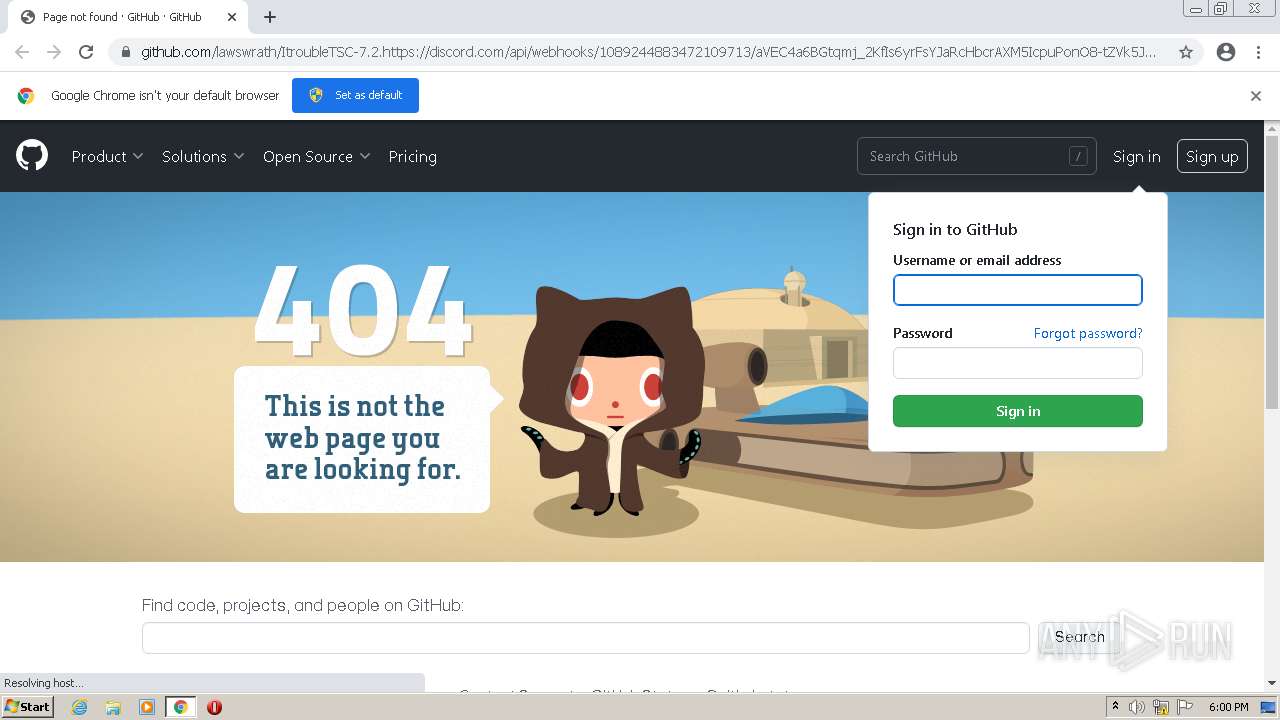
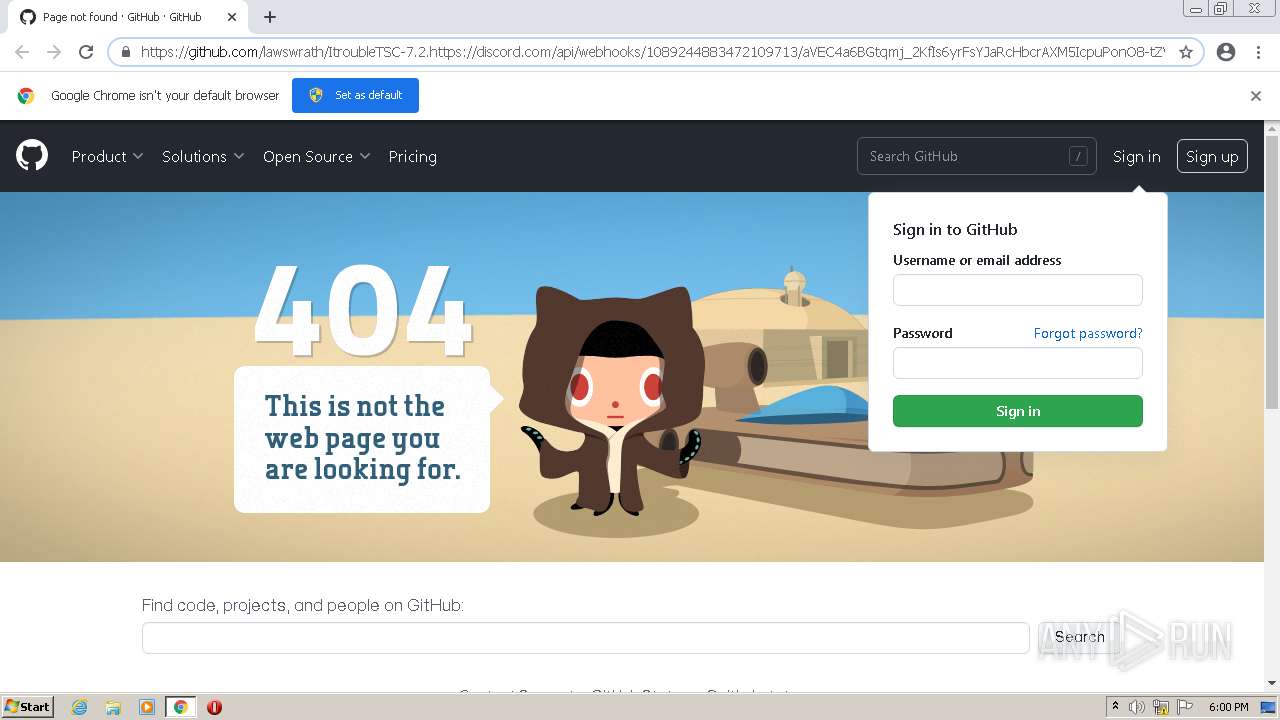
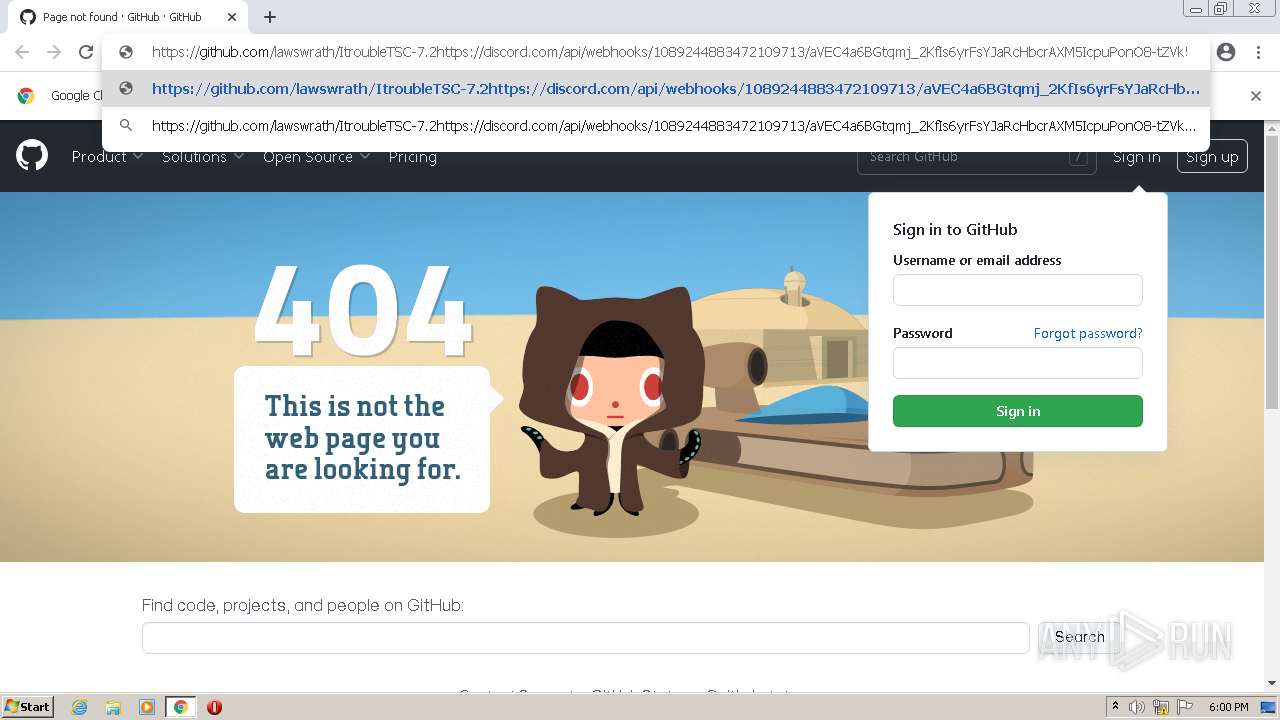
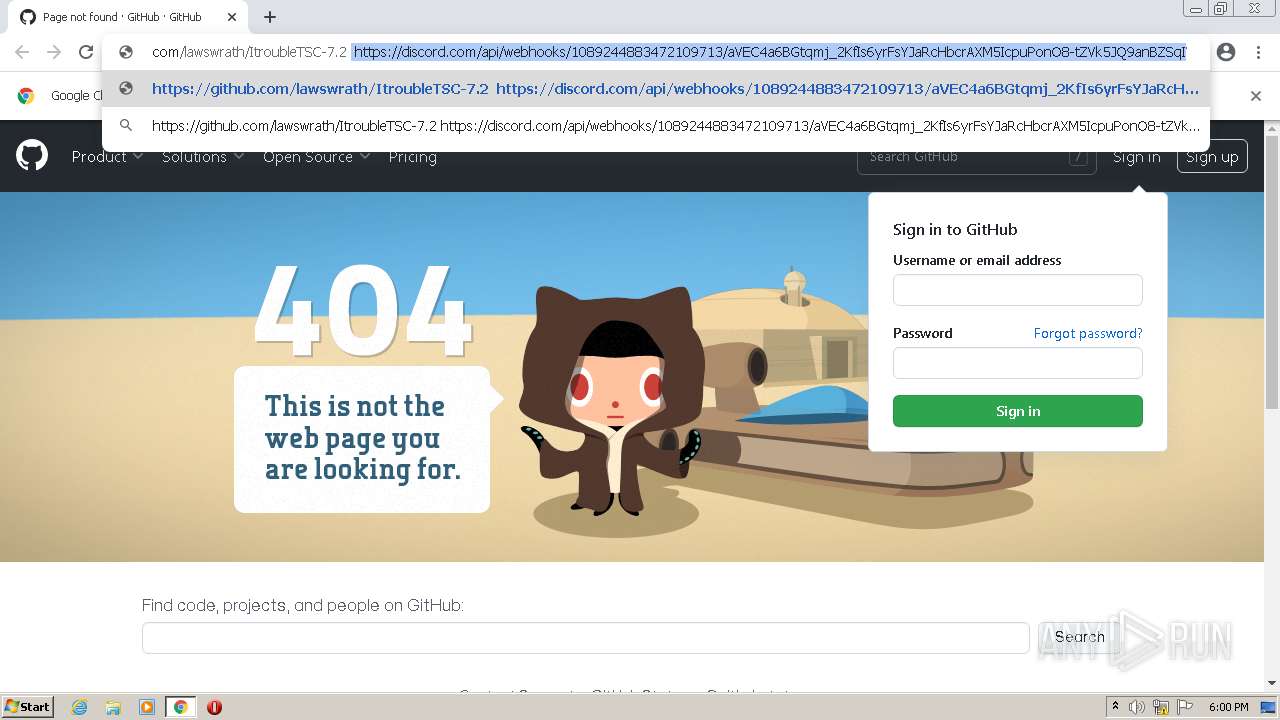
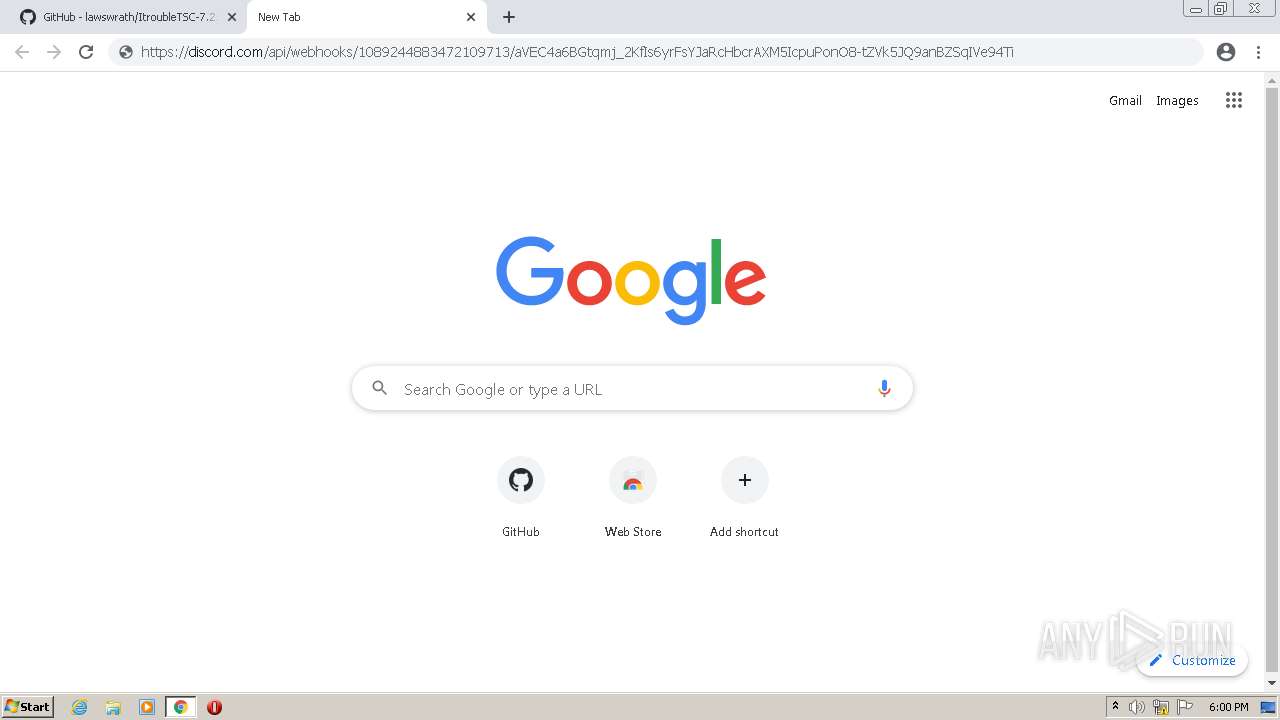
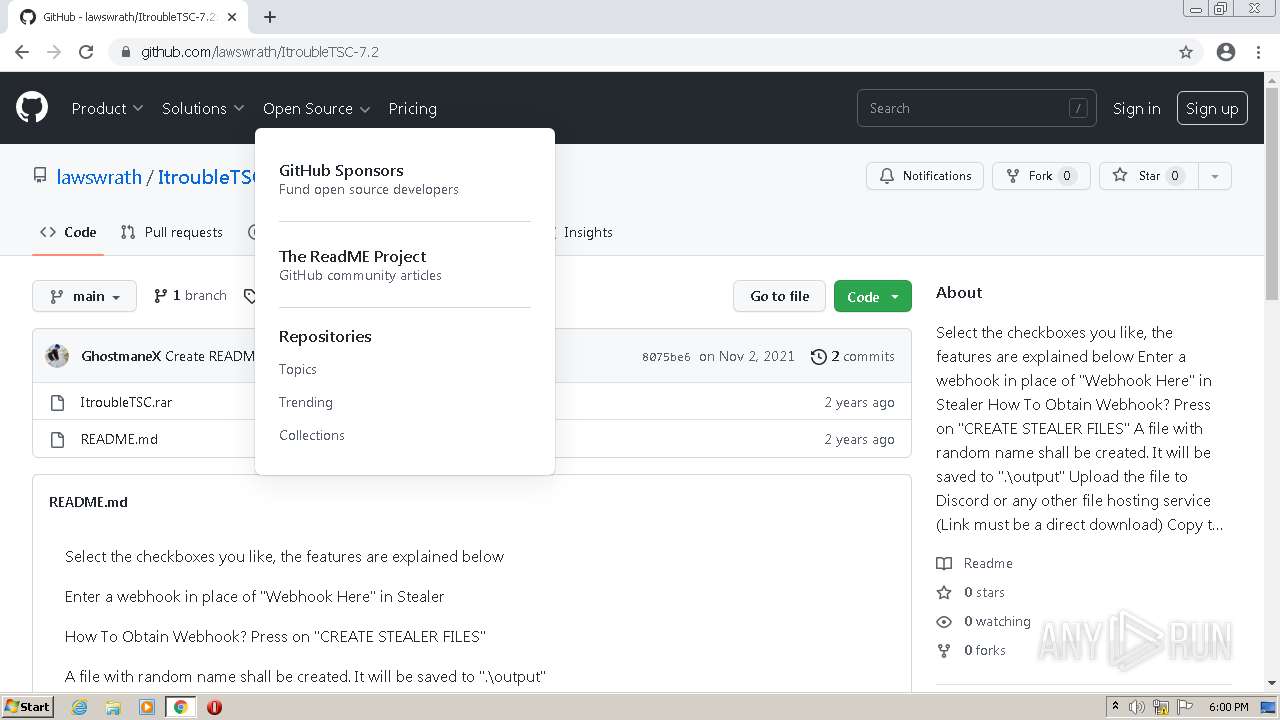
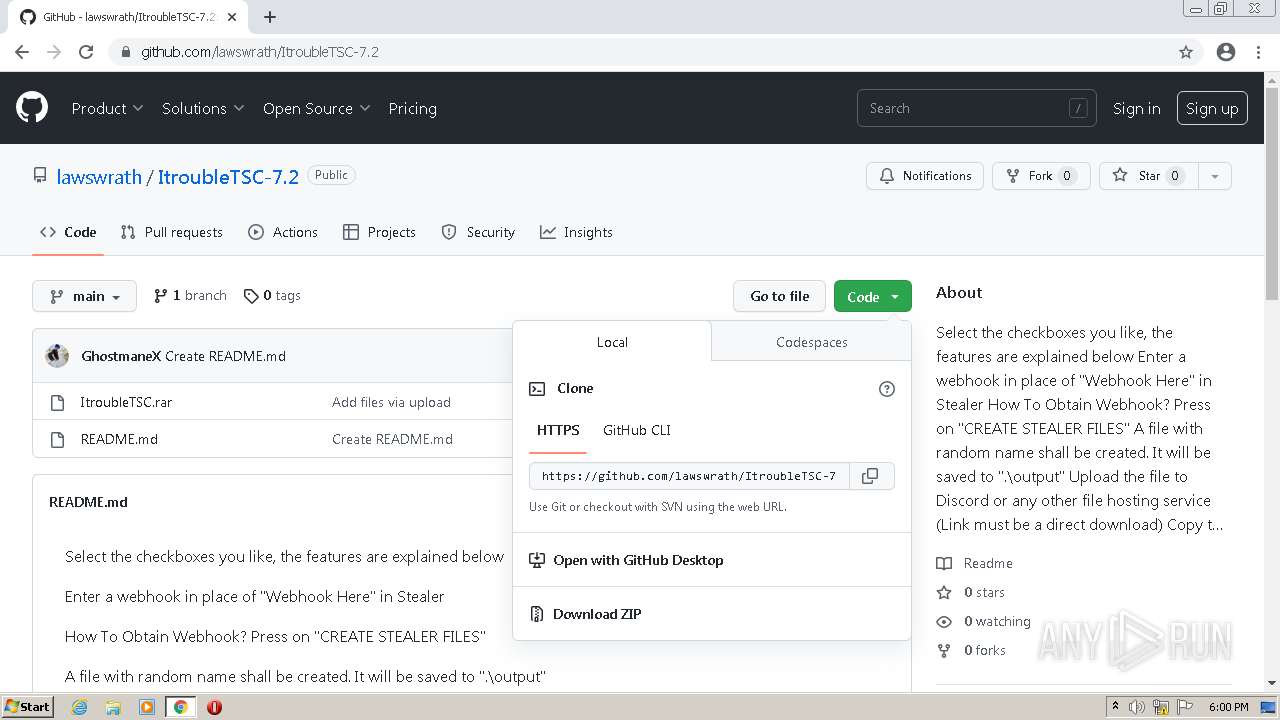
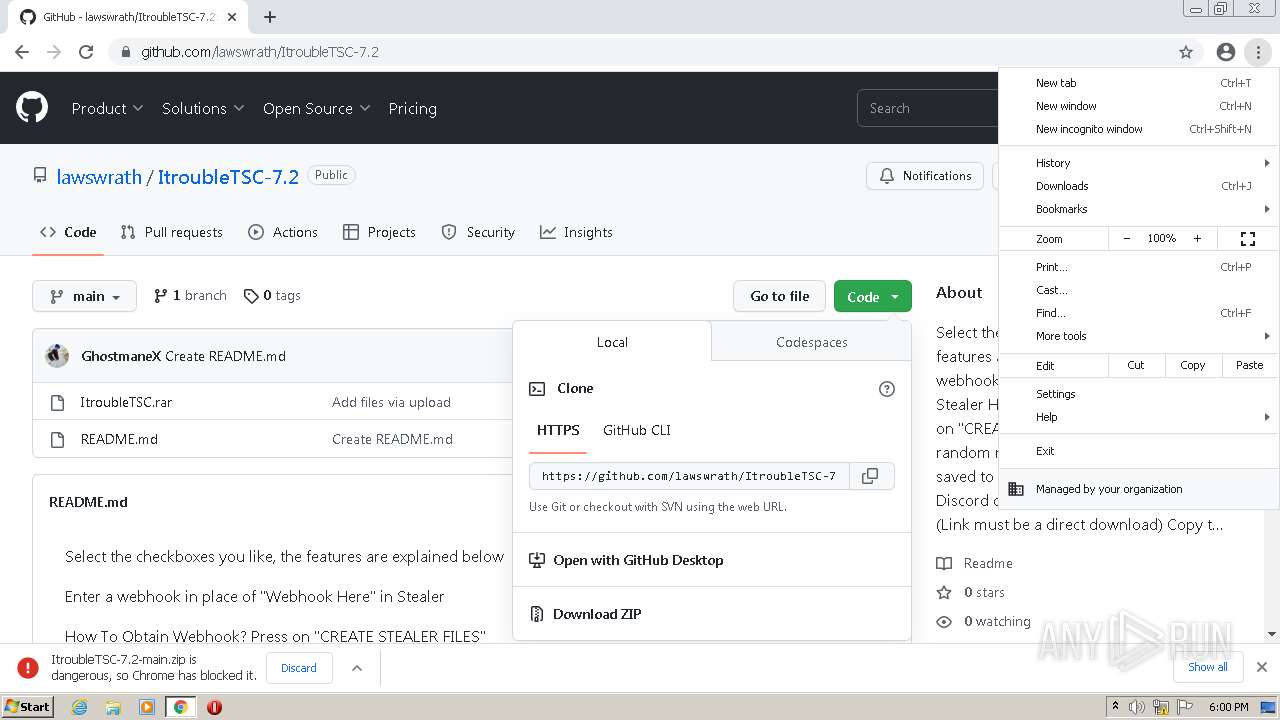
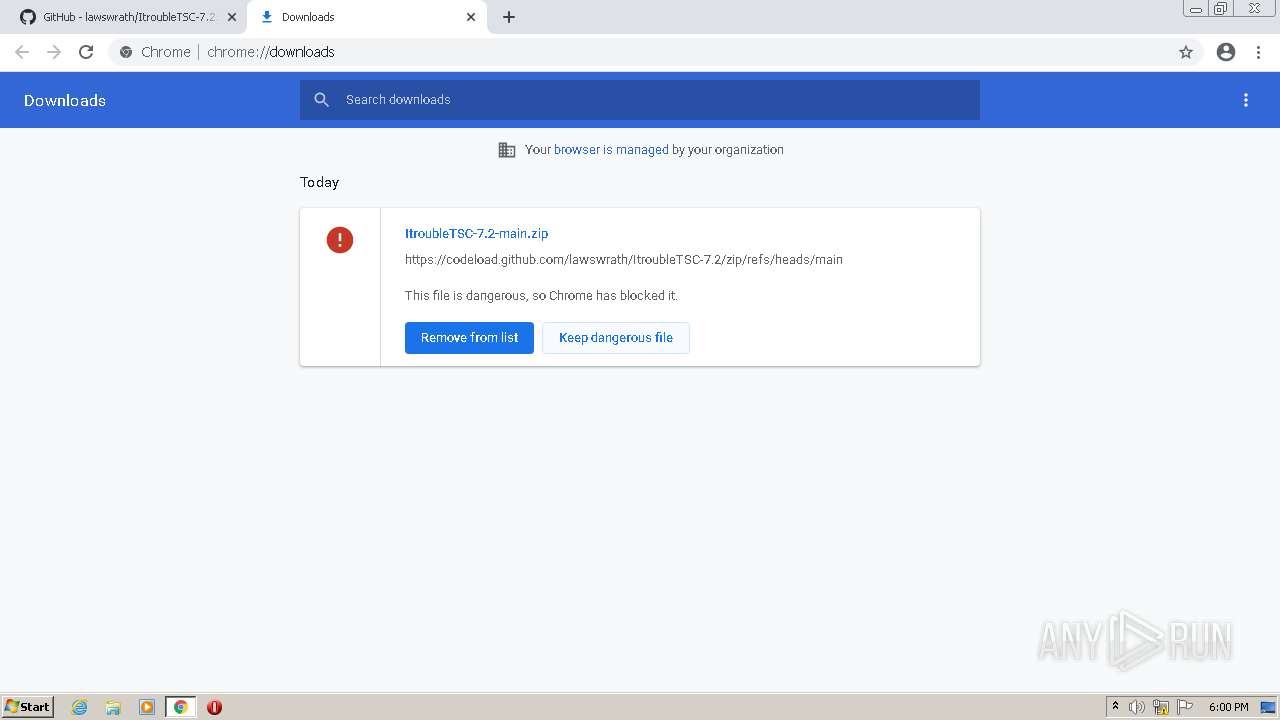
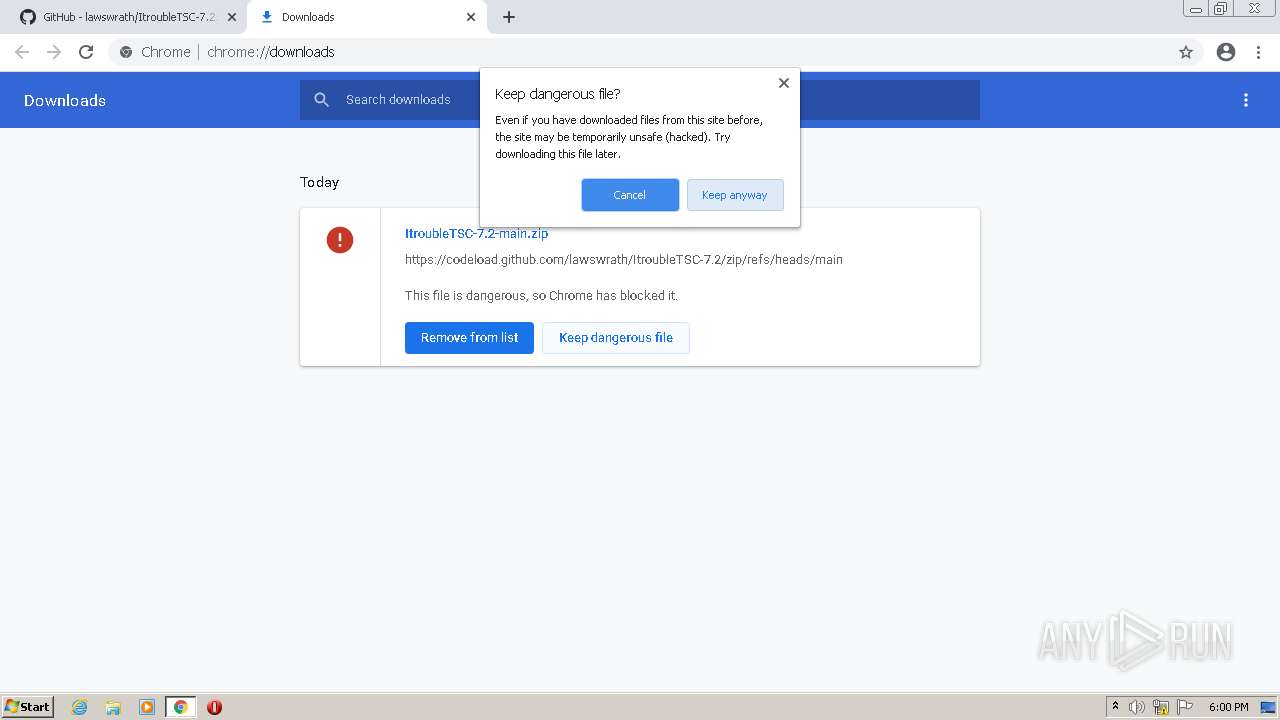
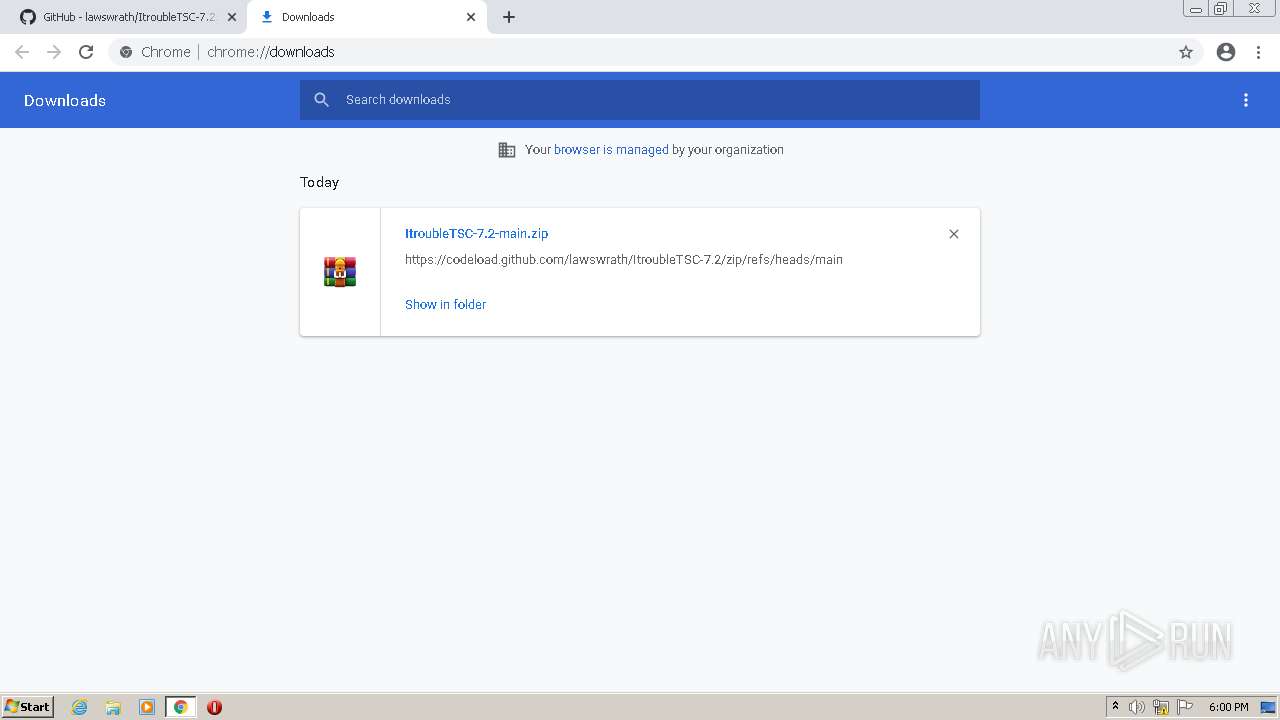
| URL: | https://github.com/lawswrath/ItroubleTSC-7.2.https://discord.com/api/webhooks/1089244883472109713/aVEC4a6BGtqmj_2KfIs6yrFsYJaRcHbcrAXM5IcpuPonO8-tZVk5JQ9anBZSqIVe94Ti |
| Full analysis: | https://app.any.run/tasks/526f54a1-26e3-4758-90a7-6c94c7c52579 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2023, 18:00:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 225CD494A702630EEF38811BF2AC41CC |
| SHA1: | D5710EE19021194B158AD9F21AD2149053A7EF0D |
| SHA256: | C8947ACD7F5B2E9E69F74034FB11A37FC38693DB96C83747CC108F06477ABA9E |
| SSDEEP: | 3:N8tEd5E1XKSOxtLCU8XkTFztmU0/TyU5830K3QqK/zvU4O:2ucdNUh0/2X3QqKLvUN |
MALICIOUS
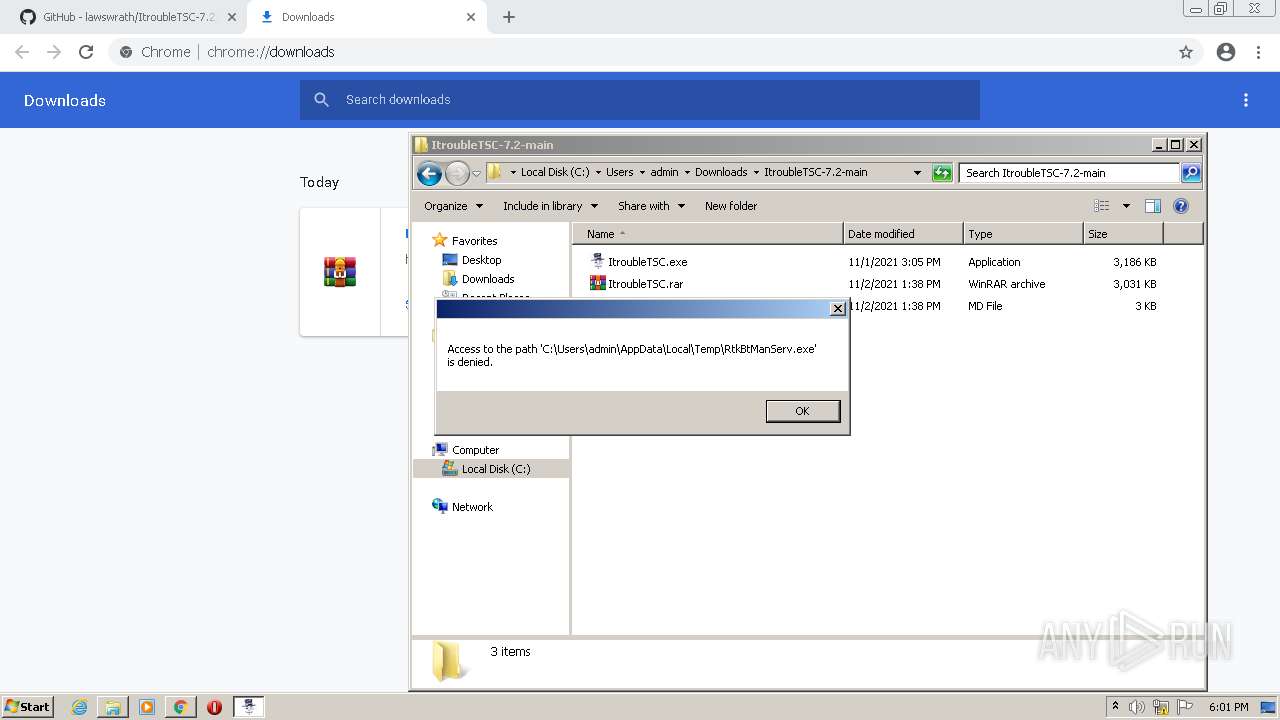
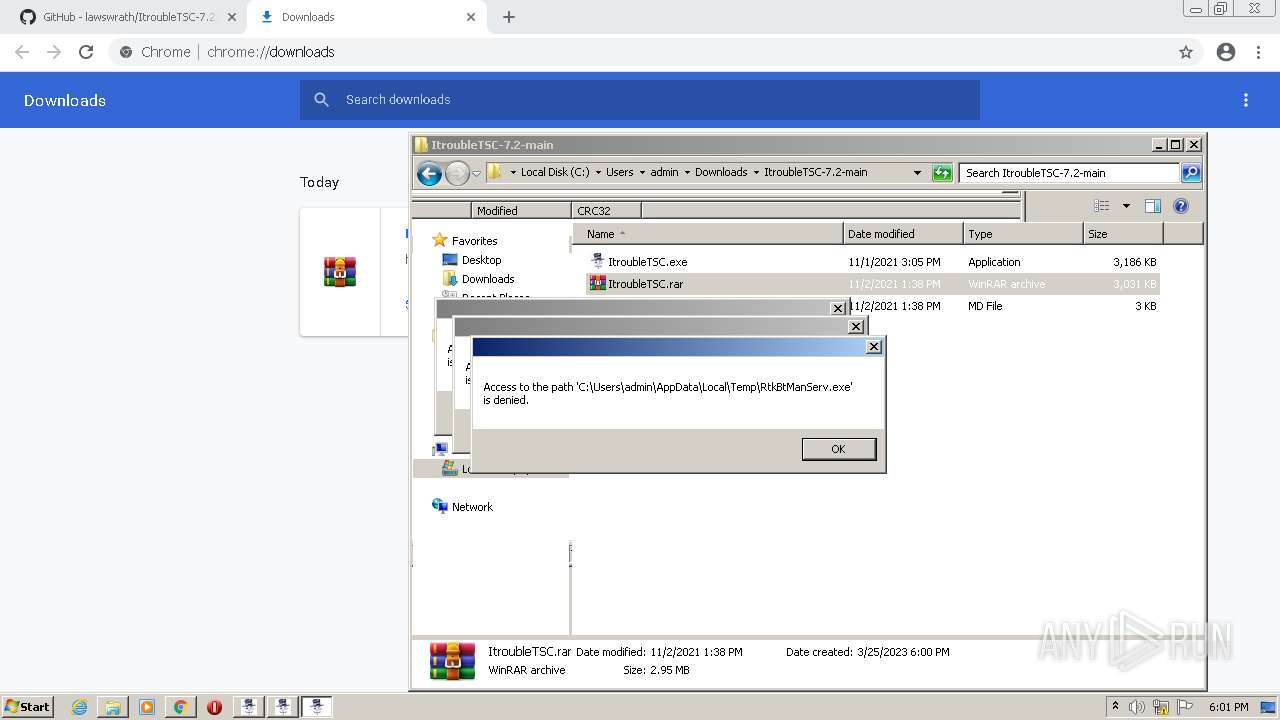
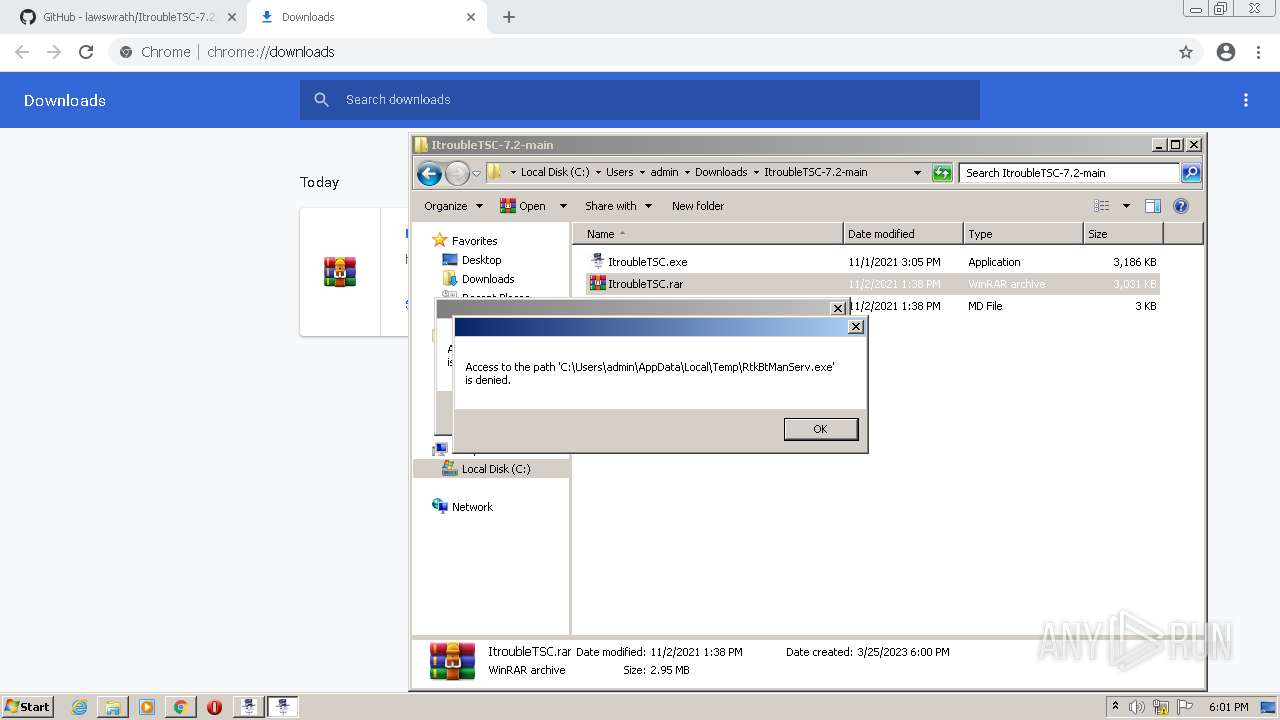
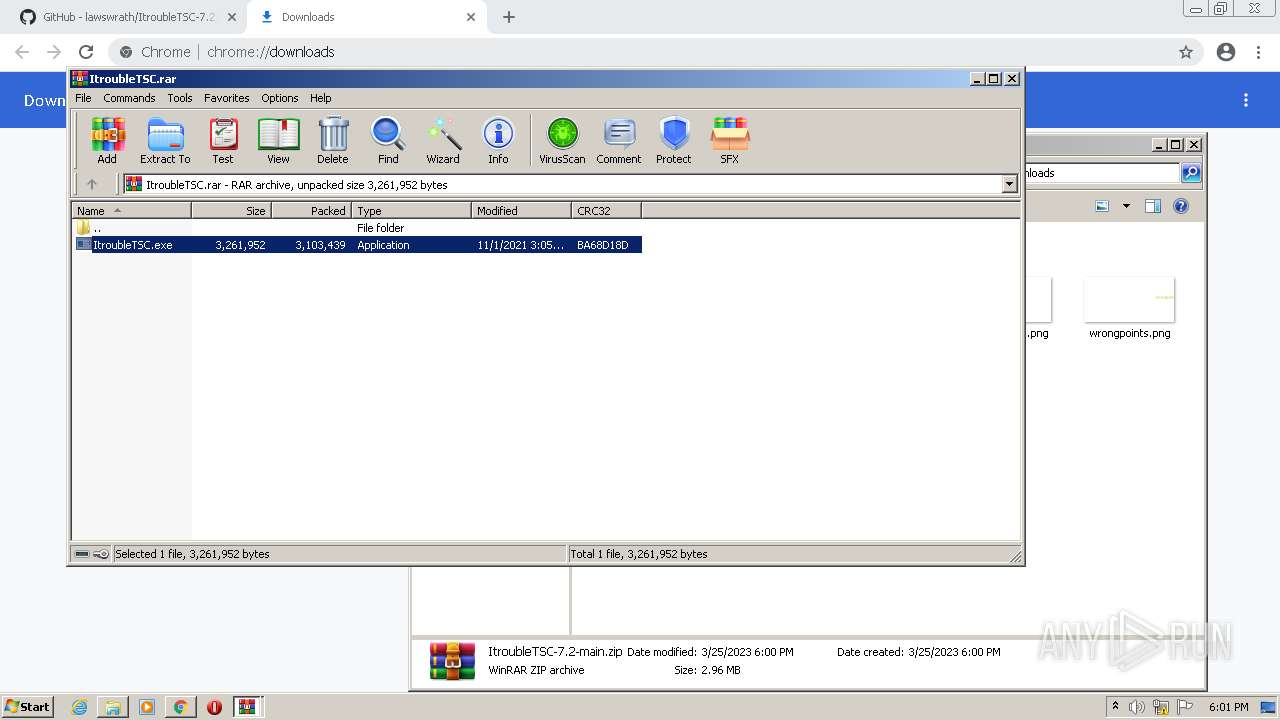
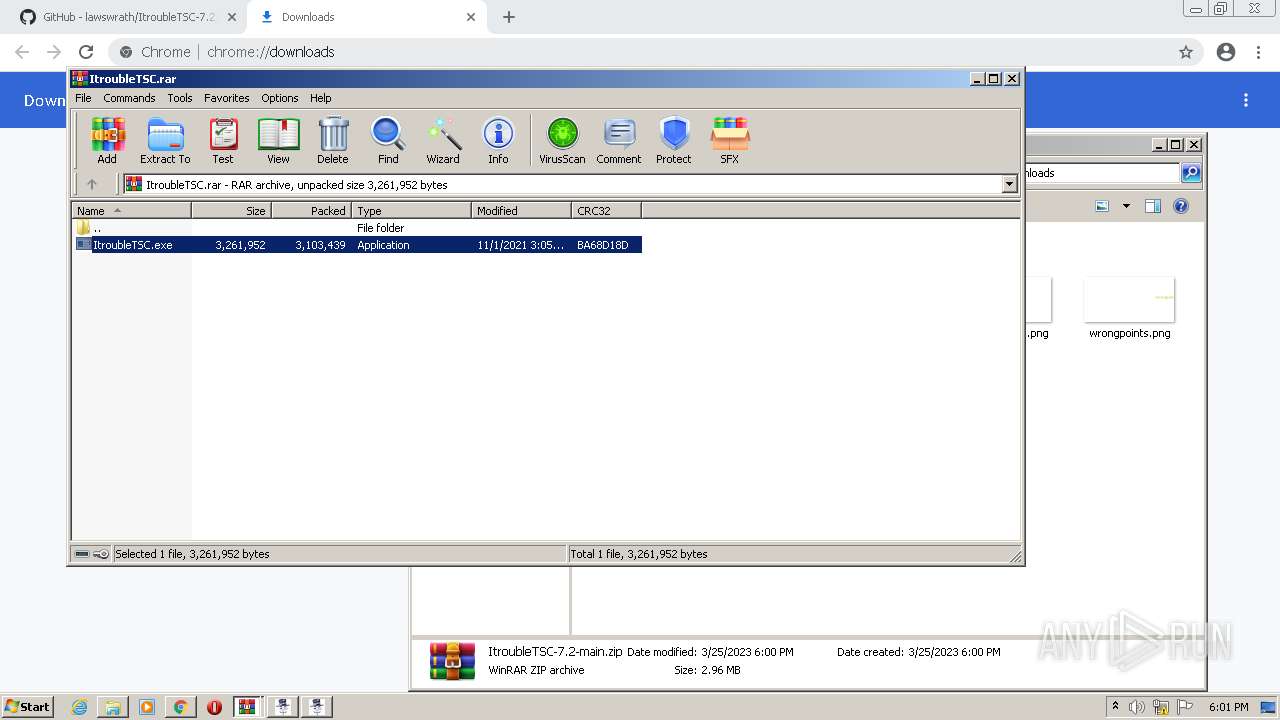
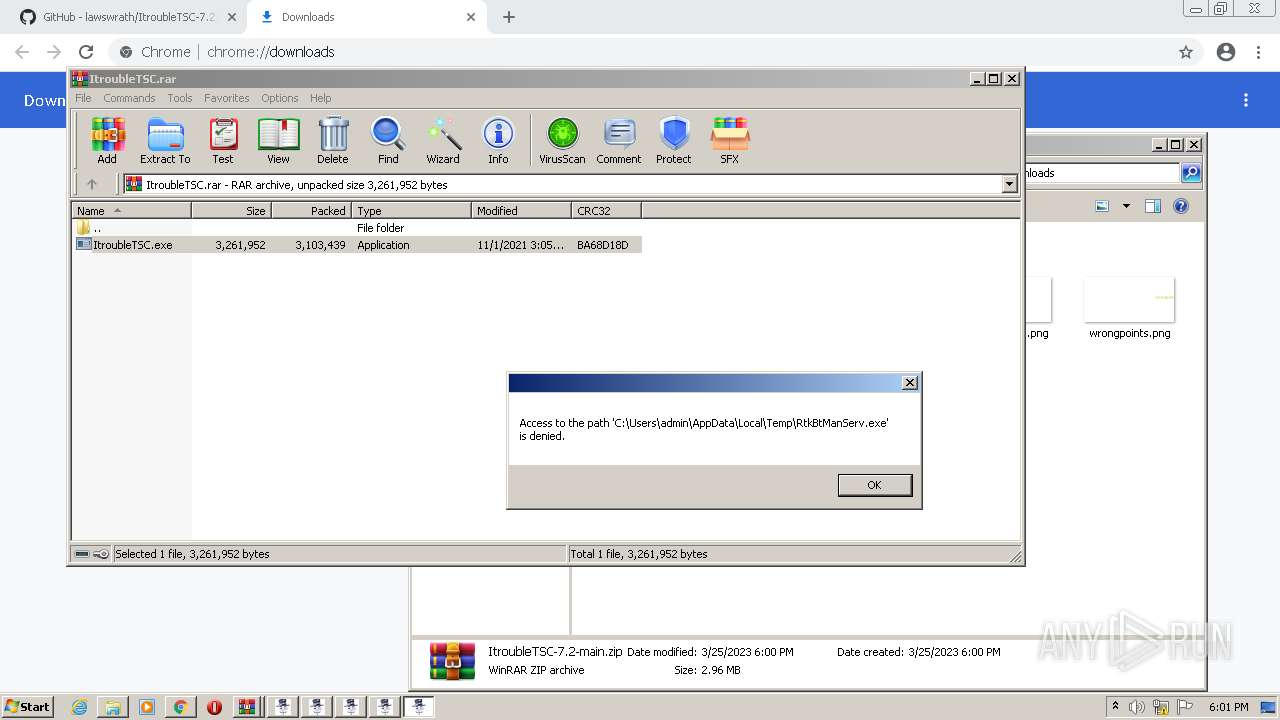
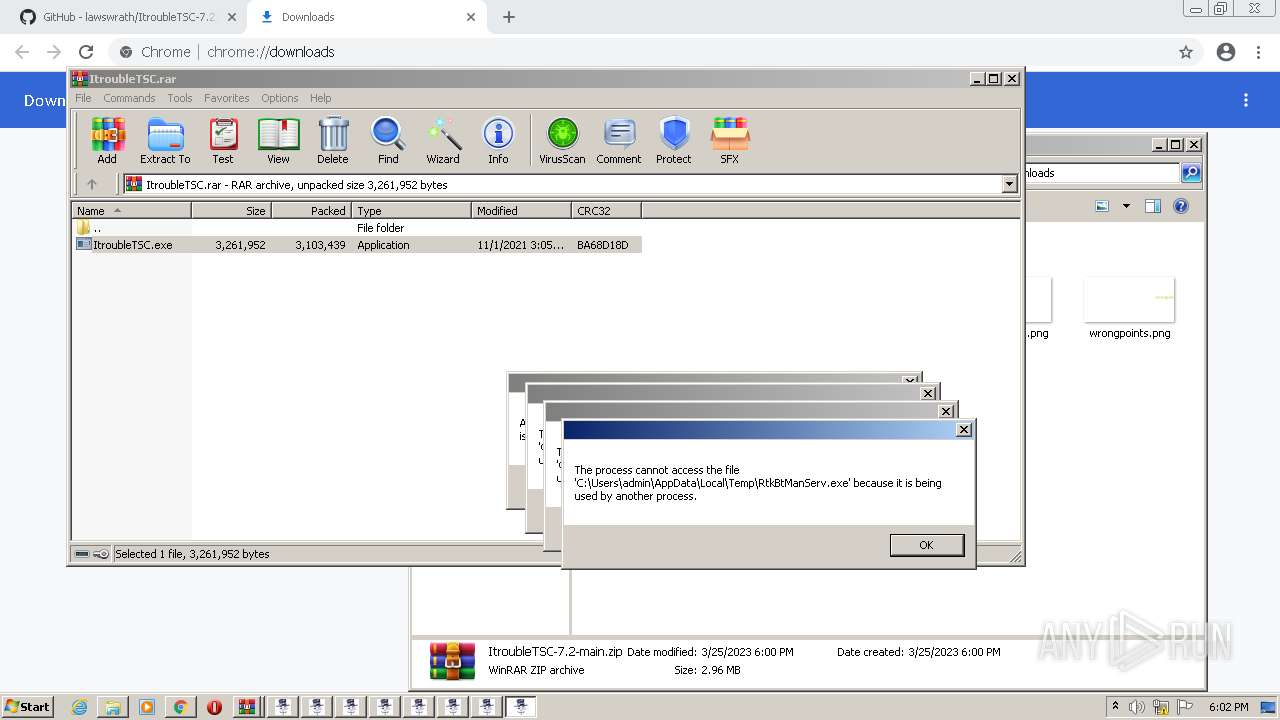
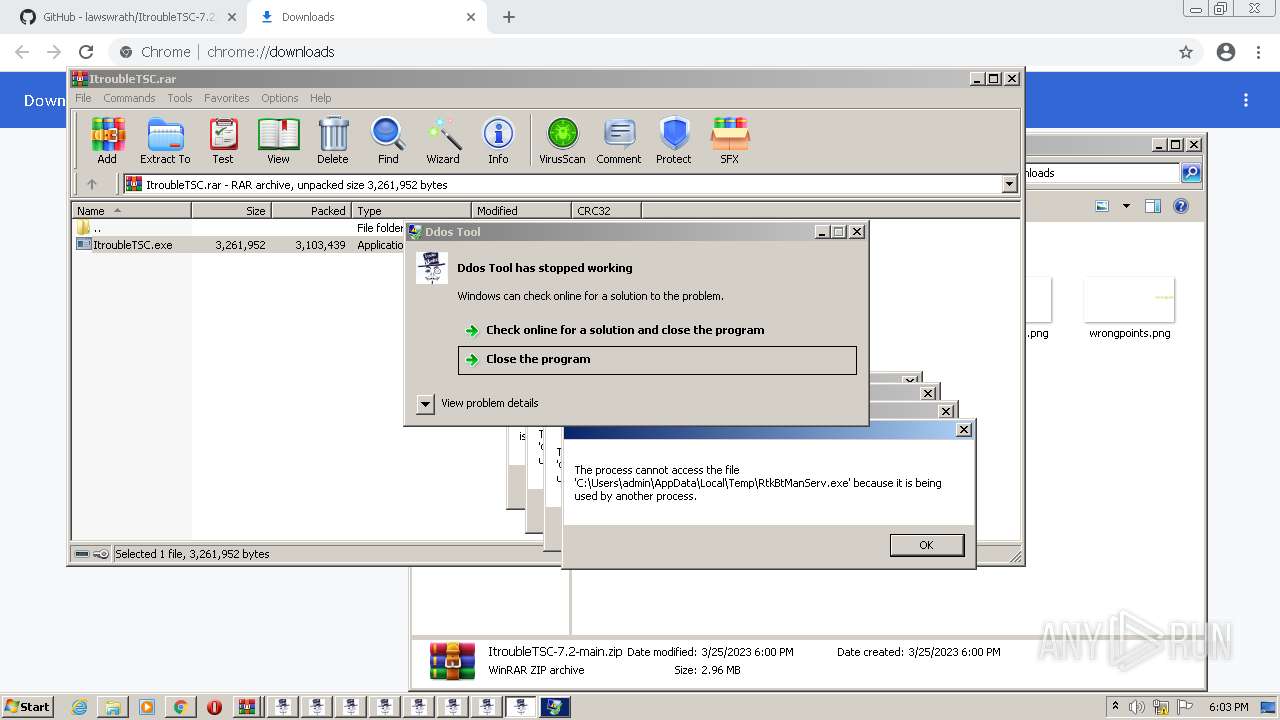
Application was dropped or rewritten from another process
- ItroubleTSC.exe (PID: 3516)
- RtkBtManServ.exe (PID: 1816)
- bfsvc.exe (PID: 2568)
