| File name: | keylogger.exe_protected.exe |
| Full analysis: | https://app.any.run/tasks/988be3eb-fec7-4bb0-af8b-480c290714cf |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 22:28:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 5D41F6C5DDF4EEDD5C56B2C2AD52877C |
| SHA1: | 1CFD2D0C8E06DCE50F1523EF655E344838D9E809 |
| SHA256: | C83DC233F912376DCBCAE8F3E28621DB674D6BC2B8BC3FB6DC0C6FE6FFCFF7D4 |
| SSDEEP: | 3072:39eM6cTroRzBPH4rpIuJYXqsu+V5CH3dzKAbKfh:894fZ+rCtZbC |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks for external IP
- keylogger.exe_protected.exe (PID: 884)
- keylogger.exe_protected.exe (PID: 2788)
- keylogger.exe_protected.exe (PID: 1792)
- keylogger.exe_protected.exe (PID: 2136)
- keylogger.exe_protected.exe (PID: 2320)
- keylogger.exe_protected.exe (PID: 2892)
- keylogger.exe_protected.exe (PID: 3580)
- keylogger.exe_protected.exe (PID: 2272)
- keylogger.exe_protected.exe (PID: 2296)
- keylogger.exe_protected.exe (PID: 2888)
- keylogger.exe_protected.exe (PID: 3568)
- keylogger.exe_protected.exe (PID: 2640)
- keylogger.exe_protected.exe (PID: 1524)
- keylogger.exe_protected.exe (PID: 2568)
- keylogger.exe_protected.exe (PID: 924)
- keylogger.exe_protected.exe (PID: 3696)
- keylogger.exe_protected.exe (PID: 3488)
- keylogger.exe_protected.exe (PID: 3944)
- keylogger.exe_protected.exe (PID: 3548)
- keylogger.exe_protected.exe (PID: 2188)
- keylogger.exe_protected.exe (PID: 772)
- keylogger.exe_protected.exe (PID: 3020)
- keylogger.exe_protected.exe (PID: 3816)
- keylogger.exe_protected.exe (PID: 1912)
- keylogger.exe_protected.exe (PID: 2616)
- keylogger.exe_protected.exe (PID: 3172)
- keylogger.exe_protected.exe (PID: 2204)
- keylogger.exe_protected.exe (PID: 852)
- keylogger.exe_protected.exe (PID: 1732)
- keylogger.exe_protected.exe (PID: 2400)
- keylogger.exe_protected.exe (PID: 3032)
- keylogger.exe_protected.exe (PID: 3364)
- keylogger.exe_protected.exe (PID: 2264)
- keylogger.exe_protected.exe (PID: 1584)
- keylogger.exe_protected.exe (PID: 2392)
- keylogger.exe_protected.exe (PID: 1676)
- keylogger.exe_protected.exe (PID: 2848)
- keylogger.exe_protected.exe (PID: 3792)
- keylogger.exe_protected.exe (PID: 3824)
- keylogger.exe_protected.exe (PID: 940)
- keylogger.exe_protected.exe (PID: 2536)
- keylogger.exe_protected.exe (PID: 2624)
- keylogger.exe_protected.exe (PID: 2368)
- keylogger.exe_protected.exe (PID: 2208)
- keylogger.exe_protected.exe (PID: 2076)
- keylogger.exe_protected.exe (PID: 3080)
- keylogger.exe_protected.exe (PID: 1684)
- keylogger.exe_protected.exe (PID: 2852)
- keylogger.exe_protected.exe (PID: 2484)
- keylogger.exe_protected.exe (PID: 2696)
- keylogger.exe_protected.exe (PID: 1824)
- keylogger.exe_protected.exe (PID: 3300)
- keylogger.exe_protected.exe (PID: 2940)
- keylogger.exe_protected.exe (PID: 4024)
- keylogger.exe_protected.exe (PID: 2916)
