| File name: | WD_PROXKey_new.exe |
| Full analysis: | https://app.any.run/tasks/eadf06f1-860a-4e27-aba6-06025790e56b |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2025, 09:31:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 59456002F251902F38DFD220AB3BCB53 |
| SHA1: | A05A6DA4961566D818F17BED4A76A5CF54C918FD |
| SHA256: | C8A2B3CE6C8D0D0E5F717CA7E1446B12E12B3C3F1624A1AE82136C55F9540730 |
| SSDEEP: | 98304:WxZgEM2TlmOKPEL2TiuSkjT/QvYe2zZwlxN+lCUSxhS9pCsJv7UB10CVEFz88pP:9/ |
MALICIOUS
Changes the autorun value in the registry
- WD_PROXKey_new.exe (PID: 5064)
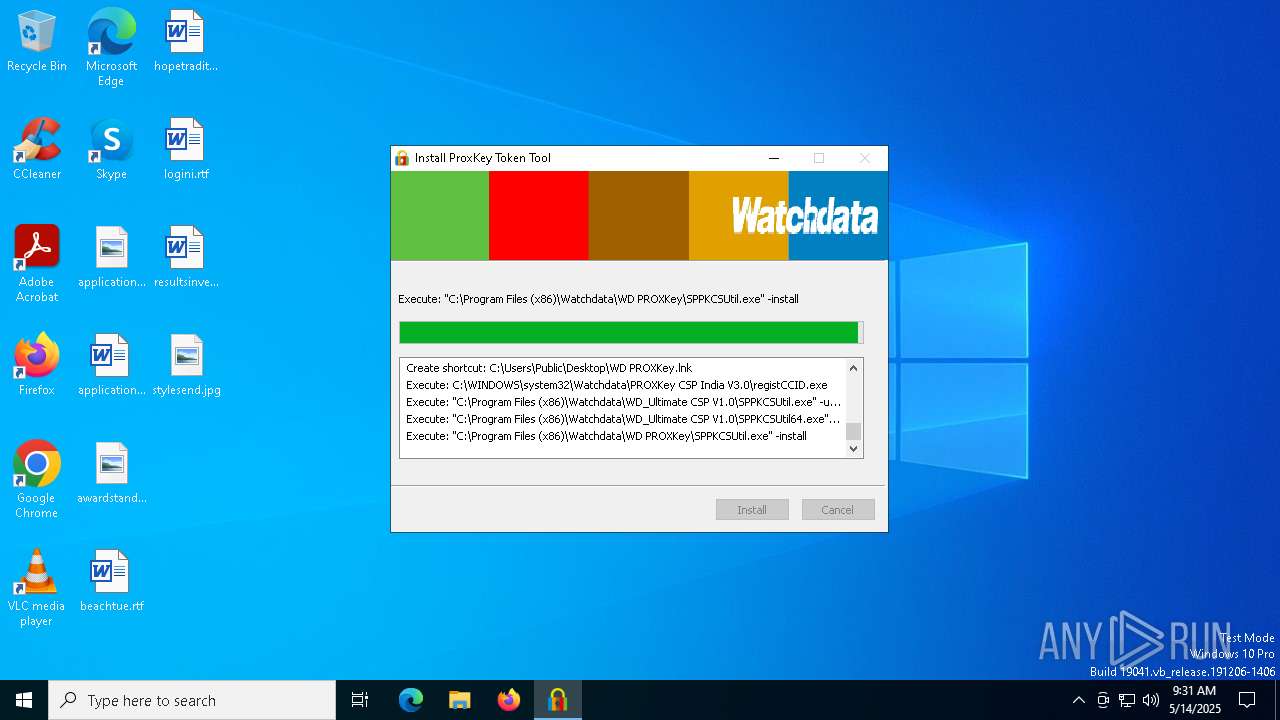
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 6048)
- cmd.exe (PID: 728)
Executing a file with an untrusted certificate
- WDKSPconfig.exe (PID: 5728)
SUSPICIOUS
The process creates files with name similar to system file names
- WD_PROXKey_new.exe (PID: 5064)
Malware-specific behavior (creating "System.dll" in Temp)
- WD_PROXKey_new.exe (PID: 5064)
Process drops legitimate windows executable
- WD_PROXKey_new.exe (PID: 5064)
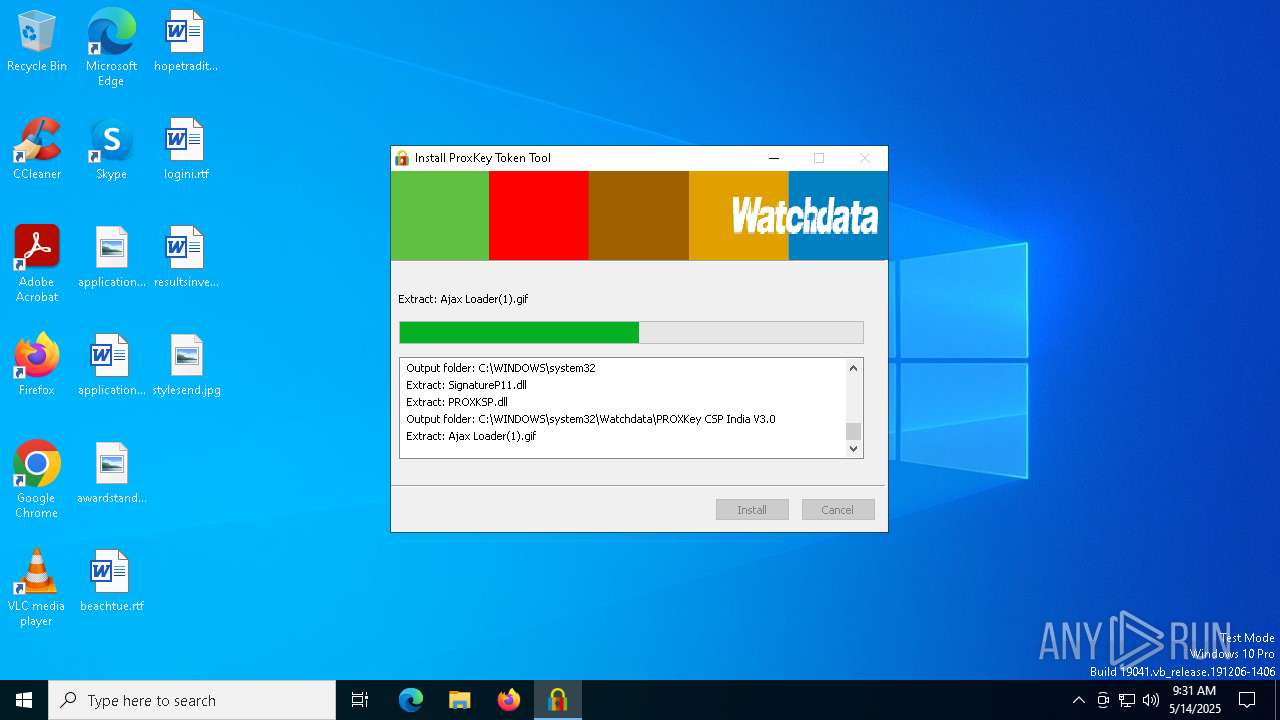
Executable content was dropped or overwritten
- WD_PROXKey_new.exe (PID: 5064)
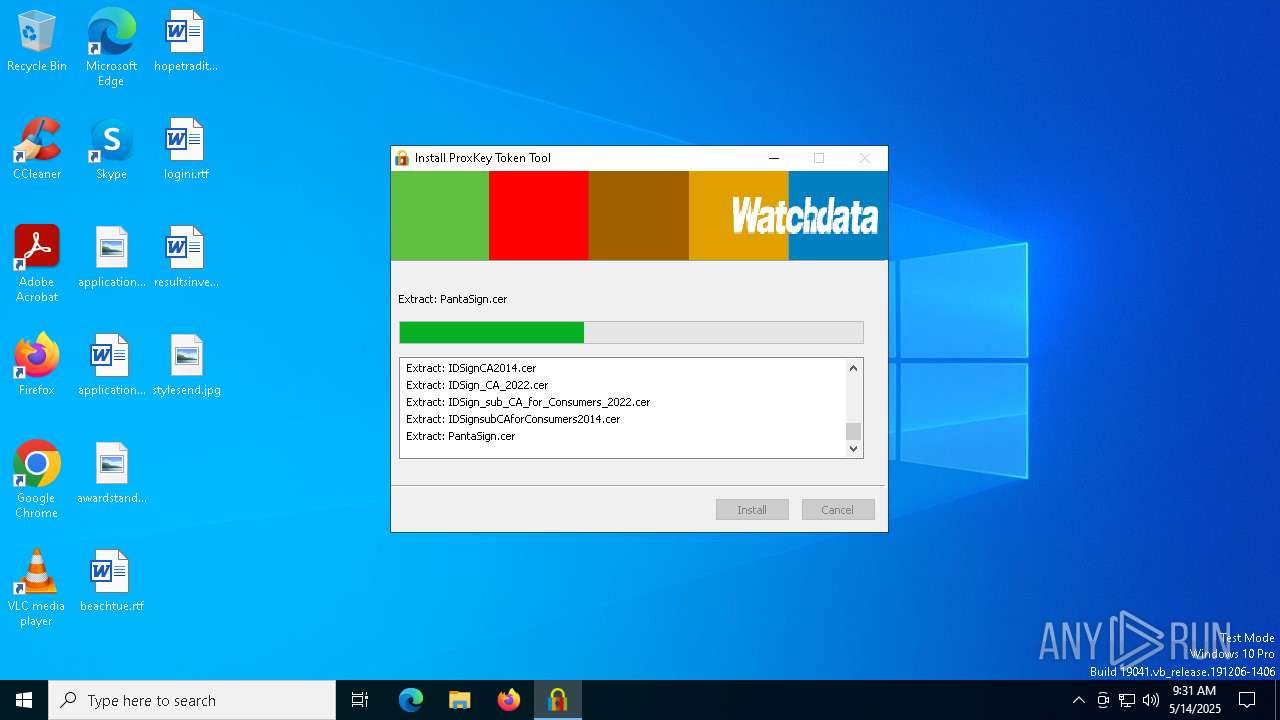
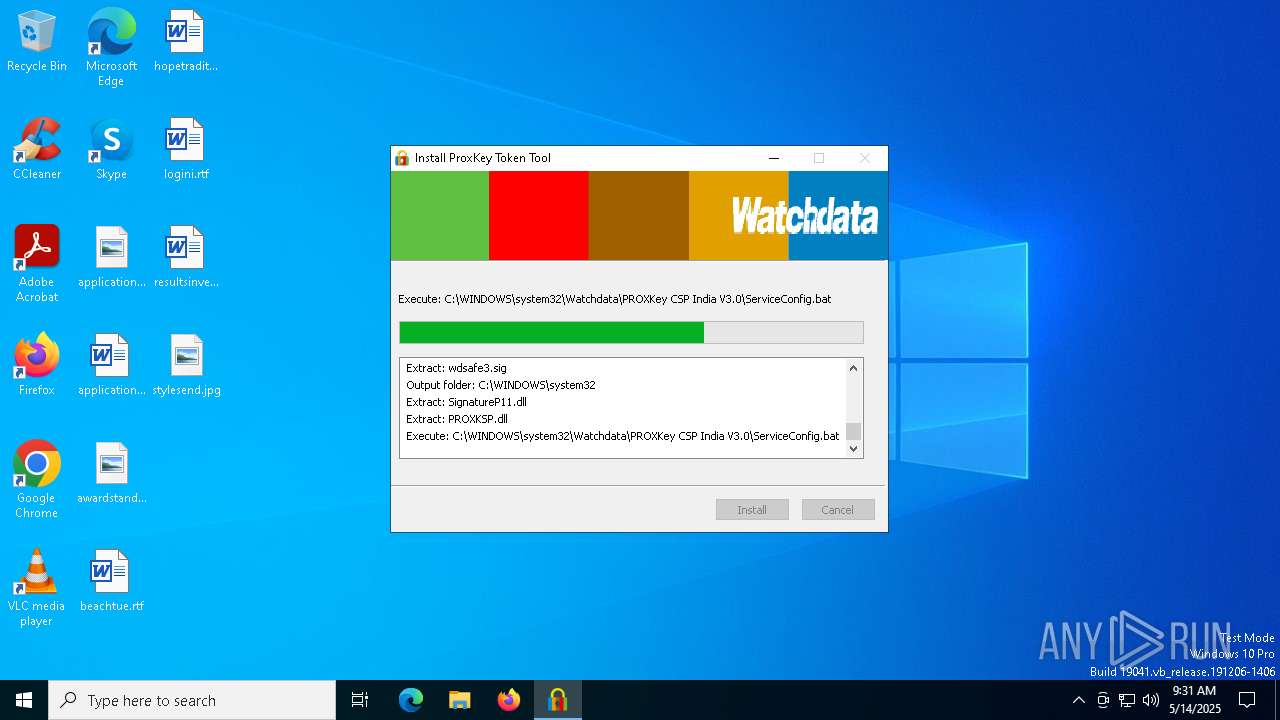
Executing commands from a ".bat" file
- WD_PROXKey_new.exe (PID: 5064)
Drops a system driver (possible attempt to evade defenses)
- WD_PROXKey_new.exe (PID: 5064)
Executes as Windows Service
- SPMonitor.exe (PID: 5668)
Starts CMD.EXE for commands execution
- WD_PROXKey_new.exe (PID: 5064)
Restarts service on failure
- sc.exe (PID: 7084)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 5008)
- regsvr32.exe (PID: 1228)