- snuvcdsm.exe (PID: 2660)
- ItroubleTSC.exe (PID: 3064)
- splwow64.exe (PID: 976)
- winhlp32.exe (PID: 2640)
- hh.exe (PID: 2716)
- ItroubleTSC.exe (PID: 2564)
- ItroubleTSC.exe (PID: 1888)
- ItroubleTSC.exe (PID: 3792)
- ItroubleTSC.exe (PID: 3788)
- ItroubleTSC.exe (PID: 2656)
- ItroubleTSC.exe (PID: 1476)
- ItroubleTSC.exe (PID: 3576)
- ItroubleTSC.exe (PID: 3676)
- RtkBtManServ.exe (PID: 1616)
- bfsvc.exe (PID: 1460)
- snuvcdsm.exe (PID: 3016)
- xwizard.exe (PID: 2744)
- splwow64.exe (PID: 3104)
- hh.exe (PID: 2092)
- xwizard.exe (PID: 3300)
- winhlp32.exe (PID: 4032)
Create files in the Startup directory
- ItroubleTSC.exe (PID: 3516)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3196)
- cmd.exe (PID: 1012)
Actions looks like stealing of personal data
- RtkBtManServ.exe (PID: 1816)
- winhlp32.exe (PID: 2640)
- splwow64.exe (PID: 976)
- snuvcdsm.exe (PID: 2660)
Creates or modifies Windows services
- reg.exe (PID: 2248)
Steals credentials from Web Browsers
- snuvcdsm.exe (PID: 2660)
- hh.exe (PID: 2716)
SUSPICIOUS
Reads the Internet Settings
- ItroubleTSC.exe (PID: 3516)
- RtkBtManServ.exe (PID: 1816)
- wscript.exe (PID: 2988)
- wscript.exe (PID: 3824)
- wscript.exe (PID: 3956)
- rundll32.exe (PID: 2924)
Executable content was dropped or overwritten
- ItroubleTSC.exe (PID: 3516)
- RtkBtManServ.exe (PID: 1816)
- RtkBtManServ.exe (PID: 1616)
- ItroubleTSC.exe (PID: 1888)
Executing commands from a ".bat" file
- ItroubleTSC.exe (PID: 3516)
- wscript.exe (PID: 2988)
- wscript.exe (PID: 3824)
- wscript.exe (PID: 3956)
- wscript.exe (PID: 624)
