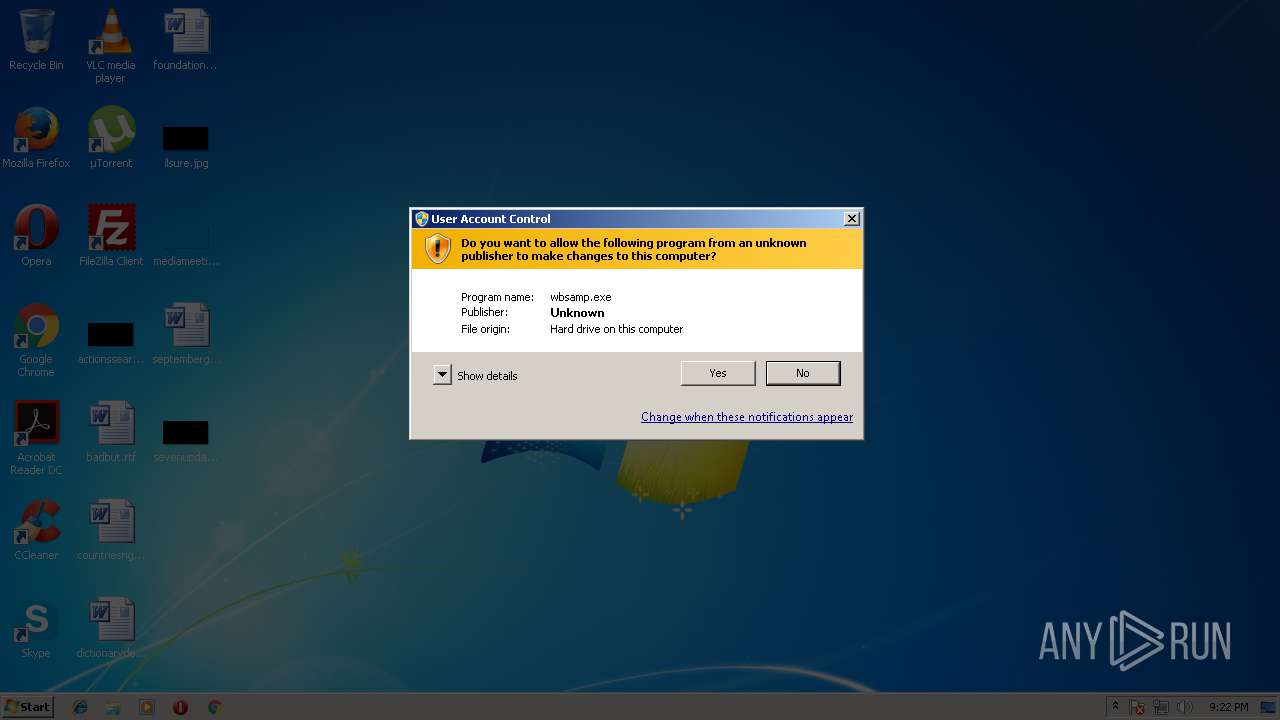
| File name: | wbsamp.exe |
| Full analysis: | https://app.any.run/tasks/2c01035b-4d83-4b34-b48d-d9d027fc52aa |
| Verdict: | Malicious activity |
| Analysis date: | May 07, 2018, 20:22:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B46D2DFE59352AE5E19F86C16F08A935 |
| SHA1: | 2F8BD63DE3AFC44B63983011B087ACBB87CDBF1E |
| SHA256: | C839278B93FFAAA9D44C95C654A77F03EEDEE2F9127091742C88E5C6EC4E7D2B |
| SSDEEP: | 24576:z593FKArIG/mDL/H0qca8gh75auGkfpQ3E8gC5xGOYwPhZwnUElM:zHIwsjHzh8gYuGGa3E8gC53PLrElM |
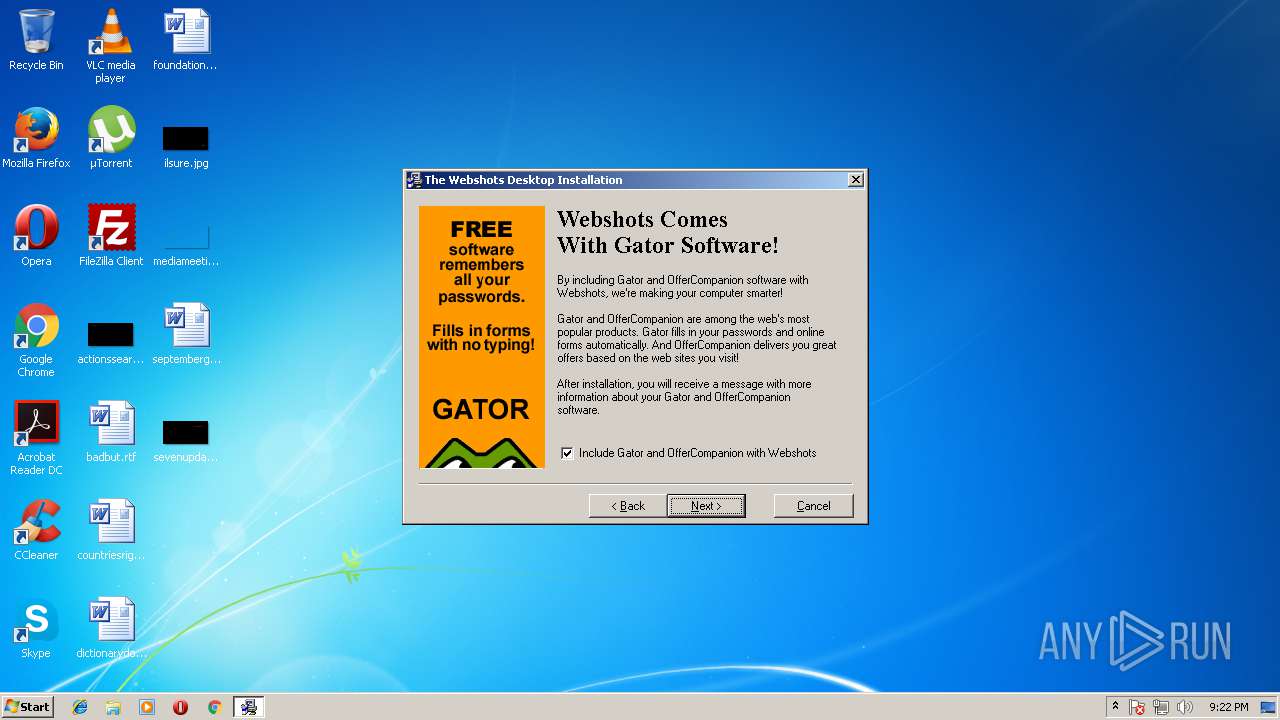
MALICIOUS
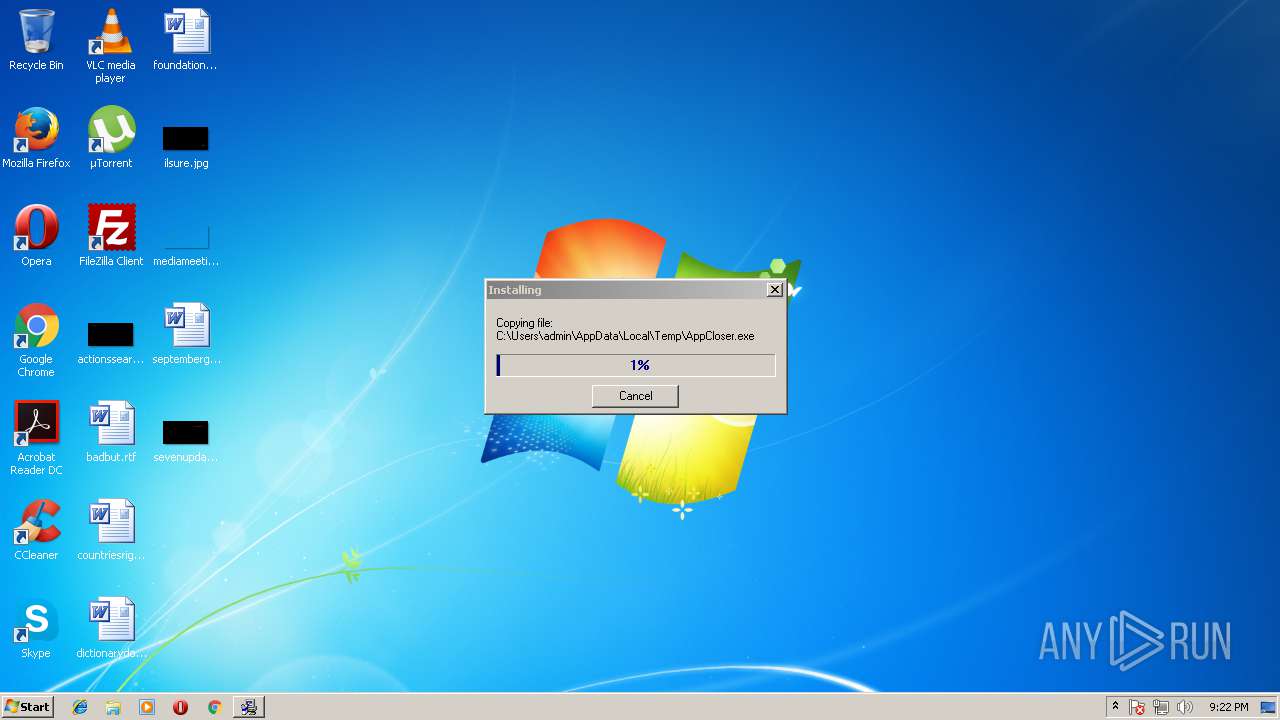
Application loaded dropped or rewritten executable
- wbsamp.exe (PID: 3380)
- WEBSHOTS.SCR (PID: 3172)
- WebshotsTray.exe (PID: 2568)
Application was dropped or rewritten from another process
- APPCLO~1.EXE (PID: 2212)
- Swebexec.exe (PID: 3048)
- fsg.exe (PID: 2416)
- WEBSHOTS.SCR (PID: 3172)
- WebshotsTray.exe (PID: 2568)
Writes to a start menu file
- WEBSHOTS.SCR (PID: 3172)
Changes the autorun value in the registry
- fsg.exe (PID: 2416)
SUSPICIOUS
Removes files from Windows directory
- wbsamp.exe (PID: 3380)
Creates files in the Windows directory
- wbsamp.exe (PID: 3380)
- Swebexec.exe (PID: 3048)
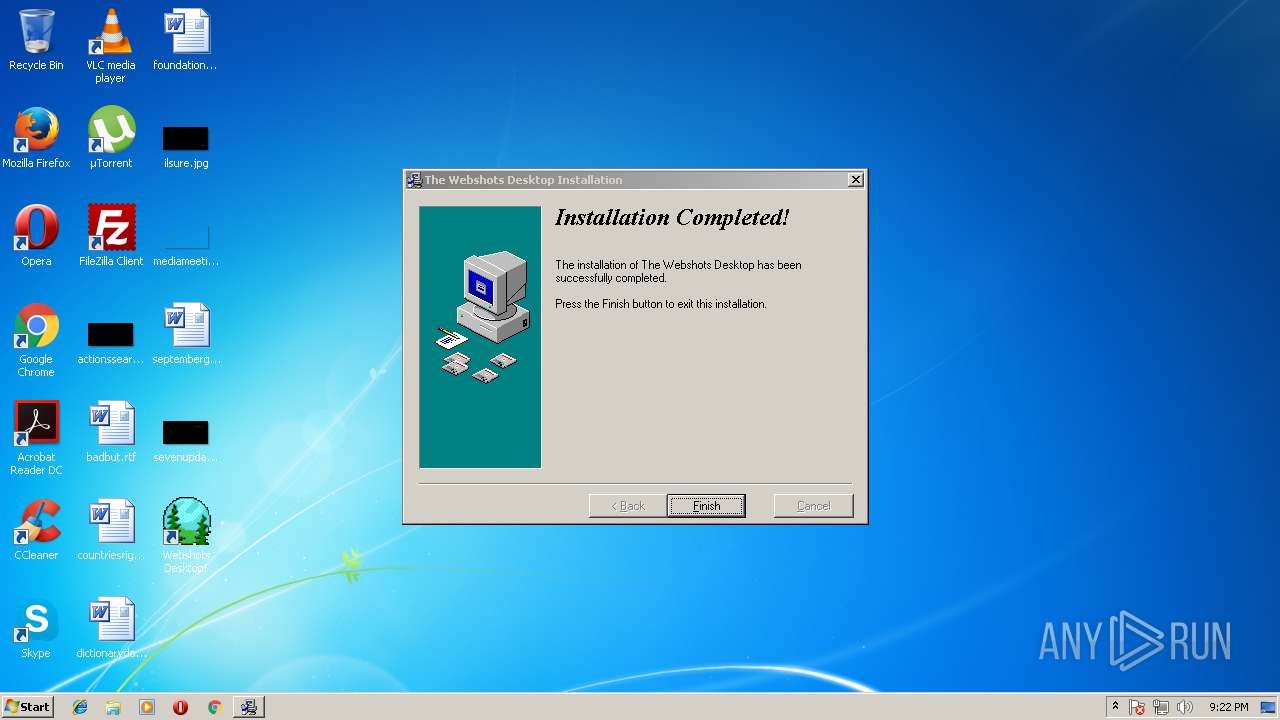
Creates a software uninstall entry
- wbsamp.exe (PID: 3380)
Creates files in the program directory
- wbsamp.exe (PID: 3380)
- WEBSHOTS.SCR (PID: 3172)