Adds/modifies Windows certificates
- SPPKCSUtil.exe (PID: 5800)
Reads security settings of Internet Explorer
- WD_PROXKey_new.exe (PID: 5064)
Reads Mozilla Firefox installation path
- SPPKCSUtil64.exe (PID: 6540)
- SPPKCSUtil64.exe (PID: 4172)
Loads DLL from Mozilla Firefox
- SPPKCSUtil64.exe (PID: 6540)
- SPPKCSUtil64.exe (PID: 4172)
There is functionality for taking screenshot (YARA)
- SPMonitor.exe (PID: 5668)
Creates a software uninstall entry
- WD_PROXKey_new.exe (PID: 5064)
INFO
Checks supported languages
- WD_PROXKey_new.exe (PID: 5064)
- SPPKCSUtil.exe (PID: 5800)
- registCCID.exe (PID: 1188)
- SPPKCSUtil64.exe (PID: 6540)
- SPMonitor.exe (PID: 5668)
- WDKSPconfig.exe (PID: 5728)
- WDAdmintool.exe (PID: 6576)
- SPPKCSUtil.exe (PID: 5728)
- SP_CertMND.exe (PID: 5216)
- SPSocketServer.exe (PID: 208)
- SPPKCSUtil64.exe (PID: 4172)
The sample compiled with english language support
- WD_PROXKey_new.exe (PID: 5064)
Creates files in the program directory
- WD_PROXKey_new.exe (PID: 5064)
Reads the computer name
- WD_PROXKey_new.exe (PID: 5064)
- SPMonitor.exe (PID: 5668)
- SPPKCSUtil64.exe (PID: 6540)
- SPPKCSUtil64.exe (PID: 4172)
- SP_CertMND.exe (PID: 5216)
- WDAdmintool.exe (PID: 6576)
Create files in a temporary directory
- WD_PROXKey_new.exe (PID: 5064)
- WDAdmintool.exe (PID: 6576)
Creates files or folders in the user directory
- SPPKCSUtil64.exe (PID: 6540)
- SPPKCSUtil64.exe (PID: 4172)
Process checks computer location settings
- WD_PROXKey_new.exe (PID: 5064)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5544)
- explorer.exe (PID: 2984)
Manual execution by a user
- WDAdmintool.exe (PID: 6576)
Reads the machine GUID from the registry
- WDAdmintool.exe (PID: 6576)
