| File name: | WSExplorer 1.3.exe |
| Full analysis: | https://app.any.run/tasks/2bcbf8b1-5ecd-4ca5-beef-1f1cdc1b1c2d |
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2019, 11:25:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4C3567554928099E25E350E05D42FD77 |
| SHA1: | CF62E7568AE54AB3333AA46AE6CE270DB674D7C8 |
| SHA256: | C880C82646266710EC7E0882C16B4F281219889646968AAFBB754FD95BB9902B |
| SSDEEP: | 49152:c6tokbhvGb4DOkGU5Qu0OQbqRBhfWnTTqeQPlVBFWBQXM:c6dOkDQJmBhfWnpQPLB |
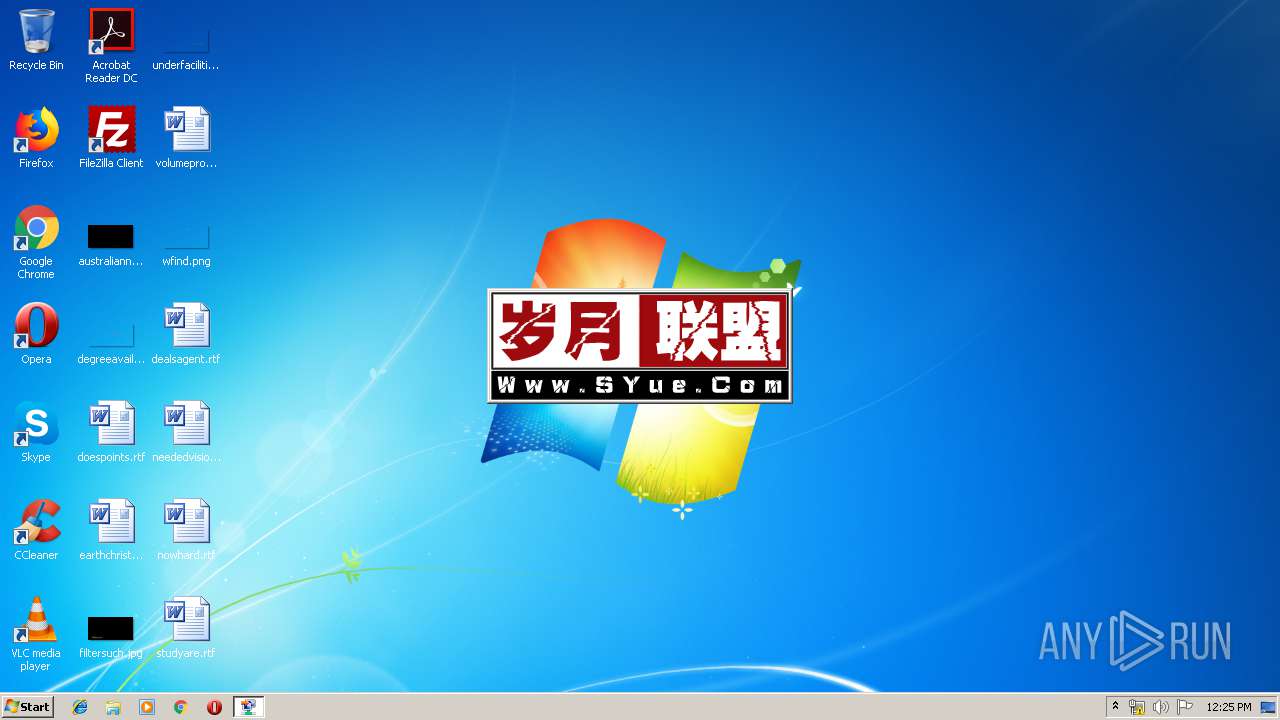
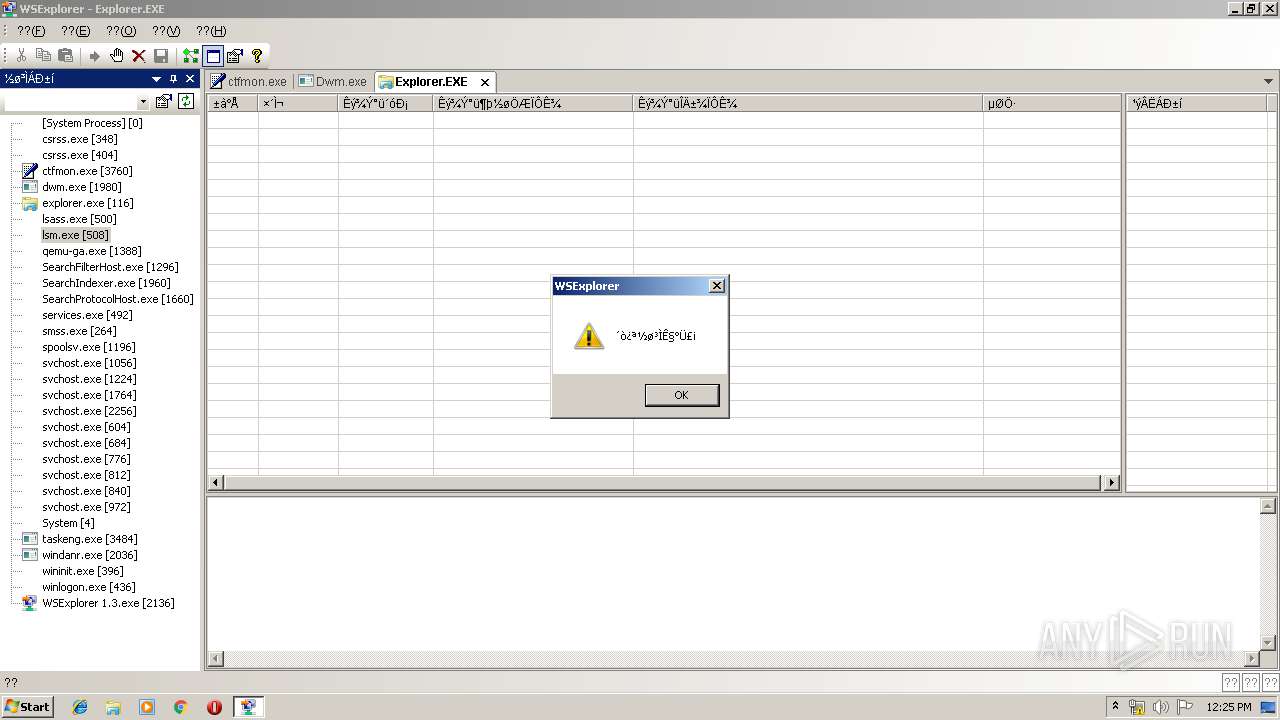
MALICIOUS
Loads dropped or rewritten executable
- ctfmon.exe (PID: 3760)
- dwm.exe (PID: 1980)
- explorer.exe (PID: 116)
- taskeng.exe (PID: 3484)
Runs injected code in another process
- WSExplorer 1.3.exe (PID: 2136)
Application was injected by another process
- explorer.exe (PID: 116)
- ctfmon.exe (PID: 3760)
- dwm.exe (PID: 1980)
- taskeng.exe (PID: 3484)
SUSPICIOUS
Executable content was dropped or overwritten
- WSExplorer 1.3.exe (PID: 2136)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (34.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (25.2) |
| .exe | | | Win64 Executable (generic) (22.3) |
| .scr | | | Windows screen saver (10.6) |
