e1.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFdf9e1.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4f4c9f7f-4958-467f-af84-6d96209acf61.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe0098.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RFe1038.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
32
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 89.6 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 179 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 10.4 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 360 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 164 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 630 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 498 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 79.4 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 862 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 957 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
532 | chrome.exe | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | unknown |
2040 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
532 | chrome.exe | 54.148.144.239:443 | cas5-0-urlprotect.trendmicro.com | AMAZON-02 | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2040 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
532 | chrome.exe | 142.250.186.164:443 | www.google.com | GOOGLE | US | whitelisted |
532 | chrome.exe | 142.250.185.74:443 | www.googleapis.com | GOOGLE | US | whitelisted |
532 | chrome.exe | 35.163.39.16:443 | cas5-0-urlprotect.trendmicro.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
cas5-0-urlprotect.trendmicro.com |
| unknown |
www.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
ctp.trendmicro.com |
| unknown |
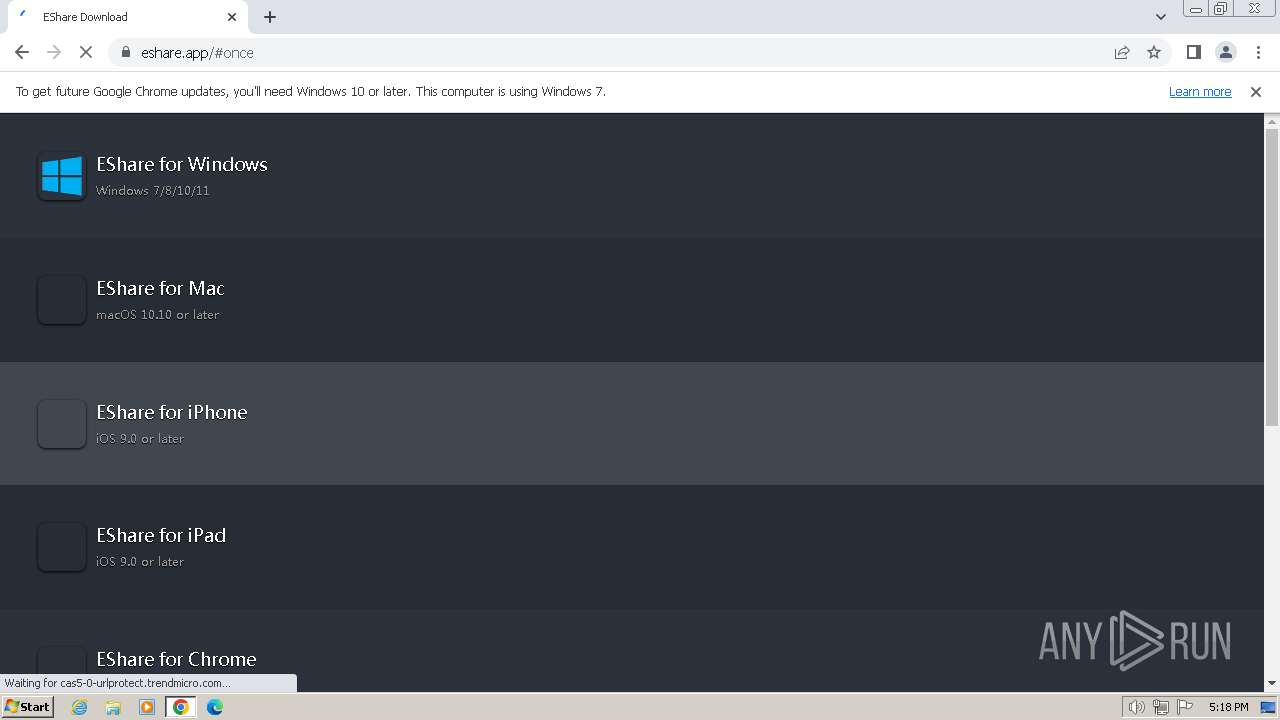
eshare.app |
| malicious |
update.googleapis.com |
| whitelisted |
cdn.sharemax.cn |
| unknown |
edgedl.me.gvt1.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
EShare.exe | registerRenderers...........