Reads the software policy settings
- slui.exe (PID: 5968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:10 12:19:31+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 25600 |
| InitializedDataSize: | 431104 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x354b |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.3.0 |
| ProductVersionNumber: | 6.0.3.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | ProxKey |
| CompanyName: | Watchdata Technologies Pte. Ltd. |
| FileDescription: | ProxKey |
| FileVersion: | 6.0.3.0 |
| LegalCopyright: | Copyright (c) 2007 Watchdata Technologies Pte. Ltd. All rights reserved. |
| ProductName: | ProxKey |
| ProductVersion: | 6.0.3.0 |
Total processes
160
Monitored processes
29
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Windows\SysWOW64\Watchdata\PROXKey CSP India V3.0\SPSocketServer.exe" | C:\Windows\SysWOW64\Watchdata\PROXKey CSP India V3.0\SPSocketServer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 728 | C:\WINDOWS\syswow64\cmd.exe /C regsvr32 /s "C:\WINDOWS\syswow64\Watchdata\PROXKey CSP India V3.0\WDCtr.dll" | C:\Windows\SysWOW64\cmd.exe | — | WD_PROXKey_new.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\WINDOWS\system32\Watchdata\PROXKey CSP India V3.0\registCCID.exe" | C:\Windows\SysWOW64\Watchdata\PROXKey CSP India V3.0\registCCID.exe | — | WD_PROXKey_new.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1228 | regsvr32 /s "C:\WINDOWS\syswow64\Watchdata\PROXKey CSP India V3.0\WDCtr.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2504 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WDKSPconfig.