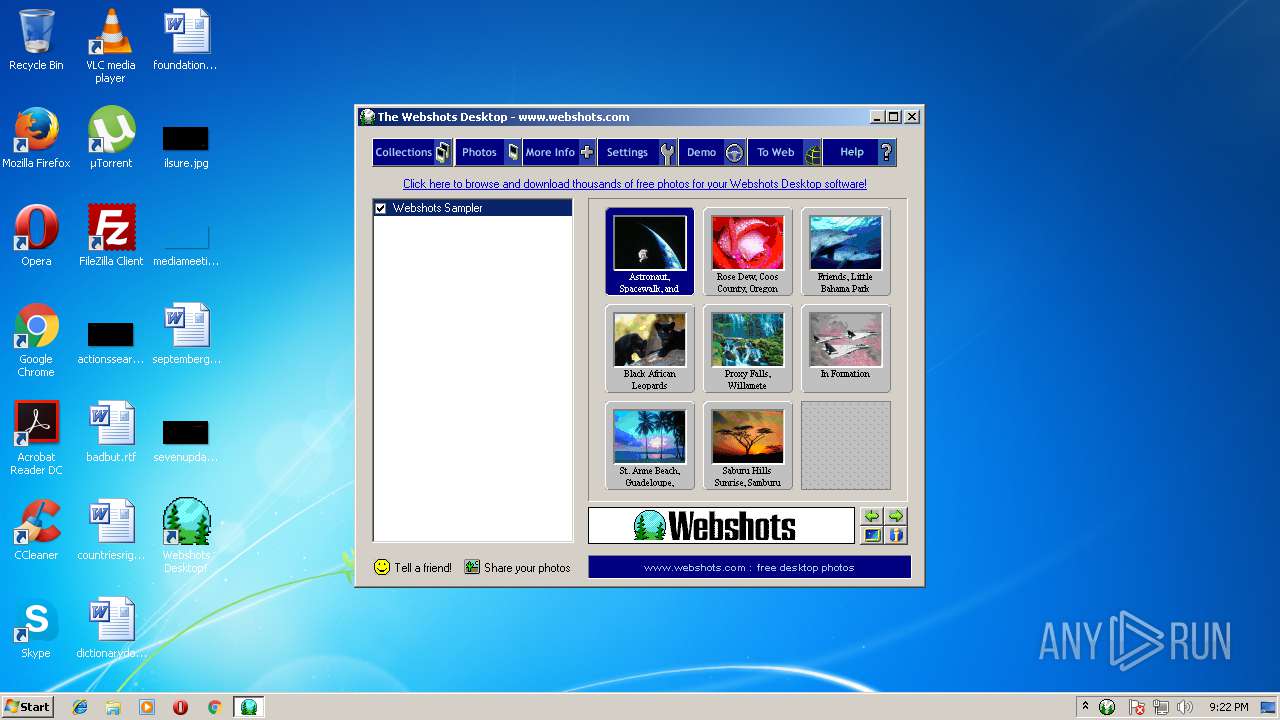
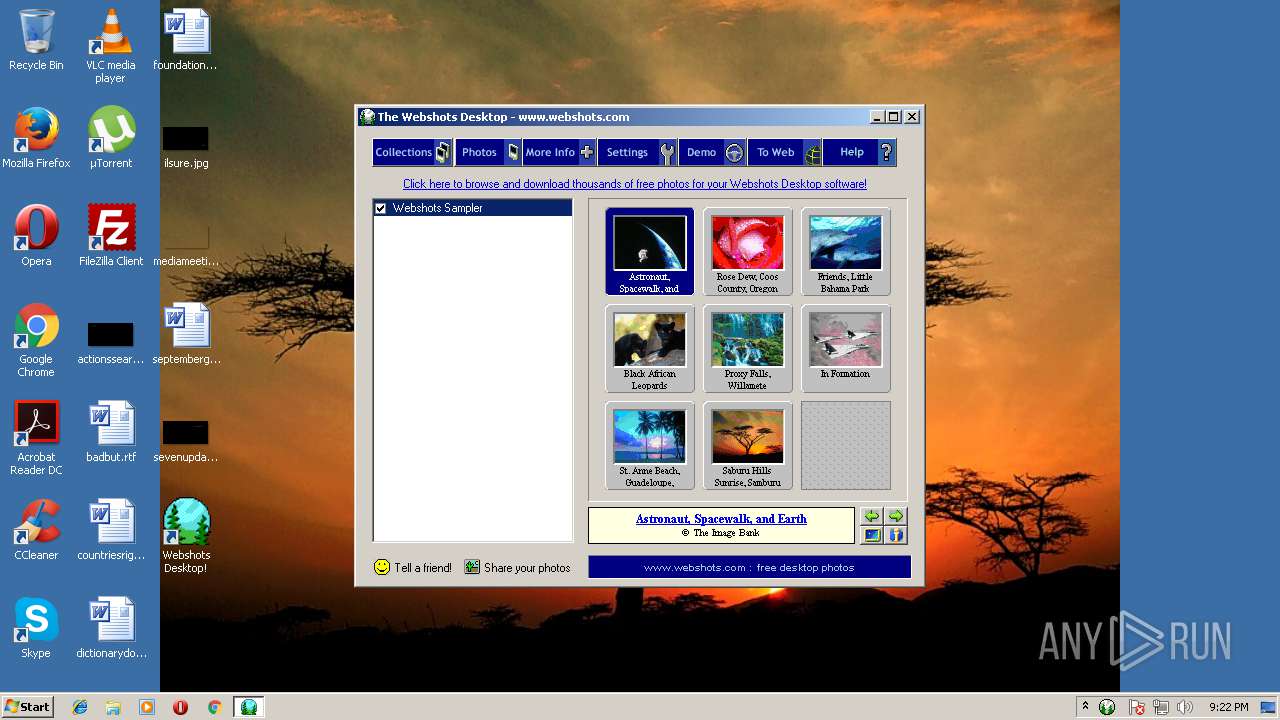
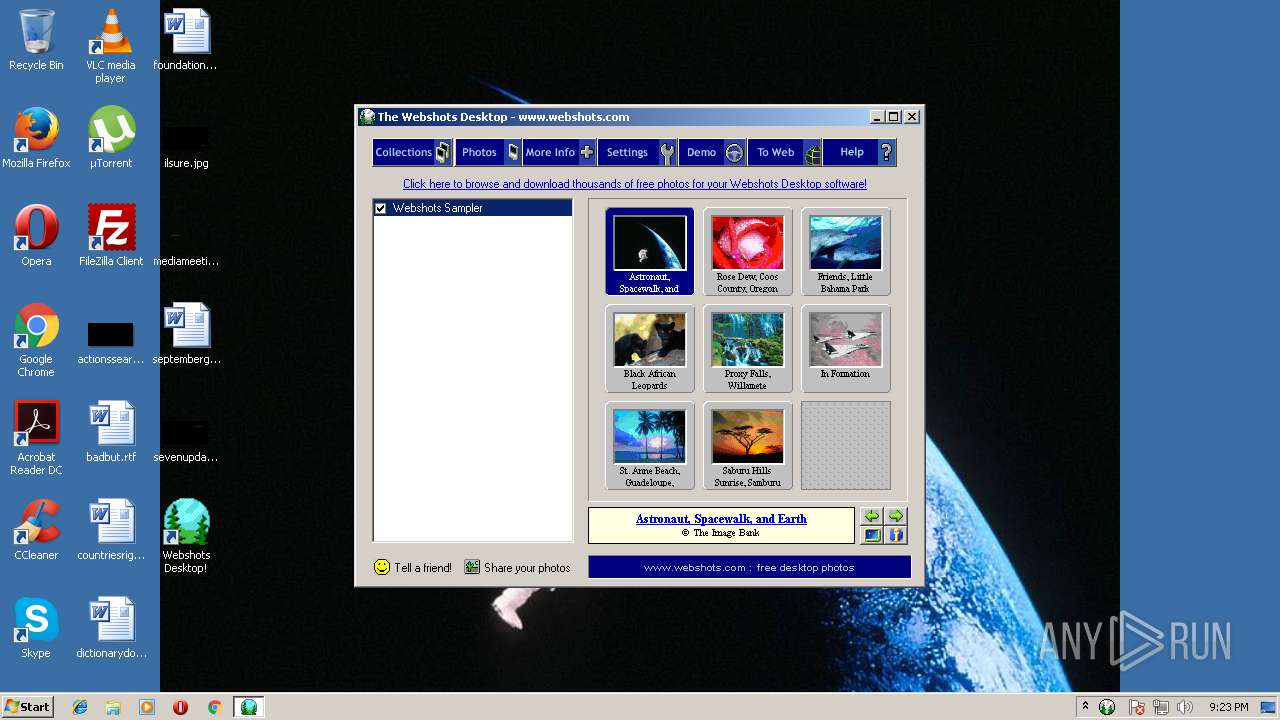
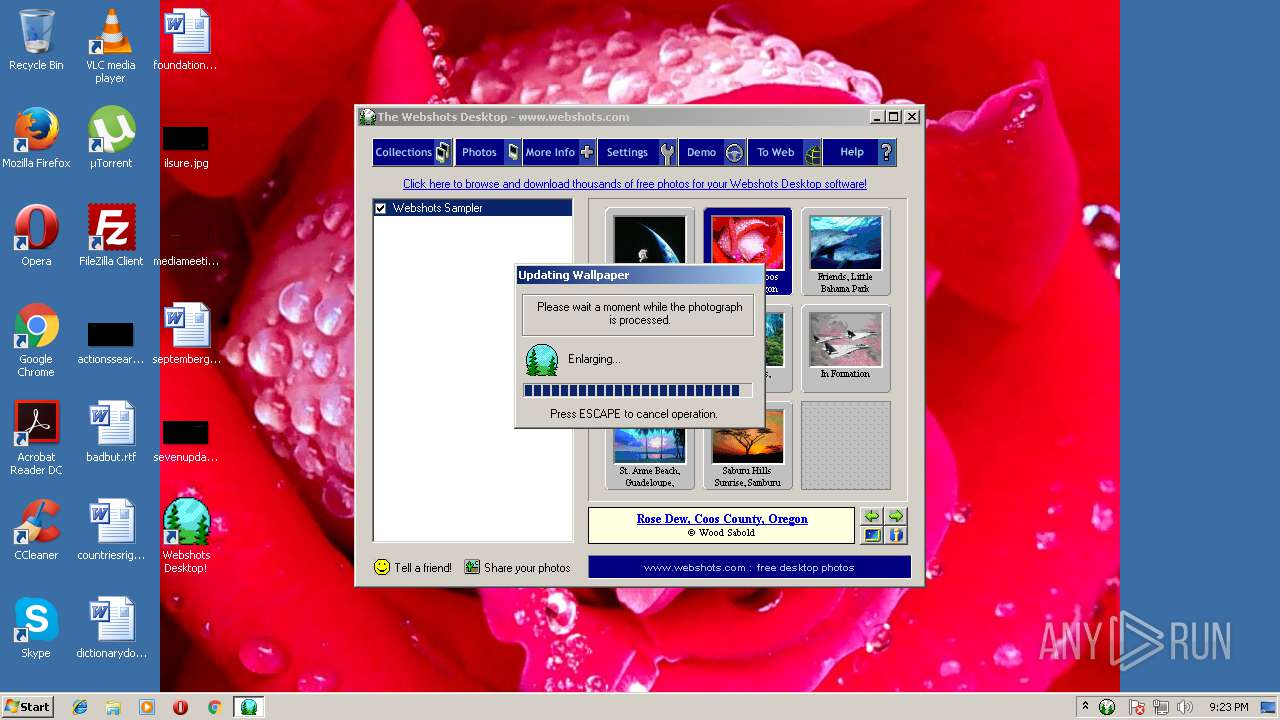
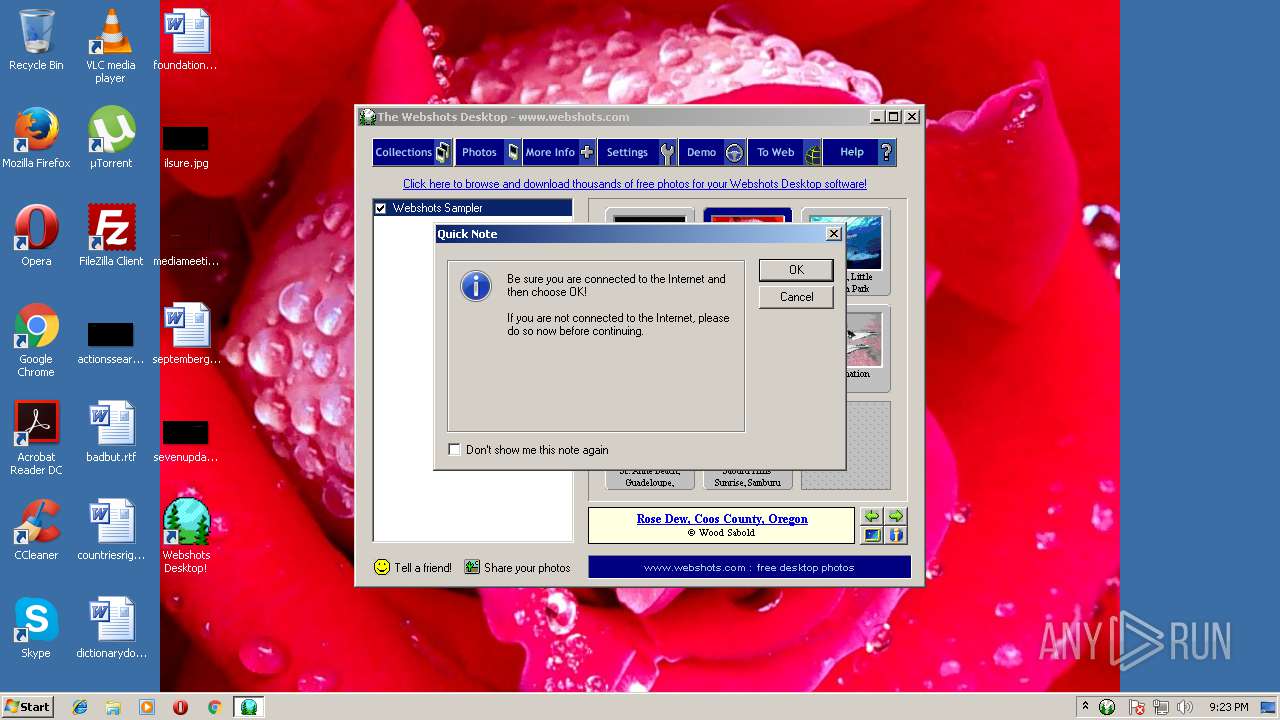
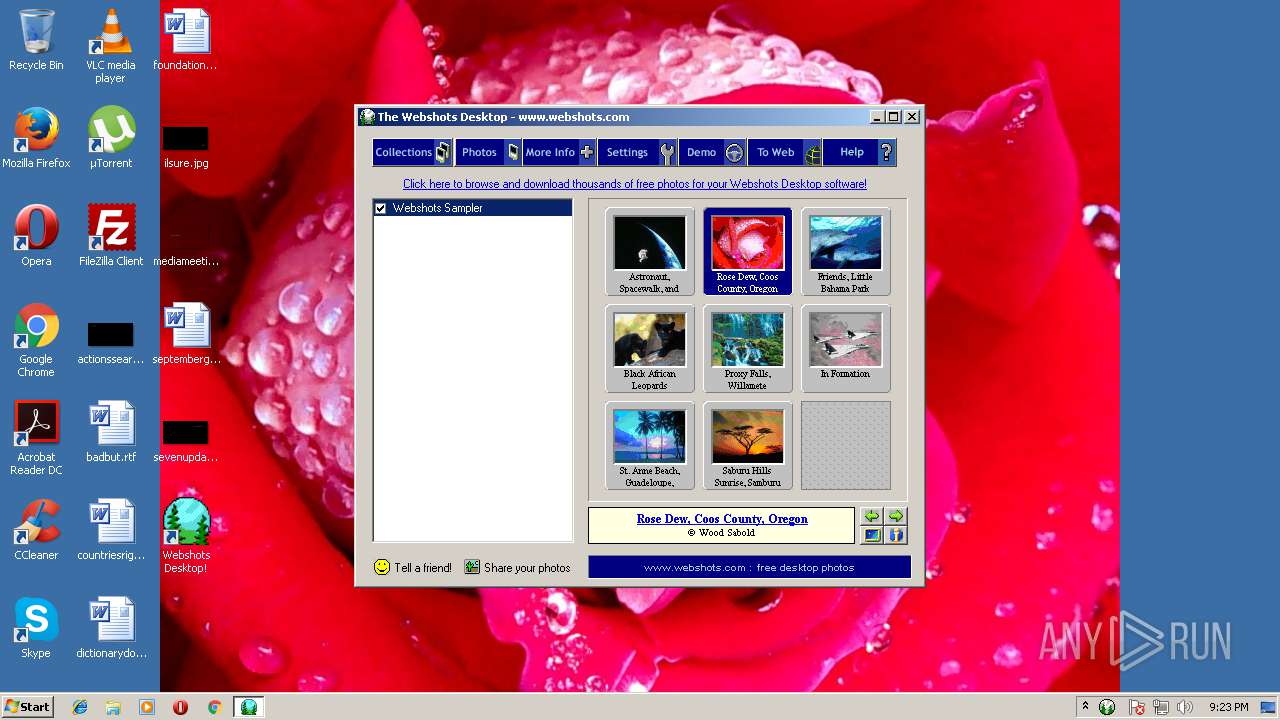
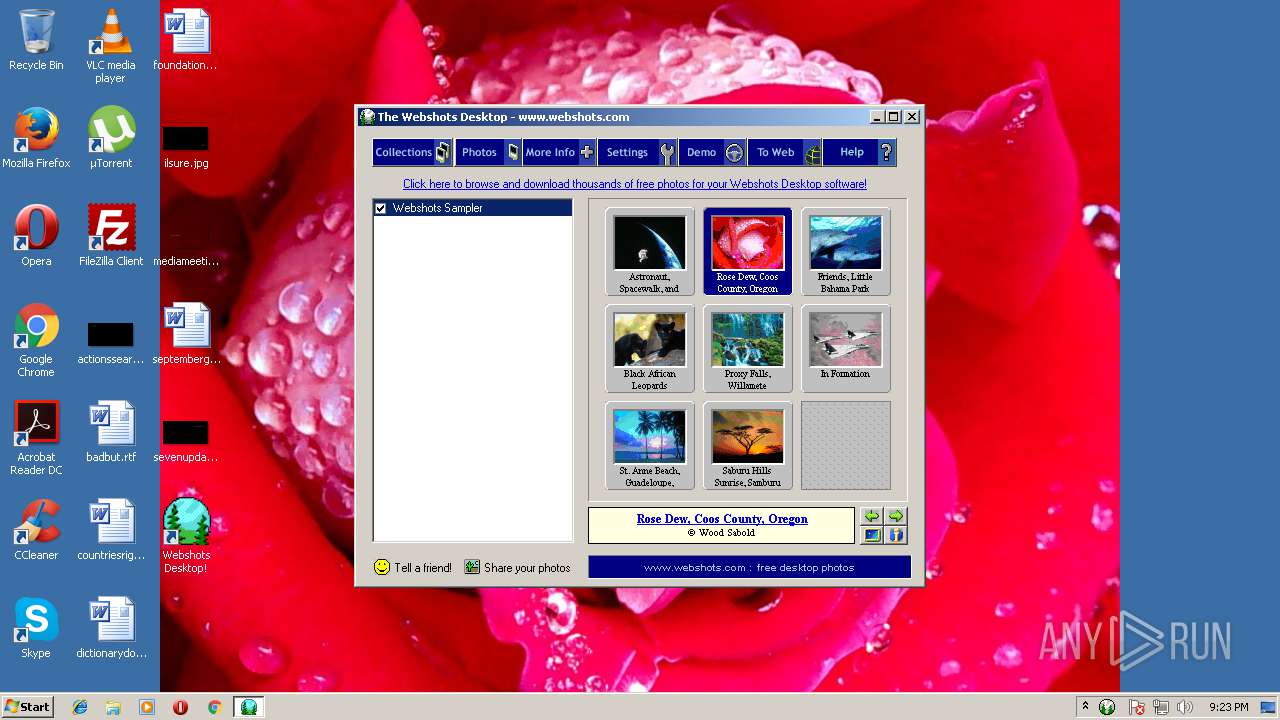
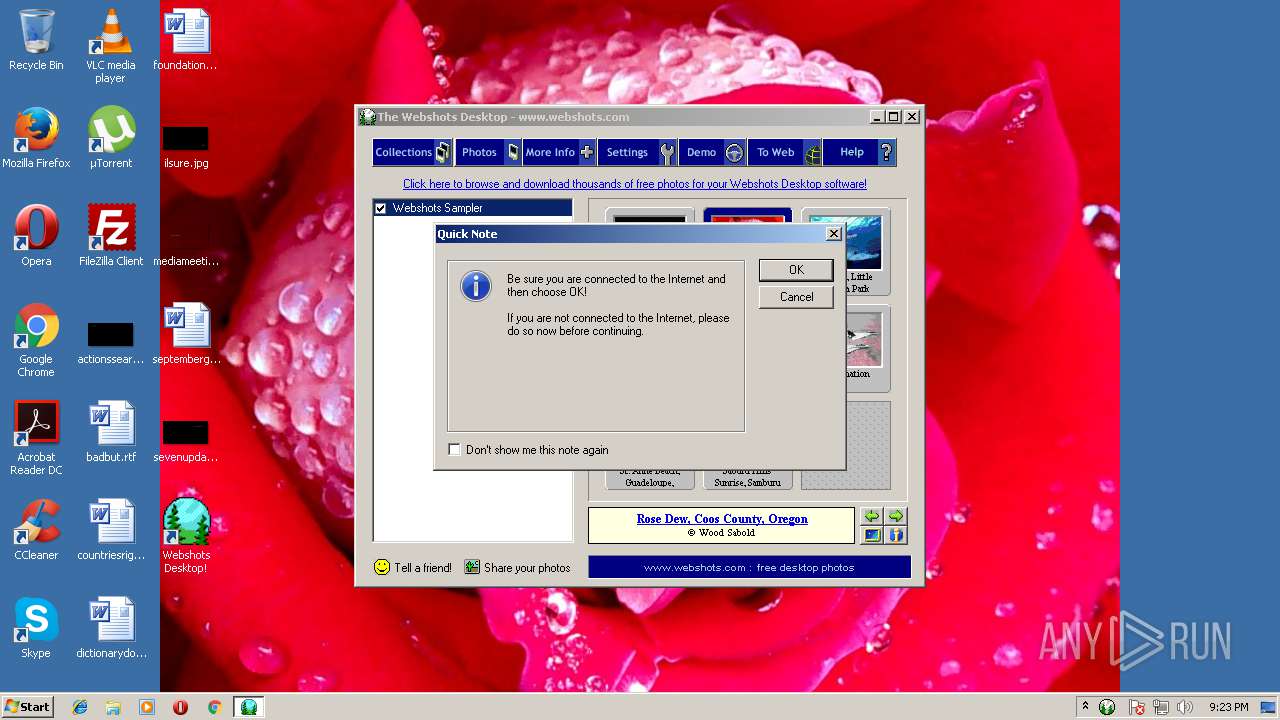
Changes the desktop background image
- WEBSHOTS.SCR (PID: 3172)
Starts application with an unusual extension
- Swebexec.exe (PID: 3048)
Modifies the open verb of a shell class
- WEBSHOTS.SCR (PID: 3172)
Creates files in the user directory
- WEBSHOTS.SCR (PID: 3172)
INFO
Dropped object may contain URL's
- wbsamp.exe (PID: 3380)
- chrome.exe (PID: 4012)
Changes settings of System certificates
- chrome.exe (PID: 4012)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 4012)
Application launched itself
- chrome.exe (PID: 4012)
Adds / modifies Windows certificates
- chrome.exe (PID: 4012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Wise Installer executable (91.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (5.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1998:02:19 18:19:45+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5.1 |
| CodeSize: | 7680 |
| InitializedDataSize: | 3584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x21c5 |
| OSVersion: | 4 |