- keylogger.exe_protected.exe (PID: 3884)
- keylogger.exe_protected.exe (PID: 3508)
- keylogger.exe_protected.exe (PID: 408)
- keylogger.exe_protected.exe (PID: 2732)
- keylogger.exe_protected.exe (PID: 2972)
- keylogger.exe_protected.exe (PID: 2748)
- keylogger.exe_protected.exe (PID: 3556)
- keylogger.exe_protected.exe (PID: 3312)
- keylogger.exe_protected.exe (PID: 3772)
- keylogger.exe_protected.exe (PID: 2284)
- keylogger.exe_protected.exe (PID: 3136)
- keylogger.exe_protected.exe (PID: 4032)
- keylogger.exe_protected.exe (PID: 1456)
- keylogger.exe_protected.exe (PID: 3576)
- keylogger.exe_protected.exe (PID: 956)
Executable content was dropped or overwritten
- keylogger.exe_protected.exe (PID: 884)
- keylogger.exe_protected.exe (PID: 1792)
- keylogger.exe_protected.exe (PID: 2136)
- keylogger.exe_protected.exe (PID: 2320)
- keylogger.exe_protected.exe (PID: 2892)
- keylogger.exe_protected.exe (PID: 3580)
- keylogger.exe_protected.exe (PID: 2272)
- keylogger.exe_protected.exe (PID: 2296)
- keylogger.exe_protected.exe (PID: 2888)
- keylogger.exe_protected.exe (PID: 3568)
- keylogger.exe_protected.exe (PID: 2640)
- keylogger.exe_protected.exe (PID: 2788)
- keylogger.exe_protected.exe (PID: 1524)
- keylogger.exe_protected.exe (PID: 2568)
- keylogger.exe_protected.exe (PID: 924)
- keylogger.exe_protected.exe (PID: 3696)
- keylogger.exe_protected.exe (PID: 3488)
- keylogger.exe_protected.exe (PID: 3548)
- keylogger.exe_protected.exe (PID: 3944)
- keylogger.exe_protected.exe (PID: 2188)
- keylogger.exe_protected.exe (PID: 772)
- keylogger.exe_protected.exe (PID: 3020)
- keylogger.exe_protected.exe (PID: 3816)
- keylogger.exe_protected.exe (PID: 1912)
- keylogger.exe_protected.exe (PID: 2616)
- keylogger.exe_protected.exe (PID: 852)
- keylogger.exe_protected.exe (PID: 3172)
- keylogger.exe_protected.exe (PID: 2204)
- keylogger.exe_protected.exe (PID: 2400)
- keylogger.exe_protected.exe (PID: 1732)
- keylogger.exe_protected.exe (PID: 3032)
- keylogger.exe_protected.exe (PID: 2264)
- keylogger.exe_protected.exe (PID: 3364)
- keylogger.exe_protected.exe (PID: 1584)
- keylogger.exe_protected.exe (PID: 1676)
- keylogger.exe_protected.exe (PID: 2848)
- keylogger.exe_protected.exe (PID: 2392)
- keylogger.exe_protected.exe (PID: 3824)
- keylogger.exe_protected.exe (PID: 940)
- keylogger.exe_protected.exe (PID: 2536)
- keylogger.exe_protected.exe (PID: 2624)
- keylogger.exe_protected.exe (PID: 2208)
- keylogger.exe_protected.exe (PID: 2368)
- keylogger.exe_protected.exe (PID: 2076)
- keylogger.exe_protected.exe (PID: 2852)
- keylogger.exe_protected.exe (PID: 3080)
- keylogger.exe_protected.exe (PID: 1684)
- keylogger.exe_protected.exe (PID: 3792)
- keylogger.exe_protected.exe (PID: 2484)
- keylogger.exe_protected.exe (PID: 2696)
- keylogger.exe_protected.exe (PID: 1824)
- keylogger.exe_protected.exe (PID: 3300)
- keylogger.exe_protected.exe (PID: 2940)
