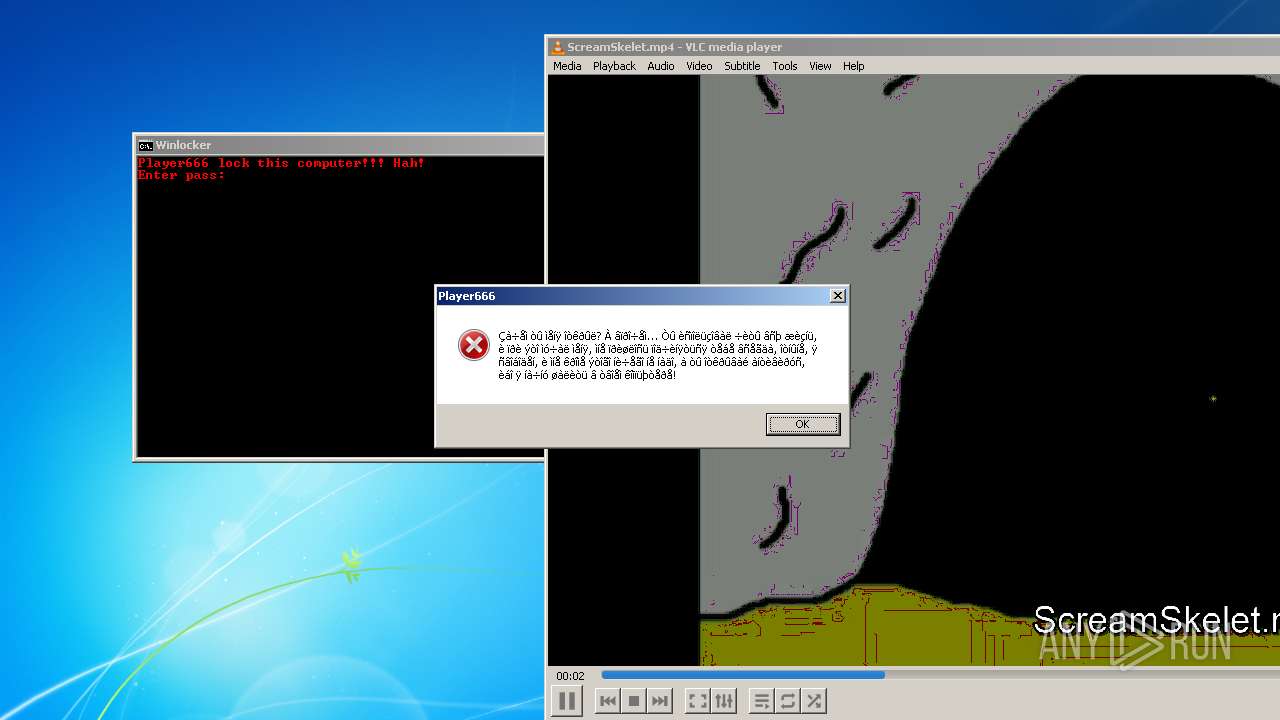
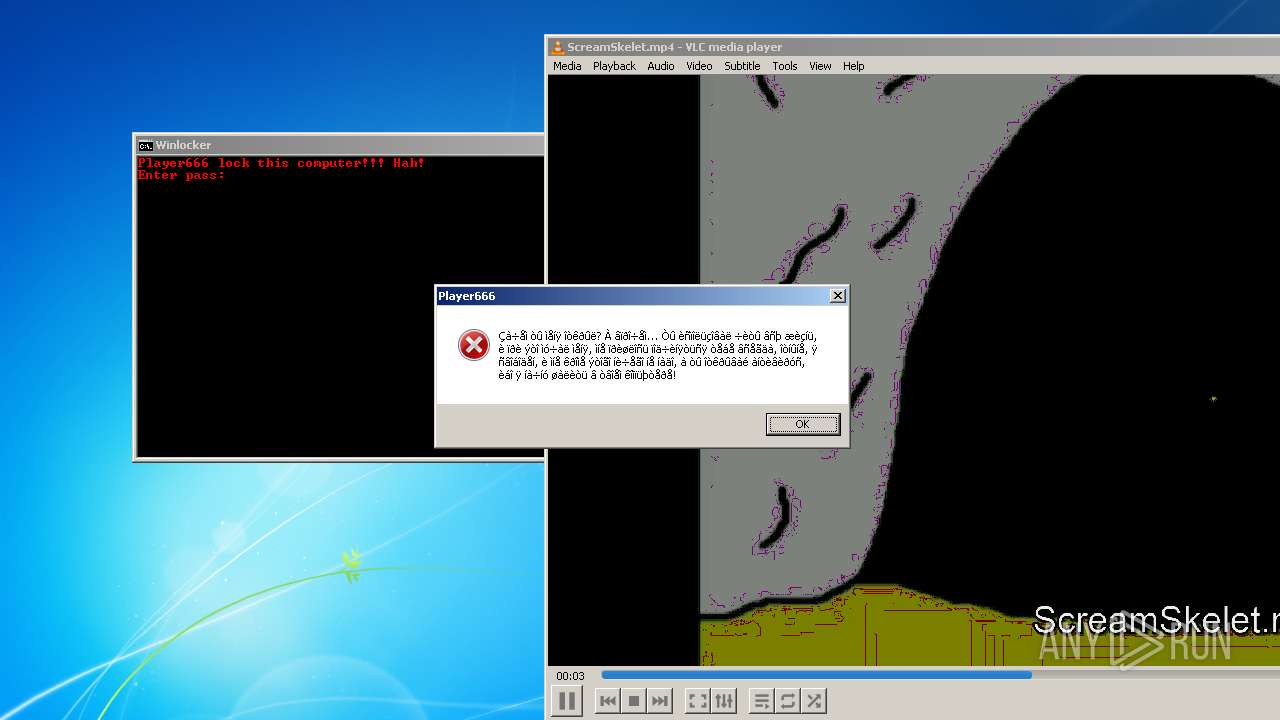
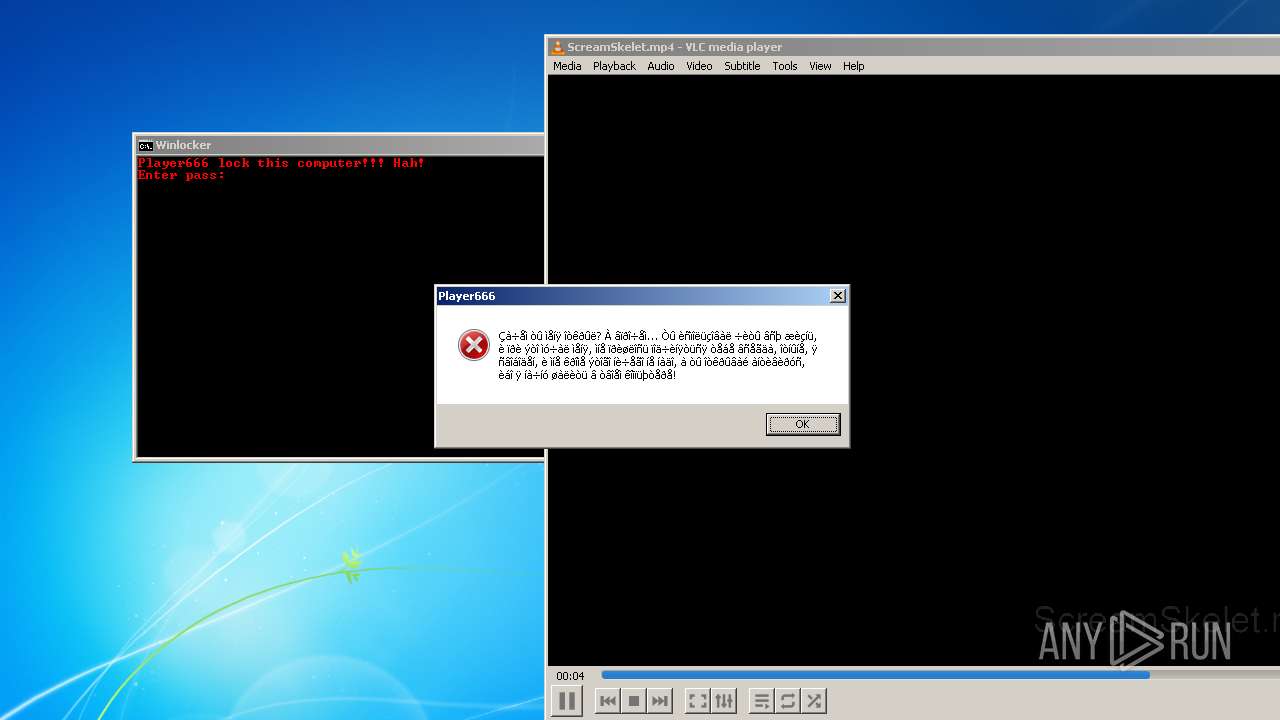
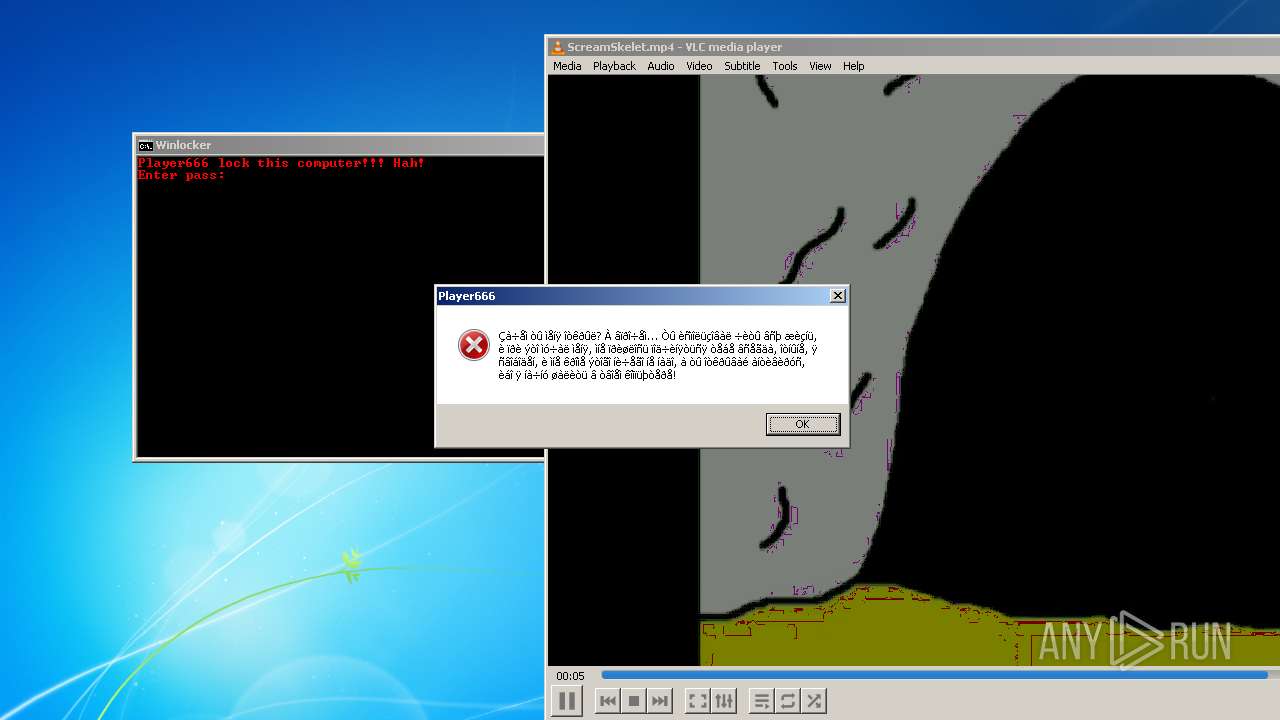
| File name: | Player666.exe |
| Full analysis: | https://app.any.run/tasks/7f8bf4a9-f18e-4bc1-9126-9d4b61c0d1b5 |
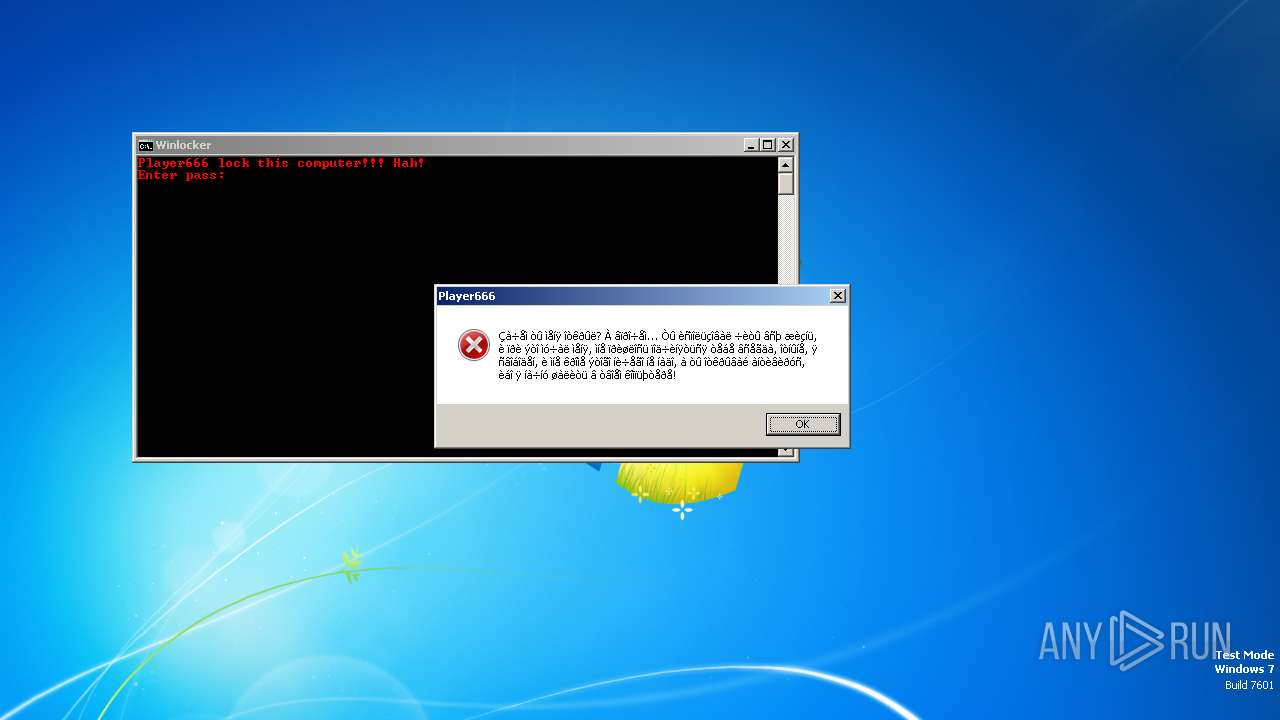
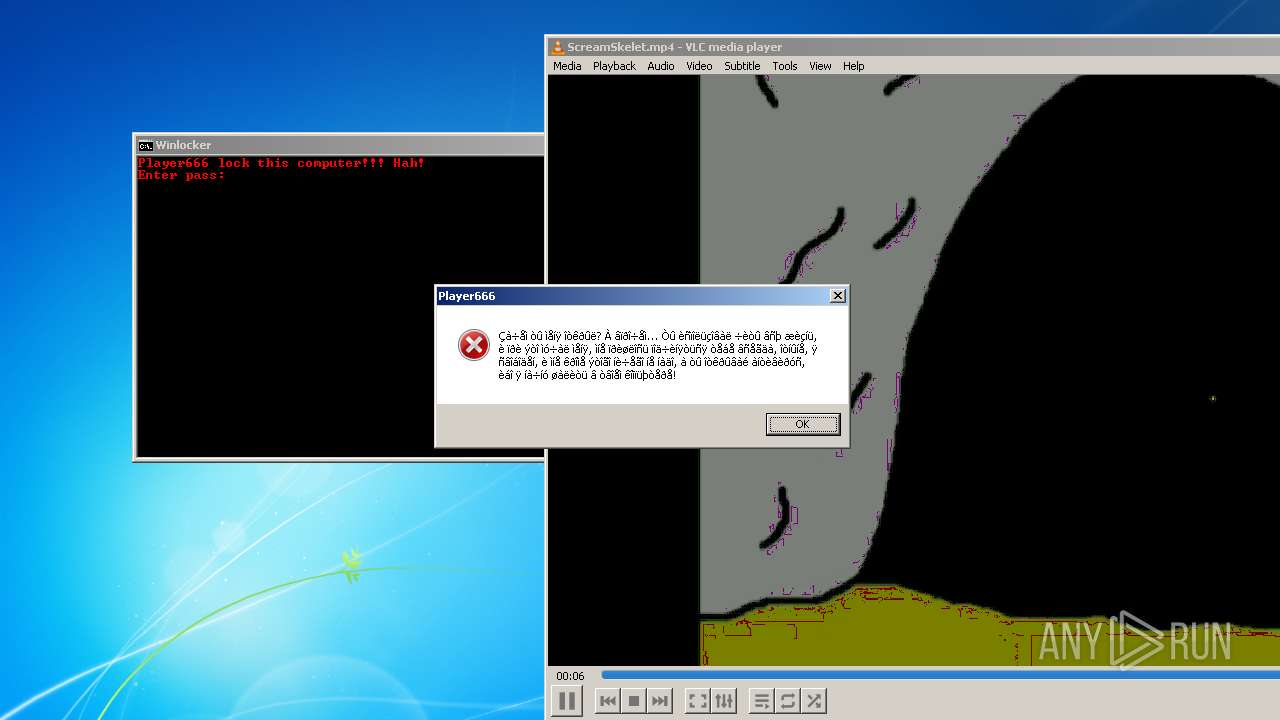
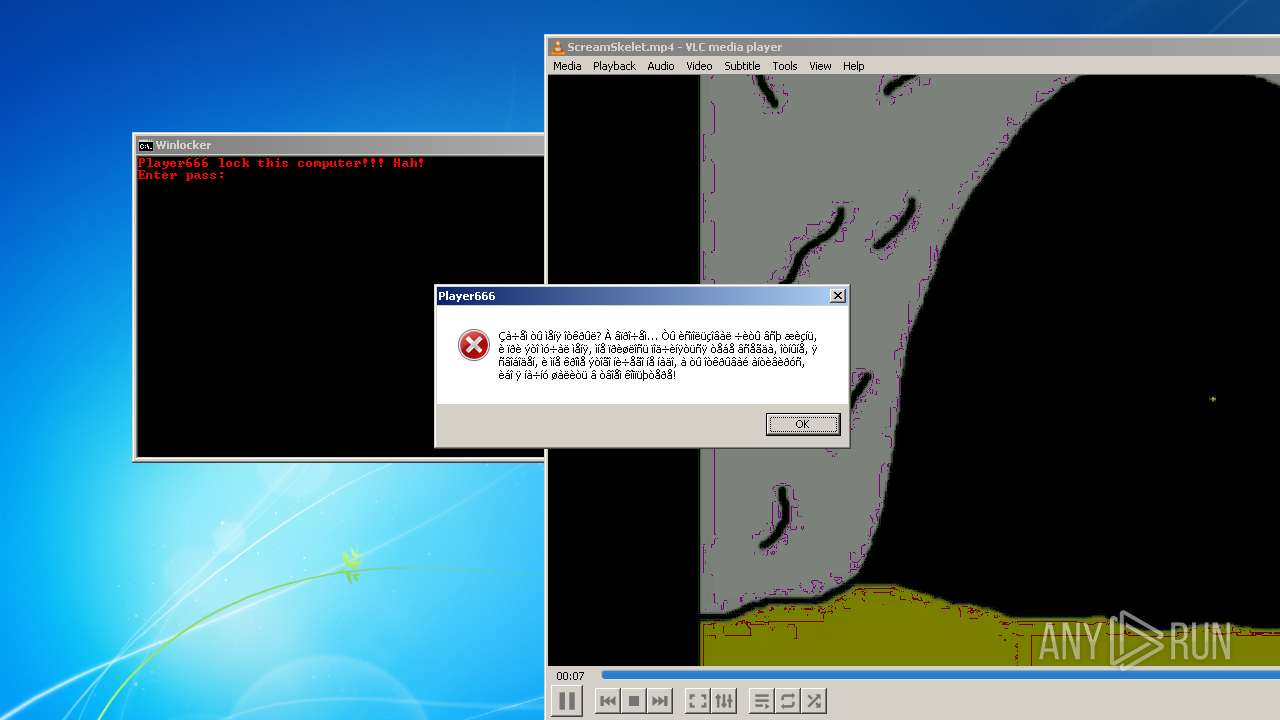
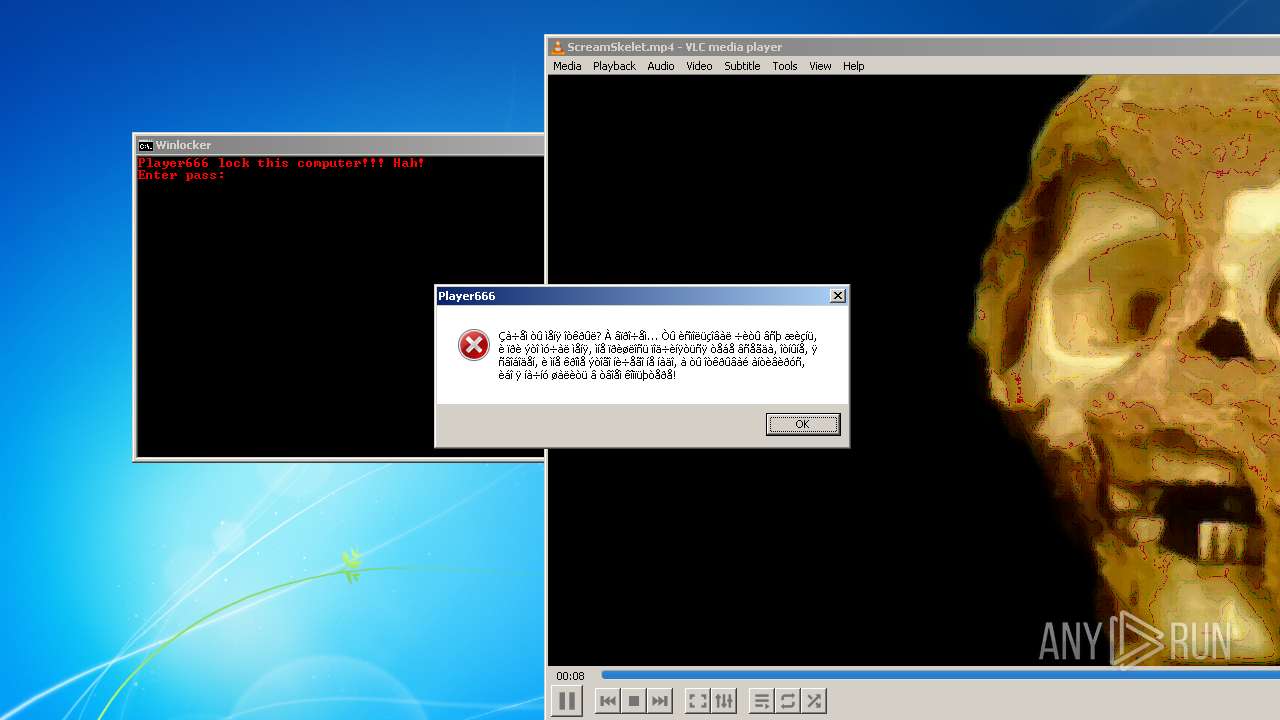
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2024, 17:42:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 13C79343952A9888DE7A341F2DDAAAFB |
| SHA1: | 5E32F77C6E85F0EA87FFA3CC4FC5312E61879F04 |
| SHA256: | C8388626AF83B1D9950E38A3B71CB98E38982329A8E692AA315C6AC73688D565 |
