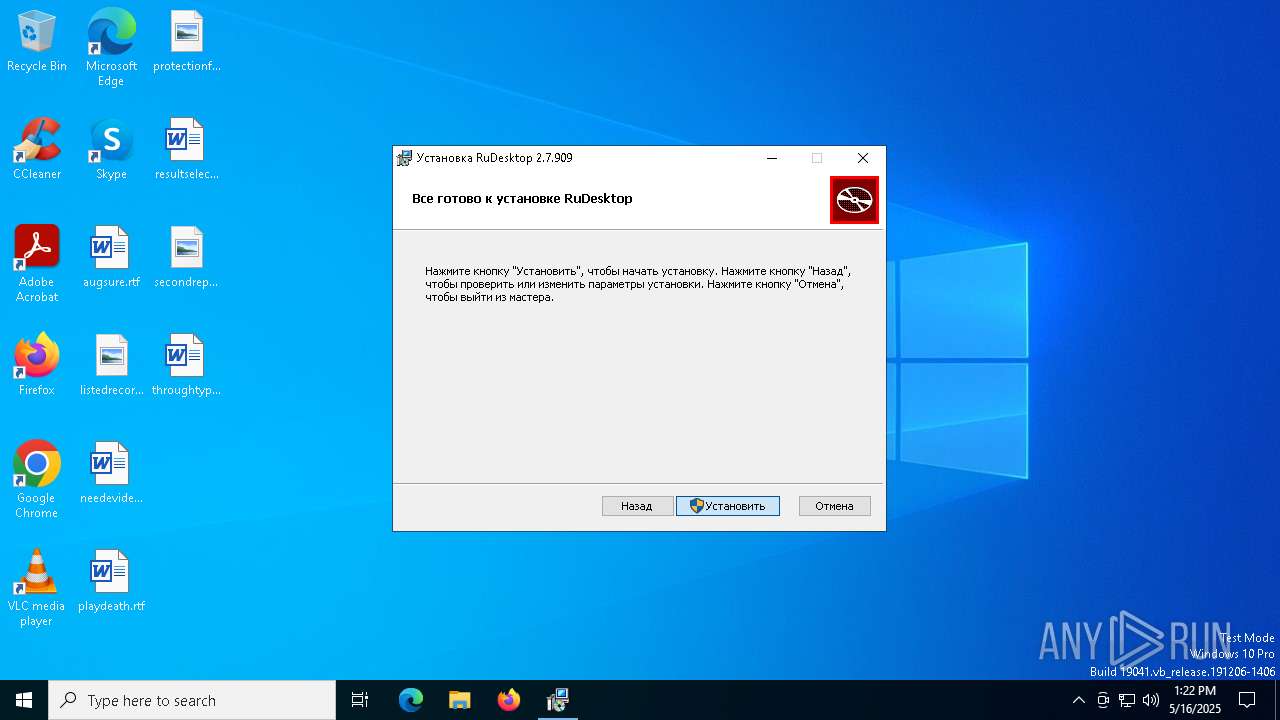
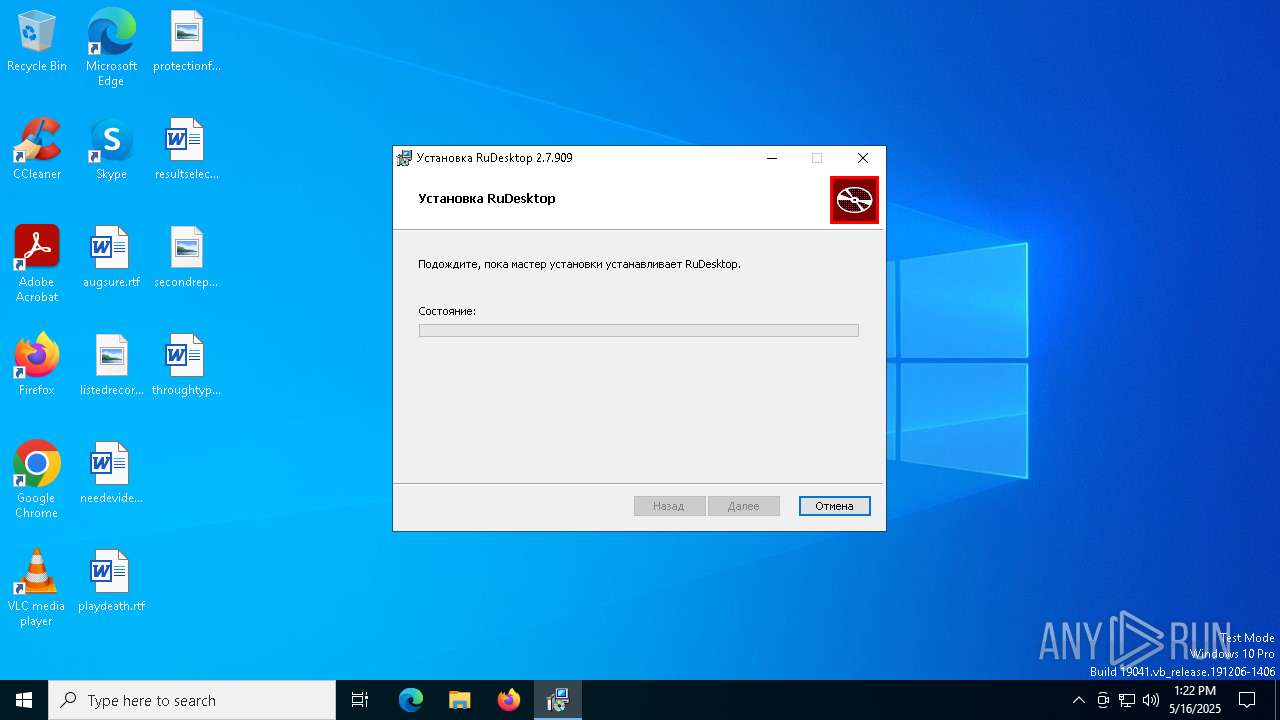
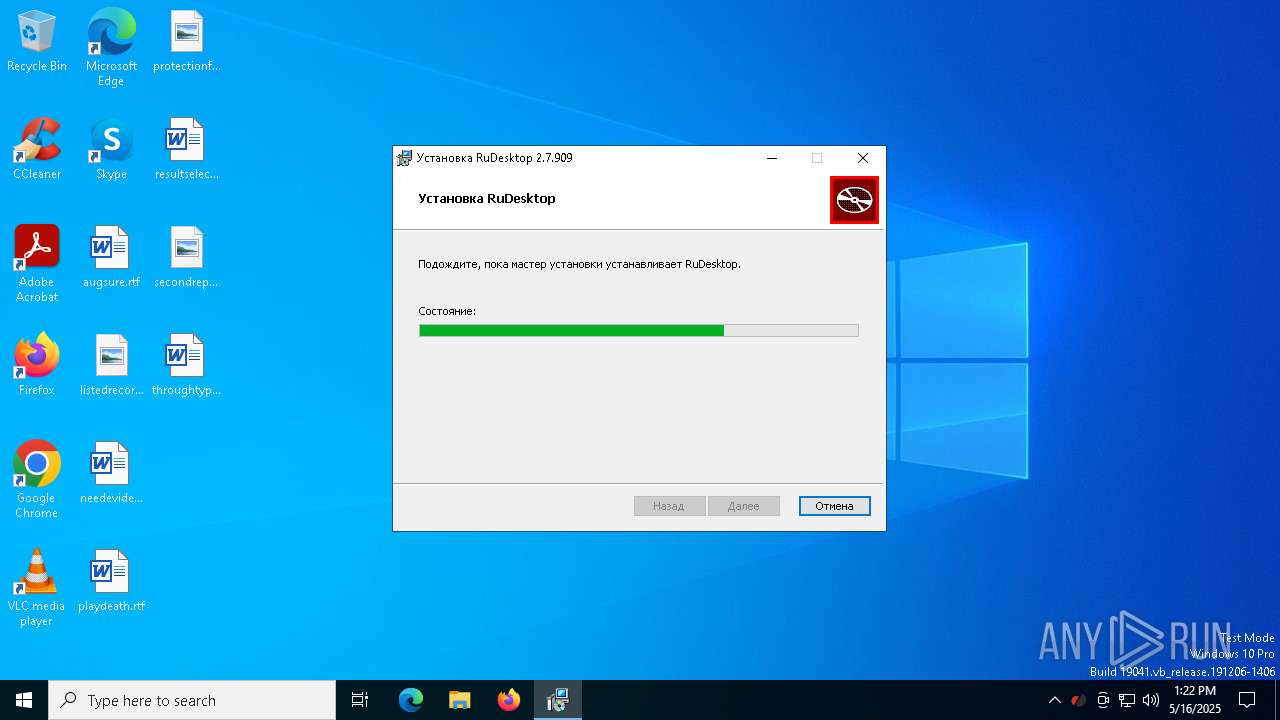
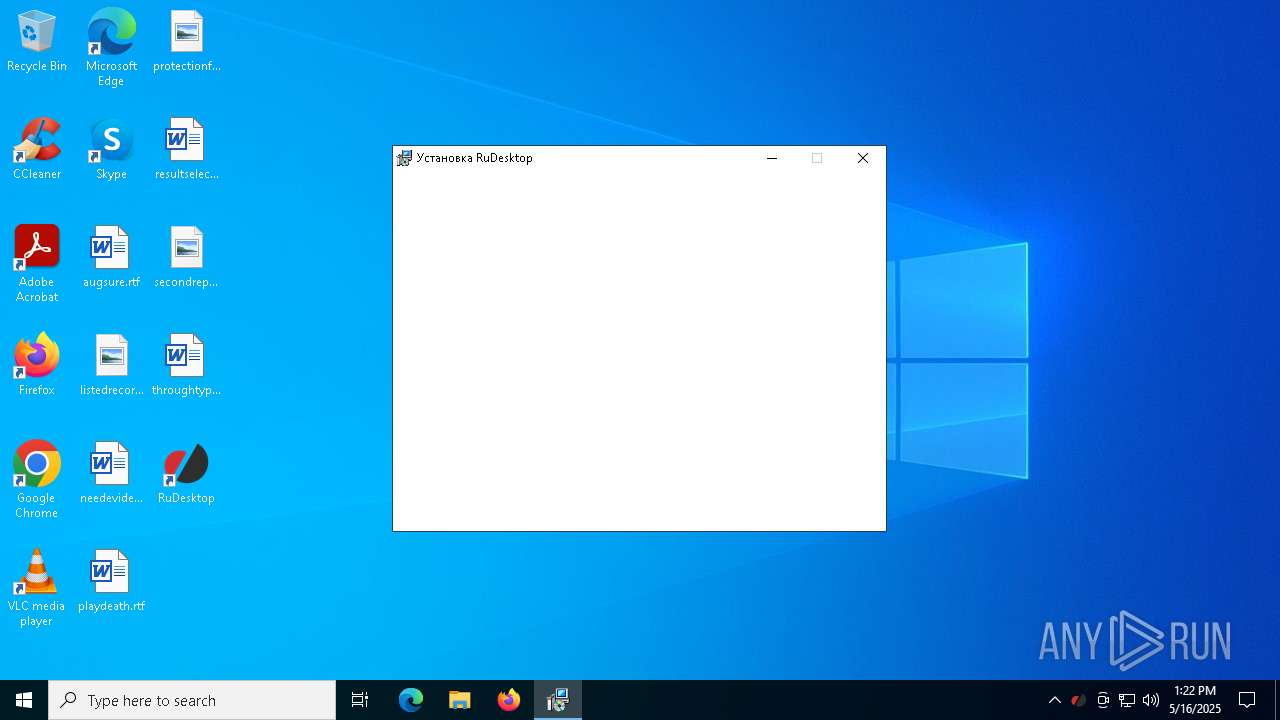
| File name: | rudesktop-x64.msi |
| Full analysis: | https://app.any.run/tasks/527dfdb7-3af3-4ffa-b139-2448f2a050bd |
| Verdict: | Malicious activity |
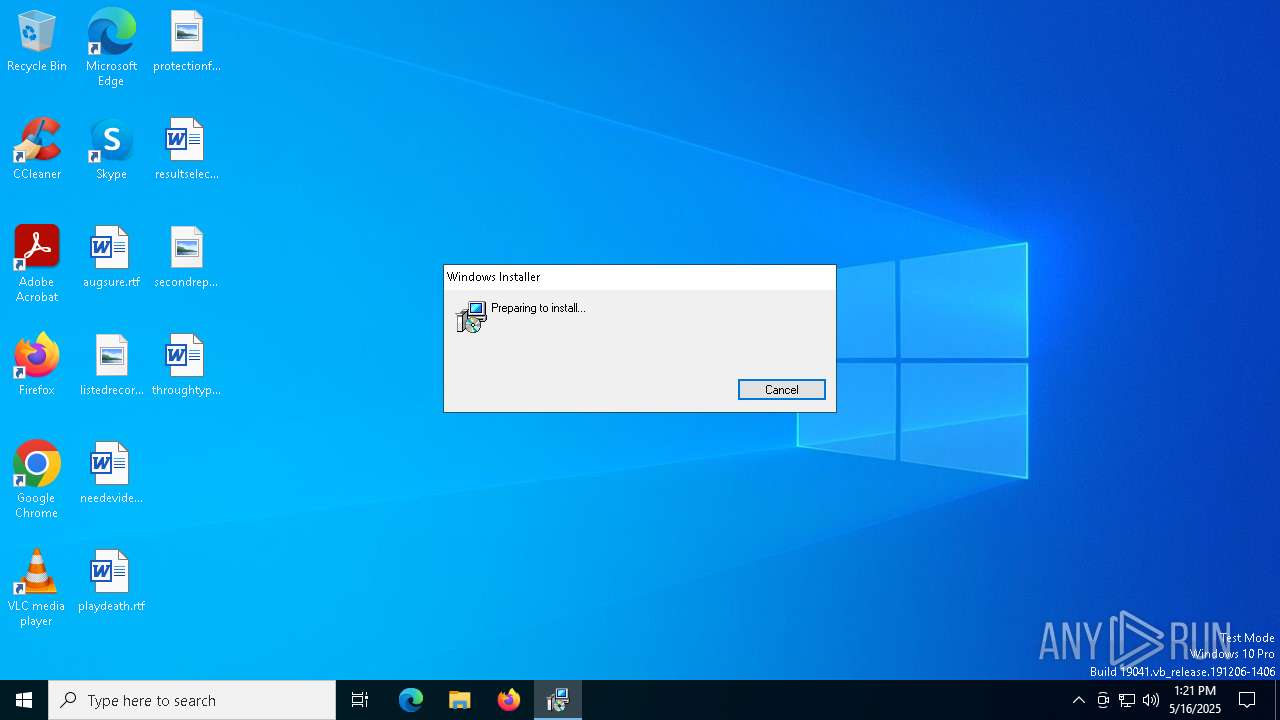
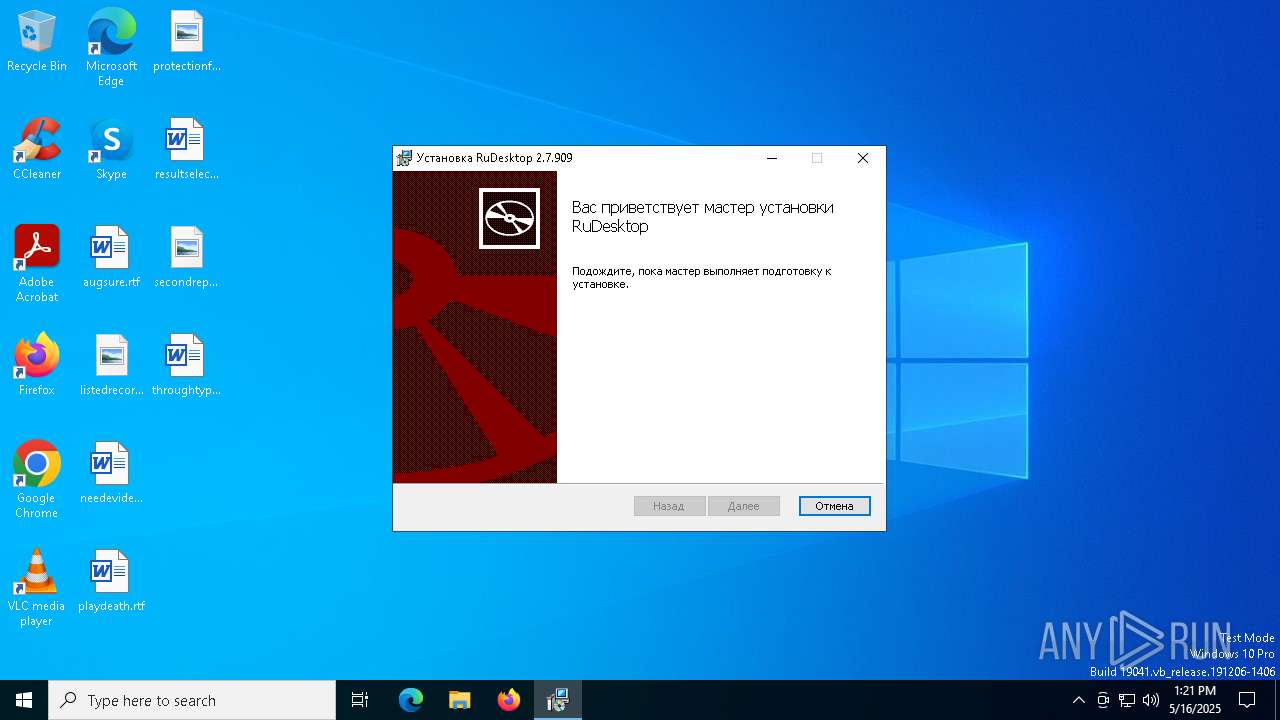
| Analysis date: | May 16, 2025, 13:21:28 |
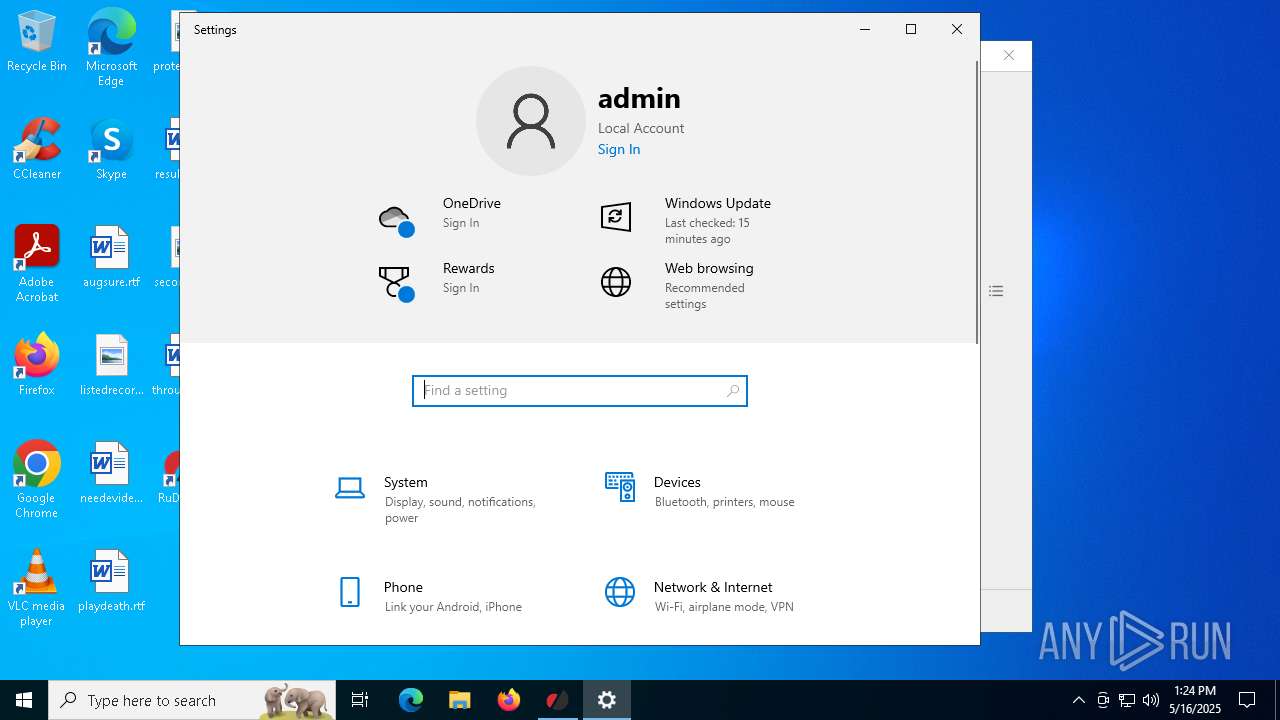
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
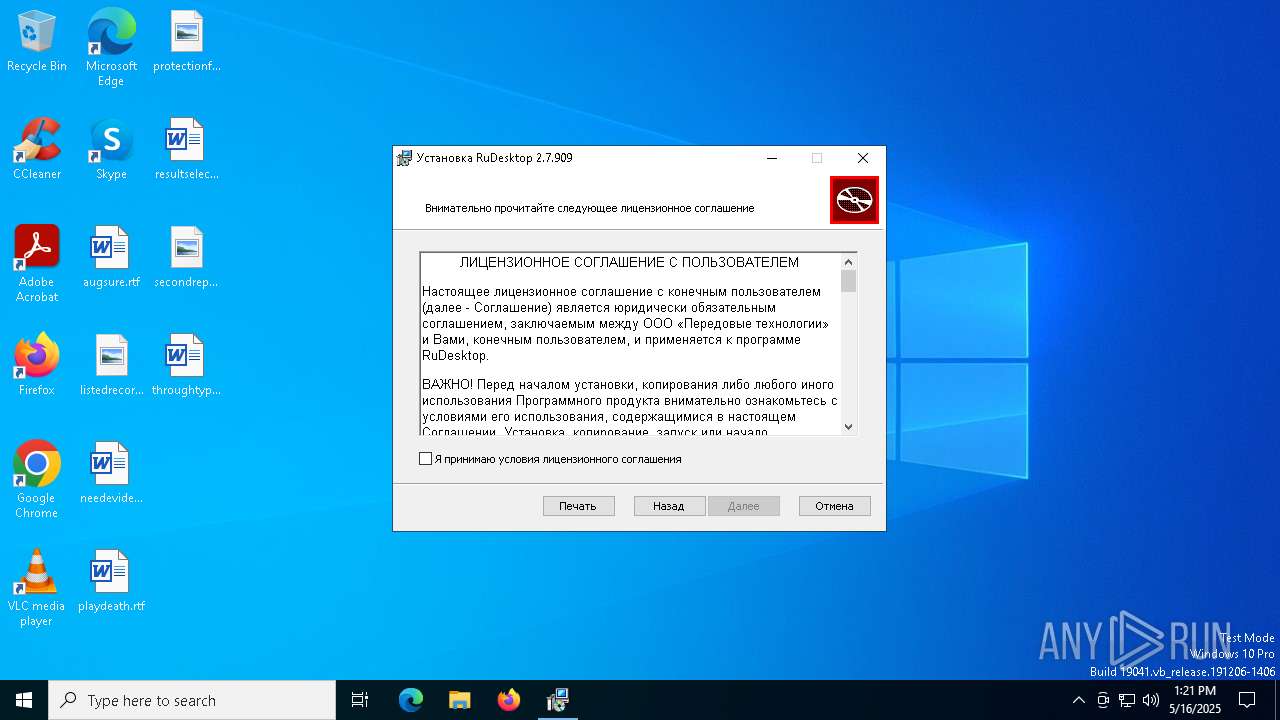
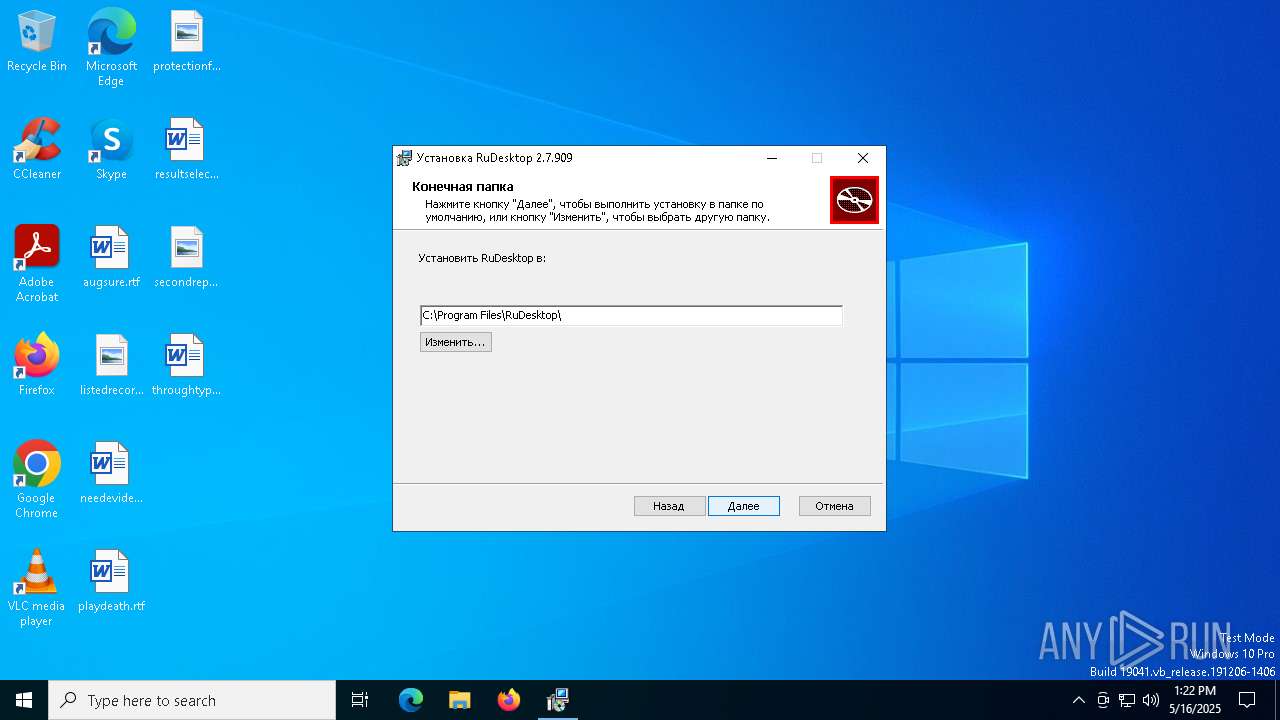
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1251, Title: Installation Database, Subject: Remote Control Software, Author: Advanced Technologies LLC, Keywords: Installer, Comments: This installer database contains the logic and data required to install RuDesktop., Template: x64;1033, Revision Number: {27A7FE62-C5AB-41CC-89F2-8EC293915B0B}, Create Time/Date: Tue Jan 28 07:10:26 2025, Last Saved Time/Date: Tue Jan 28 07:10:26 2025, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.0.8606), Security: 2 |
| MD5: | B5CB88C8C19BE5D8762ABFADB0C6DBD2 |
| SHA1: | 3F71CCFA9FBED8C4459591BCB22DCB0BF5050992 |
| SHA256: | C88B2134B6FD6E52CEA701069327AC40DFC871824158E7A7FF187674FC979F5B |