| ImageVersion: | 4 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Feb-1998 17:19:45 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 19-Feb-1998 17:19:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00001CF1 | 0x00001E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.27387 |
.rdata | 0x00003000 | 0x000005B9 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.79408 |
.data | 0x00004000 | 0x000003B4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.19125 |
.rsrc | 0x00005000 | 0x000003A0 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.02325 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.37233 | 744 | UNKNOWN | English - United States | RT_ICON |
108 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_MainWndProc@16 | 1 | 0x00002805 |
_StubFileWrite@12 | 2 | 0x00002CDC |
Total processes
49
Monitored processes
14
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Users\admin\AppData\Local\Temp\wbsamp.exe" | C:\Users\admin\AppData\Local\Temp\wbsamp.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 2212 | "C:\Users\admin\AppData\Local\Temp\APPCLO~1.EXE" | C:\Users\admin\AppData\Local\Temp\APPCLO~1.EXE | — | wbsamp.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1588,7337402122637121697,8963996651196768947,131072 --service-pipe-token=4D5409B4D3579E1EE512A8A1F57901EE --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=4D5409B4D3579E1EE512A8A1F57901EE --renderer-client-id=3 --mojo-platform-channel-handle=1600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\AppData\Local\Temp\fsg\fsg.exe" | C:\Users\admin\AppData\Local\Temp\fsg\fsg.exe | wbsamp.