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2984 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4172 | "C:\Program Files (x86)\Watchdata\WD PROXKey\SPPKCSUtil64.exe" -install | C:\Program Files (x86)\Watchdata\WD PROXKey\SPPKCSUtil64.exe | — | SP_CertMND.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SPPKCSUtil Microsoft Basic Application Exit code: 0 Version: 3, 43, 0, 2 Modules
| |||||||||||||||
| 4608 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
64 042
Read events
63 889
Write events
92
Delete events
61
Modification events
| (PID) Process: | (5064) WD_PROXKey_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WD_Stdcertm |
Value: C:\WINDOWS\SysWOW64\Watchdata\PROXKey CSP India V3.0\SP_CertMND.exe | |||
| (PID) Process: | (5064) WD_PROXKey_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WD_SPSocketServer |
Value: C:\WINDOWS\SysWOW64\Watchdata\PROXKey CSP India V3.0\SPSocketServer.exe | |||
| (PID) Process: | (5008) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B3FB9D3C-352D-4F7E-8AE6-43EB19792BFE}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (5008) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{D7018C34-D8CE-4C54-8A46-1EBE62AD2579}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (5008) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{D7018C34-D8CE-4C54-8A46-1EBE62AD2579}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (1228) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{B3FB9D3C-352D-4F7E-8AE6-43EB19792BFE}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (5064) WD_PROXKey_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Calais\SmartCards\WD_Ultimate Key Minidriver |
| Operation: | write | Name: | Primary Provider |
Value: 01110FA8F8D1D011B5C500A024297ED9 | |||