- keylogger.exe_protected.exe (PID: 4024)
- keylogger.exe_protected.exe (PID: 2916)
- keylogger.exe_protected.exe (PID: 3884)
- keylogger.exe_protected.exe (PID: 3508)
- keylogger.exe_protected.exe (PID: 2732)
- keylogger.exe_protected.exe (PID: 408)
- keylogger.exe_protected.exe (PID: 2972)
- keylogger.exe_protected.exe (PID: 2748)
- keylogger.exe_protected.exe (PID: 3556)
- keylogger.exe_protected.exe (PID: 3312)
- keylogger.exe_protected.exe (PID: 3772)
- keylogger.exe_protected.exe (PID: 2284)
- keylogger.exe_protected.exe (PID: 3136)
- keylogger.exe_protected.exe (PID: 4032)
- keylogger.exe_protected.exe (PID: 1456)
- keylogger.exe_protected.exe (PID: 3576)
Starts itself from another location
- keylogger.exe_protected.exe (PID: 884)
Application launched itself
- keylogger.exe_protected.exe (PID: 2788)
- keylogger.exe_protected.exe (PID: 1792)
- keylogger.exe_protected.exe (PID: 2136)
- keylogger.exe_protected.exe (PID: 2320)
- keylogger.exe_protected.exe (PID: 2892)
- keylogger.exe_protected.exe (PID: 3580)
- keylogger.exe_protected.exe (PID: 2272)
- keylogger.exe_protected.exe (PID: 2296)
- keylogger.exe_protected.exe (PID: 3568)
- keylogger.exe_protected.exe (PID: 2888)
- keylogger.exe_protected.exe (PID: 2640)
- keylogger.exe_protected.exe (PID: 1524)
- keylogger.exe_protected.exe (PID: 2568)
- keylogger.exe_protected.exe (PID: 924)
- keylogger.exe_protected.exe (PID: 3696)
- keylogger.exe_protected.exe (PID: 3488)
- keylogger.exe_protected.exe (PID: 3548)
- keylogger.exe_protected.exe (PID: 3944)
- keylogger.exe_protected.exe (PID: 2188)
- keylogger.exe_protected.exe (PID: 772)
- keylogger.exe_protected.exe (PID: 3816)
- keylogger.exe_protected.exe (PID: 3020)
- keylogger.exe_protected.exe (PID: 1912)
- keylogger.exe_protected.exe (PID: 2616)
- keylogger.exe_protected.exe (PID: 2204)
- keylogger.exe_protected.exe (PID: 3172)
- keylogger.exe_protected.exe (PID: 2400)
- keylogger.exe_protected.exe (PID: 852)
- keylogger.exe_protected.exe (PID: 1732)
- keylogger.exe_protected.exe (PID: 3032)
- keylogger.exe_protected.exe (PID: 3364)
- keylogger.exe_protected.exe (PID: 2264)
- keylogger.exe_protected.exe (PID: 1584)
- keylogger.exe_protected.exe (PID: 3792)
- keylogger.exe_protected.exe (PID: 1676)
- keylogger.exe_protected.exe (PID: 2848)
- keylogger.exe_protected.exe (PID: 2392)
- keylogger.exe_protected.exe (PID: 3824)
- keylogger.exe_protected.exe (PID: 940)
- keylogger.exe_protected.exe (PID: 2536)
- keylogger.exe_protected.exe (PID: 2624)
- keylogger.exe_protected.exe (PID: 2208)
- keylogger.exe_protected.exe (PID: 2368)
- keylogger.exe_protected.exe (PID: 2076)
- keylogger.exe_protected.exe (PID: 2852)
- keylogger.exe_protected.exe (PID: 1684)
- keylogger.exe_protected.exe (PID: 2484)
- keylogger.exe_protected.exe (PID: 2696)
- keylogger.exe_protected.exe (PID: 1824)
- keylogger.exe_protected.exe (PID: 3300)