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.5.0 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=61.0.3163.100 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6d857d7c,0x6d857da4,0x6d857d8c | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2568 | C:\PROGRA~1\Webshots\WebshotsTray.exe | C:\PROGRA~1\Webshots\WebshotsTray.exe | — | WEBSHOTS.SCR | |||||||||||
User: admin Company: The Webshots Corporation Integrity Level: HIGH Description: Webshots Desktop Tray Application Exit code: 0 Version: 1.3.0.3181 Modules
| |||||||||||||||
| 3048 | "C:\PROGRA~1\Webshots\Swebexec.exe" | C:\PROGRA~1\Webshots\Swebexec.exe | — | wbsamp.exe | |||||||||||
User: admin Company: The Webshots Corporation Integrity Level: HIGH Description: Swebexec Exit code: 0 Version: 1.3.0.3181 Modules
| |||||||||||||||
| 3172 | C:\Windows\WEBSHOTS.SCR /c | C:\Windows\WEBSHOTS.SCR | Swebexec.exe | ||||||||||||
User: admin Company: Auralis, Inc. Integrity Level: HIGH Description: Webshots32 Exit code: 0 Version: 1.3.0.3181 Modules
| |||||||||||||||
| 3228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1588,7337402122637121697,8963996651196768947,131072 --service-pipe-token=74B847198C3F75F6157BC41089A69B18 --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=74B847198C3F75F6157BC41089A69B18 --renderer-client-id=2 --mojo-platform-channel-handle=1752 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 