| (PID) Process: | (5064) WD_PROXKey_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Calais\SmartCards\WD_Ultimate Key Minidriver |
| Operation: | write | Name: | Crypto Provider |
Value: PROXKey CSP India V3.0 | |||
| (PID) Process: | (5064) WD_PROXKey_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{3EAA4HC5-79D7-4308-9721-2E6DBD7C110E} |
| Operation: | write | Name: | DisplayName |
Value: WD PROXKey | |||
| (PID) Process: | (5064) WD_PROXKey_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{3EAA4HC5-79D7-4308-9721-2E6DBD7C110E} |
| Operation: | write | Name: | DisplayVersion |
Value: 6.0.3 | |||
Executable files
52
Suspicious files
462
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5064 | WD_PROXKey_new.exe | C:\Windows\SysWOW64\SPNSIS.dll | executable | |
MD5:EE5E22C927B76B5C5E9C716EDAF5BEC6 | SHA256:D3BAD3DECA819FABBE75F16EE1AE88EFAE57C613E0F554068173A5BFCABFE8D1 | |||
| 5064 | WD_PROXKey_new.exe | C:\Windows\SysWOW64\Watchdata\PROXKey CSP India V3.0\SPSocketServer.exe | executable | |
MD5:F458B0346ADE562AC4BABE945849DAA3 | SHA256:EEC6F113EAAF27EB36449C6C0BE44870F96A8DC729F0C29C33E5E1436EF21936 | |||
| 5064 | WD_PROXKey_new.exe | C:\Windows\SysWOW64\Watchdata\PROXKey CSP India V3.0\Ajax Loader(1).gif | image | |
MD5:EC24D1C3A261C84E8895BAD01485F5CE | SHA256:DDA4D8BA5C625C048CE3284CC49827990874C68B3CEA2D15C341D1053934510D | |||
| 5064 | WD_PROXKey_new.exe | C:\Windows\SysWOW64\Watchdata\PROXKey CSP India V3.0\Protect.sig | binary | |
MD5:2CFFDBC1D8417D9D7E4CF103D08AD0A0 | SHA256:89CDFF3CD416B9A6038C3245808CC345BC4FA19275190A083986A076468D6FD4 | |||
| 5064 | WD_PROXKey_new.exe | C:\Windows\SysWOW64\Watchdata\PROXKey CSP India V3.0\SP_CertMND.exe | executable | |