- ItroubleTSC.exe (PID: 1888)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 3320)
- wscript.exe (PID: 4072)
- wscript.exe (PID: 3336)
Starts CMD.EXE for commands execution
- ItroubleTSC.exe (PID: 3516)
- wscript.exe (PID: 2988)
- wscript.exe (PID: 3824)
- wscript.exe (PID: 3956)
- wscript.exe (PID: 624)
- RtkBtManServ.exe (PID: 1816)
- ItroubleTSC.exe (PID: 1888)
- wscript.exe (PID: 3320)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 4072)
- wscript.exe (PID: 3336)
- RtkBtManServ.exe (PID: 1616)
Uses REG/REGEDIT.EXE to modify register
- cmd.exe (PID: 3196)
- cmd.exe (PID: 1012)
Reads browser cookies
- RtkBtManServ.exe (PID: 1816)
The process executes VB scripts
- RtkBtManServ.exe (PID: 1816)
- RtkBtManServ.exe (PID: 1616)
Reads settings of System Certificates
- RtkBtManServ.exe (PID: 1816)
Loads DLL from Mozilla Firefox
- splwow64.exe (PID: 976)
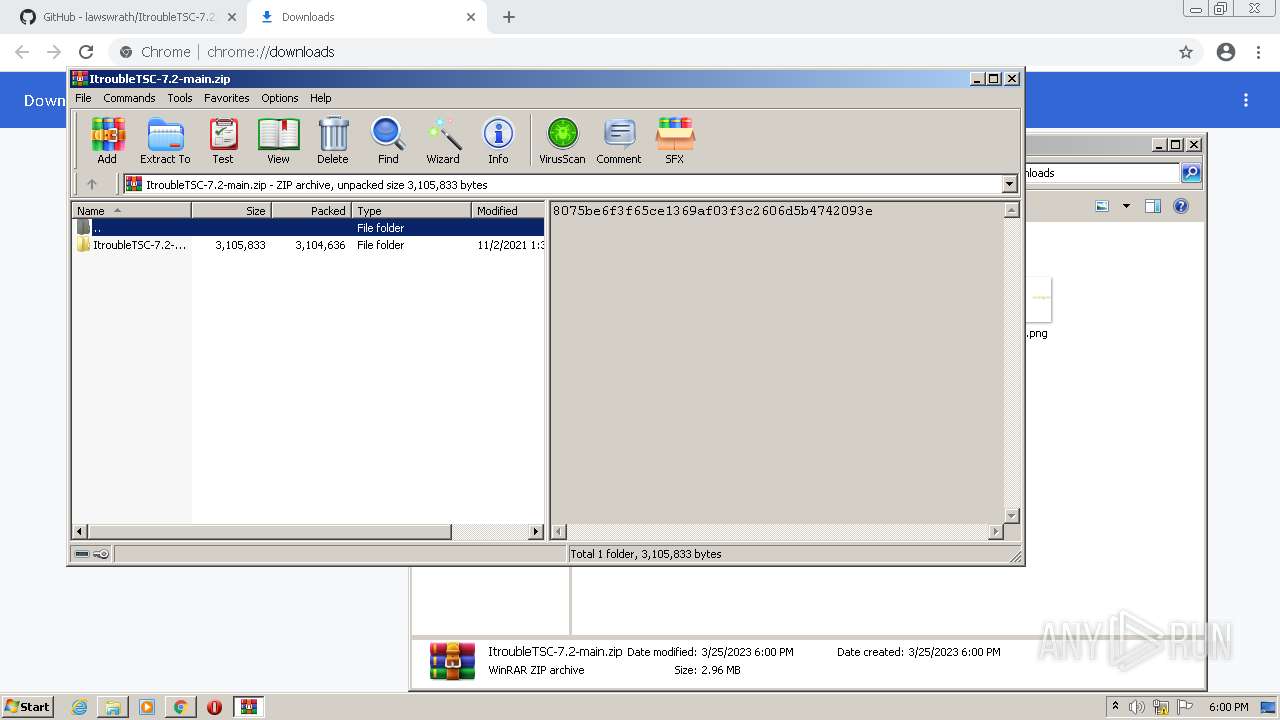
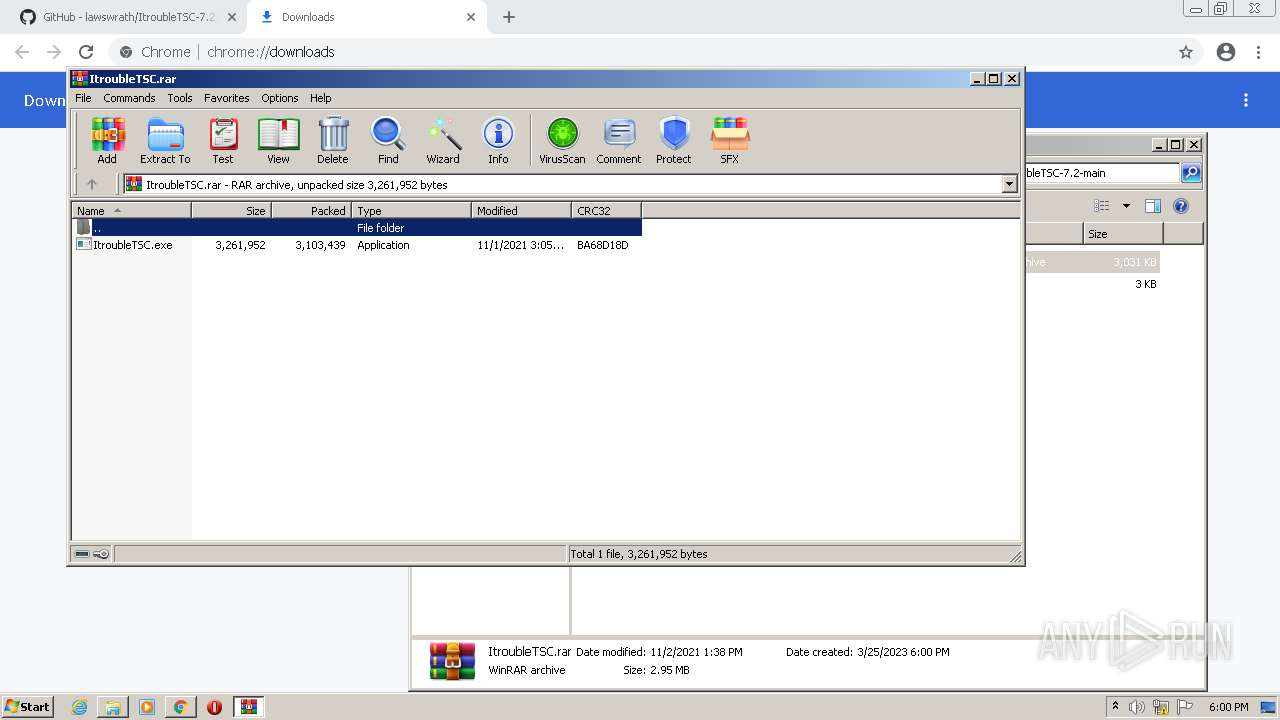
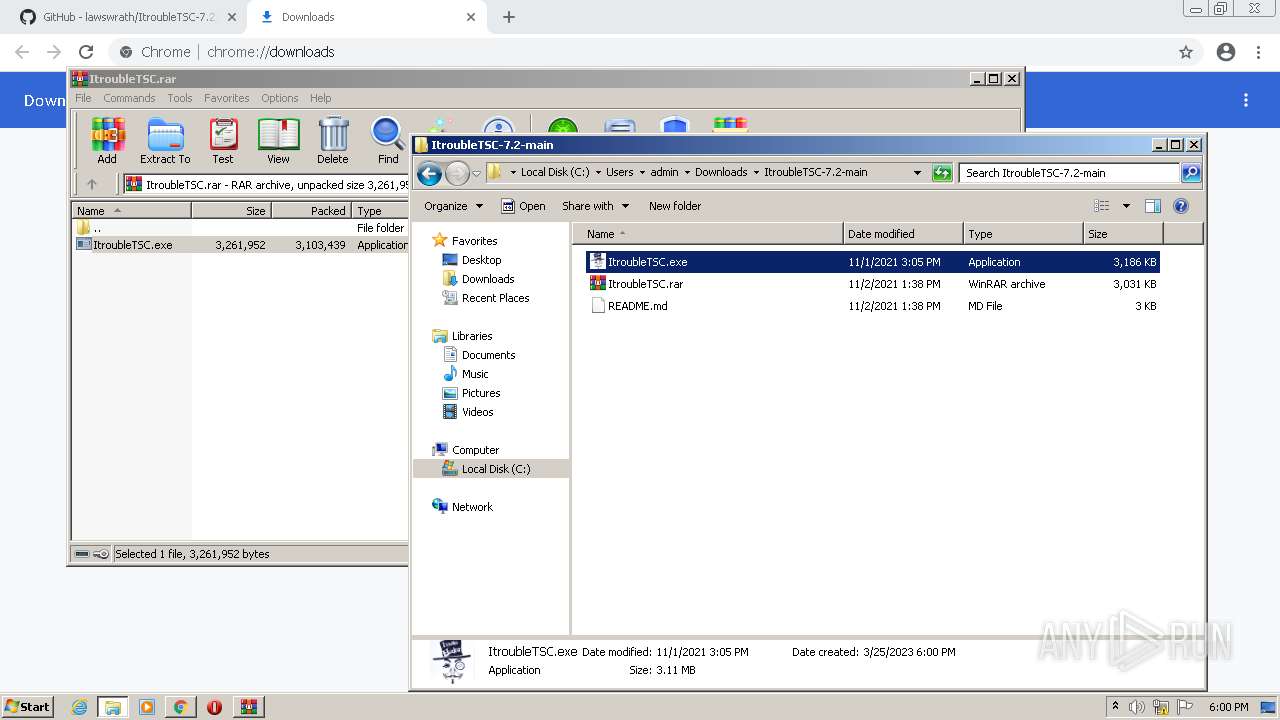
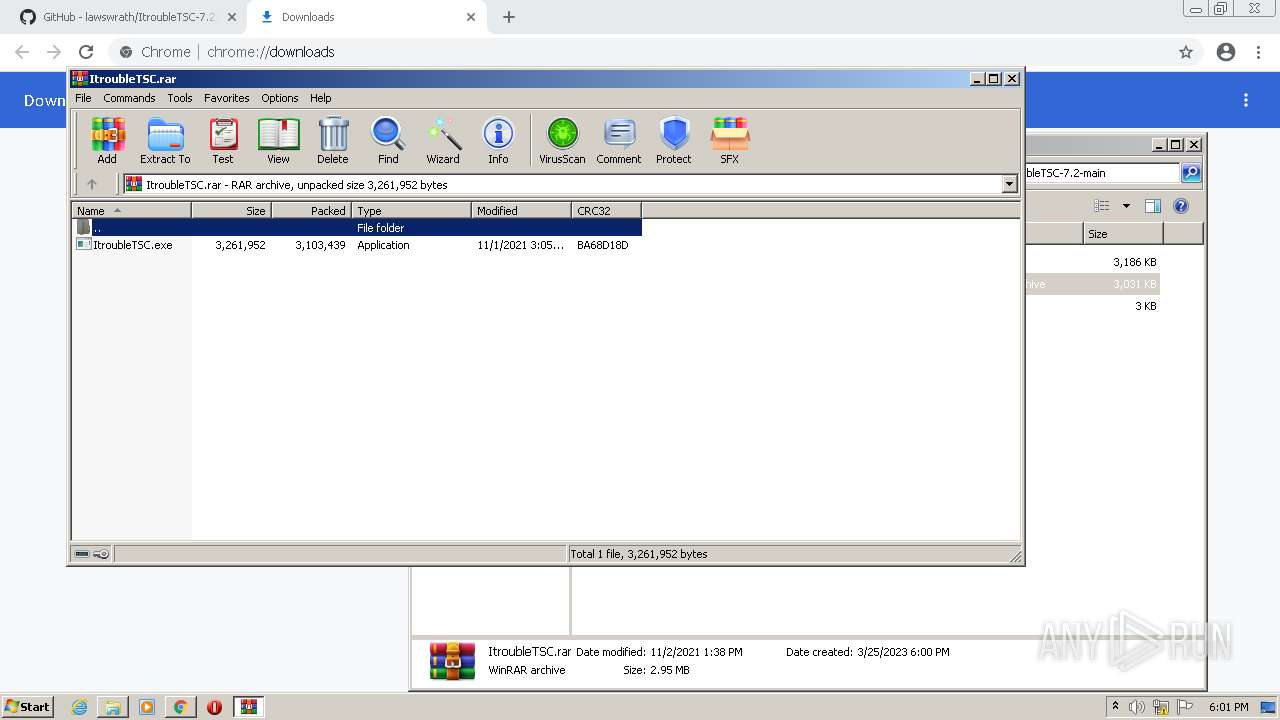
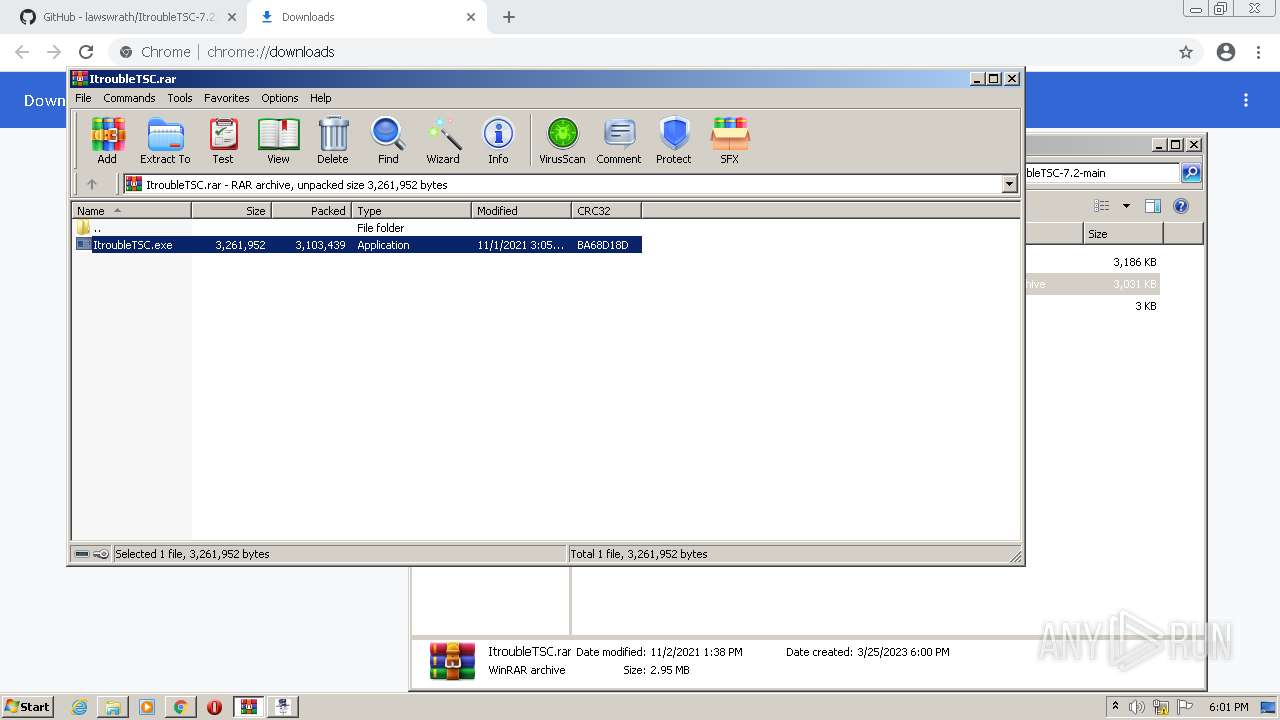
Application launched itself
- WinRAR.exe (PID: 1836)
The system shut down or reboot
- RtkBtManServ.exe (PID: 1816)
- RtkBtManServ.exe (PID: 1616)
INFO
Application launched itself
- chrome.exe (PID: 2572)
- iexplore.exe (PID: 4036)
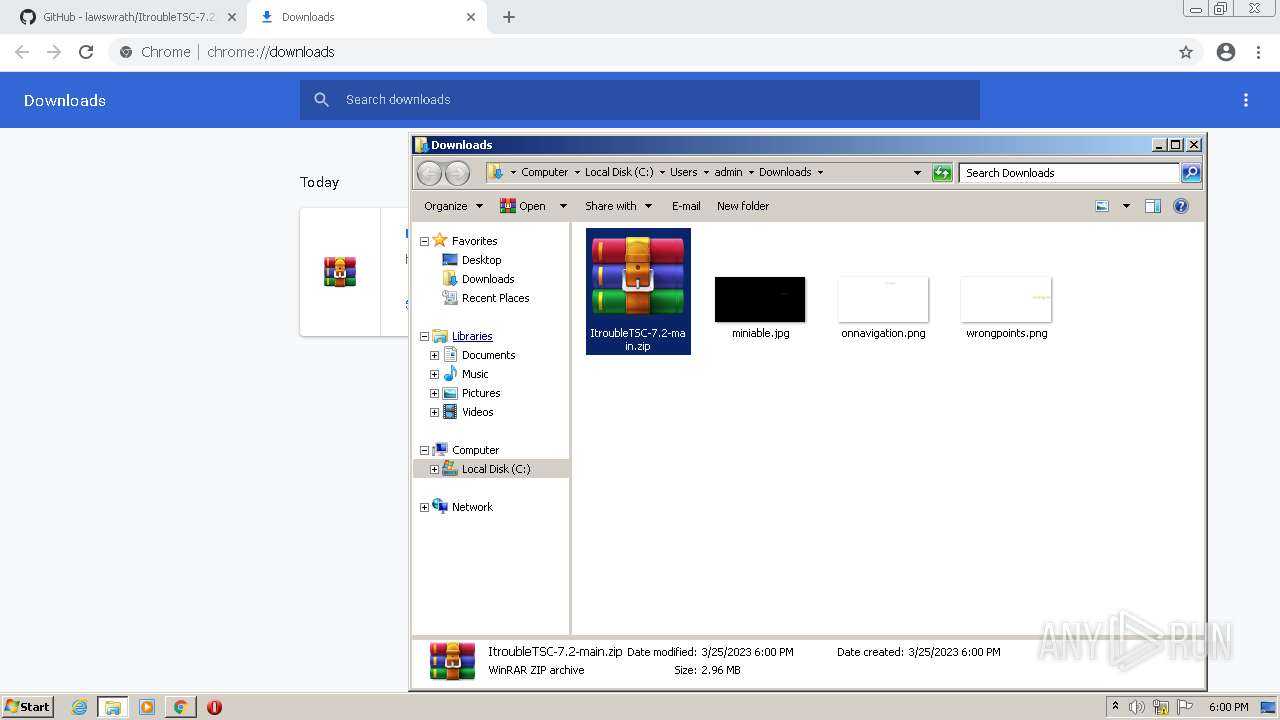
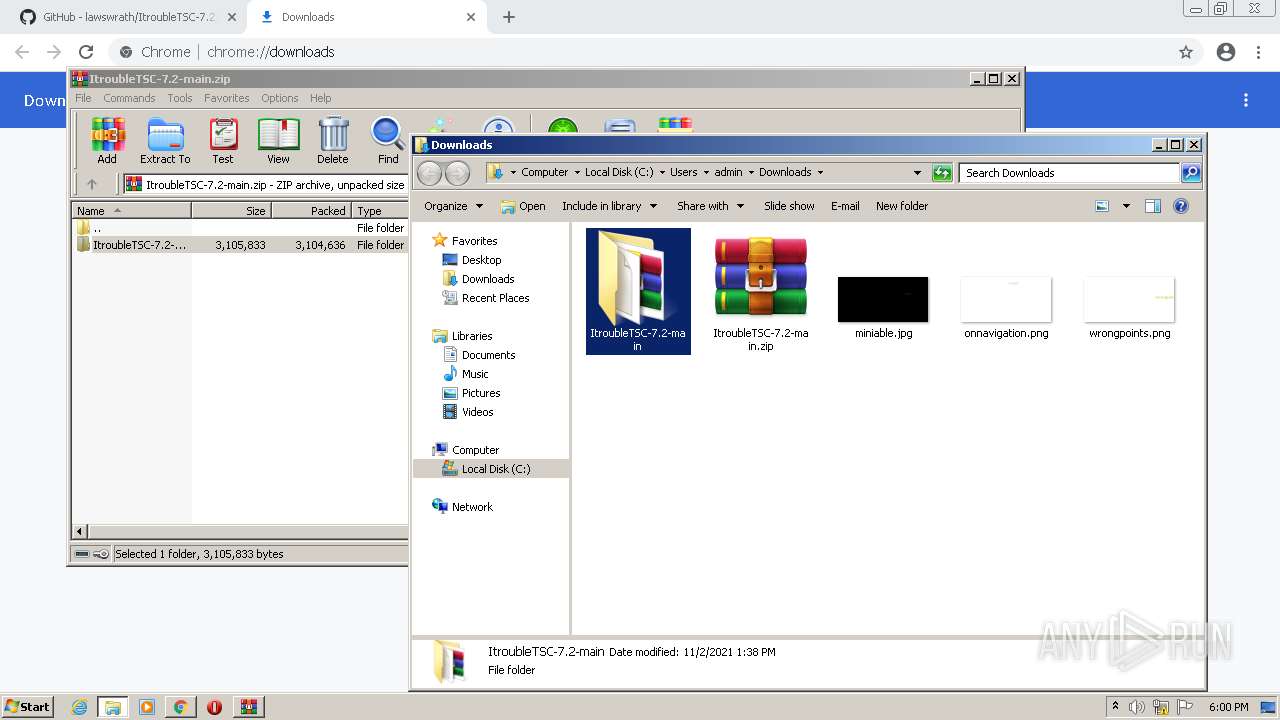
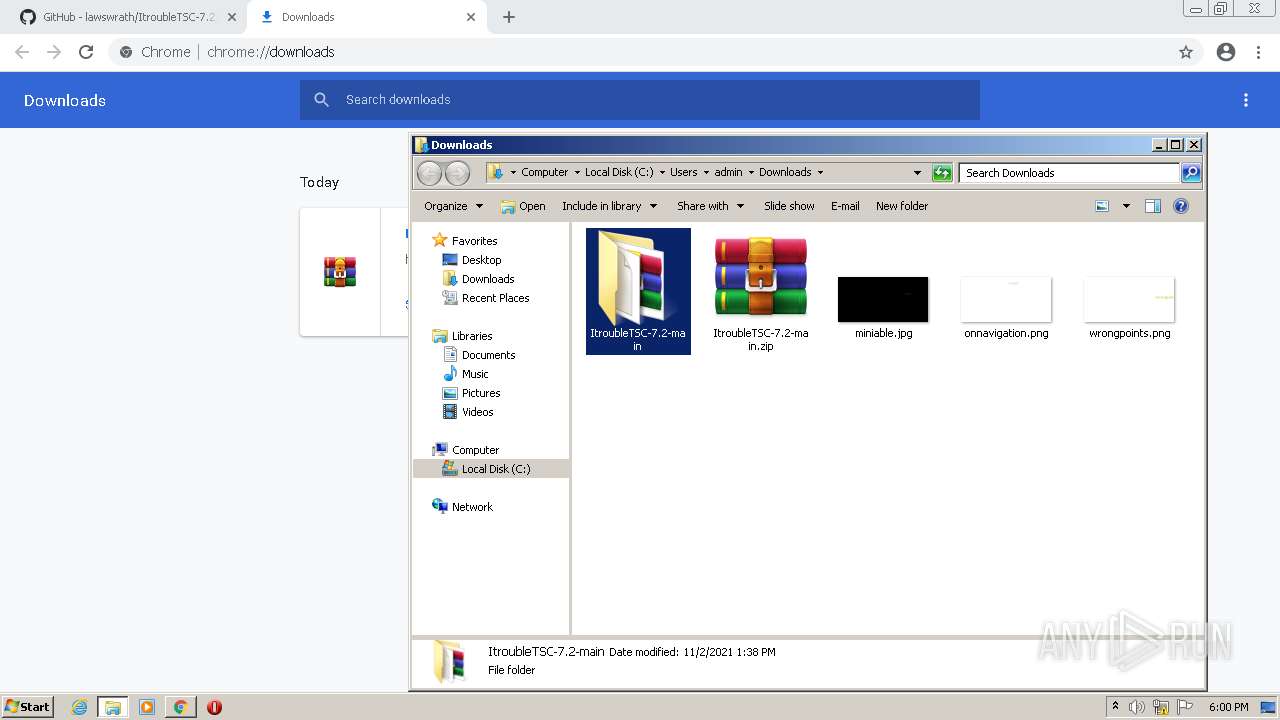
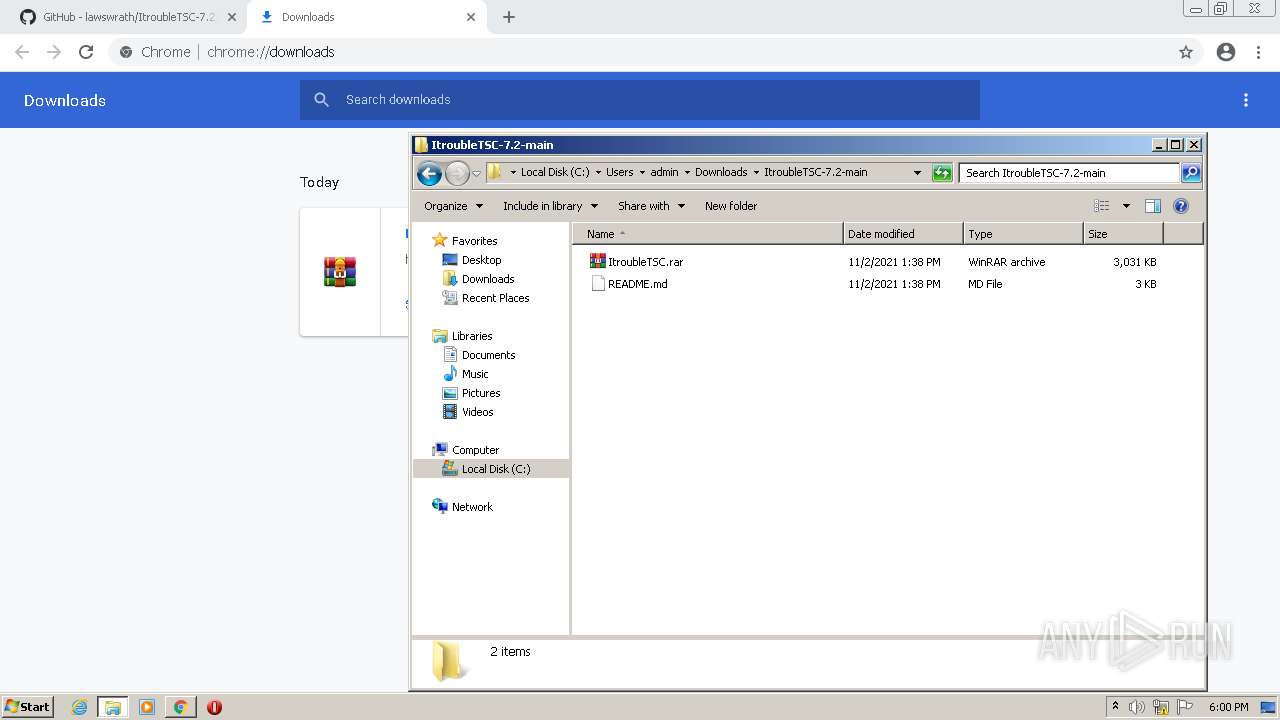
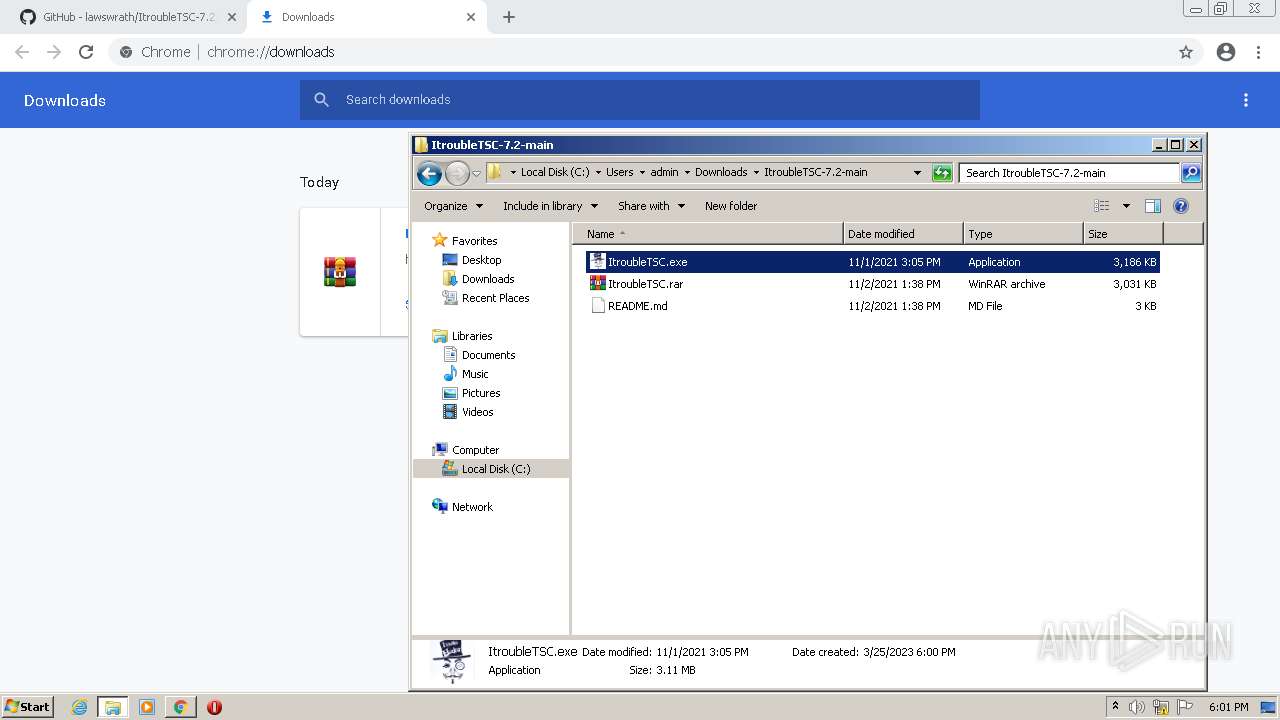
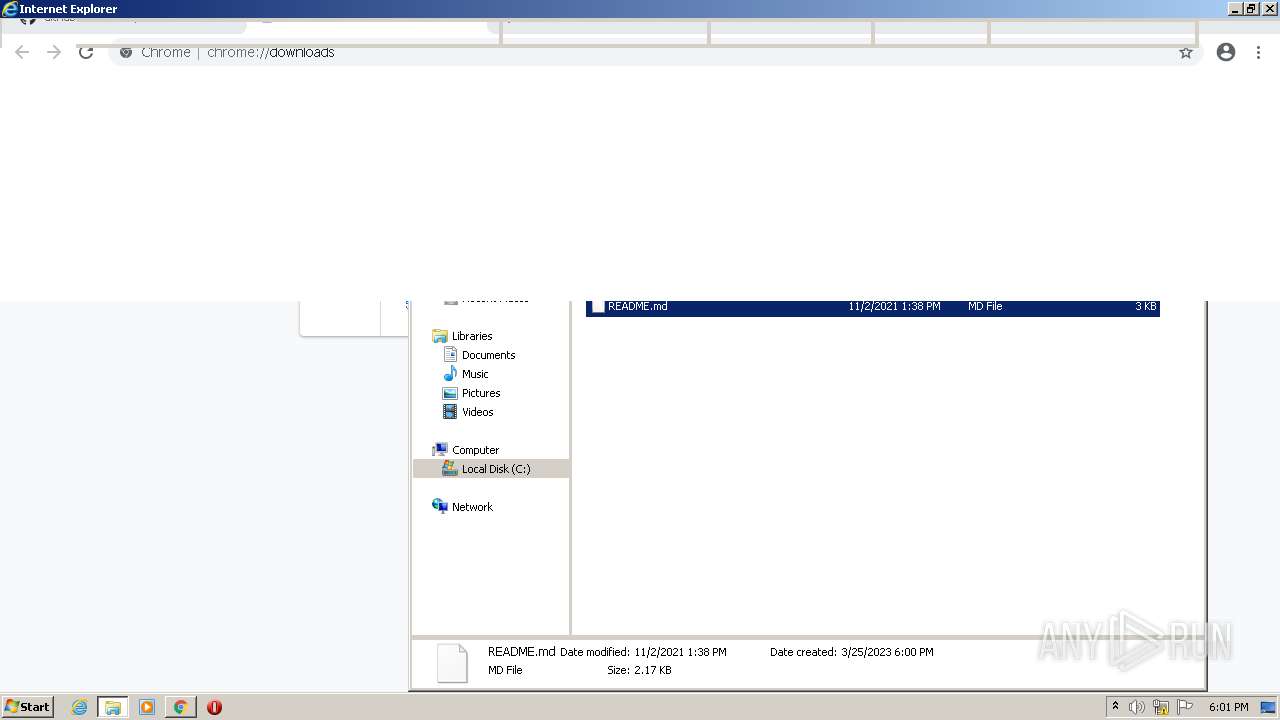
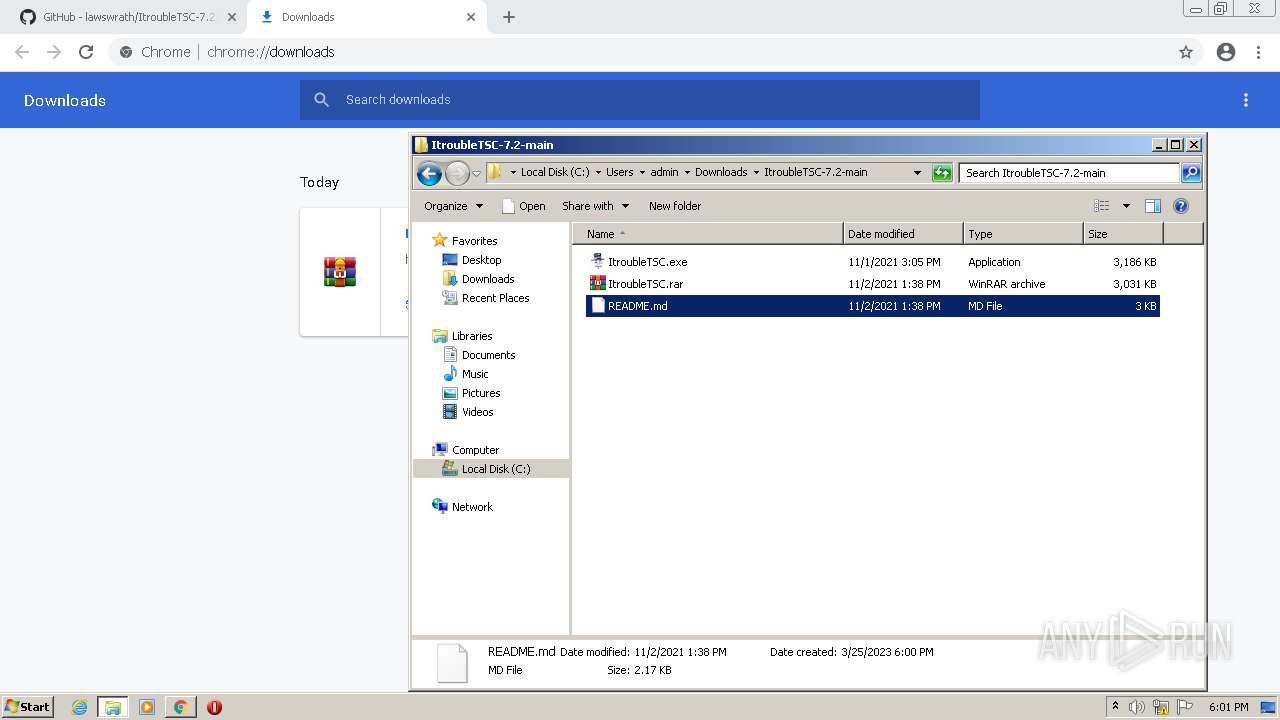