- keylogger.exe_protected.exe (PID: 2940)
- keylogger.exe_protected.exe (PID: 4024)
- keylogger.exe_protected.exe (PID: 2916)
- keylogger.exe_protected.exe (PID: 3884)
- keylogger.exe_protected.exe (PID: 3508)
- keylogger.exe_protected.exe (PID: 2732)
- keylogger.exe_protected.exe (PID: 408)
- keylogger.exe_protected.exe (PID: 2972)
- keylogger.exe_protected.exe (PID: 2748)
- keylogger.exe_protected.exe (PID: 3556)
- keylogger.exe_protected.exe (PID: 3312)
- keylogger.exe_protected.exe (PID: 3772)
- keylogger.exe_protected.exe (PID: 3080)
- keylogger.exe_protected.exe (PID: 2284)
- keylogger.exe_protected.exe (PID: 3136)
- keylogger.exe_protected.exe (PID: 4032)
- keylogger.exe_protected.exe (PID: 1456)
- keylogger.exe_protected.exe (PID: 3576)
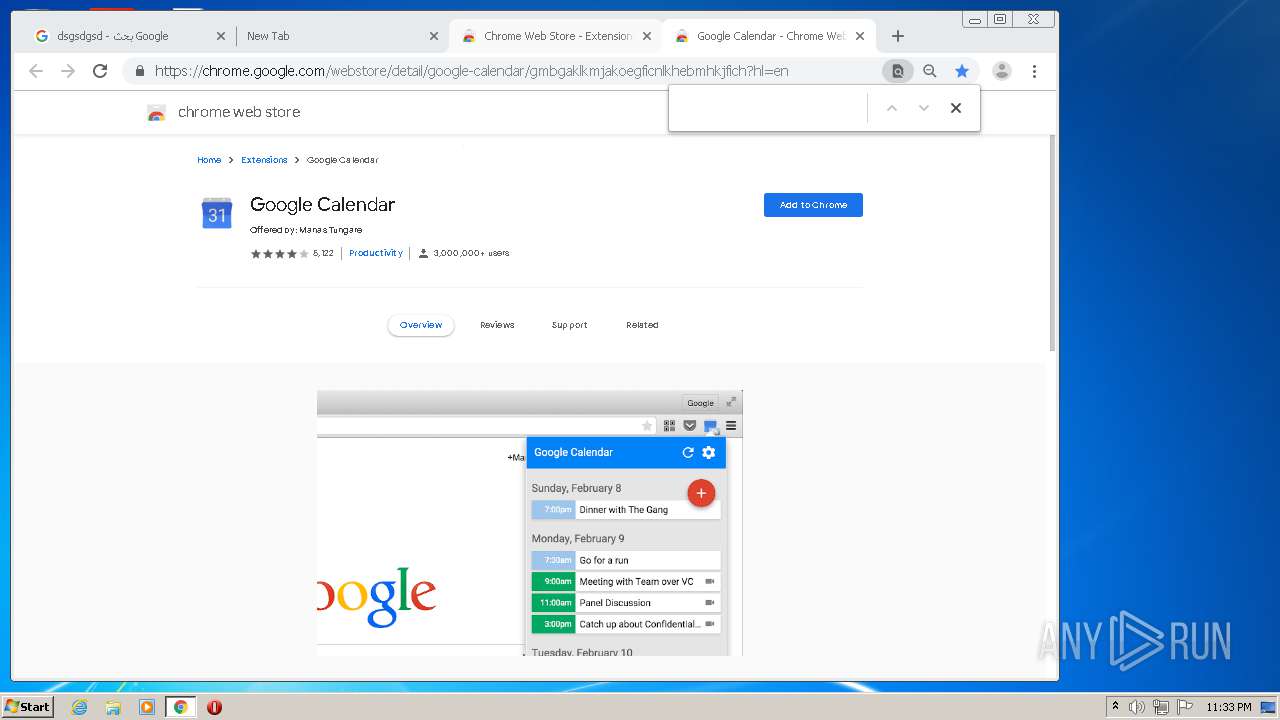
Searches for installed software
- keylogger.exe_protected.exe (PID: 884)
- keylogger.exe_protected.exe (PID: 2788)
- keylogger.exe_protected.exe (PID: 2136)
- keylogger.exe_protected.exe (PID: 1792)
- keylogger.exe_protected.exe (PID: 2320)
- keylogger.exe_protected.exe (PID: 2892)
- keylogger.exe_protected.exe (PID: 3580)
- keylogger.exe_protected.exe (PID: 2272)
- keylogger.exe_protected.exe (PID: 2296)
- keylogger.exe_protected.exe (PID: 3568)
- keylogger.exe_protected.exe (PID: 2640)
- keylogger.exe_protected.exe (PID: 1524)
- keylogger.exe_protected.exe (PID: 2888)
- keylogger.exe_protected.exe (PID: 924)
- keylogger.exe_protected.exe (PID: 3696)
- keylogger.exe_protected.exe (PID: 3488)
- keylogger.exe_protected.exe (PID: 2568)
- keylogger.exe_protected.exe (PID: 3548)
- keylogger.exe_protected.exe (PID: 3944)
- keylogger.exe_protected.exe (PID: 2188)
- keylogger.exe_protected.exe (PID: 772)
- keylogger.exe_protected.exe (PID: 3816)
- keylogger.exe_protected.exe (PID: 1912)
- keylogger.exe_protected.exe (PID: 2616)
- keylogger.exe_protected.exe (PID: 3172)
- keylogger.exe_protected.exe (PID: 3020)
- keylogger.exe_protected.exe (PID: 2204)
- keylogger.exe_protected.exe (PID: 2400)
- keylogger.exe_protected.exe (PID: 3032)
- keylogger.exe_protected.exe (PID: 852)
- keylogger.exe_protected.exe (PID: 1732)
- keylogger.exe_protected.exe (PID: 3364)
- keylogger.exe_protected.exe (PID: 2264)
- keylogger.exe_protected.exe (PID: 1584)
- keylogger.exe_protected.exe (PID: 2392)
- keylogger.exe_protected.exe (PID: 1676)
- keylogger.exe_protected.exe (PID: 3792)
- keylogger.exe_protected.exe (PID: 940)
- keylogger.exe_protected.exe (PID: 2536)
- keylogger.exe_protected.exe (PID: 3824)
- keylogger.exe_protected.exe (PID: 2624)
- keylogger.exe_protected.exe (PID: 2208)
- keylogger.exe_protected.exe (PID: 2368)
- keylogger.exe_protected.exe (PID: 2076)
- keylogger.exe_protected.exe (PID: 3080)
- keylogger.exe_protected.exe (PID: 1684)
- keylogger.exe_protected.exe (PID: 2852)
- keylogger.exe_protected.exe (PID: 2484)