| SSDEEP: | 98304:JqRDbtXmWZvxY9iwsvY6liELXH+gsjd9XtWuW43aEhBGGr7djqJhCo3cICqywL4x:sfC1I34HglPK |
MALICIOUS
No malicious indicators.SUSPICIOUS
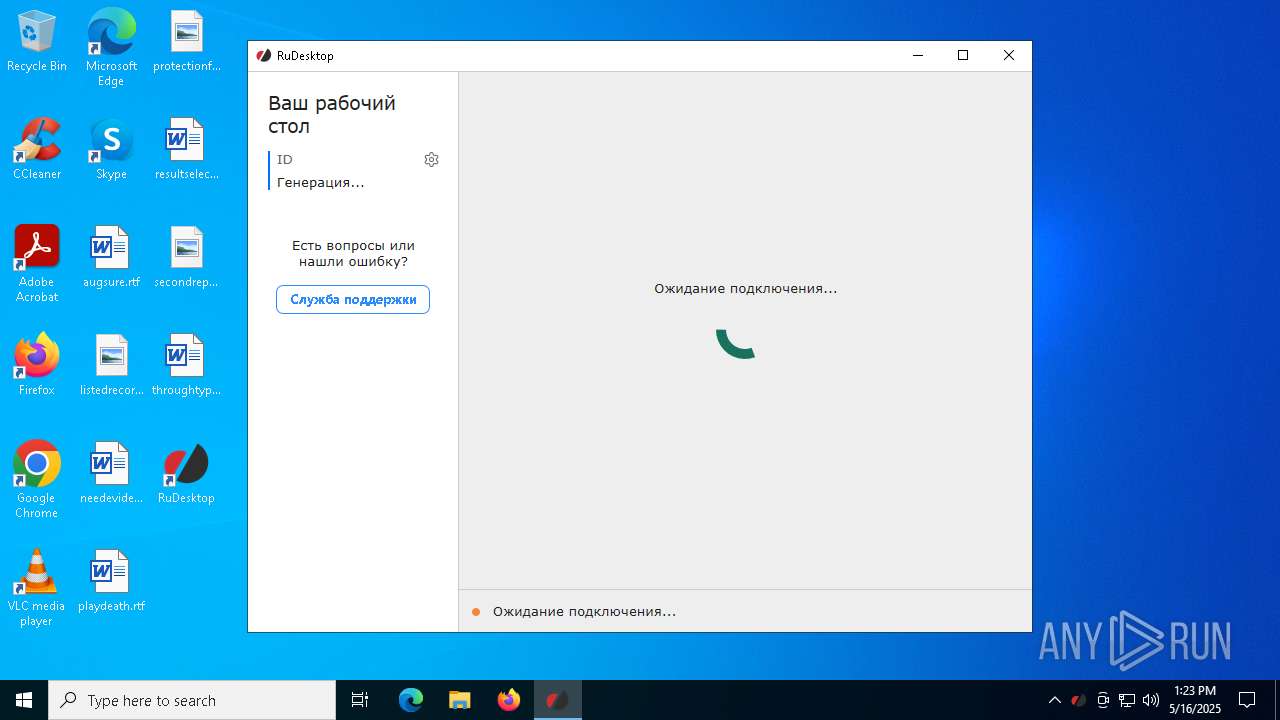
Application launched itself
- msiexec.exe (PID: 5968)
- rudesktop.exe (PID: 6828)
Executes as Windows Service
- VSSVC.exe (PID: 7864)
- rudesktop.exe (PID: 6828)
Starts CMD.EXE for commands execution
- rudesktop.exe (PID: 3888)
- rudesktop.exe (PID: 7416)
Executing commands from a ".bat" file
- rudesktop.exe (PID: 3888)
- rudesktop.exe (PID: 7416)
Starts SC.EXE for service management
- cmd.exe (PID: 4408)
- cmd.exe (PID: 7232)
Stops a currently running service
- sc.exe (PID: 6676)
Starts application with an unusual extension
- cmd.exe (PID: 7232)
- cmd.exe (PID: 4408)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4408)
- cmd.exe (PID: 7232)
Creates a new Windows service
- sc.exe (PID: 6740)
Windows service management via SC.EXE
- sc.exe (PID: 5984)
- sc.exe (PID: 684)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4408)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 4408)
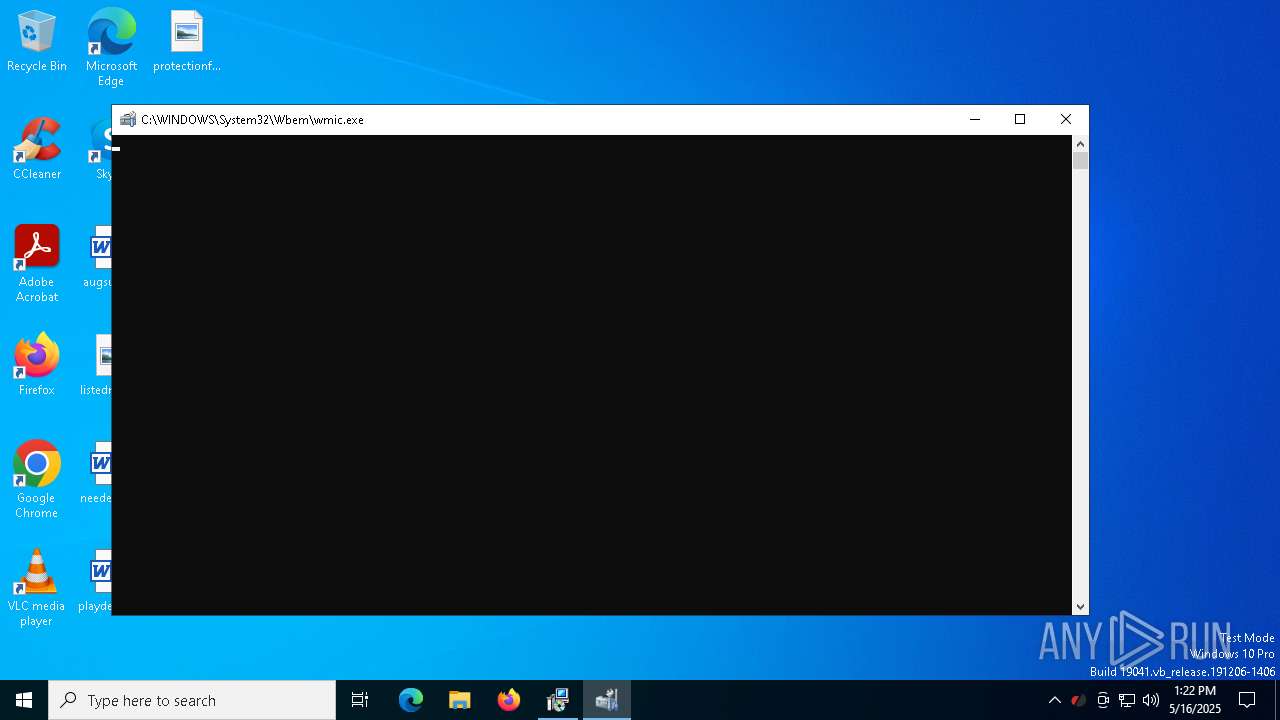
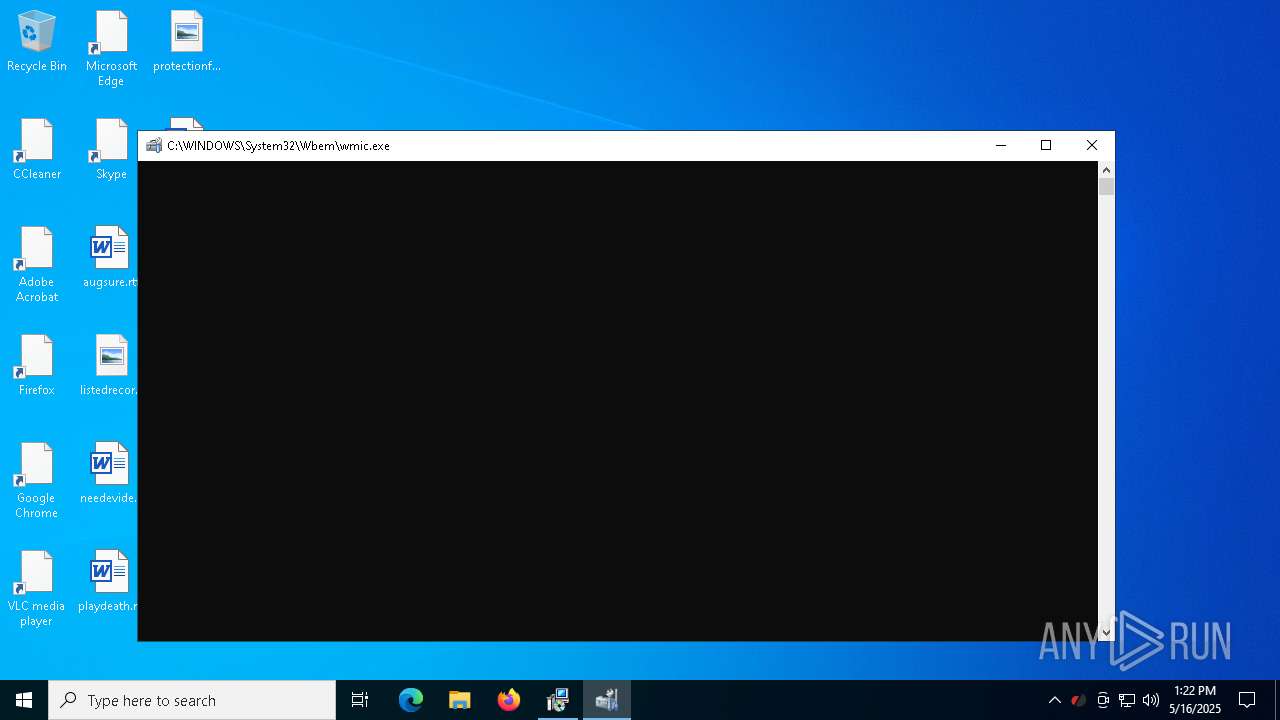
Uses WMIC.EXE to obtain operating system information
- rudesktop.exe (PID: 5352)
- rudesktop.exe (PID: 7792)
Uses RUNDLL32.EXE to load library