MD5:BF3B68005BFBBA041CCC8879B987B005 | SHA256:D8A8F49FB5CDD45E6F10A3DD804FACFE50A6F368290EB7C16972B8ABE17269E9 | |||
| 5064 | WD_PROXKey_new.exe | C:\Windows\SysWOW64\Watchdata\PROXKey CSP India V3.0\WDAlg.dll | executable | |
MD5:7CC191C5F43B4B5EF13E3D3EA59D7509 | SHA256:74C7C006B7F93FA9194B872BB6D9C5D3D3CFCA545186D397348DD97BF6D2988E | |||
| 5064 | WD_PROXKey_new.exe | C:\Windows\SysWOW64\Watchdata\PROXKey CSP India V3.0\SPMonitor.exe | executable | |
MD5:9BD992F9DDDA84894B8C25AB1C2C37C3 | SHA256:357193BE1CFF5DD0E50827B593F18A74463CF13C42D017A116E21B2797B451E8 | |||
| 5064 | WD_PROXKey_new.exe | C:\Users\admin\AppData\Local\Temp\nslB951.tmp\UserInfo.dll | executable | |
MD5:D16E06C5DE8FB8213A0464568ED9852F | SHA256:728472BA312AE8AF7F30D758AB473E0772477A68FCD1D2D547DAFE6D8800D531 | |||
| 5064 | WD_PROXKey_new.exe | C:\Users\admin\AppData\Local\Temp\nslB951.tmp\modern-header.bmp | image | |
MD5:80913BB1E48109B1C51875A8623BCDA3 | SHA256:AA4BBD56F4053557221B0F158FCD3B699B5D41A8C94A002E787DF20CDFD6967E | |||
| 5064 | WD_PROXKey_new.exe | C:\Users\admin\AppData\Local\Temp\nslB951.tmp\System.dll | executable | |
MD5:959EA64598B9A3E494C00E8FA793BE7E | SHA256:03CD57AB00236C753E7DDEEE8EE1C10839ACE7C426769982365531042E1F6F8B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
22
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3020 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3020 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3020 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
Threats
Process | Message |
|---|---|
SPMonitor.exe | [5668]:Enter GetCCIDDriverFile...
|
SPMonitor.exe | [5668]:Out GetCCIDDriverFile, failed!
|