- keylogger.exe_protected.exe (PID: 2848)
- keylogger.exe_protected.exe (PID: 2696)
- keylogger.exe_protected.exe (PID: 1824)
- keylogger.exe_protected.exe (PID: 3300)
- keylogger.exe_protected.exe (PID: 2940)
- keylogger.exe_protected.exe (PID: 2916)
- keylogger.exe_protected.exe (PID: 3884)
- keylogger.exe_protected.exe (PID: 4024)
- keylogger.exe_protected.exe (PID: 2732)
- keylogger.exe_protected.exe (PID: 408)
- keylogger.exe_protected.exe (PID: 3508)
- keylogger.exe_protected.exe (PID: 2748)
- keylogger.exe_protected.exe (PID: 3556)
- keylogger.exe_protected.exe (PID: 3312)
- keylogger.exe_protected.exe (PID: 2972)
- keylogger.exe_protected.exe (PID: 3136)
- keylogger.exe_protected.exe (PID: 3772)
- keylogger.exe_protected.exe (PID: 1456)
- keylogger.exe_protected.exe (PID: 2284)
- keylogger.exe_protected.exe (PID: 3576)
- keylogger.exe_protected.exe (PID: 956)
- keylogger.exe_protected.exe (PID: 4032)
INFO
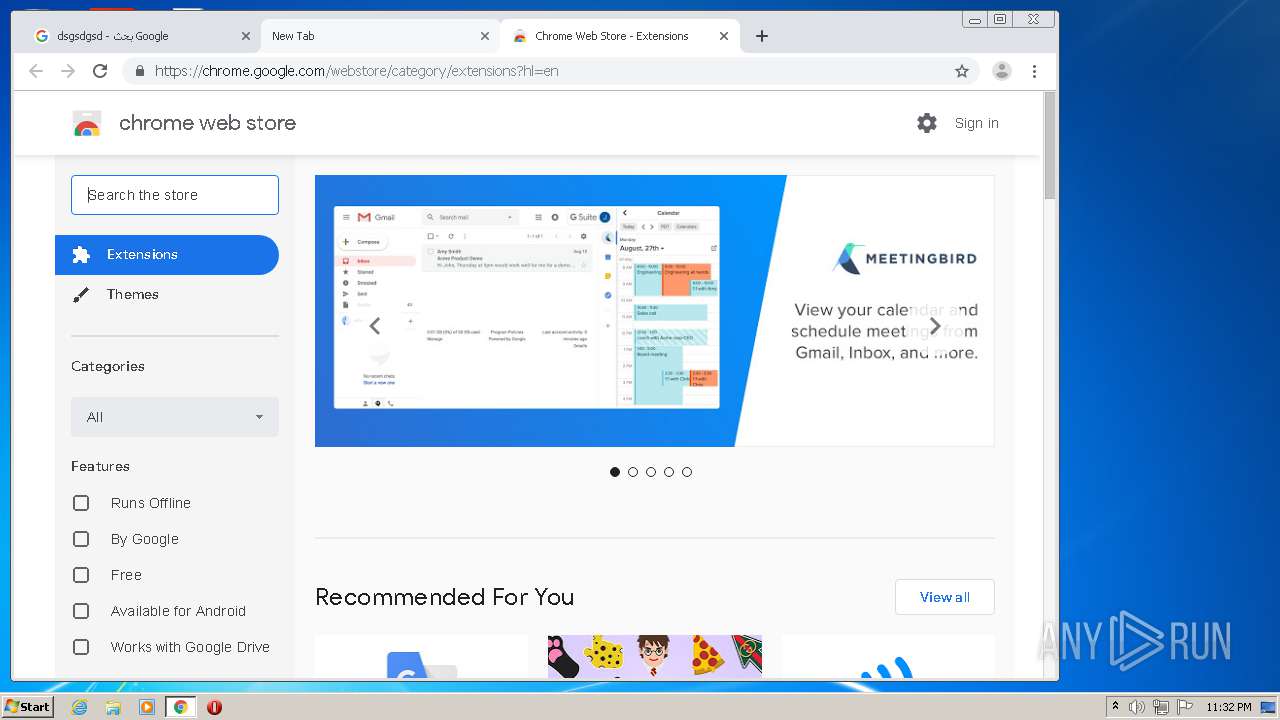
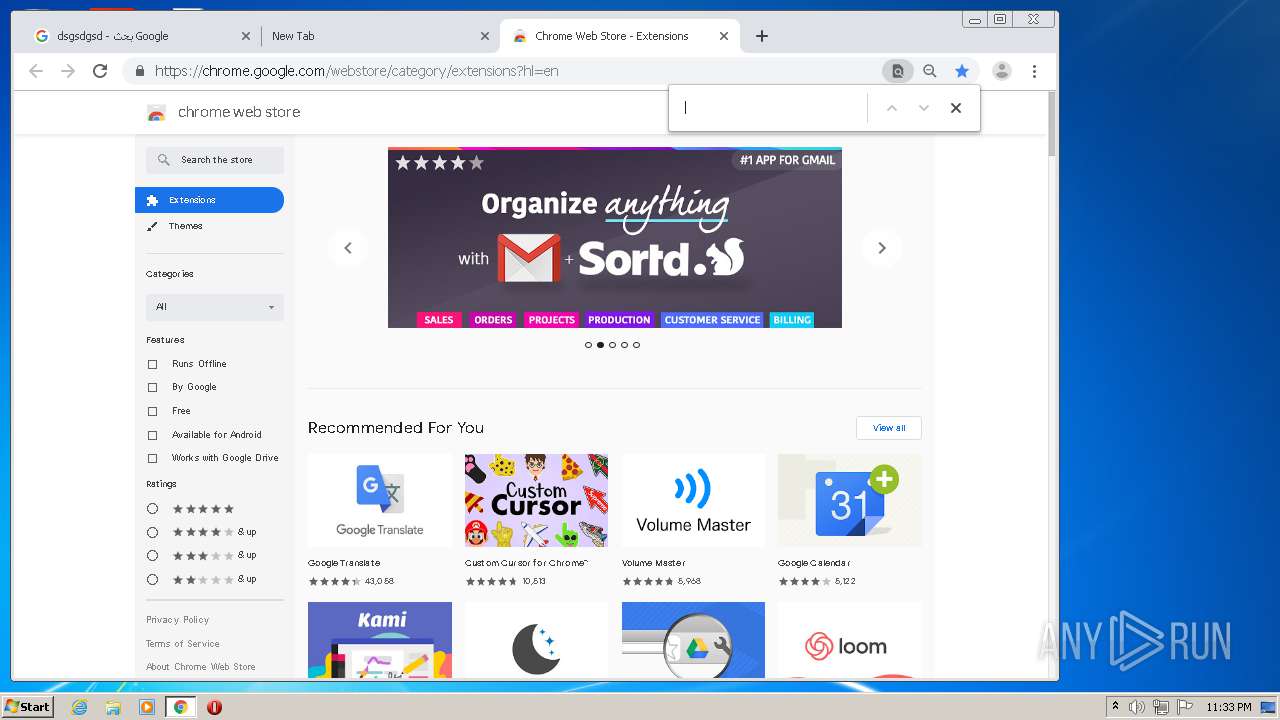
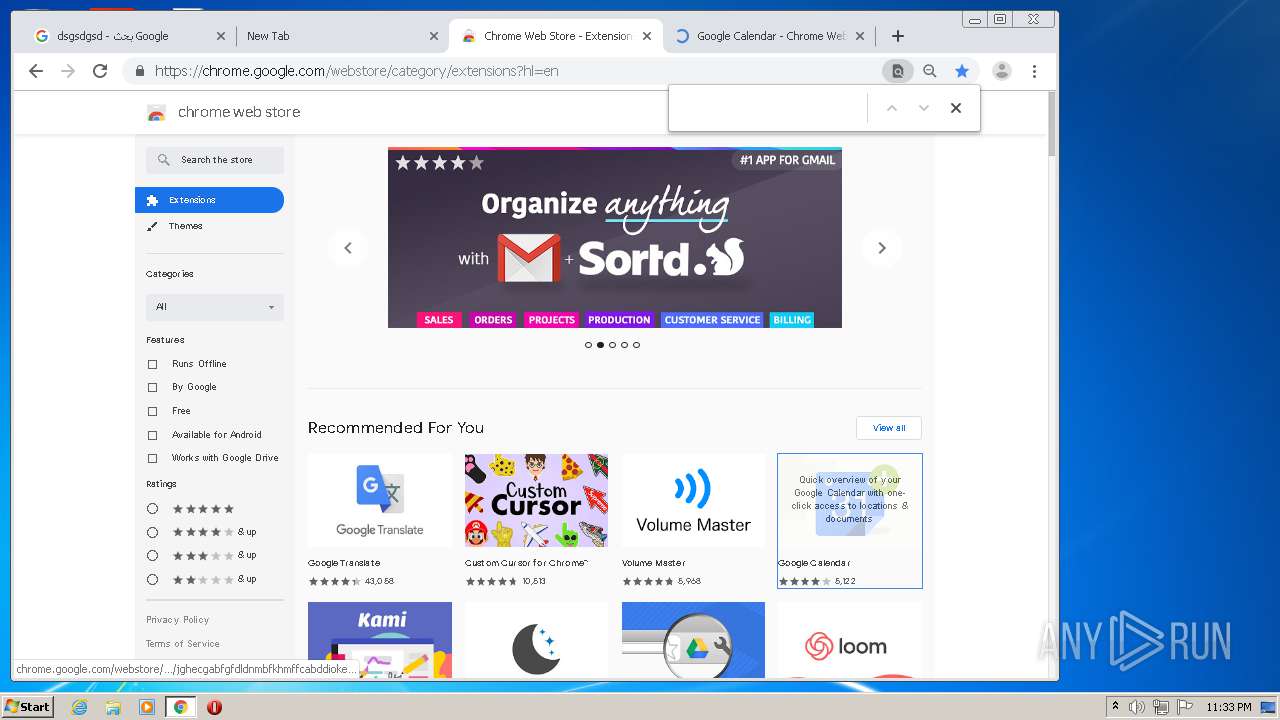
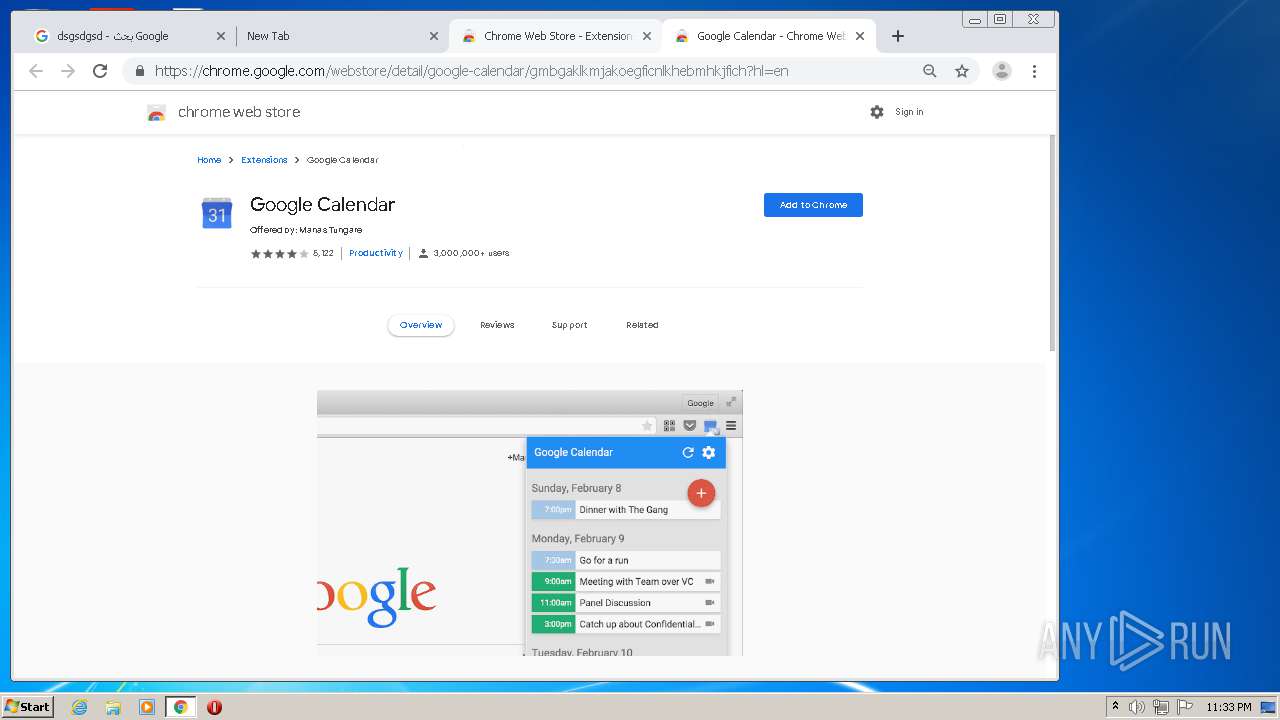
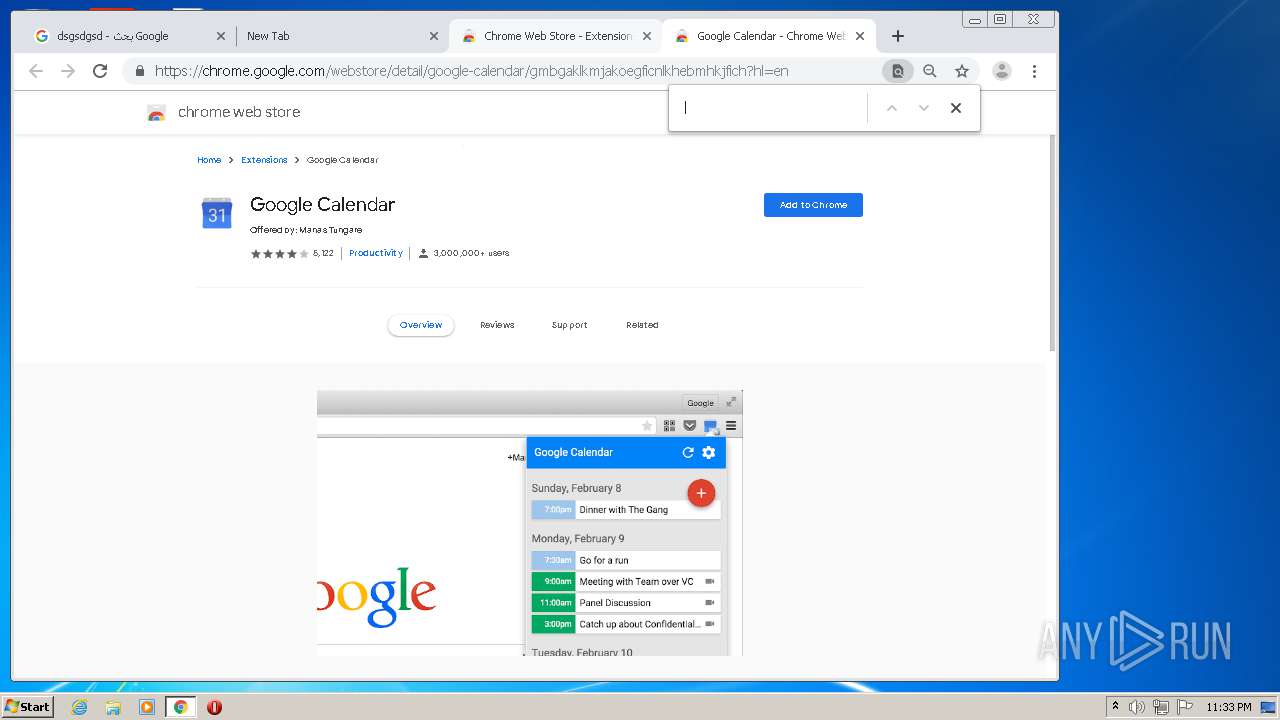
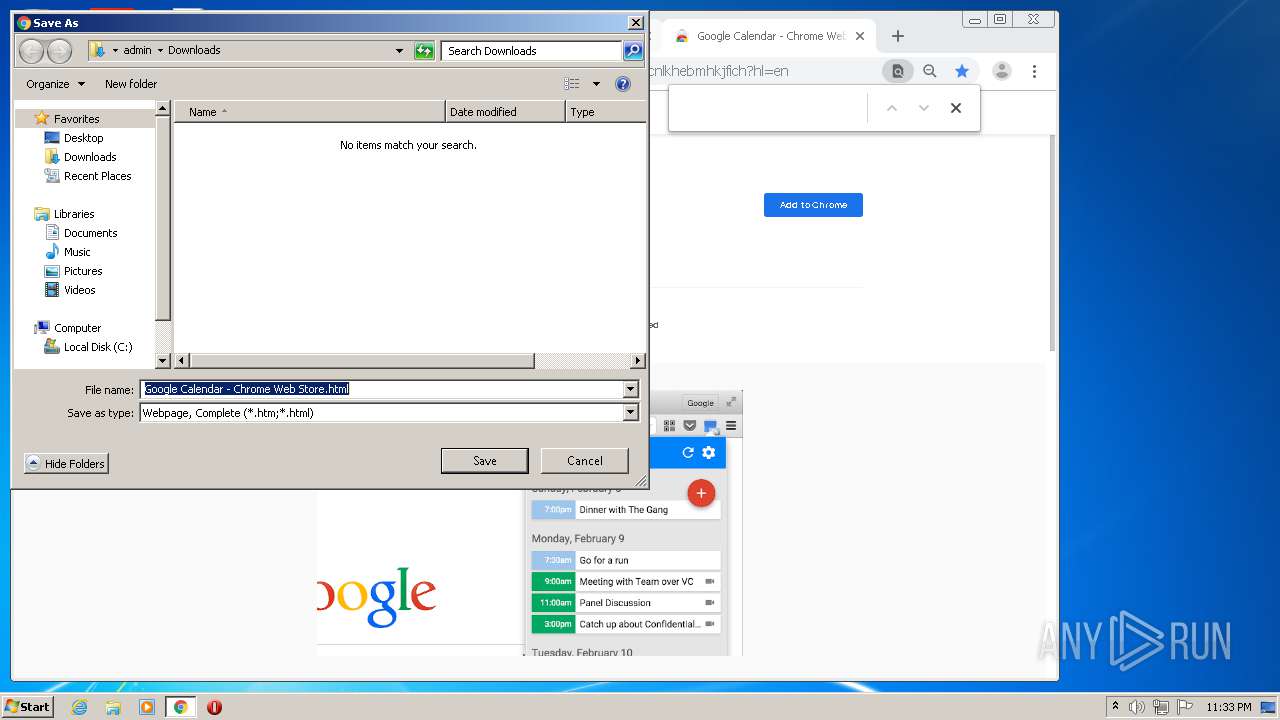
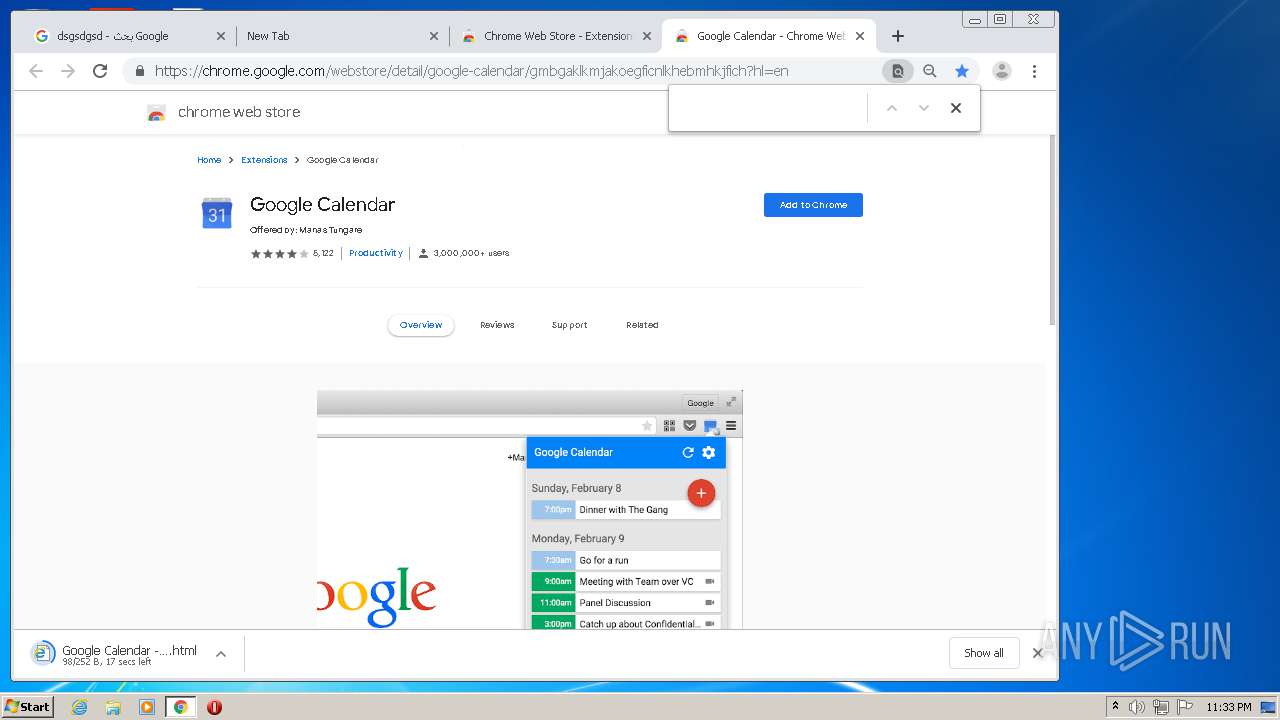
Manual execution by user
- chrome.exe (PID: 2620)
Application launched itself
- chrome.exe (PID: 2620)
Reads the hosts file
- chrome.exe (PID: 2620)
- chrome.exe (PID: 3648)
Reads settings of System Certificates
- chrome.exe (PID: 3648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:09 00:20:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 115712 |
| InitializedDataSize: | 7680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e36e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Control ACLs Program |
| CompanyName: | Microsoft @ 2015 |
| FileDescription: | Control ACLs Program |
| FileVersion: | 1.0.0.0 |
| InternalName: | keylogger.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| LegalTrademarks: | Windows |
| OriginalFileName: | keylogger.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Aug-2020 22:20:46 |
| Comments: | Control ACLs Program |
| CompanyName: | Microsoft @ 2015 |
| FileDescription: | Control ACLs Program |
| FileVersion: | 1.0.0.0 |
| InternalName: | keylogger.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| LegalTrademarks: | Windows |
| OriginalFilename: | keylogger.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 08-Aug-2020 22:20:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0001C374 | 0x0001C400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.69875 |
.rsrc | 0x00020000 | 0x00001B50 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.07462 |
.reloc | 0x00022000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.12398 | 5160 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.0815 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
136
Monitored processes
95
Malicious processes