- rudesktop.exe (PID: 6080)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 7232)
Restarts service on failure
- sc.exe (PID: 7020)
INFO
Reads the software policy settings
- msiexec.exe (PID: 6324)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6324)
Checks supported languages
- msiexec.exe (PID: 6700)
- msiexec.exe (PID: 5968)
- msiexec.exe (PID: 7804)
Reads Environment values
- msiexec.exe (PID: 6700)
An automatically generated document
- msiexec.exe (PID: 6324)
Reads the computer name
- msiexec.exe (PID: 6700)
- msiexec.exe (PID: 5968)
- msiexec.exe (PID: 7804)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6324)
- msiexec.exe (PID: 5968)
Manages system restore points
- SrTasks.exe (PID: 4424)
The sample compiled with english language support
- msiexec.exe (PID: 5968)
Changes the display of characters in the console
- cmd.exe (PID: 7232)
- cmd.exe (PID: 4408)
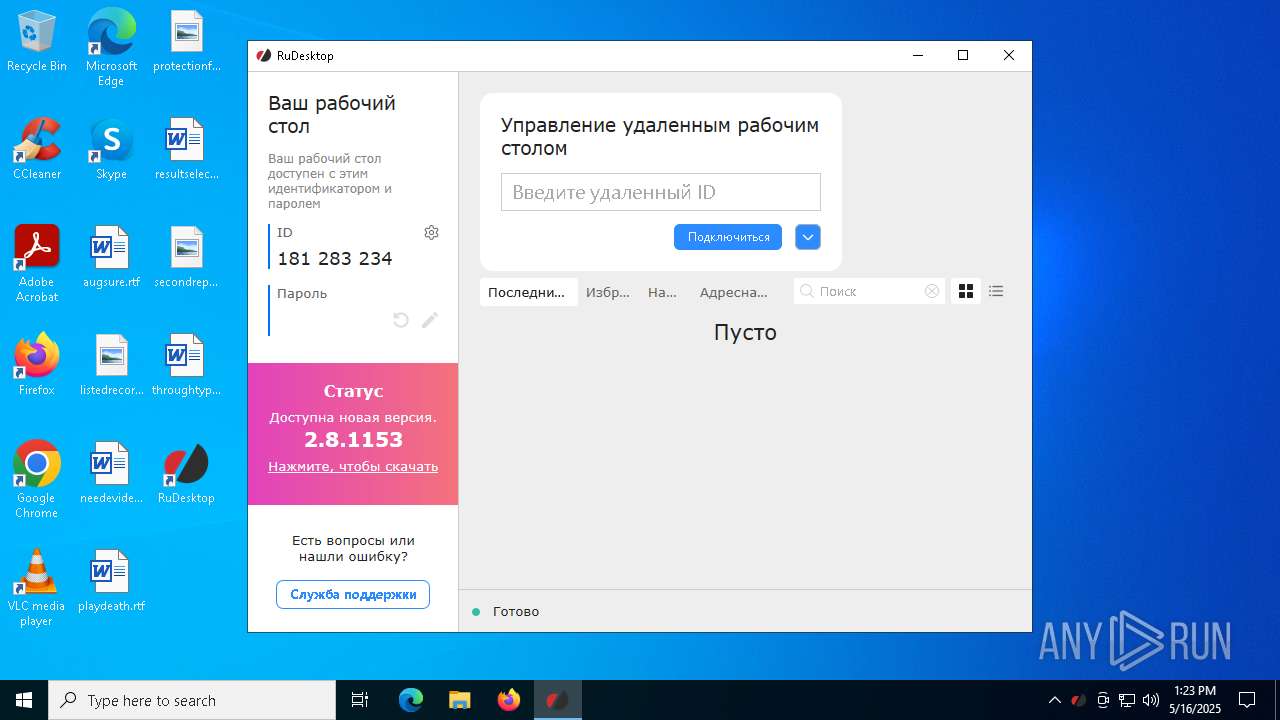
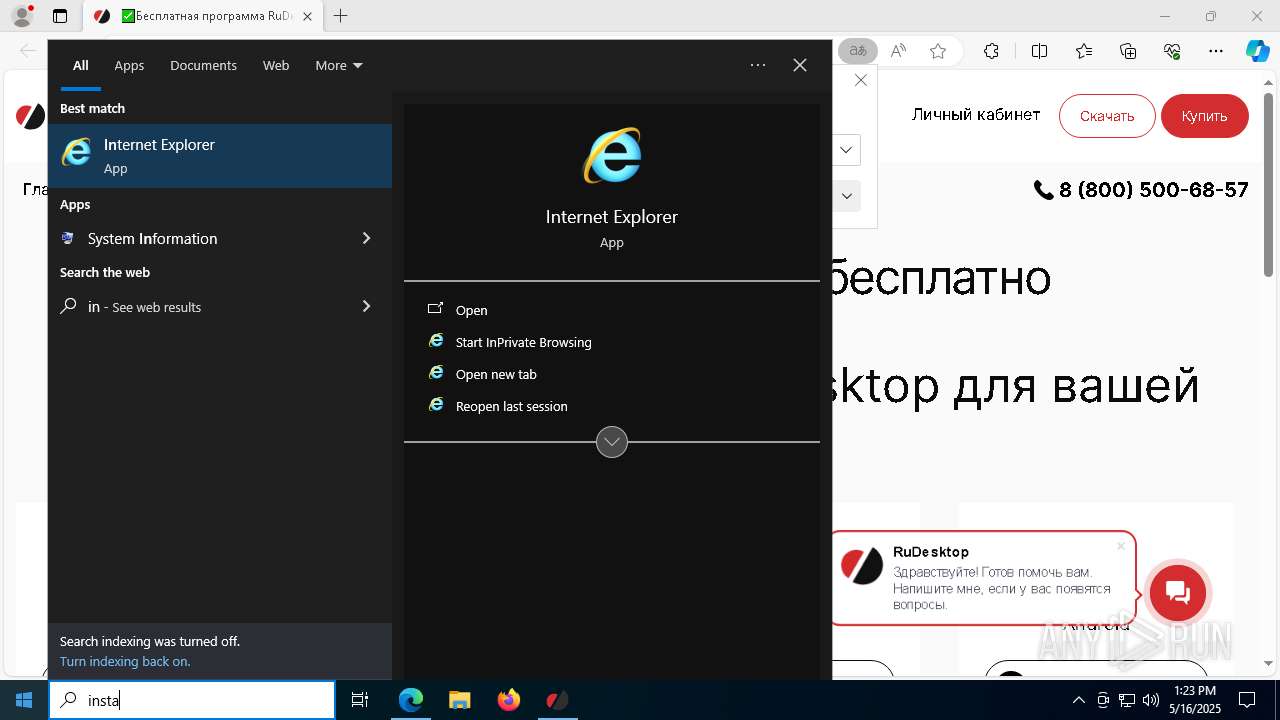
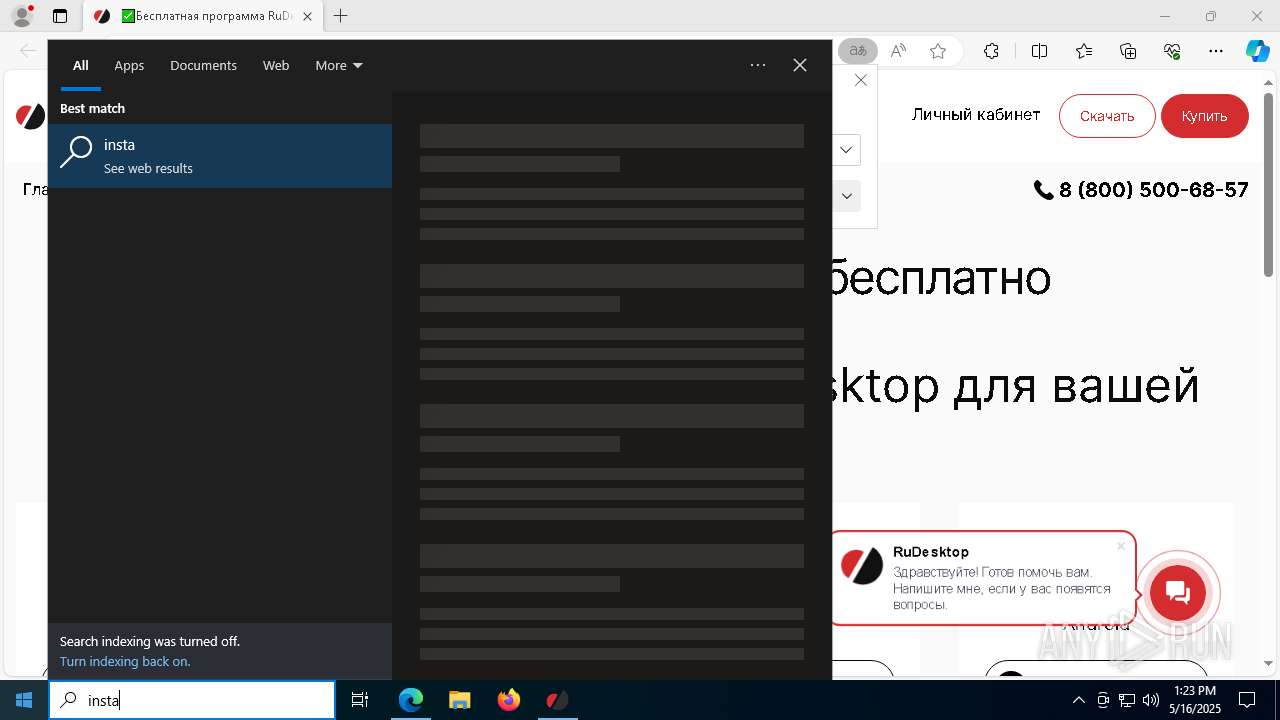
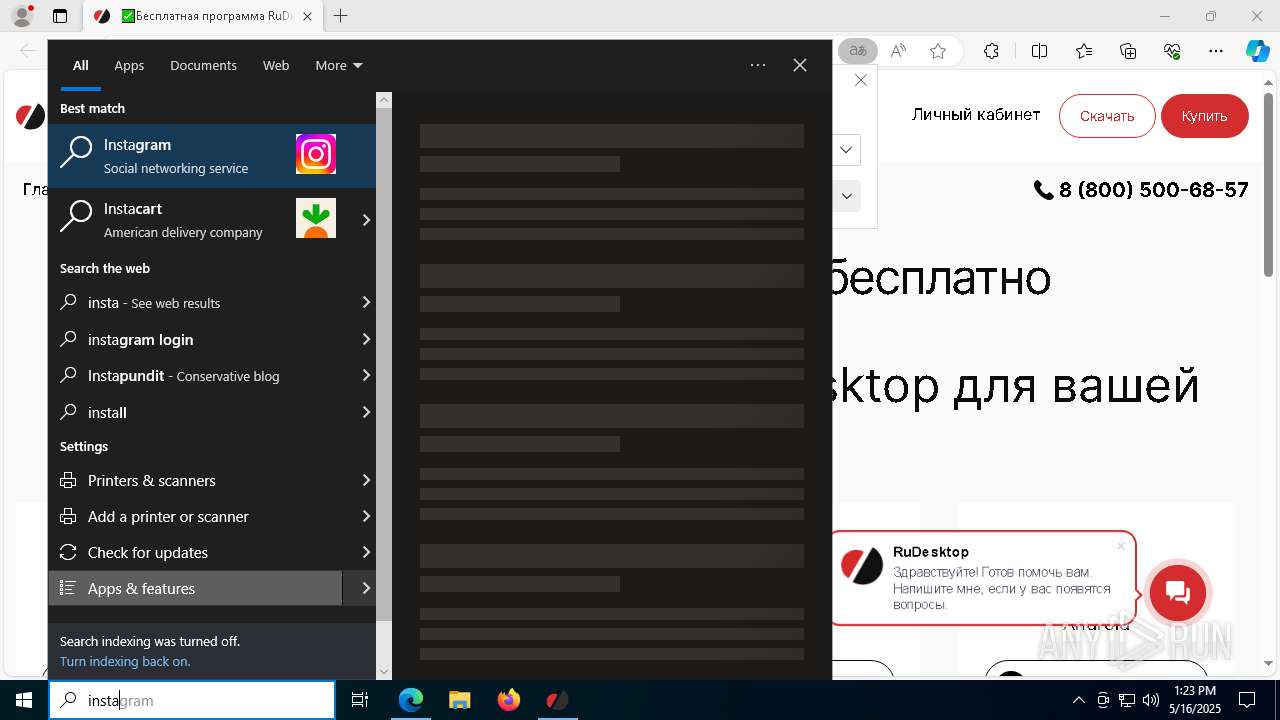
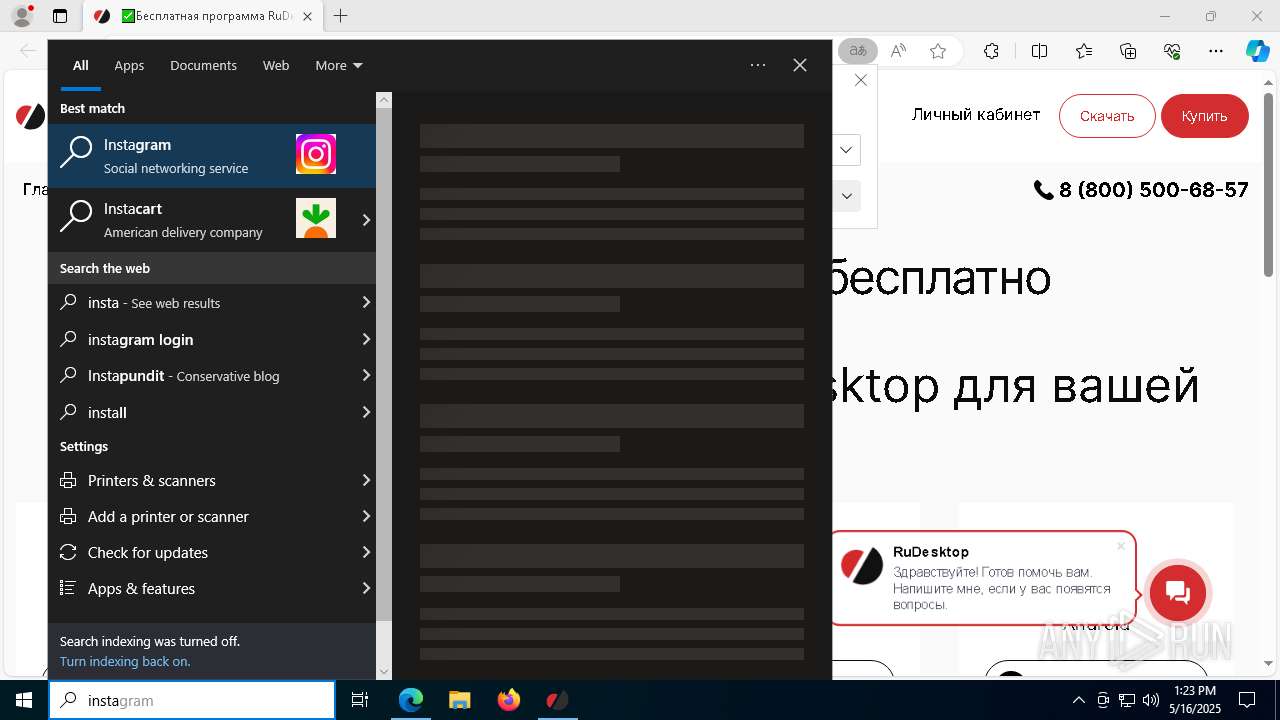
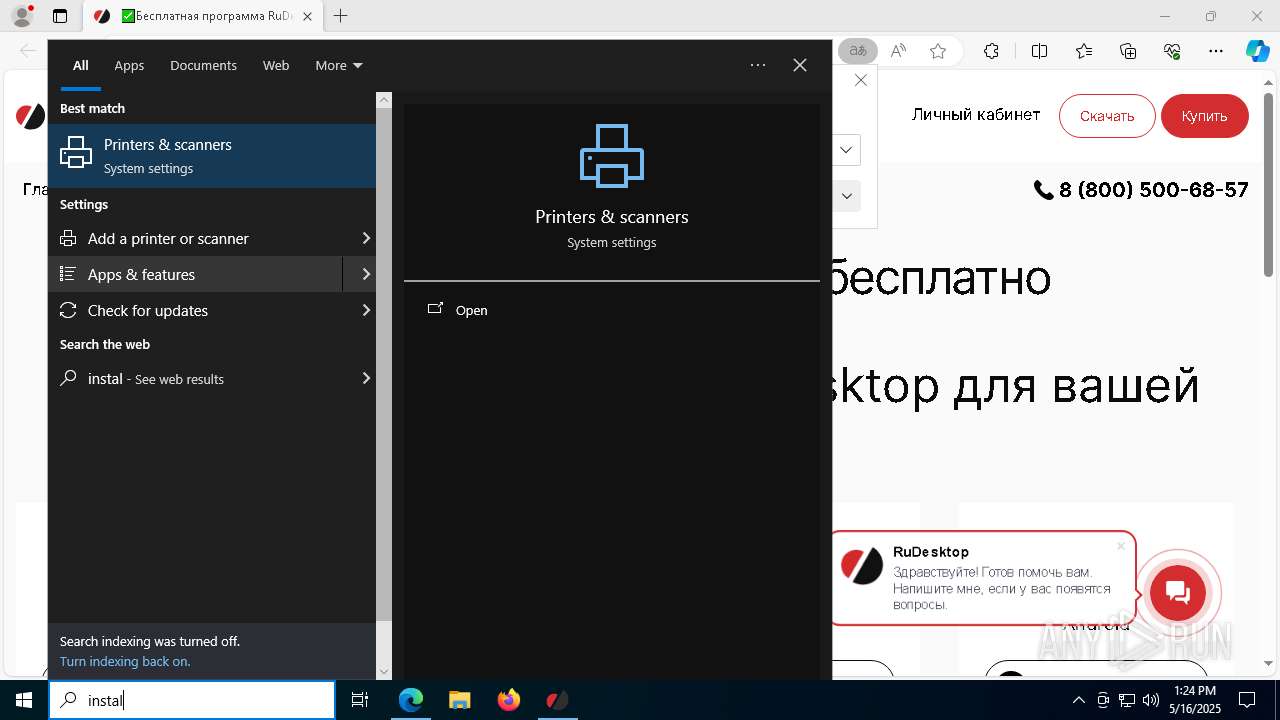
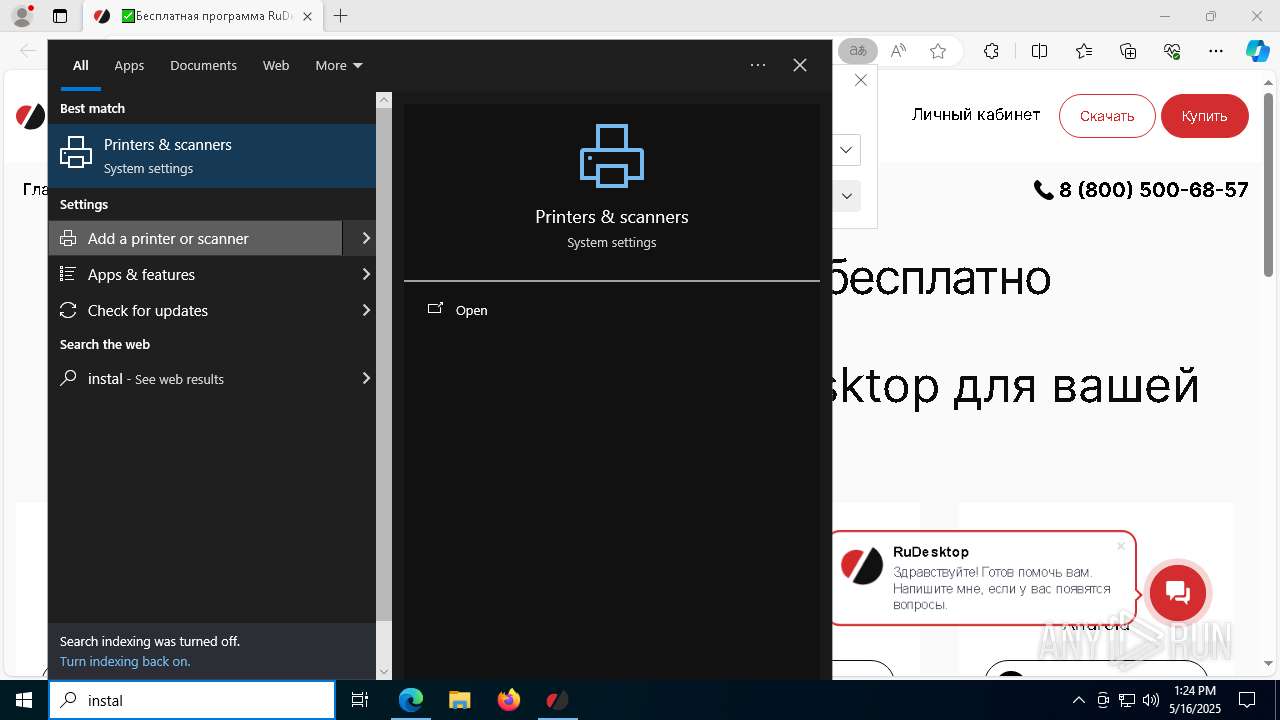
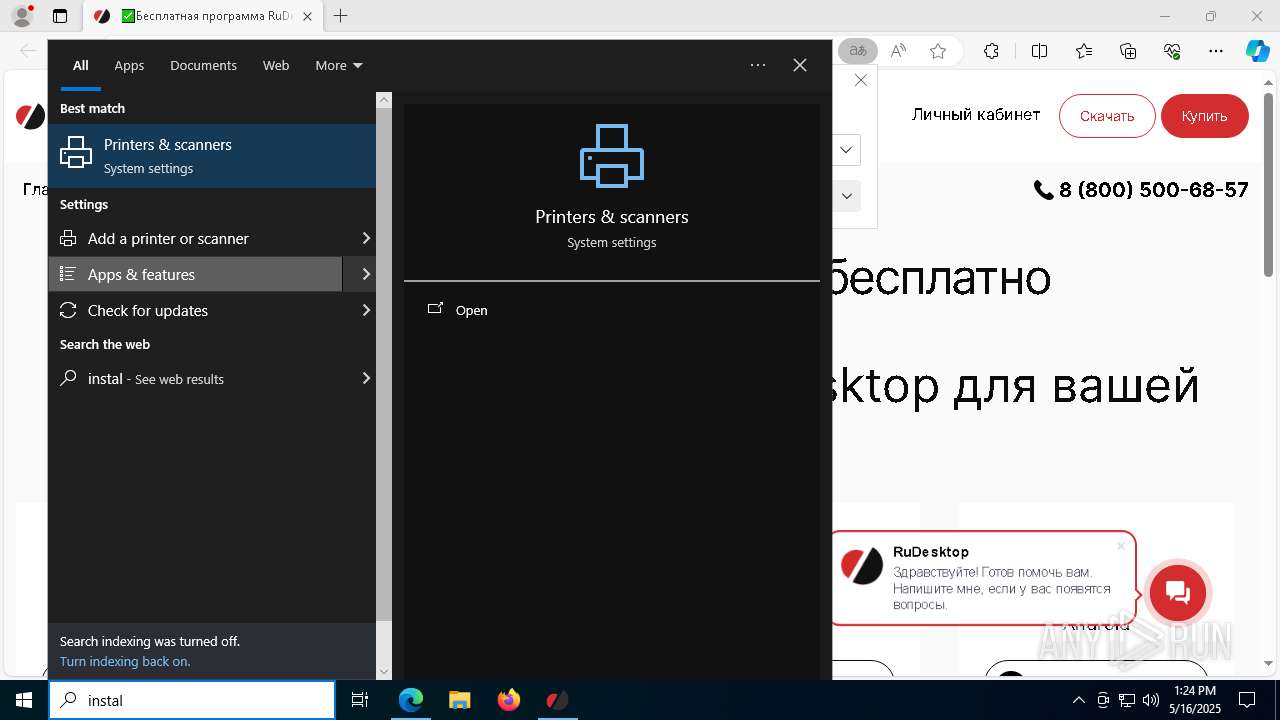
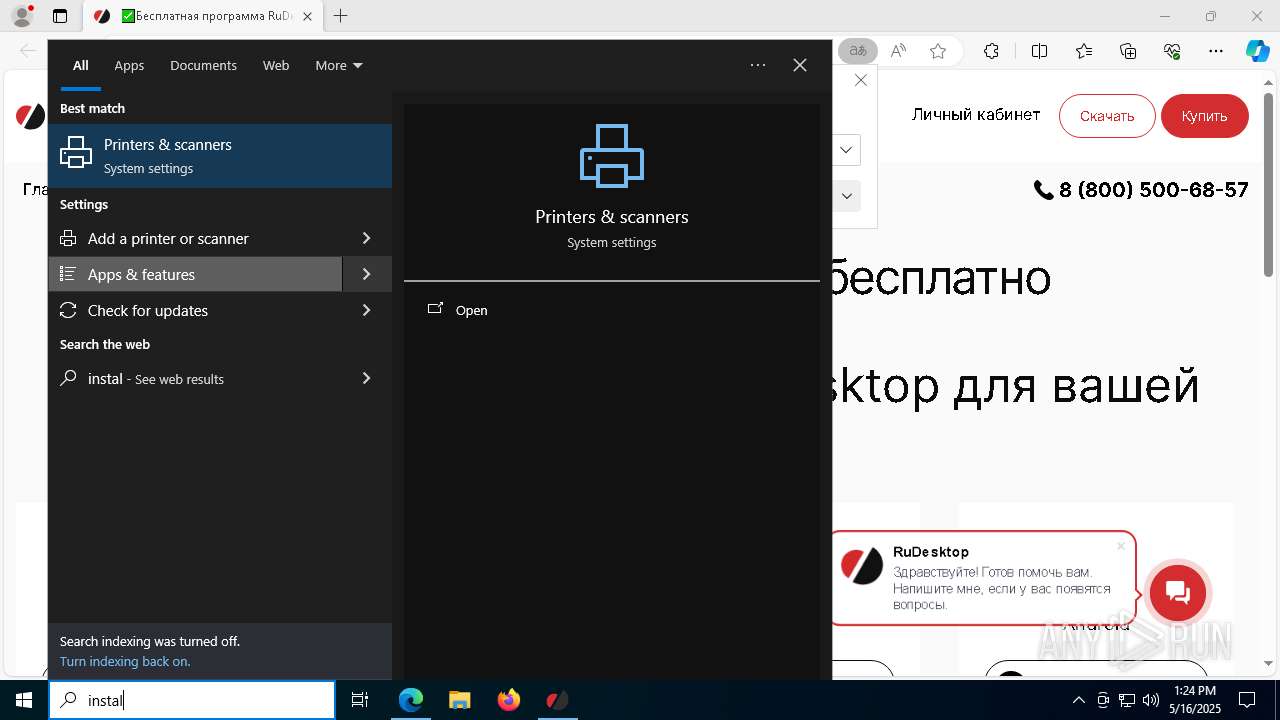
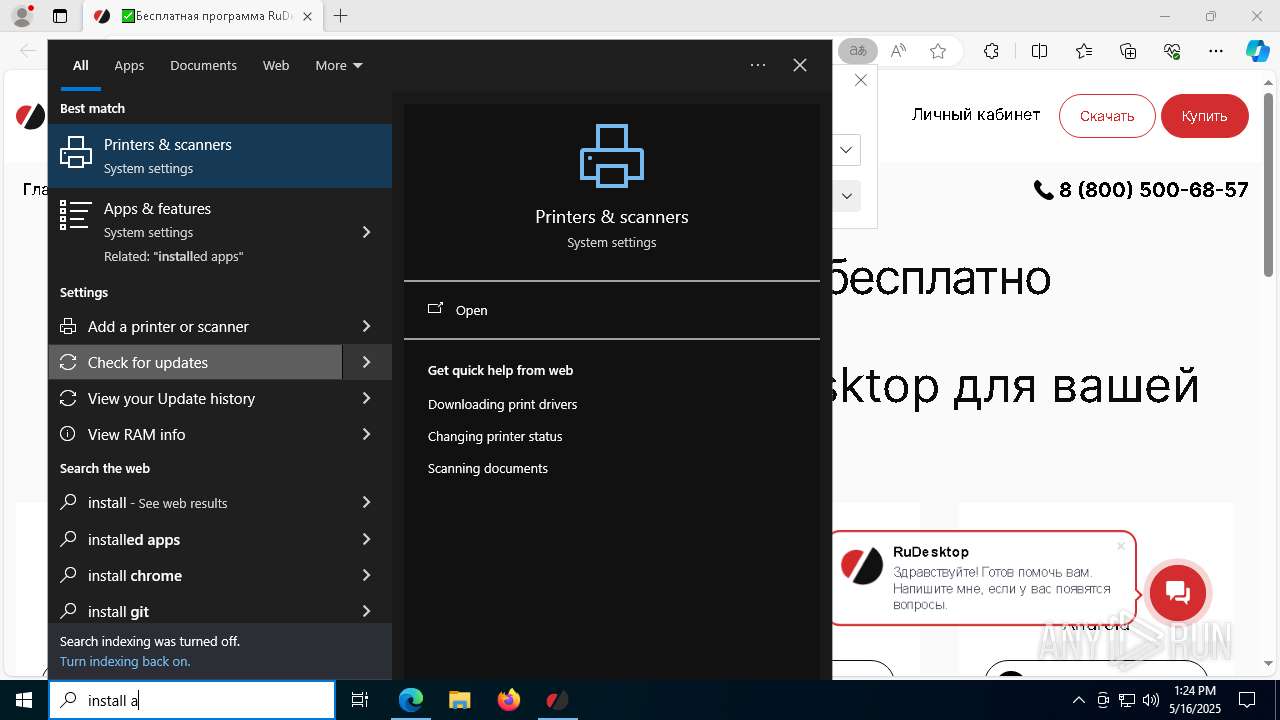
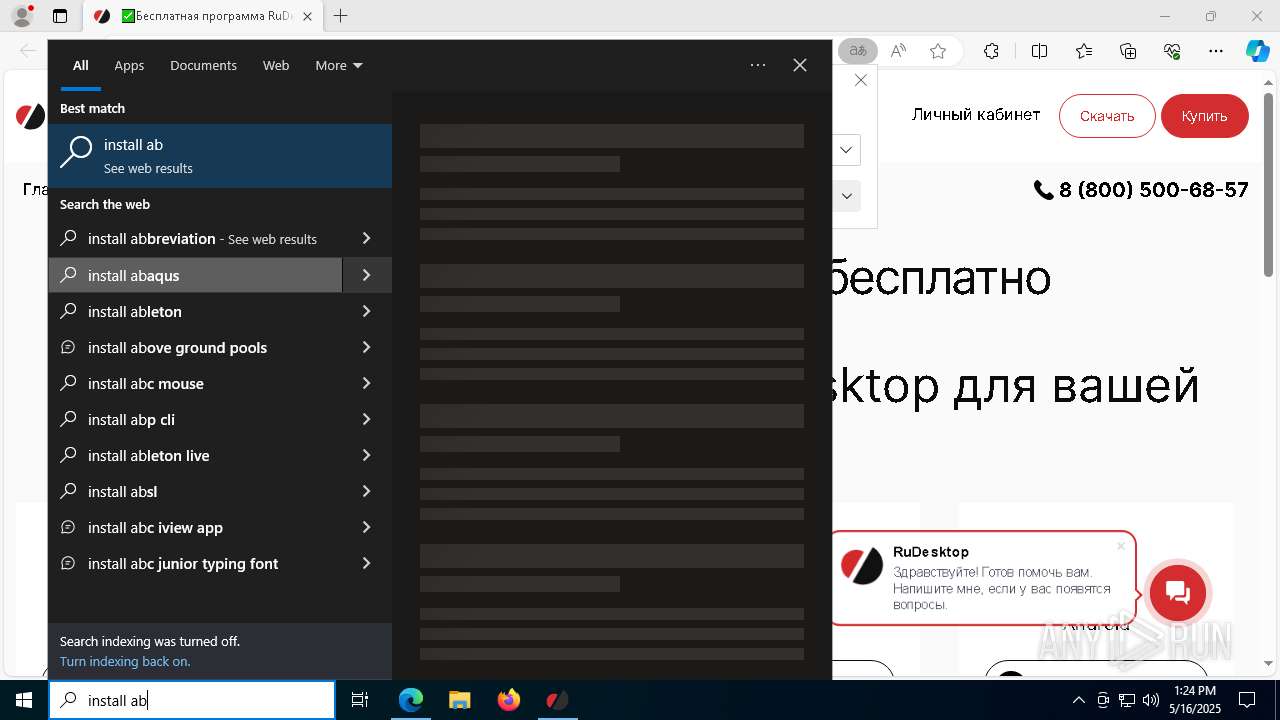