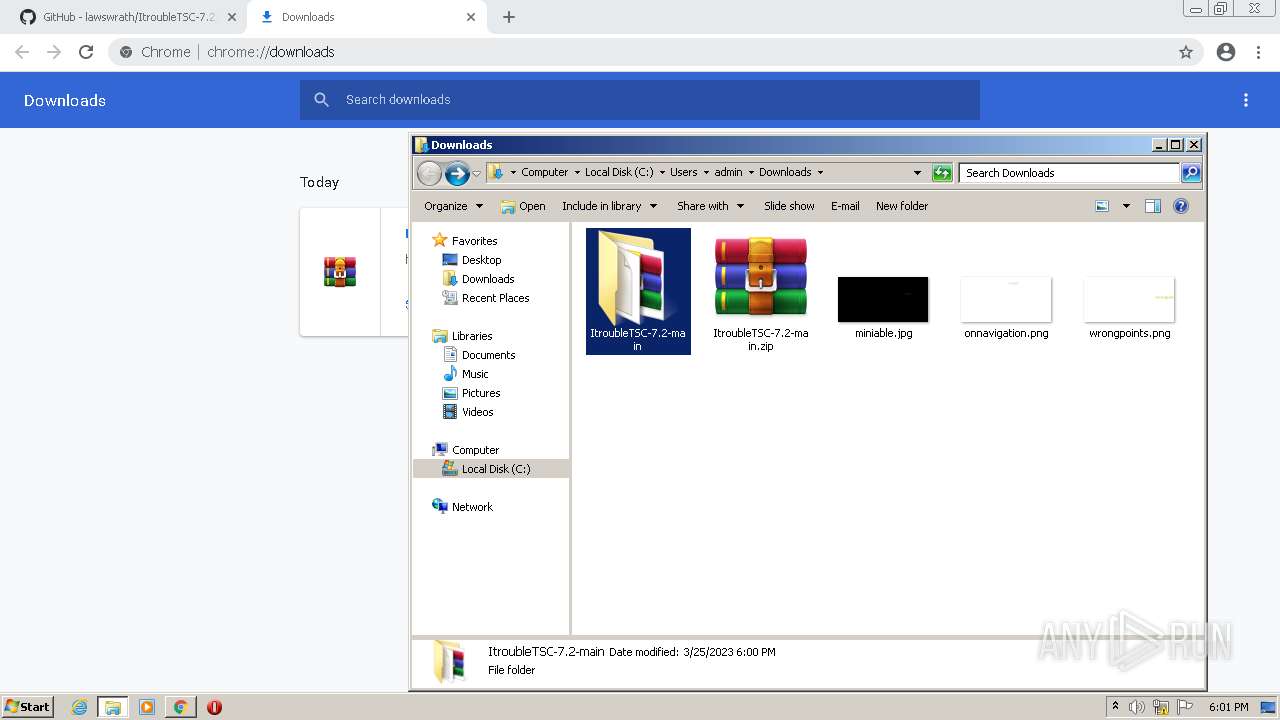
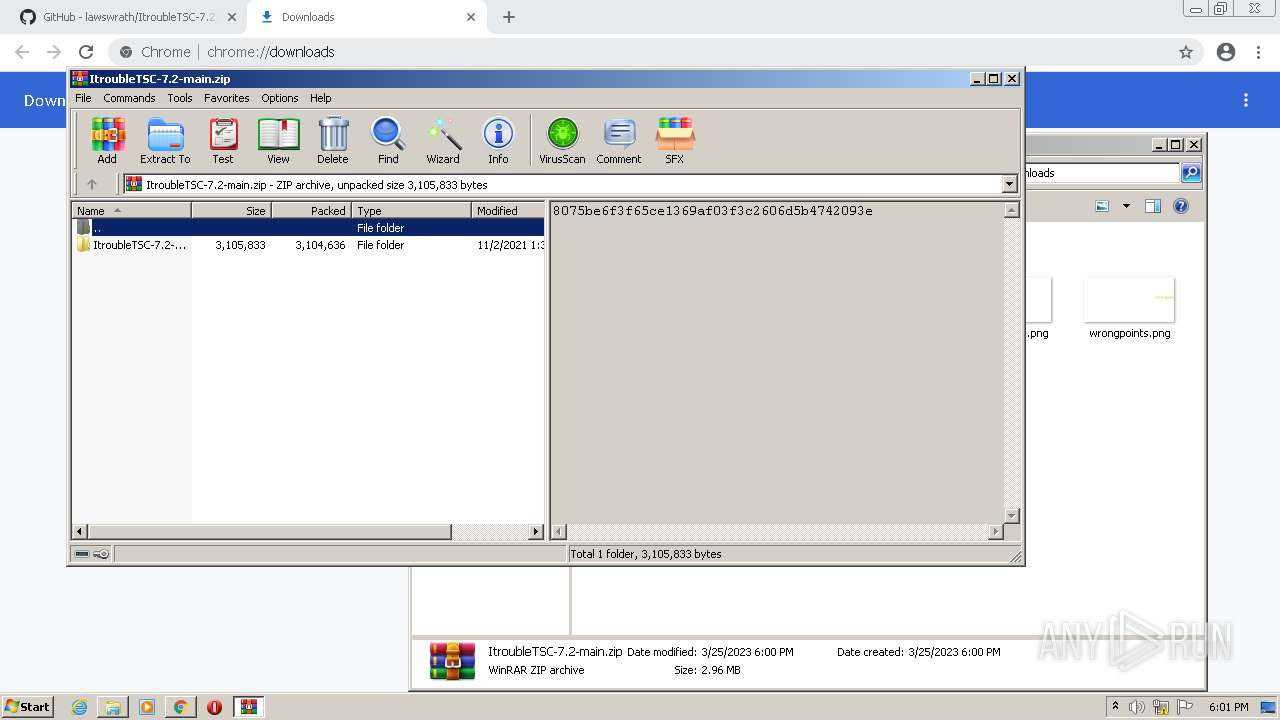
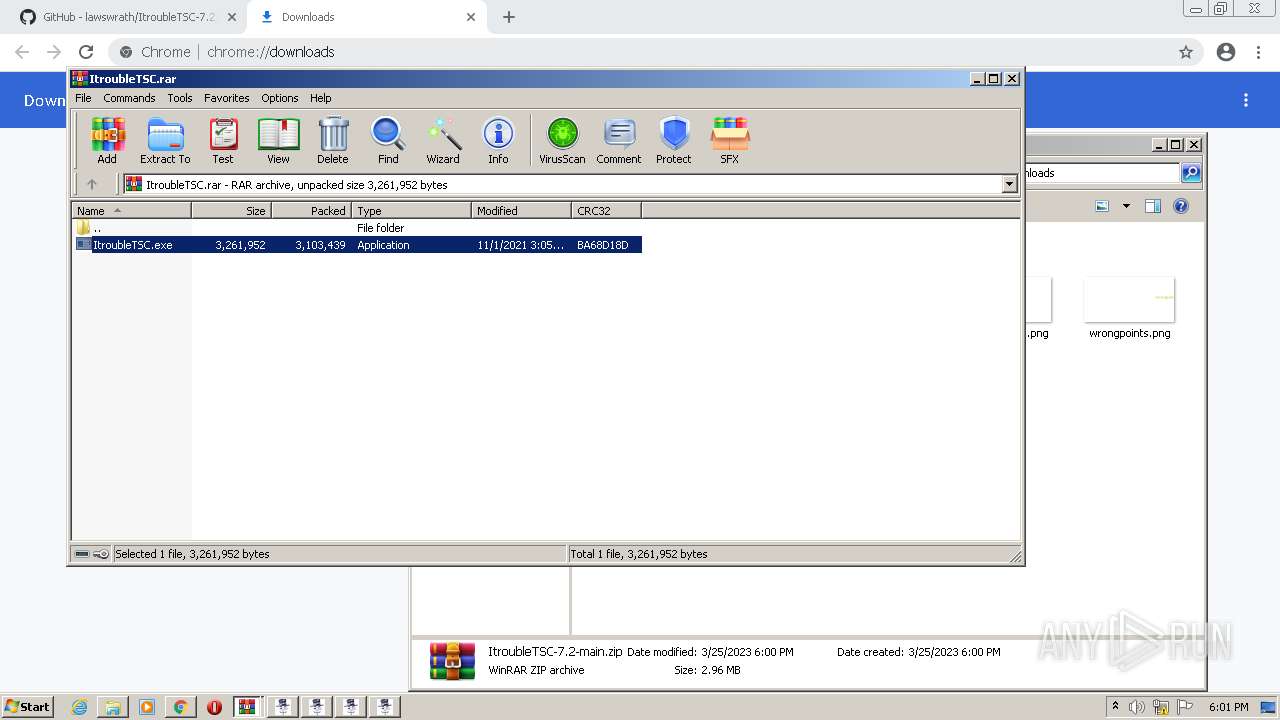
The process uses the downloaded file
- chrome.exe (PID: 2864)
- WinRAR.exe (PID: 2220)
- WinRAR.exe (PID: 1836)
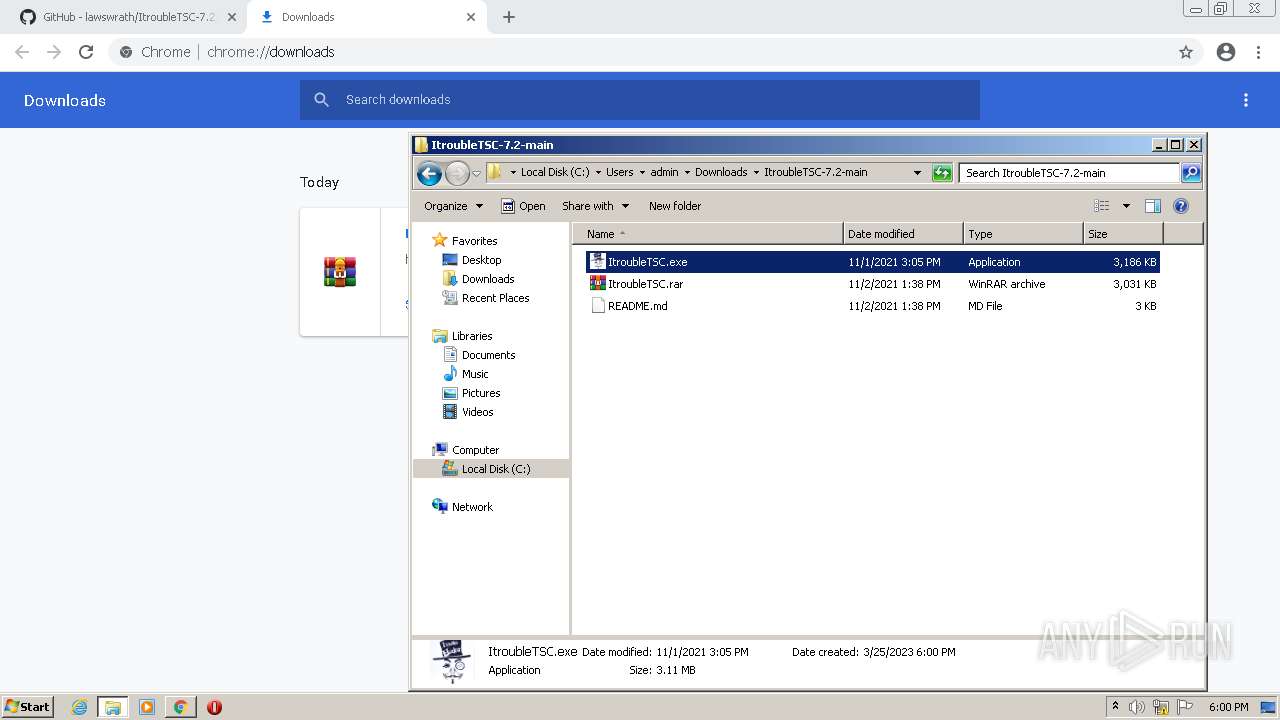
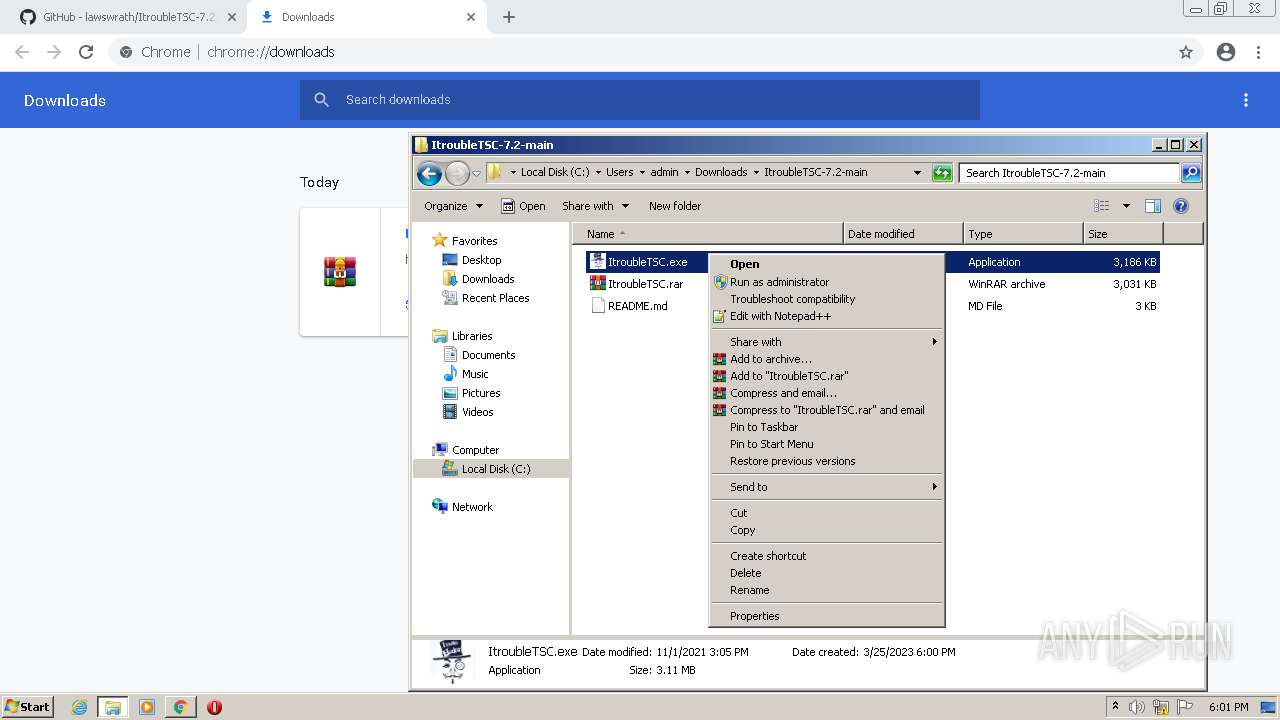
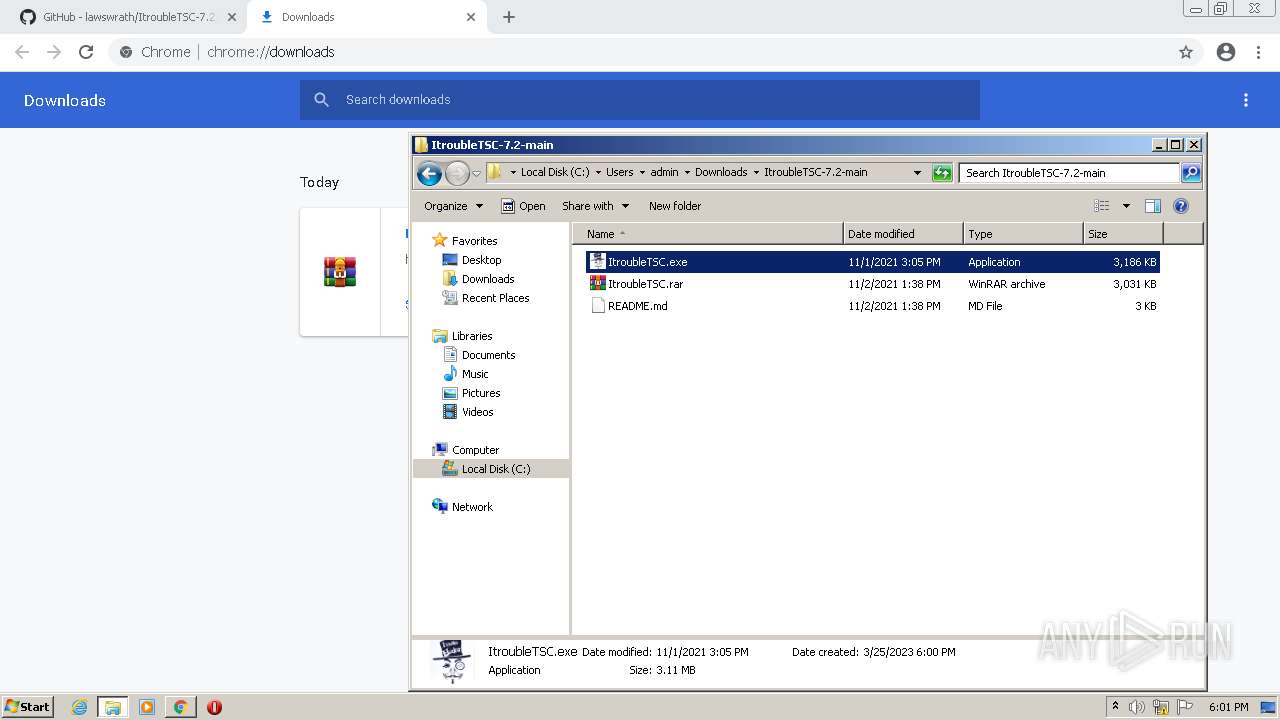
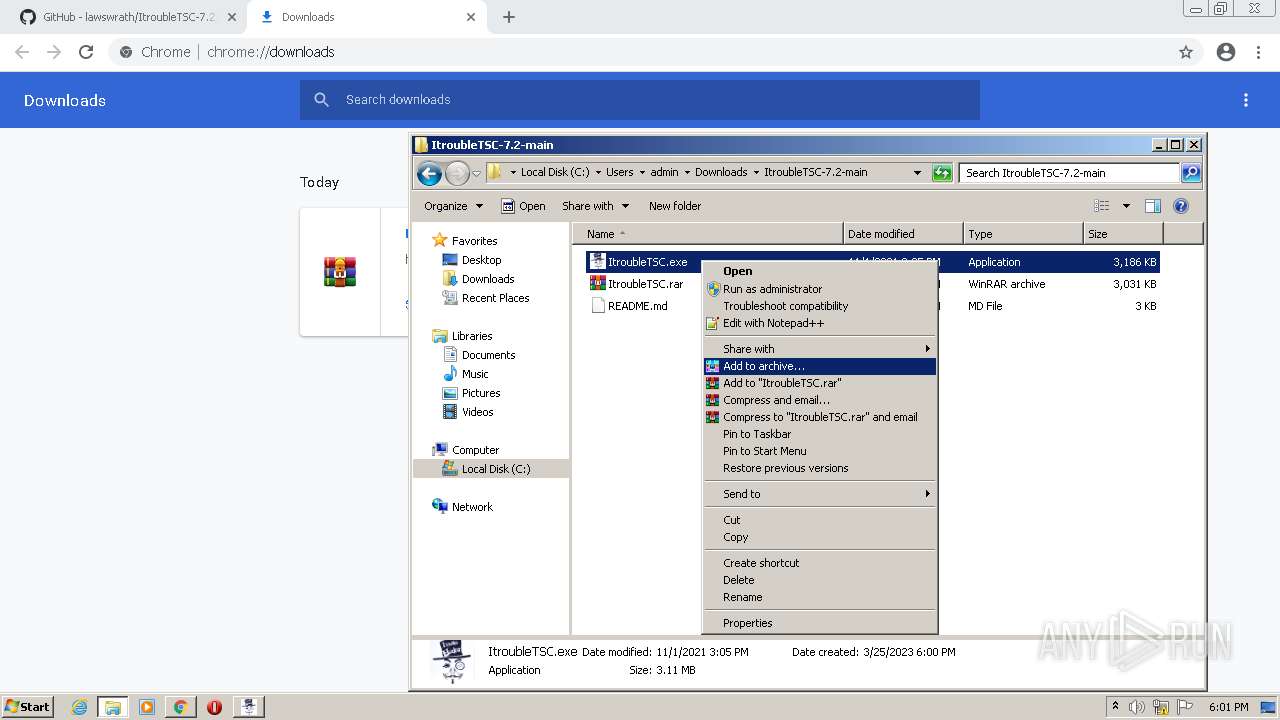
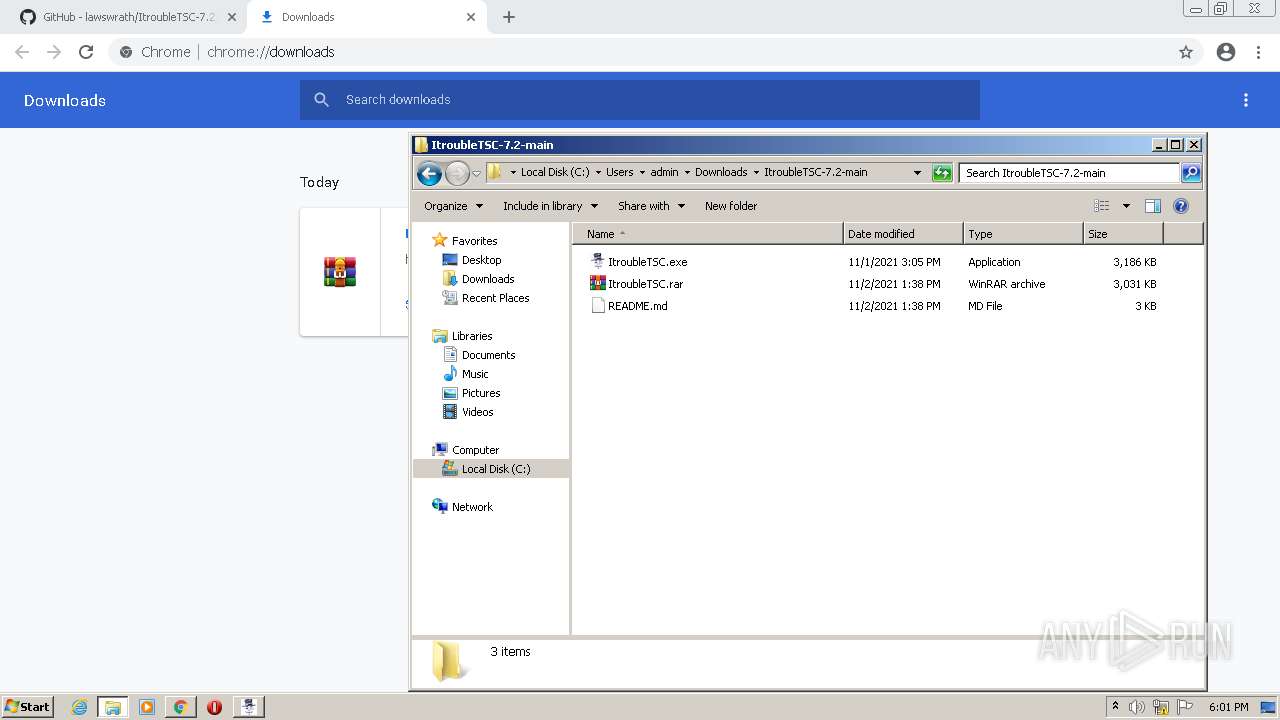
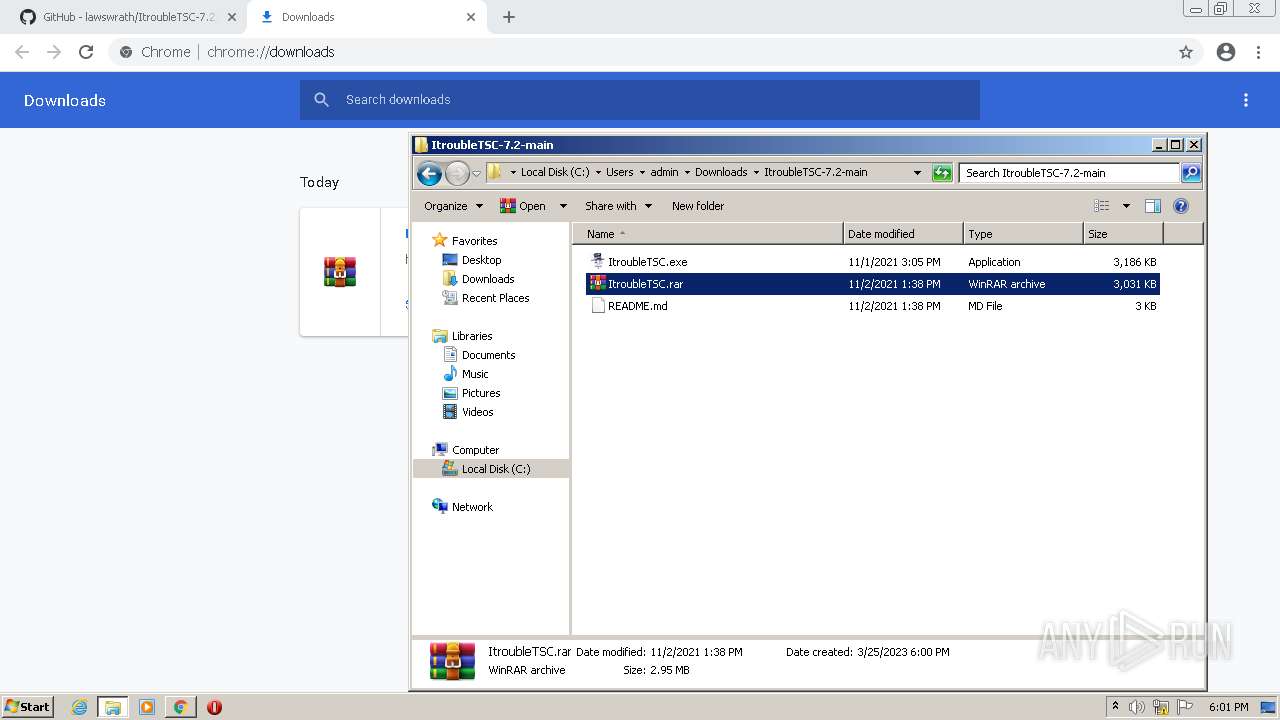
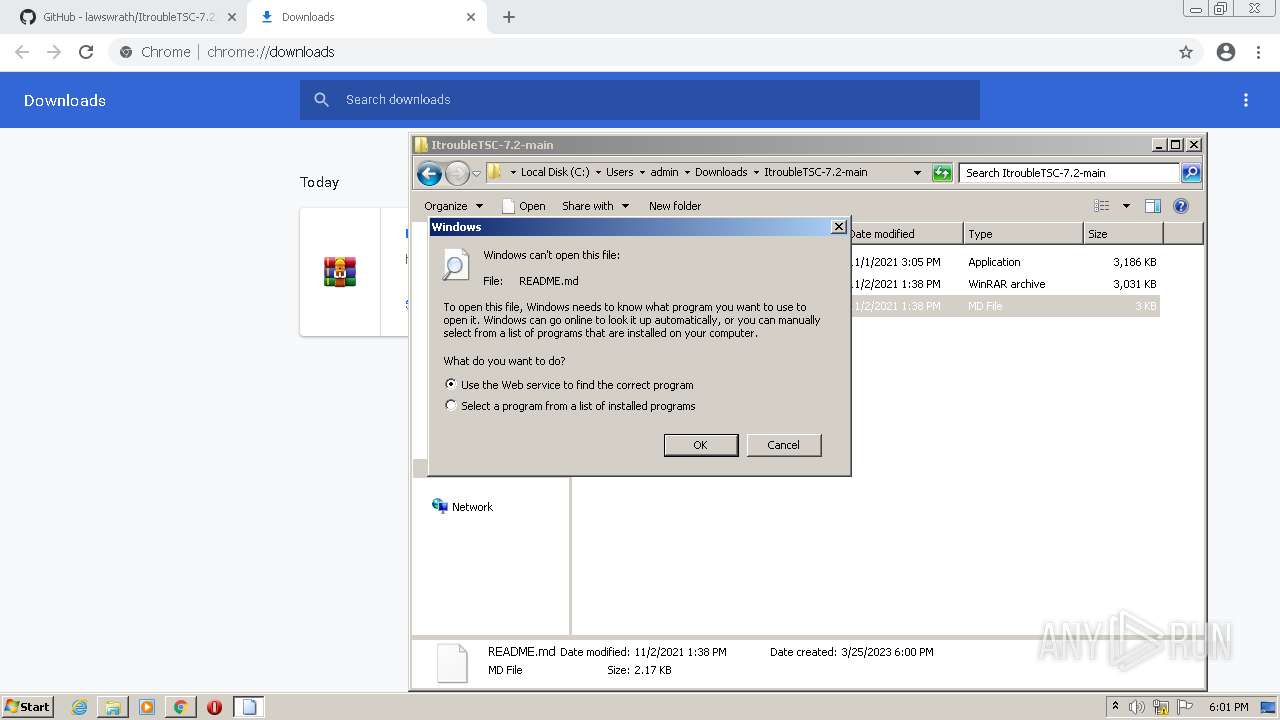
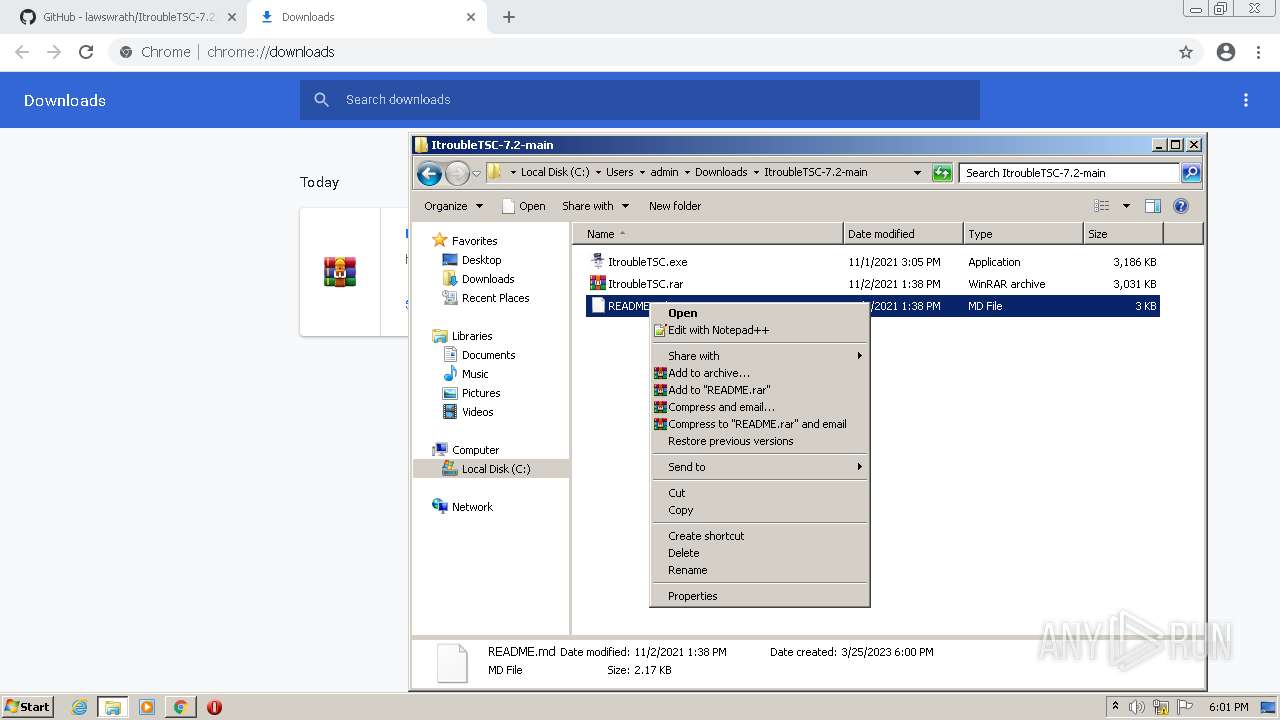
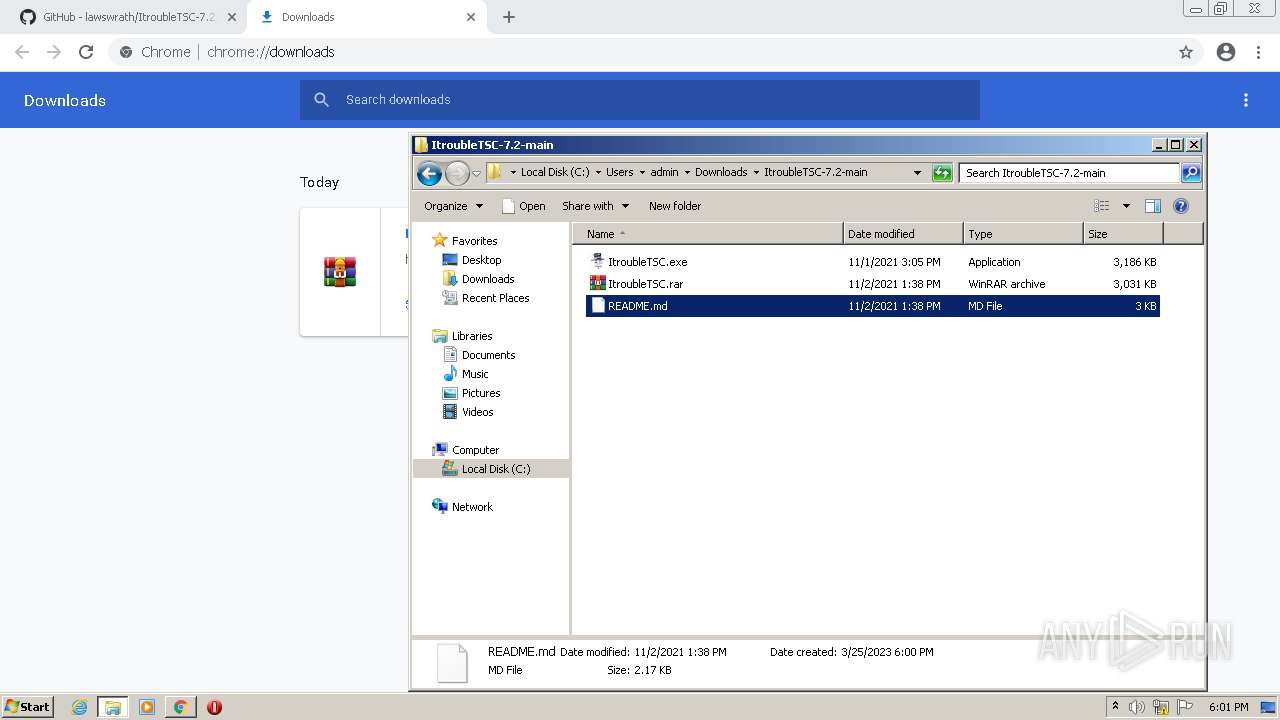
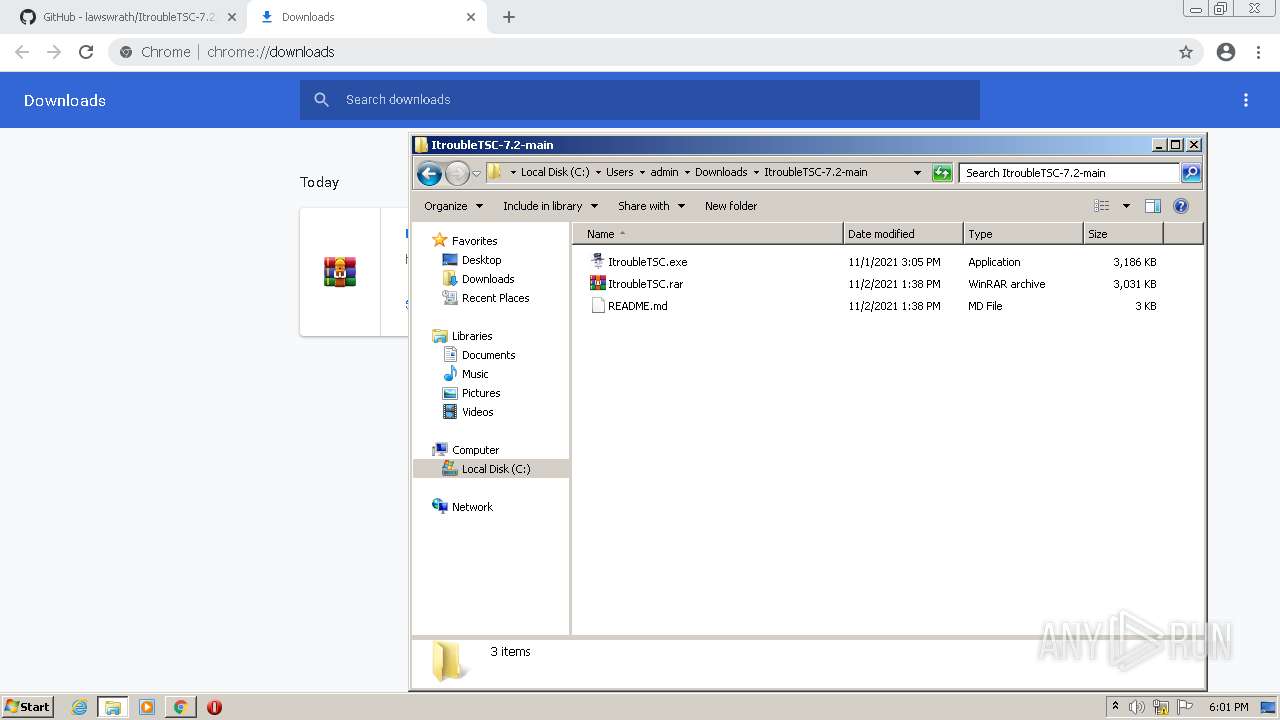
Manual execution by a user
- WinRAR.exe (PID: 2220)
- WinRAR.exe (PID: 1964)
- ItroubleTSC.exe (PID: 3516)
- ItroubleTSC.exe (PID: 3064)
- WinRAR.exe (PID: 4064)
- rundll32.exe (PID: 2924)
- notepad++.exe (PID: 2748)
- WinRAR.exe (PID: 1836)
Create files in a temporary directory
- chrome.exe (PID: 2572)
- ItroubleTSC.exe (PID: 3516)
- RtkBtManServ.exe (PID: 1816)
- snuvcdsm.exe (PID: 2660)
- ItroubleTSC.exe (PID: 3064)
- winhlp32.exe (PID: 2640)
- hh.exe (PID: 2716)
- splwow64.exe (PID: 976)
- ItroubleTSC.exe (PID: 3792)
- ItroubleTSC.exe (PID: 2564)
- ItroubleTSC.exe (PID: 1888)
- iexplore.exe (PID: 4036)
- ItroubleTSC.exe (PID: 3788)
- ItroubleTSC.exe (PID: 2656)
- ItroubleTSC.exe (PID: 1476)
- ItroubleTSC.exe (PID: 3576)
- ItroubleTSC.exe (PID: 3676)
Reads the computer name
- ItroubleTSC.exe (PID: 3516)
- RtkBtManServ.exe (PID: 1816)
- bfsvc.exe (PID: 2568)
- ItroubleTSC.exe (PID: 3064)