3280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1588,7337402122637121697,8963996651196768947,131072 --disable-direct-composition --use-gl=swiftshader-webgl --supports-dual-gpus=false --gpu-driver-bug-workarounds=9,12,13,22,23,24,27,49,84 --disable-gl-extensions="GL_KHR_blend_equation_advanced GL_KHR_blend_equation_advanced_coherent" --disable-accelerated-video-decode --gpu-vendor-id=0x1234 --gpu-device-id=0x1111 --gpu-driver-vendor="Google Inc." --gpu-driver-version=3.3.0.2 --gpu-driver-date=2017/04/07 --service-request-channel-token=A85D6FE0CC1F3CA3C869FE000C8EC550 --mojo-platform-channel-handle=3520 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
Total events
811
Read events
644
Write events
162
Delete events
5
Modification events
| (PID) Process: | (3380) wbsamp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Windows\~GLC0000.TMP | |||
| (PID) Process: | (3380) wbsamp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | Start Page |
Value: http://www.webshots.com/r/internal/start/client/RAND | |||
| (PID) Process: | (3380) wbsamp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Webshots |
| Operation: | write | Name: | DisplayName |
Value: Webshots! | |||
| (PID) Process: | (3380) wbsamp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Webshots |
| Operation: | write | Name: | UninstallString |
Value: C:\Windows\WebshotsUninstall.exe | |||