| .exe | | | Win32 Executable (generic) (3.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:01:06 15:27:11+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 2265088 |
| InitializedDataSize: | 1273856 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1357c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.0.5 |
| ProductVersionNumber: | 1.3.0.5 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Windows Socket Explorer |
| FileVersion: | 1, 3, 0, 5 |
| InternalName: | WSExplorer |
| LegalCopyright: | 版权所有 (C) 2010-2014 |
| LegalTrademarks: | - |
| OriginalFileName: | WSExplorer.EXE |
| PrivateBuild: | - |
| ProductName: | Windows Socket Explorer |
| ProductVersion: | 1, 3, 0, 5 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jan-2011 14:27:11 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Windows Socket Explorer |
| FileVersion: | 1, 3, 0, 5 |
| InternalName: | WSExplorer |
| LegalCopyright: | 版权所有 (C) 2010-2014 |
| LegalTrademarks: | - |
| OriginalFilename: | WSExplorer.EXE |
| PrivateBuild: | - |
| ProductName: | Windows Socket Explorer |
| ProductVersion: | 1, 3, 0, 5 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 06-Jan-2011 14:27:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00228557 | 0x00229000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4517 |
.rdata | 0x0022A000 | 0x000546BA | 0x00055000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.81402 |
.data | 0x0027F000 | 0x00013BE8 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.66522 |
.rsrc | 0x00293000 | 0x000CDF68 | 0x000CE000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.70186 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89203 | 652 | UNKNOWN | Chinese - PRC | RT_MANIFEST |
2 | 3.77539 | 1640 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 3.87734 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 3.44576 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 5.25997 | 5672 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 5.45829 | 3752 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 2.99731 | 68 | UNKNOWN | Chinese - PRC | RT_STRING |
8 | 3.12439 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
9 | 2.63491 | 156 | UNKNOWN | Chinese - PRC | RT_STRING |
10 | 5.09591 | 9640 | UNKNOWN | Chinese - PRC | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll |
OLEAUT32.dll |
OLEPRO32.DLL |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
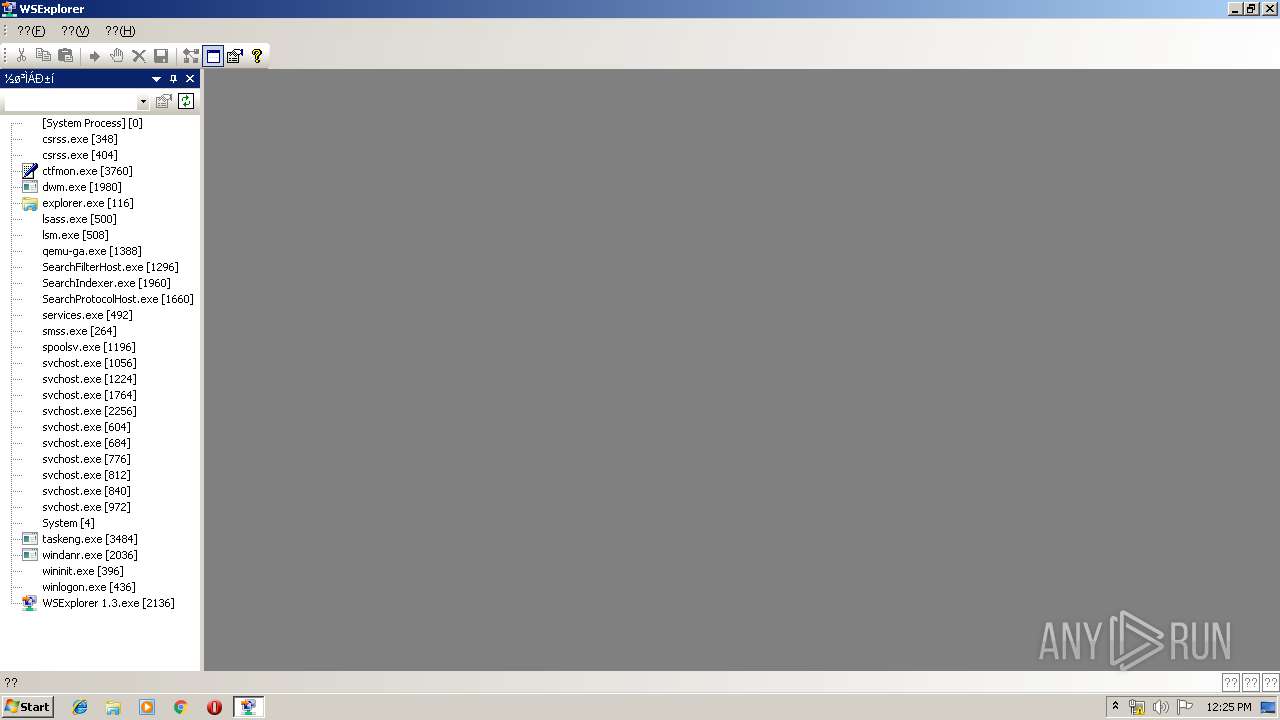
Total processes
32
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
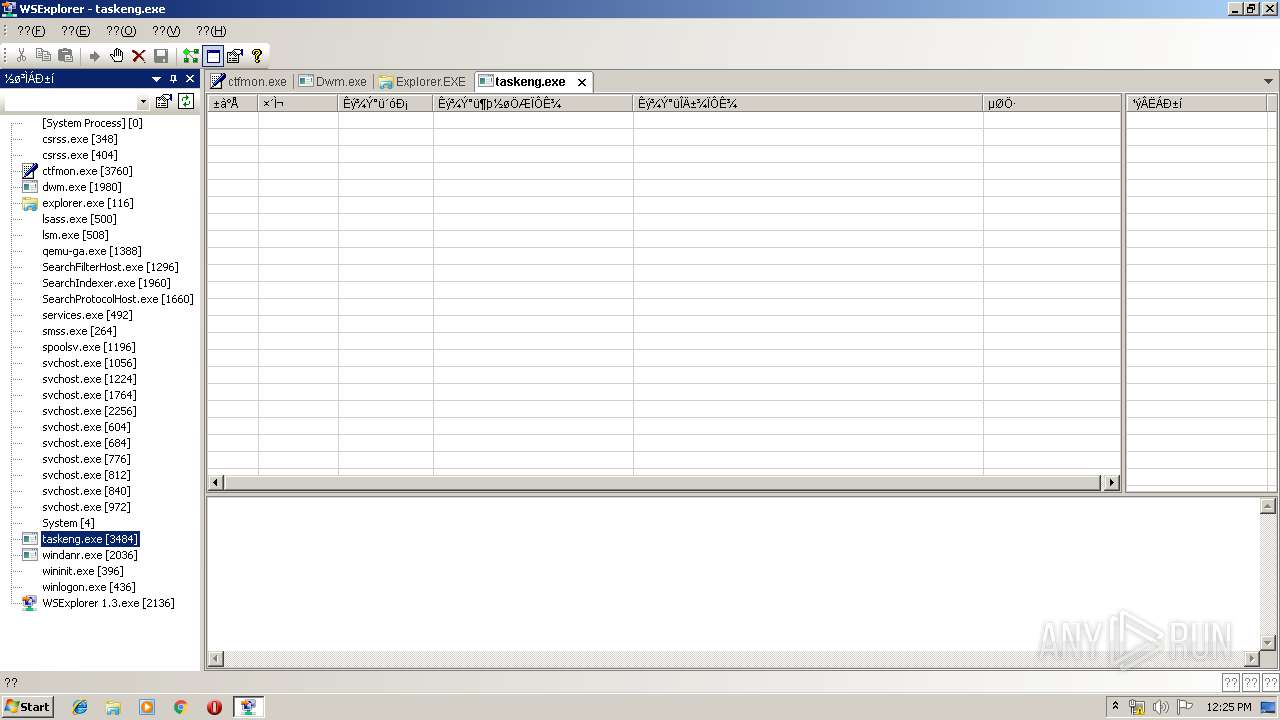
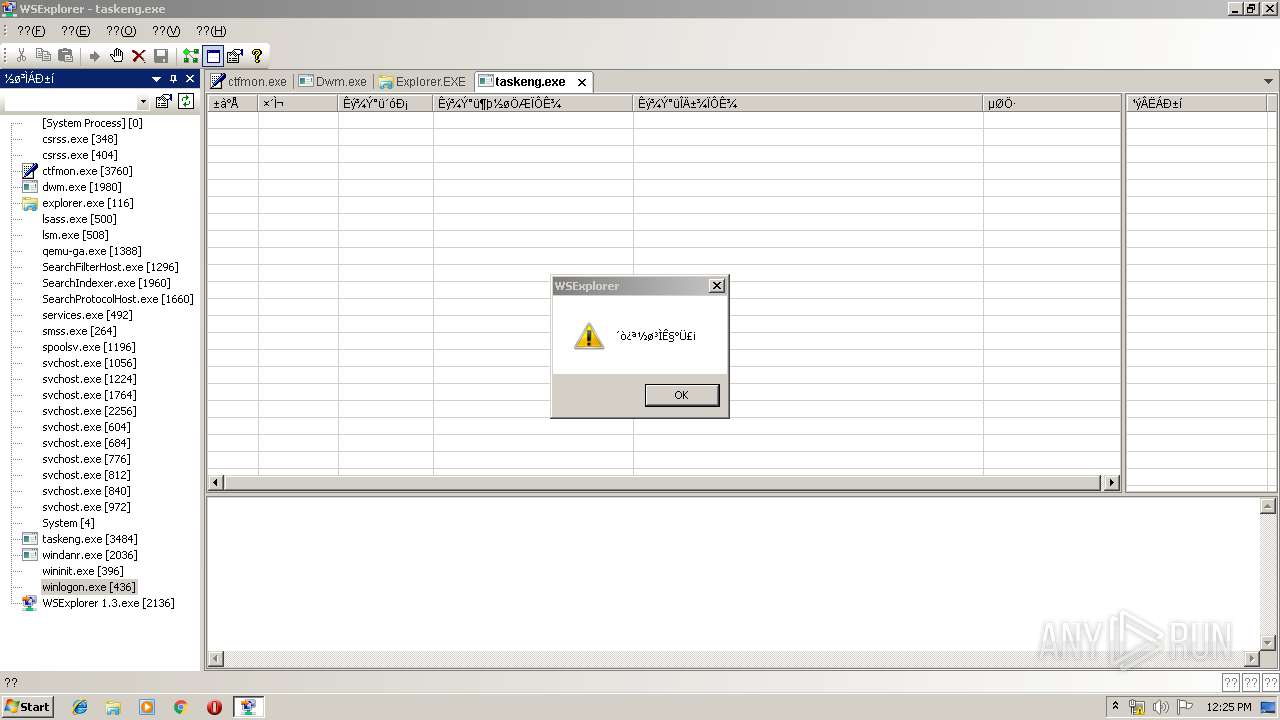
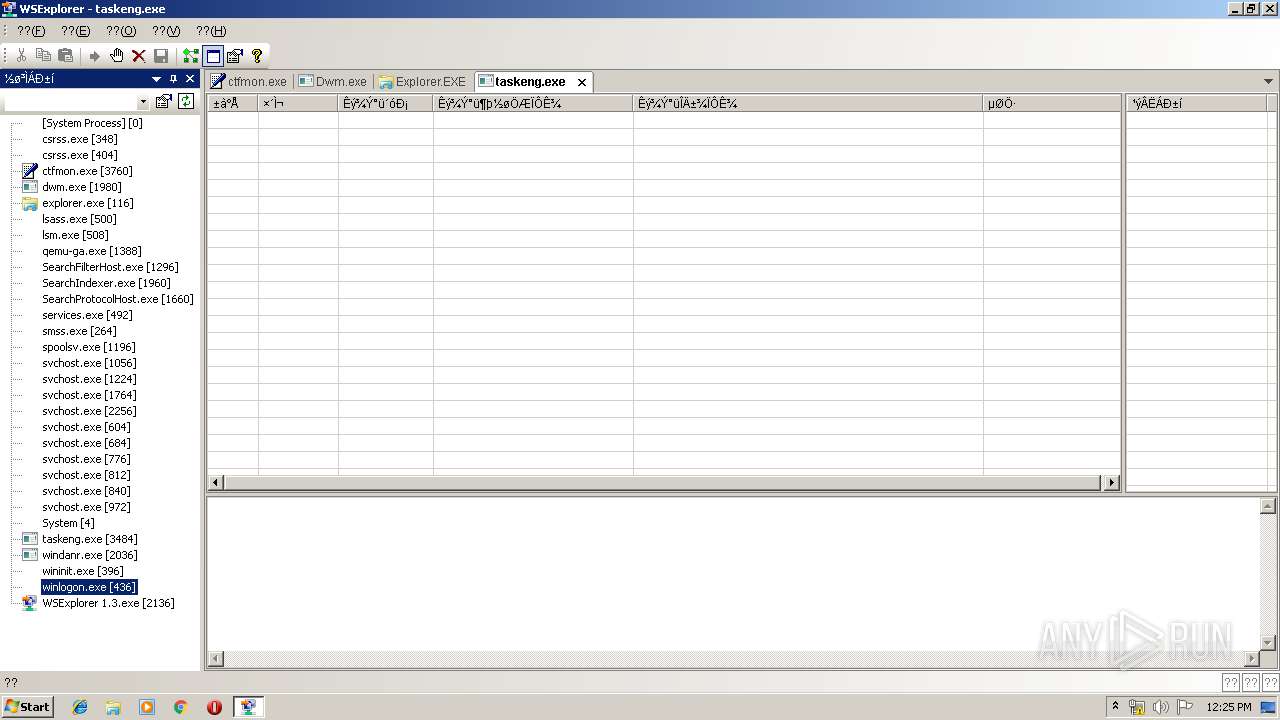