- snuvcdsm.exe (PID: 2660)
- winhlp32.exe (PID: 2640)
- ItroubleTSC.exe (PID: 3792)
- ItroubleTSC.exe (PID: 2564)
- ItroubleTSC.exe (PID: 1888)
- ItroubleTSC.exe (PID: 3788)
- ItroubleTSC.exe (PID: 2656)
- ItroubleTSC.exe (PID: 1476)
- ItroubleTSC.exe (PID: 3576)
- ItroubleTSC.exe (PID: 3676)
Reads the machine GUID from the registry
- ItroubleTSC.exe (PID: 3516)
- RtkBtManServ.exe (PID: 1816)
- ItroubleTSC.exe (PID: 3064)
- snuvcdsm.exe (PID: 2660)
- ItroubleTSC.exe (PID: 3792)
- ItroubleTSC.exe (PID: 2564)
- ItroubleTSC.exe (PID: 1888)
- ItroubleTSC.exe (PID: 3788)
- ItroubleTSC.exe (PID: 2656)
- ItroubleTSC.exe (PID: 1476)
- ItroubleTSC.exe (PID: 3576)
- ItroubleTSC.exe (PID: 3676)
Checks supported languages
- ItroubleTSC.exe (PID: 3516)
- RtkBtManServ.exe (PID: 1816)
- bfsvc.exe (PID: 2568)
- snuvcdsm.exe (PID: 2660)
- ItroubleTSC.exe (PID: 3064)
- winhlp32.exe (PID: 2640)
- splwow64.exe (PID: 976)
- hh.exe (PID: 2716)
- ItroubleTSC.exe (PID: 3792)
- ItroubleTSC.exe (PID: 2564)
- ItroubleTSC.exe (PID: 1888)
- ItroubleTSC.exe (PID: 3788)
- ItroubleTSC.exe (PID: 2656)
- ItroubleTSC.exe (PID: 3576)
- ItroubleTSC.exe (PID: 3676)
- ItroubleTSC.exe (PID: 1476)
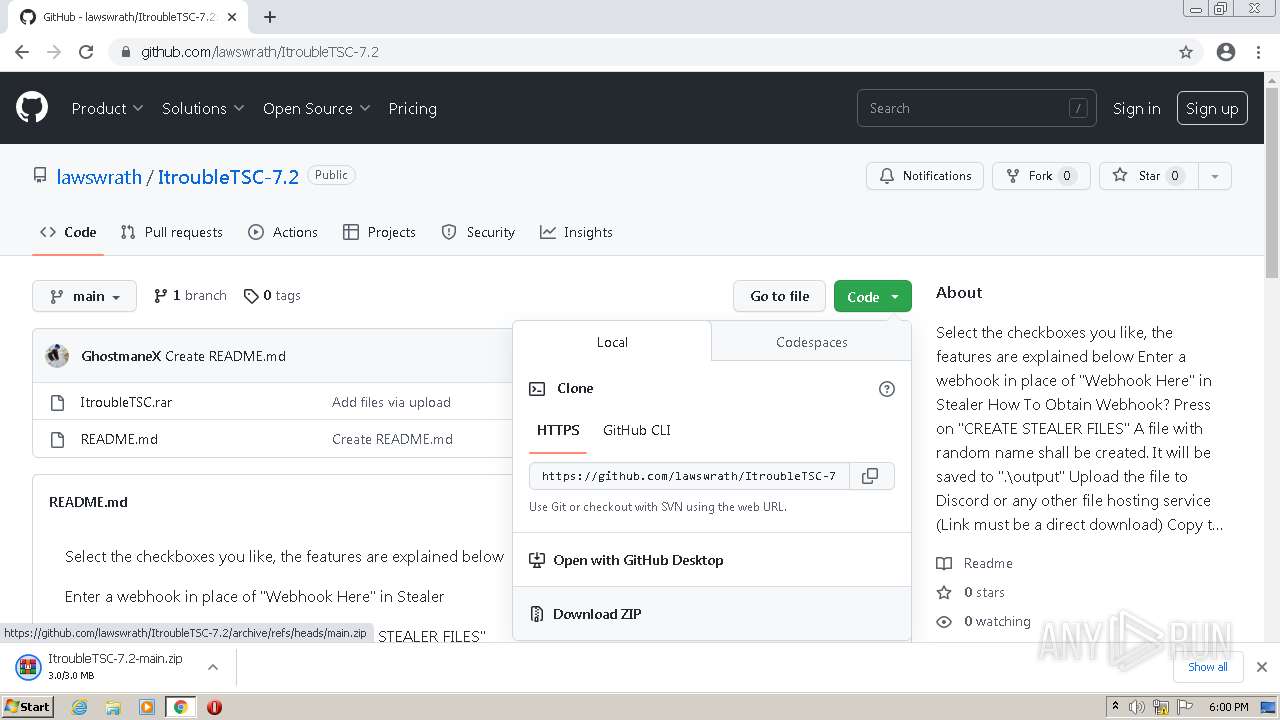
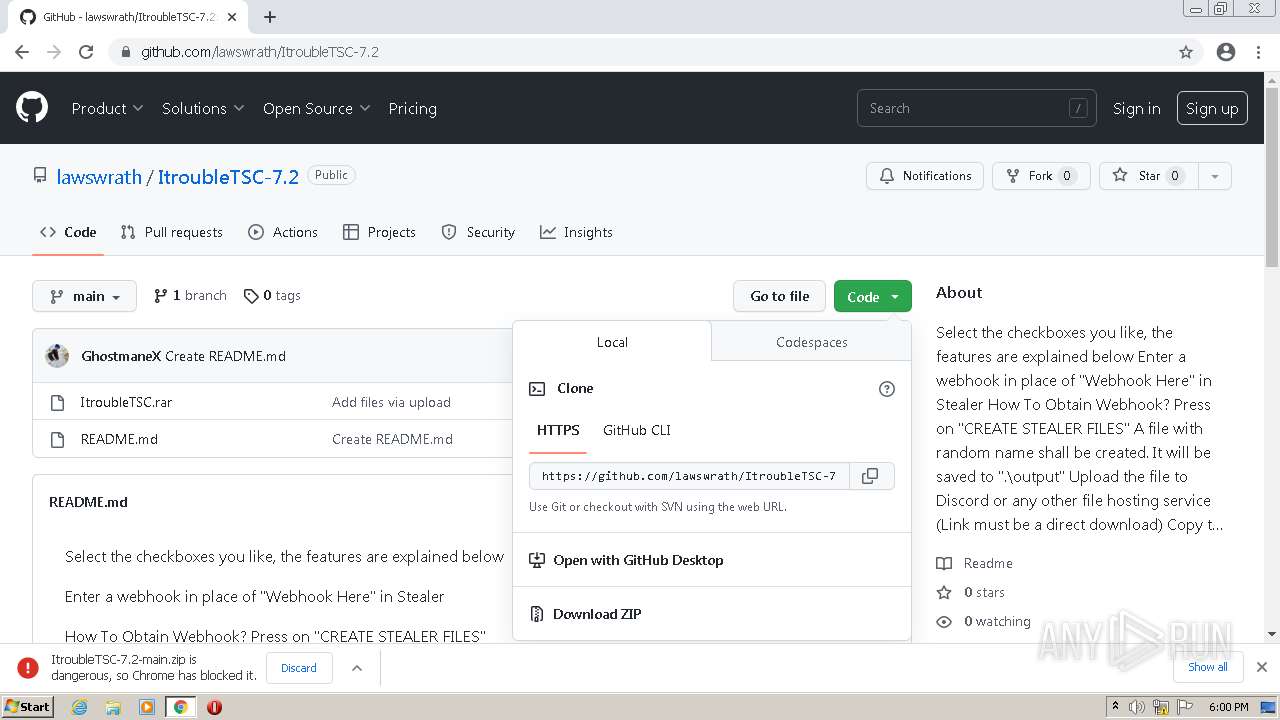
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1964)
- WinRAR.exe (PID: 4064)
- WinRAR.exe (PID: 2096)
The process checks LSA protection
- ItroubleTSC.exe (PID: 3516)
- RtkBtManServ.exe (PID: 1816)
- snuvcdsm.exe (PID: 2660)
- ItroubleTSC.exe (PID: 3064)
- ItroubleTSC.exe (PID: 3792)
- ItroubleTSC.exe (PID: 2564)
