| File name: | WD_PROXKey_new.exe |
| Full analysis: | https://app.any.run/tasks/1002d6b7-4895-48ac-8d9c-4fc33f4c764f |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2023, 16:55:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 59456002F251902F38DFD220AB3BCB53 |
| SHA1: | A05A6DA4961566D818F17BED4A76A5CF54C918FD |
| SHA256: | C8A2B3CE6C8D0D0E5F717CA7E1446B12E12B3C3F1624A1AE82136C55F9540730 |
| SSDEEP: | 98304:WxZgEM2TlmOKPEL2TiuSkjT/QvYe2zZwlxN+lCUSxhS9pCsJv7UB10CVEFz88pP:9/ |
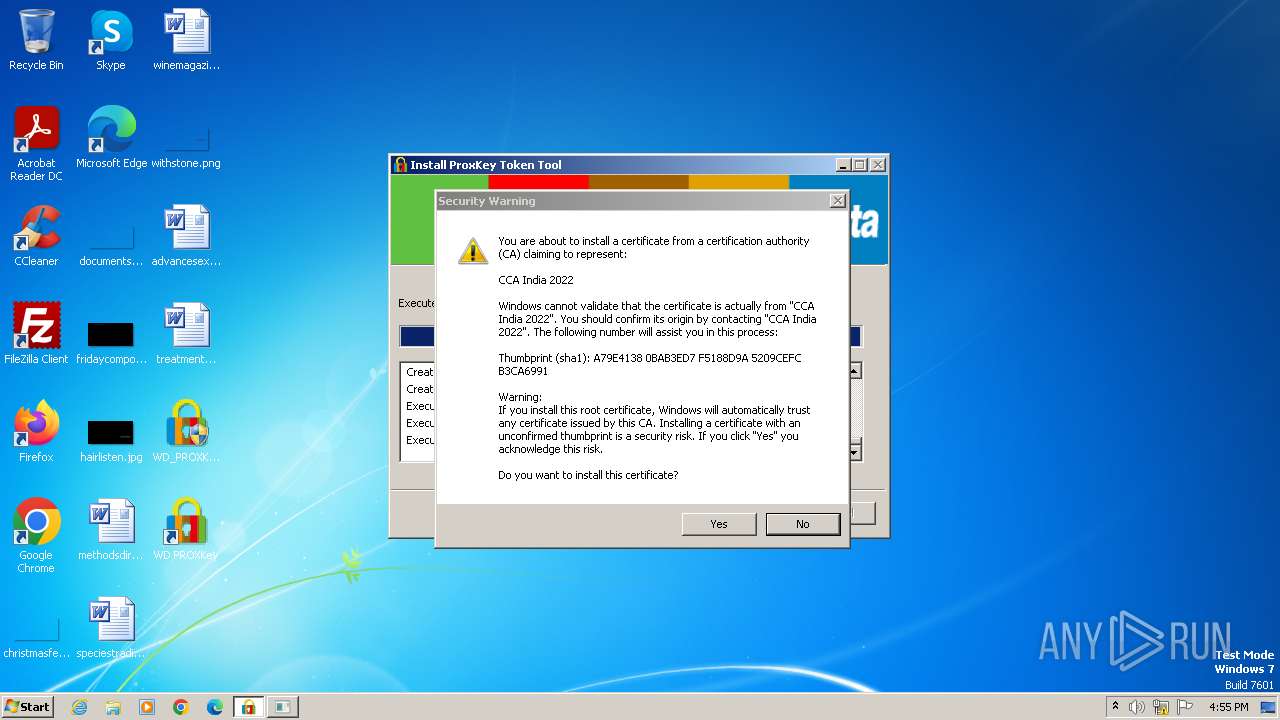
MALICIOUS
Creates a writable file in the system directory
- WD_PROXKey_new.exe (PID: 1560)
Drops the executable file immediately after the start
- WD_PROXKey_new.exe (PID: 1560)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 1844)
Steals credentials from Web Browsers
- SPPKCSUtil.exe (PID: 2716)
- SPPKCSUtil.exe (PID: 3644)
Actions looks like stealing of personal data
- SPPKCSUtil.exe (PID: 2716)
- SPPKCSUtil.exe (PID: 3644)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- WD_PROXKey_new.exe (PID: 1560)
The process creates files with name similar to system file names
- WD_PROXKey_new.exe (PID: 1560)
Drops a system driver (possible attempt to evade defenses)
- WD_PROXKey_new.exe (PID: 1560)
Process drops legitimate windows executable
- WD_PROXKey_new.exe (PID: 1560)
Executes as Windows Service
- SPMonitor.exe (PID: 3892)
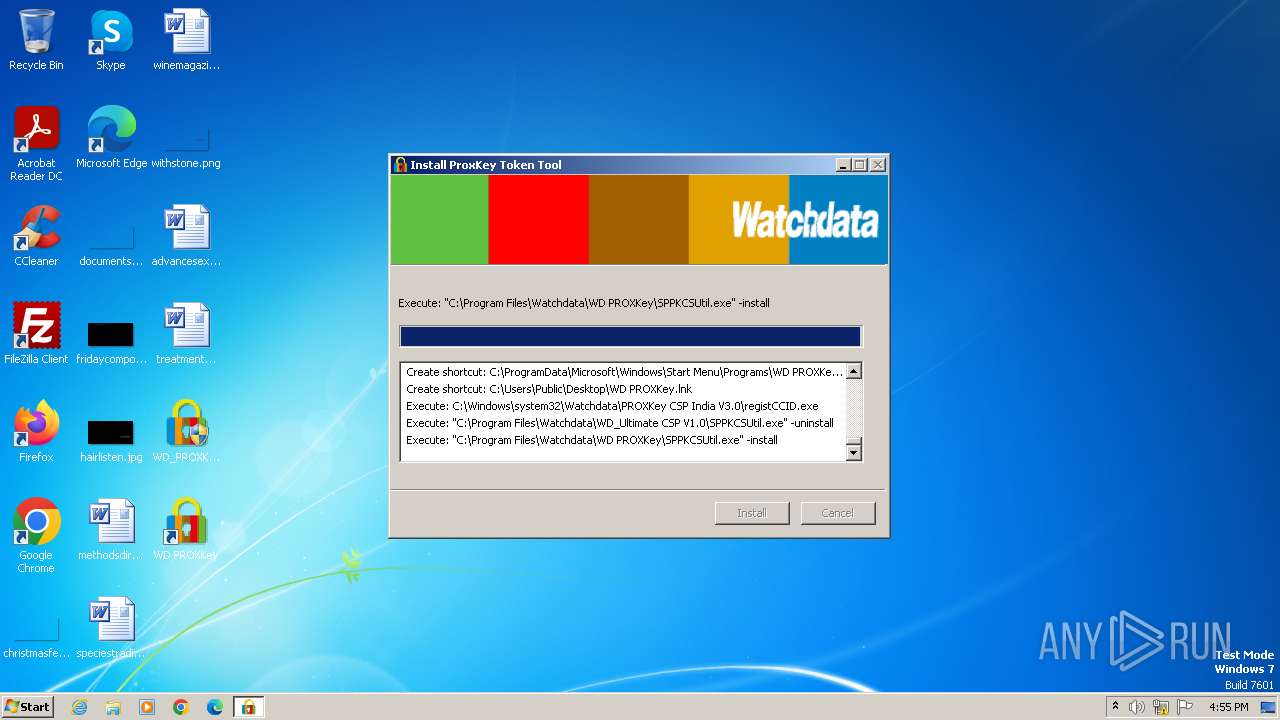
Executing commands from a ".bat" file
- WD_PROXKey_new.exe (PID: 1560)
Starts application with an unusual extension
- WD_PROXKey_new.exe (PID: 1560)
Starts SC.EXE for service management
- cmd.exe (PID: 3216)
Starts CMD.EXE for commands execution
- WD_PROXKey_new.exe (PID: 1560)
- nsA43.tmp (PID: 3112)
Loads DLL from Mozilla Firefox
- SPPKCSUtil.exe (PID: 2716)
- SPPKCSUtil.exe (PID: 3644)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 3564)
- explorer.exe (PID: 3528)
Reads the Internet Settings
- WD_PROXKey_new.exe (PID: 1560)
Reads settings of System Certificates
- SPPKCSUtil.exe (PID: 3644)
- SPPKCSUtil.exe (PID: 2716)
Reads Mozilla Firefox installation path
- SPPKCSUtil.exe (PID: 3644)
- SPPKCSUtil.exe (PID: 2716)
INFO
Checks supported languages
- WD_PROXKey_new.exe (PID: 1560)
- SPMonitor.exe (PID: 3892)
- nsA43.tmp (PID: 3112)
- registCCID.exe (PID: 3880)