| (PID) Process: | (3380) wbsamp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3380) wbsamp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2416) fsg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | StashedGEF |
Value: 64 | |||
| (PID) Process: | (2416) fsg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{21FFB6C0-0DA1-11D5-A9D5-00500413153C} |
| Operation: | write | Name: | GEF |
Value: 64 | |||
| (PID) Process: | (2416) fsg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Gator.com\Trickler |
| Operation: | write | Name: | FirstStartValue |
Value: 1 | |||
| (PID) Process: | (2416) fsg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Gator.com\Gator\dyn |
| Operation: | write | Name: | PdpFirstStart |
Value: NEW | |||
Executable files
13
Suspicious files
30
Text files
101
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3380 | wbsamp.exe | C:\Users\admin\AppData\Local\Temp\~GLH0002.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | wbsamp.exe | C:\Users\admin\AppData\Local\Temp\~GLH0003.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | wbsamp.exe | C:\Users\admin\AppData\Local\Temp\~GLH0004.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | wbsamp.exe | C:\Users\admin\AppData\Local\Temp\~GLH0005.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | wbsamp.exe | C:\Program Files\Webshots\Languages\~GLH0006.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | wbsamp.exe | C:\Program Files\Webshots\~GLH0007.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | wbsamp.exe | C:\Program Files\Webshots\~GLH0008.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | wbsamp.exe | C:\Windows\~GLH0009.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | wbsamp.exe | C:\Windows\~GLH000a.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | wbsamp.exe | C:\Program Files\Webshots\~GLH000b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
28
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 216.58.205.234:80 | http://fonts.googleapis.com/css?family=Roboto:300,400 | US | text | 604 b | whitelisted |
— | — | GET | 200 | 54.68.177.229:80 | http://www.webshots.com/zchannels/img/ic_web_email.png | US | image | 654 b | whitelisted |
— | — | GET | 200 | 151.101.2.107:80 | http://cdn.connatix.com/min/connatix.renderer.infeed.min.js | US | text | 767 b | whitelisted |
— | — | GET | 200 | 54.68.177.229:80 | http://www.webshots.com/zchannels/app.css | US | text | 13.9 Kb | whitelisted |
— | — | GET | 200 | 52.222.149.52:80 | http://d188578y7fxb.cloudfront.net/af6d8662155d6a1e05dd4a5d2fe2d84b54bf6af100db3683409e6f0566602546/1024x768.jpg | US | image | 120 Kb | whitelisted |
— | — | GET | 200 | 54.68.177.229:80 | http://www.webshots.com/redir.cgi?type=tellfriend&v=3181&u=V1525724564&d1=none&d2=none&l1=9&l2=1&tdp=0&h=-1&sw=1280&tc=1&os=36 | US | html | 9.96 Kb | whitelisted |
— | — | GET | 200 | 54.68.177.229:80 | http://www.webshots.com/zchannels/css/channels-bootstrap.css | US | text | 124 Kb | whitelisted |
— | — | GET | 200 | 54.68.177.229:80 | http://www.webshots.com/zchannels/img/ic_web_tumblr.png | US | image | 414 b | whitelisted |
— | — | GET | 200 | 172.217.22.2:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 27.0 Kb | whitelisted |
— | — | GET | 200 | 54.68.177.229:80 | http://www.webshots.com/zchannels/img/ic_web_pinterest.png | US | image | 786 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 52.73.237.192:80 | tr.connatix.com | Amazon.com, Inc. | US | unknown |
— | — | 52.73.237.192:443 | tr.connatix.com | Amazon.com, Inc. | US | unknown |
— | — | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
— | — | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 54.68.177.229:80 | www.webshots.com | Amazon.com, Inc. | US | unknown |
— | — | 216.58.205.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 151.101.2.107:80 | cdn.connatix.com | Fastly | US | malicious |
— | — | 216.58.214.67:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 2.21.160.128:80 | s7.addthis.com | Akamai International B.V. | — | whitelisted |
— | — | 172.217.22.2:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gs.gator.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
www.webshots.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.connatix.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
cdns.connatix.com |
| whitelisted |
d188578y7fxb.cloudfront.net |
| whitelisted |