- ItroubleTSC.exe (PID: 1888)
- notepad++.exe (PID: 2748)
- ItroubleTSC.exe (PID: 3788)
- ItroubleTSC.exe (PID: 2656)
- ItroubleTSC.exe (PID: 1476)
- ItroubleTSC.exe (PID: 3576)
- ItroubleTSC.exe (PID: 3676)
Creates files or folders in the user directory
- ItroubleTSC.exe (PID: 3516)
- splwow64.exe (PID: 976)
Reads Environment values
- RtkBtManServ.exe (PID: 1816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
209
Monitored processes
144
Malicious processes
17
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\compile.vbs" | C:\Windows\System32\wscript.exe | — | RtkBtManServ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | |||||||||||||||
| 660 | "shutdown" /r /s /t 0 | C:\Windows\System32\shutdown.exe | — | RtkBtManServ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 908 | "C:\Windows\System32\cmd.exe" /c compile.bat | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 976 | C:\Users\admin\AppData\Local\Temp\splwow64.exe /stext "C:\Users\admin\AppData\Local\Temp\Cookies2" | C:\Users\admin\AppData\Local\Temp\splwow64.exe | cmd.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: MZCookiesView Exit code: 0 Version: 1.58 Modules
| |||||||||||||||
| 1012 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\dav.bat" | C:\Windows\System32\cmd.exe | ItroubleTSC.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,11499286655542809225,314333781924258102,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3284 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | |||||||||||||||