70
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1204 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 408 | "C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe" C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | keylogger.exe_protected.exe | ||||||||||||
User: admin Company: Microsoft @ 2015 Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,15407834267175101807,12767333763104487108,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1416394131253391416 --mojo-platform-channel-handle=3292 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | "C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe" C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | keylogger.exe_protected.exe | ||||||||||||
User: admin Company: Microsoft @ 2015 Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 852 | "C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe" C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | keylogger.exe_protected.exe | ||||||||||||
User: admin Company: Microsoft @ 2015 Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 884 | "C:\Users\admin\AppData\Local\Temp\keylogger.exe_protected.exe" | C:\Users\admin\AppData\Local\Temp\keylogger.exe_protected.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft @ 2015 Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 924 | "C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe" C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | keylogger.exe_protected.exe | ||||||||||||
User: admin Company: Microsoft @ 2015 Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 940 | "C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe" C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | keylogger.exe_protected.exe | ||||||||||||
User: admin Company: Microsoft @ 2015 Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 956 | "C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe" C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | keylogger.exe_protected.exe | ||||||||||||
User: admin Company: Microsoft @ 2015 Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,15407834267175101807,12767333763104487108,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17591848103689575228 --mojo-platform-channel-handle=3668 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
43 869
Read events
42 736
Write events
1 126
Delete events
7
Modification events
| (PID) Process: | (884) keylogger.exe_protected.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\keylogger_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (884) keylogger.exe_protected.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\keylogger_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (884) keylogger.exe_protected.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\keylogger_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (884) keylogger.exe_protected.