| SSDEEP: | 393216:pP1qpossypSLCy6ooAiinFGxJkUOb3JBzPNQeJPgJ:pPWossMCr9iYeJEzzldQ |
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2032)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Player666.exe (PID: 128)
Executing commands from a ".bat" file
- Player666.exe (PID: 128)
The process executes VB scripts
- Player666.exe (PID: 128)
Reads the Internet Settings
- Player666.exe (PID: 128)
- wscript.exe (PID: 2032)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2072)
INFO
Checks supported languages
- vlc.exe (PID: 2408)
- Player666.exe (PID: 128)
Checks proxy server information
- wscript.exe (PID: 2032)
Create files in a temporary directory
- Player666.exe (PID: 128)
Drops the executable file immediately after the start
- Player666.exe (PID: 128)
Reads the computer name
- Player666.exe (PID: 128)
- vlc.exe (PID: 2408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:04:07 16:39:21+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201728 |
| InitializedDataSize: | 255488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ed60 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
41
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\AppData\Local\Temp\Player666.exe" | C:\Users\admin\AppData\Local\Temp\Player666.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 548 | taskkill /im explorer.exe /f | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Player666.vbs" | C:\Windows\System32\wscript.exe | — | Player666.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2032 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Media.vbs" | C:\Windows\System32\wscript.exe | — | Player666.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
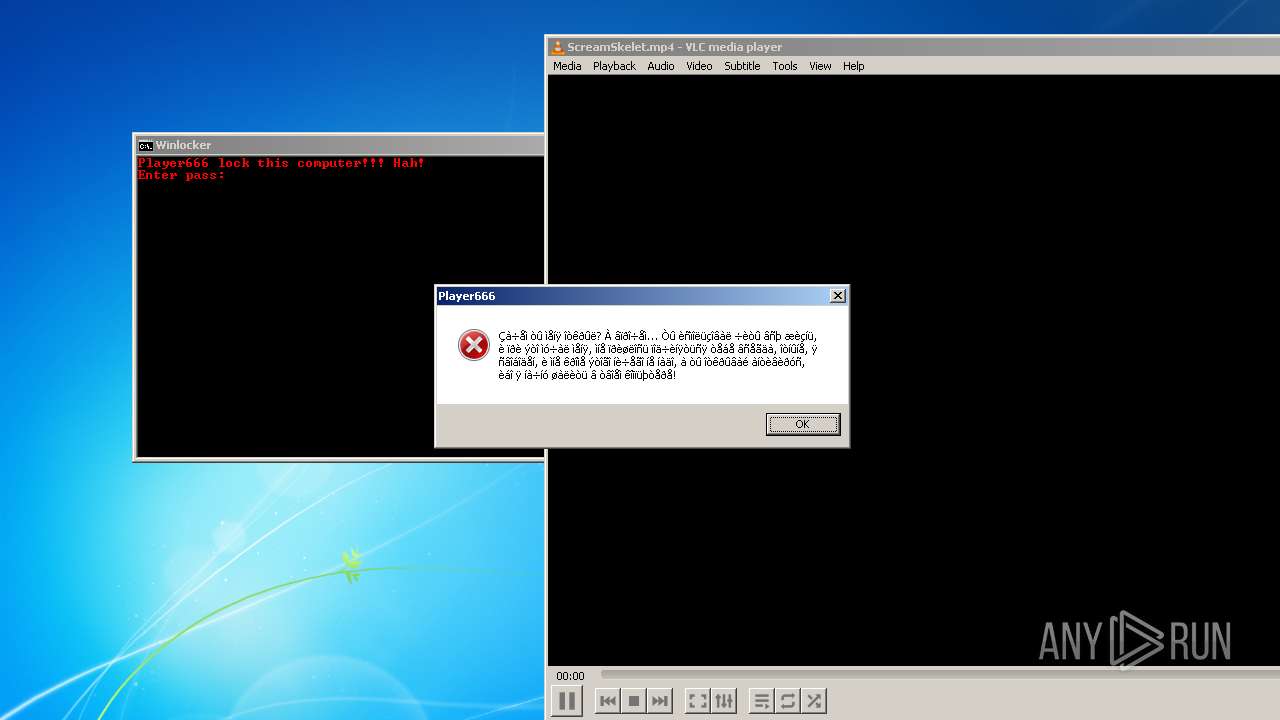
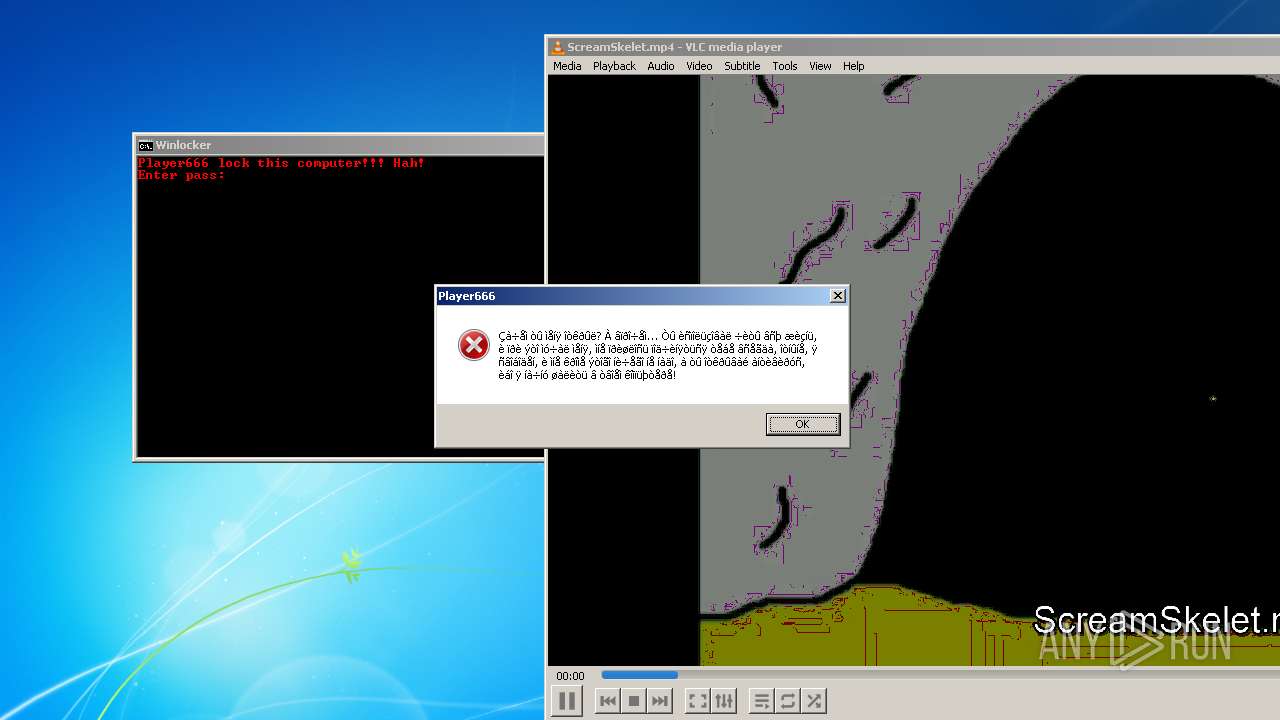
| 2072 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\runn452.bat" " | C:\Windows\System32\cmd.exe | — | Player666.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
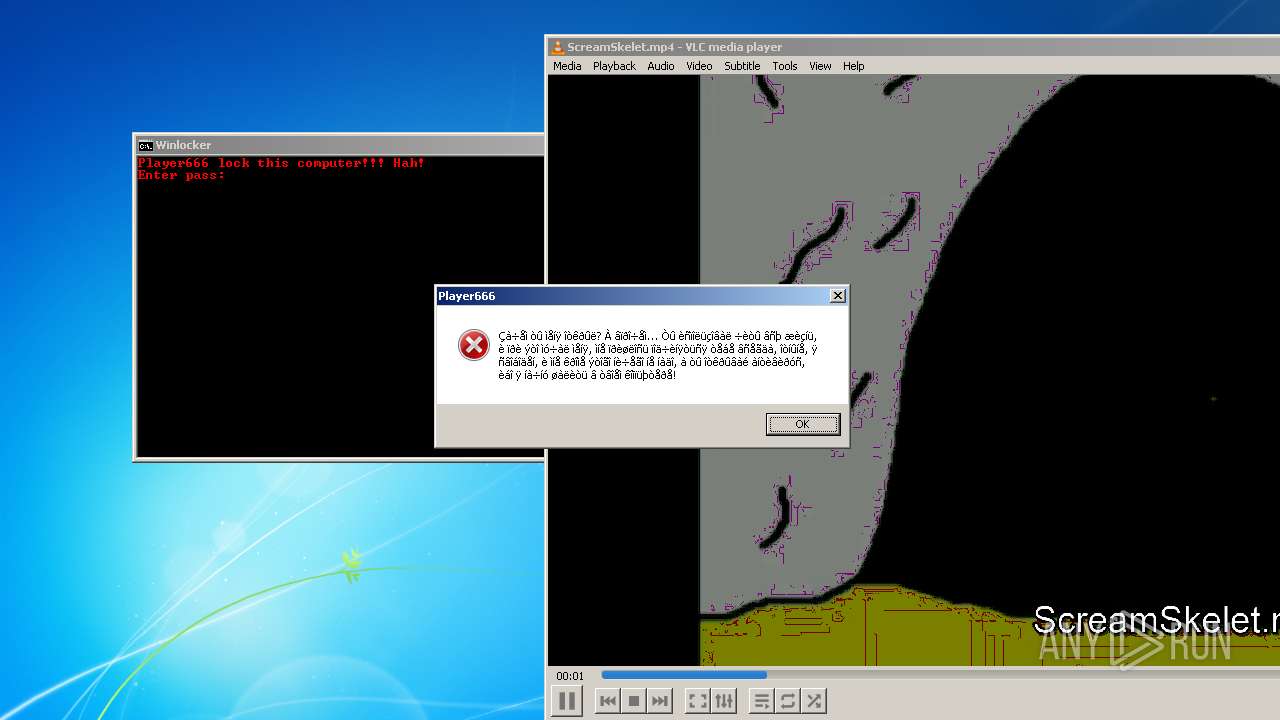
| 2408 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Temp\ScreamSkelet.mp4" | C:\Program Files\VideoLAN\VLC\vlc.exe | Player666.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 3.0.11 Modules