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1980 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\AppData\Local\Temp\WSExplorer 1.3.exe" | C:\Users\admin\AppData\Local\Temp\WSExplorer 1.3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windows Socket Explorer Exit code: 0 Version: 1, 3, 0, 5 Modules
| |||||||||||||||
| 3484 | taskeng.exe {3C3662D6-0B0A-4D7C-BD20-91493FA9748D} | C:\Windows\System32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3760 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
360
Read events
354
Write events
6
Delete events
0
Modification events
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\JFRkcybere 1.3.rkr |
Value: 0000000000000000000000001A060000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000005000000060000007328010003000000040000009FA900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000D9010B8CCA760100000000000000537ACA7694030114002000000000000001000000BCE7D90136170A7794030114100854020500000000000000FFFFFFFFD007540200000000B8E7D901E4E7D90100000000000000000000000010E8D90160015C0000000000409167760900800108E8D90135590A77940301148023490305000000F0E7D901506ACB761CC0CF7601000000EF7ACA76940301141D0000000020000008E8D90163590A7710E8D901000000000000000094030114406663760100000074E8D901A1366B76000000000000000070C25B0074E8D901B8366B76E0926E760000000000005300802349030000000070E8D9010000FFFF000100000000000000000000CF676976A822490301000000782349037CE8D901E82CF97670C25B00CF67697698EAD9017823490311000000B8455600B045560000000000FCE800004F88652EACE8D90182917275FCE8D901B0E8D9012795727500000000A486F602D8E8D901CD947275A486F60284E9D9011882F602E1947275000000001882F60284E9D901E0E8D90103000000040000009FA900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000D9010B8CCA760100000000000000537ACA7694030114002000000000000001000000BCE7D90136170A7794030114100854020500000000000000FFFFFFFFD007540200000000B8E7D901E4E7D90100000000000000000000000010E8D90160015C0000000000409167760900800108E8D90135590A77940301148023490305000000F0E7D901506ACB761CC0CF7601000000EF7ACA76940301141D0000000020000008E8D90163590A7710E8D901000000000000000094030114406663760100000074E8D901A1366B76000000000000000070C25B0074E8D901B8366B76E0926E760000000000005300802349030000000070E8D9010000FFFF000100000000000000000000CF676976A822490301000000782349037CE8D901E82CF97670C25B00CF67697698EAD9017823490311000000B8455600B045560000000000FCE800004F88652EACE8D90182917275FCE8D901B0E8D9012795727500000000A486F602D8E8D901CD947275A486F60284E9D9011882F602E1947275000000001882F60284E9D901E0E8D90103000000040000009FA900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000D9010B8CCA760100000000000000537ACA7694030114002000000000000001000000BCE7D90136170A7794030114100854020500000000000000FFFFFFFFD007540200000000B8E7D901E4E7D90100000000000000000000000010E8D90160015C0000000000409167760900800108E8D90135590A77940301148023490305000000F0E7D901506ACB761CC0CF7601000000EF7ACA76940301141D0000000020000008E8D90163590A7710E8D901000000000000000094030114406663760100000074E8D901A1366B76000000000000000070C25B0074E8D901B8366B76E0926E760000000000005300802349030000000070E8D9010000FFFF000100000000000000000000CF676976A822490301000000782349037CE8D901E82CF97670C25B00CF67697698EAD9017823490311000000B8455600B045560000000000FCE800004F88652EACE8D90182917275FCE8D901B0E8D9012795727500000000A486F602D8E8D901CD947275A486F60284E9D9011882F602E1947275000000001882F60284E9D901E0E8D901 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | WSExplorer 1.3.exe | C:\Users\admin\AppData\Local\Temp\BCGF76D.tmp | — | |
MD5:— | SHA256:— | |||
| 2136 | WSExplorer 1.3.exe | C:\Users\admin\AppData\Local\Temp\BCGF77F.tmp | — | |
MD5:— | SHA256:— | |||
| 2136 | WSExplorer 1.3.exe | C:\Users\admin\AppData\Local\Temp\WSockHooK.dll | executable | |
MD5:3AE6F9F299BC8E0B603561503D3DD38A | SHA256:FFB1679CEE959E7FCC2BD946D262F83134E288EDD4F4BD4FE6CAFBFCDD32C24B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report