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\keylogger_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (884) keylogger.exe_protected.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\keylogger_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (884) keylogger.exe_protected.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\keylogger_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (884) keylogger.exe_protected.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\keylogger_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (884) keylogger.exe_protected.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\keylogger_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (884) keylogger.exe_protected.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\keylogger_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (884) keylogger.exe_protected.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\keylogger_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
69
Suspicious files
47
Text files
611
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1792 | keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | executable | |
MD5:— | SHA256:— | |||
| 884 | keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | executable | |
MD5:— | SHA256:— | |||
| 2320 | keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | executable | |
MD5:— | SHA256:— | |||
| 2788 | keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | executable | |
MD5:— | SHA256:— | |||
| 2136 | keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | executable | |
MD5:— | SHA256:— | |||
| 3568 | keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | executable | |
MD5:— | SHA256:— | |||
| 3580 | keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | executable | |
MD5:— | SHA256:— | |||
| 2892 | keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | executable | |
MD5:— | SHA256:— | |||
| 2272 | keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | executable | |
MD5:— | SHA256:— | |||
| 2296 | keylogger.exe_protected.exe | C:\Users\admin\AppData\Roaming\keylogger.exe_protected.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
139
TCP/UDP connections
234
DNS requests
24
Threats
280
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2136 | keylogger.exe_protected.exe | GET | 200 | 116.202.55.106:80 | http://icanhazip.com/ | IN | text | 15 b | shared |
1792 | keylogger.exe_protected.exe | GET | 200 | 116.202.55.106:80 | http://icanhazip.com/ | IN | text | 15 b | shared |
2892 | keylogger.exe_protected.exe | GET | 200 | 116.202.55.106:80 | http://icanhazip.com/ | IN | text | 15 b | shared |
2320 | keylogger.exe_protected.exe | GET | 200 | 116.202.55.106:80 | http://icanhazip.com/ | IN | text | 15 b | shared |
3580 | keylogger.exe_protected.exe | GET | 200 | 116.202.55.106:80 | http://icanhazip.com/ | IN | text | 15 b | shared |