- WDKSPconfig.exe (PID: 3168)
- SPPKCSUtil.exe (PID: 3644)
- SPPKCSUtil.exe (PID: 2716)
- SP_CertMND.exe (PID: 3052)
- SPSocketServer.exe (PID: 1296)
Reads the computer name
- WD_PROXKey_new.exe (PID: 1560)
- SPMonitor.exe (PID: 3892)
- SPPKCSUtil.exe (PID: 2716)
- SPPKCSUtil.exe (PID: 3644)
- SP_CertMND.exe (PID: 3052)
Create files in a temporary directory
- WD_PROXKey_new.exe (PID: 1560)
Creates files in the program directory
- WD_PROXKey_new.exe (PID: 1560)
Creates files or folders in the user directory
- SPPKCSUtil.exe (PID: 2716)
- SPPKCSUtil.exe (PID: 3644)
Reads the Internet Settings
- explorer.exe (PID: 3092)
- explorer.exe (PID: 3252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:10 14:19:31+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 25600 |
| InitializedDataSize: | 431104 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x354b |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.3.0 |
| ProductVersionNumber: | 6.0.3.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | ProxKey |
| CompanyName: | Watchdata Technologies Pte. Ltd. |
| FileDescription: | ProxKey |
| FileVersion: | 6.0.3.0 |
| LegalCopyright: | Copyright (c) 2007 Watchdata Technologies Pte. Ltd. All rights reserved. |
| ProductName: | ProxKey |
| ProductVersion: | 6.0.3.0 |
Total processes
60
Monitored processes
18
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | "C:\Windows\System32\Watchdata\PROXKey CSP India V3.0\SPSocketServer.exe" | C:\Windows\System32\Watchdata\PROXKey CSP India V3.0\SPSocketServer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1556 | "C:\Users\admin\Desktop\WD_PROXKey_new.exe" | C:\Users\admin\Desktop\WD_PROXKey_new.exe | — | explorer.exe | |||||||||||
User: admin Company: Watchdata Technologies Pte. Ltd. Integrity Level: MEDIUM Description: ProxKey Exit code: 3221226540 Version: 6.0.3.0 Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\Desktop\WD_PROXKey_new.exe" | C:\Users\admin\Desktop\WD_PROXKey_new.exe | explorer.exe | ||||||||||||
User: admin Company: Watchdata Technologies Pte. Ltd. Integrity Level: HIGH Description: ProxKey Exit code: 0 Version: 6.0.3.0 Modules
| |||||||||||||||