|
EShare.exe | |
EShare.exe | |
EShare.exe | |
EShare.exe | DEBUG 2023-12-28 17:18:48.292 a.isSecondary false |
EShare.exe | INFO 2023-12-28 17:18:48.292 ************************************************************************ |
EShare.exe | |
EShare.exe | DEBUG 2023-12-28 17:18:48.292 a.isPrimary true |
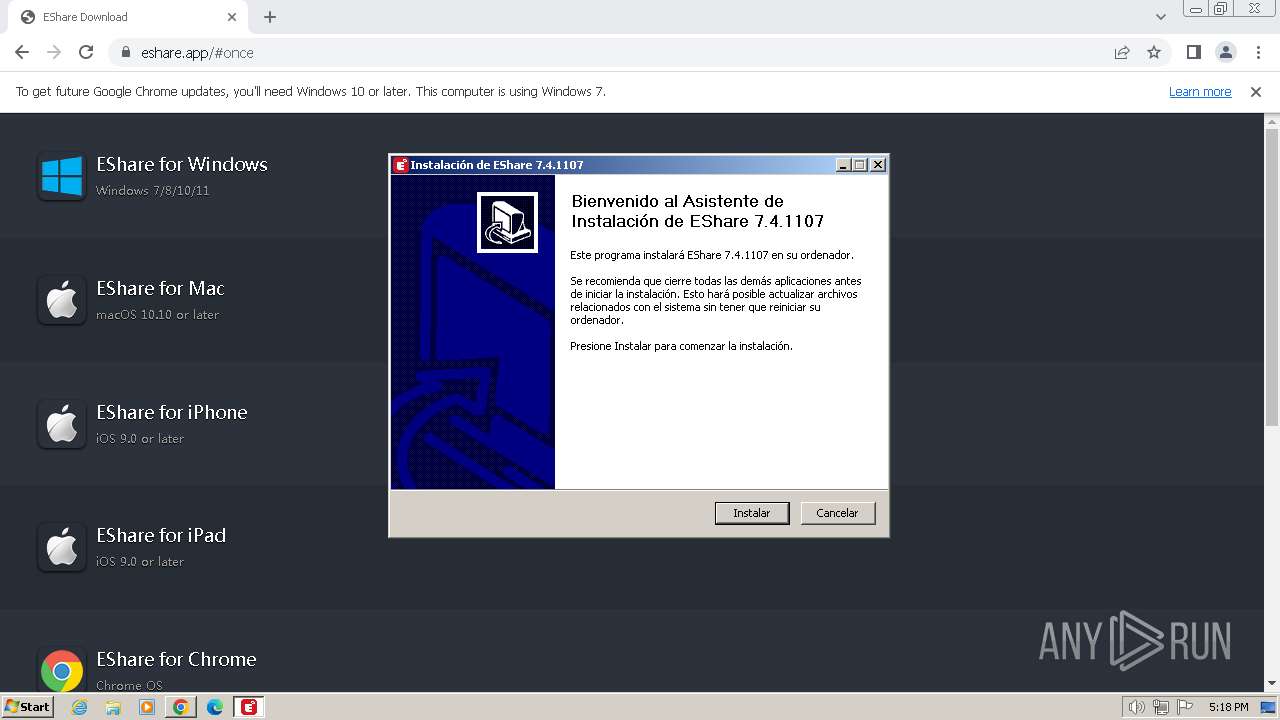
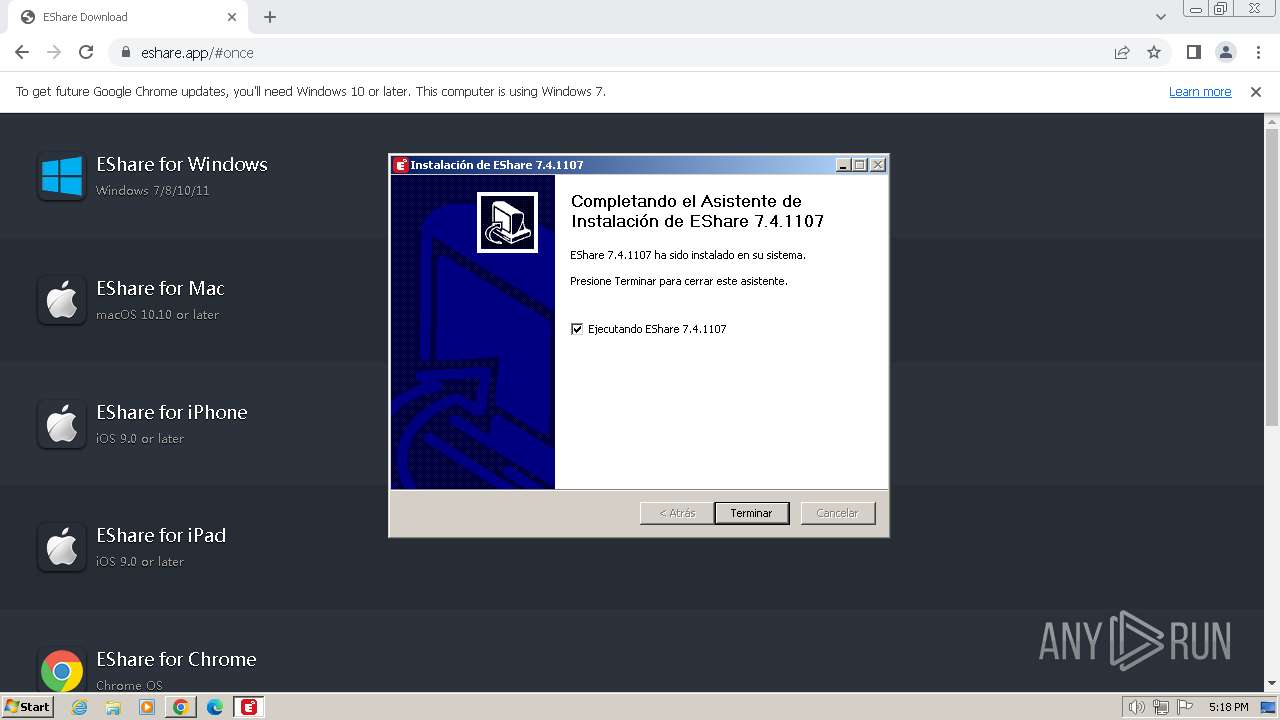
EShare.exe | INFO 2023-12-28 17:18:48.292 EShare Client Start by EXE |
EShare.exe | INFO 2023-12-28 17:18:48.292 EShare Client Start ver:: 7.4.1107 |