2296 | keylogger.exe_protected.exe | GET | 200 | 116.202.55.106:80 | http://icanhazip.com/ | IN | text | 15 b | shared |
884 | keylogger.exe_protected.exe | GET | 200 | 116.202.55.106:80 | http://icanhazip.com/ | IN | text | 15 b | shared |
3568 | keylogger.exe_protected.exe | GET | 200 | 116.202.55.106:80 | http://icanhazip.com/ | IN | text | 15 b | shared |
2272 | keylogger.exe_protected.exe | GET | 200 | 116.202.55.106:80 | http://icanhazip.com/ | IN | text | 15 b | shared |
2136 | keylogger.exe_protected.exe | GET | 404 | 104.31.3.184:80 | http://puu.sh/jMSLc.txt | US | text | 30 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
884 | keylogger.exe_protected.exe | 104.31.3.184:80 | puu.sh | Cloudflare Inc | US | suspicious |
884 | keylogger.exe_protected.exe | 116.202.55.106:80 | icanhazip.com | 334,Udyog Vihar | IN | malicious |
884 | keylogger.exe_protected.exe | 64.233.184.109:587 | smtp.gmail.com | Google Inc. | US | whitelisted |
2788 | keylogger.exe_protected.exe | 104.31.3.184:80 | puu.sh | Cloudflare Inc | US | suspicious |
2788 | keylogger.exe_protected.exe | 116.202.55.106:80 | icanhazip.com | 334,Udyog Vihar | IN | malicious |
2788 | keylogger.exe_protected.exe | 64.233.184.109:587 | smtp.gmail.com | Google Inc. | US | whitelisted |
1792 | keylogger.exe_protected.exe | 104.31.3.184:80 | puu.sh | Cloudflare Inc | US | suspicious |
1792 | keylogger.exe_protected.exe | 116.202.55.106:80 | icanhazip.com | 334,Udyog Vihar | IN | malicious |
1792 | keylogger.exe_protected.exe | 64.233.184.109:587 | smtp.gmail.com | Google Inc. | US | whitelisted |
2136 | keylogger.exe_protected.exe | 104.31.3.184:80 | puu.sh | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
puu.sh |
| shared |
icanhazip.com |
| shared |
smtp.gmail.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
884 | keylogger.exe_protected.exe | Potentially Bad Traffic | ET INFO GET to Puu.sh for TXT File with Minimal Headers |
884 | keylogger.exe_protected.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
884 | keylogger.exe_protected.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2788 | keylogger.exe_protected.exe | Potentially Bad Traffic | ET INFO GET to Puu.sh for TXT File with Minimal Headers |
2788 | keylogger.exe_protected.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
2788 | keylogger.exe_protected.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
1792 | keylogger.exe_protected.exe | Potentially Bad Traffic | ET INFO GET to Puu.sh for TXT File with Minimal Headers |
1792 | keylogger.exe_protected.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
1792 | keylogger.exe_protected.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2136 | keylogger.exe_protected.exe | Potentially Bad Traffic | ET INFO GET to Puu.sh for TXT File with Minimal Headers |
70 ETPRO signatures available at the full report