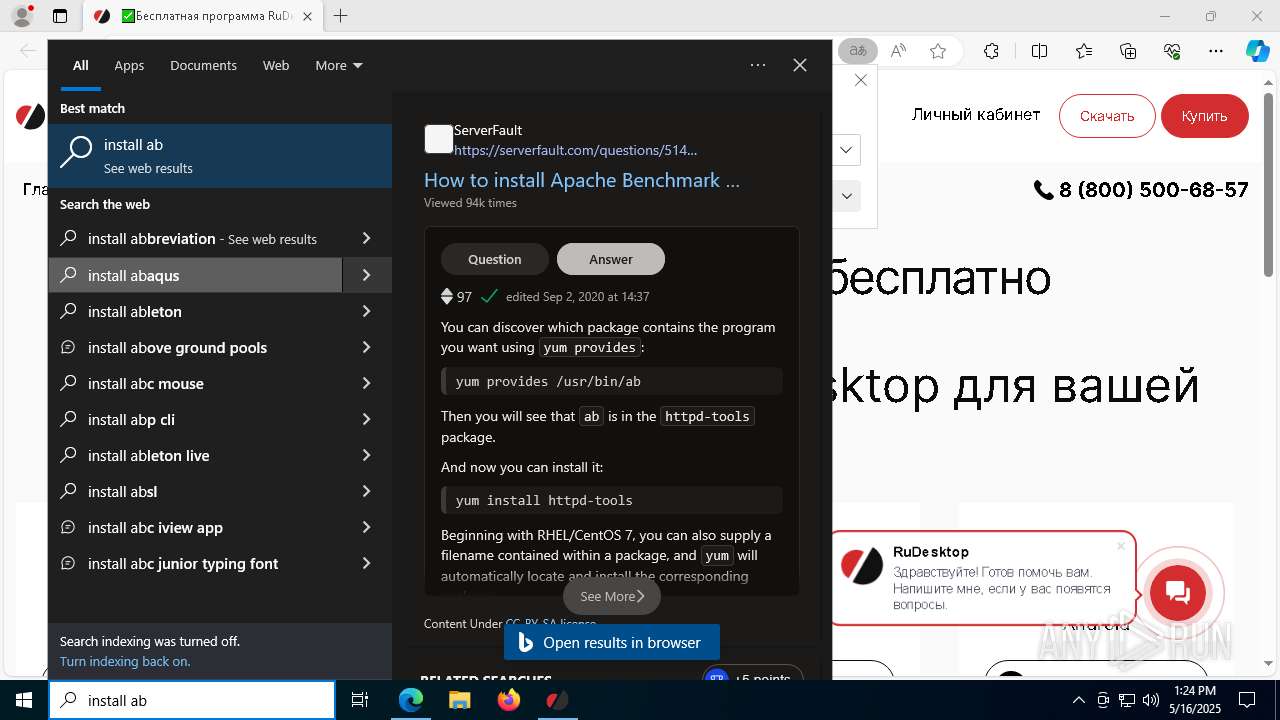
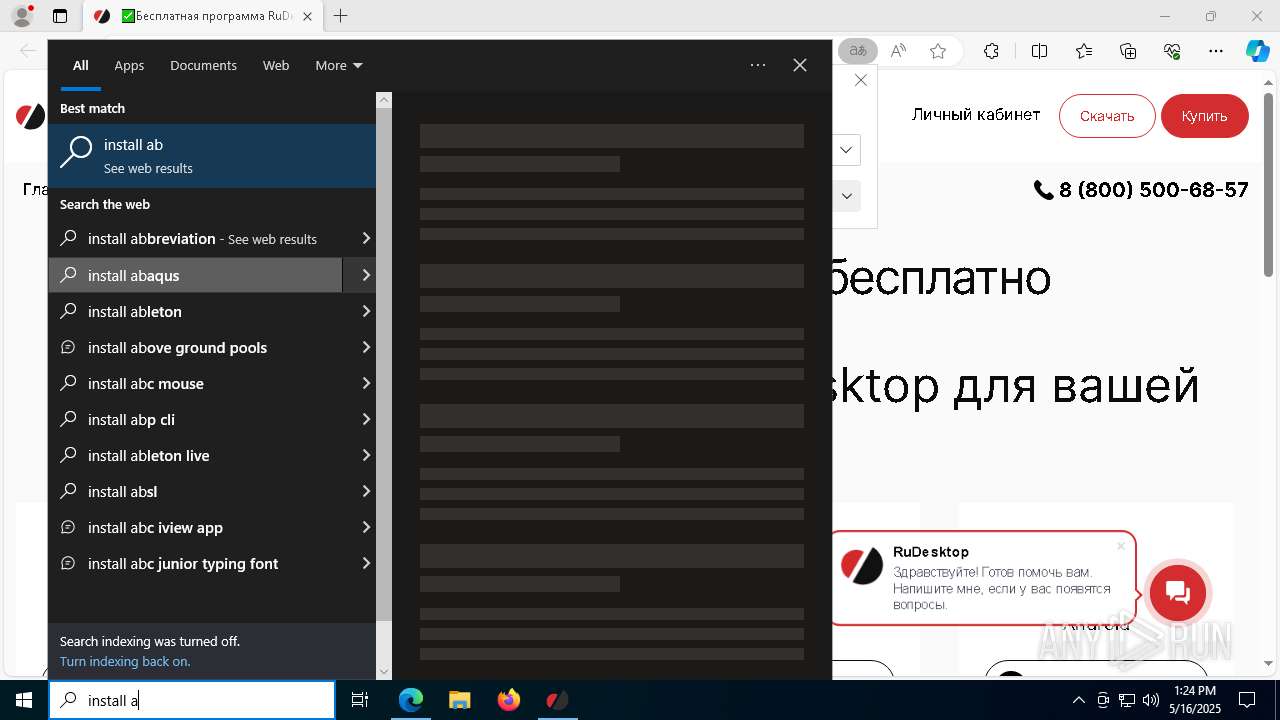
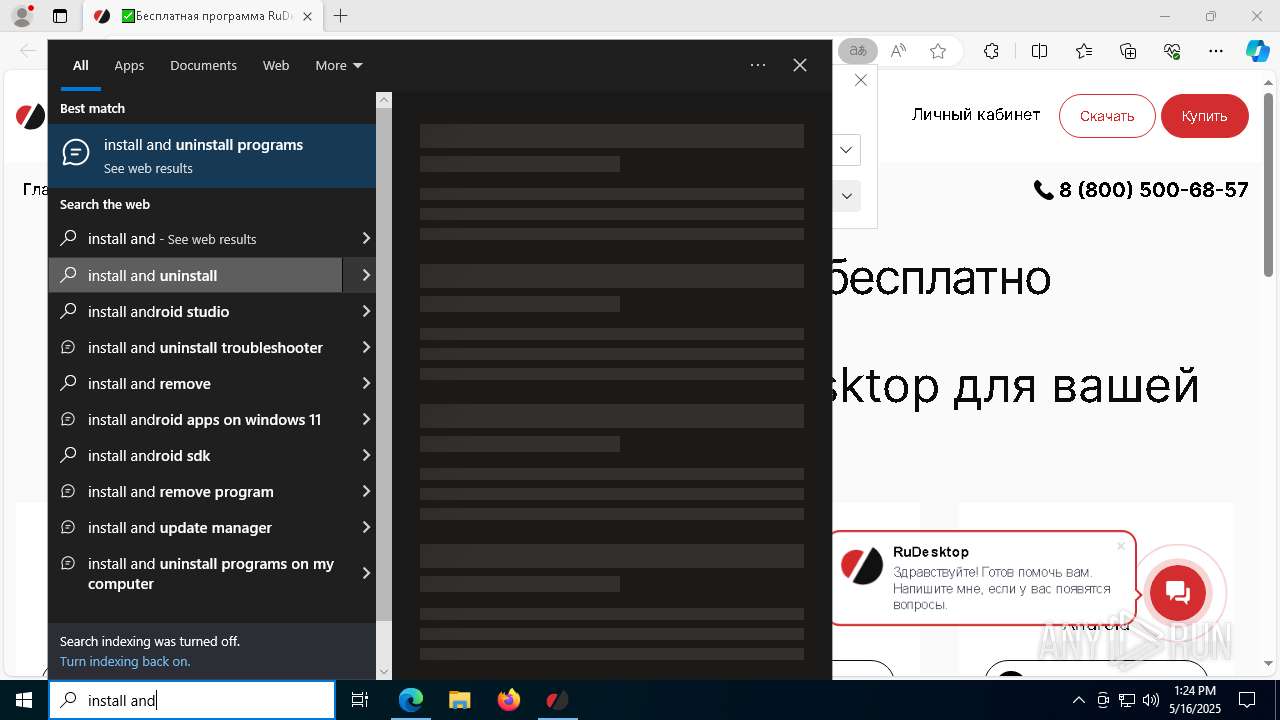
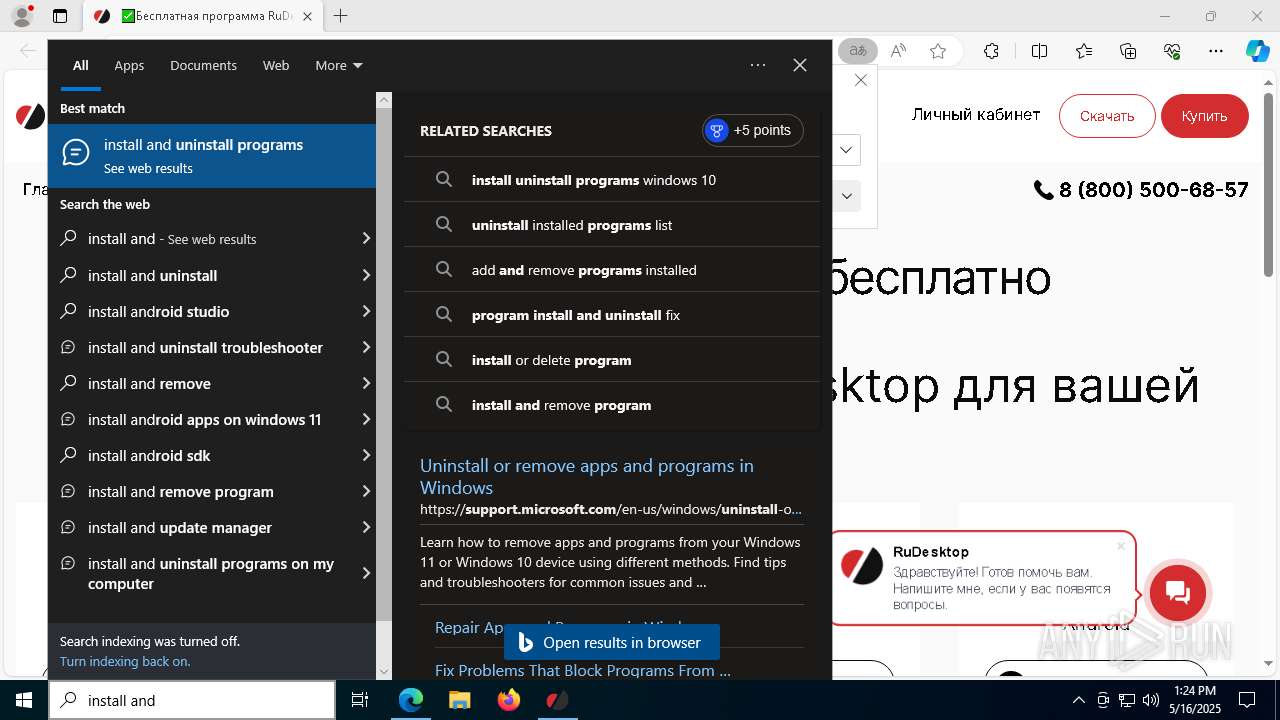
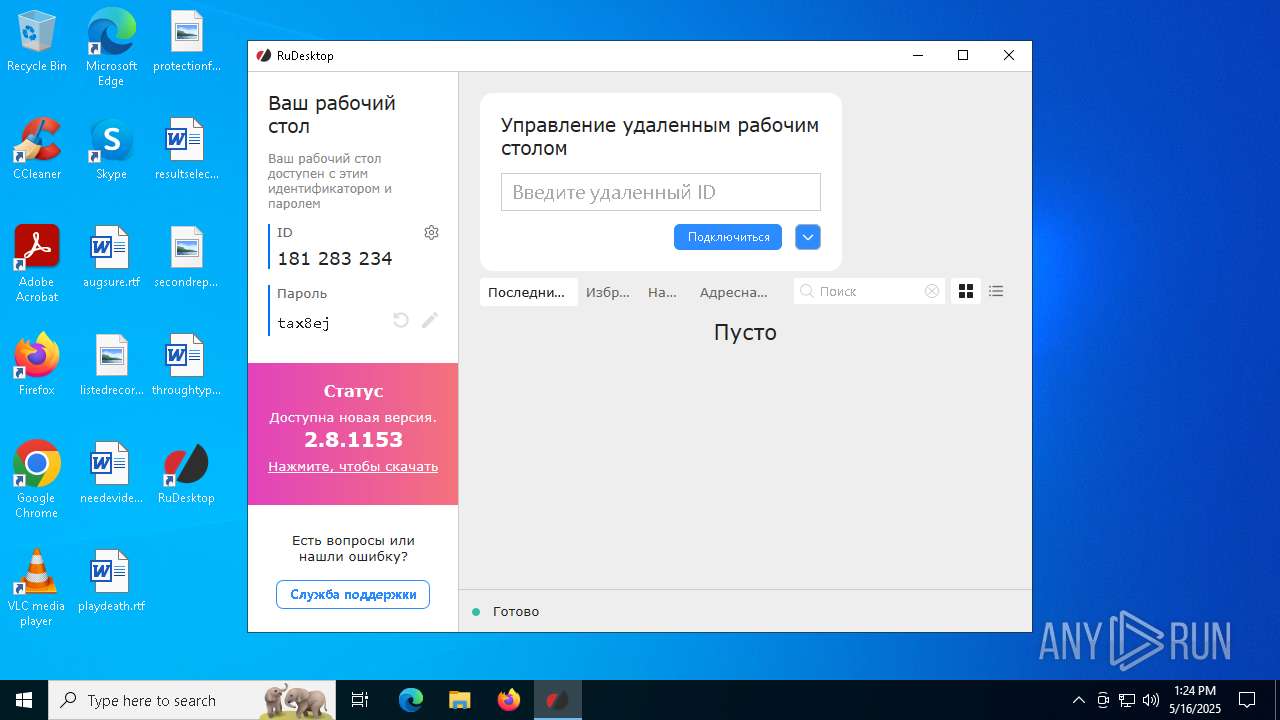
Manual execution by a user
- rudesktop.exe (PID: 6080)
Application launched itself
- msedge.exe (PID: 7520)
- msedge.exe (PID: 7436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Cyrillic |
|---|---|
| Title: | Installation Database |
| Subject: | Remote Control Software |
| Author: | Advanced Technologies LLC |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install RuDesktop. |
| Template: | x64;1033 |
| RevisionNumber: | {27A7FE62-C5AB-41CC-89F2-8EC293915B0B} |
| CreateDate: | 2025:01:28 07:10:26 |
| ModifyDate: | 2025:01:28 07:10:26 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.0.8606) |
| Security: | Read-only recommended |
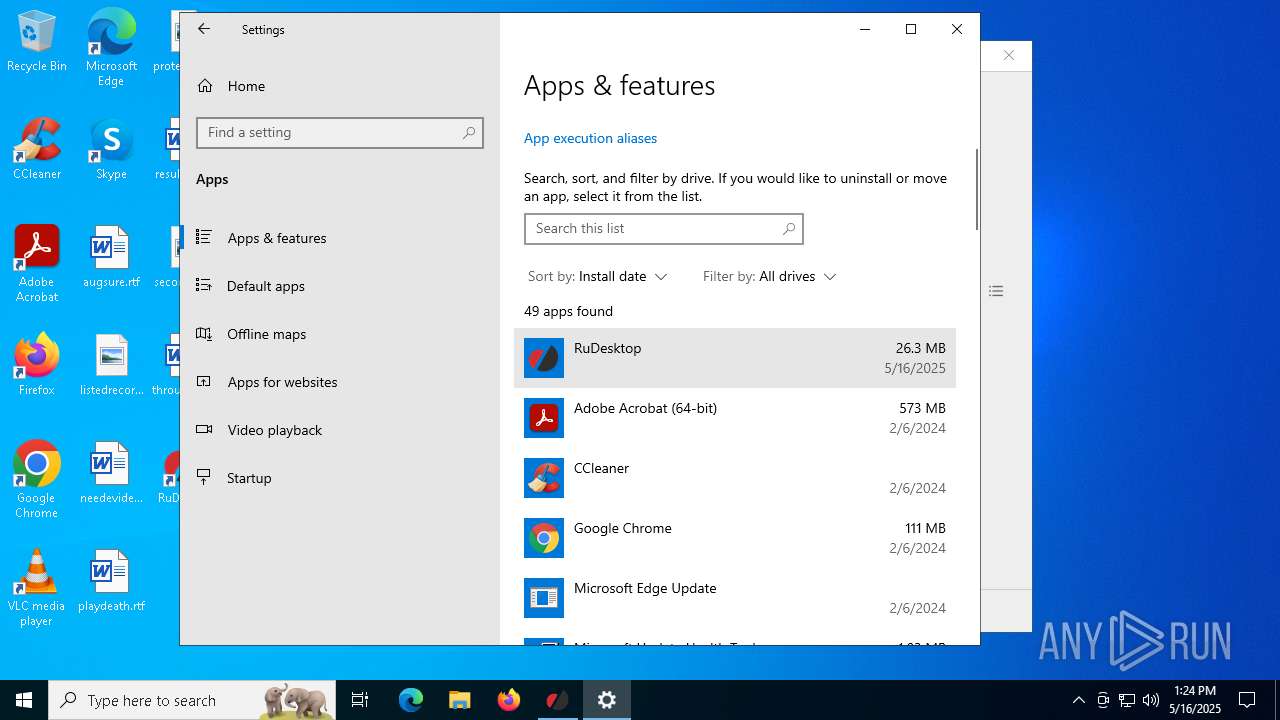
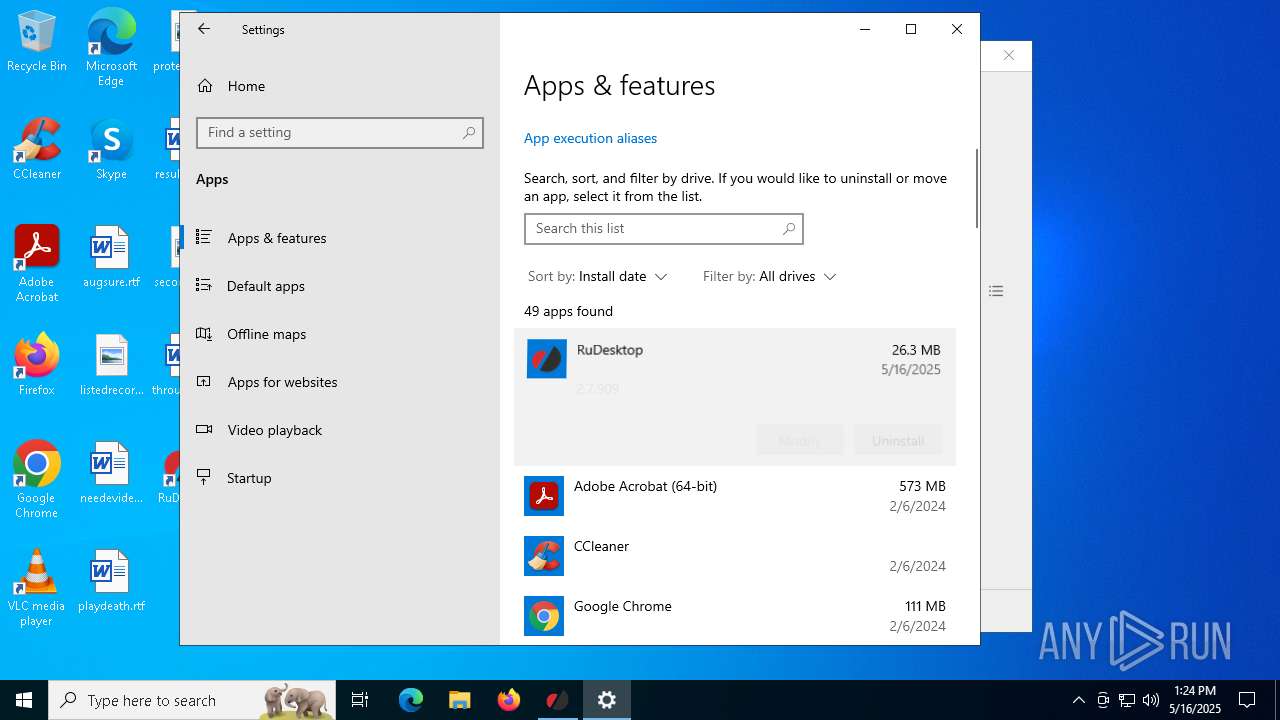
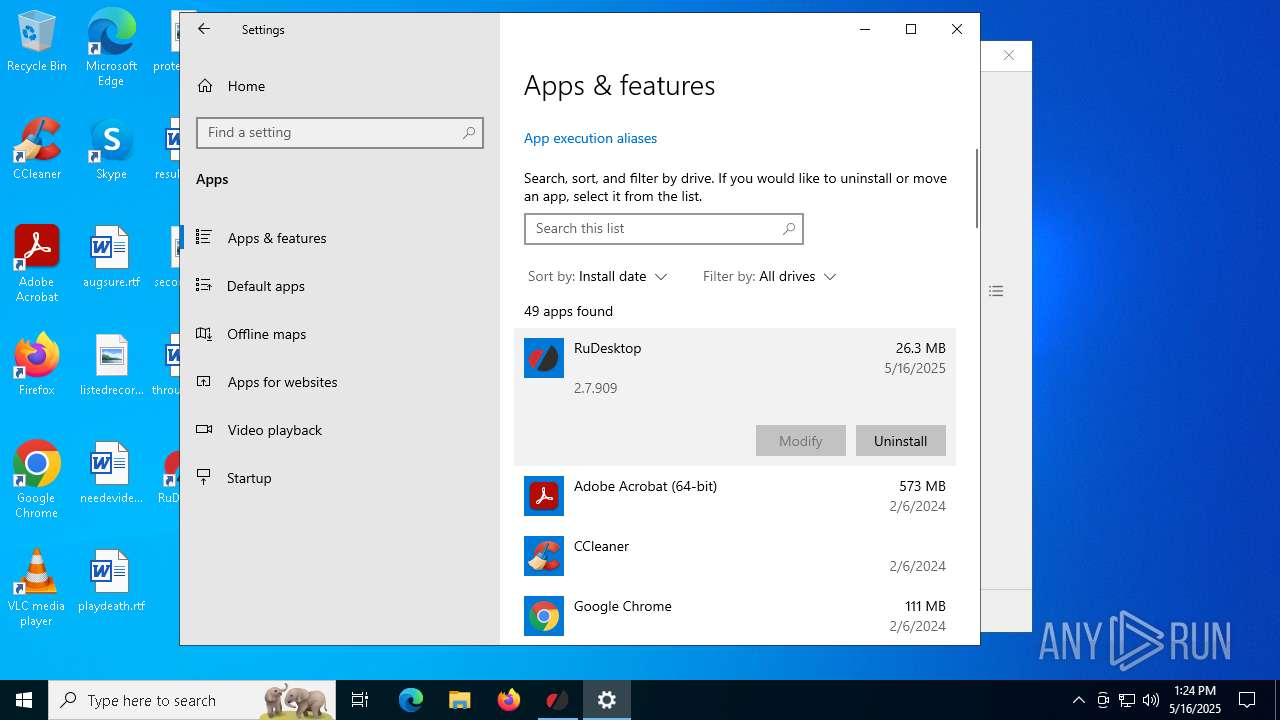
Total processes
252
Monitored processes
106
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | reg delete HKEY_CLASSES_ROOT\.rudesktop /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5360 --field-trial-handle=2380,i,7874994503931147482,11450589842387699794,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2388 --field-trial-handle=2380,i,7874994503931147482,11450589842387699794,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | sc start RuDesktop | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | "wmic" os get Caption /value | C:\Windows\System32\wbem\WMIC.exe | rudesktop.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 928 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5192 --field-trial-handle=2360,i,17103513059238026360,12102041032131110708,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1004 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4848 --field-trial-handle=2360,i,17103513059238026360,12102041032131110708,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --mojo-platform-channel-handle=4808 --field-trial-handle=2380,i,7874994503931147482,11450589842387699794,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2680 --field-trial-handle=2360,i,17103513059238026360,12102041032131110708,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
28 406
Read events
28 095
Write events
298
Delete events
13
Modification events
| (PID) Process: | (6700) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings |
| Operation: | write | Name: | JITDebug |
Value: 0 | |||
| (PID) Process: | (5968) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000004279B8B65C6DB0150170000A81E0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5968) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000004279B8B65C6DB0150170000A81E0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5968) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000A3A30D8C65C6DB0150170000A81E0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5968) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000C25A128C65C6DB0150170000A81E0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5968) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000BE2C0B8C65C6DB0150170000A81E0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5968) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000BE2C0B8C65C6DB0150170000A81E0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5968) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000009EB0A88C65C6DB0150170000A81E0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5968) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000DE5CAD8C65C6DB0150170000141F0000E8030000010000000000000000000000773531CCEB2F1B4D9524E033CBB47B4A00000000000000000000000000000000 | |||
| (PID) Process: | (7864) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
12
Suspicious files
189
Text files
152