| 1108 | reg delete "HKLM\Software\Policies\Microsoft\Windows Defender" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 1180 | reg add "HKLM\System\CurrentControlSet\Services\WinDefend" /v "Start" /t REG_DWORD /d "4" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,11499286655542809225,314333781924258102,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1276 | "C:\Windows\System32\cmd.exe" /c compile.bat | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
Total events
69 456
Read events
68 794
Write events
644
Delete events
18
Modification events
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
50
Suspicious files
196
Text files
376
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-641F36A5-A0C.pma | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e3f1ed16-9a67-4138-aceb-df238e582a18.tmp | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF24fc62.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF24fa7d.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f253ebb5-45ae-4060-bb73-50dea225510b.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
51
DNS requests
29
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.88 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 11.5 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 30.4 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 10.7 Kb | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | binary | 51.1 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 25.5 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 51.1 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 674 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 5.75 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3344 | chrome.exe | 142.250.186.142:443 | clients2.google.com | GOOGLE | US | whitelisted |
3344 | chrome.exe | 142.250.74.205:443 | accounts.google.com | GOOGLE | US | whitelisted |
3344 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | malicious |
3344 | chrome.exe | 172.217.18.97:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
3344 | chrome.exe | 185.199.110.154:443 | github.githubassets.com | FASTLY | US | suspicious |
3344 | chrome.exe | 185.199.108.133:443 | avatars.githubusercontent.com | FASTLY | US | malicious |
3344 | chrome.exe | 142.250.185.234:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
3344 | chrome.exe | 140.82.121.6:443 | api.github.com | GITHUB | US | suspicious |
3344 | chrome.exe | 216.58.212.131:443 | www.gstatic.com | GOOGLE | US | whitelisted |
3344 | chrome.exe | 142.250.185.163:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
— | — | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1816 | RtkBtManServ.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1816 | RtkBtManServ.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1816 | RtkBtManServ.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1816 | RtkBtManServ.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
— | — | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
— | — | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
— | — | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
— | — | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|