| 1844 | C:\Windows\system32\cmd.exe /C regsvr32 /s "C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\WDCtr.dll" | C:\Windows\System32\cmd.exe | — | nsA43.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1936 | sc failure SPMonitor reset= 0 actions= restart/3000/restart/3000/restart/3000 | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Watchdata\WD PROXKey\SPPKCSUtil.exe" -install | C:\Program Files\Watchdata\WD PROXKey\SPPKCSUtil.exe | WD_PROXKey_new.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SPPKCSUtil Microsoft Basic Application Exit code: 0 Version: 3, 43, 0, 2 Modules
| |||||||||||||||
| 3052 | "C:\Windows\System32\Watchdata\PROXKey CSP India V3.0\SP_CertMND.exe" | C:\Windows\System32\Watchdata\PROXKey CSP India V3.0\SP_CertMND.exe | — | explorer.exe | |||||||||||
User: admin Company: Watchdata Technologies Pte. Ltd. Integrity Level: MEDIUM Description: SP Daemon3.2 Exit code: 0 Version: 3, 2, 0, 0 Modules
| |||||||||||||||
| 3080 | regsvr32 /s "C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\WDCtr.dll" | C:\Windows\System32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3092 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\AppData\Local\Temp\nsi35C.tmp\nsA43.tmp" C:\Windows\system32\cmd.exe /C regsvr32 /s "C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\WDCtr.dll" | C:\Users\admin\AppData\Local\Temp\nsi35C.tmp\nsA43.tmp | — | WD_PROXKey_new.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
26 813
Read events
26 776
Write events
37
Delete events
0
Modification events
| (PID) Process: | (1560) WD_PROXKey_new.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\nsi35C.tmp\nsProcessW.dll | |||
| (PID) Process: | (1560) WD_PROXKey_new.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1560) WD_PROXKey_new.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1560) WD_PROXKey_new.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1560) WD_PROXKey_new.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3092) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3092) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3092) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3092) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
36
Suspicious files
459
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1560 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\Ajax Loader(1).gif | image | |
MD5:EC24D1C3A261C84E8895BAD01485F5CE | SHA256:DDA4D8BA5C625C048CE3284CC49827990874C68B3CEA2D15C341D1053934510D | |||
| 1560 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\InstallUsbccid.exe | executable | |
MD5:7EF413CD0D114777E1B50E621ECB8490 | SHA256:233CF2EAC6233B0F6A74F1B71561191C1E0EE82365FA876EFA93E07593BBC231 | |||
| 1560 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\SP_CertMND.exe | executable | |
MD5:BF3B68005BFBBA041CCC8879B987B005 | SHA256:D8A8F49FB5CDD45E6F10A3DD804FACFE50A6F368290EB7C16972B8ABE17269E9 | |||
| 1560 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\USBTokenDiagnosticTool.exe | executable | |
MD5:8BC0B236327B746080591673D2EDDFE5 | SHA256:E919ACE622518B3696BABF033E86DD20ACEE06FF1A22226B22BC7CF1CBB17160 | |||
| 1560 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\ServiceConfig.bat | text | |
MD5:D348717F3ED2120E3093FDD174F8A09E | SHA256:F011339A35E80694ADB92A953CF0547AC81AFC6D53CF668645C474F1C56BECA7 | |||
| 1560 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\Protectini.ini | text | |
MD5:18F2A646D983DD0A259B9125D9D5BAE7 | SHA256:C97CC62E28FD727E82B0E06BB46960036BE66DECCB6F2D89CB5A53DB50B52D8A | |||
| 1560 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\UIResE3.dll | executable | |
MD5:2A20DD1983F9D30C9F0887CF34CA91FB | SHA256:19112C6EEF7FFC162245D7E19C8601FA49CCD239076AC32D3FE0AD9D0AFB3E0B | |||
| 1560 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\Protect.sig | binary | |
MD5:2CFFDBC1D8417D9D7E4CF103D08AD0A0 | SHA256:89CDFF3CD416B9A6038C3245808CC345BC4FA19275190A083986A076468D6FD4 | |||
| 1560 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\WD_Ult_CertMND.exe | binary | |
MD5:A25627F4F52B73EED3713CADACC0C491 | SHA256:D716BC2A3E84E2EDB9B370742D70B00BA76B59A0D1AB5BA4A012F2E307DA7A2C | |||
| 1560 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V3.0\SPMonitor.exe | executable | |
MD5:9BD992F9DDDA84894B8C25AB1C2C37C3 | SHA256:357193BE1CFF5DD0E50827B593F18A74463CF13C42D017A116E21B2797B451E8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Threats
Process | Message |
|---|---|
SPMonitor.exe | [3892]:Enter GetCCIDDriverFile...
|
SPMonitor.exe | [3892]:Enter SetupDiEnumDeviceInfo...
|
SPMonitor.exe | [3892]:Out SetupDiEnumDeviceInfo, iWaitUpdateTime = 0
|
SPMonitor.exe | [3892]:Out GetCCIDDriverFile, succeed!
|