| |||||||||||||||
Total events
3 995
Read events
3 961
Write events
34
Delete events
0
Modification events
| (PID) Process: | (128) Player666.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (128) Player666.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (128) Player666.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (128) Player666.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2408) vlc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Explorer.EXE | |||
| (PID) Process: | (2032) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2032) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2408) vlc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: vlc.exe | |||
| (PID) Process: | (2032) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | LastScreensaverState |
Value: 4 | |||
| (PID) Process: | (2032) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | AutoMetadataCurrentDownloadCount |
Value: 0 | |||
Executable files
2
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 128 | Player666.exe | C:\Users\admin\AppData\Local\Temp\horrormusic.wav | — | |
MD5:— | SHA256:— | |||
| 128 | Player666.exe | C:\Users\admin\AppData\Local\Temp\Media.vbs | text | |
MD5:775369632164AD4F33E1D412CED3FEF3 | SHA256:B0CBE664821F2941D10F33E40EF4C72C9201AB8B77EF96BE3701A8C089CE8B8C | |||
| 2408 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini | text | |
MD5:CC4D53372A0D1029B7ED4D24CAE0E57F | SHA256:A204063E2C2C4E3AD12B5D9689D8016F654A7F45071324FDFA3C71F428416675 | |||
| 128 | Player666.exe | C:\Users\admin\AppData\Local\Temp\runn452.bat | text | |
MD5:117D0A37D5D05F10571FFEB9C8F022CB | SHA256:E4514E268F5D8DB7B7BFA51C3CDCC3E01918080FC0B10FD7AA3D12299167FA6F | |||
| 128 | Player666.exe | C:\Users\admin\AppData\Local\Temp\ScreamSkelet.mp4 | binary | |
MD5:538F5B8E3F1A8FD98456F2DEB67EA40D | SHA256:9A11A40DAB740634EC16F0D631278CBC0BAB5706CBF9AEAD72509A9A191DE9A7 | |||
| 128 | Player666.exe | C:\Users\admin\AppData\Local\Temp\Player666.vbs | text | |
MD5:EC3D556B033761194D0C81DDAB3403C4 | SHA256:0DF5ABD388CF816B28971C0DFD3F012DE58F063B374F30E855C6ABB20773A291 | |||
| 2408 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.Hp2408 | text | |
MD5:CC4D53372A0D1029B7ED4D24CAE0E57F | SHA256:A204063E2C2C4E3AD12B5D9689D8016F654A7F45071324FDFA3C71F428416675 | |||
| 2408 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.lock | text | |
MD5:BAFB8A663A2D55D4C58F9F2D59F1642F | SHA256:351D7B7E03318DD93642964AC3602F210E153221540D14000B30094697DF7C42 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Threats
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=i686-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x86/contrib/i686-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: opening config file (C:\Users\admin\AppData\Roaming\vlc\vlcrc)
|