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5968 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5968 | msiexec.exe | C:\Windows\Installer\1192d7.msi | — | |
MD5:— | SHA256:— | |||
| 5968 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{cc313577-2feb-4d1b-9524-e033cbb47b4a}_OnDiskSnapshotProp | binary | |
MD5:441DFDB63A3F24349676DF06139E2764 | SHA256:7D8E7D3AF0706AD8A60ED2591D0AFF71BFD0DBFFED649A1503C4F1438EB87778 | |||
| 5968 | msiexec.exe | C:\Program Files\RuDesktop\RuDesktopIddDriver\RuDesktopIddDriver.dll | executable | |
MD5:A00A48BA0C12550C0FA9AB82C23CF993 | SHA256:4FE51D3DEAA9F3B4E9ED29A7A2F364176B1FFC6CE8E57408CD49C517282C438C | |||
| 5968 | msiexec.exe | C:\Program Files\RuDesktop\RuDesktopIddDriver\rudesktopidddriver.cat | binary | |
MD5:0D3E0A78B54A9C732454D6D9E6D1CD6F | SHA256:BA82041A6205A3561E53F96649C6DCC4835A8866CBF63307224E5FAEB2158161 | |||
| 5968 | msiexec.exe | C:\Windows\Installer\MSI9D37.tmp | binary | |
MD5:EA51B6F173BCA31E9F8C418096399D8A | SHA256:2A6C9D6CE5311F00838F5A8BC9B3EEEDAA55F1D29D69119D77BE50FA830F90A9 | |||
| 5968 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:441DFDB63A3F24349676DF06139E2764 | SHA256:7D8E7D3AF0706AD8A60ED2591D0AFF71BFD0DBFFED649A1503C4F1438EB87778 | |||
| 6324 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | binary | |
MD5:9D17C7CE8A2B2360897BA20EE6B3EA9A | SHA256:976D7703AA0CAE5F617520CFBAA47BF1978D69FC8B7218F3062F6AFE56893CB1 | |||
| 6324 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | binary | |
MD5:C7FF438F4E671A6878E0D05B257D0F7B | SHA256:A91CCEB32F22D1FCEE44938E61776B186E451534ED93DAAE2ECA9670F093CD86 | |||
| 5968 | msiexec.exe | C:\Windows\Temp\~DF9DEA9C53F6F14853.TMP | binary | |
MD5:BA42EDA6E4CB41540F8460DF3CE347C1 | SHA256:396E741327003740BB107EB7A5760C9890EB6FE7337B7B7C1C90D94FB20AF210 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
112
DNS requests
97
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6324 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | binary | 1.67 Kb | whitelisted |
6324 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDATGh%2FSzVDsYeIH8aw%3D%3D | unknown | binary | 1.65 Kb | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7672 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | CL | — | 419 b | whitelisted |
7672 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | CL | binary | 407 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 868 b | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | DE | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6324 | msiexec.exe | 104.18.20.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | whitelisted |
6544 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |